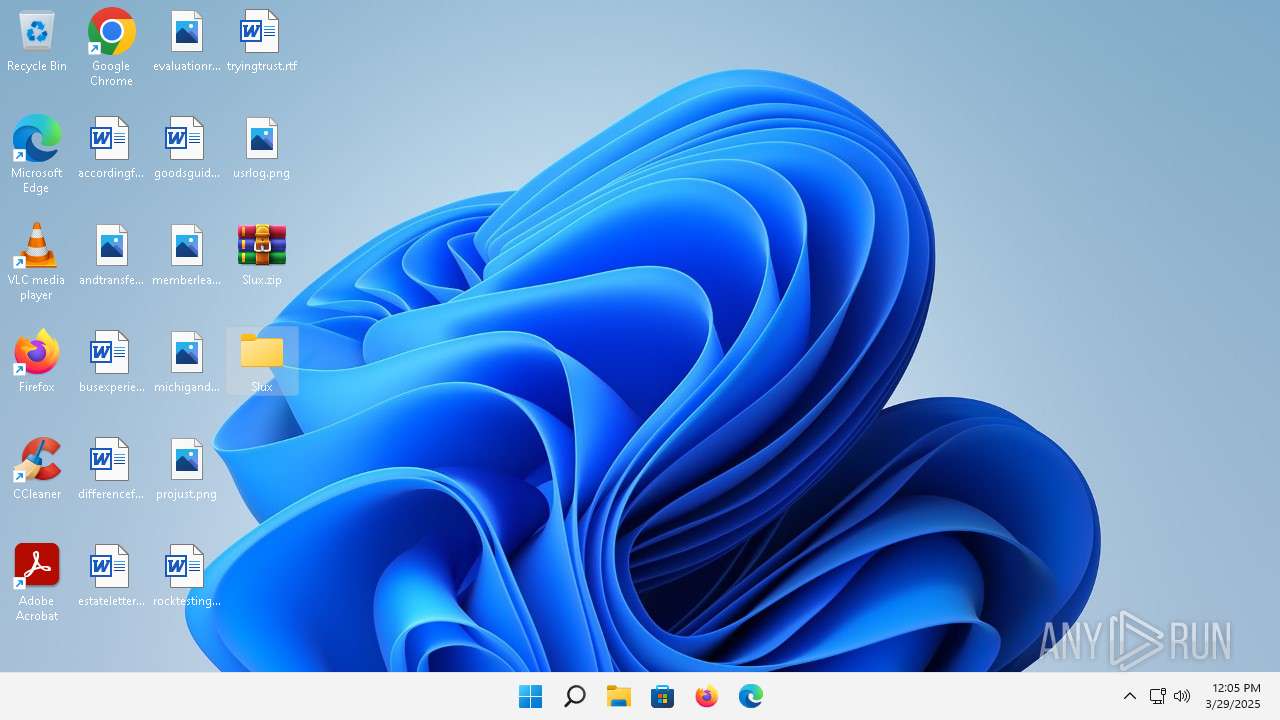
| File name: | Slux.zip |
| Full analysis: | https://app.any.run/tasks/5ee3028d-46bb-4f9f-a09a-60243f7f3a7f |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | March 29, 2025, 12:04:04 |
| OS: | Windows 11 Professional (build: 22000, 64 bit) |
| Tags: | |
| Indicators: | |
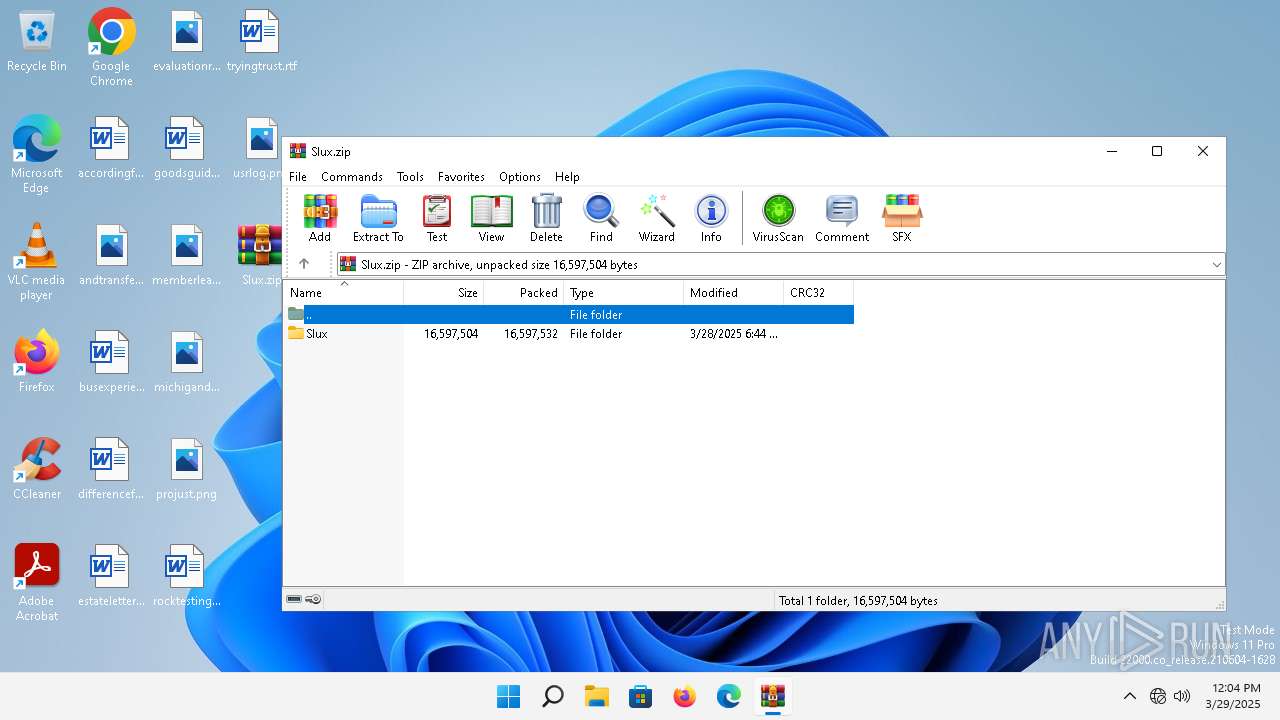
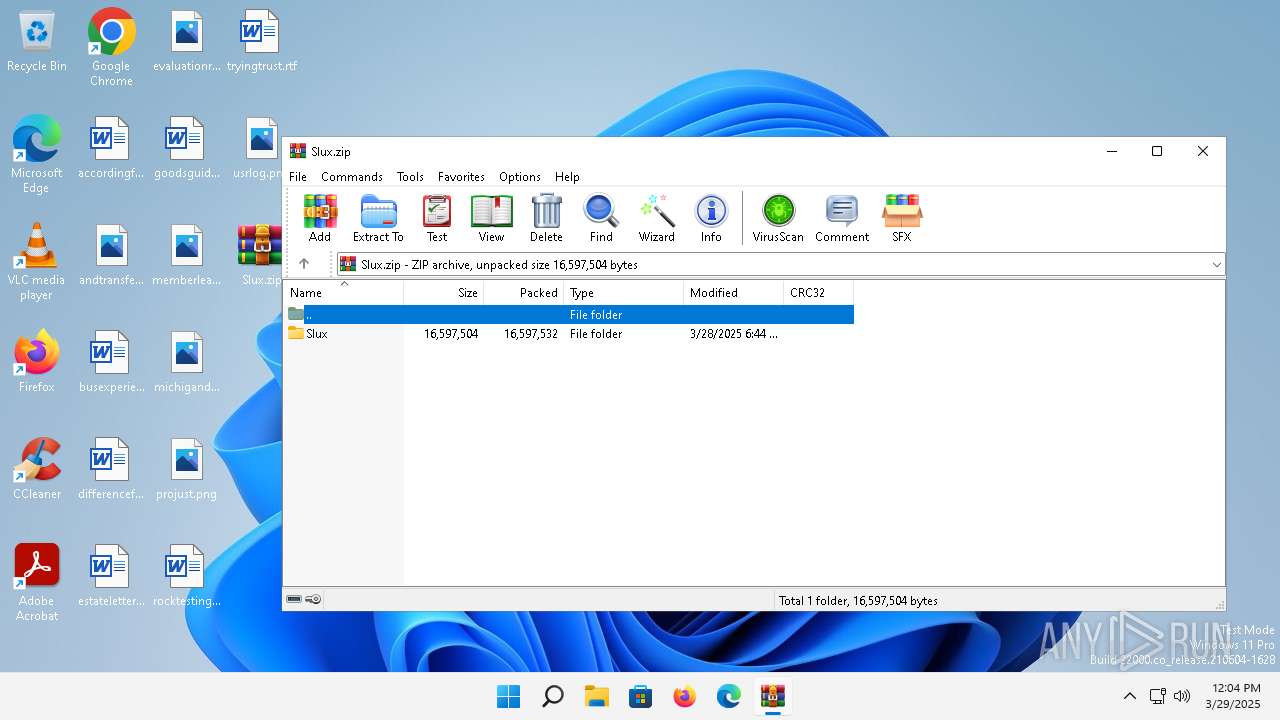
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | 0B3C1B679A431959341644360A6BB84E |
| SHA1: | A965FDD77B65F2B60C64094C6B6CBD48CE170CCC |
| SHA256: | A0E0B39FEDF51CBF9D4E38E74AF03E9F840422A7C3A321CA193C94EE8F9C3A37 |
| SSDEEP: | 98304:z3Hb61XMMhE9gwwNN6/nwzF2BuP1816SAR9QbcWS3DpvTWQ8Q6rrfhOgR36Mgoi6:lqgGN+aoou/LtyBFeZbZuU5/FOWF |
MALICIOUS
LUMMA mutex has been found
- MSBuild.exe (PID: 2580)
Actions looks like stealing of personal data
- MSBuild.exe (PID: 2580)
SUSPICIOUS
Reads the Internet Settings
- MSBuild.exe (PID: 2580)
Reads settings of System Certificates
- MSBuild.exe (PID: 2580)
Searches for installed software
- MSBuild.exe (PID: 2580)
INFO
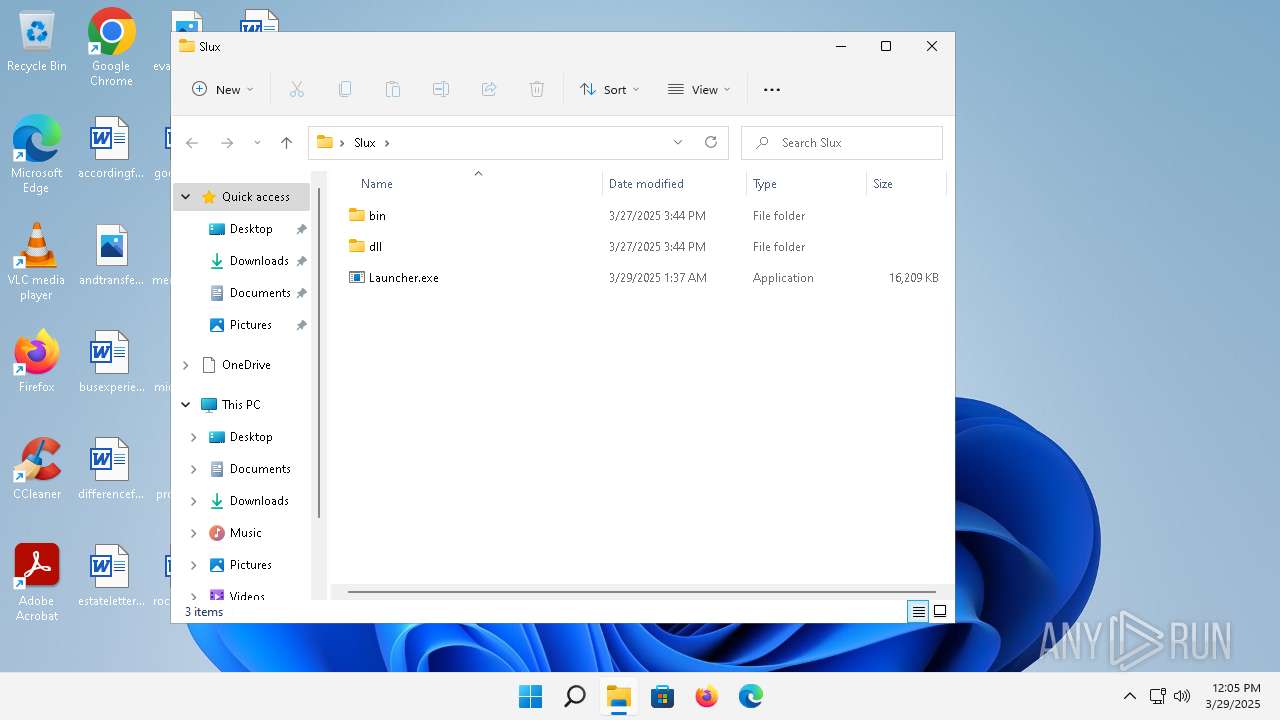
Manual execution by a user
- Launcher.exe (PID: 2328)
Executable content was dropped or overwritten
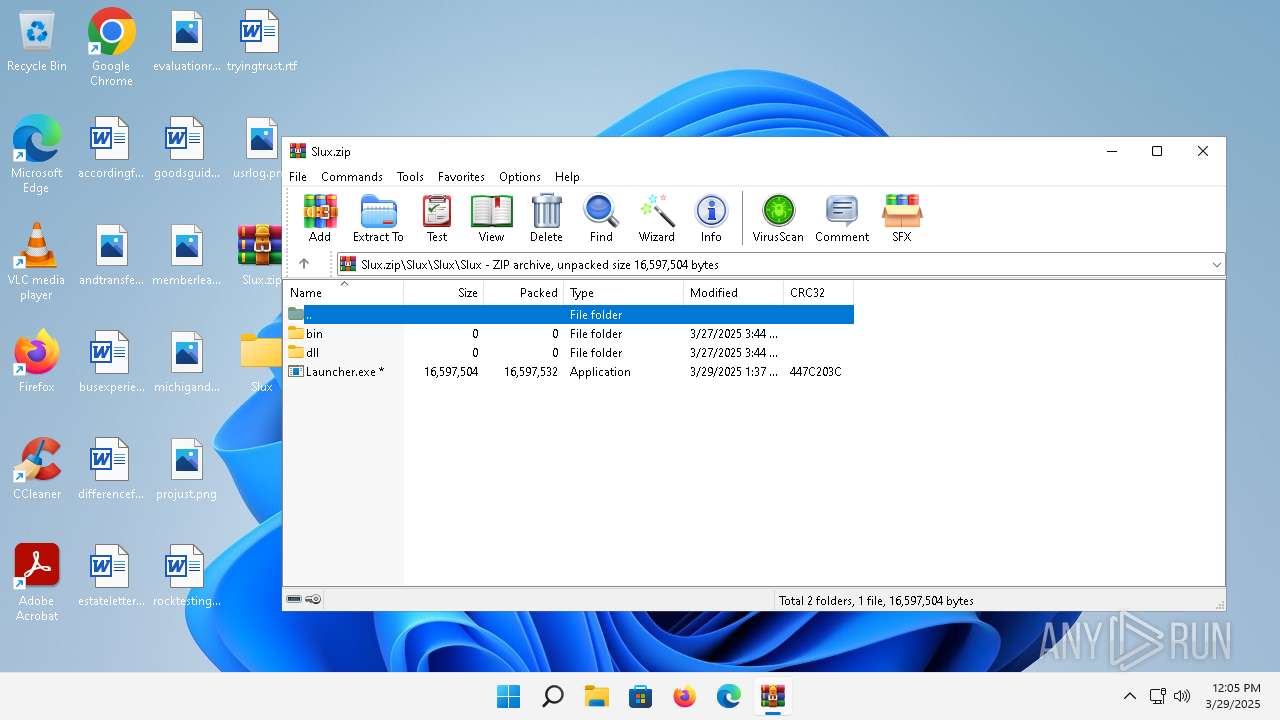
- WinRAR.exe (PID: 1160)
Checks supported languages
- MSBuild.exe (PID: 2580)
- Launcher.exe (PID: 2328)
Reads the machine GUID from the registry
- MSBuild.exe (PID: 2580)
Reads the software policy settings
- MSBuild.exe (PID: 2580)
Reads the computer name
- MSBuild.exe (PID: 2580)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2025:03:28 23:44:38 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | Slux/ |
Total processes
104
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
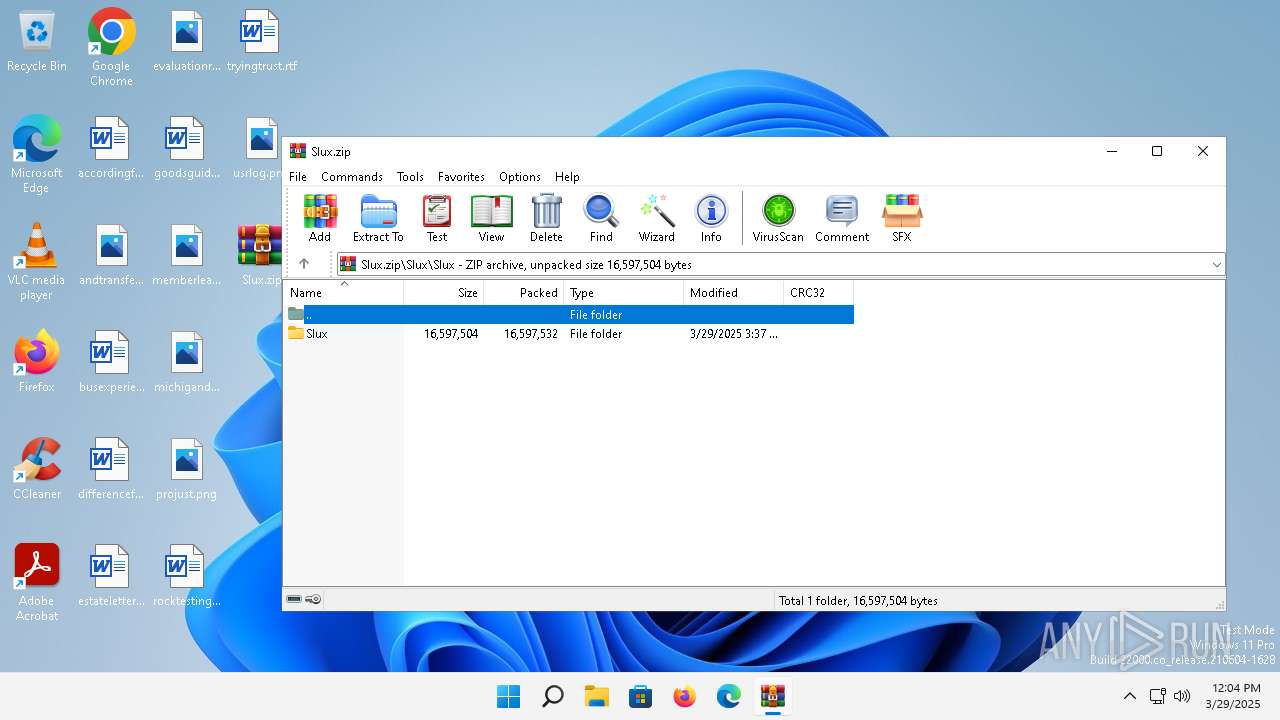
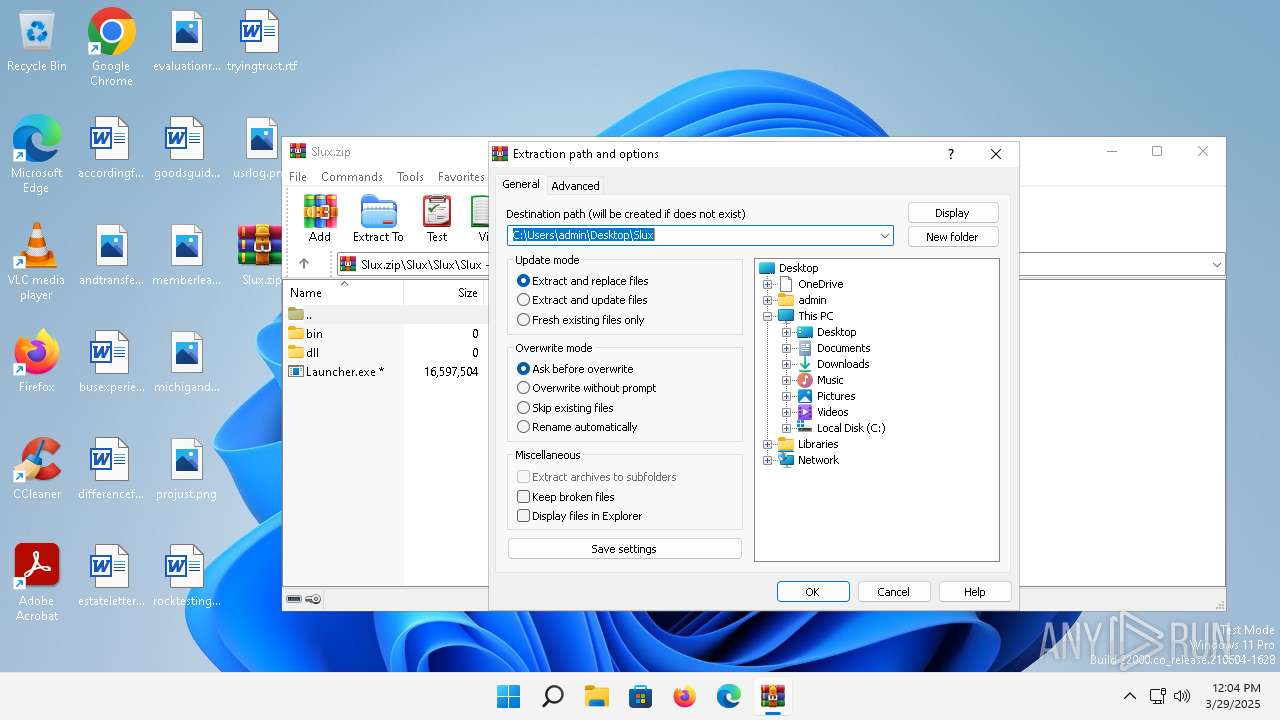
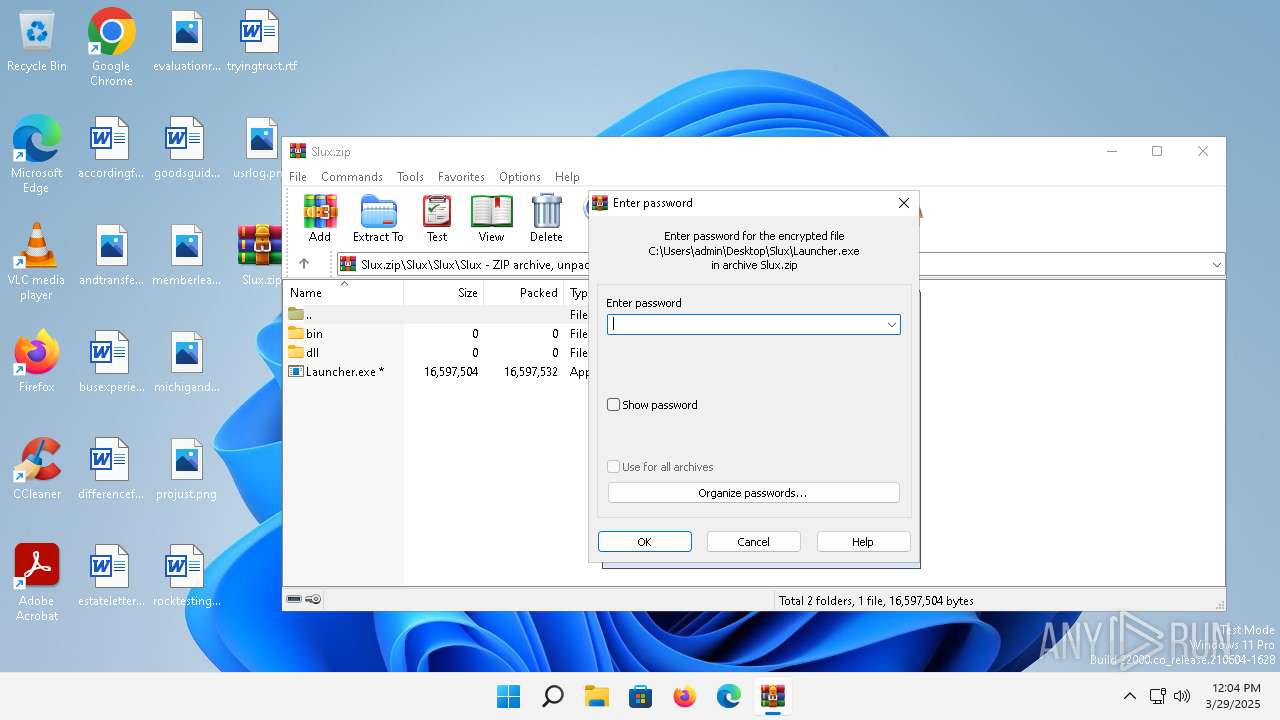
| 1160 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\Slux.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 1664 | C:\Windows\system32\svchost.exe -k NetworkService -p | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2328 | "C:\Users\admin\Desktop\Slux\Launcher.exe" | C:\Users\admin\Desktop\Slux\Launcher.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2460 | C:\Windows\System32\rundll32.exe C:\Windows\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2580 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe | Launcher.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: MSBuild.exe Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
Total events
5 637
Read events
5 615
Write events
22
Delete events
0
Modification events
| (PID) Process: | (1160) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (1160) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (1160) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\Slux.zip | |||
| (PID) Process: | (1160) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1160) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1160) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1160) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1160) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1160) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1160) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\Slux | |||
Executable files
1
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1160 | WinRAR.exe | C:\Users\admin\Desktop\Slux\Launcher.exe | executable | |
MD5:EF53A665B3D514C09D6D0095235D09EC | SHA256:402505D1F0BDC1706A8E7D510DFC68EFF23EE9BE8EAC9C536E3EE9EB71D0F880 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
34
DNS requests
16
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3828 | smartscreen.exe | GET | 404 | 199.232.210.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?61f822f41d565017 | unknown | — | — | whitelisted |
4976 | MoUsoCoreWorker.exe | GET | 404 | 199.232.214.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?2f7672412b4877c2 | unknown | — | — | whitelisted |
1352 | svchost.exe | GET | 404 | 2.18.64.212:80 | http://www.msftconnecttest.com/connecttest.txt | unknown | — | — | whitelisted |
1352 | svchost.exe | GET | 404 | 2.18.64.200:80 | http://www.msftconnecttest.com/connecttest.txt | unknown | — | — | whitelisted |
1352 | svchost.exe | GET | 404 | 2.18.64.200:80 | http://www.msftconnecttest.com/connecttest.txt | unknown | — | — | whitelisted |
2776 | svchost.exe | GET | 404 | 199.232.214.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?0f36b052feee4f5a | unknown | — | — | whitelisted |
1352 | svchost.exe | GET | 404 | 2.18.64.212:80 | http://www.msftconnecttest.com/connecttest.txt | unknown | — | — | whitelisted |
3640 | svchost.exe | GET | 404 | 199.232.214.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?c6613fd91ef18acd | unknown | — | — | whitelisted |
2776 | svchost.exe | GET | 404 | 199.232.214.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?080b14bcaa268812 | unknown | — | — | whitelisted |
2768 | svchost.exe | GET | 404 | 199.232.214.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?7201ae0c09ebf73e | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1352 | svchost.exe | 2.18.64.200:80 | www.msftconnecttest.com | Administracion Nacional de Telecomunicaciones | UY | whitelisted |
3828 | smartscreen.exe | 98.64.238.3:443 | checkappexec.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3828 | smartscreen.exe | 199.232.210.172:80 | ctldl.windowsupdate.com | FASTLY | US | whitelisted |
4976 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4976 | MoUsoCoreWorker.exe | 199.232.214.172:80 | ctldl.windowsupdate.com | FASTLY | US | whitelisted |
3640 | svchost.exe | 40.126.31.1:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3640 | svchost.exe | 199.232.214.172:80 | ctldl.windowsupdate.com | FASTLY | US | whitelisted |
2776 | svchost.exe | 20.42.73.25:443 | v10.events.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2776 | svchost.exe | 199.232.214.172:80 | ctldl.windowsupdate.com | FASTLY | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
checkappexec.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
v10.events.data.microsoft.com |
| whitelisted |
www.msftconnecttest.com |
| whitelisted |
dns.msftncsi.com |
| whitelisted |
fs.microsoft.com |
| whitelisted |
wxayfarer.live |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Generic Protocol Command Decode | SURICATA HTTP Request unrecognized authorization method |
1352 | svchost.exe | Misc activity | ET INFO Microsoft Connection Test |
1352 | svchost.exe | Misc activity | ET INFO Microsoft Connection Test |
1352 | svchost.exe | Misc activity | ET INFO Microsoft Connection Test |
1352 | svchost.exe | Misc activity | ET INFO Microsoft Connection Test |
1352 | svchost.exe | Misc activity | ET INFO Microsoft Connection Test |
1352 | svchost.exe | Misc activity | ET INFO Microsoft Connection Test |