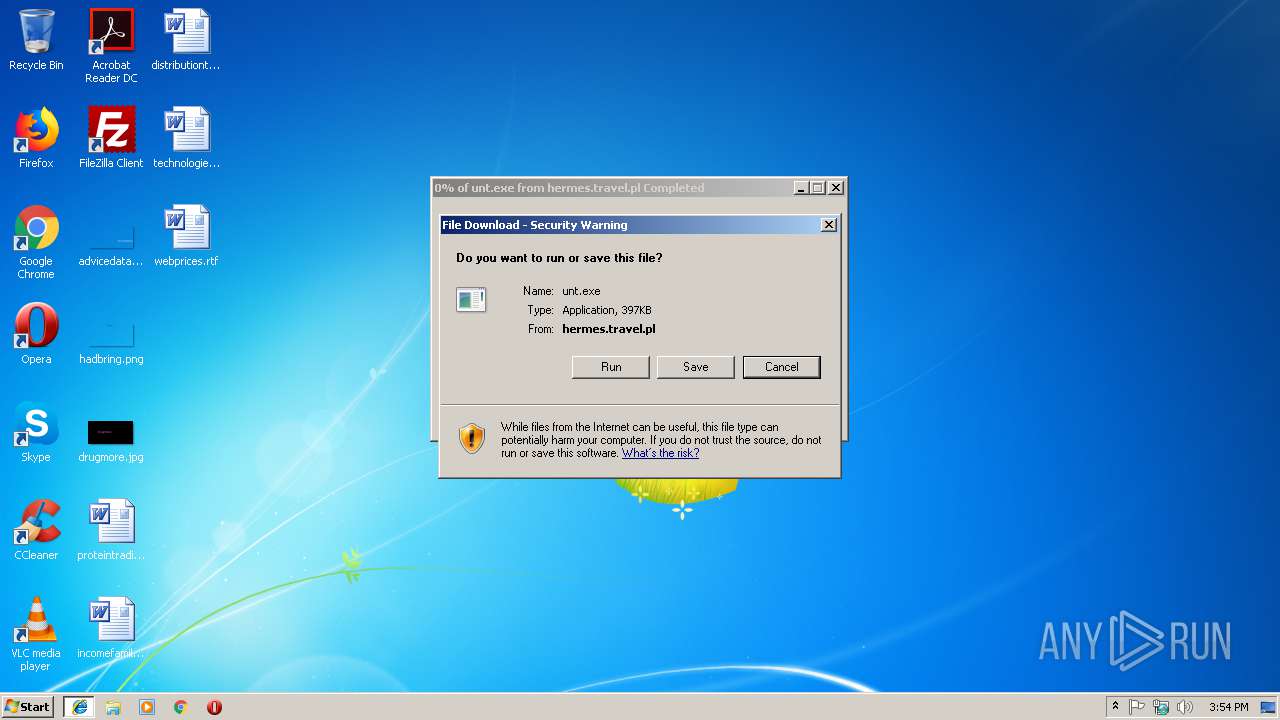
| URL: | http://hermes.travel.pl/unt.exe |
| Full analysis: | https://app.any.run/tasks/df688e07-2565-48bc-afa9-75ededaae45d |
| Verdict: | Malicious activity |
| Threats: | AZORult can steal banking information, including passwords and credit card details, as well as cryptocurrency. This constantly updated information stealer malware should not be taken lightly, as it continues to be an active threat. |
| Analysis date: | November 15, 2018, 15:53:51 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | FD436B70834E47D1F4F31D4C75DE0AF7 |
| SHA1: | 35C5894A29CF1DA9B783691B634394C4699E67F4 |
| SHA256: | A0CF67CE26CFAEBA33B7FEB0BBDDE71212A313505F7AD62001DDBE23302B473F |
| SSDEEP: | 3:N1KWAYnRKAJh5mC:CWjRb9 |
MALICIOUS
Application was dropped or rewritten from another process
- unt[1].exe (PID: 2880)
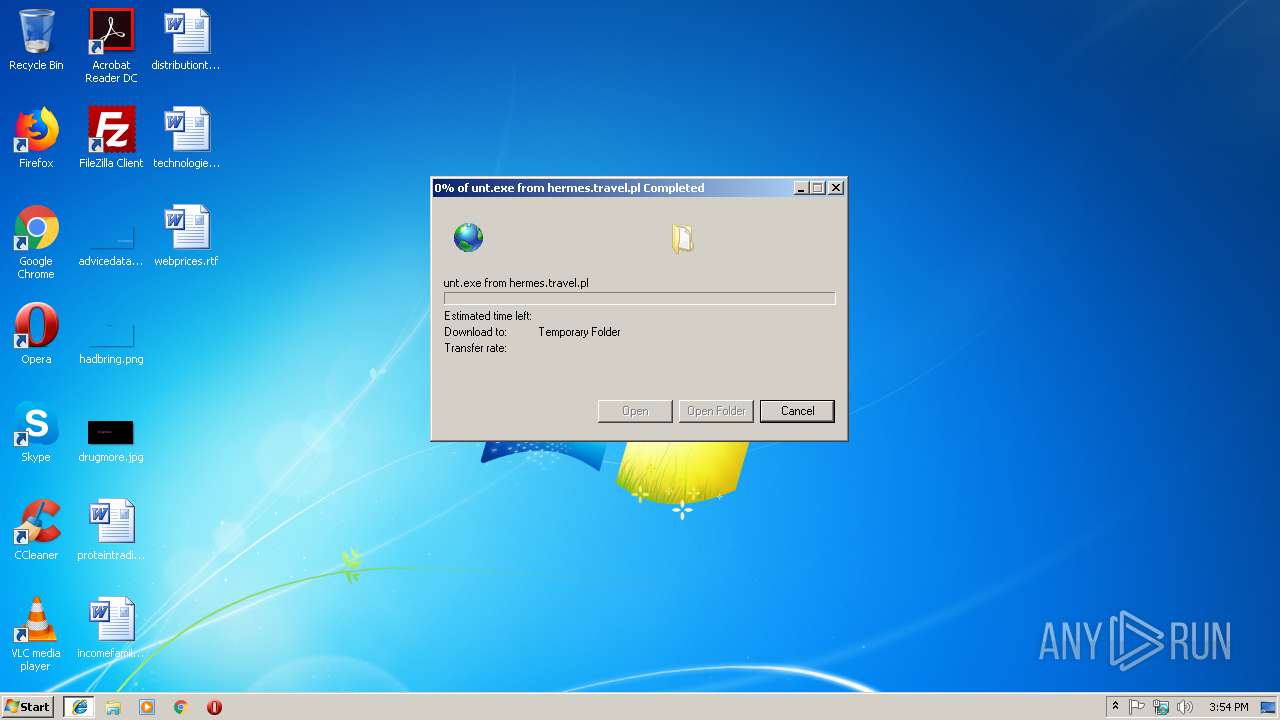
Downloads executable files from the Internet
- iexplore.exe (PID: 3168)
AZORULT was detected
- unt[1].exe (PID: 2880)
Connects to CnC server
- unt[1].exe (PID: 2880)
Actions looks like stealing of personal data
- unt[1].exe (PID: 2880)
Loads dropped or rewritten executable
- unt[1].exe (PID: 2880)
SUSPICIOUS
Executable content was dropped or overwritten
- iexplore.exe (PID: 3168)
- iexplore.exe (PID: 2928)
- unt[1].exe (PID: 2880)
Reads the cookies of Google Chrome
- unt[1].exe (PID: 2880)
Reads the cookies of Mozilla Firefox
- unt[1].exe (PID: 2880)
Starts CMD.EXE for commands execution
- unt[1].exe (PID: 2880)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 3168)
- iexplore.exe (PID: 2928)
Application launched itself
- iexplore.exe (PID: 2928)
Creates files in the user directory
- iexplore.exe (PID: 3168)
- iexplore.exe (PID: 2928)
- WINWORD.EXE (PID: 2160)
Changes internet zones settings
- iexplore.exe (PID: 2928)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2160)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
40
Monitored processes
6
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2160 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\webprices.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2880 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\unt[1].exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\unt[1].exe | iexplore.exe | ||||||||||||
User: admin Company: Intellias Women Integrity Level: MEDIUM Description: Richdollar Exit code: 0 Version: 13.8.65.88 Modules
| |||||||||||||||
| 2928 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2968 | "C:\Windows\system32\cmd.exe" /c C:\Windows\system32\timeout.exe 3 & del "unt[1].exe" | C:\Windows\system32\cmd.exe | — | unt[1].exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3168 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2928 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3764 | C:\Windows\system32\timeout.exe 3 | C:\Windows\system32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 555
Read events
1 152
Write events
392
Delete events
11
Modification events
| (PID) Process: | (2928) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2928) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2928) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2928) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2928) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2928) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2928) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {AEE181BB-E8EE-11E8-A67C-5254004AAD11} |
Value: 0 | |||
| (PID) Process: | (2928) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2928) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 3 | |||
| (PID) Process: | (2928) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E2070B0004000F000F00360008000B02 | |||
Executable files
50
Suspicious files
1
Text files
7
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2928 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3168 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@hermes.travel[1].txt | — | |
MD5:— | SHA256:— | |||
| 2928 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2928 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF04B992D018D24A5F.TMP | — | |
MD5:— | SHA256:— | |||
| 2928 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF19F5477FAFA1CDC7.TMP | — | |
MD5:— | SHA256:— | |||
| 2928 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{AEE181BB-E8EE-11E8-A67C-5254004AAD11}.dat | — | |
MD5:— | SHA256:— | |||
| 3168 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@hermes.travel[2].txt | text | |
MD5:— | SHA256:— | |||
| 2928 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{AEE181BC-E8EE-11E8-A67C-5254004AAD11}.dat | binary | |
MD5:— | SHA256:— | |||
| 3168 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\Low\History.IE5\MSHist012018111520181116\index.dat | dat | |
MD5:— | SHA256:— | |||
| 3168 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\unt[1].exe | executable | |
MD5:FB56E3F87A0A23B6DCFE4918668F3589 | SHA256:B2FFD1D5ECFF5A946E032ADD96D05413DF84BE323D6490D119A65F5F96F5DBEF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
4
DNS requests
3
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2880 | unt[1].exe | POST | 200 | 94.142.140.12:80 | http://kerondown.com/index.php | RU | binary | 4.27 Mb | malicious |
3168 | iexplore.exe | GET | 200 | 87.98.239.87:80 | http://hermes.travel.pl/unt.exe | PL | executable | 397 Kb | malicious |
2928 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
2880 | unt[1].exe | POST | 200 | 94.142.140.12:80 | http://kerondown.com/index.php | RU | text | 2 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2928 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3168 | iexplore.exe | 87.98.239.87:80 | hermes.travel.pl | OVH SAS | PL | malicious |
2880 | unt[1].exe | 94.142.140.12:80 | kerondown.com | MAROSNET Telecommunication Company LLC | RU | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
hermes.travel.pl |
| malicious |
kerondown.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3168 | iexplore.exe | Potentially Bad Traffic | ET CURRENT_EVENTS Terse alphanumeric executable downloader high likelihood of being hostile |
3168 | iexplore.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2880 | unt[1].exe | A Network Trojan was detected | MALWARE [PTsecurity] AZORult HTTP Header |
2880 | unt[1].exe | A Network Trojan was detected | MALWARE [PTsecurity] AZORult Request |
2880 | unt[1].exe | A Network Trojan was detected | MALWARE [PTsecurity] AZORult Response |
2880 | unt[1].exe | A Network Trojan was detected | MALWARE [PTsecurity] AZORult HTTP Header |
2 ETPRO signatures available at the full report