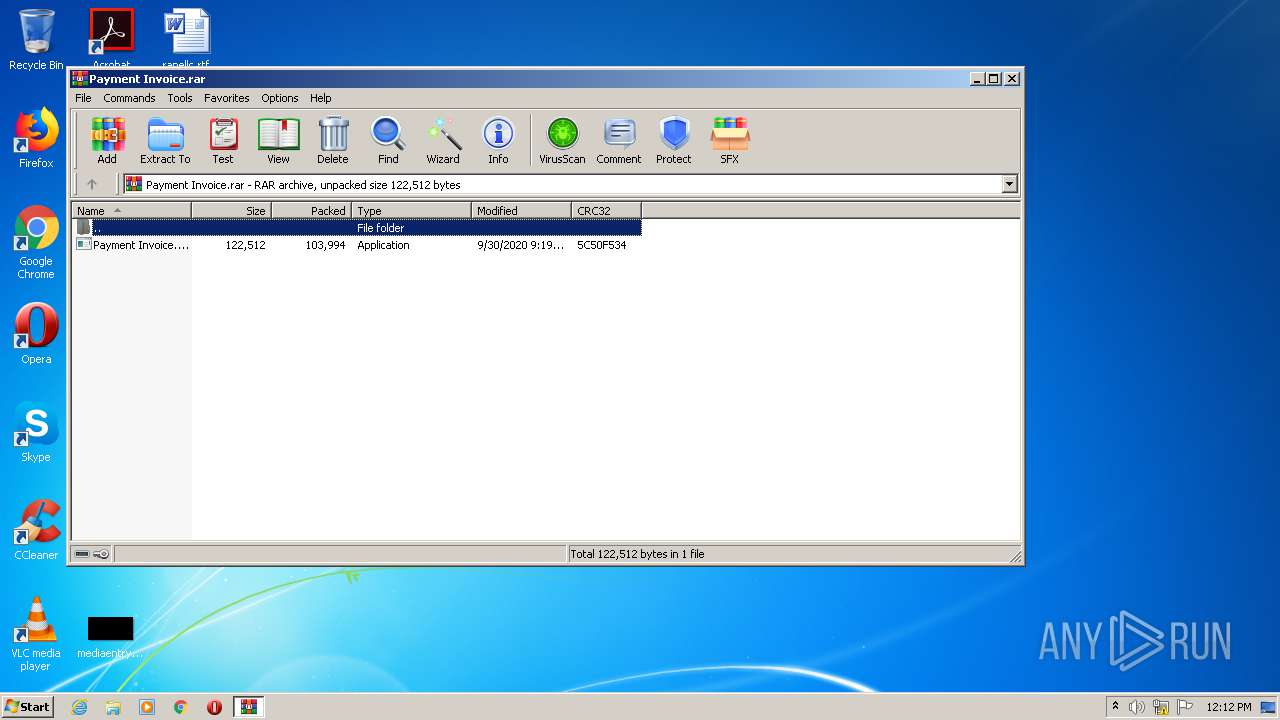
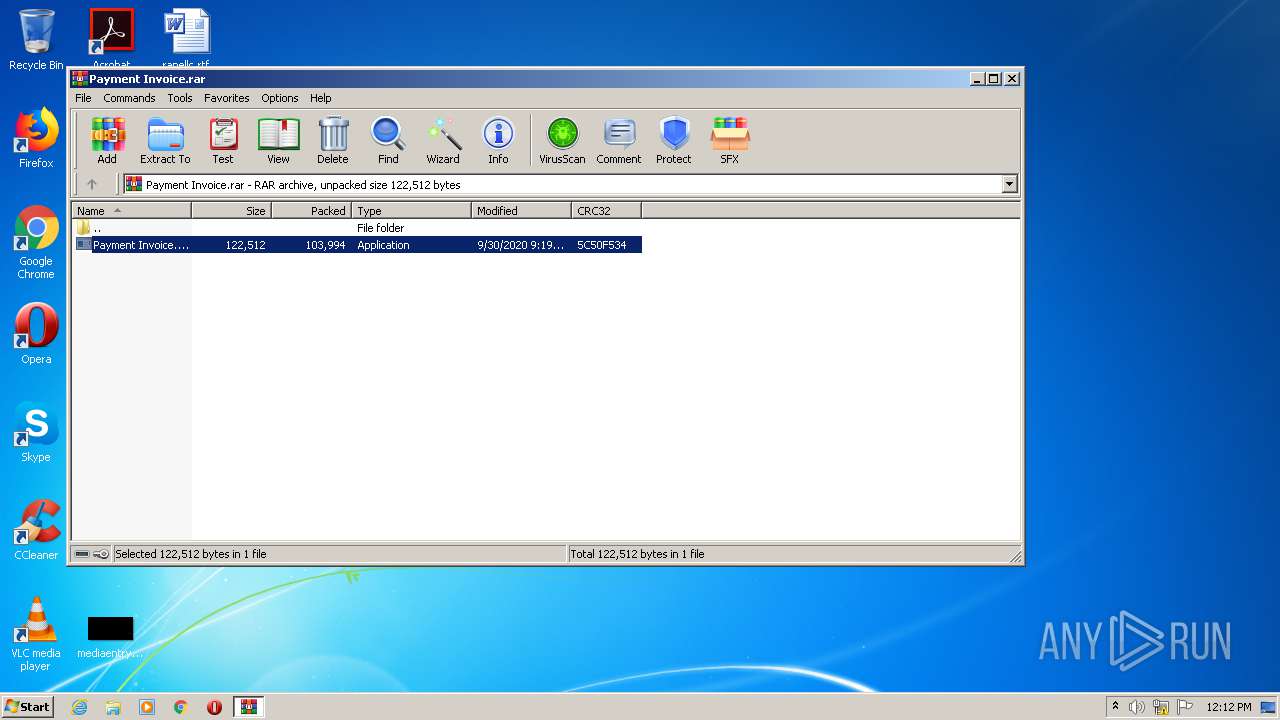
| File name: | Payment Invoice.rar |
| Full analysis: | https://app.any.run/tasks/dc6c27ee-90cc-4cb8-8073-750b8aa2d9d6 |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | September 30, 2020, 11:11:56 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | F734FE56B6728BB5F6BEF5FBA292056A |
| SHA1: | 19BB9223270EFCC6A85CD352EBBC1CFFE22B82D8 |
| SHA256: | 9F5D67AAA69A9E14D95B3E89EDFF844C8B2FF07E2E1854B6114BBFD5892CB85A |
| SSDEEP: | 3072:YTdQaFYJG2kkGeCzNQ1KL/4QcP21Hdhkg:YxQaOJfCuYmw9eg |
MALICIOUS
Application was dropped or rewritten from another process
- Payment Invoice.exe (PID: 1012)
- Payment Invoice.exe (PID: 1552)
Changes settings of System certificates
- Payment Invoice.exe (PID: 1012)
- Payment Invoice.exe (PID: 1552)
ASYNCRAT was detected
- Payment Invoice.exe (PID: 1552)
Connects to CnC server
- Payment Invoice.exe (PID: 1552)
SUSPICIOUS
Adds / modifies Windows certificates
- Payment Invoice.exe (PID: 1012)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2136)
Application launched itself
- Payment Invoice.exe (PID: 1012)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
39
Monitored processes
4
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1012 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2136.16941\Payment Invoice.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2136.16941\Payment Invoice.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 1552 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2136.16941\Payment Invoice.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2136.16941\Payment Invoice.exe | Payment Invoice.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2136 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Payment Invoice.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3136 | timeout 4 | C:\Windows\system32\timeout.exe | — | Payment Invoice.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
532
Read events
482
Write events
48
Delete events
2
Modification events
| (PID) Process: | (2136) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2136) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2136) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2136) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Payment Invoice.rar | |||
| (PID) Process: | (2136) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2136) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2136) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2136) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2136) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2136) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
1
Suspicious files
4
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1552 | Payment Invoice.exe | C:\Users\admin\AppData\Local\Temp\CabF71E.tmp | — | |
MD5:— | SHA256:— | |||
| 1552 | Payment Invoice.exe | C:\Users\admin\AppData\Local\Temp\TarF71F.tmp | — | |
MD5:— | SHA256:— | |||
| 1552 | Payment Invoice.exe | C:\Users\admin\AppData\Local\Temp\CabF730.tmp | — | |
MD5:— | SHA256:— | |||
| 1552 | Payment Invoice.exe | C:\Users\admin\AppData\Local\Temp\TarF731.tmp | — | |
MD5:— | SHA256:— | |||
| 1552 | Payment Invoice.exe | C:\Users\admin\AppData\Local\Temp\CabF7ED.tmp | — | |
MD5:— | SHA256:— | |||
| 1552 | Payment Invoice.exe | C:\Users\admin\AppData\Local\Temp\TarF7EE.tmp | — | |
MD5:— | SHA256:— | |||
| 1552 | Payment Invoice.exe | C:\Users\admin\AppData\Local\Temp\CabF85C.tmp | — | |
MD5:— | SHA256:— | |||
| 1552 | Payment Invoice.exe | C:\Users\admin\AppData\Local\Temp\TarF85D.tmp | — | |
MD5:— | SHA256:— | |||
| 1552 | Payment Invoice.exe | C:\Users\admin\AppData\Local\Temp\CabF8AD.tmp | — | |
MD5:— | SHA256:— | |||
| 1552 | Payment Invoice.exe | C:\Users\admin\AppData\Local\Temp\TarF8AE.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
3
DNS requests
4
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1552 | Payment Invoice.exe | GET | 200 | 13.107.4.50:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.5 Kb | whitelisted |
1552 | Payment Invoice.exe | GET | 304 | 13.107.4.50:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.5 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1012 | Payment Invoice.exe | 192.81.135.159:443 | paste.merkoba.com | Linode, LLC | US | unknown |
1552 | Payment Invoice.exe | 45.35.158.173:6606 | genjustu.hopto.org | Psychz Networks | US | malicious |
1552 | Payment Invoice.exe | 13.107.4.50:80 | www.download.windowsupdate.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
paste.merkoba.com |
| unknown |
genjustu.hopto.org |
| malicious |
www.download.windowsupdate.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.hopto .org |
1052 | svchost.exe | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.hopto .org |
1552 | Payment Invoice.exe | A Network Trojan was detected | MALWARE [PTsecurity] AsyncRAT |
1552 | Payment Invoice.exe | A Network Trojan was detected | ET TROJAN Observed Malicious SSL Cert (AsyncRAT CnC) |
1552 | Payment Invoice.exe | A Network Trojan was detected | MALWARE [PTsecurity] AsyncRAT |
1 ETPRO signatures available at the full report
Process | Message |
|---|---|
Payment Invoice.exe | DONT_MUTATE
|