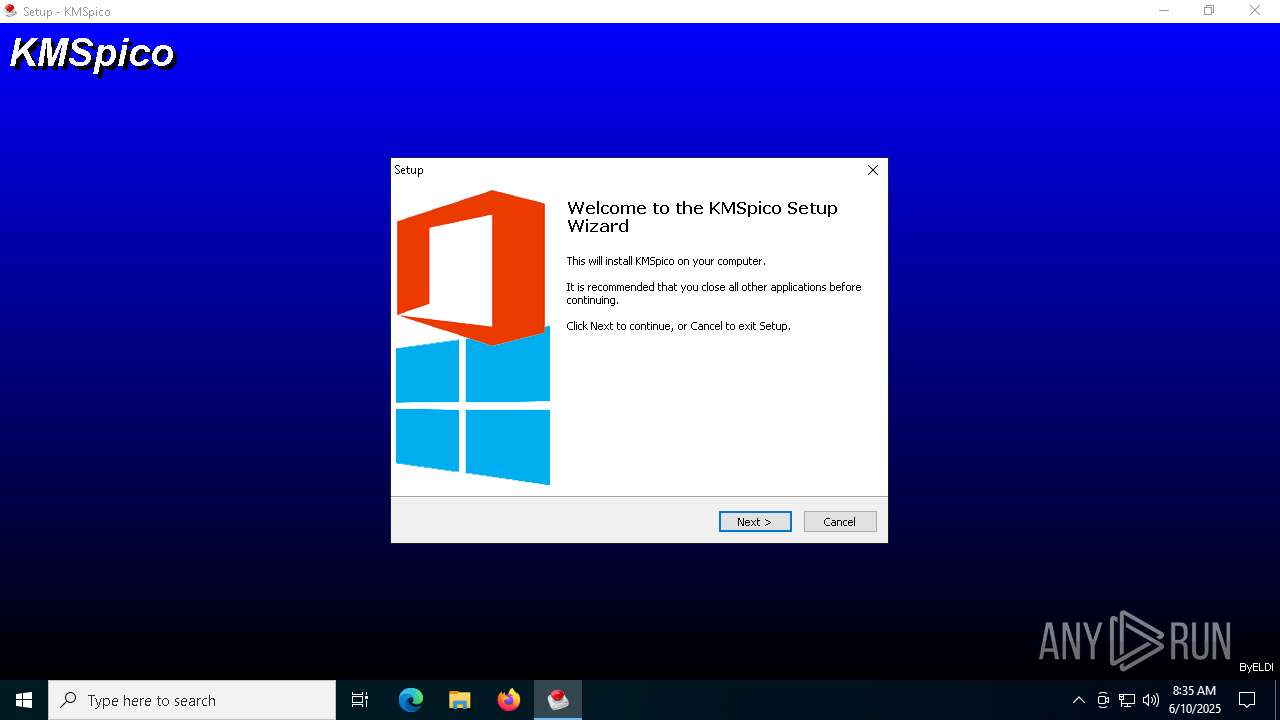
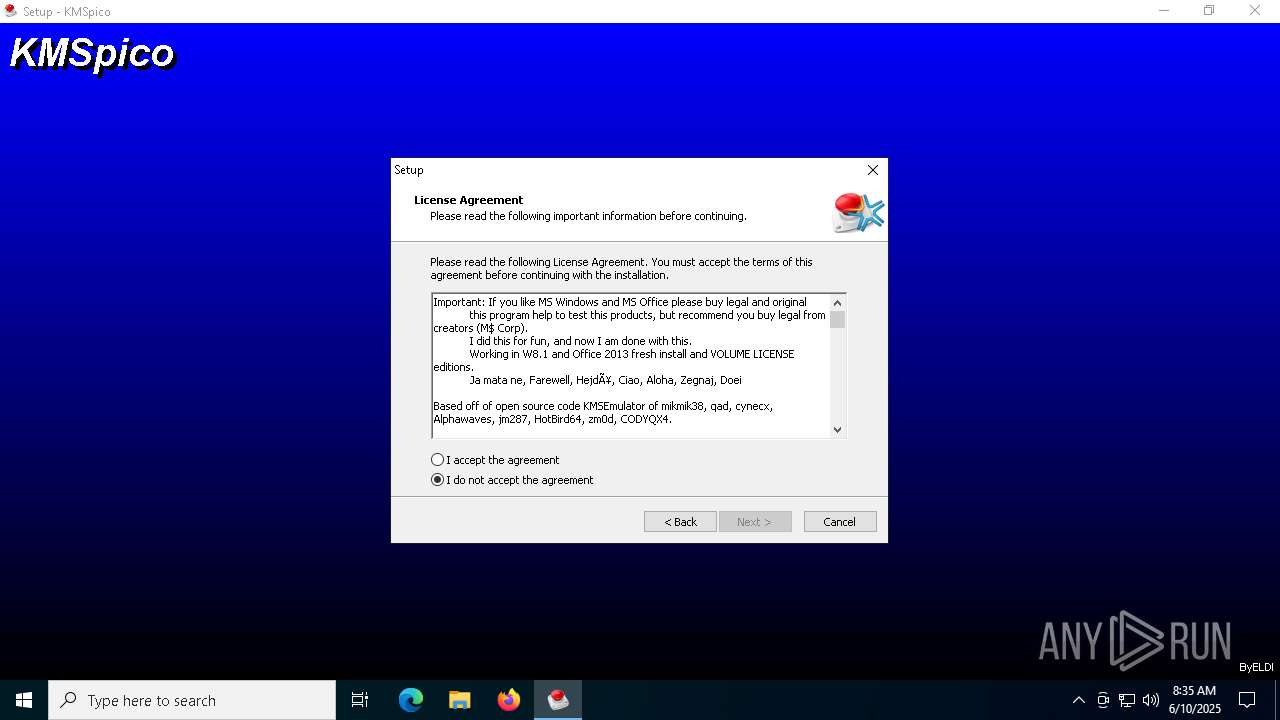
| File name: | KMSpico.exe |
| Full analysis: | https://app.any.run/tasks/29c47524-4193-403b-82e4-f8762f6e5c02 |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | June 10, 2025, 08:34:51 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 11 sections |
| MD5: | DAC0515E1FC09F2DA42C53DF3E1EB64C |
| SHA1: | 89E2EE9EFC3228627360AEFDE2CB77501F3B56A1 |
| SHA256: | 9FFBF85A2AED26C4A20BDD85FDB490F53071EB5CE73291BF71930D7BB6E1E93B |
| SSDEEP: | 98304:H6Gavilkmy6ZD/ejjm1+CBviv+0x+ctRYeJ84wr/AYrvy48MnYbY2bz0JqB6yrqE:4hWaE5sV0hrAr6rM07q |
MALICIOUS
GENERIC has been found (auto)
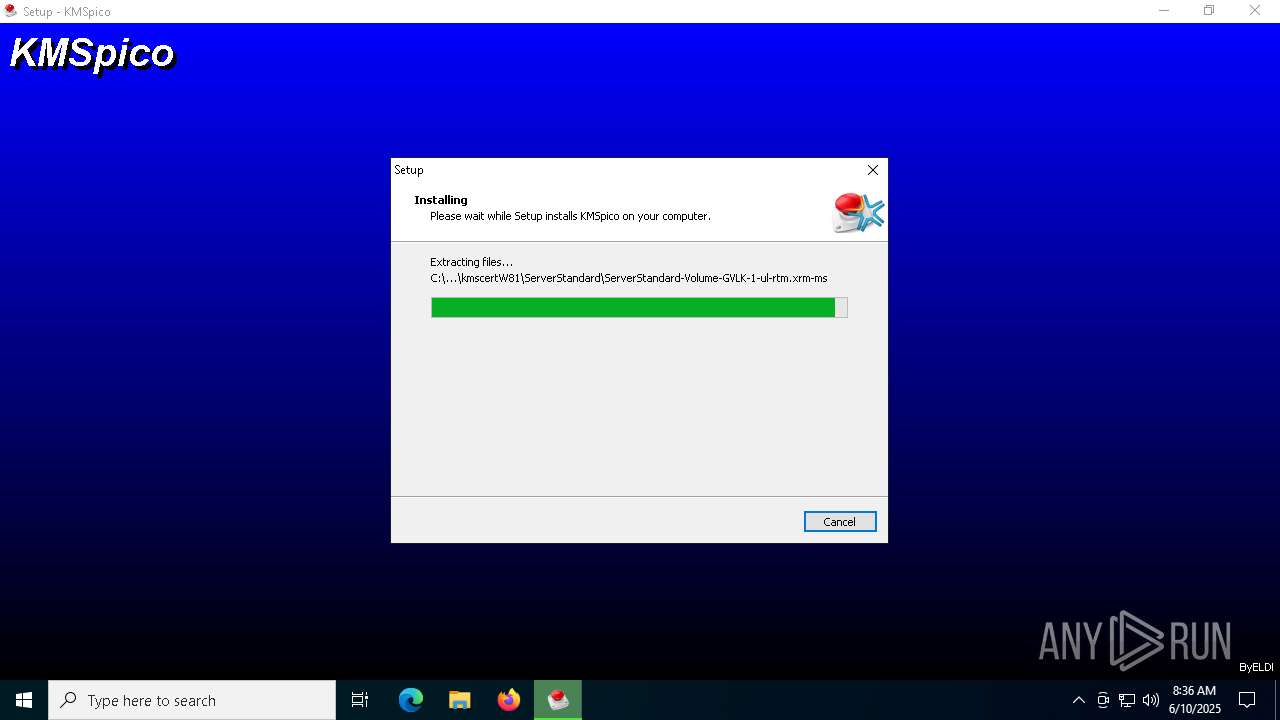
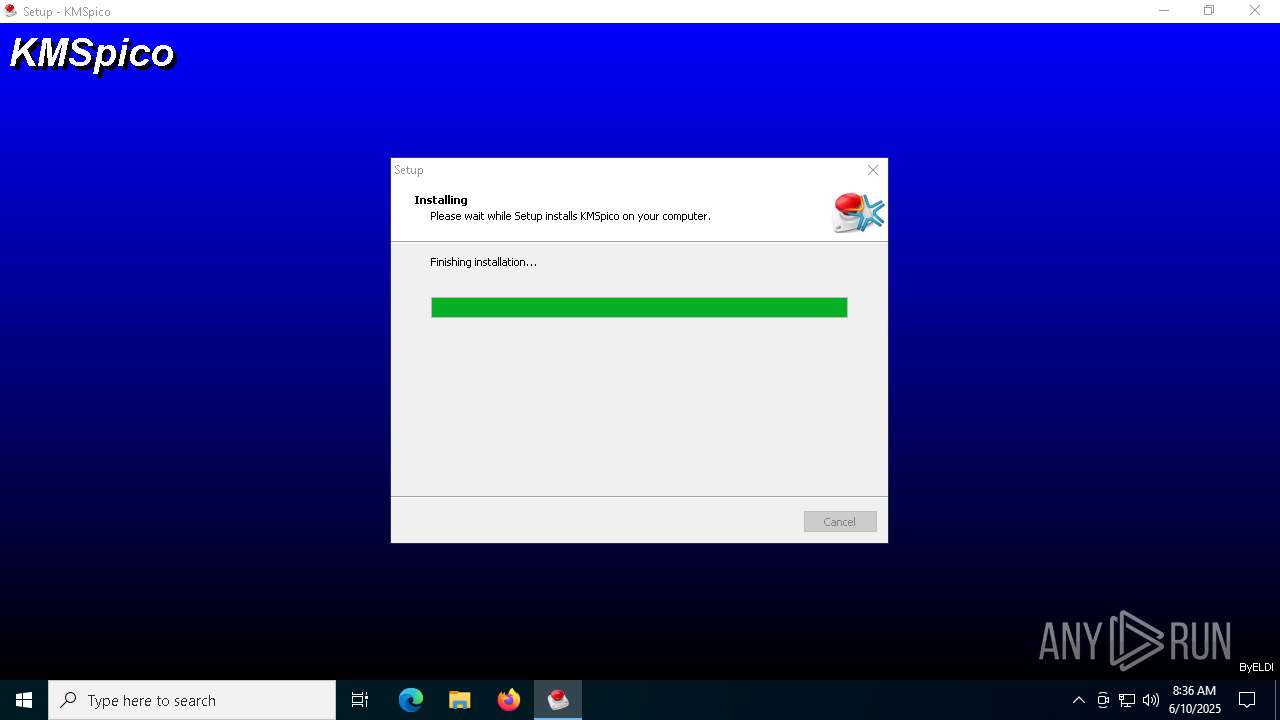
- KMSpico.tmp (PID: 2332)
Executing a file with an untrusted certificate
- KMSpico.exe (PID: 1696)
- KMSpico.exe (PID: 6476)
- KMSELDI.exe (PID: 7964)
- AutoPico.exe (PID: 1680)
Connects to the CnC server
- svchost.exe (PID: 2196)
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2196)
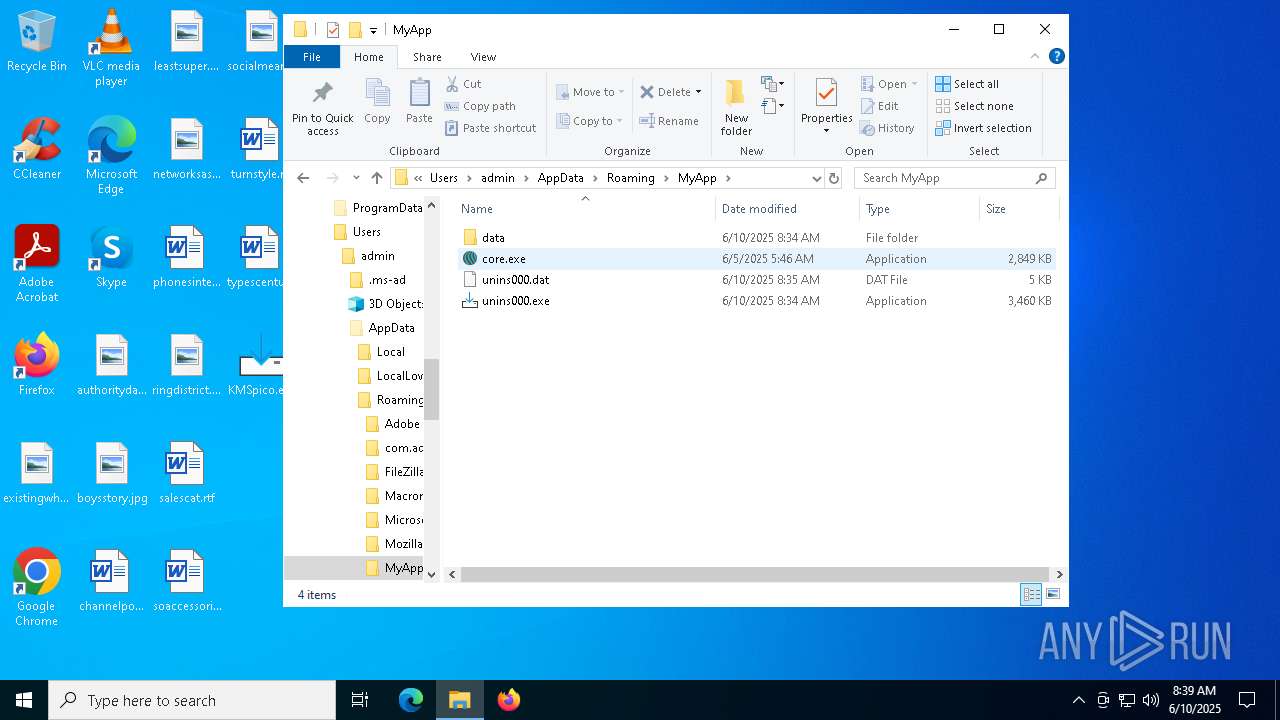
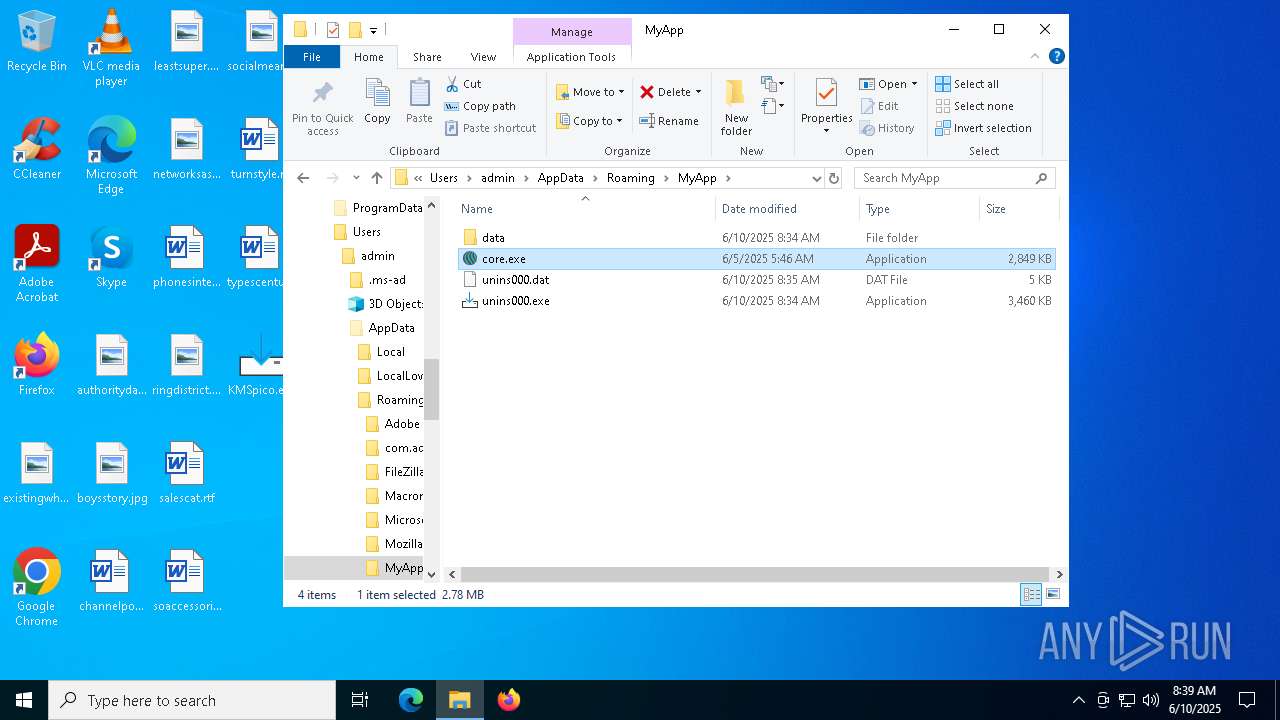
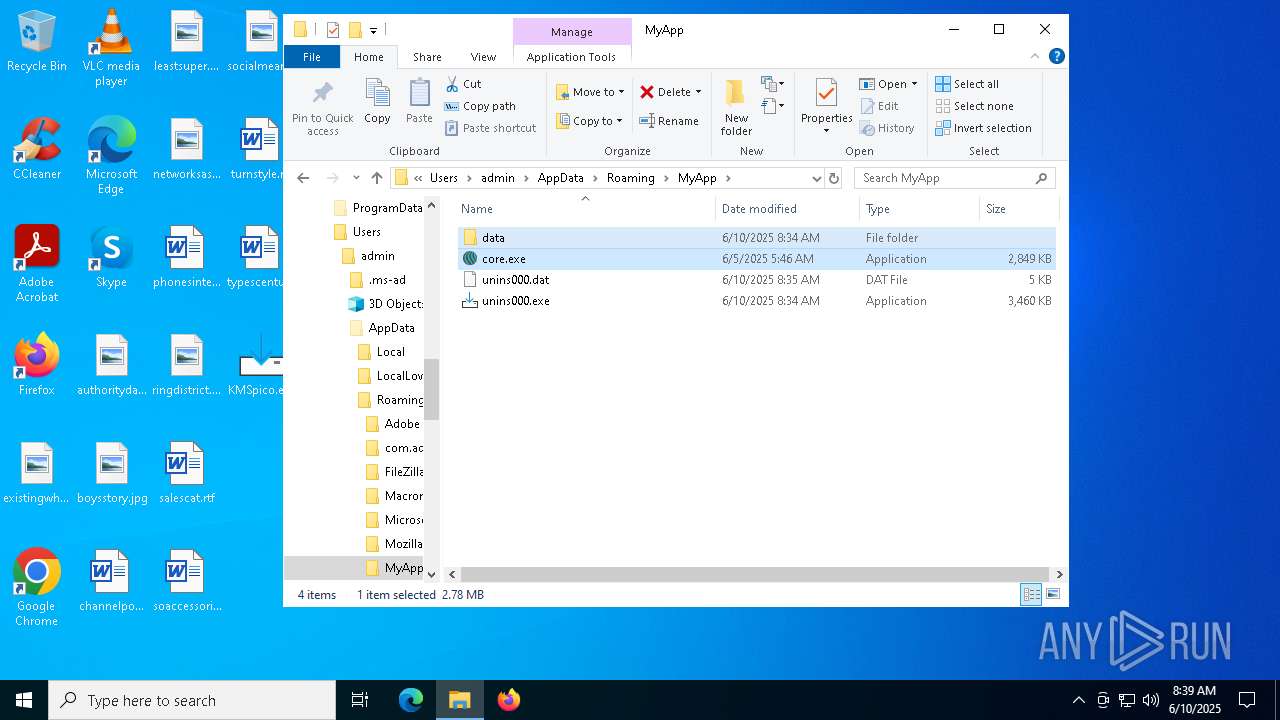
- core.exe (PID: 7316)
- core.exe (PID: 7560)
Steals credentials from Web Browsers
- core.exe (PID: 7316)
LUMMA mutex has been found
- core.exe (PID: 7316)
Actions looks like stealing of personal data
- core.exe (PID: 7316)
Changes image file execution options
- KMSELDI.exe (PID: 7964)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 6852)
SUSPICIOUS
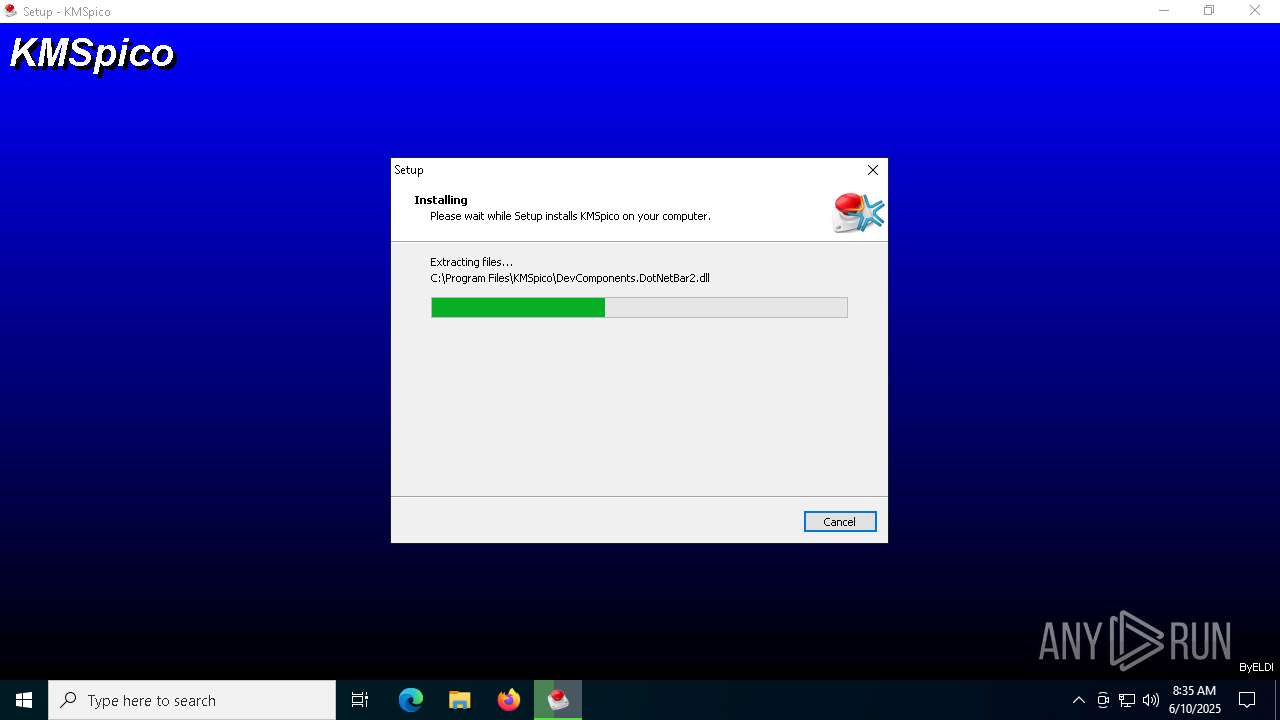
Executable content was dropped or overwritten
- KMSpico.exe (PID: 6816)
- KMSpico.tmp (PID: 2332)
- KMSpico.exe (PID: 1696)
- KMSpico.exe (PID: 6476)
- KMSpico.tmp (PID: 3268)
- KMSELDI.exe (PID: 7964)
Reads the Windows owner or organization settings
- KMSpico.tmp (PID: 2332)
- KMSpico.tmp (PID: 3268)
Reads security settings of Internet Explorer
- KMSpico.tmp (PID: 2332)
- KMSpico.tmp (PID: 4700)
Process drops legitimate windows executable
- KMSpico.tmp (PID: 3268)
Contacting a server suspected of hosting an CnC
- svchost.exe (PID: 2196)
- core.exe (PID: 7316)
- core.exe (PID: 7560)
Modifies the phishing filter of IE
- KMSpico.tmp (PID: 3268)
Executing commands from ".cmd" file
- KMSpico.tmp (PID: 3268)
Starts CMD.EXE for commands execution
- KMSpico.tmp (PID: 3268)
Creates a new Windows service
- sc.exe (PID: 6184)
Searches for installed software
- core.exe (PID: 7316)
Starts SC.EXE for service management
- cmd.exe (PID: 4976)
INFO
Checks supported languages
- KMSpico.exe (PID: 6816)
- KMSpico.tmp (PID: 2332)
- KMSpico.exe (PID: 1696)
- core.exe (PID: 7316)
- KMSpico.tmp (PID: 3268)
- KMSpico.tmp (PID: 4700)
- KMSpico.exe (PID: 6476)
- UninsHs.exe (PID: 5640)
- KMSELDI.exe (PID: 7964)
- SECOH-QAD.exe (PID: 4920)
Create files in a temporary directory
- KMSpico.exe (PID: 6816)
- KMSpico.tmp (PID: 2332)
- KMSpico.exe (PID: 1696)
- KMSpico.exe (PID: 6476)
- KMSpico.tmp (PID: 3268)
Reads the computer name
- KMSpico.tmp (PID: 2332)
- KMSpico.tmp (PID: 4700)
- KMSpico.tmp (PID: 3268)
- core.exe (PID: 7316)
- KMSELDI.exe (PID: 7964)
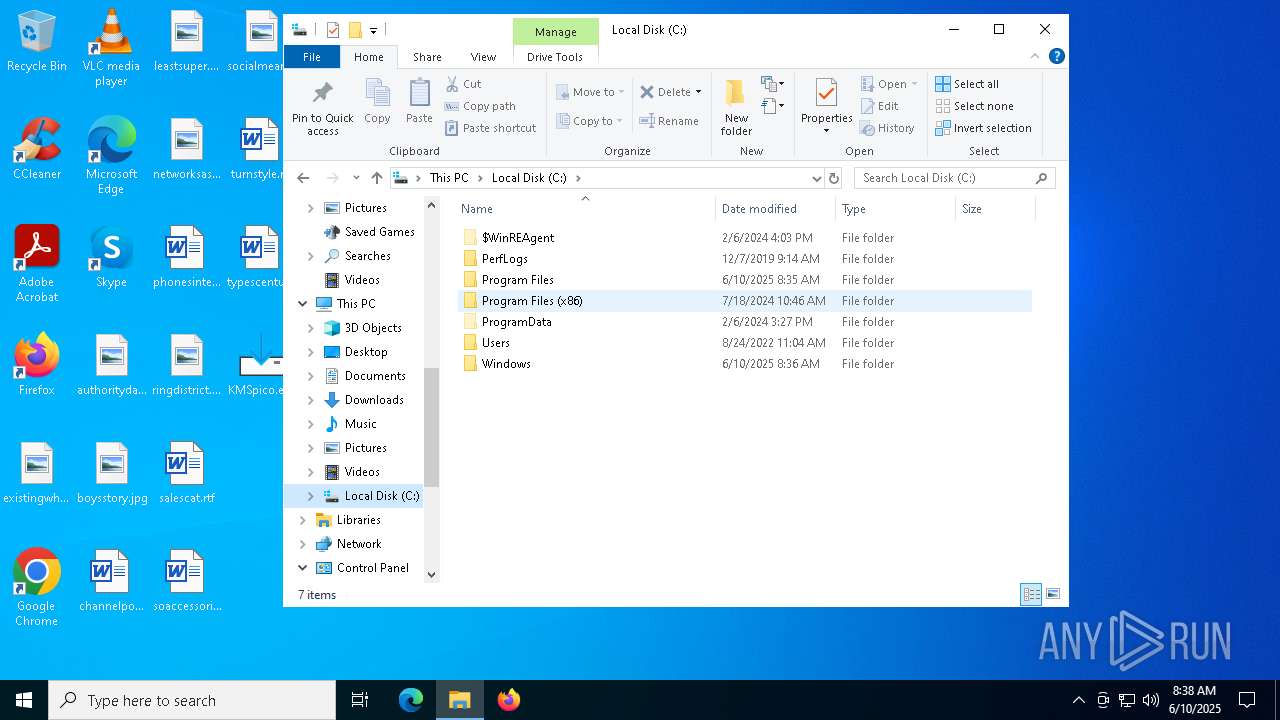
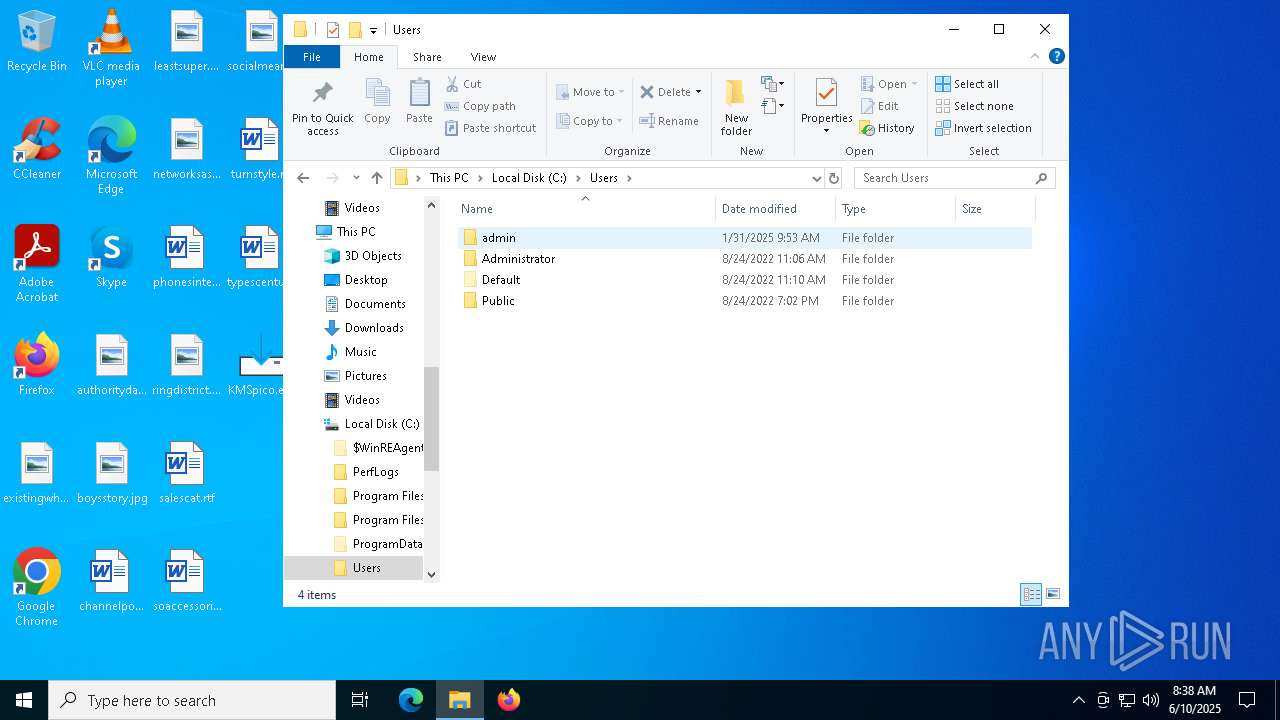
Creates files or folders in the user directory
- KMSpico.tmp (PID: 2332)
The sample compiled with english language support
- KMSpico.tmp (PID: 2332)
- KMSpico.tmp (PID: 3268)
Creates a software uninstall entry
- KMSpico.tmp (PID: 2332)
- KMSpico.tmp (PID: 3268)
Process checks computer location settings
- KMSpico.tmp (PID: 2332)
- KMSpico.tmp (PID: 4700)
Detects InnoSetup installer (YARA)
- KMSpico.exe (PID: 1696)
- KMSpico.tmp (PID: 4700)
- KMSpico.exe (PID: 6476)
- KMSpico.tmp (PID: 3268)
Compiled with Borland Delphi (YARA)
- KMSpico.tmp (PID: 4700)
- KMSpico.tmp (PID: 3268)
Reads the software policy settings
- core.exe (PID: 7316)
- slui.exe (PID: 2568)
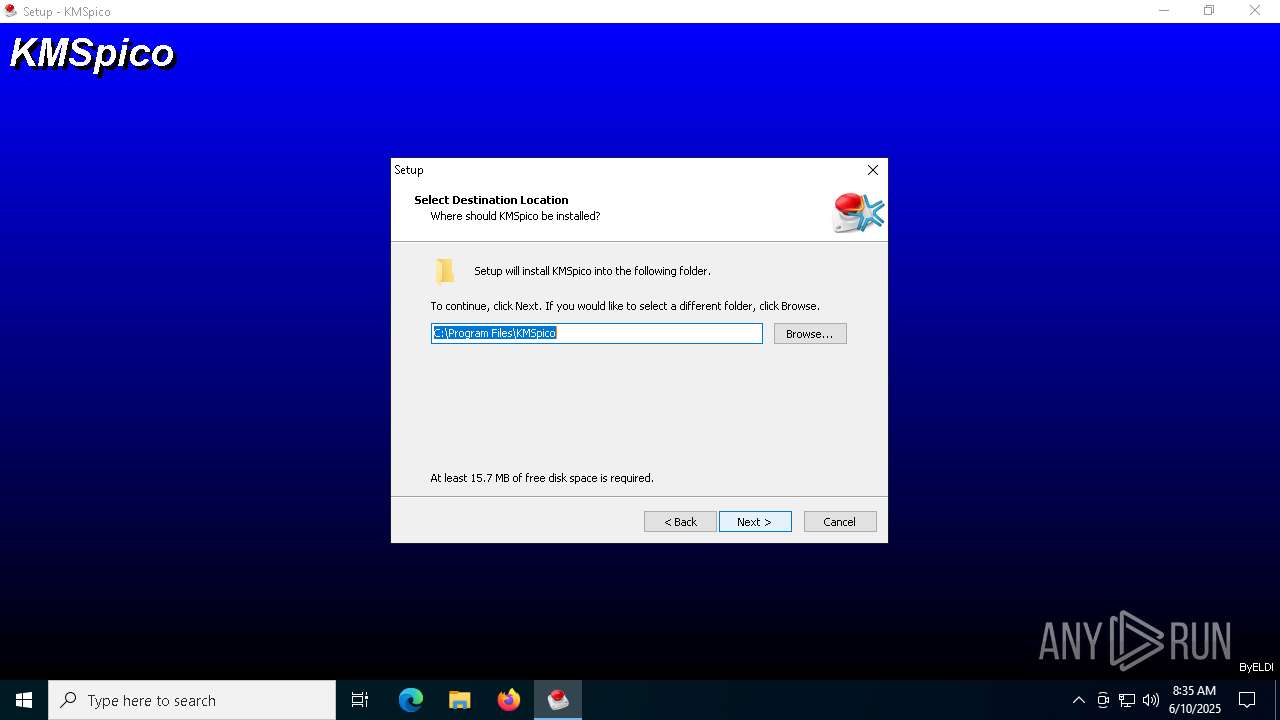
Creates files in the program directory
- KMSpico.tmp (PID: 3268)
- KMSELDI.exe (PID: 7964)
Launching a file from Task Scheduler
- cmd.exe (PID: 6852)
Reads product name
- KMSELDI.exe (PID: 7964)
Reads the machine GUID from the registry
- KMSELDI.exe (PID: 7964)
Reads Environment values
- KMSELDI.exe (PID: 7964)
Reads Microsoft Office registry keys
- KMSELDI.exe (PID: 7964)
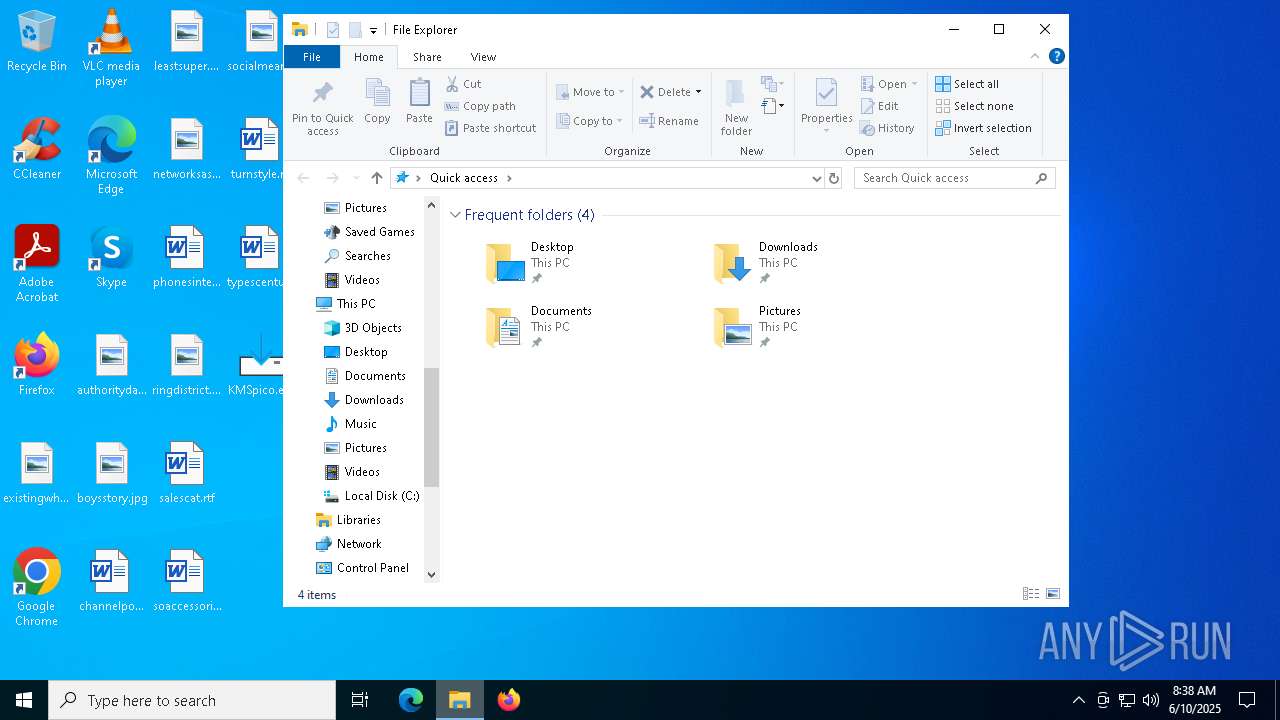
Manual execution by a user
- core.exe (PID: 7560)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (53.5) |
|---|---|---|
| .exe | | | InstallShield setup (21) |
| .exe | | | Win32 EXE PECompact compressed (generic) (20.2) |
| .exe | | | Win32 Executable (generic) (2.1) |
| .exe | | | Win16/32 Executable Delphi generic (1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:01:08 15:36:35+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 684032 |
| InitializedDataSize: | 159744 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xa7f98 |
| OSVersion: | 6.1 |
| ImageVersion: | - |
| SubsystemVersion: | 6.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | |
| FileDescription: | MyApp Setup |
| FileVersion: | |
| LegalCopyright: | |
| OriginalFileName: | |
| ProductName: | MyApp |
| ProductVersion: | 1.0 |
Total processes
165
Monitored processes
24
Malicious processes
10
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 924 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1680 | "C:\Program Files\KMSpico\AutoPico.exe" /silent | C:\Program Files\KMSpico\AutoPico.exe | KMSpico.tmp | ||||||||||||
User: admin Company: @ByELDI Integrity Level: HIGH Description: AutoPico Exit code: 0 Version: 16.1.0.0 Modules
| |||||||||||||||
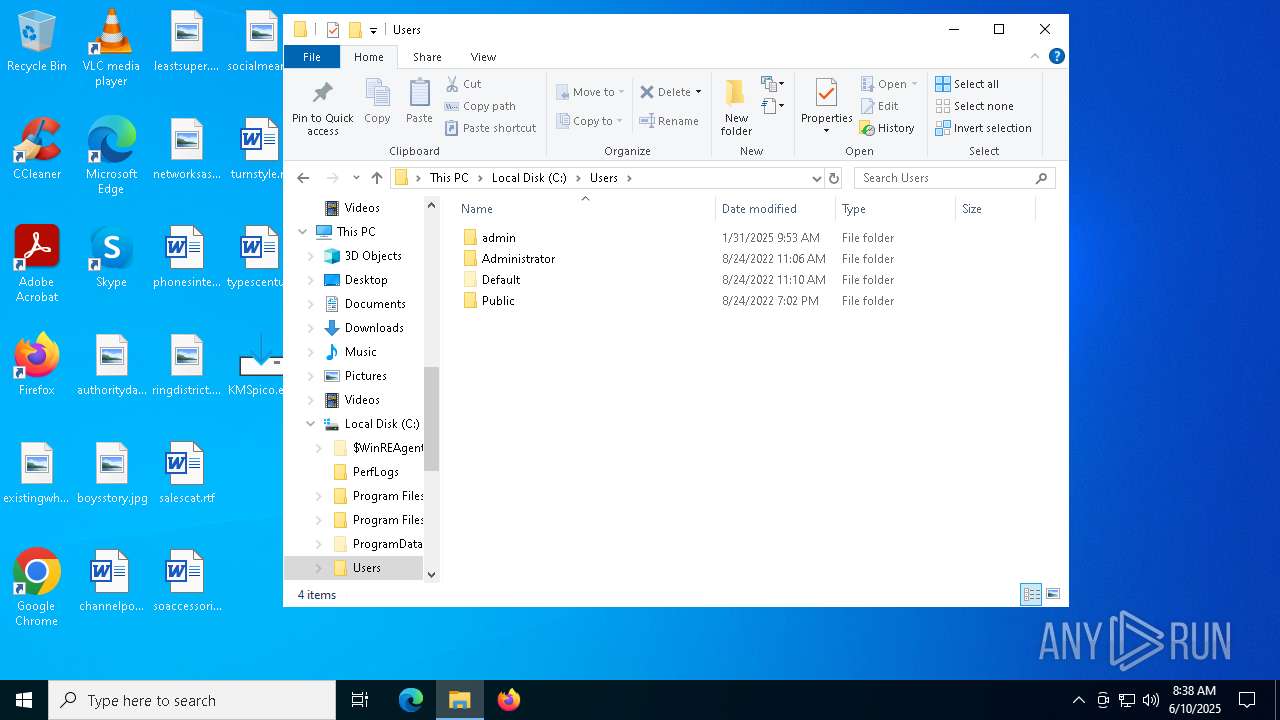
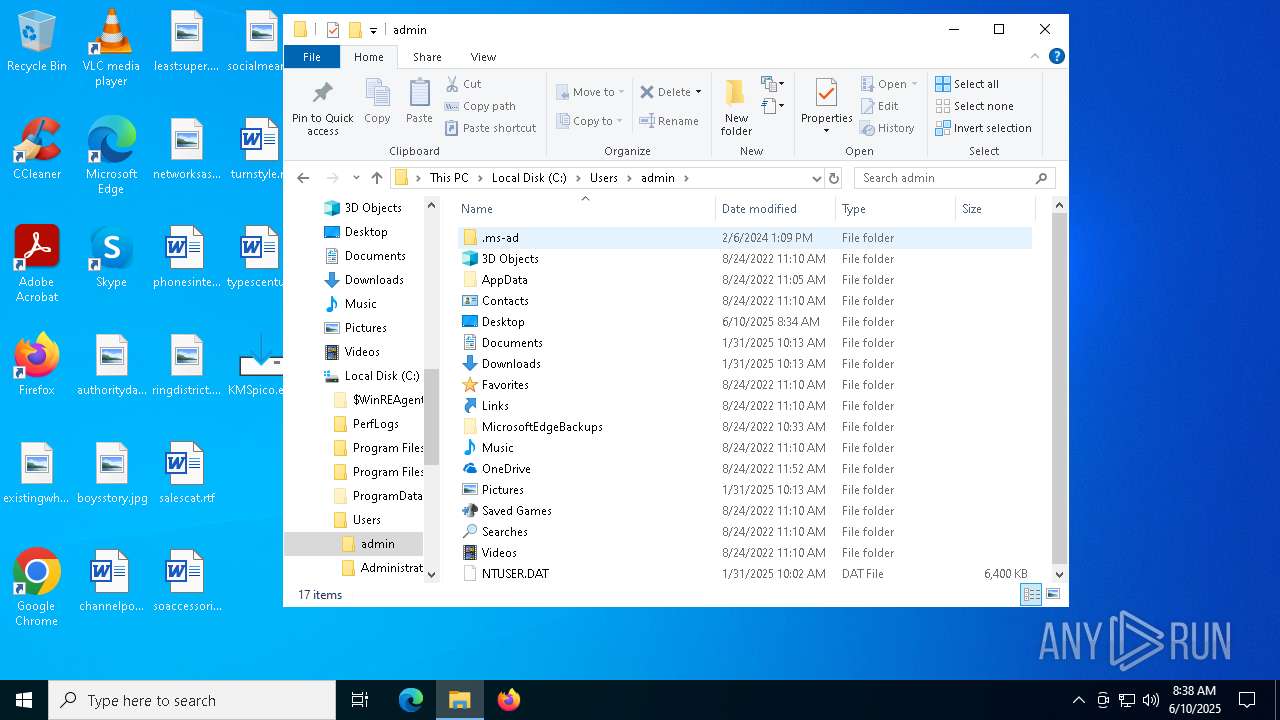
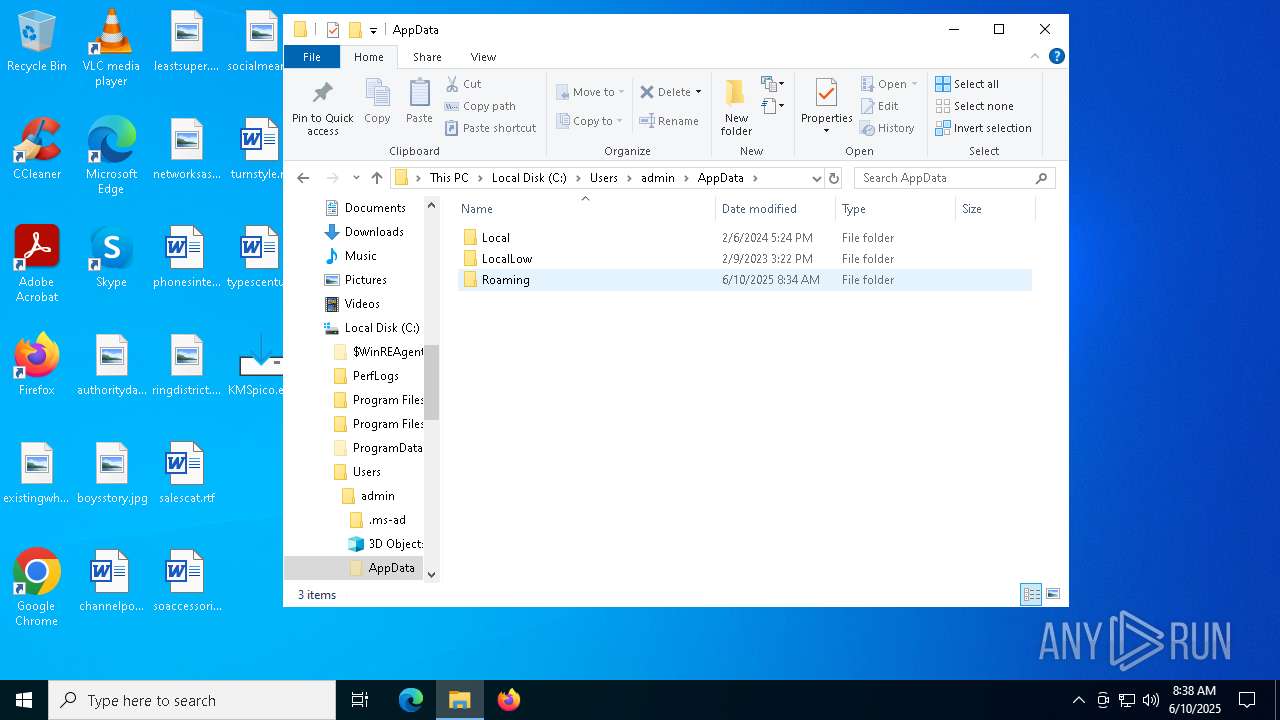
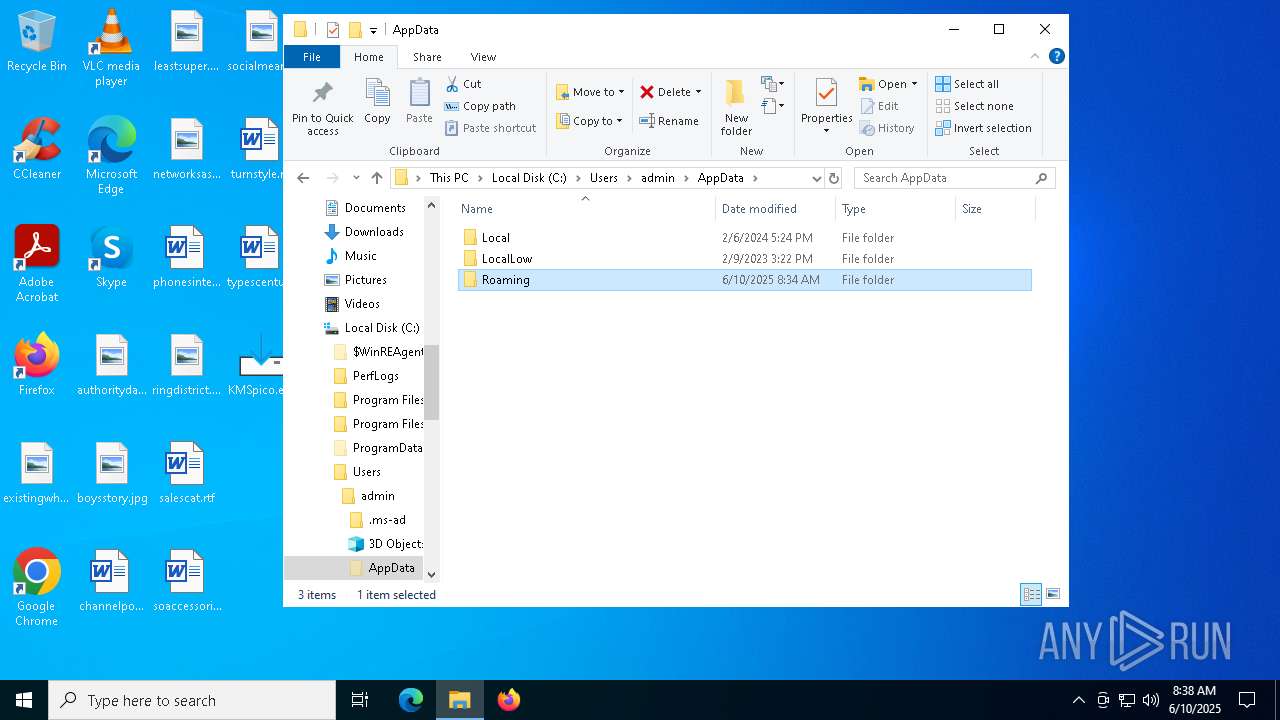
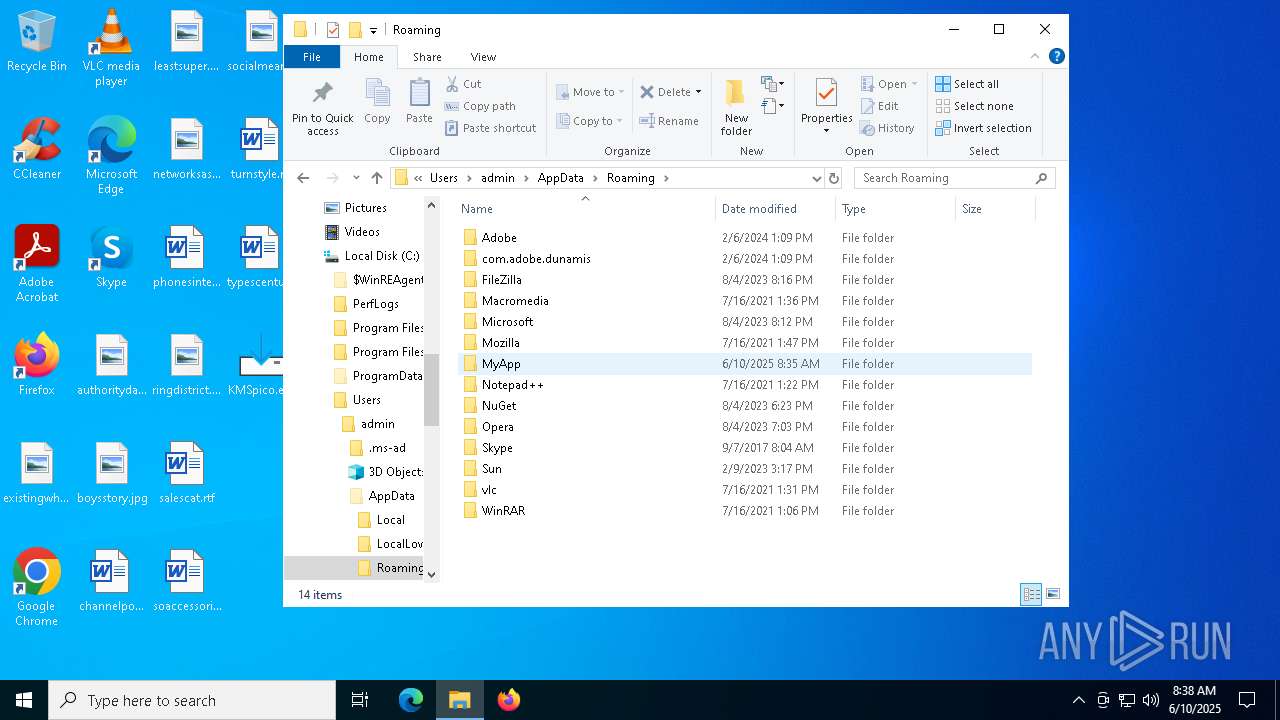
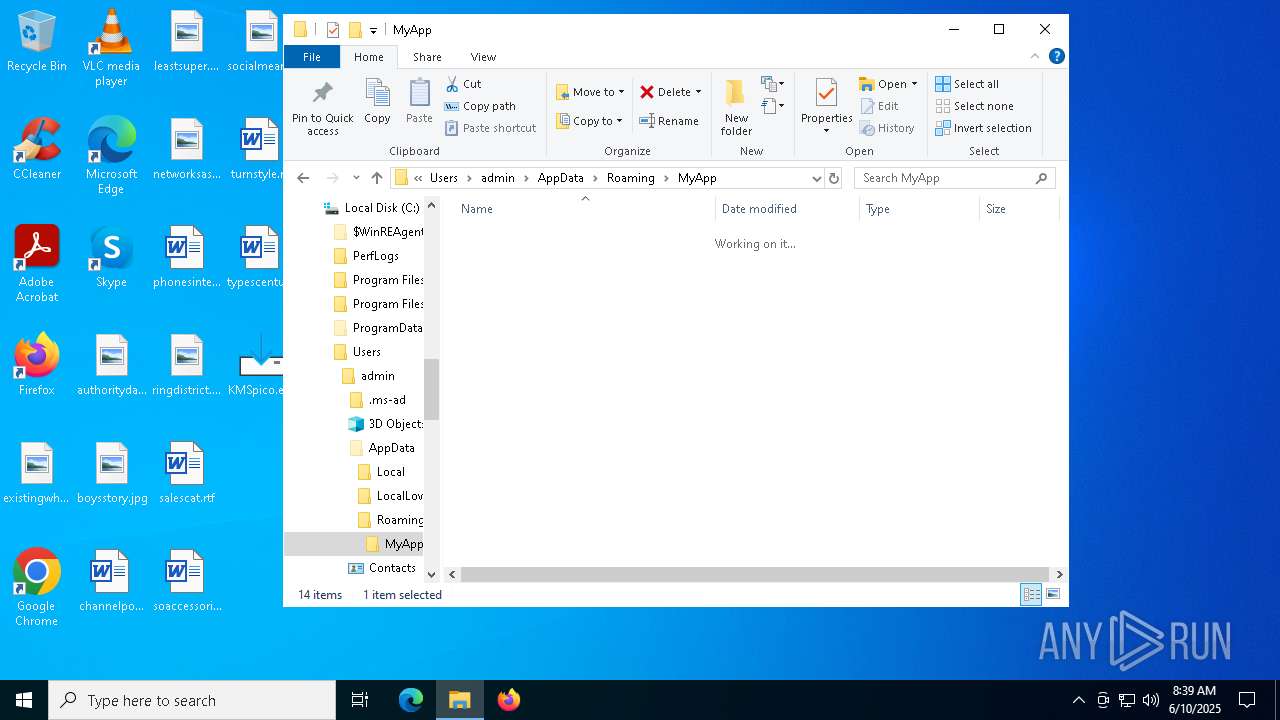
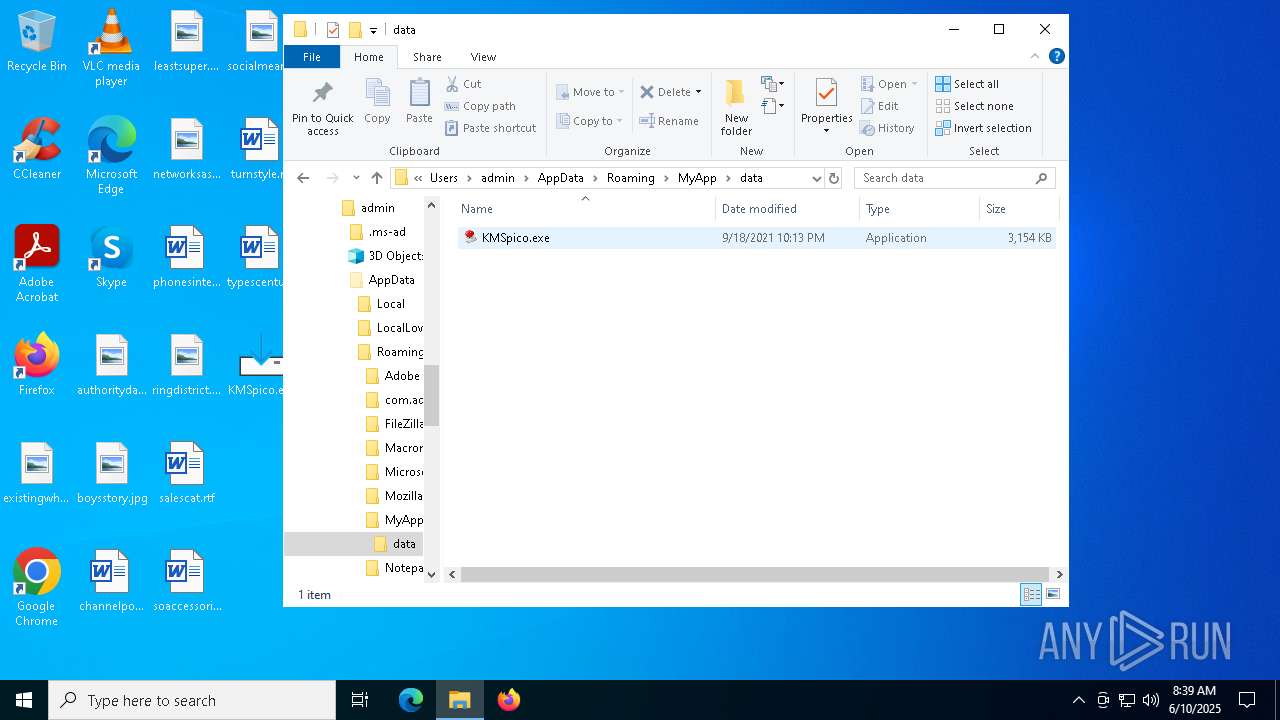
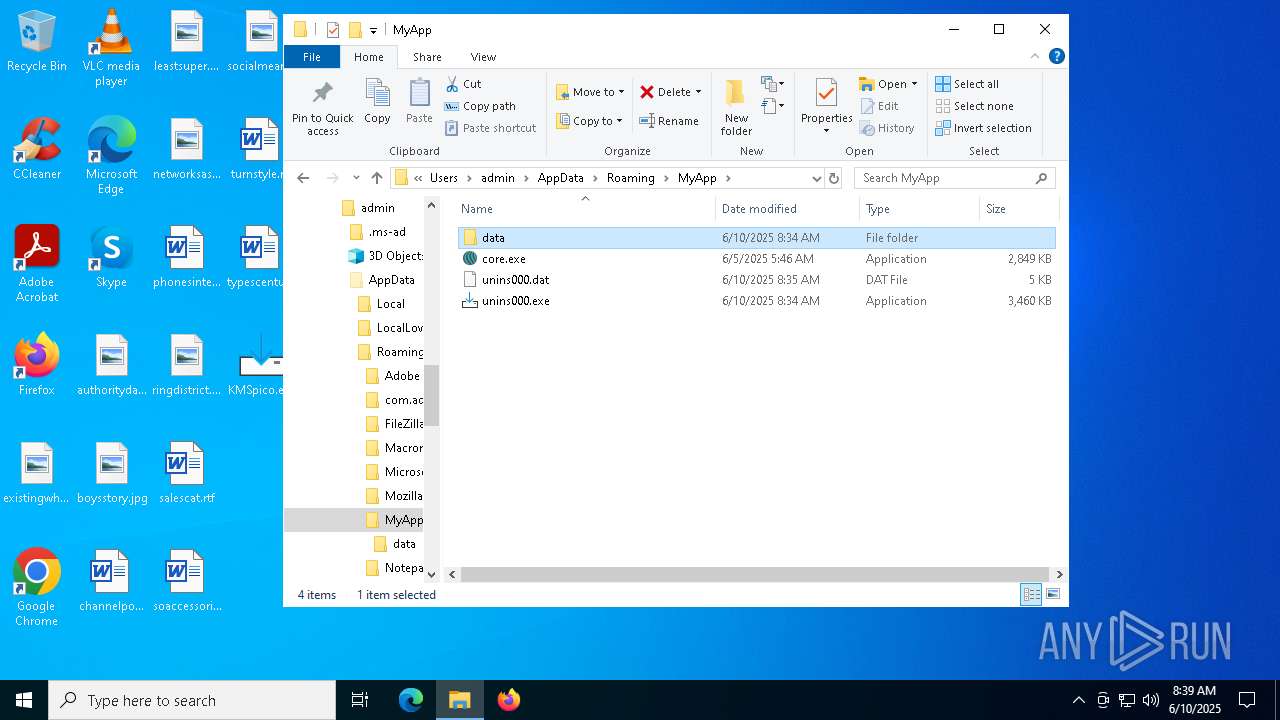
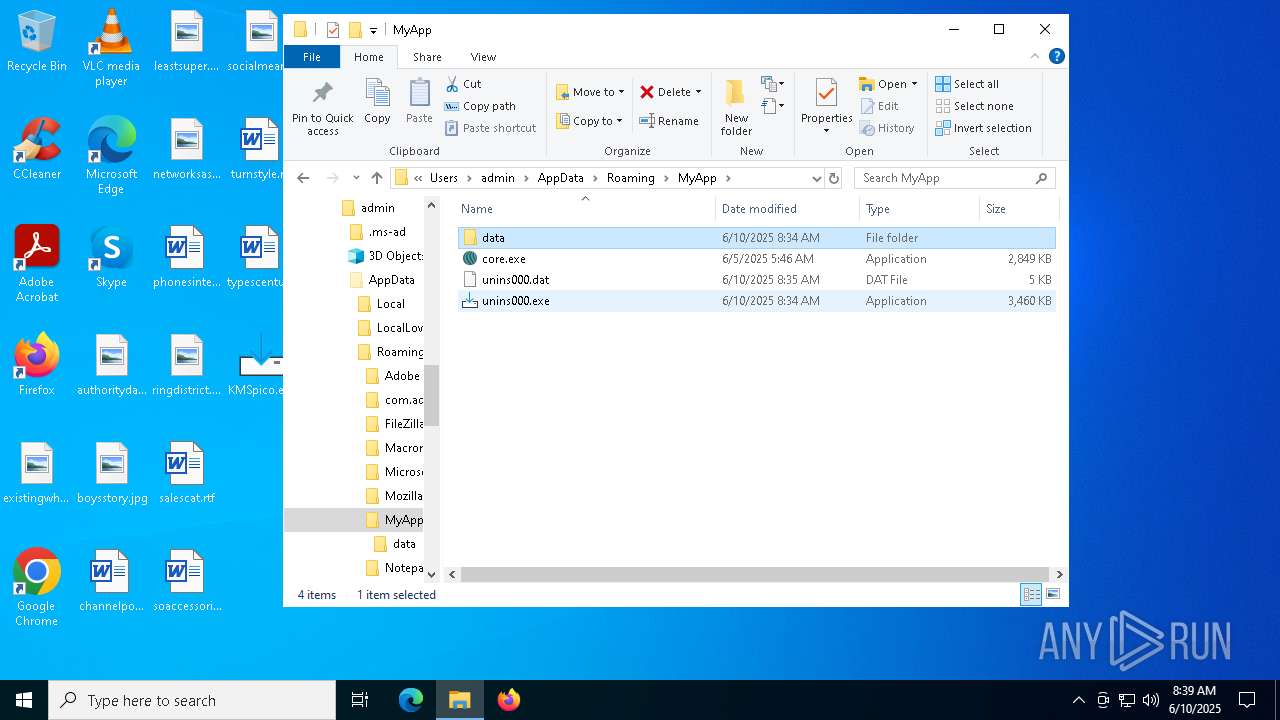
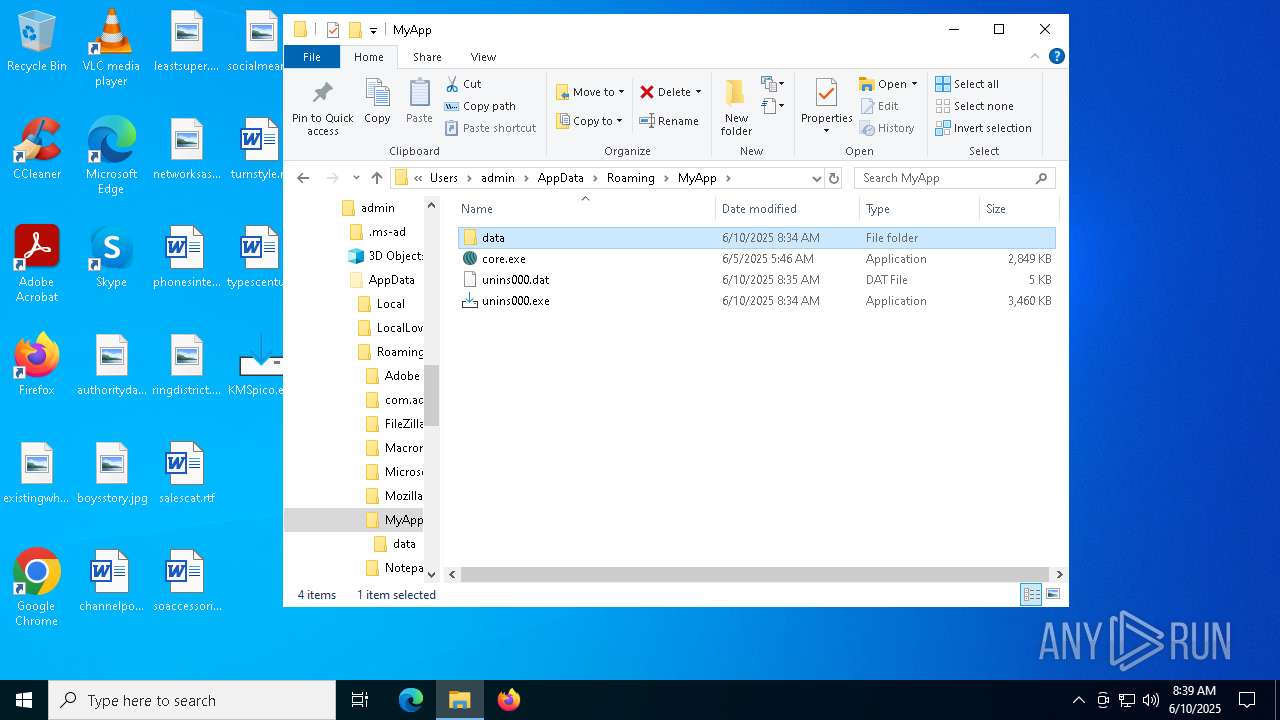
| 1696 | "C:\Users\admin\AppData\Roaming\MyApp\data\KMSpico.exe" | C:\Users\admin\AppData\Roaming\MyApp\data\KMSpico.exe | KMSpico.tmp | ||||||||||||
User: admin Company: Integrity Level: MEDIUM Description: KMSpico Setup Exit code: 0 Version: 10.2.0 Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2332 | "C:\Users\admin\AppData\Local\Temp\is-U9MJE.tmp\KMSpico.tmp" /SL5="$110284,6529308,844800,C:\Users\admin\Desktop\KMSpico.exe" | C:\Users\admin\AppData\Local\Temp\is-U9MJE.tmp\KMSpico.tmp | KMSpico.exe | ||||||||||||
User: admin Company: Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2568 | "C:\WINDOWS\System32\SLUI.exe" RuleId=eeba1977-569e-4571-b639-7623d8bfecc0;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=2de67392-b7a7-462a-b1ca-108dd189f588;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3192 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | SECOH-QAD.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3268 | "C:\Users\admin\AppData\Local\Temp\is-FNA2R.tmp\KMSpico.tmp" /SL5="$130284,2952592,69120,C:\Users\admin\AppData\Roaming\MyApp\data\KMSpico.exe" /SPAWNWND=$7036C /NOTIFYWND=$203A6 | C:\Users\admin\AppData\Local\Temp\is-FNA2R.tmp\KMSpico.tmp | KMSpico.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 4700 | "C:\Users\admin\AppData\Local\Temp\is-7QT0P.tmp\KMSpico.tmp" /SL5="$203A6,2952592,69120,C:\Users\admin\AppData\Roaming\MyApp\data\KMSpico.exe" | C:\Users\admin\AppData\Local\Temp\is-7QT0P.tmp\KMSpico.tmp | — | KMSpico.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 4920 | C:\WINDOWS\SECOH-QAD.exe C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\SECOH-QAD.exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Integrity Level: SYSTEM Exit code: 4294967295 Modules
| |||||||||||||||
Total events
7 830
Read events
7 745
Write events
80
Delete events
5
Modification events
| (PID) Process: | (2332) KMSpico.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | GlobalAssocChangedCounter |
Value: 114 | |||
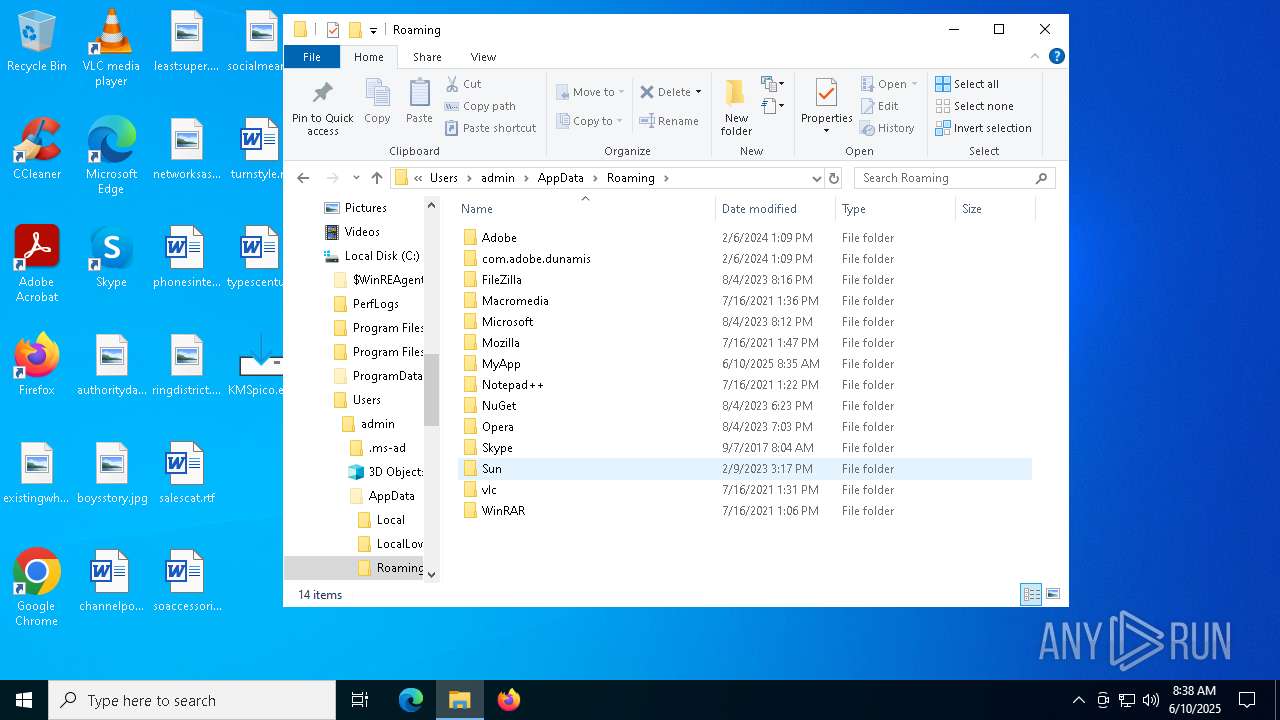
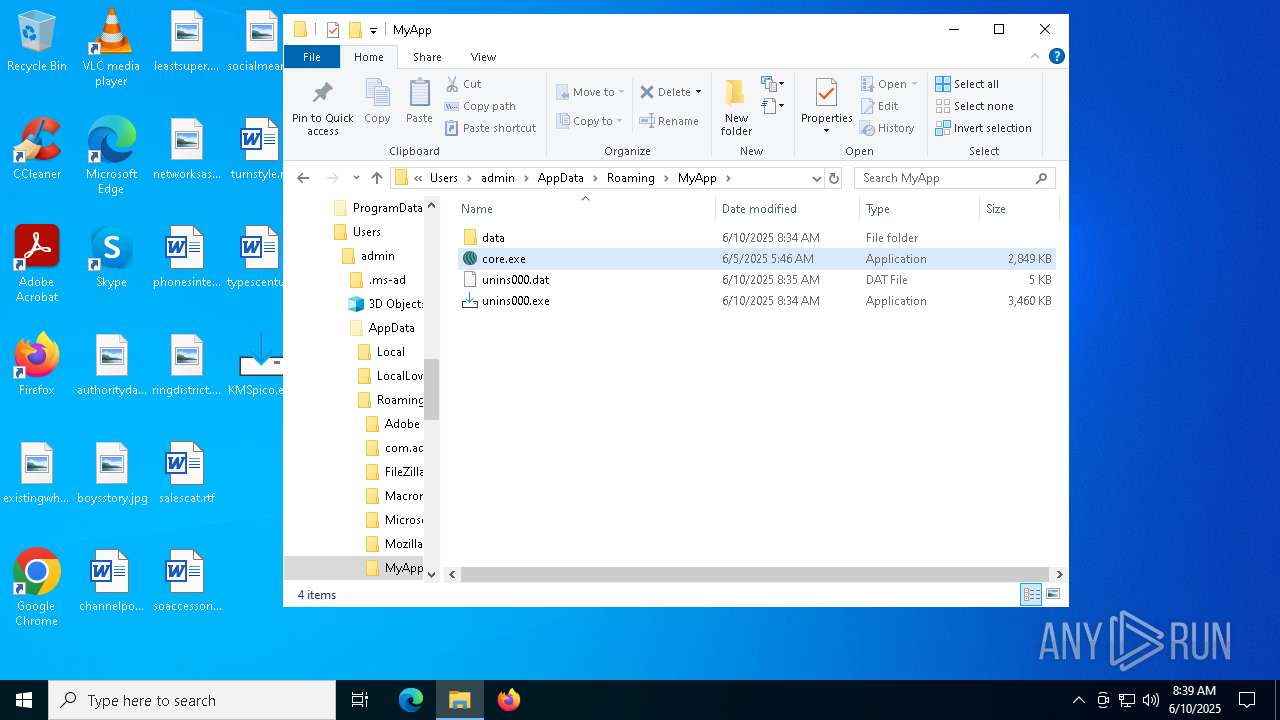
| (PID) Process: | (2332) KMSpico.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\MyApp_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 6.4.0 | |||
| (PID) Process: | (2332) KMSpico.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\MyApp_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Users\admin\AppData\Roaming\MyApp | |||
| (PID) Process: | (2332) KMSpico.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\MyApp_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Users\admin\AppData\Roaming\MyApp\ | |||
| (PID) Process: | (2332) KMSpico.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\MyApp_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: MyApp | |||
| (PID) Process: | (2332) KMSpico.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\MyApp_is1 |
| Operation: | write | Name: | Inno Setup: User |
Value: admin | |||
| (PID) Process: | (2332) KMSpico.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\MyApp_is1 |
| Operation: | write | Name: | Inno Setup: Language |
Value: default | |||
| (PID) Process: | (2332) KMSpico.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\MyApp_is1 |
| Operation: | write | Name: | DisplayName |
Value: MyApp version 1.0 | |||
| (PID) Process: | (2332) KMSpico.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\MyApp_is1 |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Users\admin\AppData\Roaming\MyApp\unins000.exe | |||
| (PID) Process: | (2332) KMSpico.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\MyApp_is1 |
| Operation: | write | Name: | UninstallString |
Value: "C:\Users\admin\AppData\Roaming\MyApp\unins000.exe" | |||
Executable files
34
Suspicious files
2
Text files
715
Unknown types
34
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6816 | KMSpico.exe | C:\Users\admin\AppData\Local\Temp\is-U9MJE.tmp\KMSpico.tmp | executable | |
MD5:E4C43138CCB8240276872FD1AEC369BE | SHA256:46BE5E3F28A5E4ED63D66B901D927C25944B4DA36EFFEA9C97FB05994360EDF5 | |||
| 2332 | KMSpico.tmp | C:\Users\admin\AppData\Roaming\MyApp\core.exe | executable | |
MD5:FB2589FDE6F7DDE19190D6A7F5065AC4 | SHA256:F70E262B41B6AD03103576FE07C654CD349750457E7A71E4EB07AAAB3E06B4A7 | |||
| 2332 | KMSpico.tmp | C:\Users\admin\AppData\Roaming\MyApp\unins000.exe | executable | |
MD5:4134EC81A9D645602B1FA265F98FBF35 | SHA256:69966257CE41717F2121EA1F03F8BFA1486423ACECFCC977DD9F1E157C911AD4 | |||
| 1696 | KMSpico.exe | C:\Users\admin\AppData\Local\Temp\is-7QT0P.tmp\KMSpico.tmp | executable | |
MD5:1778C1F66FF205875A6435A33229AB3C | SHA256:95C06ACAC4FE4598840E5556F9613D43AA1039C52DAC64536F59E45A70F79DA6 | |||
| 2332 | KMSpico.tmp | C:\Users\admin\AppData\Roaming\MyApp\unins000.dat | dat | |
MD5:9D081A031B23B21A38D5CA4F06796C90 | SHA256:67106AED09E83018821533D2107B777E5CBFFFBCDB462C4B19C5715A7FC4F120 | |||
| 2332 | KMSpico.tmp | C:\Users\admin\AppData\Roaming\MyApp\data\is-J7POR.tmp | executable | |
MD5:A02164371A50C5FF9FA2870EF6E8CFA3 | SHA256:64C731ADBE1B96CB5765203B1E215093DCF268D020B299445884A4AE62ED2D3A | |||
| 2332 | KMSpico.tmp | C:\Users\admin\AppData\Roaming\MyApp\is-370CU.tmp | executable | |
MD5:FB2589FDE6F7DDE19190D6A7F5065AC4 | SHA256:F70E262B41B6AD03103576FE07C654CD349750457E7A71E4EB07AAAB3E06B4A7 | |||
| 6476 | KMSpico.exe | C:\Users\admin\AppData\Local\Temp\is-FNA2R.tmp\KMSpico.tmp | executable | |
MD5:1778C1F66FF205875A6435A33229AB3C | SHA256:95C06ACAC4FE4598840E5556F9613D43AA1039C52DAC64536F59E45A70F79DA6 | |||
| 2332 | KMSpico.tmp | C:\Users\admin\AppData\Roaming\MyApp\data\KMSpico.exe | executable | |
MD5:A02164371A50C5FF9FA2870EF6E8CFA3 | SHA256:64C731ADBE1B96CB5765203B1E215093DCF268D020B299445884A4AE62ED2D3A | |||
| 2332 | KMSpico.tmp | C:\Users\admin\AppData\Roaming\MyApp\is-Q078F.tmp | executable | |
MD5:4134EC81A9D645602B1FA265F98FBF35 | SHA256:69966257CE41717F2121EA1F03F8BFA1486423ACECFCC977DD9F1E157C911AD4 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
43
DNS requests
25
Threats
19
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7216 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7216 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6544 | svchost.exe | 20.190.159.131:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7316 | core.exe | 195.82.147.188:443 | narrathfpt.top | Dreamtorrent Corp | RU | malicious |
6544 | svchost.exe | 40.126.31.0:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
login.live.com |
| whitelisted |
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
screhwc.live |
| unknown |
narrathfpt.top |
| unknown |
ocsp.digicert.com |
| whitelisted |
pastebin.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
2196 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (narrathfpt .top) |
2196 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (screhwc .live) |
7316 | core.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (narrathfpt .top) in TLS SNI |
7316 | core.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (narrathfpt .top) in TLS SNI |
7316 | core.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (narrathfpt .top) in TLS SNI |
7316 | core.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (narrathfpt .top) in TLS SNI |
7316 | core.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (narrathfpt .top) in TLS SNI |
7316 | core.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (narrathfpt .top) in TLS SNI |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Online Pastebin Text Storage |