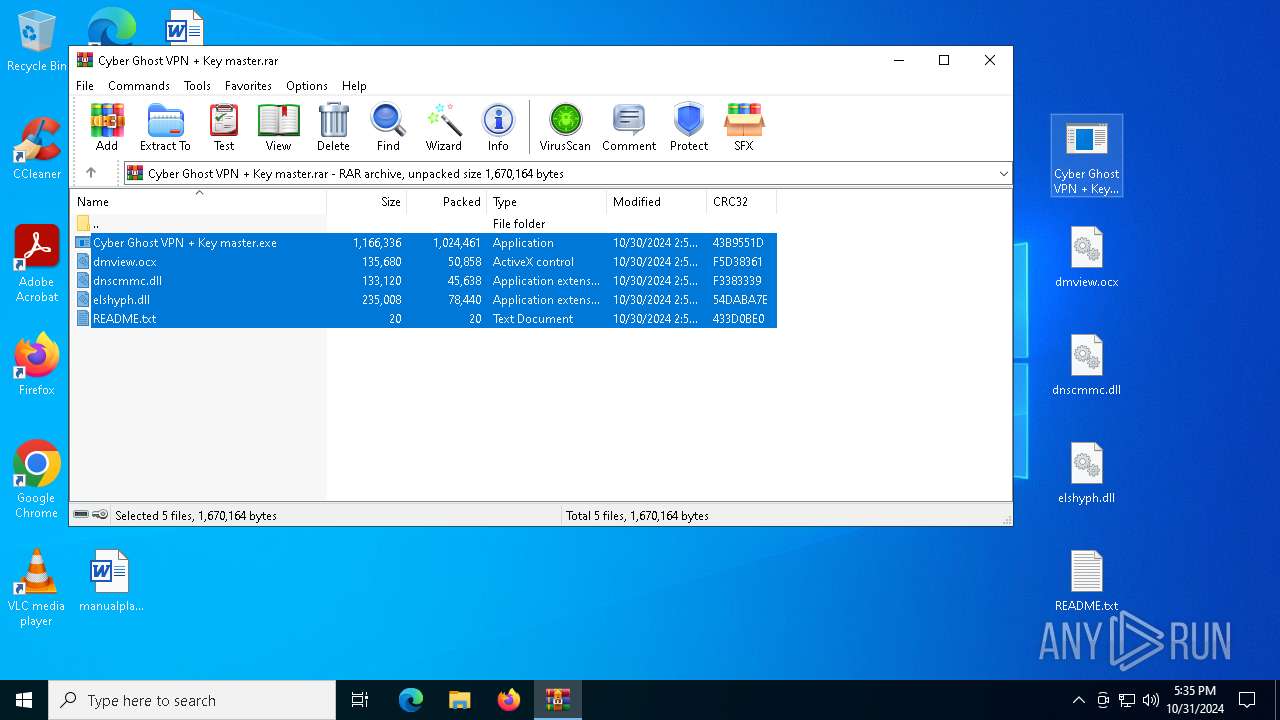
| File name: | Cyber Ghost VPN + Key master.rar |
| Full analysis: | https://app.any.run/tasks/75d49f81-8eb1-434d-9ab7-63bc0d683359 |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | October 31, 2024, 17:35:15 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
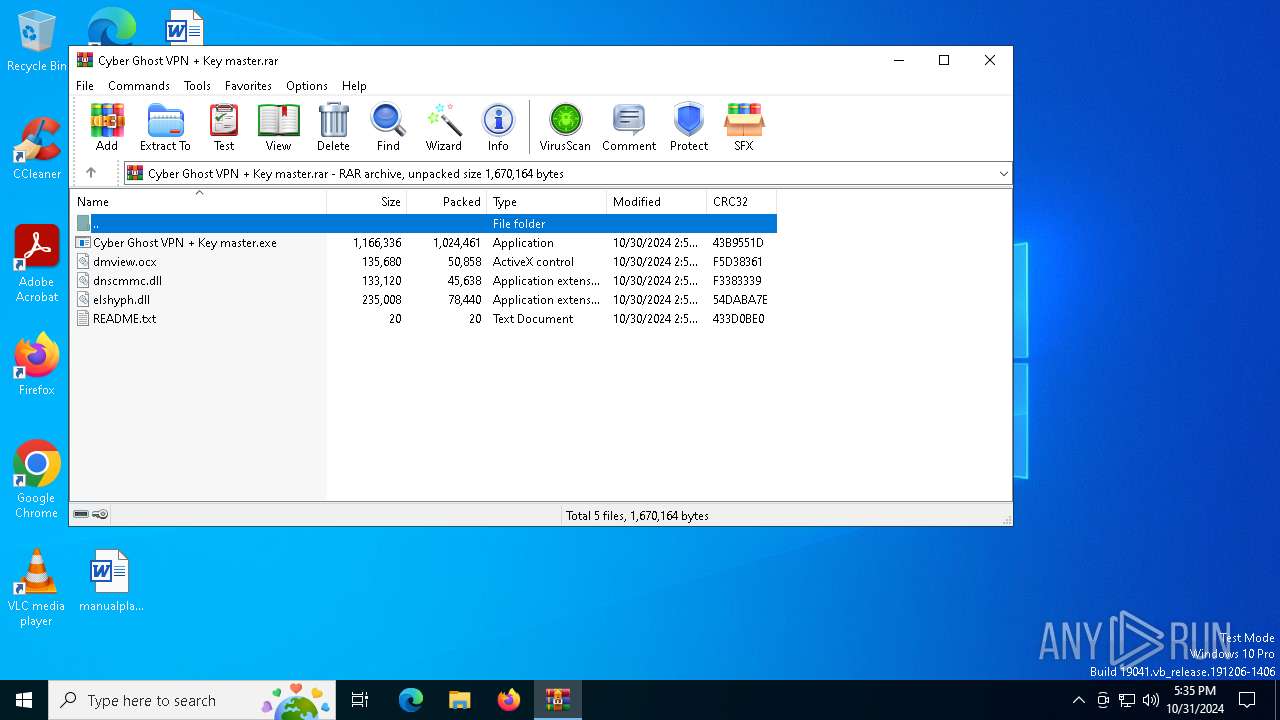
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 8E4EC8460804F45C0AE7E3FA574CDEFA |
| SHA1: | FD3CBB7B9CFF23399AC28C0E2029C5954F3EC082 |
| SHA256: | A305C74B03CF2AEB9FC6AB44D54DBC79D359D660499813DE694FF361B6D330E8 |
| SSDEEP: | 49152:DZqWrPW9ENRpSVC9BOTqCEEBcqfcA2ZM7sW4D4szFfrS2mljVh2OcKYLgJ0fQ+Vx:DIWrNlSVOBOGCEEuHdZMYW4DrzFehjVI |
MALICIOUS
Connects to the CnC server
- svchost.exe (PID: 2172)
LUMMA has been detected (SURICATA)
- dNk1n1iwmT.exe (PID: 5236)
- svchost.exe (PID: 2172)
Stealers network behavior
- dNk1n1iwmT.exe (PID: 5236)
SUSPICIOUS
Executable content was dropped or overwritten
- Cyber Ghost VPN + Key master.exe (PID: 3744)
- BGLuR40qZi.exe (PID: 1804)
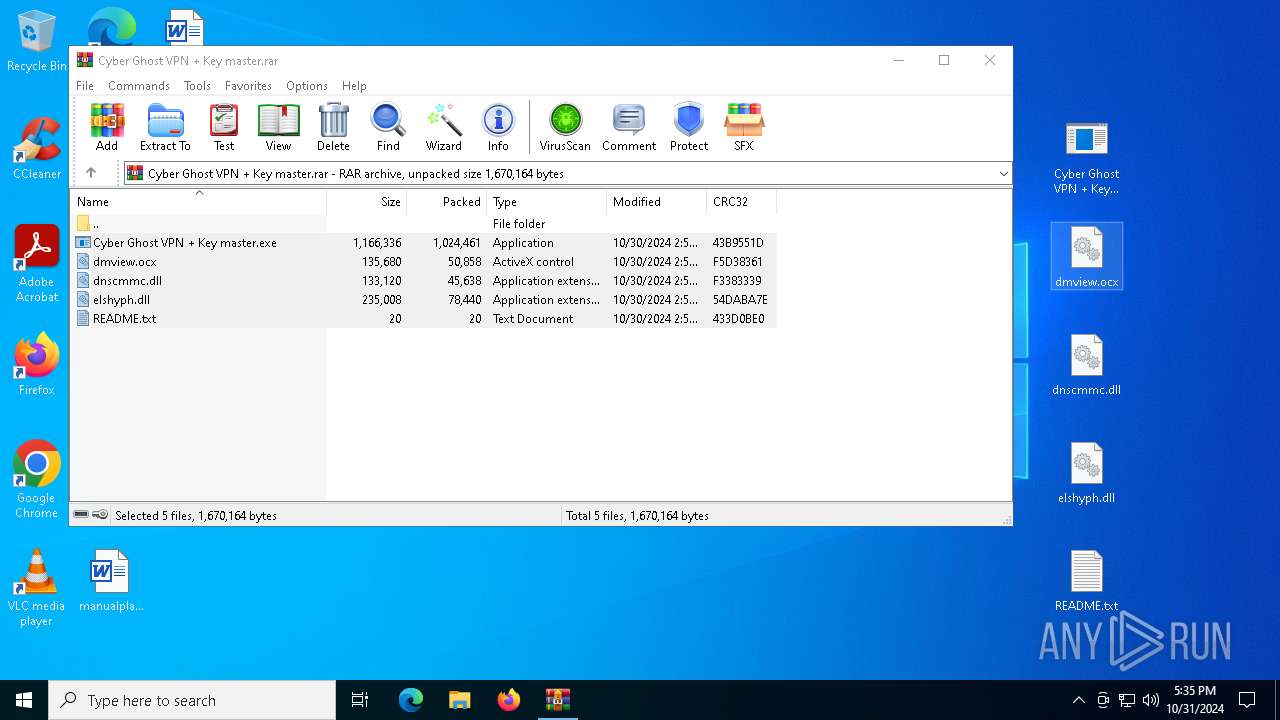
Process drops legitimate windows executable
- WinRAR.exe (PID: 6288)
Generic archive extractor
- WinRAR.exe (PID: 6288)
Executes application which crashes
- dNk1n1iwmT.exe (PID: 4680)
- Cyber Ghost VPN + Key master.exe (PID: 7148)
Application launched itself
- Cyber Ghost VPN + Key master.exe (PID: 7148)
- dNk1n1iwmT.exe (PID: 4680)
Contacting a server suspected of hosting an CnC
- svchost.exe (PID: 2172)
- dNk1n1iwmT.exe (PID: 5236)
INFO
Manual execution by a user
- Cyber Ghost VPN + Key master.exe (PID: 7148)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6288)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|---|
| CompressedSize: | 1024461 |
| UncompressedSize: | 1166336 |
| OperatingSystem: | Win32 |
| ArchivedFileName: | Cyber Ghost VPN + Key master.exe |
Total processes
143
Monitored processes
11
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 696 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 7148 -s 336 | C:\Windows\SysWOW64\WerFault.exe | — | Cyber Ghost VPN + Key master.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1804 | "C:\Users\admin\AppData\Roaming\BGLuR40qZi.exe" | C:\Users\admin\AppData\Roaming\BGLuR40qZi.exe | Cyber Ghost VPN + Key master.exe | ||||||||||||
User: admin Company: Microsoft Windows Integrity Level: MEDIUM Description: system32 Version: 15.6.13.6 Modules
| |||||||||||||||
| 2172 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3744 | "C:\Users\admin\Desktop\Cyber Ghost VPN + Key master.exe" | C:\Users\admin\Desktop\Cyber Ghost VPN + Key master.exe | Cyber Ghost VPN + Key master.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 4680 | "C:\Users\admin\AppData\Roaming\dNk1n1iwmT.exe" | C:\Users\admin\AppData\Roaming\dNk1n1iwmT.exe | Cyber Ghost VPN + Key master.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 5236 | "C:\Users\admin\AppData\Roaming\dNk1n1iwmT.exe" | C:\Users\admin\AppData\Roaming\dNk1n1iwmT.exe | dNk1n1iwmT.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 6148 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 4680 -s 304 | C:\Windows\SysWOW64\WerFault.exe | — | dNk1n1iwmT.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6288 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Cyber Ghost VPN + Key master.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 7076 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | Cyber Ghost VPN + Key master.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7088 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | dNk1n1iwmT.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
7 452
Read events
7 446
Write events
6
Delete events
0
Modification events
| (PID) Process: | (6288) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (6288) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Cyber Ghost VPN + Key master.rar | |||
| (PID) Process: | (6288) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6288) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6288) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6288) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
7
Suspicious files
2
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6148 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER38C8.tmp.WERInternalMetadata.xml | xml | |
MD5:1496D44C6BA077C639FF6D78ABD79705 | SHA256:A7A97BDC70B08E69F5F2620C9CDD0C4D50023D84D6D2F674380636A9878CB8F9 | |||
| 6148 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER38E8.tmp.xml | xml | |
MD5:DF765429A2281C138AFE4EF335668C5B | SHA256:89BFB4C84A22BF7DA71B0B07C53D0111F4860590F4D828DEF206188C2040E8FC | |||
| 696 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER2EA7.tmp.xml | xml | |
MD5:2941AC6591E583BA200476457F0B824D | SHA256:5F4874407BD53C9AFBFB19D39CF8FAAA19451E744EB61FF75ADF74394CDC99AC | |||
| 6288 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6288.44823\Cyber Ghost VPN + Key master.exe | executable | |
MD5:2ABFF13CFDBB439B7BD63D3BE7727689 | SHA256:61AEEB5A4A82B1083D1378EEFDB77AB7D30FC0B89566E6400387DEBAEDD64C37 | |||
| 6288 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6288.44823\dnscmmc.dll | executable | |
MD5:BDC7EAD1E9B59A54F61AD53EC7FEFFFB | SHA256:4F64DC86D26FF64F037EEA6FE2E8F7224A8F5988C132EBF617EC6A562080FB01 | |||
| 6288 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6288.44823\dmview.ocx | executable | |
MD5:9D3D06D04B20C9A61394144DCCF7E54C | SHA256:F11DF95FAE783DDFD452A888BEDAC3B084405CABE20F36BE26000A1738D97C9F | |||
| 6148 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER3888.tmp.dmp | binary | |
MD5:15823AA54193D2FAC68A852456475E41 | SHA256:0F890C4BCE3086BE4A018B237EA9BD8E22BCA8448B2E80F2DFD400CDEB972092 | |||
| 696 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER2E68.tmp.WERInternalMetadata.xml | xml | |
MD5:983EFF261E5F160082E38A800251F6D3 | SHA256:4297C23975594A62CADD75C44EF64E1D52837E515A5BE97358874634D067430A | |||
| 3744 | Cyber Ghost VPN + Key master.exe | C:\Users\admin\AppData\Roaming\dNk1n1iwmT.exe | executable | |
MD5:BED4B2D79AF6CAA405DDD29FB2626D85 | SHA256:AD05233BC1E74F41438D36F1EEA331DCC75EB08B2D939272098A93A8380F5C2D | |||
| 3744 | Cyber Ghost VPN + Key master.exe | C:\Users\admin\AppData\Roaming\BGLuR40qZi.exe | executable | |
MD5:5AFB8CE4DD3923219BD69BD7B5168D91 | SHA256:F727BBA8D917FA3F129D71745E0741A8511F940B1A6817FF5130AA2F3AE85C79 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
39
DNS requests
18
Threats
13
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | US | binary | 312 b | whitelisted |
6944 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
6944 | svchost.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | whitelisted |
6616 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 408 b | whitelisted |
2076 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
6616 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 418 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6944 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1752 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5488 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6944 | svchost.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
6944 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4360 | SearchApp.exe | 104.126.37.130:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4360 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
2076 | svchost.exe | 40.126.31.69:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
th.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2172 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (goalyfeastz .site) |
2172 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (seallysl .site) |
2172 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (servicedny .site) |
2172 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (opposezmny .site) |
5236 | dNk1n1iwmT.exe | A Network Trojan was detected | STEALER [ANY.RUN] Lumma Stealer TLS Connection |
5236 | dNk1n1iwmT.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (goalyfeastz .site in TLS SNI) |
5236 | dNk1n1iwmT.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (goalyfeastz .site in TLS SNI) |
5236 | dNk1n1iwmT.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (goalyfeastz .site in TLS SNI) |
5236 | dNk1n1iwmT.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (goalyfeastz .site in TLS SNI) |
5236 | dNk1n1iwmT.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (goalyfeastz .site in TLS SNI) |