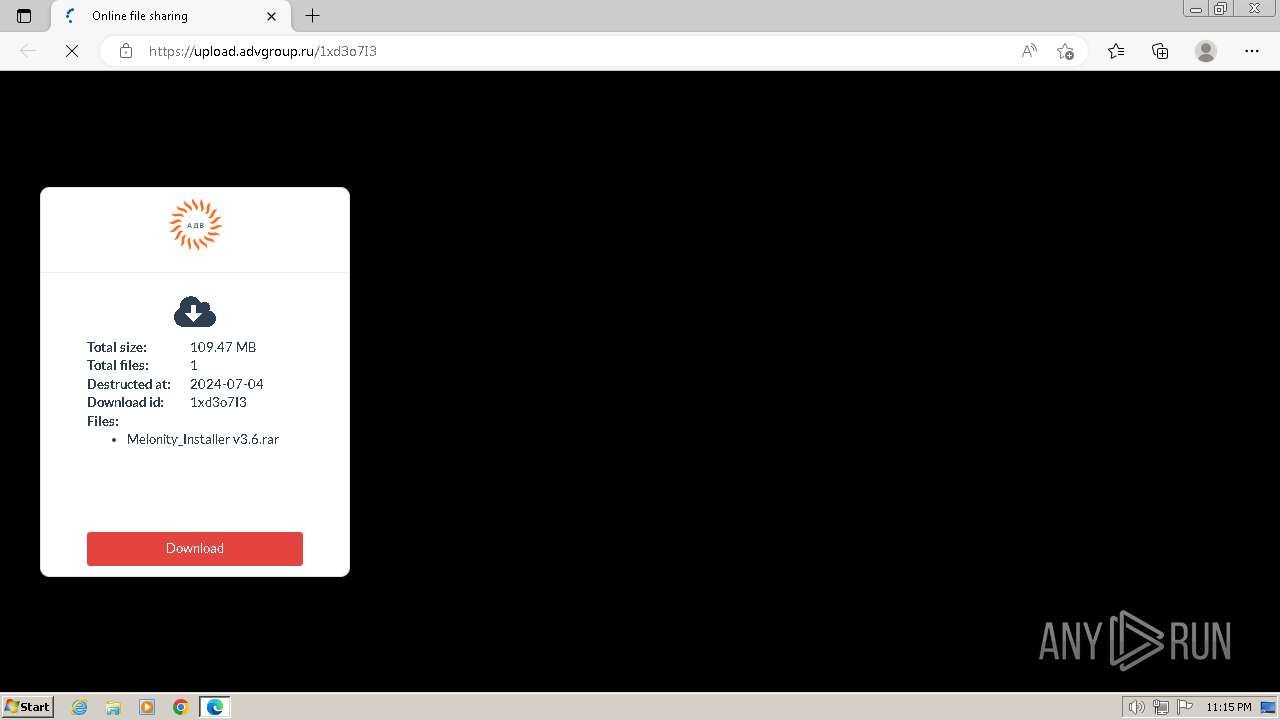
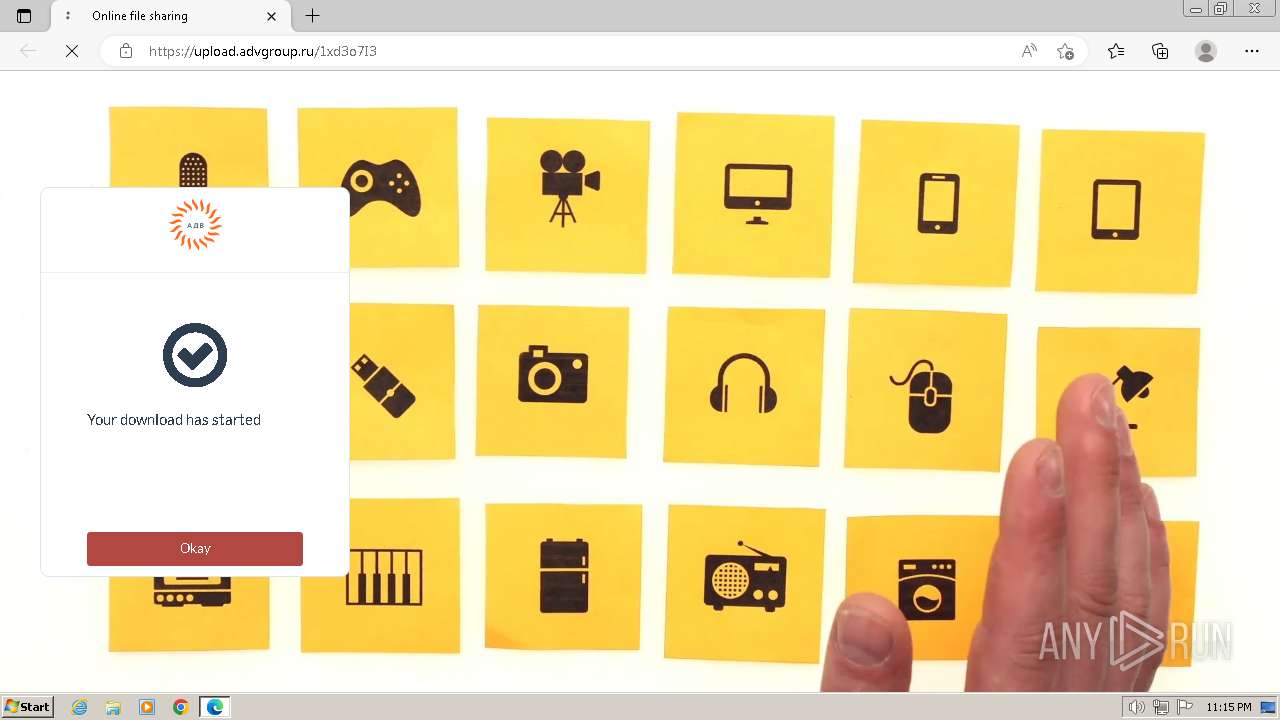
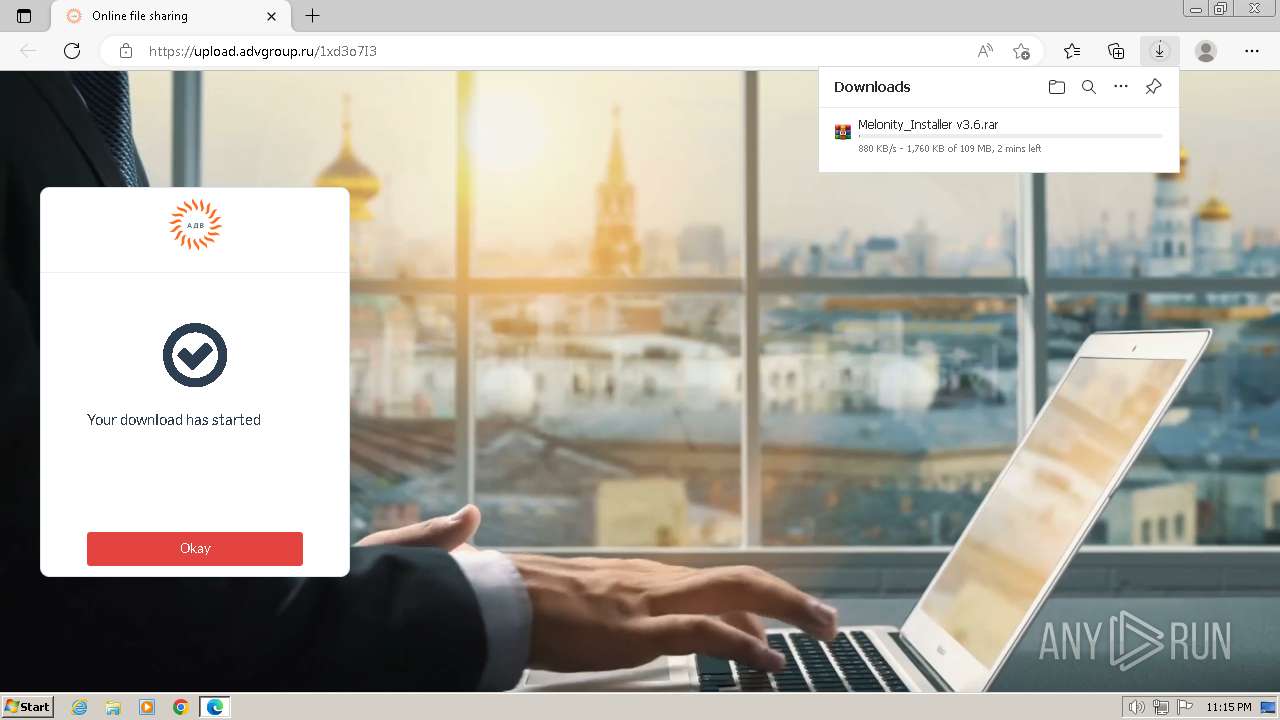
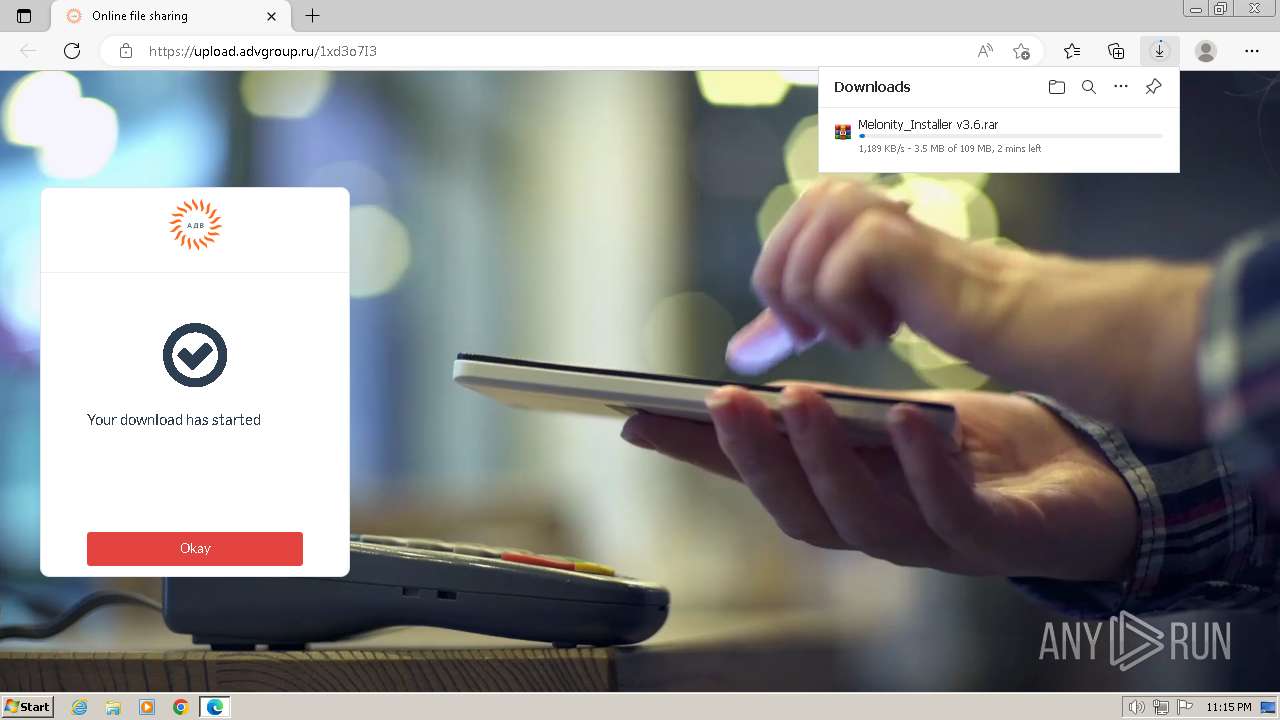
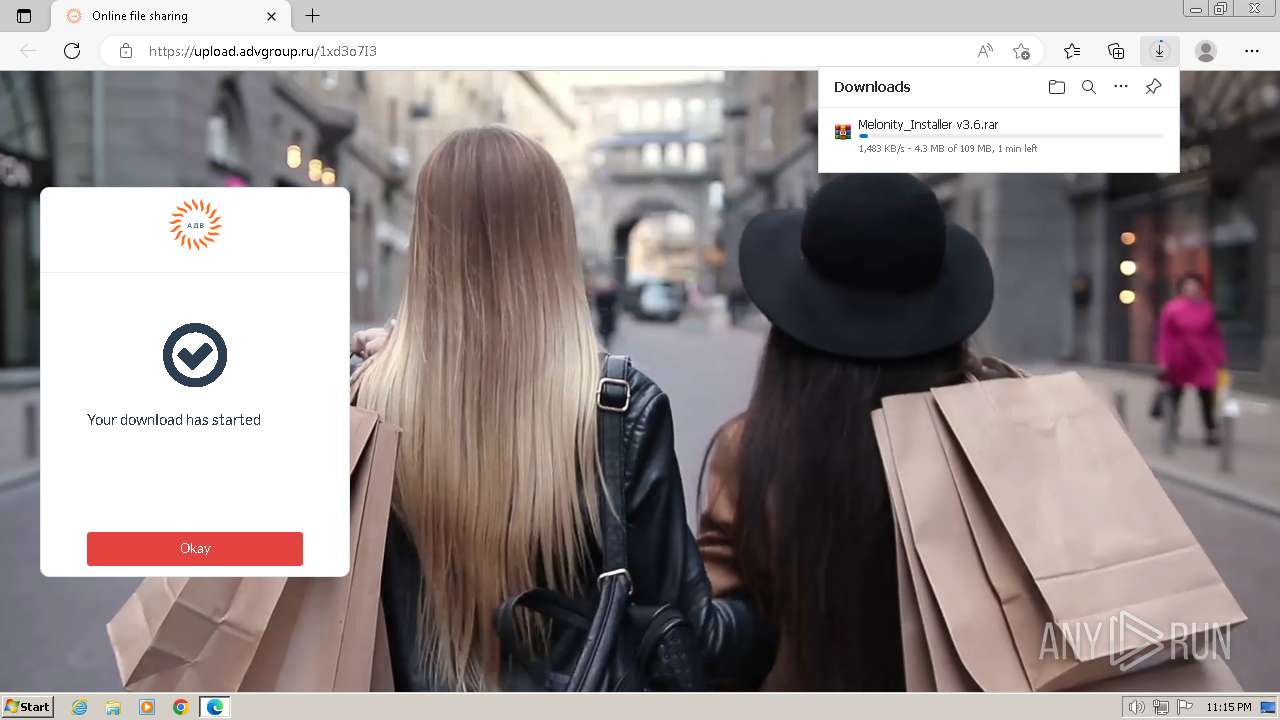
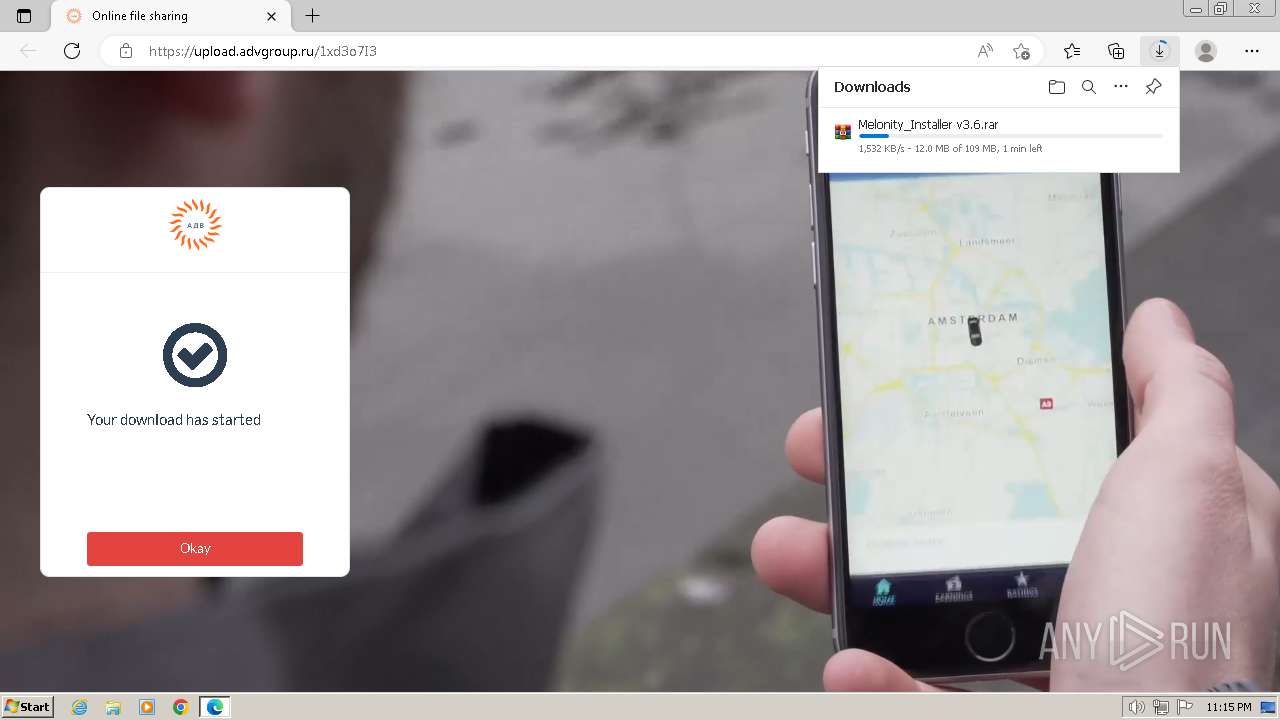
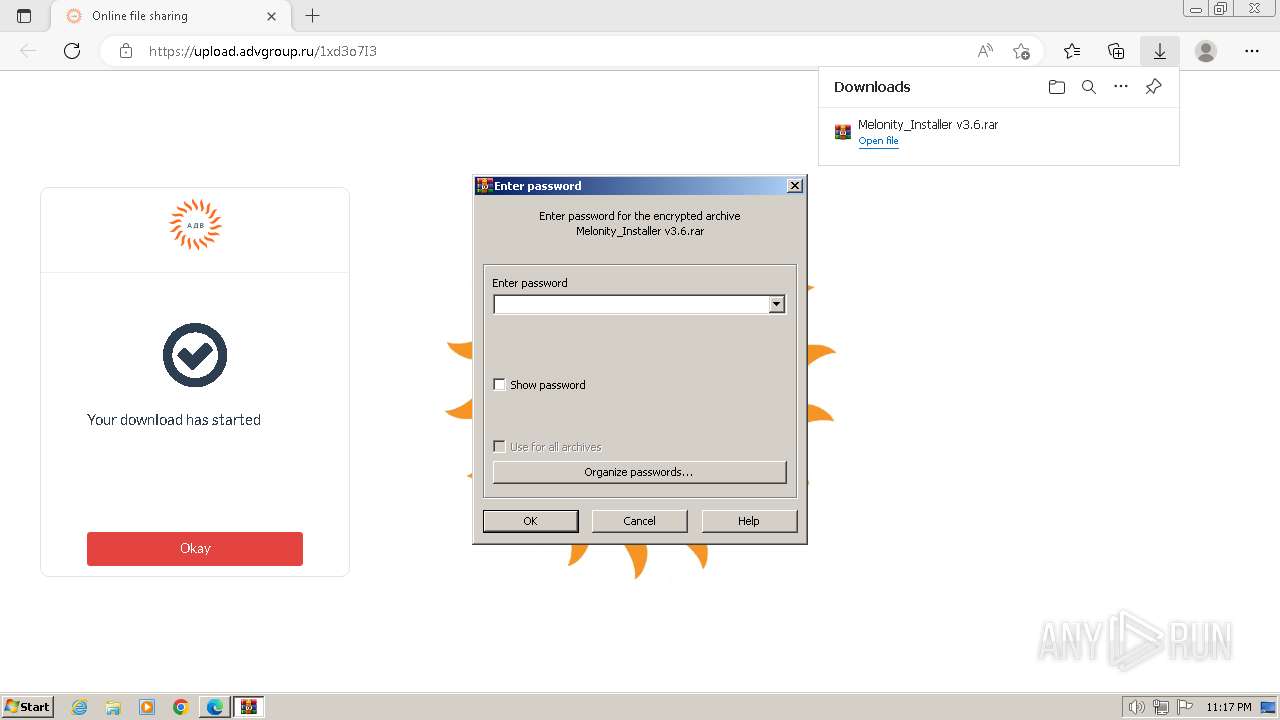
| URL: | upload.advgroup.ru/1xd3o7I3 |
| Full analysis: | https://app.any.run/tasks/f3520981-028a-4512-8cea-ae28e6a0f3d4 |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | June 23, 2024, 22:15:36 |
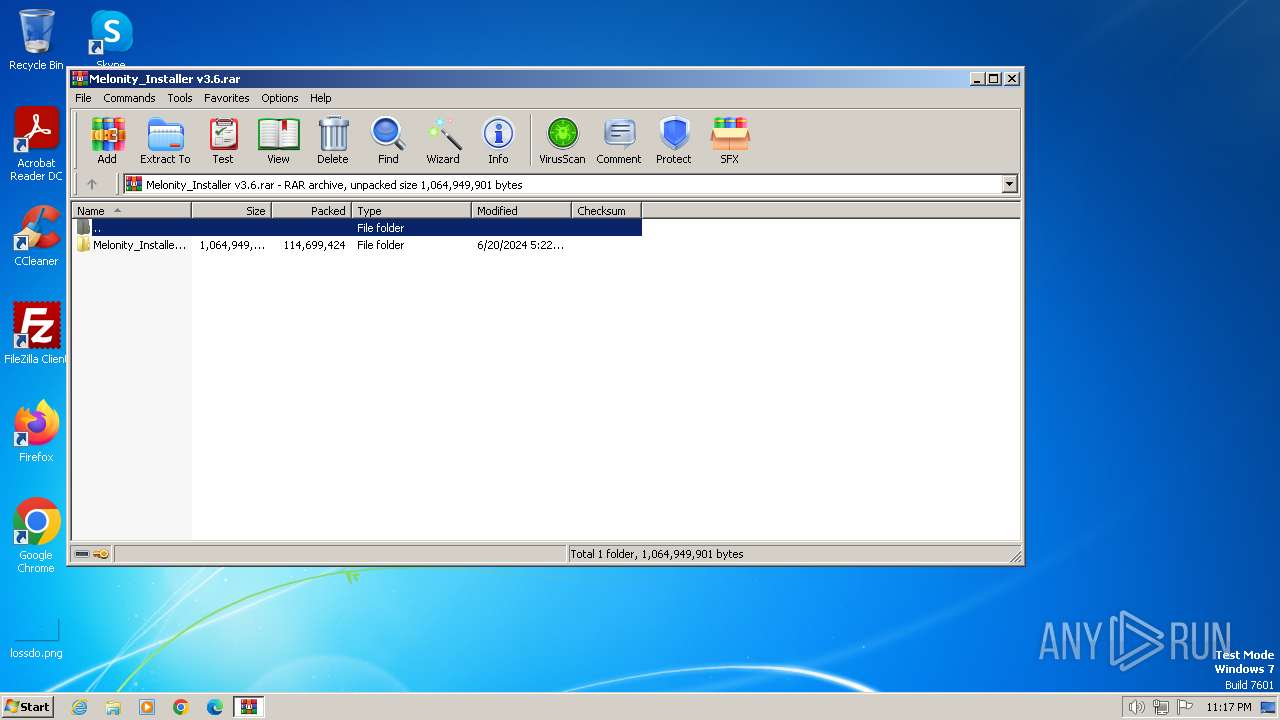
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 8C637D06DED4354222600D2909DFC93F |
| SHA1: | 01FD53AB9154EE19EAD4D6932EDD7DB4201C6FE0 |
| SHA256: | A1BCE5A1691F8E182BECC04C154790123DBBBAC2E7B489737464E8FD9E43FEB1 |
| SSDEEP: | 3:AtBcBWiW:AUWiW |
MALICIOUS
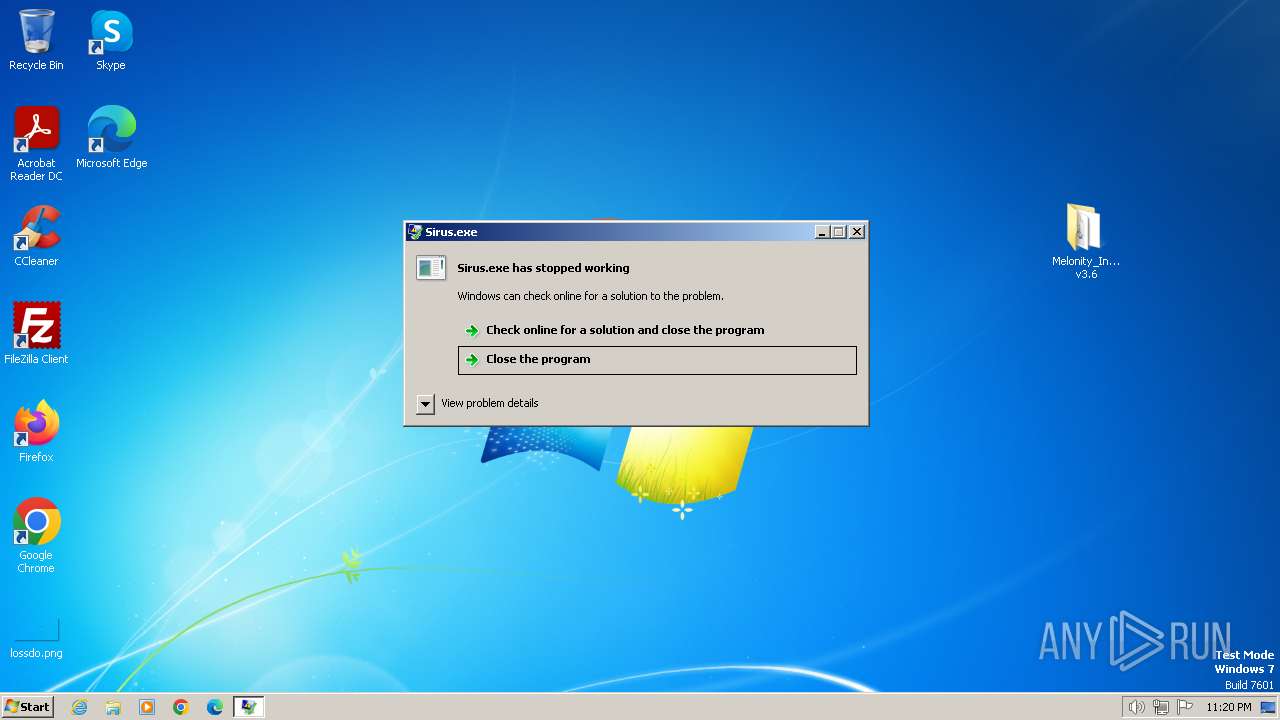
LUMMA has been detected (YARA)
- Sirus.exe (PID: 3872)
- Sirus.exe (PID: 2292)
SUSPICIOUS
No suspicious indicators.INFO
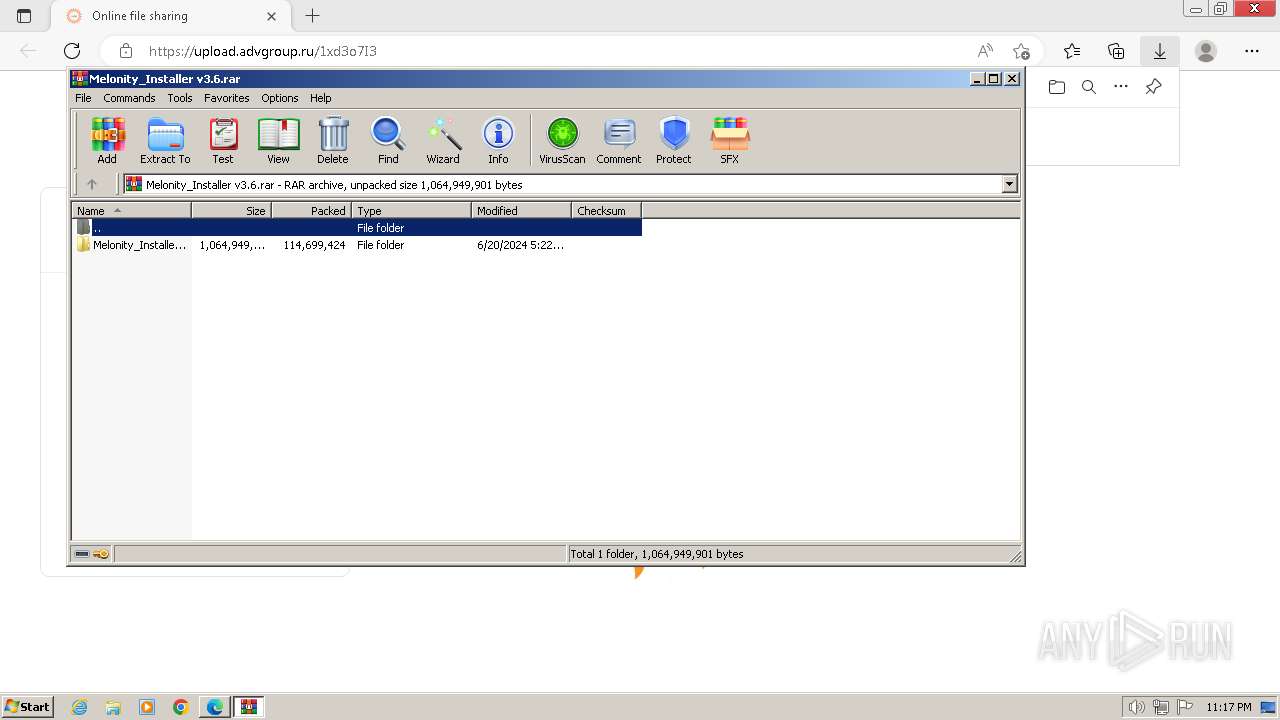
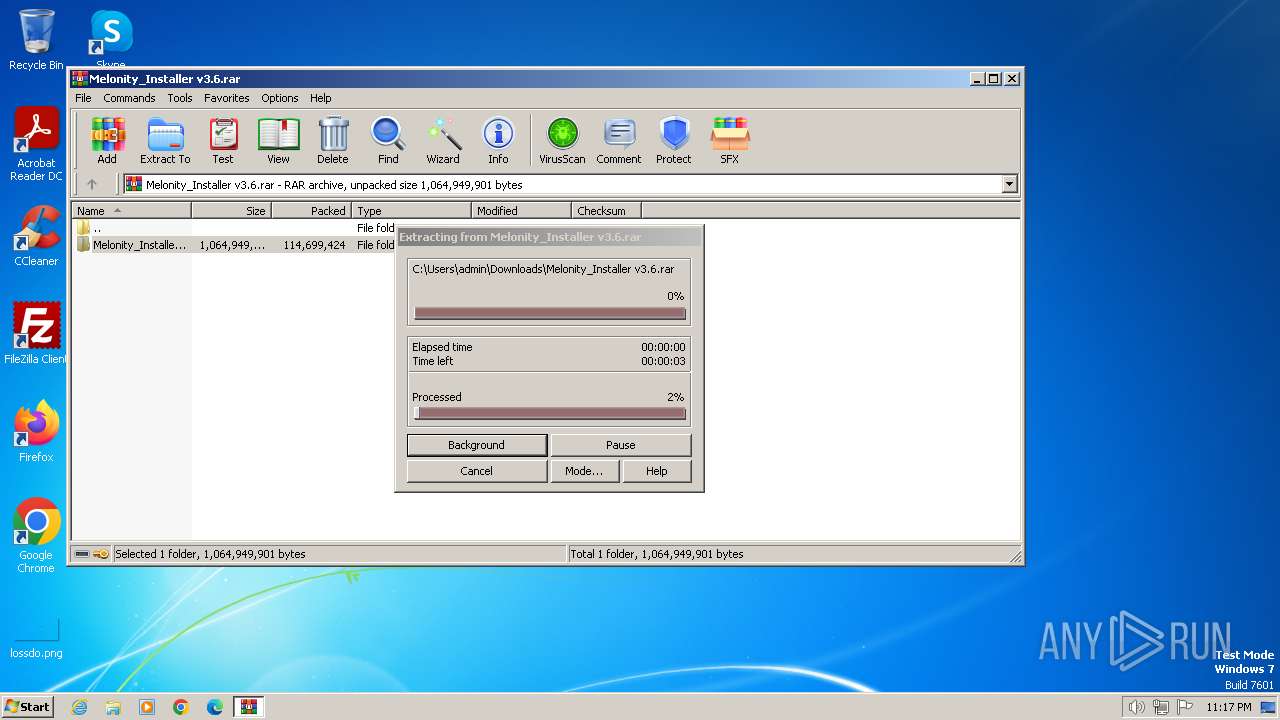
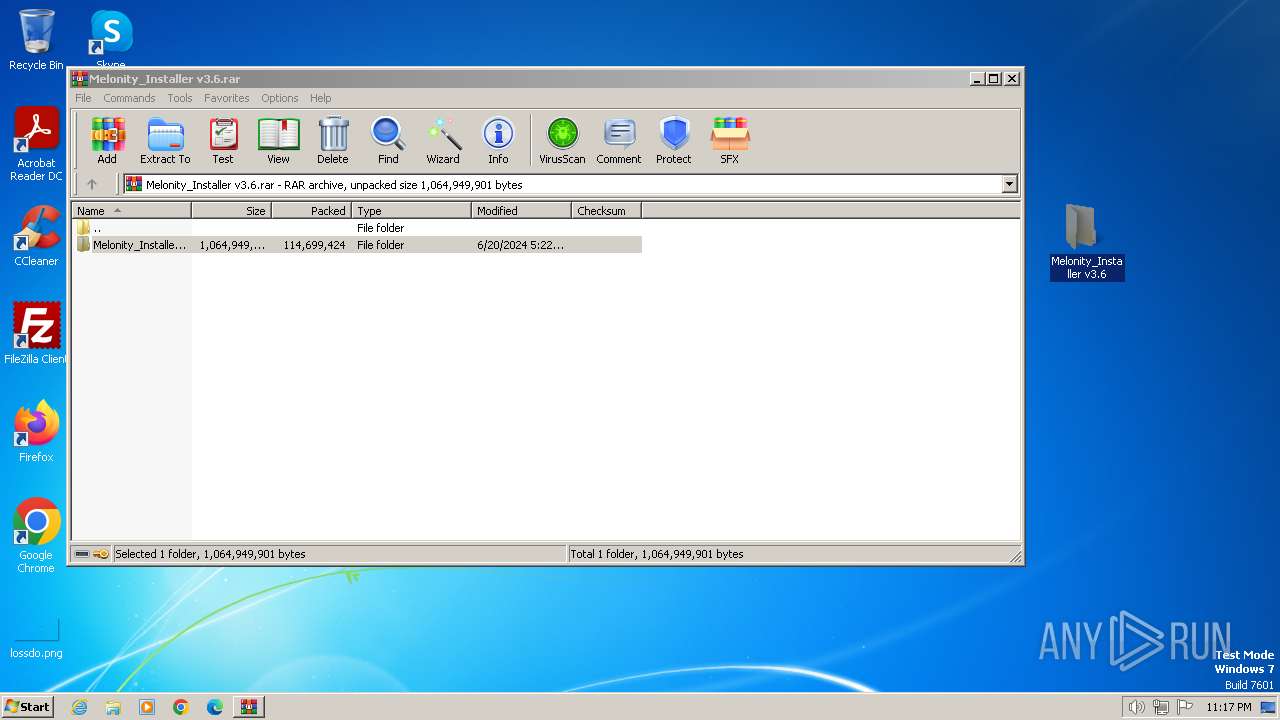
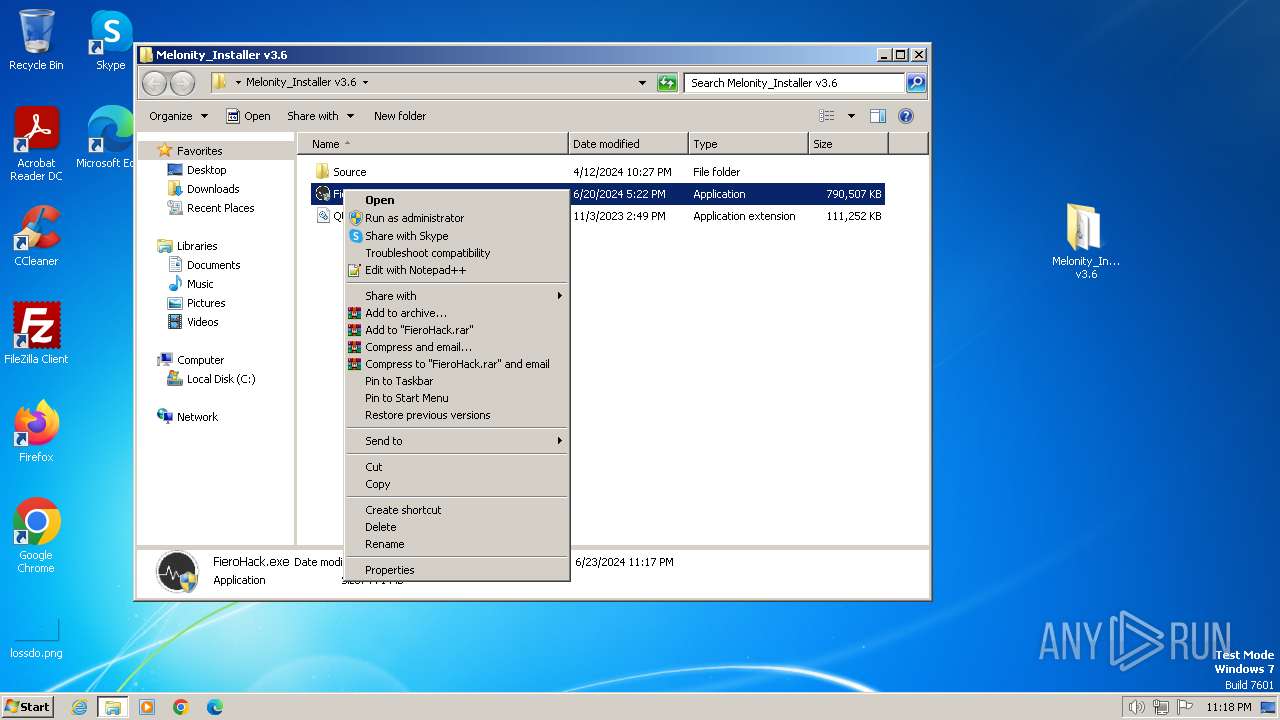
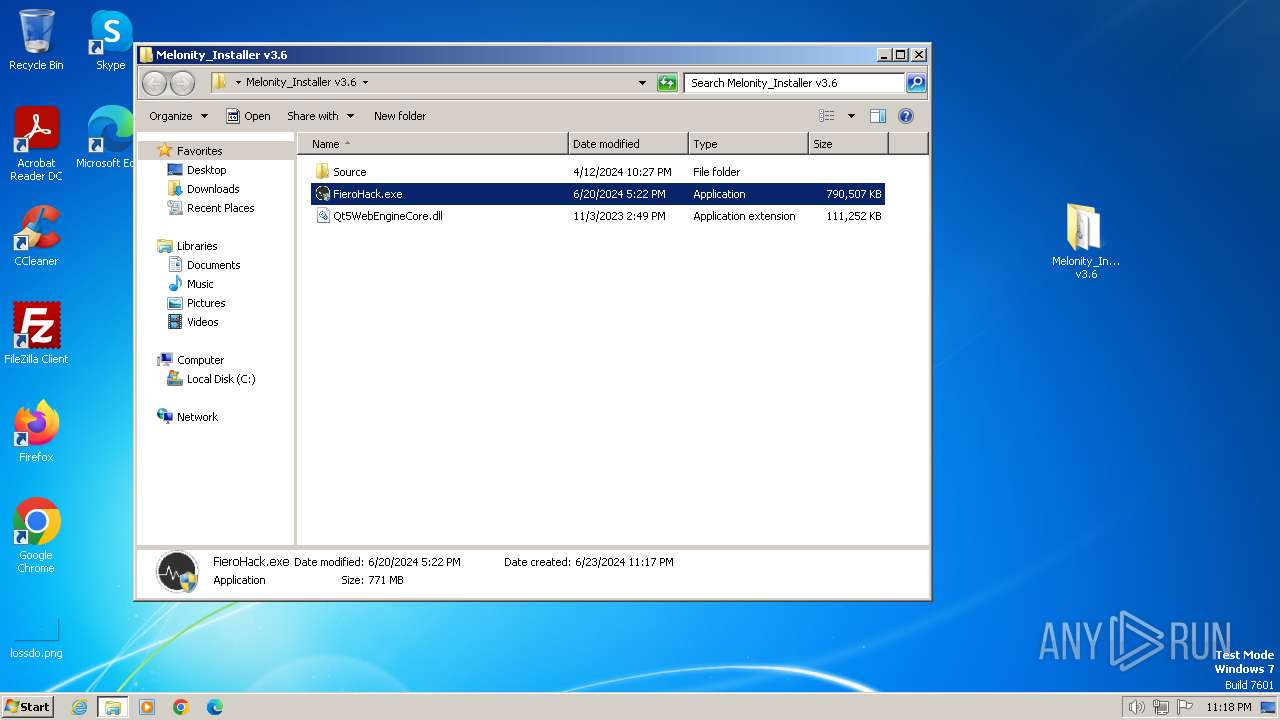
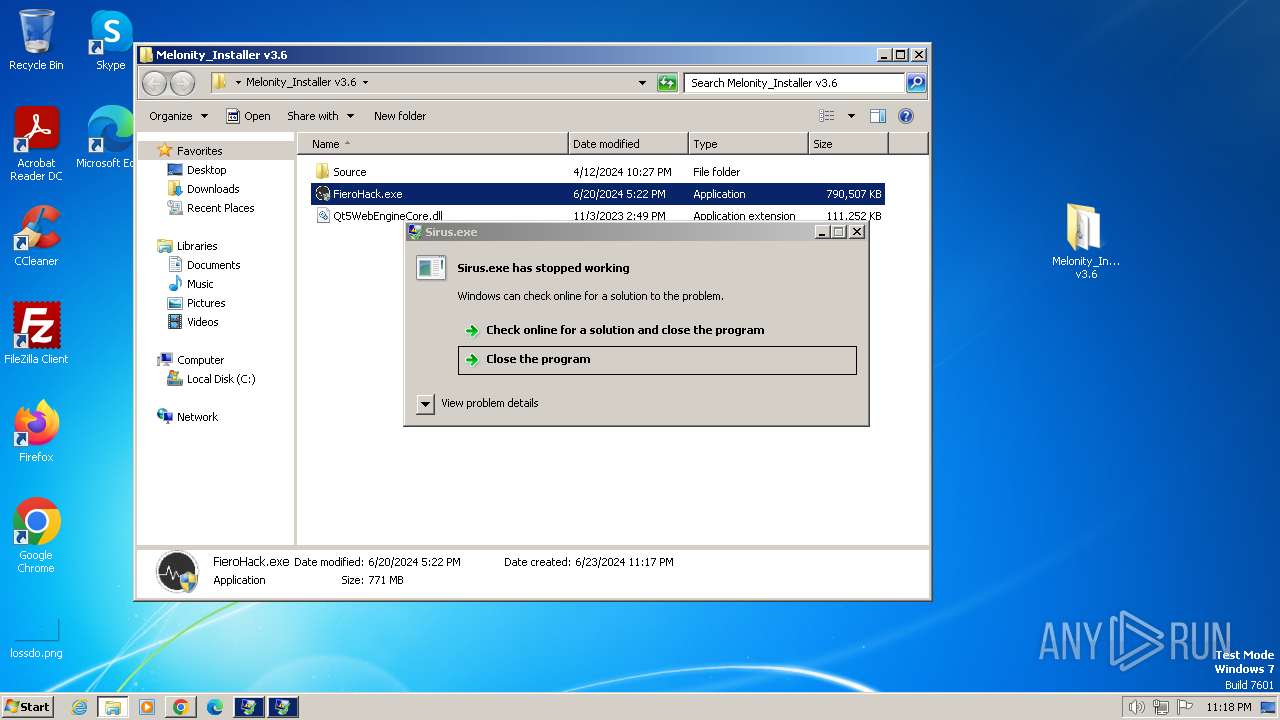
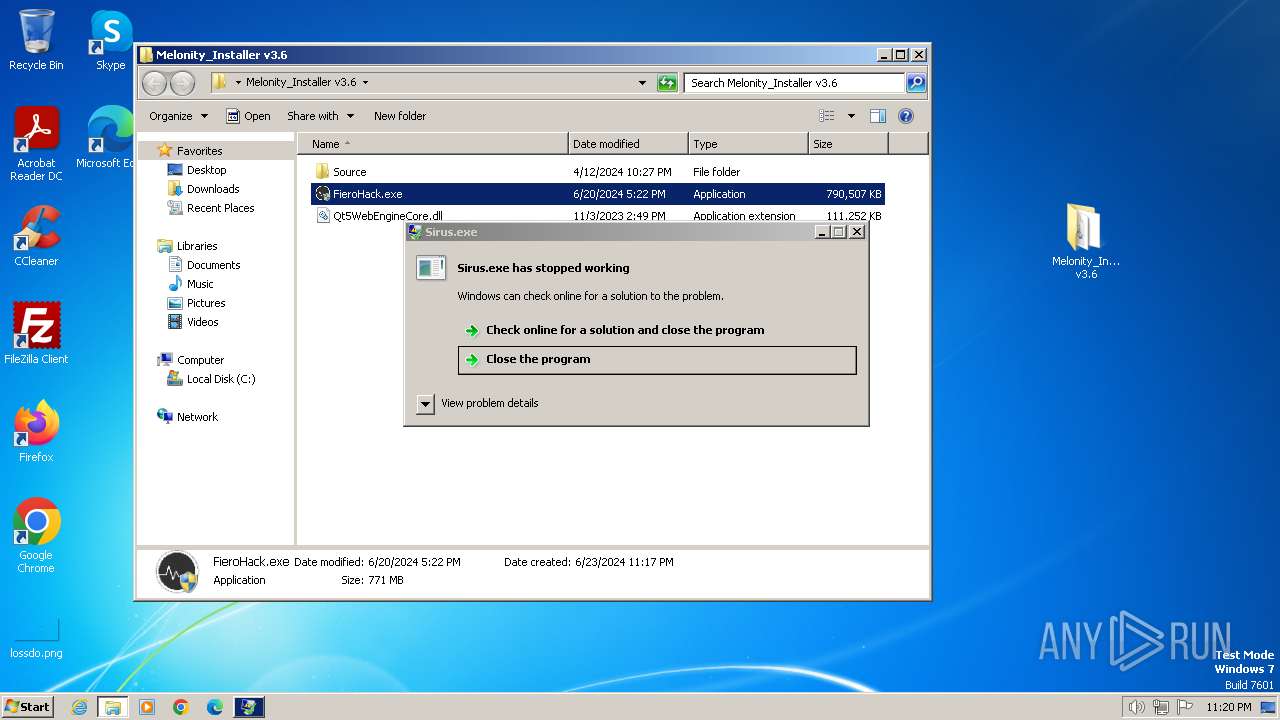
Drops the executable file immediately after the start
- WinRAR.exe (PID: 2436)
Application launched itself
- msedge.exe (PID: 3380)
Checks supported languages
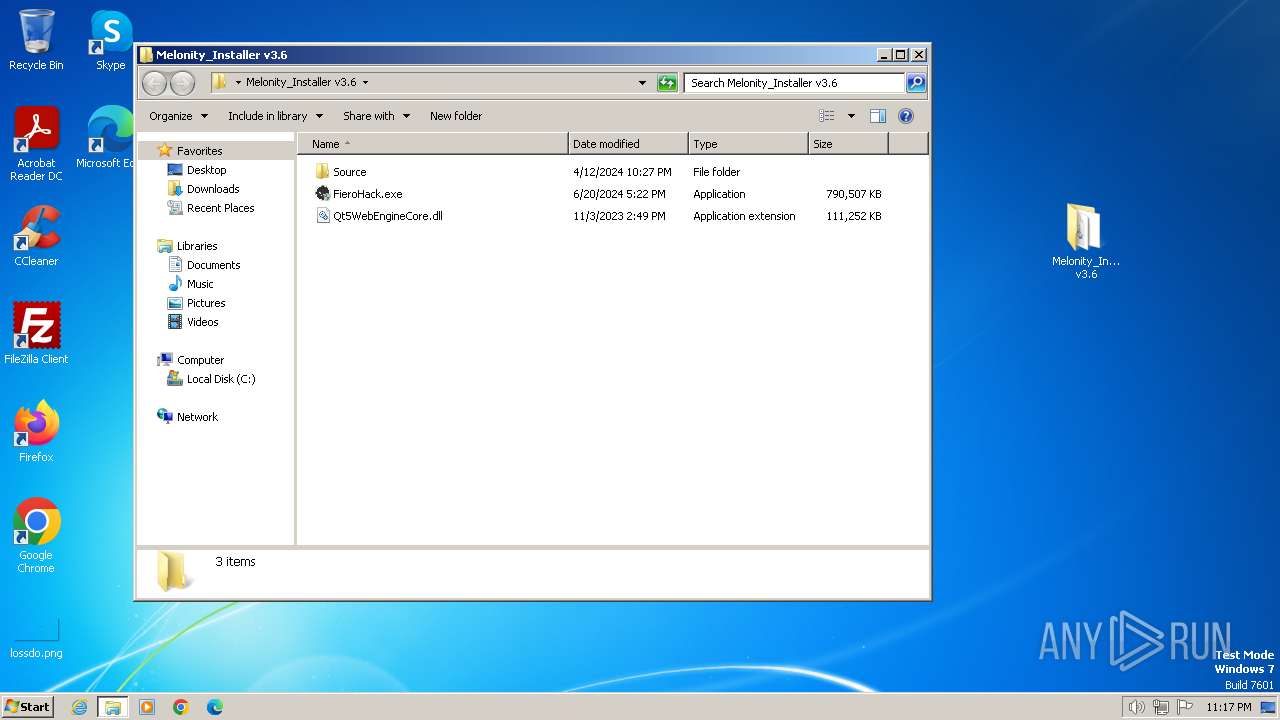
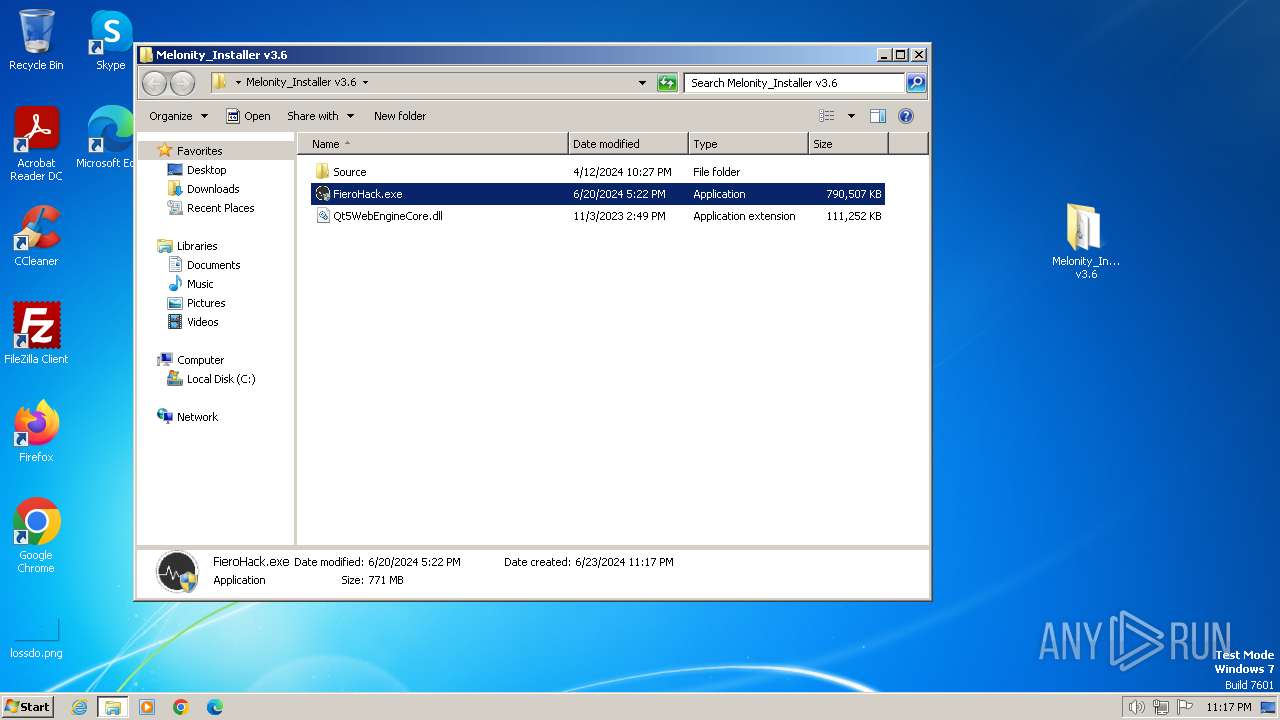
- FieroHack.exe (PID: 2036)
- FieroHack.exe (PID: 4020)
- Sirus.exe (PID: 3872)
- Sirus.exe (PID: 2292)
Reads the computer name
- FieroHack.exe (PID: 2036)
- FieroHack.exe (PID: 4020)
Creates files or folders in the user directory
- FieroHack.exe (PID: 2036)
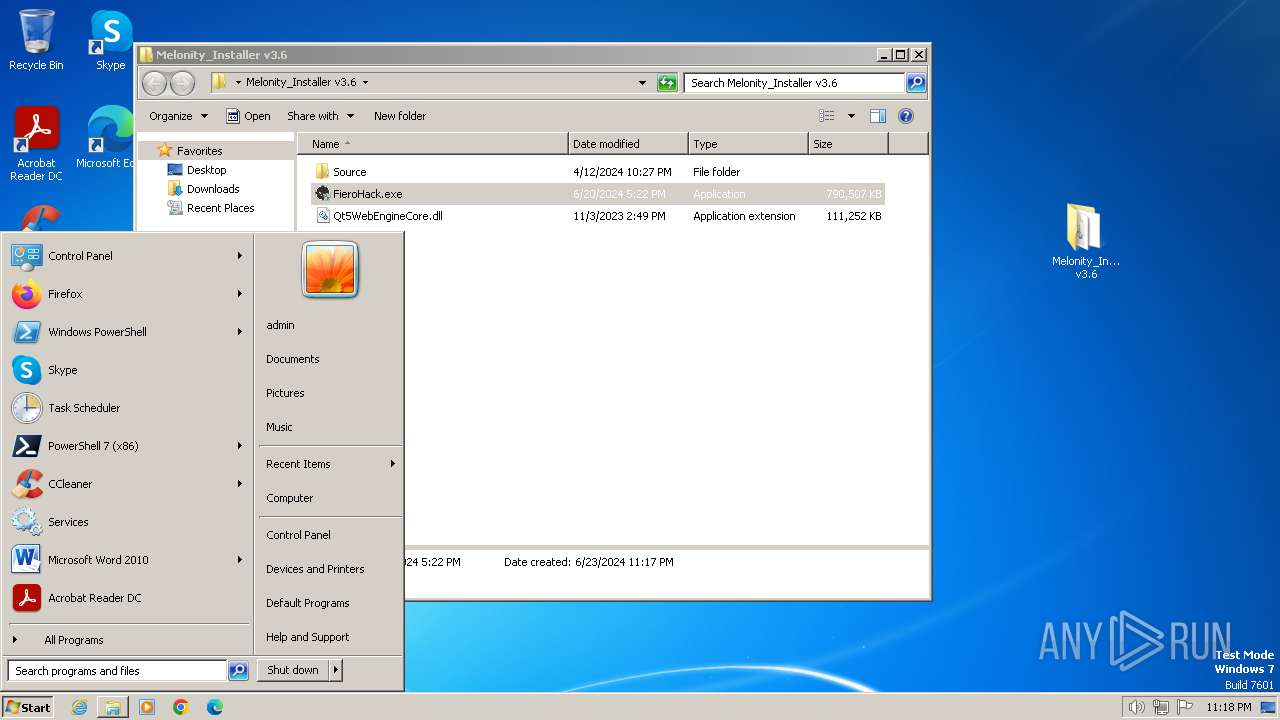
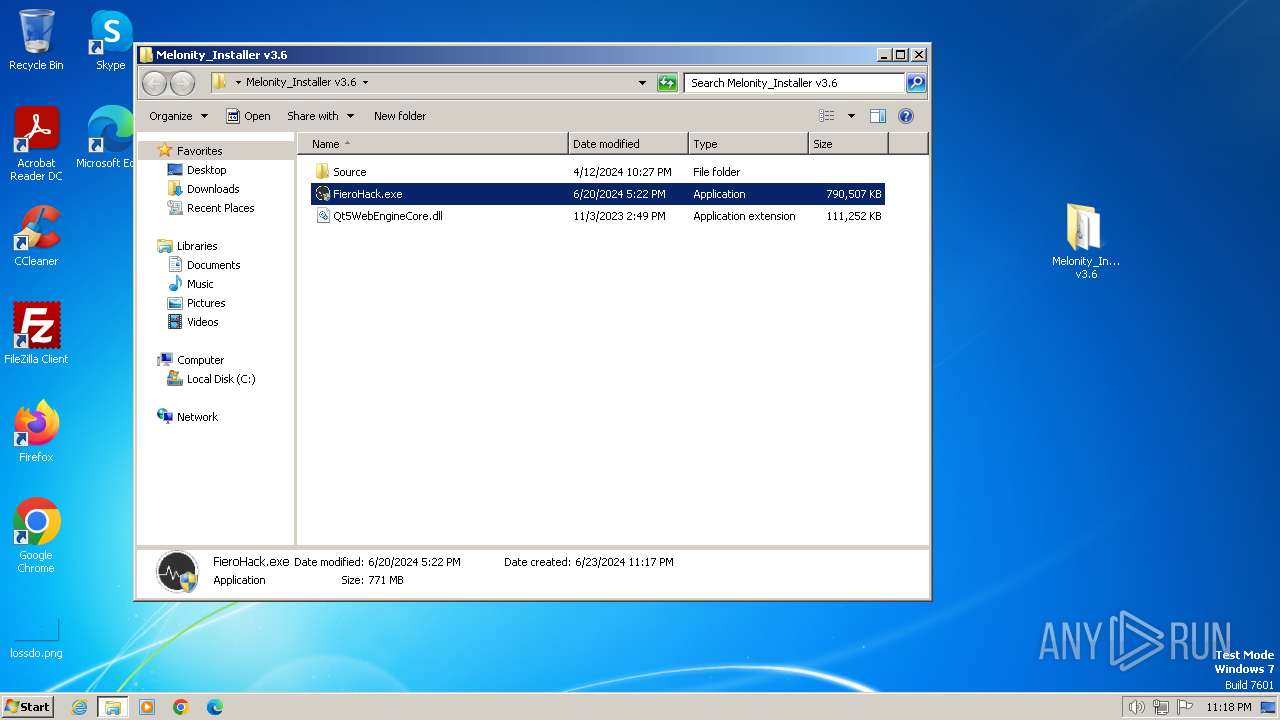
Manual execution by a user
- FieroHack.exe (PID: 3168)
- FieroHack.exe (PID: 2036)
- FieroHack.exe (PID: 4020)
The process uses the downloaded file
- WinRAR.exe (PID: 2436)
- msedge.exe (PID: 2332)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2436)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Lumma
(PID) Process(3872) Sirus.exe
C2 (9)injurypiggyoewirog.shop
bargainnygroandjwk.shop
leafcalfconflcitw.shop
composepayyersellew.shop
disappointcredisotw.shop
computerexcudesp.shop
doughtdrillyksow.shop
publicitycharetew.shop
facilitycoursedw.shop
(PID) Process(2292) Sirus.exe
C2 (9)injurypiggyoewirog.shop
bargainnygroandjwk.shop
leafcalfconflcitw.shop
composepayyersellew.shop
disappointcredisotw.shop
computerexcudesp.shop
doughtdrillyksow.shop
publicitycharetew.shop
facilitycoursedw.shop
Total processes
72
Monitored processes
24
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1044 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --first-renderer-process --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=2140 --field-trial-handle=1124,i,9157590743650421898,1809091974747508563,131072 /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1144 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_collections.mojom.CollectionsDataManager --lang=en-US --service-sandbox-type=collections --mojo-platform-channel-handle=4056 --field-trial-handle=1124,i,9157590743650421898,1809091974747508563,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1168 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=4024 --field-trial-handle=1124,i,9157590743650421898,1809091974747508563,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1620 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=audio.mojom.AudioService --lang=en-US --service-sandbox-type=audio --mojo-platform-channel-handle=2432 --field-trial-handle=1124,i,9157590743650421898,1809091974747508563,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1832 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=4716 --field-trial-handle=1124,i,9157590743650421898,1809091974747508563,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 2036 | "C:\Users\admin\Desktop\Melonity_Installer v3.6\FieroHack.exe" | C:\Users\admin\Desktop\Melonity_Installer v3.6\FieroHack.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2076 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=1200 --field-trial-handle=1124,i,9157590743650421898,1809091974747508563,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 2080 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=2156 --field-trial-handle=1124,i,9157590743650421898,1809091974747508563,131072 /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 2092 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1308 --field-trial-handle=1124,i,9157590743650421898,1809091974747508563,131072 /prefetch:3 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 2292 | C:\Users\admin\AppData\Roaming\Sirus.exe | C:\Users\admin\AppData\Roaming\Sirus.exe | FieroHack.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 3221225477 Modules
Lumma(PID) Process(2292) Sirus.exe C2 (9)injurypiggyoewirog.shop bargainnygroandjwk.shop leafcalfconflcitw.shop composepayyersellew.shop disappointcredisotw.shop computerexcudesp.shop doughtdrillyksow.shop publicitycharetew.shop facilitycoursedw.shop | |||||||||||||||
Total events
21 309
Read events
21 217
Write events
82
Delete events
10
Modification events
| (PID) Process: | (3380) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3380) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3380) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3380) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3380) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3380) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\EdgeUpdate\ClientState\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3380) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3380) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1302019708-1500728564-335382590-1000 |
Value: 3A6EC9492C7A2F00 | |||
| (PID) Process: | (3380) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\FirstNotDefault |
| Operation: | delete value | Name: | S-1-5-21-1302019708-1500728564-335382590-1000 |
Value: | |||
| (PID) Process: | (3380) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge |
| Operation: | write | Name: | UsageStatsInSample |
Value: 1 | |||
Executable files
25
Suspicious files
166
Text files
350
Unknown types
27
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3380 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF4e05a.TMP | — | |
MD5:— | SHA256:— | |||
| 3380 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3380 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF4e079.TMP | — | |
MD5:— | SHA256:— | |||
| 3380 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3380 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF4e089.TMP | — | |
MD5:— | SHA256:— | |||
| 3380 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF4e0a8.TMP | — | |
MD5:— | SHA256:— | |||
| 3380 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3380 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\shared_proto_db\metadata\LOG.old~RF4e134.TMP | text | |
MD5:5E14F5228D0155ACB62249CA5B6027C5 | SHA256:148FA281E7F8A00539FABE977F46F1E050C956204D830E6014BEEB8B4DD641F2 | |||
| 3380 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Platform Notifications\LOG.old | text | |
MD5:9D14DCB158E3908F7CBFB13D762D8F6A | SHA256:D339CBEF1BC3E4CDF15D0DCE9E2D77324E5B4F7EE4F2749472BFCEA91BB54ACE | |||
| 3380 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\shared_proto_db\metadata\LOG.old | text | |
MD5:F3FC0F220E8B793D2F3D821F0175B1D3 | SHA256:F37C4FC378816A8B7C657298C9EA7F9A0E6DF6853D876851178D20792E2180DB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
34
DNS requests
35
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2092 | msedge.exe | GET | 301 | 194.226.27.11:80 | http://upload.advgroup.ru/1xd3o7I3 | unknown | — | — | unknown |
3380 | msedge.exe | GET | 200 | 87.248.205.0:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?8c8e21be113d9e79 | unknown | — | — | unknown |
1372 | svchost.exe | GET | 304 | 87.248.205.0:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?33775f6043c93e33 | unknown | — | — | unknown |
3380 | msedge.exe | GET | 200 | 87.248.205.0:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?f3bd4f89a89743cc | unknown | — | — | unknown |
1372 | svchost.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
1372 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
1060 | svchost.exe | GET | 304 | 87.248.204.0:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?a9f83325acc8ca75 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1060 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2564 | svchost.exe | 239.255.255.250:3702 | — | — | — | whitelisted |
3380 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1372 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2092 | msedge.exe | 194.226.27.11:80 | upload.advgroup.ru | ADV Limited Liability Company | RU | unknown |
2092 | msedge.exe | 13.107.21.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
2092 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2092 | msedge.exe | 194.226.27.11:443 | upload.advgroup.ru | ADV Limited Liability Company | RU | unknown |
2092 | msedge.exe | 104.18.10.207:443 | maxcdn.bootstrapcdn.com | CLOUDFLARENET | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
upload.advgroup.ru |
| unknown |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
maxcdn.bootstrapcdn.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
netdna.bootstrapcdn.com |
| whitelisted |
www.bing.com |
| whitelisted |