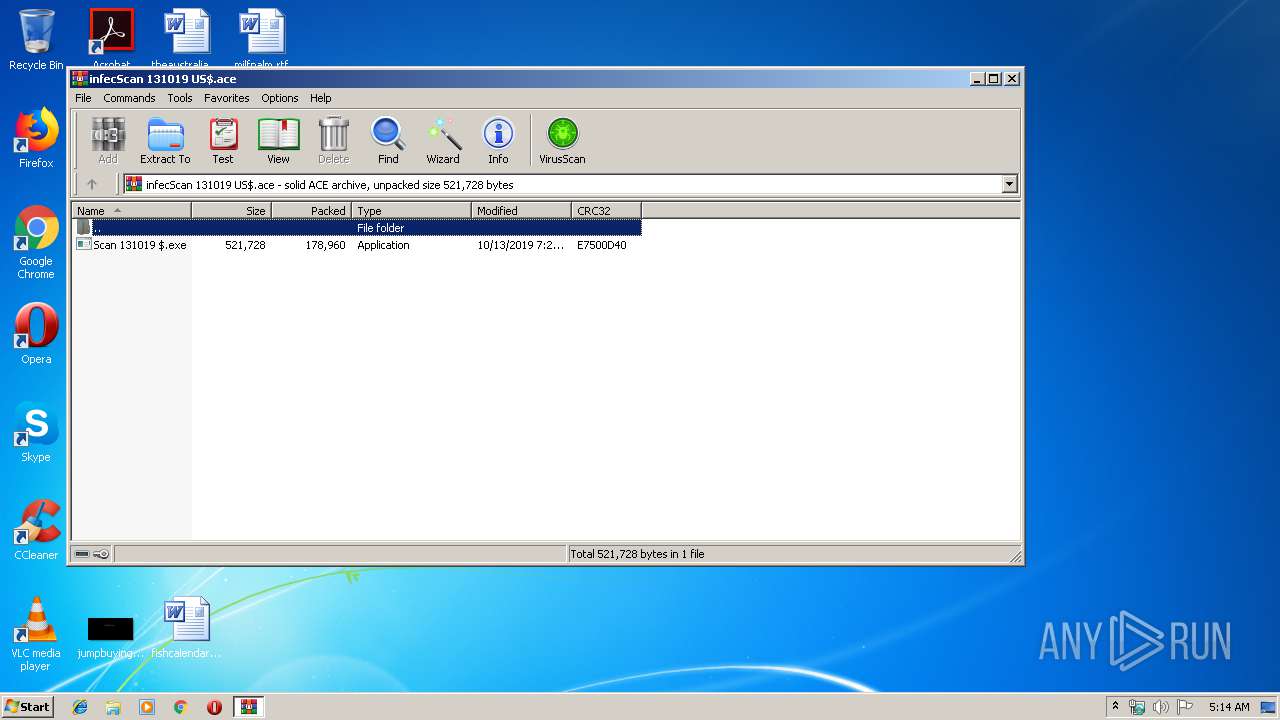
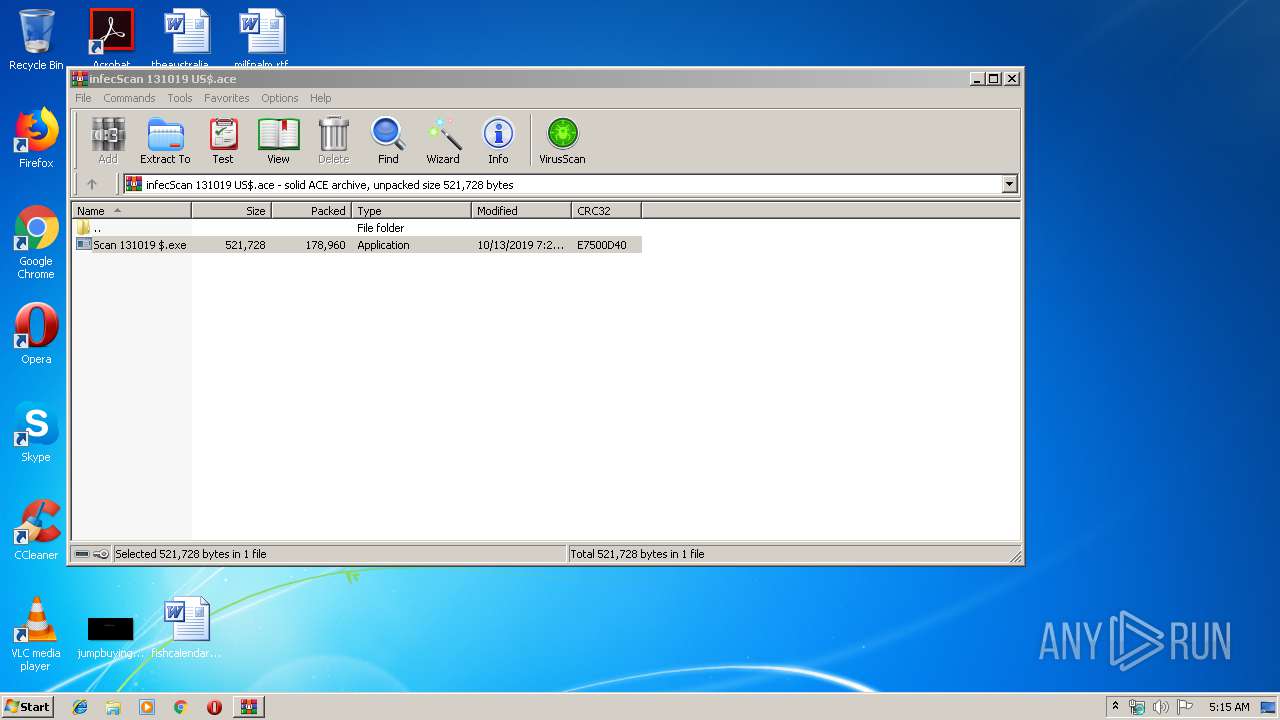
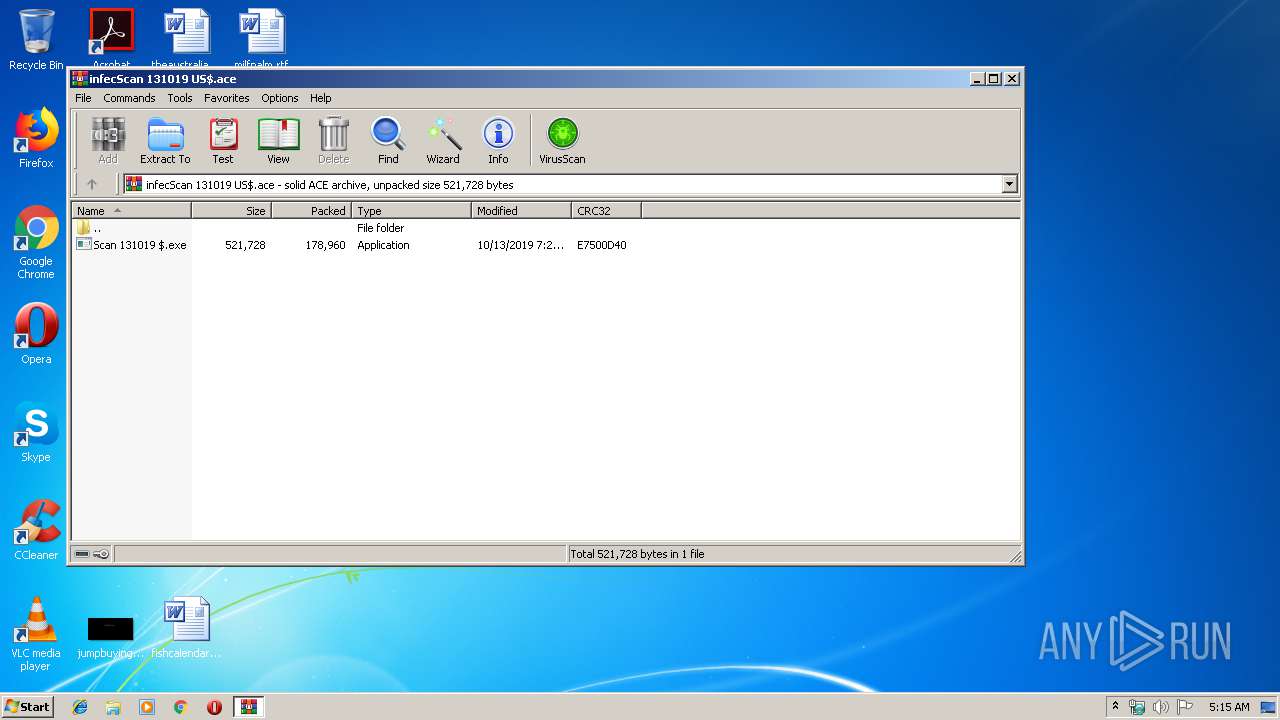
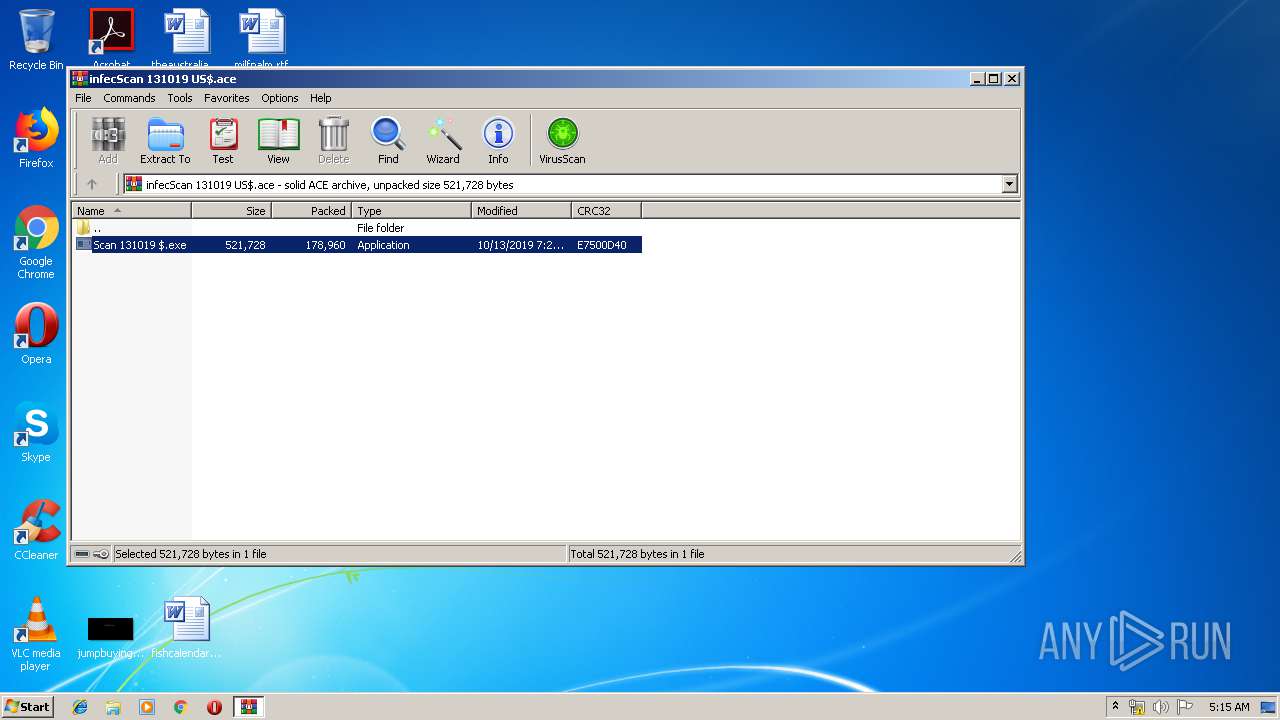
| File name: | infecScan 131019 US$.ace |
| Full analysis: | https://app.any.run/tasks/718f164f-270e-4b71-8f98-e5851061c9ba |
| Verdict: | Malicious activity |
| Threats: | FormBook is a data stealer that is being distributed as a MaaS. FormBook differs from a lot of competing malware by its extreme ease of use that allows even the unexperienced threat actors to use FormBook virus. |
| Analysis date: | October 14, 2019, 04:14:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/octet-stream |
| File info: | ACE archive data version 20, from Win/32, version 20 to extract, contains AV-String (unregistered), solid |
| MD5: | 5CD35CB057146CF2496F0F286C04650F |
| SHA1: | 7D0A293C9F151F714011E5B3F208A45F769DA01E |
| SHA256: | A1A2DF680A572C2F7553C56A0B9E70712604FA3ED26D80FB2B0054D558F27E4B |
| SSDEEP: | 3072:e3pK6JESIno8wVa+FFxZeF+jz6Hg4UK44y8rQMhNt9yb7le8Kxw:epuSRhLPmIjeHgATyY5hNtkHw8KG |
MALICIOUS
Application was dropped or rewritten from another process
- Scan 131019 $.exe (PID: 1768)
- Scan 131019 $.exe (PID: 2416)
FORMBOOK was detected
- explorer.exe (PID: 352)
- wscript.exe (PID: 2608)
- Firefox.exe (PID: 2484)
Connects to CnC server
- explorer.exe (PID: 352)
Changes the autorun value in the registry
- wscript.exe (PID: 2608)
Actions looks like stealing of personal data
- wscript.exe (PID: 2608)
Stealing of credential data
- wscript.exe (PID: 2608)
SUSPICIOUS
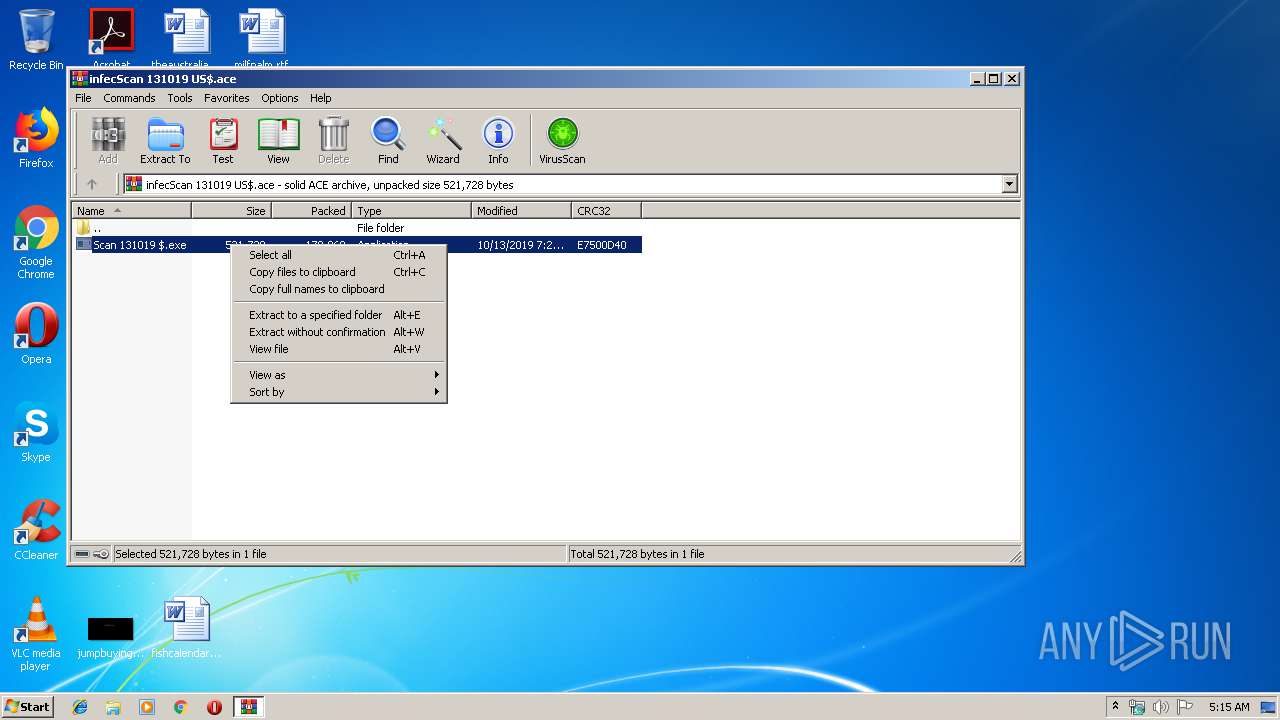
Executable content was dropped or overwritten
- WinRAR.exe (PID: 504)
Executes scripts
- explorer.exe (PID: 352)
Loads DLL from Mozilla Firefox
- wscript.exe (PID: 2608)
Starts CMD.EXE for commands execution
- wscript.exe (PID: 2608)
Creates files in the user directory
- wscript.exe (PID: 2608)
INFO
Reads the hosts file
- wscript.exe (PID: 2608)
Creates files in the user directory
- Firefox.exe (PID: 2484)
Manual execution by user
- wscript.exe (PID: 2608)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .ace | | | ACE compressed archive (100) |
|---|
Total processes
40
Monitored processes
8
Malicious processes
3
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 352 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
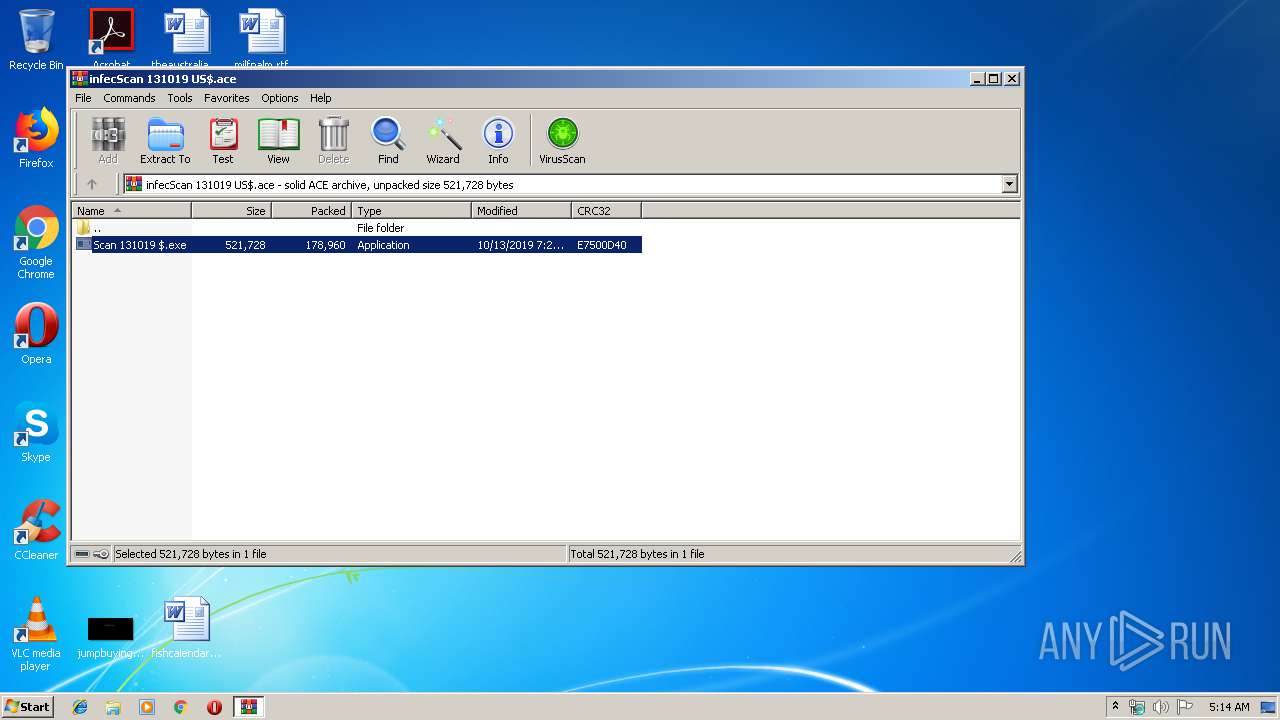
| 504 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\infecScan 131019 US$.ace" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 1768 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa504.48928\Scan 131019 $.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa504.48928\Scan 131019 $.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Acrobat Exit code: 0 Version: 10.0.0.396 Modules
| |||||||||||||||
| 2416 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa504.3377\Scan 131019 $.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa504.3377\Scan 131019 $.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Acrobat Exit code: 0 Version: 10.0.0.396 Modules
| |||||||||||||||
| 2484 | "C:\Program Files\Mozilla Firefox\Firefox.exe" | C:\Program Files\Mozilla Firefox\Firefox.exe | wscript.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 2608 | "C:\Windows\System32\wscript.exe" | C:\Windows\System32\wscript.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 3124 | /c del "C:\Users\admin\AppData\Local\Temp\Rar$EXa504.48928\Scan 131019 $.exe" | C:\Windows\System32\cmd.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3172 | "C:\Windows\System32\NAPSTAT.EXE" | C:\Windows\System32\NAPSTAT.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Network Access Protection Client UI Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
497
Read events
444
Write events
53
Delete events
0
Modification events
| (PID) Process: | (504) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (504) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (504) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (504) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\infecScan 131019 US$.ace | |||
| (PID) Process: | (504) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (504) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (504) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (504) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (504) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\ACE Compression Software\ActiveAce\2.0 |
| Operation: | write | Name: | Count |
Value: 0 | |||
| (PID) Process: | (504) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\ACE Compression Software\ActiveAce\2.0 |
| Operation: | write | Name: | Name |
Value: 542D4B42647265644B76737A7E794B566767537663764B5B7874767B4B43727A674B7E79717274447476793726242627262E37424433397674721717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171700 | |||
Executable files
2
Suspicious files
73
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2608 | wscript.exe | C:\Users\admin\AppData\Roaming\J3RN409E\J3Rlogrc.ini | binary | |
MD5:— | SHA256:— | |||
| 504 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa504.48928\Scan 131019 $.exe | executable | |
MD5:— | SHA256:— | |||
| 2608 | wscript.exe | C:\Users\admin\AppData\Roaming\J3RN409E\J3Rlogri.ini | binary | |
MD5:D63A82E5D81E02E399090AF26DB0B9CB | SHA256:EAECE2EBA6310253249603033C744DD5914089B0BB26BDE6685EC9813611BAAE | |||
| 2484 | Firefox.exe | C:\Users\admin\AppData\Roaming\J3RN409E\J3Rlogrf.ini | binary | |
MD5:— | SHA256:— | |||
| 2608 | wscript.exe | C:\Users\admin\AppData\Roaming\J3RN409E\J3Rlogim.jpeg | image | |
MD5:— | SHA256:— | |||
| 504 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa504.3377\Scan 131019 $.exe | executable | |
MD5:— | SHA256:— | |||
| 2608 | wscript.exe | C:\Users\admin\AppData\Roaming\J3RN409E\J3Rlogrv.ini | binary | |
MD5:BA3B6BC807D4F76794C4B81B09BB9BA5 | SHA256:6EEBF968962745B2E9DE2CA969AF7C424916D4E3FE3CC0BB9B3D414ABFCE9507 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
352 | explorer.exe | GET | 301 | 136.243.64.86:80 | http://www.healthlife4u.com/us/?yVftlxDh=sMcqe9GXsoYPR0ZU9BLHJHv2andjRWJR2DPff7W2Hp8eJrzG92J3guDs4mr0pRQsCiuBqA==&2d3=o8TpZlH | DE | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
352 | explorer.exe | 136.243.64.86:80 | www.healthlife4u.com | Hetzner Online GmbH | DE | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.healthlife4u.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
352 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
1 ETPRO signatures available at the full report