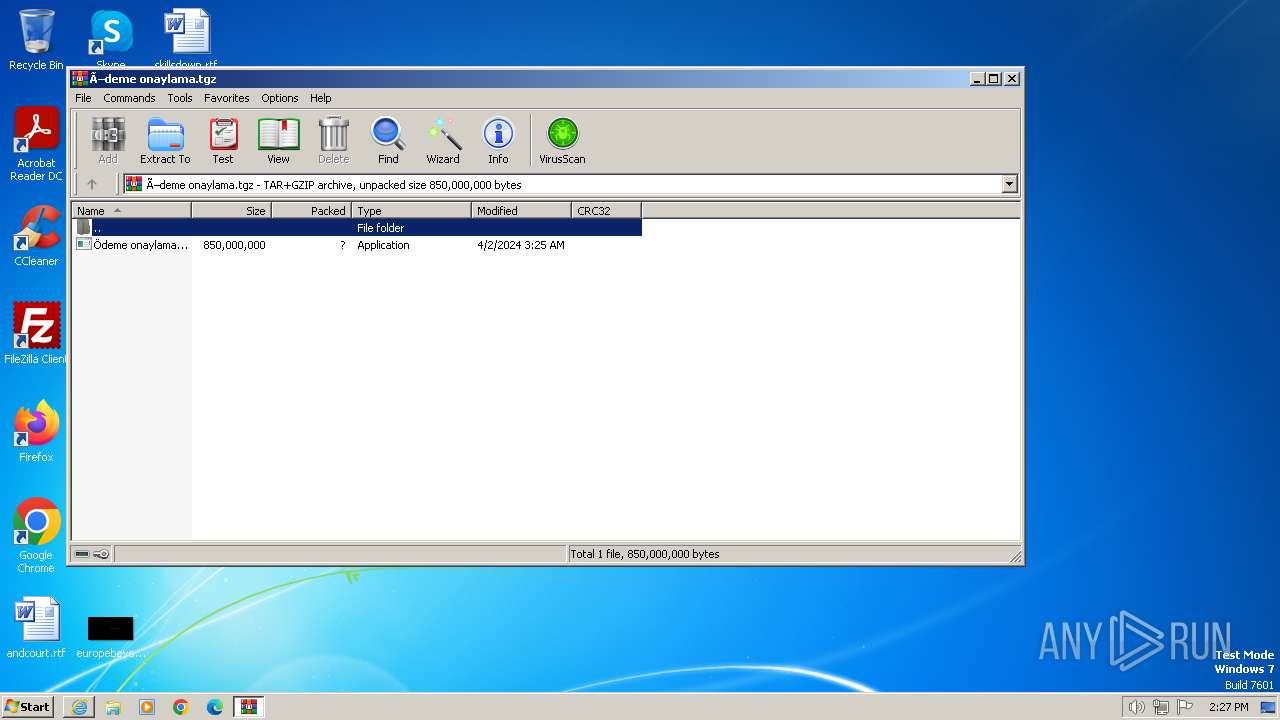
| URL: | https://www.mediafire.com/file/qyxg958fgvw6k02/Ödeme%20onaylama.tgz/file |
| Full analysis: | https://app.any.run/tasks/5a80889f-58ad-47c6-ac55-bf28313f97d7 |
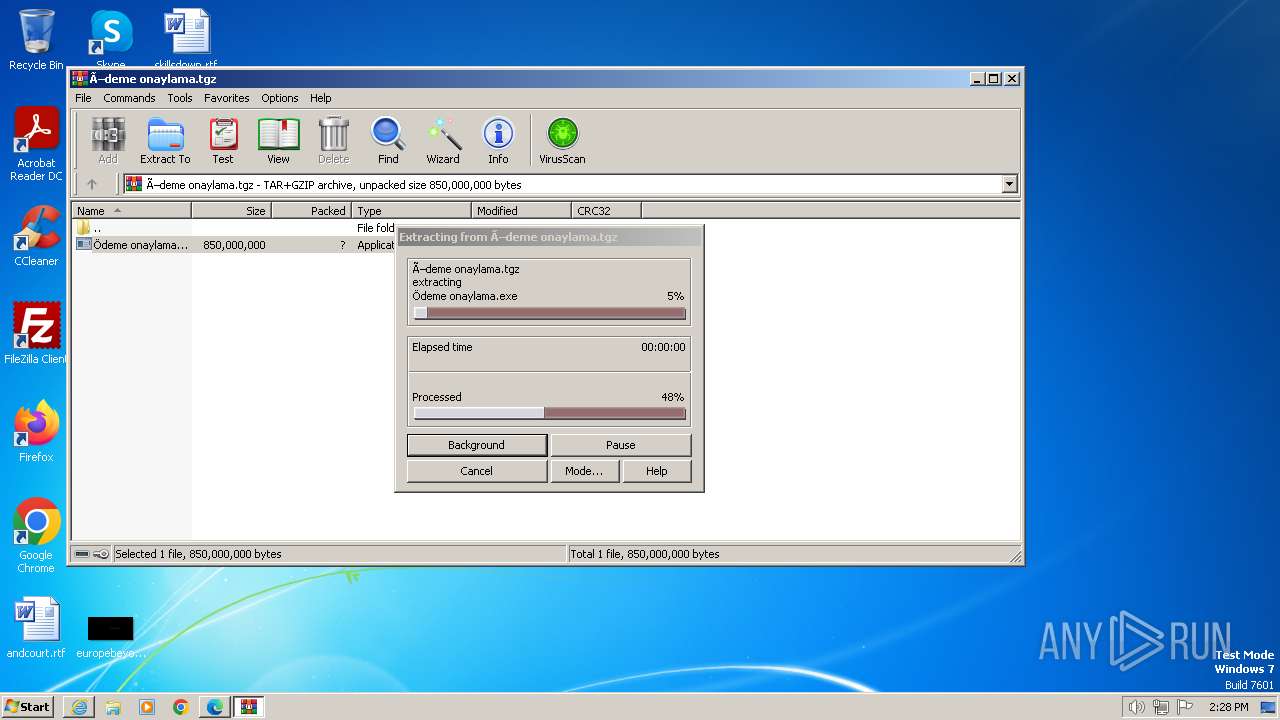
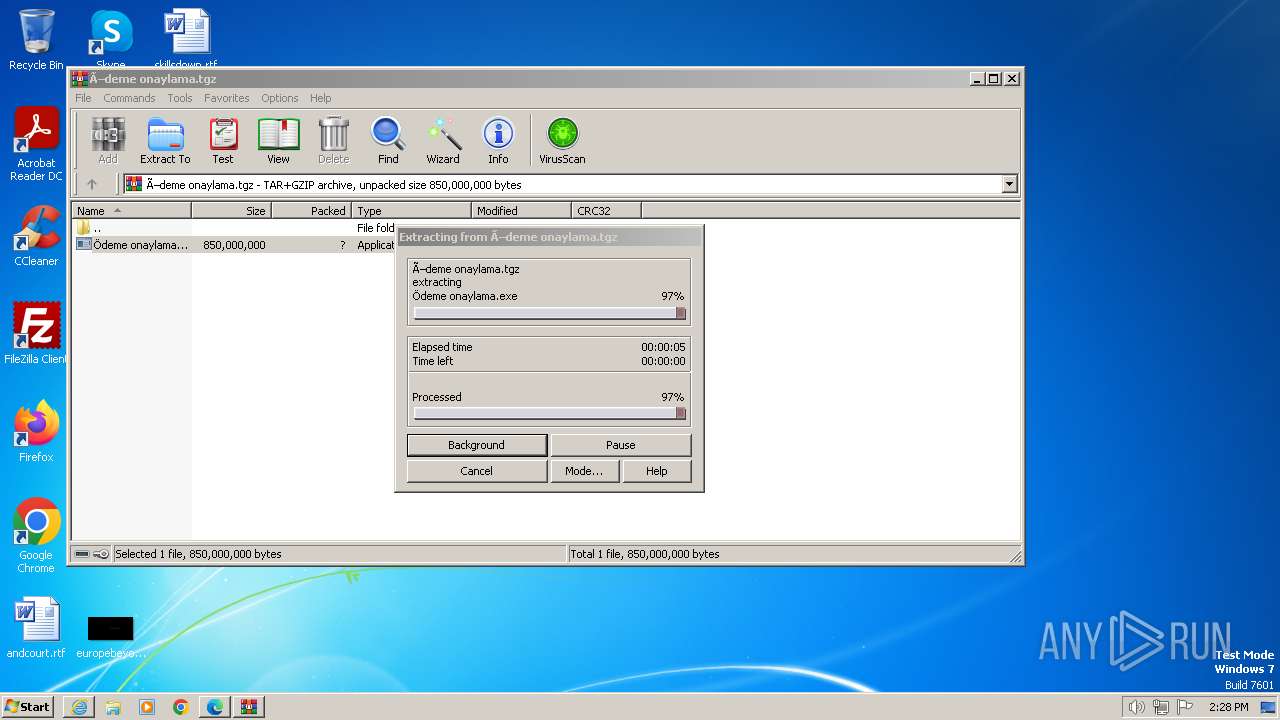
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | April 02, 2024, 13:27:19 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 454D515EDD281F5048241B8A9886E73D |
| SHA1: | 43096C3BCBFEEA2A117340C84C7DE001AA563130 |
| SHA256: | A0104F972502E702BBE70CD1B0C4579487D26B0937856E87117014CBCE251BFA |
| SSDEEP: | 3:N8DSLw3eGUoFdfQqBwBtAAFKpKzMO:2OLw3eGcpBMpKgO |
MALICIOUS
AGENTTESLA has been detected (YARA)
- Ödeme onaylama.exe (PID: 1236)
- Ödeme onaylama.exe (PID: 3984)
- Ödeme onaylama.exe (PID: 1288)
Steals credentials from Web Browsers
- Ödeme onaylama.exe (PID: 3984)
- Ödeme onaylama.exe (PID: 1288)
- Ödeme onaylama.exe (PID: 1236)
Actions looks like stealing of personal data
- Ödeme onaylama.exe (PID: 3984)
- Ödeme onaylama.exe (PID: 1288)
- Ödeme onaylama.exe (PID: 1236)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 2152)
- Ödeme onaylama.exe (PID: 1560)
- Ödeme onaylama.exe (PID: 2804)
- Ödeme onaylama.exe (PID: 3048)
Reads the Internet Settings
- Ödeme onaylama.exe (PID: 1560)
- Ödeme onaylama.exe (PID: 1236)
- Ödeme onaylama.exe (PID: 2804)
- Ödeme onaylama.exe (PID: 3984)
- Ödeme onaylama.exe (PID: 3048)
- Ödeme onaylama.exe (PID: 1288)
Application launched itself
- Ödeme onaylama.exe (PID: 1560)
- Ödeme onaylama.exe (PID: 2804)
- Ödeme onaylama.exe (PID: 3048)
Accesses Microsoft Outlook profiles
- Ödeme onaylama.exe (PID: 1236)
- Ödeme onaylama.exe (PID: 3984)
- Ödeme onaylama.exe (PID: 1288)
Reads settings of System Certificates
- Ödeme onaylama.exe (PID: 1236)
- Ödeme onaylama.exe (PID: 3984)
- Ödeme onaylama.exe (PID: 1288)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- Ödeme onaylama.exe (PID: 1236)
- Ödeme onaylama.exe (PID: 3984)
- Ödeme onaylama.exe (PID: 1288)
INFO
Modifies the phishing filter of IE
- iexplore.exe (PID: 3936)
Application launched itself
- iexplore.exe (PID: 3936)
- msedge.exe (PID: 2128)
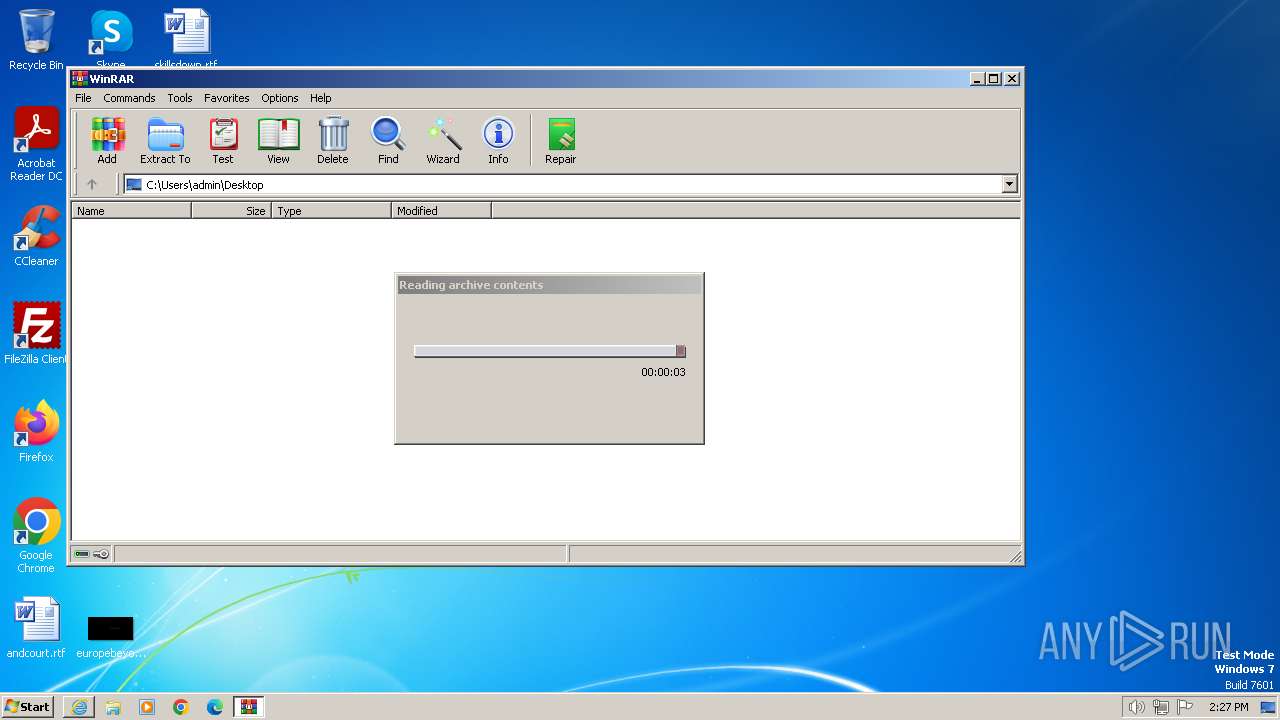
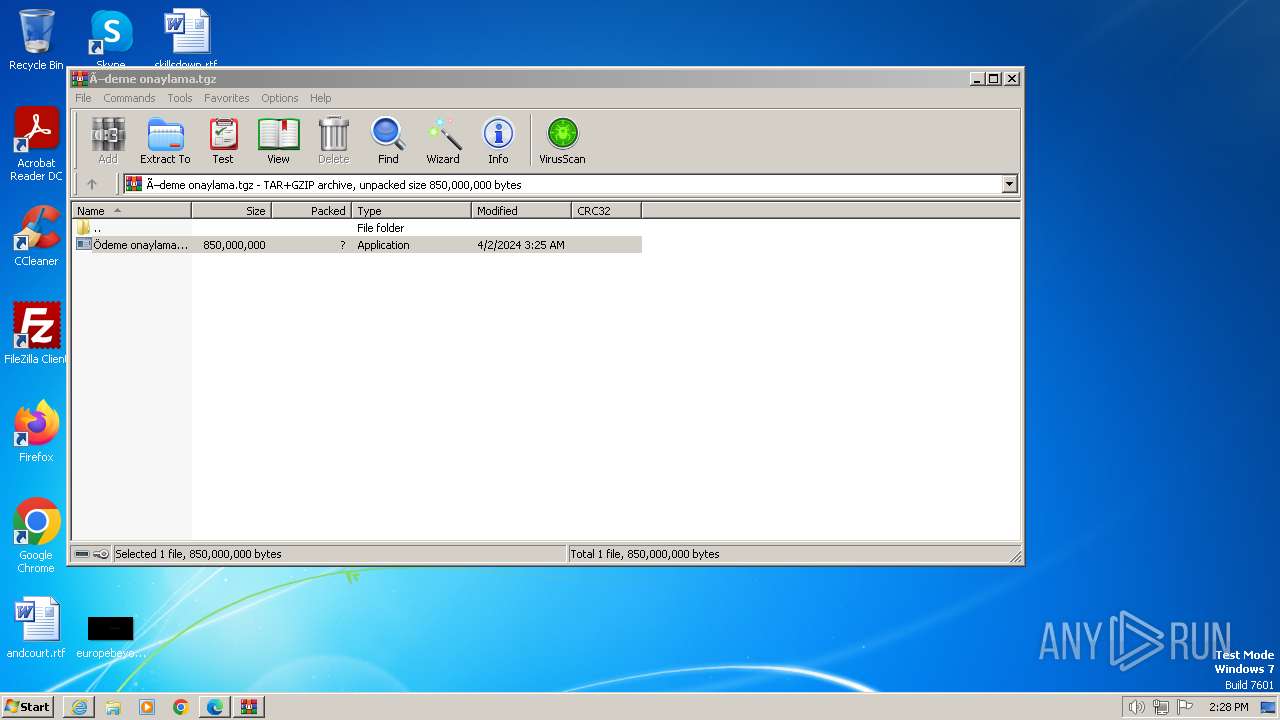
The process uses the downloaded file
- iexplore.exe (PID: 3936)
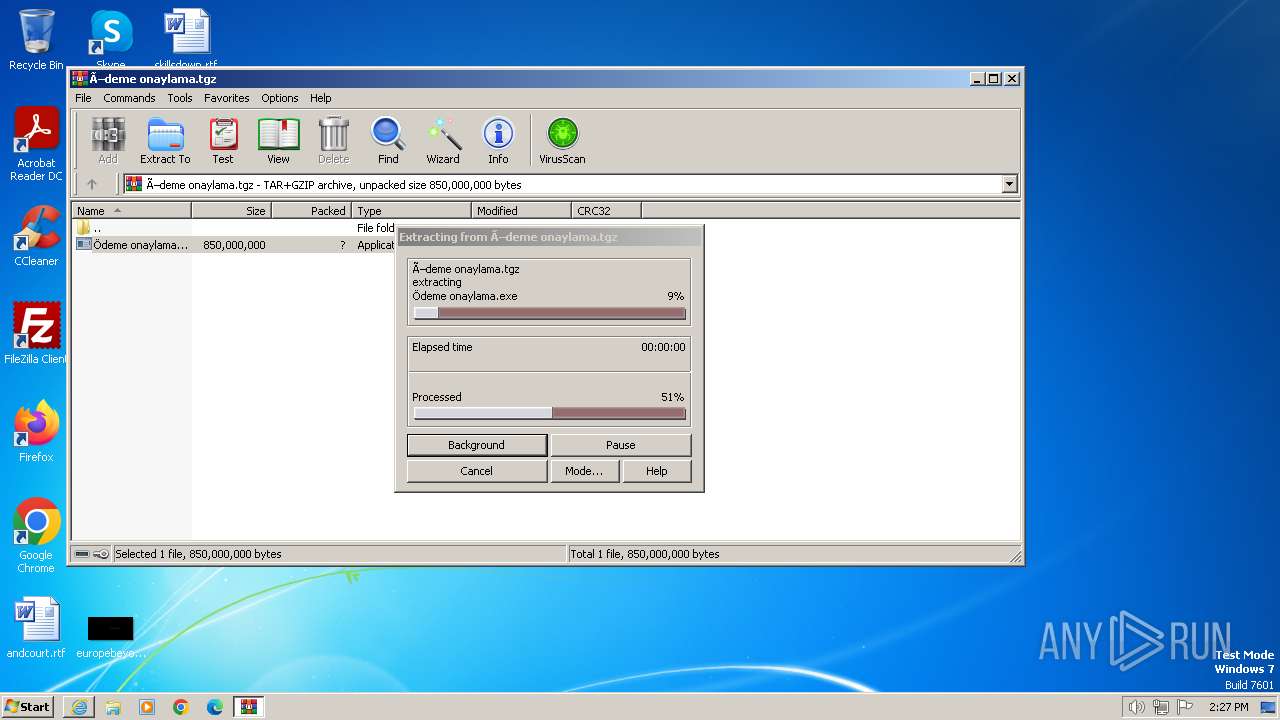
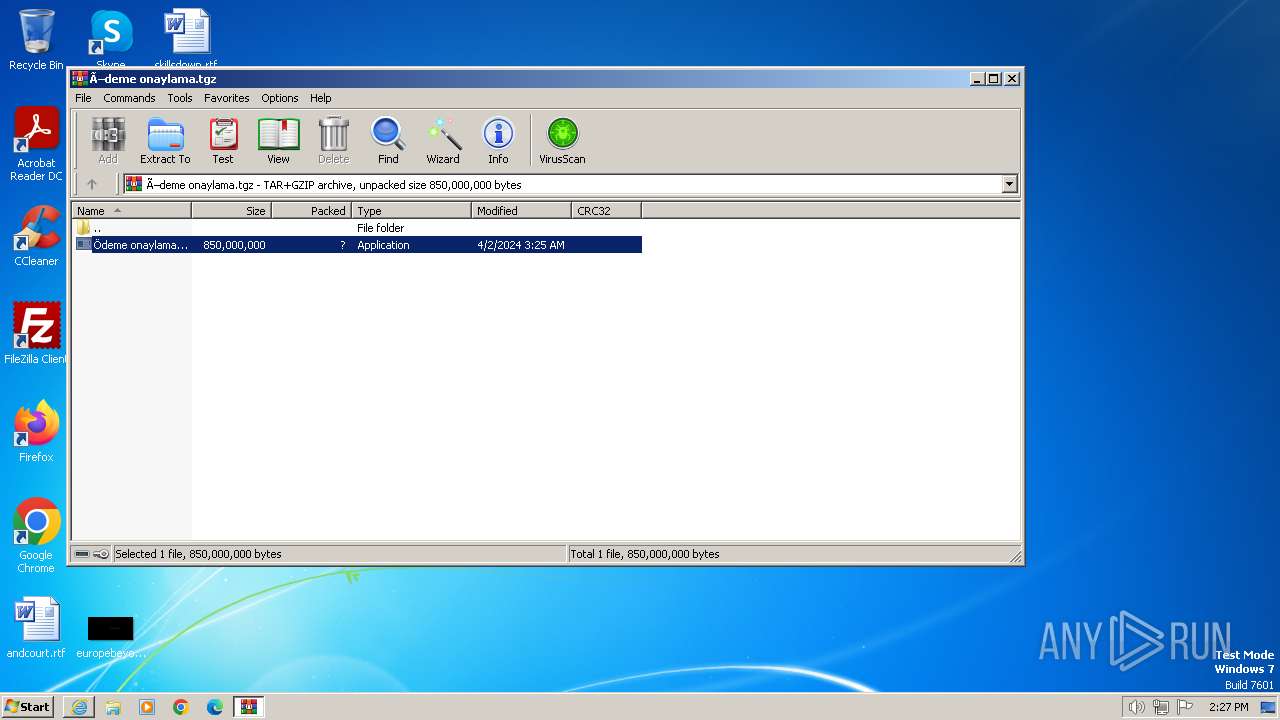
- WinRAR.exe (PID: 2152)
Checks supported languages
- Ödeme onaylama.exe (PID: 1560)
- Ödeme onaylama.exe (PID: 1236)
- Ödeme onaylama.exe (PID: 2804)
- Ödeme onaylama.exe (PID: 3984)
- Ödeme onaylama.exe (PID: 3048)
- Ödeme onaylama.exe (PID: 1288)
Reads the computer name
- Ödeme onaylama.exe (PID: 1560)
- Ödeme onaylama.exe (PID: 1236)
- Ödeme onaylama.exe (PID: 3048)
- Ödeme onaylama.exe (PID: 3984)
- Ödeme onaylama.exe (PID: 1288)
- Ödeme onaylama.exe (PID: 2804)
Reads the machine GUID from the registry
- Ödeme onaylama.exe (PID: 1560)
- Ödeme onaylama.exe (PID: 1236)
- Ödeme onaylama.exe (PID: 3984)
- Ödeme onaylama.exe (PID: 3048)
- Ödeme onaylama.exe (PID: 1288)
- Ödeme onaylama.exe (PID: 2804)
Reads Environment values
- Ödeme onaylama.exe (PID: 1236)
- Ödeme onaylama.exe (PID: 3984)
- Ödeme onaylama.exe (PID: 1288)
Reads the software policy settings
- Ödeme onaylama.exe (PID: 1236)
- Ödeme onaylama.exe (PID: 3984)
- Ödeme onaylama.exe (PID: 1288)
Manual execution by a user
- msedge.exe (PID: 2128)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
64
Monitored processes
27
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 784 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=1672 --field-trial-handle=1208,i,2606142895926852517,6615253079716849755,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 109.0.1518.115 Modules
| |||||||||||||||
| 920 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1524 --field-trial-handle=1208,i,2606142895926852517,6615253079716849755,131072 /prefetch:3 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 109.0.1518.115 Modules
| |||||||||||||||
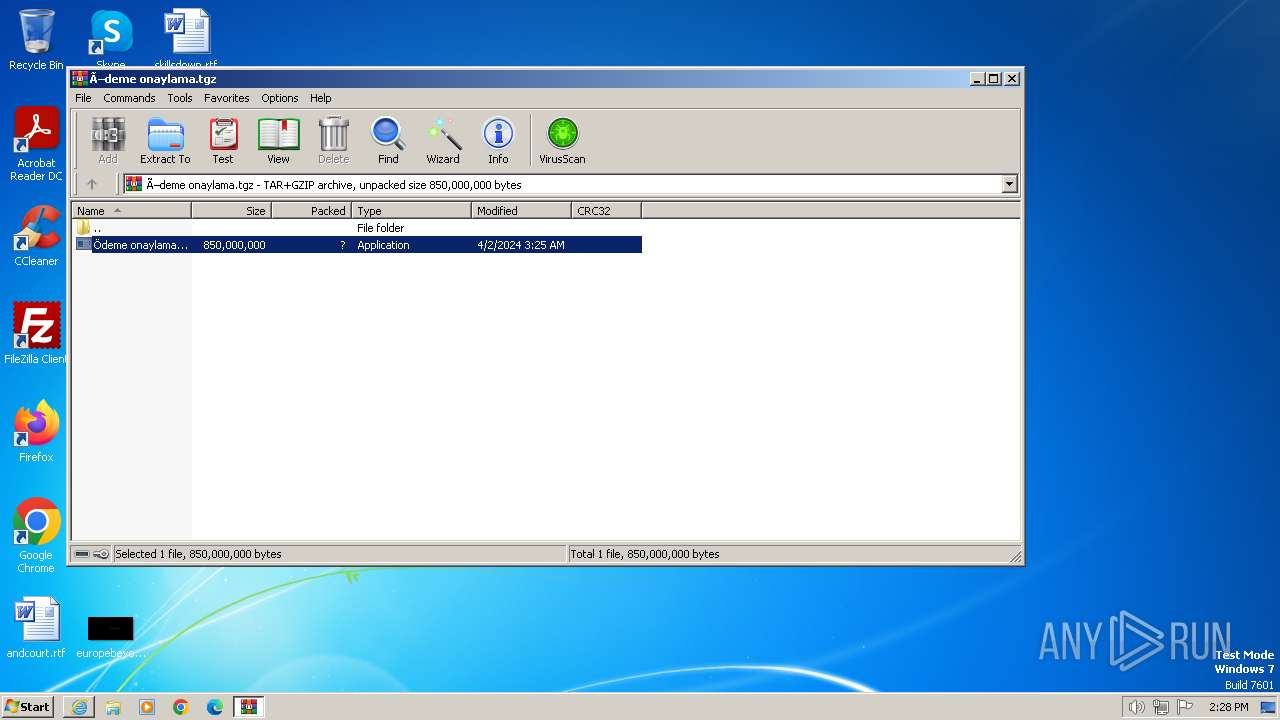
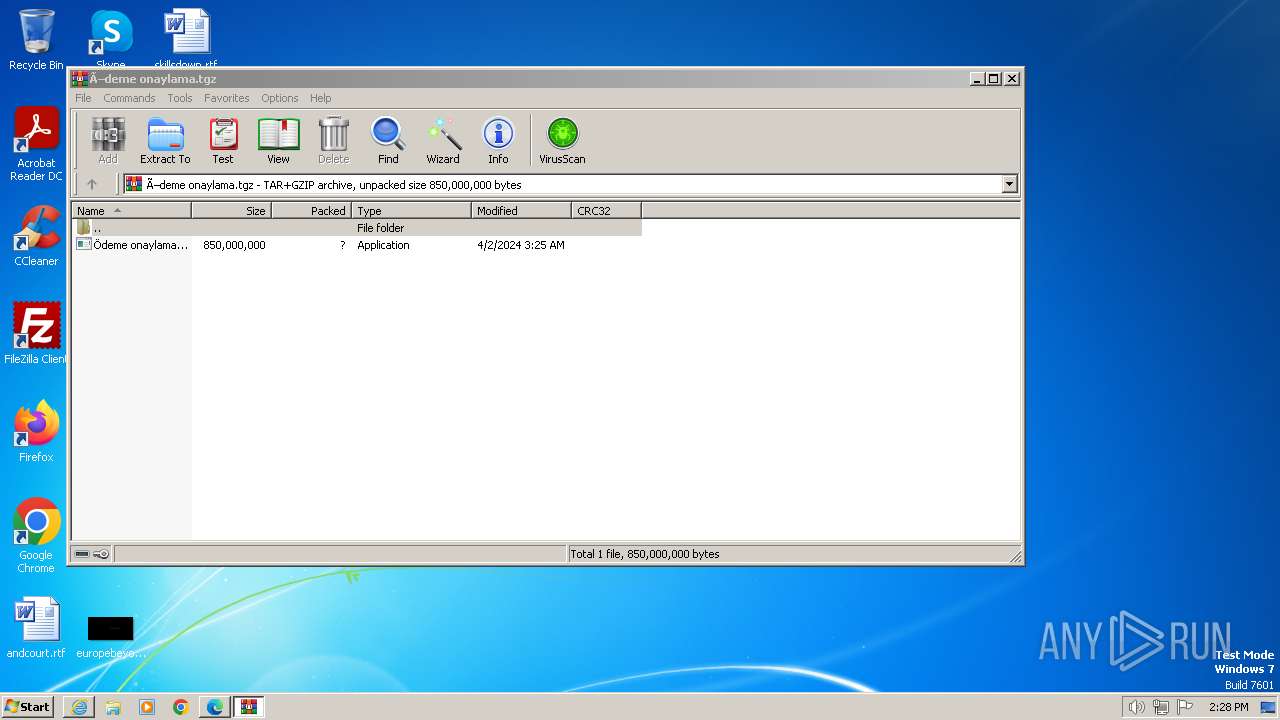
| 1112 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2152.44659\Ödeme onaylama.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2152.44659\Ödeme onaylama.exe | — | Ödeme onaylama.exe | |||||||||||
User: admin Company: Torus Integrity Level: MEDIUM Description: SimulationEngine Exit code: 4294967295 Version: 1.0.2.0 Modules
| |||||||||||||||
| 1236 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2152.44659\Ödeme onaylama.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2152.44659\Ödeme onaylama.exe | Ödeme onaylama.exe | ||||||||||||
User: admin Company: Torus Integrity Level: MEDIUM Description: SimulationEngine Exit code: 4294967295 Version: 1.0.2.0 Modules
| |||||||||||||||
| 1288 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2152.48794\Ödeme onaylama.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2152.48794\Ödeme onaylama.exe | Ödeme onaylama.exe | ||||||||||||
User: admin Company: Torus Integrity Level: MEDIUM Description: SimulationEngine Version: 1.0.2.0 Modules
| |||||||||||||||
| 1560 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2152.44659\Ödeme onaylama.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2152.44659\Ödeme onaylama.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Torus Integrity Level: MEDIUM Description: SimulationEngine Exit code: 0 Version: 1.0.2.0 Modules
| |||||||||||||||
| 1824 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=3496 --field-trial-handle=1208,i,2606142895926852517,6615253079716849755,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 2108 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1320 --field-trial-handle=1208,i,2606142895926852517,6615253079716849755,131072 /prefetch:2 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 2128 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --profile-directory=Default | C:\Program Files\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 109.0.1518.115 Modules
| |||||||||||||||
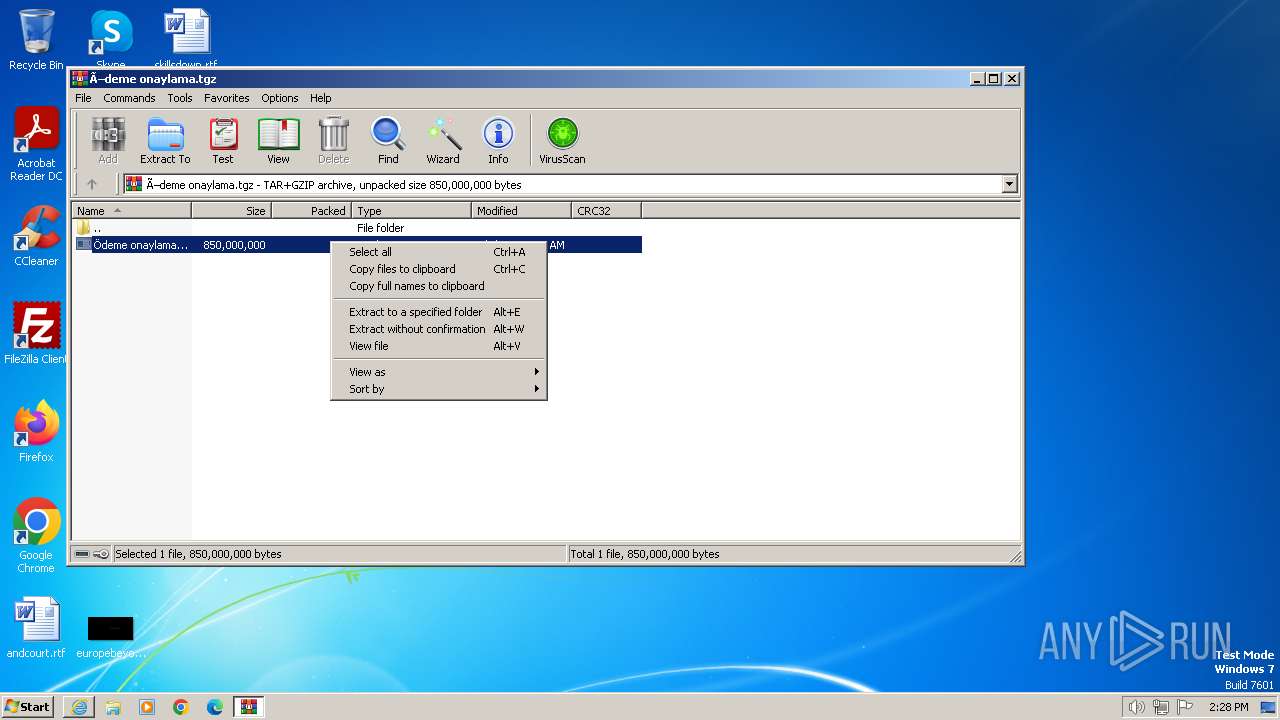
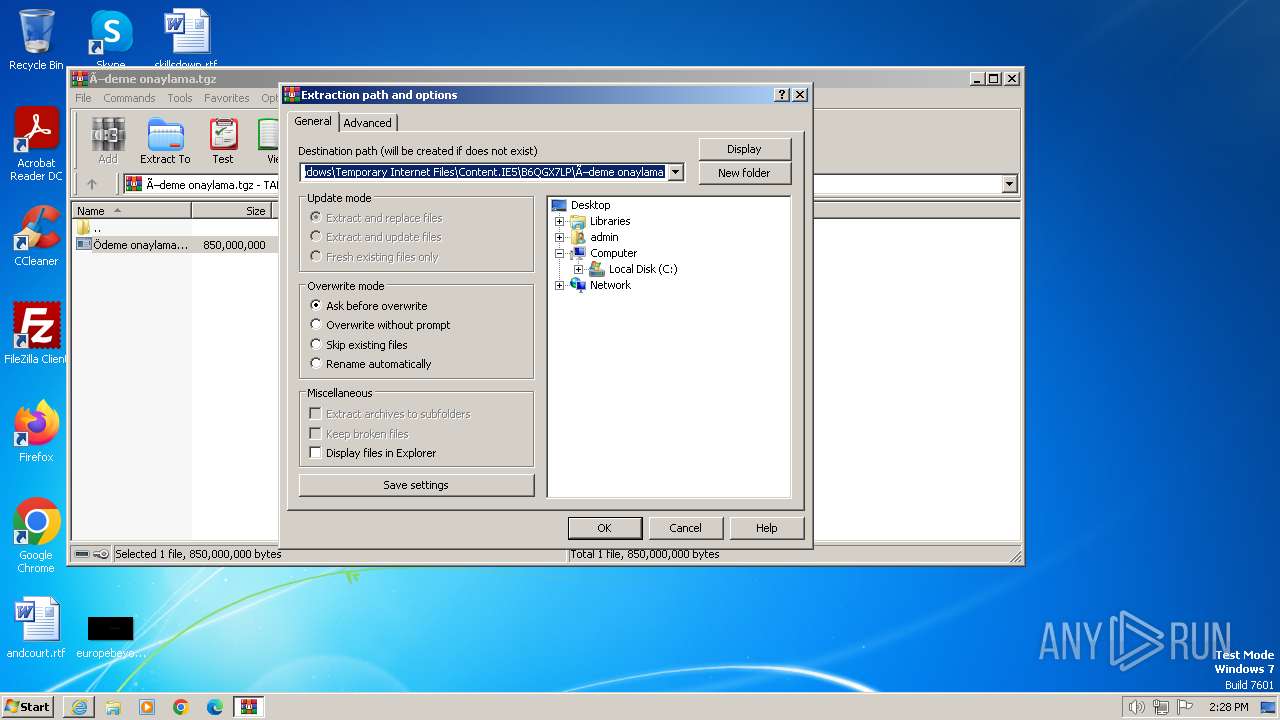
| 2152 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\Ödeme onaylama.tgz" | C:\Program Files\WinRAR\WinRAR.exe | — | iexplore.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
Total events
52 055
Read events
51 764
Write events
223
Delete events
68
Modification events
| (PID) Process: | (3936) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3936) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3936) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 31098113 | |||
| (PID) Process: | (3936) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3936) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31098113 | |||
| (PID) Process: | (3936) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3936) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3936) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3936) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3936) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
19
Suspicious files
20
Text files
49
Unknown types
197
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2572 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 2572 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | binary | |
MD5:— | SHA256:— | |||
| 2572 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | binary | |
MD5:— | SHA256:— | |||
| 2572 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\07CEF2F654E3ED6050FFC9B6EB844250_BACC6CD2B29F18349081C9FD2343833B | binary | |
MD5:— | SHA256:— | |||
| 2572 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\07CEF2F654E3ED6050FFC9B6EB844250_BACC6CD2B29F18349081C9FD2343833B | binary | |
MD5:— | SHA256:— | |||
| 2572 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\B4IJF2UR.txt | text | |
MD5:— | SHA256:— | |||
| 2572 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\K8MSRD7U.txt | text | |
MD5:— | SHA256:— | |||
| 2572 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\72BA427A91F50409B9EAC87F2B59B951_8FD6BB79A5EEF06F3F8595CB48A9AB04 | binary | |
MD5:— | SHA256:— | |||
| 2572 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\72BA427A91F50409B9EAC87F2B59B951_8FD6BB79A5EEF06F3F8595CB48A9AB04 | binary | |
MD5:— | SHA256:— | |||
| 2572 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\Ödeme onaylama[1].tgz | compressed | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
51
DNS requests
63
Threats
12
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2572 | iexplore.exe | GET | 304 | 87.248.202.1:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?5259f1aa84763c8c | unknown | — | — | unknown |
2572 | iexplore.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQh80WaEMqmyEvaHjlisSfVM4p8SAQUF9nWJSdn%2BTHCSUPZMDZEjGypT%2BsCED%2B0KeRQ8NP60VP53TIby3A%3D | unknown | — | — | unknown |
2572 | iexplore.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEBN9U5yqfDGppDNwGWiEeo0%3D | unknown | — | — | unknown |
1080 | svchost.exe | GET | 304 | 87.248.204.0:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?e90c163b6659448e | unknown | — | — | unknown |
3936 | iexplore.exe | GET | 304 | 87.248.204.0:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?719f0b64dcb4a601 | unknown | — | — | unknown |
3936 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | unknown |
3936 | iexplore.exe | GET | 304 | 87.248.204.0:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?3ffc3fbc5b315e52 | unknown | — | — | unknown |
3936 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEALnkXH7gCHpP%2BLZg4NMUMA%3D | unknown | — | — | unknown |
1080 | svchost.exe | GET | 200 | 87.248.204.0:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?1b8fee253118cbef | unknown | — | — | unknown |
3936 | iexplore.exe | GET | 304 | 87.248.204.0:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?31055eca6ea3b32e | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2572 | iexplore.exe | 104.16.113.74:443 | www.mediafire.com | CLOUDFLARENET | — | unknown |
2572 | iexplore.exe | 87.248.202.1:80 | ctldl.windowsupdate.com | LLNW | NL | unknown |
2572 | iexplore.exe | 104.18.38.233:80 | ocsp.comodoca.com | CLOUDFLARENET | — | shared |
2572 | iexplore.exe | 172.64.149.23:80 | ocsp.comodoca.com | CLOUDFLARENET | US | unknown |
2572 | iexplore.exe | 199.91.155.131:443 | download2390.mediafire.com | MEDIAFIRE | US | unknown |
1080 | svchost.exe | 87.248.204.0:80 | ctldl.windowsupdate.com | LLNW | US | unknown |
3936 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.mediafire.com |
| shared |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
download2390.mediafire.com |
| unknown |
ocsp.sectigo.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
api.telegram.org |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
1080 | svchost.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
1080 | svchost.exe | Misc activity | ET HUNTING Telegram API Domain in DNS Lookup |
1236 | Ödeme onaylama.exe | Misc activity | ET HUNTING Observed Telegram API Domain (api .telegram .org in TLS SNI) |
1236 | Ödeme onaylama.exe | Misc activity | ET HUNTING Telegram API Certificate Observed |
— | — | Successful Credential Theft Detected | STEALER [ANY.RUN] Attempt to exfiltrate via Telegram |
3984 | Ödeme onaylama.exe | Misc activity | ET HUNTING Observed Telegram API Domain (api .telegram .org in TLS SNI) |
3984 | Ödeme onaylama.exe | Misc activity | ET HUNTING Telegram API Certificate Observed |
— | — | Successful Credential Theft Detected | STEALER [ANY.RUN] Attempt to exfiltrate via Telegram |
1288 | Ödeme onaylama.exe | Misc activity | ET HUNTING Observed Telegram API Domain (api .telegram .org in TLS SNI) |