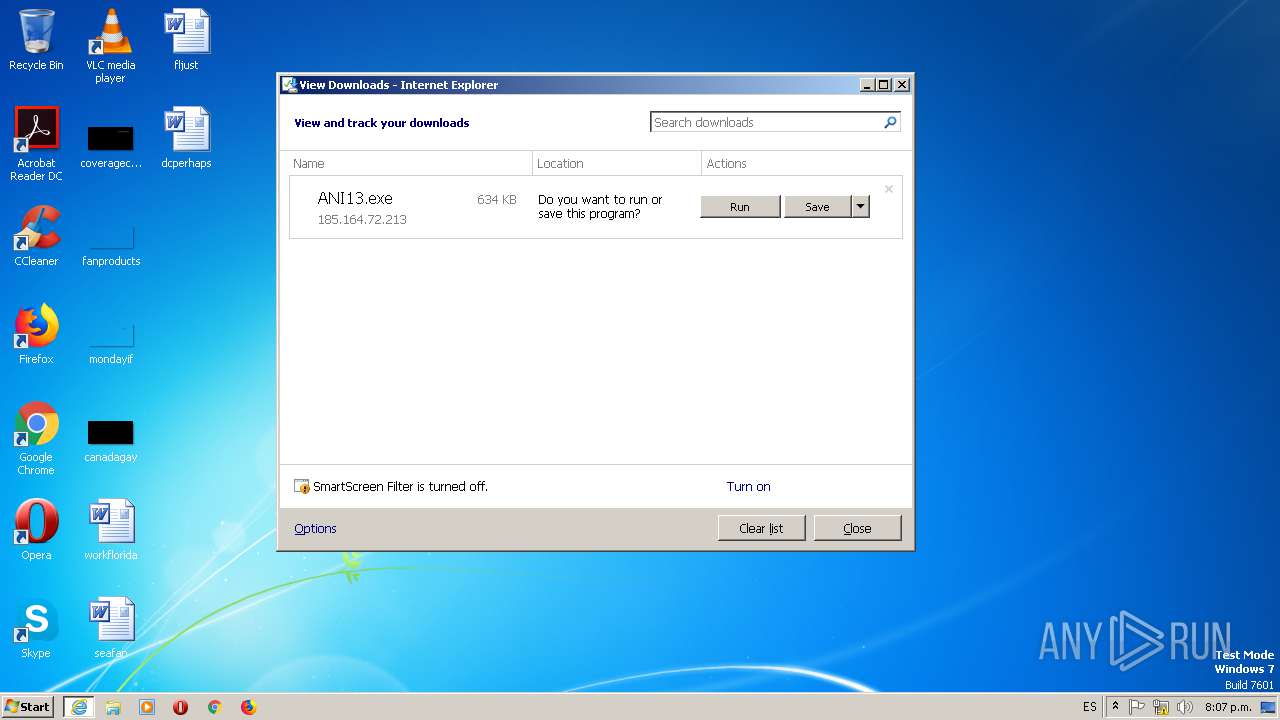
| URL: | http://185.164.72.213/ANI13.exe |
| Full analysis: | https://app.any.run/tasks/b6564815-1438-407e-93fc-cd0922db0083 |
| Verdict: | Malicious activity |
| Threats: | Hawkeye often gets installed in a bundle with other malware. This is a Trojan and keylogger that is used to retrieve private information such as passwords and login credentials. This is an advanced malware that features strong anti-evasion functions. |
| Analysis date: | June 13, 2019, 23:07:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 178F96082BE7FC7736F134493EADEC5B |
| SHA1: | 3644E593D5AC54B77CC5C9376FD336F25E5232A4 |
| SHA256: | A32A9643875DBA7103373D1DA1CF6943C4649C72D7C3EFD5E592A5868DD4FEB5 |
| SSDEEP: | 3:N1KlnaP/rssCn:ClaP/4R |
MALICIOUS
Downloads executable files from the Internet
- IEXPLORE.EXE (PID: 2396)
Downloads executable files from IP
- IEXPLORE.EXE (PID: 2396)
Application was dropped or rewritten from another process
- ANI13.exe (PID: 2272)
- ANI13.exe (PID: 2708)
Changes the login/logoff helper path in the registry
- ANI13.exe (PID: 2272)
Detected Hawkeye Keylogger
- ANI13.exe (PID: 2708)
Stealing of credential data
- vbc.exe (PID: 2456)
- vbc.exe (PID: 2444)
Actions looks like stealing of personal data
- vbc.exe (PID: 2456)
- vbc.exe (PID: 2444)
SUSPICIOUS
Executable content was dropped or overwritten
- IEXPLORE.EXE (PID: 2396)
- iexplore.exe (PID: 1688)
- ANI13.exe (PID: 2272)
Cleans NTFS data-stream (Zone Identifier)
- ANI13.exe (PID: 2272)
Creates files in the user directory
- ANI13.exe (PID: 2272)
Application launched itself
- ANI13.exe (PID: 2272)
Executes scripts
- ANI13.exe (PID: 2708)
INFO
Changes internet zones settings
- iexplore.exe (PID: 1688)
Reads Internet Cache Settings
- iexplore.exe (PID: 1688)
Reads the machine GUID from the registry
- iexplore.exe (PID: 1688)
Reads settings of System Certificates
- iexplore.exe (PID: 1688)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
38
Monitored processes
6
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1688 | "C:\Program Files\Internet Explorer\iexplore.exe" http://185.164.72.213/ANI13.exe | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2272 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\BDW1XBVN\ANI13.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\BDW1XBVN\ANI13.exe | iexplore.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: NpmTaskRunner Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2396 | "C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE" SCODEF:1688 CREDAT:267521 /prefetch:2 | C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2444 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe" /stext "C:\Users\admin\AppData\Local\Temp\tmpBB2F.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe | ANI13.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 0 Version: 8.0.50727.5483 Modules
| |||||||||||||||
| 2456 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe" /stext "C:\Users\admin\AppData\Local\Temp\tmp8F6B.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe | ANI13.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 0 Version: 8.0.50727.5483 Modules
| |||||||||||||||
| 2708 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\BDW1XBVN\ANI13.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\BDW1XBVN\ANI13.exe | ANI13.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: NpmTaskRunner Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
978
Read events
871
Write events
106
Delete events
1
Modification events
| (PID) Process: | (1688) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 2 | |||
| (PID) Process: | (1688) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: 3396740192 | |||
| (PID) Process: | (1688) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30745148 | |||
| (PID) Process: | (1688) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 3696902692 | |||
| (PID) Process: | (1688) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30745148 | |||
| (PID) Process: | (1688) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1688) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1688) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1688) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1688) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
Executable files
4
Suspicious files
5
Text files
6
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1688 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF6A663EEDD9D29EA7.TMP | — | |
MD5:— | SHA256:— | |||
| 1688 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\BDW1XBVN\ANI13.exe.212bmed.partial:Zone.Identifier | — | |
MD5:— | SHA256:— | |||
| 2456 | vbc.exe | C:\Users\admin\AppData\Local\Temp\bhv8FE8.tmp | — | |
MD5:— | SHA256:— | |||
| 1688 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFF9946F3C108FF538.TMP | — | |
MD5:— | SHA256:— | |||
| 1688 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{0812182F-8E30-11E9-8447-5254004AAD21}.dat | — | |
MD5:— | SHA256:— | |||
| 2708 | ANI13.exe | C:\Users\admin\AppData\Local\Temp\CabC8DC.tmp | — | |
MD5:— | SHA256:— | |||
| 2708 | ANI13.exe | C:\Users\admin\AppData\Local\Temp\TarC8DD.tmp | — | |
MD5:— | SHA256:— | |||
| 2396 | IEXPLORE.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\UJFUX3OG\ANI13[1].exe | executable | |
MD5:— | SHA256:— | |||
| 2396 | IEXPLORE.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\BDW1XBVN\ANI13.exe.212bmed.partial | executable | |
MD5:— | SHA256:— | |||
| 2272 | ANI13.exe | C:\Users\admin\AppData\Roaming\Z426sPaOxdzsYJQ6\cco2YAdLfmgE.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
10
DNS requests
6
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2396 | IEXPLORE.EXE | GET | 200 | 185.164.72.213:80 | http://185.164.72.213/ANI13.exe | IR | executable | 634 Kb | suspicious |
2708 | ANI13.exe | GET | 200 | 66.171.248.178:80 | http://bot.whatismyipaddress.com/ | US | text | 15 b | shared |
2708 | ANI13.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?e63d172ea3093c0f | US | compressed | 56.2 Kb | whitelisted |
2708 | ANI13.exe | GET | 200 | 192.35.177.64:80 | http://apps.identrust.com/roots/dstrootcax3.p7c | US | cat | 893 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1688 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2396 | IEXPLORE.EXE | 185.164.72.213:80 | — | Sepehr sabz Khavarmianeh International engineers PJSC | IR | suspicious |
2708 | ANI13.exe | 66.171.248.178:80 | bot.whatismyipaddress.com | Alchemy Communications, Inc. | US | malicious |
2708 | ANI13.exe | 199.79.62.11:587 | mail.cofcoainternational.com | PDR | US | malicious |
2708 | ANI13.exe | 192.35.177.64:80 | apps.identrust.com | IdenTrust | US | malicious |
2708 | ANI13.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
bot.whatismyipaddress.com |
| shared |
mail.cofcoainternational.com |
| malicious |
apps.identrust.com |
| shared |
ctldl.windowsupdate.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2396 | IEXPLORE.EXE | A Network Trojan was detected | ET INFO Executable Download from dotted-quad Host |
2396 | IEXPLORE.EXE | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2396 | IEXPLORE.EXE | Potentially Bad Traffic | ET INFO SUSPICIOUS Dotted Quad Host MZ Response |
2708 | ANI13.exe | A Network Trojan was detected | MALWARE [PTsecurity] Spy.HawkEye IP Check |
2708 | ANI13.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
2 ETPRO signatures available at the full report