| File name: | awoolazn.exe |
| Full analysis: | https://app.any.run/tasks/bd2d278c-9efc-4bf8-bbd3-2d7cb534078a |
| Verdict: | Malicious activity |
| Threats: | Crypto mining malware is a resource-intensive threat that infiltrates computers with the purpose of mining cryptocurrencies. This type of threat can be deployed either on an infected machine or a compromised website. In both cases the miner will utilize the computing power of the device and its network bandwidth. |
| Analysis date: | October 14, 2019, 17:04:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | ED2BA791AF39608677D99F0E5622AB01 |
| SHA1: | 71AEE43DD9477B97FB16D84F7C2D29546DB5F51E |
| SHA256: | A2E966E0C67BA8C7496B3DBFB40E49EDED364E1ECD982FE345E43AC9C9BC0C16 |
| SSDEEP: | 12288:3IRZTEoH9MjgxD3OOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOW:MhEodMK |
MALICIOUS
Uses SVCHOST.EXE for hidden code execution
- ejtoiurt.exe (PID: 2484)
- svchost.exe (PID: 1904)
Application was dropped or rewritten from another process
- ejtoiurt.exe (PID: 2484)
TOFSEE was detected
- svchost.exe (PID: 1904)
Looks like application has launched a miner
- svchost.exe (PID: 1904)
MINER was detected
- svchost.exe (PID: 3860)
Connects to CnC server
- svchost.exe (PID: 3860)
Modifies exclusions in Windows Defender
- svchost.exe (PID: 1904)
SUSPICIOUS
Executable content was dropped or overwritten
- awoolazn.exe (PID: 2332)
- cmd.exe (PID: 2484)
Executed as Windows Service
- ejtoiurt.exe (PID: 2484)
Starts CMD.EXE for commands execution
- awoolazn.exe (PID: 2332)
Starts SC.EXE for service management
- awoolazn.exe (PID: 2332)
Creates or modifies windows services
- svchost.exe (PID: 1904)
Uses NETSH.EXE for network configuration
- awoolazn.exe (PID: 2332)
Creates files in the Windows directory
- svchost.exe (PID: 1904)
Application launched itself
- svchost.exe (PID: 1904)
Checks for external IP
- svchost.exe (PID: 1904)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:04:21 06:43:38+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 87040 |
| InitializedDataSize: | 1922560 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1e04 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 21-Apr-2018 04:43:38 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 9 |
| Time date stamp: | 21-Apr-2018 04:43:38 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000153AB | 0x00015400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.68234 |
.rdata | 0x00017000 | 0x00023962 | 0x00023A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.7948 |
.data | 0x0003B000 | 0x001AA5F0 | 0x00002200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.666985 |
.sey | 0x001E6000 | 0x00000400 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rav | 0x001E7000 | 0x00000001 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.tls | 0x001E8000 | 0x00000009 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.gfids | 0x001E9000 | 0x000000AC | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.52941 |
.rsrc | 0x001EA000 | 0x00005928 | 0x00005A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.75197 |
.reloc | 0x001F0000 | 0x000011B4 | 0x00C6D800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.56668 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 6.48695 | 4264 | UNKNOWN | Italian - Italy | RT_ICON |
14 | 3.24486 | 608 | UNKNOWN | UNKNOWN | RT_STRING |
15 | 3.30583 | 1866 | UNKNOWN | UNKNOWN | RT_STRING |
16 | 3.32747 | 1482 | UNKNOWN | UNKNOWN | RT_STRING |
17 | 3.31644 | 1570 | UNKNOWN | UNKNOWN | RT_STRING |
18 | 3.29979 | 1988 | UNKNOWN | UNKNOWN | RT_STRING |
19 | 3.29158 | 1980 | UNKNOWN | UNKNOWN | RT_STRING |
20 | 3.31493 | 1694 | UNKNOWN | UNKNOWN | RT_STRING |
21 | 3.229 | 1084 | UNKNOWN | UNKNOWN | RT_STRING |
116 | 1.7815 | 20 | UNKNOWN | Italian - Italy | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
KERNEL32.dll |
USER32.dll |
Total processes
55
Monitored processes
12
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1552 | sc description qhkdbizj "wifi internet conection" | C:\Windows\system32\sc.exe | awoolazn.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
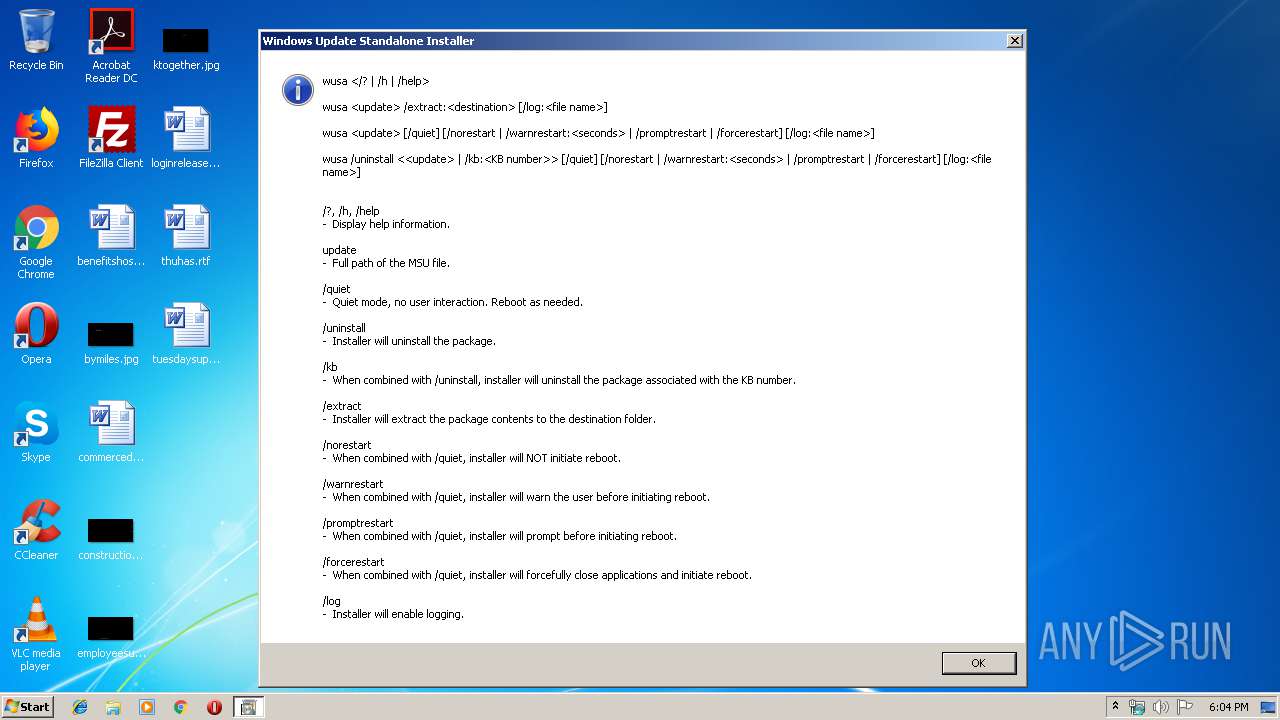
| 1784 | "C:\Windows\System32\wusa.exe" | C:\Windows\System32\wusa.exe | — | awoolazn.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Update Standalone Installer Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1904 | svchost.exe | C:\Windows\system32\svchost.exe | ejtoiurt.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2332 | "C:\Users\admin\AppData\Local\Temp\awoolazn.exe" | C:\Users\admin\AppData\Local\Temp\awoolazn.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2372 | netsh advfirewall firewall add rule name="Host-process for services of Windows" dir=in action=allow program="C:\Windows\system32\svchost.exe" enable=yes>nul | C:\Windows\system32\netsh.exe | awoolazn.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2484 | cmd /C move /Y "C:\Users\admin\AppData\Local\Temp\ejtoiurt.exe" C:\Windows\system32\qhkdbizj\ | C:\Windows\system32\cmd.exe | awoolazn.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2484 | C:\Windows\system32\qhkdbizj\ejtoiurt.exe /d"C:\Users\admin\AppData\Local\Temp\awoolazn.exe" | C:\Windows\system32\qhkdbizj\ejtoiurt.exe | — | services.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
| 2696 | sc start qhkdbizj | C:\Windows\system32\sc.exe | awoolazn.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3704 | cmd /C mkdir C:\Windows\system32\qhkdbizj\ | C:\Windows\system32\cmd.exe | awoolazn.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3736 | "C:\Windows\System32\wusa.exe" | C:\Windows\System32\wusa.exe | awoolazn.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Update Standalone Installer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
158
Read events
93
Write events
65
Delete events
0
Modification events
| (PID) Process: | (2332) awoolazn.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2332) awoolazn.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2372) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2372) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-100 |
Value: DHCP Quarantine Enforcement Client | |||
| (PID) Process: | (2372) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-101 |
Value: Provides DHCP based enforcement for NAP | |||
| (PID) Process: | (2372) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-103 |
Value: 1.0 | |||
| (PID) Process: | (2372) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-102 |
Value: Microsoft Corporation | |||
| (PID) Process: | (2372) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-1 |
Value: IPsec Relying Party | |||
| (PID) Process: | (2372) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-2 |
Value: Provides IPsec based enforcement for Network Access Protection | |||
| (PID) Process: | (2372) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-4 |
Value: 1.0 | |||
Executable files
2
Suspicious files
4
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2484 | cmd.exe | C:\Windows\system32\qhkdbizj\ejtoiurt.exe | executable | |
MD5:— | SHA256:— | |||
| 2332 | awoolazn.exe | C:\Users\admin\AppData\Local\Temp\ejtoiurt.exe | executable | |
MD5:— | SHA256:— | |||
| 1904 | svchost.exe | C:\Windows\system32\config\systemprofile:.repos | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
62
DNS requests
61
Threats
18
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1904 | svchost.exe | GET | — | 89.39.105.12:80 | http://89.39.105.12/ip.shtml | NL | — | — | suspicious |
1904 | svchost.exe | GET | — | 89.39.105.12:80 | http://89.39.105.12/ip.shtml | NL | — | — | suspicious |
1904 | svchost.exe | GET | 200 | 93.171.200.64:35000 | http://api.pr-cy.ru:35000/ | RU | binary | 5.09 Kb | malicious |
1904 | svchost.exe | GET | 200 | 104.20.16.242:80 | http://icanhazip.com/ | US | text | 15 b | shared |
1904 | svchost.exe | GET | 302 | 172.217.16.132:80 | http://www.google.com/ | US | html | 231 b | malicious |
1904 | svchost.exe | GET | 302 | 172.217.16.132:80 | http://www.google.com/ | US | html | 231 b | malicious |
1904 | svchost.exe | GET | 302 | 172.217.16.132:80 | http://www.google.com/ | US | html | 231 b | malicious |
1904 | svchost.exe | GET | 302 | 172.217.16.132:80 | http://www.google.com/ | US | html | 231 b | malicious |
1904 | svchost.exe | GET | 302 | 172.217.16.132:80 | http://www.google.com/ | US | html | 231 b | malicious |
1904 | svchost.exe | GET | 200 | 162.88.193.70:80 | http://checkip.dyndns.org/ | US | html | 106 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1904 | svchost.exe | 13.77.161.179:80 | microsoft.com | Microsoft Corporation | US | whitelisted |
1904 | svchost.exe | 209.85.233.26:25 | alt1.gmail-smtp-in.l.google.com | Google Inc. | US | whitelisted |
1904 | svchost.exe | 213.180.147.146:25 | mx.poczta.onet.pl | Grupa Onet.pl S.A. | PL | unknown |
1904 | svchost.exe | 217.97.216.15:25 | smtp.hosting.tp.pl | Orange Polska Spolka Akcyjna | PL | unknown |
1904 | svchost.exe | 172.217.194.27:25 | alt2.aspmx.l.google.com | Google Inc. | US | whitelisted |
1904 | svchost.exe | 104.47.40.36:25 | sdace-com.mail.protection.outlook.com | Microsoft Corporation | US | unknown |
1904 | svchost.exe | 144.76.199.2:420 | — | Hetzner Online GmbH | DE | malicious |
1904 | svchost.exe | 93.179.68.4:420 | — | Fop Iliushenko Volodymyr Olexandrovuch | RU | unknown |
1904 | svchost.exe | 85.25.119.25:420 | — | Host Europe GmbH | DE | malicious |
1904 | svchost.exe | 46.4.52.109:420 | — | Hetzner Online GmbH | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
microsoft.com |
| whitelisted |
microsoft-com.mail.protection.outlook.com |
| whitelisted |
yahoo.com |
| whitelisted |
mta5.am0.yahoodns.net |
| unknown |
219.175.206.85.dnsbl.sorbs.net |
| unknown |
219.175.206.85.bl.spamcop.net |
| unknown |
219.175.206.85.zen.spamhaus.org |
| unknown |
219.175.206.85.sbl-xbl.spamhaus.org |
| unknown |
telia.com |
| whitelisted |
mail.telia.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1904 | svchost.exe | A Network Trojan was detected | MALWARE [PTsecurity] Tofsee.bot |
1904 | svchost.exe | A Network Trojan was detected | MALWARE [PTsecurity] Tofsee.bot |
3860 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY Cryptocurrency Miner Checkin |
3860 | svchost.exe | Misc activity | MINER [PTsecurity] Riskware/CoinMiner JSON_RPC Response |
3860 | svchost.exe | Misc activity | MINER [PTsecurity] Risktool.W32.coinminer!c |
3860 | svchost.exe | Misc activity | MINER [PTsecurity] CoinMiner CryptoNight algo JSON_RPC server Response |
3860 | svchost.exe | Misc activity | MINER [PTsecurity] Riskware/CoinMiner JSON_RPC Response |
3860 | svchost.exe | Misc activity | MINER [PTsecurity] Risktool.W32.coinminer!c |
3860 | svchost.exe | Misc activity | MINER [PTsecurity] CoinMiner CryptoNight algo JSON_RPC server Response |
1904 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup - checkip.dyndns.org |
6 ETPRO signatures available at the full report