| File name: | P.O. #20161-38499.iso |
| Full analysis: | https://app.any.run/tasks/50506911-de01-4f77-9312-7e3111cebb04 |
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | October 14, 2019, 22:05:58 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
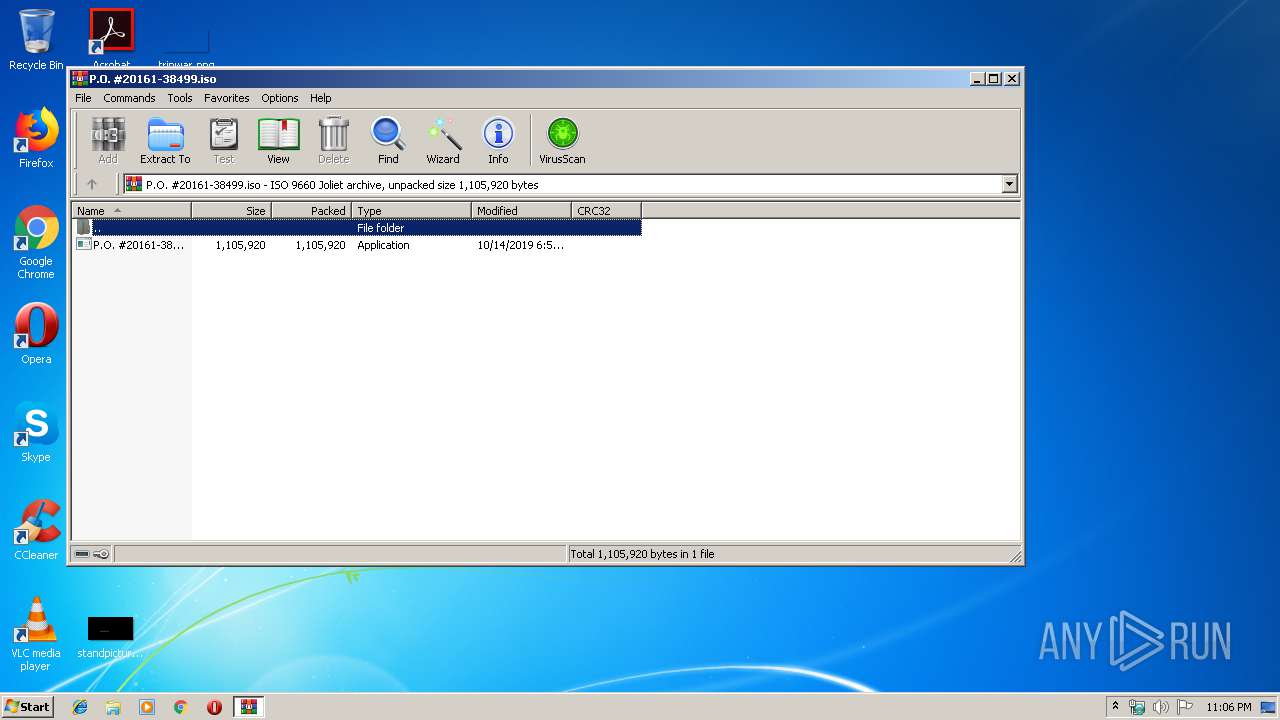
| MIME: | application/x-iso9660-image |
| File info: | ISO 9660 CD-ROM filesystem data 'P.O. #20161-38499' |
| MD5: | E18FCF4748814D4E190DD431C7131D35 |
| SHA1: | 3AE17D33C8AAAB1EB3D68B888B8C41A47565681A |
| SHA256: | A33F542DDA21BE1EF2A55D9A429E7E6F831FD0D56DD86A99548F903DF518960B |
| SSDEEP: | 12288:s+T2Wu3Lba5HRGvXYi8AR90VIruUdz9HoDB+:FTfunIEvT8w90jgJmB |
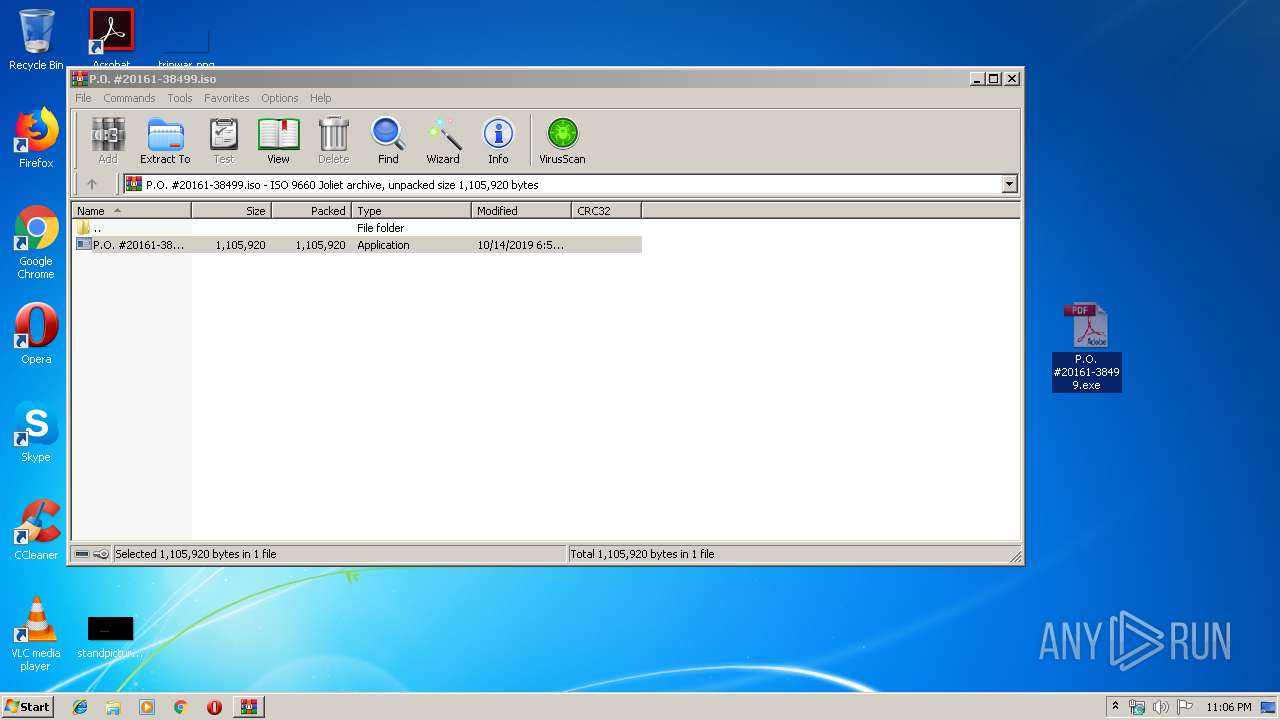
MALICIOUS
Application was dropped or rewritten from another process
- P.O. #20161-38499.exe (PID: 1756)
- P.O. #20161-38499.exe (PID: 3976)
AGENTTESLA was detected
- P.O. #20161-38499.exe (PID: 3976)
Actions looks like stealing of personal data
- P.O. #20161-38499.exe (PID: 3976)
SUSPICIOUS
Starts CMD.EXE for commands execution
- P.O. #20161-38499.exe (PID: 1756)
Application launched itself
- P.O. #20161-38499.exe (PID: 1756)
Reads Windows Product ID
- P.O. #20161-38499.exe (PID: 3976)
Reads Environment values
- P.O. #20161-38499.exe (PID: 3976)
Creates files in the user directory
- P.O. #20161-38499.exe (PID: 3976)
Reads the cookies of Google Chrome
- P.O. #20161-38499.exe (PID: 3976)
Reads the cookies of Mozilla Firefox
- P.O. #20161-38499.exe (PID: 3976)
Checks for external IP
- P.O. #20161-38499.exe (PID: 3976)
Connects to SMTP port
- P.O. #20161-38499.exe (PID: 3976)
INFO
Manual execution by user
- P.O. #20161-38499.exe (PID: 1756)
Reads settings of System Certificates
- P.O. #20161-38499.exe (PID: 3976)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .atn | | | Photoshop Action (37.5) |
|---|---|---|
| .gmc | | | Game Music Creator Music (8.4) |
| .abr | | | Adobe PhotoShop Brush (7.5) |
EXIF
ISO
| System: | Win32 |
|---|---|
| VolumeName: | P.O. #20161-38499 |
| VolumeBlockCount: | 570 |
| VolumeBlockSize: | 2048 |
| RootDirectoryCreateDate: | 2019:10:14 13:55:09+08:00 |
| Software: | PowerISO |
| VolumeCreateDate: | 2019:10:14 13:55:09.00+08:00 |
| VolumeModifyDate: | 2019:10:14 13:55:09.00+08:00 |
Composite
| VolumeSize: | 1140 kB |
|---|
Total processes
39
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 504 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\P.O. #20161-38499.iso" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 1756 | "C:\Users\admin\Desktop\P.O. #20161-38499.exe" | C:\Users\admin\Desktop\P.O. #20161-38499.exe | — | explorer.exe | |||||||||||
User: admin Company: @NPMK:;BM:7;8HA<F; Integrity Level: MEDIUM Description: DN9NP7K7@HE=DJ@CF7; Exit code: 0 Version: 7.11.15.18 Modules
| |||||||||||||||
| 3976 | "C:\Users\admin\Desktop\P.O. #20161-38499.exe" | C:\Users\admin\Desktop\P.O. #20161-38499.exe | P.O. #20161-38499.exe | ||||||||||||
User: admin Company: @NPMK:;BM:7;8HA<F; Integrity Level: MEDIUM Description: DN9NP7K7@HE=DJ@CF7; Exit code: 0 Version: 7.11.15.18 Modules
| |||||||||||||||
| 4048 | "C:\Windows\System32\cmd.exe" /C type nul > "C:\Users\admin\Desktop\P.O. #20161-38499.exe:Zone.Identifier" | C:\Windows\System32\cmd.exe | — | P.O. #20161-38499.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
614
Read events
574
Write events
40
Delete events
0
Modification events
| (PID) Process: | (504) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (504) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (504) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (504) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\P.O. #20161-38499.iso | |||
| (PID) Process: | (504) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (504) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (504) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (504) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1756) P.O. #20161-38499.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1756) P.O. #20161-38499.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
0
Suspicious files
1
Text files
0
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 504 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa504.29293\P.O. #20161-38499.exe | — | |
MD5:— | SHA256:— | |||
| 3976 | P.O. #20161-38499.exe | C:\Users\admin\AppData\Roaming\tousxan1.qi2\Chrome\Default\Cookies | — | |
MD5:— | SHA256:— | |||
| 3976 | P.O. #20161-38499.exe | C:\Users\admin\AppData\Roaming\tousxan1.qi2\Firefox\Profiles\qldyz51w.default\cookies.sqlite | — | |
MD5:— | SHA256:— | |||
| 3976 | P.O. #20161-38499.exe | C:\Users\admin\AppData\Local\Temp\637066912609873750_a38a522f-e2d6-4459-a6dc-3c29c9afc669.db | sqlite | |
MD5:— | SHA256:— | |||
| 3976 | P.O. #20161-38499.exe | C:\Users\admin\AppData\Roaming\tousxan1.qi2.zip | compressed | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
3
DNS requests
2
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3976 | P.O. #20161-38499.exe | GET | 200 | 18.205.71.63:80 | http://checkip.amazonaws.com/ | US | text | 13 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3976 | P.O. #20161-38499.exe | 217.70.178.9:587 | mail.gandi.net | GANDI SAS | FR | malicious |
3976 | P.O. #20161-38499.exe | 18.205.71.63:80 | checkip.amazonaws.com | — | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
checkip.amazonaws.com |
| malicious |
mail.gandi.net |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3976 | P.O. #20161-38499.exe | A Network Trojan was detected | MALWARE [PTsecurity] AgentTesla IP Check |
3976 | P.O. #20161-38499.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
3976 | P.O. #20161-38499.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
2 ETPRO signatures available at the full report