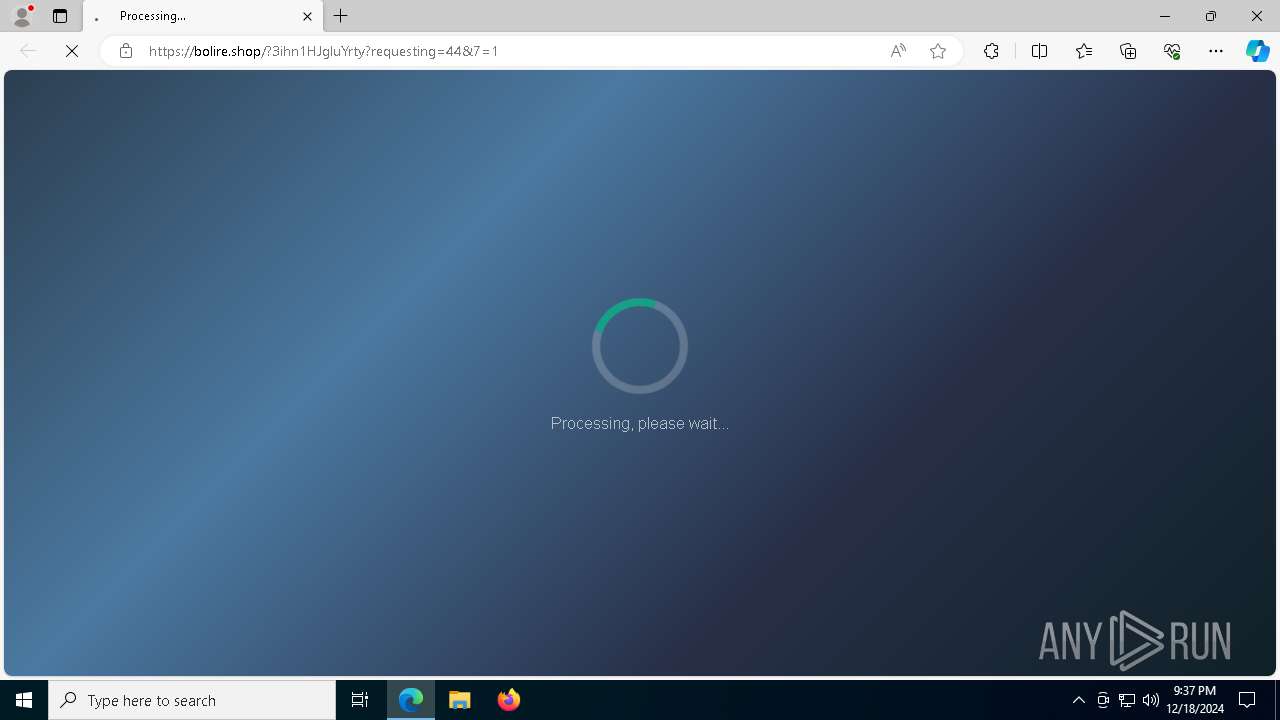
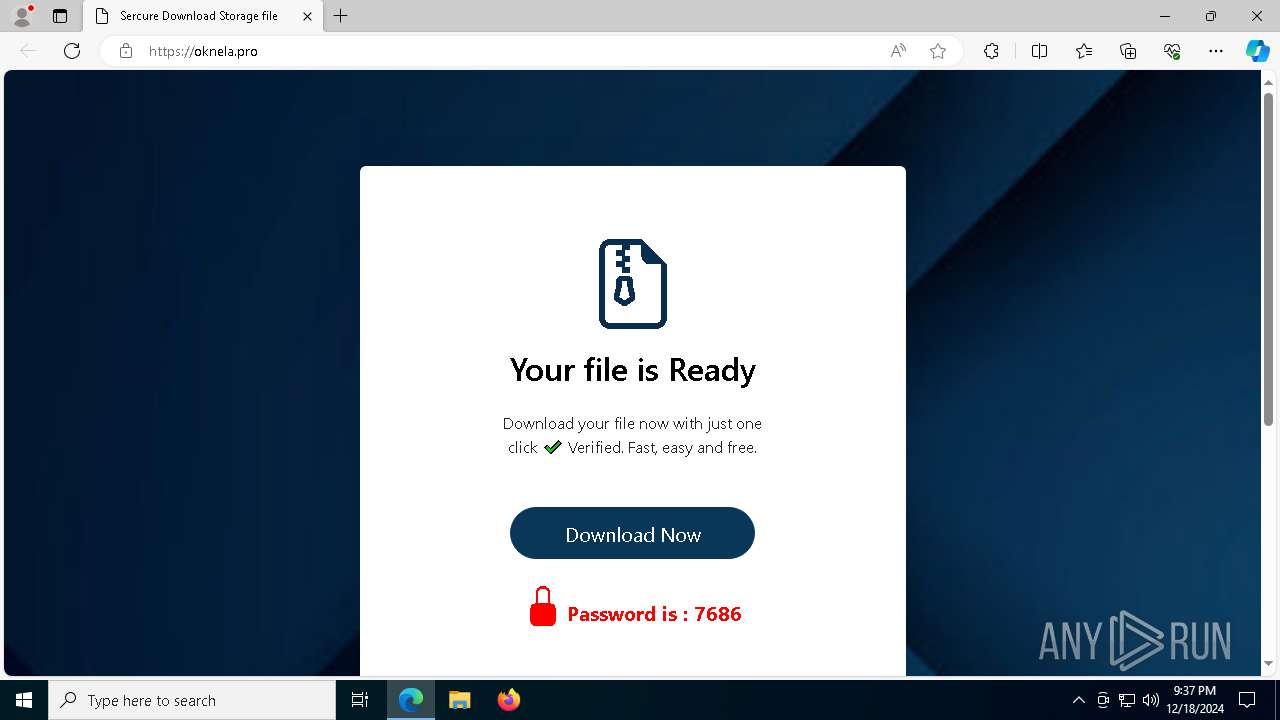
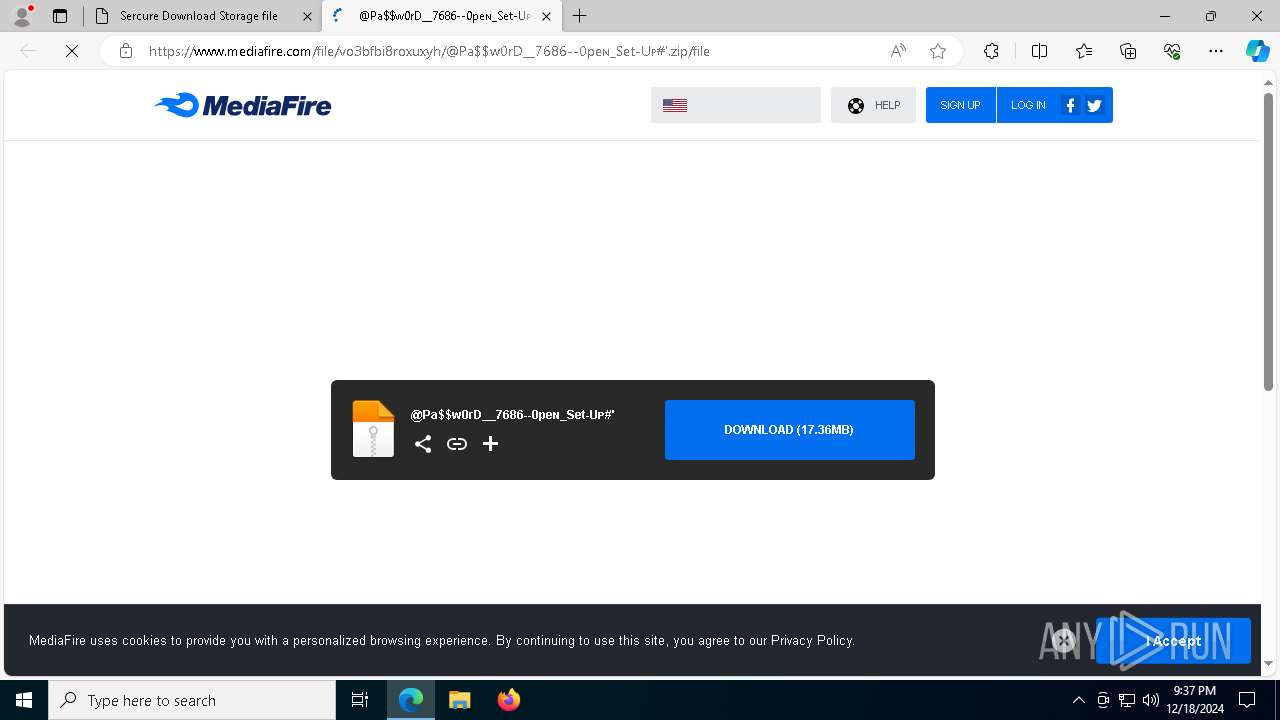
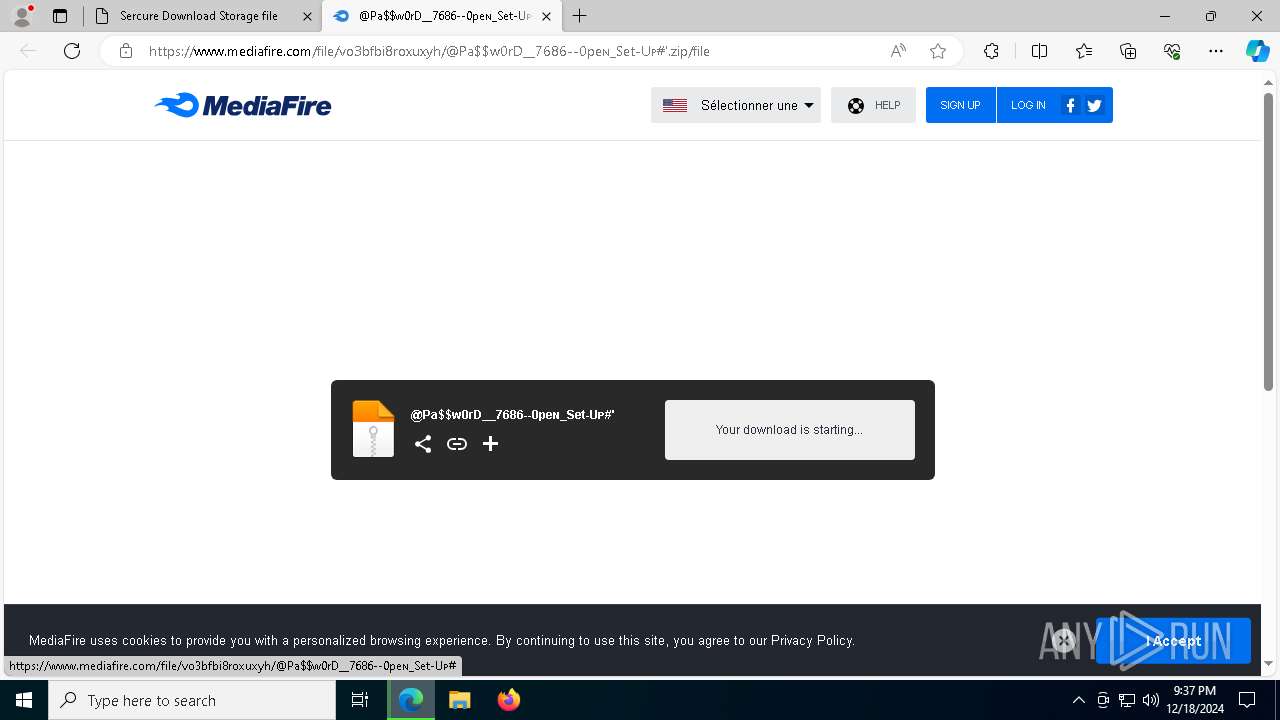
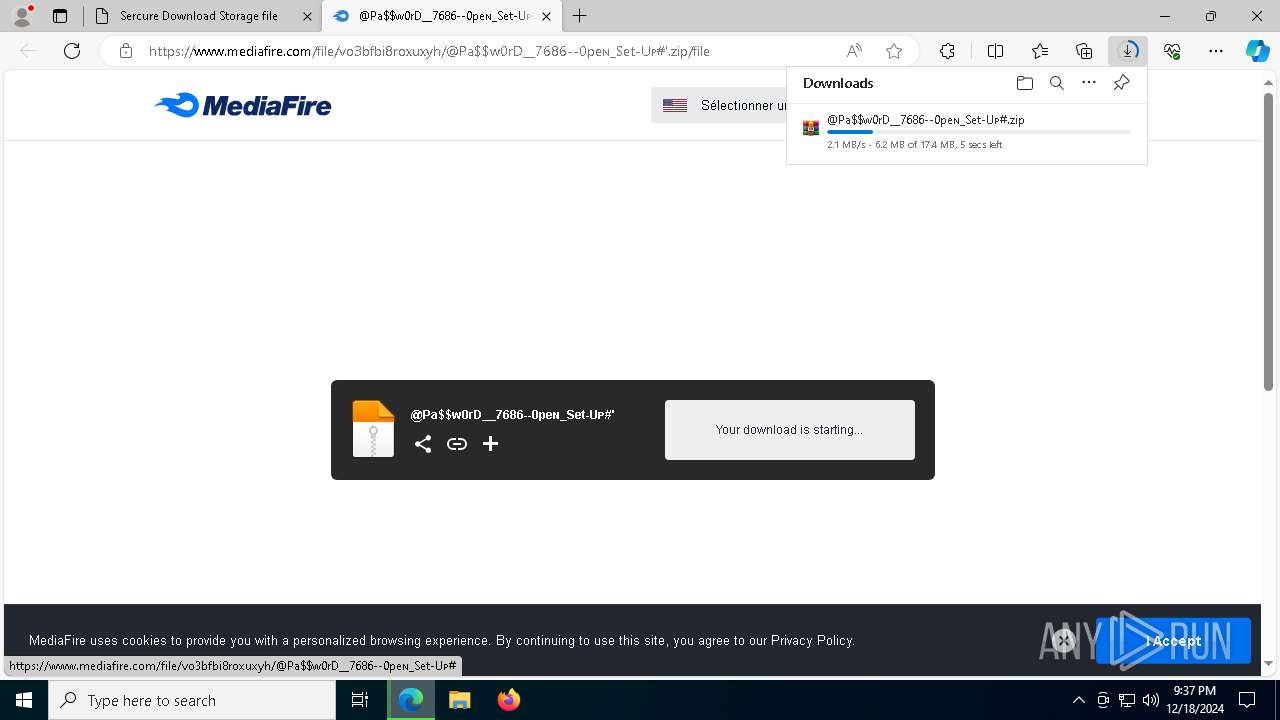
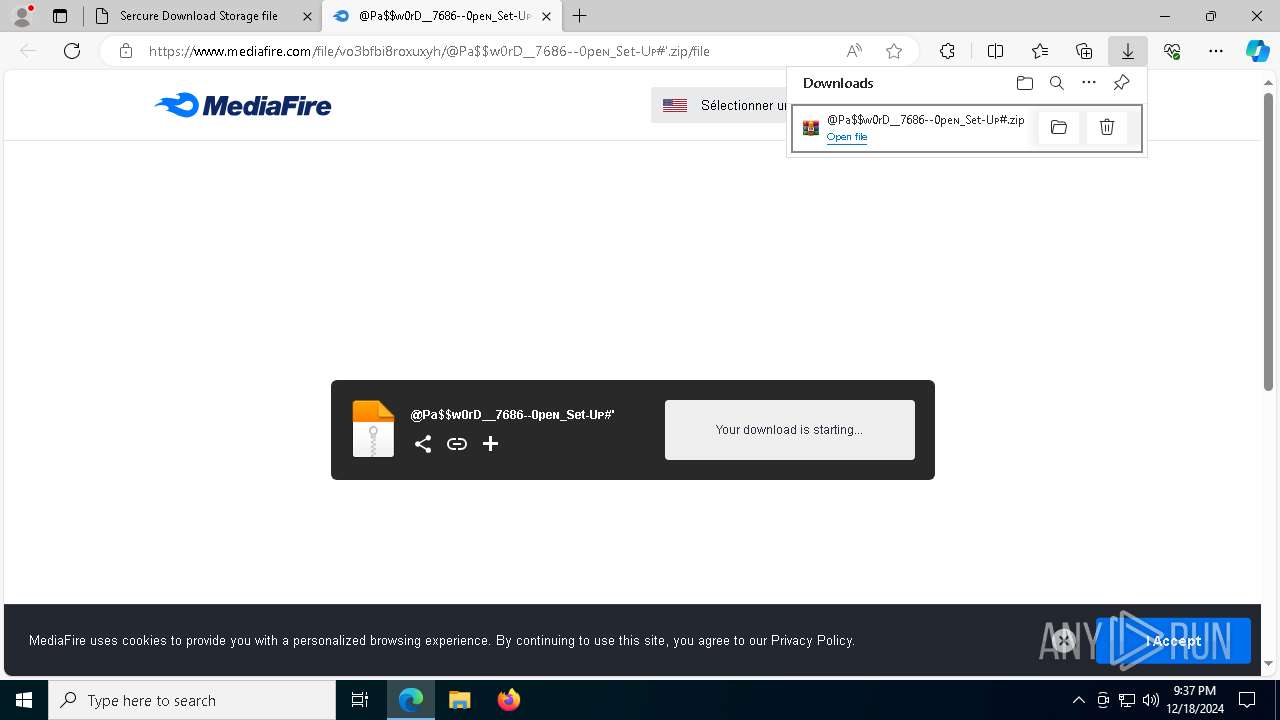
| URL: | https://bolire.shop/?s=Wondershare-Filmora-Crack-14-0-11---Key-Full-Download--Latest-&p=18 |
| Full analysis: | https://app.any.run/tasks/c3792adf-14e3-442d-af64-731cdcdc7624 |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | December 18, 2024, 21:37:32 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | C5221D7FD009838FF9B14FDFE5A6781D |
| SHA1: | 8325F98C662282F770E6B465F5A358680421E345 |
| SHA256: | A1FDA5F2127251998A59E6AA653DA5F755402D3DA417B2C7F023F1C9B6A69E6B |
| SSDEEP: | 3:N8pXALKKVPWQI0DAP9c2K4EE+IpEhRAn:25ALKKVOQRQc2Ft3qHA |
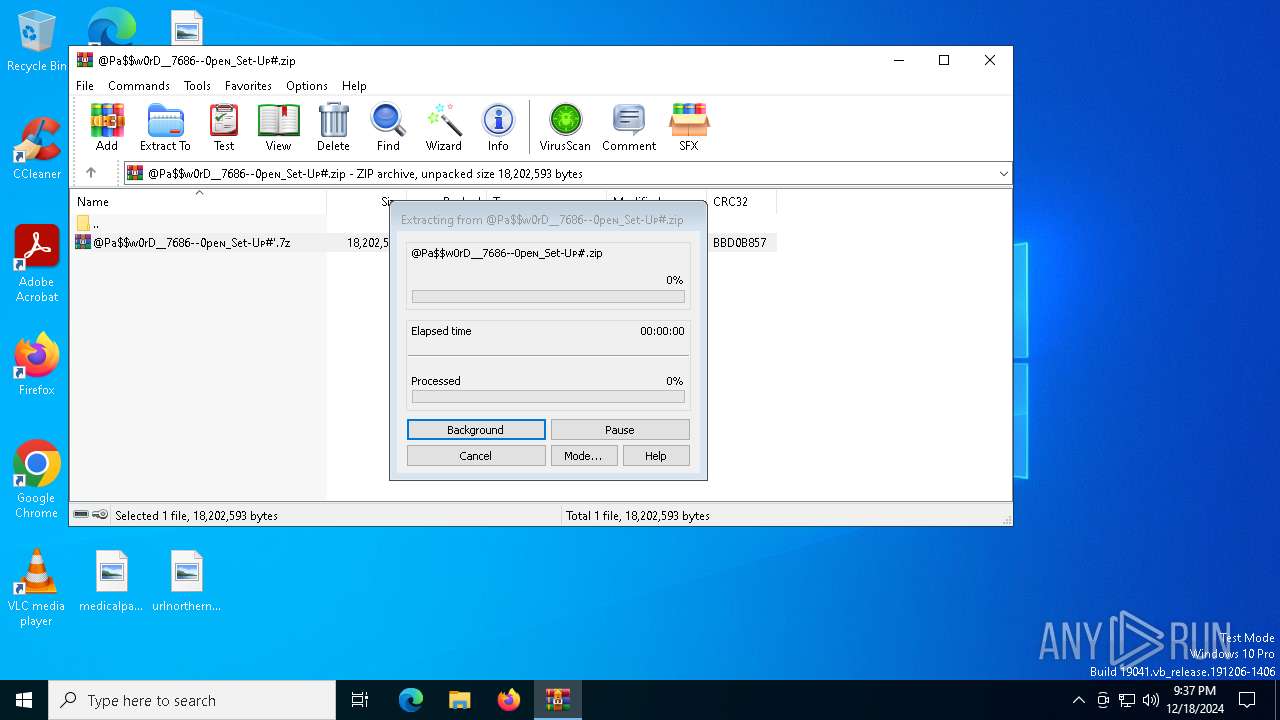
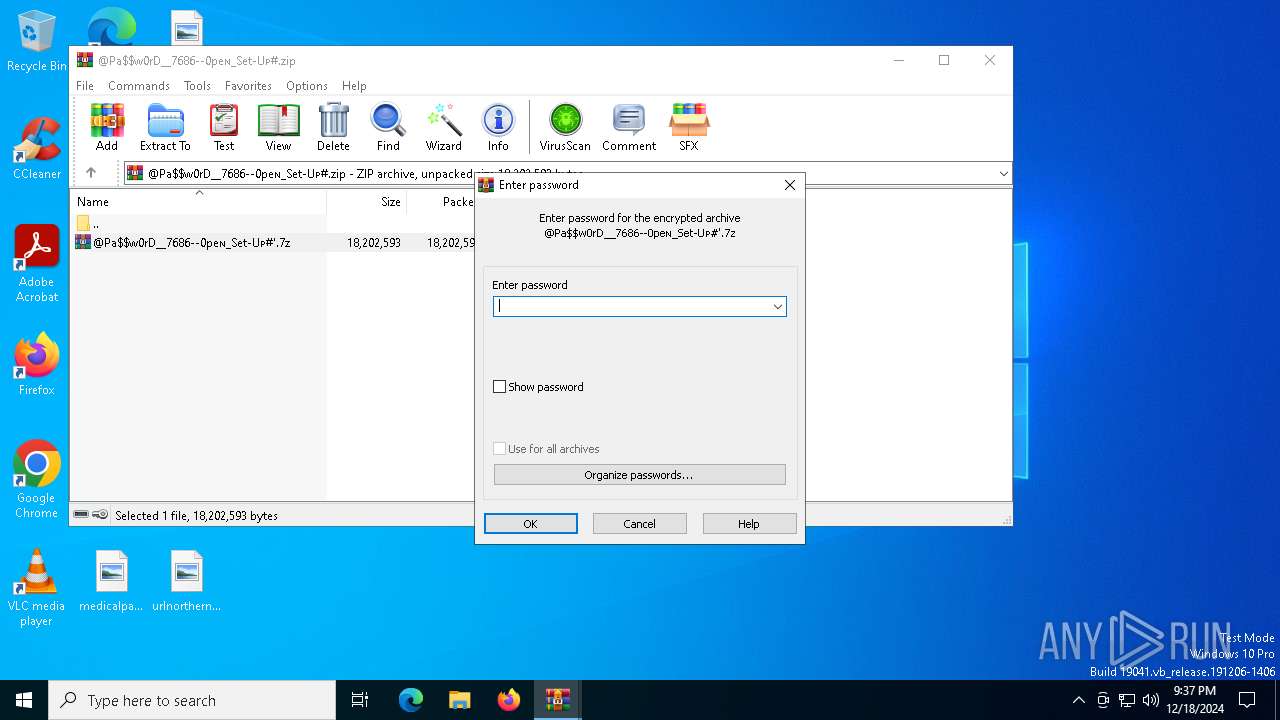
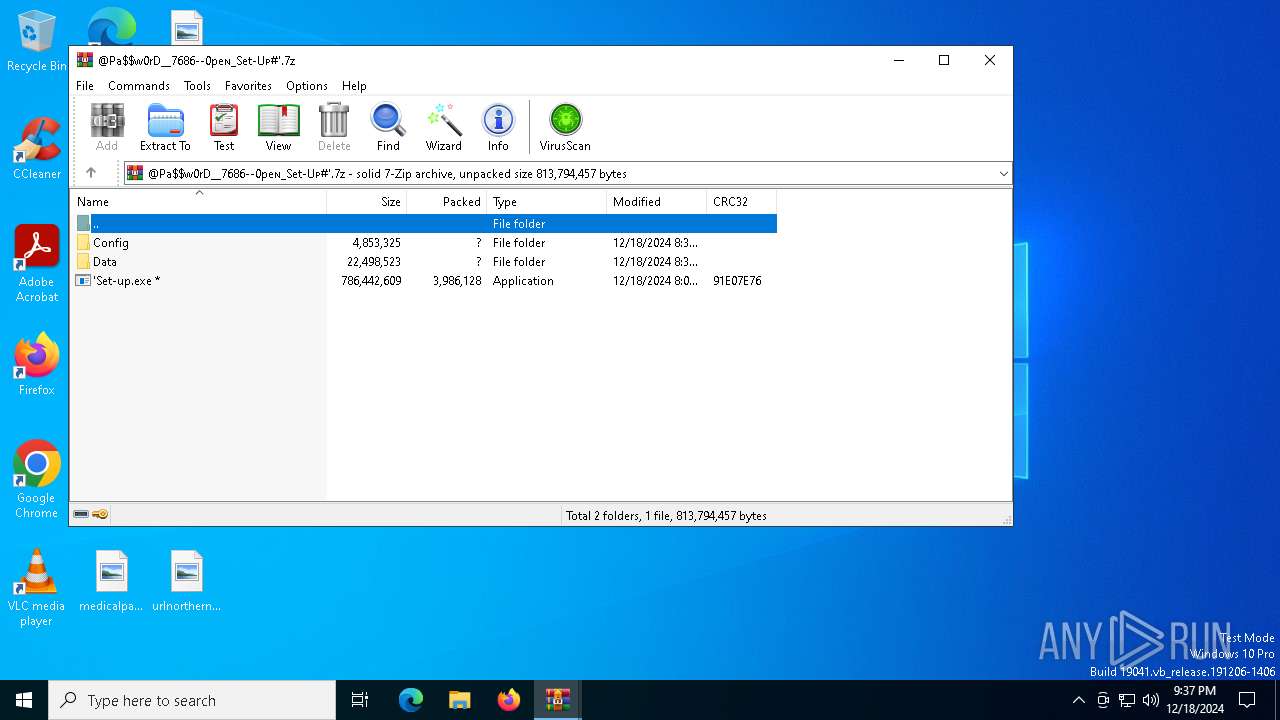
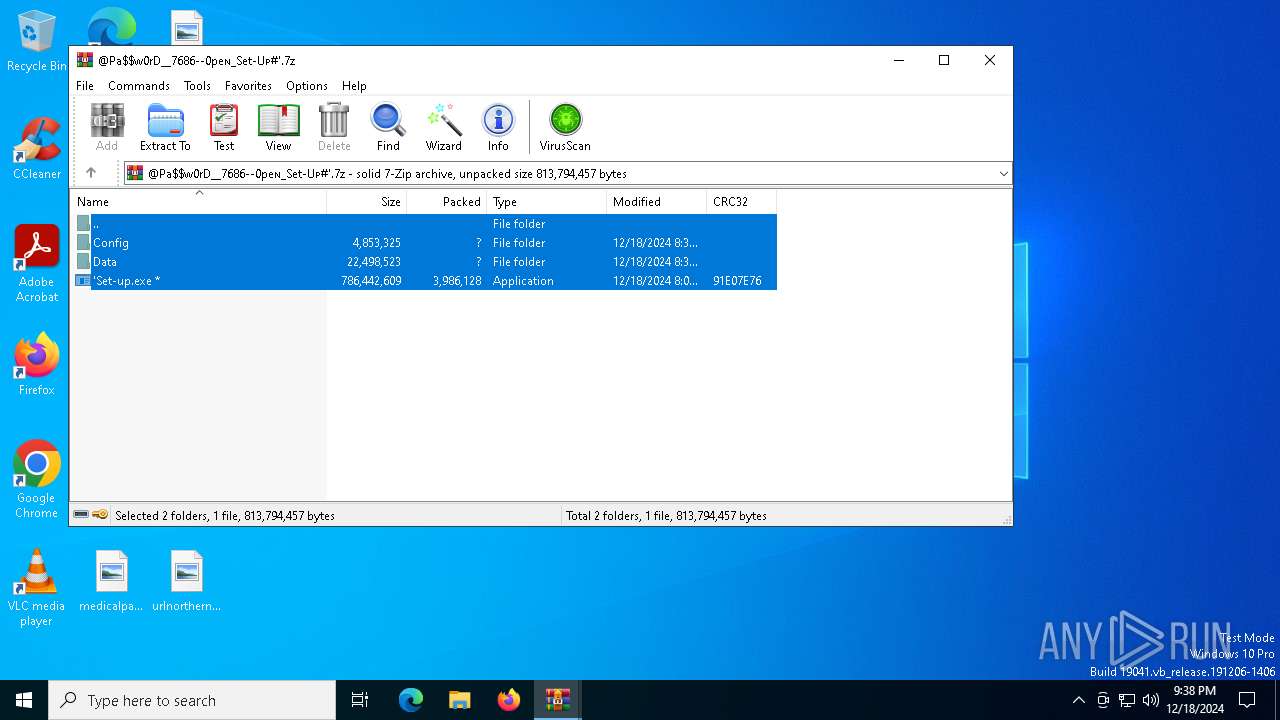
MALICIOUS
Executing a file with an untrusted certificate
- 'Set-up.exe (PID: 6672)
AutoIt loader has been detected (YARA)
- Warcraft.com (PID: 8080)
Actions looks like stealing of personal data
- Warcraft.com (PID: 8080)
LUMMA mutex has been found
- Warcraft.com (PID: 8080)
Bypass execution policy to execute commands
- powershell.exe (PID: 3736)
Run PowerShell with an invisible window
- powershell.exe (PID: 3736)
Changes powershell execution policy (Bypass)
- Warcraft.com (PID: 8080)
SUSPICIOUS
Reads security settings of Internet Explorer
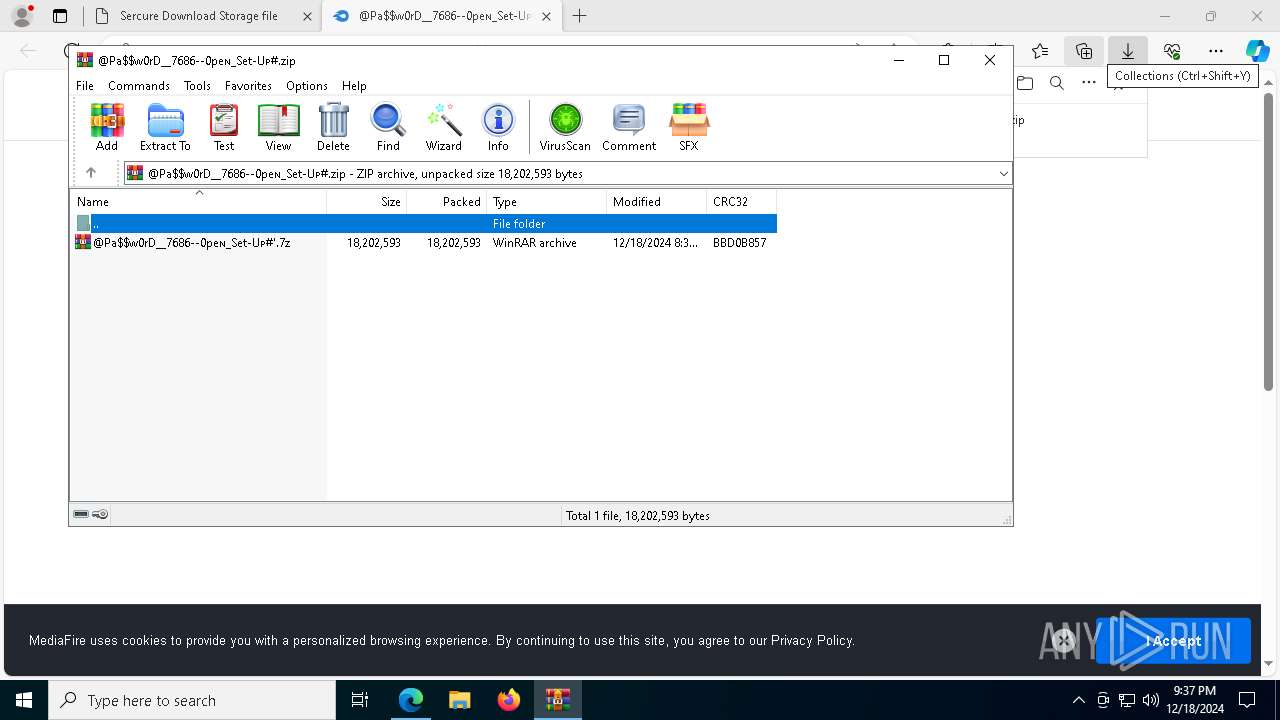
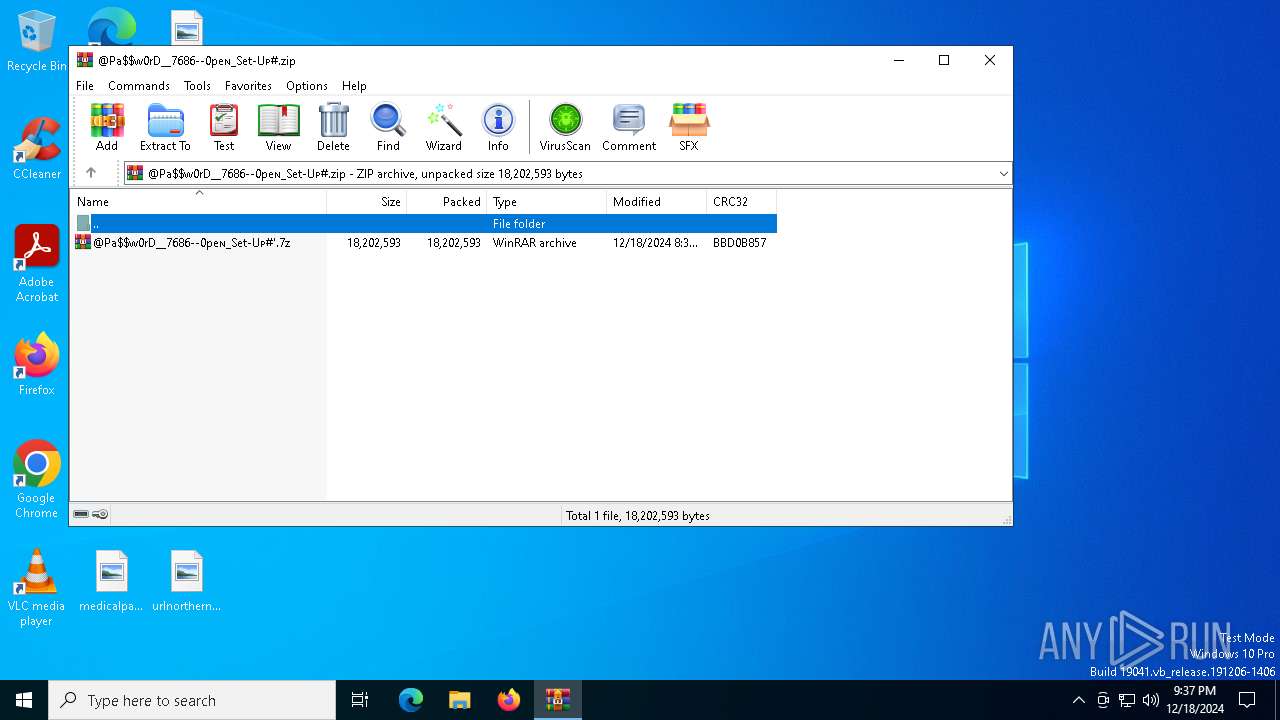
- WinRAR.exe (PID: 5640)
Potential Corporate Privacy Violation
- msedge.exe (PID: 6688)
Application launched itself
- WinRAR.exe (PID: 5640)
- cmd.exe (PID: 7720)
Process drops legitimate windows executable
- WinRAR.exe (PID: 7636)
Starts CMD.EXE for commands execution
- 'Set-up.exe (PID: 6672)
- cmd.exe (PID: 7720)
Executing commands from ".cmd" file
- 'Set-up.exe (PID: 6672)
Get information on the list of running processes
- cmd.exe (PID: 7720)
The executable file from the user directory is run by the CMD process
- Warcraft.com (PID: 8080)
Starts the AutoIt3 executable file
- cmd.exe (PID: 7720)
Starts POWERSHELL.EXE for commands execution
- Warcraft.com (PID: 8080)
HTML script is executed
- Warcraft.com (PID: 8080)
Found IP address in command line
- powershell.exe (PID: 3736)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 7720)
Starts application with an unusual extension
- cmd.exe (PID: 7720)
INFO
Application launched itself
- msedge.exe (PID: 6320)
- msedge.exe (PID: 6564)
Reads Environment values
- identity_helper.exe (PID: 7304)
- identity_helper.exe (PID: 3260)
Reads the computer name
- identity_helper.exe (PID: 7304)
- identity_helper.exe (PID: 3260)
- Warcraft.com (PID: 8080)
Checks supported languages
- identity_helper.exe (PID: 7304)
- identity_helper.exe (PID: 3260)
- 'Set-up.exe (PID: 6672)
- Warcraft.com (PID: 8080)
Reads Microsoft Office registry keys
- msedge.exe (PID: 6320)
The process uses the downloaded file
- WinRAR.exe (PID: 5640)
- WinRAR.exe (PID: 7636)
- 'Set-up.exe (PID: 6672)
The sample compiled with english language support
- WinRAR.exe (PID: 7636)
- msedge.exe (PID: 8056)
Manual execution by a user
- 'Set-up.exe (PID: 6672)
Create files in a temporary directory
- 'Set-up.exe (PID: 6672)
- powershell.exe (PID: 3736)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7636)
- msedge.exe (PID: 8056)
Process checks computer location settings
- 'Set-up.exe (PID: 6672)
Creates a new folder
- cmd.exe (PID: 6324)
Reads mouse settings
- Warcraft.com (PID: 8080)
Reads the software policy settings
- Warcraft.com (PID: 8080)
- powershell.exe (PID: 3736)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 3736)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
207
Monitored processes
78
Malicious processes
6
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 644 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4388 --field-trial-handle=2352,i,9293474071139525394,16501459541237191218,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 900 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4884 --field-trial-handle=2352,i,9293474071139525394,16501459541237191218,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1488 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=2696 --field-trial-handle=2352,i,9293474071139525394,16501459541237191218,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1556 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6824 --field-trial-handle=2192,i,12491704456049901380,9610153397761981876,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1556 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=3496 --field-trial-handle=2352,i,9293474071139525394,16501459541237191218,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1804 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --no-appcompat-clear --gpu-preferences=WAAAAAAAAADoAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAABEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=5156 --field-trial-handle=2352,i,9293474071139525394,16501459541237191218,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2216 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://bolire.shop/?s=Wondershare-Filmora-Crack-14-0-11---Key-Full-Download--Latest-&p=18" | C:\Program Files\Internet Explorer\iexplore.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2512 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2996 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=3548 --field-trial-handle=2352,i,9293474071139525394,16501459541237191218,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 3060 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --no-appcompat-clear --mojo-platform-channel-handle=5460 --field-trial-handle=2352,i,9293474071139525394,16501459541237191218,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
16 891
Read events
16 813
Write events
78
Delete events
0
Modification events
| (PID) Process: | (2216) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2216) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2216) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2216) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2216) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2216) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | DisableFirstRunCustomize |
Value: 1 | |||
| (PID) Process: | (6320) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6320) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6320) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6320) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
Executable files
34
Suspicious files
509
Text files
178
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6320 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF135660.TMP | — | |
MD5:— | SHA256:— | |||
| 6320 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF135660.TMP | — | |
MD5:— | SHA256:— | |||
| 6320 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6320 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6320 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF135680.TMP | — | |
MD5:— | SHA256:— | |||
| 6320 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6320 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF135680.TMP | — | |
MD5:— | SHA256:— | |||
| 6320 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6320 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF135680.TMP | — | |
MD5:— | SHA256:— | |||
| 6320 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
125
DNS requests
128
Threats
26
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6472 | svchost.exe | GET | 206 | 23.48.23.7:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/8699fac5-cf38-4f97-a2f8-fb1e47f5e54e?P1=1734856634&P2=404&P3=2&P4=Lk9M%2b%2fuhp48iuocqmHCWbqB20PuzeaINrgCE1qV4j712ogo0R2YV5Slq1KcKKGkmEo0r9SiceAf26AHyesSuyQ%3d%3d | unknown | — | — | whitelisted |
6472 | svchost.exe | GET | 206 | 23.48.23.7:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/8699fac5-cf38-4f97-a2f8-fb1e47f5e54e?P1=1734856634&P2=404&P3=2&P4=Lk9M%2b%2fuhp48iuocqmHCWbqB20PuzeaINrgCE1qV4j712ogo0R2YV5Slq1KcKKGkmEo0r9SiceAf26AHyesSuyQ%3d%3d | unknown | — | — | whitelisted |
6472 | svchost.exe | GET | 206 | 23.48.23.7:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/8699fac5-cf38-4f97-a2f8-fb1e47f5e54e?P1=1734856634&P2=404&P3=2&P4=Lk9M%2b%2fuhp48iuocqmHCWbqB20PuzeaINrgCE1qV4j712ogo0R2YV5Slq1KcKKGkmEo0r9SiceAf26AHyesSuyQ%3d%3d | unknown | — | — | whitelisted |
6472 | svchost.exe | GET | 206 | 23.48.23.7:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/8699fac5-cf38-4f97-a2f8-fb1e47f5e54e?P1=1734856634&P2=404&P3=2&P4=Lk9M%2b%2fuhp48iuocqmHCWbqB20PuzeaINrgCE1qV4j712ogo0R2YV5Slq1KcKKGkmEo0r9SiceAf26AHyesSuyQ%3d%3d | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
6472 | svchost.exe | HEAD | 200 | 23.48.23.7:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/8699fac5-cf38-4f97-a2f8-fb1e47f5e54e?P1=1734856634&P2=404&P3=2&P4=Lk9M%2b%2fuhp48iuocqmHCWbqB20PuzeaINrgCE1qV4j712ogo0R2YV5Slq1KcKKGkmEo0r9SiceAf26AHyesSuyQ%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5156 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 104.126.37.162:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6688 | msedge.exe | 104.21.22.251:443 | bolire.shop | — | — | malicious |
6320 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
bolire.shop |
| malicious |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6688 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
6688 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
6688 | msedge.exe | Potential Corporate Privacy Violation | ET INFO Fingerprinting Service in DNS Lookup (customfingerprints .bablosoft .com) |
6688 | msedge.exe | Potential Corporate Privacy Violation | ET INFO Fingerprinting Service in DNS Lookup (customfingerprints .bablosoft .com) |
6688 | msedge.exe | Potential Corporate Privacy Violation | ET INFO Browser Automation Toolkit in DNS Lookup (bablosoft .com) |
6688 | msedge.exe | Potential Corporate Privacy Violation | ET INFO Browser Automation Toolkit in DNS Lookup (bablosoft .com) |
6688 | msedge.exe | Potential Corporate Privacy Violation | ET INFO Browser Automation Toolkit in TLS SNI (bablosoft .com) |
6688 | msedge.exe | Potential Corporate Privacy Violation | ET INFO Fingerprinting Service in TLS SNI (customfingerprints .bablosoft .com) |
6688 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
6688 | msedge.exe | Potential Corporate Privacy Violation | ET INFO Fingerprinting Service in DNS Lookup (customfingerprints .bablosoft .com) |