| File name: | tdrpl[1].exe |
| Full analysis: | https://app.any.run/tasks/26769620-7f99-49b6-8e5d-c5eb2d077a4d |
| Verdict: | Malicious activity |
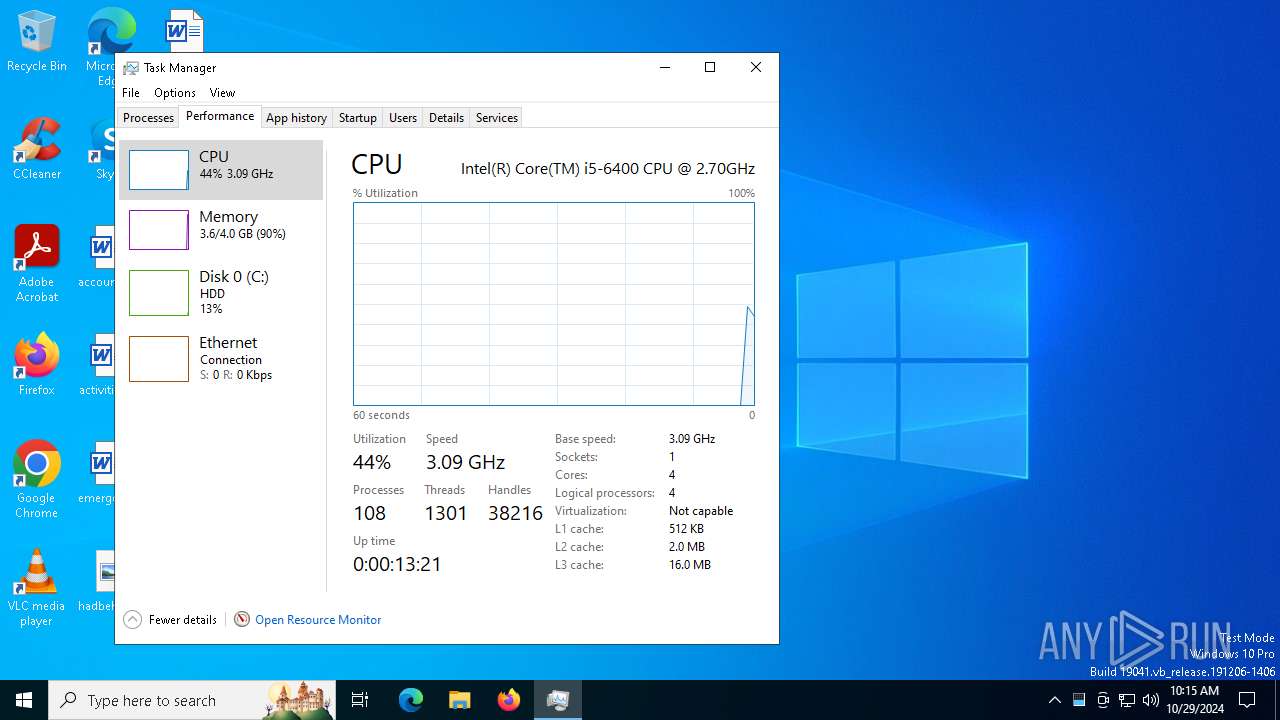
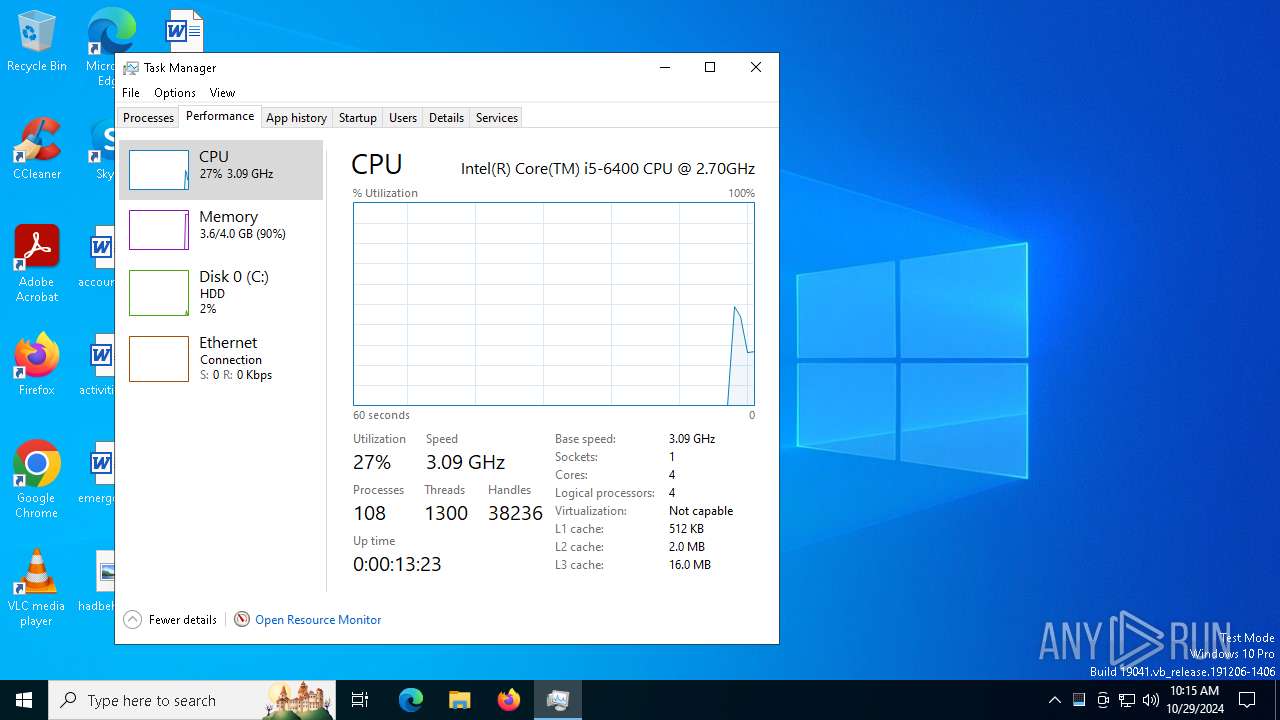
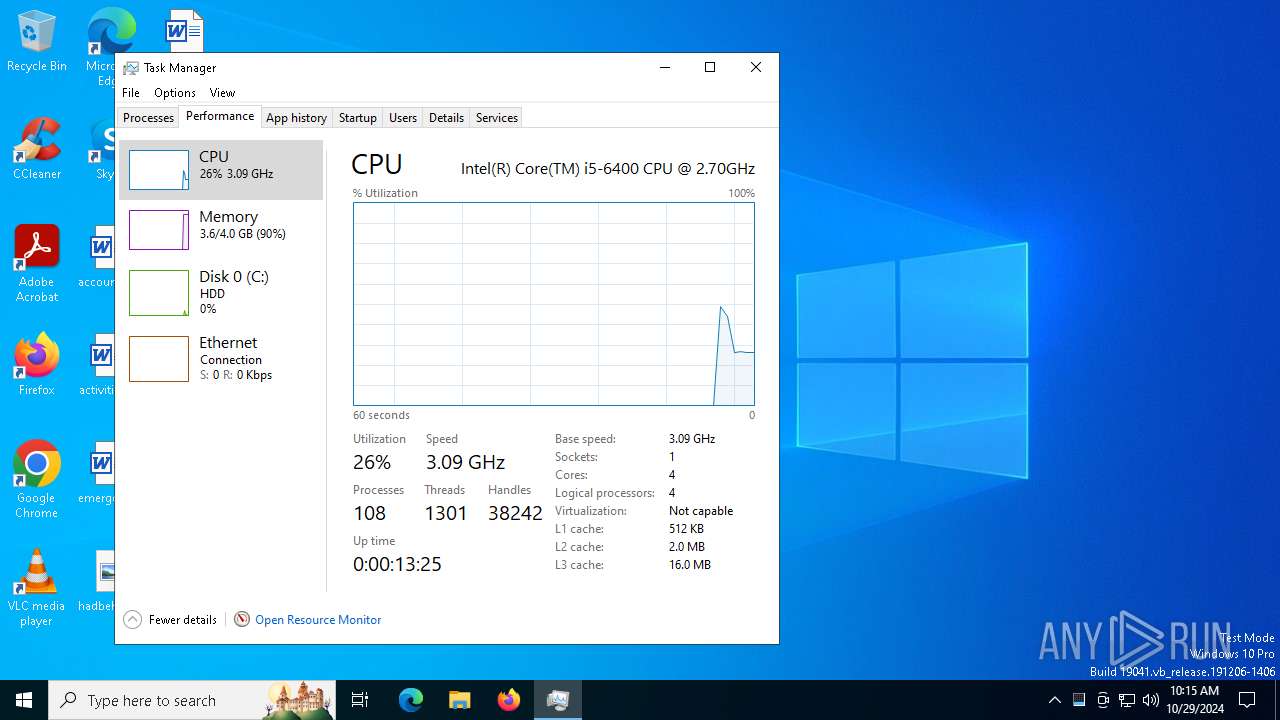
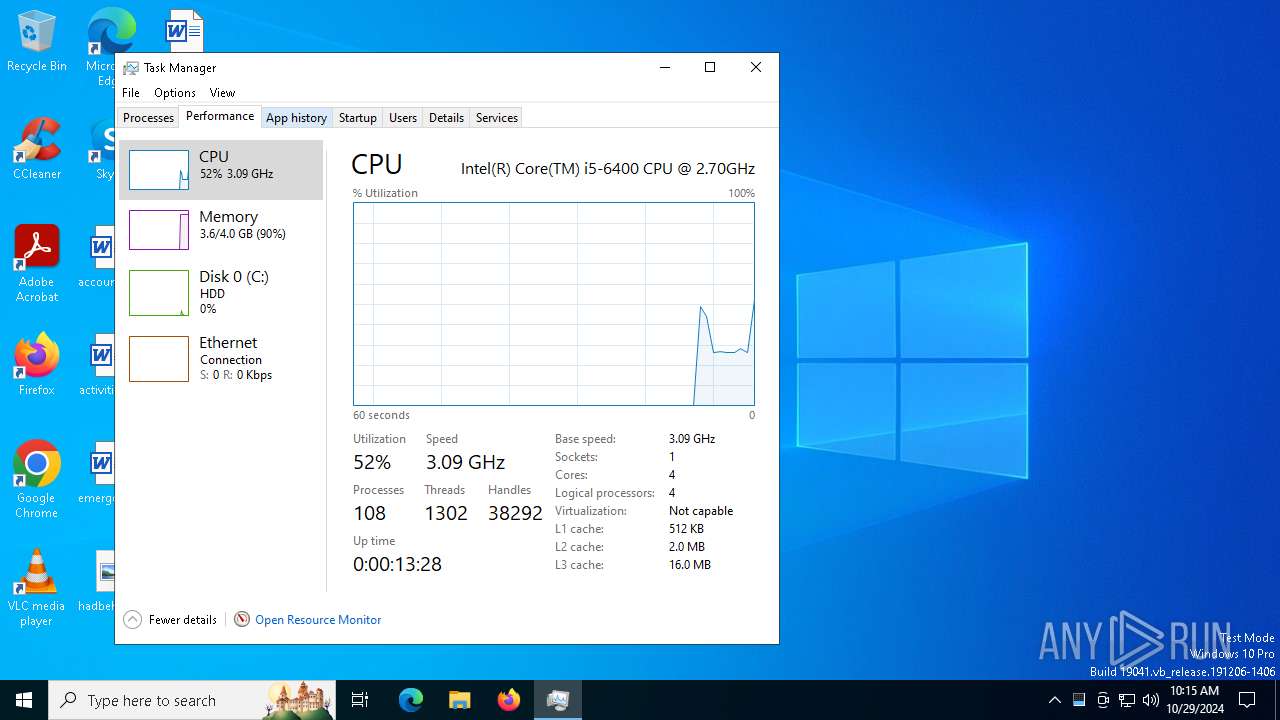
| Threats: | Crypto mining malware is a resource-intensive threat that infiltrates computers with the purpose of mining cryptocurrencies. This type of threat can be deployed either on an infected machine or a compromised website. In both cases the miner will utilize the computing power of the device and its network bandwidth. |
| Analysis date: | October 29, 2024, 10:11:13 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 3 sections |
| MD5: | 06560B5E92D704395BC6DAE58BC7E794 |
| SHA1: | FBD3E4AE28620197D1F02BFC24ADAF4DDACD2372 |
| SHA256: | 9EAAADF3857E4A3E83F4F78D96AB185213B6528C8E470807F9D16035DAADF33D |
| SSDEEP: | 3072:MI/hMNfDU6NP/mAyp/8+62bSKI2agc2yToeEnb6xaiHl4p9diPYRZWDvowFi61cX:uLAF1EK |
MALICIOUS
Changes the autorun value in the registry
- tdrpl[1].exe (PID: 6548)
Adds path to the Windows Defender exclusion list
- sysppvrdnvs.exe (PID: 5920)
- cmd.exe (PID: 5240)
- sysppvrdnvs.exe (PID: 6524)
- cmd.exe (PID: 1804)
Changes the Windows auto-update feature
- sysppvrdnvs.exe (PID: 5920)
Changes Security Center notification settings
- sysppvrdnvs.exe (PID: 5920)
PHORPIEX has been detected (SURICATA)
- sysppvrdnvs.exe (PID: 5920)
- sysppvrdnvs.exe (PID: 6524)
Connects to the CnC server
- sysppvrdnvs.exe (PID: 5920)
- dwm.exe (PID: 5640)
- sysppvrdnvs.exe (PID: 6524)
- dwm.exe (PID: 1244)
PHORPIEX has been detected (YARA)
- sysppvrdnvs.exe (PID: 5920)
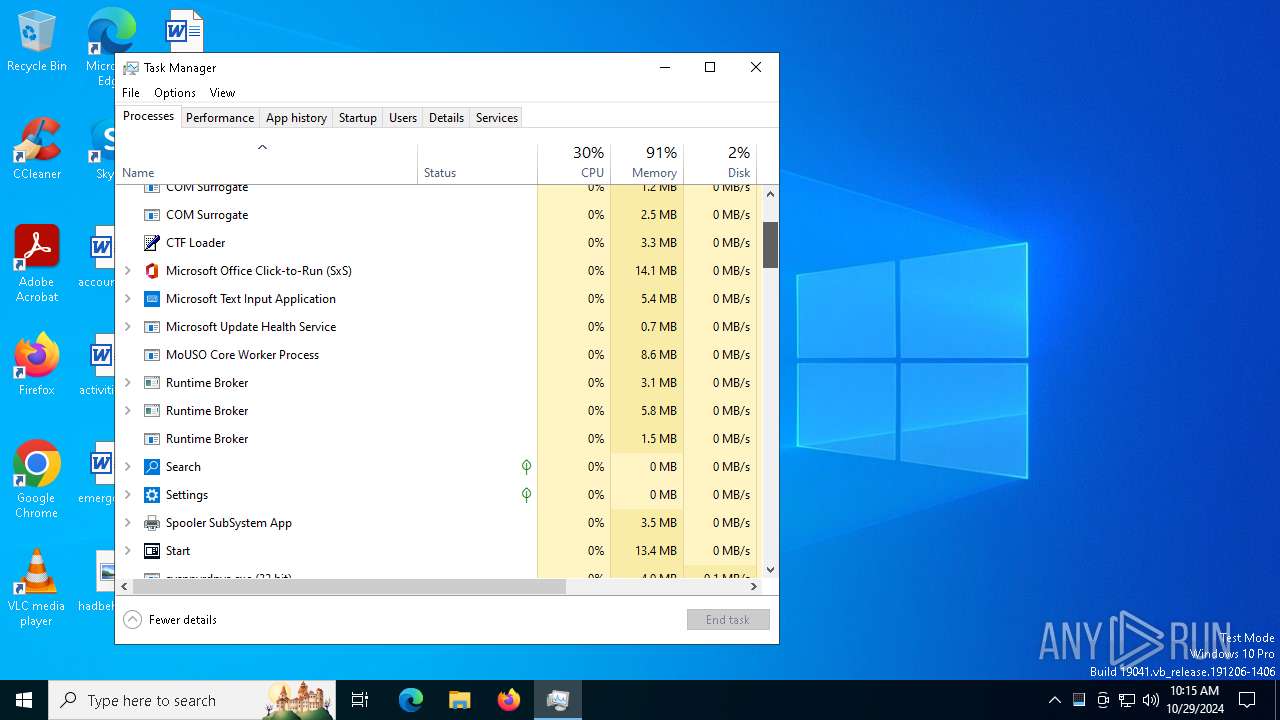
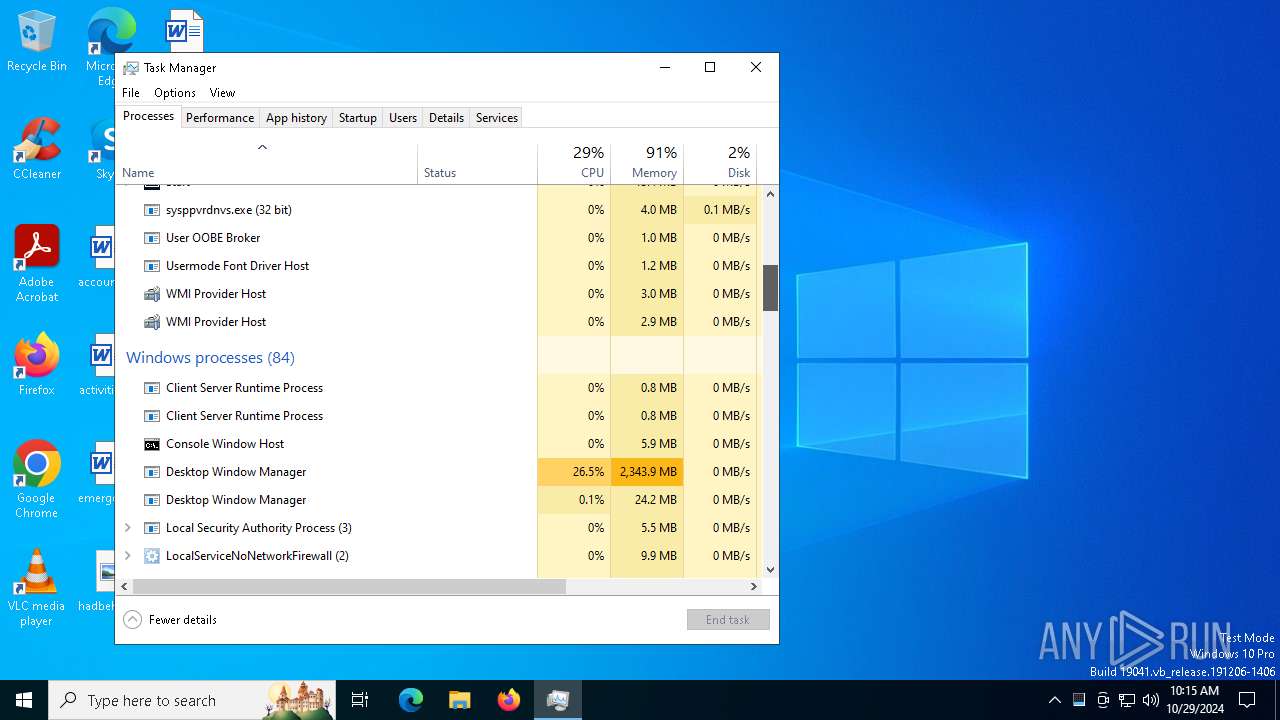
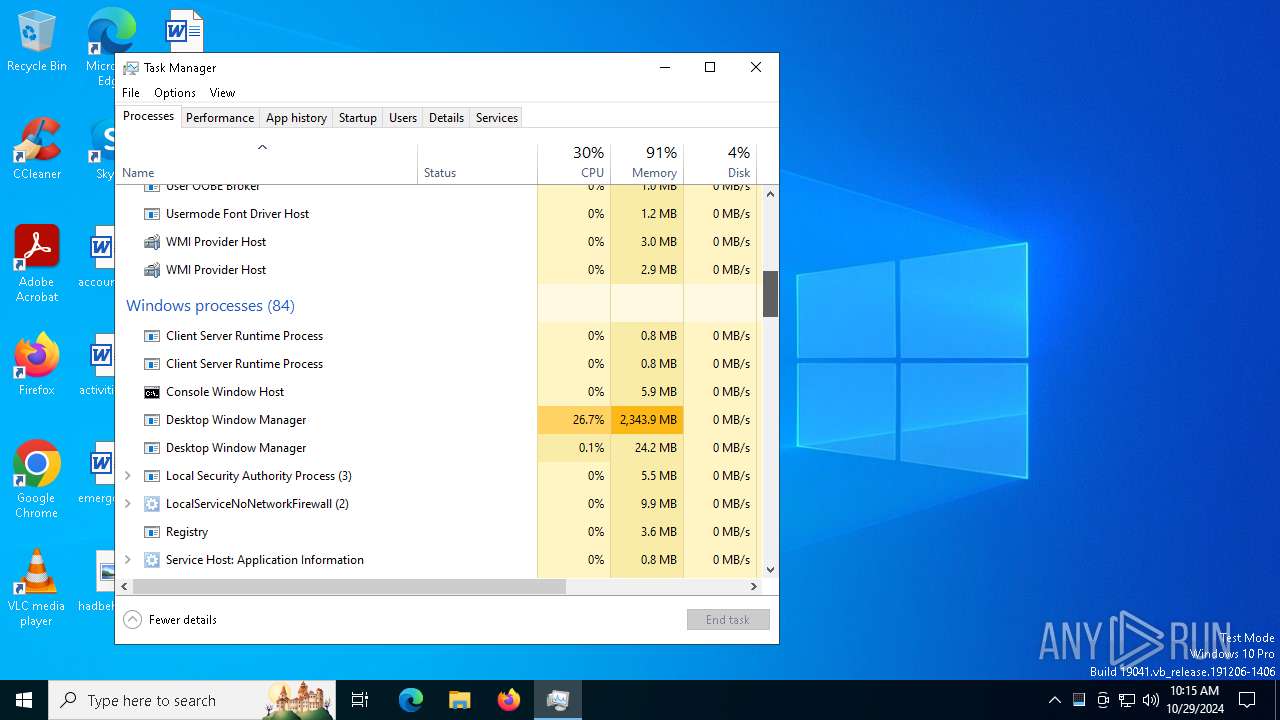
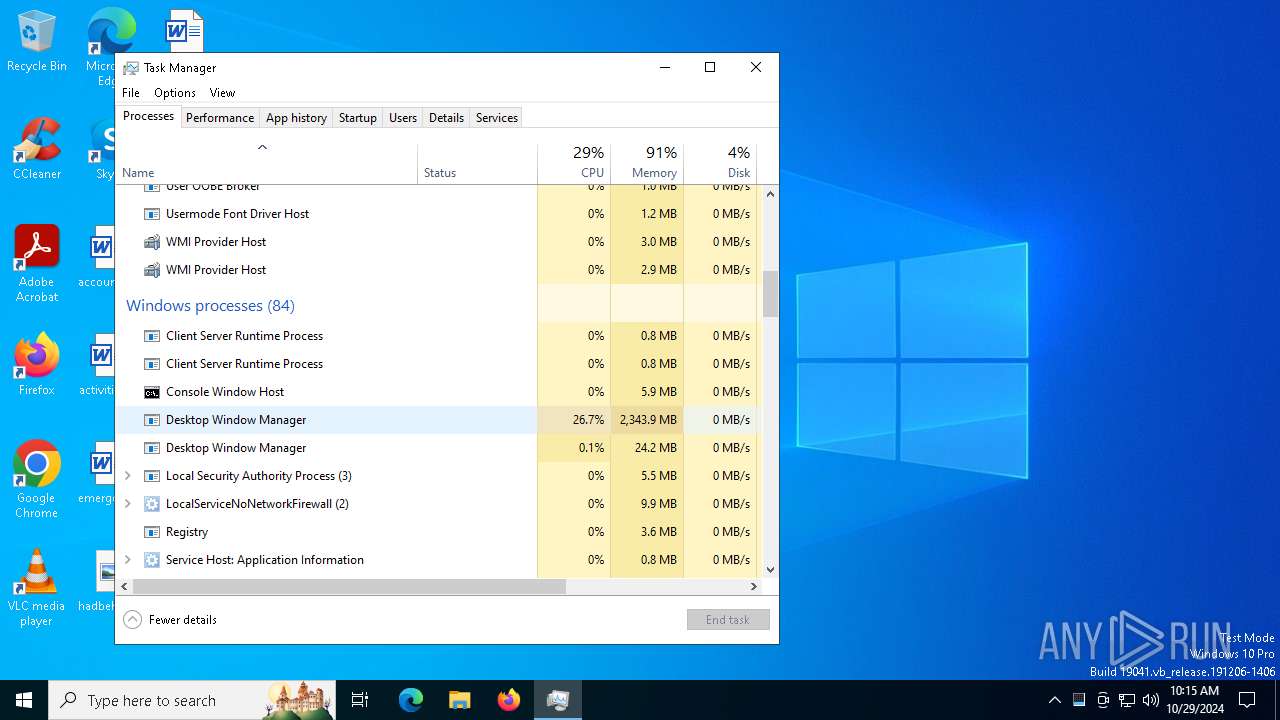
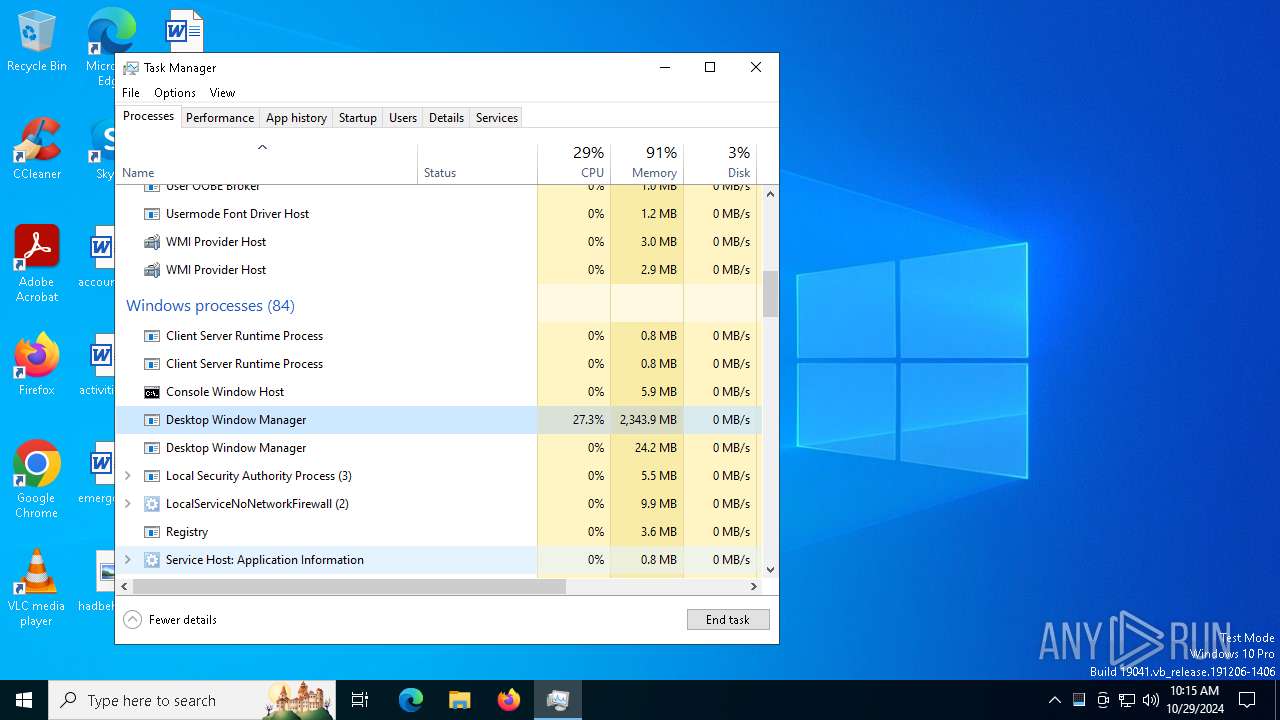
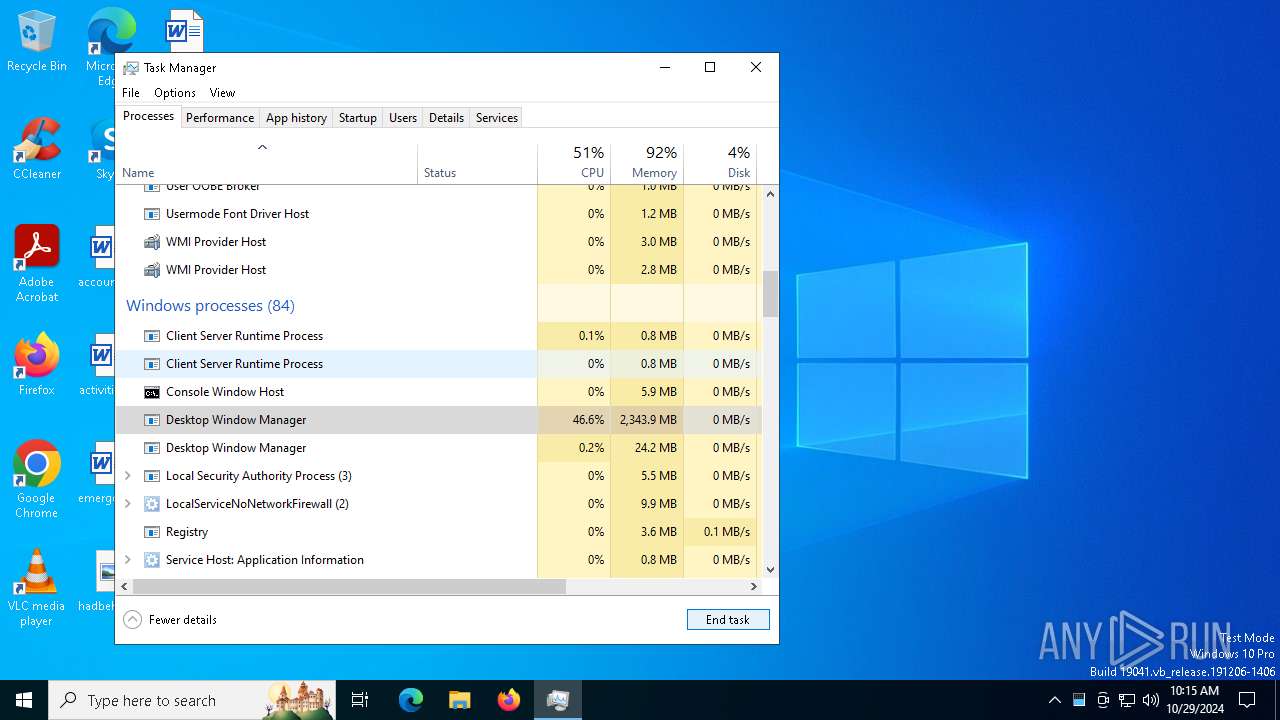
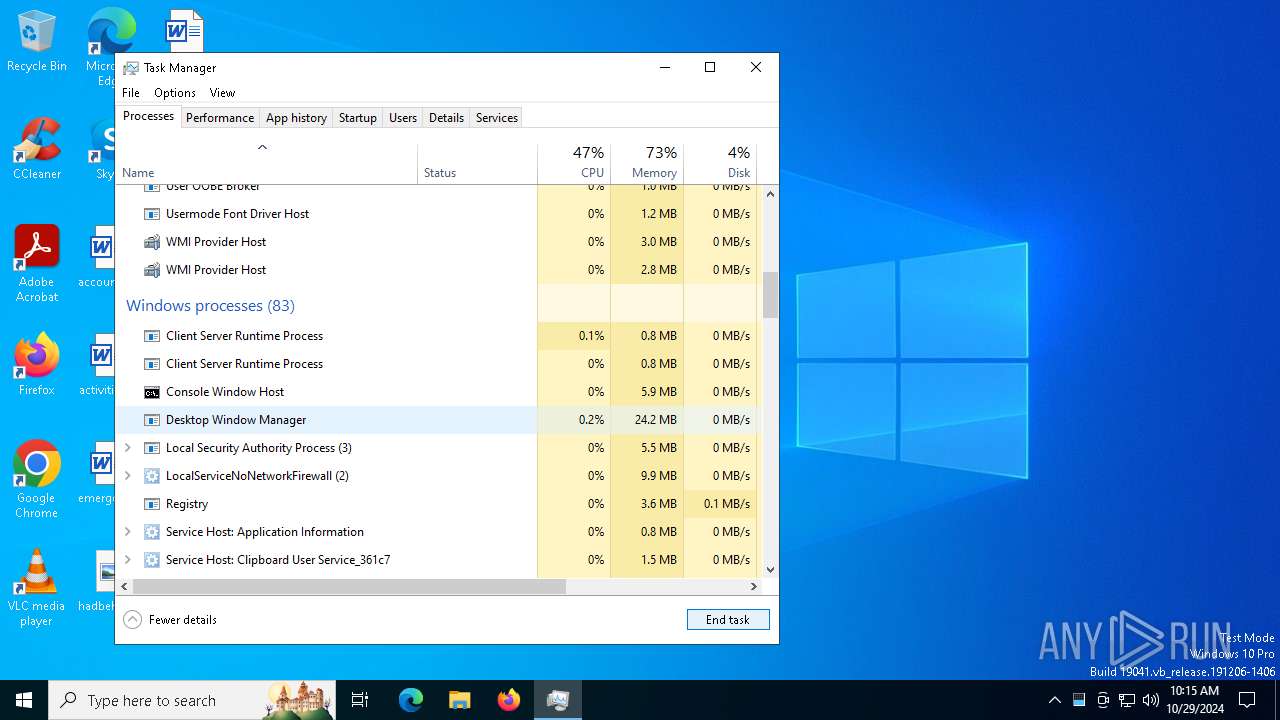
MINER has been detected (SURICATA)
- dwm.exe (PID: 5640)
- dwm.exe (PID: 1244)
SUSPICIOUS
Starts itself from another location
- tdrpl[1].exe (PID: 6548)
- sysppvrdnvs.exe (PID: 5920)
- 299155427.exe (PID: 1752)
Executable content was dropped or overwritten
- tdrpl[1].exe (PID: 6548)
- 1820919950.exe (PID: 2128)
- 1761226776.exe (PID: 6488)
- winupsecvmgr.exe (PID: 6984)
- 299155427.exe (PID: 1752)
- winupsecvmgr.exe (PID: 4032)
Starts CMD.EXE for commands execution
- sysppvrdnvs.exe (PID: 5920)
- 1281611328.exe (PID: 5328)
- sysppvrdnvs.exe (PID: 6524)
- 825714472.exe (PID: 6716)
Reads security settings of Internet Explorer
- sysppvrdnvs.exe (PID: 5920)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 5240)
- cmd.exe (PID: 1804)
Manipulates environment variables
- powershell.exe (PID: 5068)
- powershell.exe (PID: 6164)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 5240)
- cmd.exe (PID: 1804)
Connects to unusual port
- sysppvrdnvs.exe (PID: 5920)
- dwm.exe (PID: 5640)
- dwm.exe (PID: 1244)
- sysppvrdnvs.exe (PID: 6524)
Connects to the server without a host name
- sysppvrdnvs.exe (PID: 5920)
- 2938917736.exe (PID: 6644)
- 1761226776.exe (PID: 6488)
- sysppvrdnvs.exe (PID: 6524)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 2784)
- cmd.exe (PID: 7072)
Deletes scheduled task without confirmation
- schtasks.exe (PID: 3020)
- schtasks.exe (PID: 300)
Process requests binary or script from the Internet
- 1761226776.exe (PID: 6488)
Potential Corporate Privacy Violation
- 1761226776.exe (PID: 6488)
- dwm.exe (PID: 5640)
- dwm.exe (PID: 1244)
Drops a system driver (possible attempt to evade defenses)
- winupsecvmgr.exe (PID: 6984)
Crypto Currency Mining Activity Detected
- dwm.exe (PID: 5640)
INFO
The process uses the downloaded file
- tdrpl[1].exe (PID: 6548)
- sysppvrdnvs.exe (PID: 5920)
Checks supported languages
- sysppvrdnvs.exe (PID: 5920)
- tdrpl[1].exe (PID: 6548)
Reads the computer name
- sysppvrdnvs.exe (PID: 5920)
Process checks computer location settings
- sysppvrdnvs.exe (PID: 5920)
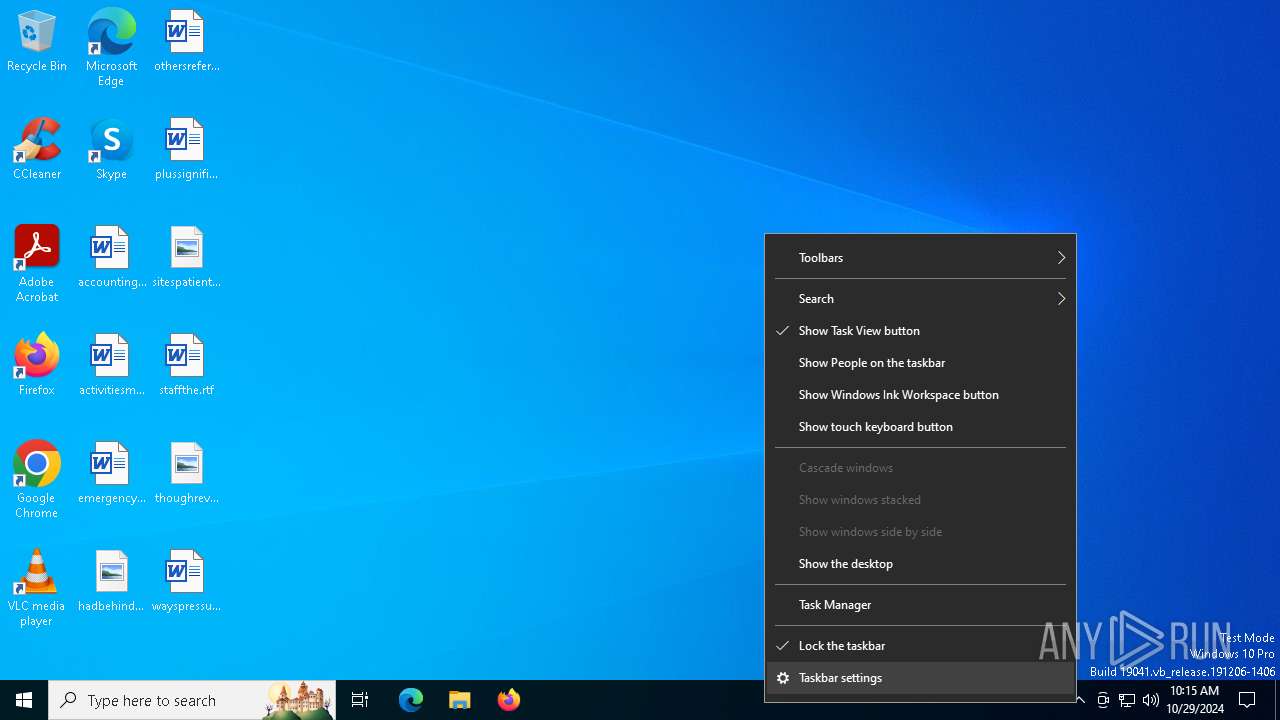
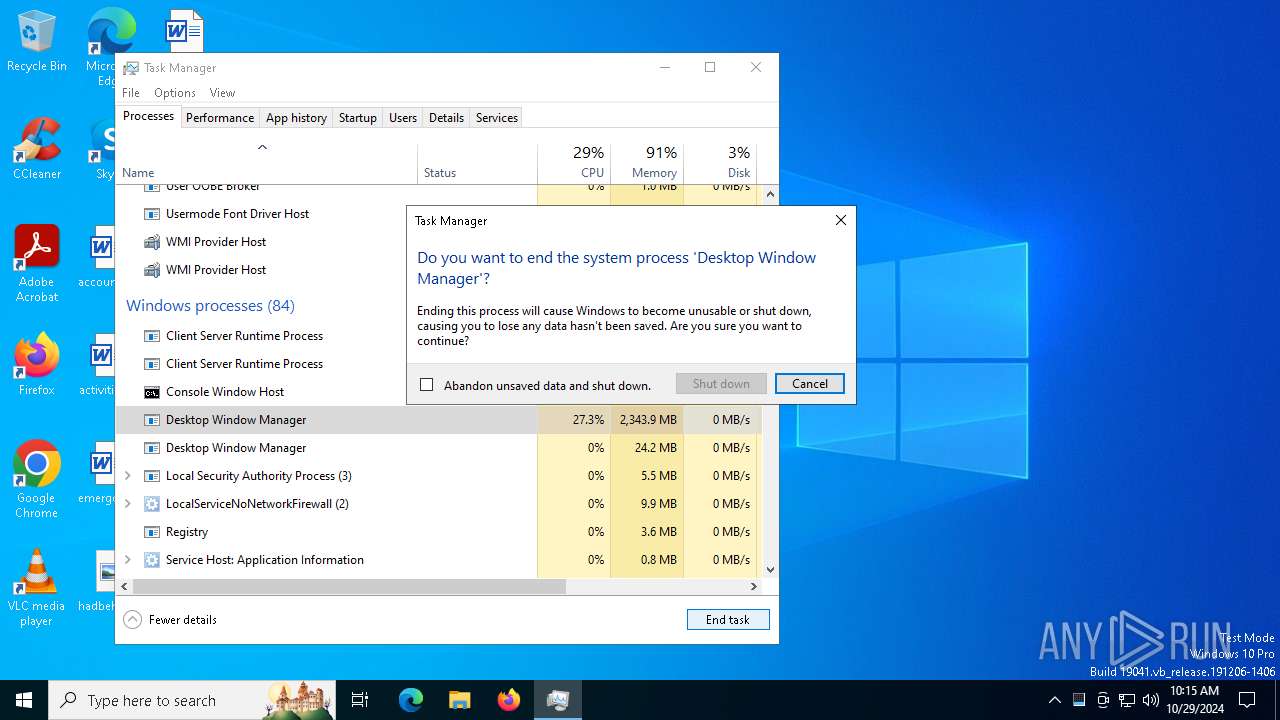
Manual execution by a user
- conhost.exe (PID: 6940)
- reg.exe (PID: 4292)
- reg.exe (PID: 6564)
- dwm.exe (PID: 5640)
- winupsecvmgr.exe (PID: 6984)
- Taskmgr.exe (PID: 3832)
- Taskmgr.exe (PID: 5828)
- winupsecvmgr.exe (PID: 4032)
- reg.exe (PID: 4548)
- reg.exe (PID: 6480)
- dwm.exe (PID: 1244)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:10:10 07:39:16+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 60928 |
| InitializedDataSize: | 28672 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x7940 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
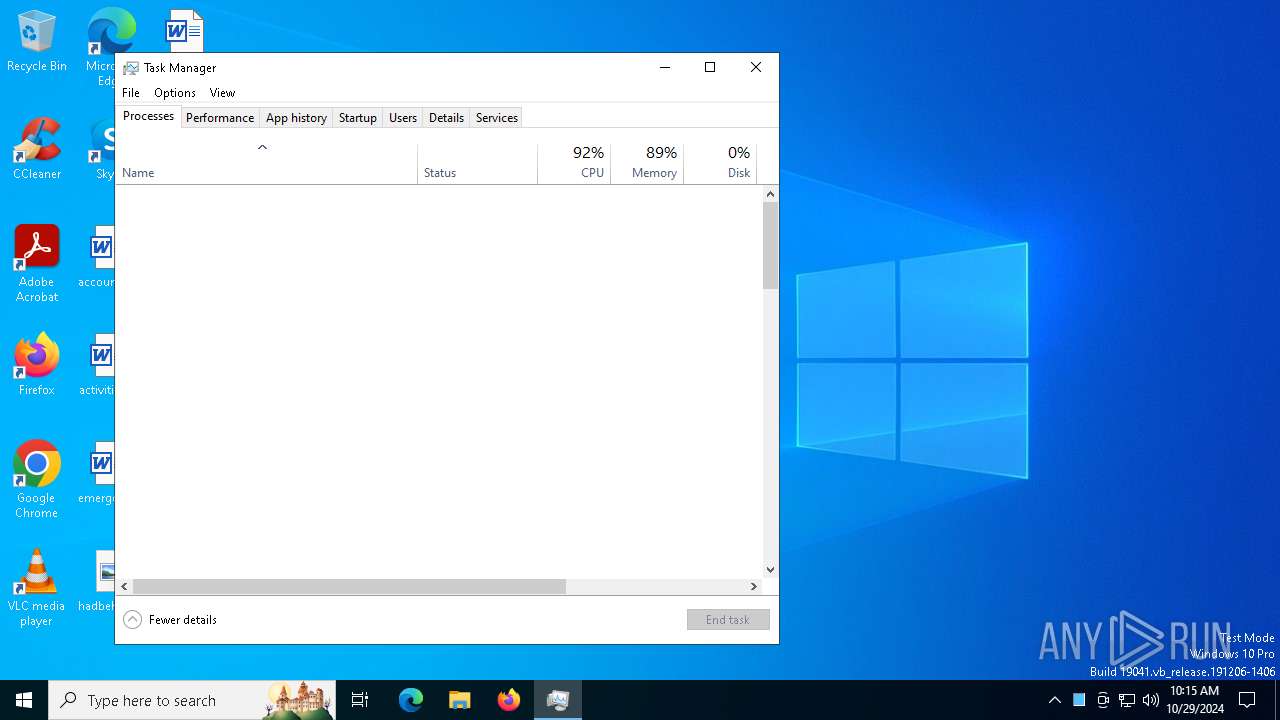
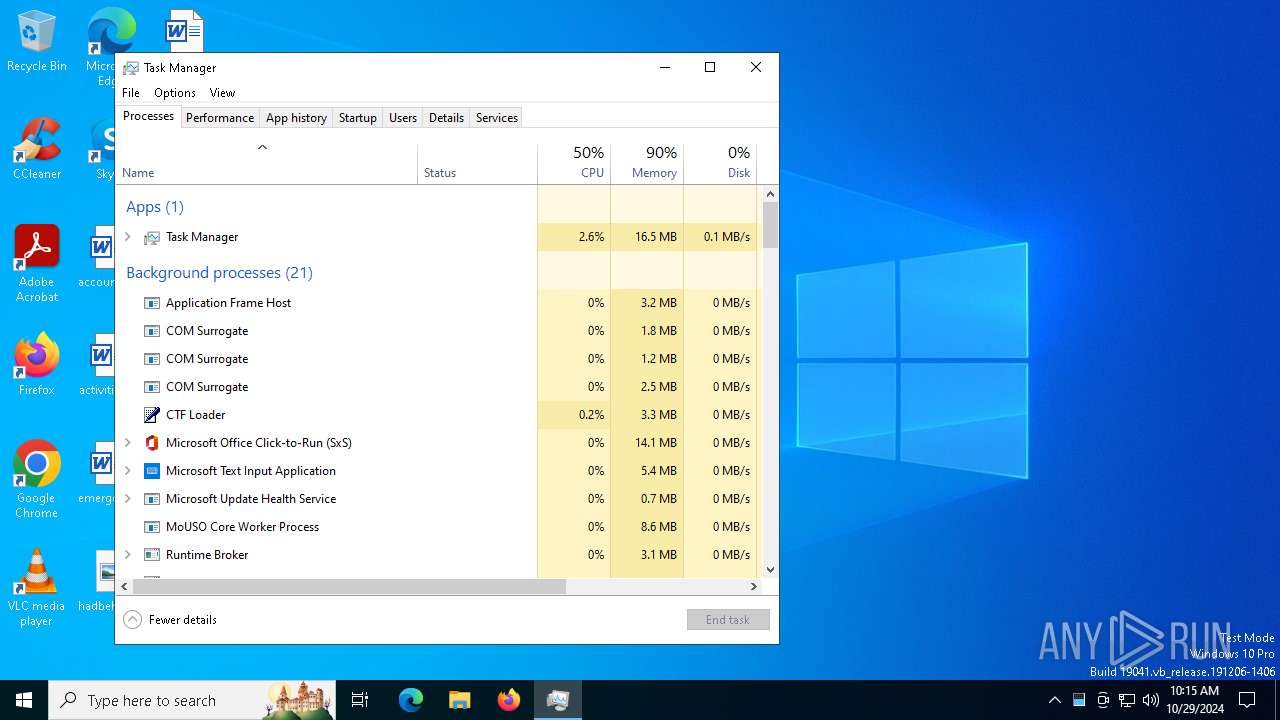
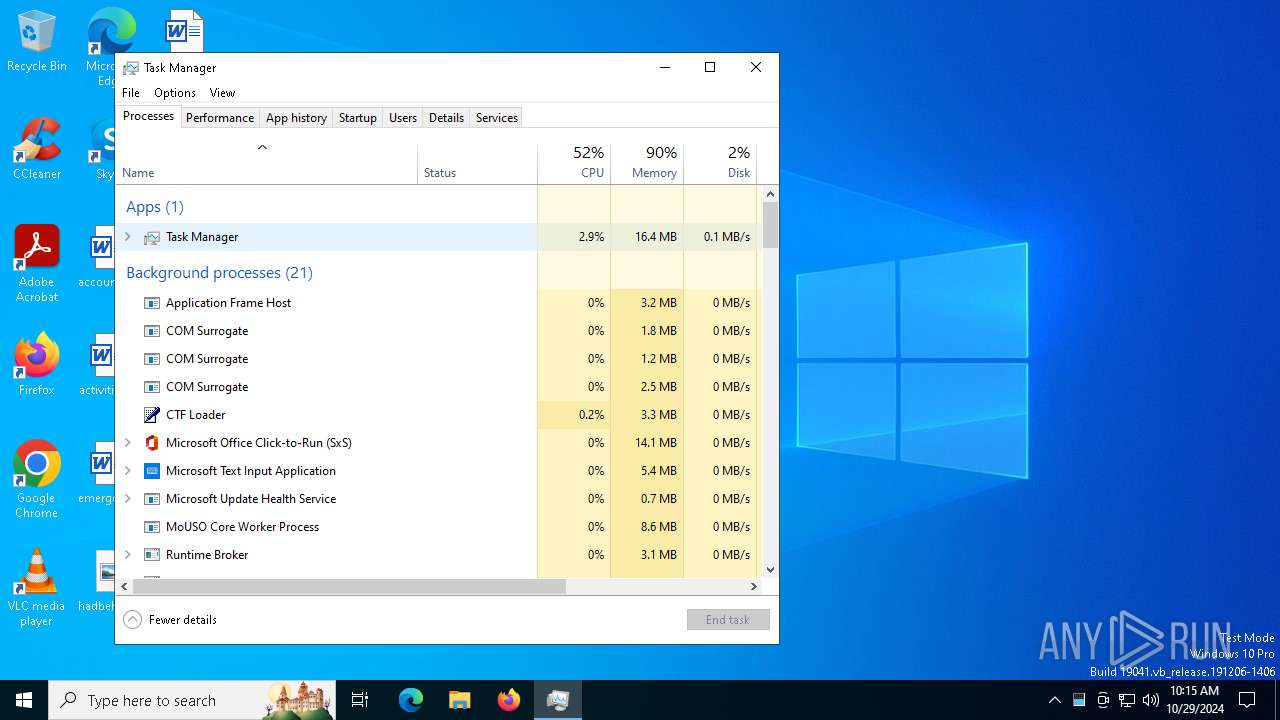
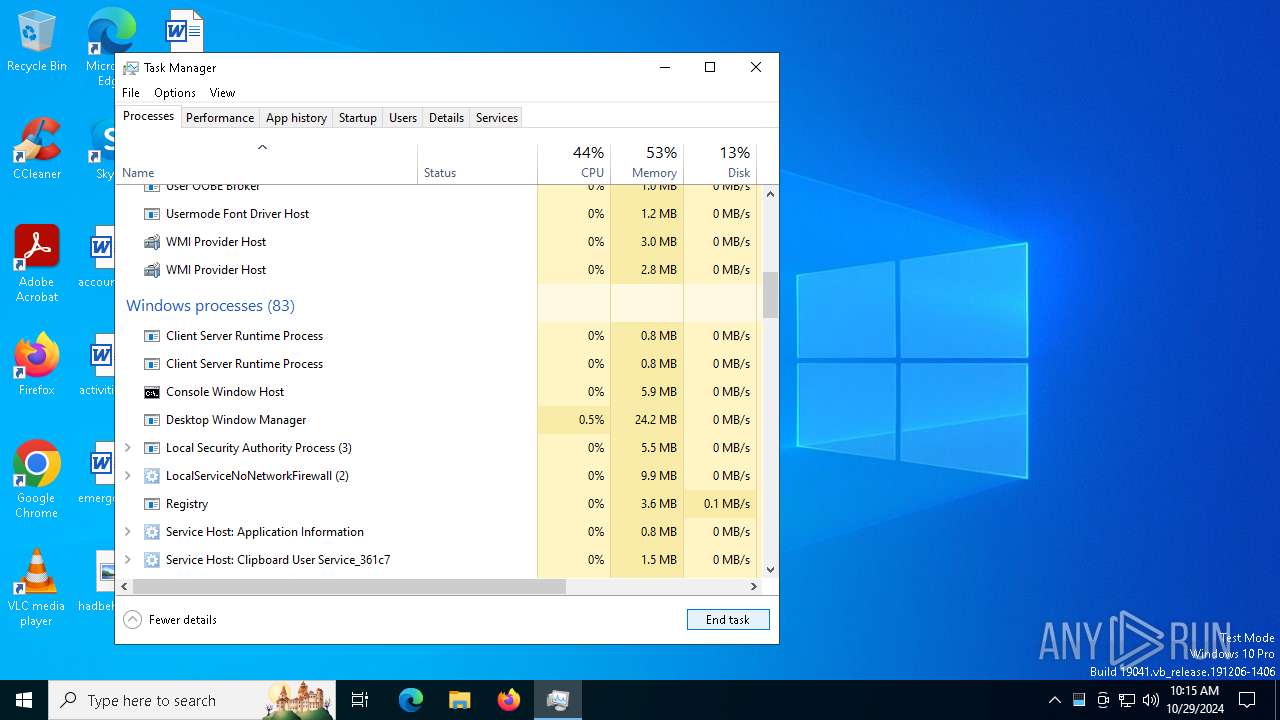
Total processes
209
Monitored processes
62
Malicious processes
5
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 300 | schtasks /delete /f /tn "Windows Upgrade Manager" | C:\Windows\System32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 916 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 948 | sc stop BITS /wait | C:\Windows\SysWOW64\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Service Control Manager Configuration Tool Exit code: 5 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1048 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1244 | C:\WINDOWS\System32\dwm.exe | C:\Windows\System32\dwm.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Desktop Window Manager Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1336 | sc stop WaaSMedicSvc | C:\Windows\SysWOW64\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Service Control Manager Configuration Tool Exit code: 5 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1452 | sc stop UsoSvc | C:\Windows\SysWOW64\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Service Control Manager Configuration Tool Exit code: 5 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1748 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1752 | C:\Users\admin\AppData\Local\Temp\299155427.exe | C:\Users\admin\AppData\Local\Temp\299155427.exe | sysppvrdnvs.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1804 | "C:\Windows\System32\cmd.exe" /c powershell -Command "Add-MpPreference -ExclusionPath $env:windir; Add-MpPreference -ExclusionPath $env:TEMP; Add-MpPreference -ExclusionPath $env:USERPROFILE" | C:\Windows\SysWOW64\cmd.exe | — | sysppvrdnvs.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
23 949
Read events
23 893
Write events
42
Delete events
14
Modification events
| (PID) Process: | (6548) tdrpl[1].exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Windows Settings |
Value: C:\Users\admin\sysppvrdnvs.exe | |||
| (PID) Process: | (5920) sysppvrdnvs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows\WindowsUpdate |
| Operation: | write | Name: | DisableWindowsUpdate |
Value: 1 | |||
| (PID) Process: | (5920) sysppvrdnvs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows\WindowsUpdate\AU |
| Operation: | write | Name: | NoAutoUpdate |
Value: 1 | |||
| (PID) Process: | (5920) sysppvrdnvs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows\WindowsUpdate\AU |
| Operation: | write | Name: | AlwaysAutoUpdate |
Value: 0 | |||
| (PID) Process: | (5920) sysppvrdnvs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows\WindowsUpdate\AU |
| Operation: | write | Name: | OverrideNotice |
Value: 1 | |||
| (PID) Process: | (5920) sysppvrdnvs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Security Center |
| Operation: | write | Name: | FirewallOverride |
Value: 1 | |||
| (PID) Process: | (5920) sysppvrdnvs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Security Center |
| Operation: | write | Name: | FirewallDisableNotify |
Value: 1 | |||
| (PID) Process: | (5920) sysppvrdnvs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Security Center |
| Operation: | write | Name: | AntiSpywareOverride |
Value: 1 | |||
| (PID) Process: | (5920) sysppvrdnvs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Security Center |
| Operation: | write | Name: | AntiVirusOverride |
Value: 1 | |||
| (PID) Process: | (5920) sysppvrdnvs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Security Center |
| Operation: | write | Name: | AntiVirusDisableNotify |
Value: 1 | |||
Executable files
9
Suspicious files
25
Text files
9
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5068 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_z0n5g02t.0hb.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6548 | tdrpl[1].exe | C:\Users\admin\sysppvrdnvs.exe | executable | |
MD5:06560B5E92D704395BC6DAE58BC7E794 | SHA256:9EAAADF3857E4A3E83F4F78D96AB185213B6528C8E470807F9D16035DAADF33D | |||
| 5920 | sysppvrdnvs.exe | C:\Users\admin\AppData\Local\Temp\556829747.exe | binary | |
MD5:1FCB78FB6CF9720E9D9494C42142D885 | SHA256:84652BB8C63CA4FD7EB7A2D6EF44029801F3057AA2961867245A3A765928DD02 | |||
| 5068 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_yenpgukt.drf.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5920 | sysppvrdnvs.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\AH8CR9J5\1[1] | binary | |
MD5:1FCB78FB6CF9720E9D9494C42142D885 | SHA256:84652BB8C63CA4FD7EB7A2D6EF44029801F3057AA2961867245A3A765928DD02 | |||
| 5068 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:131D663ECBC1405E9E9EFA3097711447 | SHA256:F07DEB997019C3E15C71210CF88F65A796338A06E640FAEA8F4AC4C8877009D0 | |||
| 5920 | sysppvrdnvs.exe | C:\Users\admin\AppData\Local\Temp\1761226776.exe | binary | |
MD5:2266F0AECD351E1B4092E82B941211EA | SHA256:CBBAD0AB02CD973C9C4E73336E3BCD0849AEB2232A7BDBC38F0B50696B5C28C3 | |||
| 5920 | sysppvrdnvs.exe | C:\Users\admin\AppData\Local\Temp\119407321.exe | binary | |
MD5:1FCB78FB6CF9720E9D9494C42142D885 | SHA256:84652BB8C63CA4FD7EB7A2D6EF44029801F3057AA2961867245A3A765928DD02 | |||
| 5068 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_4xj0z2xv.k15.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6488 | 1761226776.exe | C:\Users\admin\AppData\Local\Temp\1820919950.exe | executable | |
MD5:13B26B2C7048A92D6A843C1302618FAD | SHA256:1753AD35ECE25AB9A19048C70062E9170F495E313D7355EBBBA59C38F5D90256 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
127
DNS requests
25
Threats
70
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5920 | sysppvrdnvs.exe | GET | — | 185.215.113.66:80 | http://185.215.113.66/1 | unknown | — | — | malicious |
7028 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5920 | sysppvrdnvs.exe | GET | 200 | 185.215.113.66:80 | http://185.215.113.66/1 | unknown | — | — | malicious |
5488 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6860 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6860 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5920 | sysppvrdnvs.exe | GET | — | 185.215.113.66:80 | http://185.215.113.66/3 | unknown | — | — | malicious |
5920 | sysppvrdnvs.exe | GET | 200 | 185.215.113.66:80 | http://185.215.113.66/4 | unknown | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6944 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1752 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5488 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4360 | SearchApp.exe | 104.126.37.160:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4360 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7028 | svchost.exe | 40.126.32.140:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
7028 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
5920 | sysppvrdnvs.exe | 185.215.113.66:80 | twizthash.net | 1337team Limited | SC | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
th.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5920 | sysppvrdnvs.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 32 |
5920 | sysppvrdnvs.exe | A Network Trojan was detected | ET MALWARE Win32/Phorpiex UDP Peer-to-Peer CnC |
5920 | sysppvrdnvs.exe | A Network Trojan was detected | ET MALWARE Win32/Phorpiex UDP Peer-to-Peer CnC |
5920 | sysppvrdnvs.exe | A Network Trojan was detected | ET MALWARE Win32/Phorpiex UDP Peer-to-Peer CnC |
5920 | sysppvrdnvs.exe | A Network Trojan was detected | ET MALWARE Win32/Phorpiex UDP Peer-to-Peer CnC |
5920 | sysppvrdnvs.exe | A Network Trojan was detected | ET MALWARE Win32/Phorpiex UDP Peer-to-Peer CnC |
5920 | sysppvrdnvs.exe | A Network Trojan was detected | ET MALWARE Win32/Phorpiex UDP Peer-to-Peer CnC |
5920 | sysppvrdnvs.exe | A Network Trojan was detected | ET MALWARE Win32/Phorpiex UDP Peer-to-Peer CnC |
5920 | sysppvrdnvs.exe | A Network Trojan was detected | ET MALWARE Win32/Phorpiex UDP Peer-to-Peer CnC |
5920 | sysppvrdnvs.exe | A Network Trojan was detected | ET MALWARE Win32/Phorpiex UDP Peer-to-Peer CnC |
25 ETPRO signatures available at the full report