| File name: | a26095cf5fff9a7ec04c3fd3fb60372f38f3dc300addf4983e0ce4f7490ef7b2.exe |
| Full analysis: | https://app.any.run/tasks/f1711974-3bd0-4247-9de7-d457aab64987 |
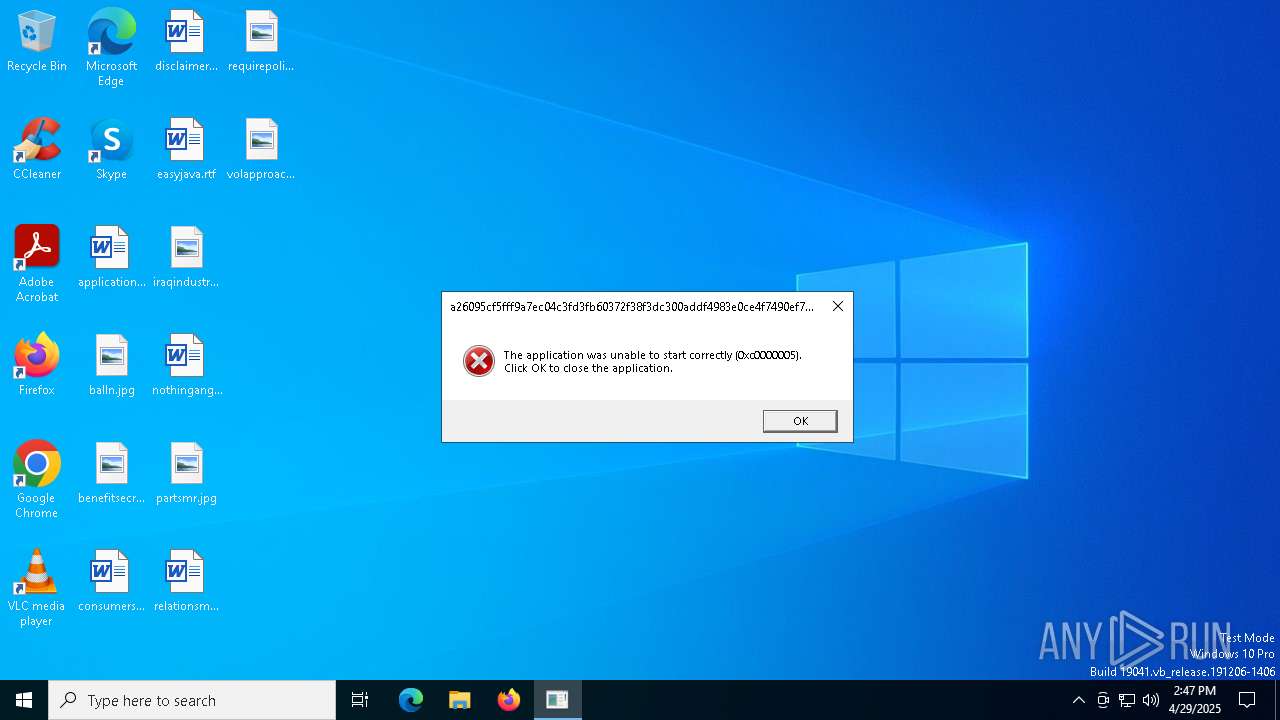
| Verdict: | Malicious activity |
| Threats: | Stealc is a stealer malware that targets victims’ sensitive data, which it exfiltrates from browsers, messaging apps, and other software. The malware is equipped with advanced features, including fingerprinting, control panel, evasion mechanisms, string obfuscation, etc. Stealc establishes persistence and communicates with its C2 server through HTTP POST requests. |
| Analysis date: | April 29, 2025, 14:47:14 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 5 sections |
| MD5: | 12247EBF4653796EC00ABD7C8F59B149 |
| SHA1: | 7181B8D68AAC0861EF505E6FE00B6A4E33A06F3F |
| SHA256: | A26095CF5FFF9A7EC04C3FD3FB60372F38F3DC300ADDF4983E0CE4F7490EF7B2 |
| SSDEEP: | 24576:rHbmRMFgEmArJeNP8eoSBTms/w77rS1Ag:HmagEmArJokeoSBTms/w77rS1Ag |
MALICIOUS
STEALC has been detected (YARA)
- a26095cf5fff9a7ec04c3fd3fb60372f38f3dc300addf4983e0ce4f7490ef7b2.exe (PID: 660)
SUSPICIOUS
No suspicious indicators.INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Stealc
(PID) Process(660) a26095cf5fff9a7ec04c3fd3fb60372f38f3dc300addf4983e0ce4f7490ef7b2.exe
C2 (1)91.92.46.133/8f11bd01520293d6.php
Keys
RC4 (1)QThYf0OqcX
Strings (53)20
04
20
25
kernel32.dll
advapi32.dll
GetProcAddress
LoadLibraryA
ExitProcess
CloseHandle
GetUserDefaultLangID
OpenEventW
CreateEventW
Sleep
GetComputerNameW
GetUserNameW
91.92.46.133
/8f11bd01520293d6.php
gdiplus.dll
crypt32.dll
gdi32.dll
rstrtmgr.dll
ole32.dll
winhttp.dll
user32.dll
shlwapi.dll
shell32.dll
ntdll.dll
GdipGetImageEncodersSize
GdipGetImageEncoders
GdipCreateBitmapFromHBITMAP
GdiplusStartup
GdiplusShutdown
GdipSaveImageToStream
GdipDisposeImage
RegQueryValueExA
RegEnumKeyExA
RegQueryValueExW
RegOpenKeyExW
RegCloseKey
ConvertStringSecurityDescriptorToSecurityDescriptorA
RegOpenKeyExA
CryptUnprotectData
CryptStringToBinaryA
CryptBinaryToStringA
CreateCompatibleBitmap
SelectObject
CreateCompatibleDC
DeleteDC
DeleteObject
BitBlt
RmGetList
RmRegisterResources
ExpirationDate2025-04-20
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:04:08 18:52:40+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.43 |
| CodeSize: | 450048 |
| InitializedDataSize: | 369152 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3f864 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Total processes
130
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 660 | "C:\Users\admin\AppData\Local\Temp\a26095cf5fff9a7ec04c3fd3fb60372f38f3dc300addf4983e0ce4f7490ef7b2.exe" | C:\Users\admin\AppData\Local\Temp\a26095cf5fff9a7ec04c3fd3fb60372f38f3dc300addf4983e0ce4f7490ef7b2.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
Stealc(PID) Process(660) a26095cf5fff9a7ec04c3fd3fb60372f38f3dc300addf4983e0ce4f7490ef7b2.exe C2 (1)91.92.46.133/8f11bd01520293d6.php Keys RC4 (1)QThYf0OqcX Strings (53)20 04 20 25 kernel32.dll advapi32.dll GetProcAddress LoadLibraryA ExitProcess CloseHandle GetUserDefaultLangID OpenEventW CreateEventW Sleep GetComputerNameW GetUserNameW 91.92.46.133 /8f11bd01520293d6.php gdiplus.dll crypt32.dll gdi32.dll rstrtmgr.dll ole32.dll winhttp.dll user32.dll shlwapi.dll shell32.dll ntdll.dll GdipGetImageEncodersSize GdipGetImageEncoders GdipCreateBitmapFromHBITMAP GdiplusStartup GdiplusShutdown GdipSaveImageToStream GdipDisposeImage RegQueryValueExA RegEnumKeyExA RegQueryValueExW RegOpenKeyExW RegCloseKey ConvertStringSecurityDescriptorToSecurityDescriptorA RegOpenKeyExA CryptUnprotectData CryptStringToBinaryA CryptBinaryToStringA CreateCompatibleBitmap SelectObject CreateCompatibleDC DeleteDC DeleteObject BitBlt RmGetList RmRegisterResources ExpirationDate2025-04-20 | |||||||||||||||
| 4164 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5508 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
118
Read events
118
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
20
DNS requests
11
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.30:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.216.77.30:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
632 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
632 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 23.216.77.30:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.30:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.160.128:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |