| File name: | 2025-07-24_c47a0a11ea531538911ed1a133c30b11_chaos_destroyer_elex_wannacry.exe |
| Full analysis: | https://app.any.run/tasks/db3d2c50-a85e-488b-a8d3-4a06343220fa |
| Verdict: | Malicious activity |
| Threats: | Chaos ransomware is a malware family known for its destructive capabilities and diverse variants. It first appeared in 2021 as a ransomware builder and later acted as a wiper. Unlike most ransomware strains that encrypt data to extort payment, early Chaos variants permanently corrupted files, while later versions adopted more conventional encryption techniques. |
| Analysis date: | July 24, 2025, 18:44:57 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | C47A0A11EA531538911ED1A133C30B11 |
| SHA1: | 2A322BEED33ACB7119C7D994F38AF61C14849E3F |
| SHA256: | A00371F49FAC49C7F5A5A92E61F8639CF0B52E7B0906DC2F8AD7847E0C0108B1 |
| SSDEEP: | 384:eh9yeBxz0zoaeBZBxdDjhCCTh3gJciDr91CkaExmrGD3:nkxz0zoa45dxCsh3Itr9xa3rM |
MALICIOUS
Create files in the Startup directory
- dread_is_here.exe (PID: 4400)
RYUK (CHAOS) has been detected (YARA)
- dread_is_here.exe (PID: 4400)
RANSOMWARE has been detected
- dread_is_here.exe (PID: 4400)
SUSPICIOUS
Reads security settings of Internet Explorer
- 2025-07-24_c47a0a11ea531538911ed1a133c30b11_chaos_destroyer_elex_wannacry.exe (PID: 3736)
- dread_is_here.exe (PID: 4400)
Executable content was dropped or overwritten
- 2025-07-24_c47a0a11ea531538911ed1a133c30b11_chaos_destroyer_elex_wannacry.exe (PID: 3736)
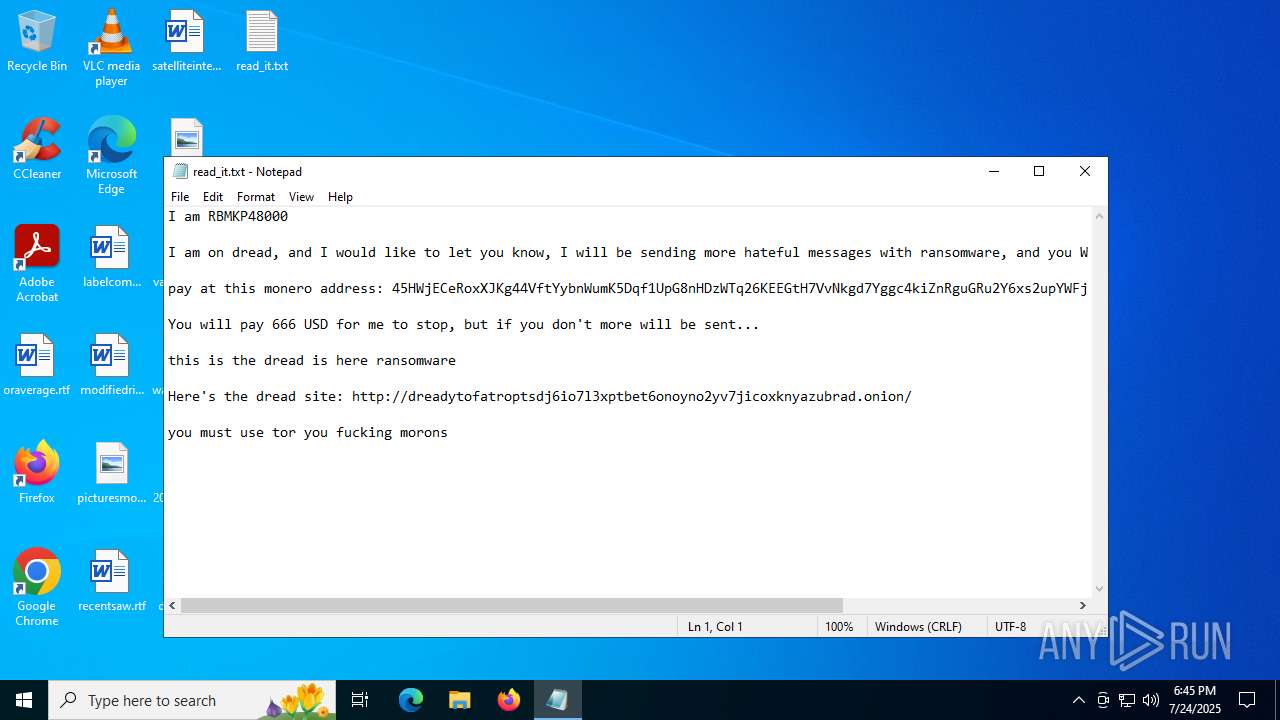
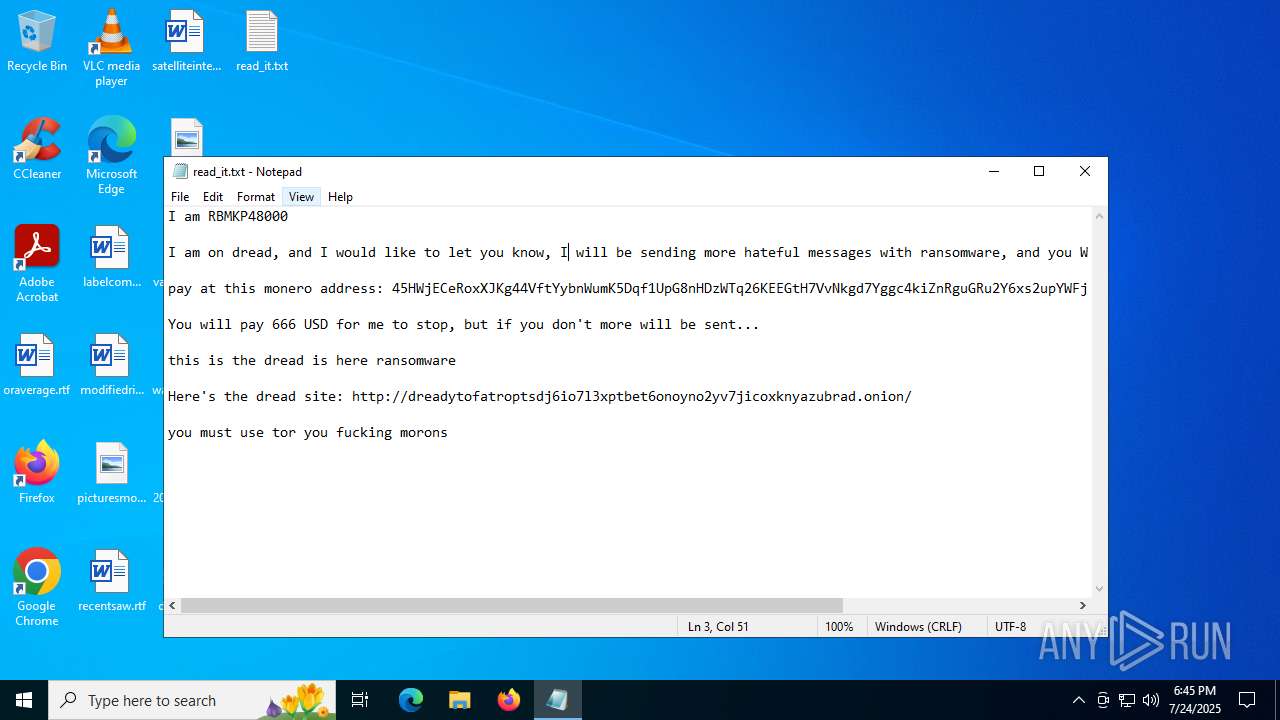
Start notepad (likely ransomware note)
- dread_is_here.exe (PID: 4400)
Reads the date of Windows installation
- dread_is_here.exe (PID: 4400)
- 2025-07-24_c47a0a11ea531538911ed1a133c30b11_chaos_destroyer_elex_wannacry.exe (PID: 3736)
Found regular expressions for crypto-addresses (YARA)
- dread_is_here.exe (PID: 4400)
Starts itself from another location
- 2025-07-24_c47a0a11ea531538911ed1a133c30b11_chaos_destroyer_elex_wannacry.exe (PID: 3736)
INFO
Reads the computer name
- 2025-07-24_c47a0a11ea531538911ed1a133c30b11_chaos_destroyer_elex_wannacry.exe (PID: 3736)
- dread_is_here.exe (PID: 4400)
Checks supported languages
- 2025-07-24_c47a0a11ea531538911ed1a133c30b11_chaos_destroyer_elex_wannacry.exe (PID: 3736)
- dread_is_here.exe (PID: 4400)
Creates files or folders in the user directory
- 2025-07-24_c47a0a11ea531538911ed1a133c30b11_chaos_destroyer_elex_wannacry.exe (PID: 3736)
- dread_is_here.exe (PID: 4400)
Launching a file from the Startup directory
- dread_is_here.exe (PID: 4400)
Reads Microsoft Office registry keys
- dread_is_here.exe (PID: 4400)
Reads the machine GUID from the registry
- dread_is_here.exe (PID: 4400)
Process checks computer location settings
- dread_is_here.exe (PID: 4400)
- 2025-07-24_c47a0a11ea531538911ed1a133c30b11_chaos_destroyer_elex_wannacry.exe (PID: 3736)
Reads security settings of Internet Explorer
- notepad.exe (PID: 3100)
Checks proxy server information
- slui.exe (PID: 6648)
Reads the software policy settings
- slui.exe (PID: 6648)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:07:24 09:11:20+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 19968 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x6cbe |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | |
| FileVersion: | 0.0.0.0 |
| InternalName: | nrpsrv.exe |
| LegalCopyright: | |
| OriginalFileName: | nrpsrv.exe |
| ProductVersion: | 0.0.0.0 |
| AssemblyVersion: | 0.0.0.0 |
Total processes
135
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3100 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Roaming\read_it.txt | C:\Windows\System32\notepad.exe | — | dread_is_here.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3736 | "C:\Users\admin\Desktop\2025-07-24_c47a0a11ea531538911ed1a133c30b11_chaos_destroyer_elex_wannacry.exe" | C:\Users\admin\Desktop\2025-07-24_c47a0a11ea531538911ed1a133c30b11_chaos_destroyer_elex_wannacry.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 1 Version: 0.0.0.0 Modules
| |||||||||||||||
| 4400 | "C:\Users\admin\AppData\Roaming\dread_is_here.exe" | C:\Users\admin\AppData\Roaming\dread_is_here.exe | 2025-07-24_c47a0a11ea531538911ed1a133c30b11_chaos_destroyer_elex_wannacry.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Version: 0.0.0.0 Modules
| |||||||||||||||
| 6648 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
4 614
Read events
4 613
Write events
1
Delete events
0
Modification events
| (PID) Process: | (4400) dread_is_here.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.txt\OpenWithProgids |
| Operation: | write | Name: | txtfile |
Value: | |||
Executable files
1
Suspicious files
0
Text files
88
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3736 | 2025-07-24_c47a0a11ea531538911ed1a133c30b11_chaos_destroyer_elex_wannacry.exe | C:\Users\admin\AppData\Roaming\dread_is_here.exe | executable | |
MD5:C47A0A11EA531538911ED1A133C30B11 | SHA256:A00371F49FAC49C7F5A5A92E61F8639CF0B52E7B0906DC2F8AD7847E0C0108B1 | |||
| 4400 | dread_is_here.exe | C:\Users\admin\Documents\OneNote Notebooks\My Notebook\read_it.txt | text | |
MD5:AFABD76E0DF374E7D85AF08891ECAC56 | SHA256:FF278748C688E82F7D0714B3B59C99FDD2888DE91EFB984B36748BC2020907AF | |||
| 4400 | dread_is_here.exe | C:\Users\admin\Pictures\Saved Pictures\read_it.txt | text | |
MD5:AFABD76E0DF374E7D85AF08891ECAC56 | SHA256:FF278748C688E82F7D0714B3B59C99FDD2888DE91EFB984B36748BC2020907AF | |||
| 4400 | dread_is_here.exe | C:\Users\admin\Links\read_it.txt | text | |
MD5:AFABD76E0DF374E7D85AF08891ECAC56 | SHA256:FF278748C688E82F7D0714B3B59C99FDD2888DE91EFB984B36748BC2020907AF | |||
| 4400 | dread_is_here.exe | C:\Users\admin\Pictures\read_it.txt | text | |
MD5:AFABD76E0DF374E7D85AF08891ECAC56 | SHA256:FF278748C688E82F7D0714B3B59C99FDD2888DE91EFB984B36748BC2020907AF | |||
| 4400 | dread_is_here.exe | C:\Users\admin\OneDrive\read_it.txt | text | |
MD5:AFABD76E0DF374E7D85AF08891ECAC56 | SHA256:FF278748C688E82F7D0714B3B59C99FDD2888DE91EFB984B36748BC2020907AF | |||
| 4400 | dread_is_here.exe | C:\Users\admin\Downloads\read_it.txt | text | |
MD5:AFABD76E0DF374E7D85AF08891ECAC56 | SHA256:FF278748C688E82F7D0714B3B59C99FDD2888DE91EFB984B36748BC2020907AF | |||
| 4400 | dread_is_here.exe | C:\Users\admin\Pictures\Camera Roll\read_it.txt | text | |
MD5:AFABD76E0DF374E7D85AF08891ECAC56 | SHA256:FF278748C688E82F7D0714B3B59C99FDD2888DE91EFB984B36748BC2020907AF | |||
| 4400 | dread_is_here.exe | C:\Users\admin\Music\read_it.txt | text | |
MD5:AFABD76E0DF374E7D85AF08891ECAC56 | SHA256:FF278748C688E82F7D0714B3B59C99FDD2888DE91EFB984B36748BC2020907AF | |||
| 4400 | dread_is_here.exe | C:\Users\admin\Saved Games\read_it.txt | text | |
MD5:AFABD76E0DF374E7D85AF08891ECAC56 | SHA256:FF278748C688E82F7D0714B3B59C99FDD2888DE91EFB984B36748BC2020907AF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
18
DNS requests
7
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | GET | 200 | 23.55.110.211:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.55.110.211:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4552 | RUXIMICS.exe | GET | 200 | 23.55.110.211:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4552 | RUXIMICS.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | POST | 500 | 20.83.72.98:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
— | — | POST | 500 | 40.91.76.224:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4552 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 23.55.110.211:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 23.55.110.211:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4552 | RUXIMICS.exe | 23.55.110.211:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
4552 | RUXIMICS.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |