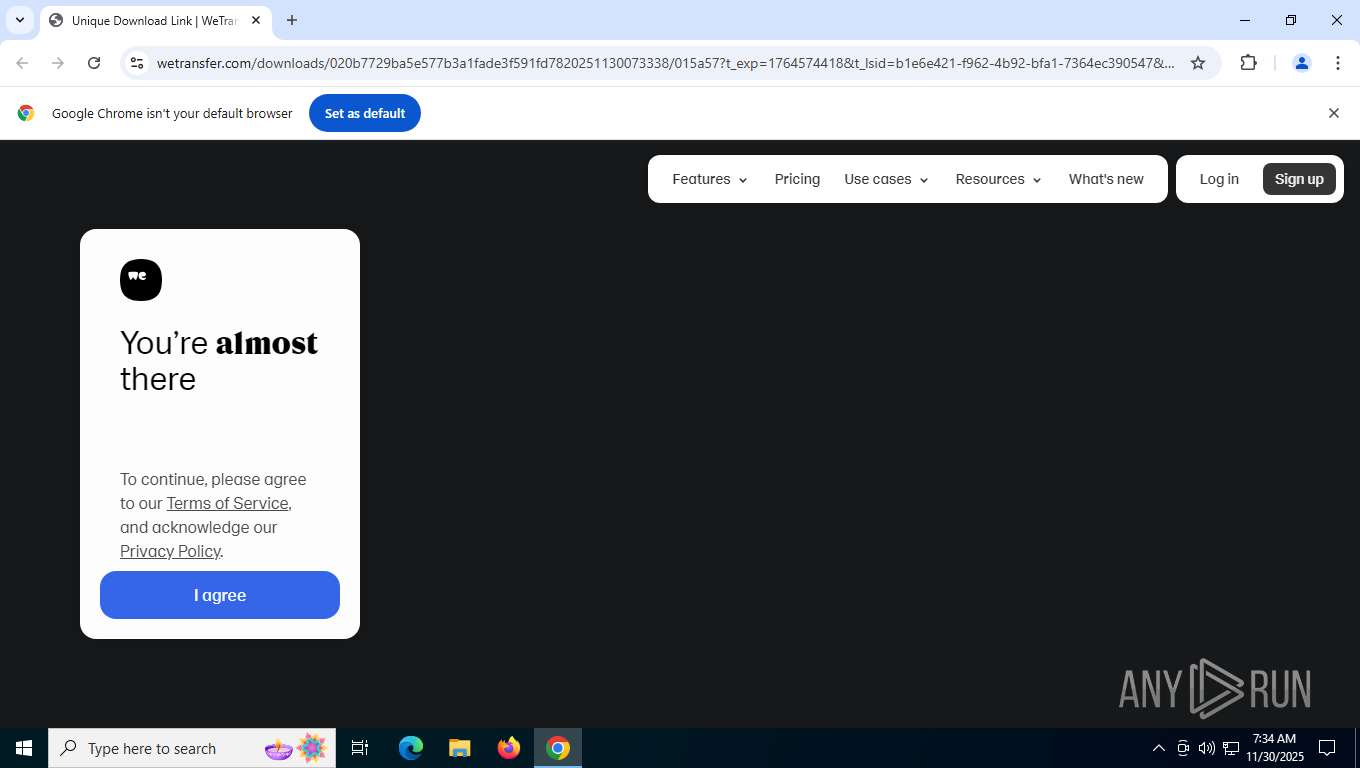
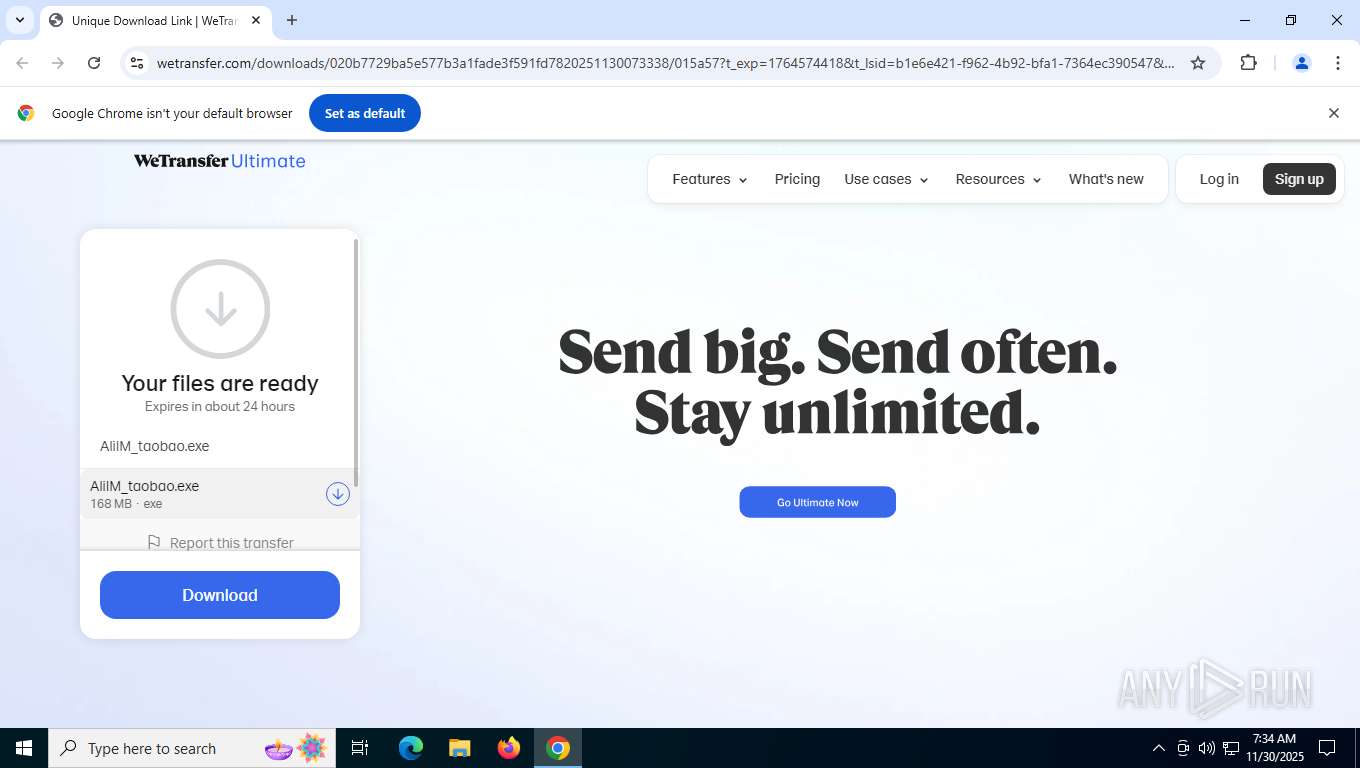
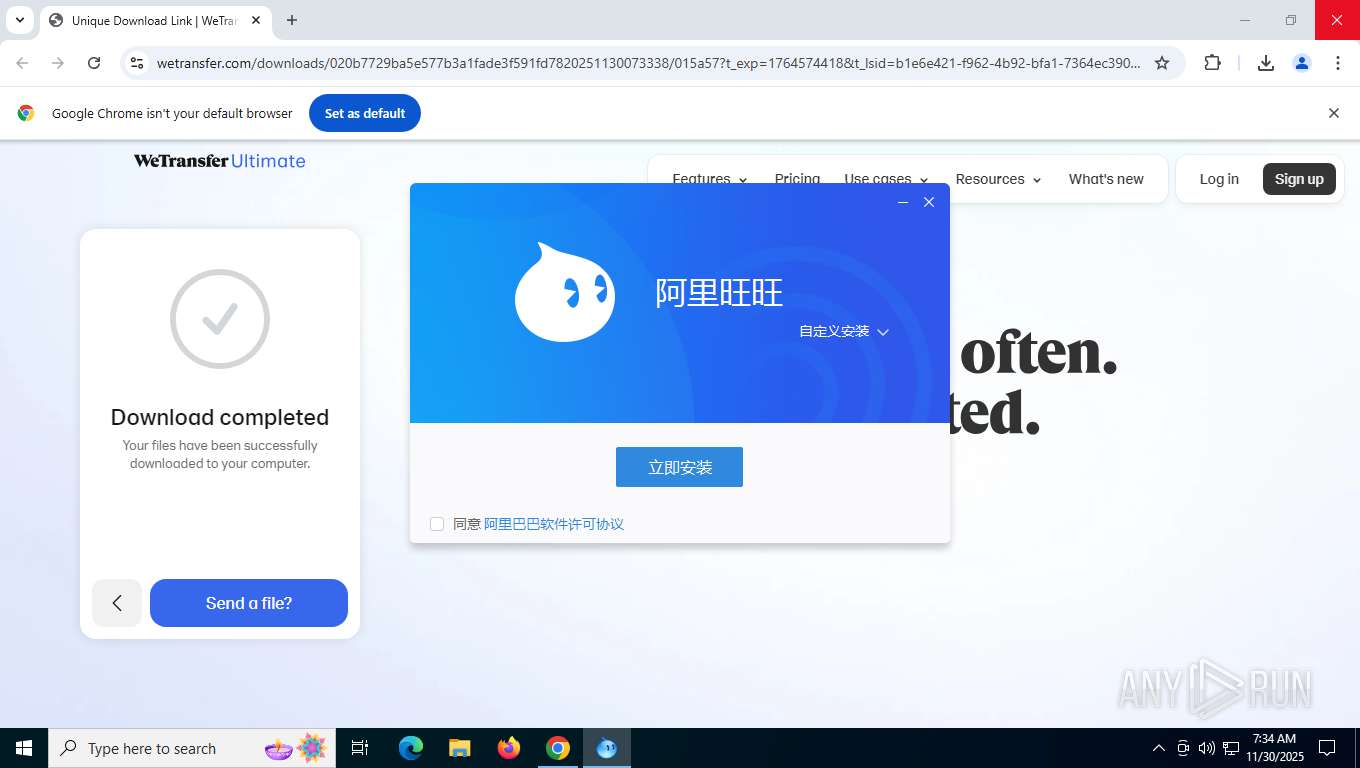
| URL: | https://we.tl/t-0Xi9tzvNoT |
| Full analysis: | https://app.any.run/tasks/52677161-920d-4bbd-8bb4-63800b931f95 |
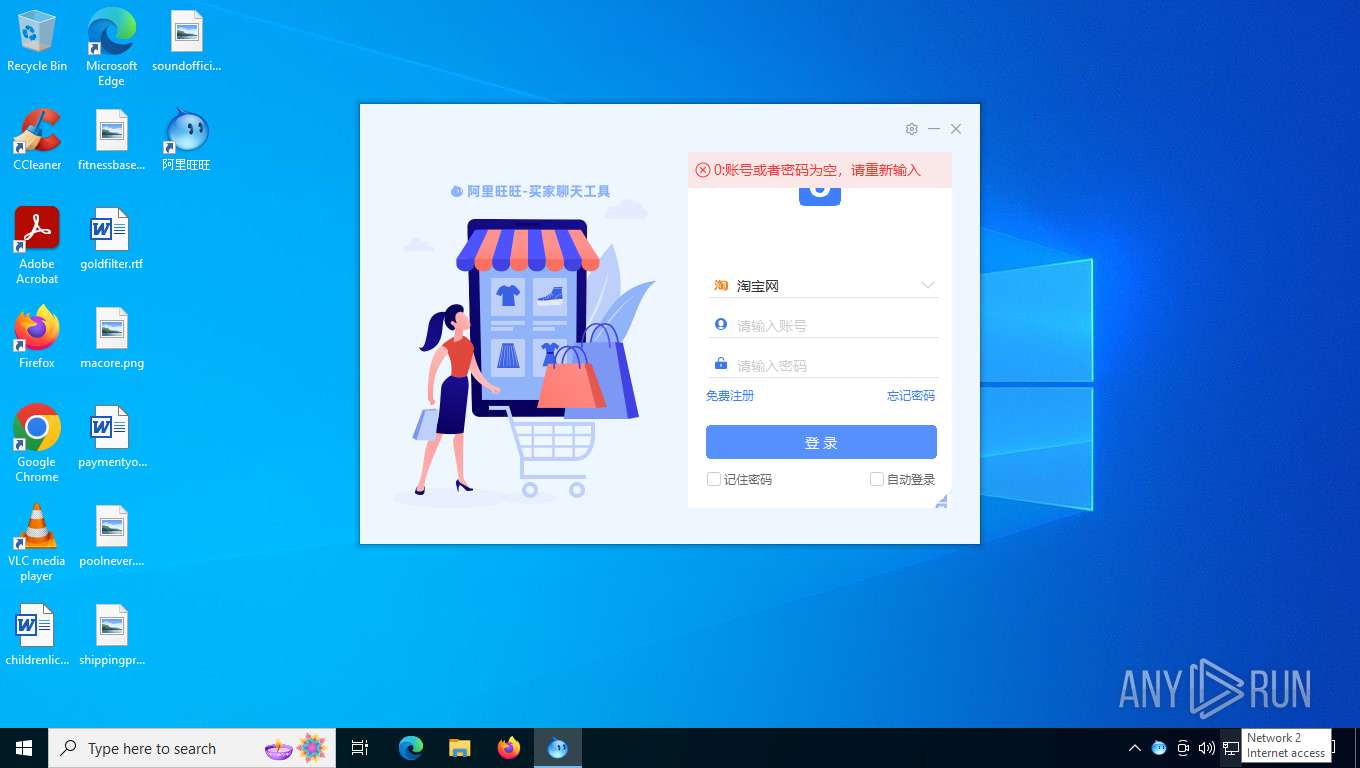
| Verdict: | Malicious activity |
| Threats: | Ransomware is a type of malicious software that locks users out of their system or data using different methods to force them to pay a ransom. Most often, such programs encrypt files on an infected machine and demand a fee to be paid in exchange for the decryption key. Additionally, such programs can be used to steal sensitive information from the compromised computer and even conduct DDoS attacks against affected organizations to pressure them into paying. |
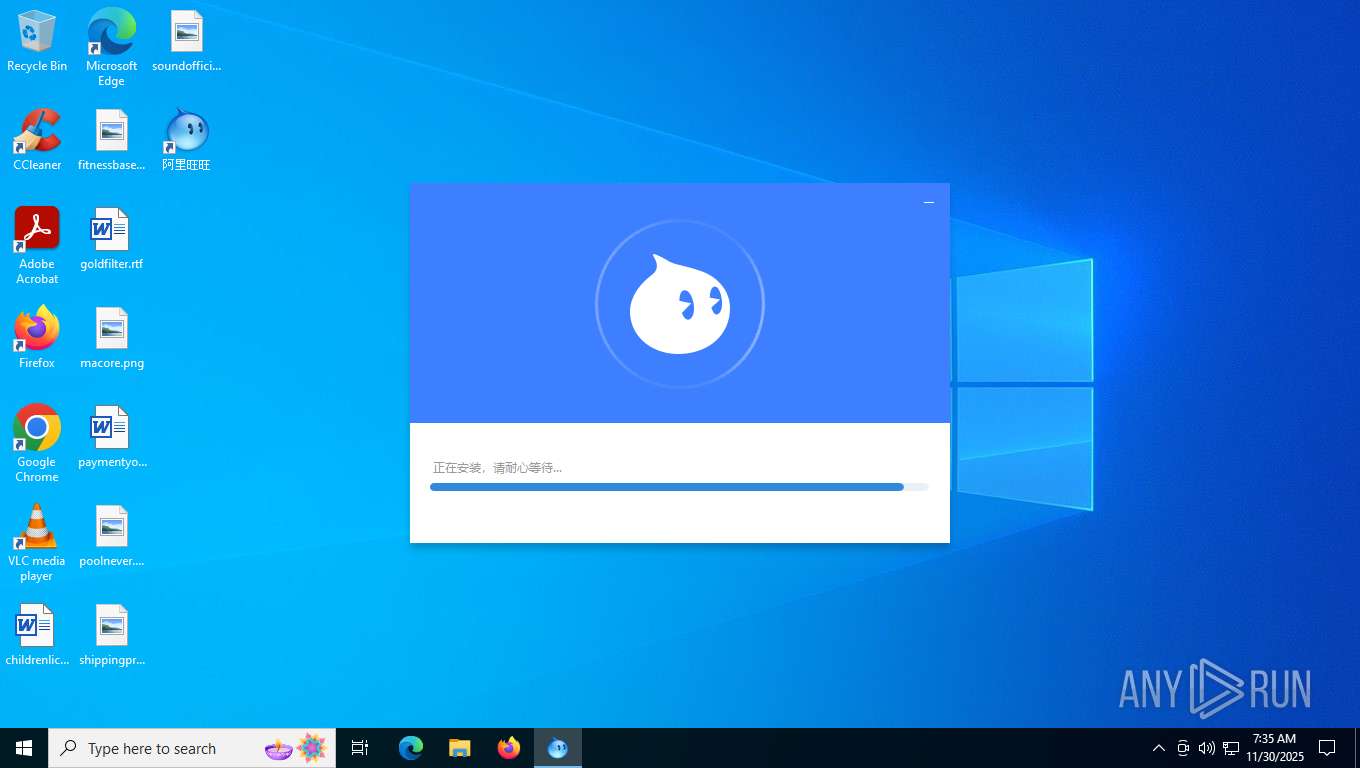
| Analysis date: | November 30, 2025, 07:34:00 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | FA9A47C6EA9DC193813AF80E41EF131D |
| SHA1: | 7BC0FD634875928C52F3D75DD79FD2341F572560 |
| SHA256: | A16B66B938AD6C3F9F6ABAF657421BEA223290308077A1DFAD038C57ACDA118E |
| SSDEEP: | 3:N8RlJK2fun:2tun |
MALICIOUS
XORed URL has been found (YARA)
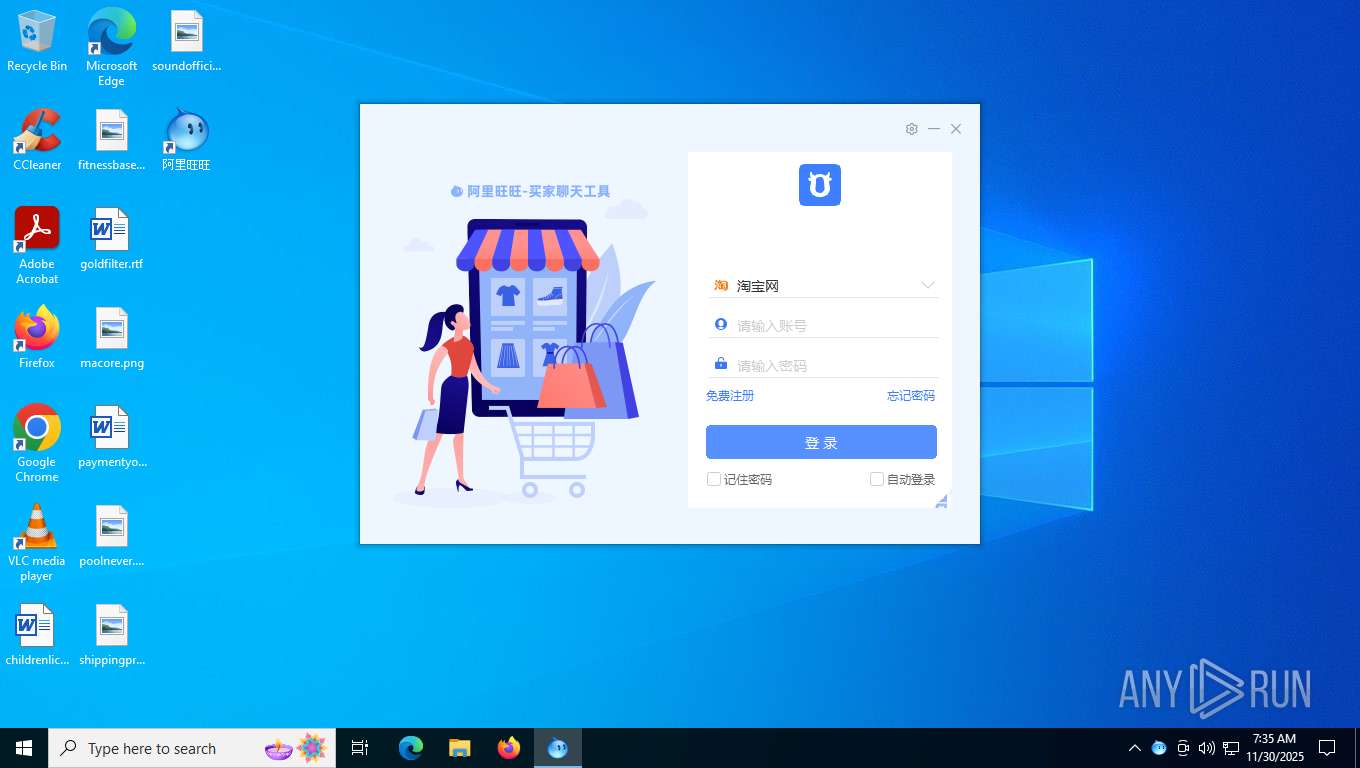
- AliIM_taobao.exe (PID: 6428)
- AlibabaProtect.exe (PID: 4604)
- AliIM.exe (PID: 7644)
Executing a file with an untrusted certificate
- pc-sdk-setup.exe (PID: 2636)
VOBFUS mutex has been found
- pc-sdk-setup.exe (PID: 2636)
Changes settings of System certificates
- AlibabaProtect.exe (PID: 4604)
WANNACRY mutex has been found
- AlibabaProtect.exe (PID: 4604)
Reads a specific registry key of the VM
- AlibabaProtect.exe (PID: 4604)
- AliIM.exe (PID: 7644)
SUSPICIOUS
There is functionality for taking screenshot (YARA)
- AliIM_taobao.exe (PID: 6428)
- AlibabaProtect.exe (PID: 4604)
- AliRender.exe (PID: 6904)
- AliIM.exe (PID: 7644)
- AliRender.exe (PID: 6444)
Drops 7-zip archiver for unpacking
- AliIM_taobao.exe (PID: 6428)
Executable content was dropped or overwritten
- AliIM_taobao.exe (PID: 6428)
- AlibabaProtect.exe (PID: 4604)
- pc-sdk-setup.exe (PID: 2636)
Process drops legitimate windows executable
- AliIM_taobao.exe (PID: 6428)
- pc-sdk-setup.exe (PID: 2636)
Drops a system driver (possible attempt to evade defenses)
- pc-sdk-setup.exe (PID: 2636)
- AlibabaProtect.exe (PID: 4604)
The process drops C-runtime libraries
- AliIM_taobao.exe (PID: 6428)
Malware-specific behavior (creating "System.dll" in Temp)
- pc-sdk-setup.exe (PID: 2636)
Executes as Windows Service
- AlibabaProtect.exe (PID: 4604)
Non windows owned service launched
- AlibabaProtect.exe (PID: 4604)
Adds/modifies Windows certificates
- AlibabaProtect.exe (PID: 4604)
Write to the desktop.ini file (may be used to cloak folders)
- AlibabaProtect.exe (PID: 4604)
The process checks if it is being run in the virtual environment
- AlibabaProtect.exe (PID: 4604)
- AliIM.exe (PID: 7644)
Reads the BIOS version
- AlibabaProtect.exe (PID: 4604)
- AliIM.exe (PID: 7644)
Read disk information to detect sandboxing environments
- AlibabaProtect.exe (PID: 4604)
- AliIM.exe (PID: 7644)
Creates files in the driver directory
- AlibabaProtect.exe (PID: 4604)
Starts CMD.EXE for commands execution
- AlibabaProtect.exe (PID: 4604)
Creates or modifies Windows services
- AlibabaProtect.exe (PID: 4604)
Uses SYSTEMINFO.EXE to read the environment
- cmd.exe (PID: 7772)
Creates/Modifies COM task schedule object
- AliIM.exe (PID: 7644)
Reads security settings of Internet Explorer
- AliIM.exe (PID: 7644)
There is functionality for communication over UDP network (YARA)
- AlibabaProtect.exe (PID: 4604)
There is functionality for VM detection VirtualBox (YARA)
- AlibabaProtect.exe (PID: 4604)
- AliIM.exe (PID: 7644)
INFO
Application launched itself
- chrome.exe (PID: 6372)
Checks supported languages
- AliIM_taobao.exe (PID: 6428)
- AlibabaProtectCon.exe (PID: 4952)
- pc-sdk-setup.exe (PID: 2636)
- AlibabaProtect.exe (PID: 8176)
- AlibabaProtect.exe (PID: 4604)
- arphaCrashReport.exe (PID: 7748)
- AliIM.exe (PID: 7684)
- AlibabaProtect.exe (PID: 892)
- qnacctool.exe (PID: 7688)
- AliIM.exe (PID: 7644)
- AliRender.exe (PID: 7984)
- arphaCrashReport.exe (PID: 7196)
- AliRender.exe (PID: 6444)
- AliRender.exe (PID: 6904)
Reads the computer name
- AliIM_taobao.exe (PID: 6428)
- pc-sdk-setup.exe (PID: 2636)
- AlibabaProtectCon.exe (PID: 4952)
- AliIM.exe (PID: 7684)
- AlibabaProtect.exe (PID: 4604)
- AlibabaProtect.exe (PID: 892)
- AlibabaProtect.exe (PID: 8176)
- AliIM.exe (PID: 7644)
- AliRender.exe (PID: 6444)
- arphaCrashReport.exe (PID: 7196)
- AliRender.exe (PID: 6904)
The sample compiled with english language support
- AliIM_taobao.exe (PID: 6428)
- pc-sdk-setup.exe (PID: 2636)
The sample compiled with chinese language support
- AliIM_taobao.exe (PID: 6428)
- pc-sdk-setup.exe (PID: 2636)
- AlibabaProtect.exe (PID: 4604)
Creates files in the program directory
- AliIM_taobao.exe (PID: 6428)
- pc-sdk-setup.exe (PID: 2636)
- AlibabaProtect.exe (PID: 8176)
- AlibabaProtect.exe (PID: 4604)
- AlibabaProtectCon.exe (PID: 4952)
- cmd.exe (PID: 7772)
- AliIM.exe (PID: 7644)
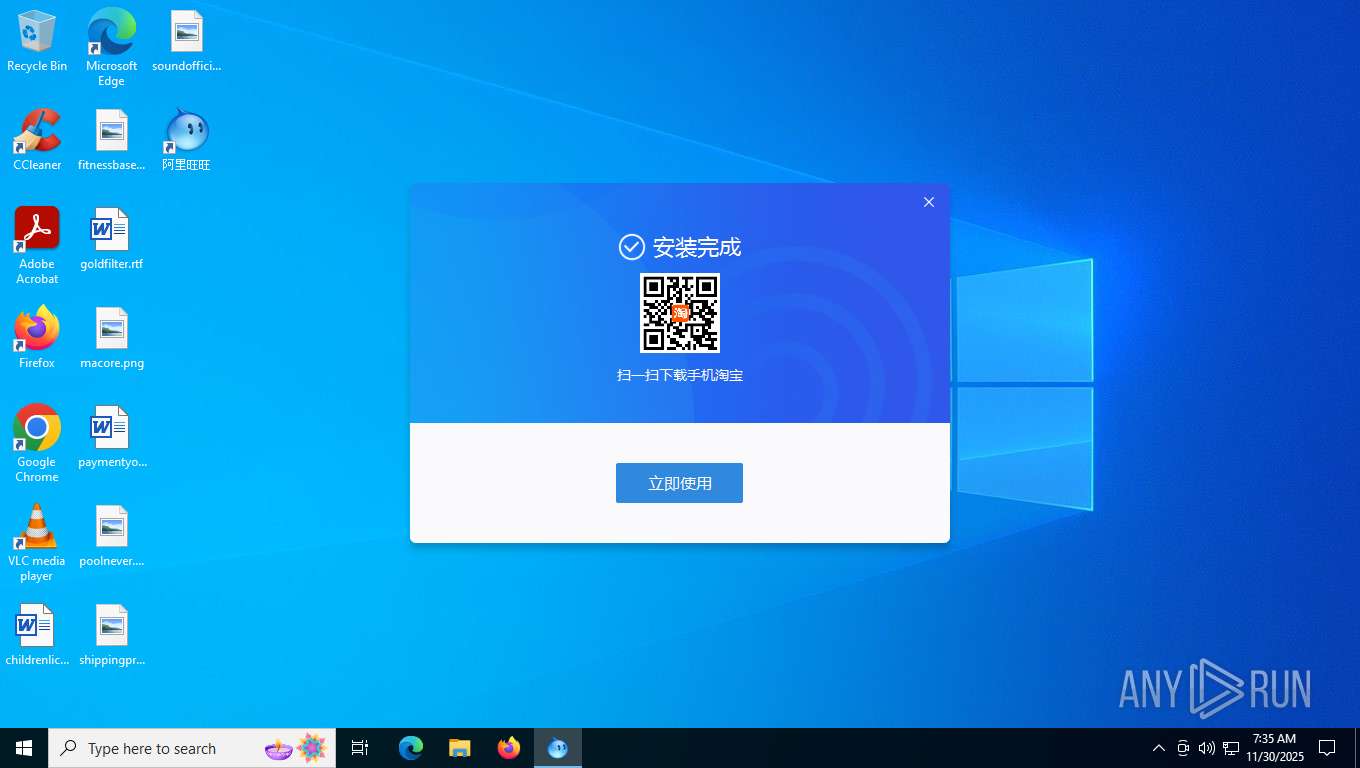
Creates a software uninstall entry
- AliIM_taobao.exe (PID: 6428)
Create files in a temporary directory
- pc-sdk-setup.exe (PID: 2636)
Reads the machine GUID from the registry
- AlibabaProtect.exe (PID: 4604)
- arphaCrashReport.exe (PID: 7196)
- AliIM.exe (PID: 7644)
- AliRender.exe (PID: 6444)
- AliRender.exe (PID: 6904)
Creates files or folders in the user directory
- AliIM.exe (PID: 7644)
- AliRender.exe (PID: 7984)
- arphaCrashReport.exe (PID: 7196)
Reads CPU info
- AliIM.exe (PID: 7644)
Checks proxy server information
- AliIM.exe (PID: 7644)
- slui.exe (PID: 3460)
Reads Microsoft Office registry keys
- AliIM.exe (PID: 7644)
UPX packer has been detected
- AliIM.exe (PID: 7644)
- AlibabaProtect.exe (PID: 4604)
VMProtect protector has been detected
- AliIM.exe (PID: 7644)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
xor-url
(PID) Process(6428) AliIM_taobao.exe
Decrypted-URLs (1)http://www.ijs.si/software/snprintf/
(PID) Process(4604) AlibabaProtect.exe
Decrypted-URLs (1)http://www.ijs.si/software/snprintf/
(PID) Process(7644) AliIM.exe
Decrypted-URLs (1)http://www.ijs.si/software/snprintf/
Total processes
196
Monitored processes
41
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 892 | "C:\Program Files (x86)\AlibabaProtect\1.0.70.1684\AlibabaProtect.exe" /uninstall | C:\Program Files (x86)\AlibabaProtect\1.0.70.1684\AlibabaProtect.exe | — | pc-sdk-setup.exe | |||||||||||
User: admin Company: Alibaba Group Integrity Level: HIGH Description: Alibaba PC Safe Service Exit code: 1 Modules
| |||||||||||||||
| 1128 | C:\WINDOWS\winsxs\amd64_microsoft-windows-servicingstack_31bf3856ad364e35_10.0.19041.3989_none_7ddb45627cb30e03\TiWorker.exe -Embedding | C:\Windows\WinSxS\amd64_microsoft-windows-servicingstack_31bf3856ad364e35_10.0.19041.3989_none_7ddb45627cb30e03\TiWorker.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Modules Installer Worker Exit code: 0 Version: 10.0.19041.3989 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1584 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=6772,i,16171898239146010510,8320941329644047549,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=6700 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2268 | "C:\Users\admin\Downloads\AliIM_taobao.exe" | C:\Users\admin\Downloads\AliIM_taobao.exe | — | chrome.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2320 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=15 --field-trial-handle=6008,i,16171898239146010510,8320941329644047549,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=6076 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2636 | "C:\Program Files (x86)\AliWangWang\10.01.07C\SafeGuard\pc-sdk-setup.exe" | C:\Program Files (x86)\AliWangWang\10.01.07C\SafeGuard\pc-sdk-setup.exe | AlibabaProtectCon.exe | ||||||||||||
User: admin Company: 阿里巴巴 Integrity Level: HIGH Description: 阿里巴巴基础安全服务安装程序 Exit code: 0 Version: 1.0.70.1684 Modules
| |||||||||||||||
| 3460 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4400 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | AlibabaProtect.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4604 | "C:\Program Files (x86)\AlibabaProtect\1.0.70.1684\AlibabaProtect.exe" | C:\Program Files (x86)\AlibabaProtect\1.0.70.1684\AlibabaProtect.exe | services.exe | ||||||||||||
User: SYSTEM Company: Alibaba Group Integrity Level: SYSTEM Description: Alibaba PC Safe Service Modules
xor-url(PID) Process(4604) AlibabaProtect.exe Decrypted-URLs (1)http://www.ijs.si/software/snprintf/ | |||||||||||||||
| 4952 | "C:\Program Files (x86)\AliWangWang\10.01.07C\SafeGuard\AlibabaProtectCon.exe" /local_load "C:\Program Files (x86)\AliWangWang\10.01.07C\SafeGuard\pc-sdk-setup.exe" "C:\Program Files (x86)\AliWangWang" | C:\Program Files (x86)\AliWangWang\10.01.07C\SafeGuard\AlibabaProtectCon.exe | AliIM_taobao.exe | ||||||||||||
User: admin Company: Alibaba Group Integrity Level: HIGH Description: AlibabaProtectCon Exit code: 0 Modules
| |||||||||||||||
Total events
51 783
Read events
51 662
Write events
96
Delete events
25
Modification events
| (PID) Process: | (6428) AliIM_taobao.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\App Paths\AliIM.exe |
| Operation: | write | Name: | Path |
Value: C:\Program Files (x86)\AliWangWang | |||
| (PID) Process: | (6428) AliIM_taobao.exe | Key: | HKEY_CLASSES_ROOT\aliim |
| Operation: | write | Name: | URL Protocol |
Value: | |||
| (PID) Process: | (6428) AliIM_taobao.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\ProtocolExecute\aliim |
| Operation: | write | Name: | WarnOnOpen |
Value: 0 | |||
| (PID) Process: | (6428) AliIM_taobao.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\阿里旺旺 |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Program Files (x86)\AliWangWang\Uninstall.exe | |||
| (PID) Process: | (6428) AliIM_taobao.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\阿里旺旺 |
| Operation: | write | Name: | DisplayName |
Value: 阿里旺旺 | |||
| (PID) Process: | (6428) AliIM_taobao.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\阿里旺旺 |
| Operation: | write | Name: | Publisher |
Value: 阿里巴巴(中国)有限公司 | |||
| (PID) Process: | (6428) AliIM_taobao.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\阿里旺旺 |
| Operation: | write | Name: | DisplayVersion |
Value: 10.01.07C | |||
| (PID) Process: | (6428) AliIM_taobao.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\阿里旺旺 |
| Operation: | write | Name: | UninstallString |
Value: C:\Program Files (x86)\AliWangWang\Uninstall.exe | |||
| (PID) Process: | (6428) AliIM_taobao.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\阿里旺旺 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files (x86)\AliWangWang | |||
| (PID) Process: | (6428) AliIM_taobao.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\阿里旺旺 |
| Operation: | write | Name: | NoModify |
Value: 1 | |||
Executable files
202
Suspicious files
302
Text files
608
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6372 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old~RF1622ee.TMP | — | |
MD5:— | SHA256:— | |||
| 6372 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF1622ee.TMP | — | |
MD5:— | SHA256:— | |||
| 6372 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6372 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF1622fe.TMP | — | |
MD5:— | SHA256:— | |||
| 6372 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6372 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF1622fe.TMP | — | |
MD5:— | SHA256:— | |||
| 6372 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6372 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6372 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF16230d.TMP | — | |
MD5:— | SHA256:— | |||
| 6372 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
34
TCP/UDP connections
158
DNS requests
181
Threats
15
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7328 | chrome.exe | GET | 200 | 142.250.186.142:80 | http://clients2.google.com/time/1/current?cup2key=8:RtXu7YMU54Cz6Cn0slZVtSWe5VkDVka2CDiEfgMHCXw&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
4384 | svchost.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6156 | svchost.exe | GET | 200 | 162.159.142.9:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7432 | SIHClient.exe | GET | 200 | 23.3.109.244:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7432 | SIHClient.exe | GET | 200 | 23.3.109.244:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7432 | SIHClient.exe | GET | 200 | 23.3.109.244:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.3.crl | unknown | — | — | whitelisted |
7432 | SIHClient.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
7432 | SIHClient.exe | GET | 200 | 23.3.109.244:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.3.crl | unknown | — | — | whitelisted |
7432 | SIHClient.exe | GET | 200 | 23.3.109.244:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Time-Stamp%20PCA%202010(1).crl | unknown | — | — | whitelisted |
7644 | AliIM.exe | GET | 200 | 104.18.21.226:80 | http://ocsp2.globalsign.com/rootr3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBT1nGh%2FJBjWKnkPdZIzB1bqhelHBwQUj%2FBLf6guRSSuTVD6Y5qL3uLdG7wCEQCB5auY5G81uRwv%2BheHGMha | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
4384 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5596 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3548 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
7328 | chrome.exe | 142.250.185.74:443 | safebrowsingohttpgateway.googleapis.com | GOOGLE | US | whitelisted |
7328 | chrome.exe | 142.250.186.142:80 | google.com | GOOGLE | US | whitelisted |
7328 | chrome.exe | 3.174.46.56:443 | we.tl | AMAZON-02 | US | whitelisted |
7328 | chrome.exe | 108.177.15.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
7328 | chrome.exe | 3.174.46.57:443 | wetransfer.com | AMAZON-02 | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
we.tl |
| whitelisted |
accounts.google.com |
| whitelisted |
wetransfer.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
cdn.wetransfer.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7328 | chrome.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (wetransfer .com) |
7328 | chrome.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (wetransfer .com) |
7328 | chrome.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (wetransfer .com) |
7328 | chrome.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (wetransfer .com) |
7328 | chrome.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (wetransfer .com) |
7328 | chrome.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (wetransfer .com) |
7328 | chrome.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (wetransfer .com) |
7328 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7328 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
Process | Message |
|---|---|
AlibabaProtect.exe | arphaDump.dll
1: Hotfix present and filter active
2: Hotfix not present, filter active if this is an affected system
0: Hotfix present, filter not active
Current Filter Status:2 |
AliIM.exe | arphaDump.dll
1: Hotfix present and filter active
2: Hotfix not present, filter active if this is an affected system
0: Hotfix present, filter not active
Current Filter Status:2 |
AliIM.exe | arphaDump.dll
1: Hotfix present and filter active
2: Hotfix not present, filter active if this is an affected system
0: Hotfix present, filter not active
Current Filter Status:2 |
AliRender.exe | arphaDump.dll
1: Hotfix present and filter active
2: Hotfix not present, filter active if this is an affected system
0: Hotfix present, filter not active
Current Filter Status:2 |
AliIM.exe | Unknown property cursor
|
AliIM.exe | Unknown property cursor
|
AliIM.exe | Unknown property cursor
|
AliIM.exe | Unknown property cursor
|
AliIM.exe | Unknown property cursor
|
AliIM.exe | Unknown property cursor
|