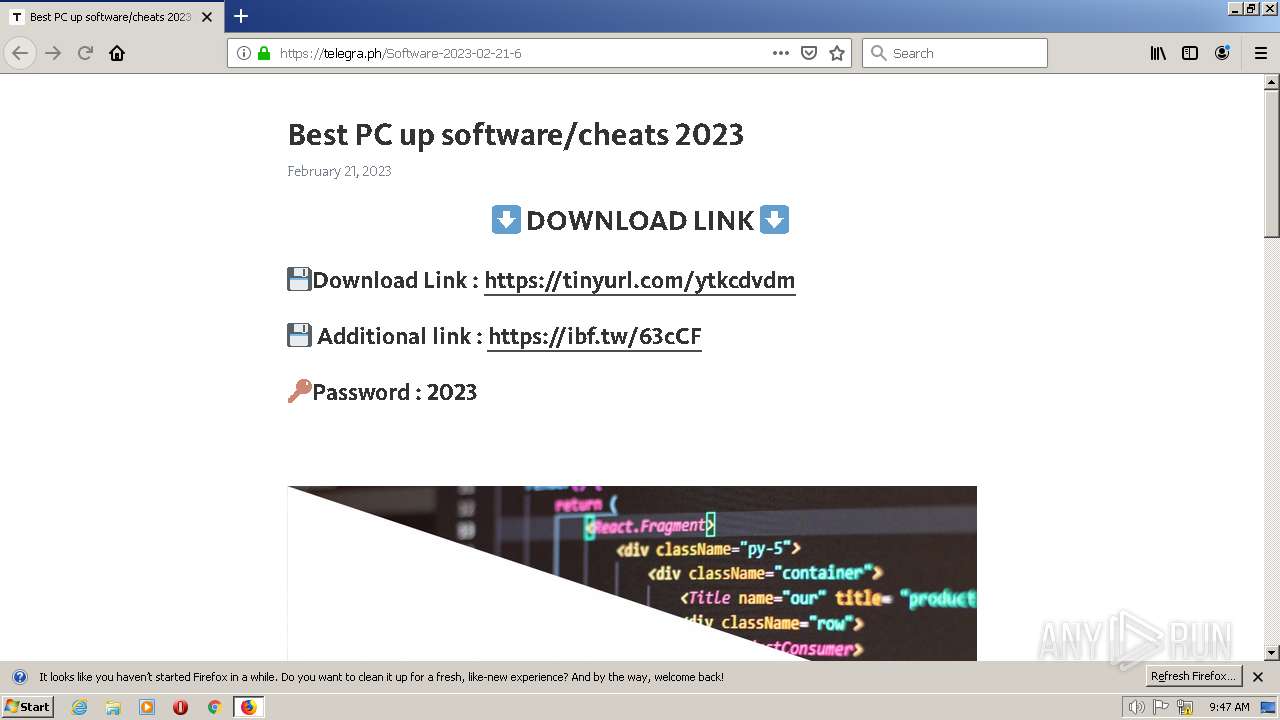
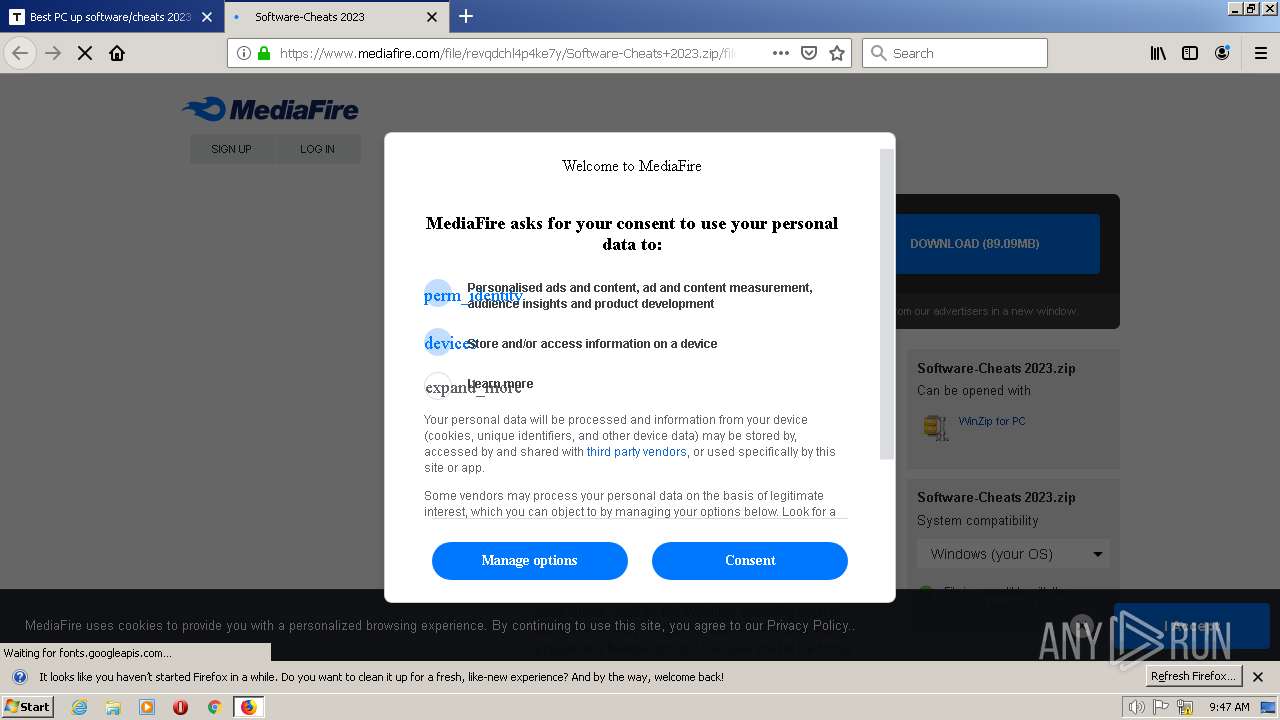
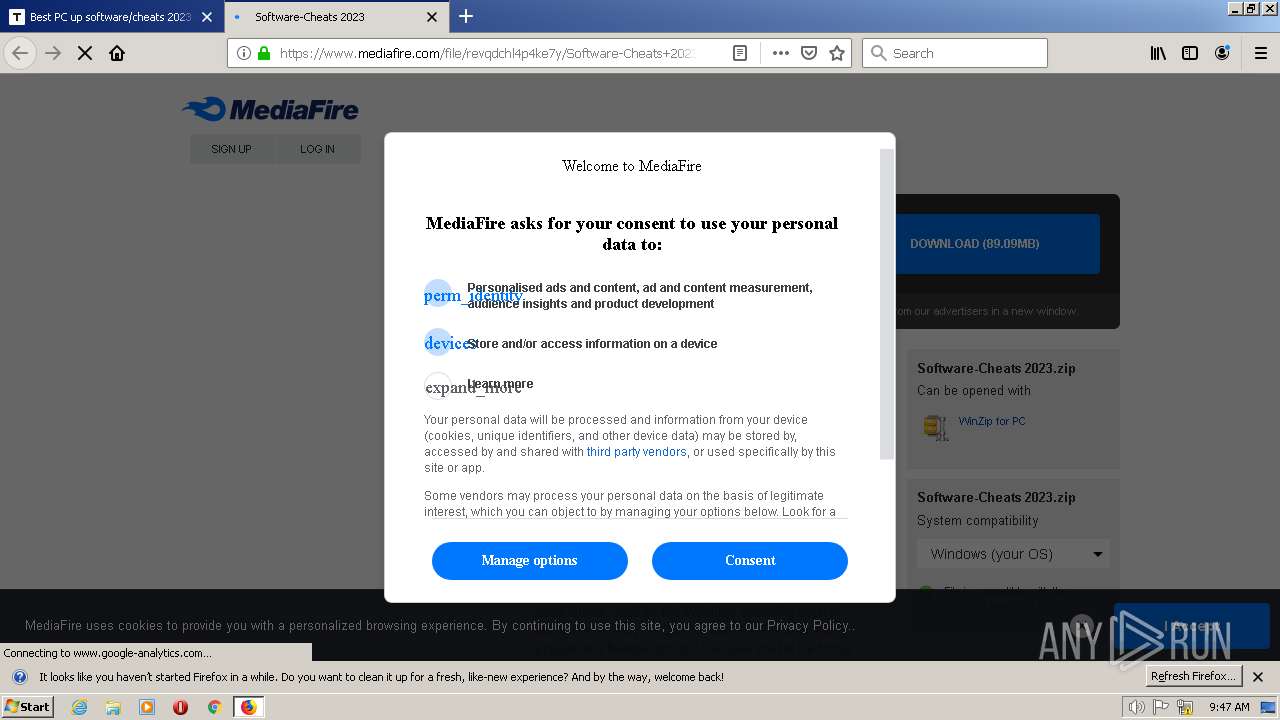
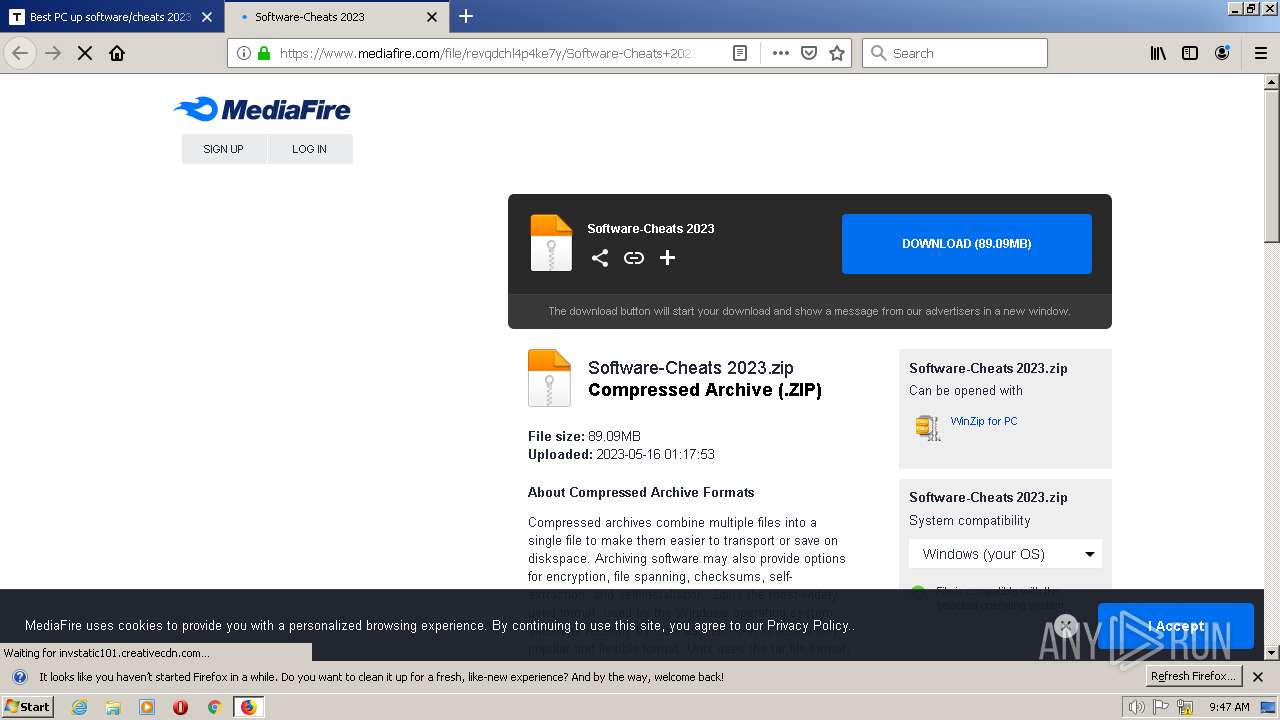
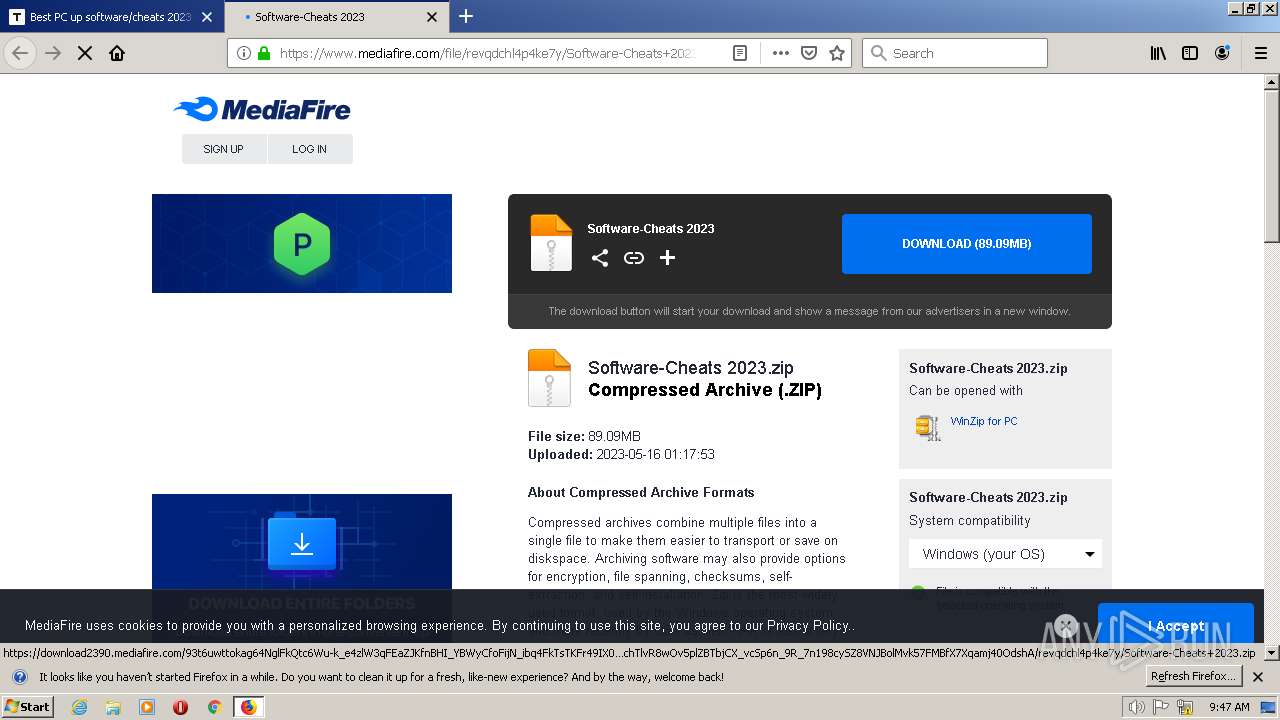
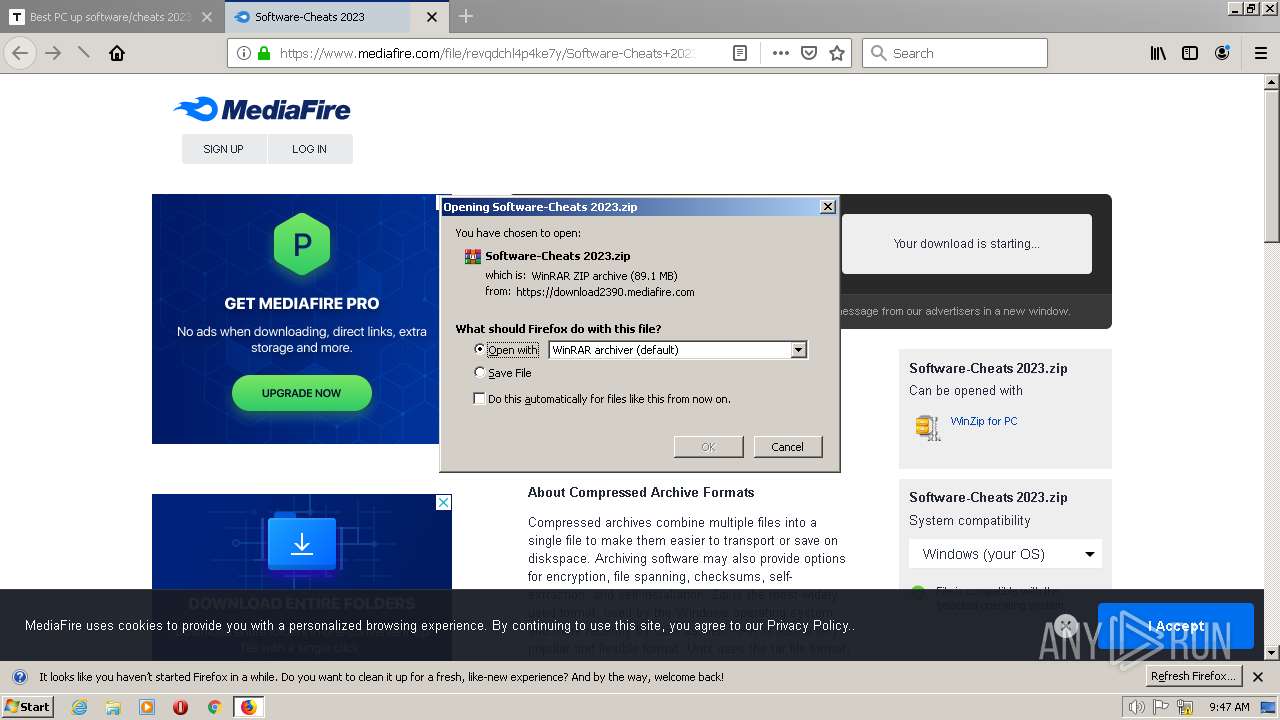
| URL: | https://telegra.ph/Software-2023-02-21-6 |
| Full analysis: | https://app.any.run/tasks/0b297cac-375b-409c-b7a6-c56336c8ee9f |
| Verdict: | Malicious activity |
| Threats: | Raccoon is an info stealer type malware available as a Malware as a Service. It can be obtained for a subscription and costs $200 per month. Raccoon malware has already infected over 100,000 devices and became one of the most mentioned viruses on the underground forums in 2019. |
| Analysis date: | May 19, 2023, 09:46:57 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 36F6055BF423920F04BE0CF204A2C6B9 |
| SHA1: | FD23C41AF490F6F8B7DB10D10903121AE4DAD56D |
| SHA256: | 9F798D7E845B4A0AAB2C027CF5616C544F1D48336DF420B5655DC0FAD0B27824 |
| SSDEEP: | 3:N8INb9t2n:2Izt2n |
MALICIOUS
RACCOON detected by memory dumps
- Sеtup.exe (PID: 308)
SUSPICIOUS
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- firefox.exe (PID: 2556)
Connects to the server without a host name
- Sеtup.exe (PID: 308)
Reads the Internet Settings
- Sеtup.exe (PID: 308)
INFO
Create files in a temporary directory
- firefox.exe (PID: 2556)
Application launched itself
- firefox.exe (PID: 2556)
Reads the machine GUID from the registry
- Sеtup.exe (PID: 308)
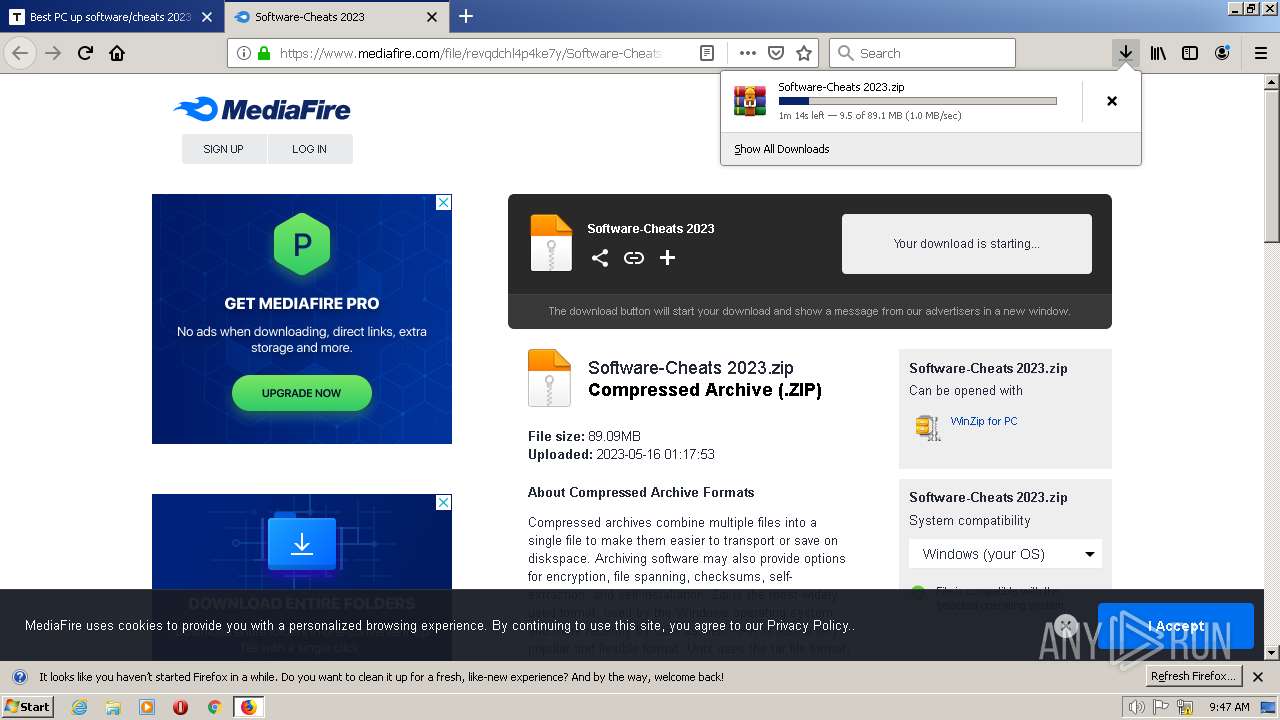
The process uses the downloaded file
- WinRAR.exe (PID: 1624)
- firefox.exe (PID: 2556)
Checks supported languages
- Sеtup.exe (PID: 308)
Executable content was dropped or overwritten
- firefox.exe (PID: 2556)
Reads the computer name
- Sеtup.exe (PID: 308)
Checks proxy server information
- Sеtup.exe (PID: 308)
The process checks LSA protection
- Sеtup.exe (PID: 308)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Raccoon
(PID) Process(308) Sеtup.exe
C2 (2)http://37.220.87.66/
http://45.9.74.99
Keys
xorb9b4a5e42f50e8047f7ce664bfc89e14
Total processes
39
Monitored processes
8
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
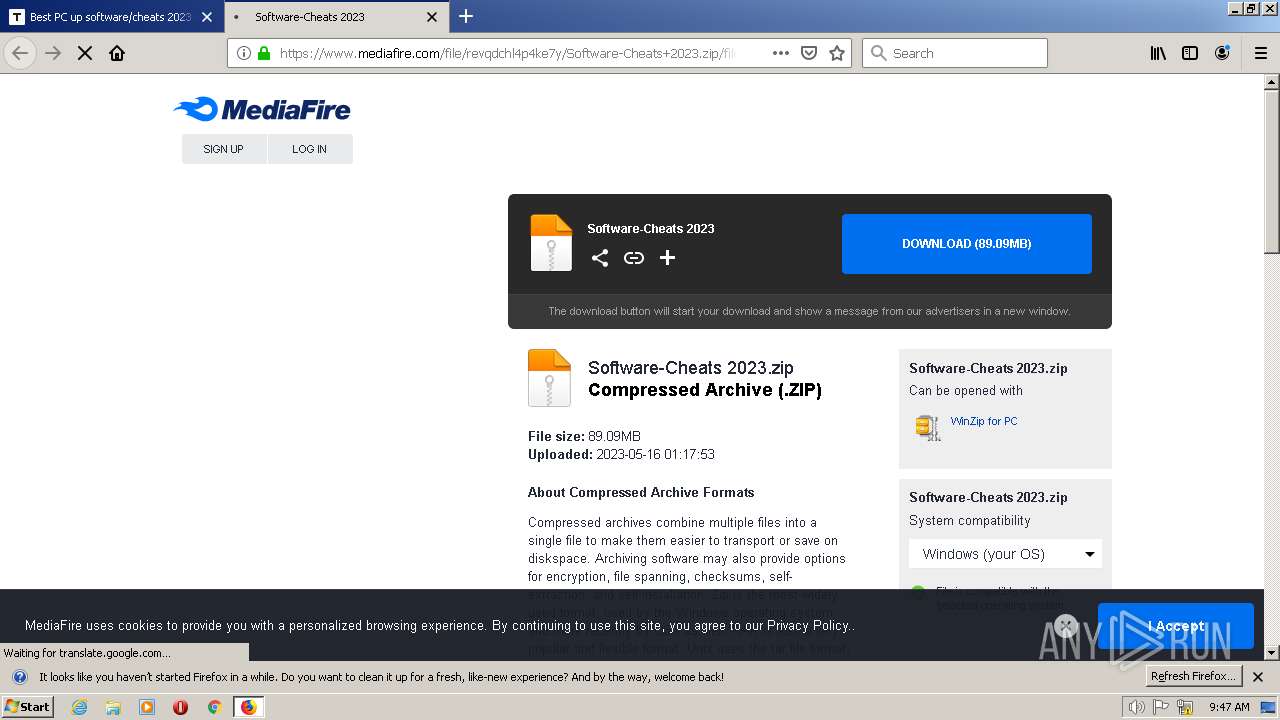
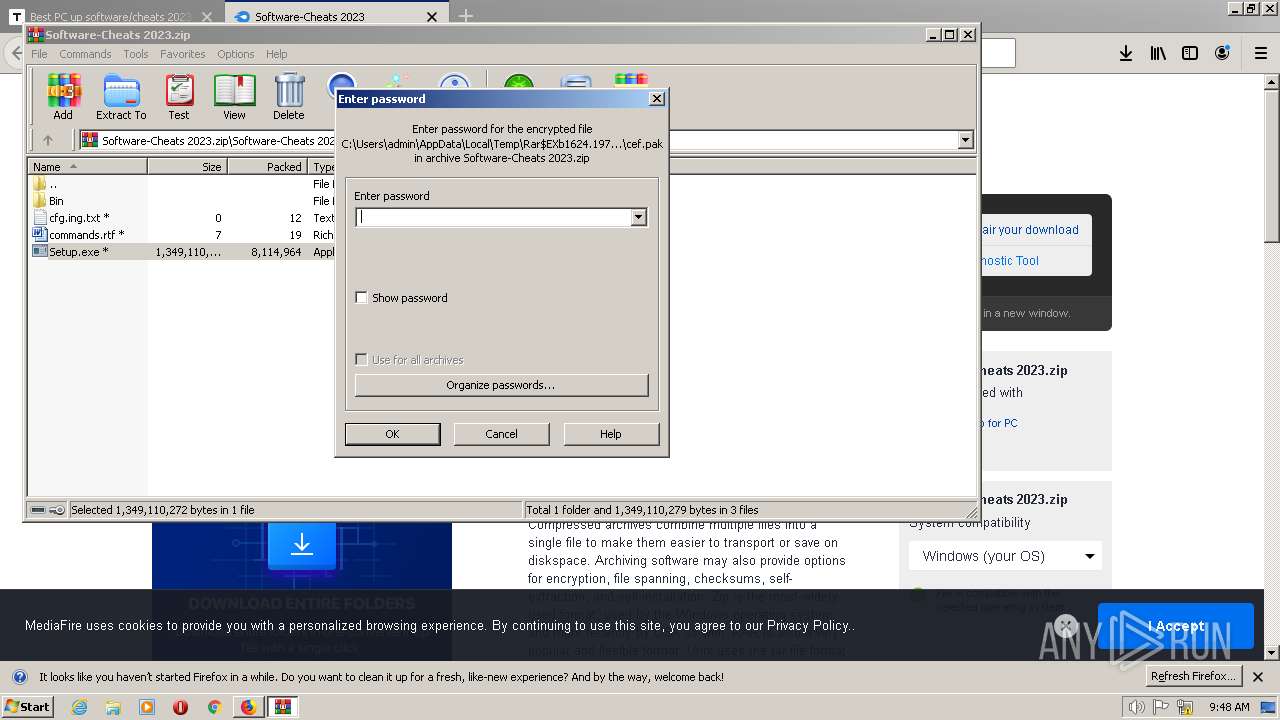
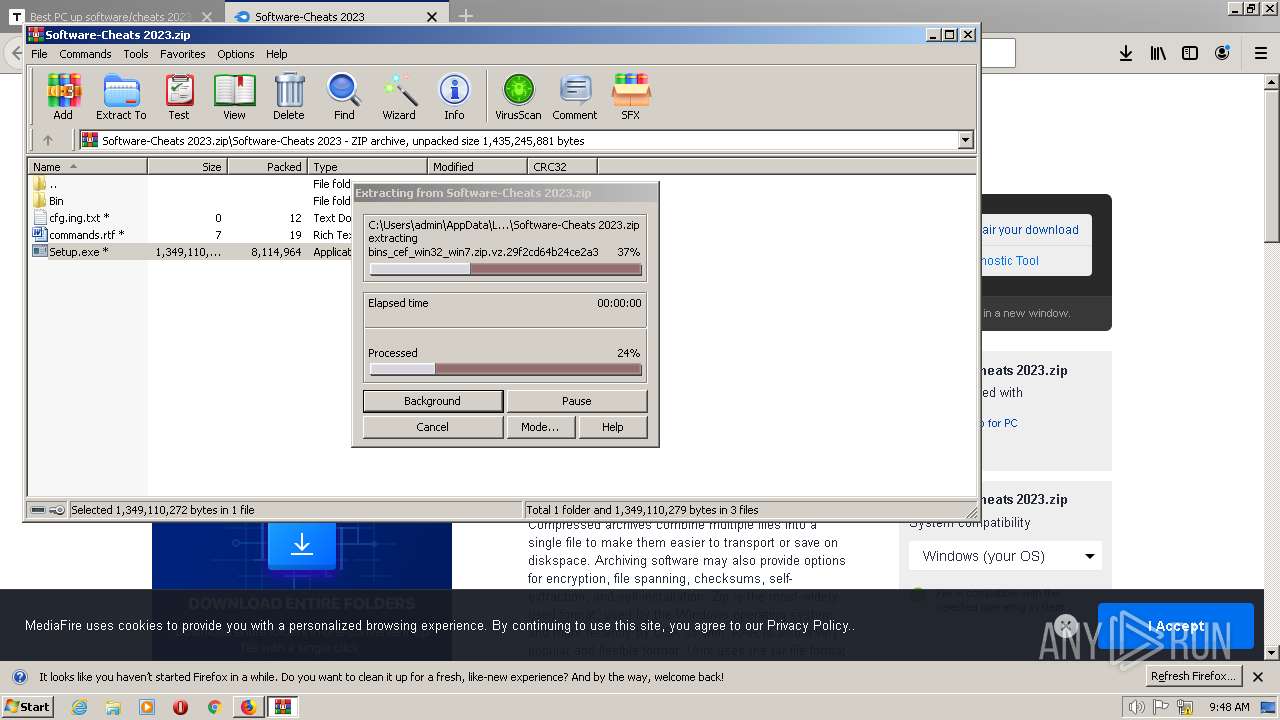
| 308 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb1624.19758\Software-Cheats 2023\Sеtup.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb1624.19758\Software-Cheats 2023\Sеtup.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
Raccoon(PID) Process(308) Sеtup.exe C2 (2)http://37.220.87.66/ http://45.9.74.99 Keys xorb9b4a5e42f50e8047f7ce664bfc89e14 | |||||||||||||||
| 700 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2556.0.36889297\1012182768" -parentBuildID 20190619235627 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 2556 "\\.\pipe\gecko-crash-server-pipe.2556" 1176 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 67.0.4 Modules
| |||||||||||||||
| 1624 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Software-Cheats 2023.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | firefox.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2556 | "C:\Program Files\Mozilla Firefox\firefox.exe" "https://telegra.ph/Software-2023-02-21-6" | C:\Program Files\Mozilla Firefox\firefox.exe | explorer.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 67.0.4 Modules
| |||||||||||||||
| 2684 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2556.20.545313678\1466286298" -childID 3 -isForBrowser -prefsHandle 3464 -prefMapHandle 3468 -prefsLen 6545 -prefMapSize 189239 -parentBuildID 20190619235627 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 2556 "\\.\pipe\gecko-crash-server-pipe.2556" 3476 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 67.0.4 Modules
| |||||||||||||||
| 2708 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2556.27.768860194\808120796" -childID 4 -isForBrowser -prefsHandle 7560 -prefMapHandle 7556 -prefsLen 6768 -prefMapSize 189239 -parentBuildID 20190619235627 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 2556 "\\.\pipe\gecko-crash-server-pipe.2556" 7584 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 67.0.4 Modules
| |||||||||||||||
| 2788 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2556.3.20997476\1211886323" -childID 1 -isForBrowser -prefsHandle 1736 -prefMapHandle 1344 -prefsLen 1 -prefMapSize 189239 -parentBuildID 20190619235627 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 2556 "\\.\pipe\gecko-crash-server-pipe.2556" 1748 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 67.0.4 Modules
| |||||||||||||||
| 2976 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2556.13.648229925\1142204121" -childID 2 -isForBrowser -prefsHandle 2792 -prefMapHandle 2796 -prefsLen 5823 -prefMapSize 189239 -parentBuildID 20190619235627 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 2556 "\\.\pipe\gecko-crash-server-pipe.2556" 2808 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 67.0.4 Modules
| |||||||||||||||
Total events
6 279
Read events
6 239
Write events
40
Delete events
0
Modification events
| (PID) Process: | (2556) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: 0000000000000000 | |||
| (PID) Process: | (2556) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2556) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000008B000000010000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2556) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2556) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2556) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2556) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1624) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\14C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1624) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (1624) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7AndW2K8R2-KB3191566-x64.zip | |||
Executable files
8
Suspicious files
318
Text files
51
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2556 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\nltxvmn2.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 2556 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\nltxvmn2.default\startupCache\urlCache-current.bin | binary | |
MD5:6BED2A248268034CA1F73B2925365DE2 | SHA256:A45996AA907815E86366A17ED448F75A584D7B600AA9398E14DE21DFAD3D613A | |||
| 2556 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\nltxvmn2.default\startupCache\scriptCache-child-current.bin | binary | |
MD5:2B6B5ABCA010270C502C5DD277CD9E7A | SHA256:99DF8717921F70577FCE3386BB7962A804E490C7157F764458001843A1EC606C | |||
| 2556 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\nltxvmn2.default\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 2556 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\nltxvmn2.default\sessionCheckpoints.json | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 2556 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\nltxvmn2.default\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 2556 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\nltxvmn2.default\storage\permanent\chrome\idb\1657114595AmcateirvtiSty.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 2556 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\nltxvmn2.default\prefs.js | text | |
MD5:1759FBCEFAC92AE1A7B8E457ACF71748 | SHA256:5DA473B0E0C84BE5B289DC97C259B98F674E17AF49F4723B4A90F73AA972B739 | |||
| 2556 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\nltxvmn2.default\cache2\entries\7F864014FF7612DDB9A0E82E4FA3D5666532F077 | binary | |
MD5:17F7DEC6217C8B15CF7E65CD1AAA9918 | SHA256:662290A1D9BAF1B56AE74C954B246527CF35974D90009DAD1914EDE94245C958 | |||
| 2556 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\NLTXVM~1.DEF\cert9.db-journal | binary | |
MD5:2B0C52D13322F3BE8DA9F469DC562841 | SHA256:DCD5FD42BA43DFB1A06780739F627C835DB91EA804B4E58353883E21C5C2502B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
40
TCP/UDP connections
167
DNS requests
261
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2556 | firefox.exe | POST | 200 | 2.16.186.27:80 | http://r3.o.lencr.org/ | unknown | binary | 503 b | shared |
2556 | firefox.exe | POST | — | 52.222.226.205:80 | http://ocsp.r2m02.amazontrust.com/ | US | — | — | whitelisted |
2556 | firefox.exe | POST | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3 | US | binary | 471 b | whitelisted |
2556 | firefox.exe | POST | 200 | 192.229.221.95:80 | http://status.geotrust.com/ | US | binary | 471 b | whitelisted |
2556 | firefox.exe | POST | 200 | 2.16.186.27:80 | http://r3.o.lencr.org/ | unknown | binary | 503 b | shared |
2556 | firefox.exe | POST | 200 | 192.124.249.36:80 | http://ocsp.godaddy.com/ | US | der | 1.74 Kb | whitelisted |
2556 | firefox.exe | POST | 200 | 2.16.186.27:80 | http://r3.o.lencr.org/ | unknown | binary | 503 b | shared |
2556 | firefox.exe | POST | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3 | US | der | 471 b | whitelisted |
2556 | firefox.exe | POST | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3 | US | der | 471 b | whitelisted |
2556 | firefox.exe | POST | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3 | US | der | 472 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
328 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
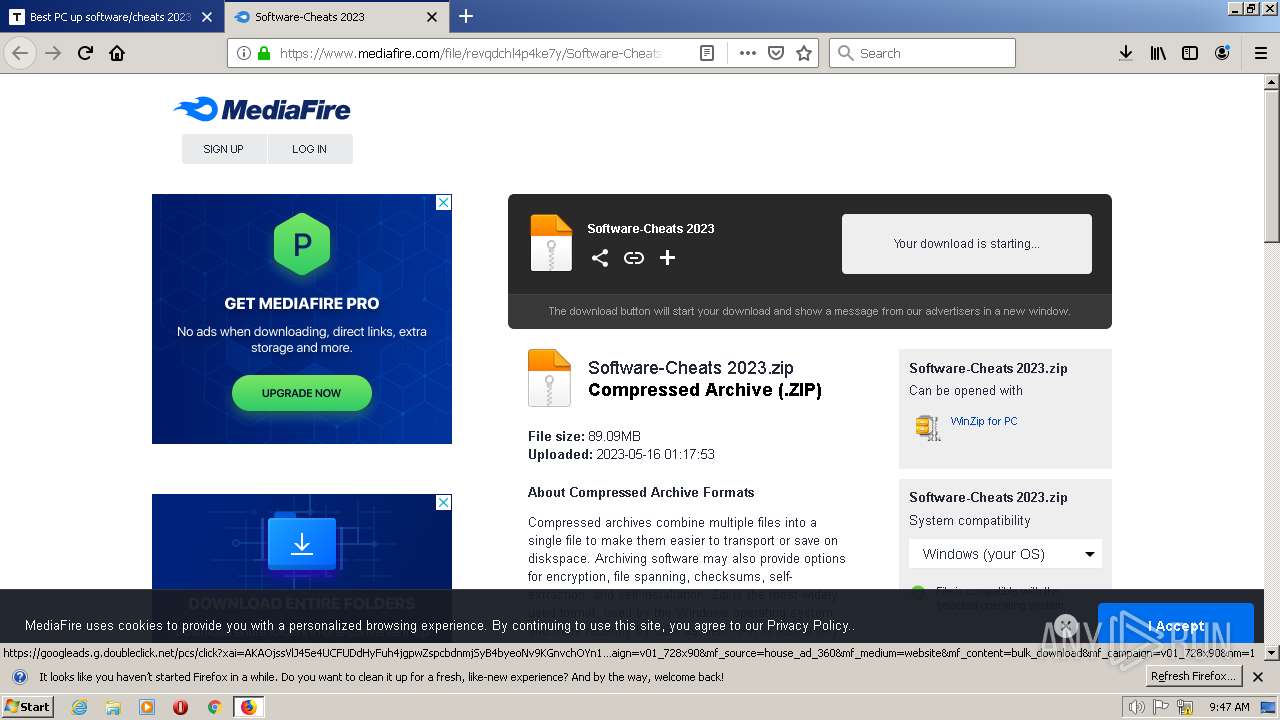
2556 | firefox.exe | 149.154.164.13:443 | telegra.ph | Telegram Messenger Inc | GB | suspicious |
2556 | firefox.exe | 34.160.46.54:443 | search.services.mozilla.com | GOOGLE | US | suspicious |
2556 | firefox.exe | 192.124.249.36:80 | ocsp.godaddy.com | SUCURI-SEC | US | suspicious |
2556 | firefox.exe | 13.32.121.49:443 | snippets.cdn.mozilla.net | AMAZON-02 | US | suspicious |
2556 | firefox.exe | 34.117.65.55:443 | push.services.mozilla.com | GOOGLE-CLOUD-PLATFORM | US | suspicious |
2556 | firefox.exe | 2.16.186.27:80 | r3.o.lencr.org | Akamai International B.V. | DE | whitelisted |
2556 | firefox.exe | 104.20.138.65:443 | tinyurl.com | CLOUDFLARENET | — | suspicious |
2556 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
telegra.ph |
| malicious |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
ocsp.godaddy.com |
| whitelisted |
ocsp.godaddy.com.akadns.net |
| whitelisted |
search.services.mozilla.com |
| whitelisted |
search.r53-2.services.mozilla.com |
| whitelisted |
t.me |
| whitelisted |
push.services.mozilla.com |
| whitelisted |
autopush.prod.mozaws.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2556 | firefox.exe | Misc activity | ET INFO Observed Telegram Domain (t .me in TLS SNI) |
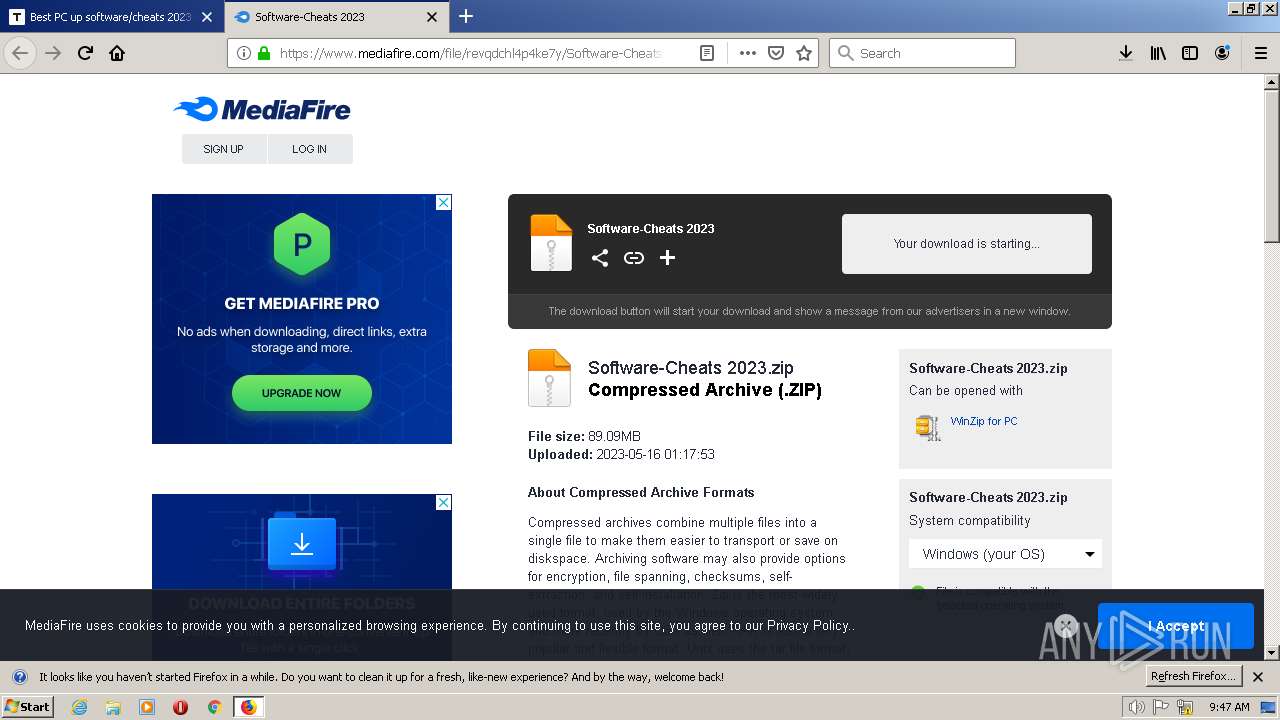
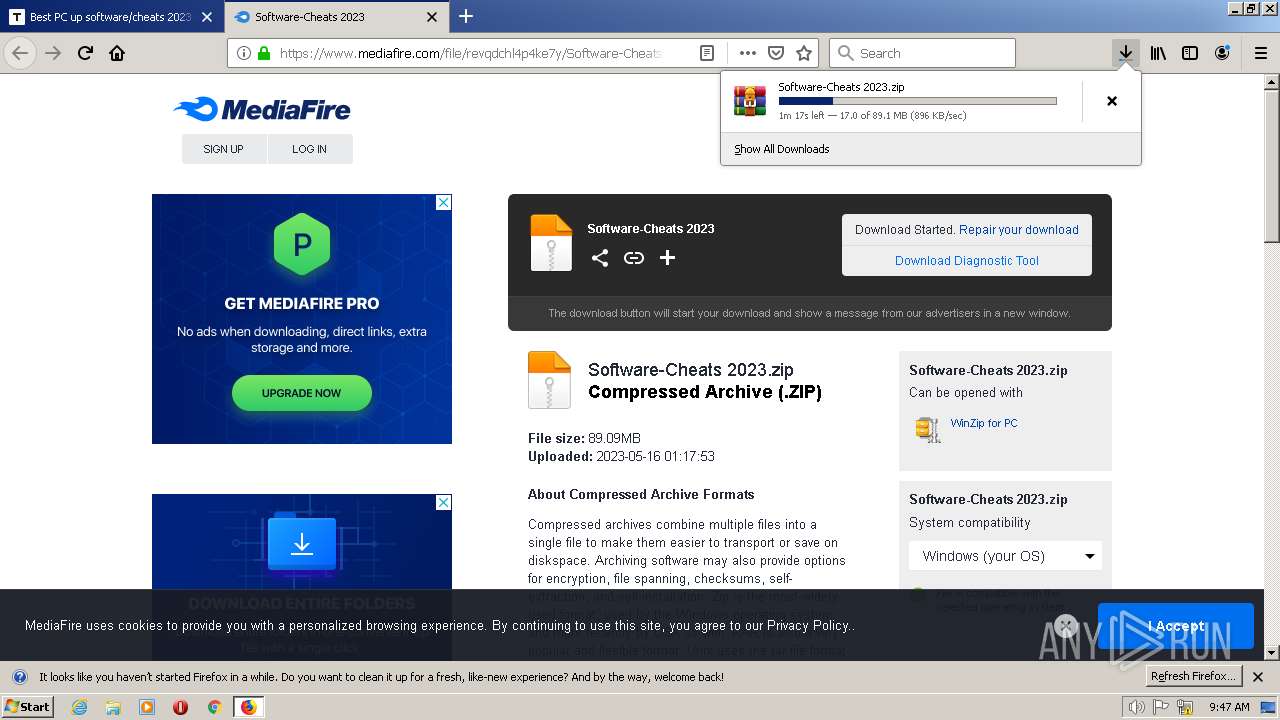
328 | svchost.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
328 | svchost.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
328 | svchost.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
328 | svchost.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
328 | svchost.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
328 | svchost.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
328 | svchost.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
328 | svchost.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |