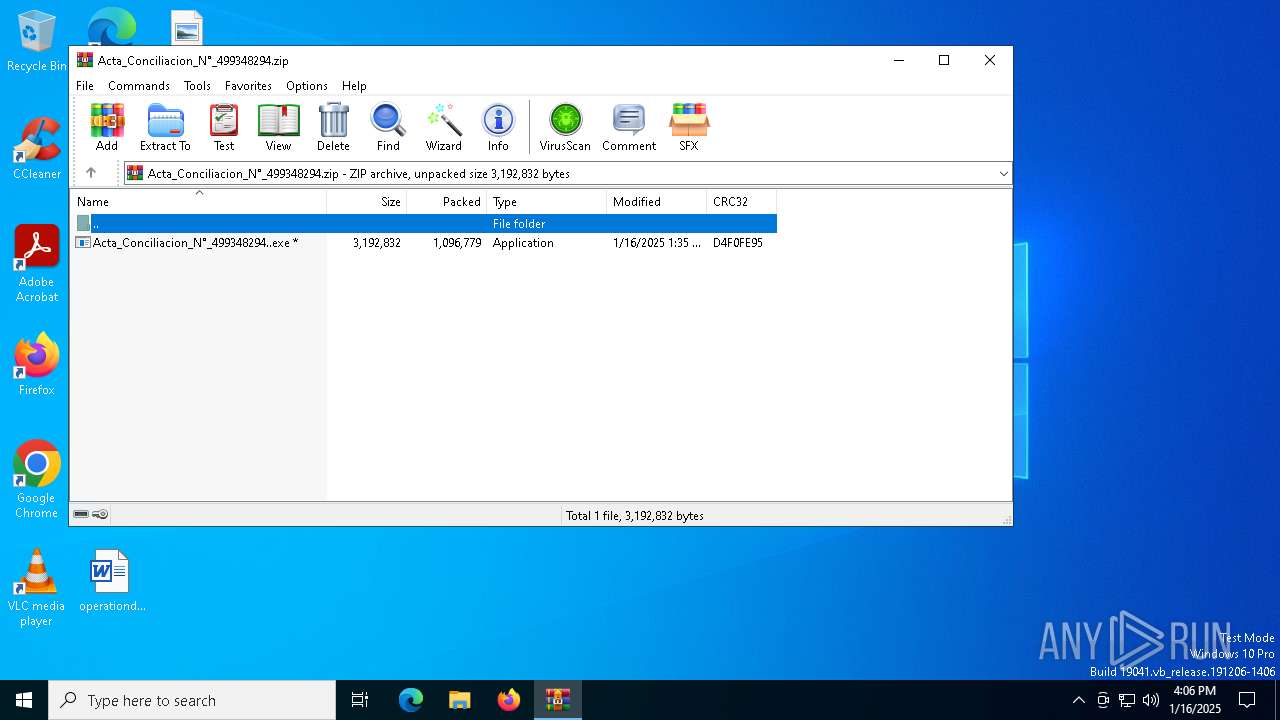
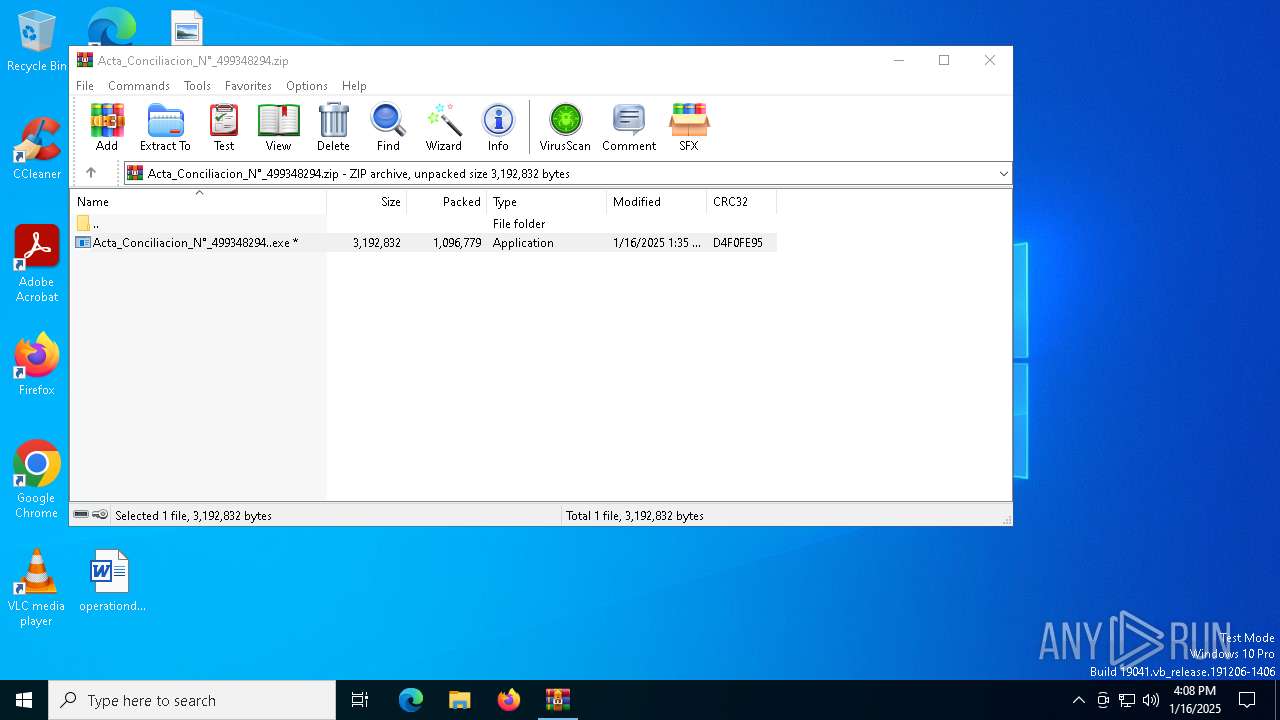
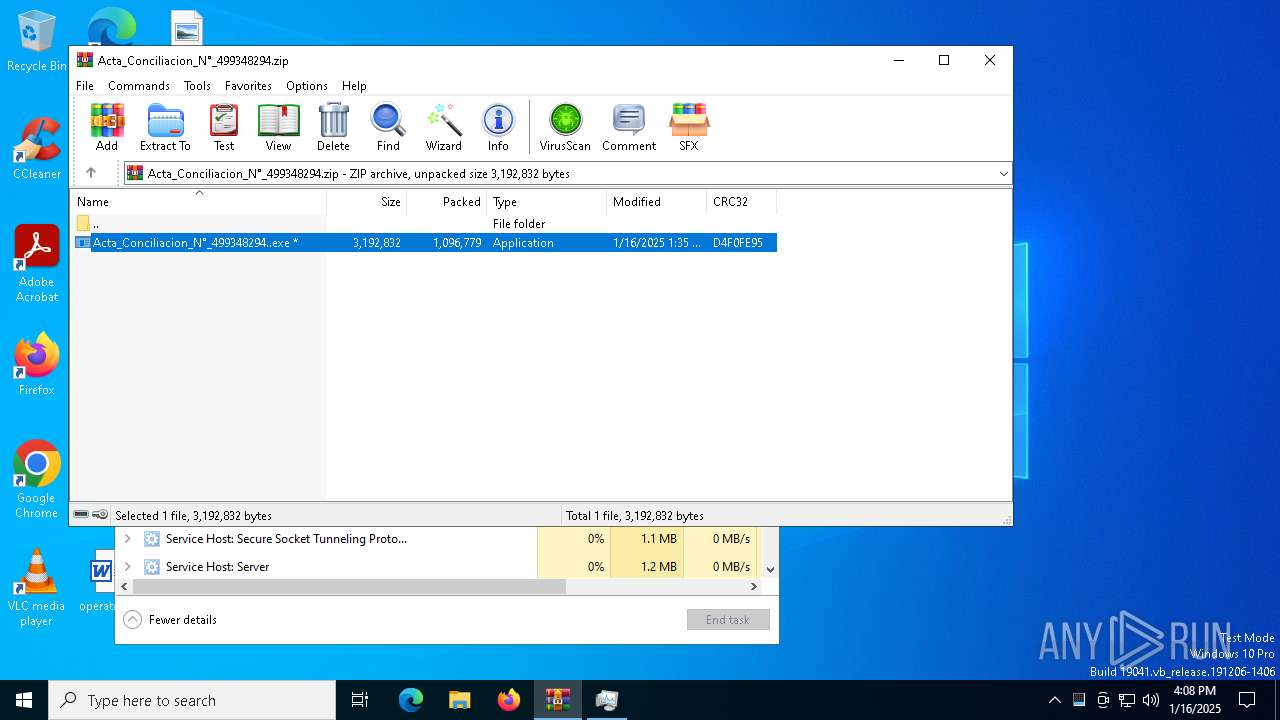
| File name: | Acta_Conciliacion_N°_499348294.zip |
| Full analysis: | https://app.any.run/tasks/606d422a-8b48-4bd2-a24c-6f66eb0ed198 |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | January 16, 2025, 16:05:25 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
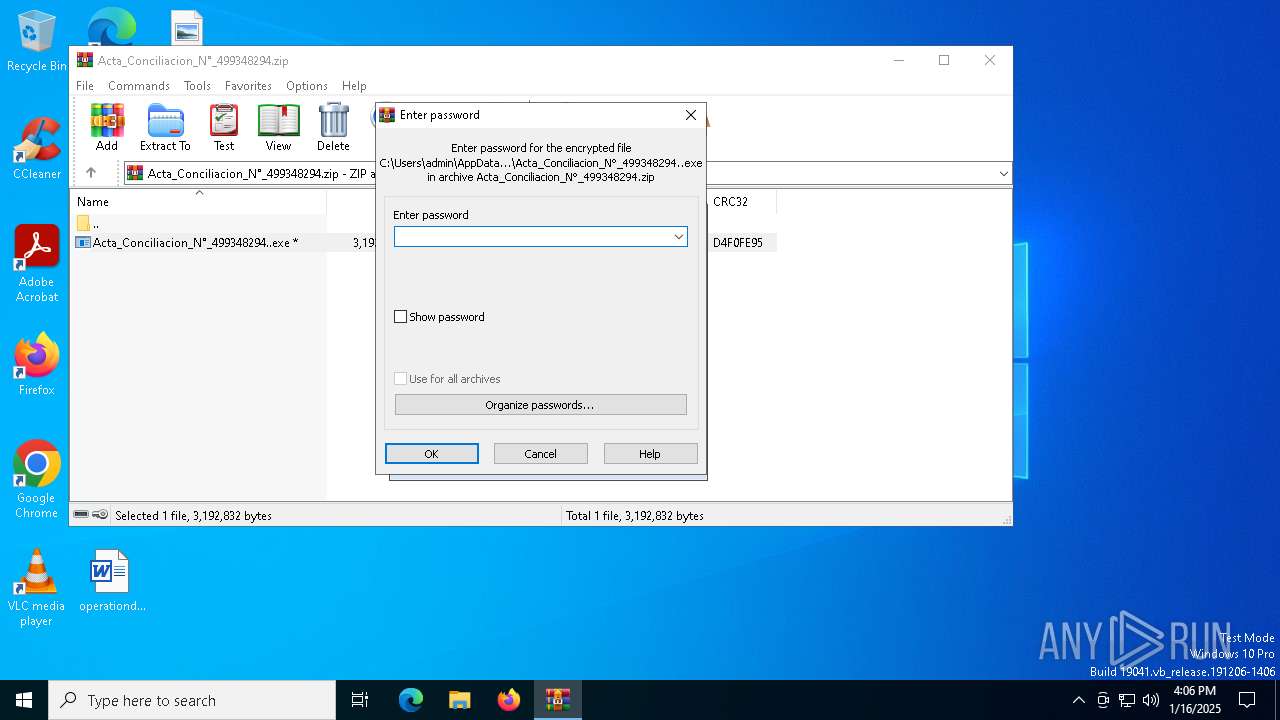
| File info: | Zip archive data, at least v2.0 to extract, compression method=AES Encrypted |
| MD5: | E828163B0AC94389B5848112B3CB862B |
| SHA1: | 06138A95E1B3749A6A03538A9DF41B0C69A2F5EB |
| SHA256: | A32F70CB6DF6D19C9464A586DE85176F3F7D5536DF698DD77D79D1BEB4D22E18 |
| SSDEEP: | 49152:Jl0TfiaLFH4a+w1U748eLj7LgCC9PJyg/71GkOjUKnEilMTL8/ClKwJcjF4Oip6d:Jler65uXgX9PoiUlnt6TWmI4O48GGgD6 |
MALICIOUS
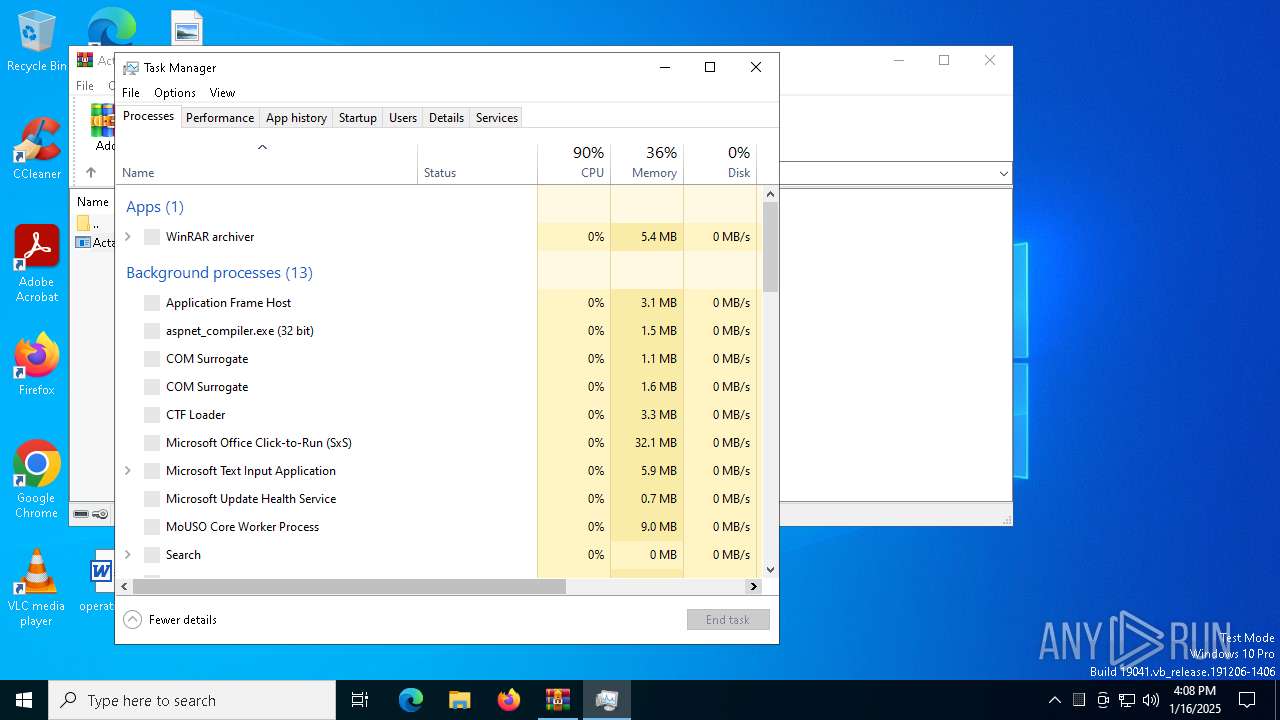
Starts Visual C# compiler
- Acta_Conciliacion_N°_499348294..exe (PID: 3488)
Changes the autorun value in the registry
- Acta_Conciliacion_N°_499348294..exe (PID: 3488)
DCRAT mutex has been found
- csc.exe (PID: 2408)
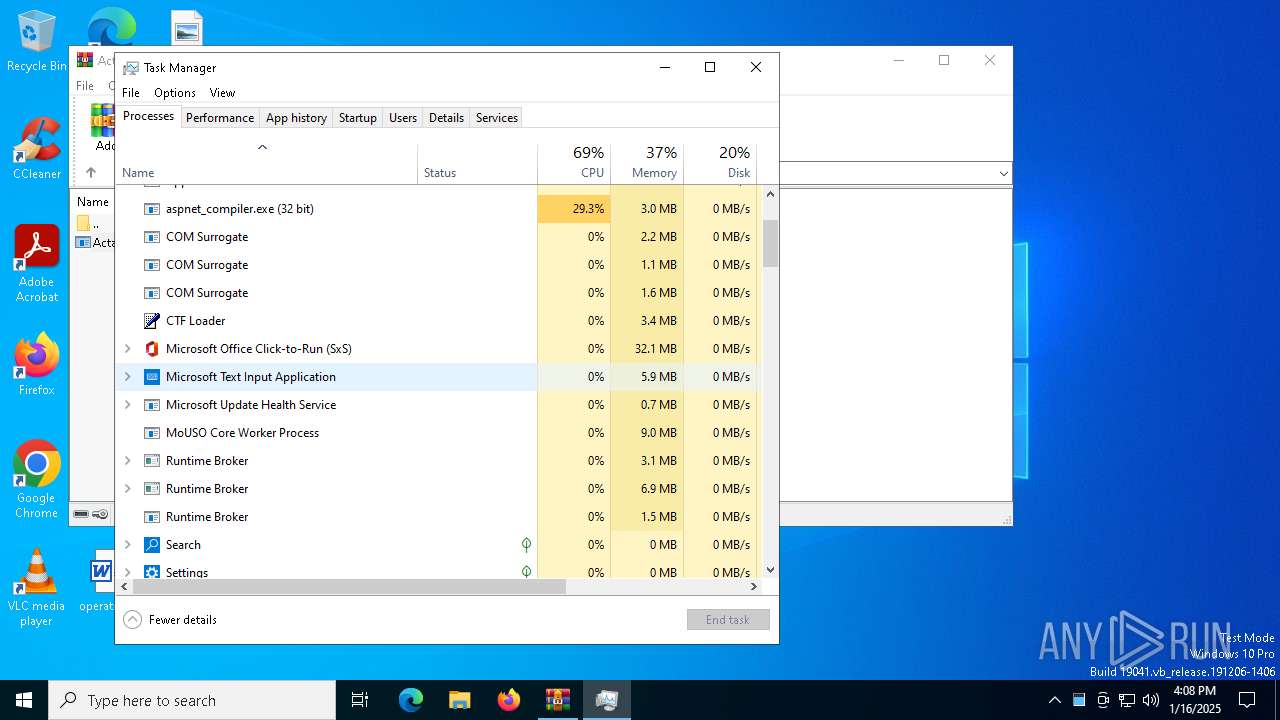
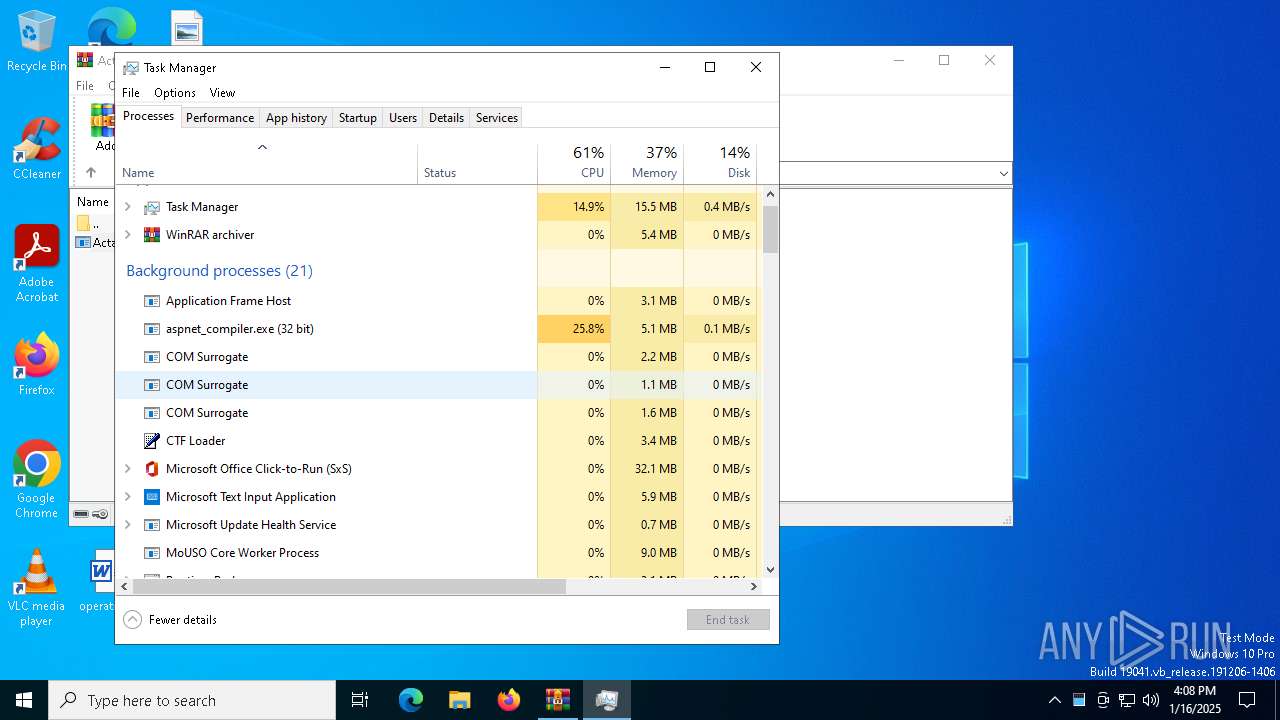
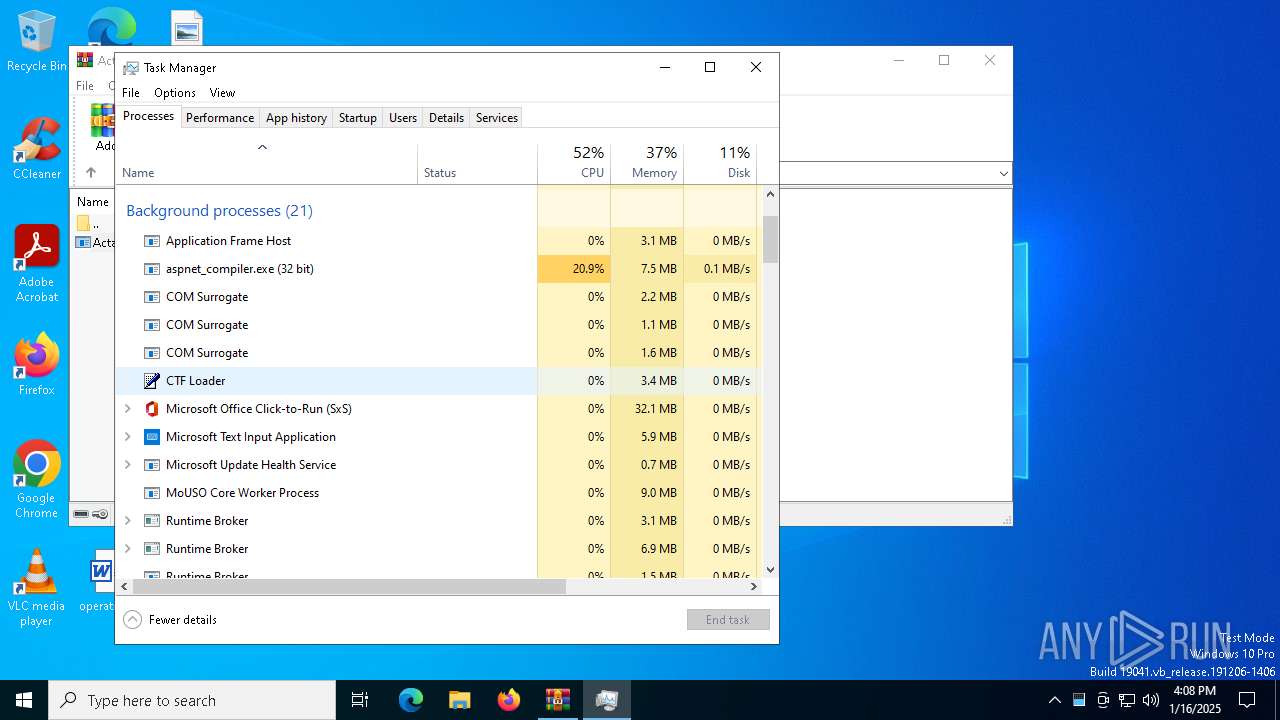
ASYNCRAT has been detected (SURICATA)
- csc.exe (PID: 2408)
- aspnet_compiler.exe (PID: 5212)
ASYNCRAT has been detected (YARA)
- csc.exe (PID: 2408)
- aspnet_compiler.exe (PID: 5212)
ASYNCRAT has been detected (MUTEX)
- aspnet_compiler.exe (PID: 5212)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 3052)
Contacting a server suspected of hosting an CnC
- csc.exe (PID: 2408)
- aspnet_compiler.exe (PID: 5212)
Connects to unusual port
- csc.exe (PID: 2408)
- aspnet_compiler.exe (PID: 5212)
Starts CMD.EXE for commands execution
- aspnet_compiler.exe (PID: 5212)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 2828)
Executing commands from a ".bat" file
- aspnet_compiler.exe (PID: 5212)
INFO
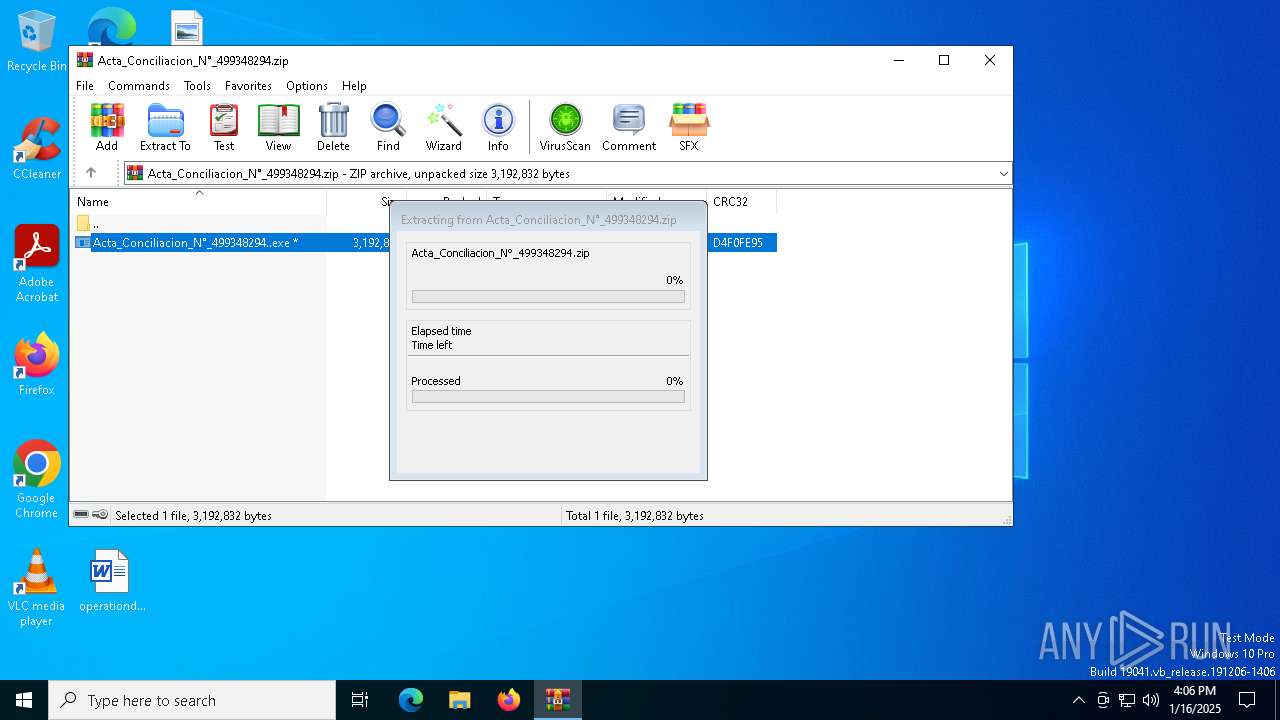
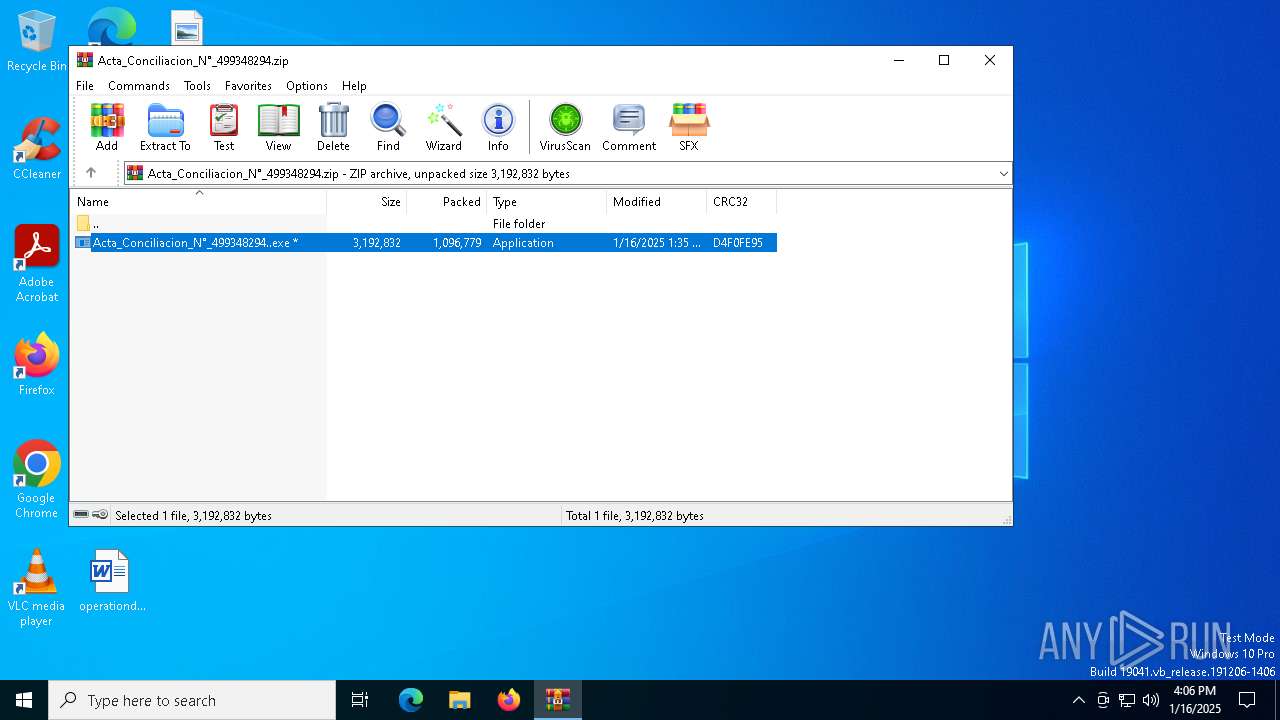
The process uses the downloaded file
- WinRAR.exe (PID: 3052)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3052)
Checks supported languages
- csc.exe (PID: 2408)
- Acta_Conciliacion_N°_499348294..exe (PID: 3488)
- aspnet_compiler.exe (PID: 5212)
Reads the computer name
- csc.exe (PID: 2408)
- aspnet_compiler.exe (PID: 5212)
Reads the machine GUID from the registry
- csc.exe (PID: 2408)
- aspnet_compiler.exe (PID: 5212)
Reads the software policy settings
- csc.exe (PID: 2408)
- aspnet_compiler.exe (PID: 5212)
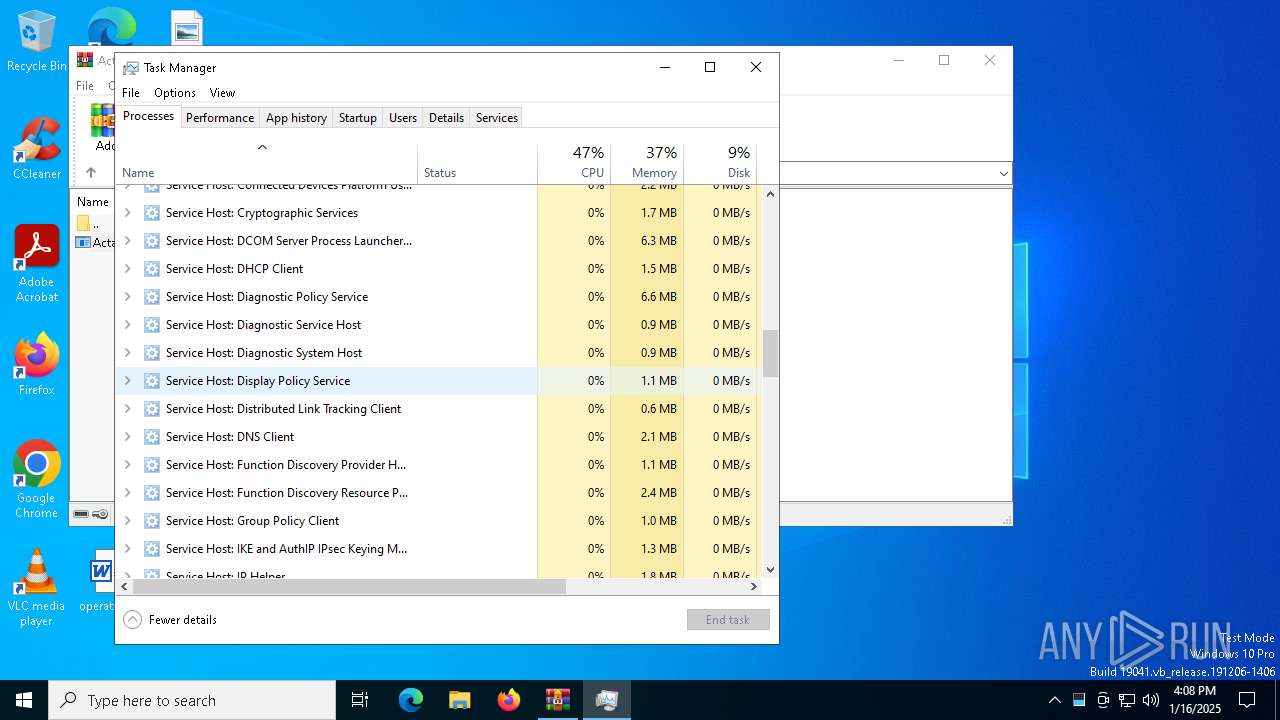
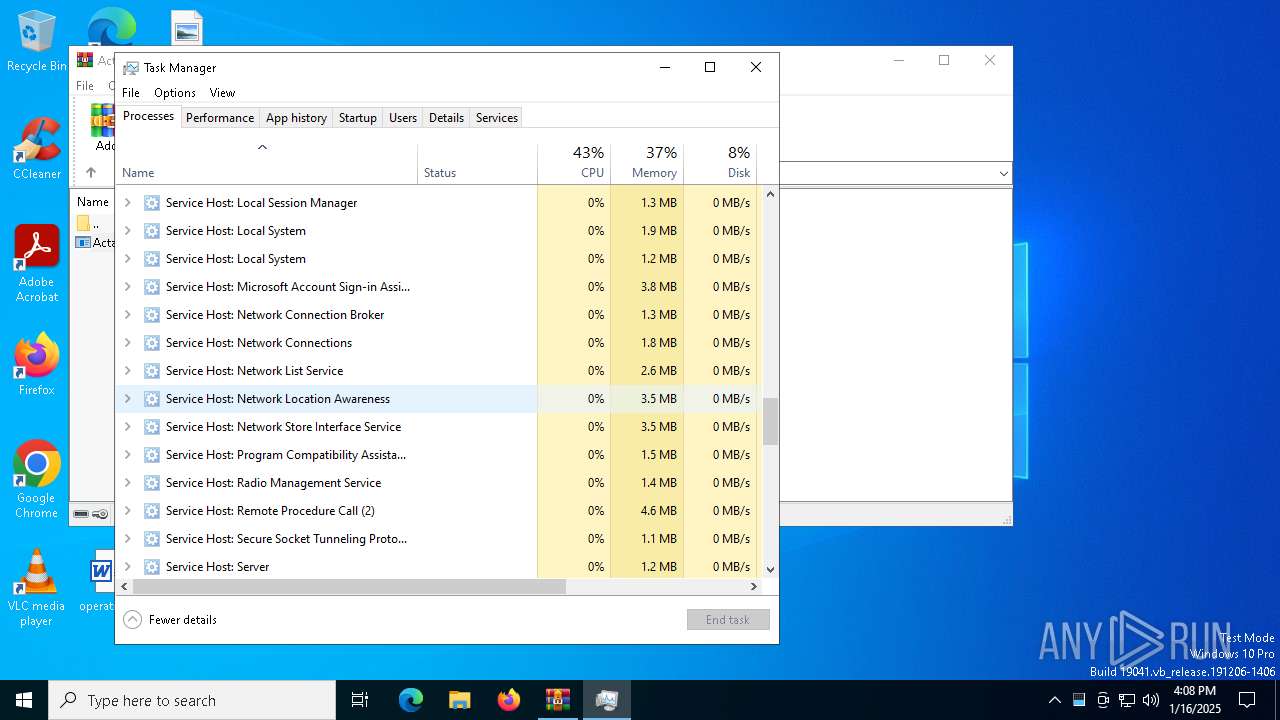
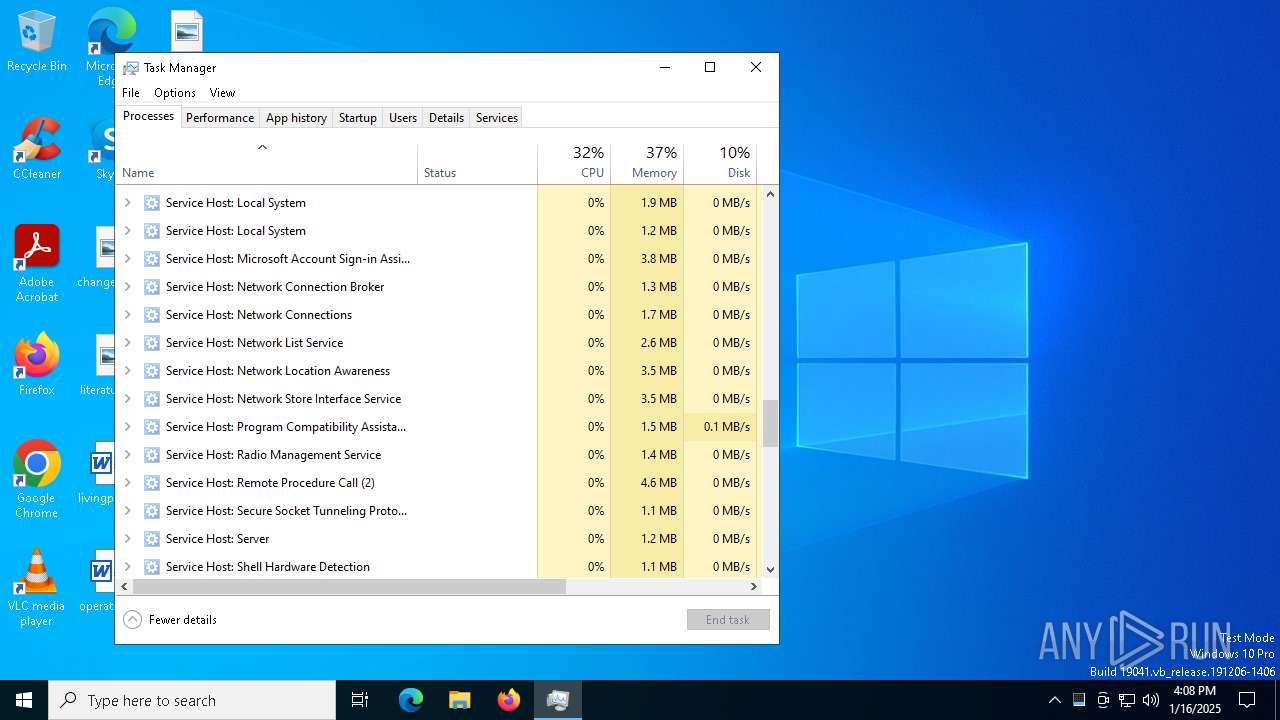
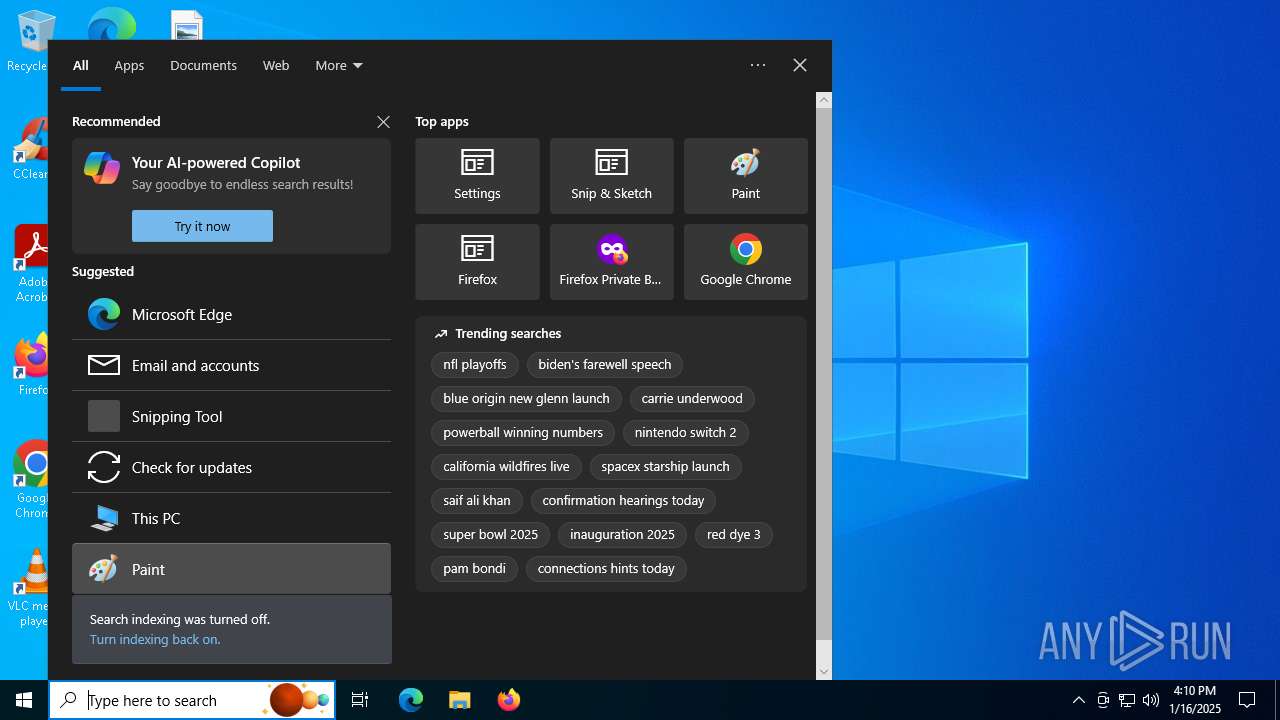
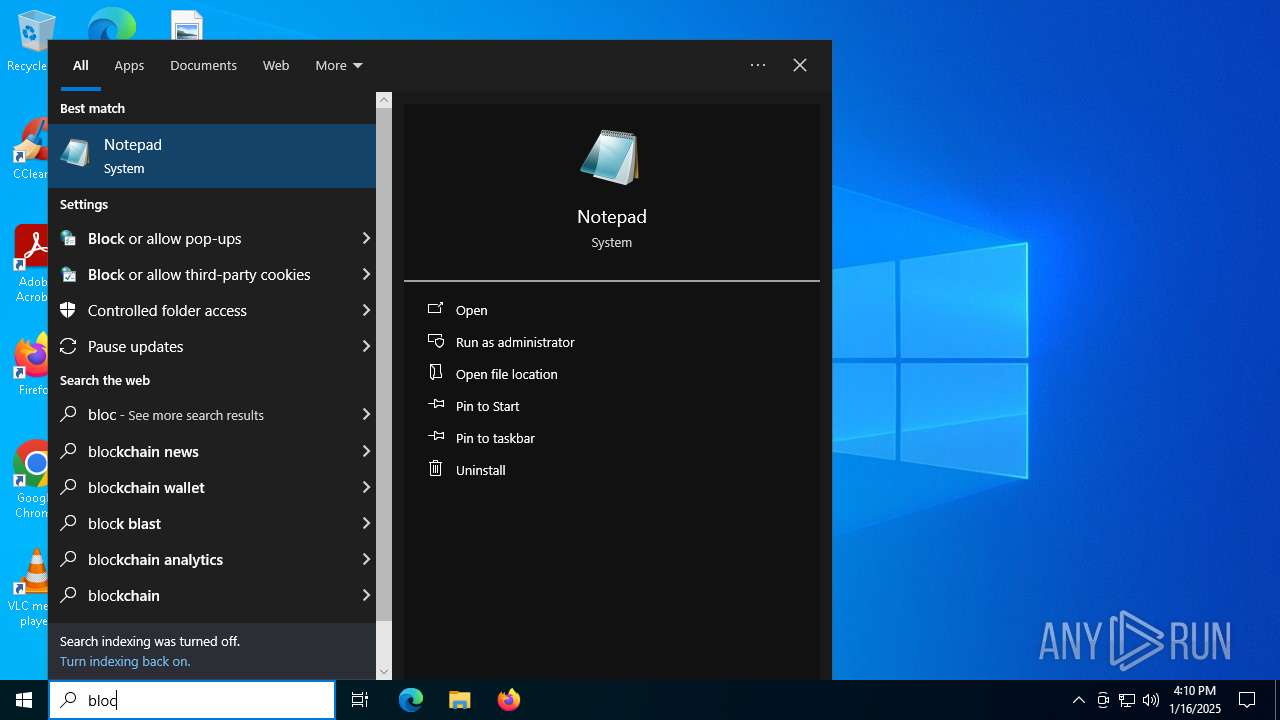
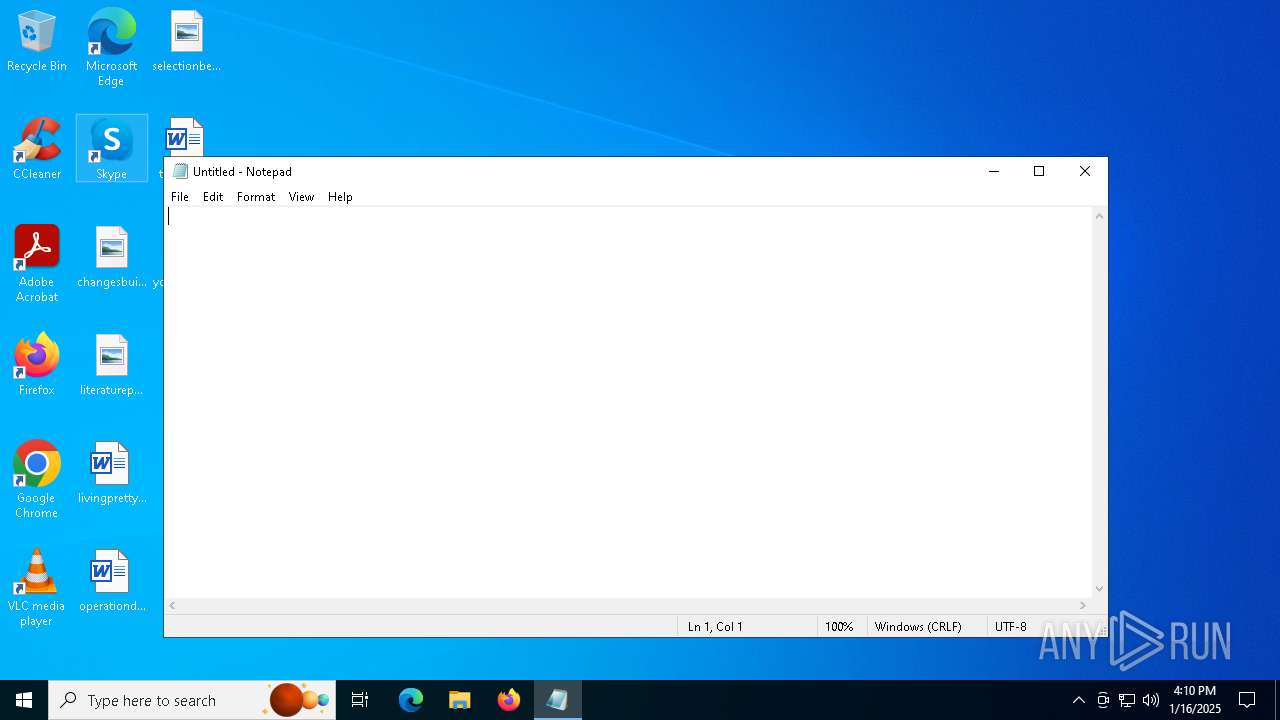
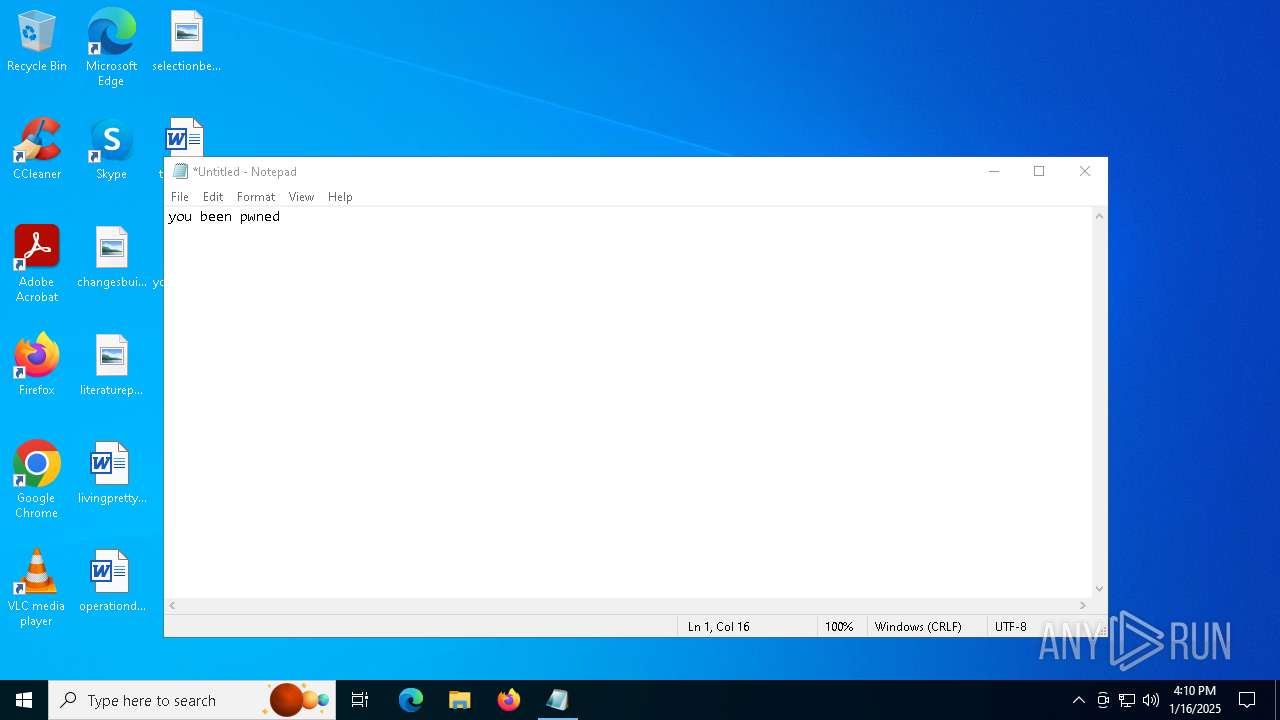
Manual execution by a user
- Taskmgr.exe (PID: 8)
- Taskmgr.exe (PID: 4132)
- notepad.exe (PID: 4648)
Reads security settings of Internet Explorer
- Taskmgr.exe (PID: 4132)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
AsyncRat
(PID) Process(2408) csc.exe
C2 (1)2201.mysynology.net
Ports (2)8329
2201
Version1.0.7
Options
AutoRunfalse
MutexDcRatMutex_qwqdanchun
InstallFolder%AppData%
Certificates
Cert1MIICMDCCAZmgAwIBAgIVAPdJPjCx7pYvZ/1H2FuVvfr12RcjMA0GCSqGSIb3DQEBDQUAMGQxFTATBgNVBAMMDERjUmF0IFNlcnZlcjETMBEGA1UECwwKcXdxZGFuY2h1bjEcMBoGA1UECgwTRGNSYXQgQnkgcXdxZGFuY2h1bjELMAkGA1UEBwwCU0gxCzAJBgNVBAYTAkNOMB4XDTIxMTIwOTIwNDY0MFoXDTMyMDkxNzIwNDY0MFowEDEOMAwGA1UEAwwFRGNSYXQwgZ8wDQYJKoZIhvcNAQEBBQADgY0A...
Server_SignatureH0QYyQvWpAITuIKRrbjjWItiPBCLrrmljvfKrEegwJEfM3iPZvTxk9etEAeQFv+wGI1G1v0kCoAiWciJVvxiazxk+4frZMl4RuRNe7twWLzB2Zm6p9W8HaZ4yZzSD2ecQHKrG3yApaIs2UDEiH2tRAaOj7gwFaqGDlq3CRvxKHU=
Keys
AES0dbec3e9df85bb19d9d656863f8b9bf2f55a63212e8c06431b7f2174de1afe6e
SaltDcRatByqwqdanchun
(PID) Process(5212) aspnet_compiler.exe
C2 (1)bypass-asyn.4cloud.click
Ports (1)8887
Version| nelsontriana980
Options
AutoRunfalse
MutexAsyncMutex_654I8OkPnk
InstallFolder%AppData%
Certificates
Cert1MIIE8jCCAtqgAwIBAgIQAPeWQ4YJ3MvReCGwLzn7rTANBgkqhkiG9w0BAQ0FADAaMRgwFgYDVQQDDA9Bc3luY1JBVCBTZXJ2ZXIwIBcNMjIwNDI1MDA0MTA5WhgPOTk5OTEyMzEyMzU5NTlaMBoxGDAWBgNVBAMMD0FzeW5jUkFUIFNlcnZlcjCCAiIwDQYJKoZIhvcNAQEBBQADggIPADCCAgoCggIBAKT9nYYTjYTZhY+g1tekZ8/F29gsEIDgf/8odvCbCmYKGGZZi2yND9NjtBXEMANM9PAXCyMapGva...
Server_SignatureBb1S+ur8QT7rjD7qN6qbN/59FeemD8NW4hX1PXf5hYVLmqMBxKoc27YQSKQKHXajRXamhdIWf72L6S++lWuv5iro9PEsAxWJZZrtXd4F1hMrSVmulB4kX1ChKiCn/xkSuN8gc44chdSCkR/comwoUh2sN6DNJ0Vqki0JV1eyHdpQVvbkHJDGsnSLEONxPVWBTXr/LS+zhYsV+nbrZ+Y6ZI3hq3gsEtHx6nUQatflhncaA6cGKUrasFPJWJHwoMcS/6VUKvmiZnoL91VhCNvPM0PuxAhXY8Ut3QAnATVDXhUE...
Keys
AES012f267ff1aeb428e3c2e4022c724f4bc77698a5608eef6efed7502a84c72899
Saltbfeb1e56fbcd973bb219022430a57843003d5644d21e62b9d4f180e7e6c33941
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2025:01:16 08:35:26 |
| ZipCRC: | 0xd4f0fe95 |
| ZipCompressedSize: | 1096779 |
| ZipUncompressedSize: | 3192832 |
| ZipFileName: | Acta_Conciliacion_N?_499348294..exe |
Total processes
127
Monitored processes
11
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 8 | "C:\WINDOWS\system32\taskmgr.exe" /4 | C:\Windows\System32\Taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Manager Exit code: 3221226540 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 712 | timeout 3 | C:\Windows\SysWOW64\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2148 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2408 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe | Acta_Conciliacion_N°_499348294..exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Version: 4.8.9037.0 built by: NET481REL1 Modules
AsyncRat(PID) Process(2408) csc.exe C2 (1)2201.mysynology.net Ports (2)8329 2201 Version1.0.7 Options AutoRunfalse MutexDcRatMutex_qwqdanchun InstallFolder%AppData% Certificates Cert1MIICMDCCAZmgAwIBAgIVAPdJPjCx7pYvZ/1H2FuVvfr12RcjMA0GCSqGSIb3DQEBDQUAMGQxFTATBgNVBAMMDERjUmF0IFNlcnZlcjETMBEGA1UECwwKcXdxZGFuY2h1bjEcMBoGA1UECgwTRGNSYXQgQnkgcXdxZGFuY2h1bjELMAkGA1UEBwwCU0gxCzAJBgNVBAYTAkNOMB4XDTIxMTIwOTIwNDY0MFoXDTMyMDkxNzIwNDY0MFowEDEOMAwGA1UEAwwFRGNSYXQwgZ8wDQYJKoZIhvcNAQEBBQADgY0A... Server_SignatureH0QYyQvWpAITuIKRrbjjWItiPBCLrrmljvfKrEegwJEfM3iPZvTxk9etEAeQFv+wGI1G1v0kCoAiWciJVvxiazxk+4frZMl4RuRNe7twWLzB2Zm6p9W8HaZ4yZzSD2ecQHKrG3yApaIs2UDEiH2tRAaOj7gwFaqGDlq3CRvxKHU= Keys AES0dbec3e9df85bb19d9d656863f8b9bf2f55a63212e8c06431b7f2174de1afe6e SaltDcRatByqwqdanchun | |||||||||||||||
| 2828 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\tmp2000.tmp.bat"" | C:\Windows\SysWOW64\cmd.exe | — | aspnet_compiler.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3052 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Acta_Conciliacion_N°_499348294.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3488 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb3052.41394\Acta_Conciliacion_N°_499348294..exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb3052.41394\Acta_Conciliacion_N°_499348294..exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3611307768 Modules
| |||||||||||||||
| 4132 | "C:\WINDOWS\system32\taskmgr.exe" /4 | C:\Windows\System32\Taskmgr.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Manager Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4648 | "C:\WINDOWS\system32\notepad.exe" | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
11 152
Read events
11 125
Write events
25
Delete events
2
Modification events
| (PID) Process: | (3052) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3052) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3052) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (3052) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (3052) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (3052) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Acta_Conciliacion_N°_499348294.zip | |||
| (PID) Process: | (3052) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3052) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3052) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (3488) Acta_Conciliacion_N°_499348294..exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | NordicVPN |
Value: C:\Users\admin\Documents\NordVPNnetworkTAP\Lang\RemotePCPrinter.exe | |||
Executable files
1
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3488 | Acta_Conciliacion_N°_499348294..exe | C:\Users\admin\Documents\NordVPNnetworkTAP\Lang\RemotePCPrinter.exe | — | |
MD5:— | SHA256:— | |||
| 4132 | Taskmgr.exe | C:\Users\admin\AppData\Local\D3DSCache\3534848bb9f4cb71\F4EB2D6C-ED2B-4BDD-AD9D-F913287E6768.lock | text | |
MD5:F49655F856ACB8884CC0ACE29216F511 | SHA256:7852FCE59C67DDF1D6B8B997EAA1ADFAC004A9F3A91C37295DE9223674011FBA | |||
| 5212 | aspnet_compiler.exe | C:\Users\admin\AppData\Local\Temp\tmp2000.tmp.bat | text | |
MD5:504610283196D0B8E68EDB059A949500 | SHA256:CF891637E1E98EE8207DD5ADA47FF8897C220D90C64F4B4F77D5E3010C300FAC | |||
| 3052 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb3052.41394\Acta_Conciliacion_N°_499348294..exe | executable | |
MD5:4297B6B6DA978BBE22296C3F900A75BC | SHA256:39ED2E526804C859DE3D0D593BF595209B25563DA279979A2915BA348F9D6E47 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
55
DNS requests
27
Threats
14
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 184.24.77.37:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2940 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 184.24.77.37:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5064 | SearchApp.exe | 184.86.251.27:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
5064 | SearchApp.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
1176 | svchost.exe | 40.126.31.69:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1176 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
— | — | 2.23.242.9:443 | go.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2408 | csc.exe | Domain Observed Used for C2 Detected | REMOTE [ANY.RUN] AsyncRAT SSL certificate |
2192 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.mysynology .net Domain |
2408 | csc.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Malicious SSL Cert (AsyncRAT) |
2408 | csc.exe | Malware Command and Control Activity Detected | REMOTE [ANY.RUN] AsyncRAT Successful Connection |
2192 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.4cloud .click Domain |
5212 | aspnet_compiler.exe | Domain Observed Used for C2 Detected | REMOTE [ANY.RUN] AsyncRAT SSL certificate |
5212 | aspnet_compiler.exe | Domain Observed Used for C2 Detected | ET MALWARE Generic AsyncRAT Style SSL Cert |
5212 | aspnet_compiler.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Malicious SSL Cert (AsyncRAT Server) |
5212 | aspnet_compiler.exe | Malware Command and Control Activity Detected | REMOTE [ANY.RUN] AsyncRAT Successful Connection |
5 ETPRO signatures available at the full report