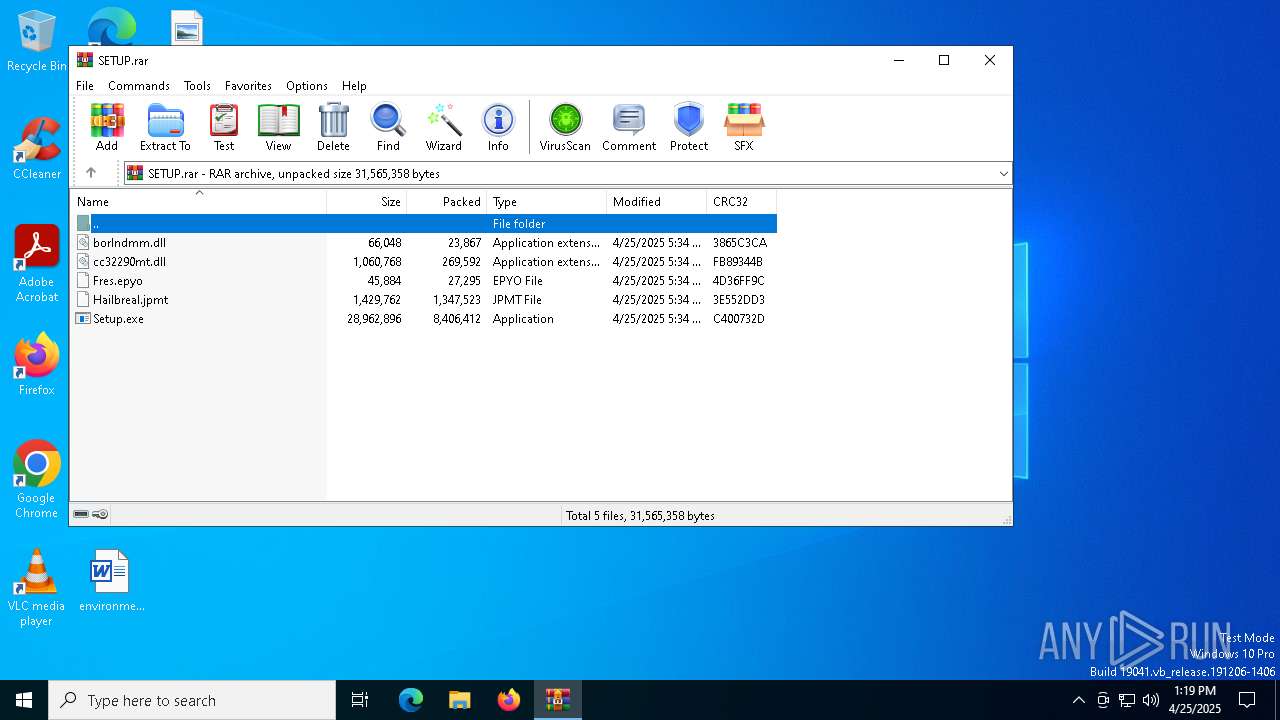
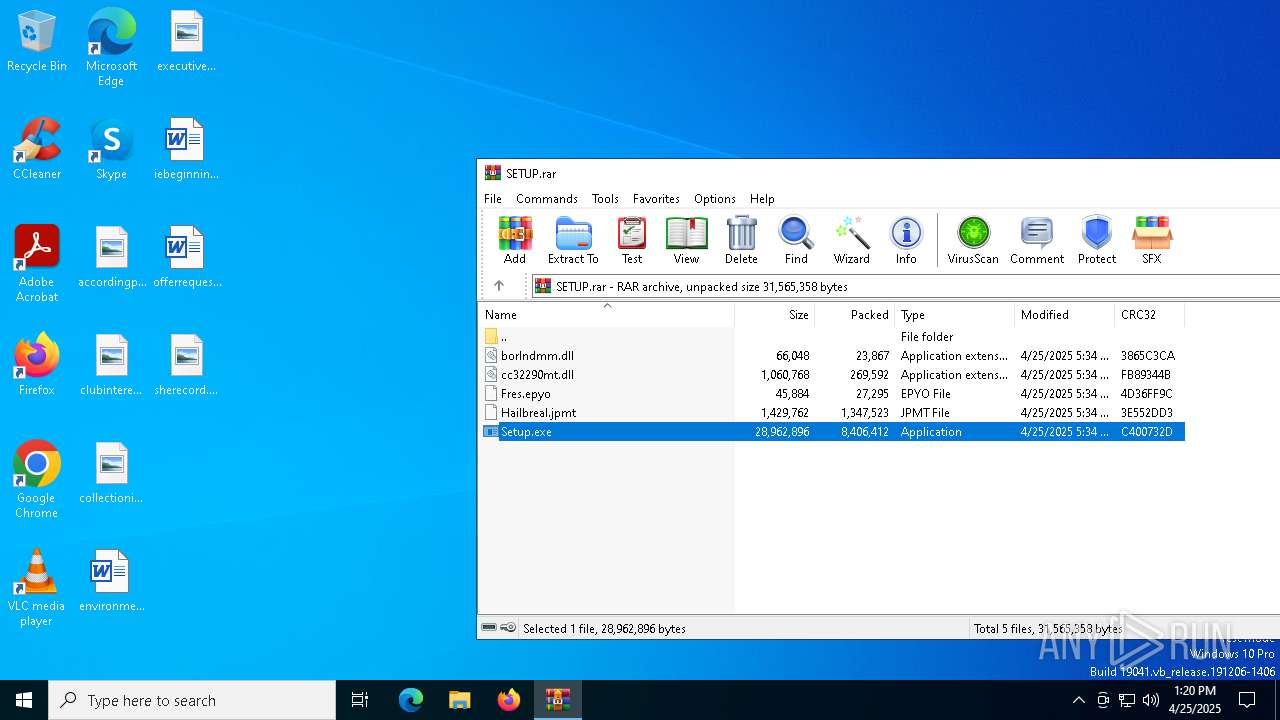
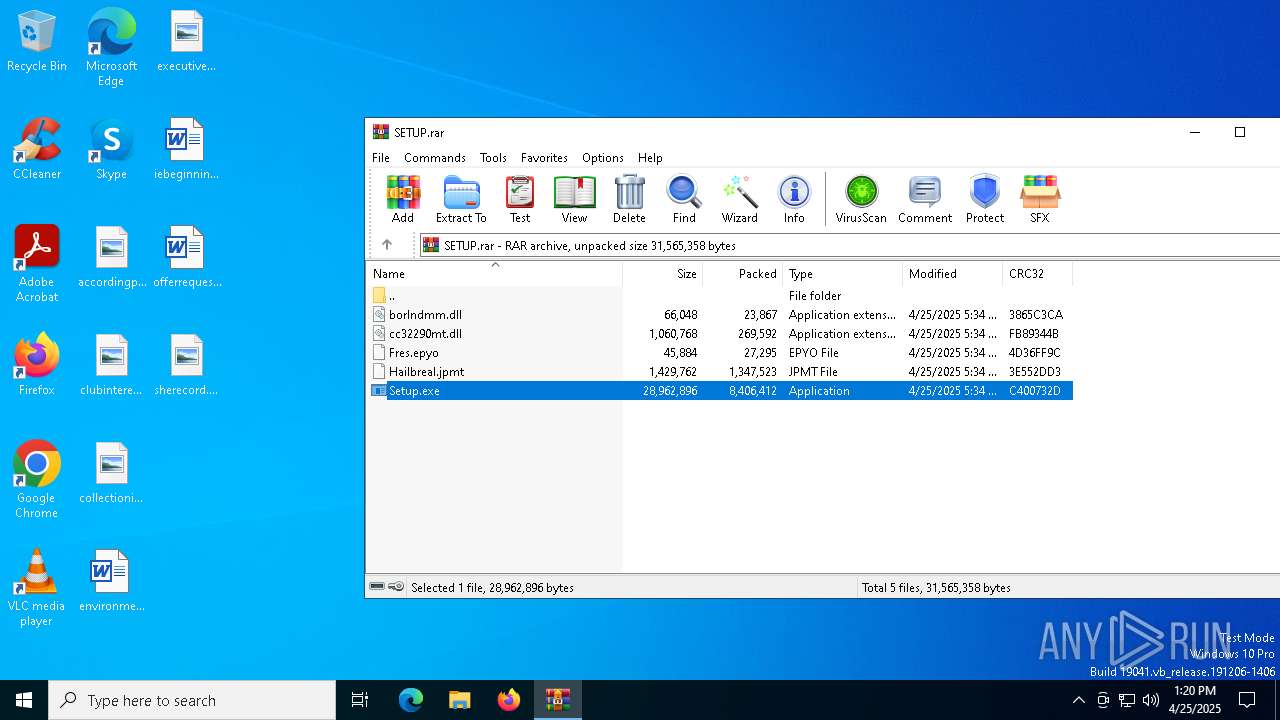
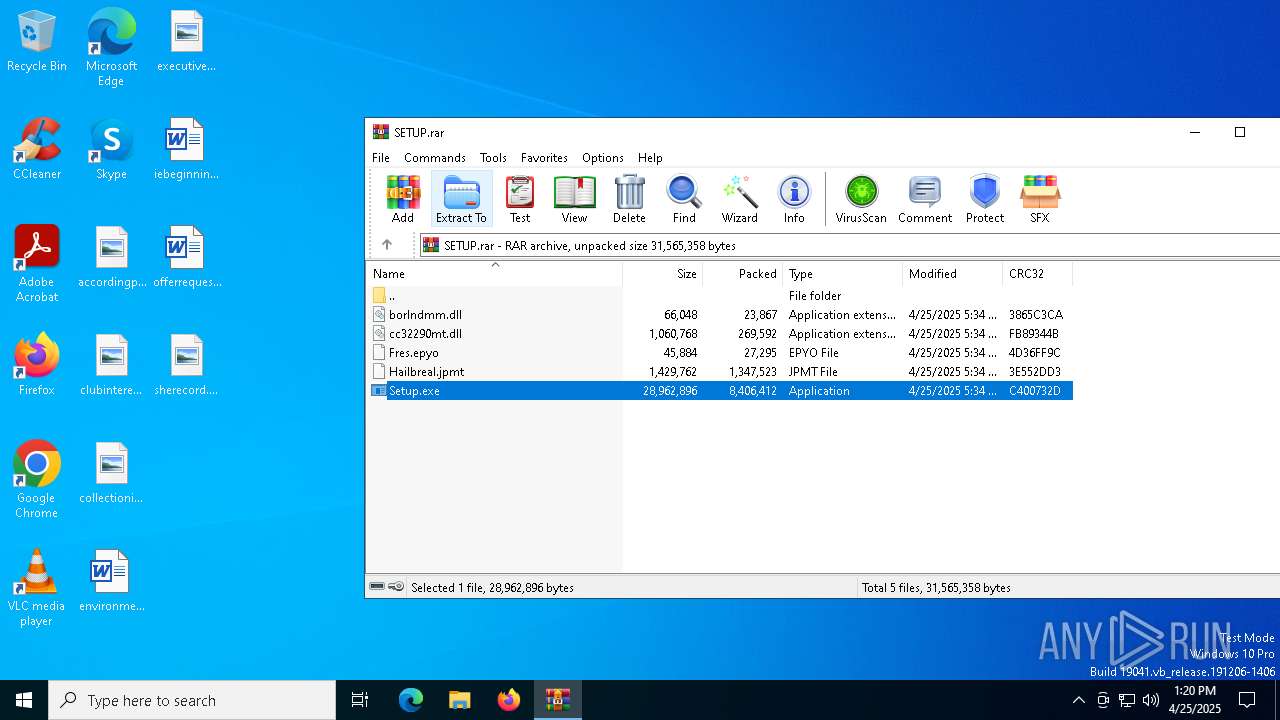
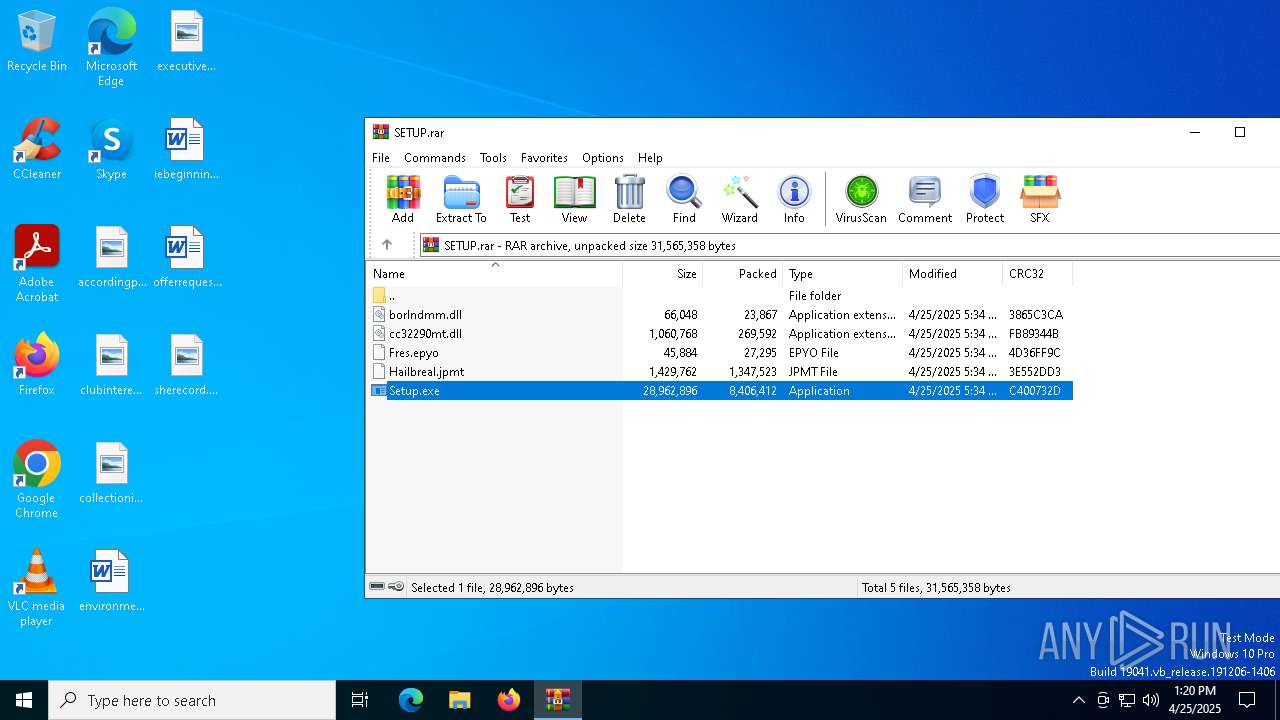
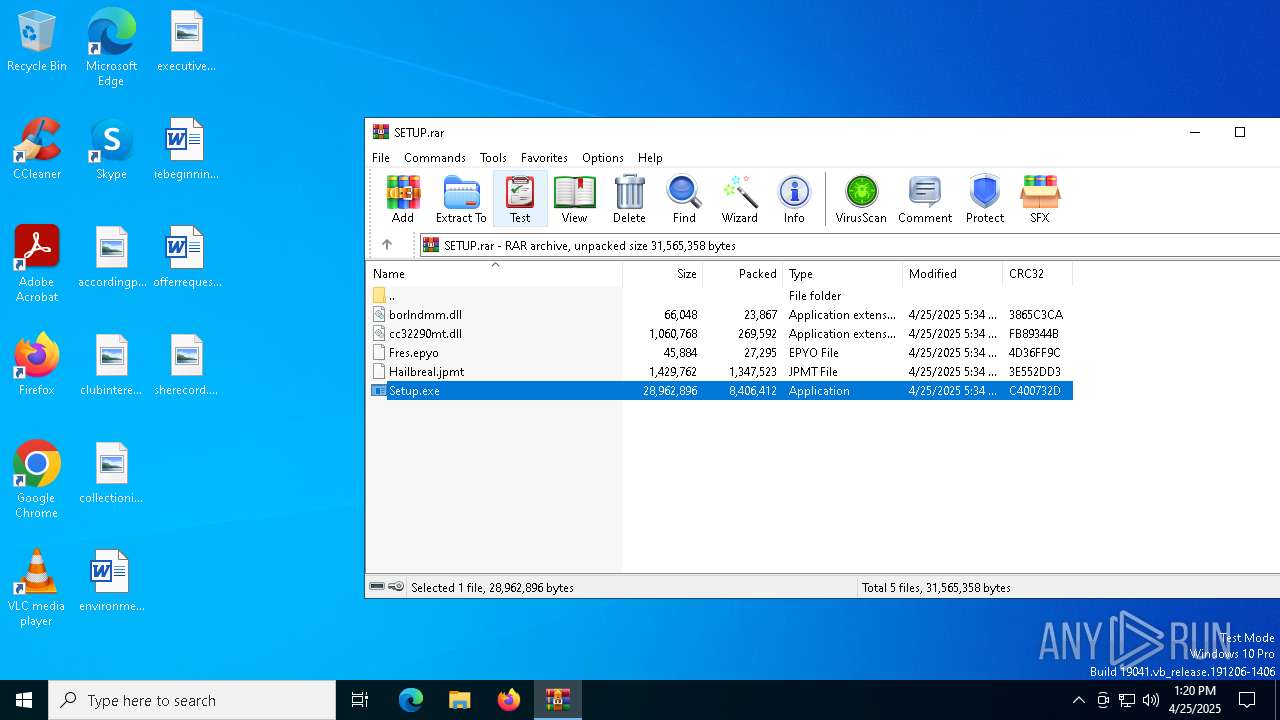
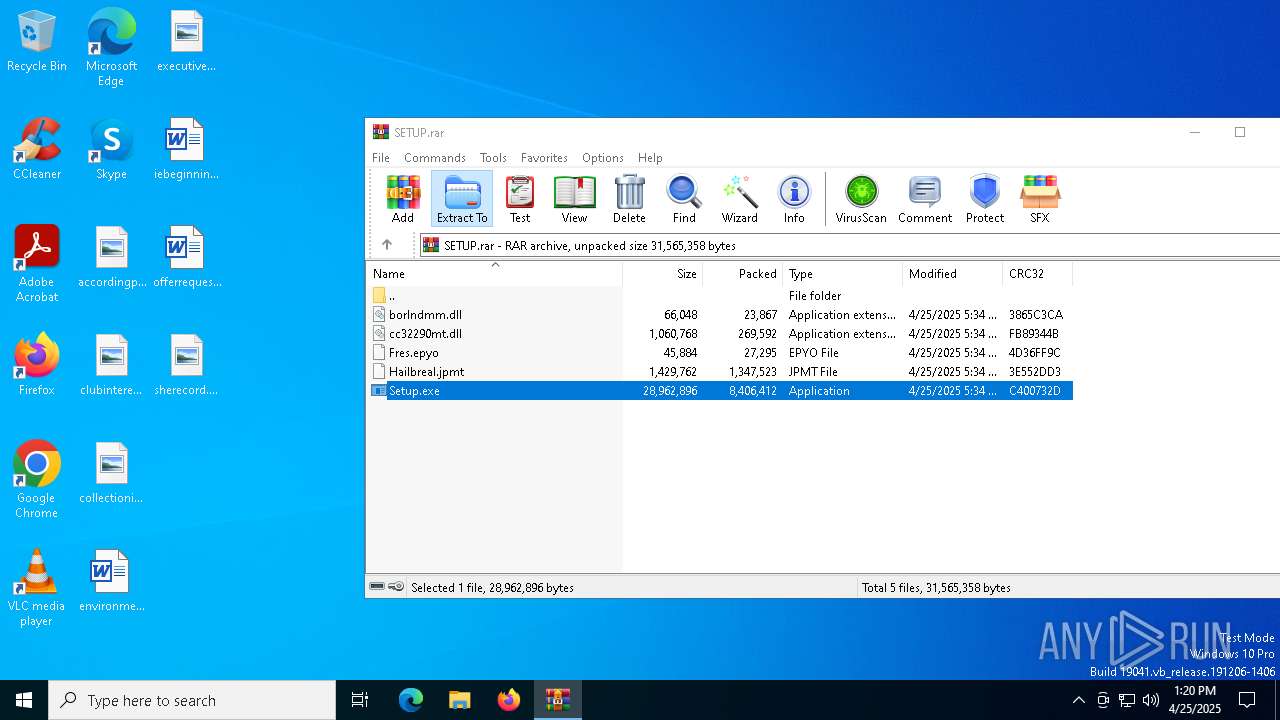
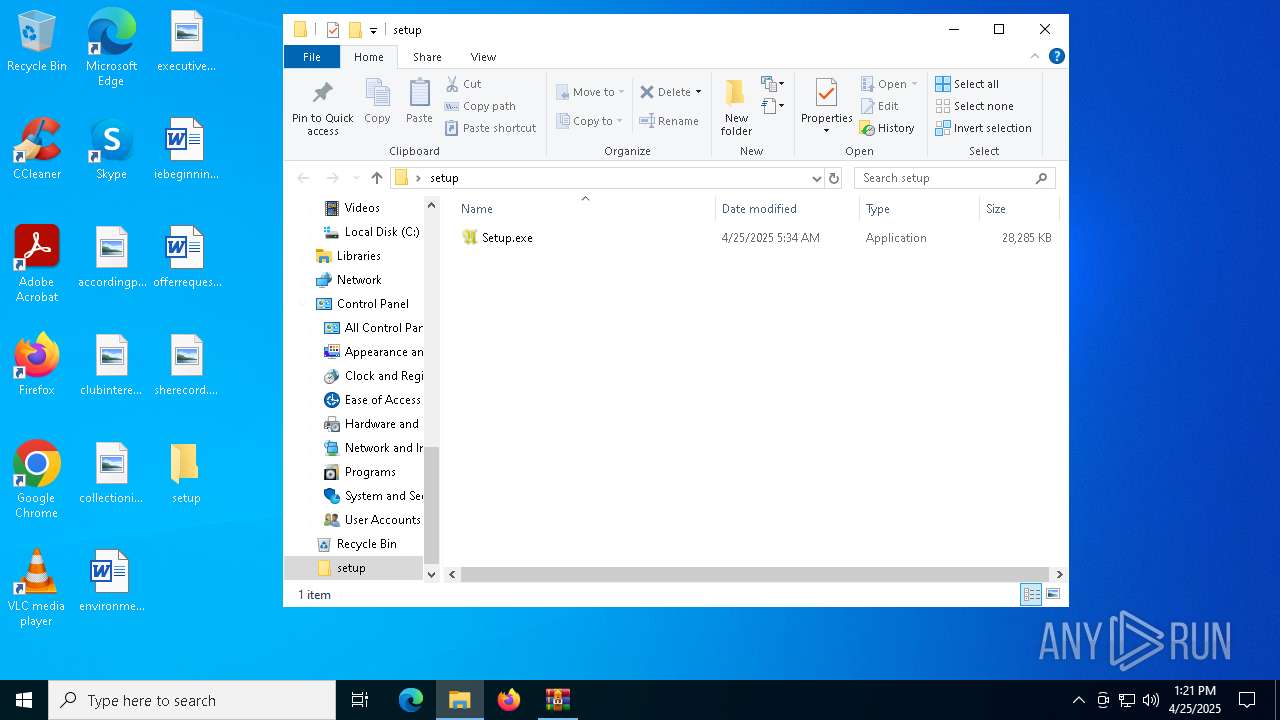
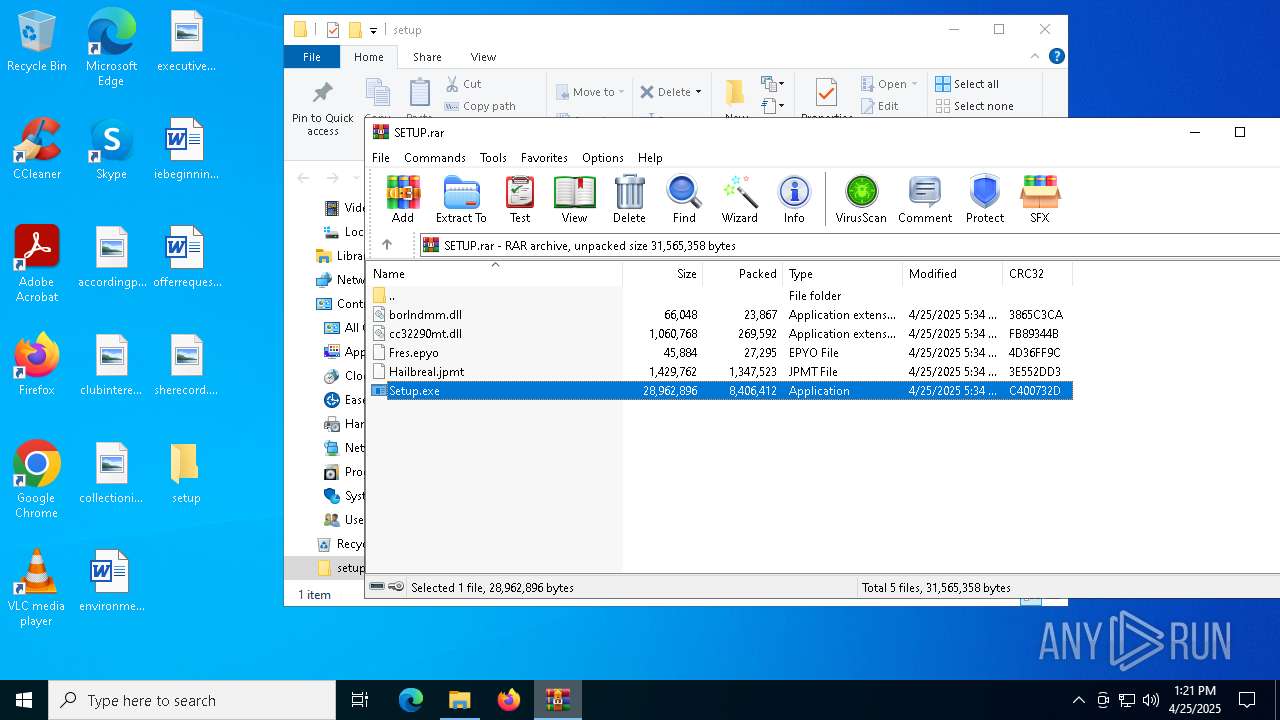
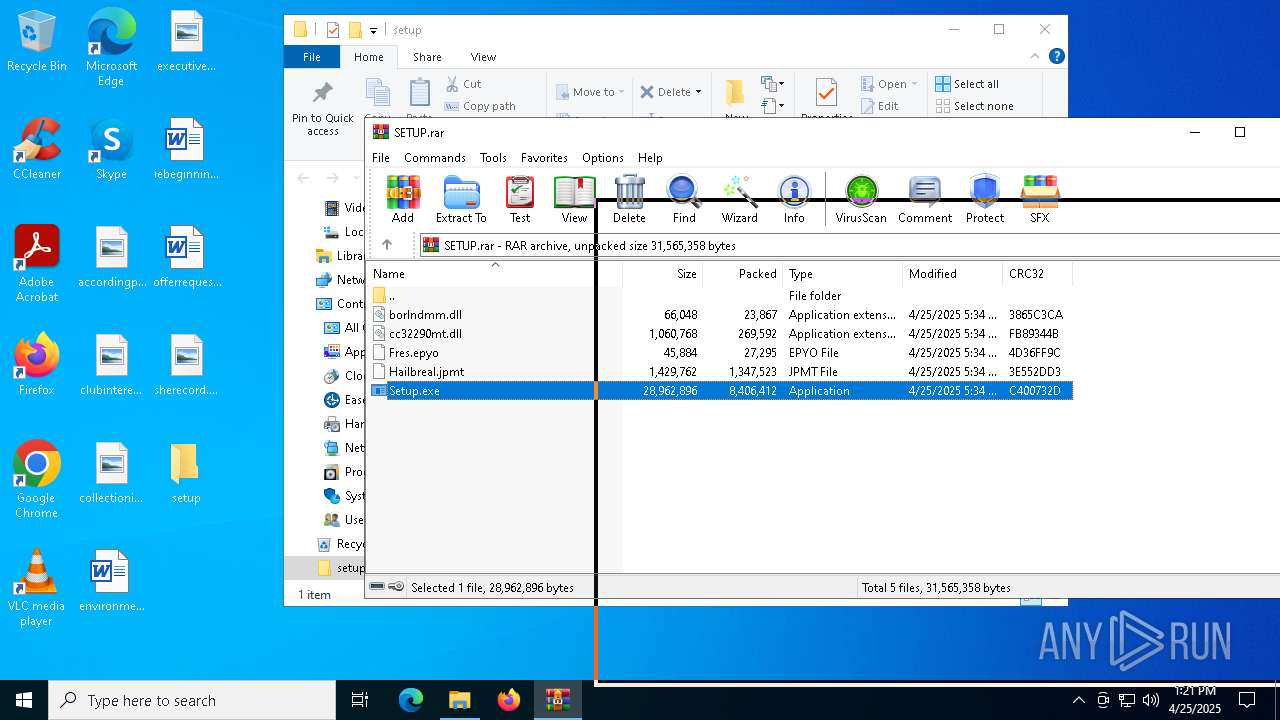
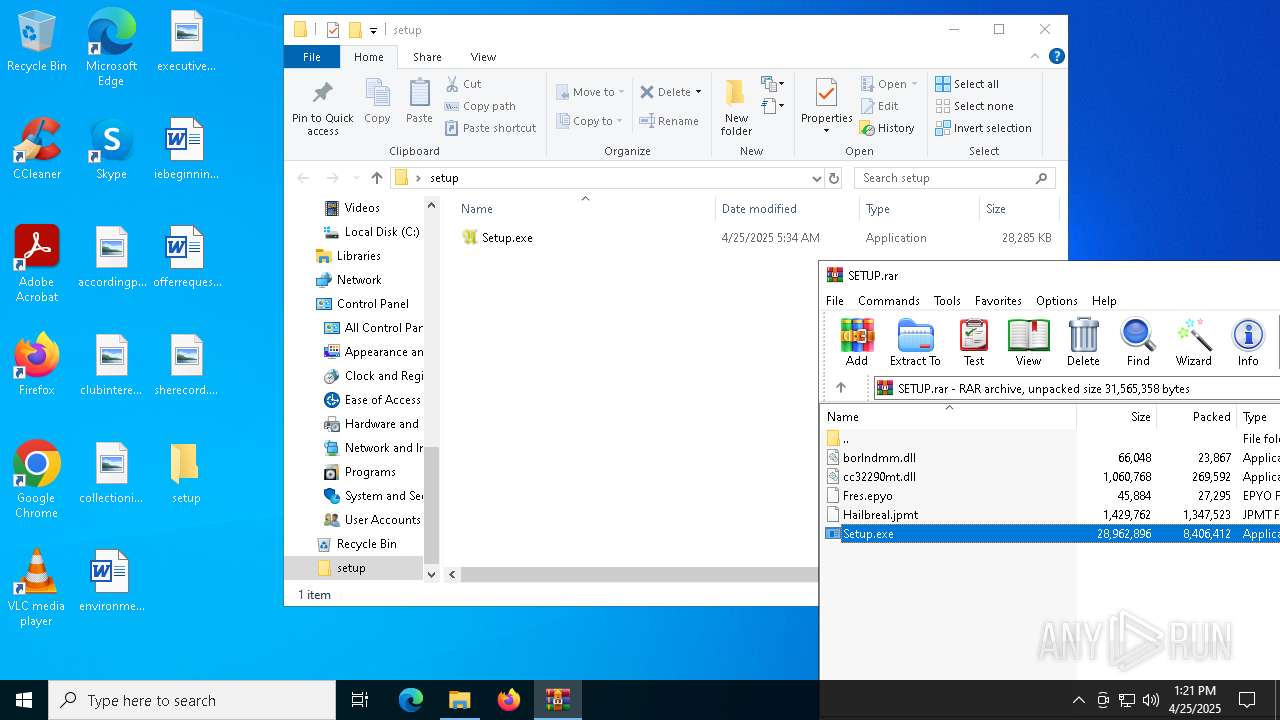
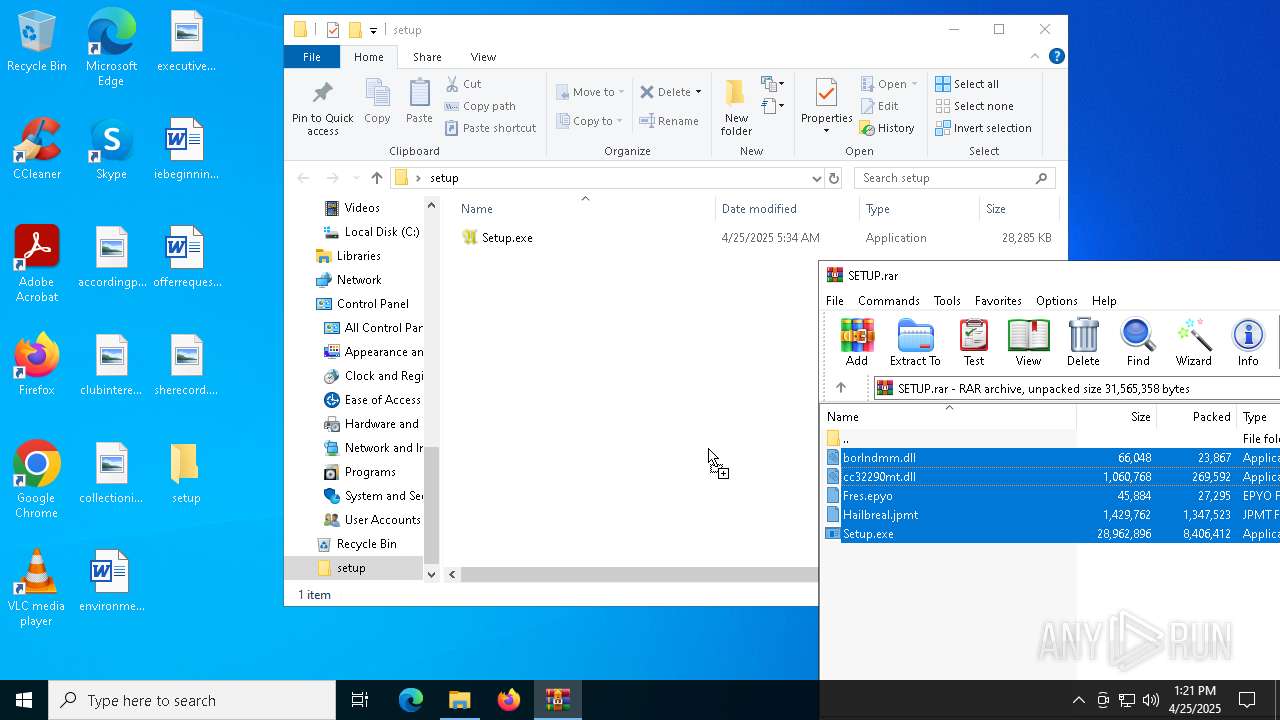
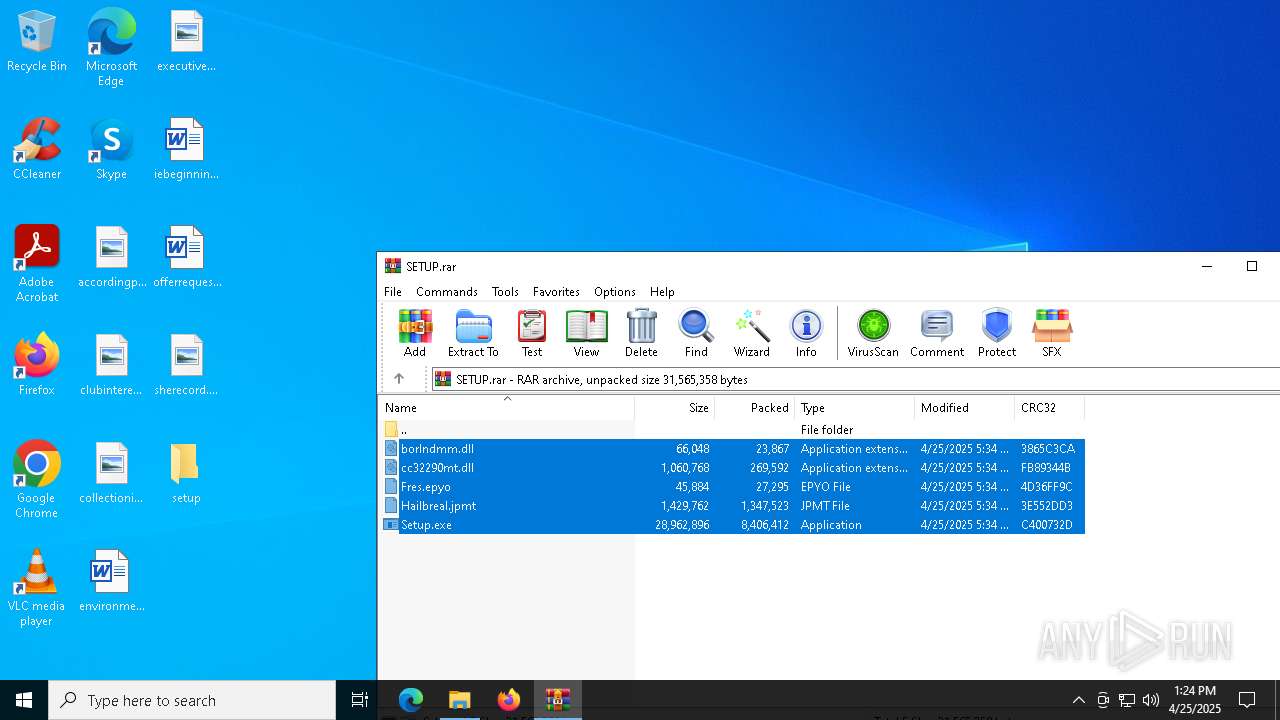
| File name: | SETUP.rar |
| Full analysis: | https://app.any.run/tasks/0bd284a7-6f1b-4bd6-902a-e649bd081e08 |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | April 25, 2025, 13:19:30 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
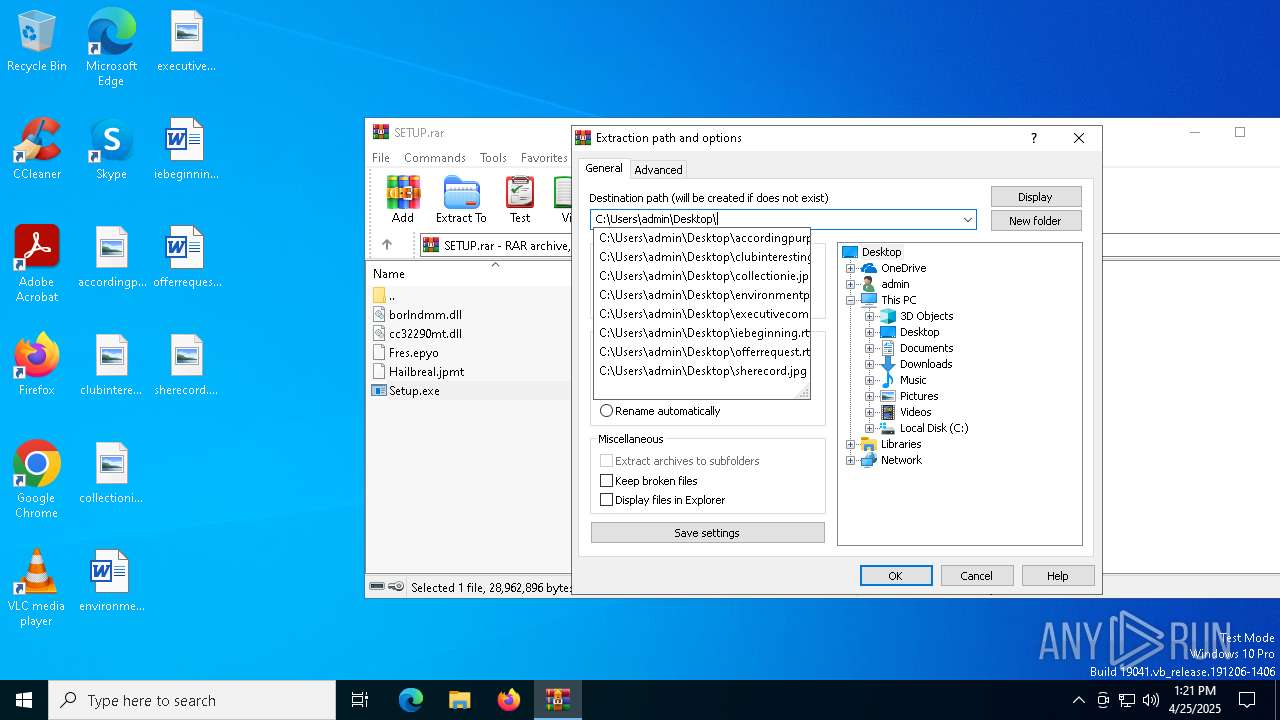
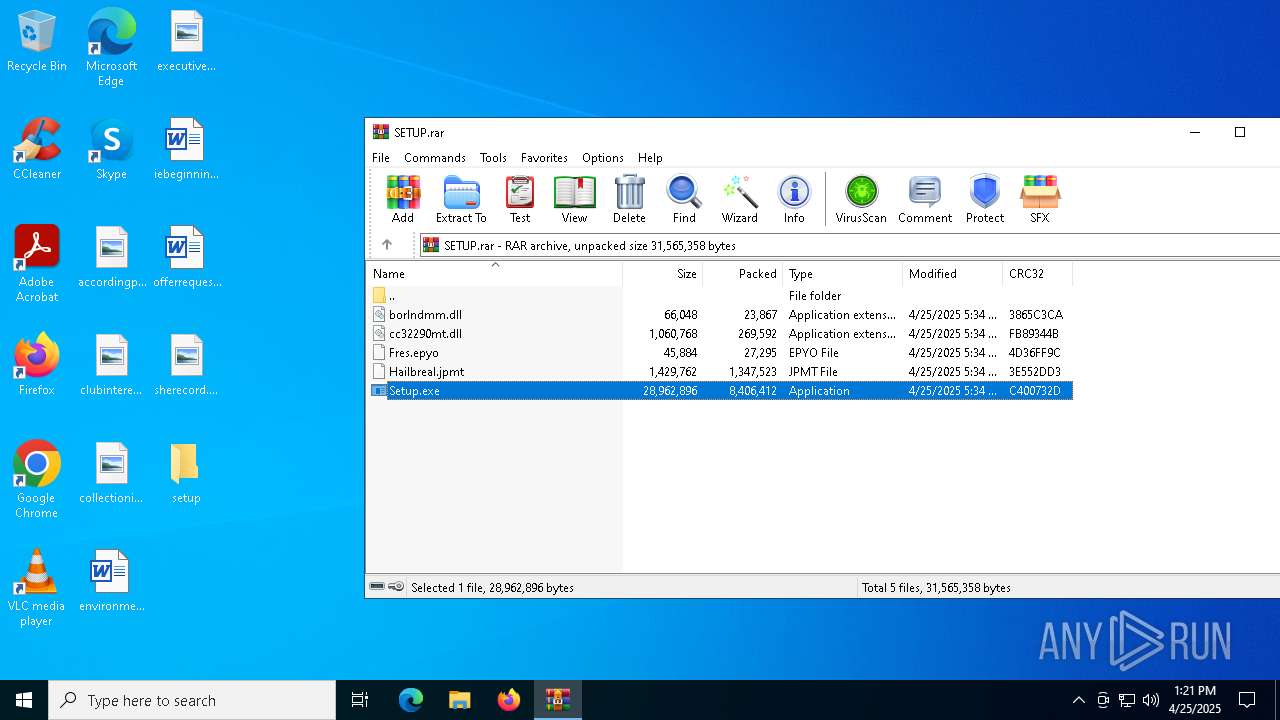
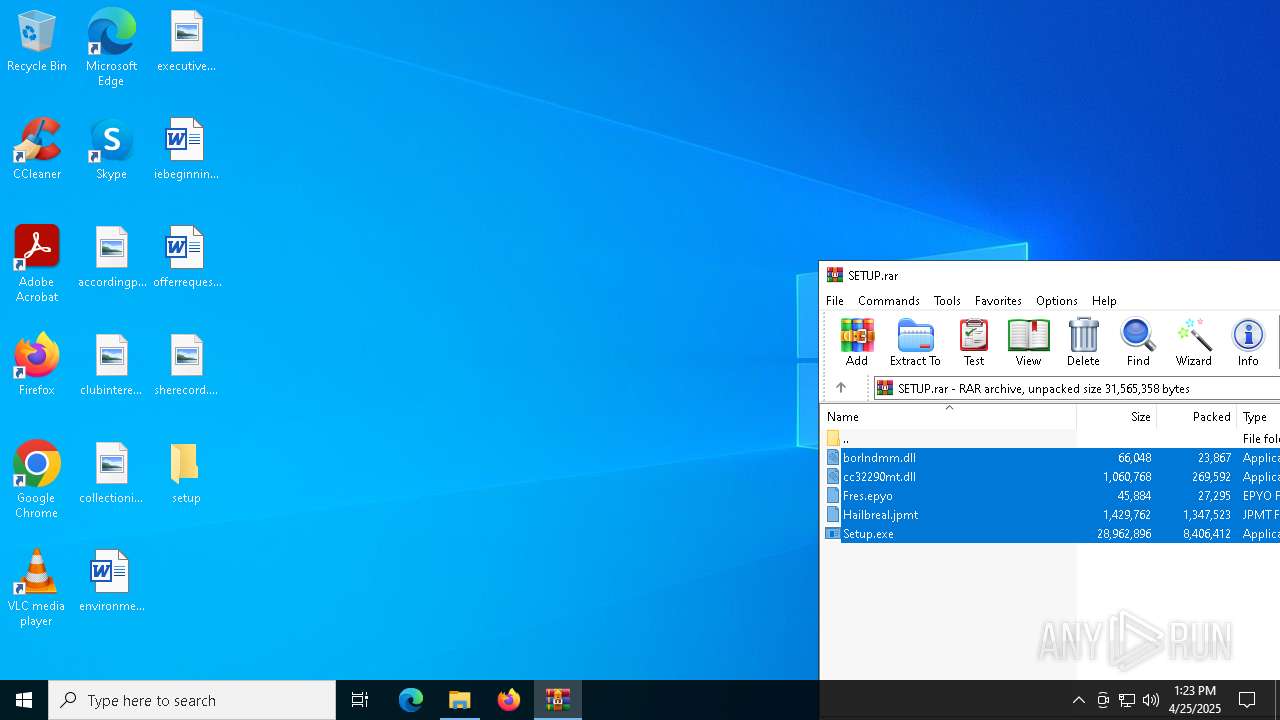
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | D35BD7D8CAF3216BE5AF5814AD4DCDE7 |
| SHA1: | 15F68EED152211839EBC342FFA556F508D458858 |
| SHA256: | 9FDBBA3903346CD556B18241CE138563C2433A1D94D8A5CB8EB48114EF9419F2 |
| SSDEEP: | 98304:XilI8V+7HpsiVCeHQCtBWHq7e8WNYMRk58DSeQgRdELlyI7KHzE6krzWDEbxJxNS:JCq8hNwskk/Hcofc9qRb |
MALICIOUS
GENERIC has been found (auto)
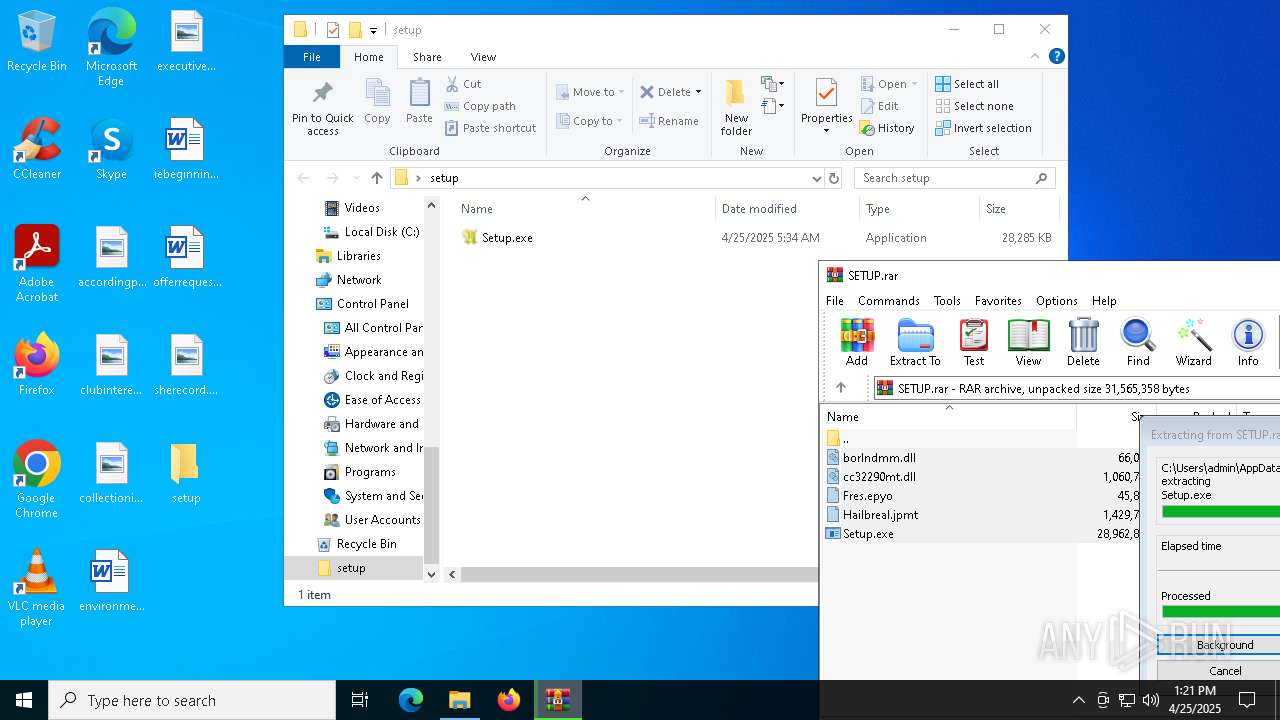
- WinRAR.exe (PID: 7220)
LUMMA has been detected (YARA)
- Commelina.com (PID: 8128)
Actions looks like stealing of personal data
- Commelina.com (PID: 8128)
Steals credentials from Web Browsers
- Commelina.com (PID: 8128)
LUMMA mutex has been found
- Commelina.com (PID: 8128)
SUSPICIOUS
There is functionality for taking screenshot (YARA)
- Commelina.com (PID: 8128)
- B1HNXVBKKIFR6KBFO4XBIDYQRO5J68W.exe (PID: 3240)
Searches for installed software
- Commelina.com (PID: 8128)
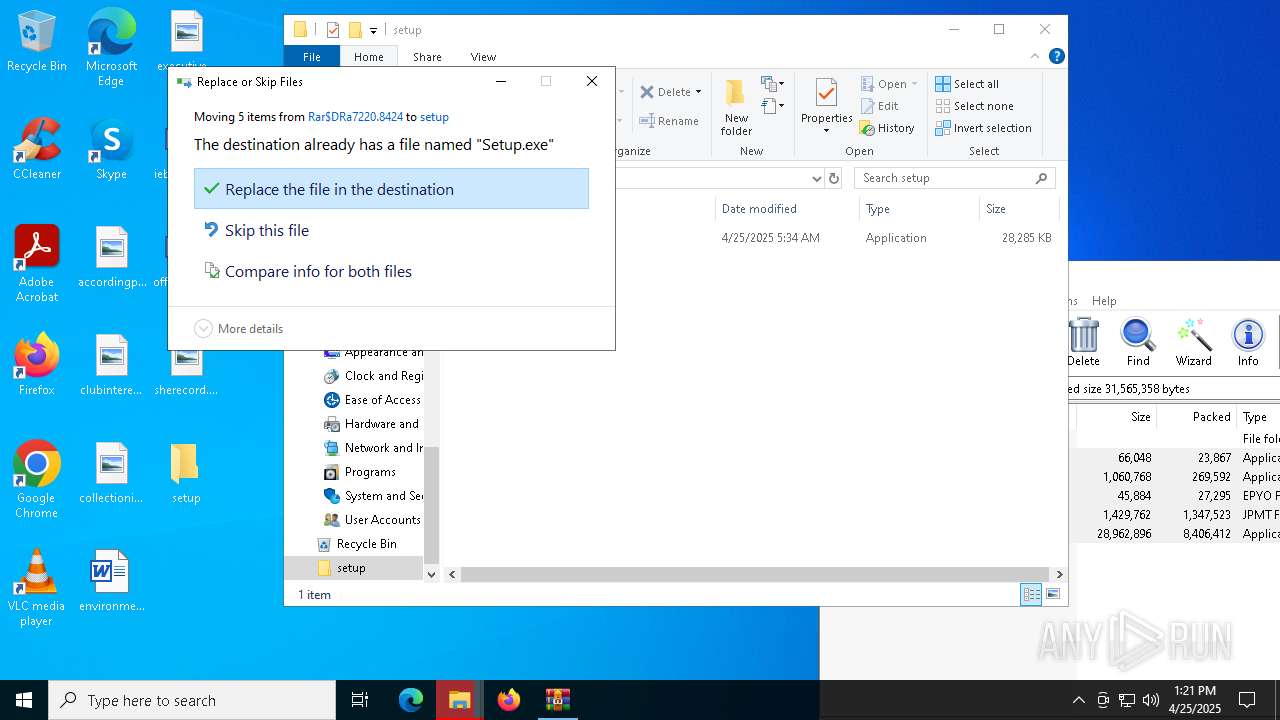
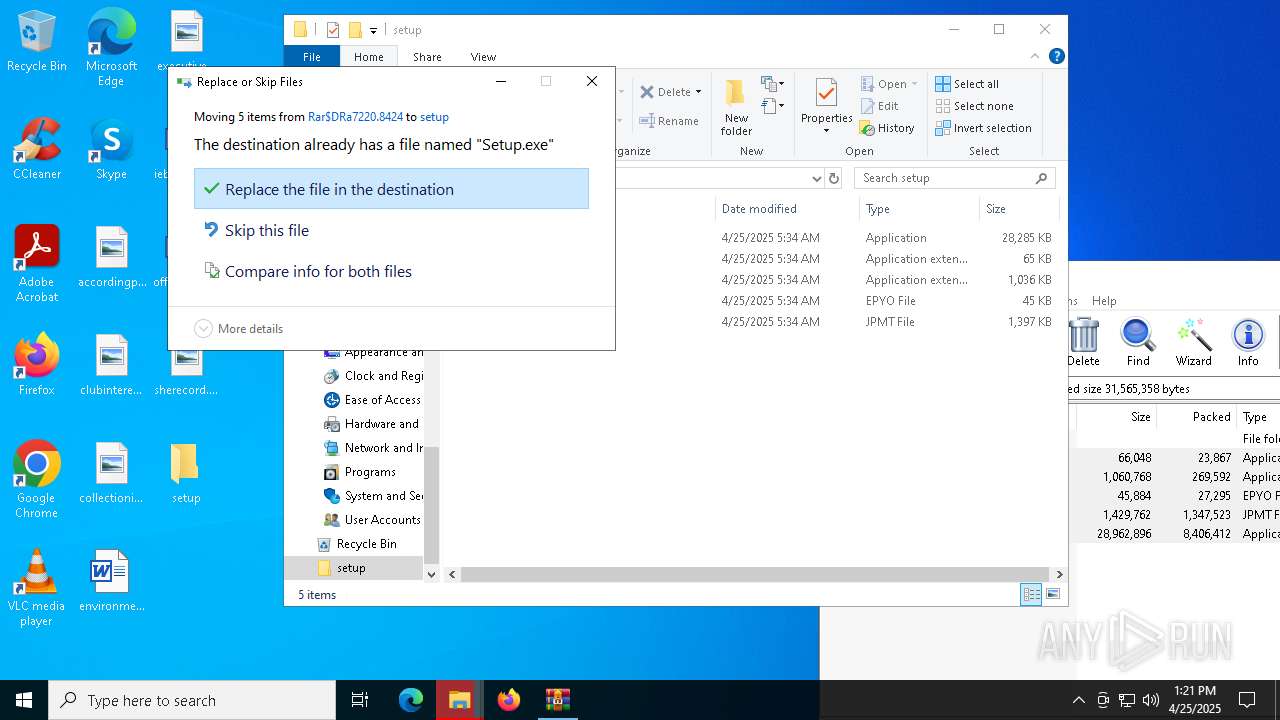
Executable content was dropped or overwritten
- Commelina.com (PID: 8128)
- Setup.exe (PID: 8100)
Connects to unusual port
- B1HNXVBKKIFR6KBFO4XBIDYQRO5J68W.exe (PID: 3240)
Executes application which crashes
- B1HNXVBKKIFR6KBFO4XBIDYQRO5J68W.exe (PID: 3240)
Starts application with an unusual extension
- Setup.exe (PID: 8100)
INFO
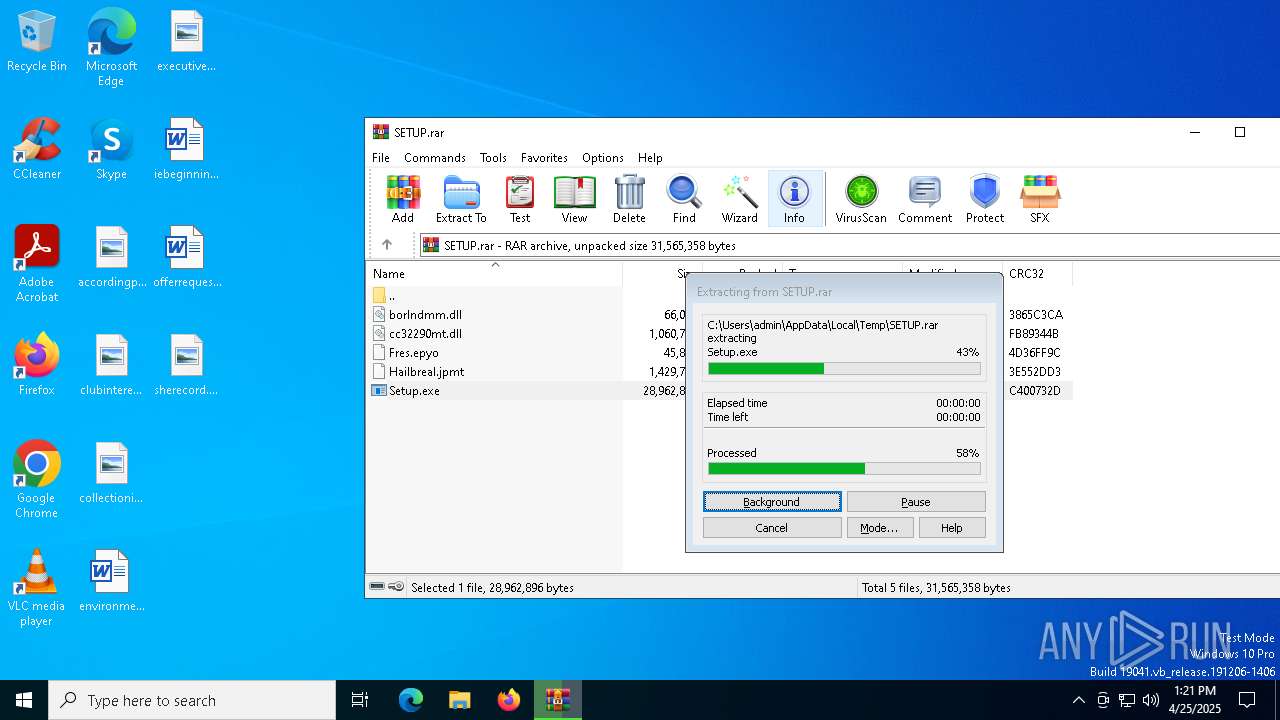
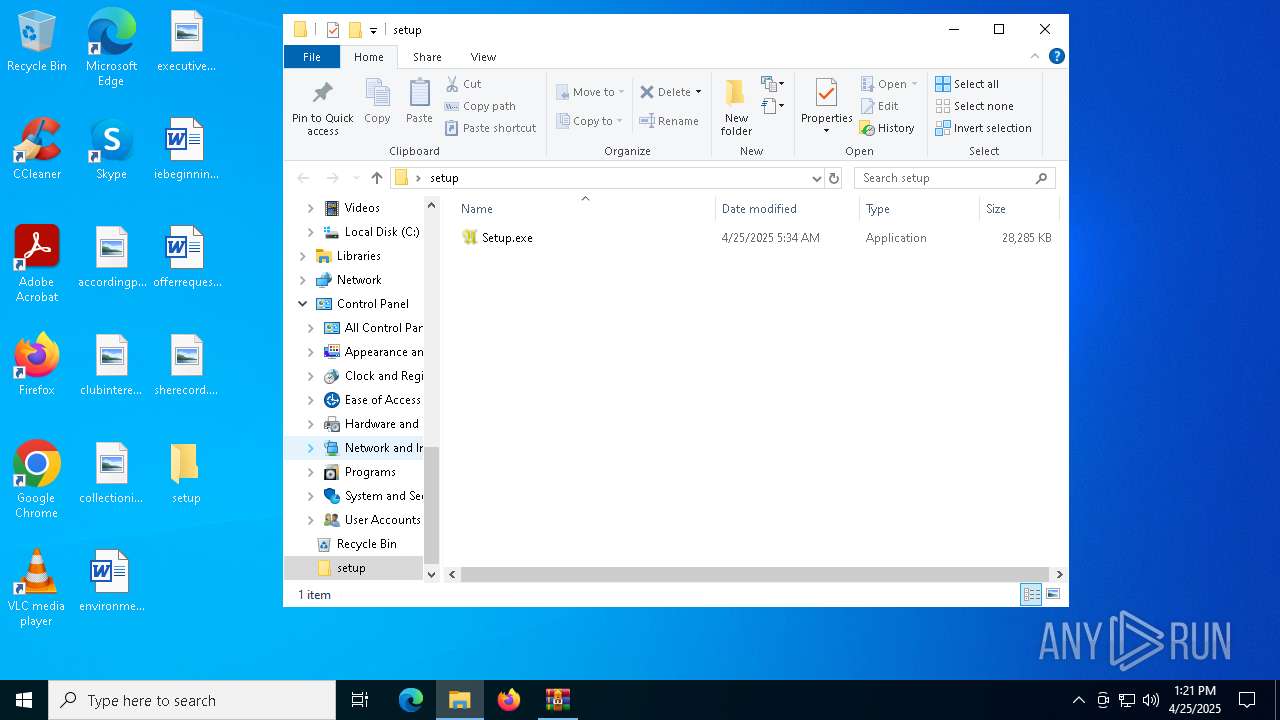
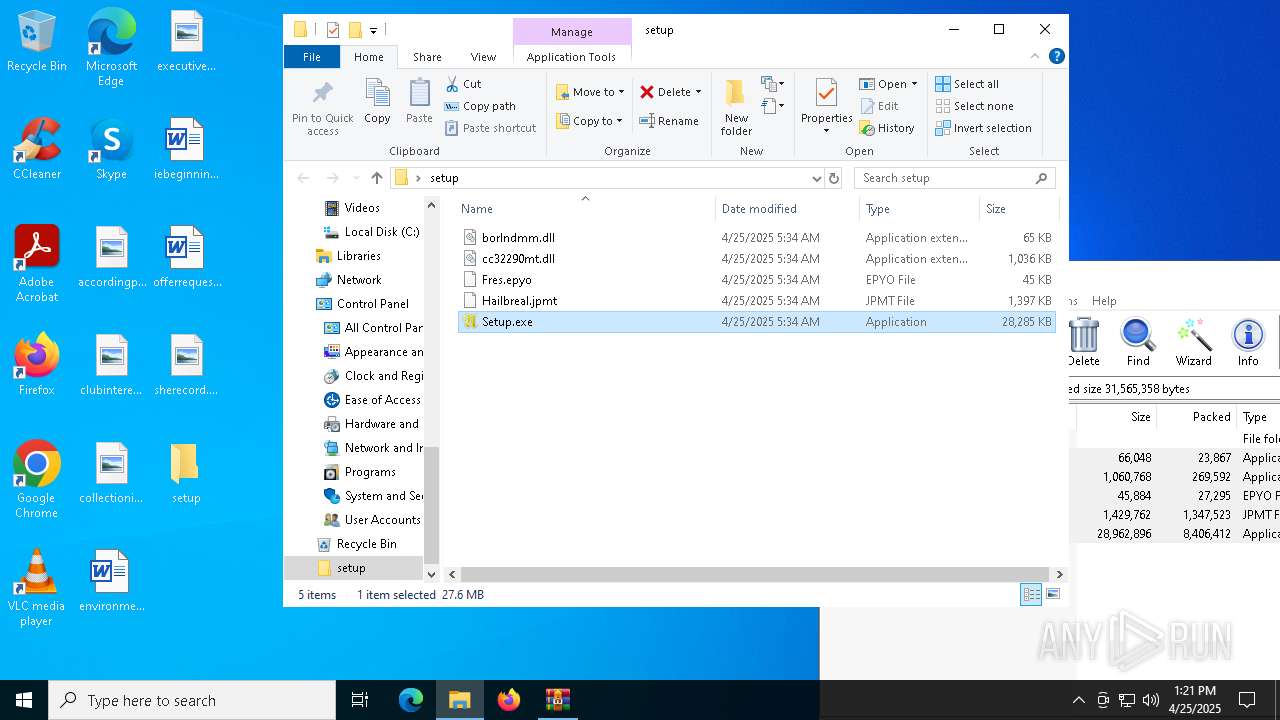
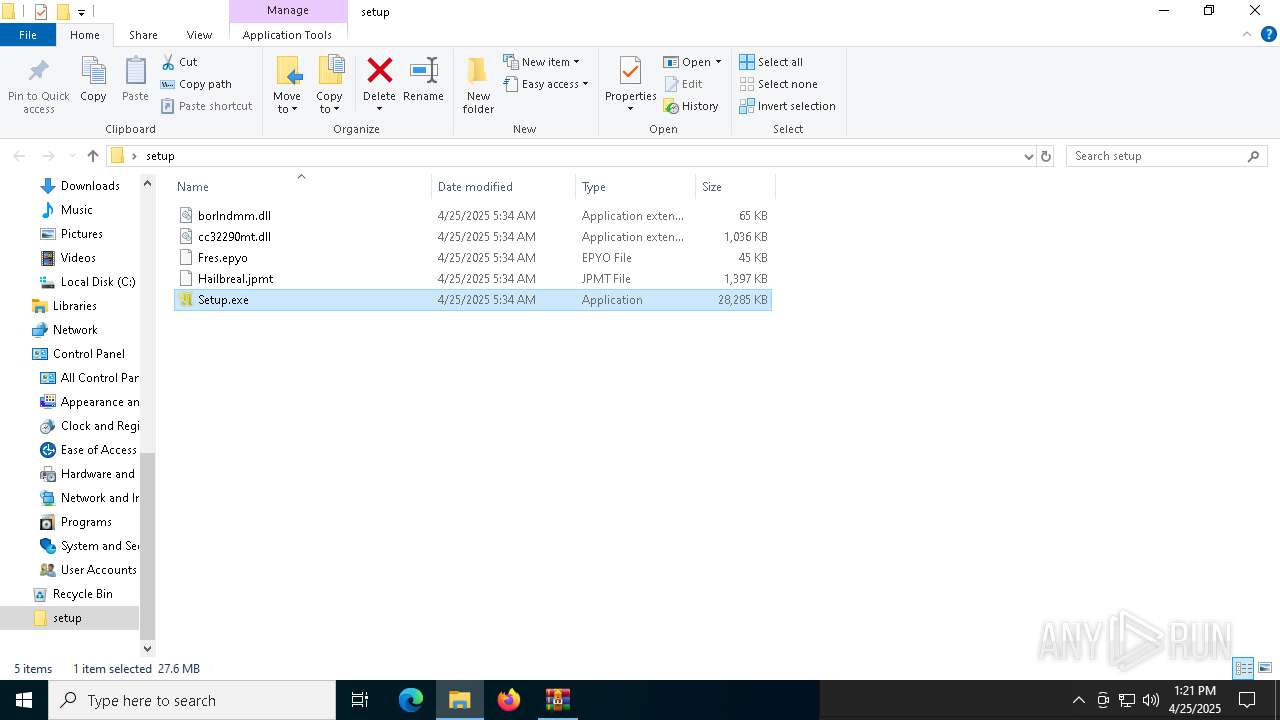
Manual execution by a user
- Setup.exe (PID: 8100)
The sample compiled with english language support
- WinRAR.exe (PID: 7220)
- Setup.exe (PID: 8100)
Reads the software policy settings
- slui.exe (PID: 7876)
- Commelina.com (PID: 8128)
- B1HNXVBKKIFR6KBFO4XBIDYQRO5J68W.exe (PID: 3240)
Reads the computer name
- Commelina.com (PID: 8128)
- Setup.exe (PID: 8100)
- B1HNXVBKKIFR6KBFO4XBIDYQRO5J68W.exe (PID: 3240)
Checks proxy server information
- slui.exe (PID: 7876)
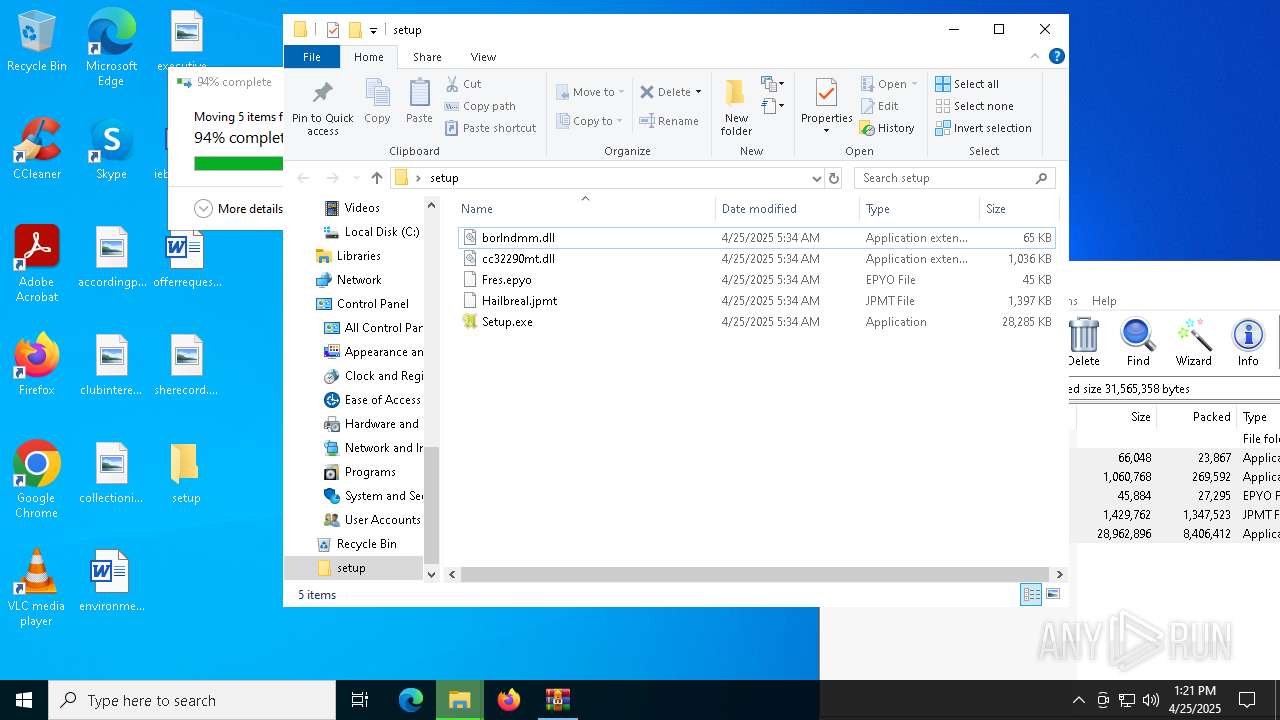
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7220)
Checks supported languages
- Setup.exe (PID: 8100)
- B1HNXVBKKIFR6KBFO4XBIDYQRO5J68W.exe (PID: 3240)
- Commelina.com (PID: 8128)
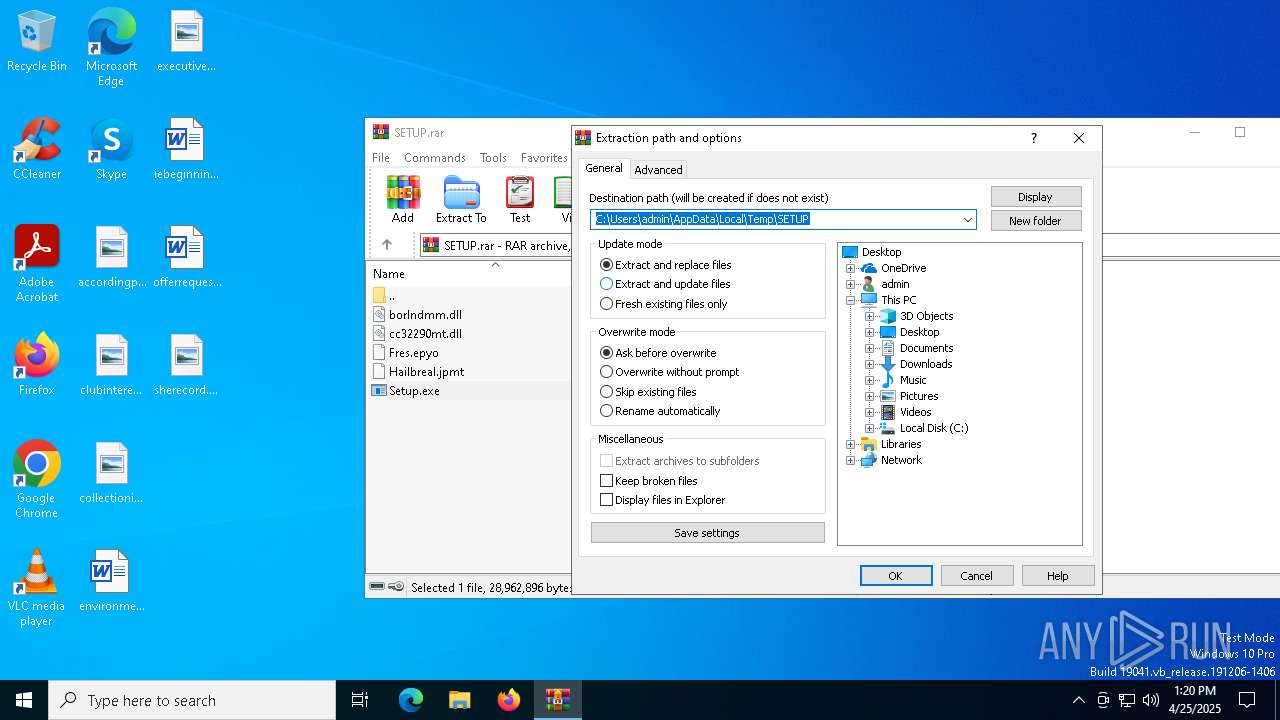
Create files in a temporary directory
- Commelina.com (PID: 8128)
- Setup.exe (PID: 8100)
Compiled with Borland Delphi (YARA)
- B1HNXVBKKIFR6KBFO4XBIDYQRO5J68W.exe (PID: 3240)
- Setup.exe (PID: 8100)
Reads the machine GUID from the registry
- B1HNXVBKKIFR6KBFO4XBIDYQRO5J68W.exe (PID: 3240)
Creates files in the program directory
- Setup.exe (PID: 8100)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|---|
| CompressedSize: | 23867 |
| UncompressedSize: | 66048 |
| OperatingSystem: | Win32 |
| ArchivedFileName: | borlndmm.dll |
Total processes
158
Monitored processes
15
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 904 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 3240 -s 876 | C:\Windows\SysWOW64\WerFault.exe | — | B1HNXVBKKIFR6KBFO4XBIDYQRO5J68W.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2560 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 3240 -s 948 | C:\Windows\SysWOW64\WerFault.exe | — | B1HNXVBKKIFR6KBFO4XBIDYQRO5J68W.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3240 | "C:\Users\admin\AppData\Local\Temp\B1HNXVBKKIFR6KBFO4XBIDYQRO5J68W.exe" | C:\Users\admin\AppData\Local\Temp\B1HNXVBKKIFR6KBFO4XBIDYQRO5J68W.exe | Commelina.com | ||||||||||||
User: admin Company: Greenshot Integrity Level: MEDIUM Description: Greenshot Version: 1.2.9.129 Modules
| |||||||||||||||
| 4756 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 3240 -s 640 | C:\Windows\SysWOW64\WerFault.exe | — | B1HNXVBKKIFR6KBFO4XBIDYQRO5J68W.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5376 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 3240 -s 580 | C:\Windows\SysWOW64\WerFault.exe | — | B1HNXVBKKIFR6KBFO4XBIDYQRO5J68W.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5408 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 3240 -s 616 | C:\Windows\SysWOW64\WerFault.exe | — | B1HNXVBKKIFR6KBFO4XBIDYQRO5J68W.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6040 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 3240 -s 1408 | C:\Windows\SysWOW64\WerFault.exe | — | B1HNXVBKKIFR6KBFO4XBIDYQRO5J68W.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6372 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 3240 -s 580 | C:\Windows\SysWOW64\WerFault.exe | — | B1HNXVBKKIFR6KBFO4XBIDYQRO5J68W.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
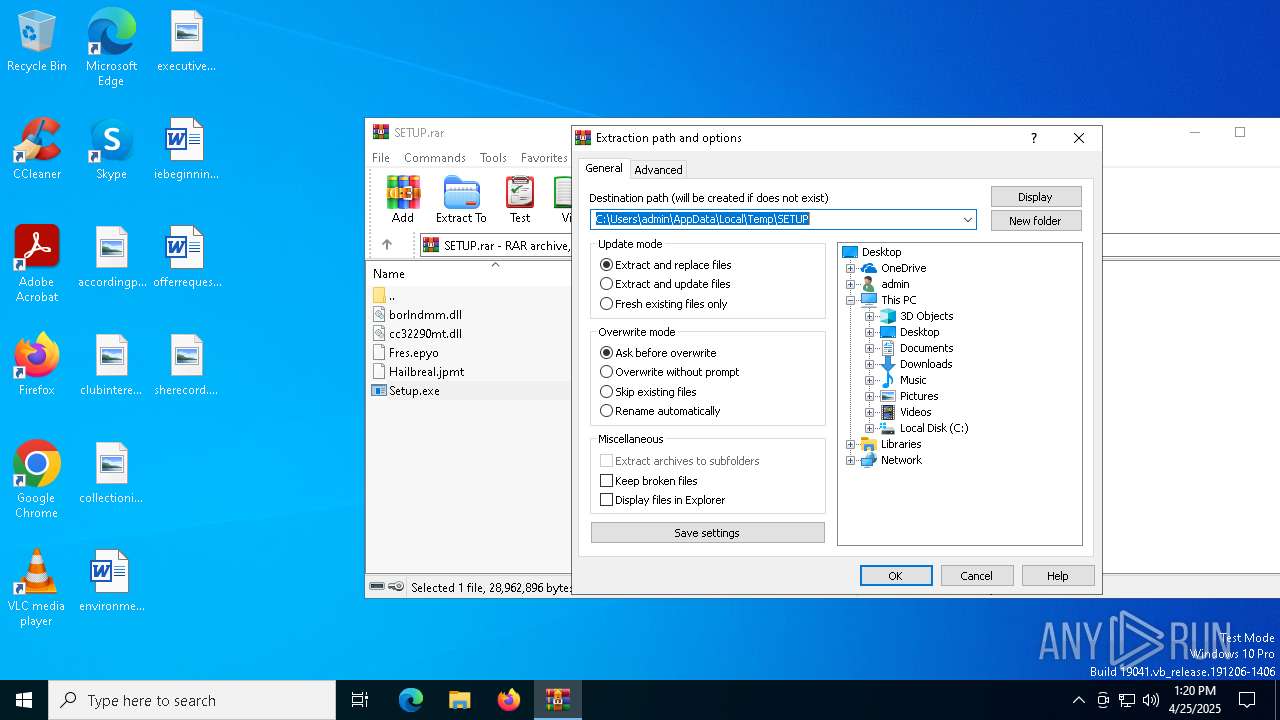
| 7220 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\SETUP.rar | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 7484 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 3240 -s 1596 | C:\Windows\SysWOW64\WerFault.exe | — | B1HNXVBKKIFR6KBFO4XBIDYQRO5J68W.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
9 241
Read events
9 217
Write events
11
Delete events
13
Modification events
| (PID) Process: | (7220) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7220) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7220) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7220) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\SETUP.rar | |||
| (PID) Process: | (7220) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7220) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7220) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7220) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7220) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 15 |
Value: | |||
| (PID) Process: | (7220) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 14 |
Value: | |||
Executable files
8
Suspicious files
6
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 8100 | Setup.exe | C:\Users\admin\AppData\Local\Temp\C684CF0.tmp | — | |
MD5:— | SHA256:— | |||
| 7220 | WinRAR.exe | C:\Users\admin\Desktop\setup\Setup.exe | executable | |
MD5:950F3BEBB7563EE8354B21EF9CBEA4A2 | SHA256:8F4F53BC02348A549F3437444AACEC43EAE5F90875EA3C5EC96600BA1CB4A061 | |||
| 7220 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7220.8424\cc32290mt.dll | executable | |
MD5:9F481987D195C59039C9703E48D445BE | SHA256:BA296434EE777FBBFA2A2EC2713AF3CF4E44DDC7D1AB58BE847753AF17DA0FBD | |||
| 8100 | Setup.exe | C:\Users\admin\AppData\Local\Temp\2276626.tmp | binary | |
MD5:F616FBB5051C102035860F6B61443FC5 | SHA256:37FBA1F0A0C8BD988DDB06FB4B3CCFC6FA78518EC4C4E3693B7FCE9177091E4D | |||
| 8100 | Setup.exe | C:\ProgramData\sliz_png_2\Fres.epyo | binary | |
MD5:7BE13EEBBC01888A41E1C6BAD59CADD6 | SHA256:C1B1AFECB6CF19BE939C029D5BBB9C51DE6E5BC974F36DFE98E0EEB5328D0C9A | |||
| 8100 | Setup.exe | C:\ProgramData\sliz_png_2\borlndmm.dll | executable | |
MD5:6272E6A937FF4B7A390251952B2438E9 | SHA256:81E5E63468B98CCA9C961844A2C6B98D1AF9F825651686F4AD6D0E33B22C802F | |||
| 8100 | Setup.exe | C:\Users\admin\AppData\Local\Temp\167404D.tmp | binary | |
MD5:1F042384432C801EA4C57A6FE6AD73C0 | SHA256:401C59AA9A35F19C51997A2C6504B9953F46837BC56EA75AA7929A200C9B22CD | |||
| 7220 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7220.8424\borlndmm.dll | executable | |
MD5:6272E6A937FF4B7A390251952B2438E9 | SHA256:81E5E63468B98CCA9C961844A2C6B98D1AF9F825651686F4AD6D0E33B22C802F | |||
| 7220 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7220.8424\Fres.epyo | binary | |
MD5:7BE13EEBBC01888A41E1C6BAD59CADD6 | SHA256:C1B1AFECB6CF19BE939C029D5BBB9C51DE6E5BC974F36DFE98E0EEB5328D0C9A | |||
| 7220 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7220.8424\Hailbreal.jpmt | binary | |
MD5:B4876CC930BBC58CE3510363EE02C569 | SHA256:2DBF38B3DB7B8ECCFEEDA4376820EFE0759231D6DF1B79BFC2E7CE0104216806 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
43
DNS requests
21
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 92.122.244.42:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.61.29.203:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.61.29.203:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7712 | SIHClient.exe | GET | 200 | 23.61.29.203:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 23.63.118.230:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7712 | SIHClient.exe | GET | 200 | 23.61.29.203:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 92.122.244.42:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.61.29.203:80 | www.microsoft.com | NTT DOCOMO, INC. | JP | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.61.29.203:80 | www.microsoft.com | NTT DOCOMO, INC. | JP | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2112 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.159.73:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Misc activity | ET TA_ABUSED_SERVICES DNS Query to Commonly Actor Abused Online Service (data-seed-prebsc-2-s1 .binance .org) |
3240 | B1HNXVBKKIFR6KBFO4XBIDYQRO5J68W.exe | Misc activity | ET TA_ABUSED_SERVICES Observed Commonly Actor Abused Online Service Domain (data-seed-prebsc-2-s1 .binance .org in TLS SNI) |