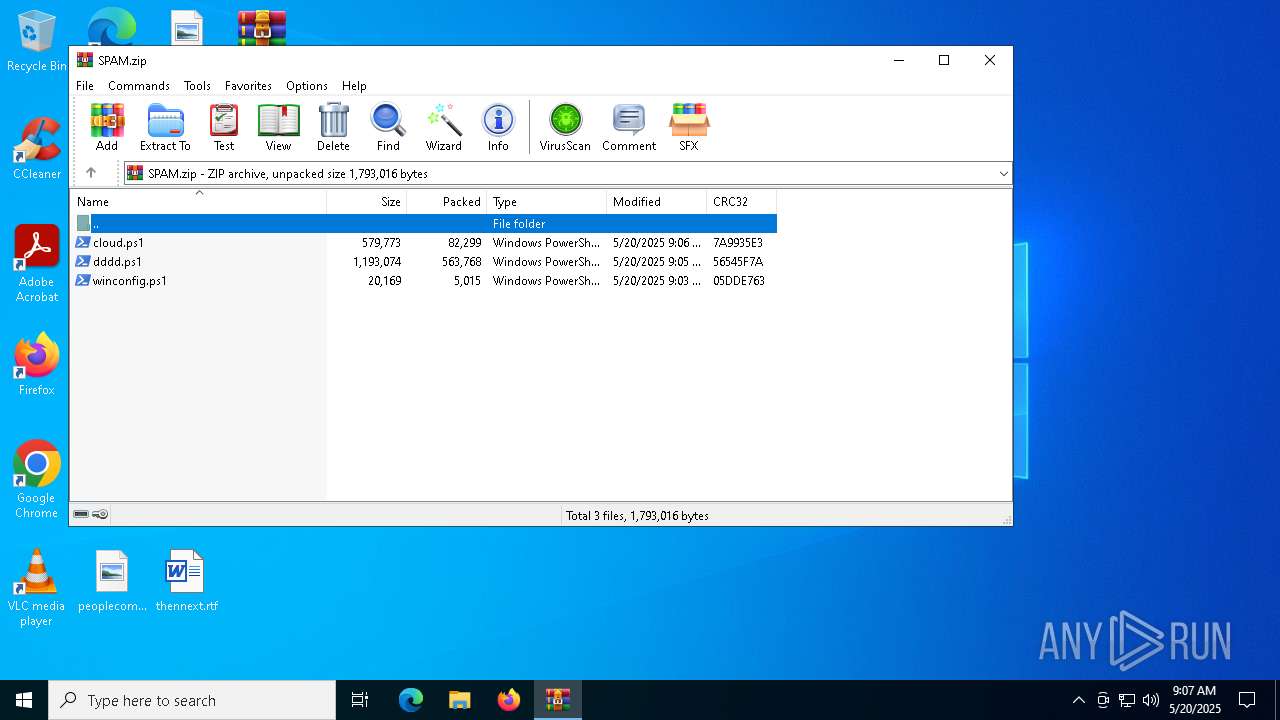
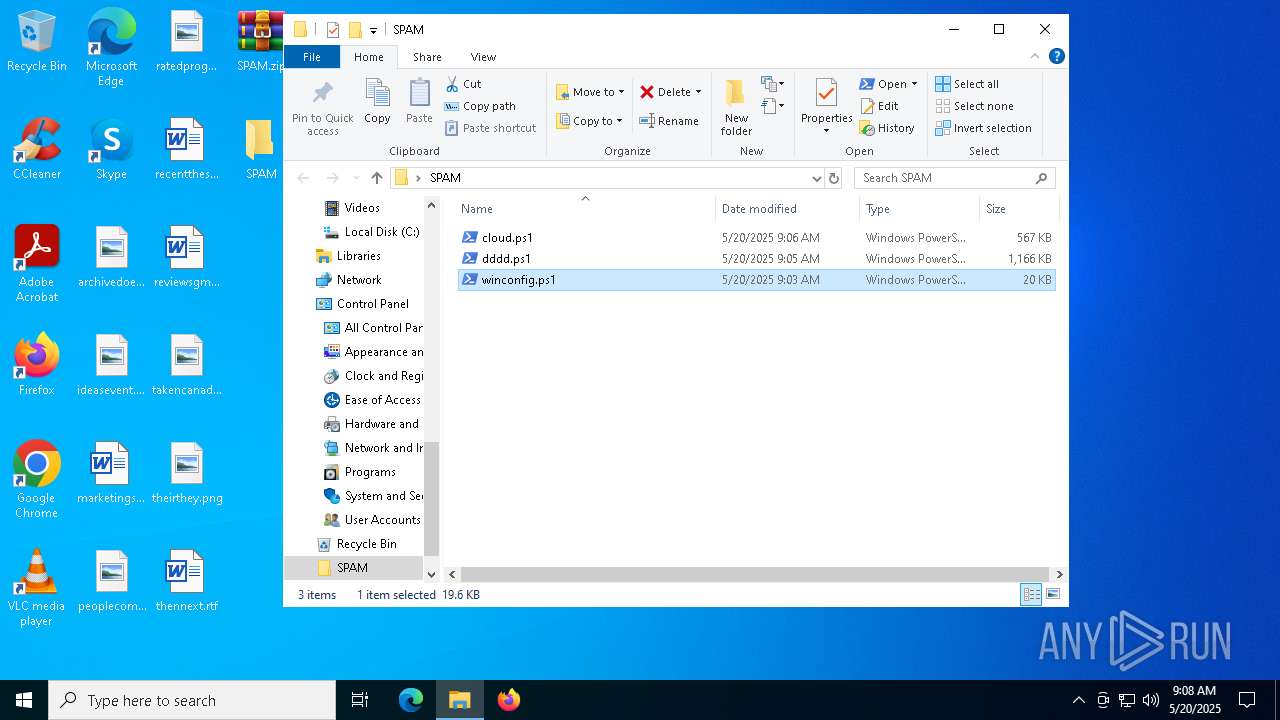
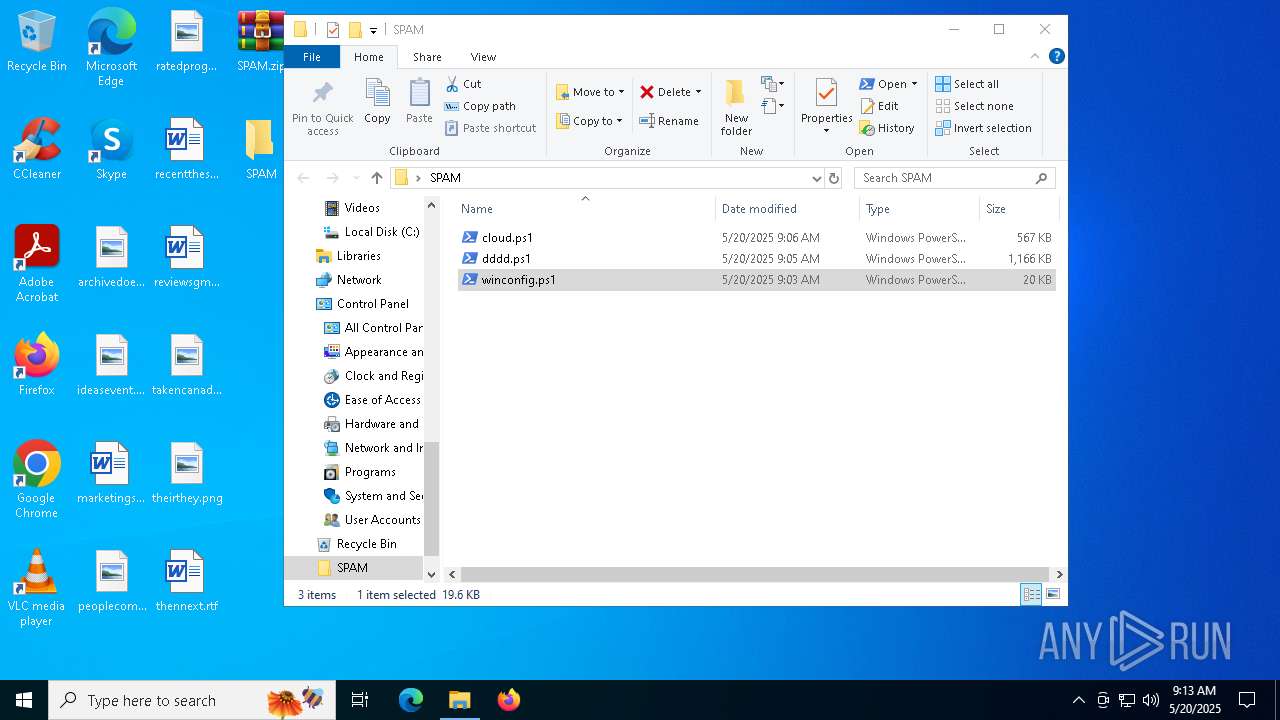
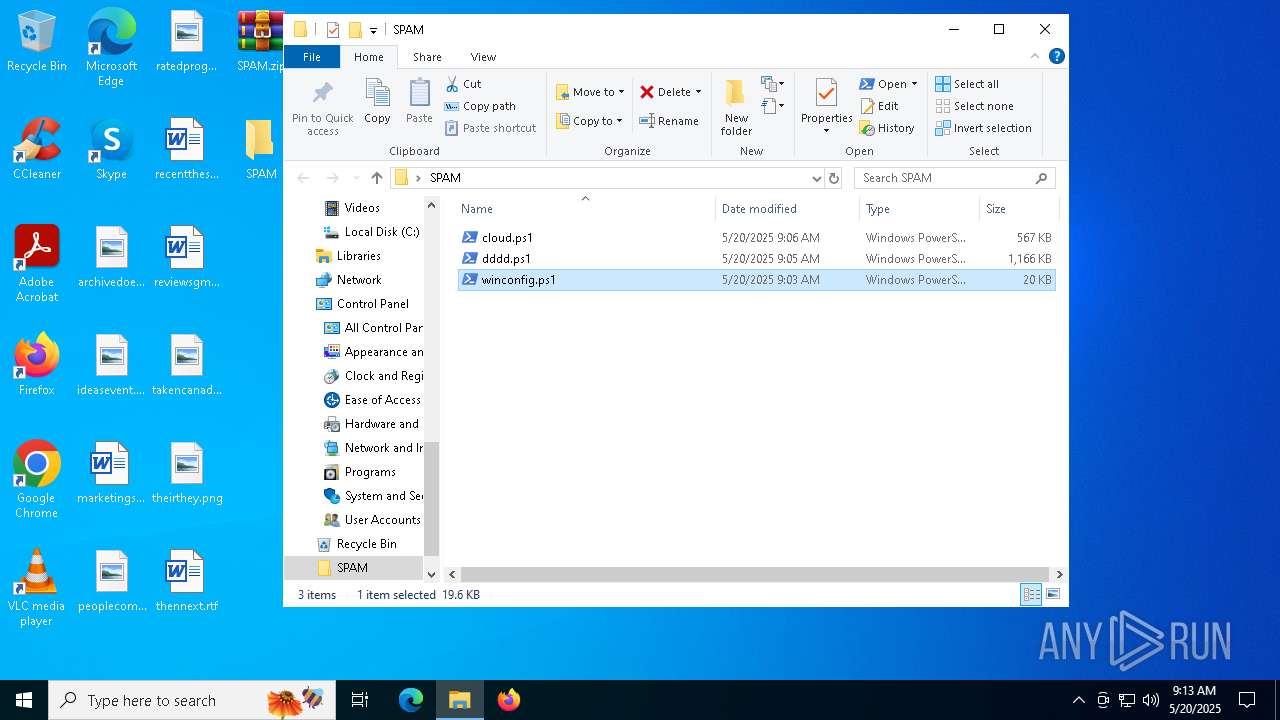
| File name: | SPAM.zip |
| Full analysis: | https://app.any.run/tasks/820c44eb-5335-4c94-930d-a48520928875 |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | May 20, 2025, 09:07:15 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | BB2D7AE9A8B61391F18349B165D34E46 |
| SHA1: | 957DA13E6CBC546833D761A7EF5219535FA3F3B9 |
| SHA256: | A0A3FFBEBA71DFE4510A578AA88BC992BA60B7ADCDD3863FC51D3F51C0EB51F7 |
| SSDEEP: | 24576:ectaFLgFMEgECYRCpVvpeVq3q6S+lS7kHNCp7UNQ3jx2kouXYZlD3:ectaFLgFMEgECYRCpVvpIq3q6S+lSYtH |
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 1912)
Bypass execution policy to execute commands
- powershell.exe (PID: 7036)
- powershell.exe (PID: 4988)
- powershell.exe (PID: 900)
- powershell.exe (PID: 1184)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 7036)
Script downloads file (POWERSHELL)
- powershell.exe (PID: 4988)
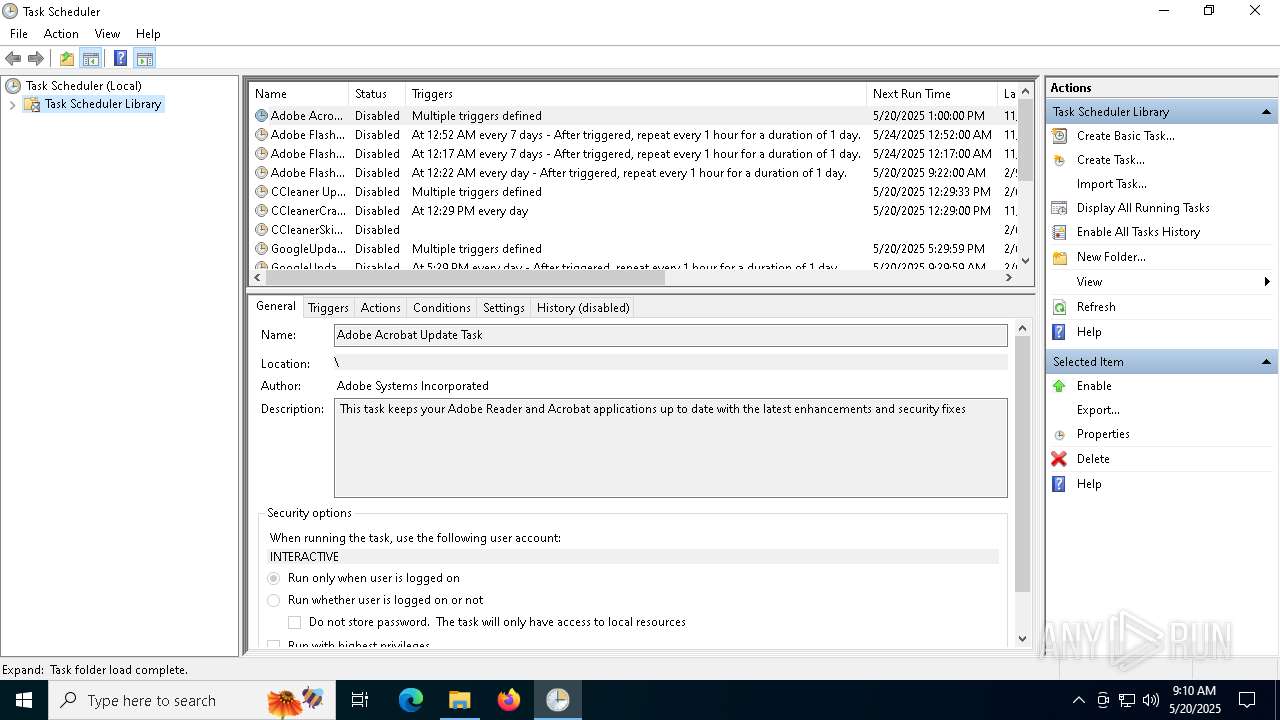
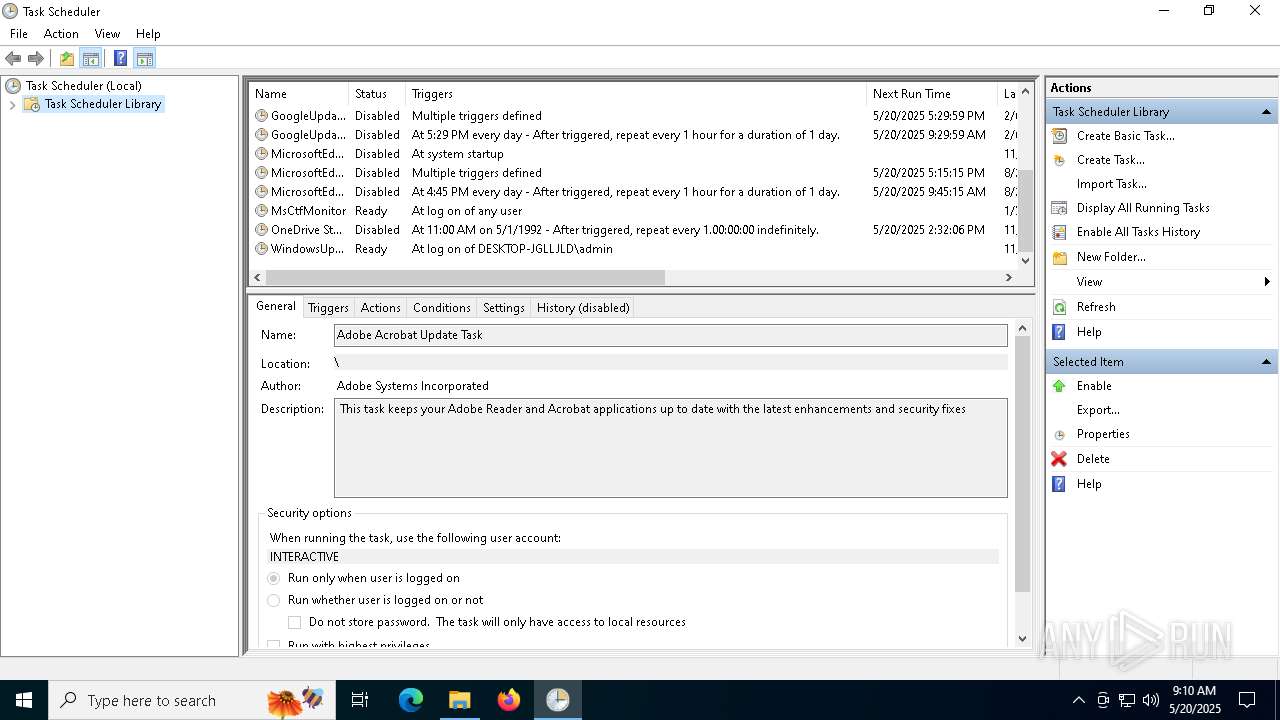
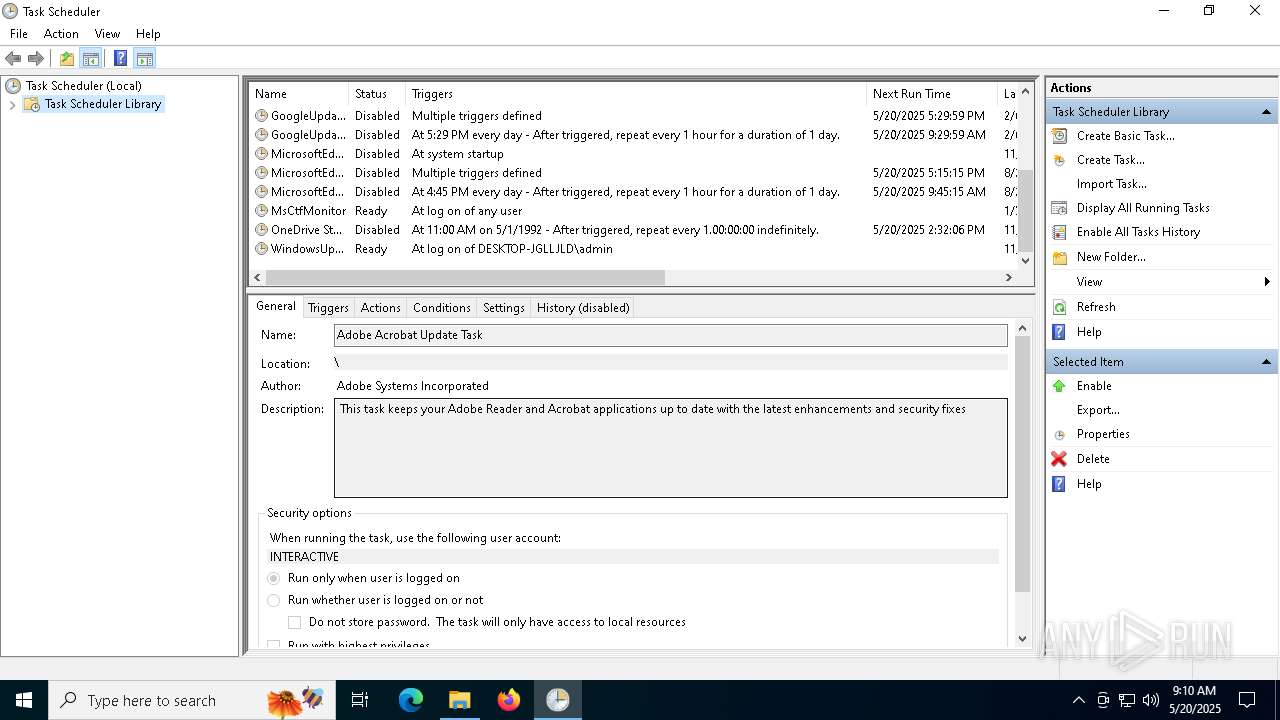
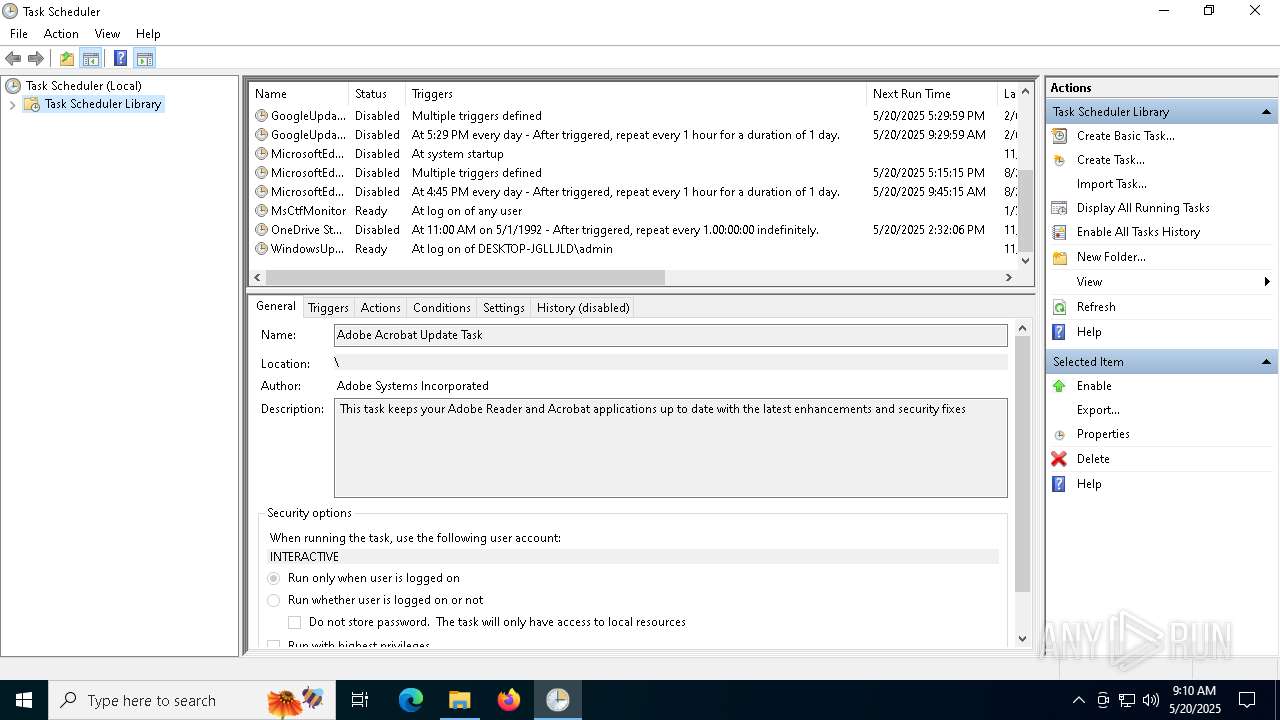
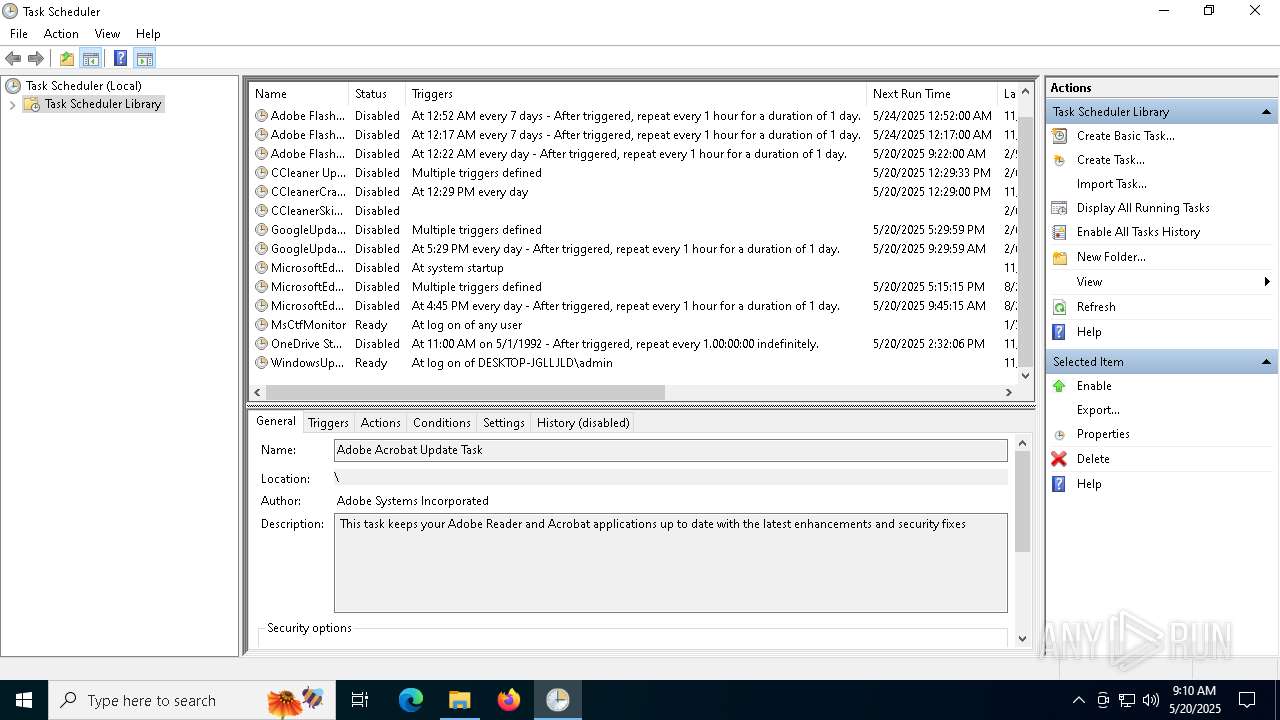
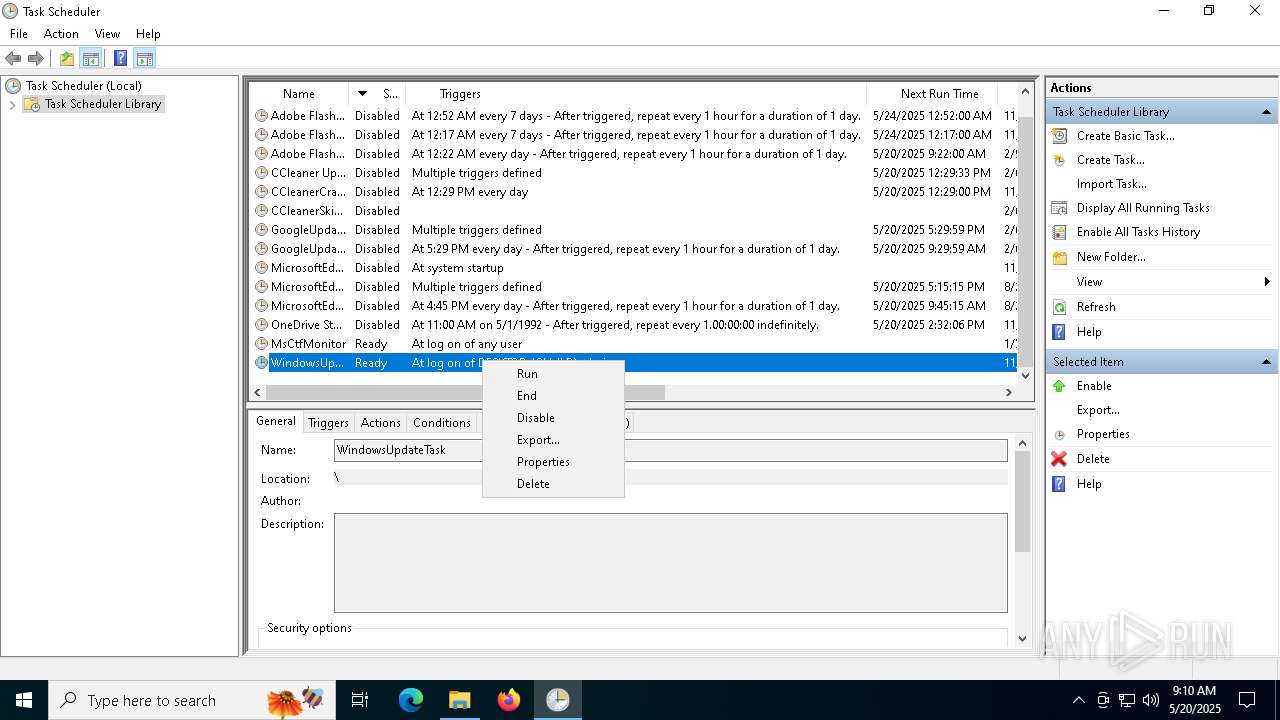
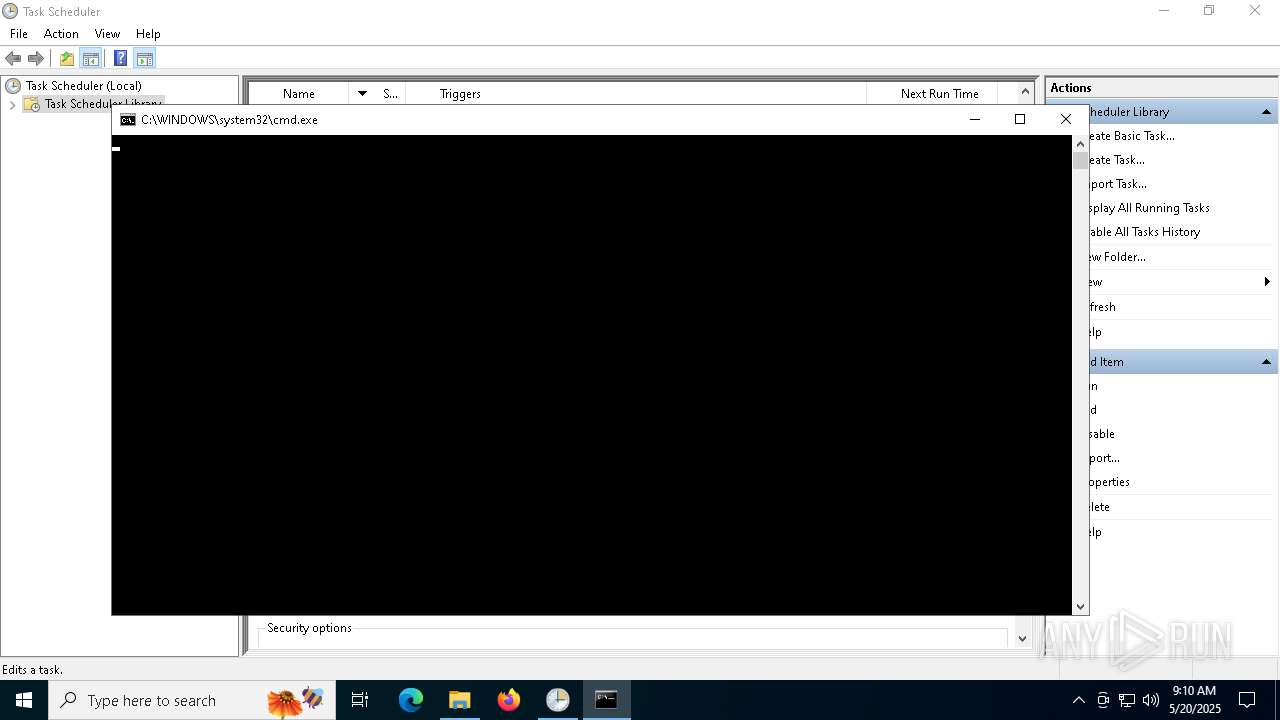
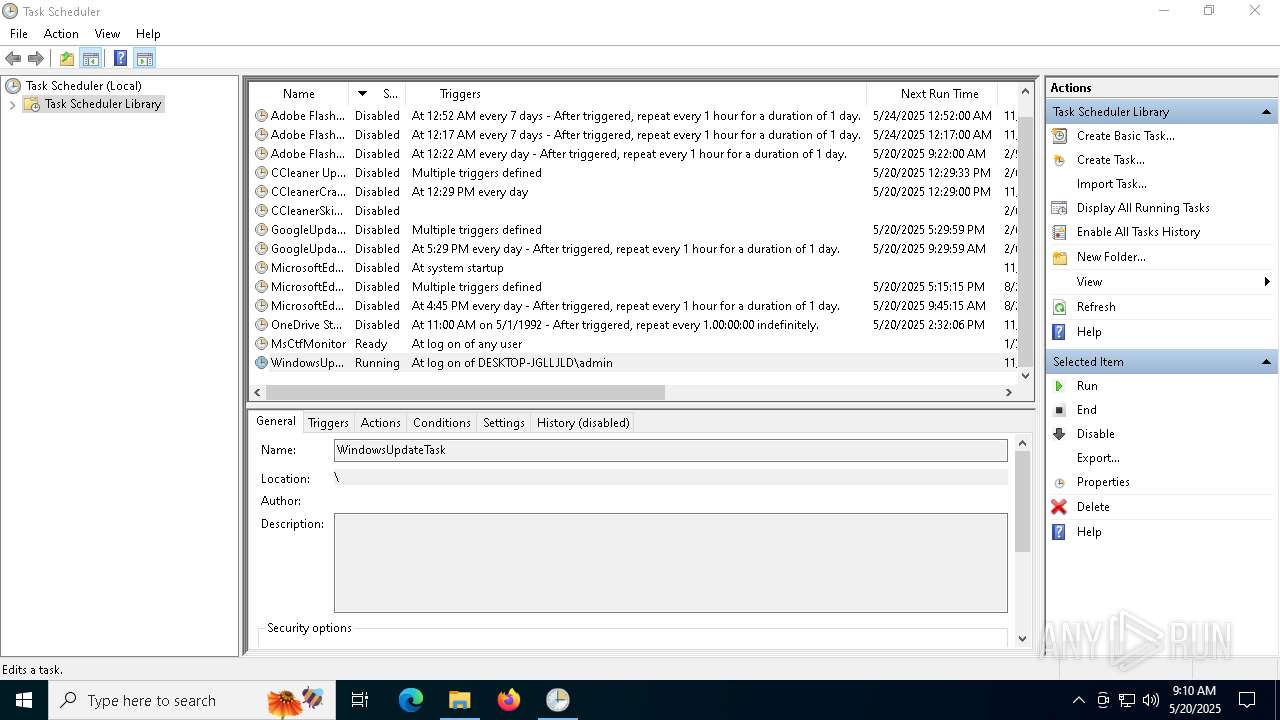
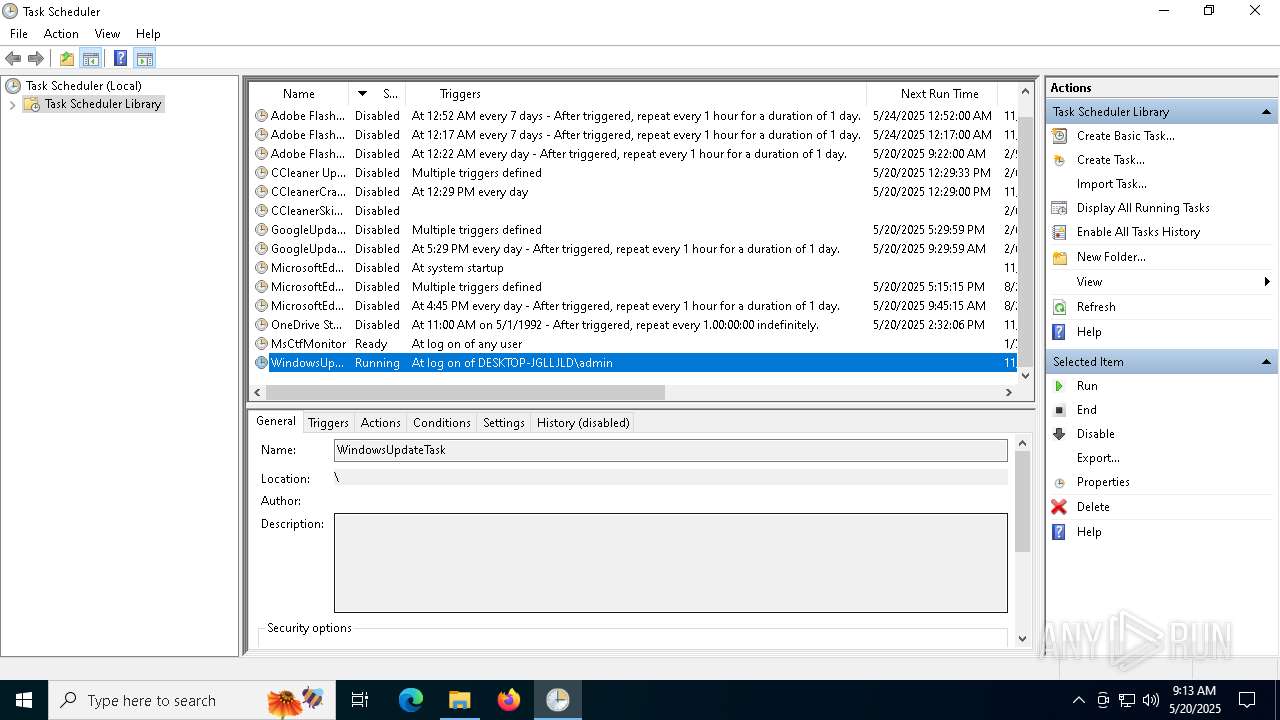
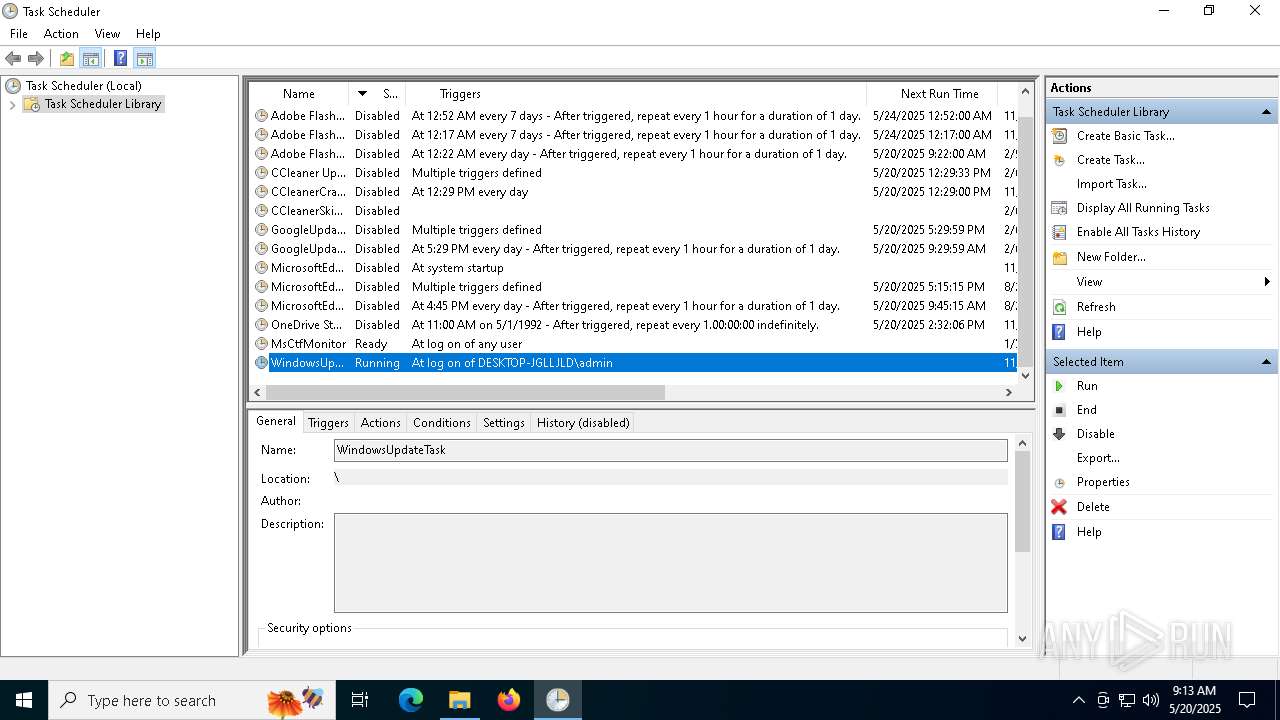
Uses Task Scheduler to run other applications
- wscript.exe (PID: 2552)
ASYNCRAT has been detected (MUTEX)
- RegSvcs.exe (PID: 2240)
Steals credentials from Web Browsers
- RegSvcs.exe (PID: 2240)
ASYNCRAT has been detected (SURICATA)
- RegSvcs.exe (PID: 2240)
- jsc.exe (PID: 5744)
Create files in the Startup directory
- cmd.exe (PID: 812)
Actions looks like stealing of personal data
- RegSvcs.exe (PID: 2240)
ASYNCRAT has been detected (YARA)
- RegSvcs.exe (PID: 2240)
- jsc.exe (PID: 5744)
Run PowerShell with an invisible window
- powershell.exe (PID: 1184)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 924)
SUSPICIOUS
Converts a specified value to an integer (POWERSHELL)
- powershell.exe (PID: 7036)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 4988)
- powershell.exe (PID: 900)
Executable content was dropped or overwritten
- powershell.exe (PID: 4988)
- Guard.exe (PID: 4200)
Writes data into a file (POWERSHELL)
- powershell.exe (PID: 4988)
The process executes VB scripts
- powershell.exe (PID: 4988)
Starts the AutoIt3 executable file
- wscript.exe (PID: 2552)
Drops a file with a rarely used extension (PIF)
- Guard.exe (PID: 4200)
Runs shell command (SCRIPT)
- wscript.exe (PID: 2552)
Checks a user's role membership (POWERSHELL)
- powershell.exe (PID: 900)
Connects to unusual port
- RegSvcs.exe (PID: 2240)
- powershell.exe (PID: 900)
- jsc.exe (PID: 5744)
- powershell.exe (PID: 1184)
Contacting a server suspected of hosting an CnC
- RegSvcs.exe (PID: 2240)
- jsc.exe (PID: 5744)
Checks for external IP
- powershell.exe (PID: 900)
- powershell.exe (PID: 1184)
Potential Corporate Privacy Violation
- powershell.exe (PID: 900)
- powershell.exe (PID: 1184)
Multiple wallet extension IDs have been found
- RegSvcs.exe (PID: 2240)
Process drops legitimate windows executable
- Guard.exe (PID: 4200)
There is functionality for taking screenshot (YARA)
- Guard.exe (PID: 4200)
- Guard.exe (PID: 6108)
- Guard.exe (PID: 6668)
The process executes via Task Scheduler
- cmd.exe (PID: 924)
The process executes Powershell scripts
- cmd.exe (PID: 924)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 924)
INFO
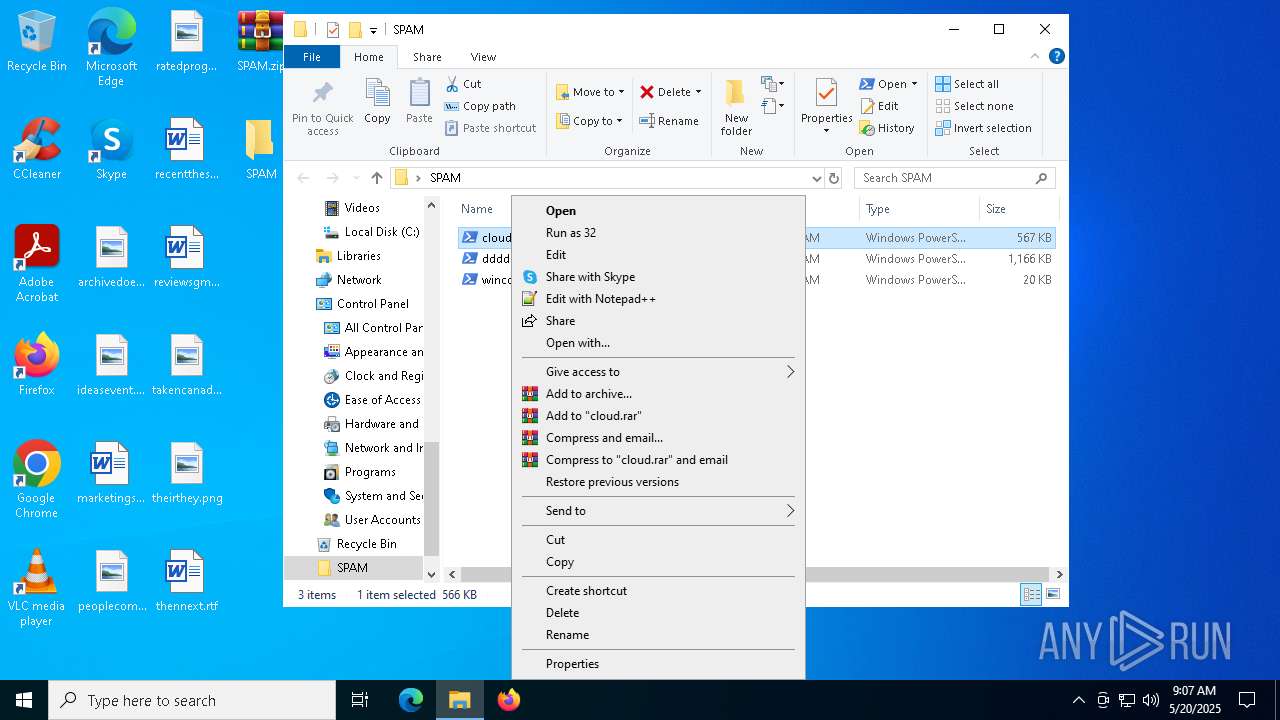
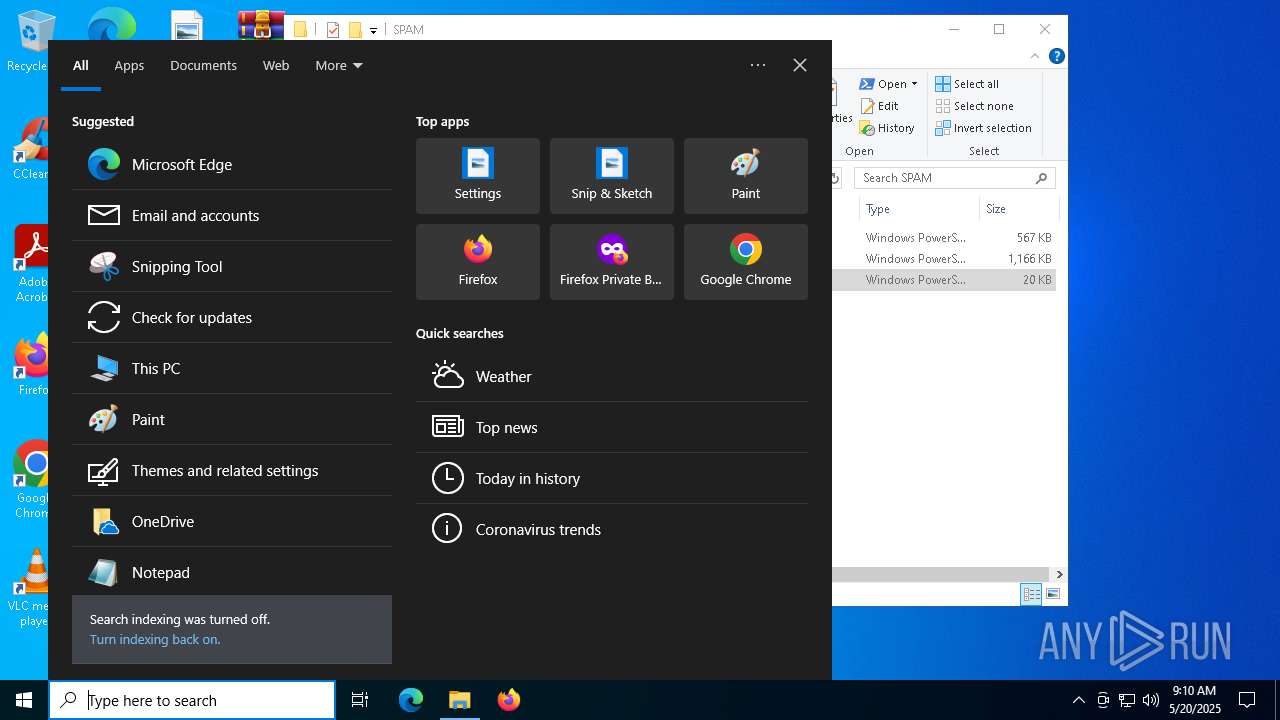
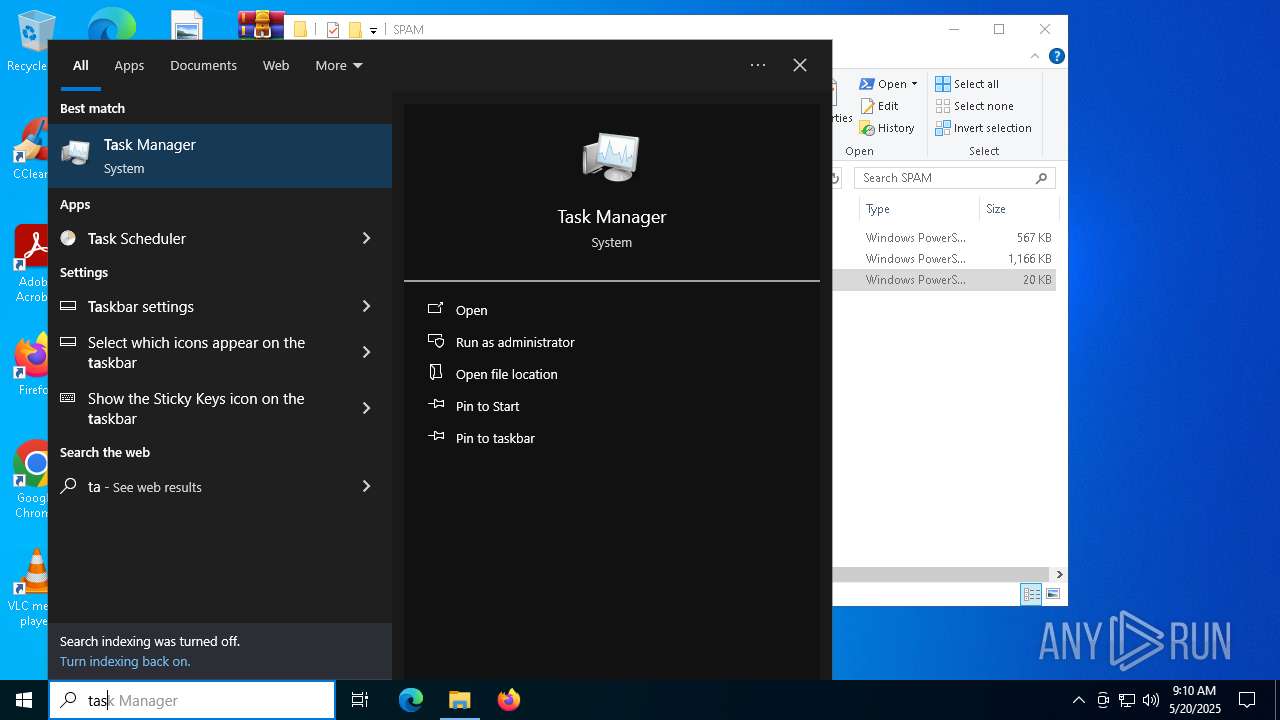
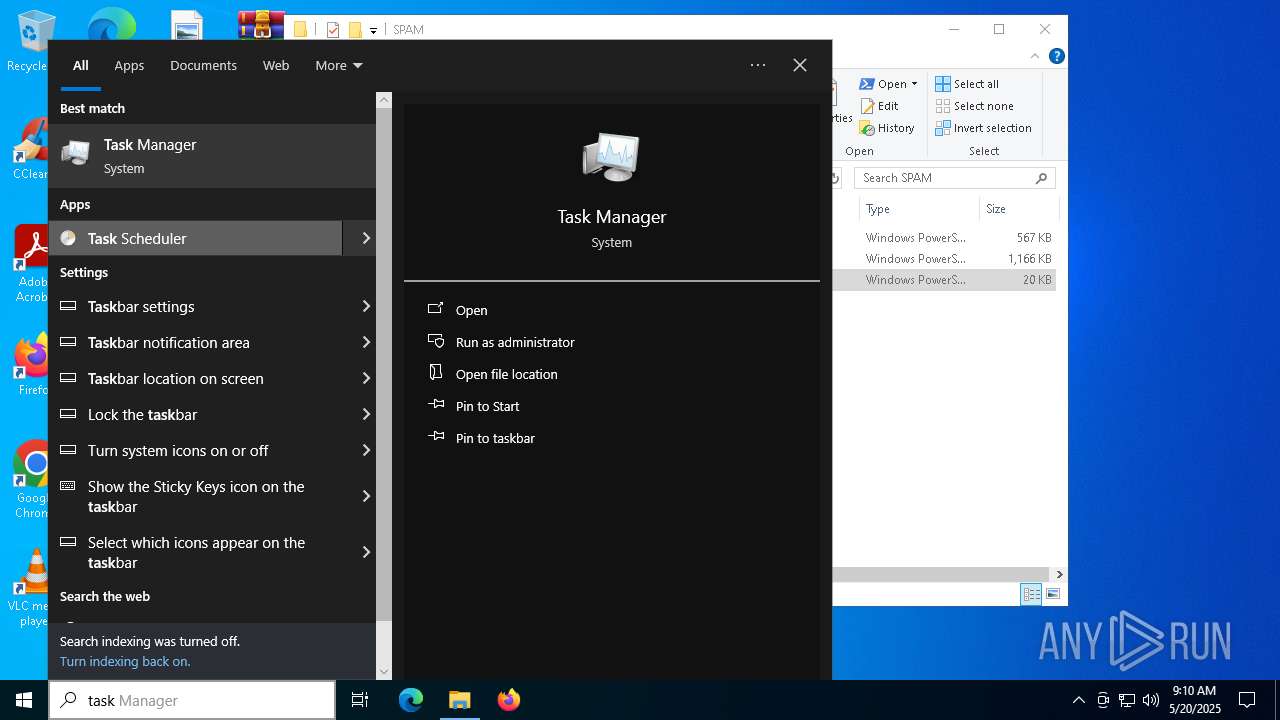
Manual execution by a user
- powershell.exe (PID: 7036)
- WinRAR.exe (PID: 5508)
- powershell.exe (PID: 4988)
- cmd.exe (PID: 812)
- powershell.exe (PID: 900)
- jsc.exe (PID: 5744)
- jsc.exe (PID: 6240)
- mmc.exe (PID: 6372)
- mmc.exe (PID: 240)
- jsc.exe (PID: 4400)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 7036)
- powershell.exe (PID: 900)
Disables trace logs
- powershell.exe (PID: 4988)
- powershell.exe (PID: 900)
Checks proxy server information
- powershell.exe (PID: 4988)
- powershell.exe (PID: 900)
Gets data length (POWERSHELL)
- powershell.exe (PID: 7036)
- powershell.exe (PID: 900)
The sample compiled with english language support
- powershell.exe (PID: 4988)
- Guard.exe (PID: 4200)
Reads the computer name
- RegSvcs.exe (PID: 2240)
- Guard.exe (PID: 4200)
- jsc.exe (PID: 5744)
Checks supported languages
- RegSvcs.exe (PID: 2240)
- Guard.exe (PID: 4200)
- jsc.exe (PID: 5744)
Reads the machine GUID from the registry
- RegSvcs.exe (PID: 2240)
- jsc.exe (PID: 5744)
Reads mouse settings
- Guard.exe (PID: 4200)
Creates files or folders in the user directory
- Guard.exe (PID: 4200)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 900)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 900)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 900)
Reads the software policy settings
- RegSvcs.exe (PID: 2240)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2025:05:20 11:06:32 |
| ZipCRC: | 0x7a9935e3 |
| ZipCompressedSize: | 82299 |
| ZipUncompressedSize: | 579773 |
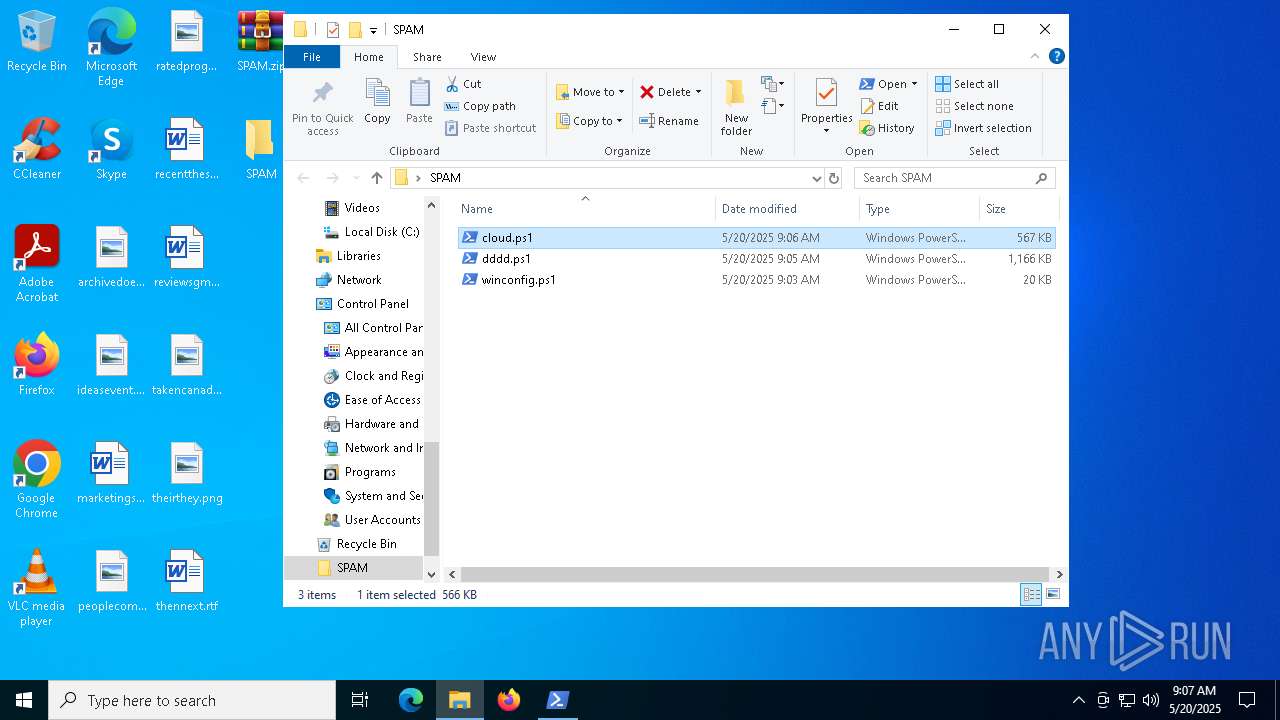
| ZipFileName: | cloud.ps1 |
Total processes
165
Monitored processes
28
Malicious processes
7
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 240 | "C:\WINDOWS\system32\mmc.exe" "C:\WINDOWS\system32\taskschd.msc" /s | C:\Windows\System32\mmc.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Management Console Exit code: 3221226540 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 812 | cmd /k echo [InternetShortcut] > "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\SwiftWrite.url" & echo URL="C:\Users\admin\AppData\Local\WordGenius Technologies\SwiftWrite.js" >> "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\SwiftWrite.url" & exit | C:\Windows\SysWOW64\cmd.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 900 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ep bypass "C:\Users\admin\Desktop\SPAM\winconfig.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 924 | "cmd.exe" /c "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Config\winconfig.bat" | C:\Windows\System32\cmd.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1184 | powershell.exe -WindowStyle Hidden -ExecutionPolicy Bypass -File "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Config\winconfig.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1912 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\SPAM.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2240 | "C:\\Windows\\Microsoft.Net\\Framework\\v4.0.30319\\RegSvcs.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegSvcs.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Services Installation Utility Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 2392 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2552 | "C:\WINDOWS\system32\wscript.exe" C:\Users\admin\AppData\Local\Microsoft\backup\TaskCreator.vbs | C:\Windows\System32\wscript.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 4200 | "C:\Users\admin\AppData\Local\Microsoft\backup\Guard.exe" "C:\Users\admin\AppData\Local\Microsoft\backup\Secure.au3" | C:\Users\admin\AppData\Local\Microsoft\backup\Guard.exe | wscript.exe | ||||||||||||
User: admin Company: AutoIt Team Integrity Level: MEDIUM Description: AutoIt v3 Script Exit code: 0 Version: 3, 3, 14, 3 Modules
| |||||||||||||||
Total events
38 725
Read events
38 683
Write events
41
Delete events
1
Modification events
| (PID) Process: | (1912) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (1912) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (1912) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (1912) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\SPAM.zip | |||
| (PID) Process: | (1912) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1912) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1912) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1912) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1912) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
| (PID) Process: | (1912) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
Executable files
4
Suspicious files
10
Text files
19
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
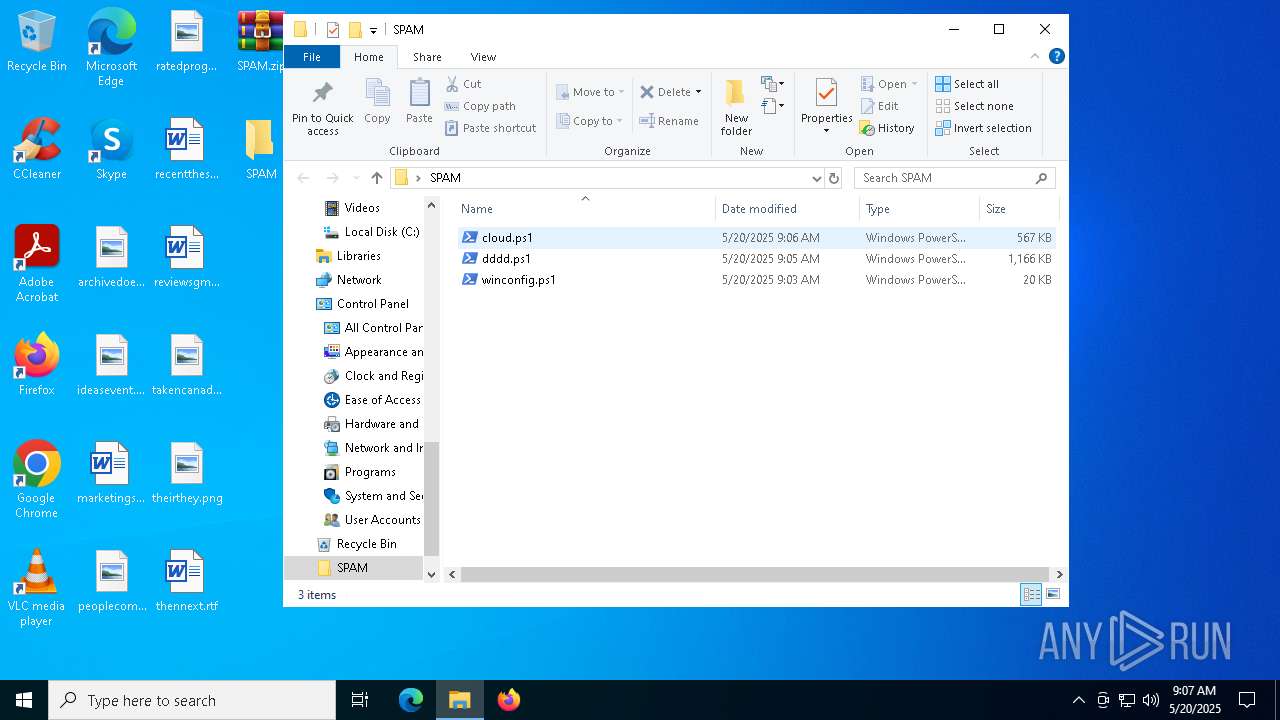
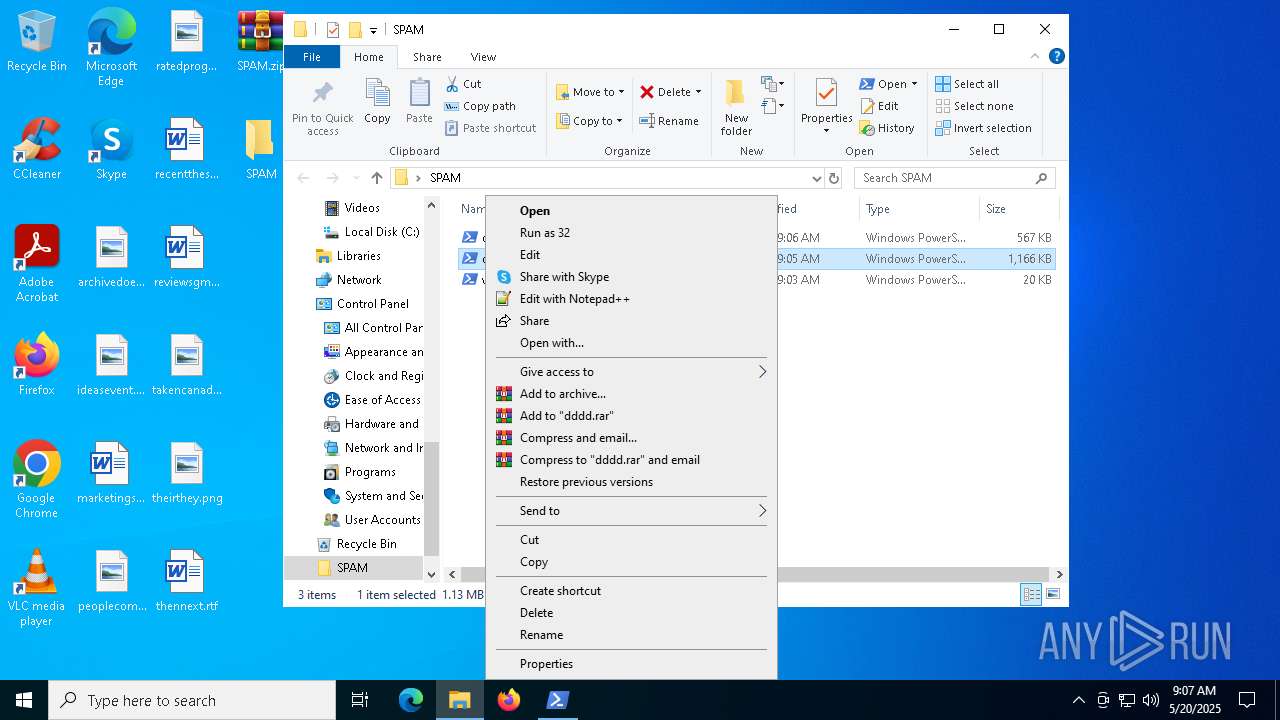
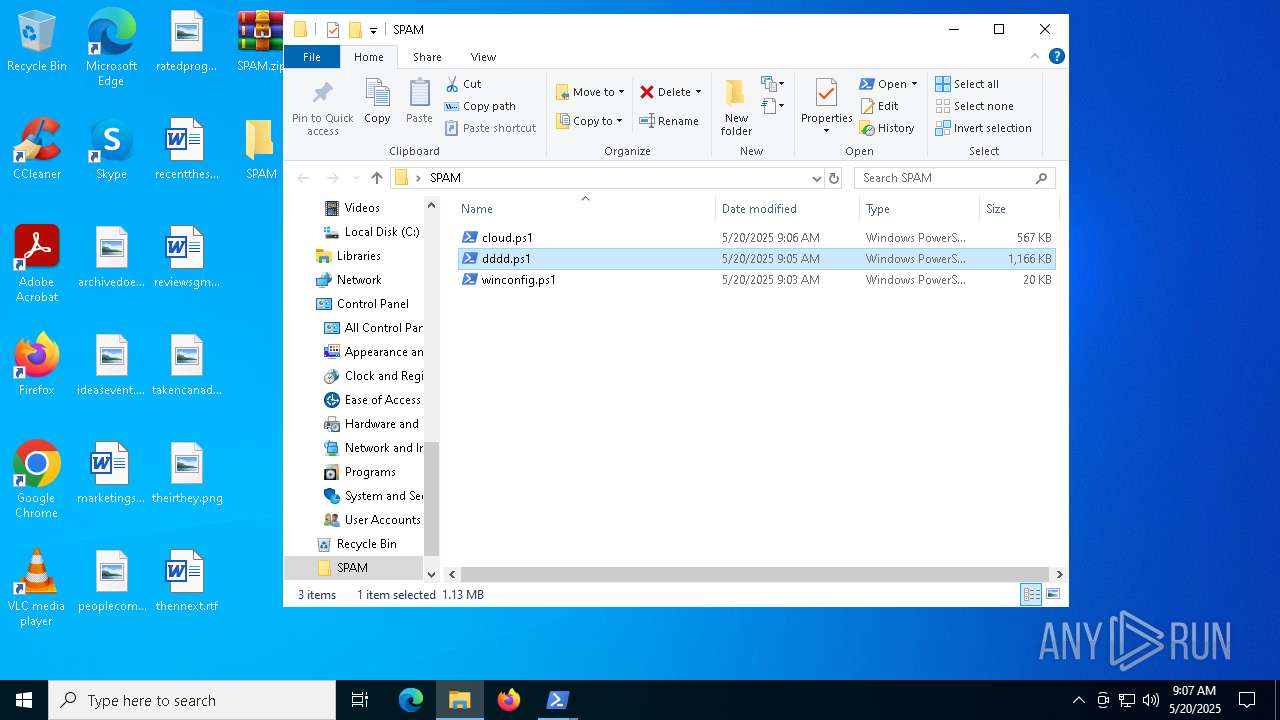
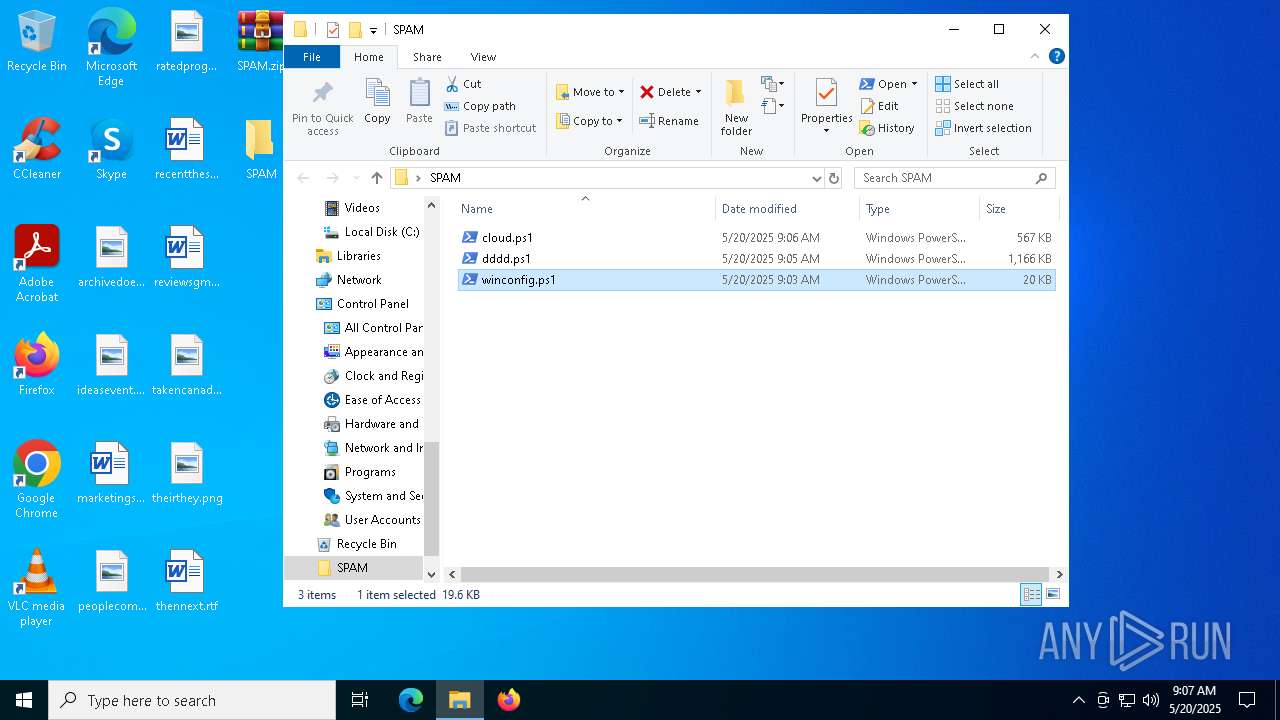
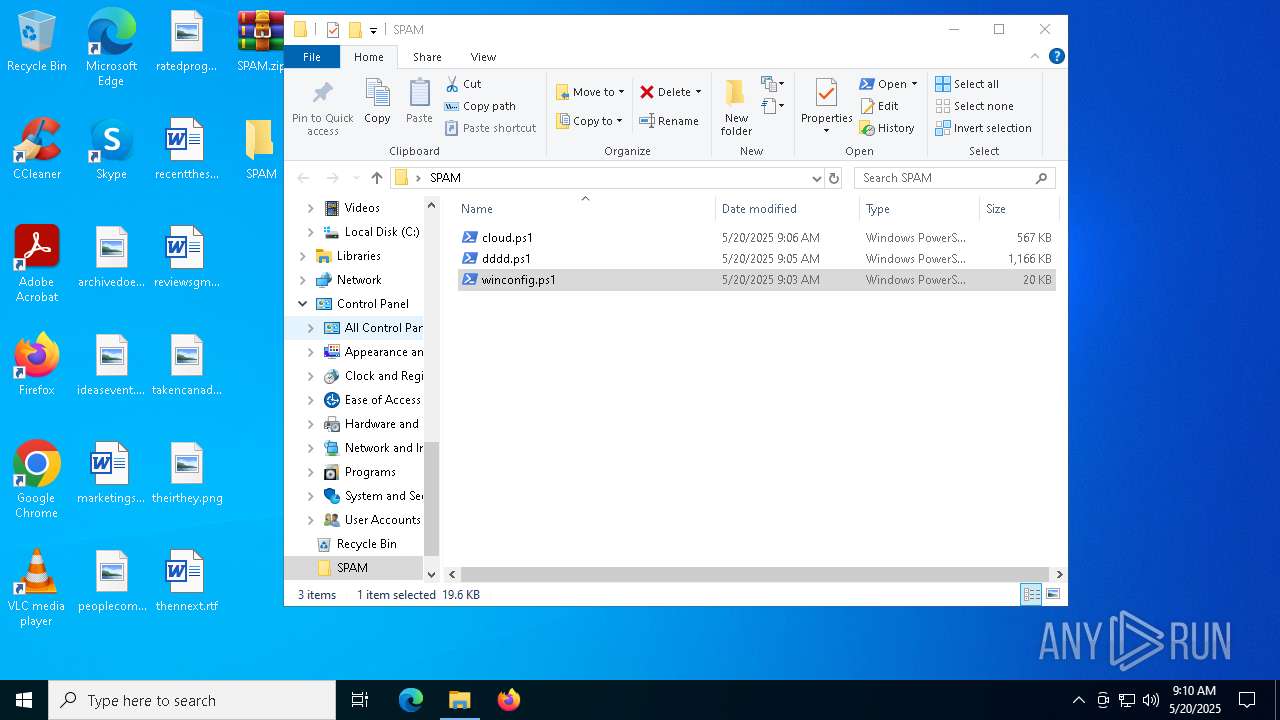
| 5508 | WinRAR.exe | C:\Users\admin\Desktop\SPAM\cloud.ps1 | text | |
MD5:84C1D9F6499DDD34C80470B51E3A8B24 | SHA256:70BAAD1FC7ED2D05B14F3B30F844E8987F208474E65C107984E6945FAD7D4E83 | |||
| 7036 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\JXNGS0R2J1X3E4J60JOQ.temp | binary | |
MD5:2EC984216C4D2991737DD80255EE0ECC | SHA256:7BF33364C1D9D5C5C8C60E82EA204EB96C232C4594933F795B39D752E466AA51 | |||
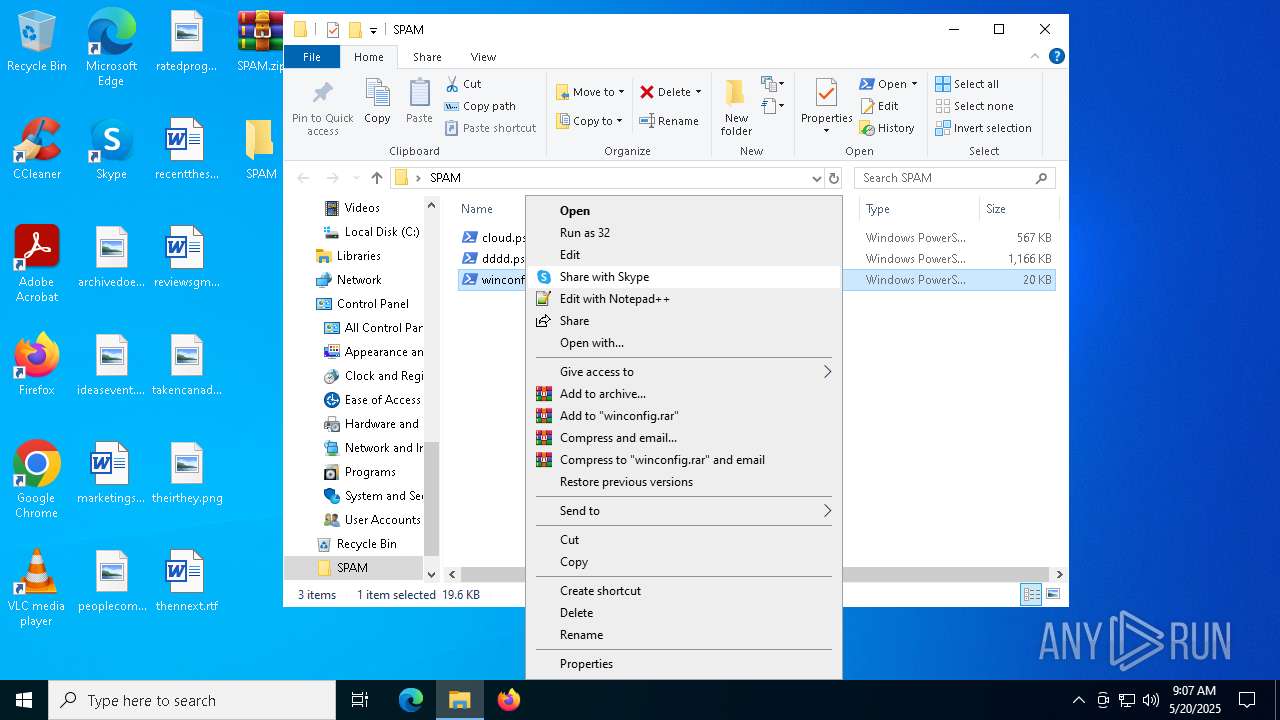
| 5508 | WinRAR.exe | C:\Users\admin\Desktop\SPAM\winconfig.ps1 | text | |
MD5:FEAA4AC1A1C51D1680B2ED73FF5DA5F2 | SHA256:0A4888750A50461EFFD10757FC9BEBFACBC661A9AD57FD4C23EEFBC735F7CA94 | |||
| 7036 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_z5doaykj.q1k.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7036 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:2EC984216C4D2991737DD80255EE0ECC | SHA256:7BF33364C1D9D5C5C8C60E82EA204EB96C232C4594933F795B39D752E466AA51 | |||
| 7036 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF1100b8.TMP | binary | |
MD5:D040F64E9E7A2BB91ABCA5613424598E | SHA256:D04E0A6940609BD6F3B561B0F6027F5CA4E8C5CF0FB0D0874B380A0374A8D670 | |||
| 7036 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_5xfmx3m1.fdv.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5508 | WinRAR.exe | C:\Users\admin\Desktop\SPAM\dddd.ps1 | text | |
MD5:86DC22FE5D147FDA6039C0BA94A12FCC | SHA256:E744E919E1BB49E73095C1BEAFDF0623438241E3C3C6FDF88D5B9711BD7D4CB3 | |||
| 7036 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:58688B580A9DB7731CBA57256B18D3DC | SHA256:3DD3E4D3EAC33A1692F25206A5548FBFA53304D0821BAADA881ADE87A3FCD529 | |||
| 4988 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\backup\Guard.exe | executable | |
MD5:18CE19B57F43CE0A5AF149C96AECC685 | SHA256:D8B7C7178FBADBF169294E4F29DCE582F89A5CF372E9DA9215AA082330DC12FD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
81
DNS requests
29
Threats
19
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4528 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
4528 | SIHClient.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4528 | SIHClient.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
4528 | SIHClient.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicTimStaPCA_2010-07-01.crl | unknown | — | — | whitelisted |
4528 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4528 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
4528 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
4528 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2112 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4988 | powershell.exe | 188.114.97.3:443 | neohomesloan.com | CLOUDFLARENET | NL | unknown |
2240 | RegSvcs.exe | 95.214.55.246:8383 | bncisdor.nriasoruvd.info | Meverywhere sp. z o.o. | PL | malicious |
900 | powershell.exe | 104.26.13.205:443 | api.ipify.org | CLOUDFLARENET | US | shared |
900 | powershell.exe | 89.117.79.31:88 | myststemsgame.com | — | LT | unknown |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
neohomesloan.com |
| unknown |
nbhkmKSQnaDrIkubbvvLMhHdgigs.nbhkmKSQnaDrIkubbvvLMhHdgigs |
| unknown |
bncisdor.nriasoruvd.info |
| unknown |
api.ipify.org |
| shared |
myststemsgame.com |
| unknown |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
arc.msn.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2240 | RegSvcs.exe | Domain Observed Used for C2 Detected | REMOTE [ANY.RUN] AsyncRAT SSL certificate |
2240 | RegSvcs.exe | Domain Observed Used for C2 Detected | ET MALWARE Generic AsyncRAT/zgRAT Style SSL Cert |
2240 | RegSvcs.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Malicious SSL Cert (AsyncRAT Server) |
2196 | svchost.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
— | — | Device Retrieving External IP Address Detected | ET INFO External IP Lookup api.ipify.org |
— | — | Device Retrieving External IP Address Detected | POLICY [ANY.RUN] External IP Lookup by HTTP (api .ipify .org) |
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
900 | powershell.exe | Potential Corporate Privacy Violation | ET INFO Possible IP Check api.ipify.org |
900 | powershell.exe | Misc activity | ET INFO External IP Address Lookup Domain (ipify .org) in TLS SNI |
— | — | Device Retrieving External IP Address Detected | SUSPICIOUS [ANY.RUN] An IP address was received from the server as a result of an HTTP request |