| File name: | Setup.exe |
| Full analysis: | https://app.any.run/tasks/eca8dc67-ef09-4bff-99b2-621da35db2fb |
| Verdict: | Malicious activity |
| Threats: | HijackLoader is a modular malware acting as a vehicle for distributing different types of malicious software on compromised systems. It gained prominence during the summer of 2023 and has since been used in multiple attacks against organizations from various sectors, including hospitality businesses. |
| Analysis date: | February 16, 2025, 13:22:43 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 10 sections |
| MD5: | E0AB36D709228689B82949B4FE7677EB |
| SHA1: | 216100A41663D9116EC31984813084CFB10CC69E |
| SHA256: | A1806CF726130491BB2CA7D83E2A4A7982493AC5FB3392E7E2624F435669EB21 |
| SSDEEP: | 98304:HtQYN1vdU7Ga9bkDNjFmjUV6DN0p2Fg+i9g84lcaFO22IX0sm+NUKY4k3GKur+9x:zhoS+siklqPfgBCqnWELKzz |
MALICIOUS
Actions looks like stealing of personal data
- Setup.exe (PID: 6804)
Steals credentials from Web Browsers
- Setup.exe (PID: 6804)
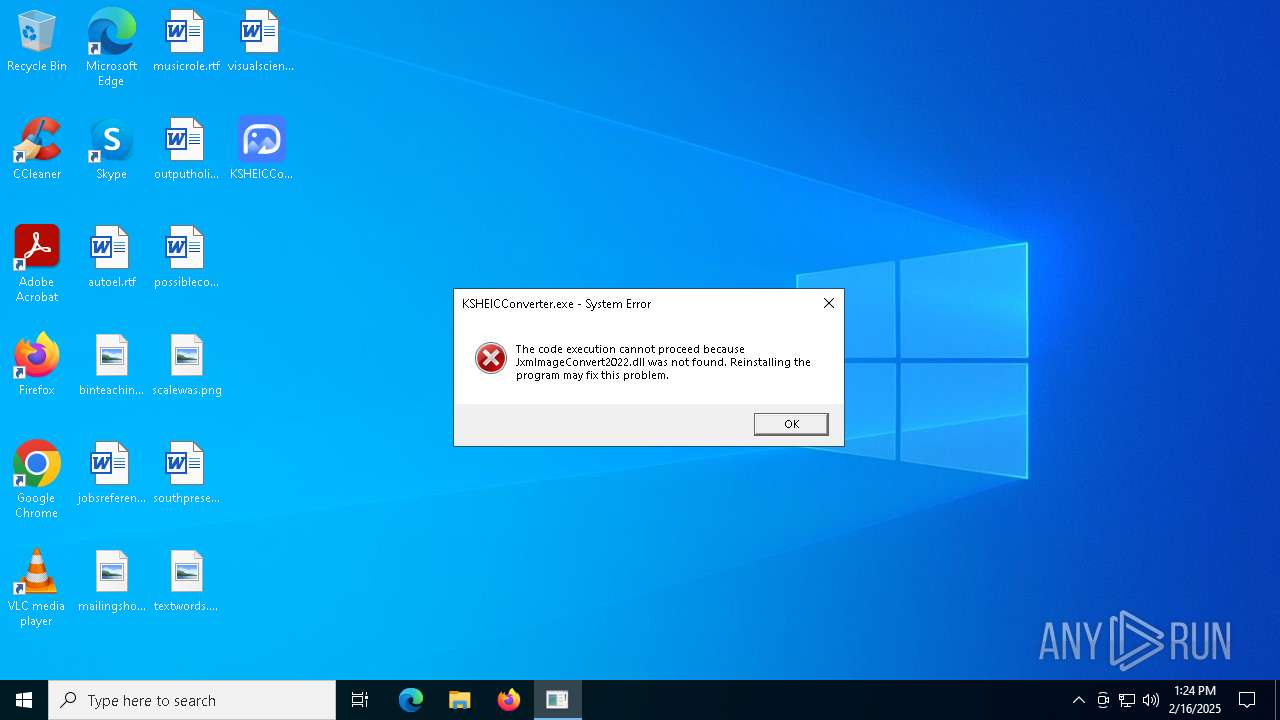
HIJACKLOADER has been detected (YARA)
- KSHEICConverter.exe (PID: 5740)
- KSHEICConverter.exe (PID: 644)
Known privilege escalation attack
- dllhost.exe (PID: 3792)
SUSPICIOUS
Reads security settings of Internet Explorer
- Setup.exe (PID: 6804)
Checks Windows Trust Settings
- Setup.exe (PID: 6804)
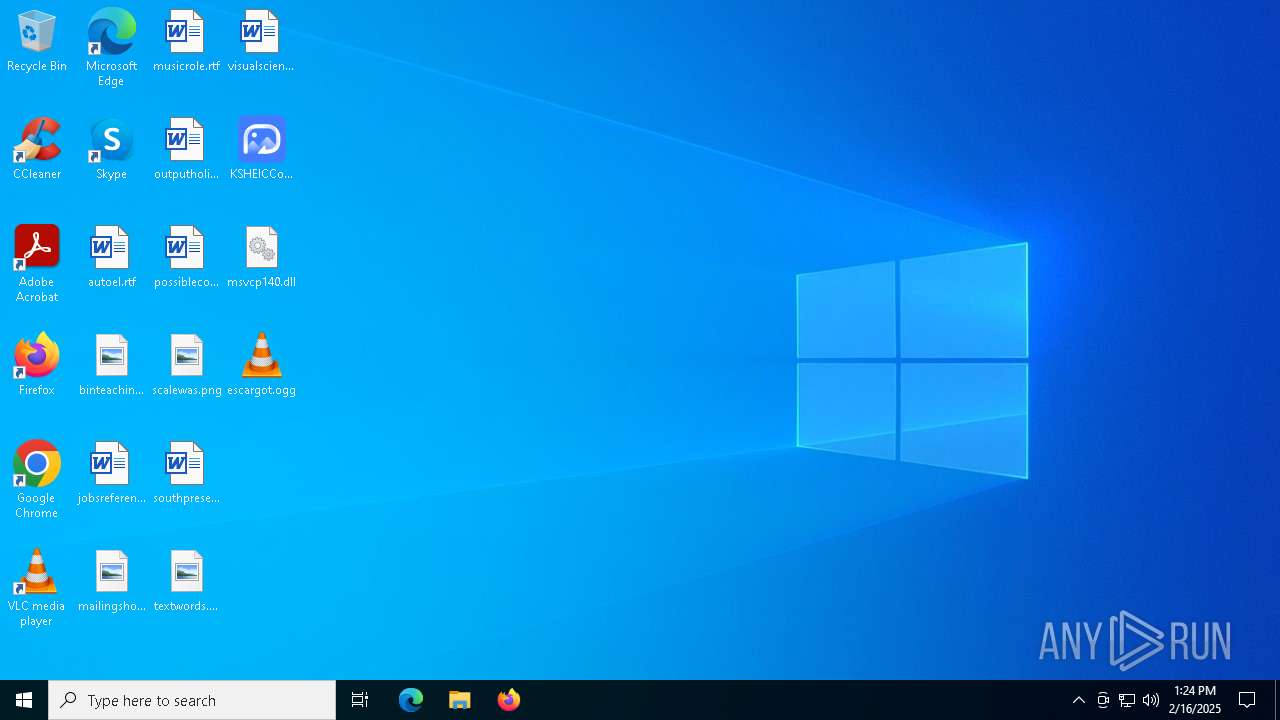
The process drops C-runtime libraries
- Setup.exe (PID: 6804)
- KSHEICConverter.exe (PID: 5740)
- Dashboard.exe (PID: 1488)
Process drops legitimate windows executable
- Setup.exe (PID: 6804)
- KSHEICConverter.exe (PID: 5740)
- Dashboard.exe (PID: 1488)
Executable content was dropped or overwritten
- Setup.exe (PID: 6804)
- KSHEICConverter.exe (PID: 5740)
- Dashboard.exe (PID: 1488)
Starts itself from another location
- KSHEICConverter.exe (PID: 5740)
- Dashboard.exe (PID: 1488)
There is functionality for taking screenshot (YARA)
- KSHEICConverter.exe (PID: 644)
Starts CMD.EXE for commands execution
- KSHEICConverter.exe (PID: 644)
- Dashboard.exe (PID: 7068)
- KSHEICConverter.exe (PID: 5568)
- Dashboard.exe (PID: 536)
INFO
Checks supported languages
- Setup.exe (PID: 6804)
- KSHEICConverter.exe (PID: 5740)
- Dashboard.exe (PID: 1488)
- KSHEICConverter.exe (PID: 644)
- vlc.exe (PID: 5040)
- vlc.exe (PID: 5432)
- Dashboard.exe (PID: 7068)
- KSHEICConverter.exe (PID: 5568)
- Dashboard.exe (PID: 536)
Creates files or folders in the user directory
- Setup.exe (PID: 6804)
- Dashboard.exe (PID: 1488)
Application launched itself
- chrome.exe (PID: 6952)
- msedge.exe (PID: 6388)
Reads the computer name
- Setup.exe (PID: 6804)
- KSHEICConverter.exe (PID: 5740)
- Dashboard.exe (PID: 7068)
- vlc.exe (PID: 5432)
- KSHEICConverter.exe (PID: 644)
- Dashboard.exe (PID: 1488)
- KSHEICConverter.exe (PID: 5568)
- Dashboard.exe (PID: 536)
Reads the software policy settings
- Setup.exe (PID: 6804)
Reads the machine GUID from the registry
- Setup.exe (PID: 6804)
The sample compiled with chinese language support
- Setup.exe (PID: 6804)
- KSHEICConverter.exe (PID: 5740)
Process checks computer location settings
- Setup.exe (PID: 6804)
The sample compiled with english language support
- Setup.exe (PID: 6804)
- KSHEICConverter.exe (PID: 5740)
- Dashboard.exe (PID: 1488)
Creates files in the program directory
- KSHEICConverter.exe (PID: 5740)
Manual execution by a user
- KSHEICConverter.exe (PID: 4724)
- vlc.exe (PID: 5432)
- vlc.exe (PID: 5040)
Create files in a temporary directory
- KSHEICConverter.exe (PID: 644)
- Dashboard.exe (PID: 7068)
- KSHEICConverter.exe (PID: 5568)
Reads security settings of Internet Explorer
- dllhost.exe (PID: 3792)
Checks proxy server information
- Setup.exe (PID: 6804)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:02:15 10:19:19+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.4 |
| CodeSize: | 12904448 |
| InitializedDataSize: | 1635328 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2a05b53 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 7.1.0.44 |
| ProductVersionNumber: | 7.1.0.44 |
| FileFlagsMask: | 0x0017 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| CompanyName: | Adobe Inc |
| FileDescription: | Adobe IPC Broker |
| FileVersion: | 7.1.0.44 |
| LegalCopyright: | Copyright 2021, Adobe Inc. All rights reserved. |
| OriginalFileName: | AdobeIPCBroker.exe |
| ProductName: | Adobe IPC Broker |
| ProductVersion: | 7.1.0.44 |
Total processes
159
Monitored processes
38
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 8 | C:\WINDOWS\SysWOW64\cmd.exe | C:\Windows\SysWOW64\cmd.exe | — | Dashboard.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 536 | "C:\Users\admin\AppData\Roaming\GUPM\Dashboard.exe" | C:\Users\admin\AppData\Roaming\GUPM\Dashboard.exe | — | dllhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Live installer client executable Version: 12.0.1202.0516 Modules
| |||||||||||||||
| 624 | C:\WINDOWS\SysWOW64\cmd.exe | C:\Windows\SysWOW64\cmd.exe | — | KSHEICConverter.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 644 | C:\ProgramData\DPChipv\KSHEICConverter.exe | C:\ProgramData\DPChipv\KSHEICConverter.exe | KSHEICConverter.exe | ||||||||||||
User: admin Company: Kingshiper Software Co., Ltd. Integrity Level: MEDIUM Description: Kingshiper HEIC to JPG Converter Exit code: 1 Version: 3.6.6.0 Modules
| |||||||||||||||
| 936 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4664 --field-trial-handle=1940,i,14685338190285576200,2262586659669459010,262144 --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1488 | "C:\Users\admin\K0Rvq.exe\Dashboard.exe" | C:\Users\admin\K0Rvq.exe\Dashboard.exe | Setup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Live installer client executable Exit code: 0 Version: 12.0.1202.0516 Modules
| |||||||||||||||
| 1744 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --remote-debugging-port=43861 --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --mojo-platform-channel-handle=4516 --field-trial-handle=1940,i,14685338190285576200,2262586659669459010,262144 --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2612 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --remote-debugging-port=4949 --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=3444 --field-trial-handle=2424,i,17987805436896280855,8971906500486980740,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 3172 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
8 022
Read events
8 004
Write events
18
Delete events
0
Modification events
| (PID) Process: | (6804) Setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6804) Setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6804) Setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (6952) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6952) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6952) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6952) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6952) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (6388) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6388) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
Executable files
52
Suspicious files
169
Text files
100
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF13a76e.TMP | — | |
MD5:— | SHA256:— | |||
| 6952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF13a76e.TMP | — | |
MD5:— | SHA256:— | |||
| 6952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF13a76e.TMP | — | |
MD5:— | SHA256:— | |||
| 6952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF13a76e.TMP | — | |
MD5:— | SHA256:— | |||
| 6952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF13a78e.TMP | — | |
MD5:— | SHA256:— | |||
| 6952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
74
DNS requests
69
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6804 | Setup.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6476 | backgroundTaskHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
6804 | Setup.exe | GET | 200 | 216.58.206.35:80 | http://c.pki.goog/r/gsr1.crl | unknown | — | — | whitelisted |
6804 | Setup.exe | GET | 200 | 216.58.206.35:80 | http://c.pki.goog/r/r4.crl | unknown | — | — | whitelisted |
5536 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5536 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6804 | Setup.exe | GET | 200 | 23.209.209.135:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5064 | SearchApp.exe | 2.19.122.9:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
1544 | RUXIMICS.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1176 | svchost.exe | 20.190.159.128:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1176 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
1076 | svchost.exe | 2.18.97.227:443 | go.microsoft.com | Akamai International B.V. | FR | whitelisted |
6804 | Setup.exe | 104.102.49.254:443 | steamcommunity.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
steamcommunity.com |
| whitelisted |
effectsstardust.shop |
| unknown |
c.pki.goog |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Misc activity | ET FILE_SHARING Anonymous File Sharing Domain in DNS Lookup (qu .ax) |
6804 | Setup.exe | Misc activity | ET FILE_SHARING Observed Anonymous File Sharing Service Domain (qu .ax) in TLS SNI |
Process | Message |
|---|---|
vlc.exe | main libvlc debug: Copyright © 1996-2020 the VideoLAN team
|
vlc.exe | main libvlc debug: revision 3.0.11-0-gdc0c5ced72
|
vlc.exe | main libvlc debug: VLC media player - 3.0.11 Vetinari
|
vlc.exe | main libvlc debug: configured with ../extras/package/win32/../../../configure '--enable-update-check' '--enable-lua' '--enable-faad' '--enable-flac' '--enable-theora' '--enable-avcodec' '--enable-merge-ffmpeg' '--enable-dca' '--enable-mpc' '--enable-libass' '--enable-schroedinger' '--enable-realrtsp' '--enable-live555' '--enable-dvdread' '--enable-shout' '--enable-goom' '--enable-caca' '--enable-qt' '--enable-skins2' '--enable-sse' '--enable-mmx' '--enable-libcddb' '--enable-zvbi' '--disable-telx' '--enable-nls' '--host=x86_64-w64-mingw32' '--with-breakpad=https://win.crashes.videolan.org' 'host_alias=x86_64-w64-mingw32' 'PKG_CONFIG_LIBDIR=/home/jenkins/workspace/vlc-release/windows/vlc-release-win32-x64/contrib/x86_64-w64-mingw32/lib/pkgconfig'
|
vlc.exe | main libvlc debug: min period: 1 ms, max period: 1000000 ms
|
vlc.exe | main libvlc debug: using multimedia timers as clock source
|
vlc.exe | main libvlc debug: searching plug-in modules
|
vlc.exe | main libvlc debug: loading plugins cache file C:\Program Files\VideoLAN\VLC\plugins\plugins.dat
|
vlc.exe | main libvlc debug: recursively browsing `C:\Program Files\VideoLAN\VLC\plugins'
|
vlc.exe | main libvlc debug: plug-ins loaded: 494 modules
|