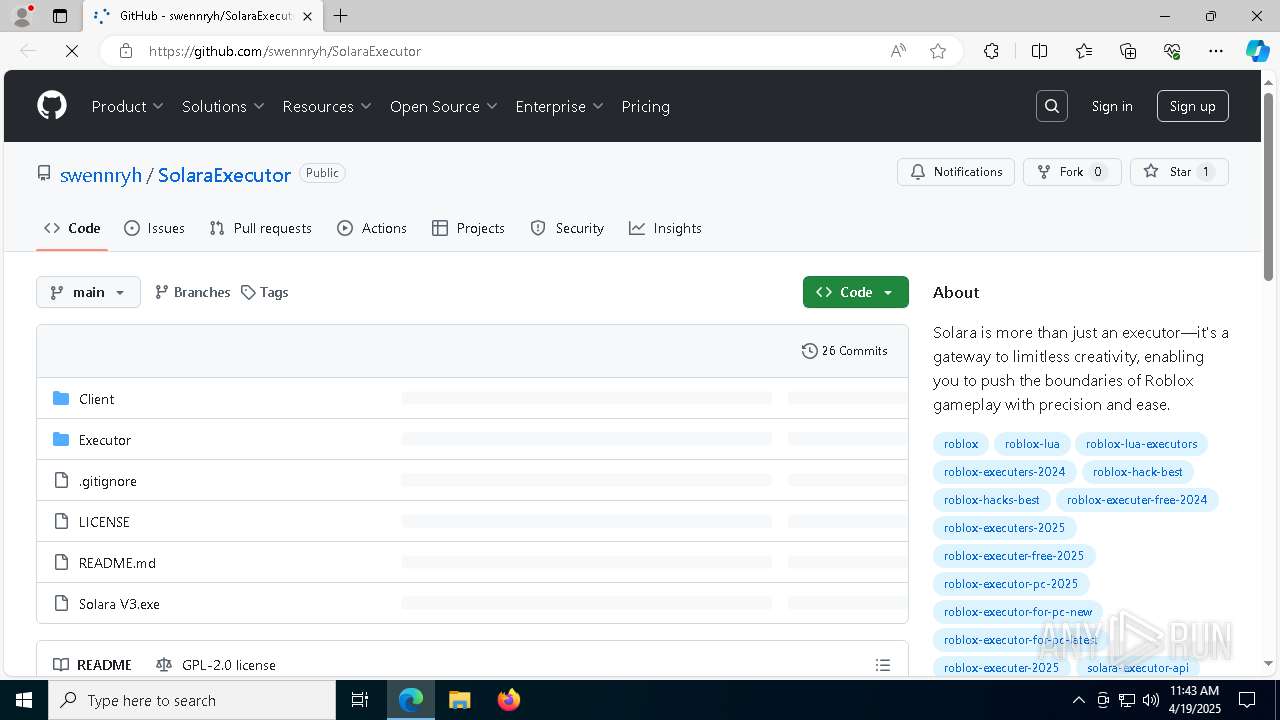
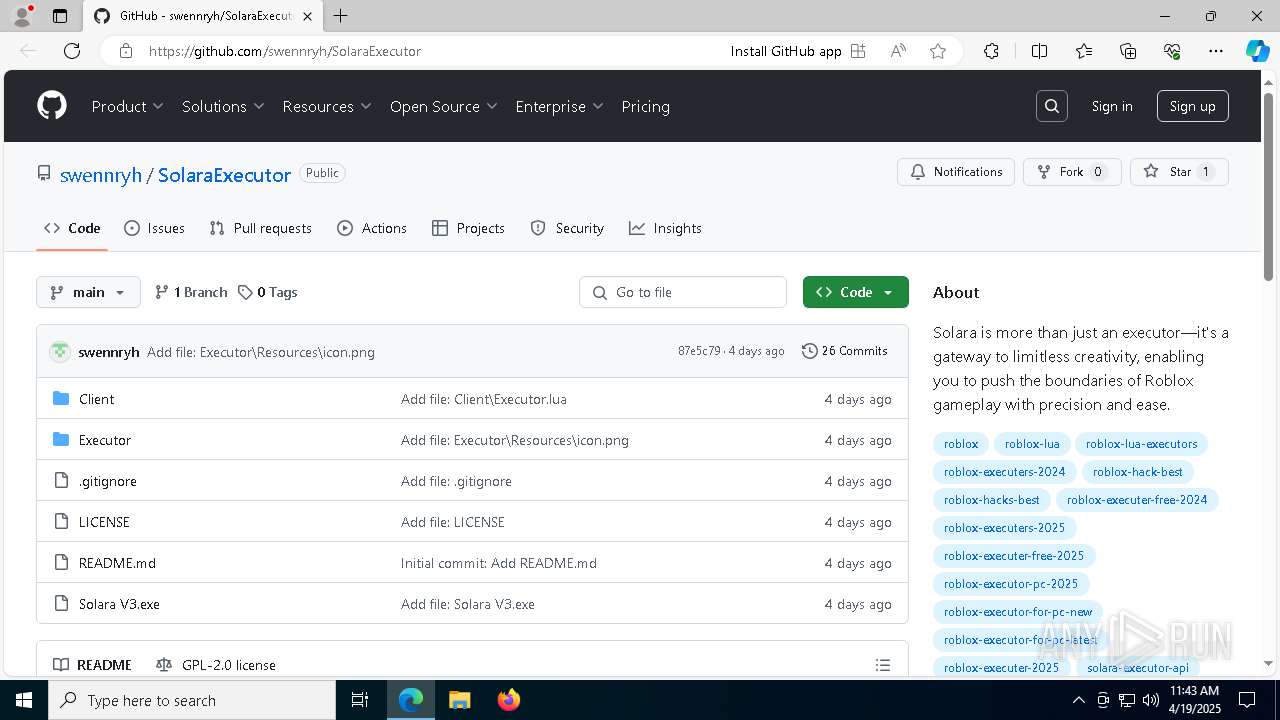
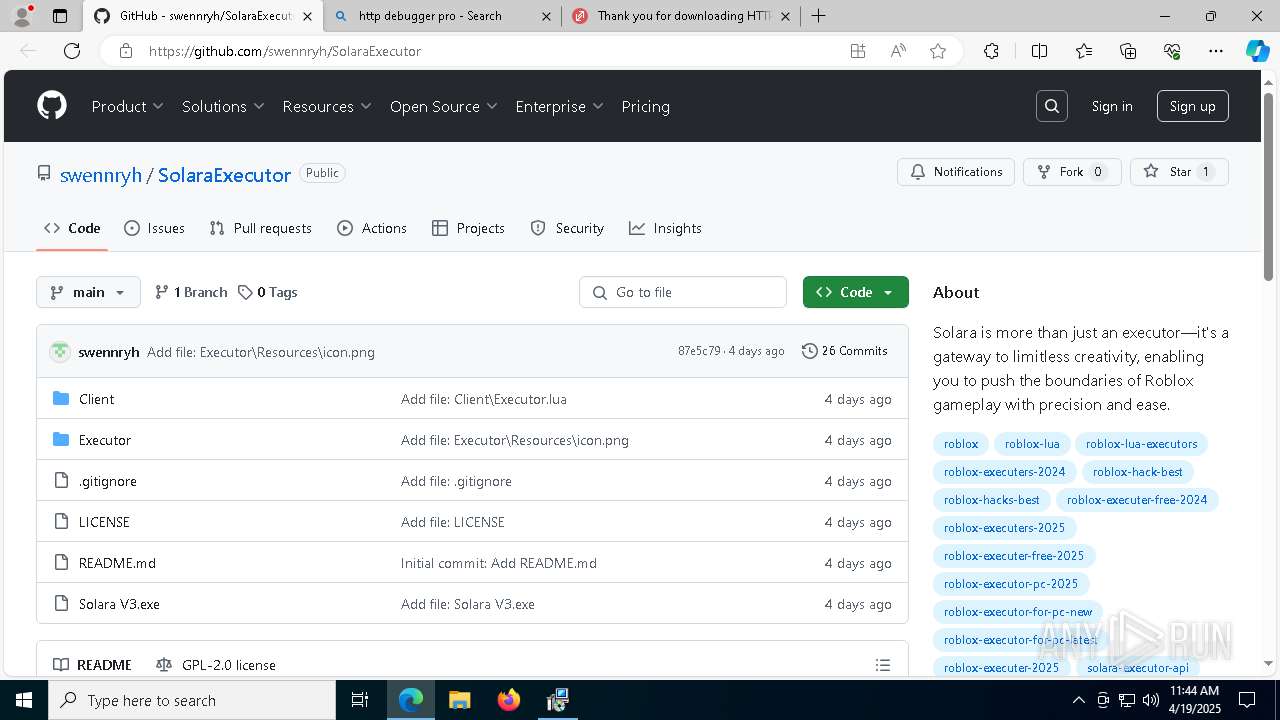
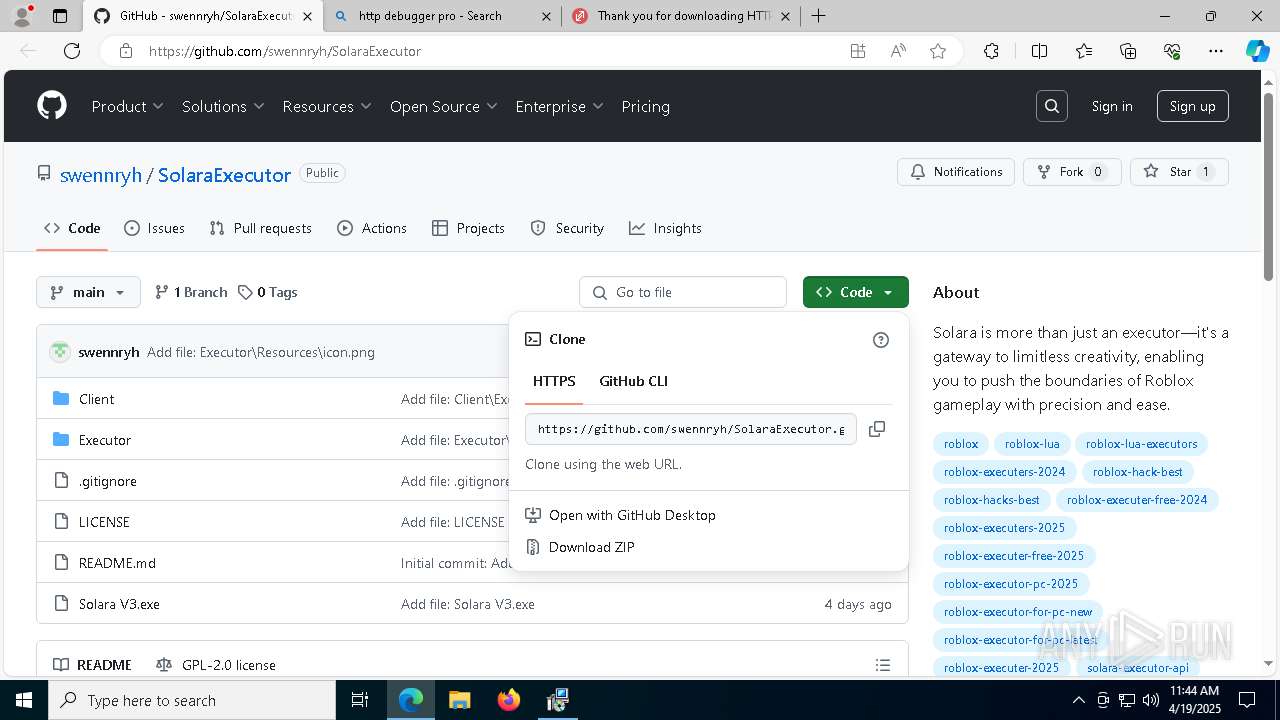
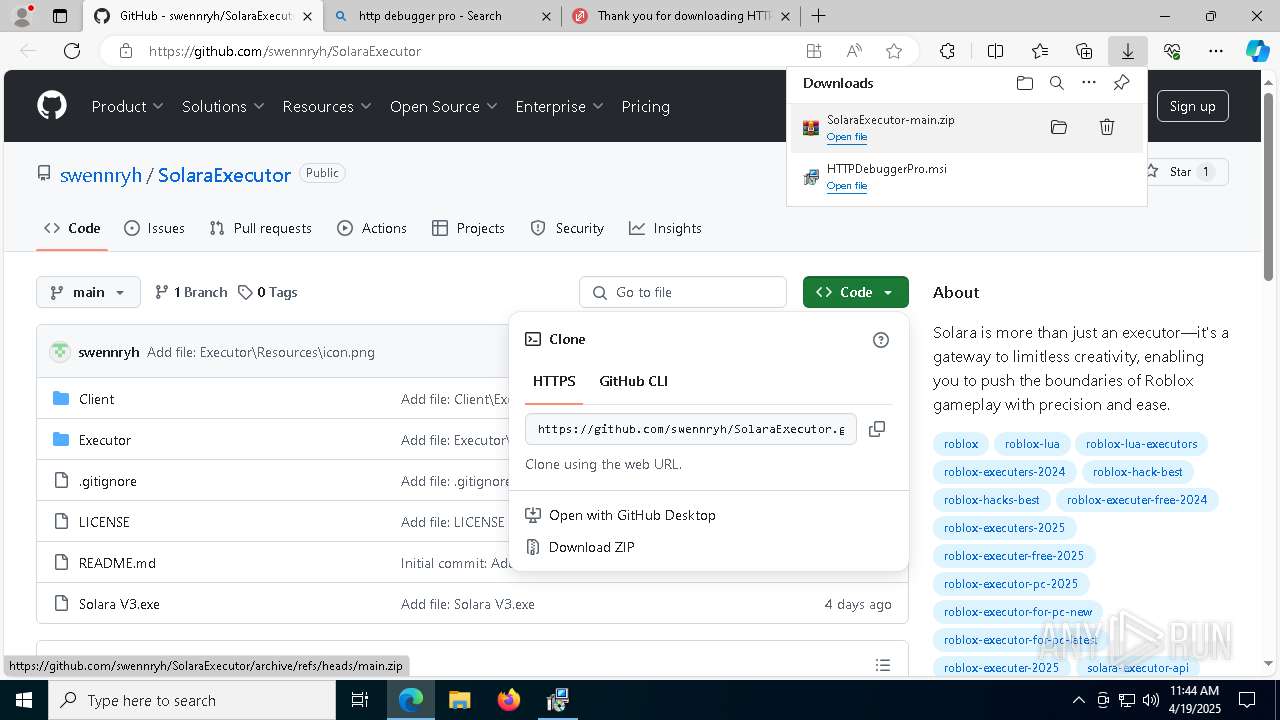
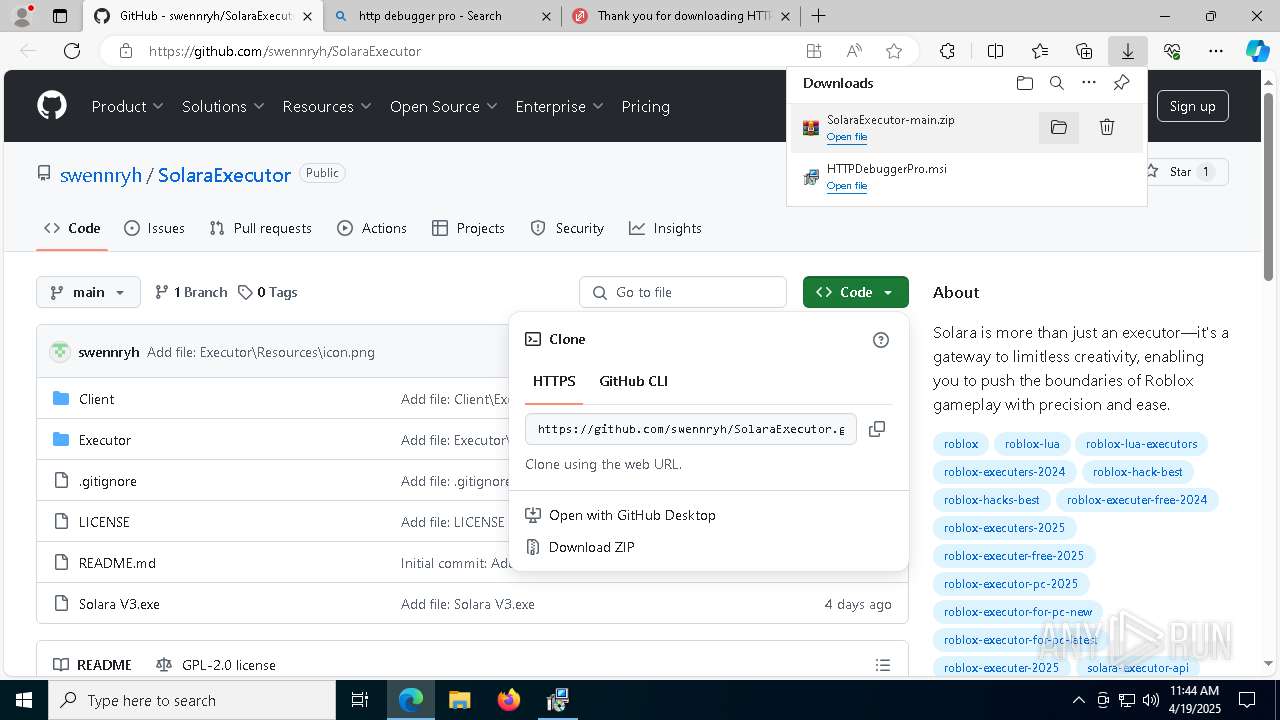
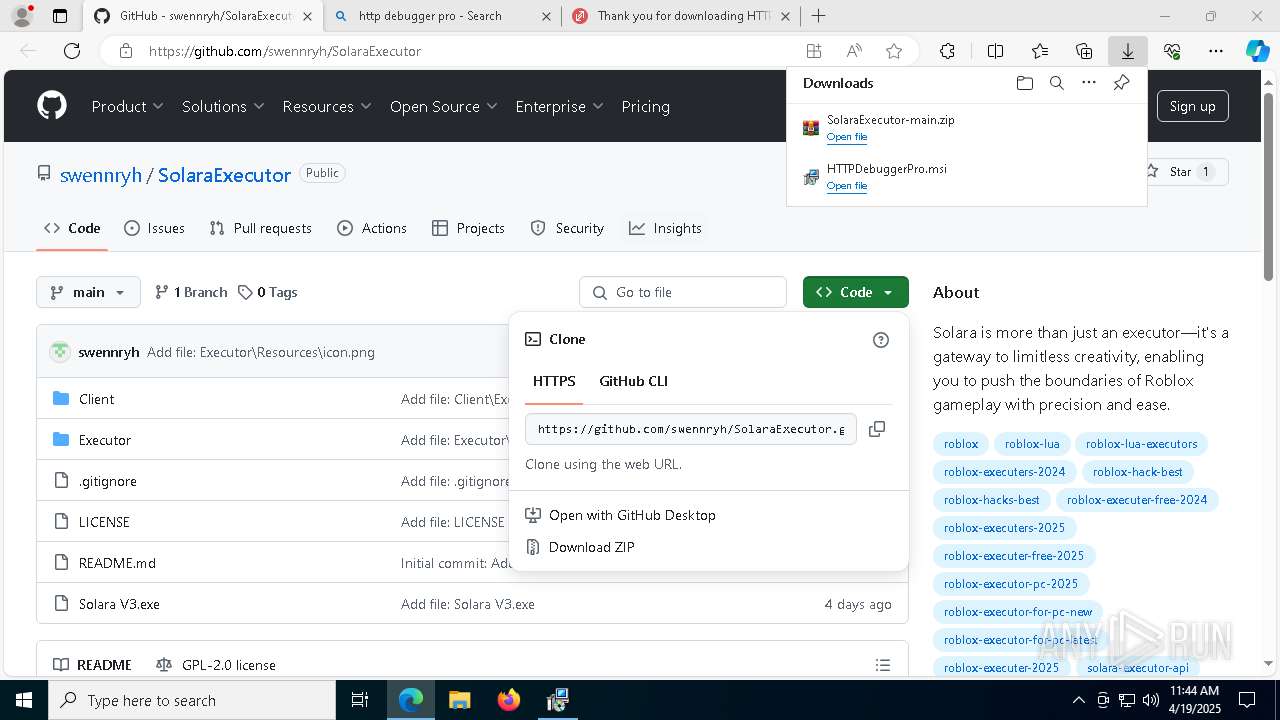
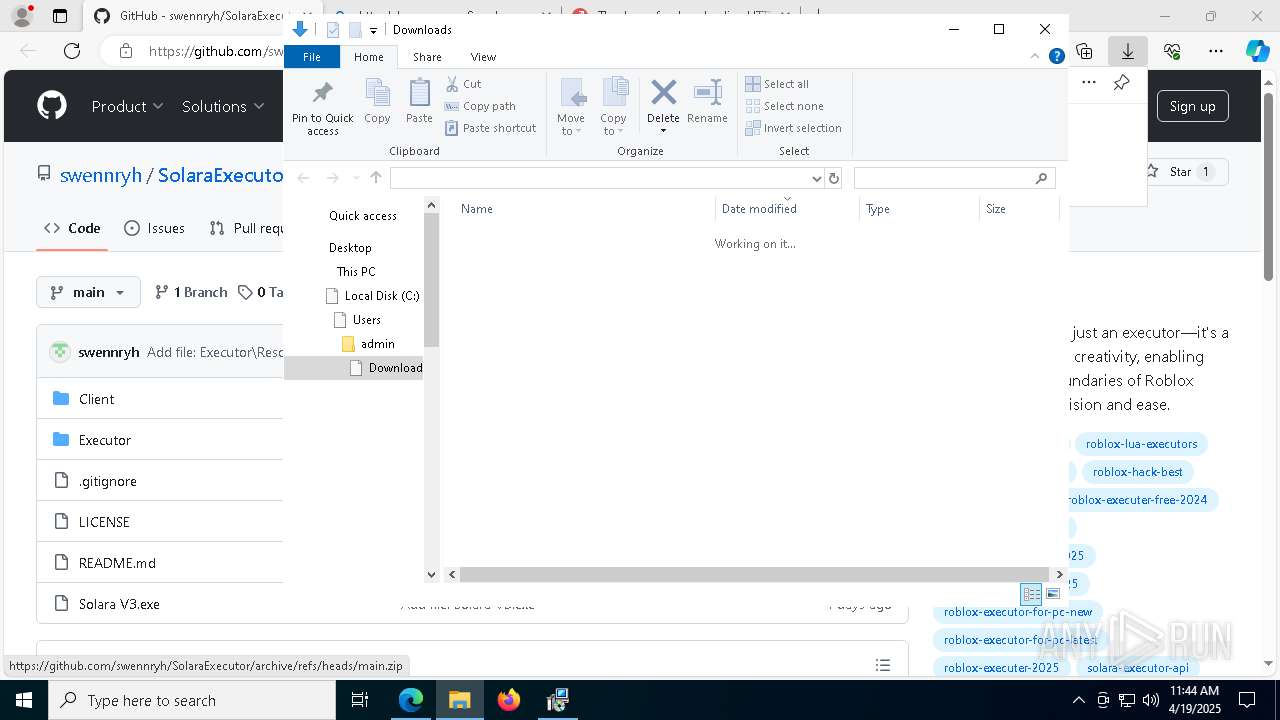
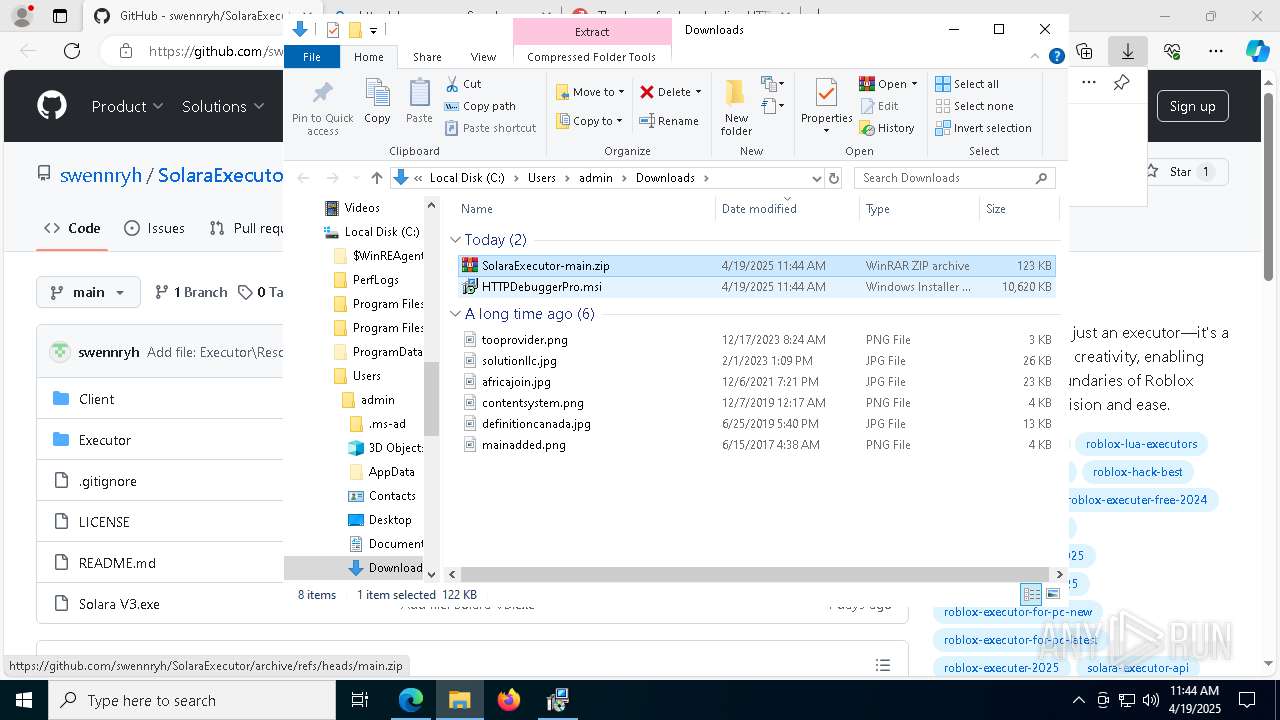
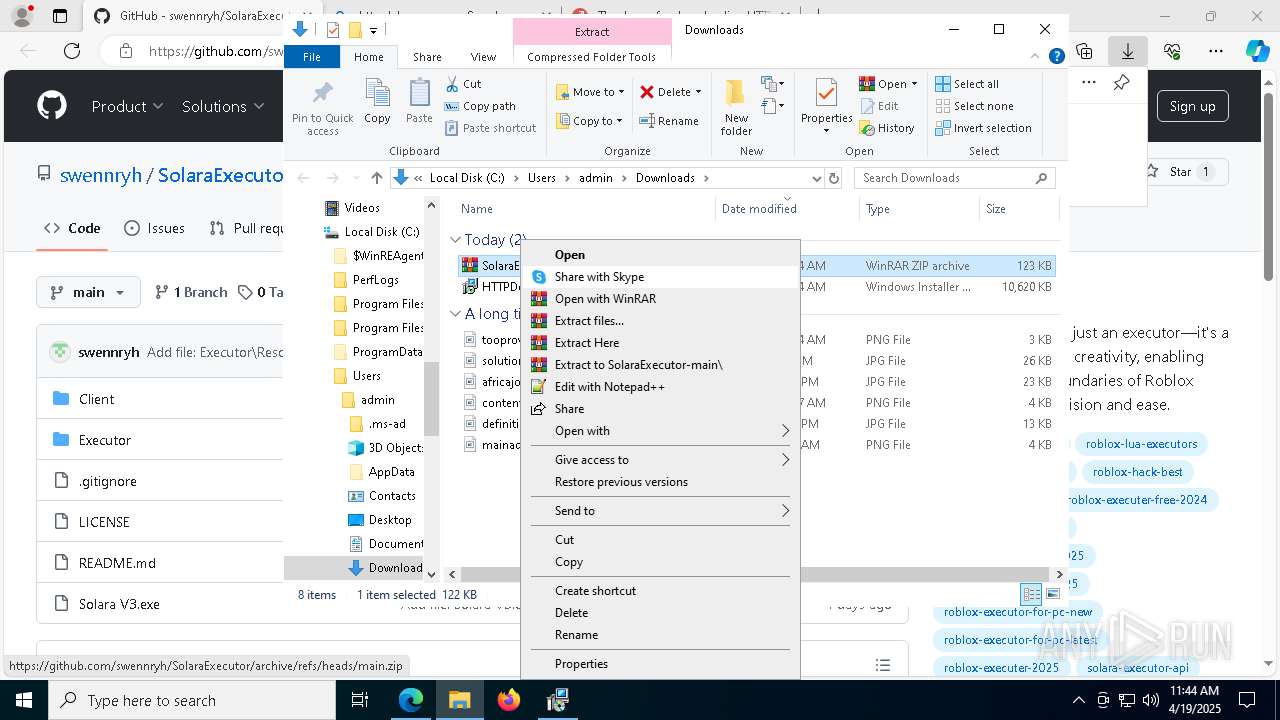
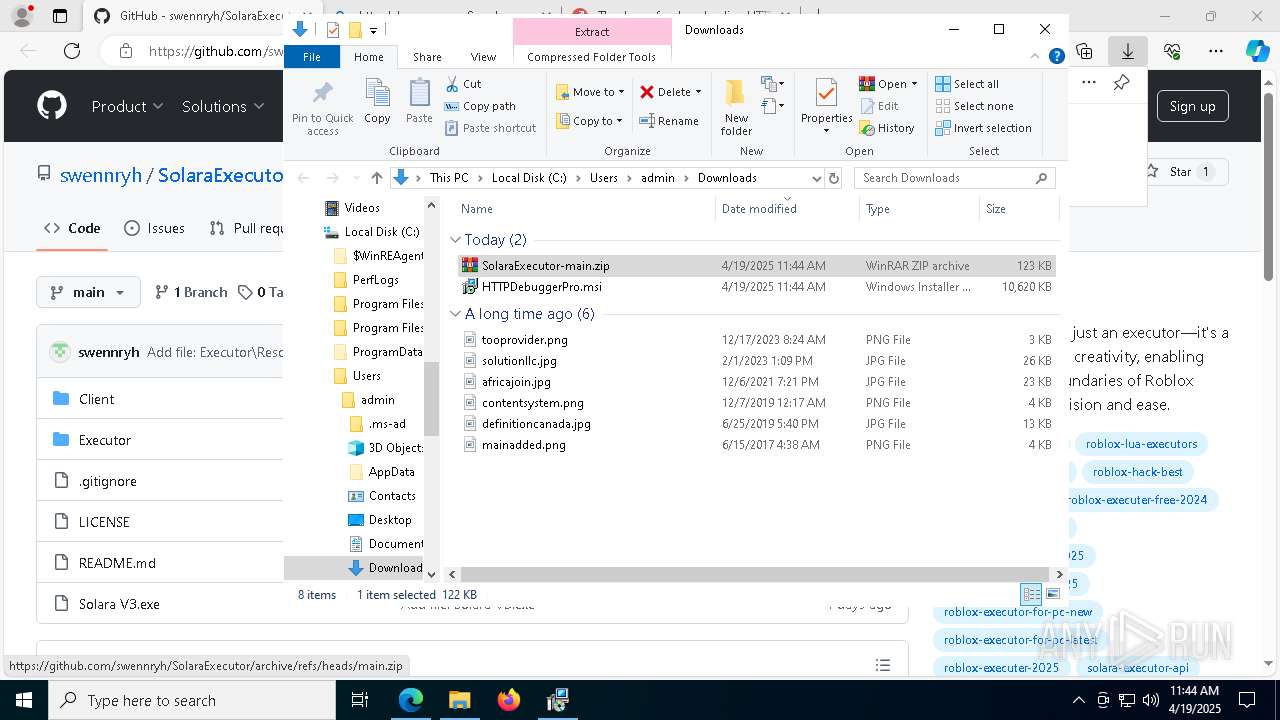
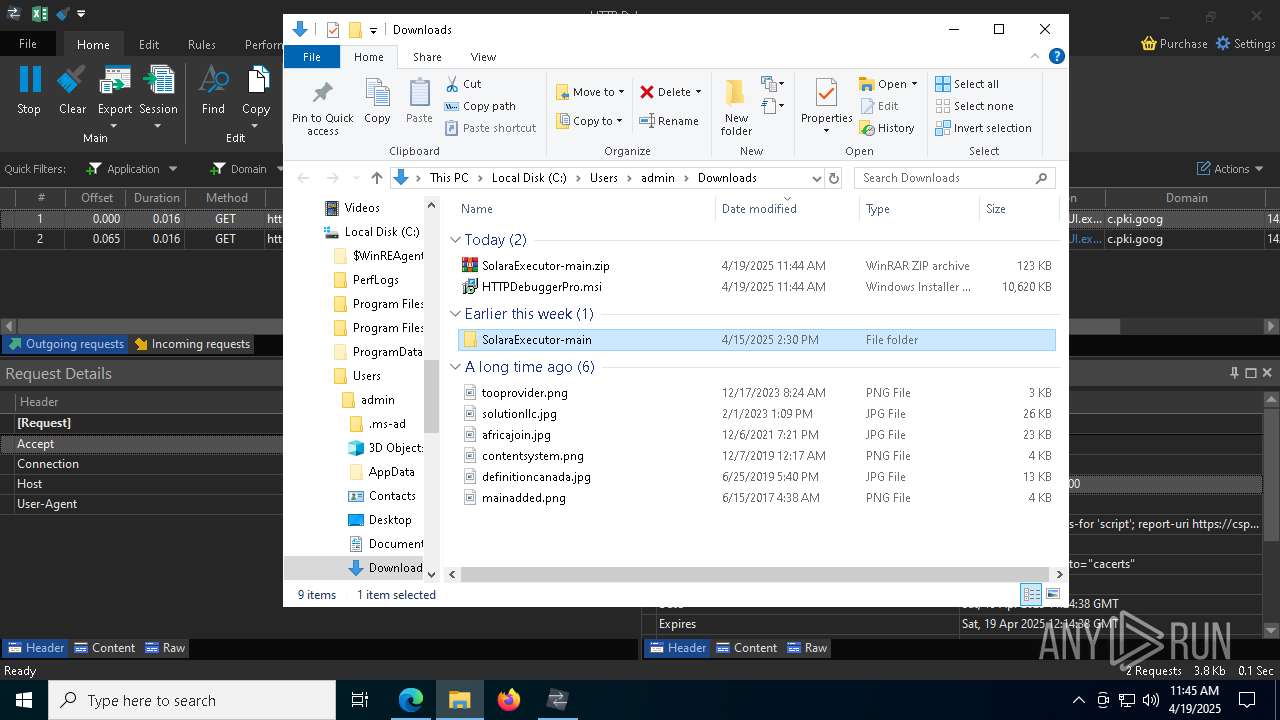
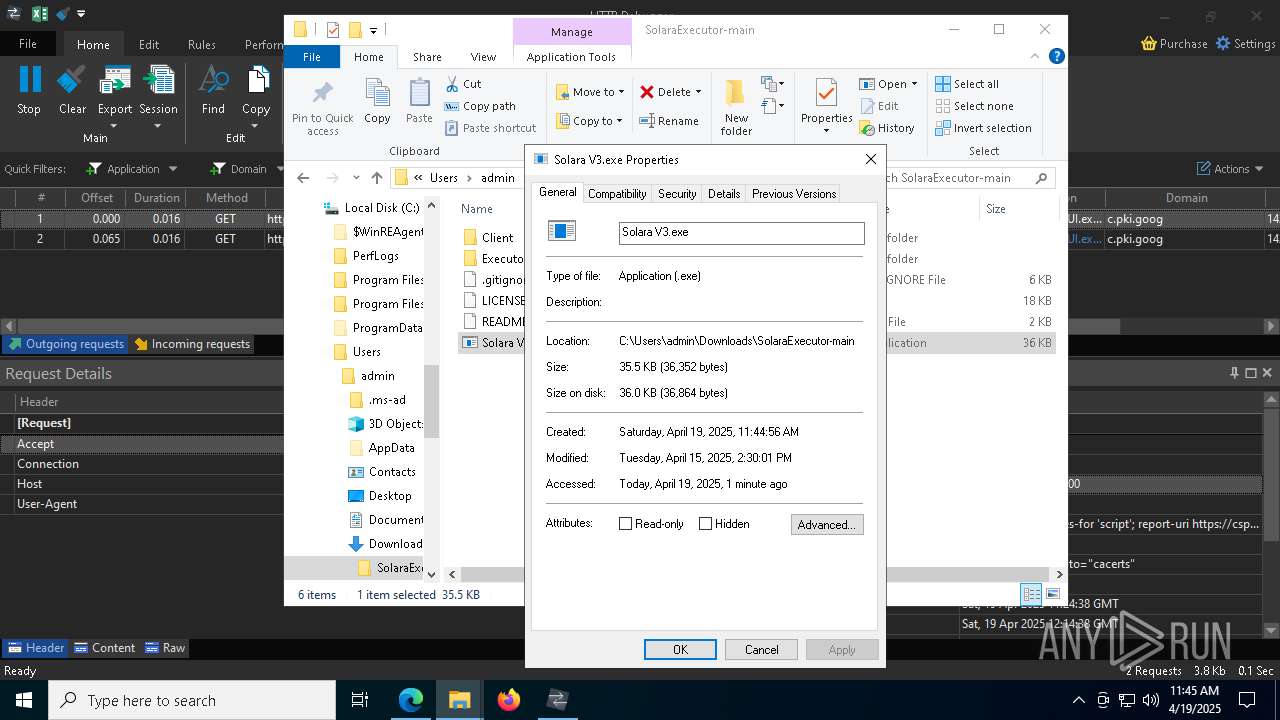
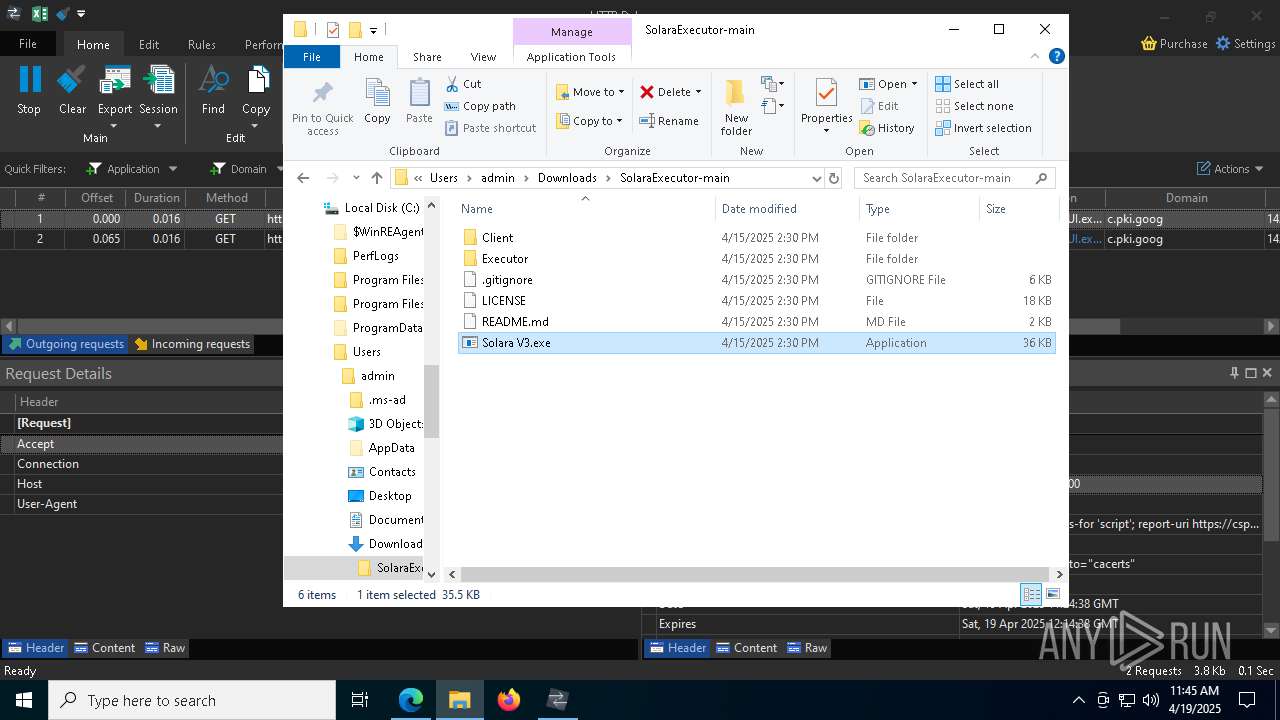
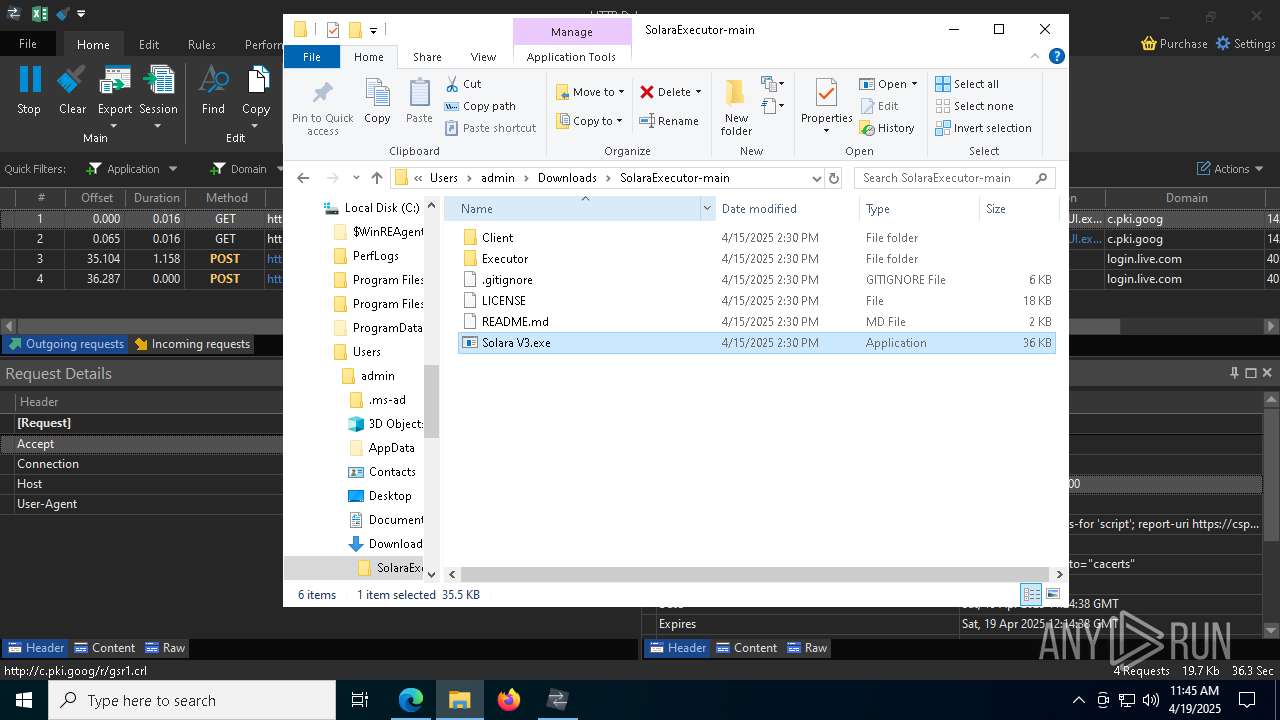
| URL: | https://github.com/swennryh/SolaraExecutor |
| Full analysis: | https://app.any.run/tasks/413270f1-c014-47da-9e6a-5bbb5373d1fa |
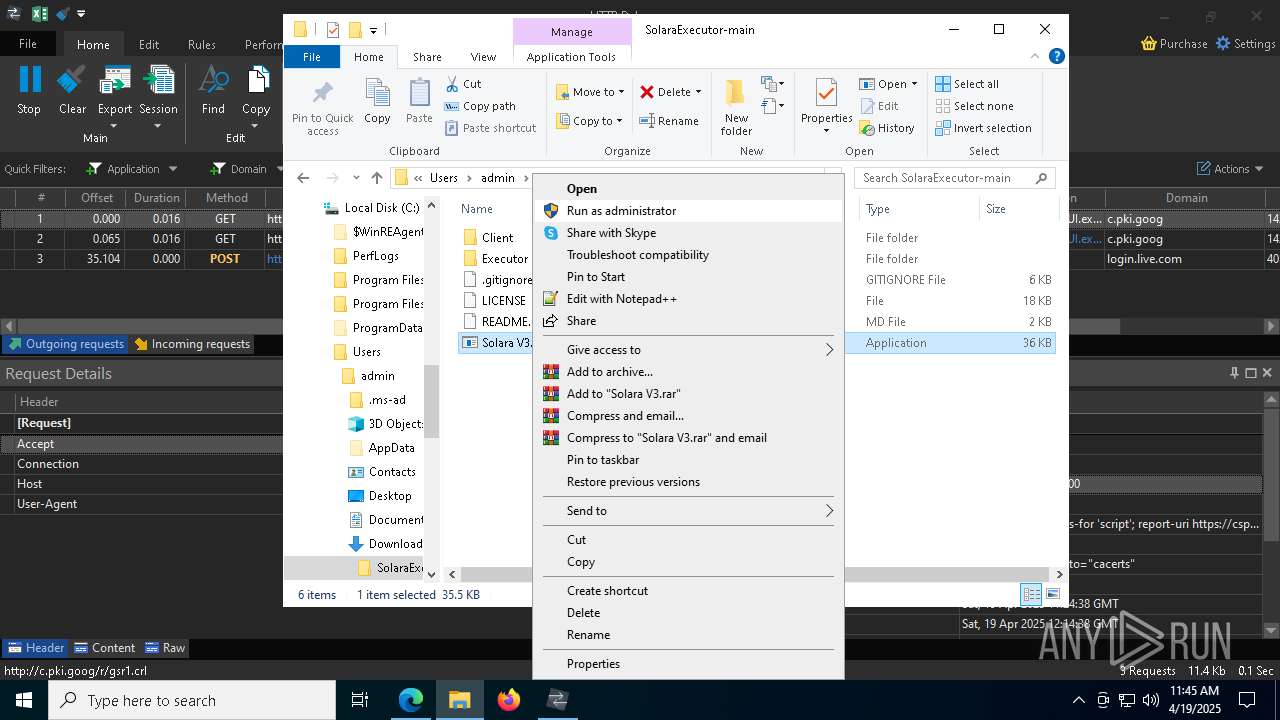
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | April 19, 2025, 11:43:40 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 256C15839A982C578C722337291236CD |
| SHA1: | 945BDCF2B6DACA97E64261B2F084F5289B461C41 |
| SHA256: | 9FD0F226F118772F6AEE341F1DFF3BC6161A2C6A9163201DA31F3FBECB1648CF |
| SSDEEP: | 3:N8tEdmSxK7ZGEKX:2uw37ZGEM |
MALICIOUS
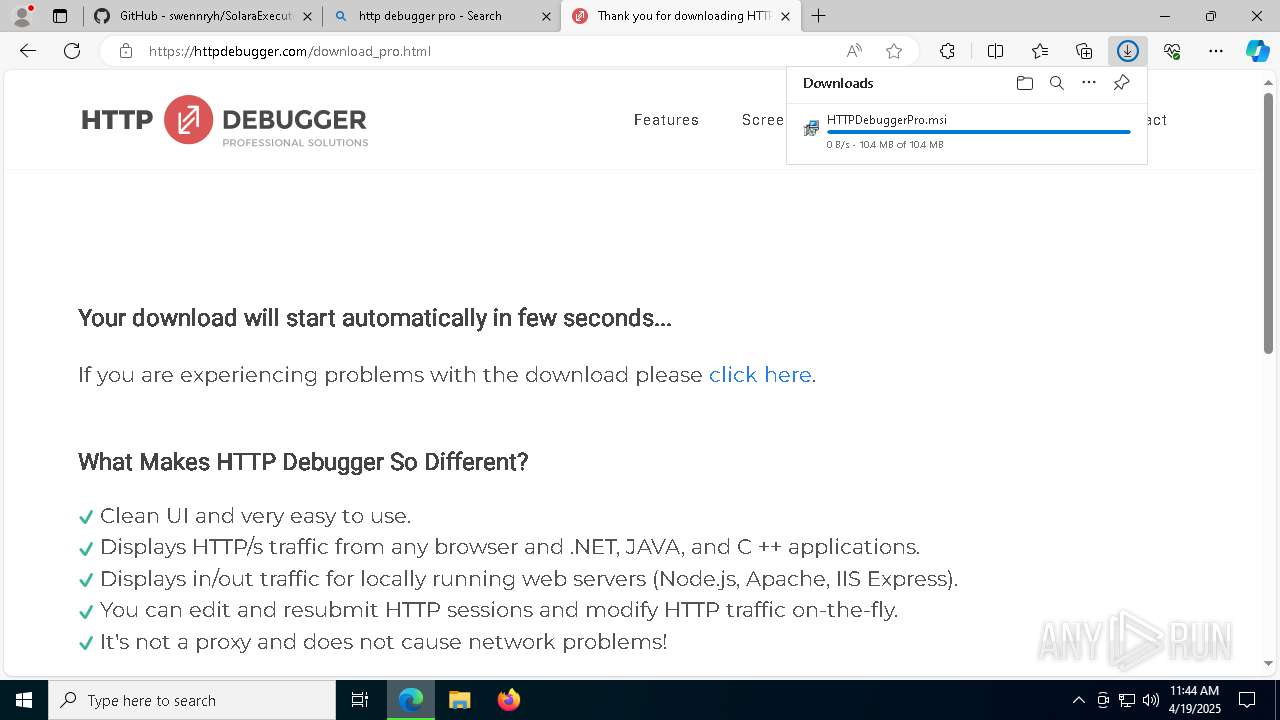
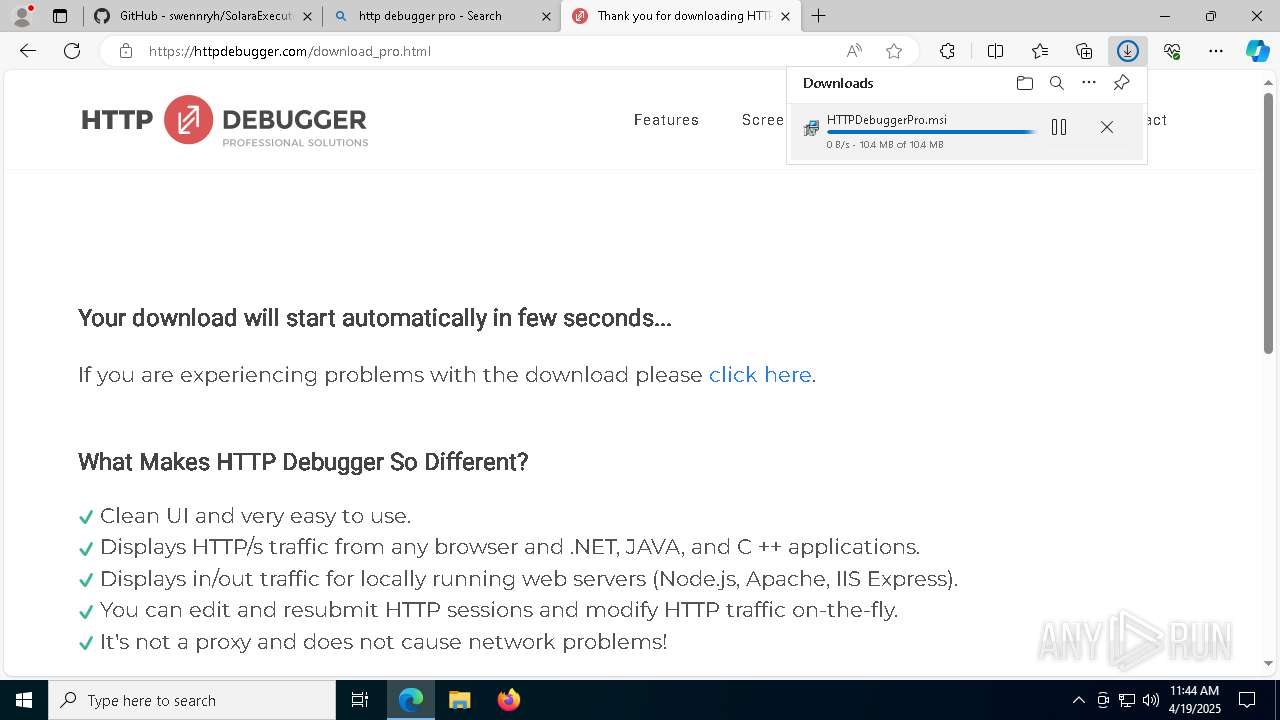
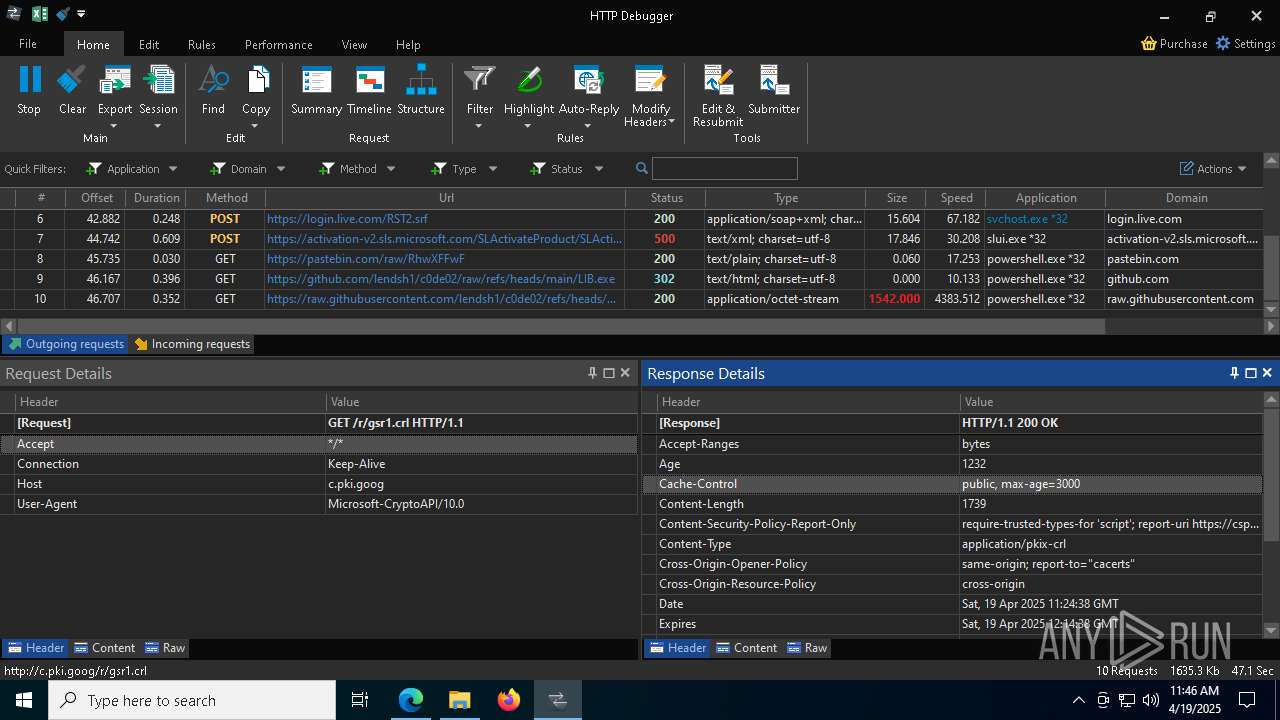
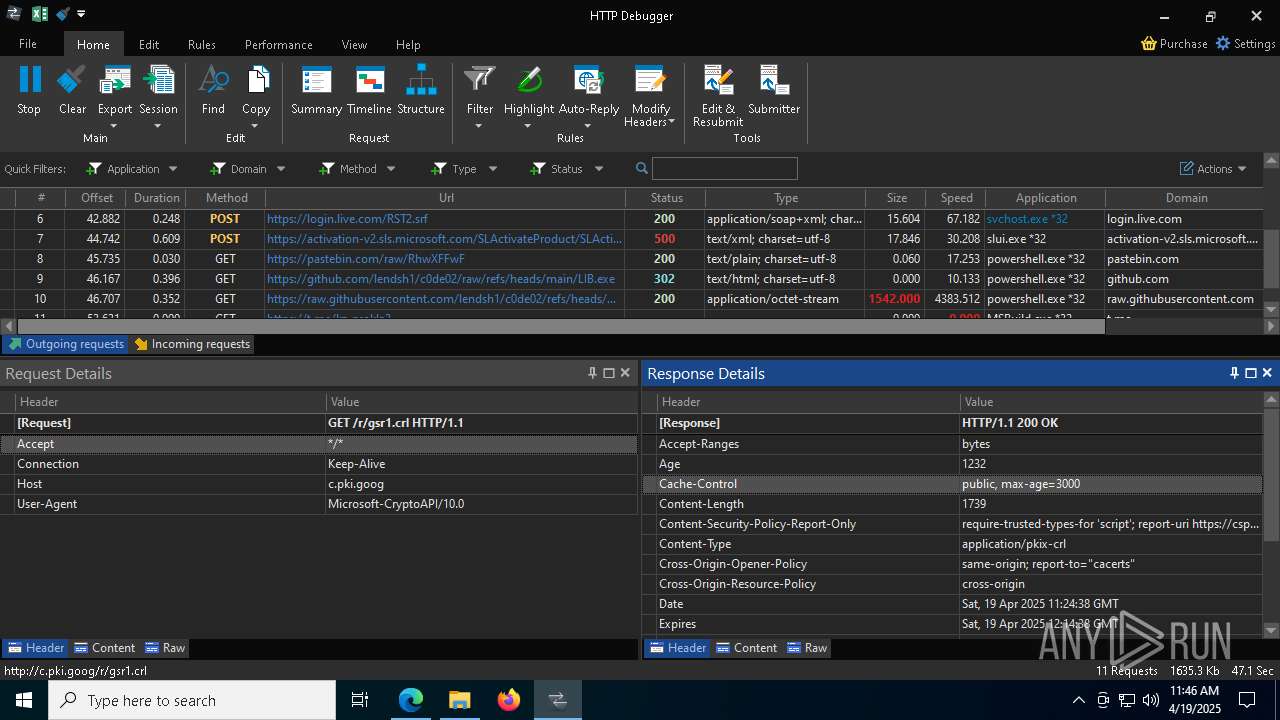
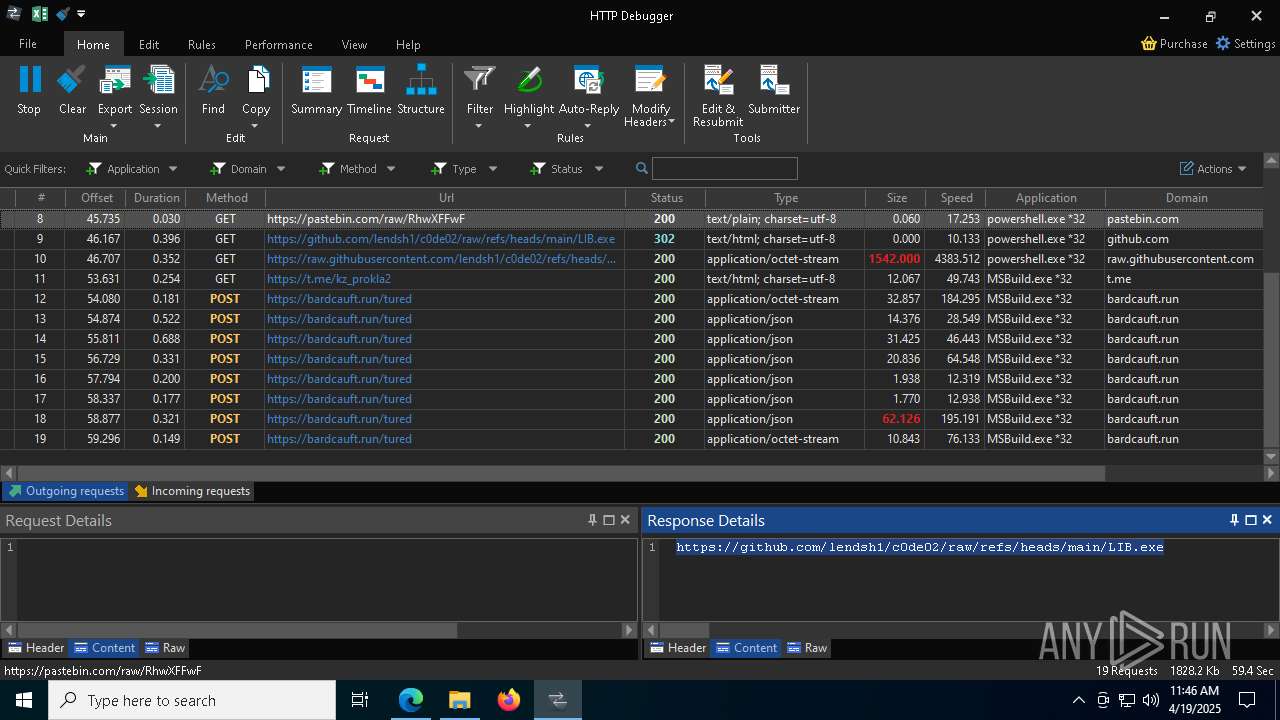
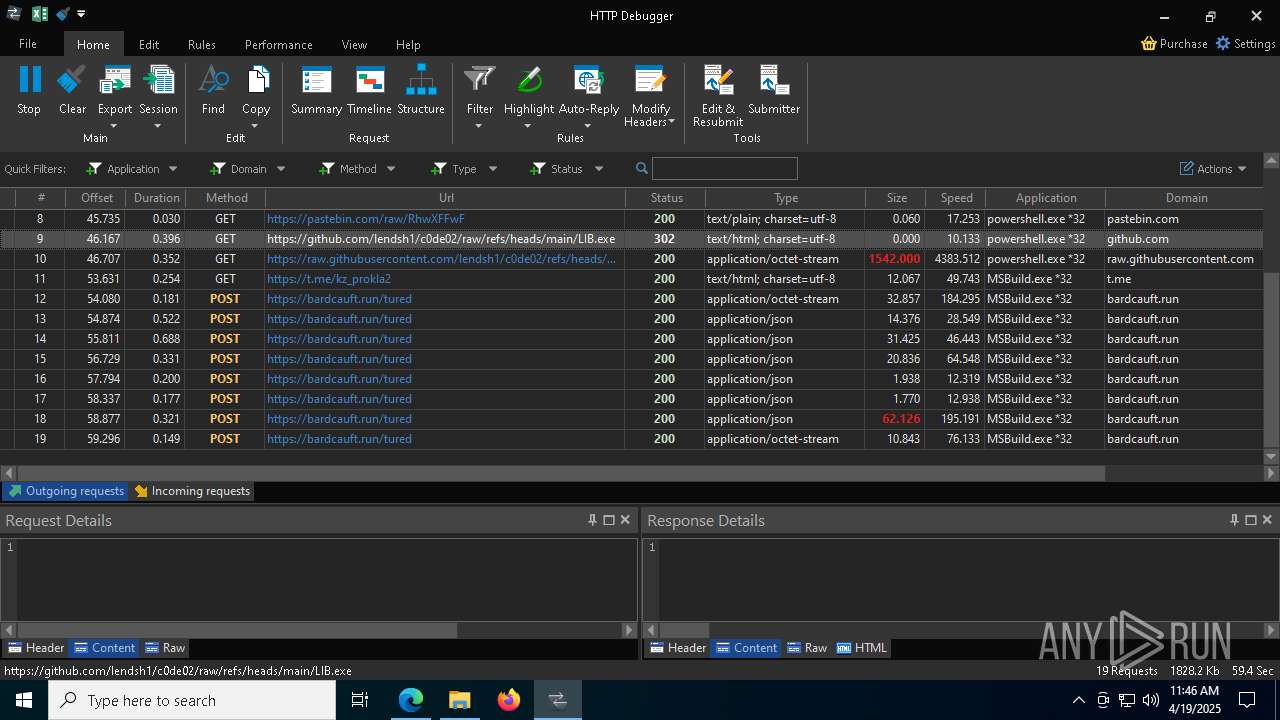
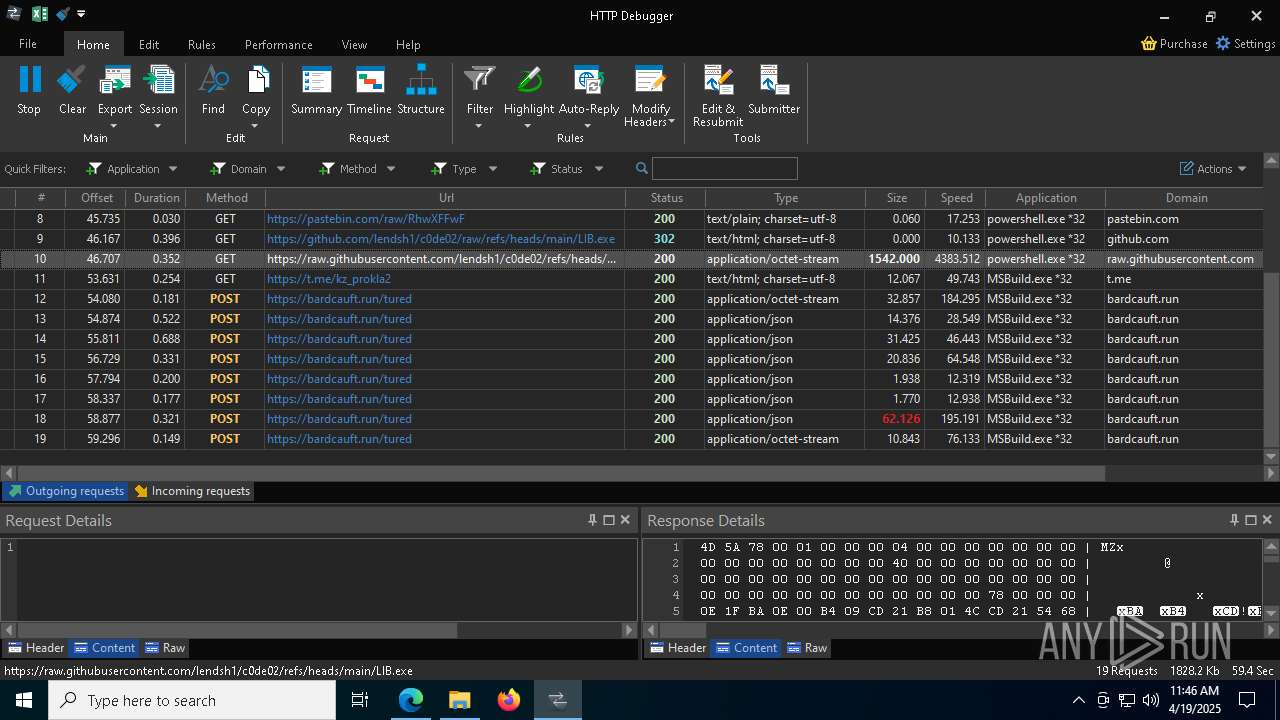
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 9008)
Script downloads file (POWERSHELL)
- powershell.exe (PID: 9008)
LUMMA mutex has been found
- MSBuild.exe (PID: 7676)
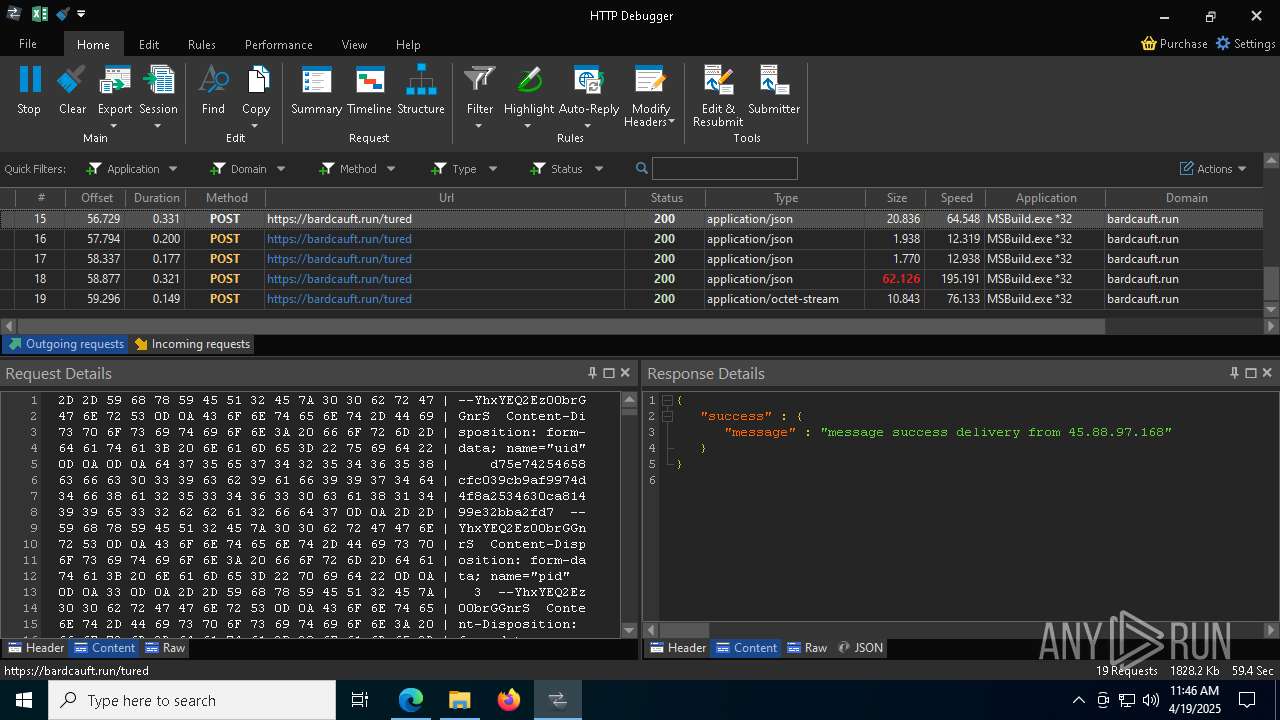
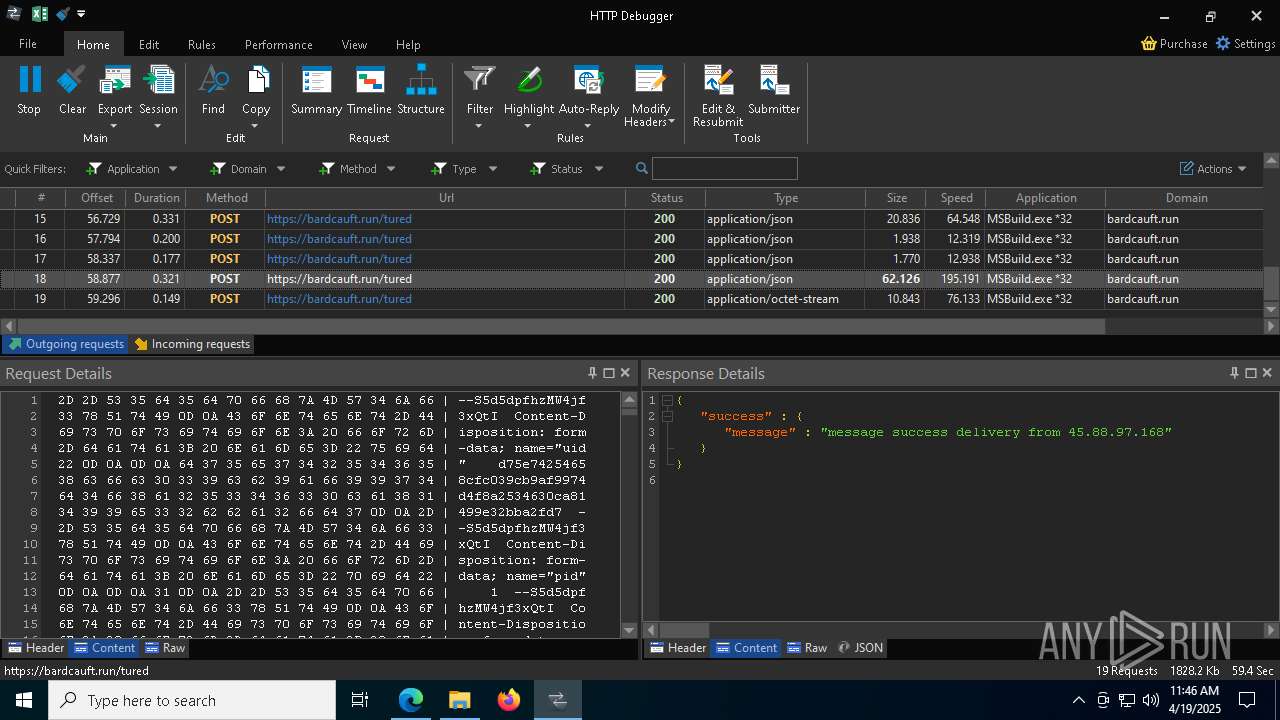
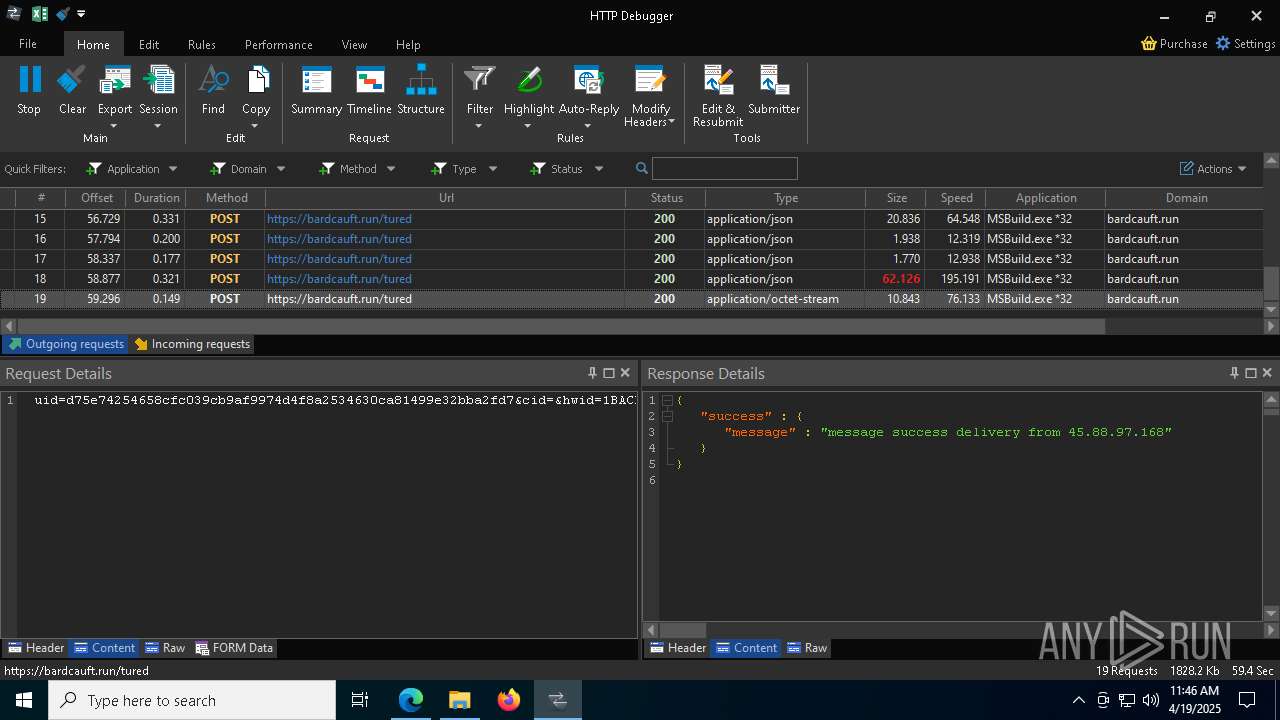
Steals credentials from Web Browsers
- MSBuild.exe (PID: 7676)
Actions looks like stealing of personal data
- MSBuild.exe (PID: 7676)
SUSPICIOUS
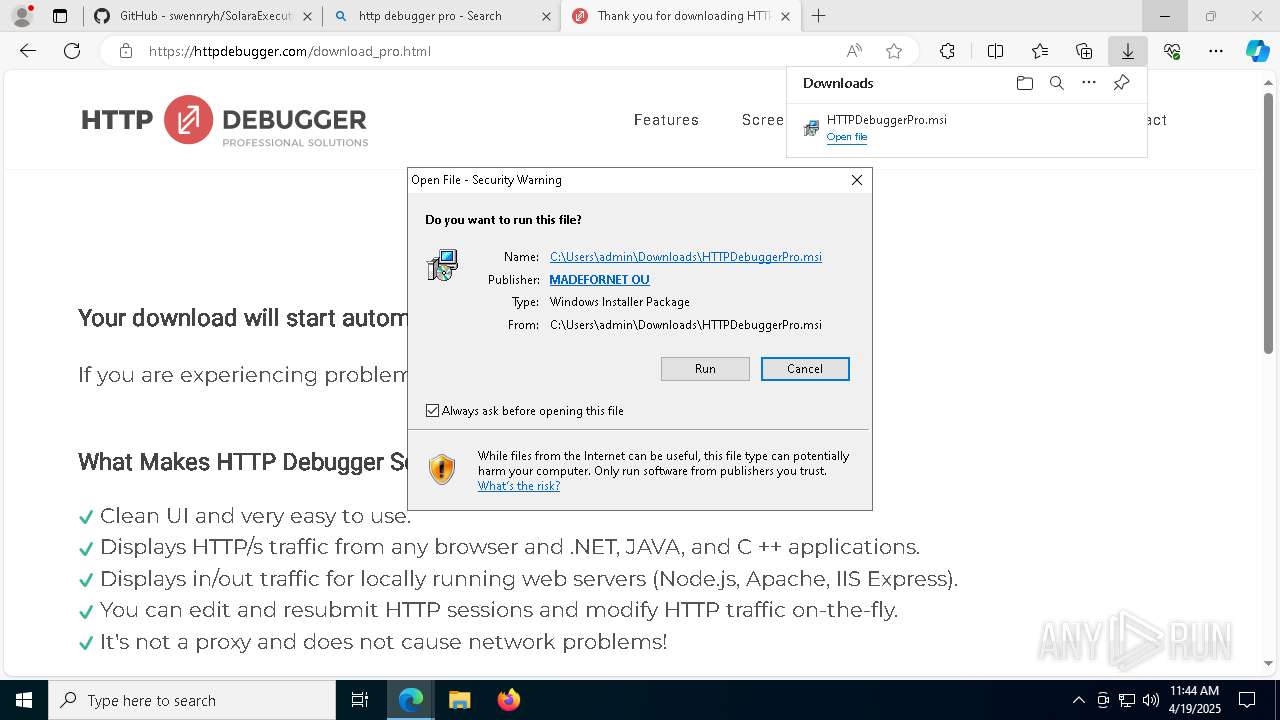
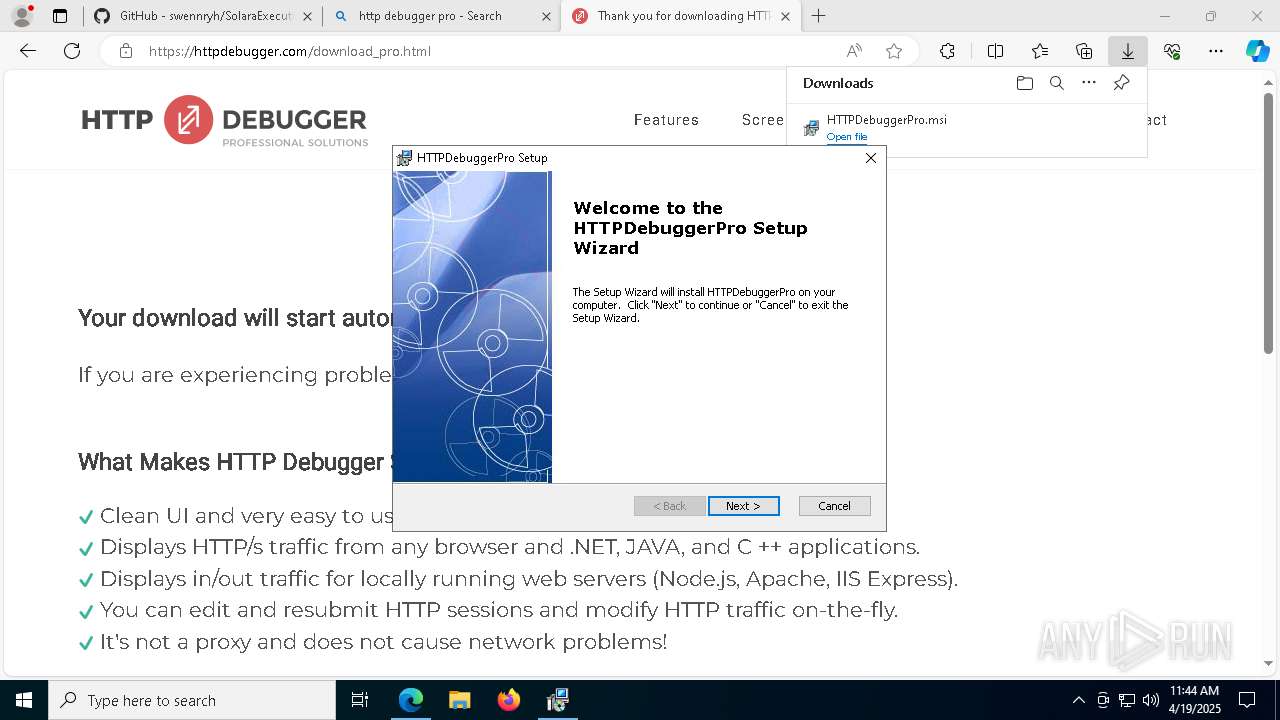
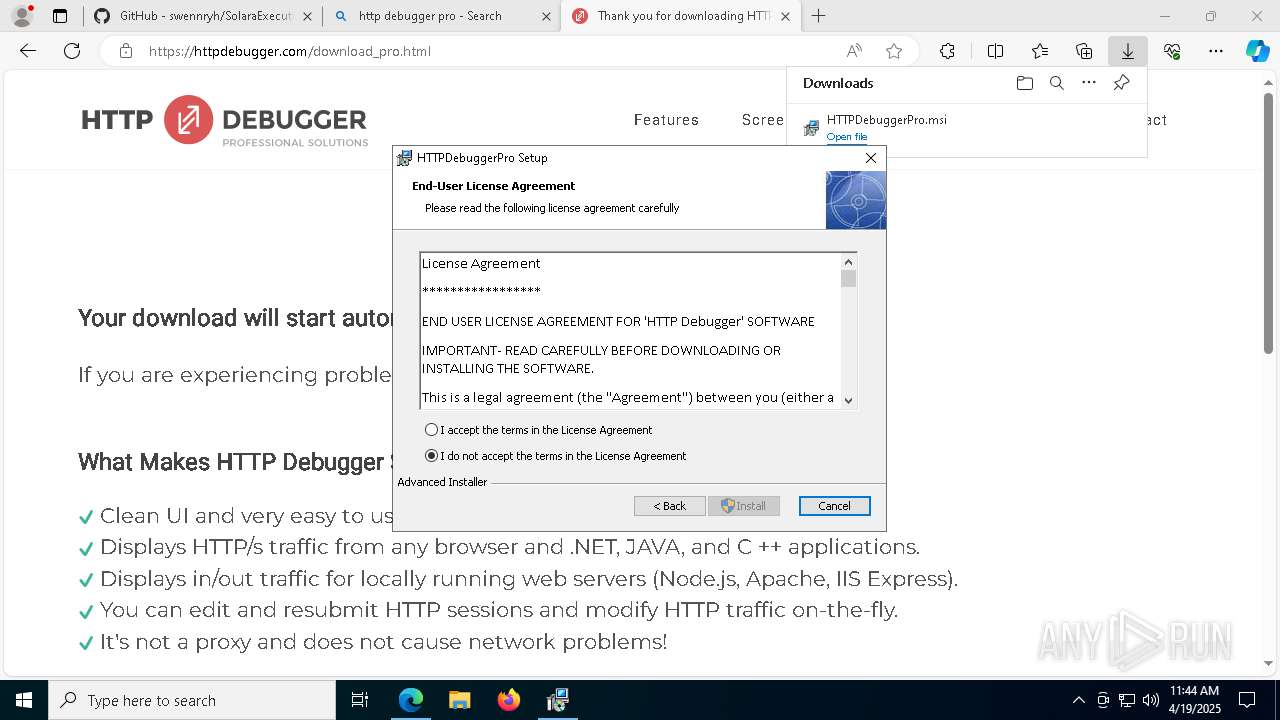
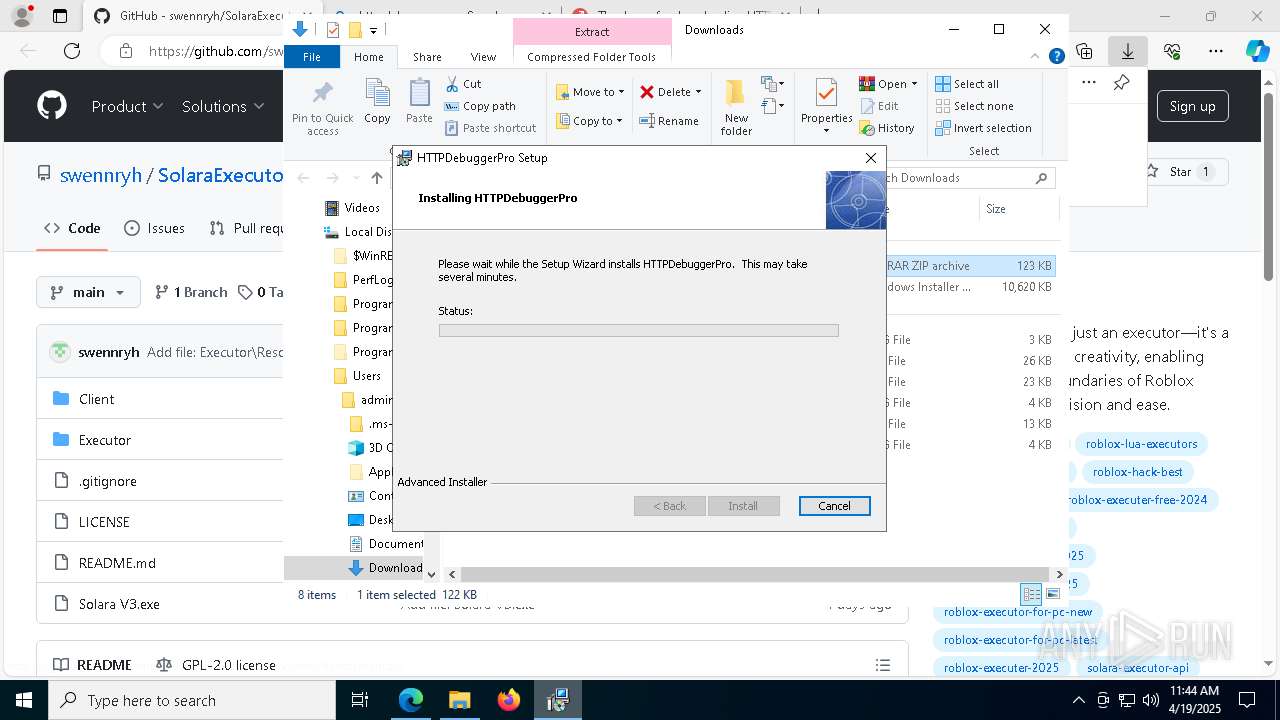
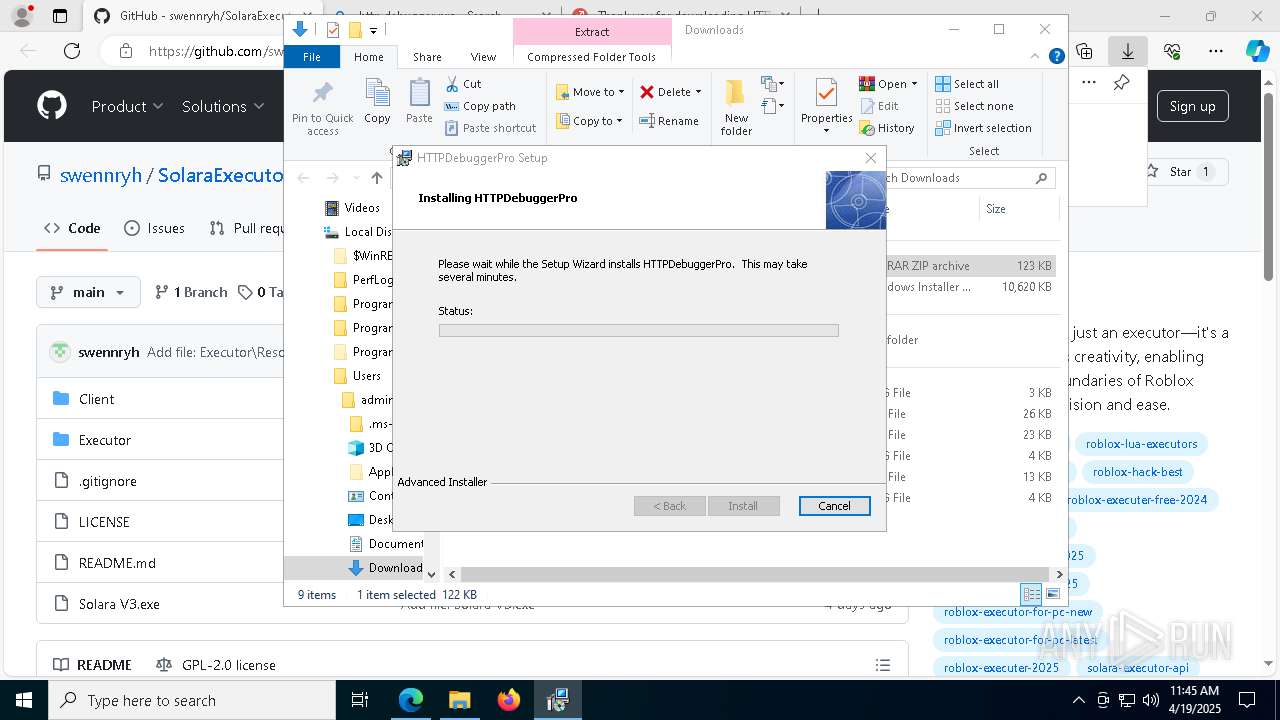
Detects AdvancedInstaller (YARA)
- msiexec.exe (PID: 6148)
- msiexec.exe (PID: 6564)
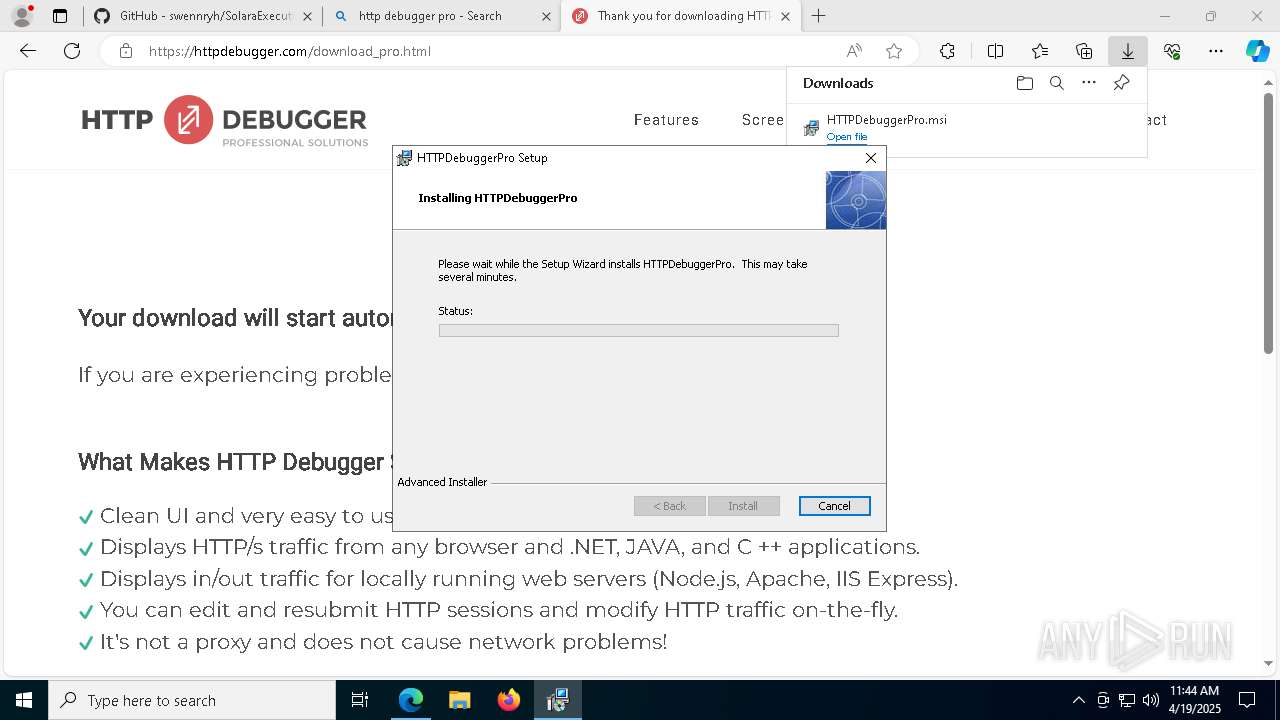
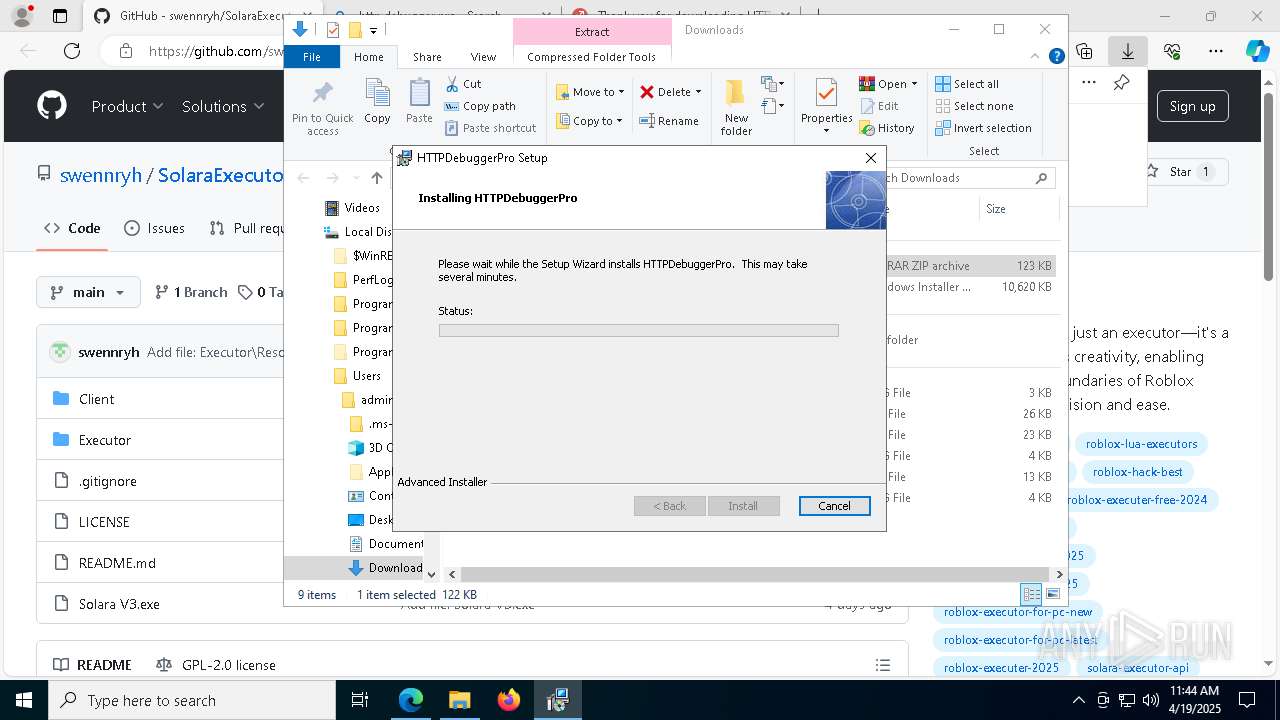
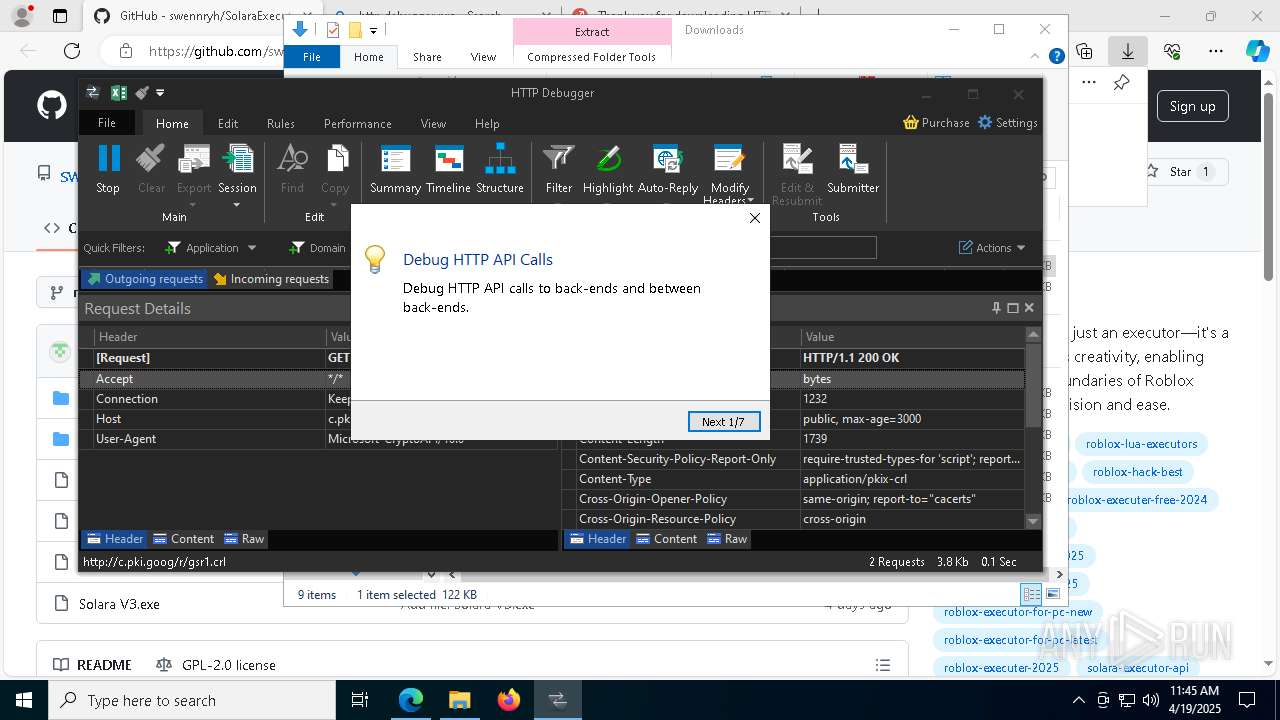
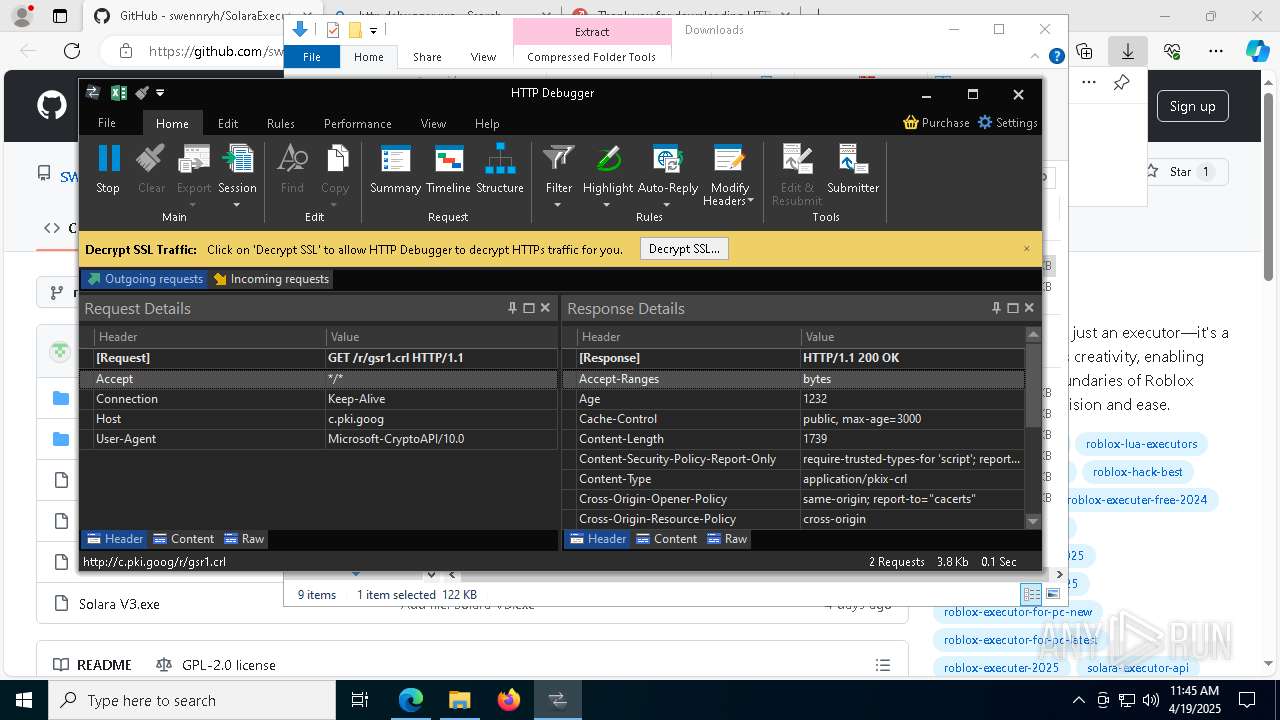
Executes as Windows Service
- VSSVC.exe (PID: 5056)
- HTTPDebuggerSvc.exe (PID: 9064)
Drops a system driver (possible attempt to evade defenses)
- msiexec.exe (PID: 6148)
- HTTPDebuggerSvc.exe (PID: 9064)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 6148)
Creates/Modifies COM task schedule object
- msiexec.exe (PID: 9040)
Creates files in the driver directory
- HTTPDebuggerSvc.exe (PID: 9064)
Executable content was dropped or overwritten
- HTTPDebuggerSvc.exe (PID: 9064)
- powershell.exe (PID: 9008)
The process creates files with name similar to system file names
- msiexec.exe (PID: 6148)
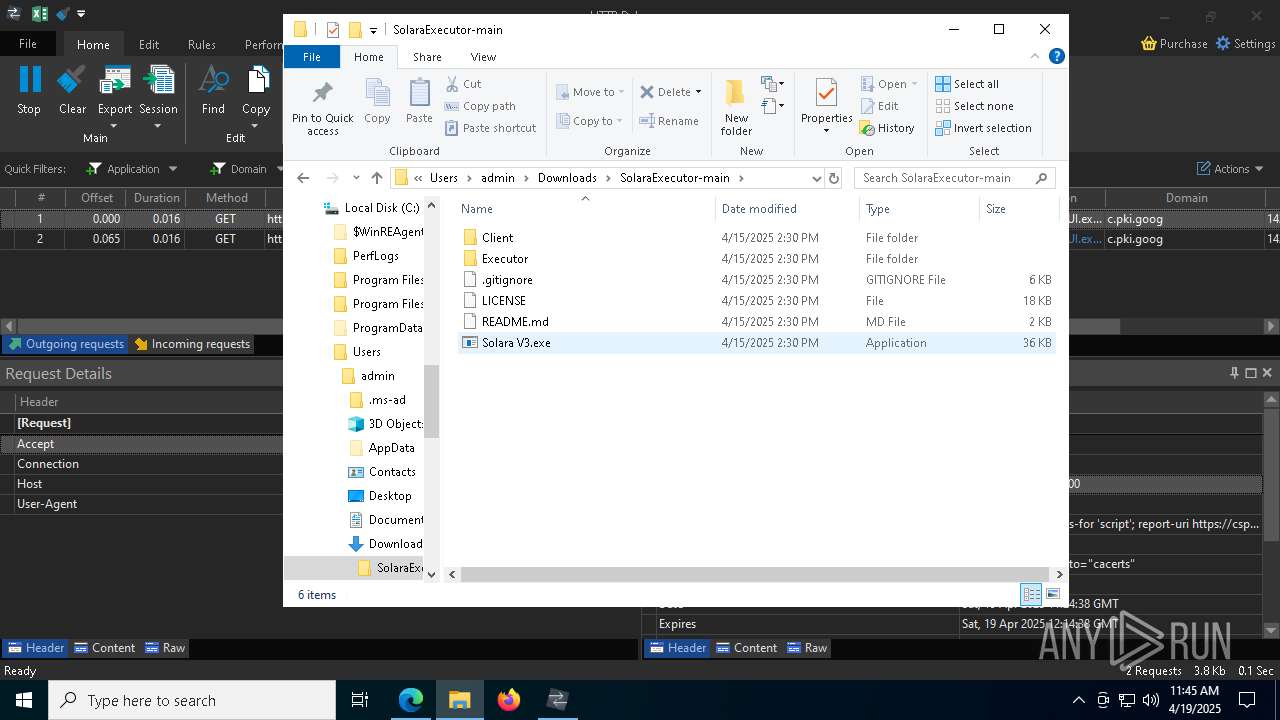
Reads security settings of Internet Explorer
- msiexec.exe (PID: 3364)
- HTTPDebuggerUI.exe (PID: 9204)
- Solara V3.exe (PID: 8720)
Reads Microsoft Outlook installation path
- HTTPDebuggerUI.exe (PID: 9204)
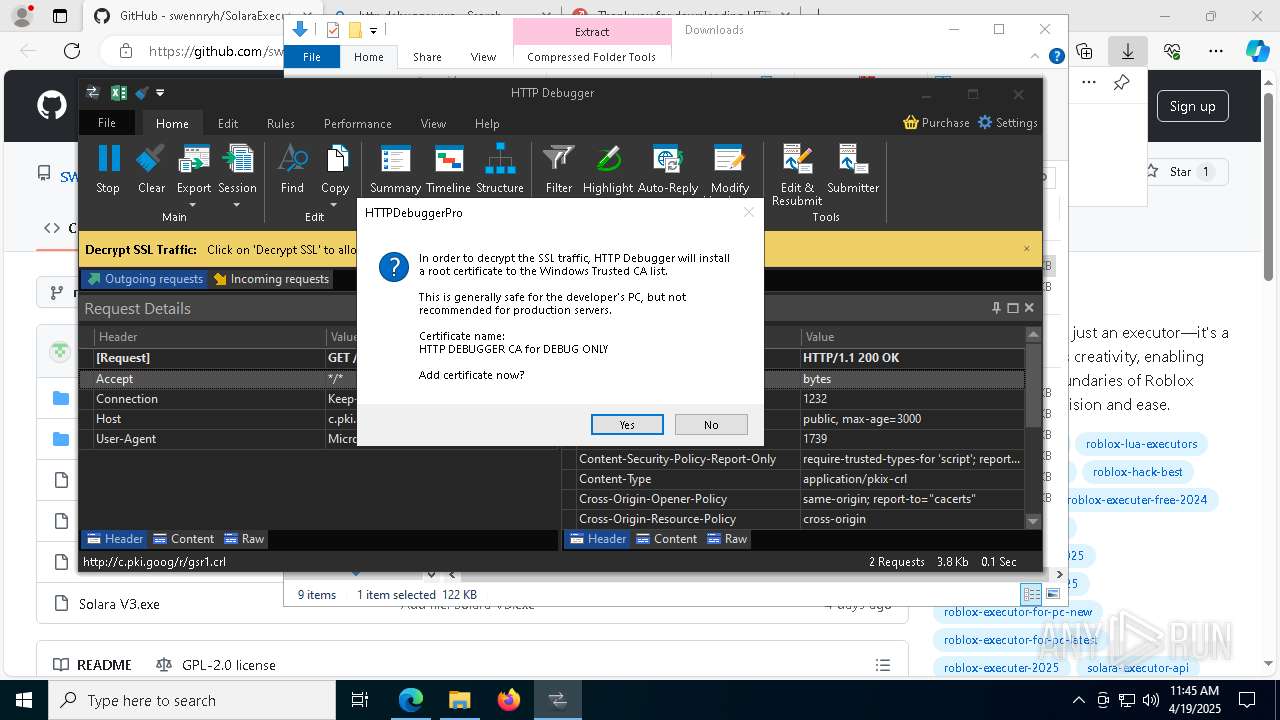
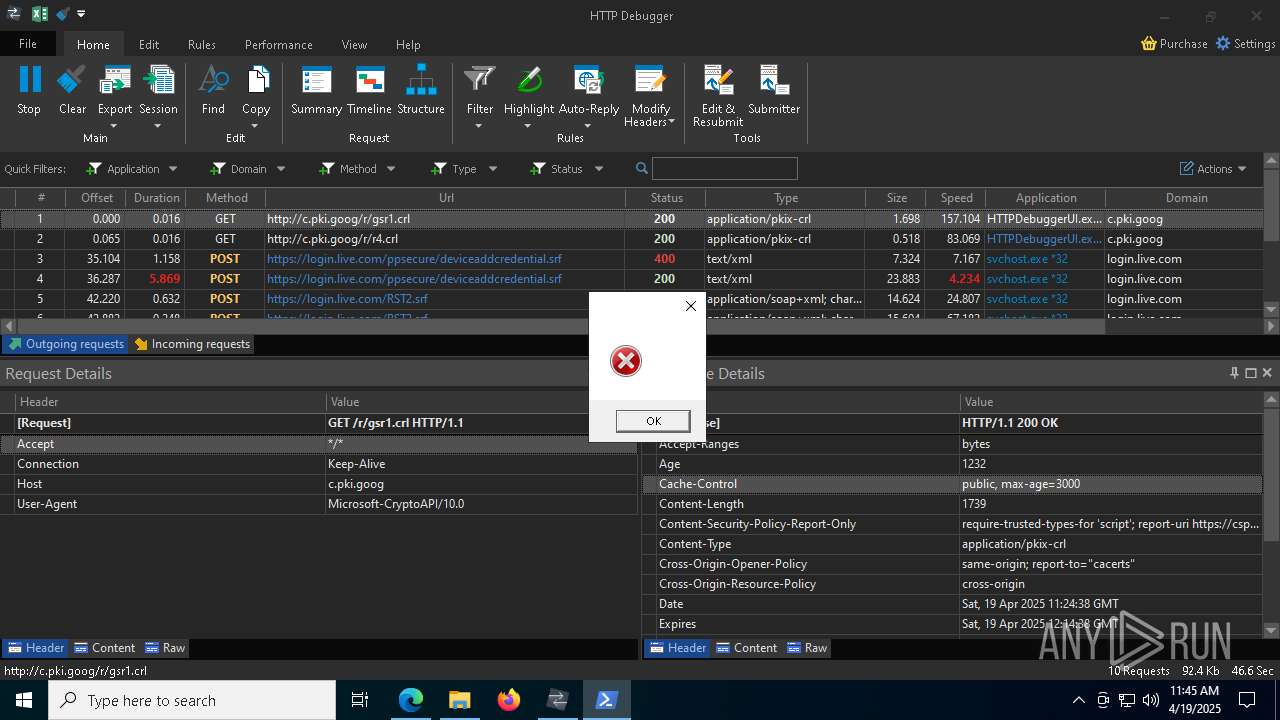
Adds/modifies Windows certificates
- HTTPDebuggerSvc.exe (PID: 9064)
Reads Internet Explorer settings
- HTTPDebuggerUI.exe (PID: 9204)
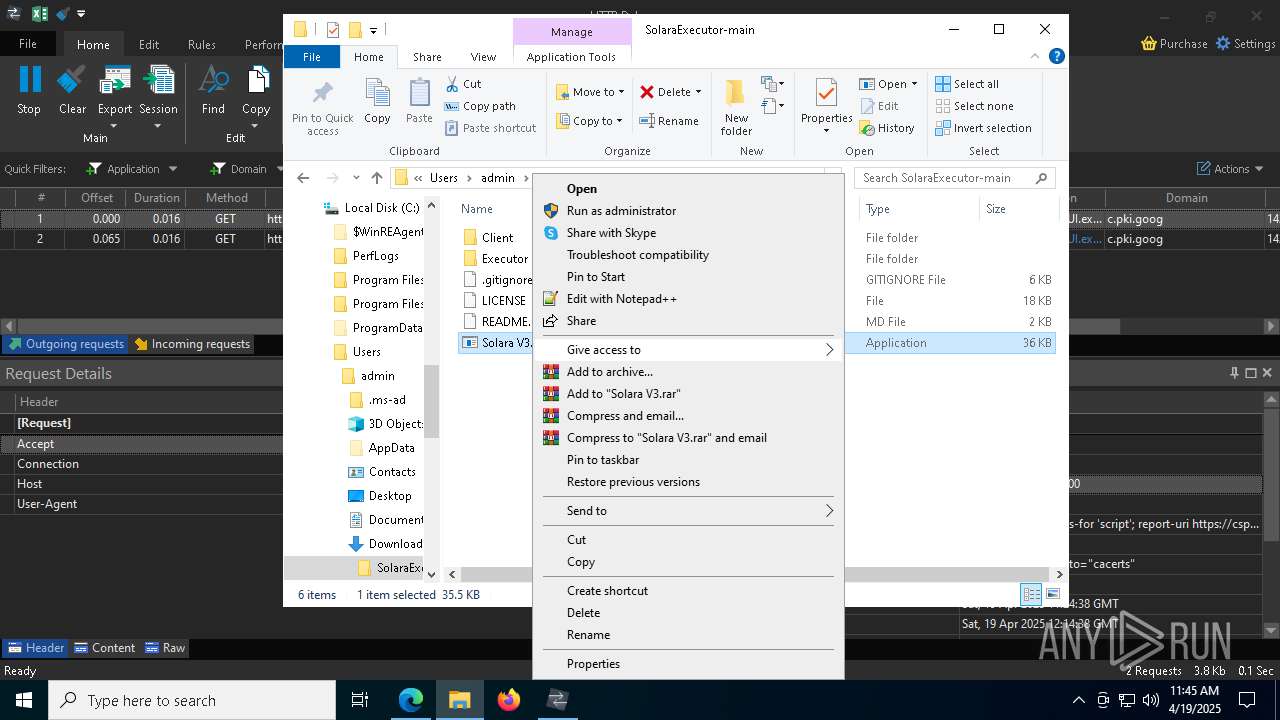
Base64-obfuscated command line is found
- Solara V3.exe (PID: 8720)
Application launched itself
- powershell.exe (PID: 9008)
BASE64 encoded PowerShell command has been detected
- Solara V3.exe (PID: 8720)
Starts POWERSHELL.EXE for commands execution
- Solara V3.exe (PID: 8720)
- powershell.exe (PID: 9008)
Process drops legitimate windows executable
- powershell.exe (PID: 9008)
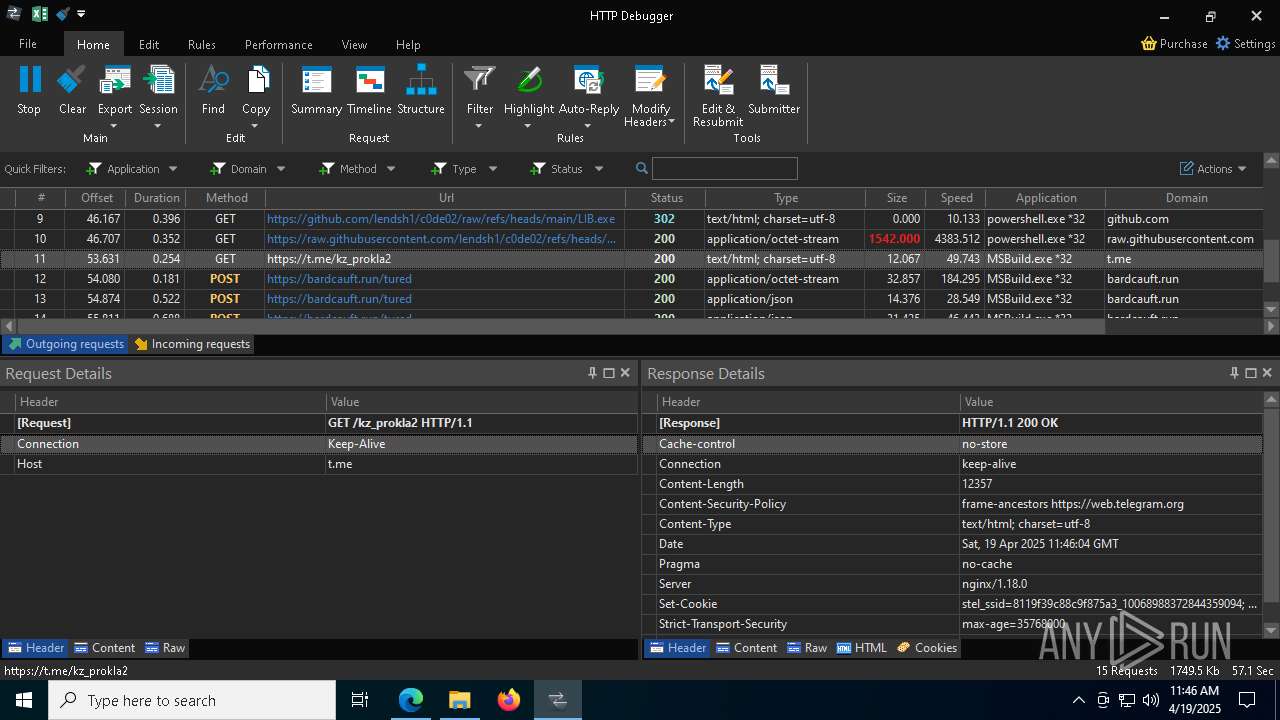
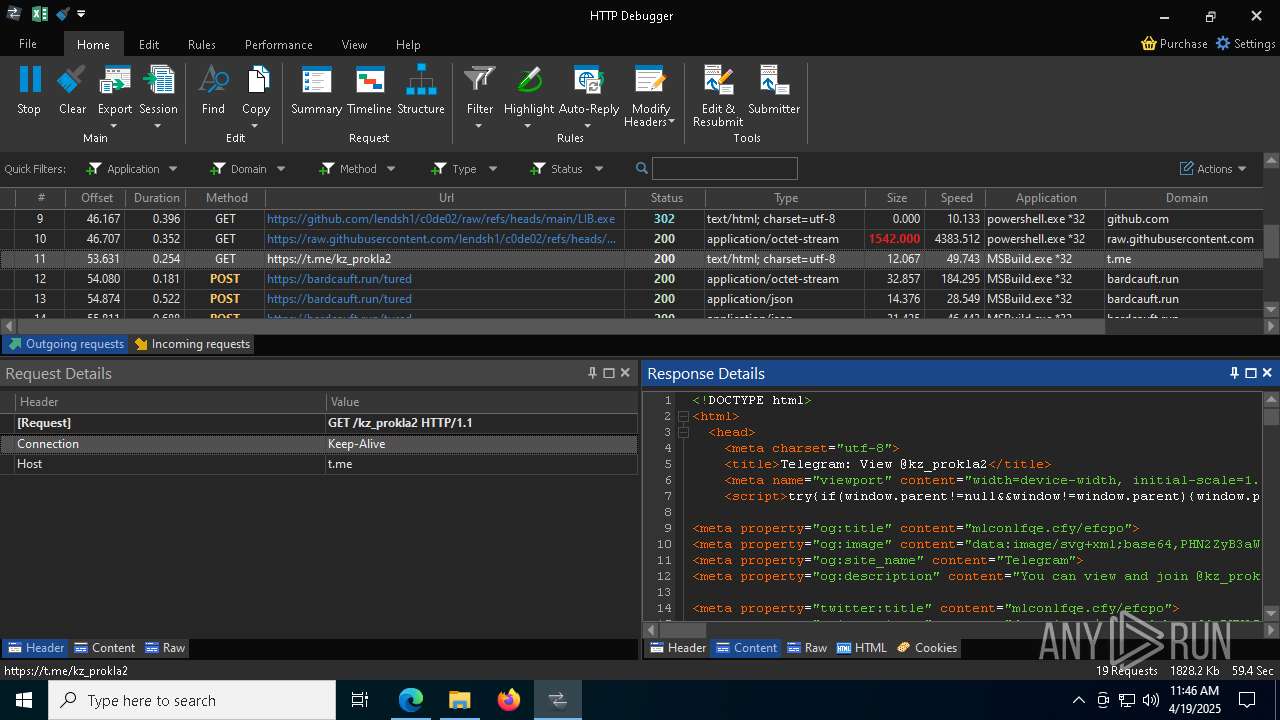
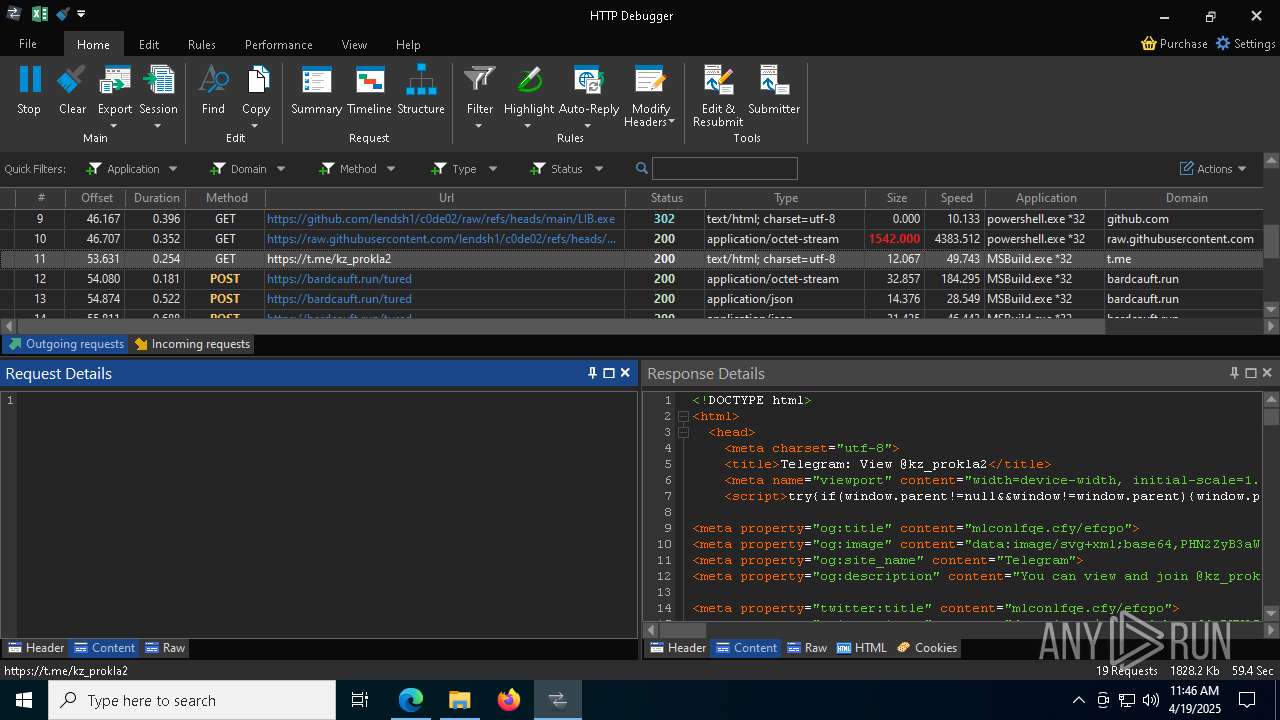
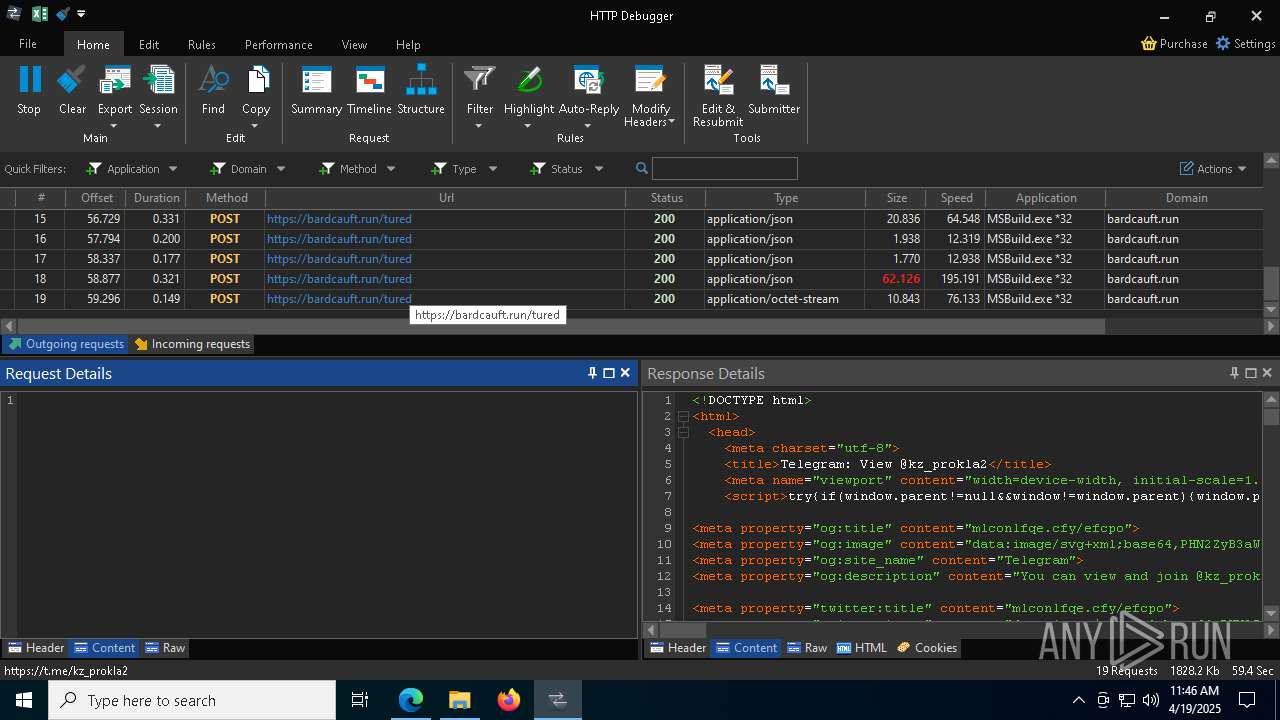
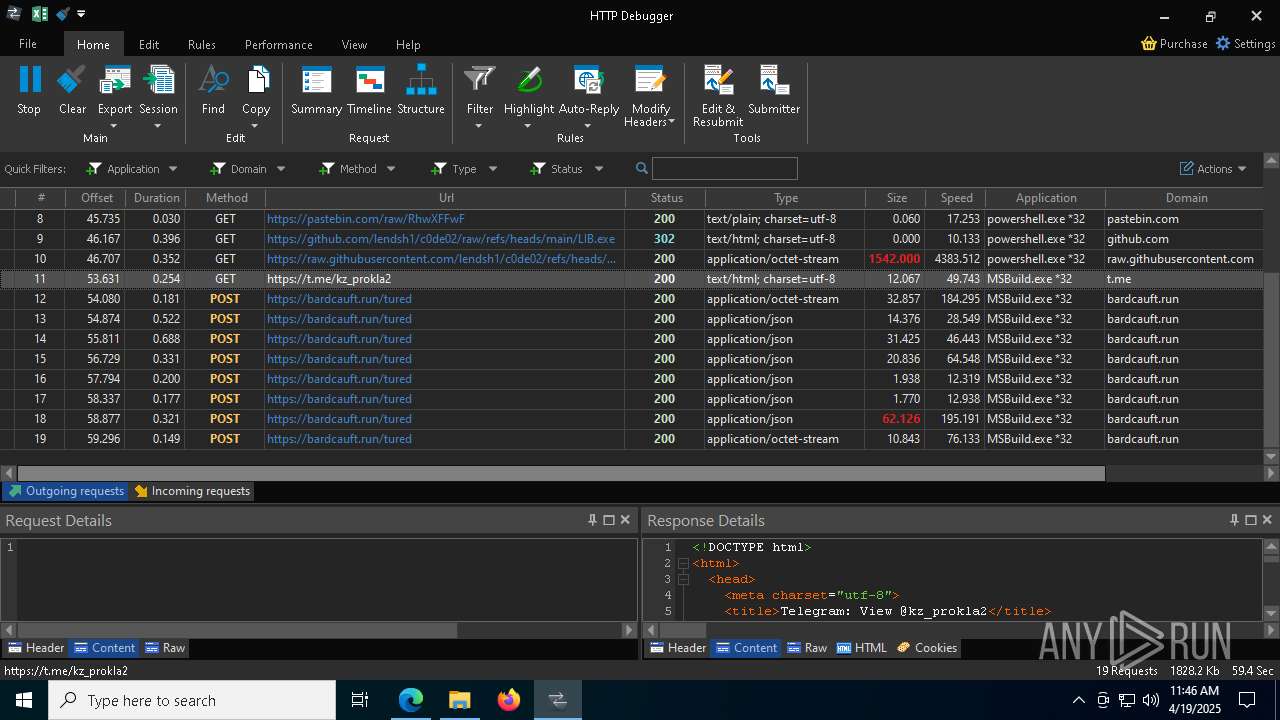
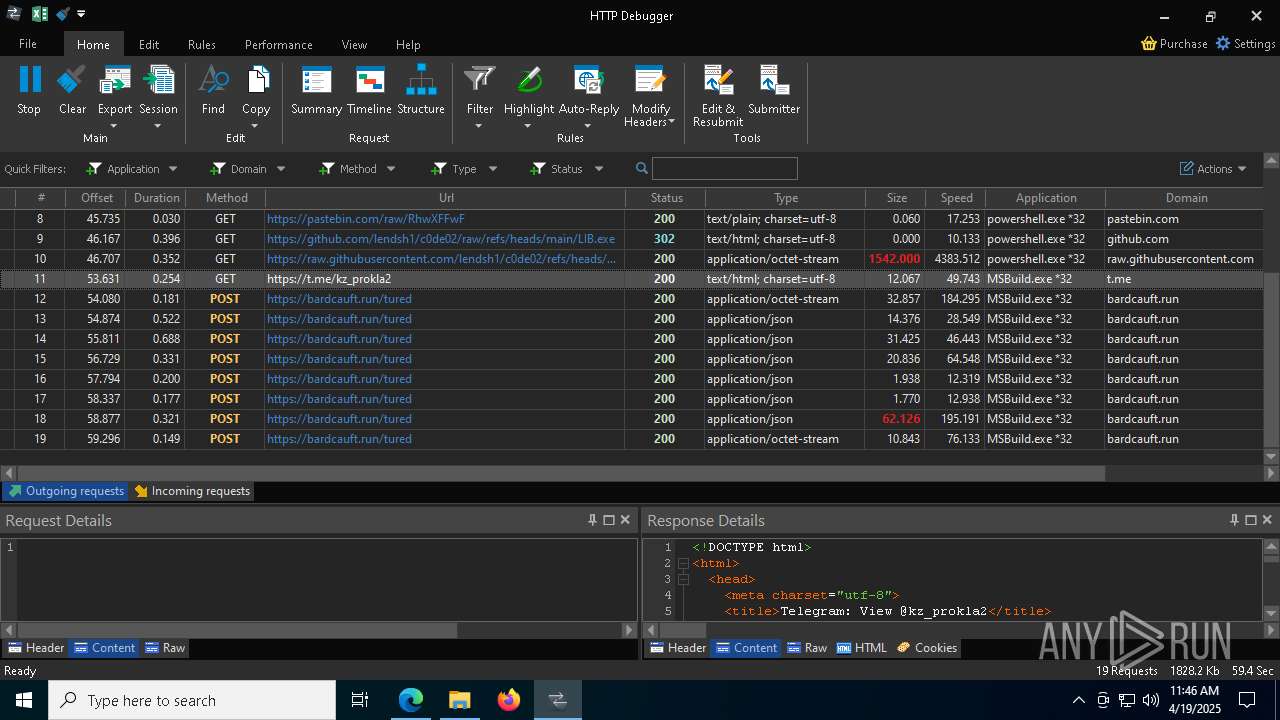
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- MSBuild.exe (PID: 7676)
Searches for installed software
- MSBuild.exe (PID: 7676)
INFO
Reads Environment values
- identity_helper.exe (PID: 4880)
- Solara V3.exe (PID: 8720)
Application launched itself
- msedge.exe (PID: 4724)
Reads the computer name
- identity_helper.exe (PID: 4880)
- msiexec.exe (PID: 6148)
- msiexec.exe (PID: 3364)
- msiexec.exe (PID: 8992)
- HTTPDebuggerSvc.exe (PID: 9064)
- HTTPDebuggerUI.exe (PID: 9204)
- certutil.exe (PID: 8760)
- Solara V3.exe (PID: 8720)
- MSBuild.exe (PID: 7676)
- HTTPDebuggerSvc.exe (PID: 9128)
Reads the software policy settings
- msiexec.exe (PID: 6564)
- slui.exe (PID: 7976)
- msiexec.exe (PID: 6148)
- HTTPDebuggerUI.exe (PID: 9204)
- powershell.exe (PID: 9192)
- slui.exe (PID: 8544)
- MSBuild.exe (PID: 7676)
Checks supported languages
- identity_helper.exe (PID: 4880)
- msiexec.exe (PID: 3364)
- msiexec.exe (PID: 6148)
- HTTPDebuggerSvc.exe (PID: 9064)
- msiexec.exe (PID: 8992)
- HTTPDebuggerSvc.exe (PID: 9128)
- HTTPDebuggerUI.exe (PID: 9204)
- certutil.exe (PID: 8760)
- Solara V3.exe (PID: 8720)
- iqrhpael.bhu0.exe (PID: 8620)
- MSBuild.exe (PID: 7676)
Reads Microsoft Office registry keys
- msedge.exe (PID: 4724)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 6564)
- powershell.exe (PID: 9192)
Executable content was dropped or overwritten
- msiexec.exe (PID: 6564)
- WinRAR.exe (PID: 8748)
- msiexec.exe (PID: 6148)
- msedge.exe (PID: 9172)
The sample compiled with english language support
- msiexec.exe (PID: 6564)
- msiexec.exe (PID: 6148)
- HTTPDebuggerSvc.exe (PID: 9064)
- powershell.exe (PID: 9008)
- msedge.exe (PID: 9172)
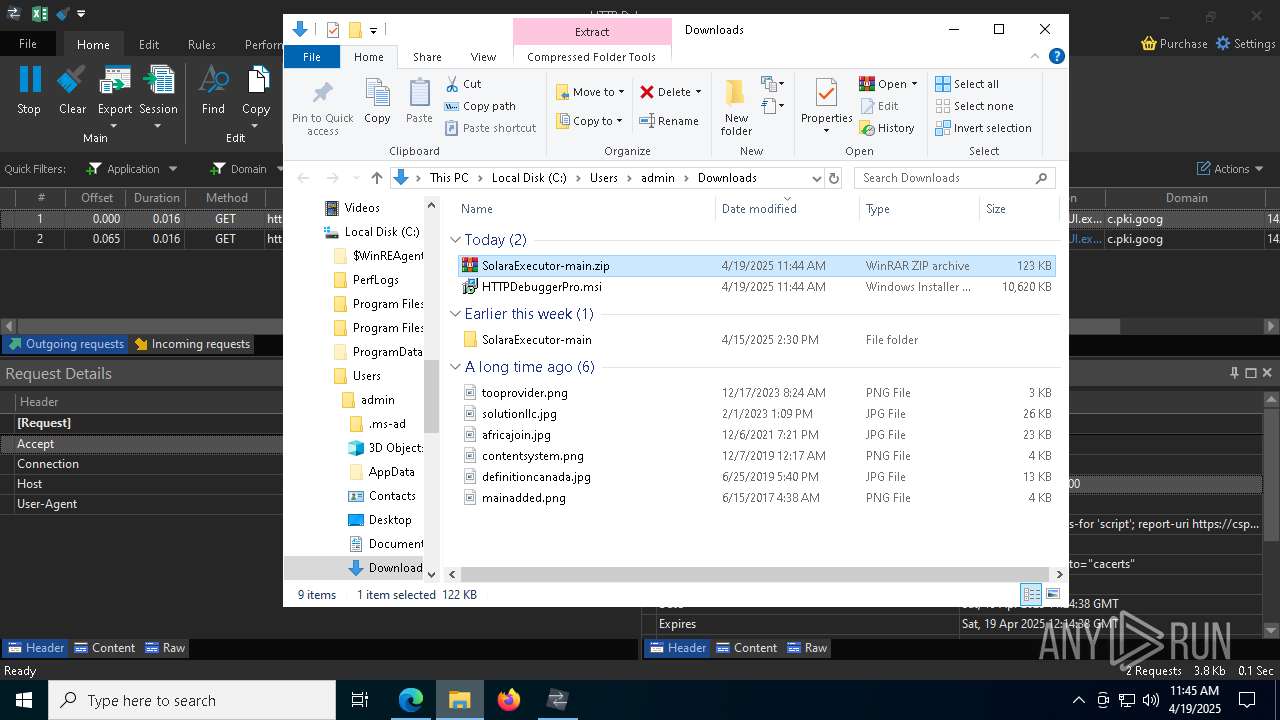
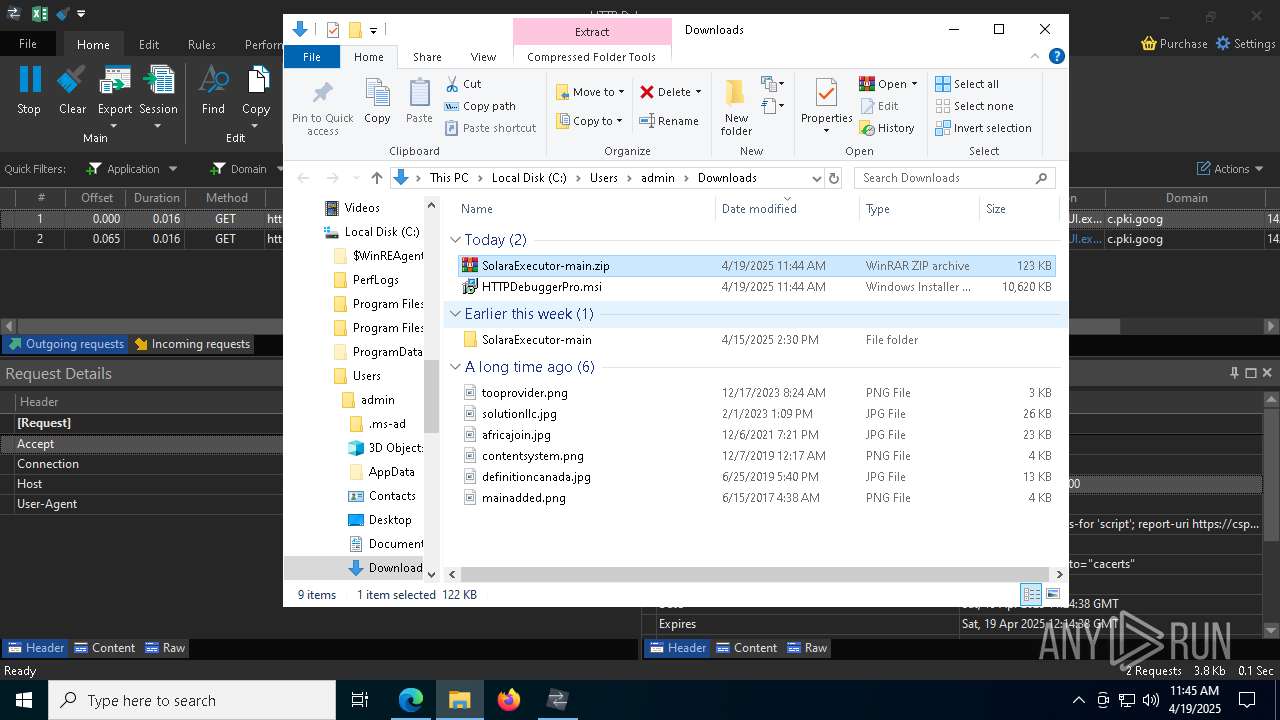
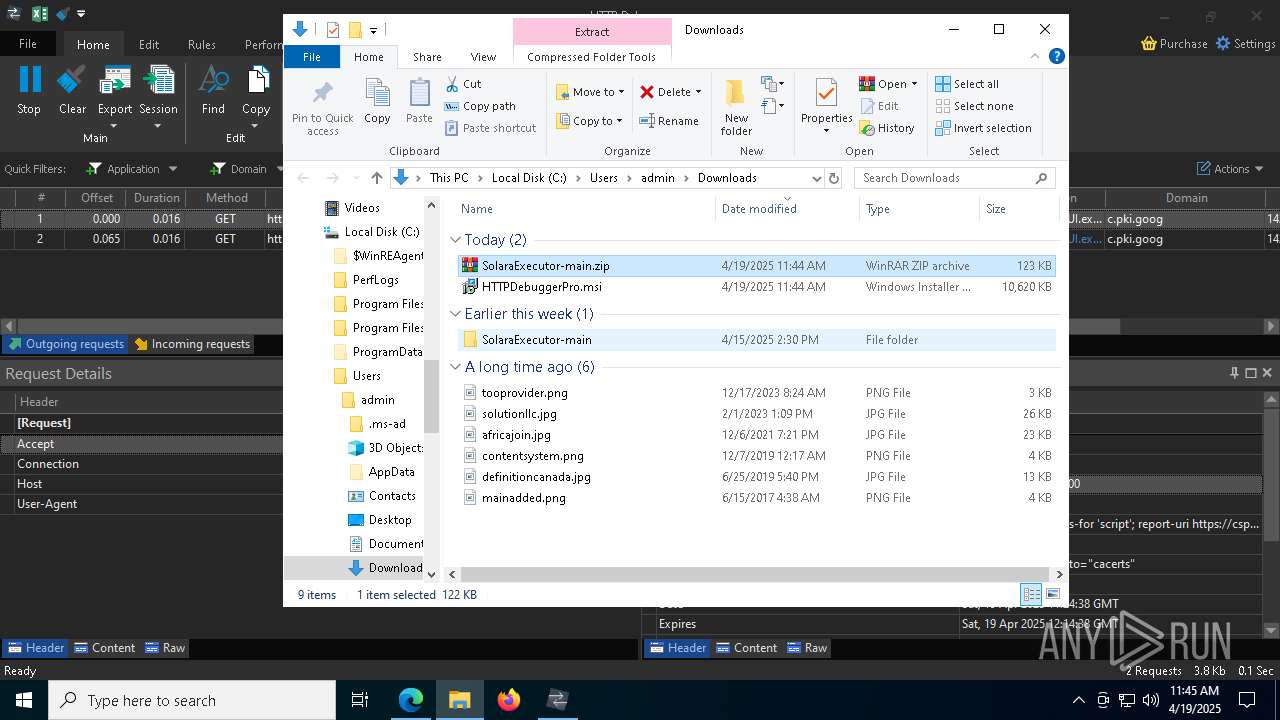
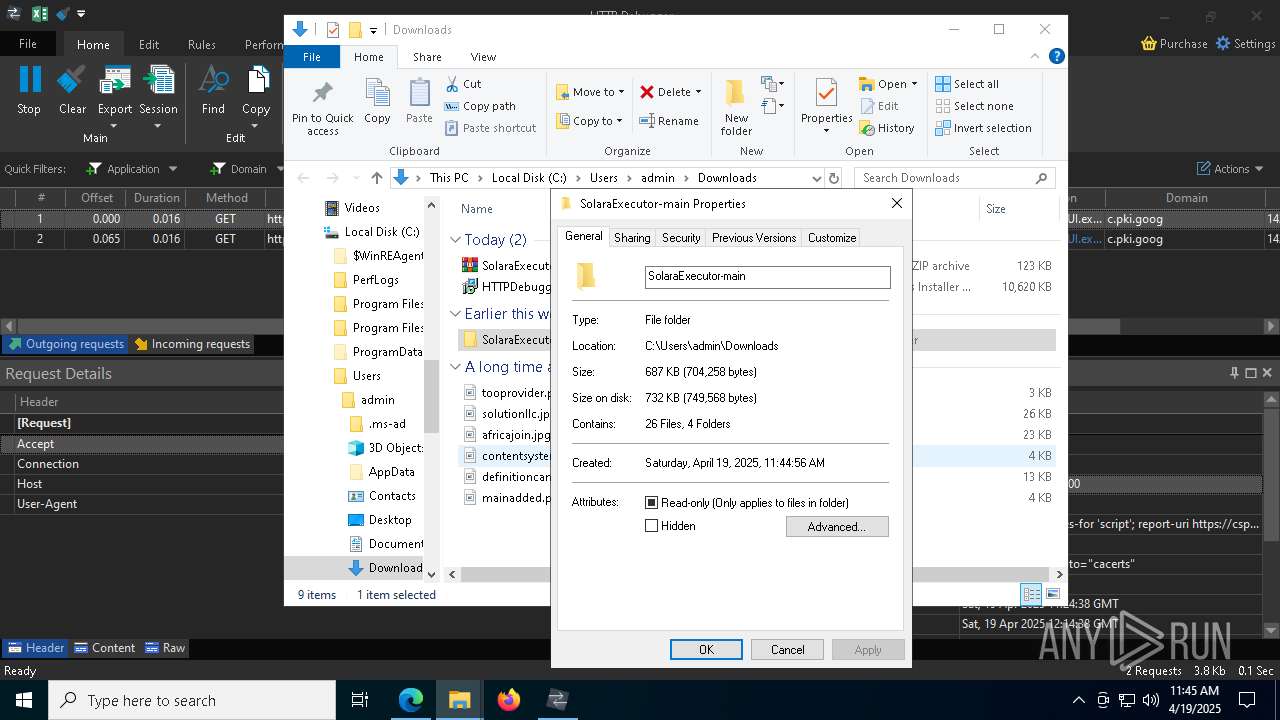
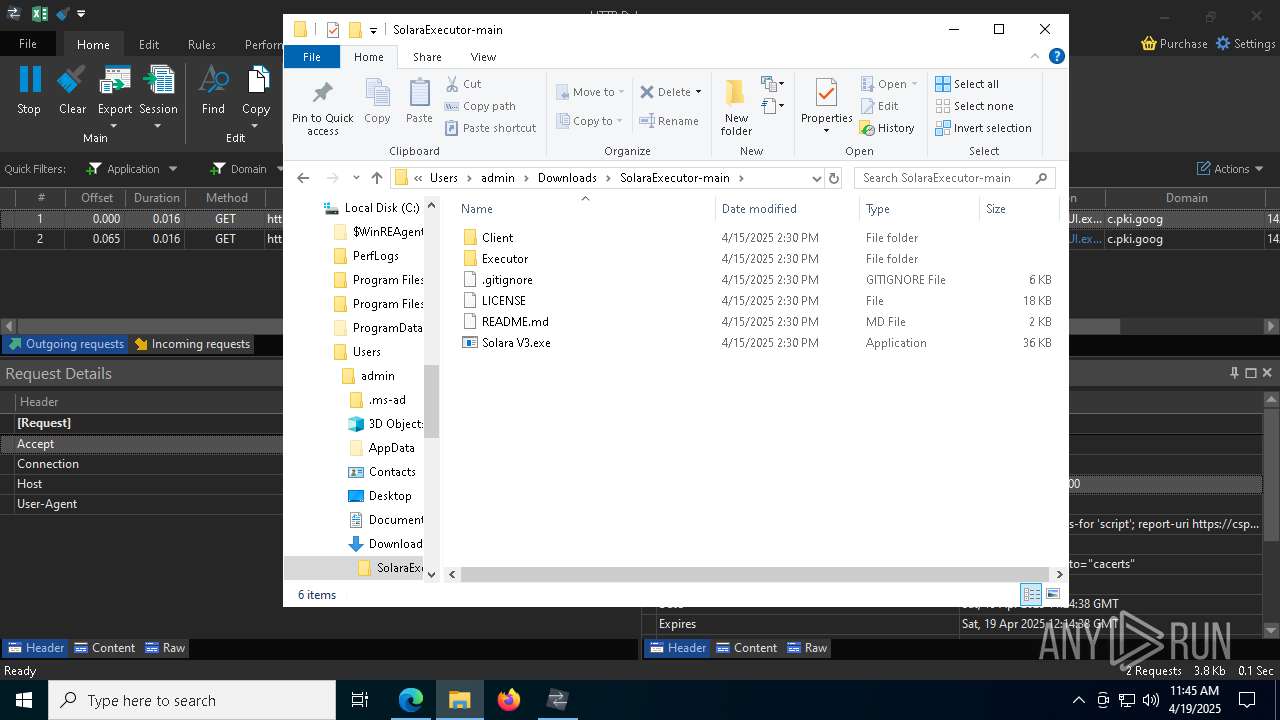
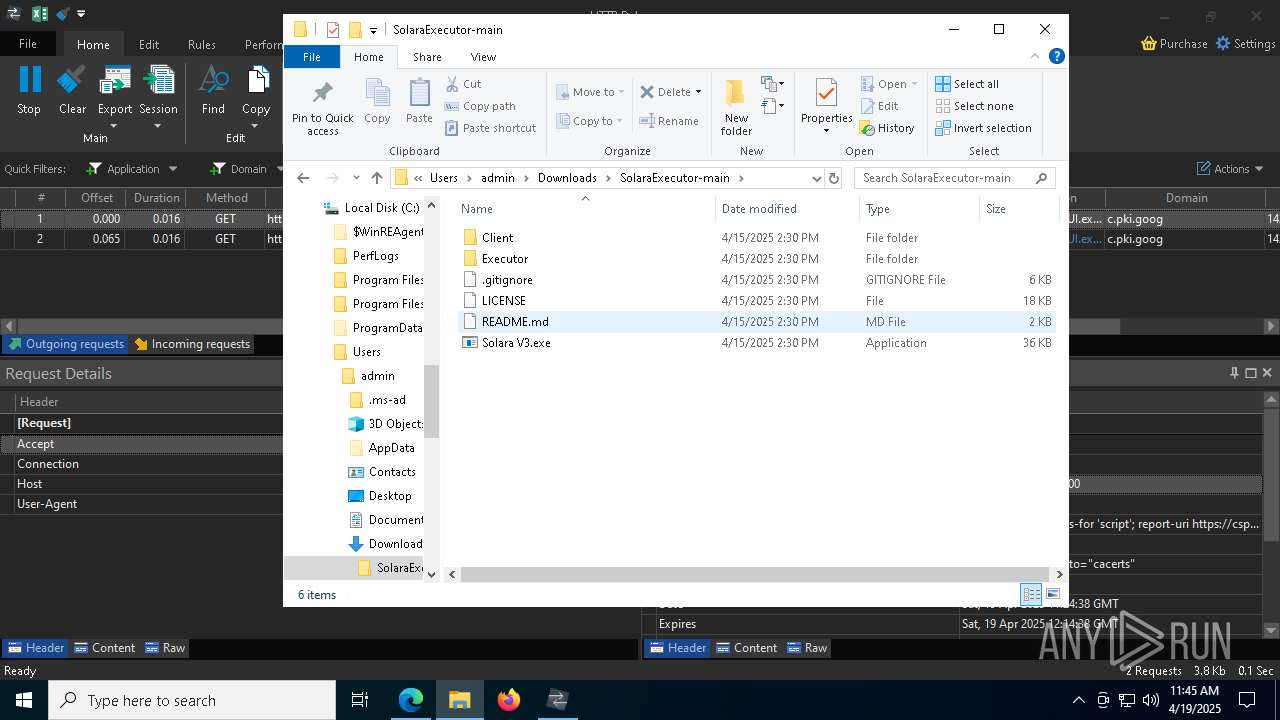
Manual execution by a user
- WinRAR.exe (PID: 8748)
- Solara V3.exe (PID: 8720)
Manages system restore points
- SrTasks.exe (PID: 8848)
Reads the machine GUID from the registry
- msiexec.exe (PID: 6148)
- HTTPDebuggerSvc.exe (PID: 9064)
- HTTPDebuggerUI.exe (PID: 9204)
- Solara V3.exe (PID: 8720)
- HTTPDebuggerSvc.exe (PID: 9128)
- MSBuild.exe (PID: 7676)
Creates files in the program directory
- HTTPDebuggerSvc.exe (PID: 9064)
Checks proxy server information
- HTTPDebuggerUI.exe (PID: 9204)
- slui.exe (PID: 8544)
- powershell.exe (PID: 9008)
Creates files or folders in the user directory
- HTTPDebuggerUI.exe (PID: 9204)
Process checks computer location settings
- msiexec.exe (PID: 3364)
Create files in a temporary directory
- Solara V3.exe (PID: 8720)
- powershell.exe (PID: 9192)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 9008)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 9008)
Disables trace logs
- powershell.exe (PID: 9008)
Gets data length (POWERSHELL)
- powershell.exe (PID: 9008)
The executable file from the user directory is run by the Powershell process
- iqrhpael.bhu0.exe (PID: 8620)
Creates a software uninstall entry
- msiexec.exe (PID: 6148)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
232
Monitored processes
91
Malicious processes
6
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 232 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --no-appcompat-clear --gpu-preferences=WAAAAAAAAADoAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAABEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=8608 --field-trial-handle=2420,i,17292958852734760221,4747629199571579782,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 644 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6524 --field-trial-handle=2420,i,17292958852734760221,4747629199571579782,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 680 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x300,0x304,0x308,0x2f8,0x310,0x7ffc886c5fd8,0x7ffc886c5fe4,0x7ffc886c5ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 720 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=8516 --field-trial-handle=2420,i,17292958852734760221,4747629199571579782,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 720 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6648 --field-trial-handle=2420,i,17292958852734760221,4747629199571579782,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 968 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=5672 --field-trial-handle=2420,i,17292958852734760221,4747629199571579782,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1188 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6820 --field-trial-handle=2420,i,17292958852734760221,4747629199571579782,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1228 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=29 --mojo-platform-channel-handle=6004 --field-trial-handle=2420,i,17292958852734760221,4747629199571579782,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1760 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=8956 --field-trial-handle=2420,i,17292958852734760221,4747629199571579782,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2552 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=2404 --field-trial-handle=2420,i,17292958852734760221,4747629199571579782,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
44 209
Read events
43 822
Write events
369
Delete events
18
Modification events
| (PID) Process: | (4724) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (4724) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (4724) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4724) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (4724) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: E30D6B6EB6912F00 | |||
| (PID) Process: | (4724) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 8003766EB6912F00 | |||
| (PID) Process: | (4724) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262992 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {21C02BB7-1914-45BA-B663-F62EB568ABC3} | |||
| (PID) Process: | (4724) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262992 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {FB1B5AA5-DC1D-403A-82E1-005F093DDF78} | |||
| (PID) Process: | (4724) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262992 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {3A040667-6298-4048-B5EC-CC26BBBB80C2} | |||
| (PID) Process: | (4724) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262992 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {4AA1A082-5418-4CAF-933C-A68A66DDFC52} | |||
Executable files
86
Suspicious files
1 008
Text files
192
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4724 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10e62c.TMP | — | |
MD5:— | SHA256:— | |||
| 4724 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4724 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10e62c.TMP | — | |
MD5:— | SHA256:— | |||
| 4724 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10e62c.TMP | — | |
MD5:— | SHA256:— | |||
| 4724 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4724 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10e65a.TMP | — | |
MD5:— | SHA256:— | |||
| 4724 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10e65a.TMP | — | |
MD5:— | SHA256:— | |||
| 4724 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4724 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4724 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
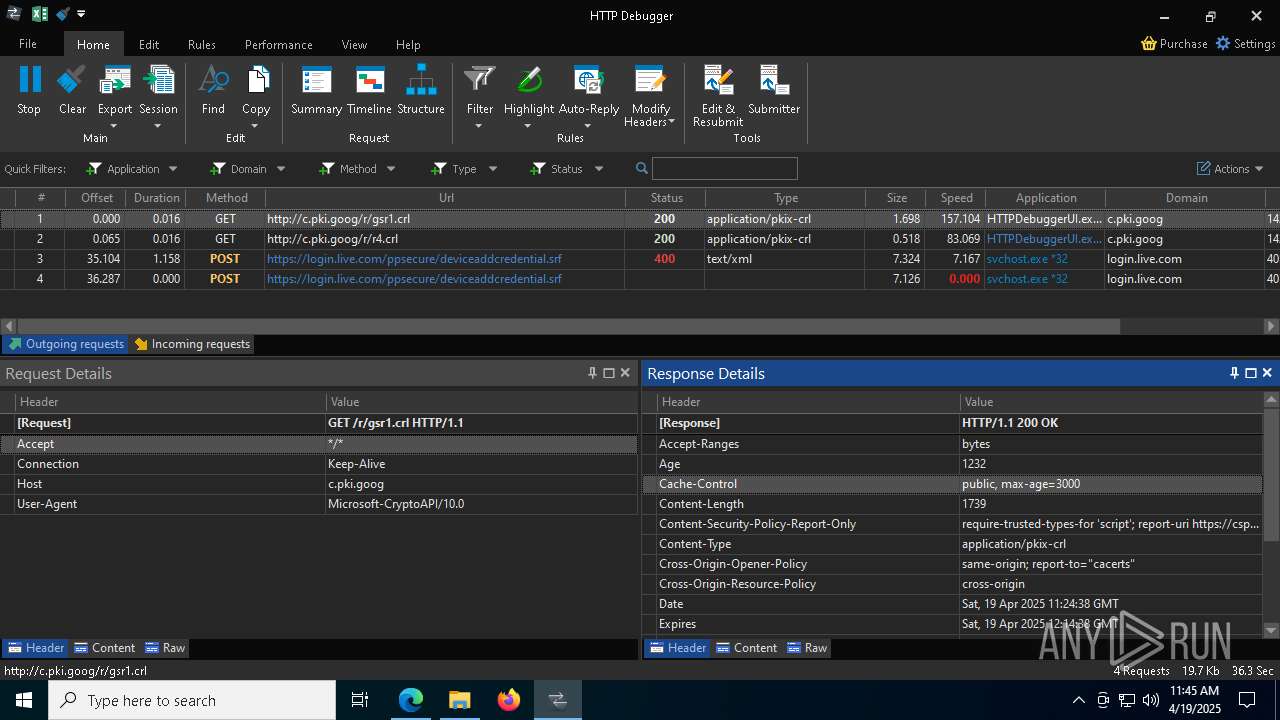
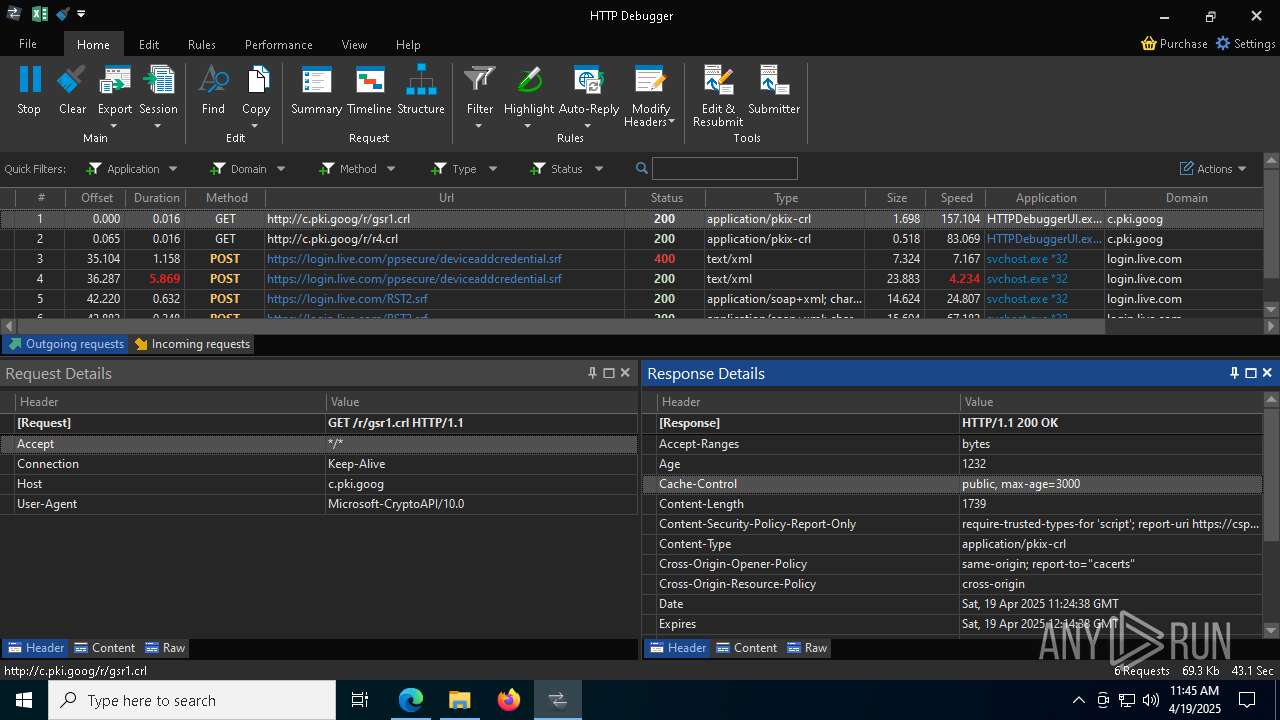
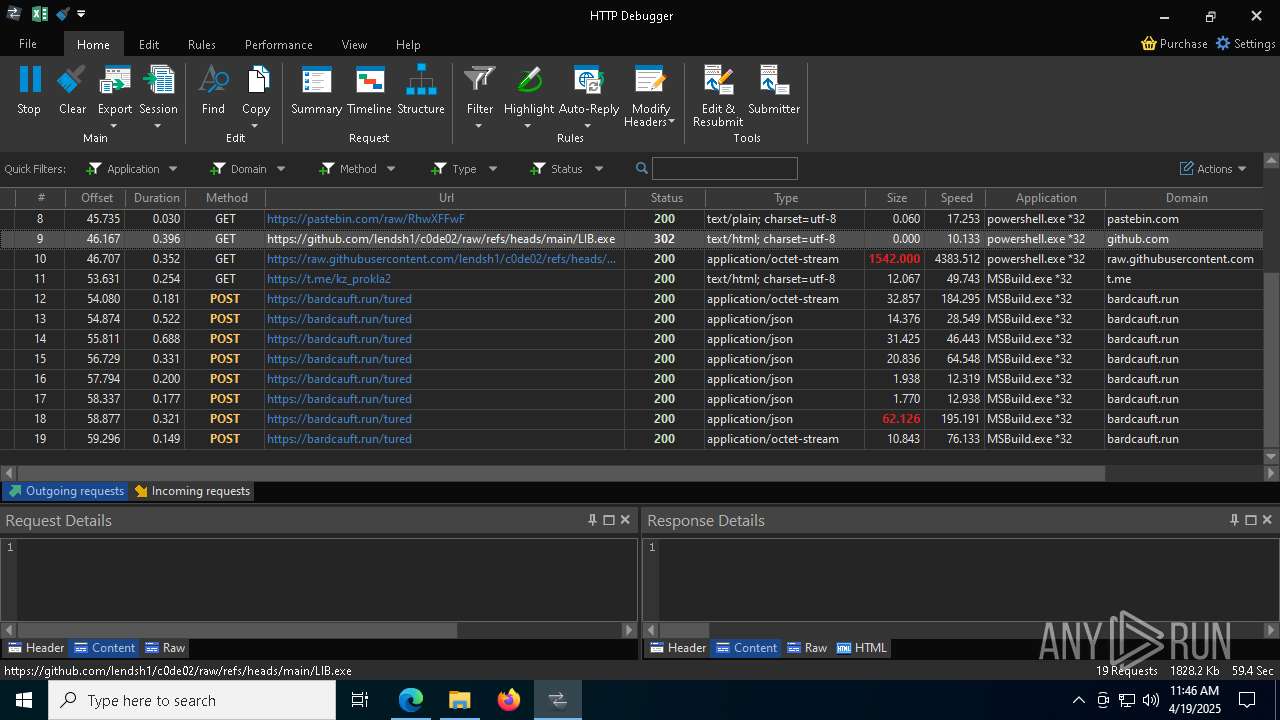
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
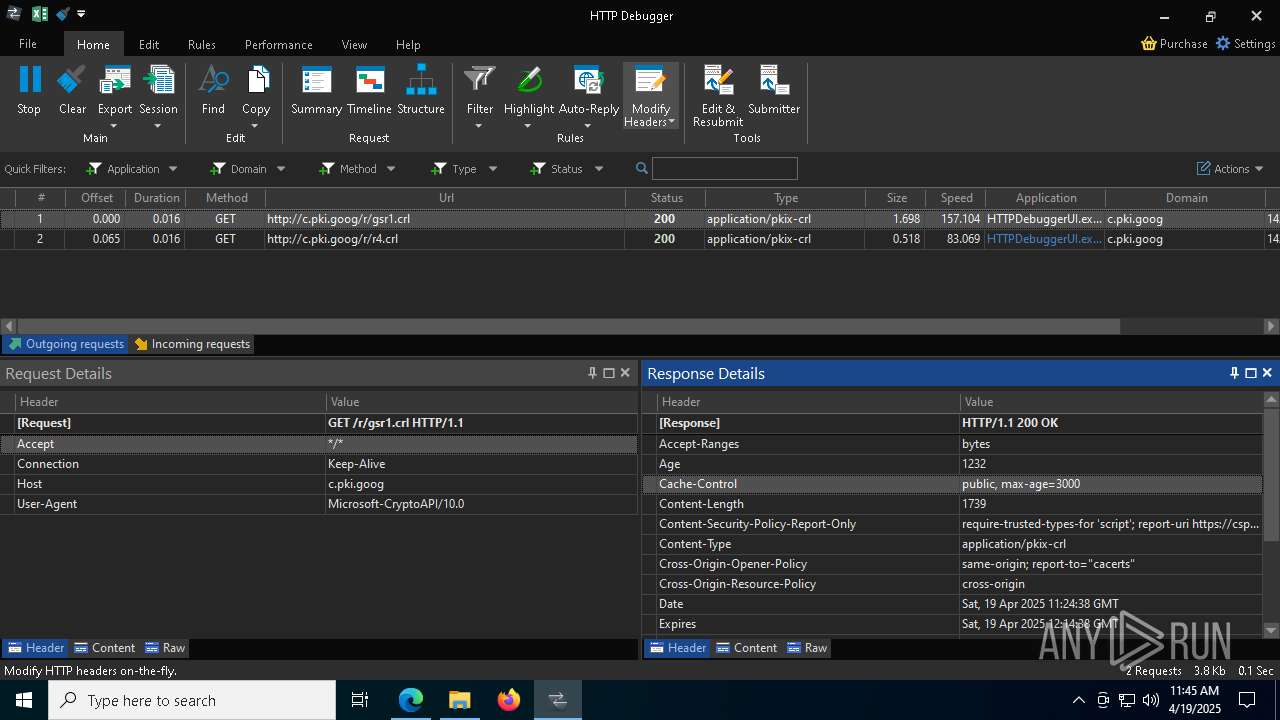
HTTP(S) requests
58
TCP/UDP connections
176
DNS requests
191
Threats
12
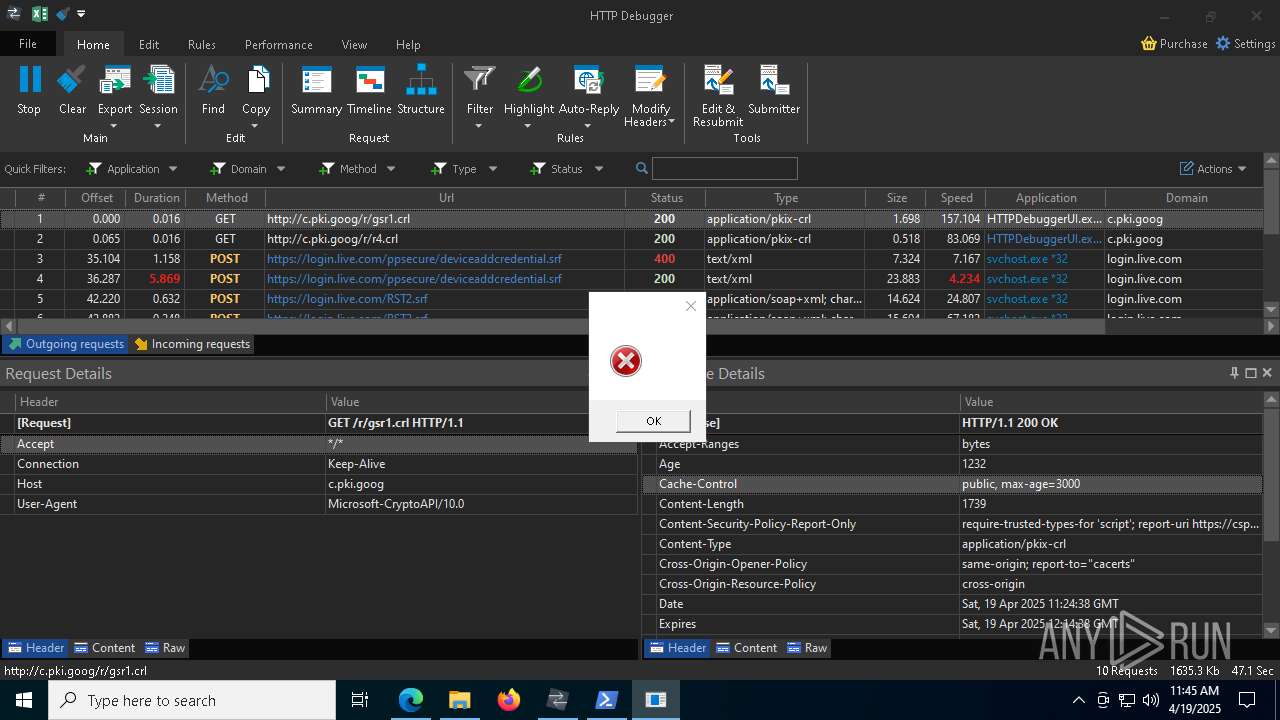
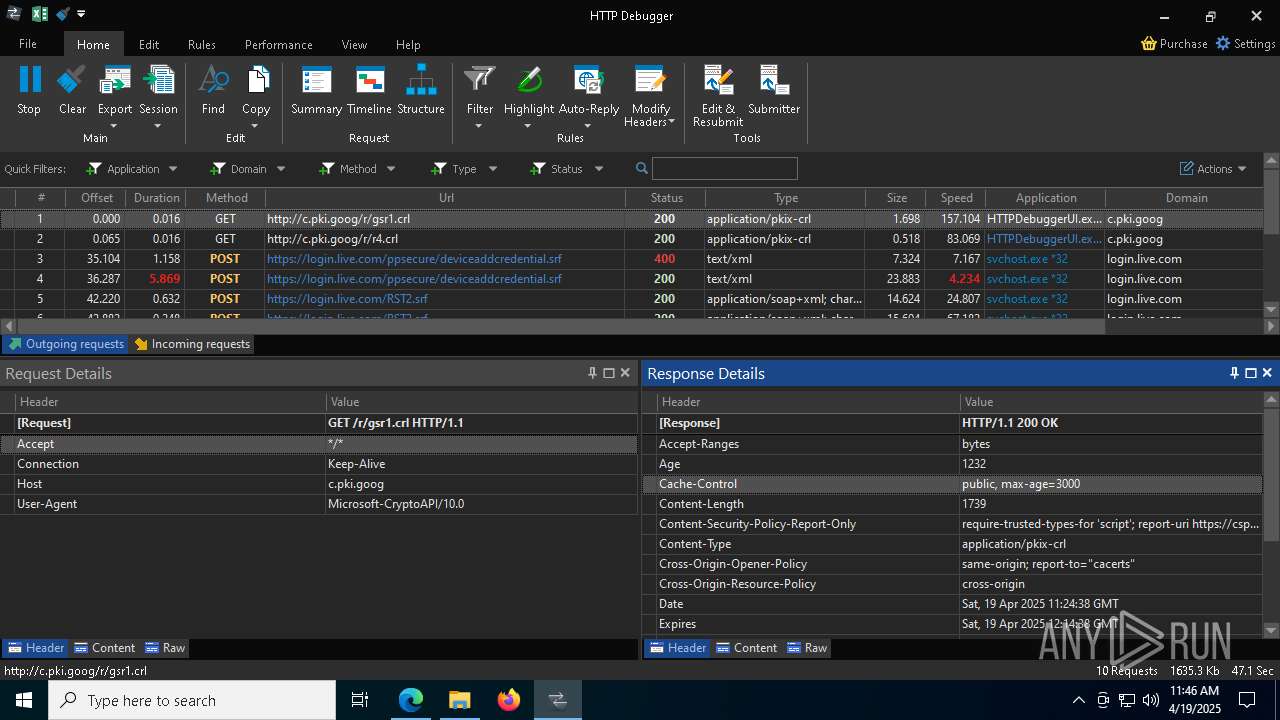
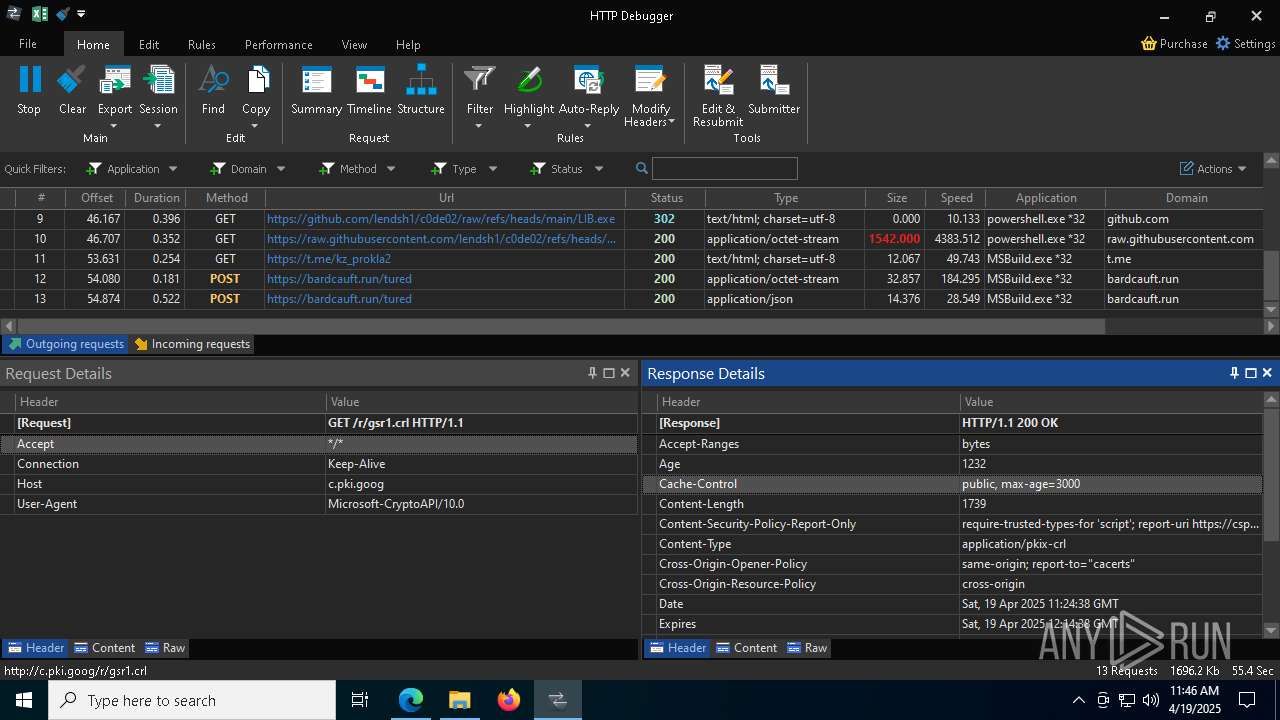
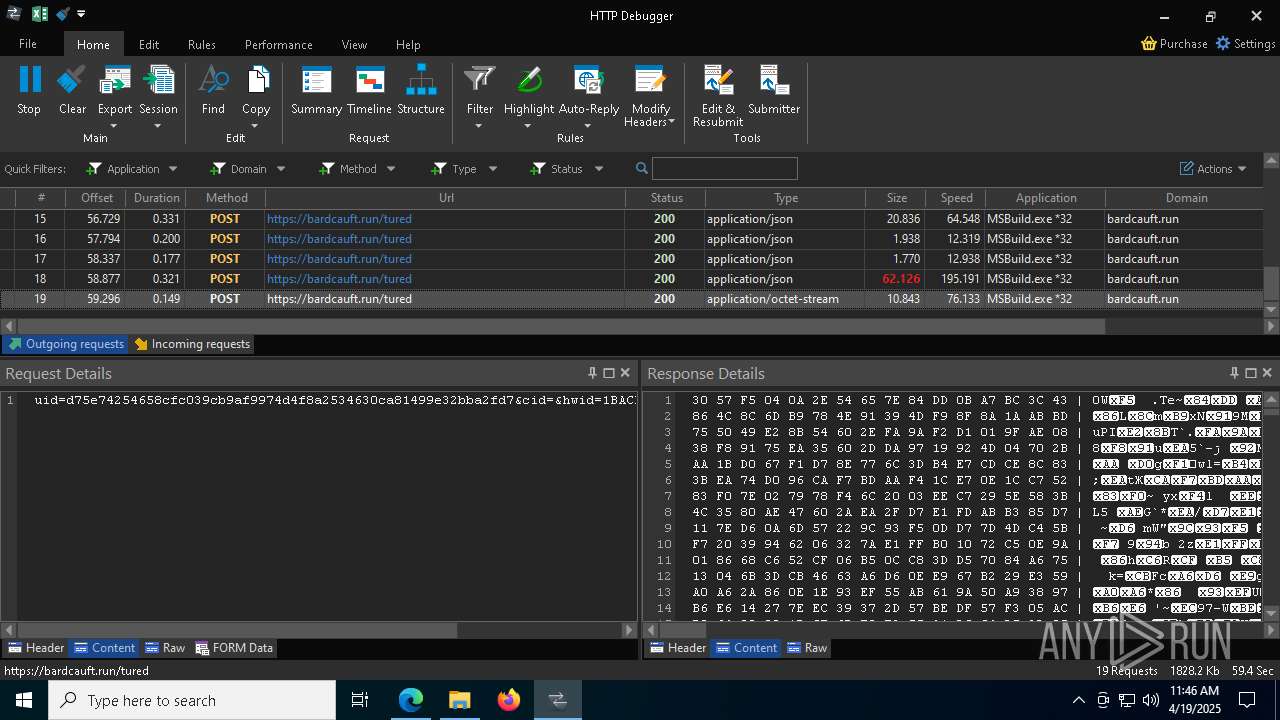
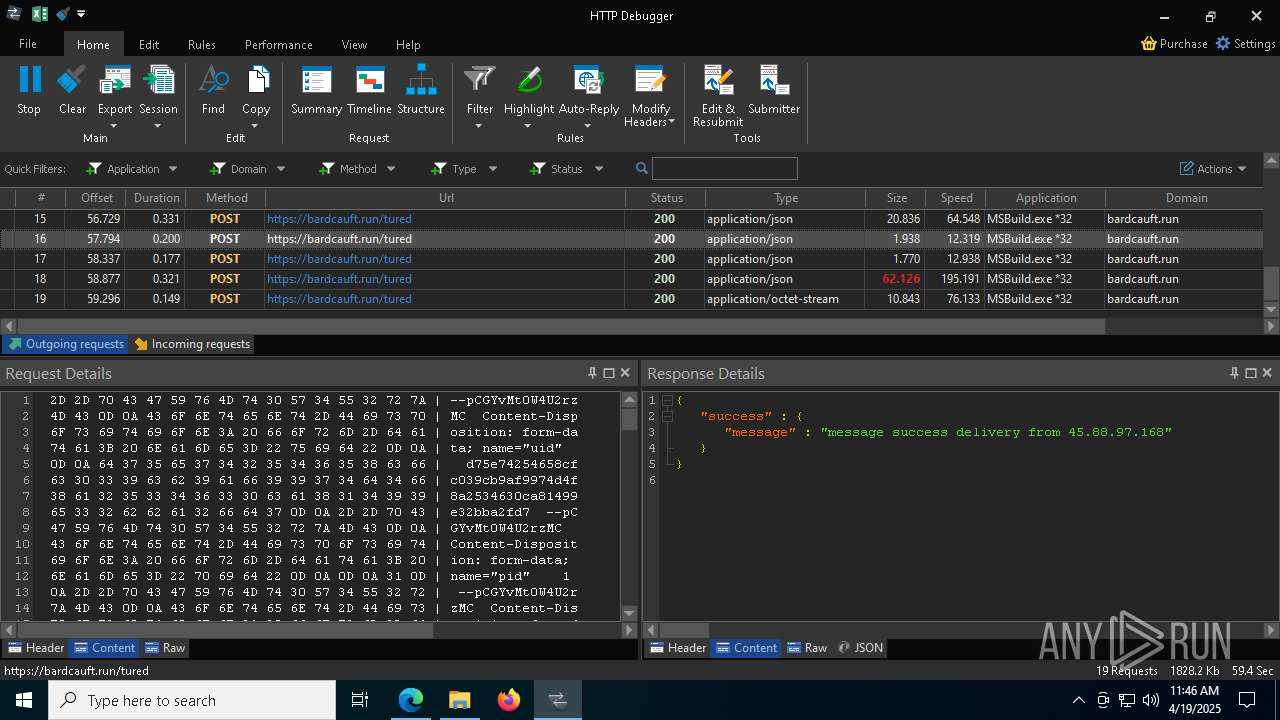
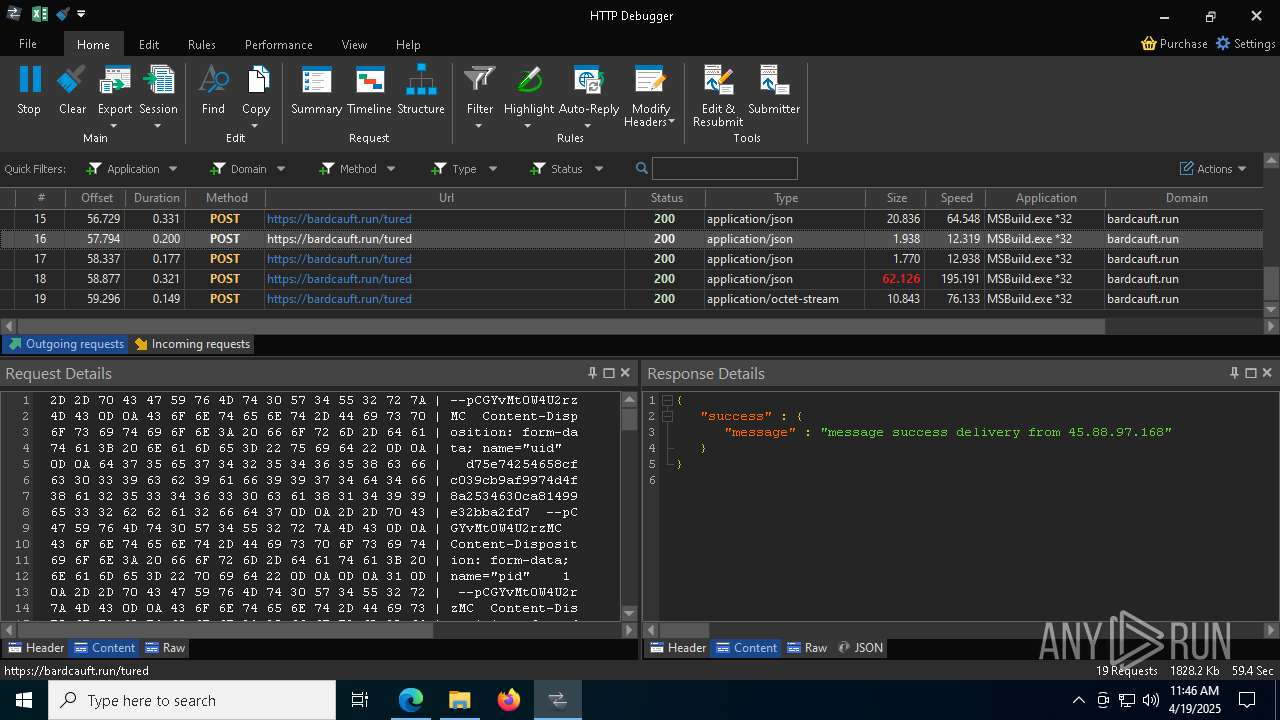
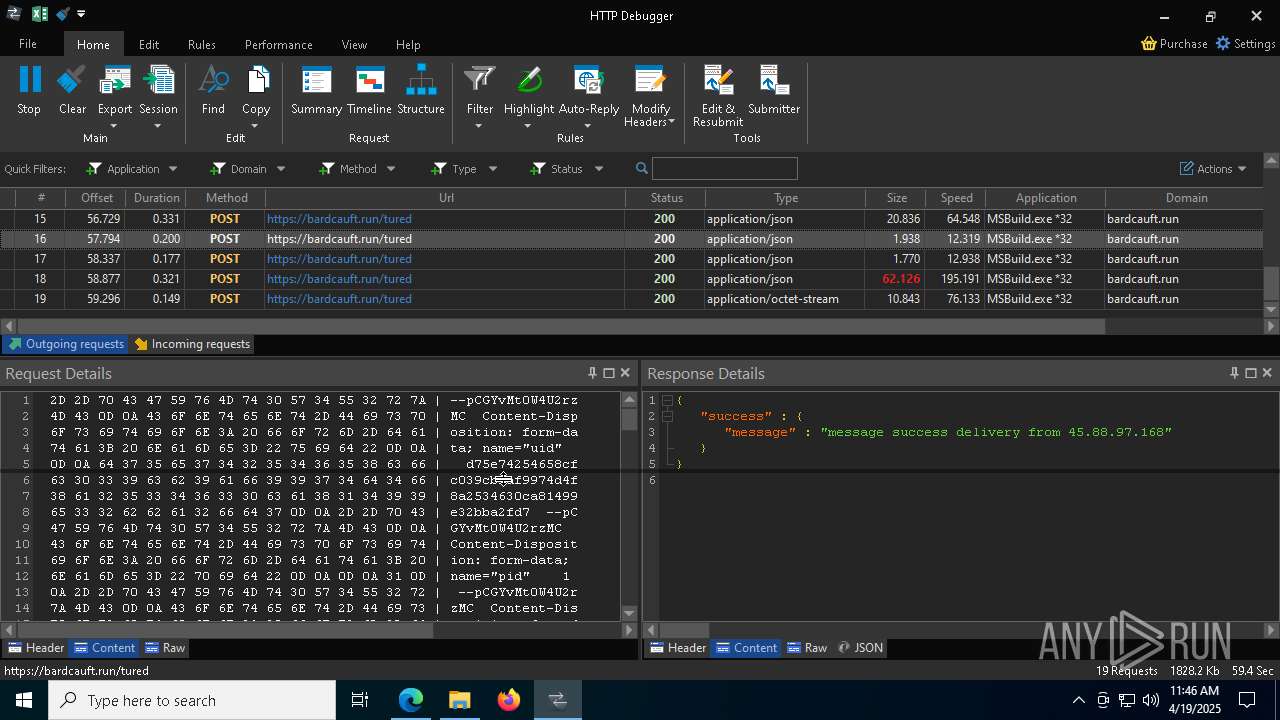
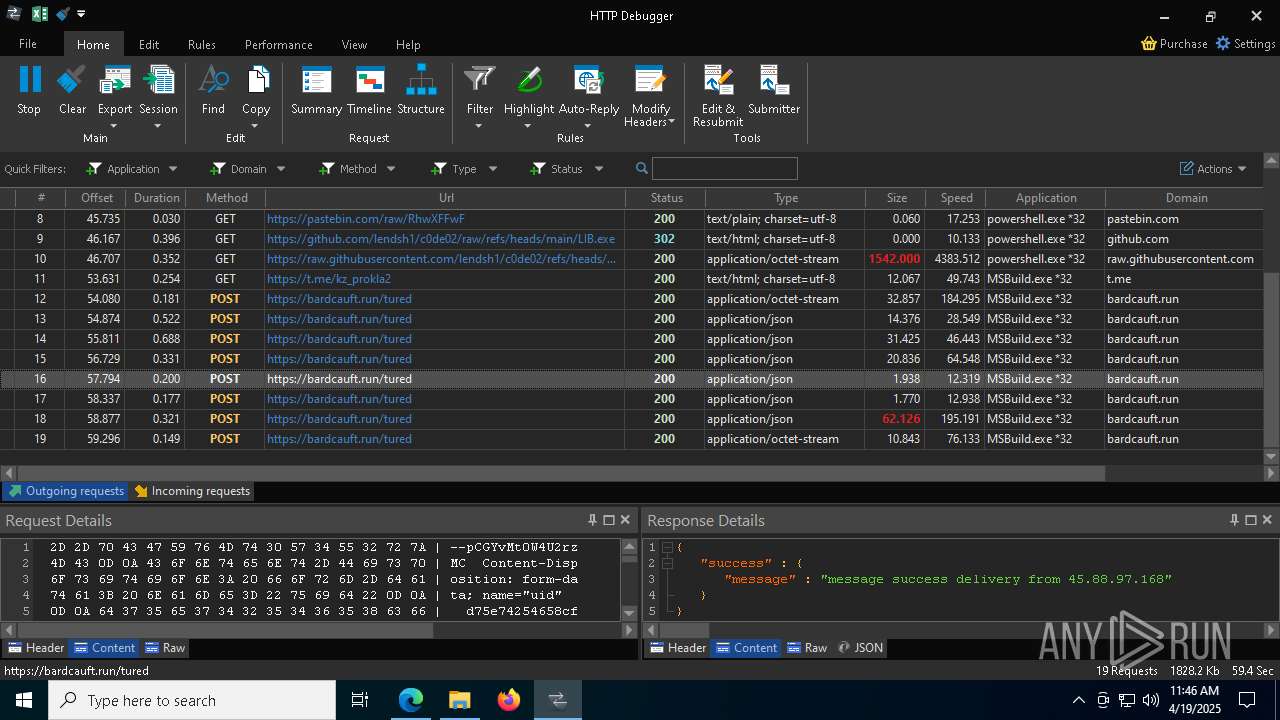
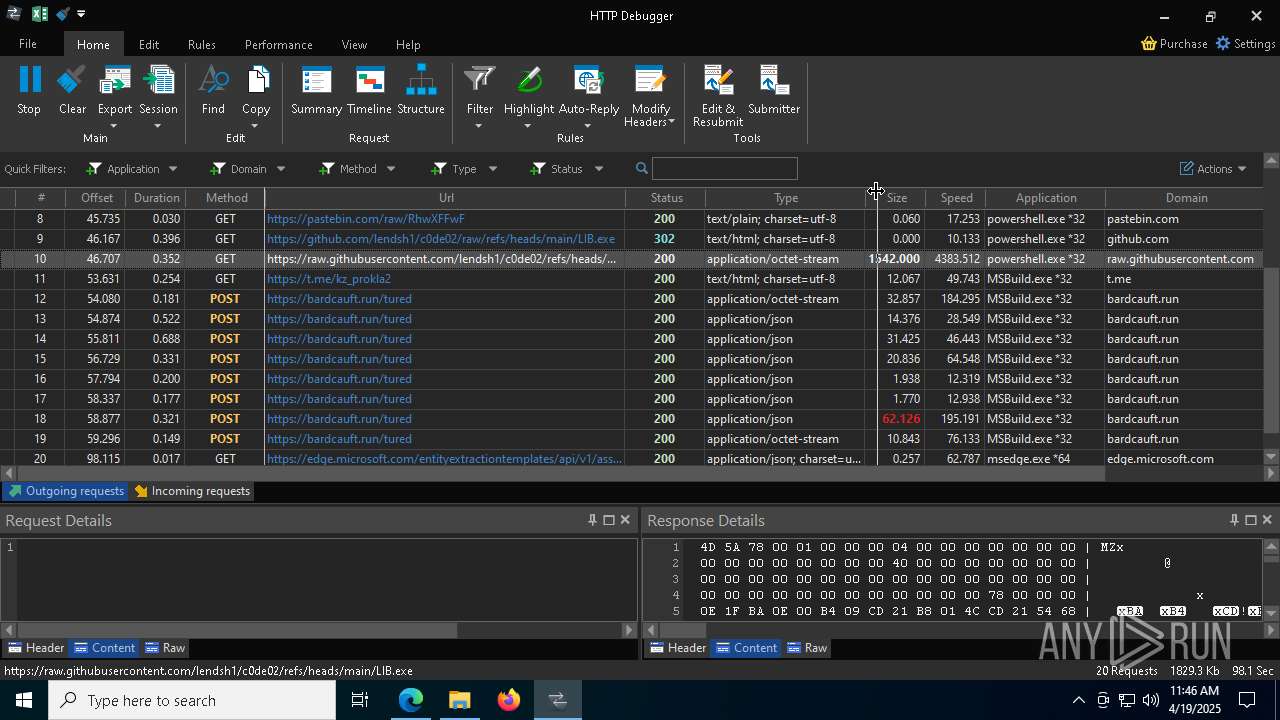
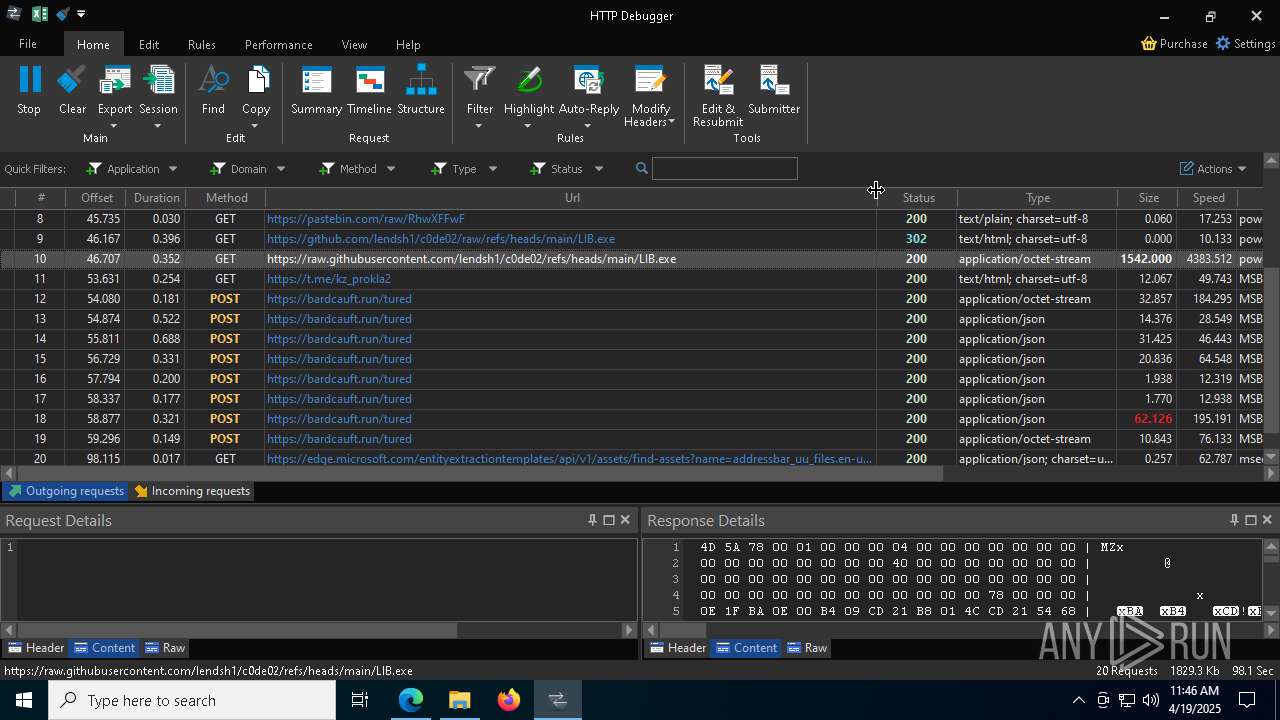
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4200 | SIHClient.exe | GET | 200 | 2.16.253.202:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4724 | msedge.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEEj8k7RgVZSNNqfJionWlBY%3D | unknown | — | — | whitelisted |
4200 | SIHClient.exe | GET | 200 | 2.16.253.202:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4724 | msedge.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSdE3gf41WAic8Uh9lF92%2BIJqh5qwQUMuuSmv81lkgvKEBCcCA2kVwXheYCEGIdbQxSAZ47kHkVIIkhHAo%3D | unknown | — | — | whitelisted |
4724 | msedge.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.sectigo.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBQVD%2BnGf79Hpedv3mhy6uKMVZkPCQQUDyrLIIcouOxvSK4rVKYpqhekzQwCEQDtthVfU%2B%2F7gocIV2%2BT%2FEao | unknown | — | — | whitelisted |
8232 | svchost.exe | HEAD | 200 | 208.89.74.19:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1745622716&P2=404&P3=2&P4=d56yqe6YYyLEVPEVQW4FPu8UkaKaXb%2bG%2b%2fc4rgvscDesokXmHdSiHu3DwYBoVKdiRQPeqQqHff0rf2hvocEa3g%3d%3d | unknown | — | — | whitelisted |
8232 | svchost.exe | GET | 206 | 208.89.74.19:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1745622716&P2=404&P3=2&P4=d56yqe6YYyLEVPEVQW4FPu8UkaKaXb%2bG%2b%2fc4rgvscDesokXmHdSiHu3DwYBoVKdiRQPeqQqHff0rf2hvocEa3g%3d%3d | unknown | — | — | whitelisted |
8232 | svchost.exe | GET | 206 | 208.89.74.19:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1745622716&P2=404&P3=2&P4=d56yqe6YYyLEVPEVQW4FPu8UkaKaXb%2bG%2b%2fc4rgvscDesokXmHdSiHu3DwYBoVKdiRQPeqQqHff0rf2hvocEa3g%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1600 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4724 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2984 | msedge.exe | 140.82.121.3:443 | github.com | GITHUB | US | whitelisted |
2984 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2984 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2984 | msedge.exe | 13.107.253.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2984 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2984 | msedge.exe | 23.48.23.51:443 | bzib.nelreports.net | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
github.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
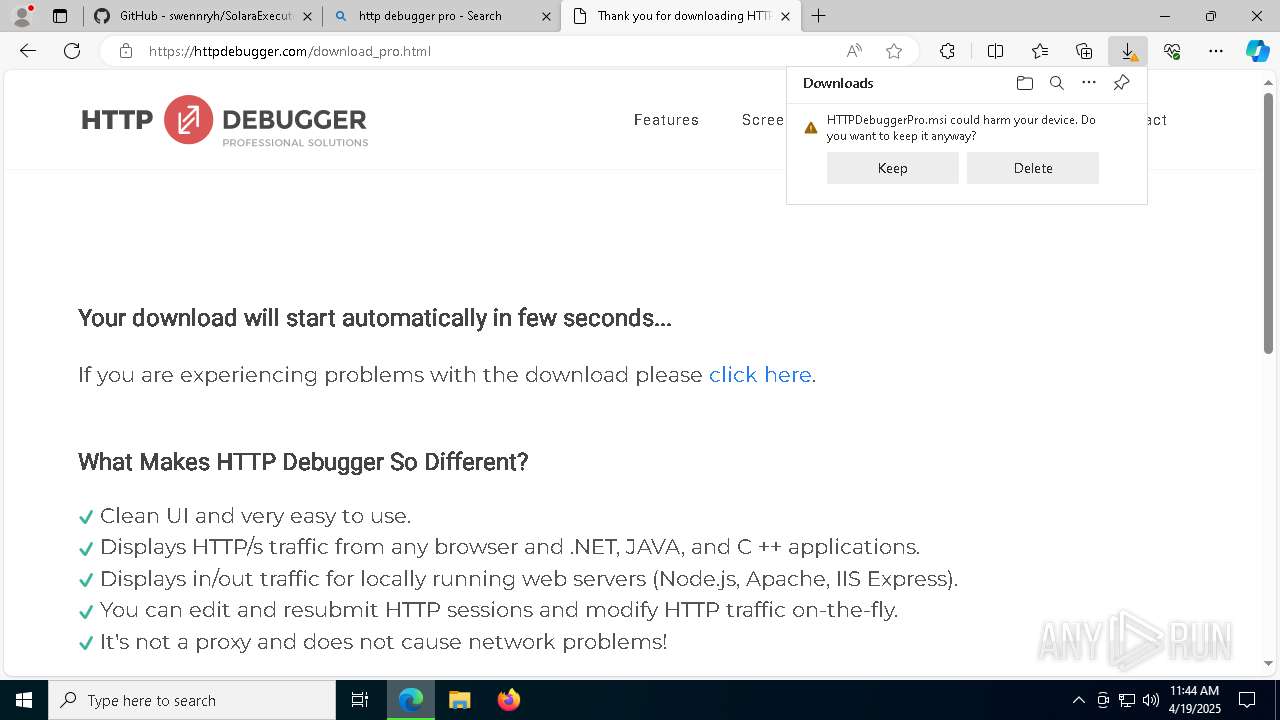
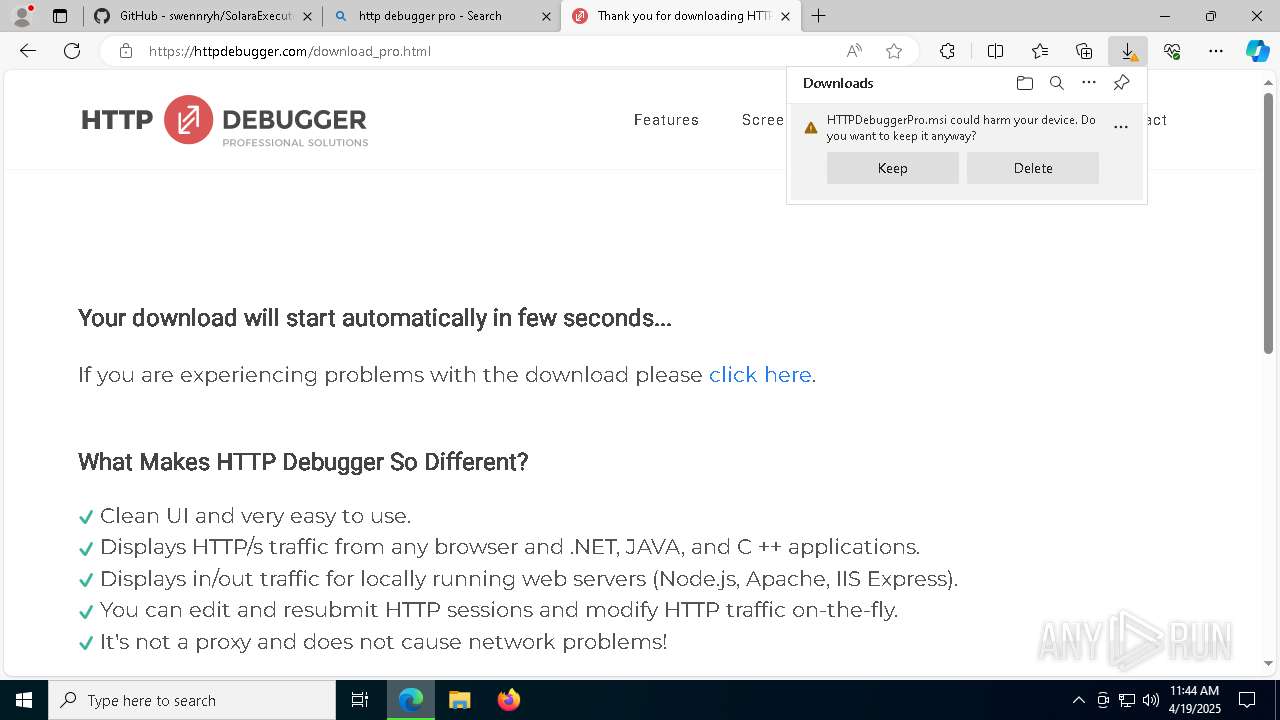
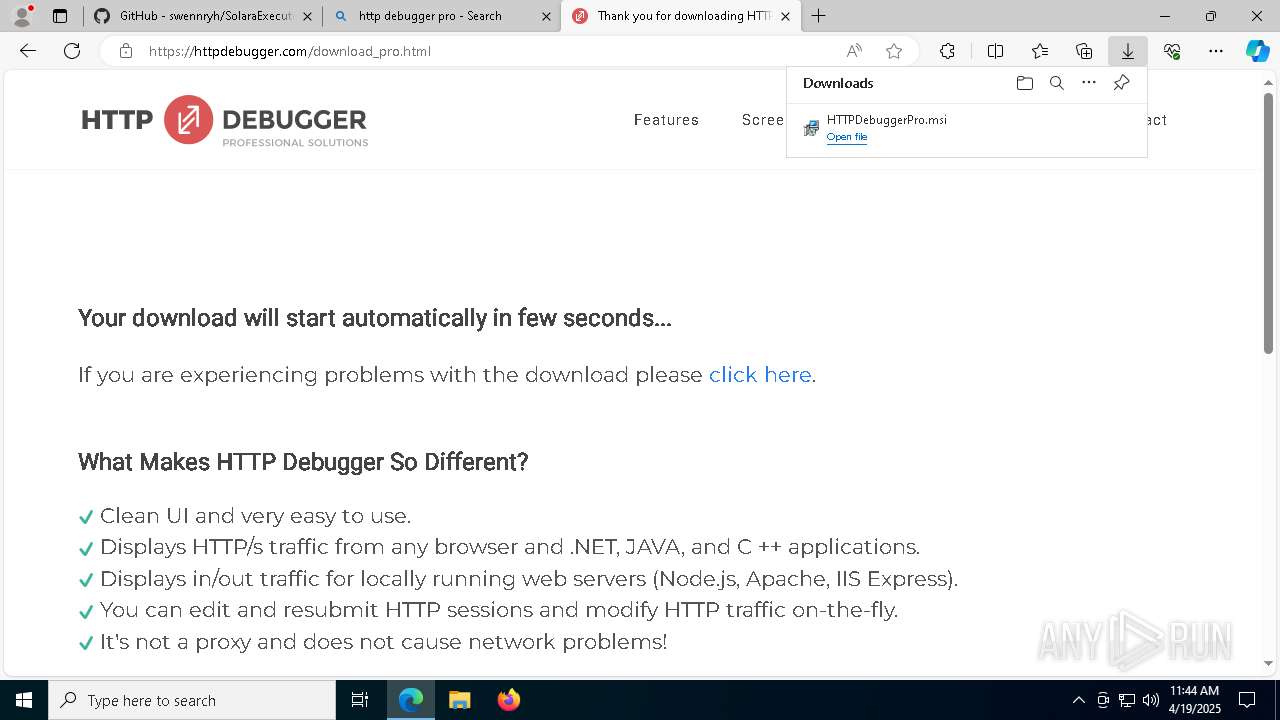
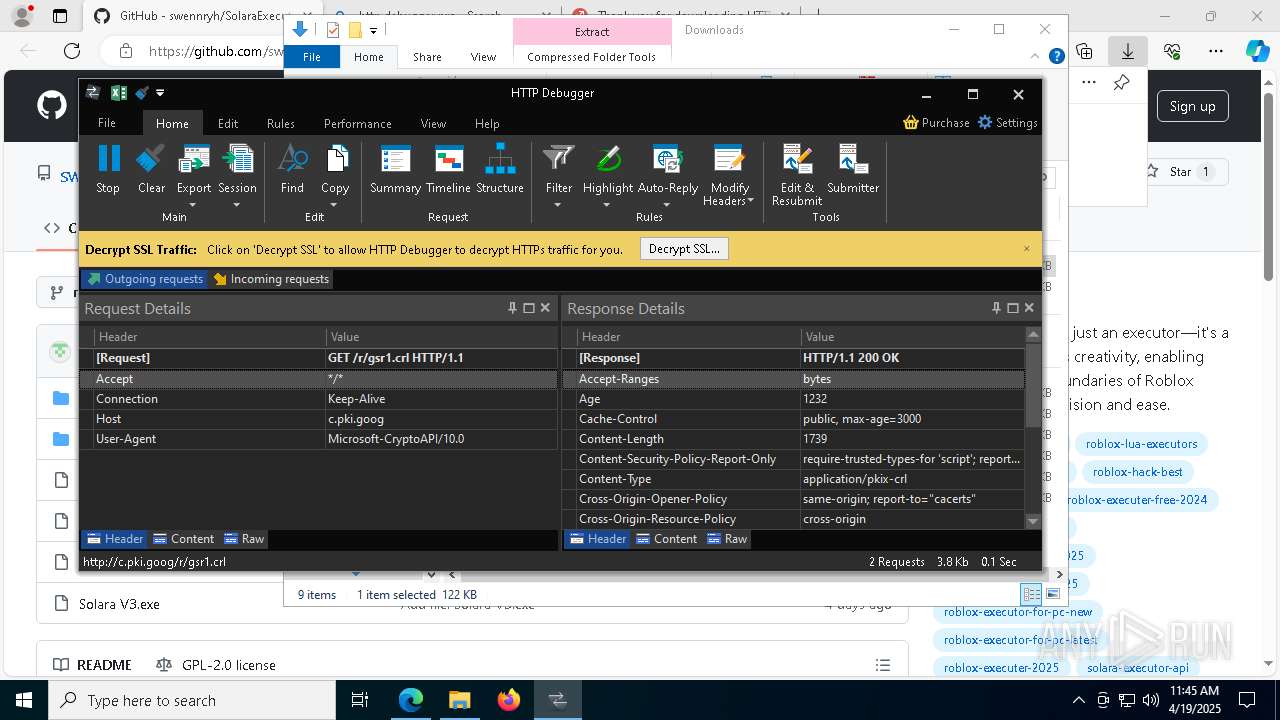
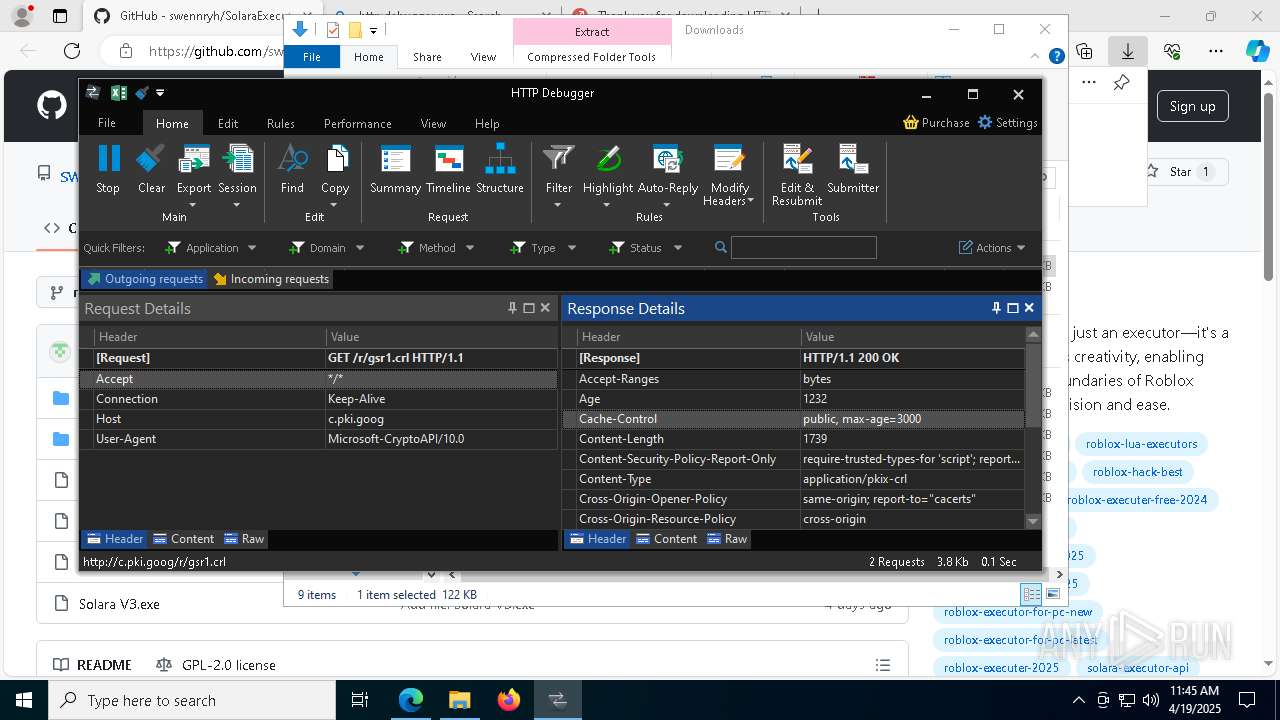
2984 | msedge.exe | Misc activity | ET INFO Observed DNS Query to HTTP Sniffer Domain (httpdebugger .com) |
2984 | msedge.exe | Misc activity | ET INFO Observed DNS Query to HTTP Sniffer Domain (httpdebugger .com) |
2984 | msedge.exe | Misc activity | ET INFO Observed DNS Query to HTTP Sniffer Domain (httpdebugger .com) |
2984 | msedge.exe | Misc activity | ET INFO Observed DNS Query to HTTP Sniffer Domain (httpdebugger .com) |
2984 | msedge.exe | Misc activity | ET INFO HTTP Sniffer Domain in TLS SNI (httpdebugger .com) |
2984 | msedge.exe | Misc activity | ET INFO HTTP Sniffer Domain in TLS SNI (httpdebugger .com) |
2984 | msedge.exe | Misc activity | ET INFO HTTP Sniffer Domain in TLS SNI (httpdebugger .com) |
2984 | msedge.exe | Misc activity | ET INFO HTTP Sniffer Domain in TLS SNI (httpdebugger .com) |
2984 | msedge.exe | Misc activity | ET INFO HTTP Sniffer Domain in TLS SNI (httpdebugger .com) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Online Pastebin Text Storage |