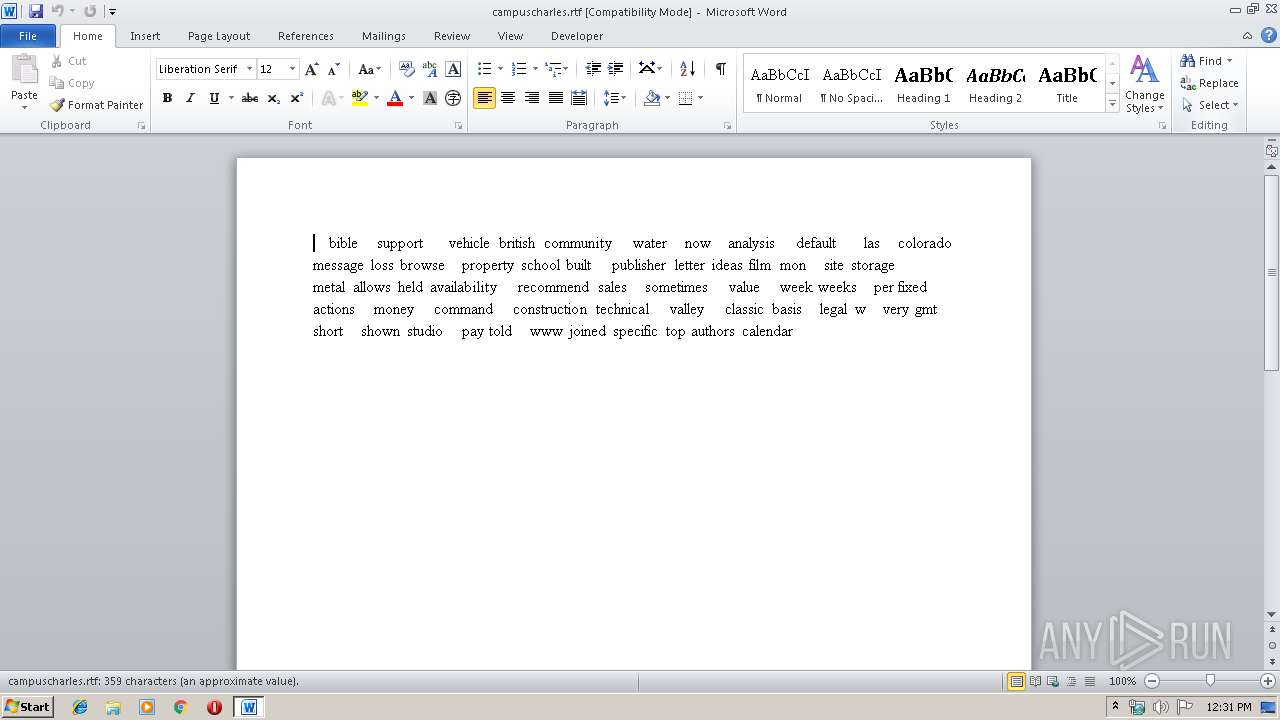
| download: | SWIFT_messageMT103_hsbc.pdf.exe |
| Full analysis: | https://app.any.run/tasks/a4edd755-ae3e-468f-b7e5-537dc67d7605 |
| Verdict: | Malicious activity |
| Threats: | WarZone RAT is a remote access trojan, which is written in C++ and offered as a malware-as-a-service. It packs a wide range of capabilities, from stealing victims’ files and passwords to capturing desktop activities. WarZone RAT is primarily distributed via phishing emails and receives regular updates from its C2. |
| Analysis date: | December 06, 2019, 12:30:52 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | ACF207F099161994A7B991BB540209D0 |
| SHA1: | 77B5B4F0ADAE6AFD9501EB4A897F387697246E5D |
| SHA256: | A24C6BB23EC62350D40ED8E595E5339BF12D669C9108C82C2FE3580F801927B6 |
| SSDEEP: | 24576:jAHnh+eWsN3skA4RV1Hom2KXMmHae3S7i/OyC5:uh+ZkldoPK8Yae6 |
MALICIOUS
Writes to a start menu file
- SWIFT_messageMT103_hsbc.pdf.exe (PID: 2764)
- jus.exe (PID: 3272)
- SWIFT_messageMT103_hsbc.pdf.exe (PID: 624)
- jus.exe (PID: 1244)
Runs app for hidden code execution
- SWIFT_messageMT103_hsbc.pdf.exe (PID: 2424)
- jus.exe (PID: 3356)
AVEMARIA was detected
- SWIFT_messageMT103_hsbc.pdf.exe (PID: 2424)
- jus.exe (PID: 3356)
Changes the autorun value in the registry
- SWIFT_messageMT103_hsbc.pdf.exe (PID: 2424)
Loads dropped or rewritten executable
- dism.exe (PID: 4020)
- dism.exe (PID: 4008)
SUSPICIOUS
Application launched itself
- SWIFT_messageMT103_hsbc.pdf.exe (PID: 2764)
- jus.exe (PID: 3272)
- SWIFT_messageMT103_hsbc.pdf.exe (PID: 624)
- jus.exe (PID: 1244)
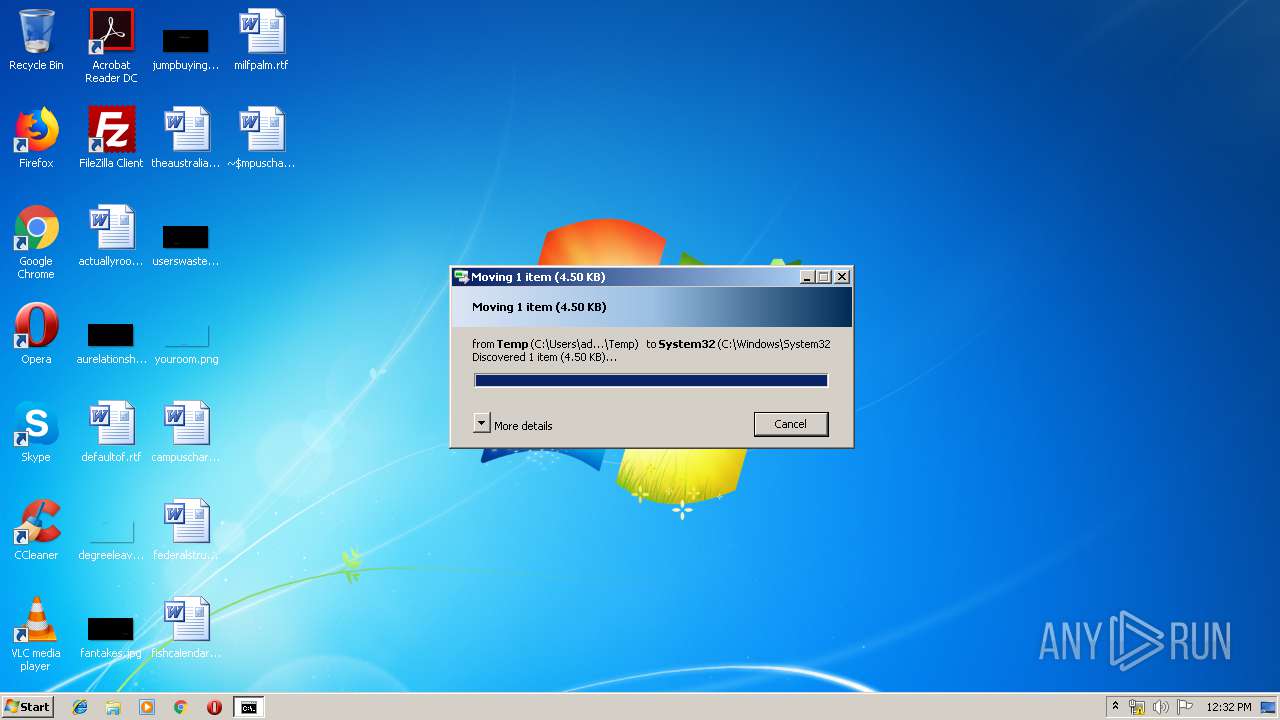
Executable content was dropped or overwritten
- SWIFT_messageMT103_hsbc.pdf.exe (PID: 2764)
- SWIFT_messageMT103_hsbc.pdf.exe (PID: 2424)
- cmd.exe (PID: 2980)
- DllHost.exe (PID: 1928)
- cmd.exe (PID: 3604)
- jus.exe (PID: 3272)
- SWIFT_messageMT103_hsbc.pdf.exe (PID: 624)
- jus.exe (PID: 1244)
- DllHost.exe (PID: 1876)
Starts CMD.EXE for commands execution
- SWIFT_messageMT103_hsbc.pdf.exe (PID: 2424)
- jus.exe (PID: 3356)
Creates files in the user directory
- SWIFT_messageMT103_hsbc.pdf.exe (PID: 2764)
- SWIFT_messageMT103_hsbc.pdf.exe (PID: 2424)
- powershell.exe (PID: 2992)
- powershell.exe (PID: 952)
Executed via COM
- DllHost.exe (PID: 1928)
- DllHost.exe (PID: 1876)
Starts itself from another location
- SWIFT_messageMT103_hsbc.pdf.exe (PID: 2424)
Connects to unusual port
- jus.exe (PID: 3356)
- SWIFT_messageMT103_hsbc.pdf.exe (PID: 4024)
- jus.exe (PID: 2076)
Executes PowerShell scripts
- SWIFT_messageMT103_hsbc.pdf.exe (PID: 4024)
- jus.exe (PID: 2076)
INFO
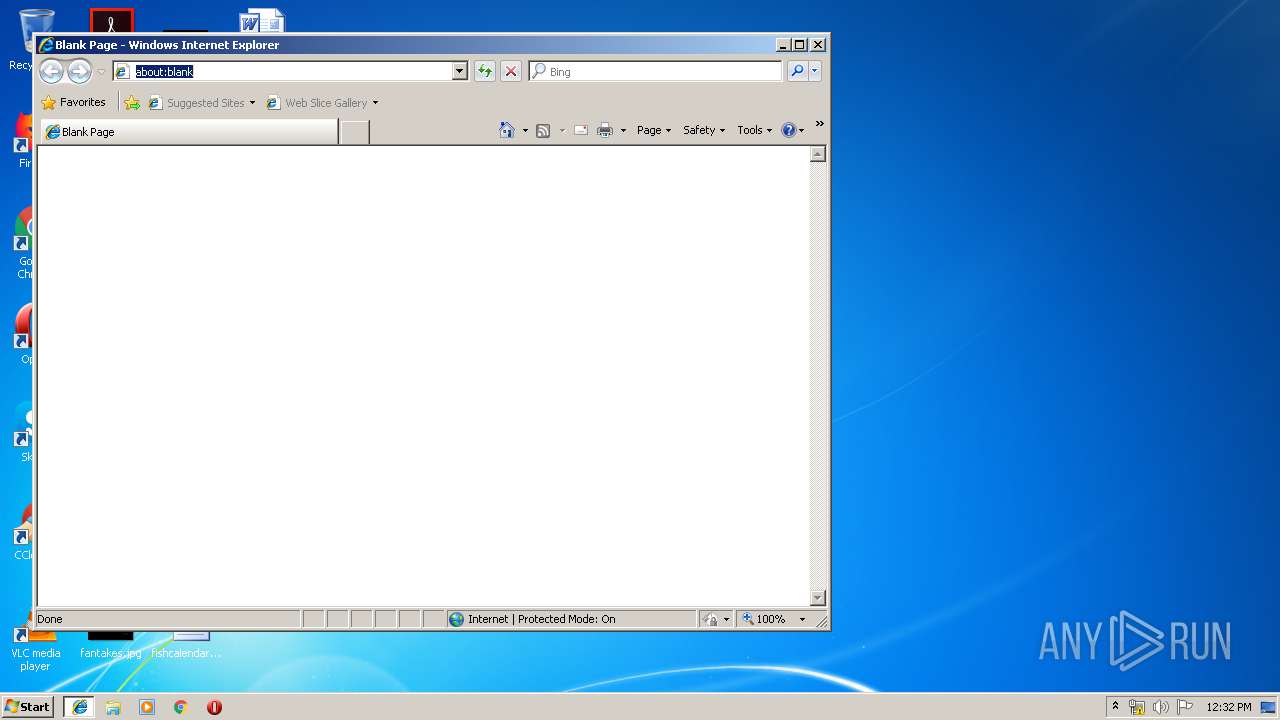
Manual execution by user
- WINWORD.EXE (PID: 2152)
- iexplore.exe (PID: 2336)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2152)
Creates files in the user directory
- WINWORD.EXE (PID: 2152)
Changes internet zones settings
- iexplore.exe (PID: 2336)
Reads internet explorer settings
- iexplore.exe (PID: 3728)
Application launched itself
- iexplore.exe (PID: 2336)
Reads Internet Cache Settings
- iexplore.exe (PID: 3728)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:04:09 17:01:24+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 12 |
| CodeSize: | 581632 |
| InitializedDataSize: | 500736 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2800a |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (British) |
| CharacterSet: | Unicode |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 09-Apr-2019 15:01:24 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000110 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 09-Apr-2019 15:01:24 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0008DFDD | 0x0008E000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.67525 |
.rdata | 0x0008F000 | 0x0002FD8E | 0x0002FE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.76324 |
.data | 0x000BF000 | 0x00008F74 | 0x00005200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.19638 |
.rsrc | 0x000C8000 | 0x0003E0C8 | 0x0003E200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.28456 |
.reloc | 0x00107000 | 0x00007134 | 0x00007200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.78396 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.40026 | 1007 | Latin 1 / Western European | English - United Kingdom | RT_MANIFEST |
2 | 2.05883 | 296 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
3 | 2.25499 | 296 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
4 | 4.51126 | 4304 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
7 | 3.34702 | 1428 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
8 | 3.2817 | 1674 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
9 | 3.28849 | 1168 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
10 | 3.28373 | 1532 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
11 | 3.26322 | 1628 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
12 | 3.25812 | 1126 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
IPHLPAPI.DLL |
KERNEL32.dll |
MPR.dll |
OLEAUT32.dll |
PSAPI.DLL |
SHELL32.dll |
Total processes
74
Monitored processes
23
Malicious processes
4
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 624 | "C:\Users\admin\AppData\Local\Temp\SWIFT_messageMT103_hsbc.pdf.exe" | C:\Users\admin\AppData\Local\Temp\SWIFT_messageMT103_hsbc.pdf.exe | dism.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 952 | powershell Add-MpPreference -ExclusionPath C:\ | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | jus.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1244 | "C:\Users\admin\AppData\Roaming\jus.exe" | C:\Users\admin\AppData\Roaming\jus.exe | dism.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1876 | C:\Windows\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\system32\DllHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1928 | C:\Windows\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\system32\DllHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2076 | "C:\Users\admin\AppData\Roaming\jus.exe" | C:\Users\admin\AppData\Roaming\jus.exe | jus.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2152 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\campuscharles.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2336 | "C:\Program Files\Internet Explorer\iexplore.exe" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2424 | "C:\Users\admin\AppData\Local\Temp\SWIFT_messageMT103_hsbc.pdf.exe" | C:\Users\admin\AppData\Local\Temp\SWIFT_messageMT103_hsbc.pdf.exe | SWIFT_messageMT103_hsbc.pdf.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2764 | "C:\Users\admin\AppData\Local\Temp\SWIFT_messageMT103_hsbc.pdf.exe" | C:\Users\admin\AppData\Local\Temp\SWIFT_messageMT103_hsbc.pdf.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
2 395
Read events
1 946
Write events
301
Delete events
148
Modification events
| (PID) Process: | (2152) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | "qb |
Value: 2271620068080000010000000000000000000000 | |||
| (PID) Process: | (2152) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2152) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2152) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2152) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2152) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2152) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2152) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2152) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2152) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1334181951 | |||
Executable files
9
Suspicious files
4
Text files
20
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2152 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRF102.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2152 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{2551C4B7-56CE-41D5-8AB8-961624A5D14F}.tmp | — | |
MD5:— | SHA256:— | |||
| 2152 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{AFAC0412-E29C-4958-ADC1-4965D20CE28D}.tmp | — | |
MD5:— | SHA256:— | |||
| 2152 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{0374E85C-F71F-458A-8590-0E3430C9EF7E}.tmp | — | |
MD5:— | SHA256:— | |||
| 2336 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2336 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2336 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF2140C22CADA76340.TMP | — | |
MD5:— | SHA256:— | |||
| 2336 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Last Active\RecoveryStore.{79E1419F-1824-11EA-AB41-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 2336 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF97CDF72A1632B9E4.TMP | — | |
MD5:— | SHA256:— | |||
| 2336 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{79E1419E-1824-11EA-AB41-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
10
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2336 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 107.173.219.120:7500 | jamesxx.dynu.net | ColoCrossing | US | unknown |
2336 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3356 | jus.exe | 107.173.219.120:7500 | jamesxx.dynu.net | ColoCrossing | US | unknown |
2076 | jus.exe | 107.173.219.120:7500 | jamesxx.dynu.net | ColoCrossing | US | unknown |
4024 | SWIFT_messageMT103_hsbc.pdf.exe | 107.173.219.120:7500 | jamesxx.dynu.net | ColoCrossing | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
jamesxx.dynu.net |
| unknown |