| File name: | take3.exe |
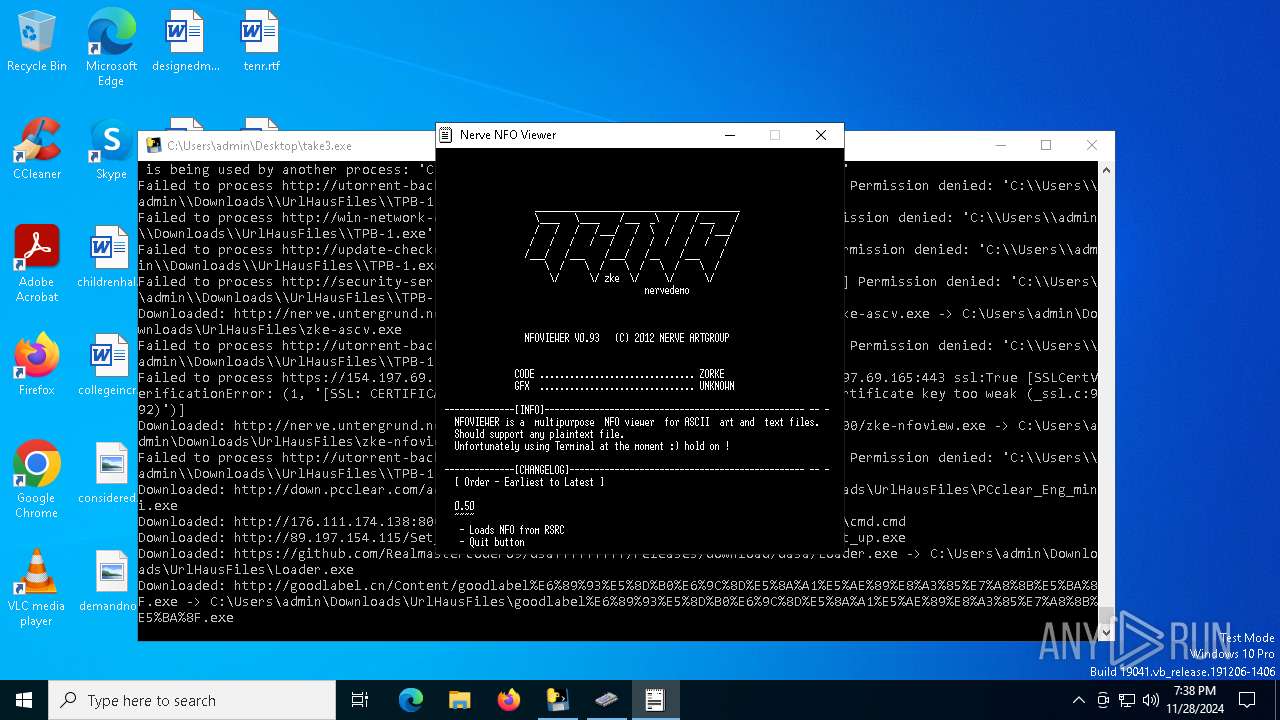
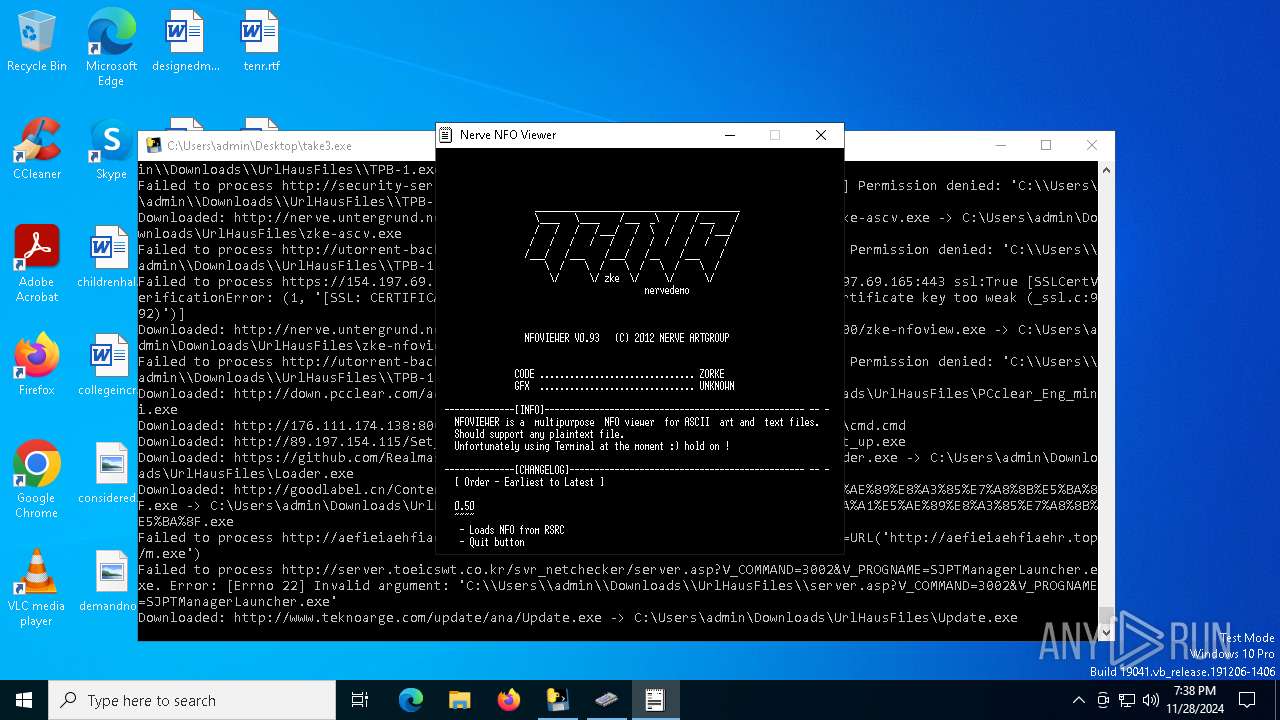
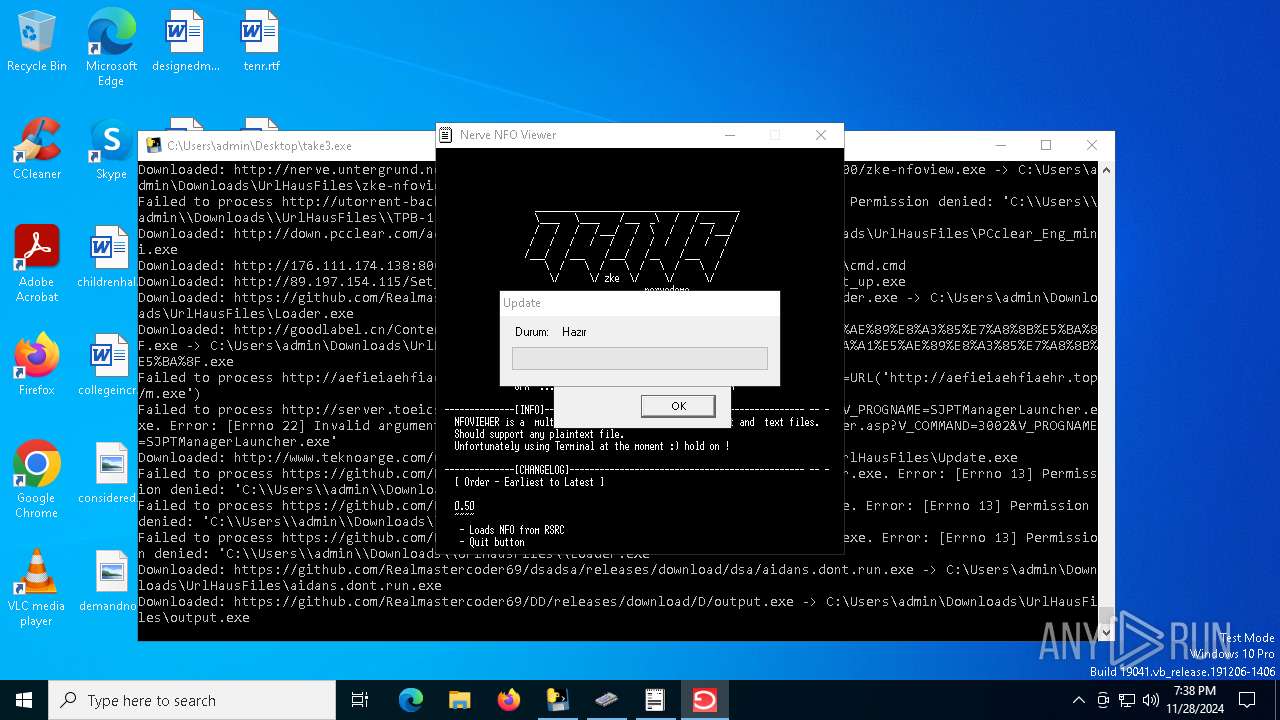
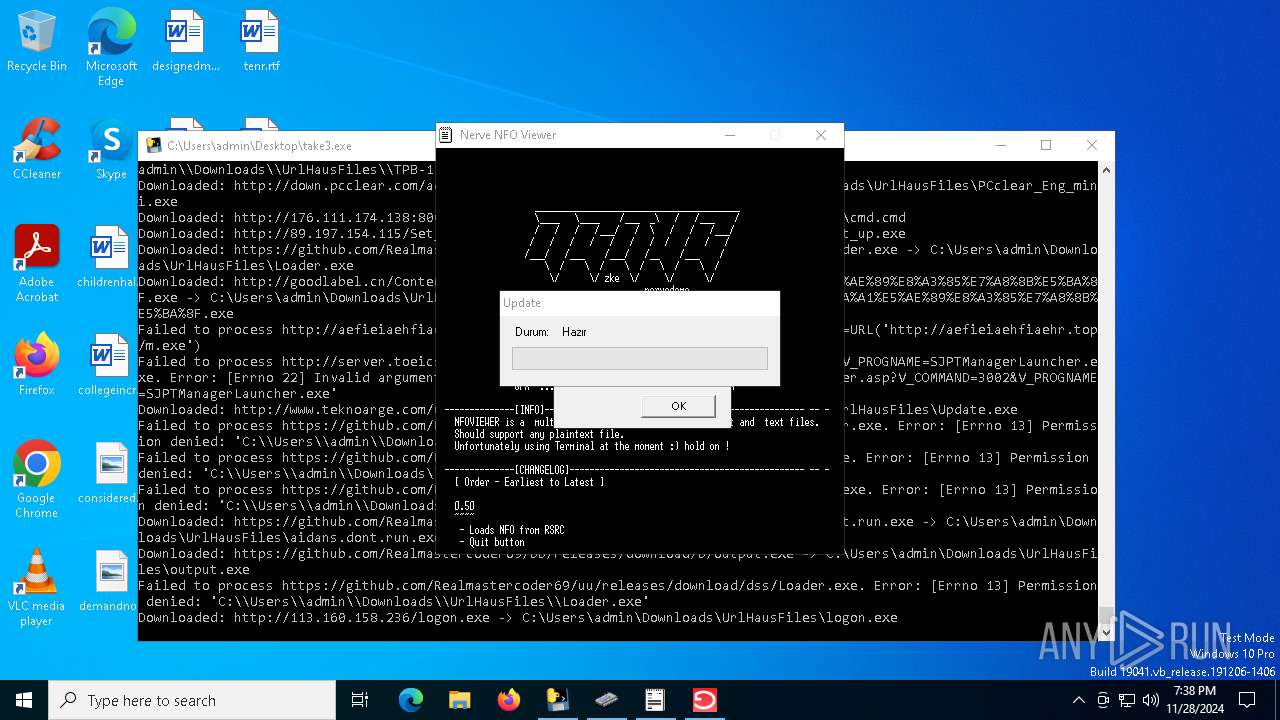
| Full analysis: | https://app.any.run/tasks/7e2c8d27-b17c-4e68-b4a4-44aceceb92e3 |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | November 28, 2024, 19:37:50 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (console) x86-64, for MS Windows, 6 sections |
| MD5: | 84C0EA78EB89B7ABEE5E03AE8EE708E4 |
| SHA1: | 91339BD35BD8F01868B8FF39D57B2F07FB050A0B |
| SHA256: | 9F9CFE42A0768CC02609FCABF58B8CCCE826D5D768E8C6D3A6728F543C4EAC53 |
| SSDEEP: | 196608:+7C92OaZ2N3TeRi/Bq1nAOugneT4Euo0:lnN3KRi5qeO1/2 |
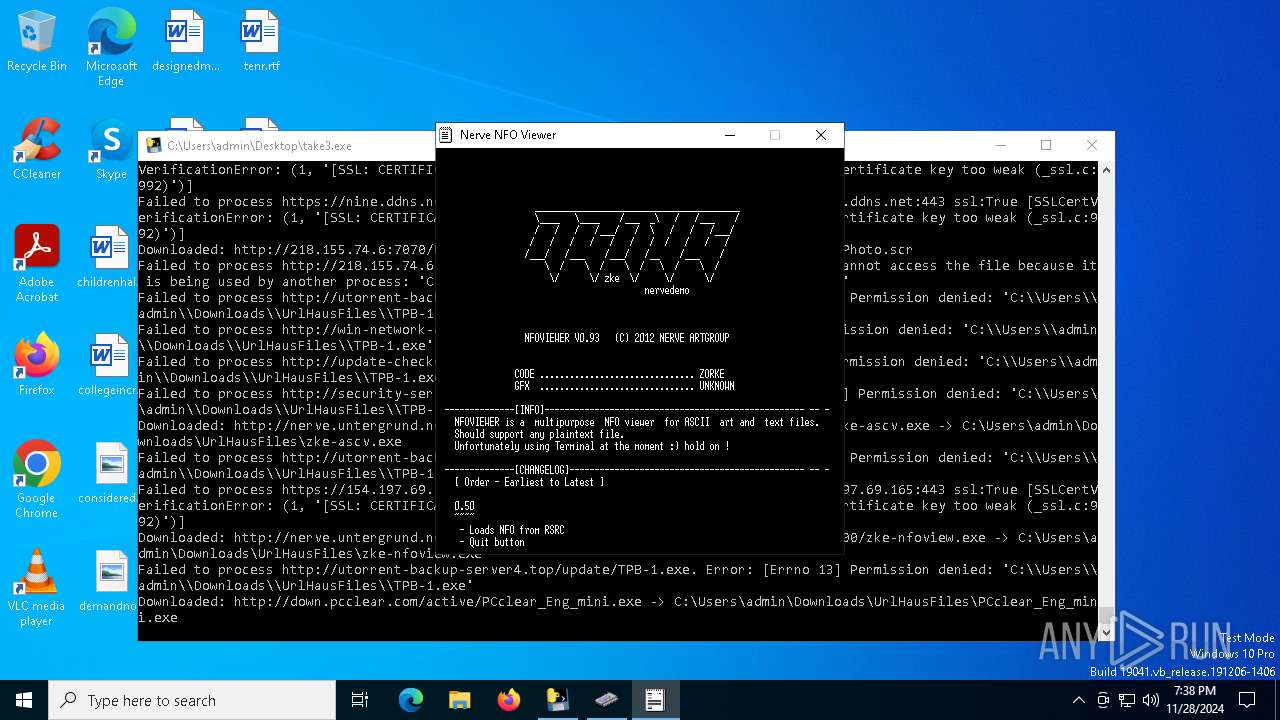
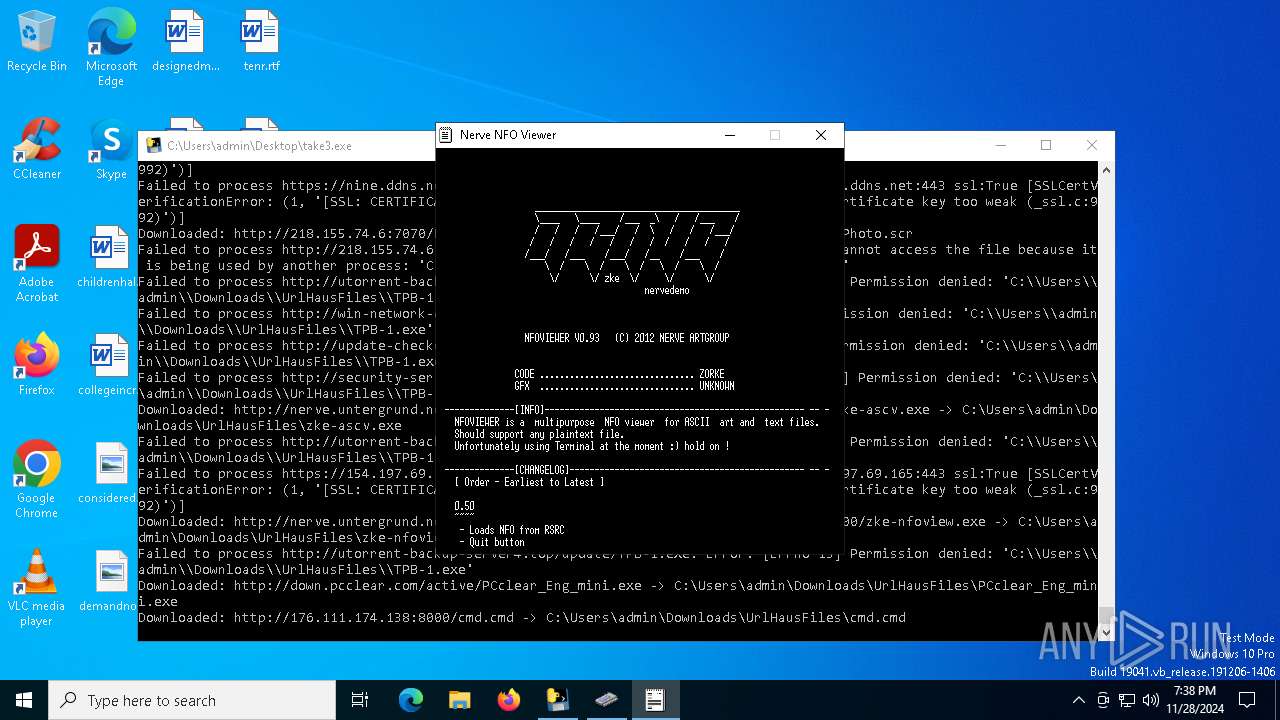
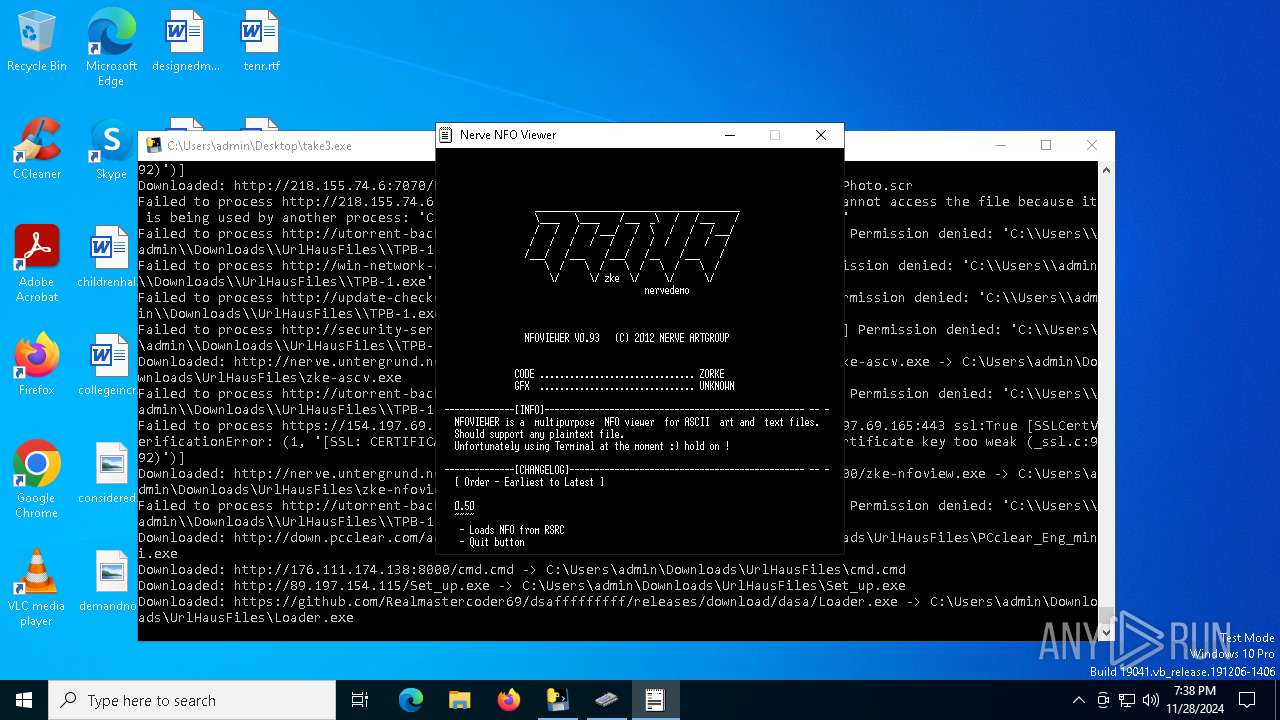
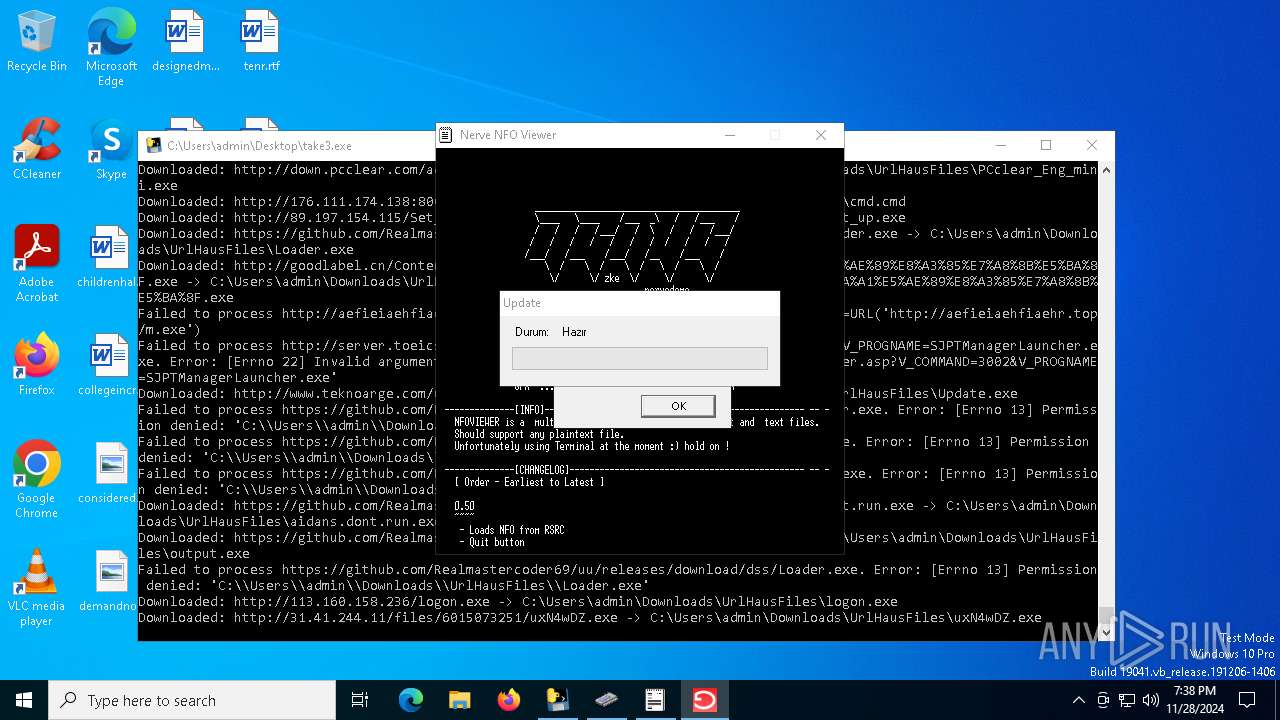
MALICIOUS
Downloads files via BITSADMIN.EXE
- tvtC9D3.exe (PID: 6944)
Connects to the CnC server
- svchost.exe (PID: 2192)
PHORPIEX has been detected (SURICATA)
- svchost.exe (PID: 2192)
Actions looks like stealing of personal data
- TPB-1.exe (PID: 3988)
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2192)
- uxN4wDZ.exe (PID: 8000)
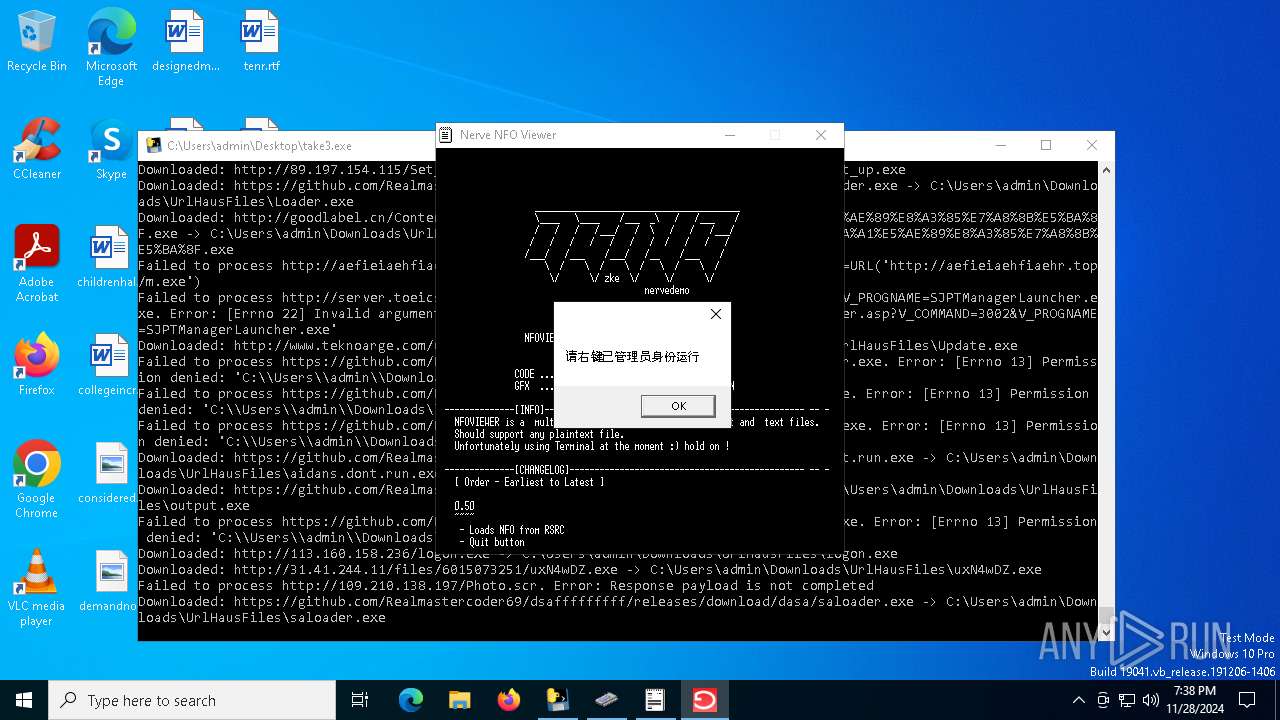
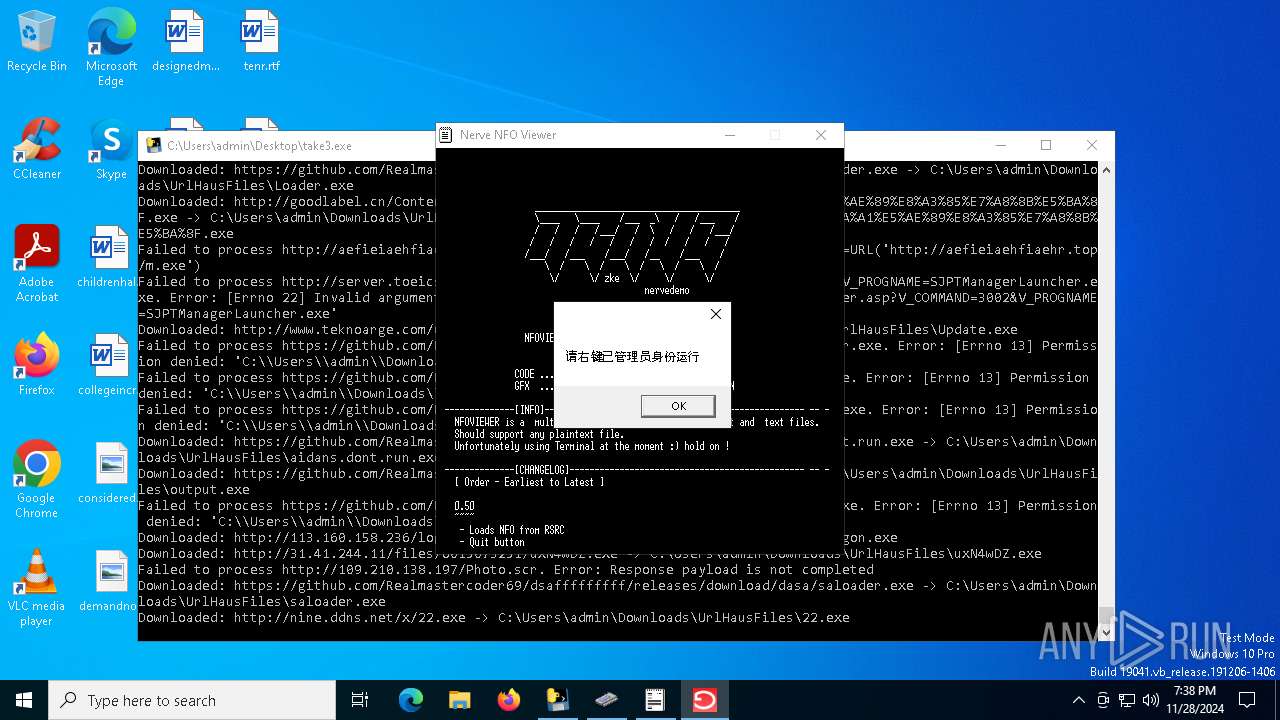
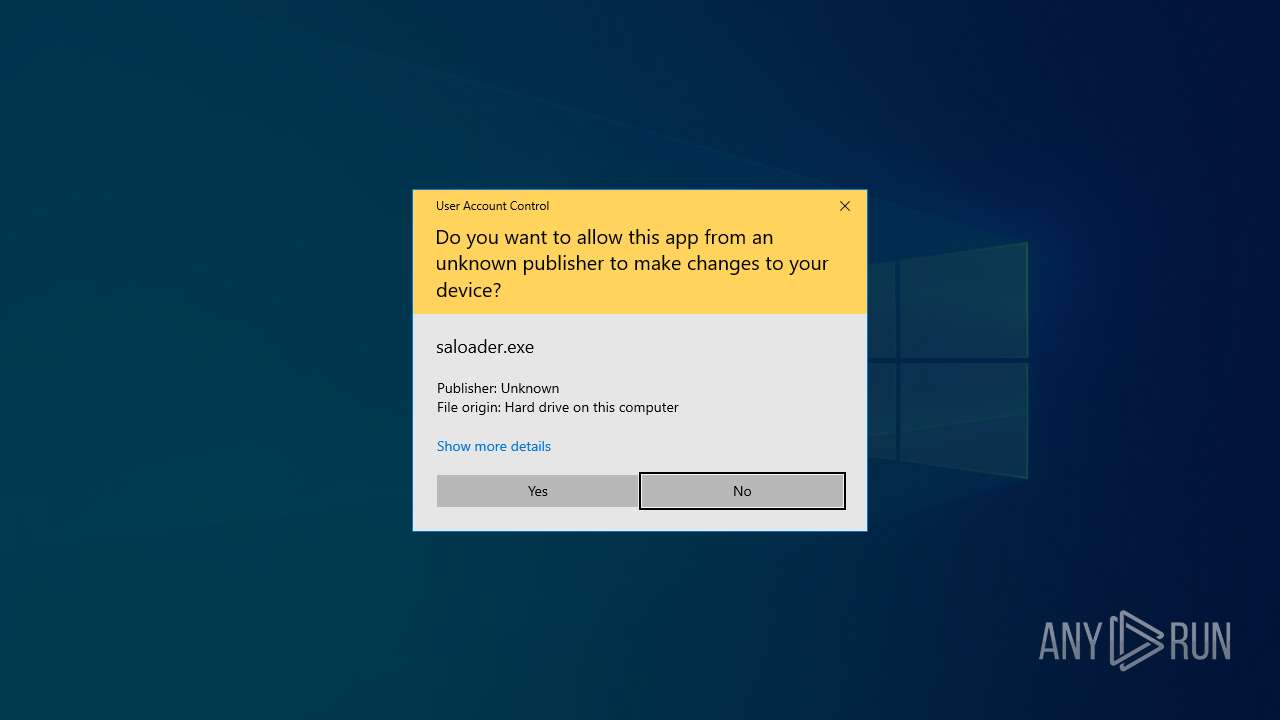
Adds path to the Windows Defender exclusion list
- saloader.exe (PID: 7732)
Changes antivirus protection settings for downloading files from the Internet (IOAVProtection)
- powershell.exe (PID: 6776)
Changes settings for checking scripts for malicious actions
- powershell.exe (PID: 6776)
Changes Controlled Folder Access settings
- powershell.exe (PID: 6776)
Changes settings for real-time protection
- powershell.exe (PID: 6776)
Changes settings for sending potential threat samples to Microsoft servers
- powershell.exe (PID: 6776)
Changes settings for reporting to Microsoft Active Protection Service (MAPS)
- powershell.exe (PID: 6776)
Changes settings for protection against network attacks (IPS)
- powershell.exe (PID: 6776)
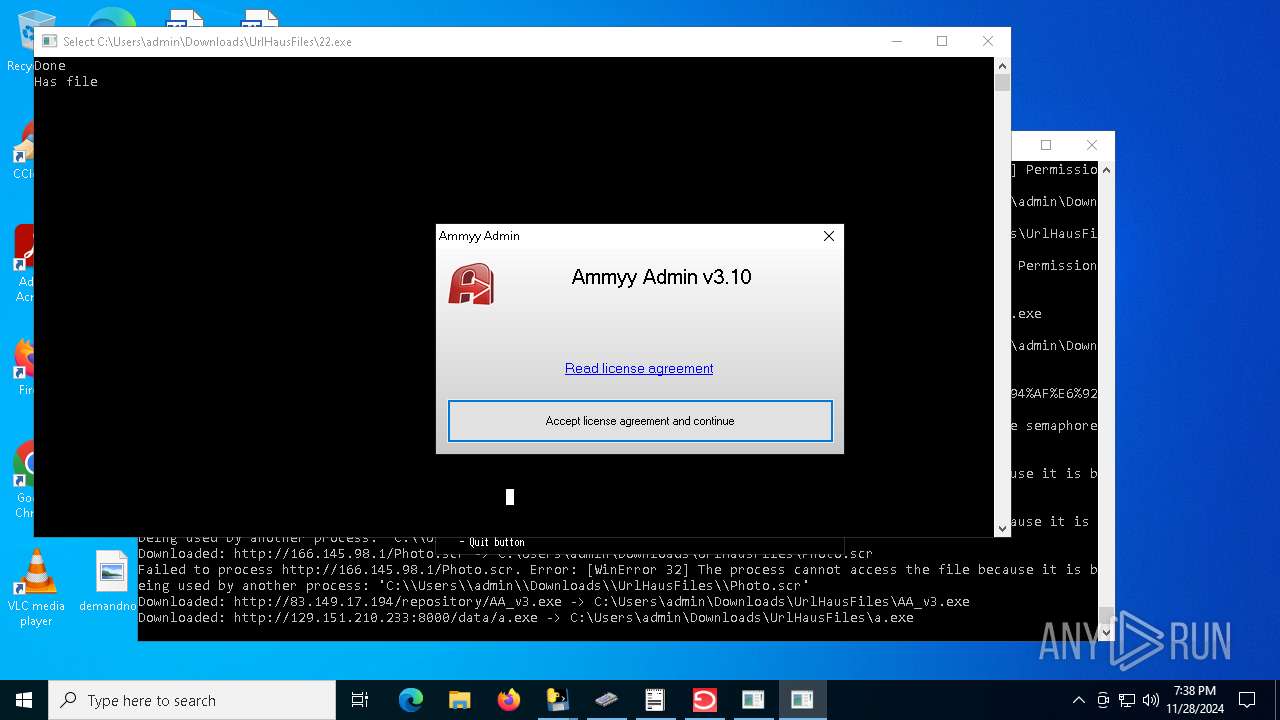
Attempting to use instant messaging service
- output.exe (PID: 7576)
- saloader.exe (PID: 7732)
Stealers network behavior
- output.exe (PID: 7576)
- saloader.exe (PID: 7732)
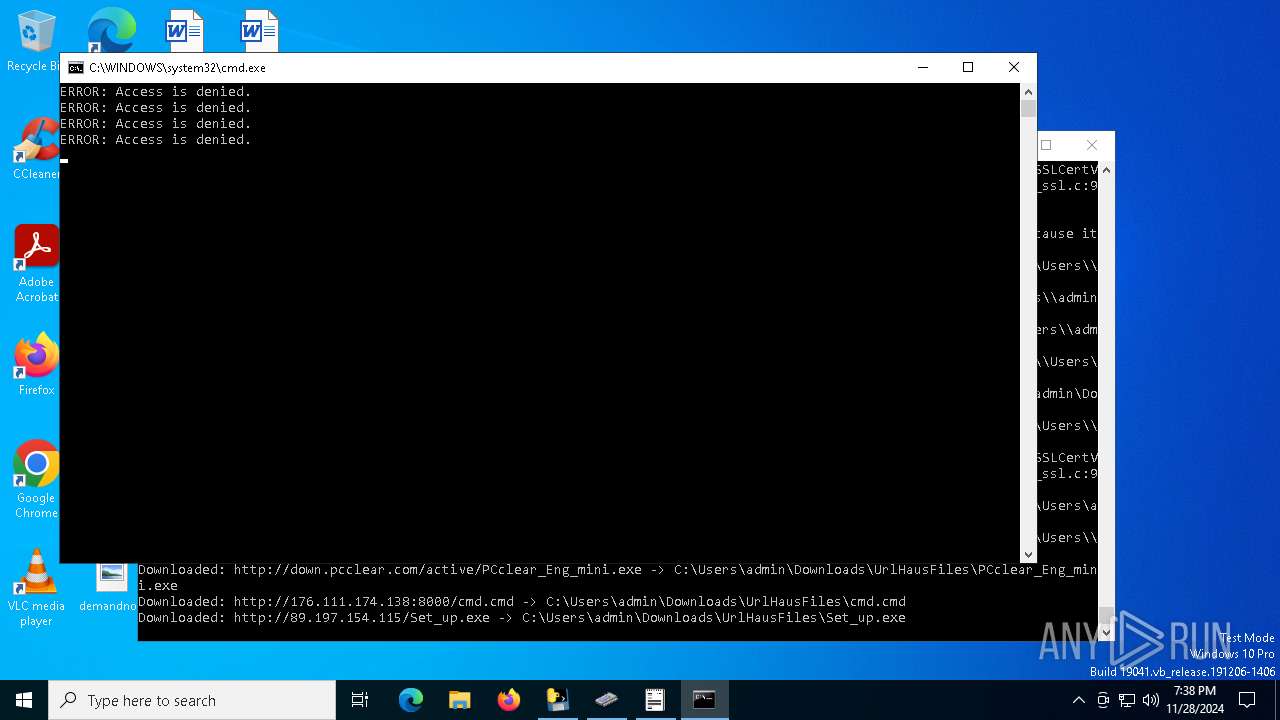
Starts CMD.EXE for self-deleting
- saloader.exe (PID: 7732)
METASPLOIT has been detected (YARA)
- Set_up.exe (PID: 7000)
NJRAT has been detected (YARA)
- svchost.exe (PID: 7208)
Executing a file with an untrusted certificate
- letgrtsC1.exe (PID: 1856)
- letgrtsC1.exe (PID: 8004)
- letgrtsC1.exe (PID: 432)
- letgrtsC1.exe (PID: 7828)
- letgrtsC1.exe (PID: 1536)
- letgrtsC1.exe (PID: 8156)
- letgrtsC1.exe (PID: 1064)
- letgrtsC1.exe (PID: 3744)
ASYNCRAT has been detected (YARA)
- Loader.exe (PID: 7308)
SUSPICIOUS
Process drops legitimate windows executable
- take3.exe (PID: 6504)
- letgrtsC1.exe (PID: 1856)
- letgrtsC1.exe (PID: 432)
- letgrtsC1.exe (PID: 8156)
- letgrtsC1.exe (PID: 7828)
Process drops python dynamic module
- take3.exe (PID: 6504)
- letgrtsC1.exe (PID: 1856)
- letgrtsC1.exe (PID: 432)
- letgrtsC1.exe (PID: 8156)
- letgrtsC1.exe (PID: 7828)
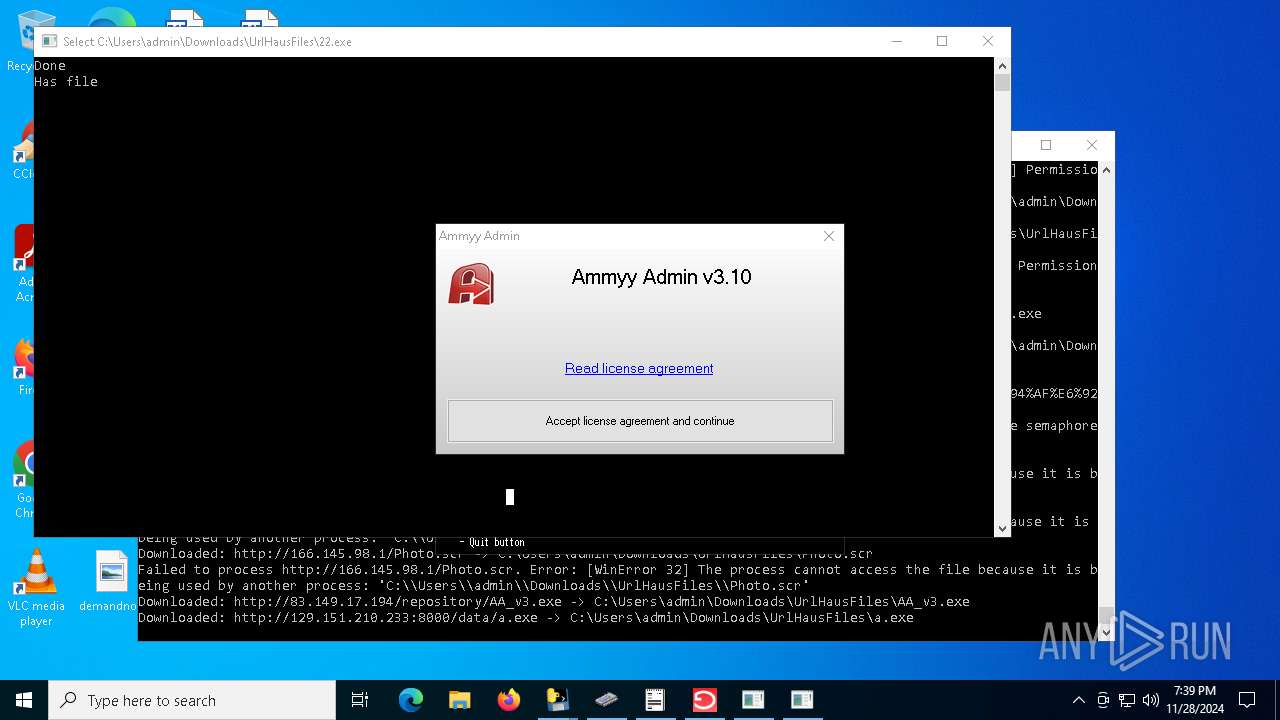
Application launched itself
- take3.exe (PID: 6504)
- uxN4wDZ.exe (PID: 7916)
- saloader.exe (PID: 7032)
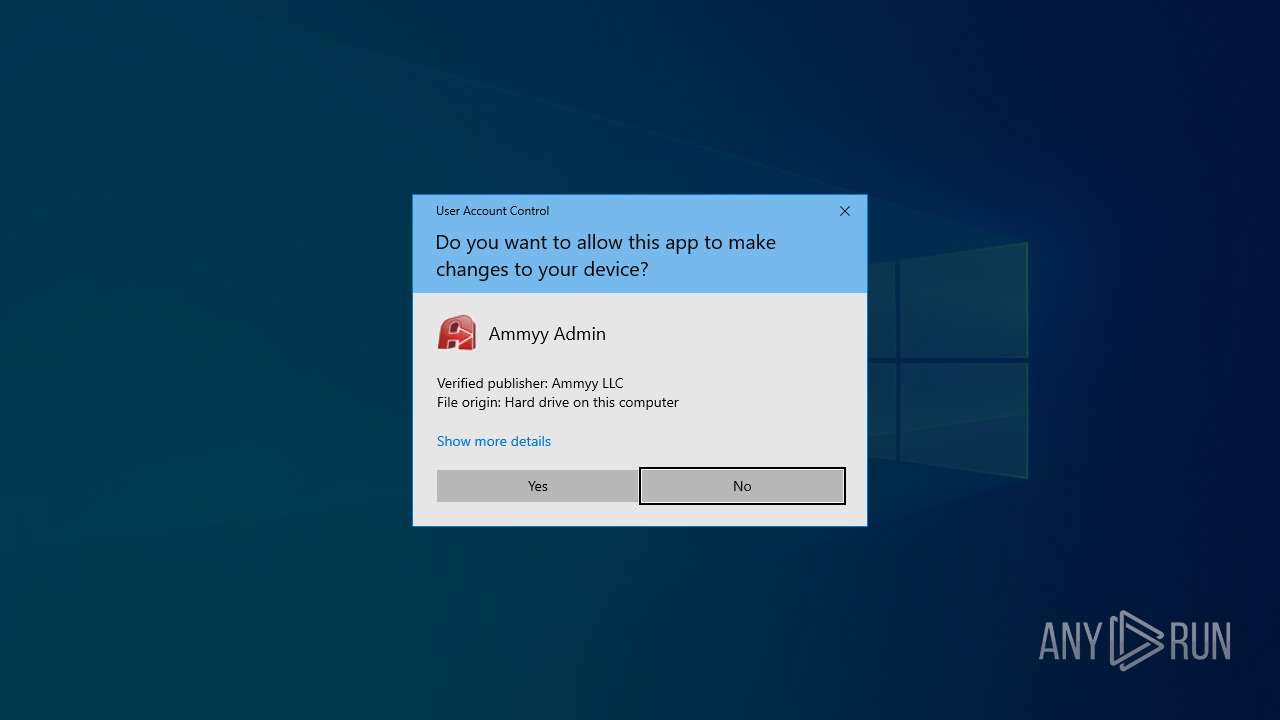
- AA_v3.exe (PID: 7812)
- AA_v3.exe (PID: 7976)
- letgrtsC1.exe (PID: 1856)
- letgrtsC1.exe (PID: 432)
- letgrtsC1.exe (PID: 8156)
- letgrtsC1.exe (PID: 7828)
The process drops C-runtime libraries
- take3.exe (PID: 6504)
- letgrtsC1.exe (PID: 1856)
- letgrtsC1.exe (PID: 432)
- letgrtsC1.exe (PID: 8156)
- letgrtsC1.exe (PID: 7828)
Loads Python modules
- take3.exe (PID: 6584)
- letgrtsC1.exe (PID: 1536)
- letgrtsC1.exe (PID: 1064)
- letgrtsC1.exe (PID: 8004)
- letgrtsC1.exe (PID: 3744)
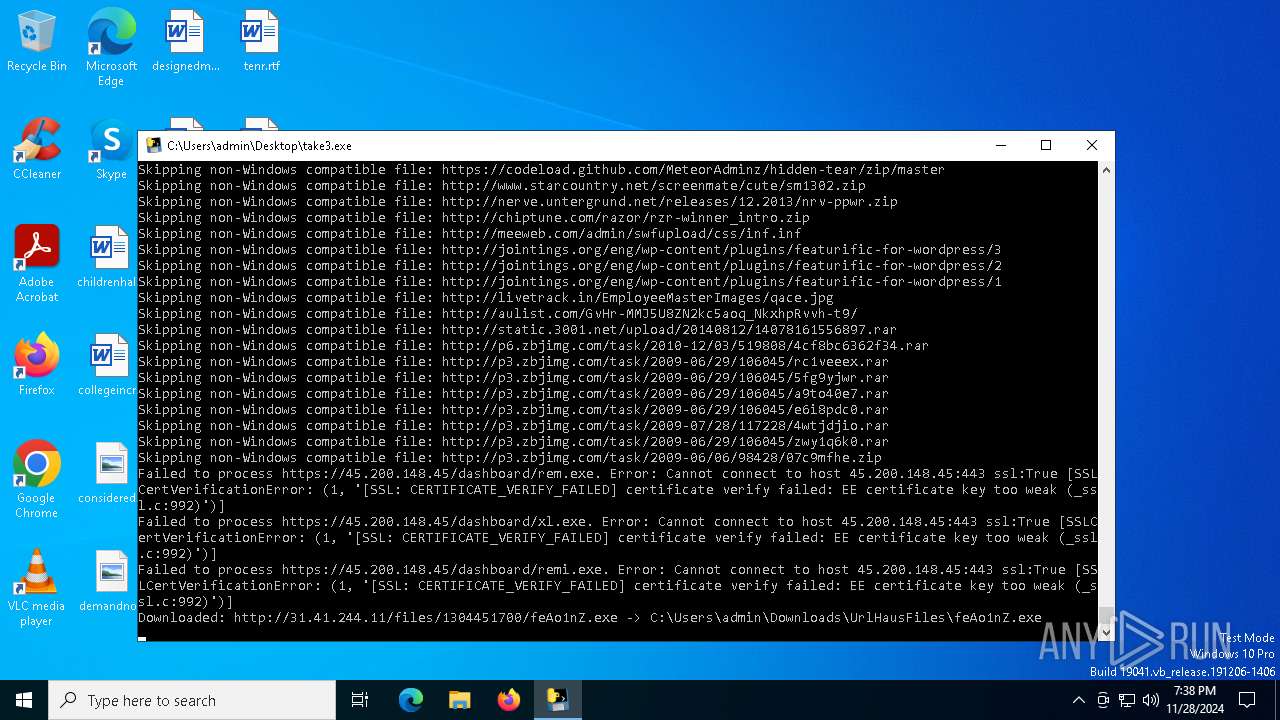
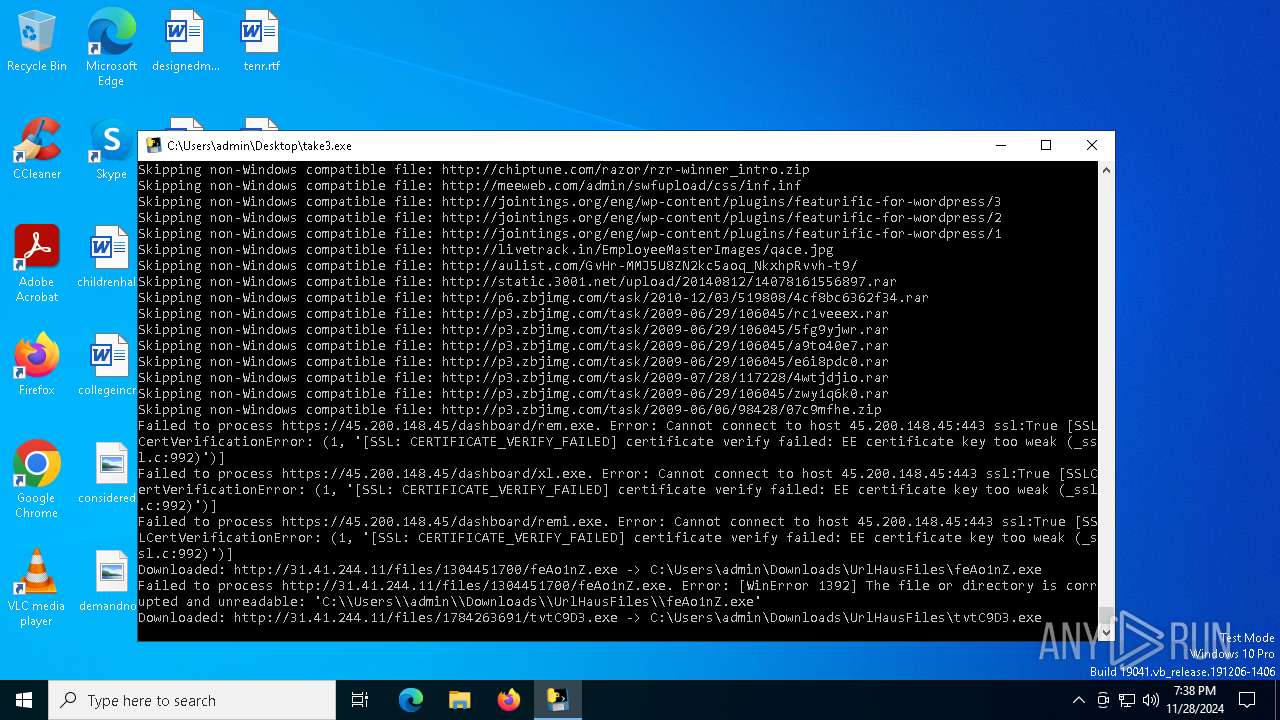
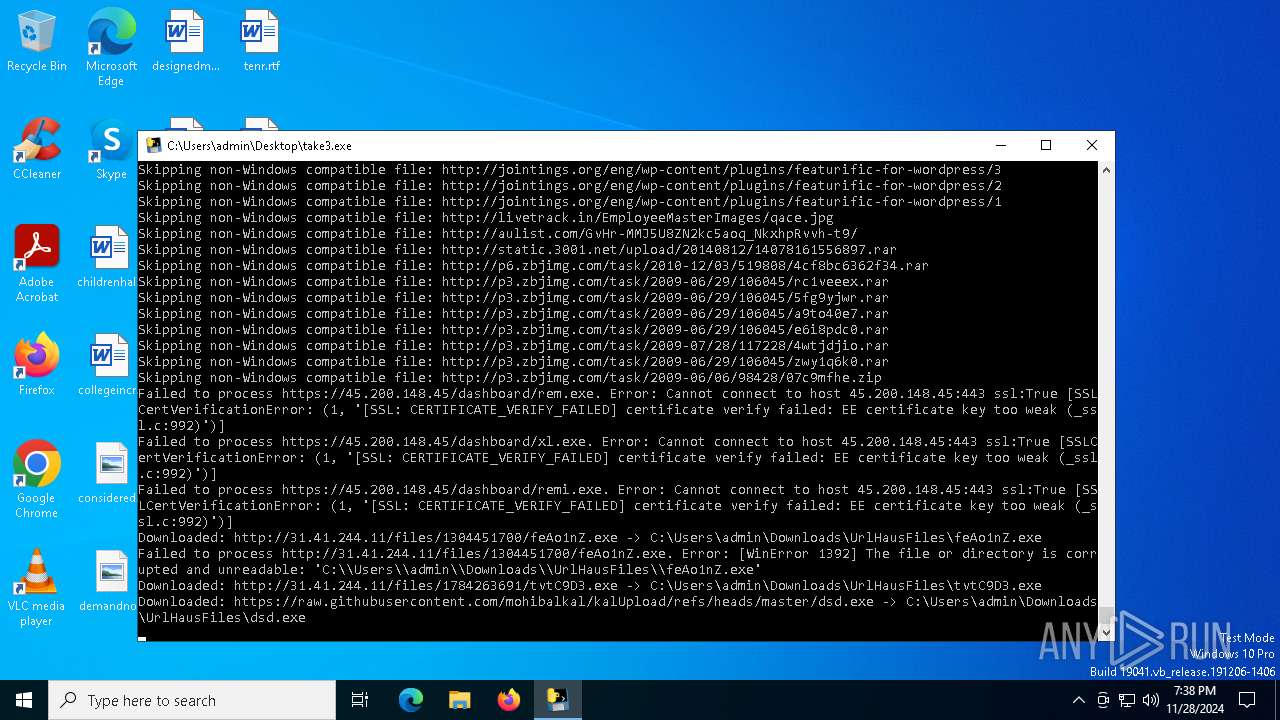
Executable content was dropped or overwritten
- take3.exe (PID: 6504)
- take3.exe (PID: 6584)
- tvtC9D3.exe (PID: 6944)
- dsd.exe (PID: 5592)
- aidans.dont.run.exe (PID: 7512)
- svchost.exe (PID: 7124)
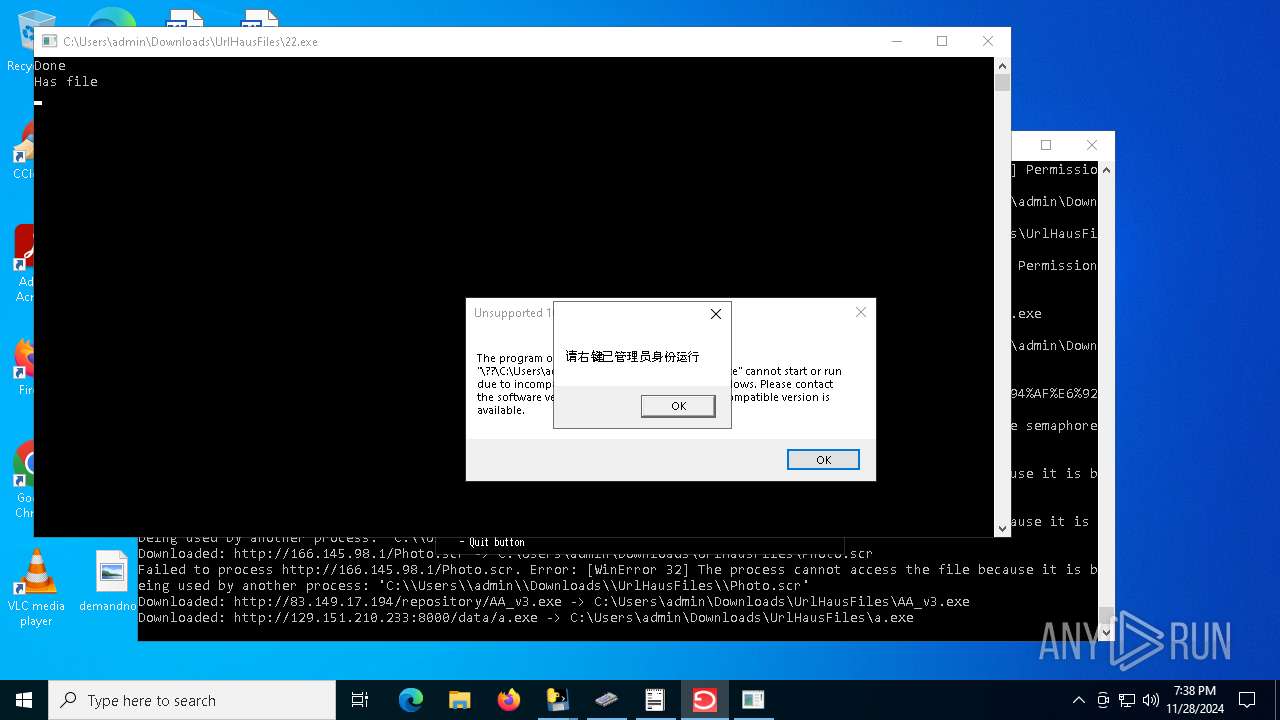
- 22.exe (PID: 7916)
- saloader.exe (PID: 7732)
- letgrtsC1.exe (PID: 1856)
- letgrtsC1.exe (PID: 8156)
- letgrtsC1.exe (PID: 432)
- letgrtsC1.exe (PID: 7828)
Connects to unusual port
- take3.exe (PID: 6584)
- Loader.exe (PID: 7308)
- Set_up.exe (PID: 7000)
- 22.exe (PID: 7916)
- windows.exe (PID: 7556)
- svchost.exe (PID: 7208)
- RegAsm.exe (PID: 4628)
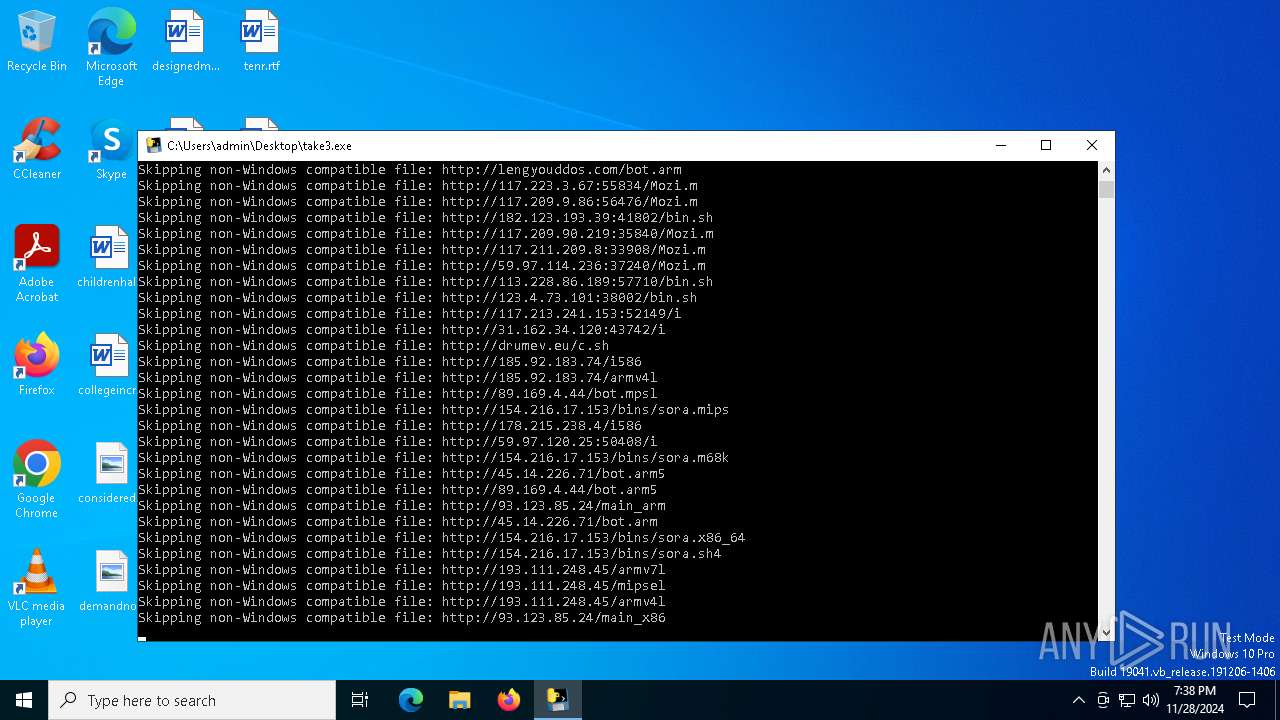
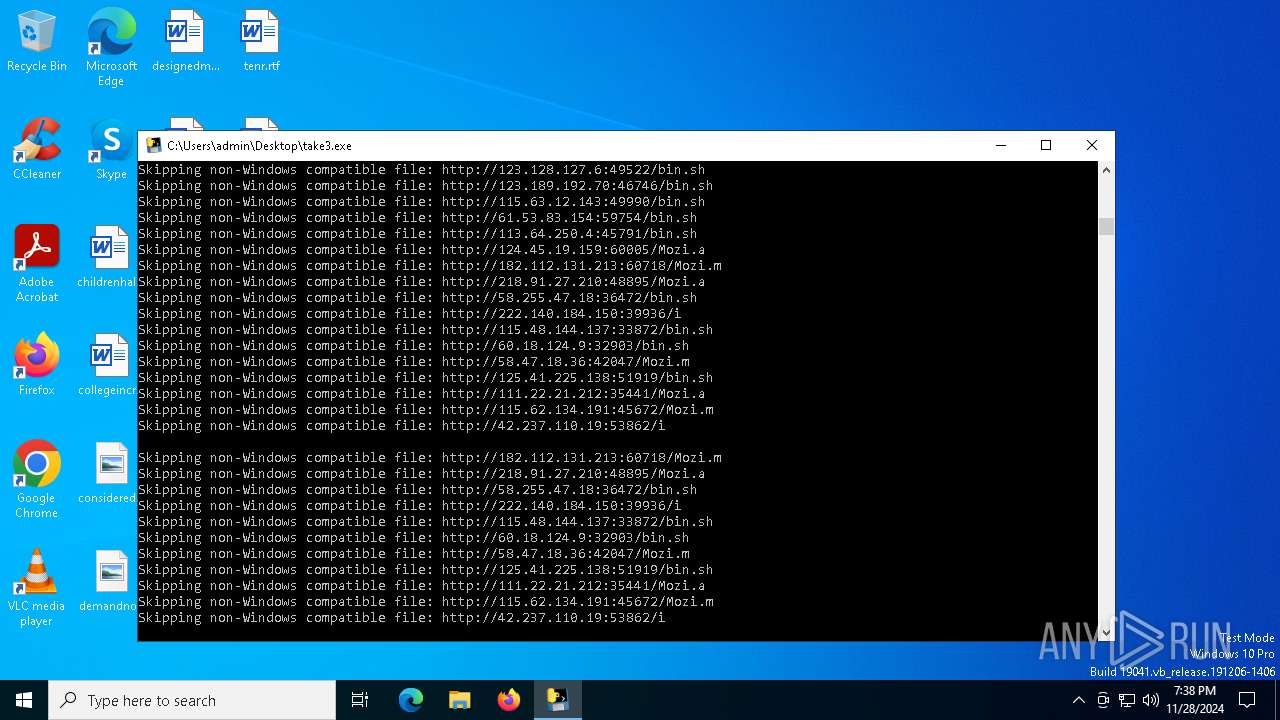
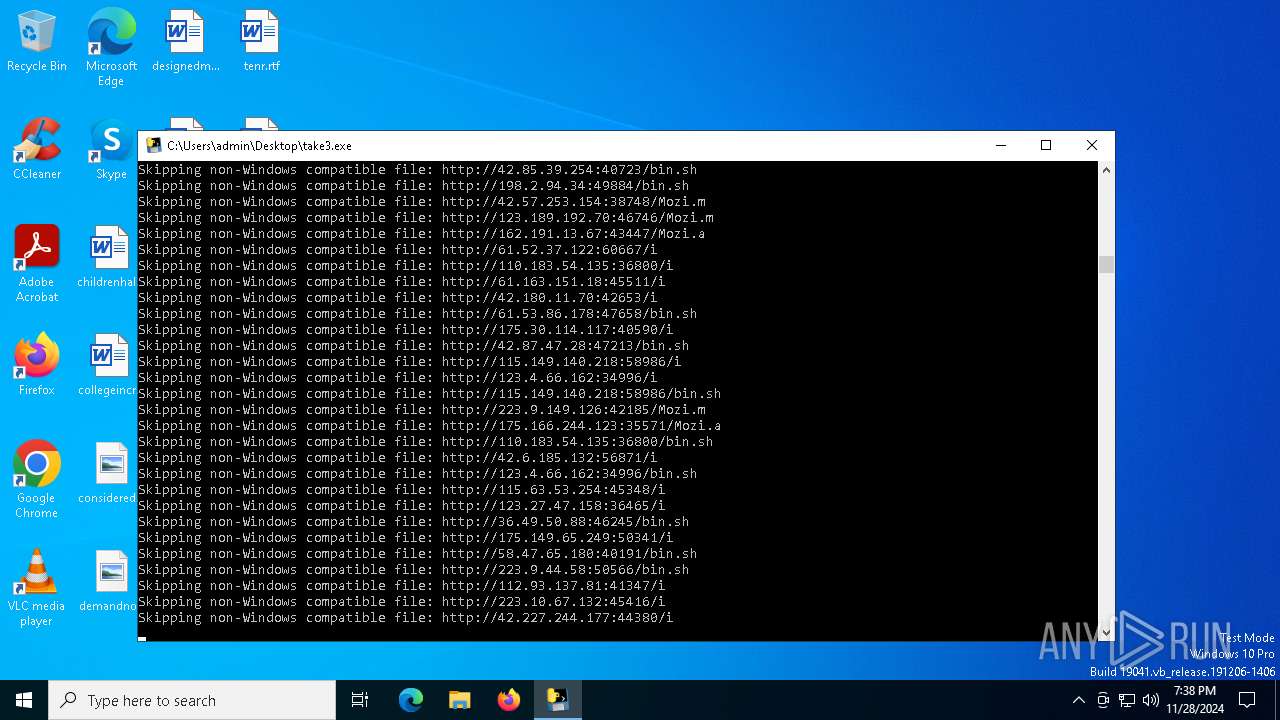
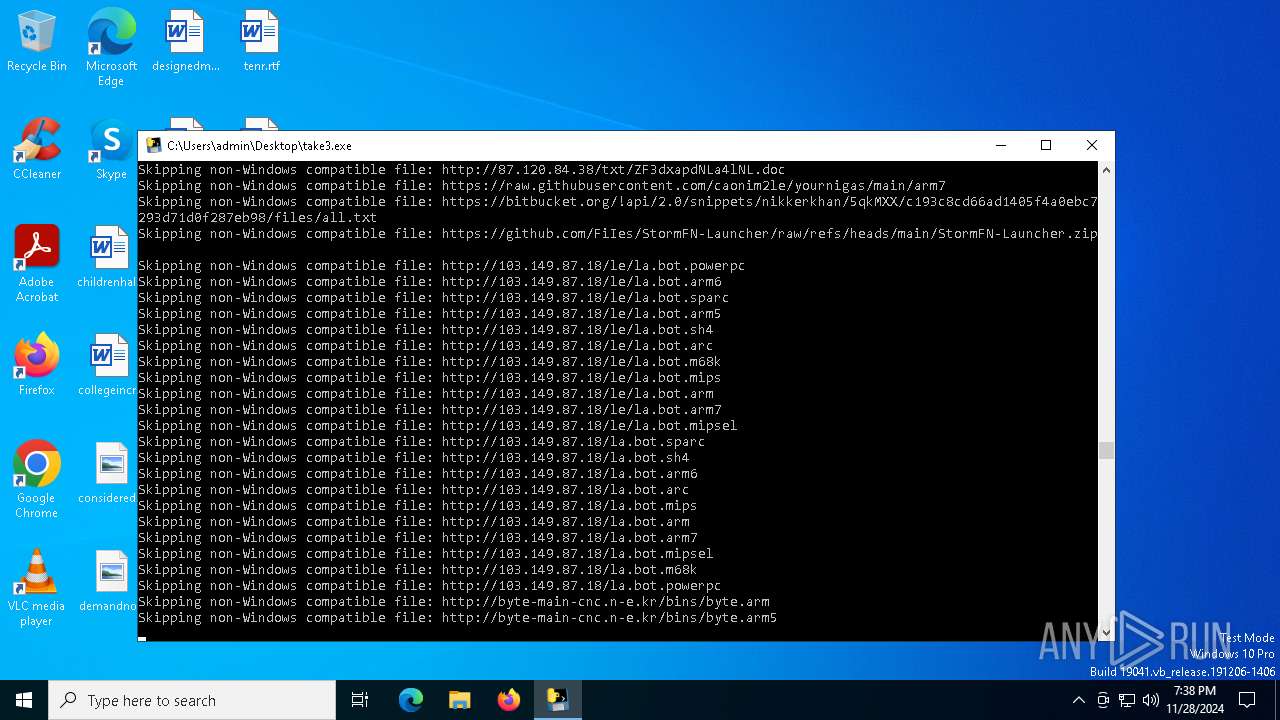
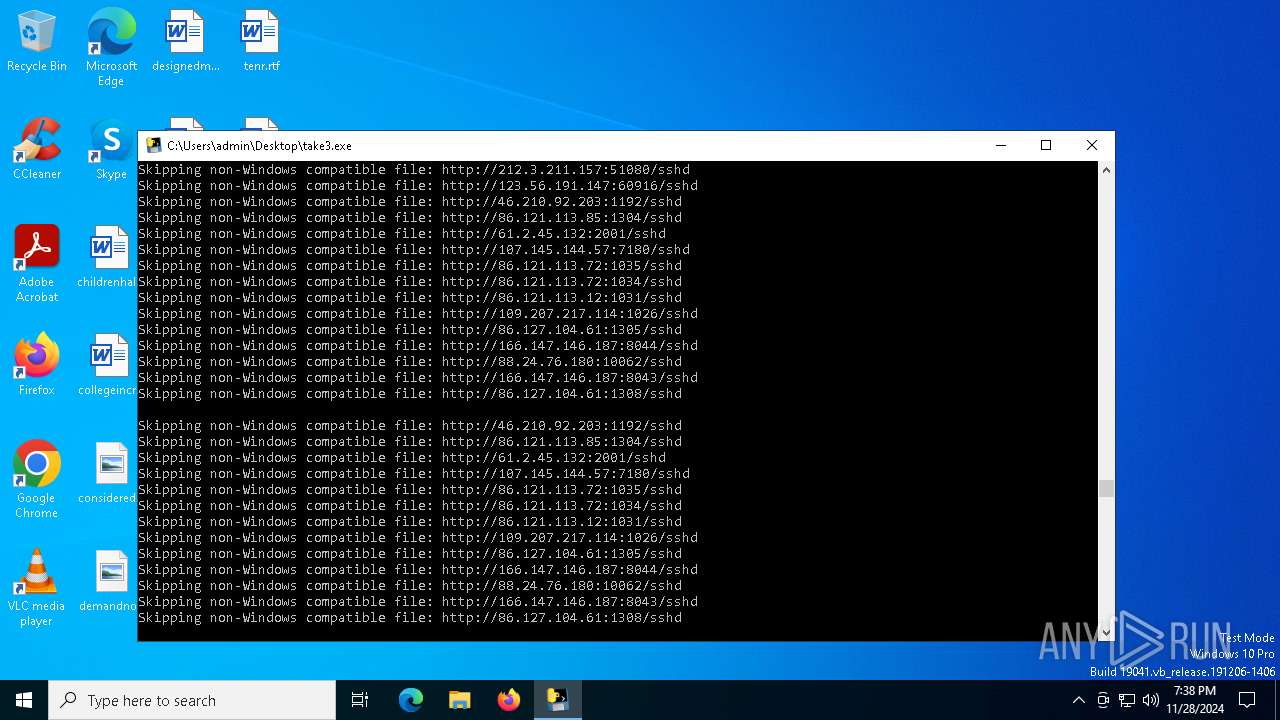
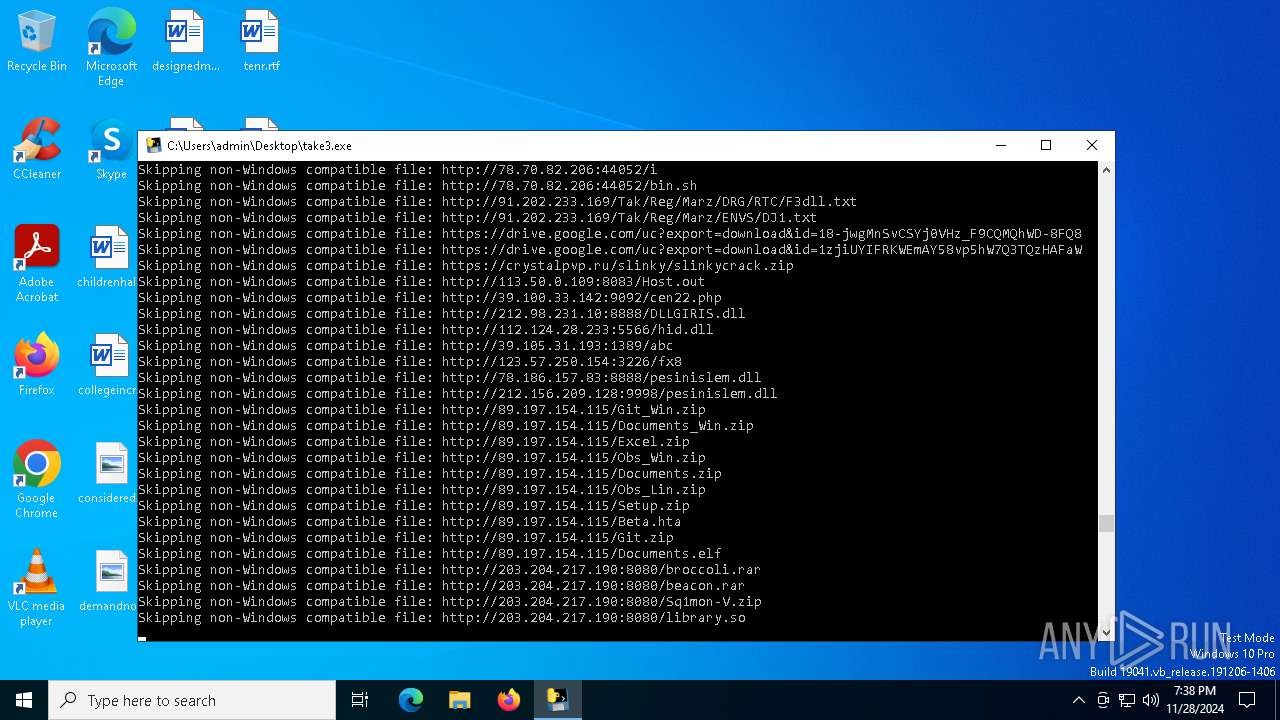
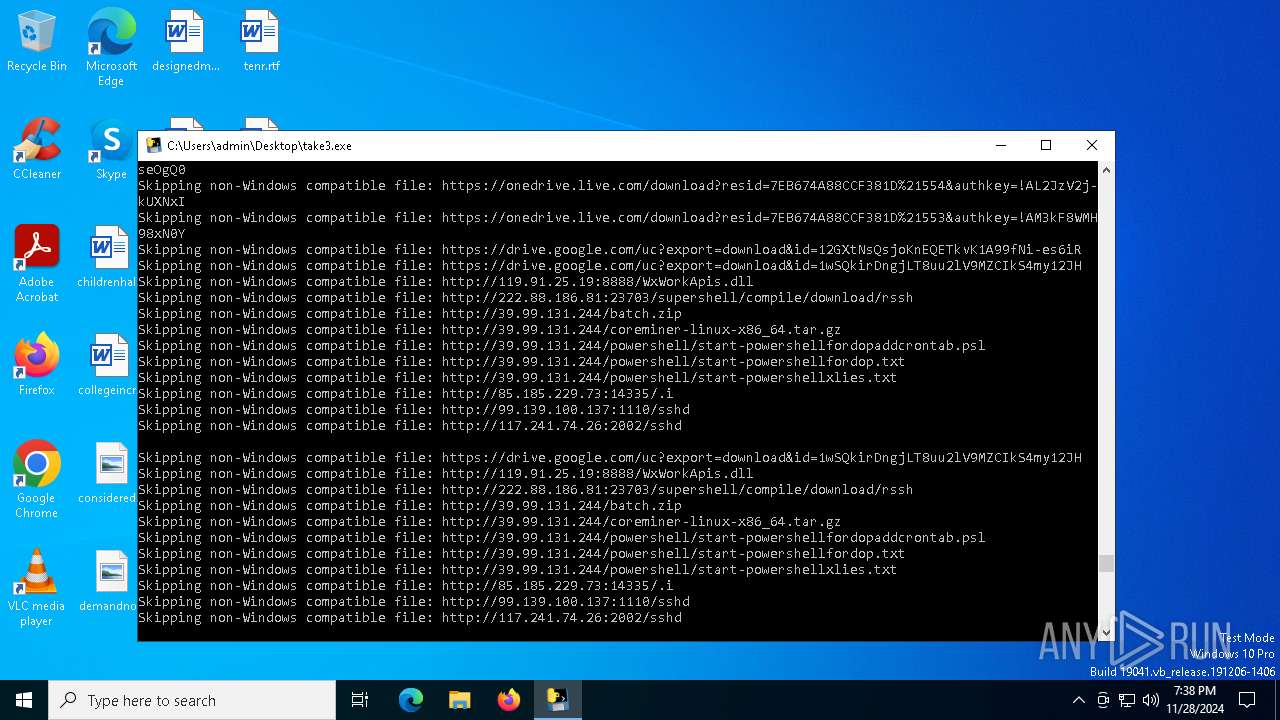
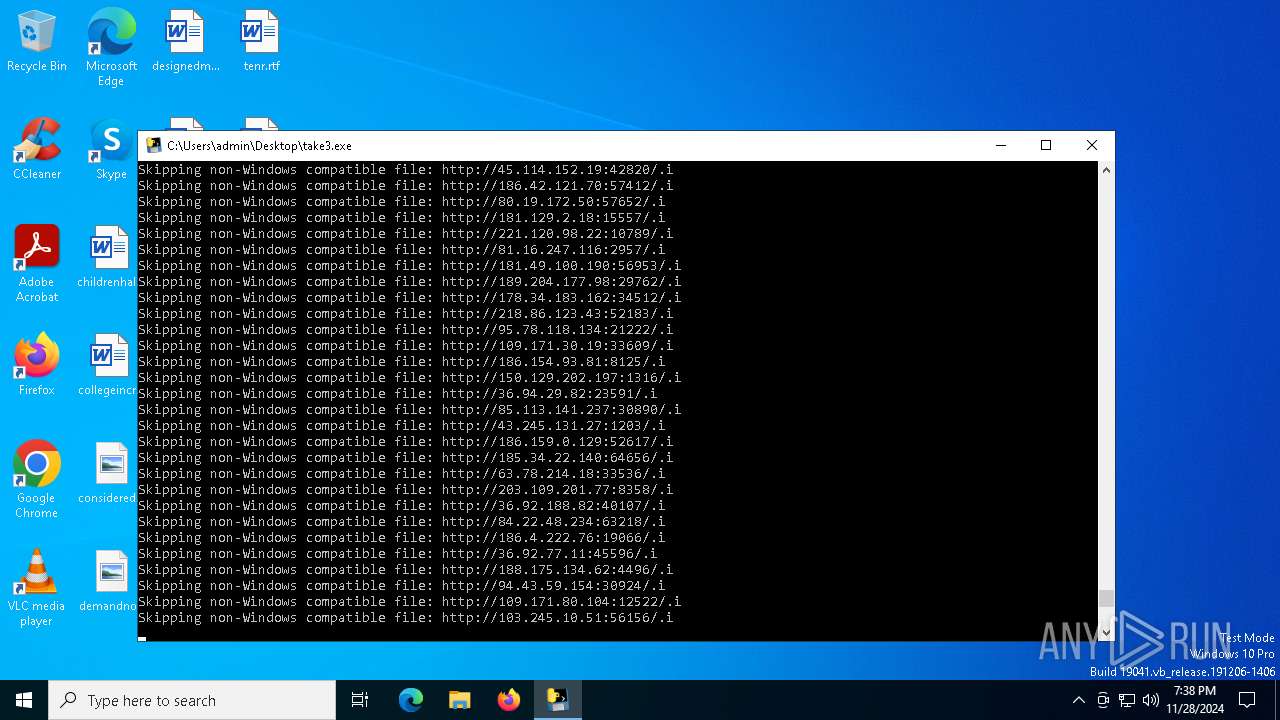
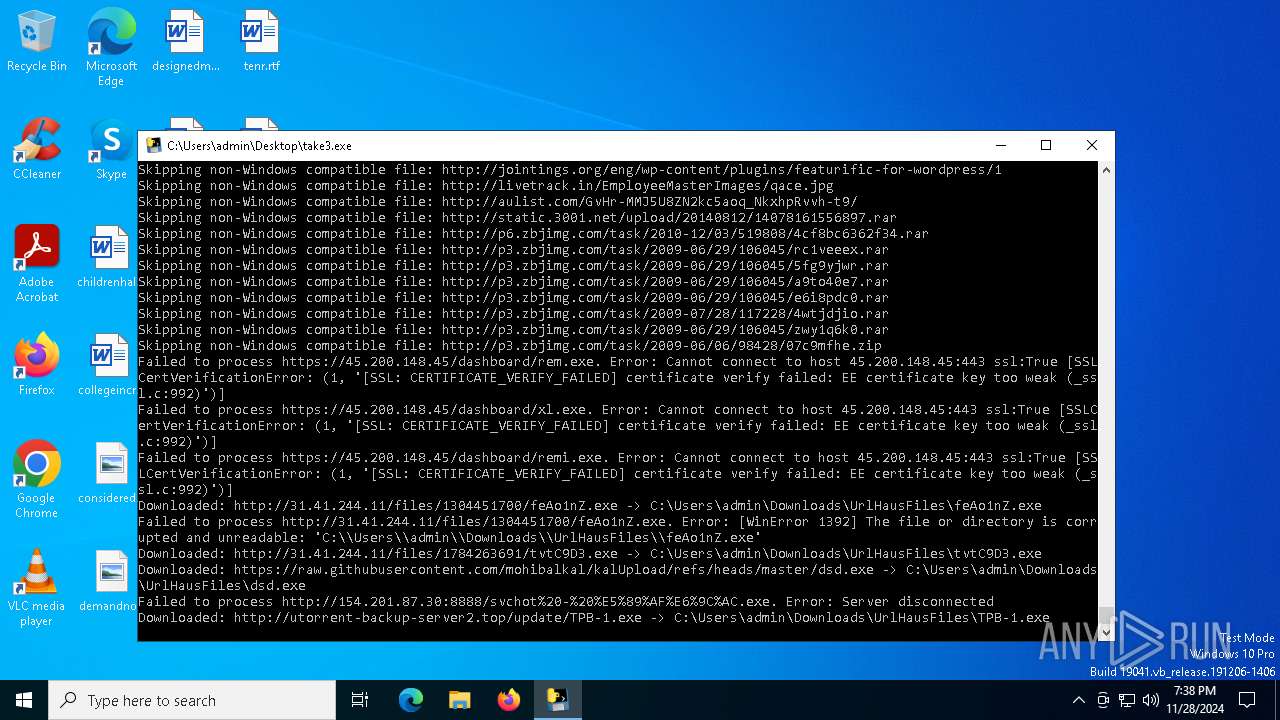
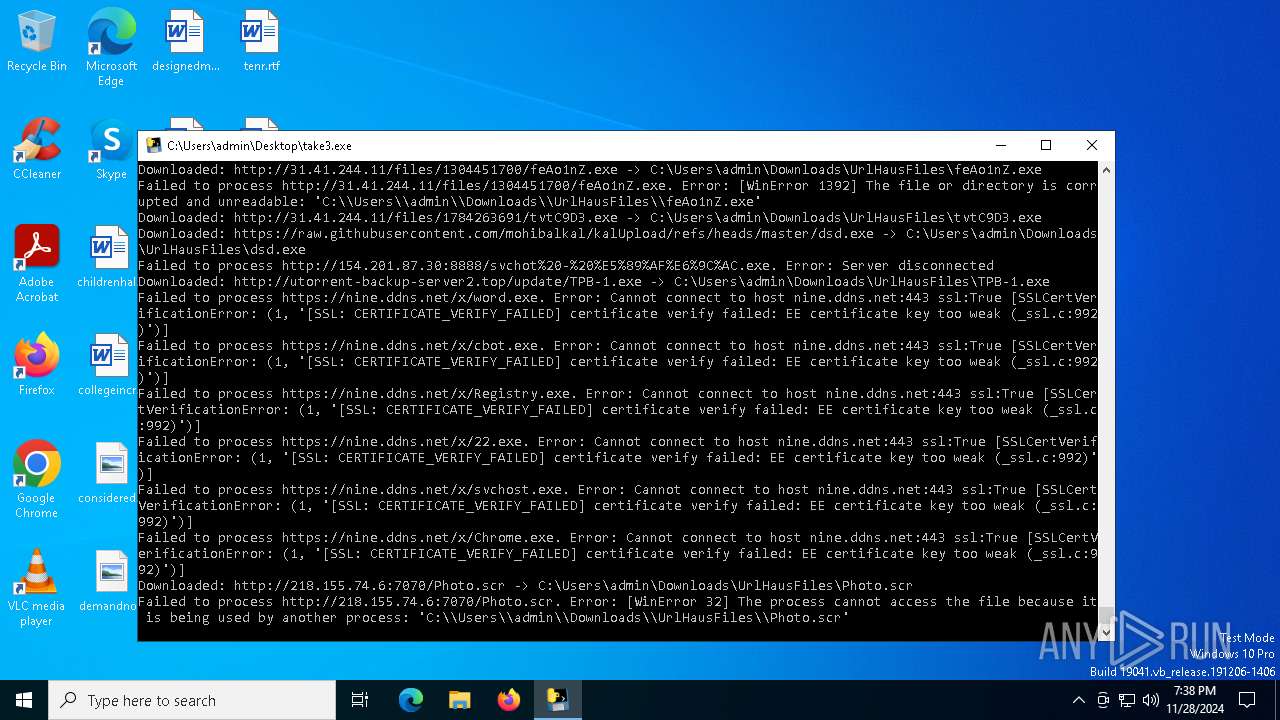
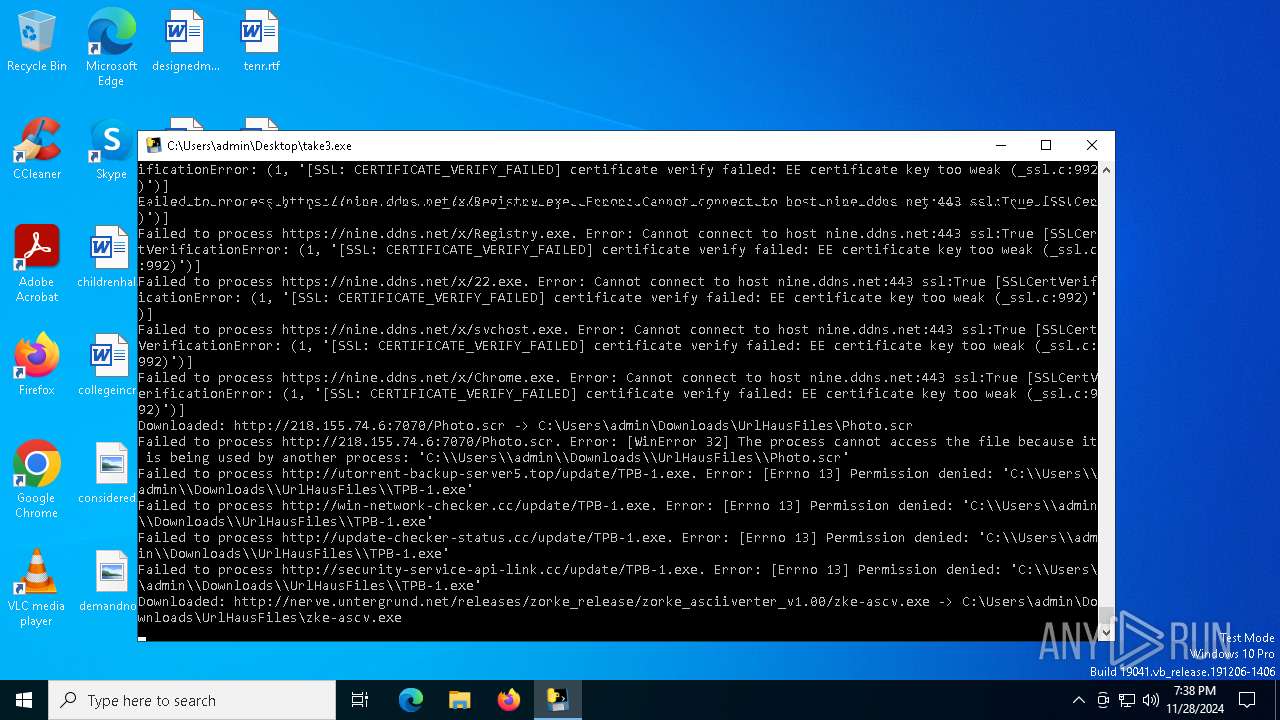
Process requests binary or script from the Internet
- take3.exe (PID: 6584)
- svchost.exe (PID: 7124)
Connects to the server without a host name
- take3.exe (PID: 6584)
- svchost.exe (PID: 7124)
Runs PING.EXE to delay simulation
- tvtC9D3.exe (PID: 6944)
Block-list domains
- take3.exe (PID: 6584)
Contacting a server suspected of hosting an CnC
- svchost.exe (PID: 2192)
- uxN4wDZ.exe (PID: 8000)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- TPB-1.exe (PID: 3988)
Potential Corporate Privacy Violation
- svchost.exe (PID: 7124)
- take3.exe (PID: 6584)
Starts CMD.EXE for commands execution
- take3.exe (PID: 6584)
- aidans.dont.run.exe (PID: 7512)
- saloader.exe (PID: 7732)
- TPB-1.exe (PID: 3988)
- RegAsm.exe (PID: 4628)
Executing commands from ".cmd" file
- take3.exe (PID: 6584)
Starts itself from another location
- dsd.exe (PID: 5592)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 6500)
Executing commands from a ".bat" file
- aidans.dont.run.exe (PID: 7512)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 7776)
- cmd.exe (PID: 7920)
The executable file from the user directory is run by the CMD process
- windows.exe (PID: 7556)
Uses NETSH.EXE to add a firewall rule or allowed programs
- svchost.exe (PID: 7208)
Starts POWERSHELL.EXE for commands execution
- saloader.exe (PID: 7732)
Uses ATTRIB.EXE to modify file attributes
- saloader.exe (PID: 7732)
Script adds exclusion path to Windows Defender
- saloader.exe (PID: 7732)
Script disables Windows Defender's real-time protection
- saloader.exe (PID: 7732)
Script disables Windows Defender's IPS
- saloader.exe (PID: 7732)
Executes as Windows Service
- AA_v3.exe (PID: 7976)
Uses WMIC.EXE to obtain Windows Installer data
- saloader.exe (PID: 7732)
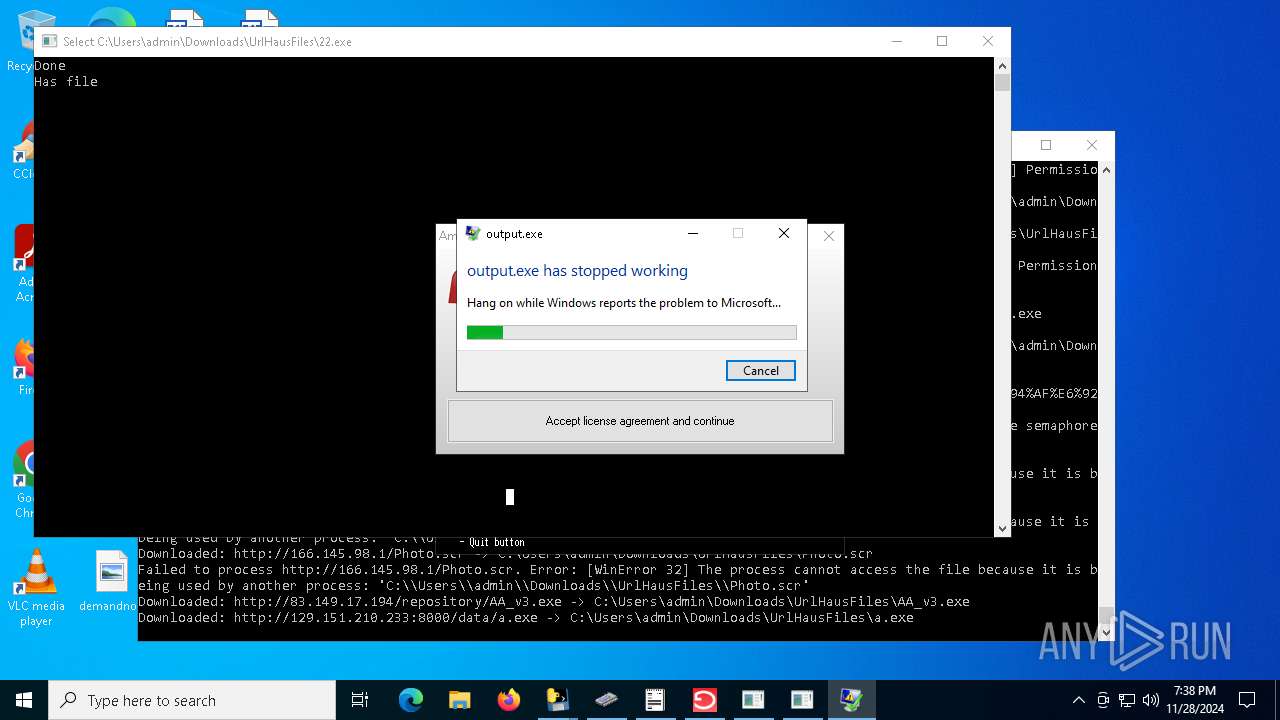
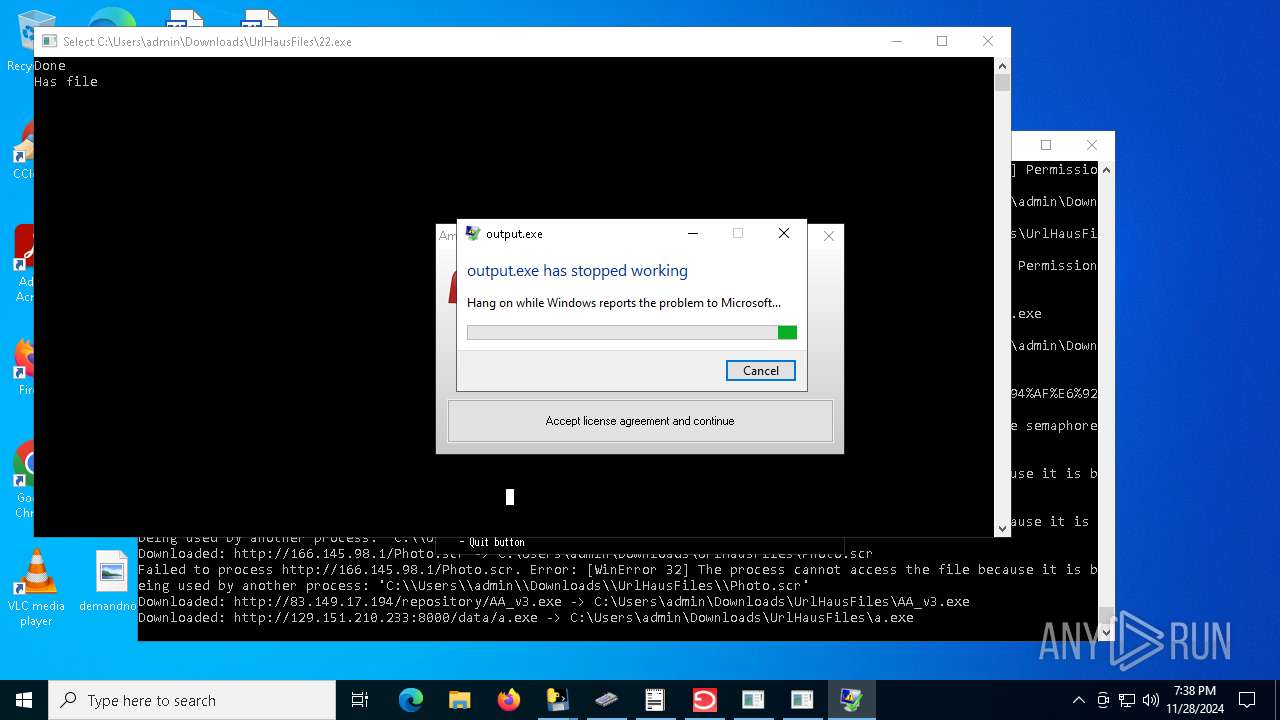
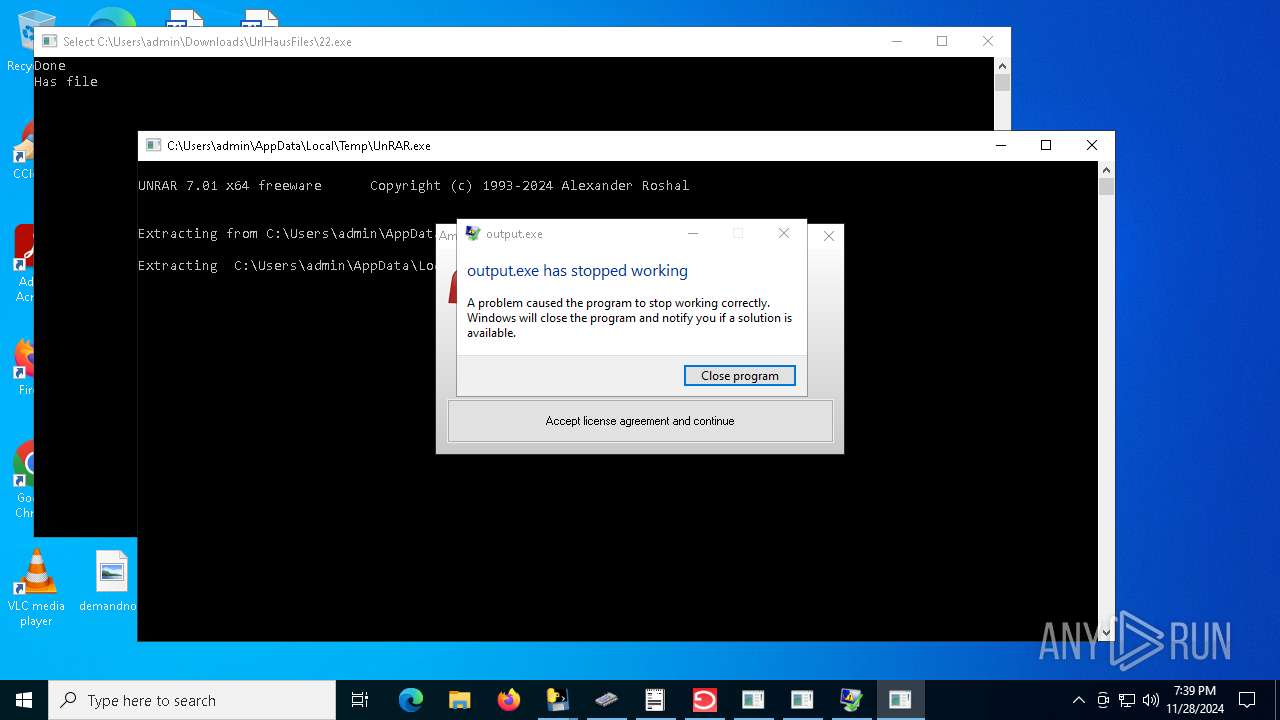
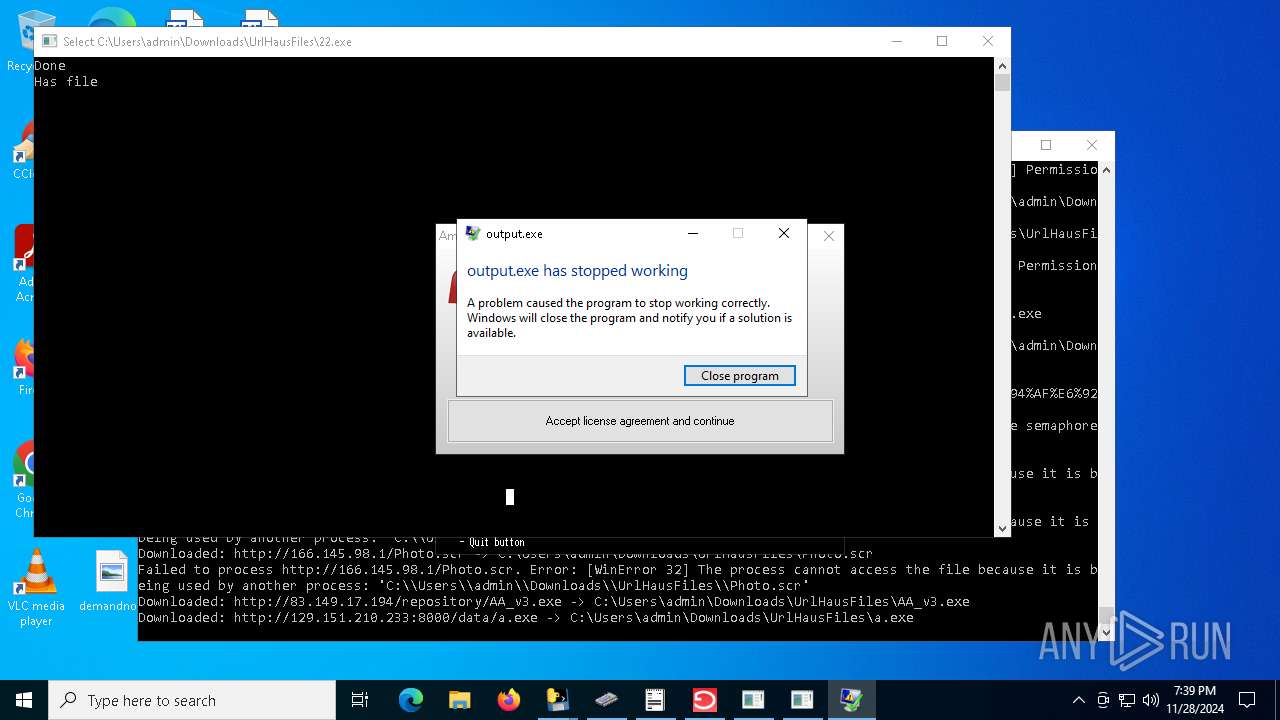
Executes application which crashes
- output.exe (PID: 7576)
Accesses operating system name via WMI (SCRIPT)
- WMIC.exe (PID: 8088)
Uses WMIC.EXE to obtain computer system information
- saloader.exe (PID: 7732)
Accesses product unique identifier via WMI (SCRIPT)
- WMIC.exe (PID: 8016)
Uses WMIC.EXE to obtain a list of video controllers
- saloader.exe (PID: 7732)
Accesses video controller name via WMI (SCRIPT)
- WMIC.exe (PID: 7196)
Checks for external IP
- svchost.exe (PID: 2192)
- output.exe (PID: 7576)
- saloader.exe (PID: 7732)
- RegAsm.exe (PID: 4628)
Uses WMIC.EXE to obtain operating system information
- saloader.exe (PID: 7732)
The process connected to a server suspected of theft
- output.exe (PID: 7576)
- saloader.exe (PID: 7732)
Loads DLL from Mozilla Firefox
- RegAsm.exe (PID: 4628)
Starts application with an unusual extension
- cmd.exe (PID: 8012)
- cmd.exe (PID: 6764)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 8012)
Uses NETSH.EXE to obtain data on the network
- cmd.exe (PID: 8012)
- cmd.exe (PID: 6764)
INFO
Reads the computer name
- take3.exe (PID: 6504)
- take3.exe (PID: 6584)
Checks supported languages
- take3.exe (PID: 6504)
- take3.exe (PID: 6584)
Checks proxy server information
- take3.exe (PID: 6584)
Create files in a temporary directory
- take3.exe (PID: 6504)
- tvtC9D3.exe (PID: 6944)
- svchost.exe (PID: 7124)
PyInstaller has been detected (YARA)
- take3.exe (PID: 6504)
- take3.exe (PID: 6584)
The process uses the downloaded file
- take3.exe (PID: 6584)
Creates files in the program directory
- TPB-1.exe (PID: 3988)
Attempting to use instant messaging service
- TPB-1.exe (PID: 3988)
- svchost.exe (PID: 2192)
- output.exe (PID: 7576)
- saloader.exe (PID: 7732)
Creates files or folders in the user directory
- TPB-1.exe (PID: 3988)
Application launched itself
- chrome.exe (PID: 1140)
- msedge.exe (PID: 8076)
- chrome.exe (PID: 1080)
- msedge.exe (PID: 3732)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 4640)
- powershell.exe (PID: 6776)
- powershell.exe (PID: 7928)
- powershell.exe (PID: 6032)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 4640)
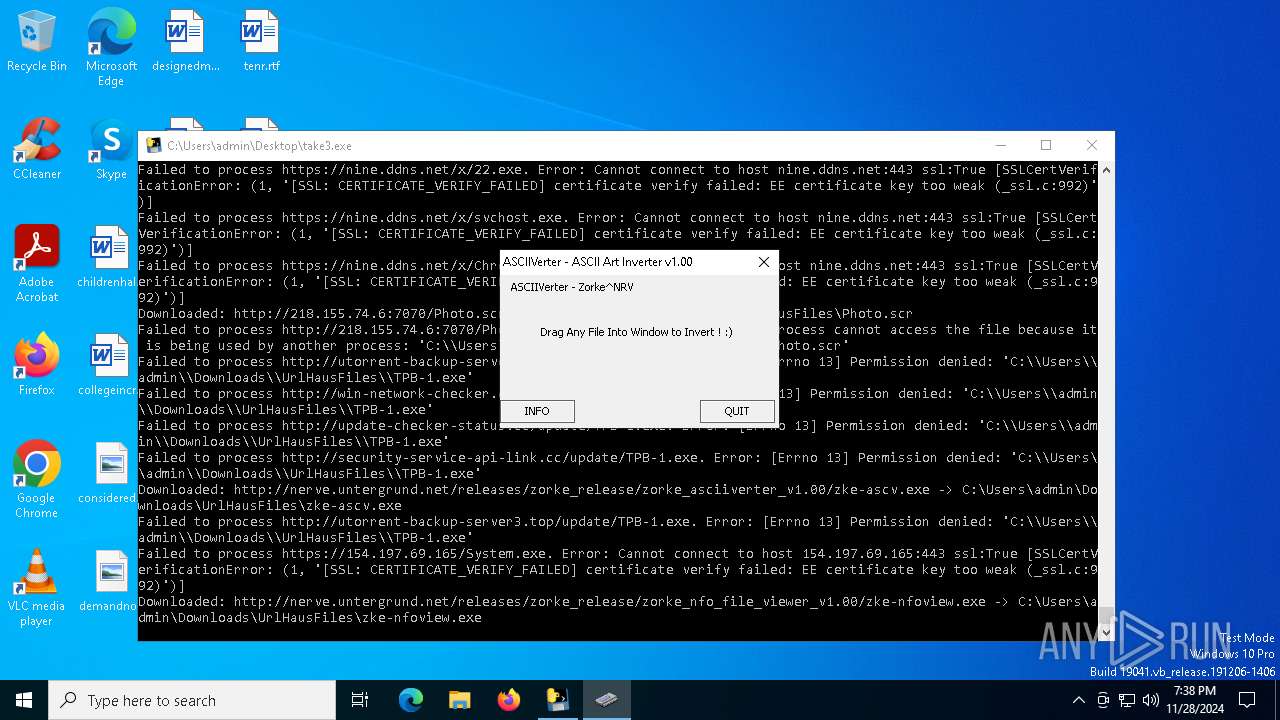
Mpress packer has been detected
- zke-ascv.exe (PID: 5256)
- zke-nfoview.exe (PID: 6404)
Sends debugging messages
- chrome.exe (PID: 1080)
- msedge.exe (PID: 3732)
Changes the display of characters in the console
- cmd.exe (PID: 8012)
- cmd.exe (PID: 6764)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2024:11:28 01:48:12+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.41 |
| CodeSize: | 176640 |
| InitializedDataSize: | 152576 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xc380 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
Total processes
268
Monitored processes
136
Malicious processes
28
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 432 | "C:\Users\admin\AppData\Local\Temp\letgrtsC1.exe" | C:\Users\admin\AppData\Local\Temp\letgrtsC1.exe | tvtC9D3.exe | ||||||||||||
User: admin Company: Apple Inc. Integrity Level: MEDIUM Description: iTunes Installer Exit code: 0 Version: 12.13.4.4 Modules
| |||||||||||||||
| 536 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 768 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --extension-process --no-appcompat-clear --remote-debugging-port=9223 --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --mojo-platform-channel-handle=3656 --field-trial-handle=1928,i,14458754527280324051,18154487367376887704,262144 --variations-seed-version /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1064 | "C:\Users\admin\AppData\Local\Temp\letgrtsC1.exe" | C:\Users\admin\AppData\Local\Temp\letgrtsC1.exe | — | letgrtsC1.exe | |||||||||||
User: admin Company: Apple Inc. Integrity Level: MEDIUM Description: iTunes Installer Exit code: 0 Version: 12.13.4.4 Modules
| |||||||||||||||
| 1080 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --user-data-dir="C:\Users\admin\AppData\Local\Google\Chrome\User Data" --remote-debugging-port=9222 --remote-allow-origins=* --headless --profile-directory="Default" | C:\Program Files\Google\Chrome\Application\chrome.exe | RegAsm.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 4294967295 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1140 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --remote-debugging-port=9223 --profile-directory="Default" | C:\Program Files\Google\Chrome\Application\chrome.exe | TPB-1.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1216 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win64 --annotation=prod=Chrome --annotation=ver=122.0.6261.70 --initial-client-data=0x224,0x228,0x22c,0x200,0x230,0x7ff82136dc40,0x7ff82136dc4c,0x7ff82136dc58 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 4294967295 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1224 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1380 | REG ADD "HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Terminal Server\WinStations\RDP-Tcp" /f /v SecurityLayer /t REG_DWORD /d "00000001" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1488 | "powershell.exe" Get-ItemPropertyValue -Path 'HKLM:System\CurrentControlSet\Control\Session Manager\Environment' -Name PROCESSOR_IDENTIFIER | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | saloader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
57 172
Read events
57 063
Write events
106
Delete events
3
Modification events
| (PID) Process: | (7124) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\BITS |
| Operation: | write | Name: | PerfMMFileName |
Value: Global\MMF_BITSa5e01612-4884-43c1-9c26-781b68e53e69 | |||
| (PID) Process: | (3988) TPB-1.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3988) TPB-1.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3988) TPB-1.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1140) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1140) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6168) PCclear_Eng_mini.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Applets\Regedit |
| Operation: | delete value | Name: | LastKey |
Value: Computer\HKEY_LOCAL_MACHINE\SOFTWARE\Adobe\Licensing | |||
| (PID) Process: | (6168) PCclear_Eng_mini.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Internet Explorer\ActiveX Compatibility\{625F76EE-DE78-428A-8B2D-96F06F3707A5} |
| Operation: | write | Name: | Compatibility Flags |
Value: 1024 | |||
| (PID) Process: | (6168) PCclear_Eng_mini.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\intmedia\activex_Eng |
| Operation: | write | Name: | activex_pid |
Value: | |||
| (PID) Process: | (1140) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
Executable files
122
Suspicious files
155
Text files
176
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6504 | take3.exe | C:\Users\admin\AppData\Local\Temp\_MEI65042\VCRUNTIME140.dll | executable | |
MD5:F12681A472B9DD04A812E16096514974 | SHA256:D66C3B47091CEB3F8D3CC165A43D285AE919211A0C0FCB74491EE574D8D464F8 | |||
| 6504 | take3.exe | C:\Users\admin\AppData\Local\Temp\_MEI65042\_decimal.pyd | executable | |
MD5:D47E6ACF09EAD5774D5B471AB3AB96FF | SHA256:D0DF57988A74ACD50B2D261E8B5F2C25DA7B940EC2AAFBEE444C277552421E6E | |||
| 6504 | take3.exe | C:\Users\admin\AppData\Local\Temp\_MEI65042\_lzma.pyd | executable | |
MD5:337B0E65A856568778E25660F77BC80A | SHA256:613DE58E4A9A80EFF8F8BC45C350A6EAEBF89F85FFD2D7E3B0B266BF0888A60A | |||
| 6504 | take3.exe | C:\Users\admin\AppData\Local\Temp\_MEI65042\_asyncio.pyd | executable | |
MD5:2859C39887921DAD2FF41FEDA44FE174 | SHA256:AEBC378DB08617EA81A0A3A3BC044BCC7E6303E314630392DD51BAB12F879BD9 | |||
| 6504 | take3.exe | C:\Users\admin\AppData\Local\Temp\_MEI65042\_overlapped.pyd | executable | |
MD5:01AD7CA8BC27F92355FD2895FC474157 | SHA256:A083E83F609ED7A2FC18A95D44D8F91C9DC74842F33E19E91988E84DB94C3B5B | |||
| 6504 | take3.exe | C:\Users\admin\AppData\Local\Temp\_MEI65042\_cffi_backend.cp311-win_amd64.pyd | executable | |
MD5:739D352BD982ED3957D376A9237C9248 | SHA256:9AEE90CF7980C8FF694BB3FFE06C71F87EB6A613033F73E3174A732648D39980 | |||
| 6504 | take3.exe | C:\Users\admin\AppData\Local\Temp\_MEI65042\_ctypes.pyd | executable | |
MD5:6A9CA97C039D9BBB7ABF40B53C851198 | SHA256:E662D2B35BB48C5F3432BDE79C0D20313238AF800968BA0FAA6EA7E7E5EF4535 | |||
| 6504 | take3.exe | C:\Users\admin\AppData\Local\Temp\_MEI65042\_bz2.pyd | executable | |
MD5:4101128E19134A4733028CFAAFC2F3BB | SHA256:5843872D5E2B08F138A71FE9BA94813AFEE59C8B48166D4A8EB0F606107A7E80 | |||
| 6504 | take3.exe | C:\Users\admin\AppData\Local\Temp\_MEI65042\_brotli.cp311-win_amd64.pyd | executable | |
MD5:D9FC15CAF72E5D7F9A09B675E309F71D | SHA256:1FCD75B03673904D9471EC03C0EF26978D25135A2026020E679174BDEF976DCF | |||
| 6504 | take3.exe | C:\Users\admin\AppData\Local\Temp\_MEI65042\_uuid.pyd | executable | |
MD5:9A4957BDC2A783ED4BA681CBA2C99C5C | SHA256:F7F57807C15C21C5AA9818EDF3993D0B94AEF8AF5808E1AD86A98637FC499D44 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
203
TCP/UDP connections
389
DNS requests
122
Threats
529
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.21.20.133:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
6584 | take3.exe | GET | 301 | 140.82.121.4:80 | http://github.com/VIPEK1990/napewnonievoiderhook/raw/main/seksiak.exe | US | — | — | shared |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
6584 | take3.exe | GET | 301 | 140.82.121.4:80 | http://github.com/realmastercoder69/bothg/releases/download/das/start.exe | US | — | — | shared |
6584 | take3.exe | GET | — | 109.137.108.215:8083 | http://109.137.108.215:8083/Photo.scr | BE | — | — | unknown |
6584 | take3.exe | GET | — | 109.210.138.197:80 | http://109.210.138.197/Photo.scr | FR | — | — | unknown |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | US | binary | 314 b | whitelisted |
6584 | take3.exe | GET | — | 80.15.103.89:80 | http://80.15.103.89/Photo.scr | FR | — | — | unknown |
6584 | take3.exe | GET | — | 31.41.244.11:80 | http://31.41.244.11/files/5824956135/TcMBq5M.exe | RU | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6072 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 2.21.20.133:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5064 | SearchApp.exe | 104.126.37.131:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1176 | svchost.exe | 20.190.159.71:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
urlhaus.abuse.ch |
| whitelisted |
nine.ddns.net |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.ddns .net |
2192 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
2192 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
2192 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
2192 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
6584 | take3.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
6584 | take3.exe | Potentially Bad Traffic | ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response |
6584 | take3.exe | Misc activity | ET HUNTING HTTP request for resource ending in .scr |
6584 | take3.exe | A Network Trojan was detected | ET MALWARE Possible Windows executable sent when remote host claims to send a Text File |
6584 | take3.exe | Misc activity | ET HUNTING HTTP request for resource ending in .scr |
86 ETPRO signatures available at the full report
Process | Message |
|---|---|
chrome.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Google\Chrome\User Data directory exists )
|
chrome.exe | [1128/194018.678:ERROR:network_service_instance_impl.cc(599)] Network service crashed, restarting service.
|
msedge.exe | [1128/194032.815:ERROR:gpu_process_host.cc(1030)] GPU process exited unexpectedly: exit_code=-1
|
msedge.exe | [1128/194032.816:WARNING:gpu_process_host.cc(1420)] The GPU process has crashed 1 time(s)
|
msedge.exe | [1128/194032.824:ERROR:network_service_instance_impl.cc(614)] Network service crashed, restarting service.
|
msedge.exe | [1128/194032.926:WARNING:gpu_process_host.cc(1052)] Reinitialized the GPU process after a crash. The reported initialization time was 36 ms
|