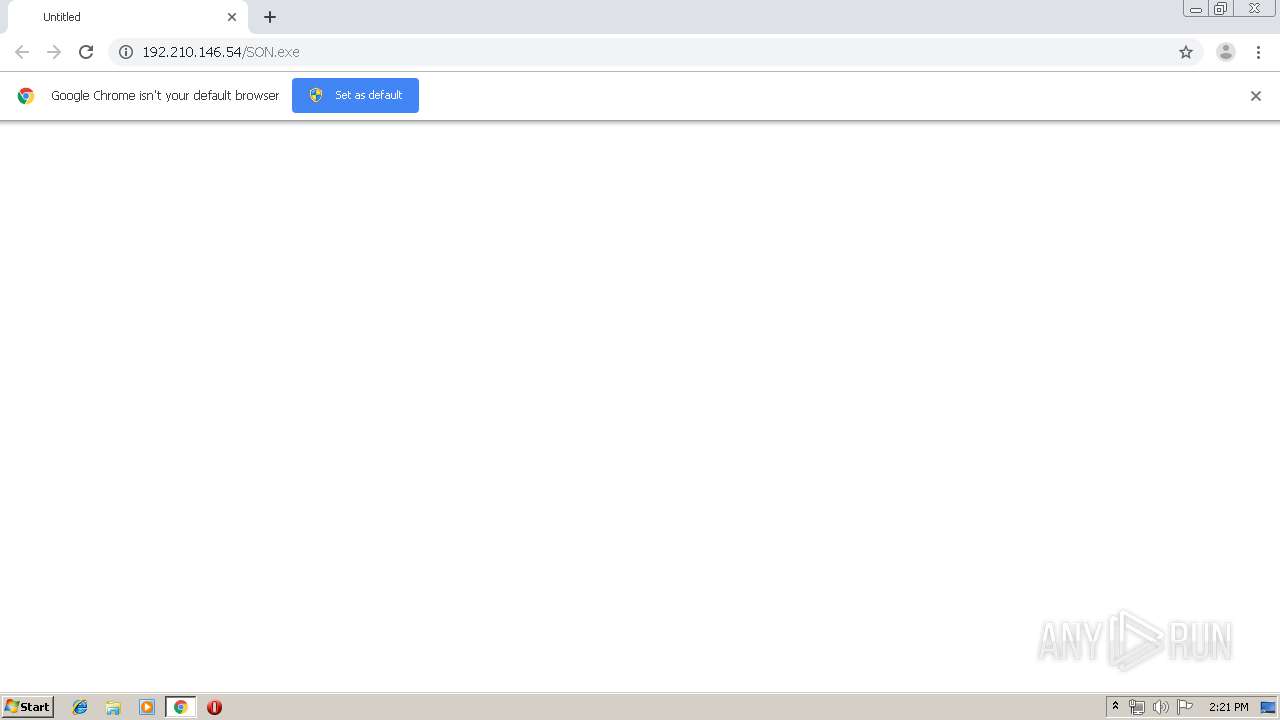
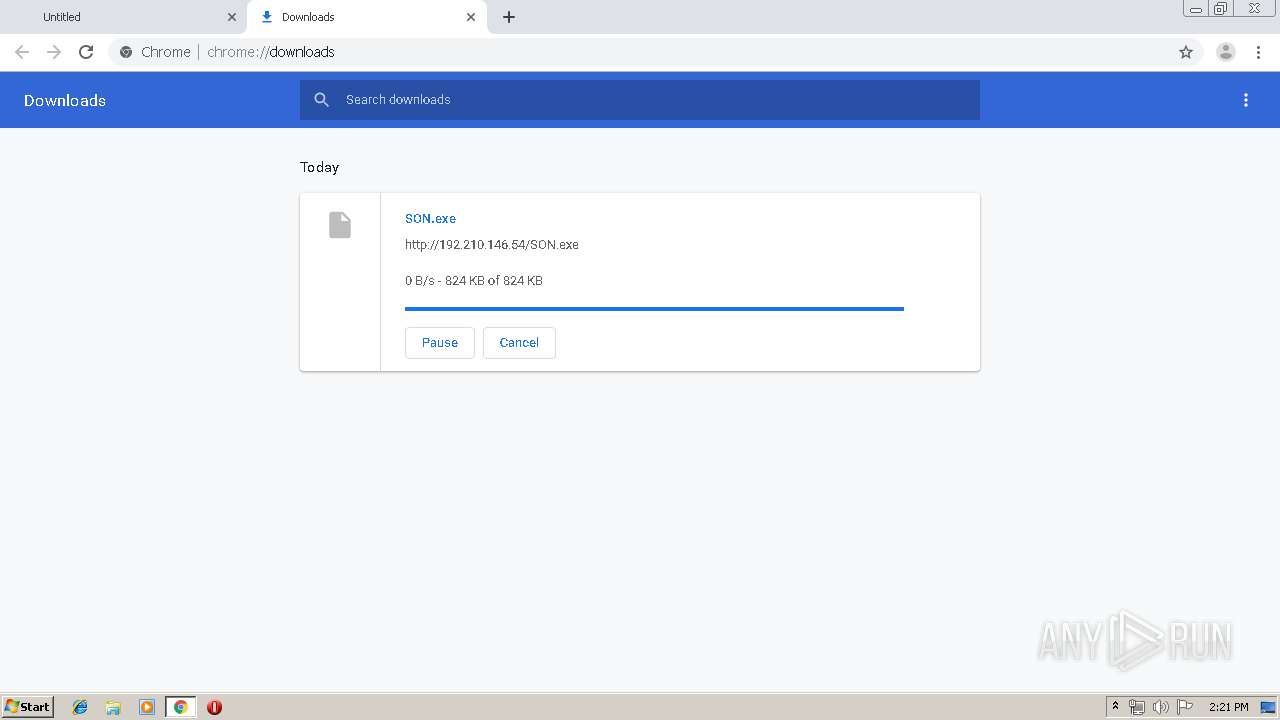
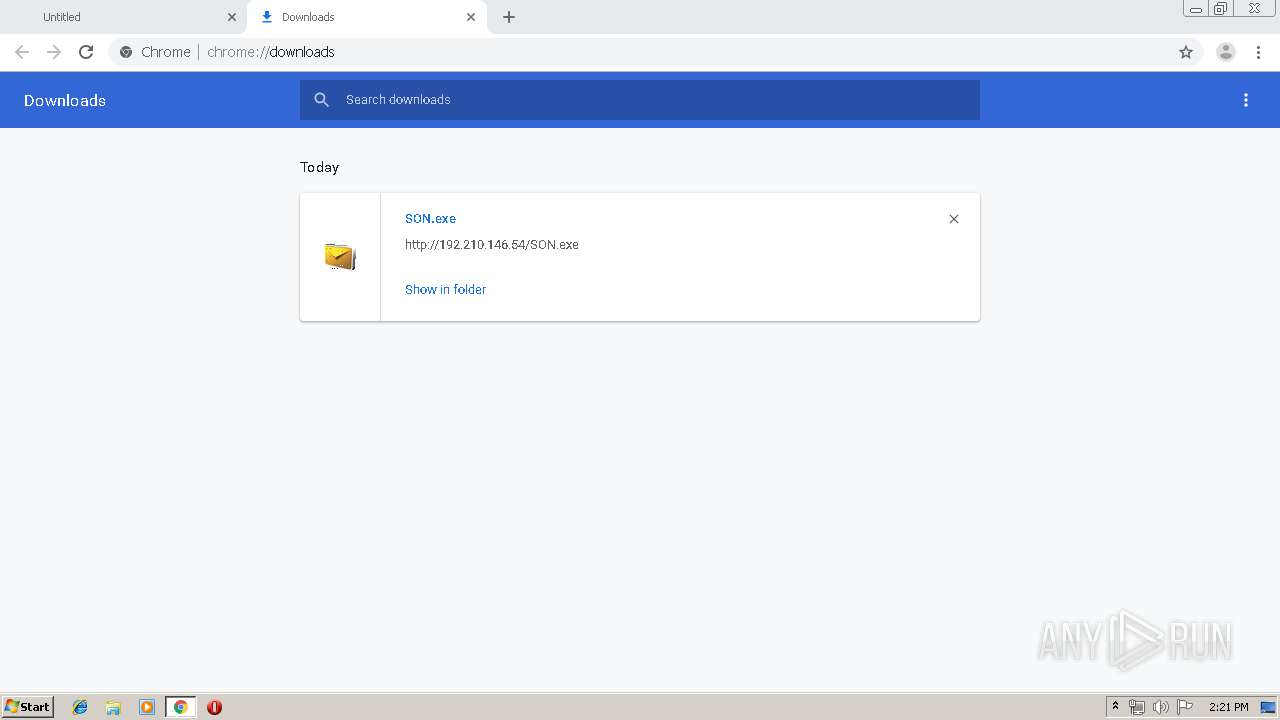
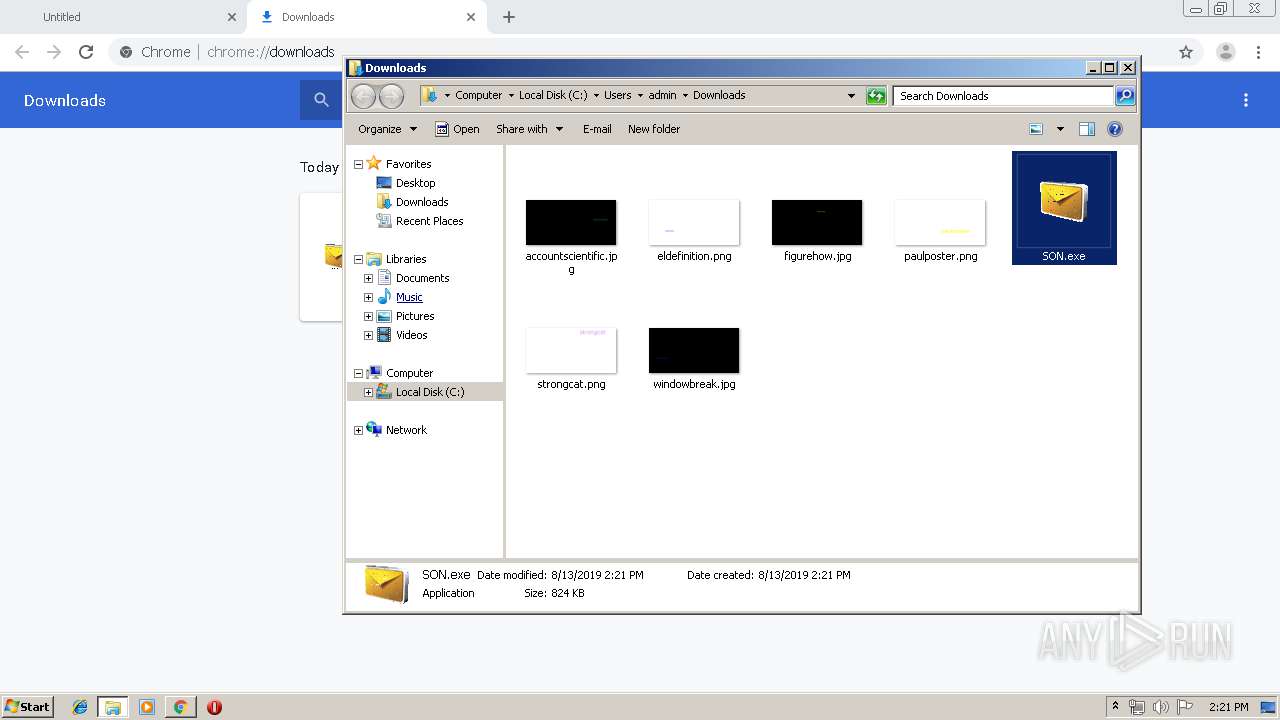
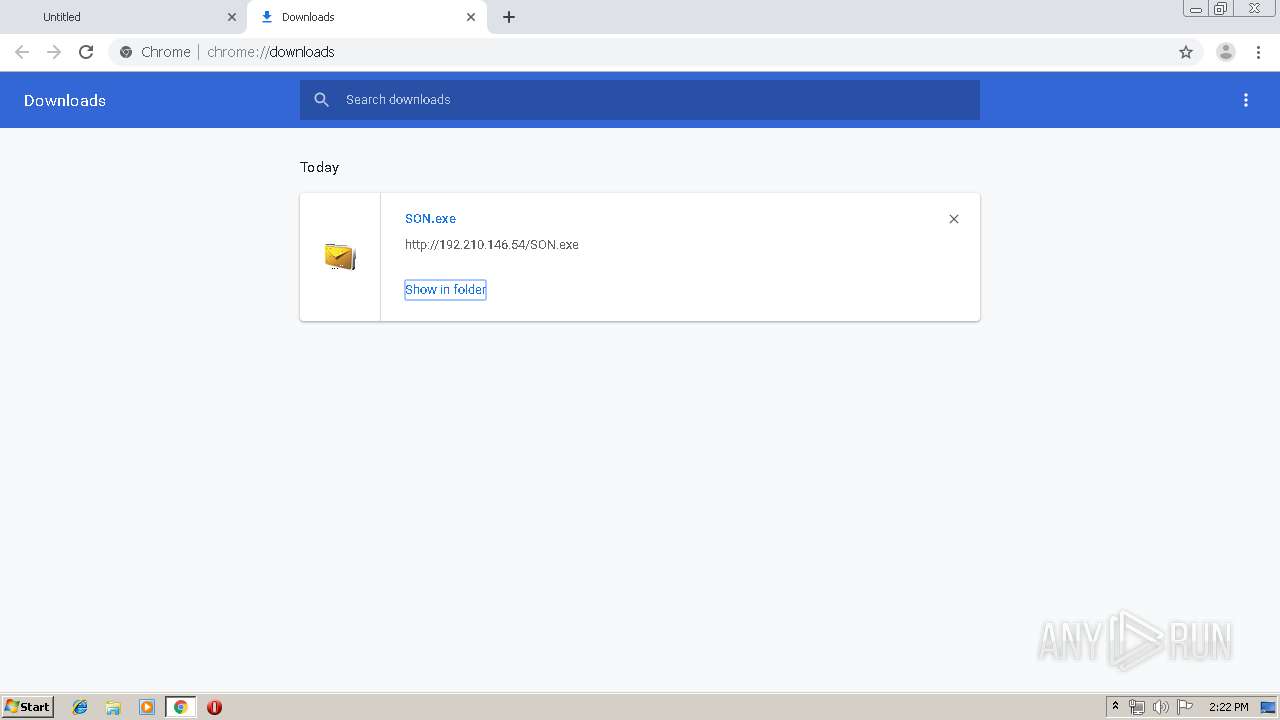
| URL: | http://192.210.146.54/SON.exe |
| Full analysis: | https://app.any.run/tasks/02f15692-5b0a-4619-9d4e-bba5c58f1219 |
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | August 13, 2019, 13:21:18 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 1F226D9DBF6662B5D3B1AC17C8A6E810 |
| SHA1: | 14890B9BF66B86B4C7D04452D910AEAF732D6641 |
| SHA256: | 9F17C49F8ADFC57724FA14D6209782AEEE6A23E9D1D8E7FEE1858CE52569700B |
| SSDEEP: | 3:N1KkX9NL4An:CktNLN |
MALICIOUS
Application was dropped or rewritten from another process
- SON.exe (PID: 2176)
- SON.exe (PID: 2252)
AGENTTESLA was detected
- SON.exe (PID: 2176)
Actions looks like stealing of personal data
- SON.exe (PID: 2176)
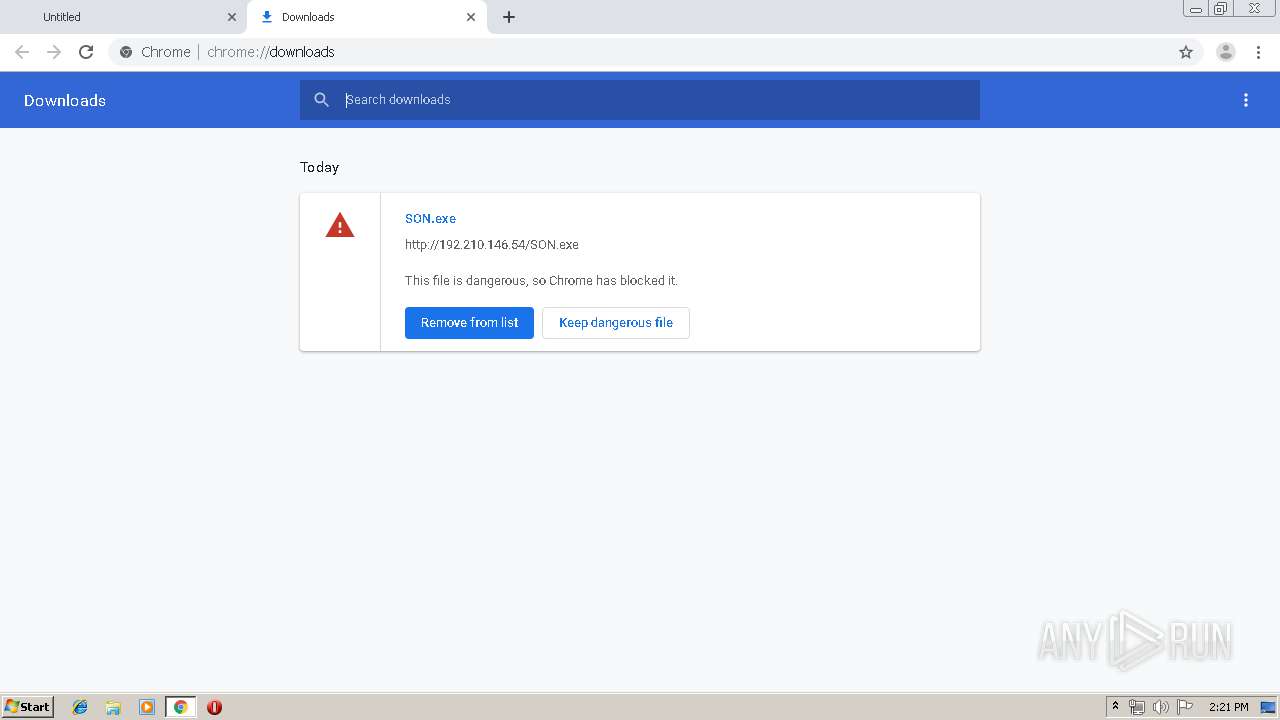
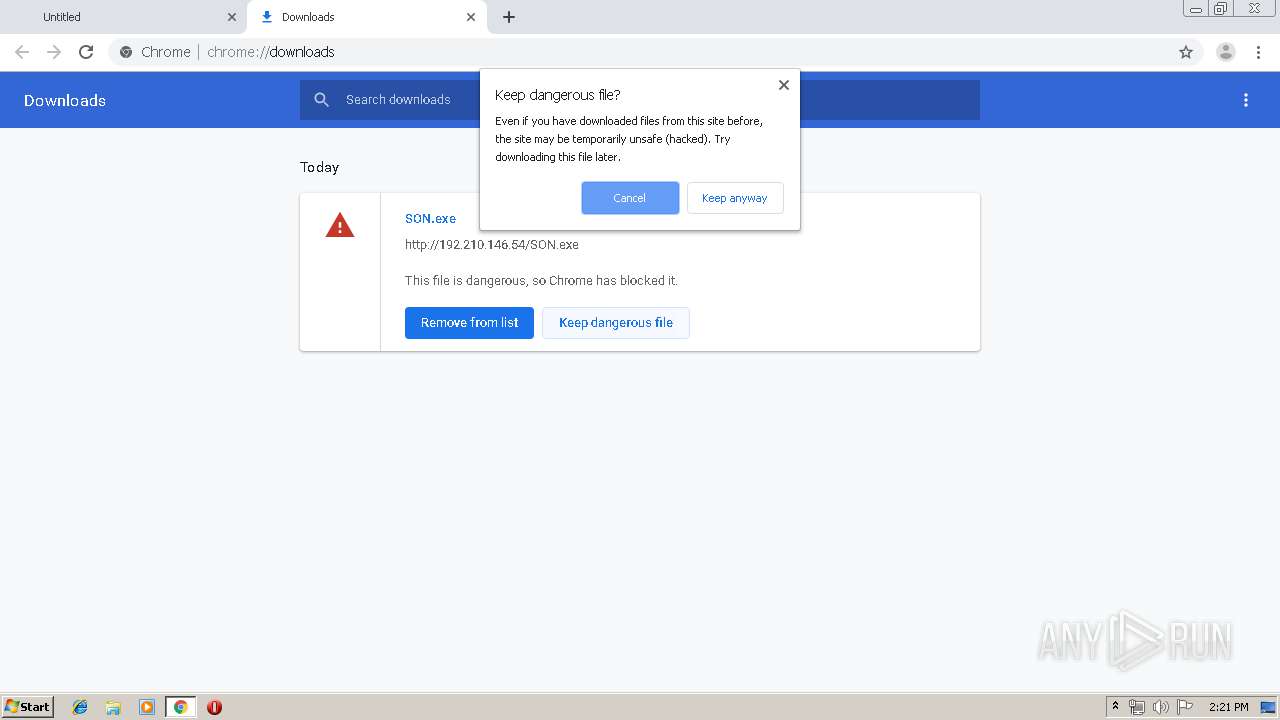
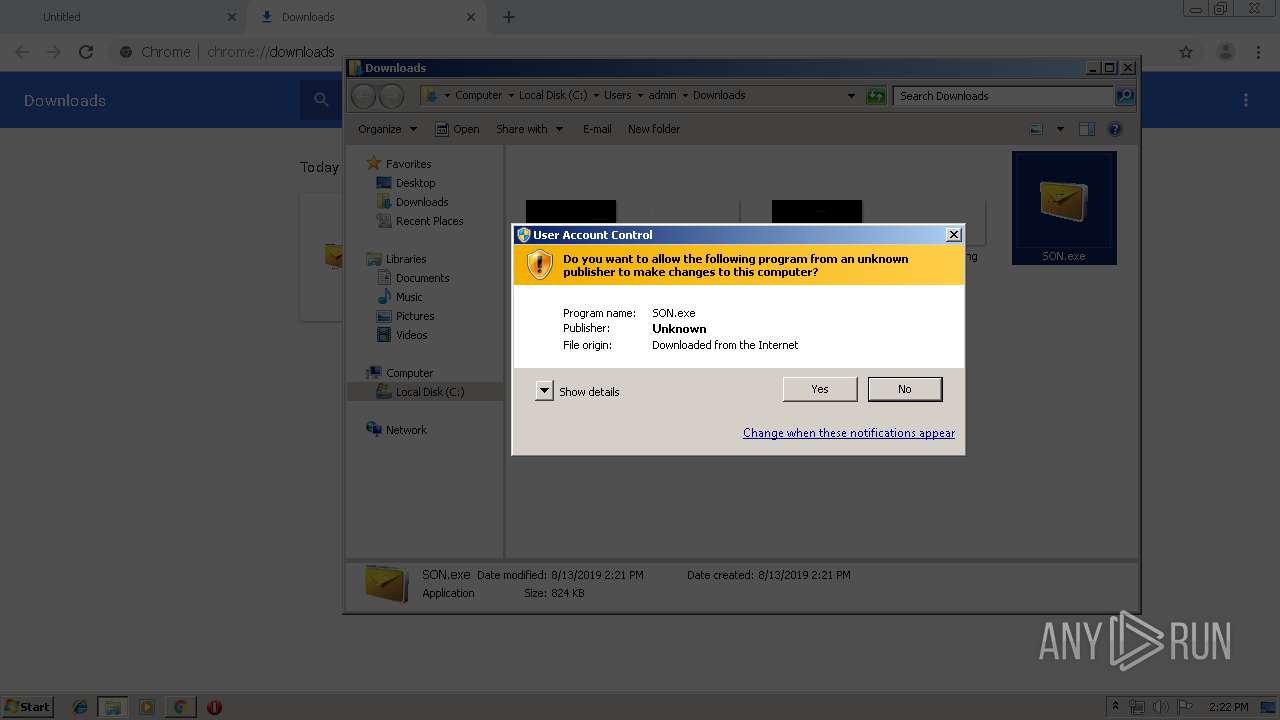
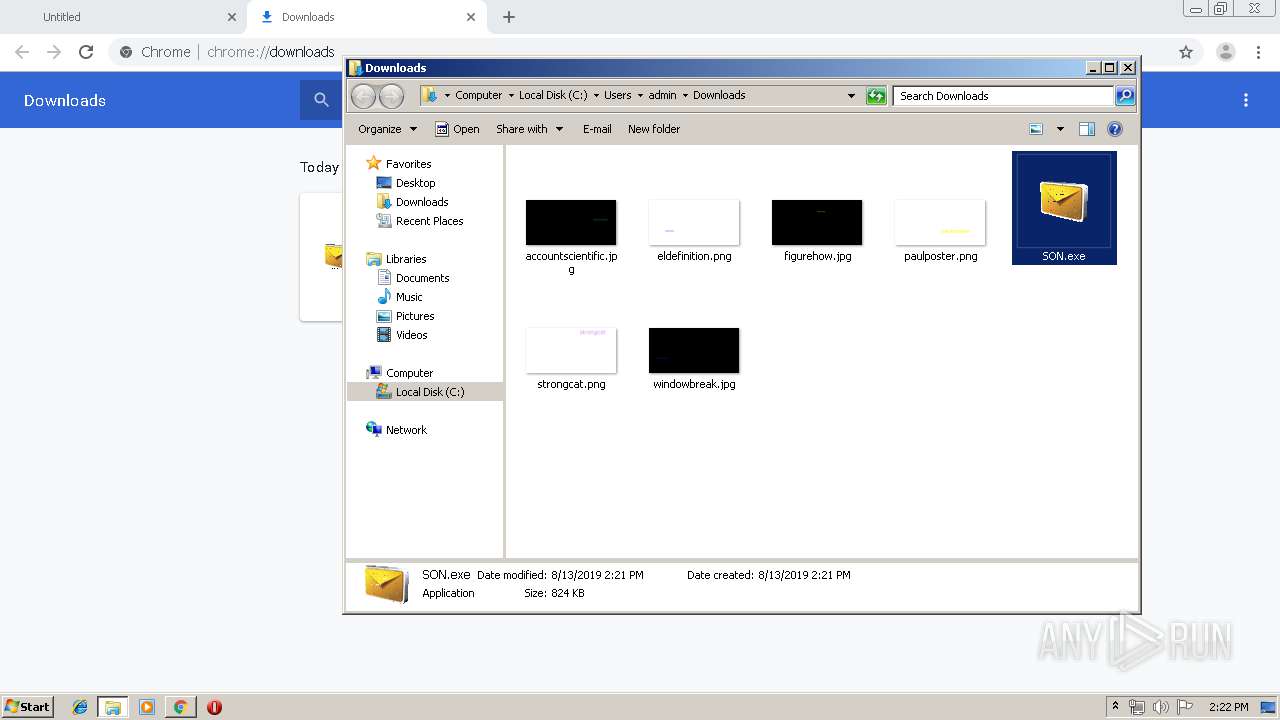
Downloads executable files from the Internet
- chrome.exe (PID: 3764)
Downloads executable files from IP
- chrome.exe (PID: 3764)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 3988)
- chrome.exe (PID: 3764)
Checks for external IP
- SON.exe (PID: 2176)
Application launched itself
- SON.exe (PID: 2252)
INFO
Application launched itself
- chrome.exe (PID: 3988)
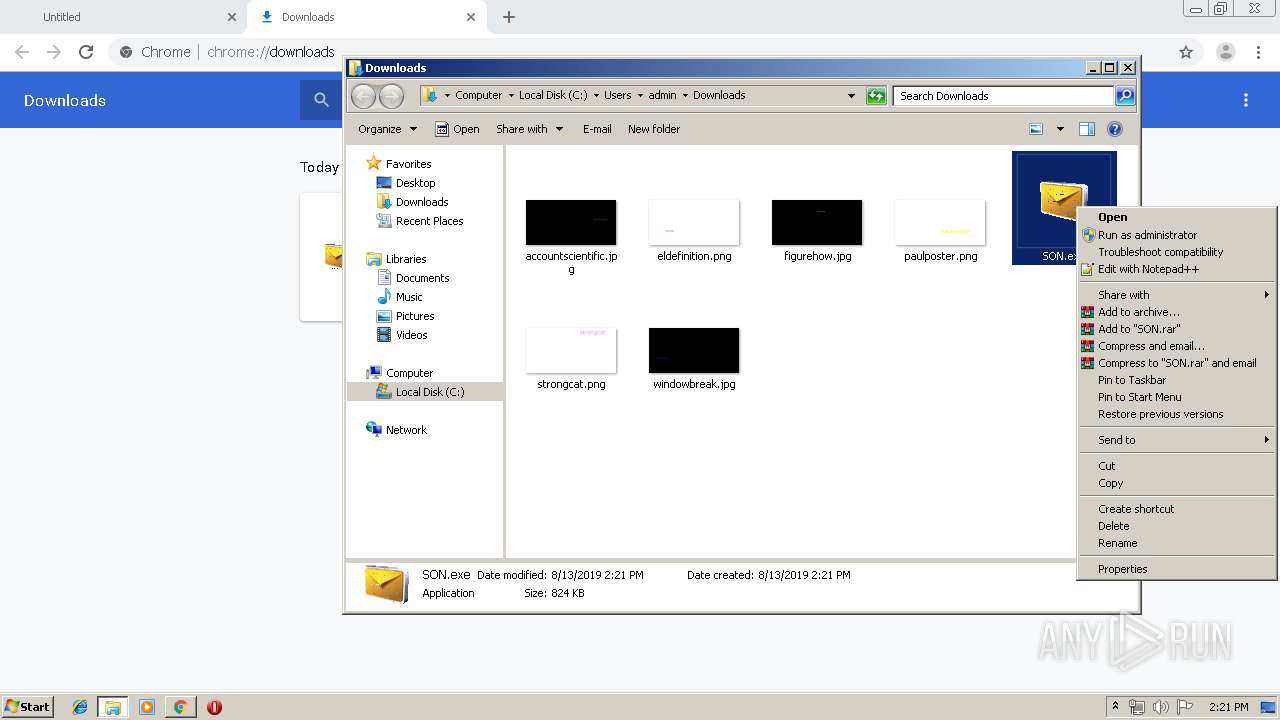
Manual execution by user
- SON.exe (PID: 2252)
Reads Internet Cache Settings
- chrome.exe (PID: 3988)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
51
Monitored processes
13
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 456 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6eafa9d0,0x6eafa9e0,0x6eafa9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1400 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=360 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1924 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1000,11971724106329951457,1978939448585659609,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=12253518711978943154 --mojo-platform-channel-handle=1024 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2176 | "C:\Users\admin\Downloads\SON.exe" | C:\Users\admin\Downloads\SON.exe | SON.exe | ||||||||||||
User: admin Company: CrinieralucCephalochord Integrity Level: HIGH Description: Crinieralucdisch2 Exit code: 0 Version: 7.09.0004 Modules
| |||||||||||||||
| 2252 | "C:\Users\admin\Downloads\SON.exe" | C:\Users\admin\Downloads\SON.exe | explorer.exe | ||||||||||||
User: admin Company: CrinieralucCephalochord Integrity Level: HIGH Description: Crinieralucdisch2 Exit code: 0 Version: 7.09.0004 Modules
| |||||||||||||||
| 2600 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,11971724106329951457,1978939448585659609,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8604831636902472764 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2220 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2648 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,11971724106329951457,1978939448585659609,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5299675832809897767 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2440 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2820 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,11971724106329951457,1978939448585659609,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3884675598796750225 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2164 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2928 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,11971724106329951457,1978939448585659609,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10061942862203757280 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3456 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2960 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,11971724106329951457,1978939448585659609,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12241216469236718212 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3500 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
619
Read events
563
Write events
53
Delete events
3
Modification events
| (PID) Process: | (3988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (3988) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3988-13210176094588375 |
Value: 259 | |||
Executable files
5
Suspicious files
21
Text files
78
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\9b20792a-1814-4f38-9793-64581cbecd19.tmp | — | |
MD5:— | SHA256:— | |||
| 3988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF36d3c4.TMP | text | |
MD5:— | SHA256:— | |||
| 3988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF36d402.TMP | text | |
MD5:— | SHA256:— | |||
| 3988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF36d3c4.TMP | text | |
MD5:— | SHA256:— | |||
| 3988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF36d3c4.TMP | text | |
MD5:— | SHA256:— | |||
| 3988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\MANIFEST-000001 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
14
DNS requests
9
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3764 | chrome.exe | GET | 200 | 192.210.146.54:80 | http://192.210.146.54/SON.exe | US | executable | 824 Kb | suspicious |
2176 | SON.exe | GET | 200 | 18.205.71.63:80 | http://checkip.amazonaws.com/ | US | text | 14 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3764 | chrome.exe | 192.210.146.54:80 | — | ColoCrossing | US | suspicious |
3764 | chrome.exe | 172.217.18.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3764 | chrome.exe | 172.217.22.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
3764 | chrome.exe | 172.217.22.46:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
3764 | chrome.exe | 172.217.18.100:443 | www.google.com | Google Inc. | US | whitelisted |
3764 | chrome.exe | 216.58.205.227:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3764 | chrome.exe | 172.217.9.206:443 | safebrowsing.google.com | Google Inc. | US | whitelisted |
2176 | SON.exe | 208.91.199.223:587 | smtp.luckyshippinq.com | PDR | US | shared |
2176 | SON.exe | 18.205.71.63:80 | checkip.amazonaws.com | — | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
sb-ssl.google.com |
| whitelisted |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
safebrowsing.google.com |
| whitelisted |
checkip.amazonaws.com |
| malicious |
smtp.luckyshippinq.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3764 | chrome.exe | A Network Trojan was detected | ET INFO Executable Download from dotted-quad Host |
3764 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3764 | chrome.exe | Potentially Bad Traffic | ET INFO SUSPICIOUS Dotted Quad Host MZ Response |
2176 | SON.exe | A Network Trojan was detected | MALWARE [PTsecurity] AgentTesla IP Check |
2176 | SON.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
2176 | SON.exe | A Network Trojan was detected | AV TROJAN Win.Keylogger.AgentTesla variant outbound SMTP connection |
2176 | SON.exe | A Network Trojan was detected | MALWARE [PTsecurity] Trojan-Spy.Keylogger.AgentTesla Exfiltration by SMTP |
3 ETPRO signatures available at the full report