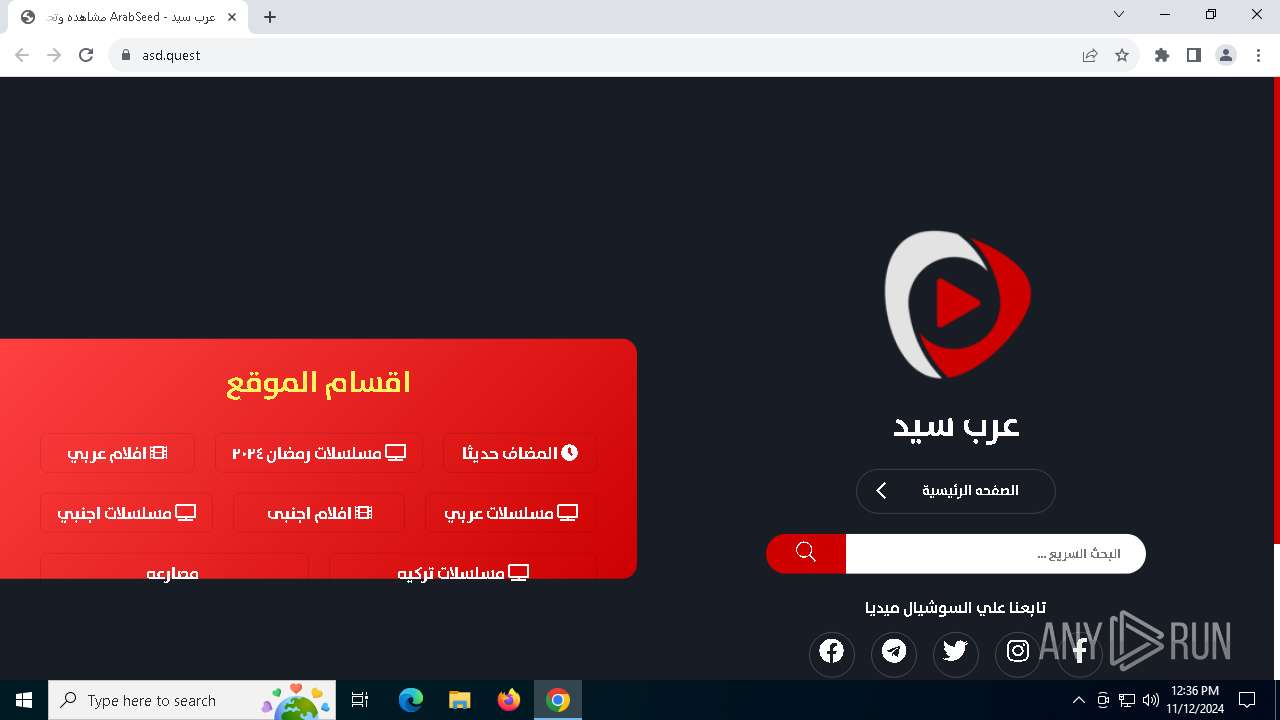
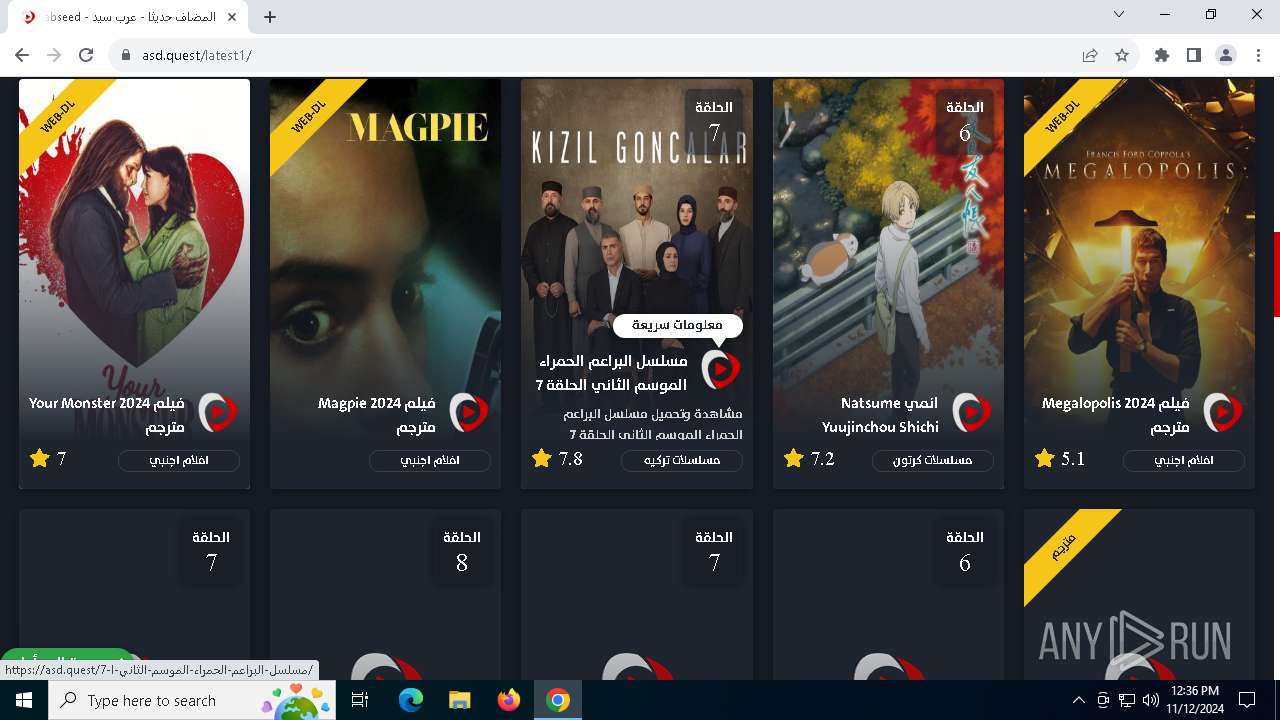
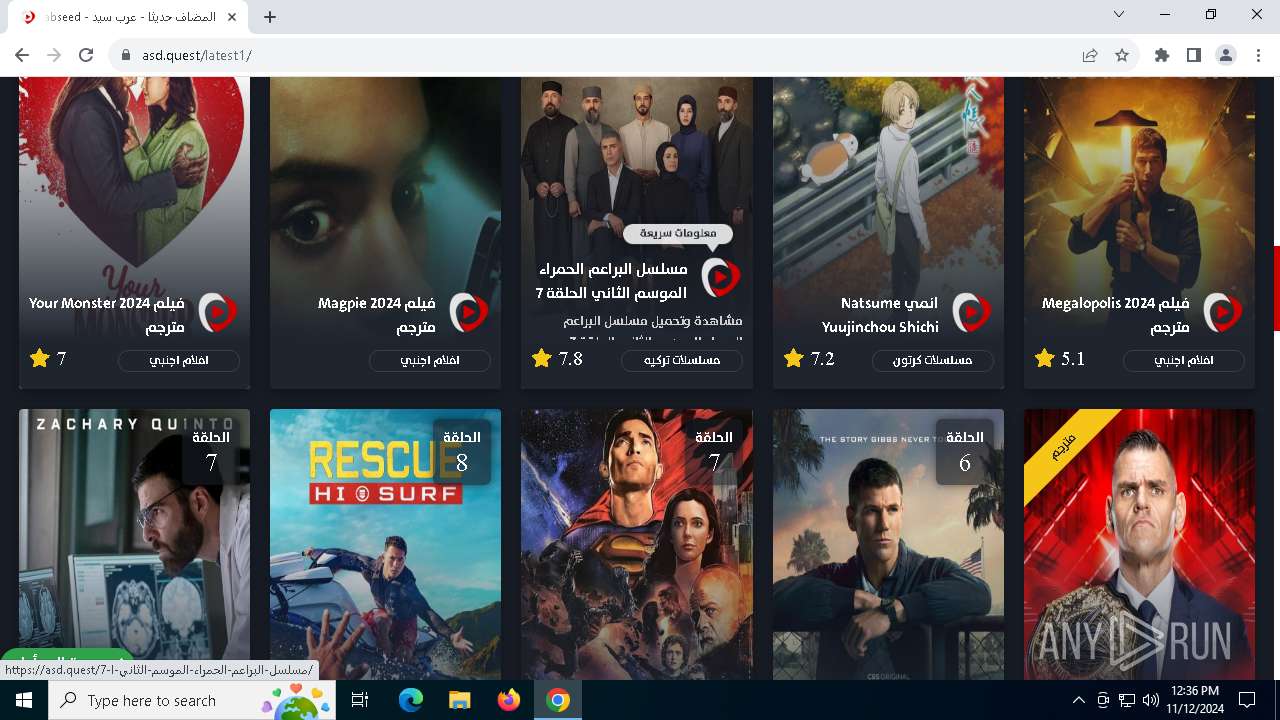
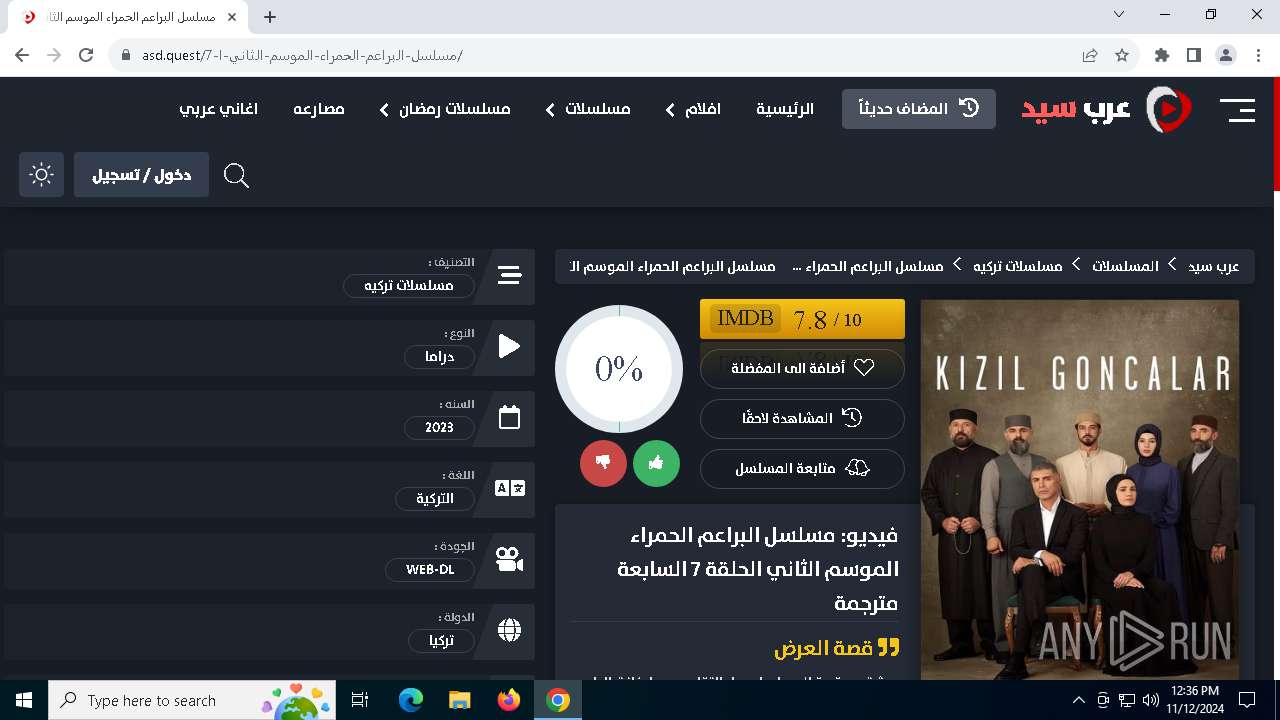
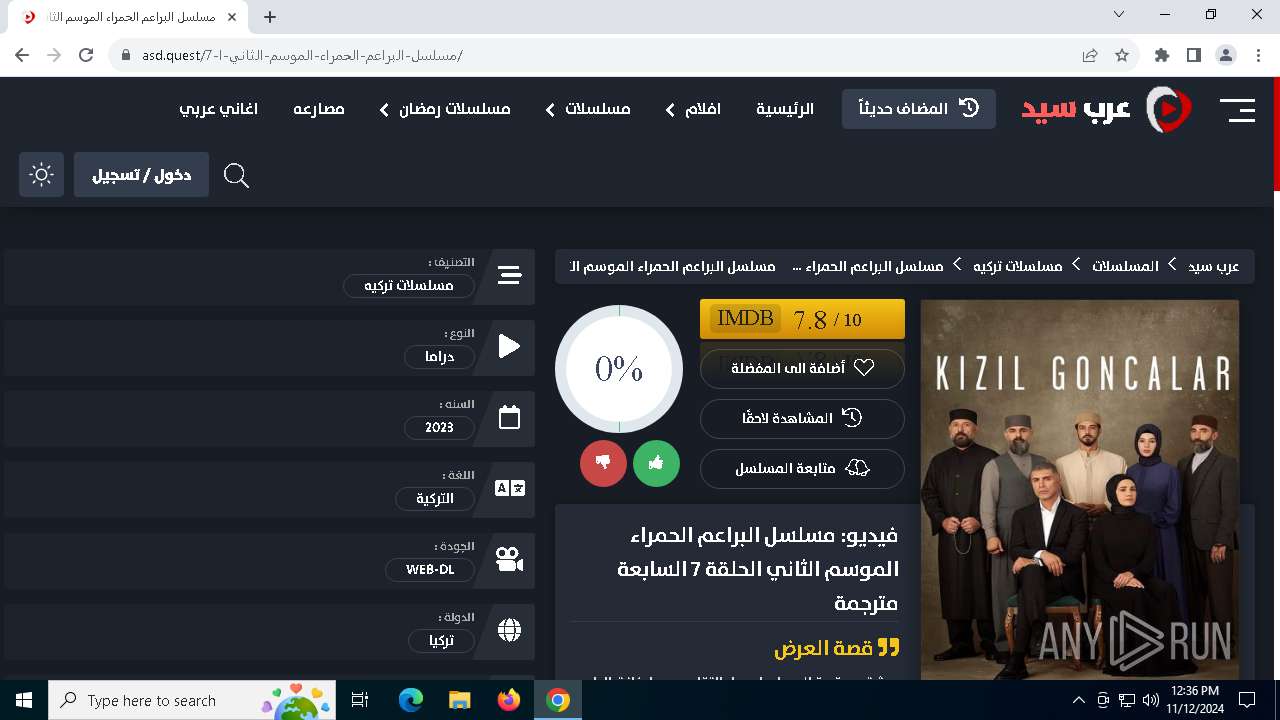
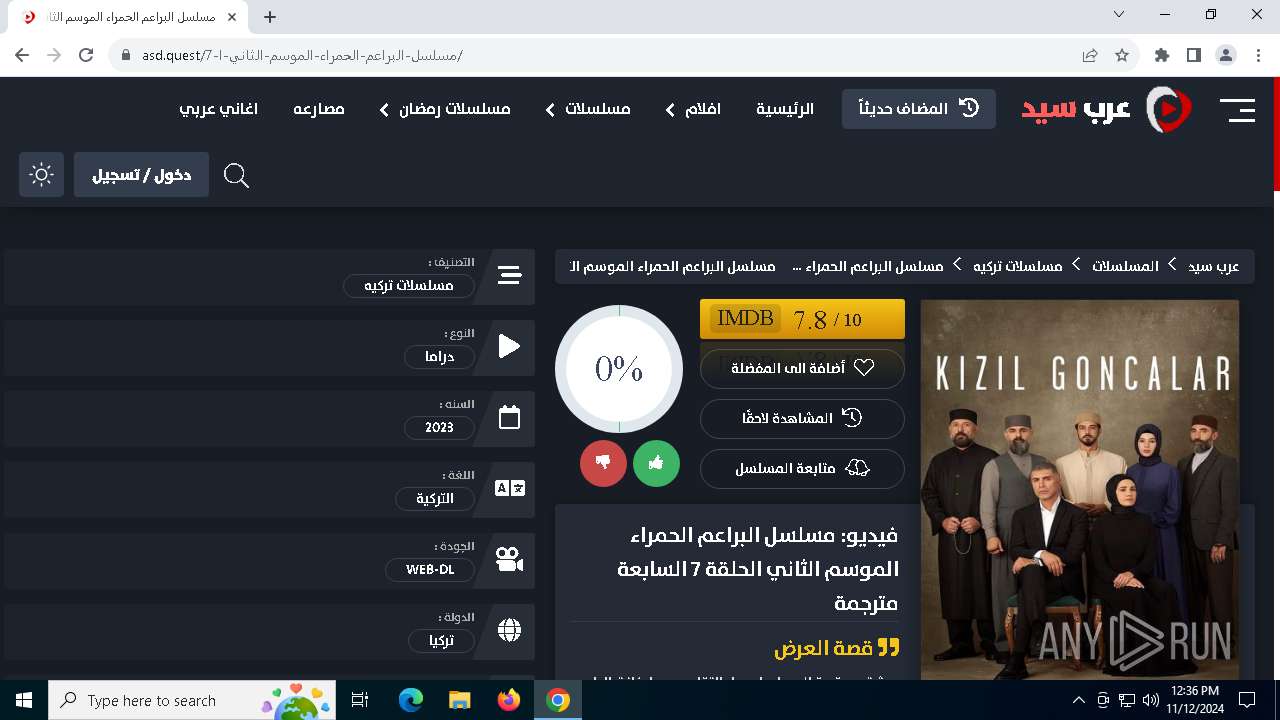
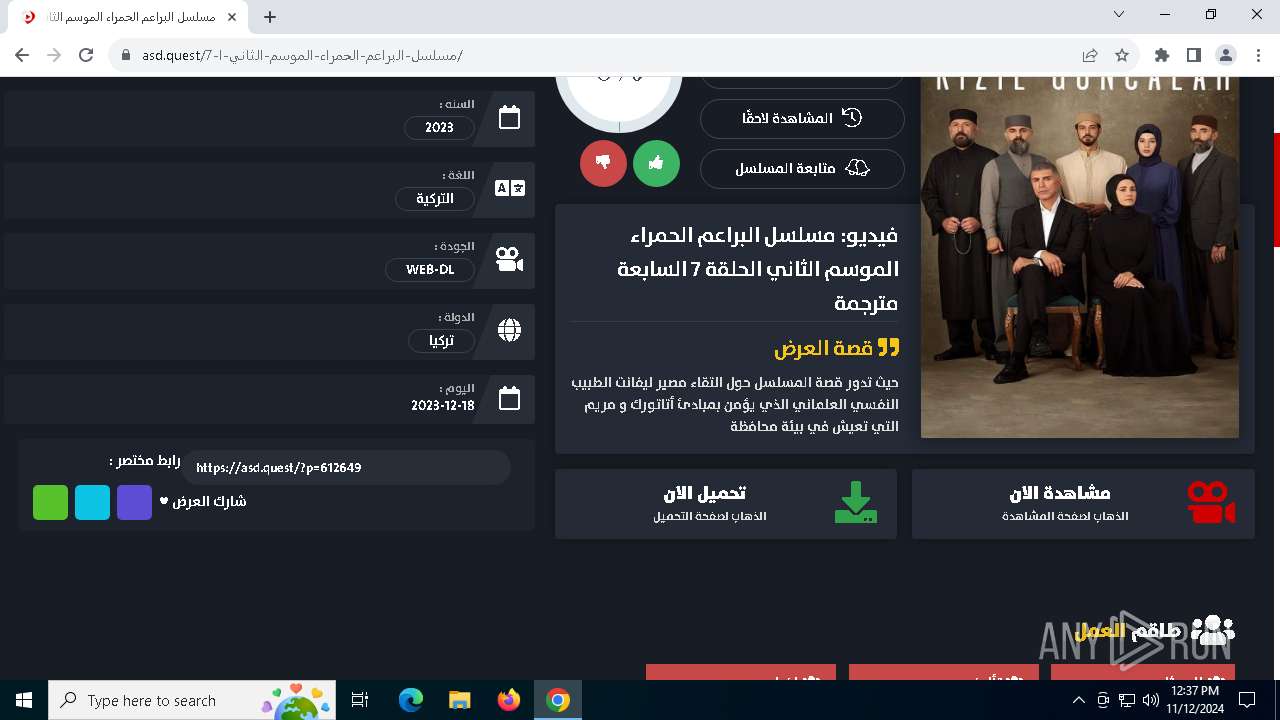
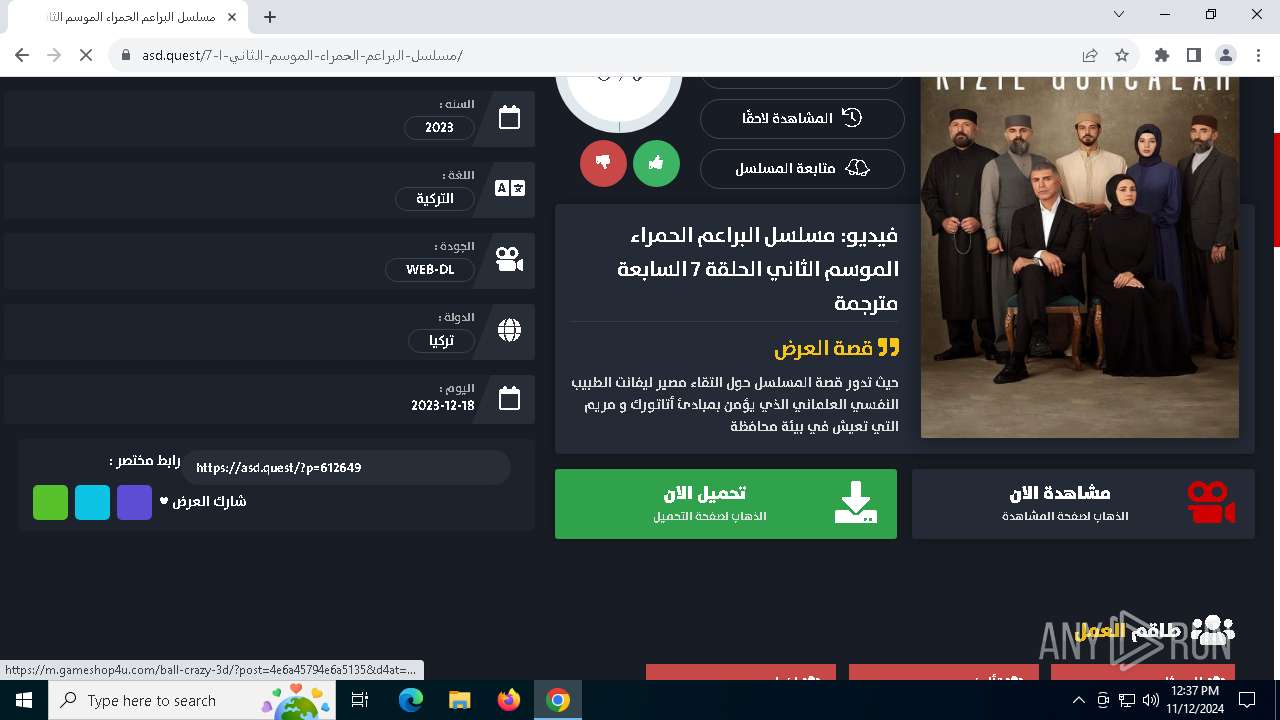
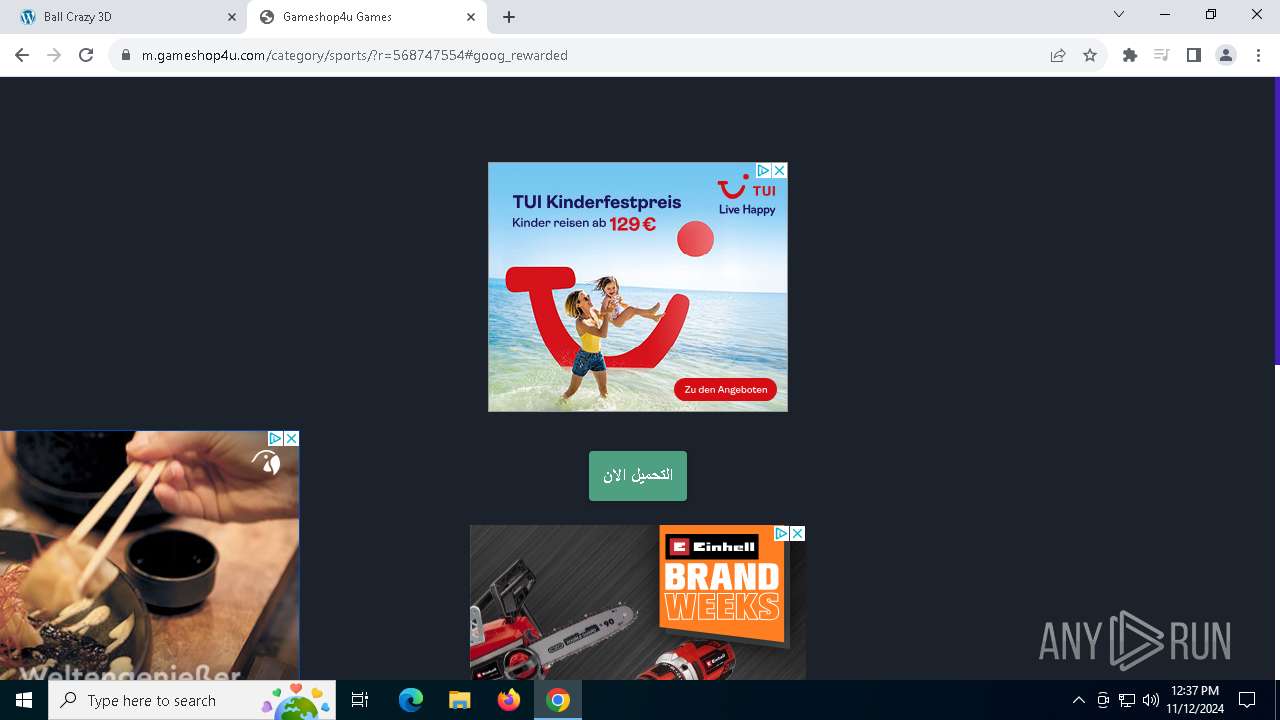
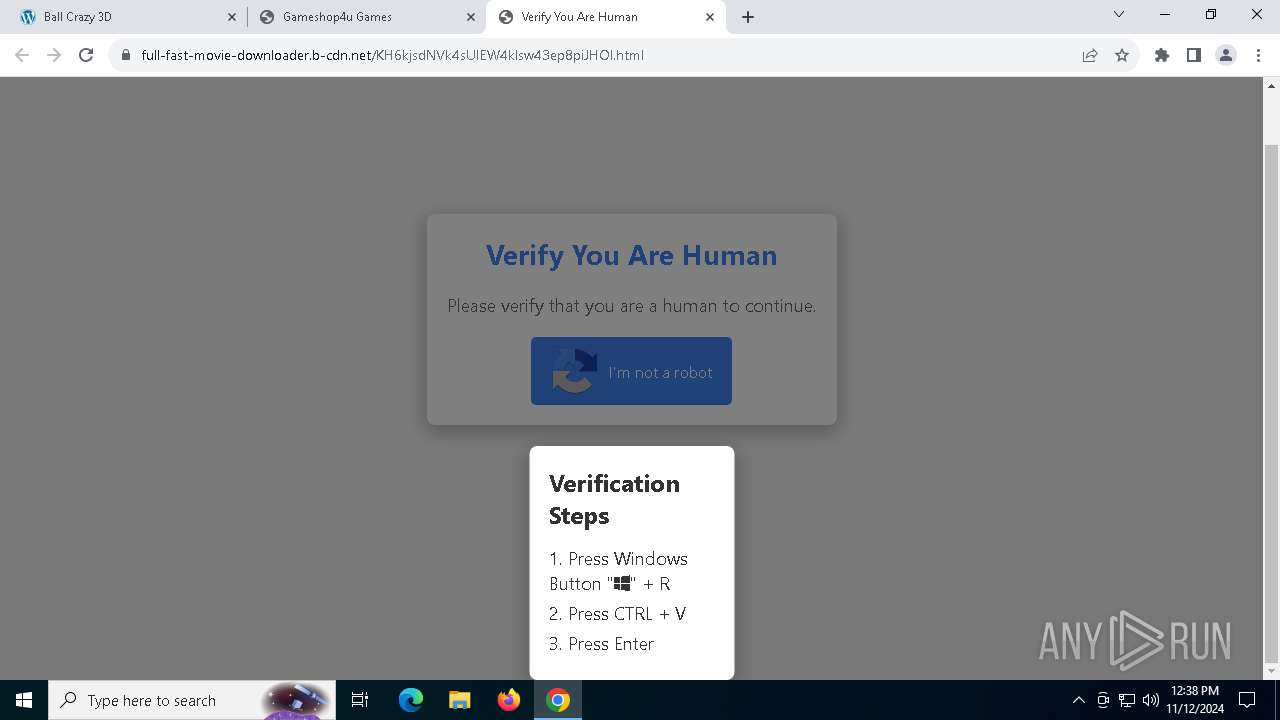
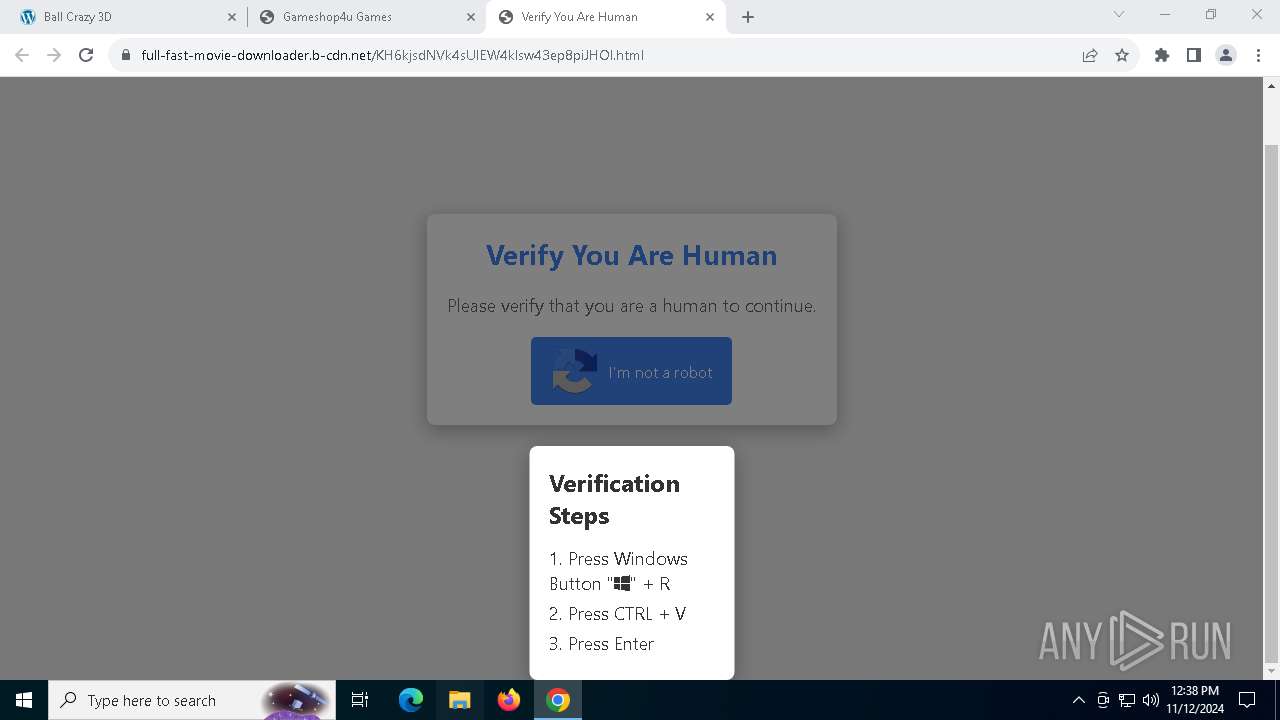
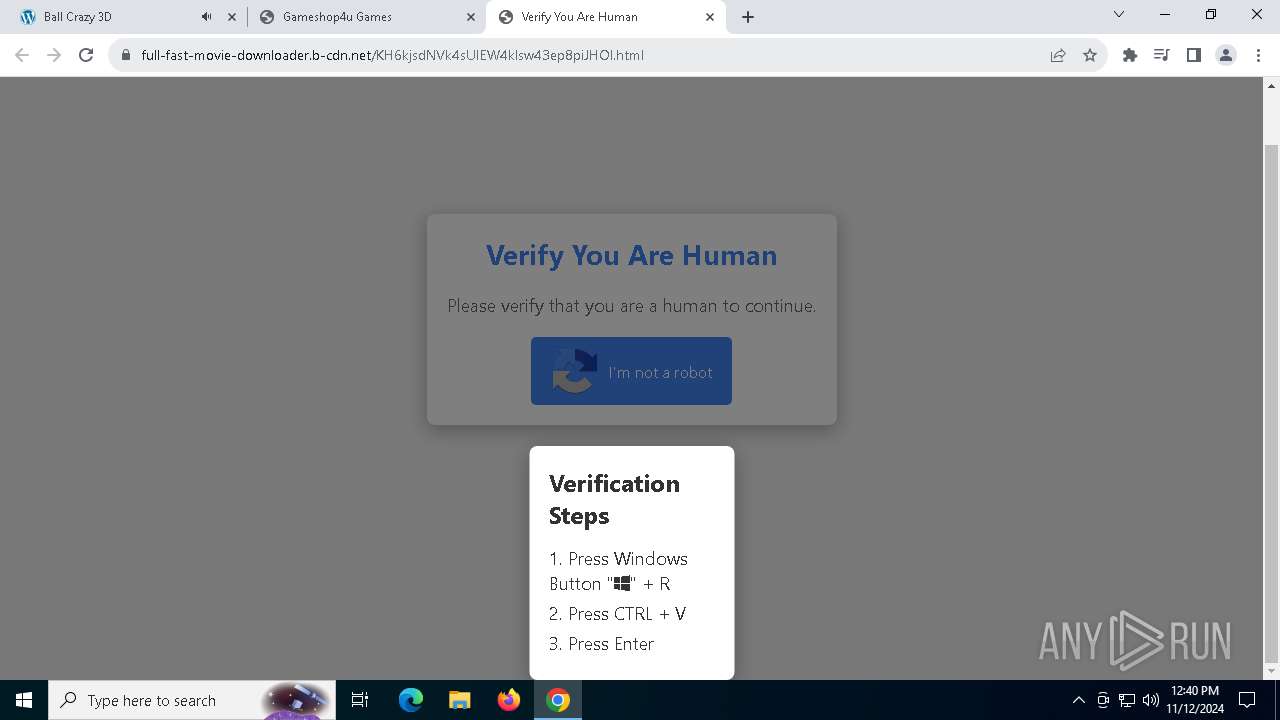
| URL: | https://arabseed.show |
| Full analysis: | https://app.any.run/tasks/cc77a289-f6ae-4648-9022-fd51b0cceb6c |
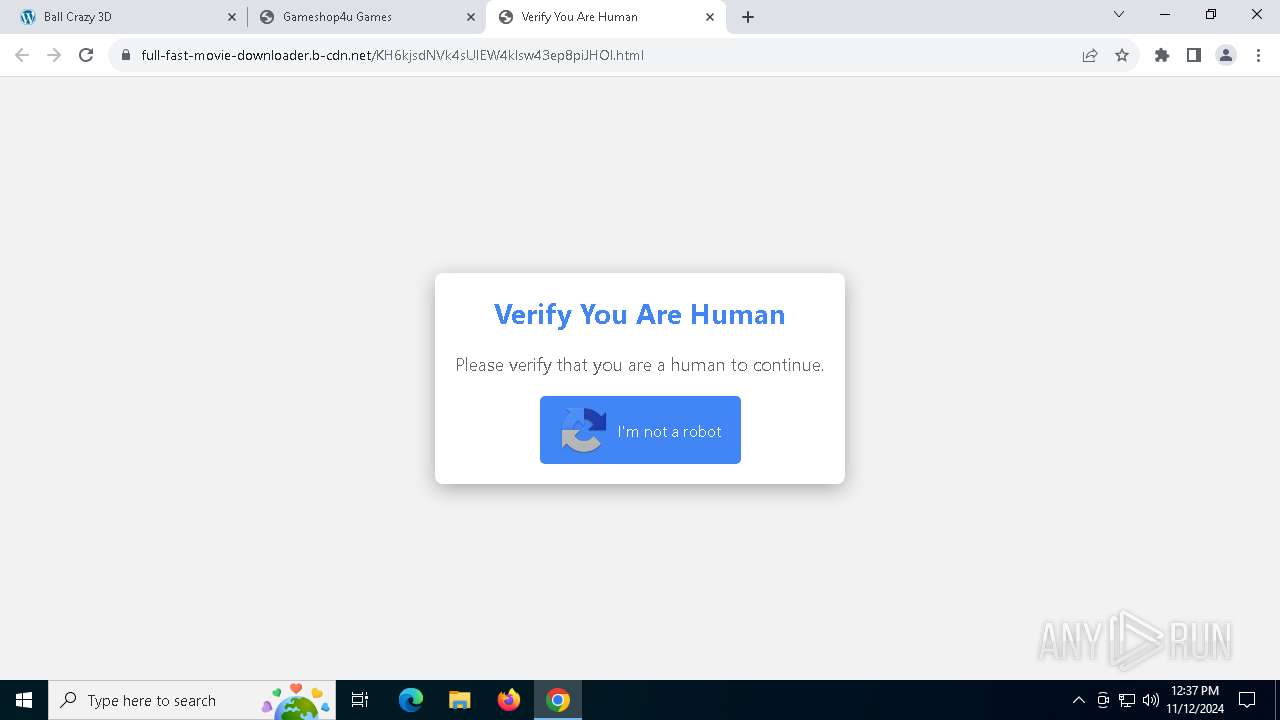
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | November 12, 2024, 12:35:56 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 3347C4688C678696375EC11B1784BEFB |
| SHA1: | A0AAF76F2CE6CBB4E2960A3524B701C125E38DDC |
| SHA256: | A159F7ED7485C5B7D7CD8D7BB3F4EF06E3395AF0D87A833974E2CF5A7A6A7BD4 |
| SSDEEP: | 3:N8ZABuKS:2+o |
MALICIOUS
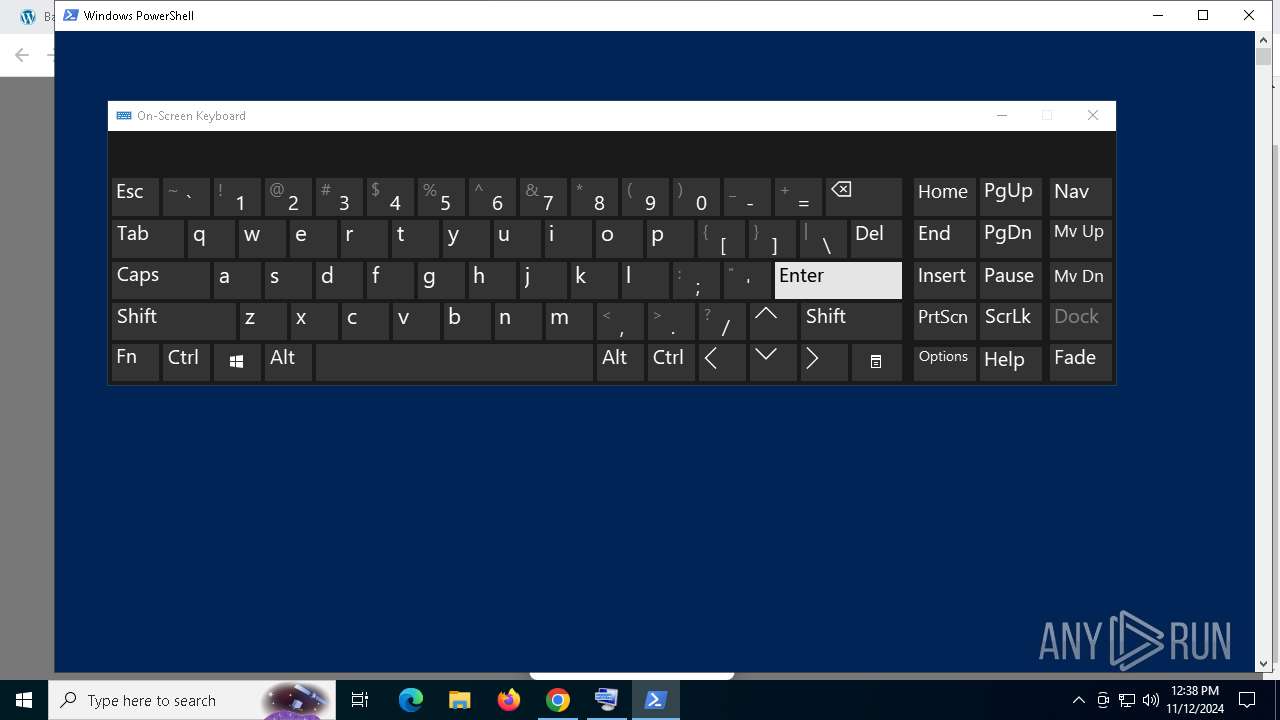
Run PowerShell with an invisible window
- powershell.exe (PID: 7556)
AutoIt loader has been detected (YARA)
- War.pif (PID: 8104)
LUMMA has been detected (SURICATA)
- War.pif (PID: 8104)
Actions looks like stealing of personal data
- War.pif (PID: 8104)
Changes powershell execution policy (Bypass)
- War.pif (PID: 8104)
- powershell.exe (PID: 6432)
Bypass execution policy to execute commands
- powershell.exe (PID: 6432)
- powershell.exe (PID: 7960)
SUSPICIOUS
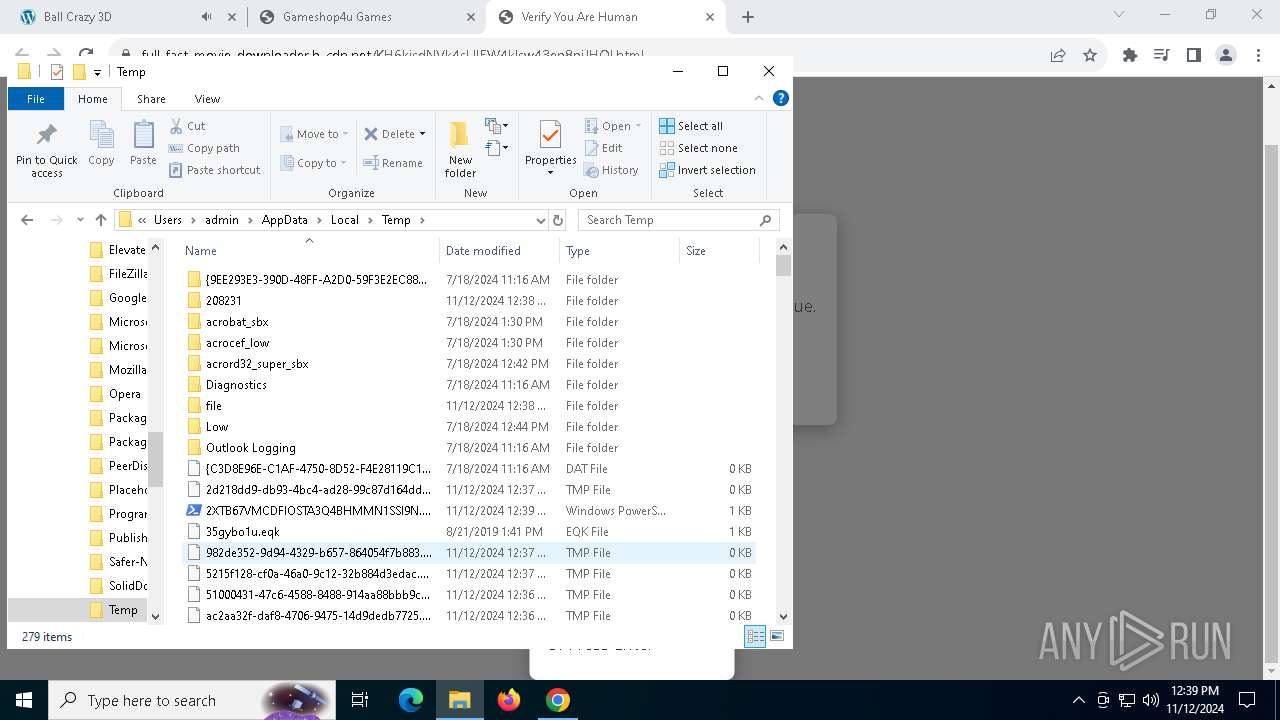
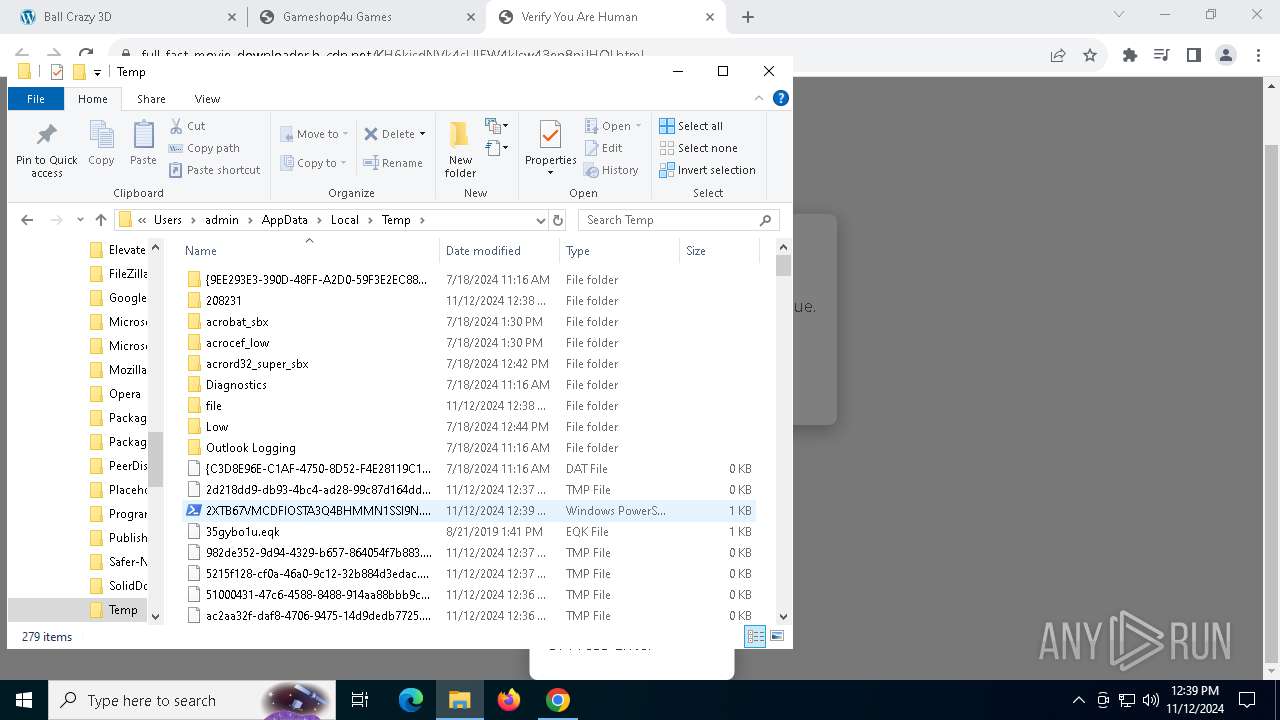
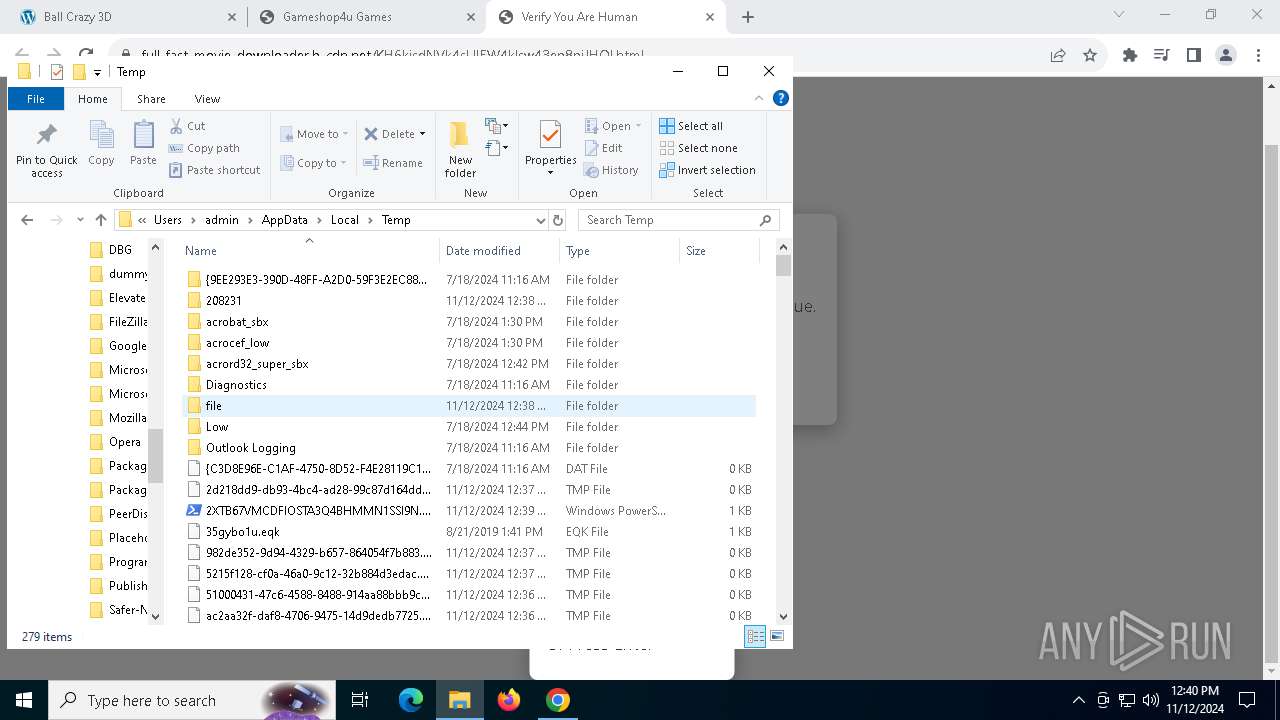
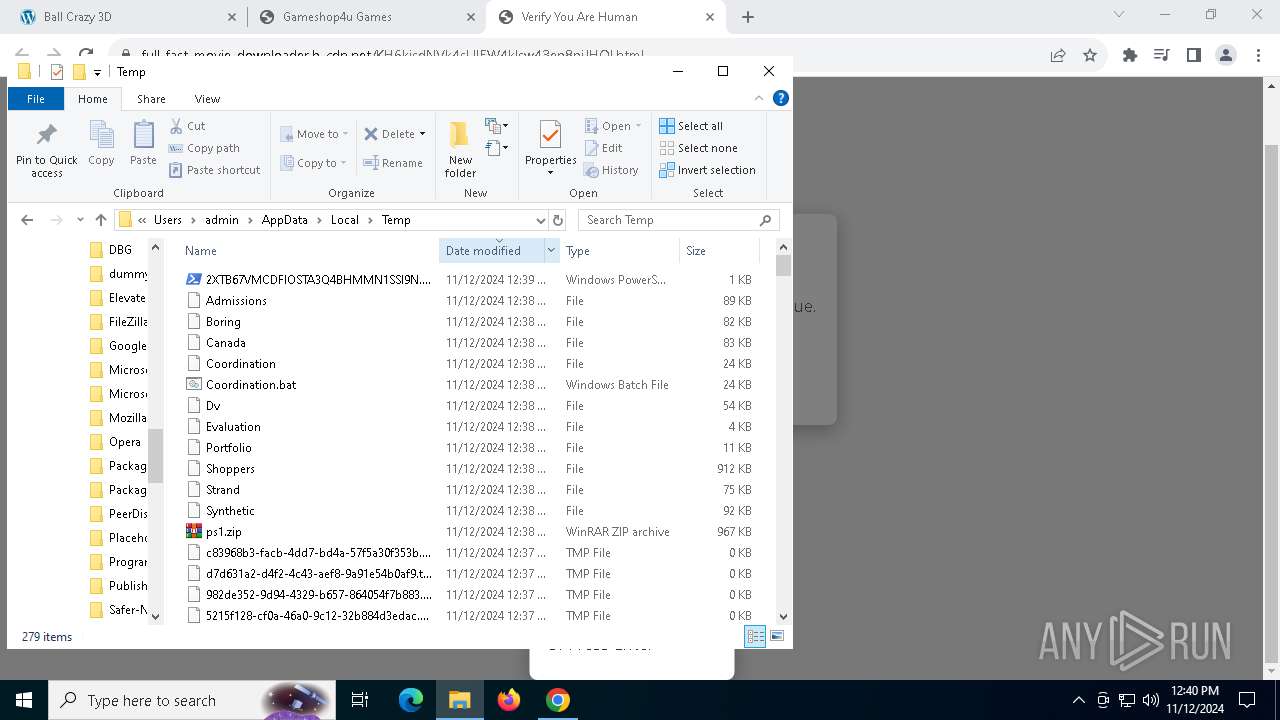
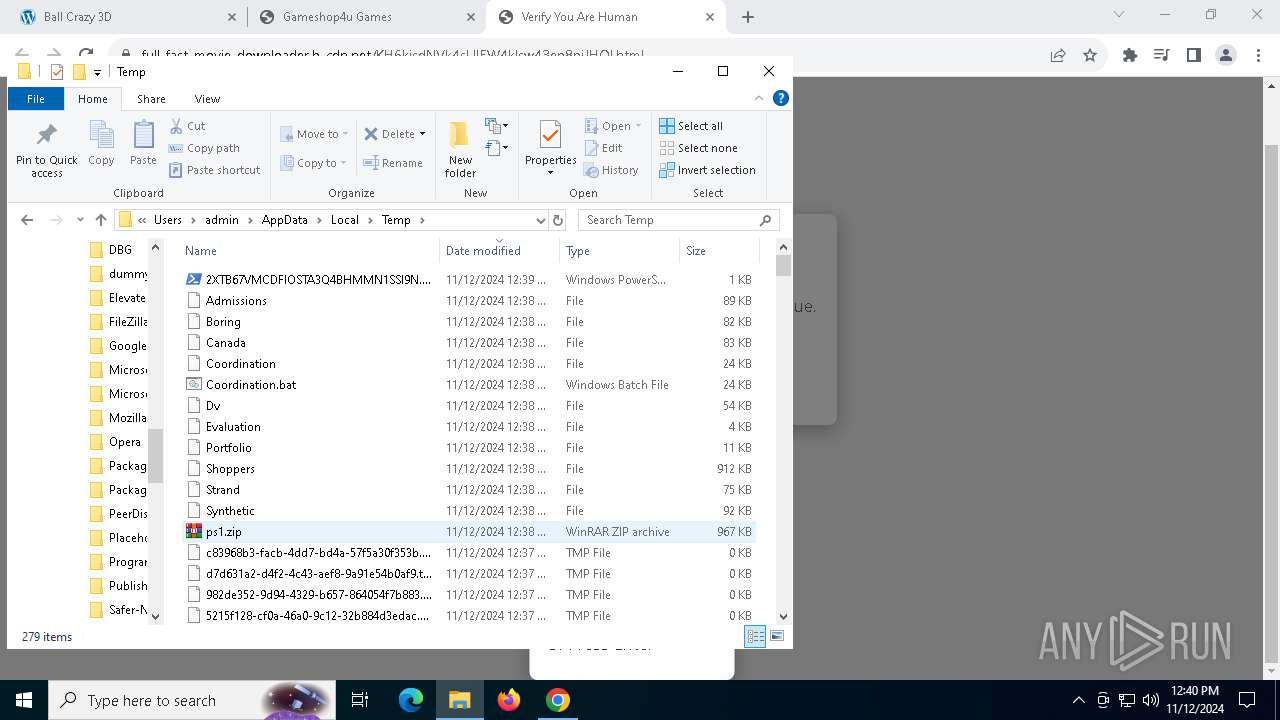
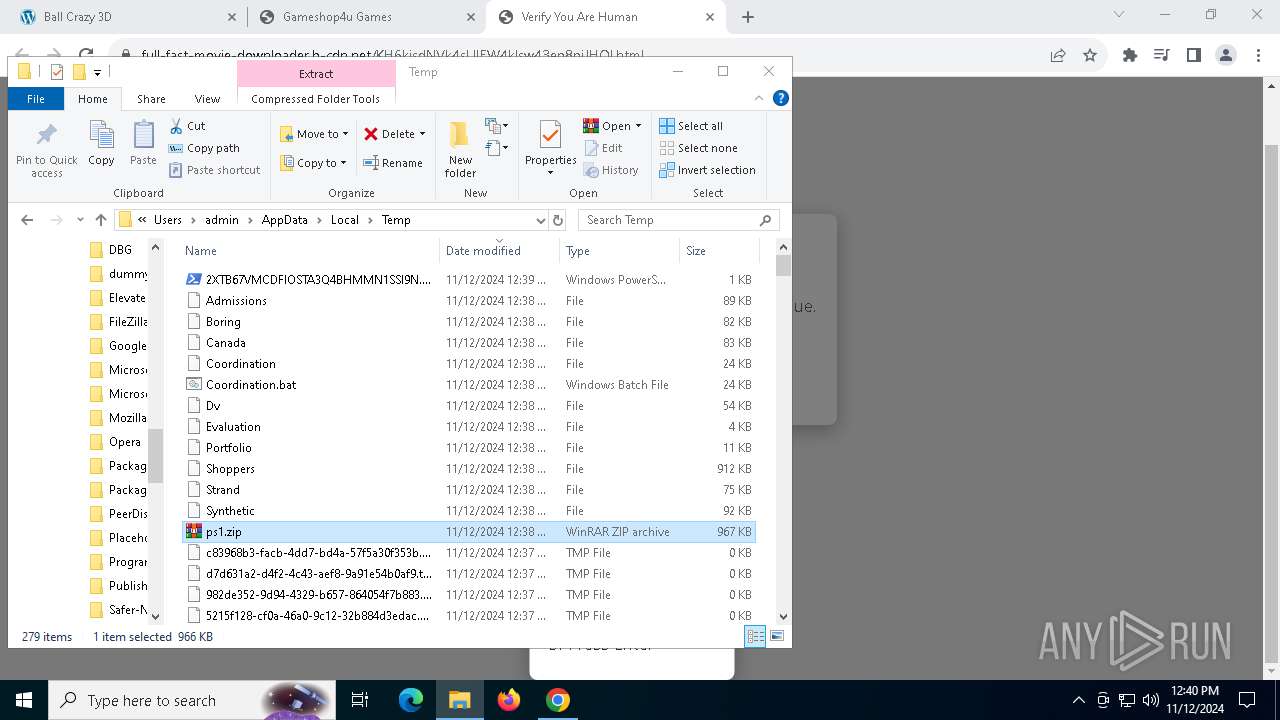
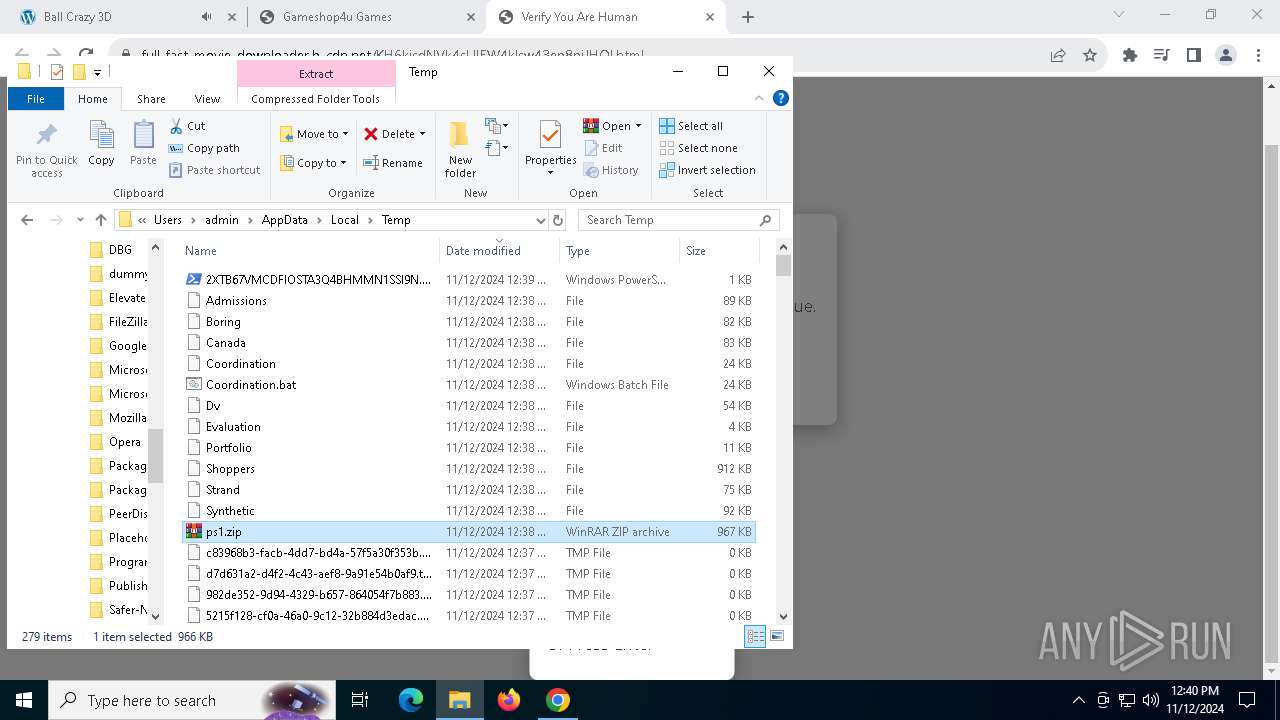
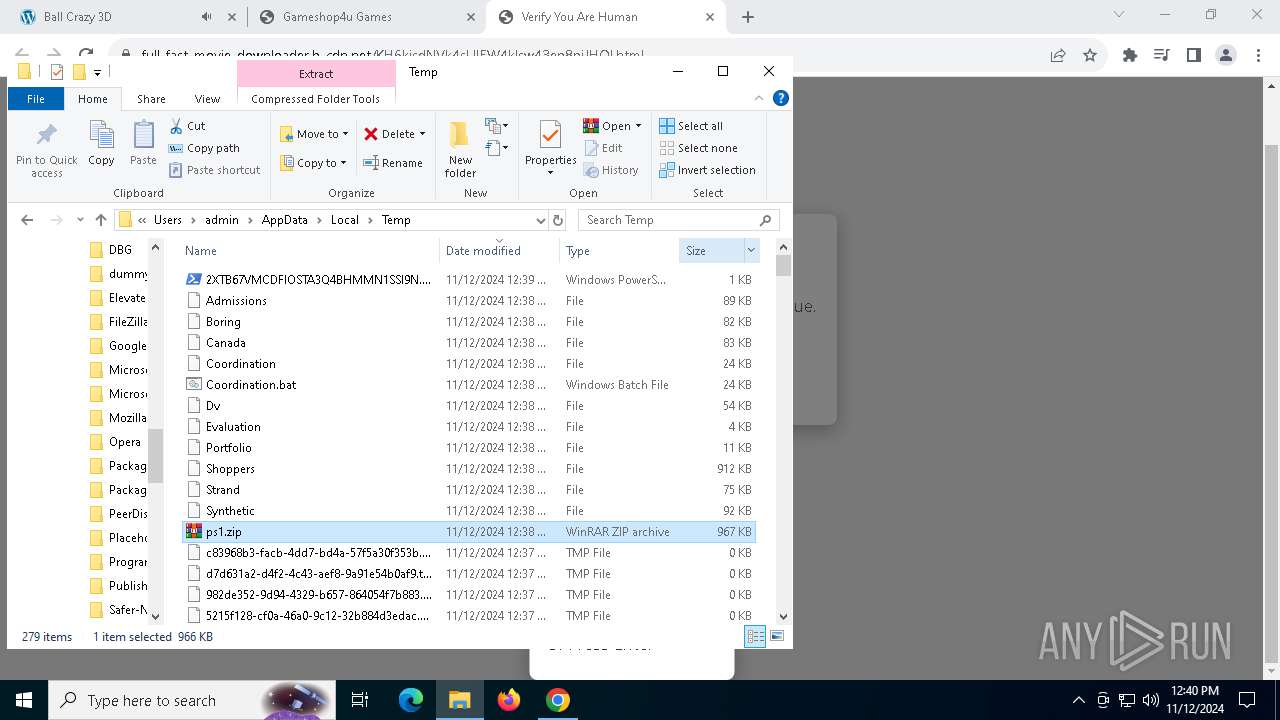
Executable content was dropped or overwritten
- powershell.exe (PID: 7556)
- cmd.exe (PID: 7824)
- War.pif (PID: 8104)
- YIR4GD.pif (PID: 8088)
Gets file extension (POWERSHELL)
- powershell.exe (PID: 7556)
Extracts files to a directory (POWERSHELL)
- powershell.exe (PID: 7556)
Reads security settings of Internet Explorer
- AccessoryLiberty.exe (PID: 7764)
Starts CMD.EXE for commands execution
- AccessoryLiberty.exe (PID: 7764)
- cmd.exe (PID: 7824)
Get information on the list of running processes
- cmd.exe (PID: 7824)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 7824)
Application launched itself
- cmd.exe (PID: 7824)
- powershell.exe (PID: 6432)
Starts application with an unusual extension
- cmd.exe (PID: 7824)
- War.pif (PID: 8104)
Drops a file with a rarely used extension (PIF)
- cmd.exe (PID: 7824)
The executable file from the user directory is run by the CMD process
- War.pif (PID: 8104)
Starts POWERSHELL.EXE for commands execution
- War.pif (PID: 8104)
- powershell.exe (PID: 6432)
Executing commands from a ".bat" file
- AccessoryLiberty.exe (PID: 7764)
The process executes Powershell scripts
- War.pif (PID: 8104)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 6432)
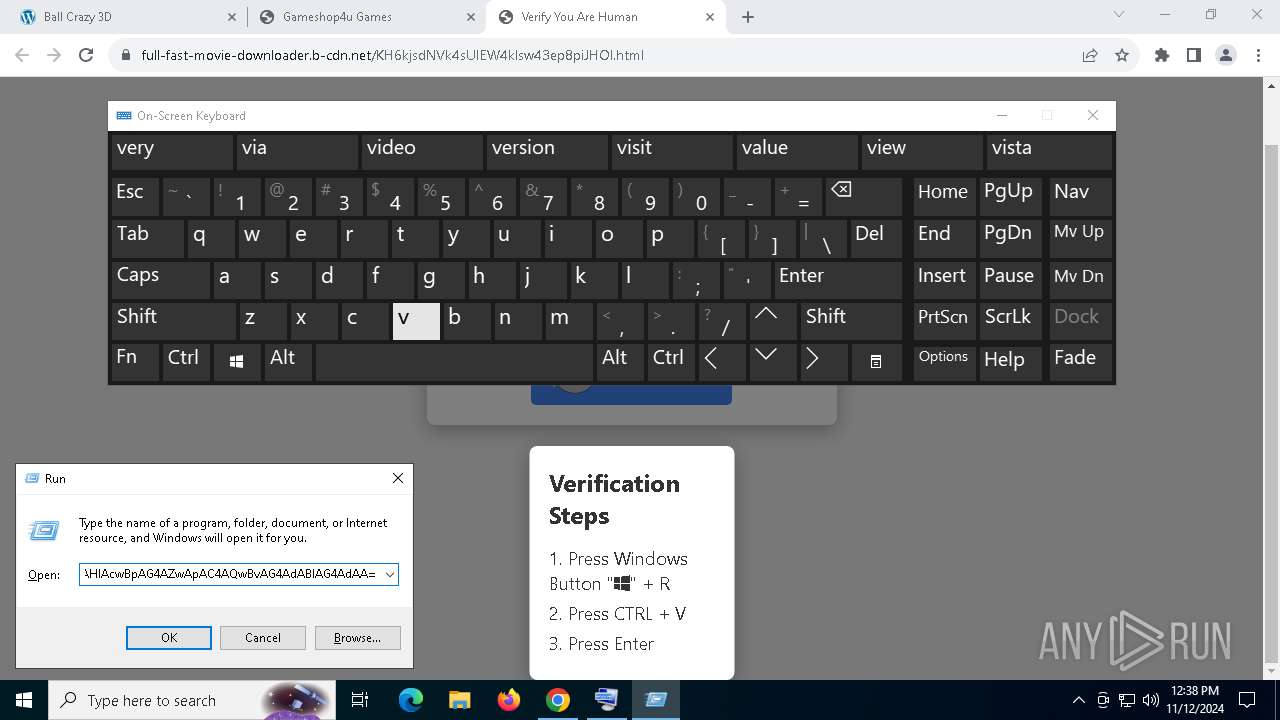
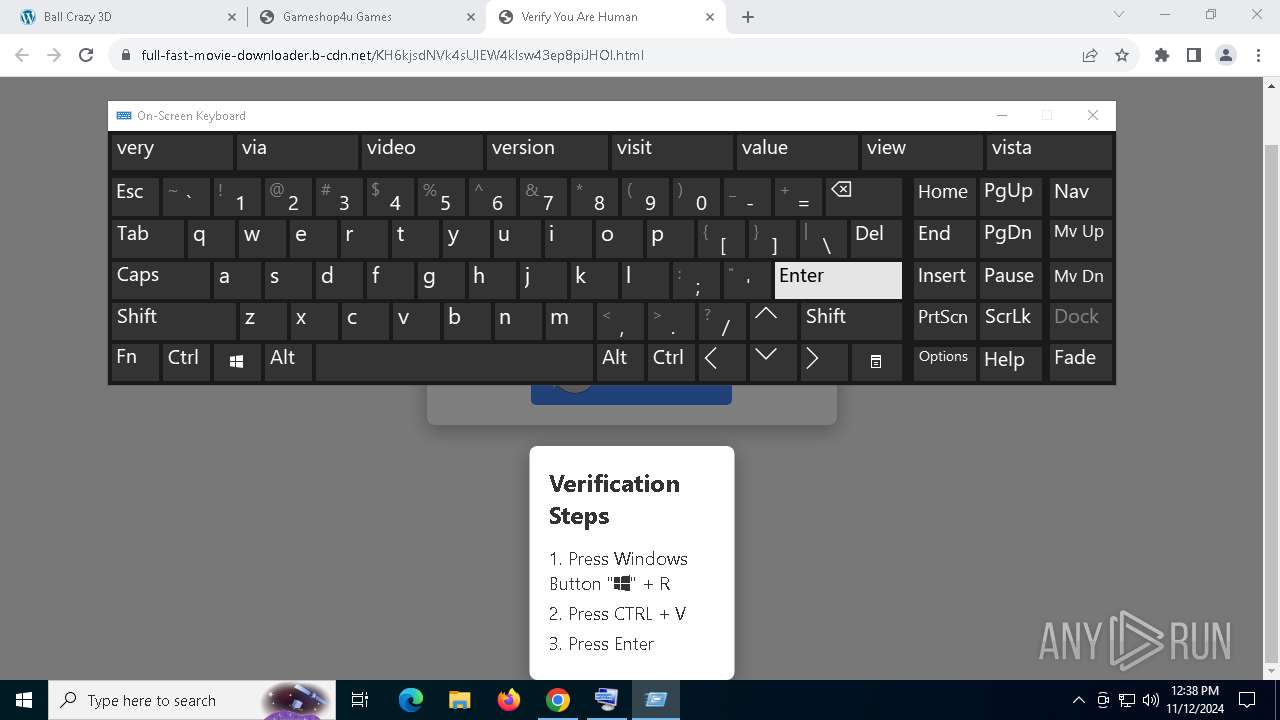
BASE64 encoded PowerShell command has been detected
- powershell.exe (PID: 6432)
Base64-obfuscated command line is found
- powershell.exe (PID: 6432)
The process bypasses the loading of PowerShell profile settings
- powershell.exe (PID: 6432)
Checks whether the computer is part of a domain (POWERSHELL)
- powershell.exe (PID: 7960)
The process executes VB scripts
- YIR4GD.pif (PID: 8088)
INFO
Application launched itself
- chrome.exe (PID: 6664)
Disables trace logs
- powershell.exe (PID: 7556)
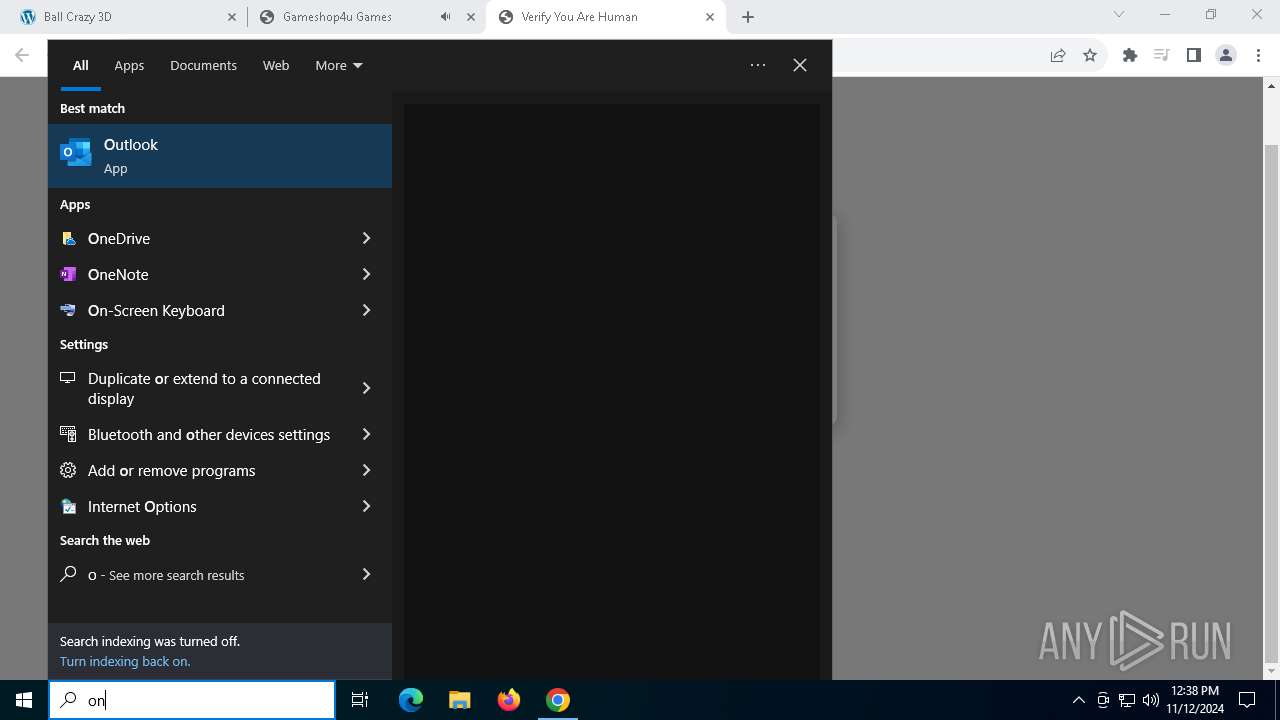
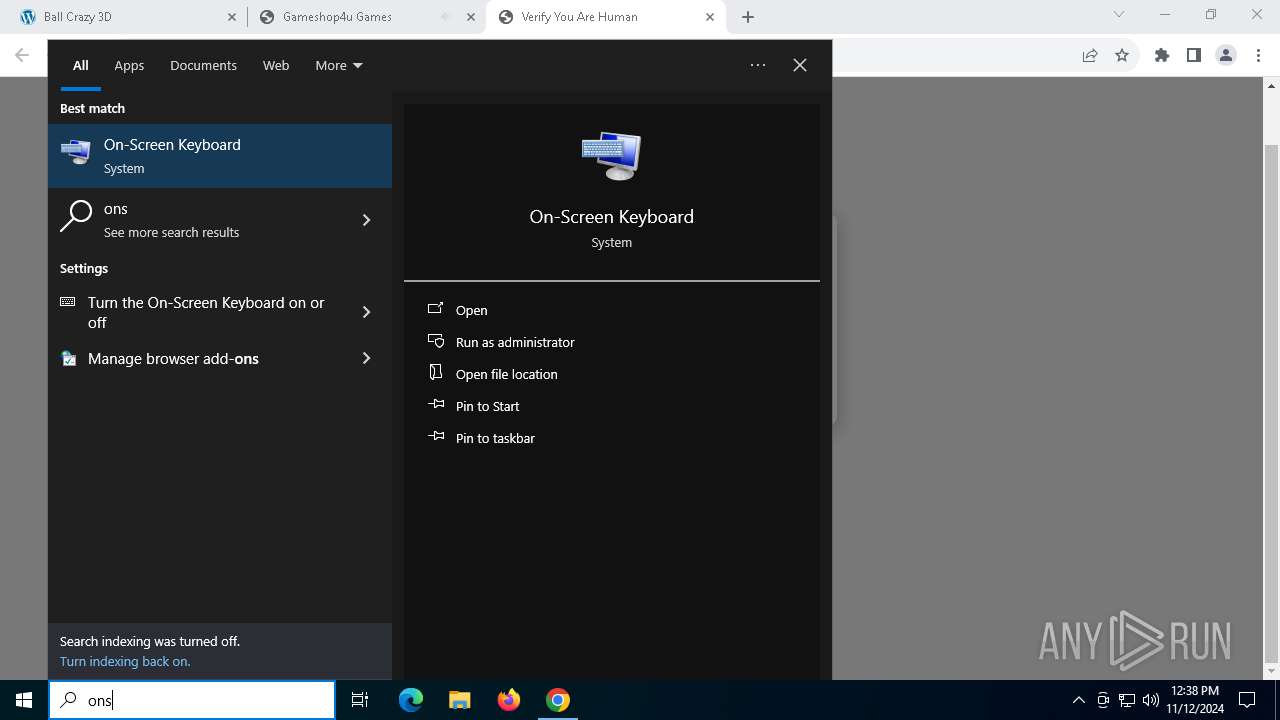
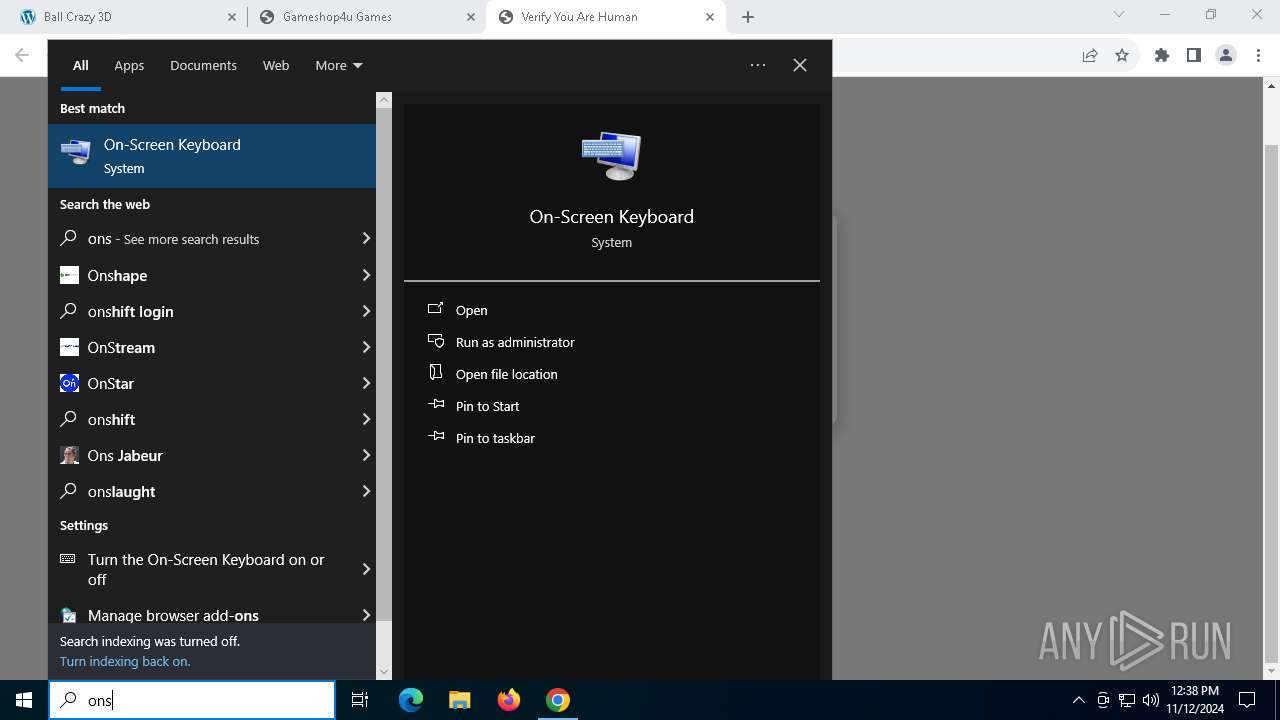
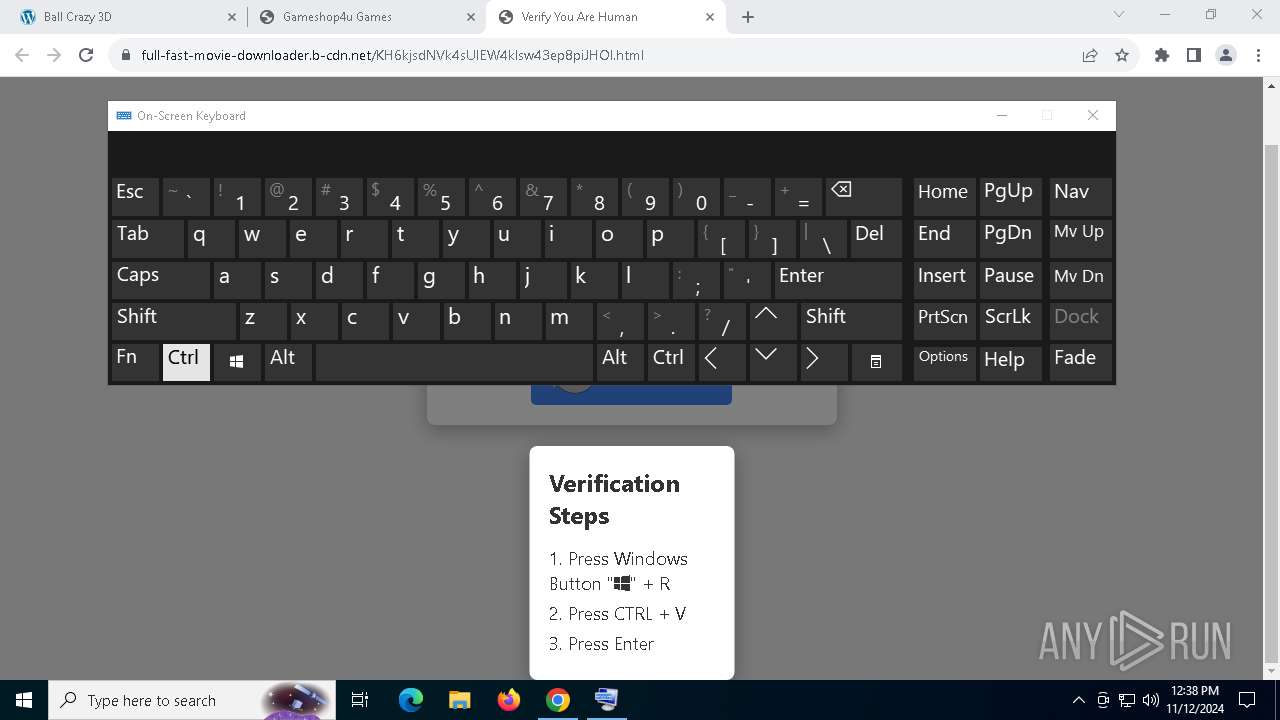
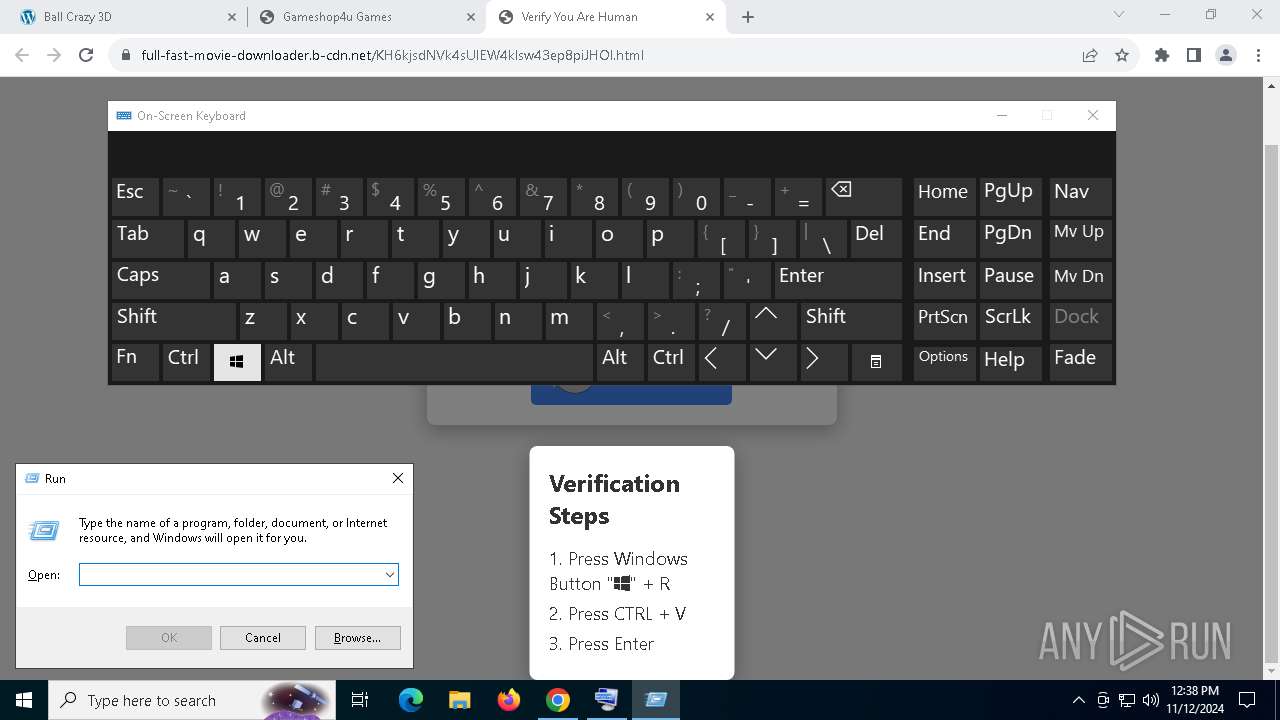
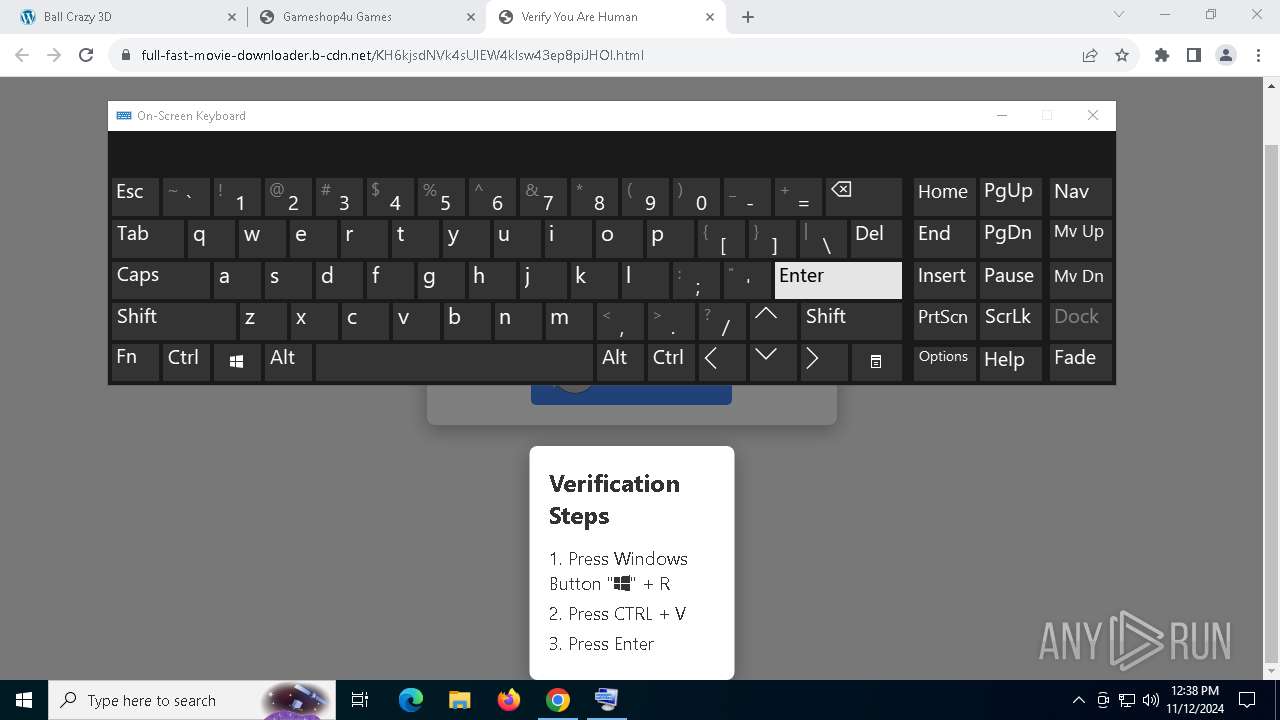
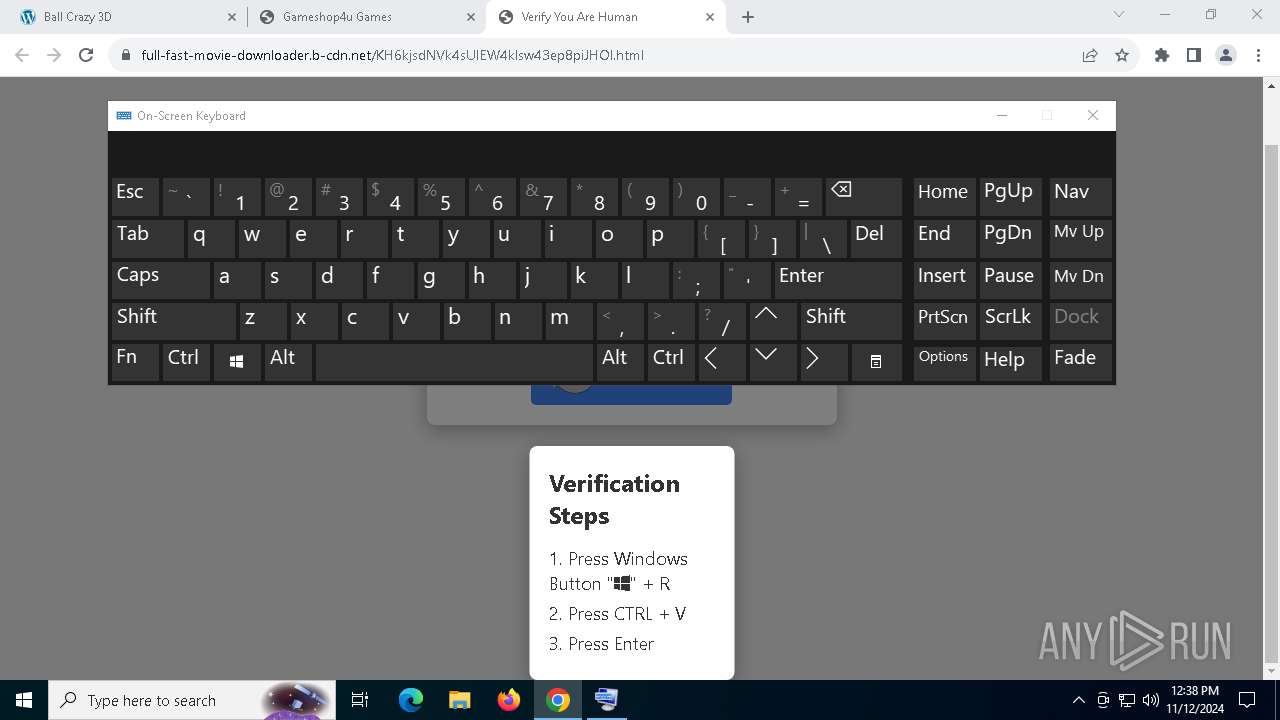
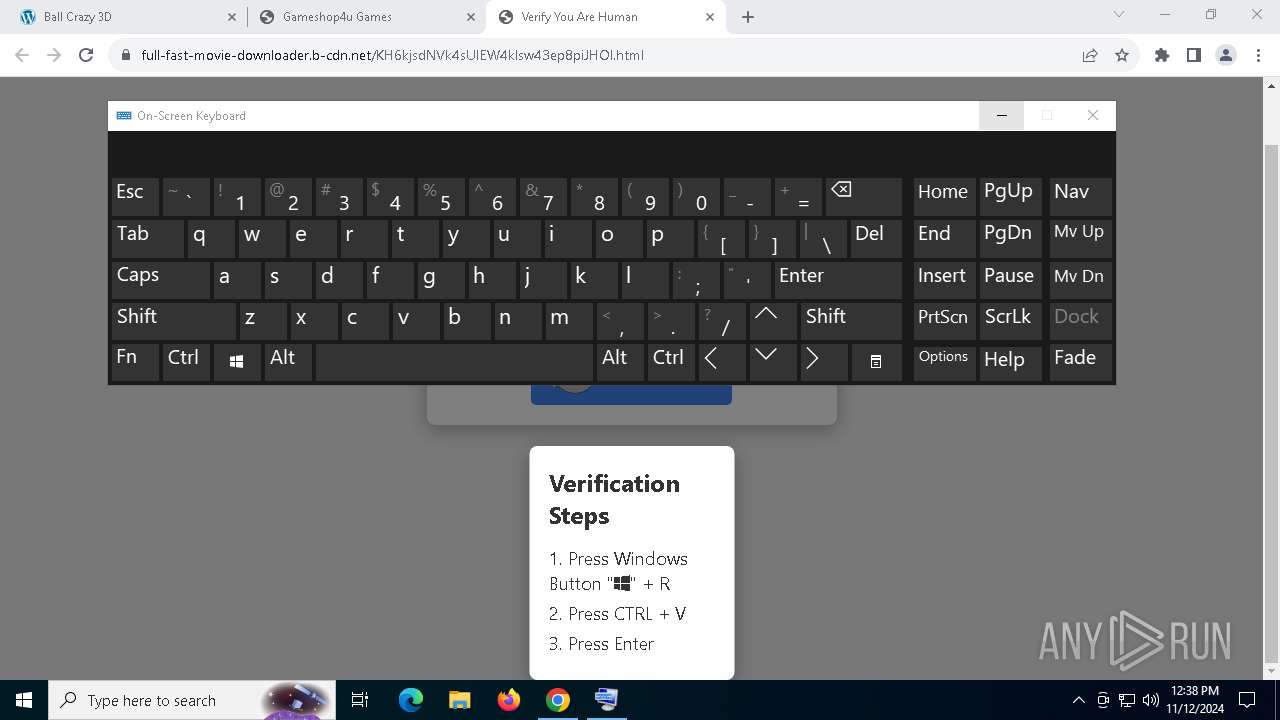
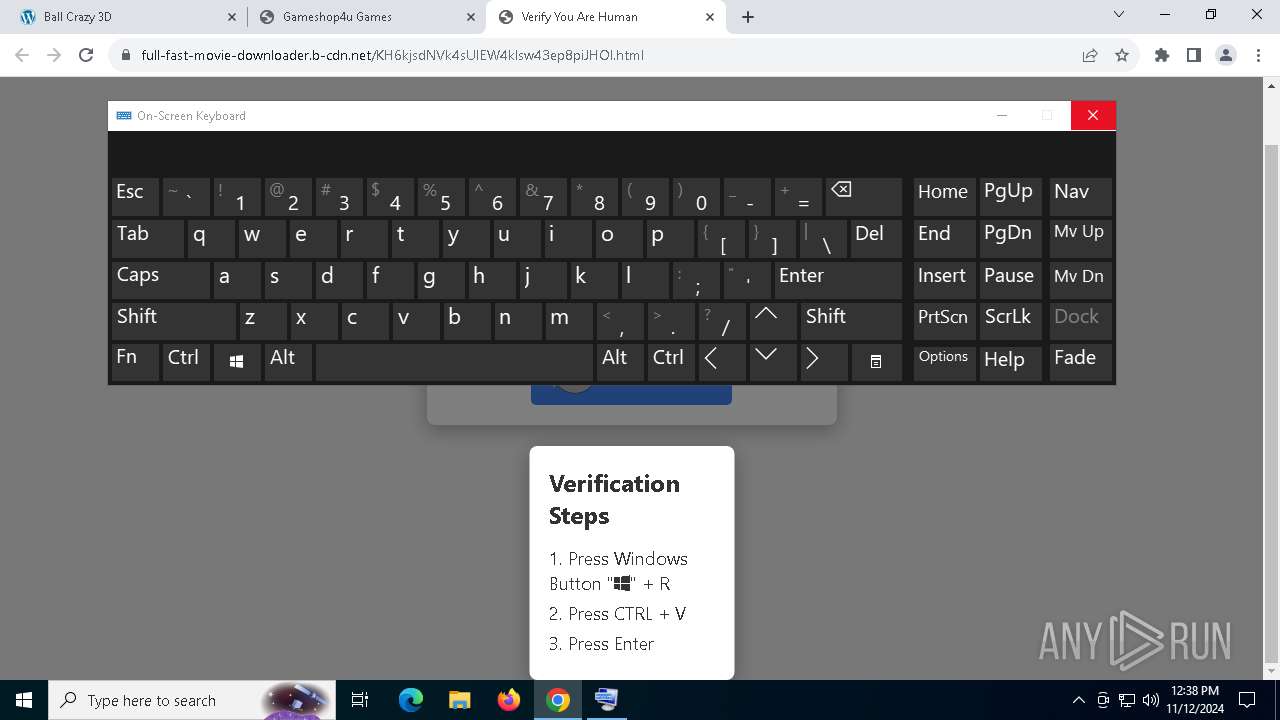
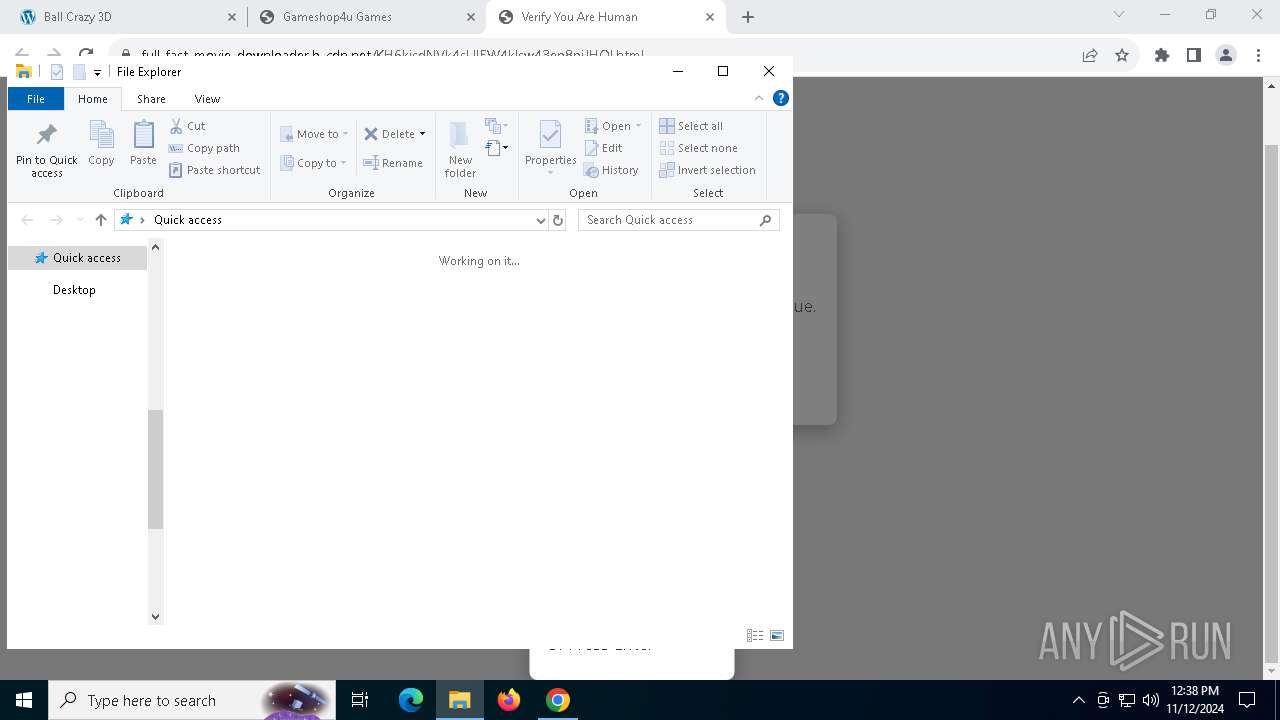
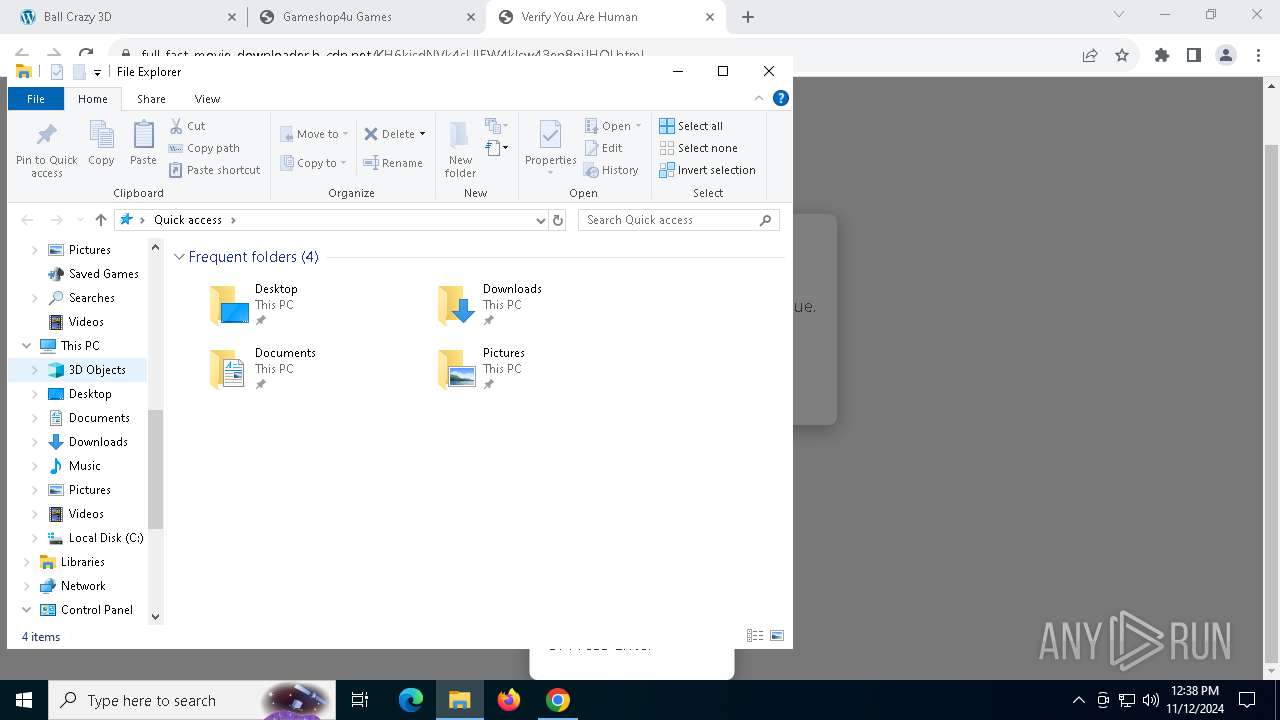
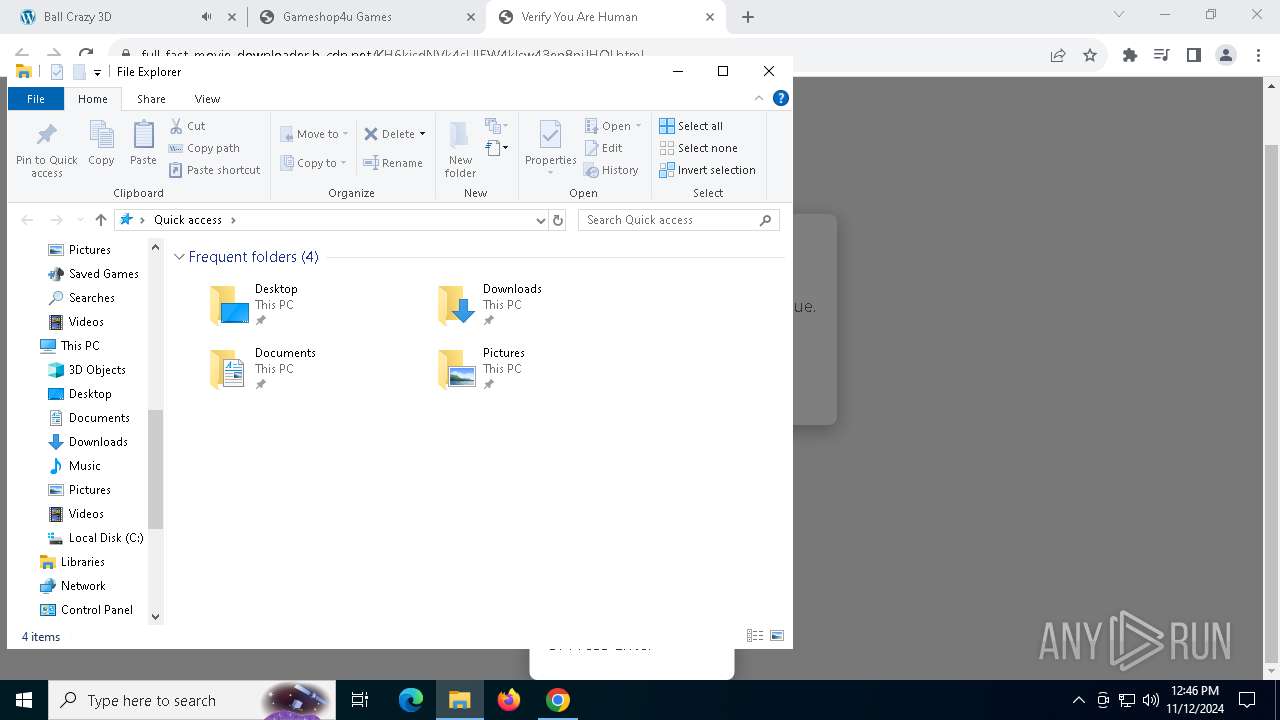
Manual execution by a user
- osk.exe (PID: 7192)
- osk.exe (PID: 7064)
- powershell.exe (PID: 7556)
- WinRAR.exe (PID: 2128)
- WinRAR.exe (PID: 1376)
Checks proxy server information
- powershell.exe (PID: 7556)
Checks supported languages
- AccessoryLiberty.exe (PID: 7764)
- War.pif (PID: 8104)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 7556)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7556)
Reads the computer name
- AccessoryLiberty.exe (PID: 7764)
- War.pif (PID: 8104)
The process uses the downloaded file
- powershell.exe (PID: 7556)
- AccessoryLiberty.exe (PID: 7764)
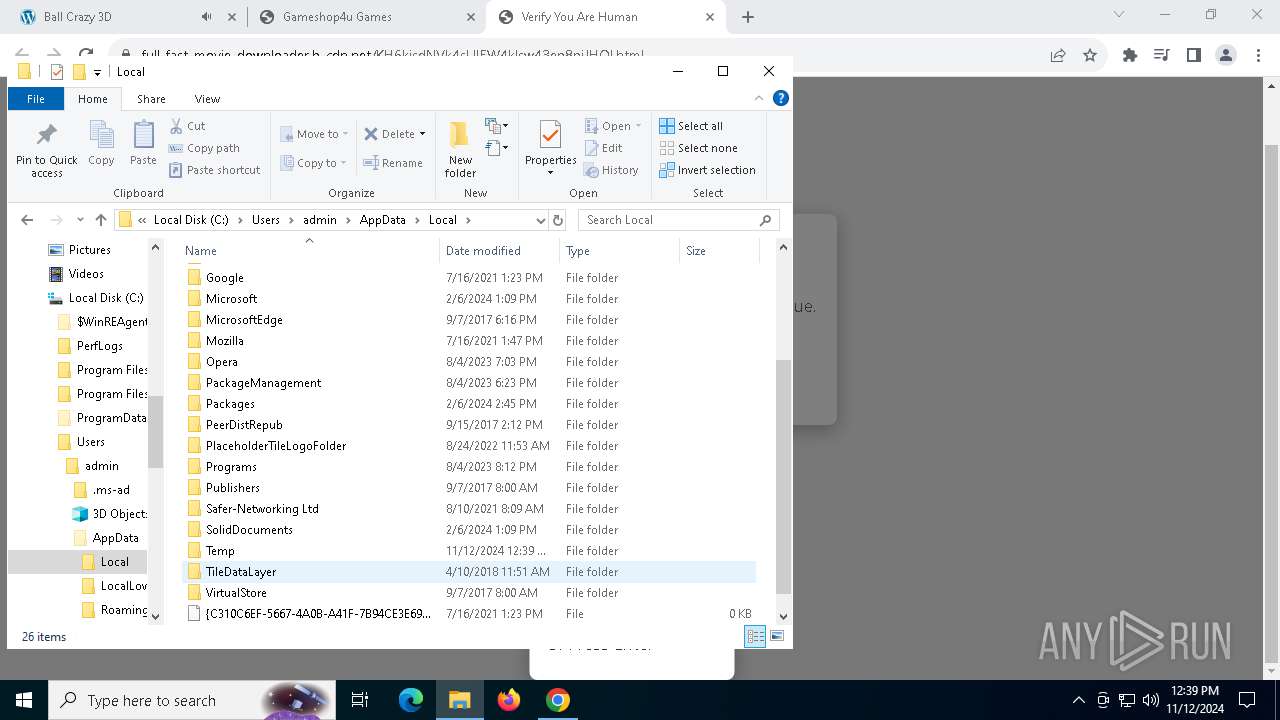
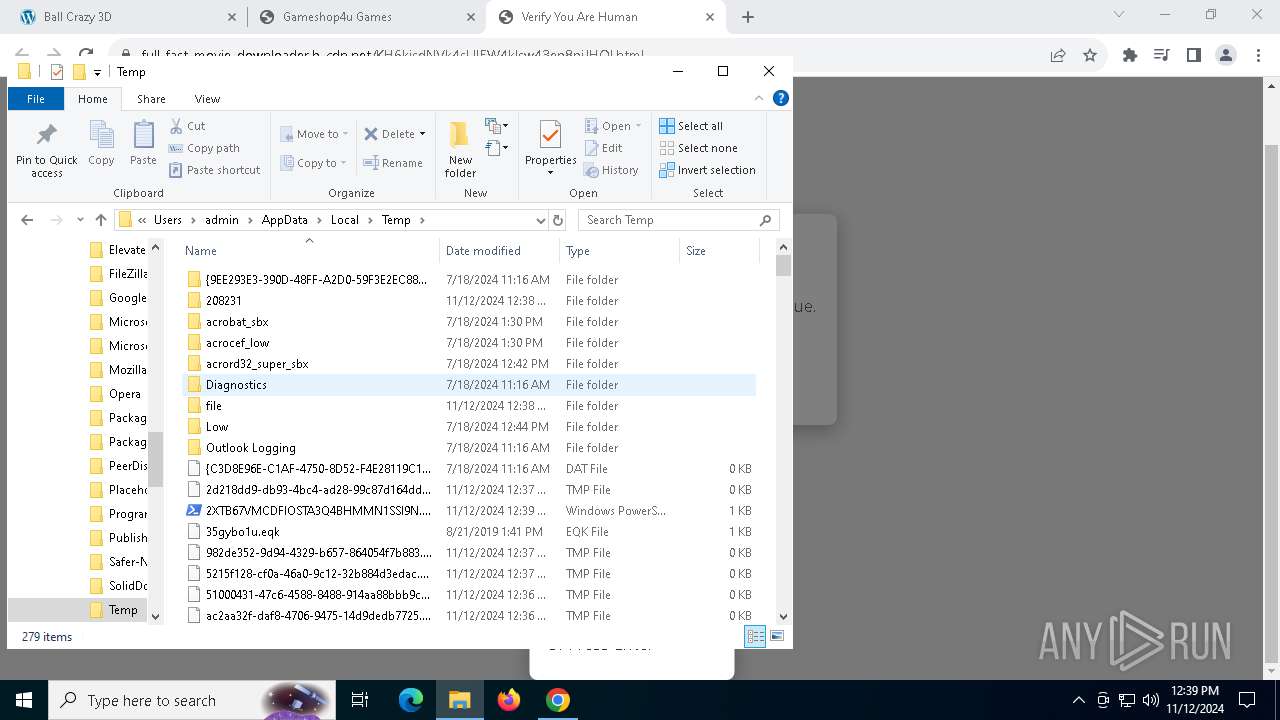
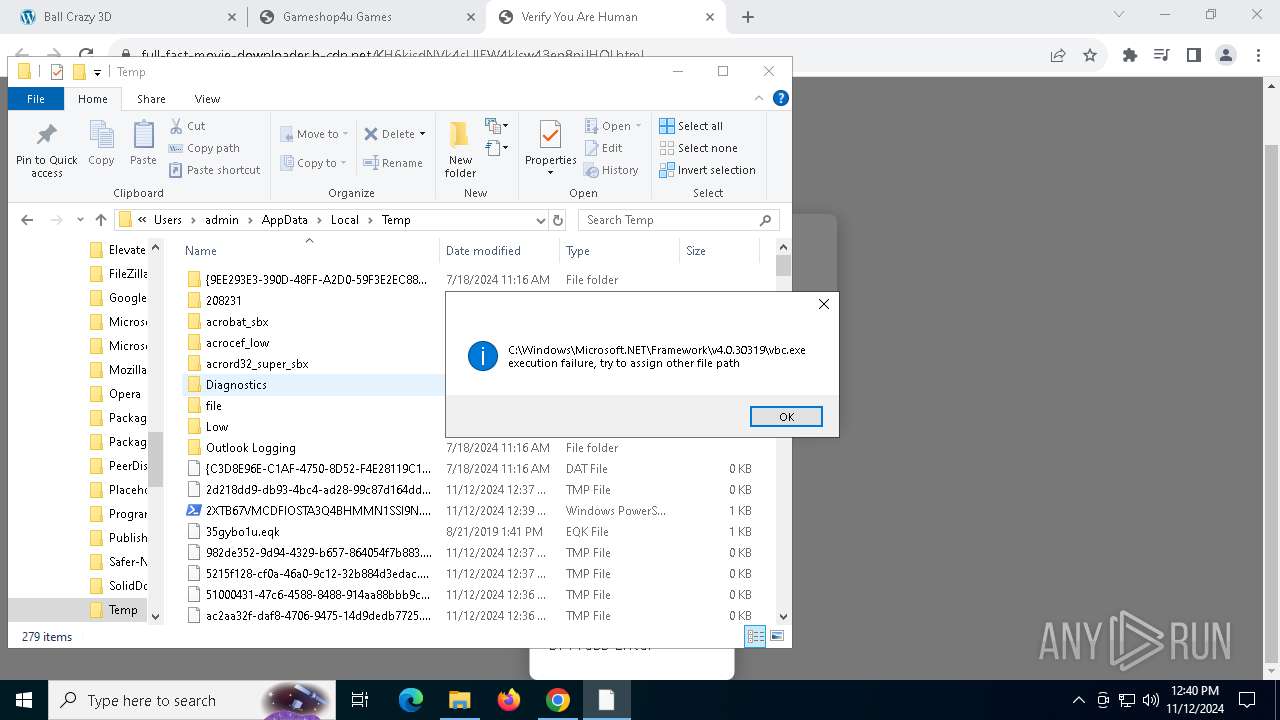
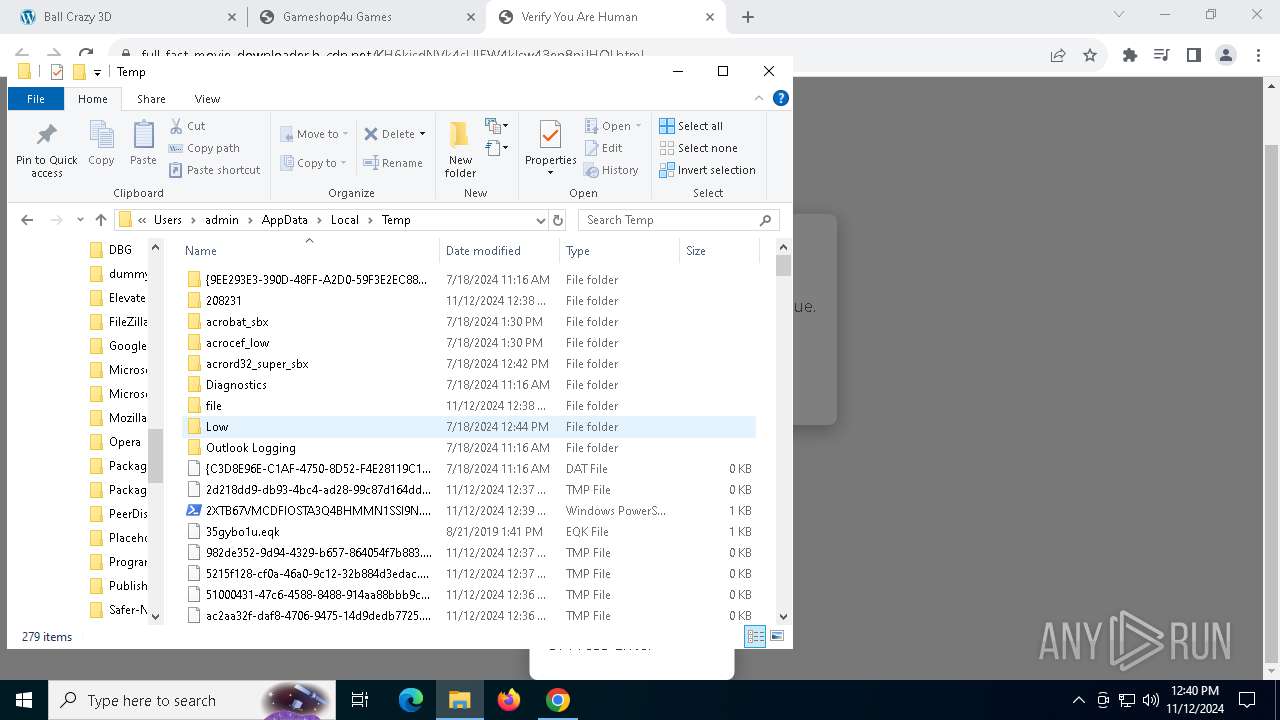
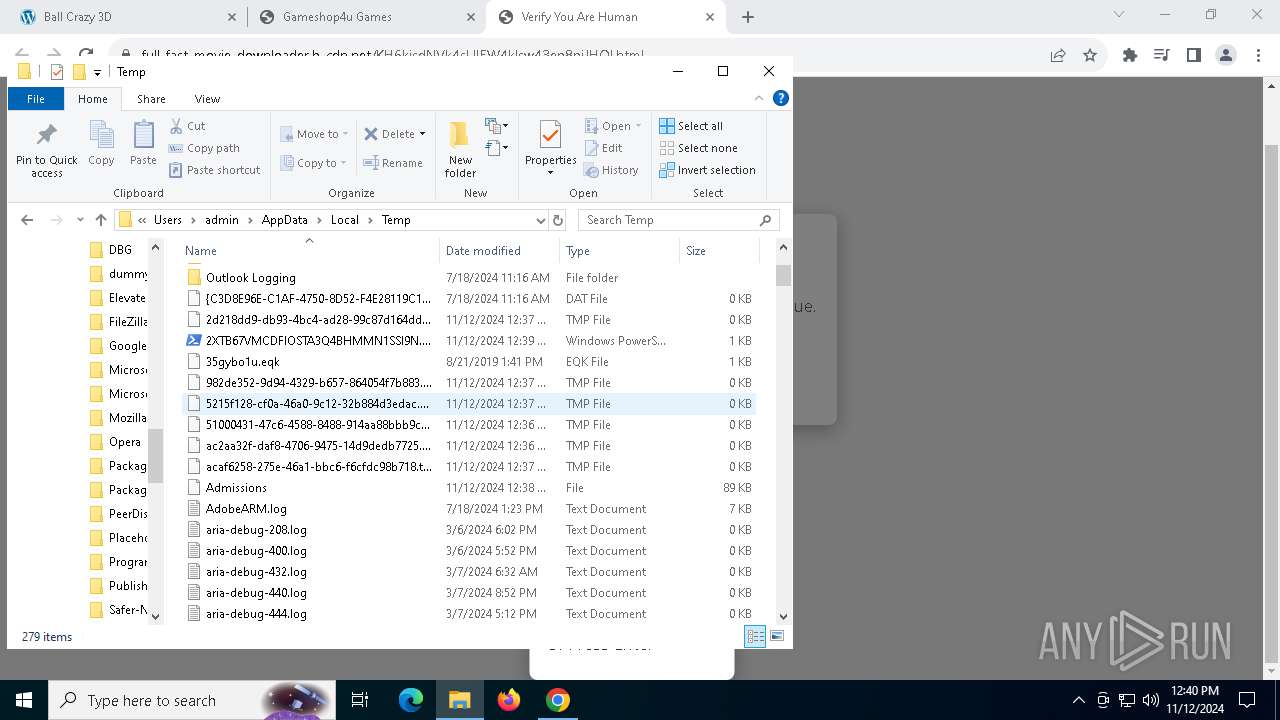
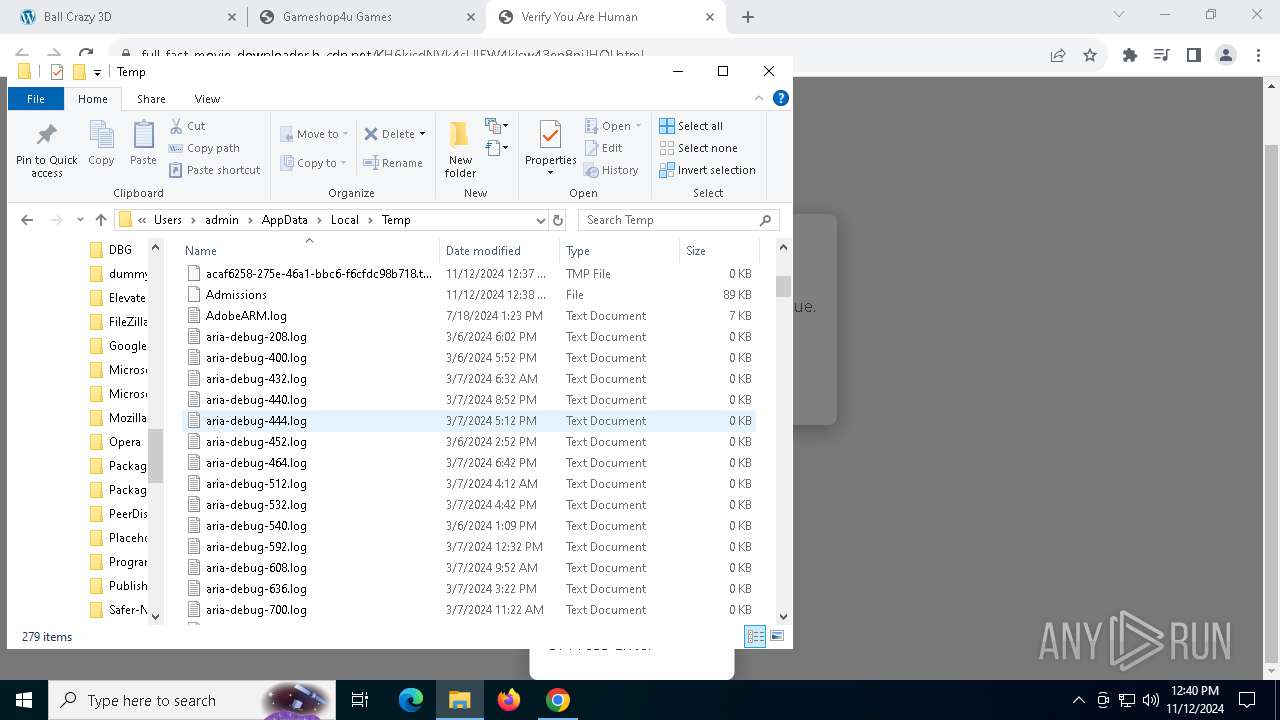
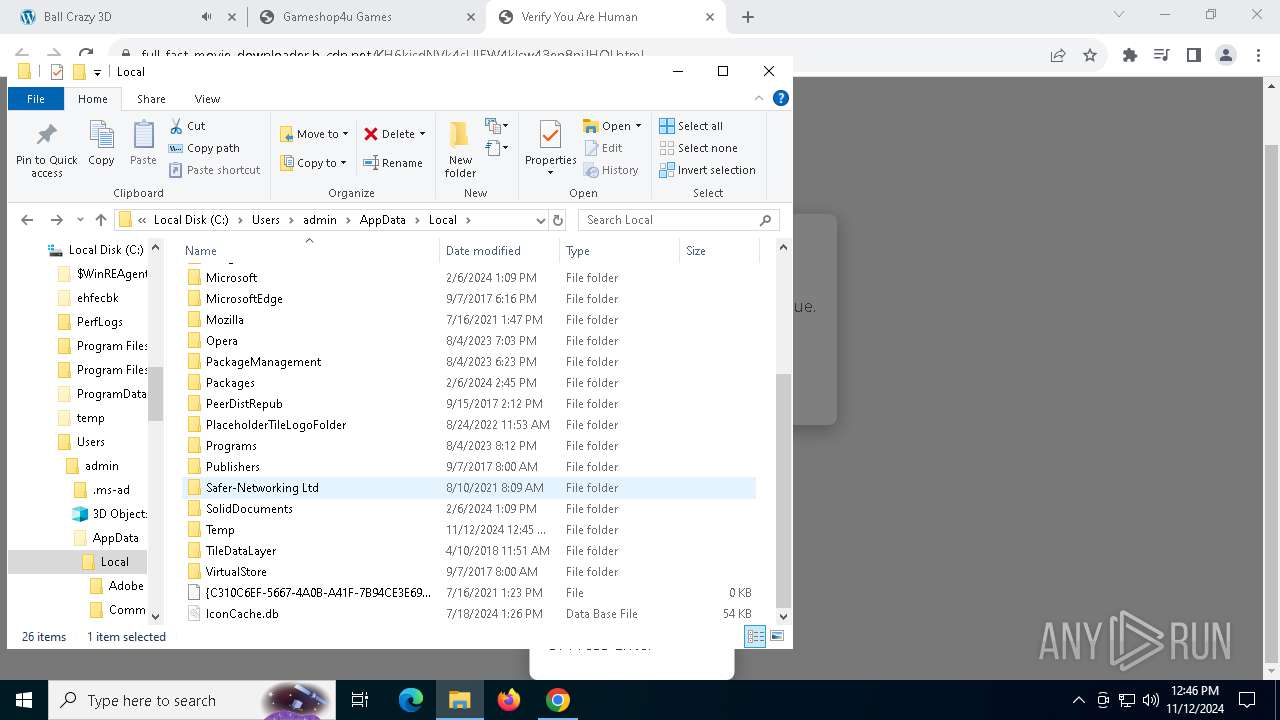
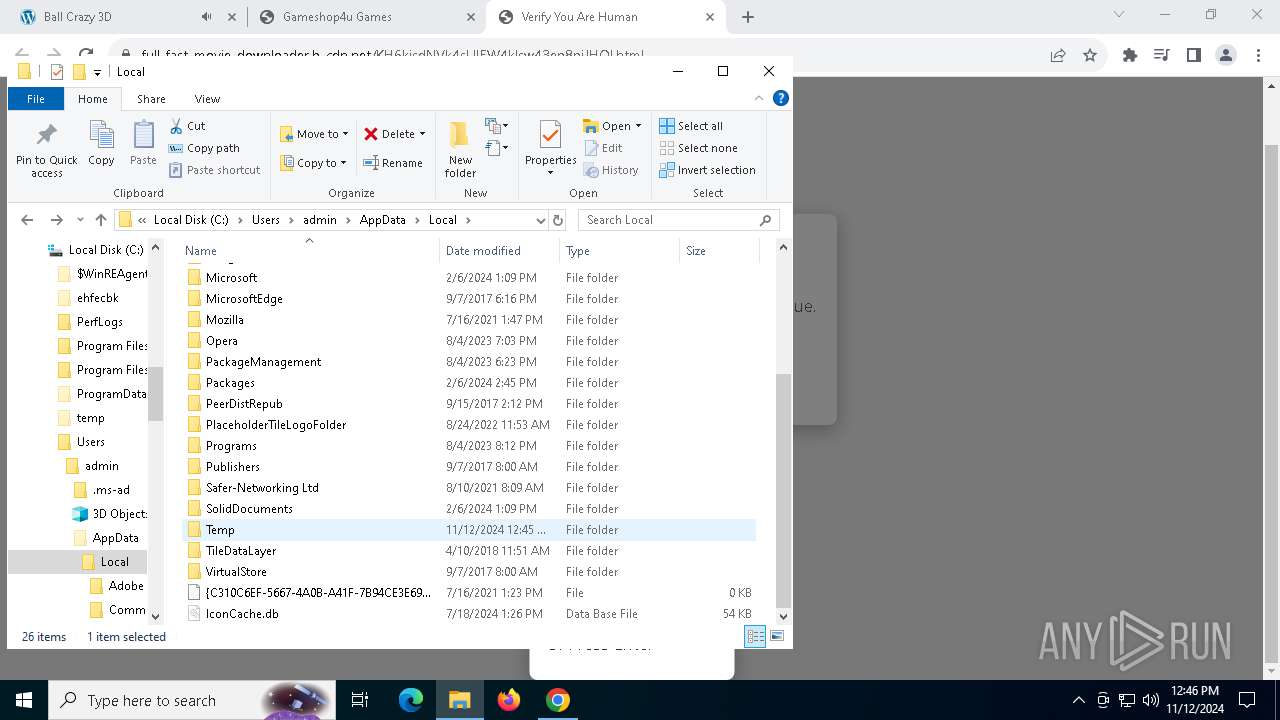
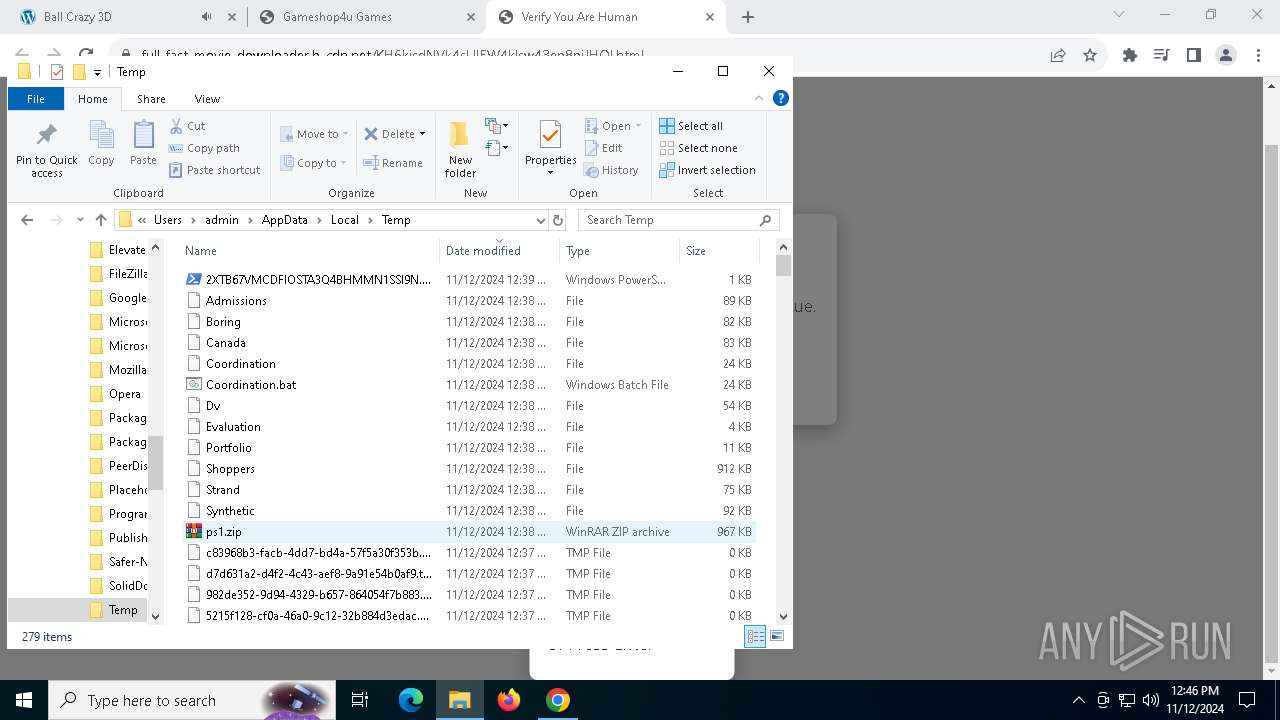
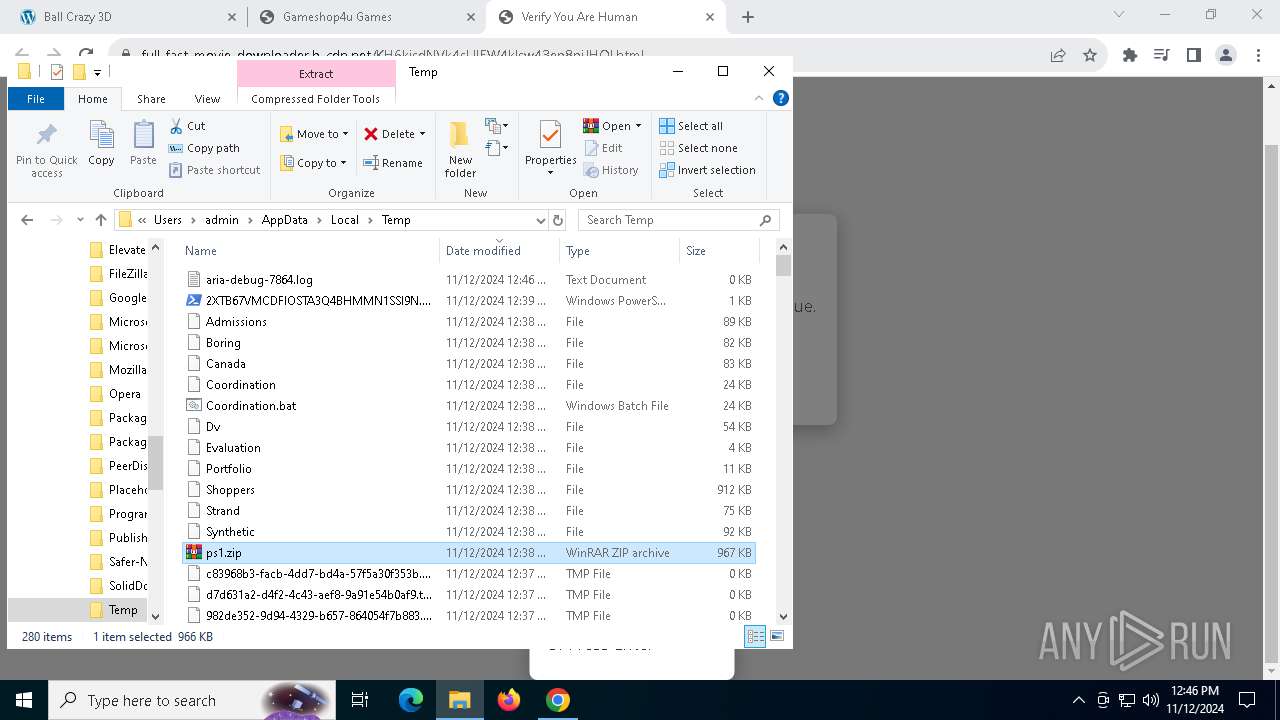
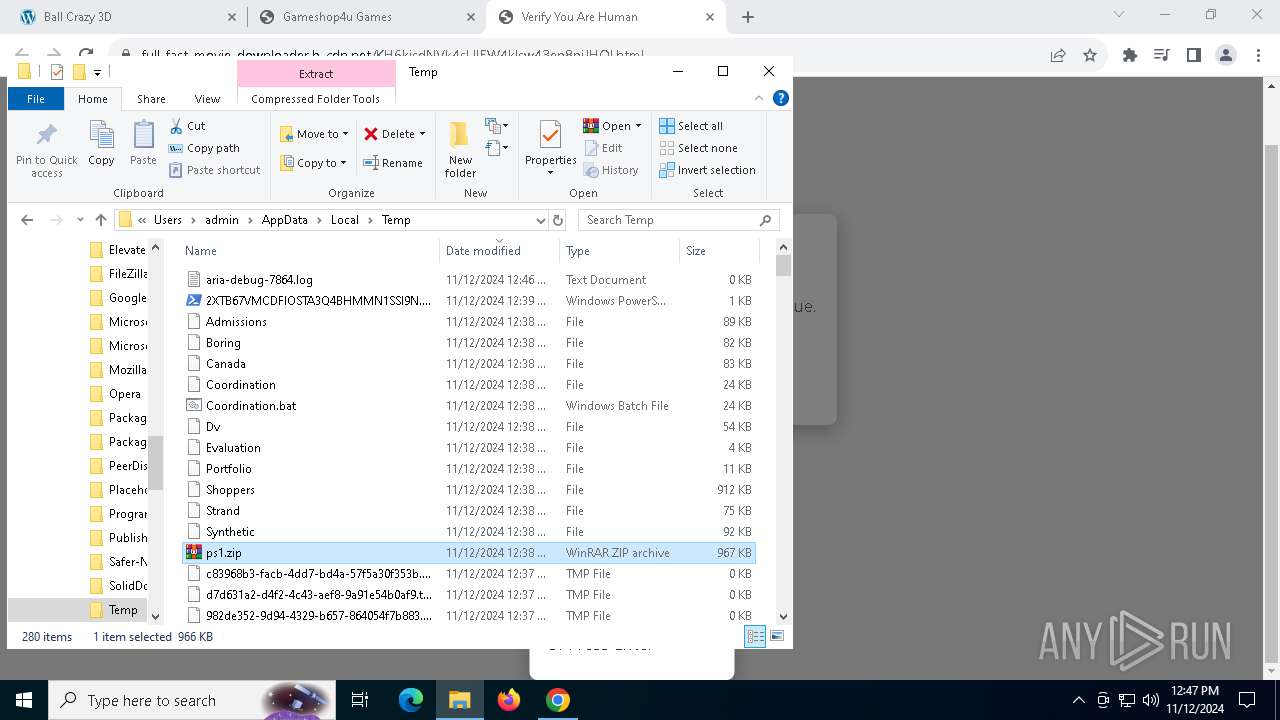
Create files in a temporary directory
- AccessoryLiberty.exe (PID: 7764)
Process checks computer location settings
- AccessoryLiberty.exe (PID: 7764)
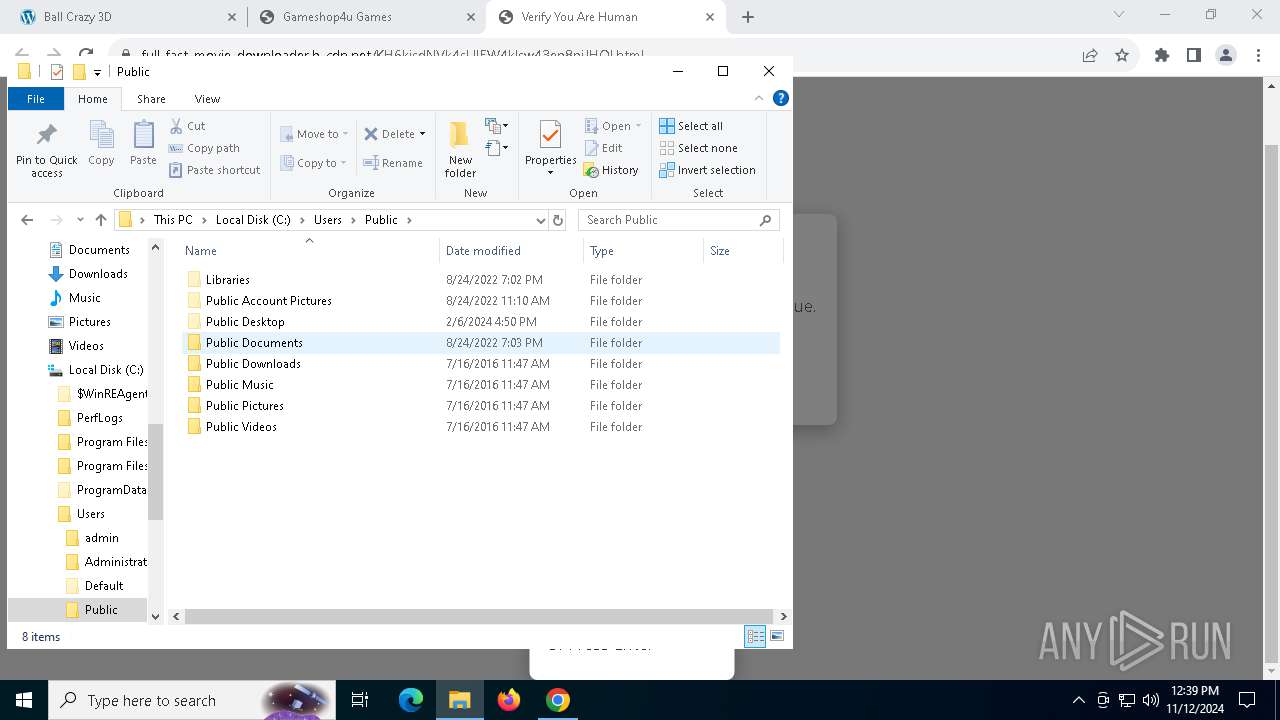
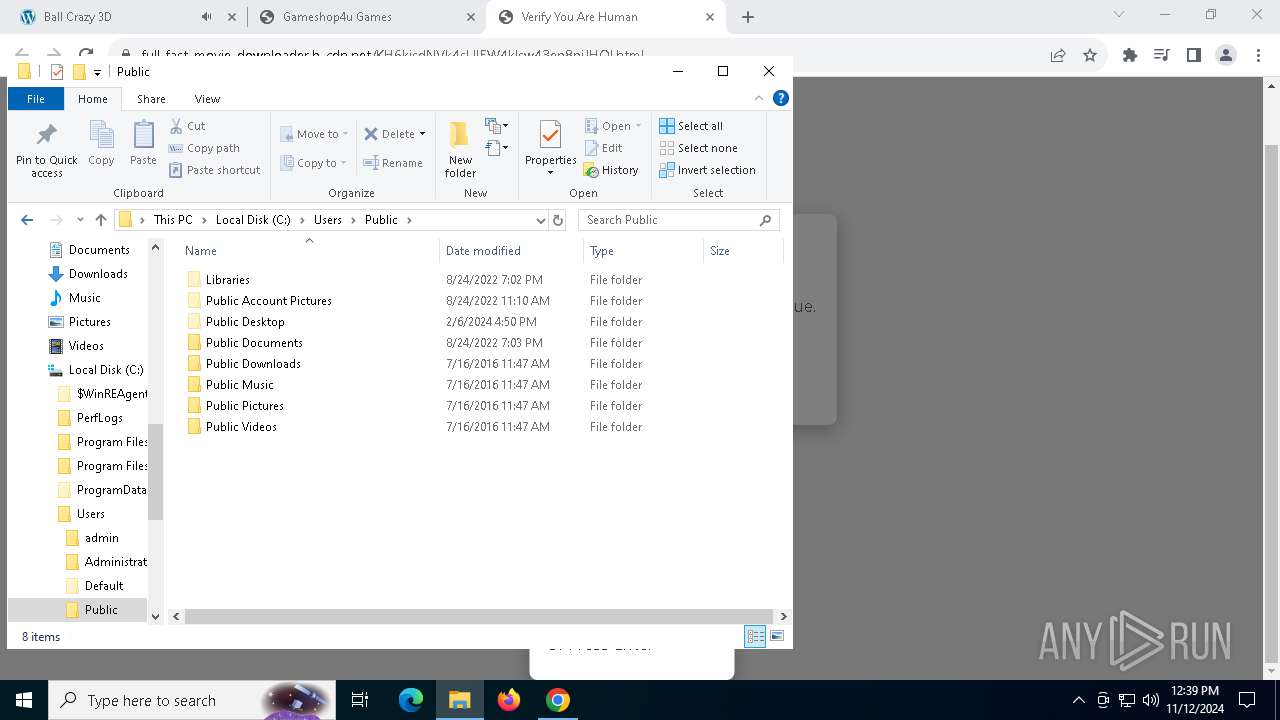
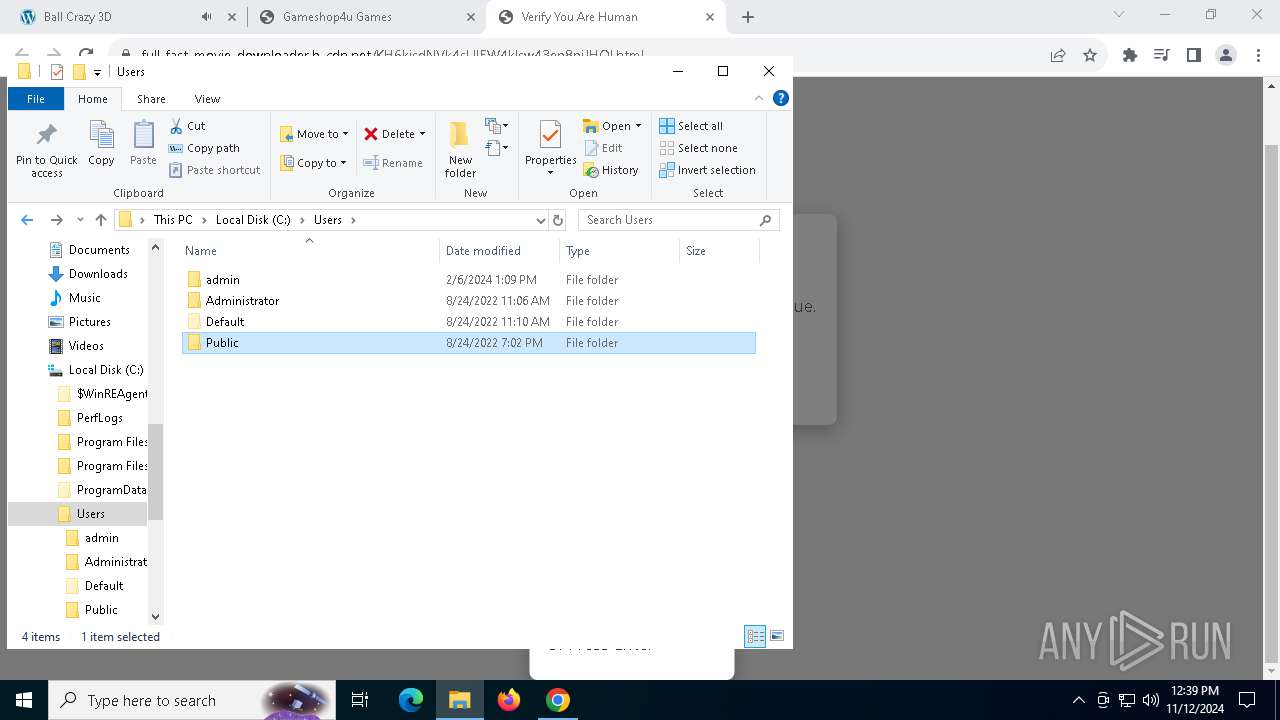
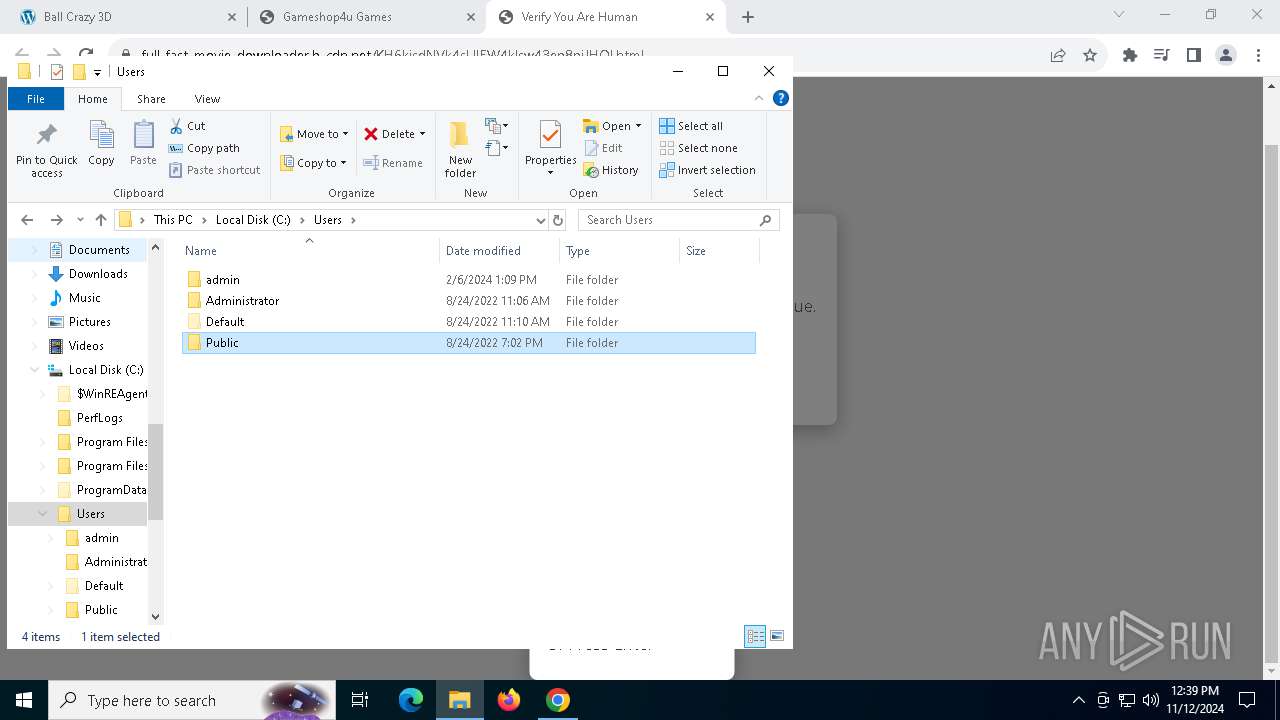
Creates a new folder
- cmd.exe (PID: 8040)
Reads the software policy settings
- War.pif (PID: 8104)
Reads mouse settings
- War.pif (PID: 8104)
Reads the machine GUID from the registry
- War.pif (PID: 8104)
Executable content was dropped or overwritten
- chrome.exe (PID: 7840)
Gets data length (POWERSHELL)
- powershell.exe (PID: 7960)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
239
Monitored processes
99
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 860 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\vbc.exe | C:\Windows\Microsoft.NET\Framework\v4.0.30319\vbc.exe | — | YIR4GD.pif | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 0 Version: 14.8.9037.0 Modules
| |||||||||||||||
| 1008 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=audio.mojom.AudioService --lang=en-US --service-sandbox-type=audio --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4764 --field-trial-handle=1844,i,3754803709958774791,7552877113219960587,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1336 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=21 --mojo-platform-channel-handle=4900 --field-trial-handle=1844,i,3754803709958774791,7552877113219960587,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
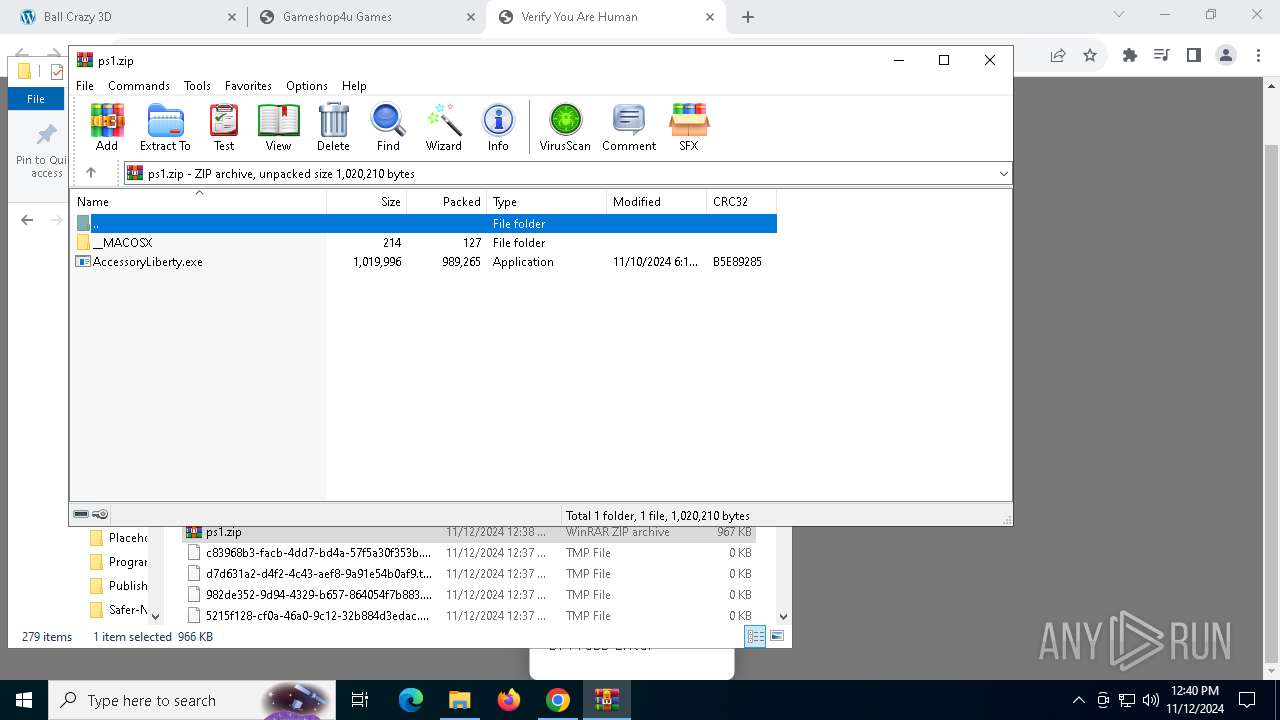
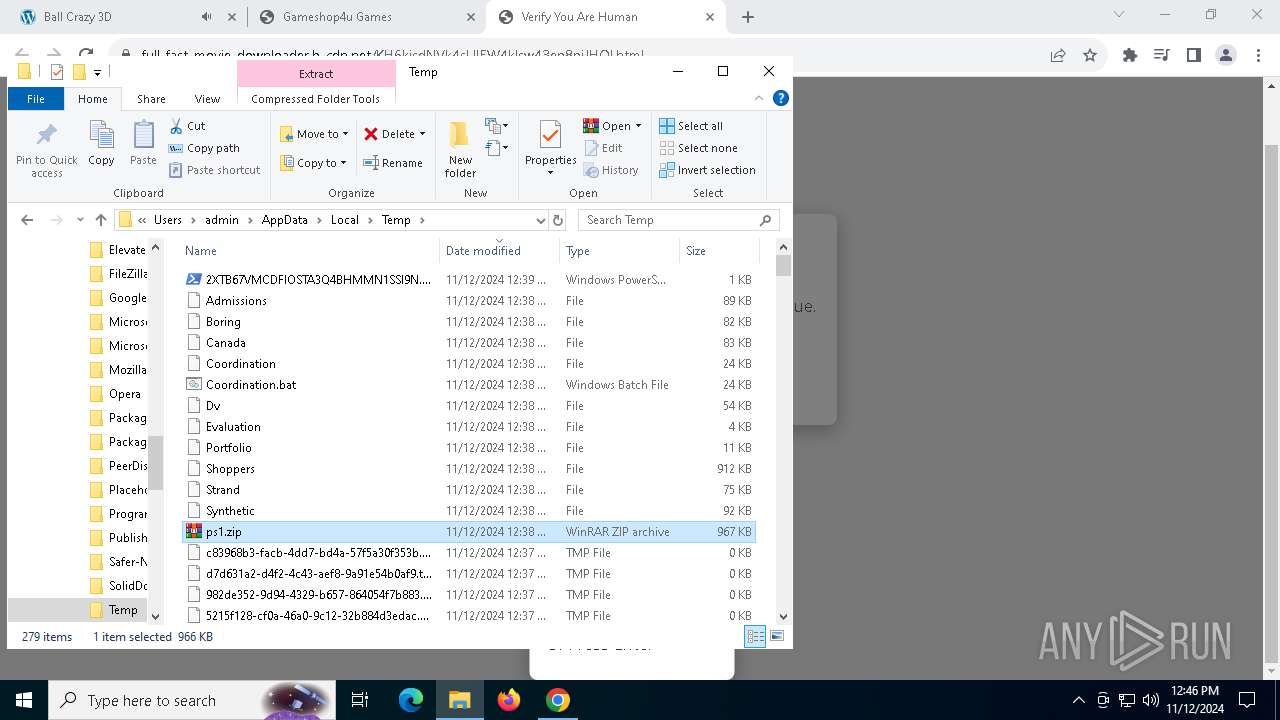
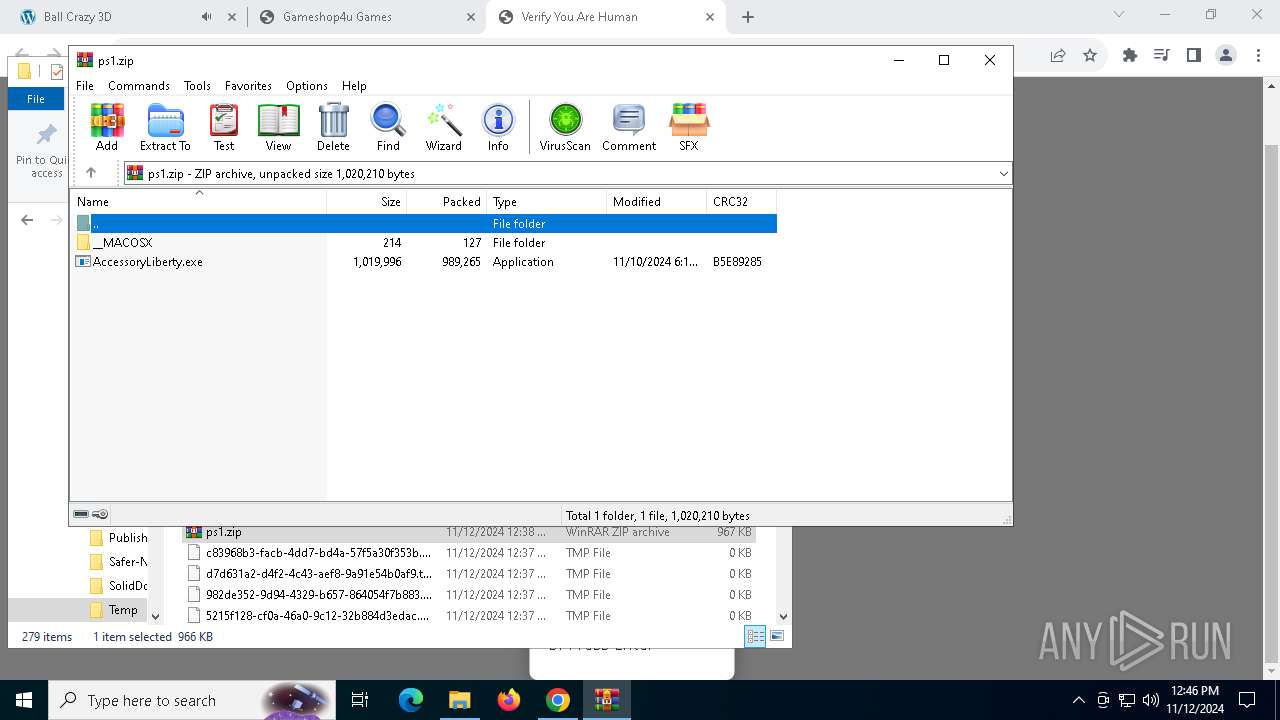
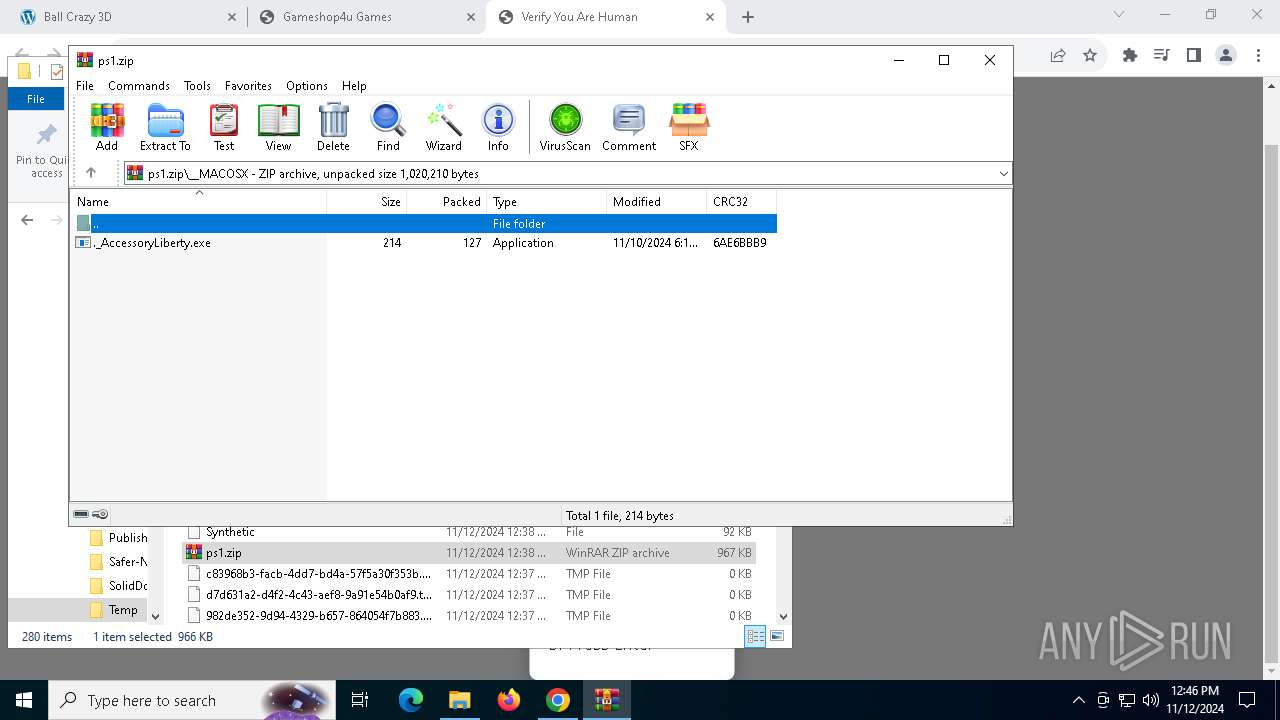
| 1376 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\ps1.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2128 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\ps1.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2420 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=13 --mojo-platform-channel-handle=5924 --field-trial-handle=1844,i,3754803709958774791,7552877113219960587,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2620 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgABAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=1840 --field-trial-handle=1844,i,3754803709958774791,7552877113219960587,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2780 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=14 --mojo-platform-channel-handle=6016 --field-trial-handle=1844,i,3754803709958774791,7552877113219960587,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 3848 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=3100 --field-trial-handle=1844,i,3754803709958774791,7552877113219960587,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 3848 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\vbc.exe | C:\Windows\Microsoft.NET\Framework\v4.0.30319\vbc.exe | — | YIR4GD.pif | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 0 Version: 14.8.9037.0 Modules
| |||||||||||||||
Total events
33 449
Read events
33 276
Write events
165
Delete events
8
Modification events
| (PID) Process: | (6664) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6664) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6664) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6664) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6664) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (6664) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C1I |
Value: 1 | |||
| (PID) Process: | (6664) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C2I |
Value: 1 | |||
| (PID) Process: | (6664) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C7I |
Value: 1 | |||
| (PID) Process: | (6664) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C1S |
Value: 1 | |||
| (PID) Process: | (6664) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C7S |
Value: 1 | |||
Executable files
5
Suspicious files
392
Text files
63
Unknown types
222
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6664 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF8d087.TMP | — | |
MD5:— | SHA256:— | |||
| 6664 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6664 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF8d097.TMP | — | |
MD5:— | SHA256:— | |||
| 6664 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF8d087.TMP | — | |
MD5:— | SHA256:— | |||
| 6664 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6664 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6664 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF8d097.TMP | — | |
MD5:— | SHA256:— | |||
| 6664 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6664 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF8d097.TMP | — | |
MD5:— | SHA256:— | |||
| 6664 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF8d0a7.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1 492
TCP/UDP connections
460
DNS requests
347
Threats
43
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | POST | 204 | 216.239.32.36:443 | https://region1.google-analytics.com/g/collect?v=2&tid=G-D8NNSFR7SN>m=45je4b70v9120641116za200&_p=1731414971028&gcd=13l3l3l2l1l1&npa=1&dma_cps=syphamo&dma=1&tag_exp=101823848~101925629~102077854&cid=570940001.1731414972&ul=en-us&sr=1280x720&uaa=x86&uab=64&uafvl=Chromium%3B122.0.6261.70%7CNot(A%253ABrand%3B24.0.0.0%7CGoogle%2520Chrome%3B122.0.6261.70&uamb=0&uam=&uap=Windows&uapv=10.0.0&uaw=0&frm=0&pscdl=noapi&_s=1&sid=1731414971&sct=1&seg=0&dl=https%3A%2F%2Fasd.quest%2F&dt=%D8%B9%D8%B1%D8%A8%20%D8%B3%D9%8A%D8%AF%20-%20ArabSeed%20%D9%85%D8%B4%D8%A7%D9%87%D8%AF%D9%87%20%D9%88%D8%AA%D8%AD%D9%85%D9%8A%D9%84%20%D8%A7%D9%84%D8%A7%D9%81%D9%84%D8%A7%D9%85%20%D9%88%D8%A7%D9%84%D9%85%D8%B3%D9%84%D8%B3%D9%84%D8%A7%D8%AA&en=page_view&_fv=1&_nsi=1&_ss=1&_ee=1&tfd=2535 | unknown | — | — | unknown |
— | — | GET | 200 | 188.114.97.3:443 | https://asd.quest/wp-content/themes/Elshaikh2021/UI/images/logo.webp | unknown | image | 5.38 Kb | unknown |
— | — | GET | 200 | 188.114.96.3:443 | https://asd.quest/ | unknown | html | 482 Kb | unknown |
— | — | GET | 200 | 188.114.97.3:443 | https://asd.quest/wp-content/themes/Elshaikh2021/UI/images/logo.webp | unknown | image | 5.38 Kb | unknown |
— | — | GET | 200 | 142.250.186.138:443 | https://content-autofill.googleapis.com/v1/pages/ChRDaHJvbWUvMTIyLjAuNjI2MS43MBIZCQ86QwGOK2w3EgUNvtSfsyEvaMEK5-qA9g==?alt=proto | unknown | text | 16 b | whitelisted |
— | — | GET | 200 | 188.114.96.3:443 | https://asd.quest/wp-content/themes/Elshaikh2021/style.css?ver=1.0 | unknown | text | 305 b | unknown |
— | — | GET | 200 | 142.250.185.138:443 | https://fonts.googleapis.com/css2?family=Righteous&display=swap | unknown | text | 851 b | whitelisted |
— | — | GET | 200 | 104.17.246.203:443 | https://unpkg.com/sweetalert2@9.17.4/dist/sweetalert2.all.min.js | unknown | binary | 66.0 Kb | whitelisted |
— | — | GET | 200 | 188.114.97.3:443 | https://asd.quest/wp-content/themes/Elshaikh2021/UI/fonts/Bahij_TheSansArabic-Bold.woff2 | unknown | binary | 58.7 Kb | unknown |
— | — | GET | 200 | 104.18.40.68:443 | https://kit-pro.fontawesome.com/releases/v5.13.0/css/pro.min.css | unknown | text | 302 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 2.16.204.138:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
6944 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2660 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5488 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.16.204.148:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6820 | chrome.exe | 172.67.187.191:443 | arabseed.show | CLOUDFLARENET | US | unknown |
6664 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6820 | chrome.exe | 74.125.143.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
arabseed.show |
| unknown |
accounts.google.com |
| whitelisted |
asd.quest |
| unknown |
fonts.googleapis.com |
| whitelisted |
unpkg.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
kit-pro.fontawesome.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6820 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Global content delivery network (unpkg .com) |
6820 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Global content delivery network (unpkg .com) |
6820 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
6820 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
6820 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
6820 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
6820 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
11 ETPRO signatures available at the full report