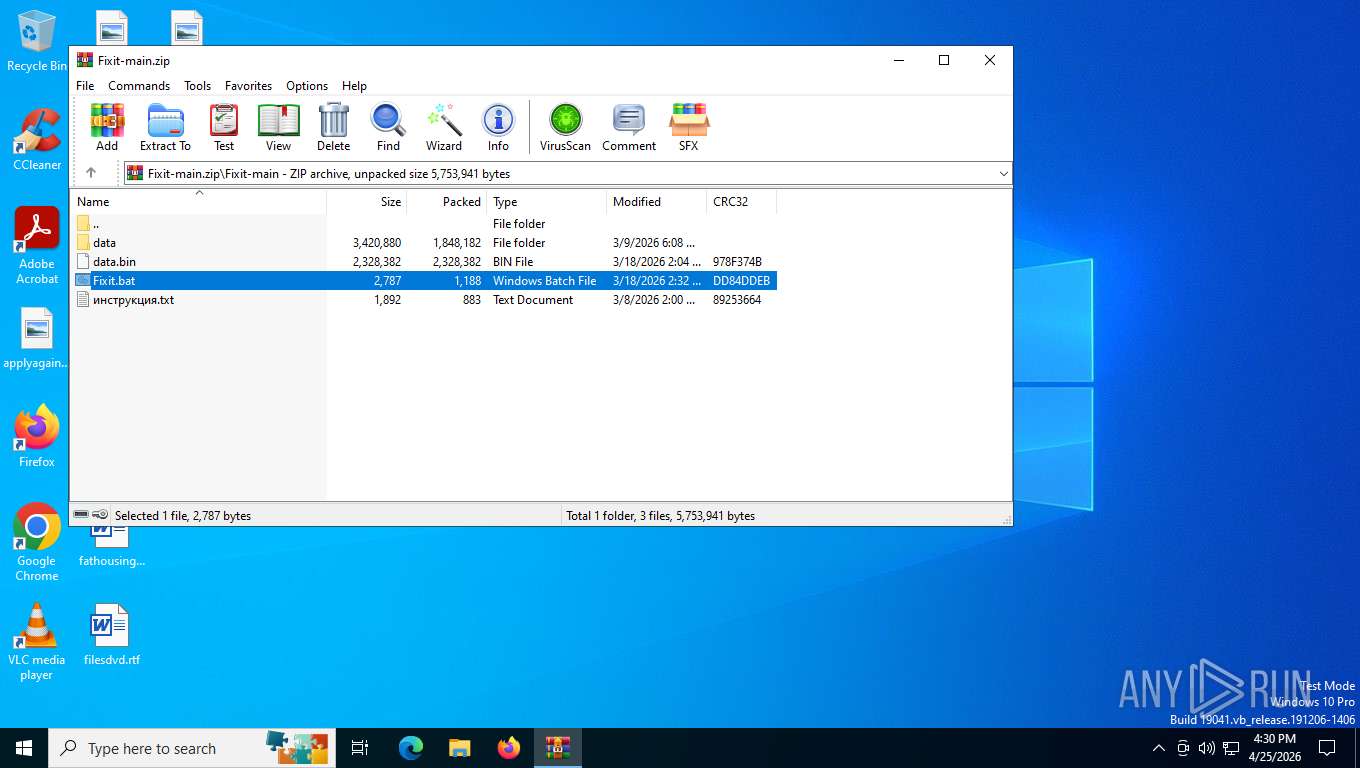
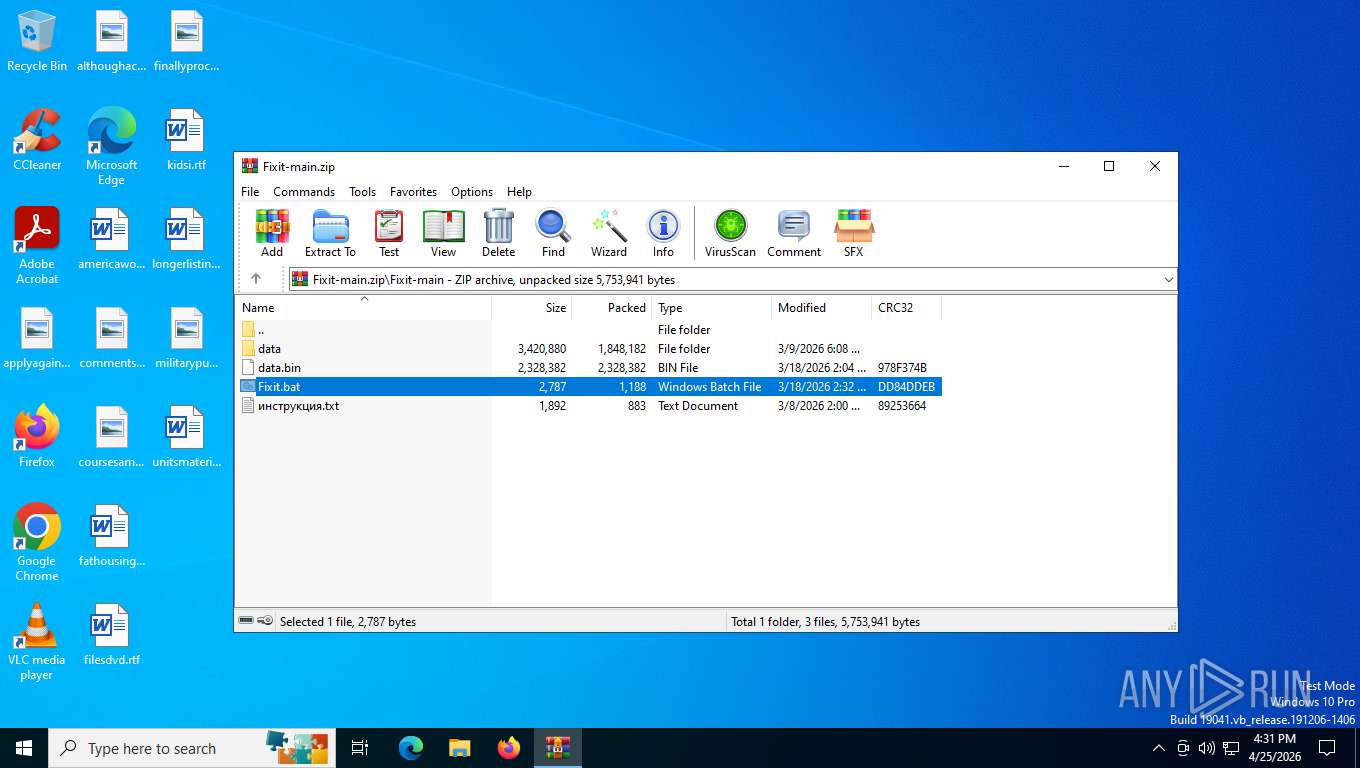
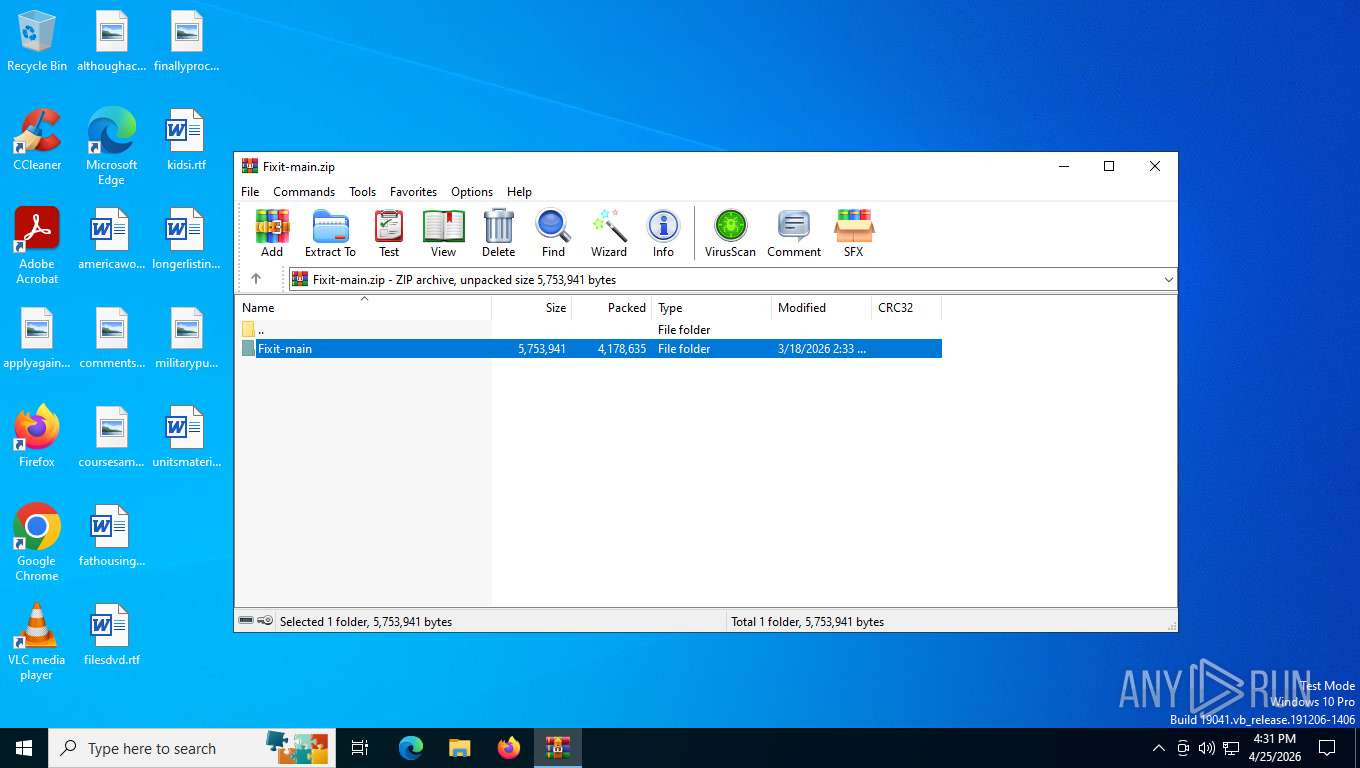
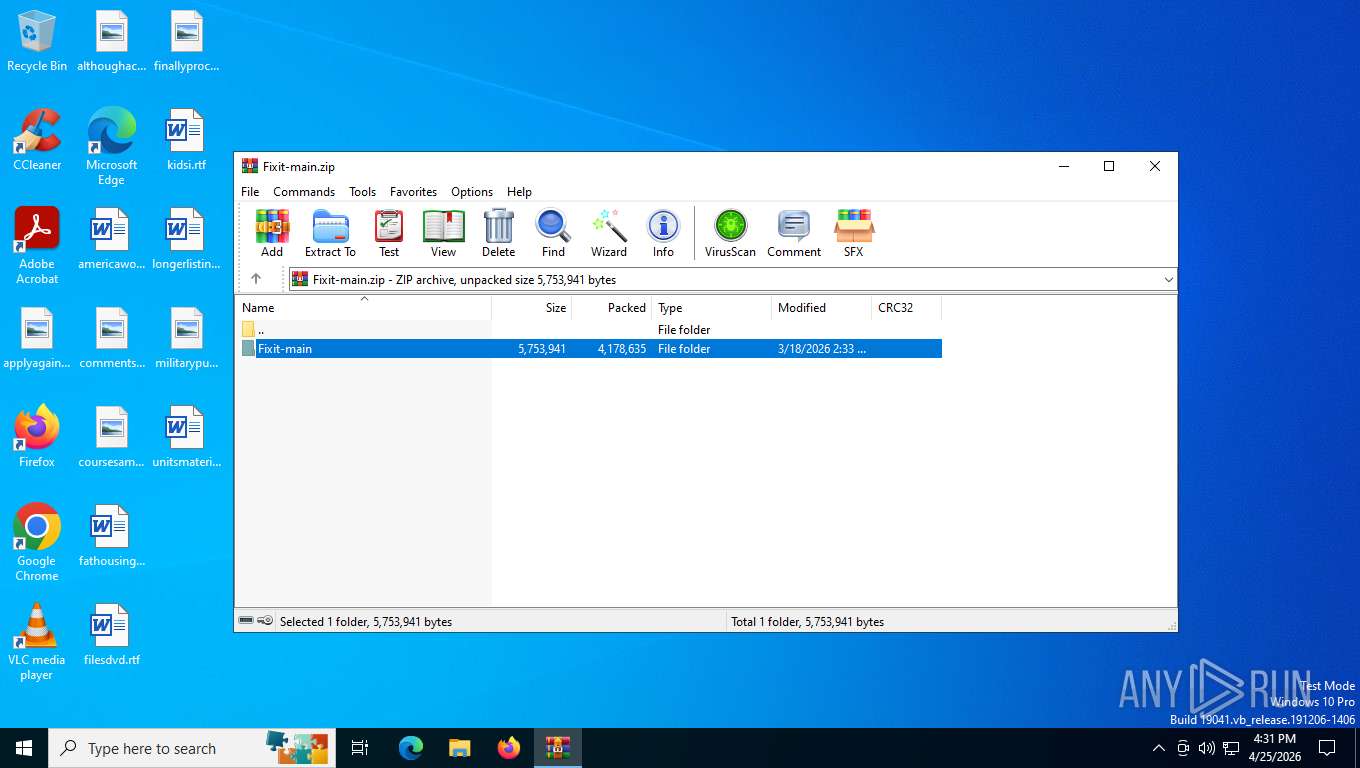
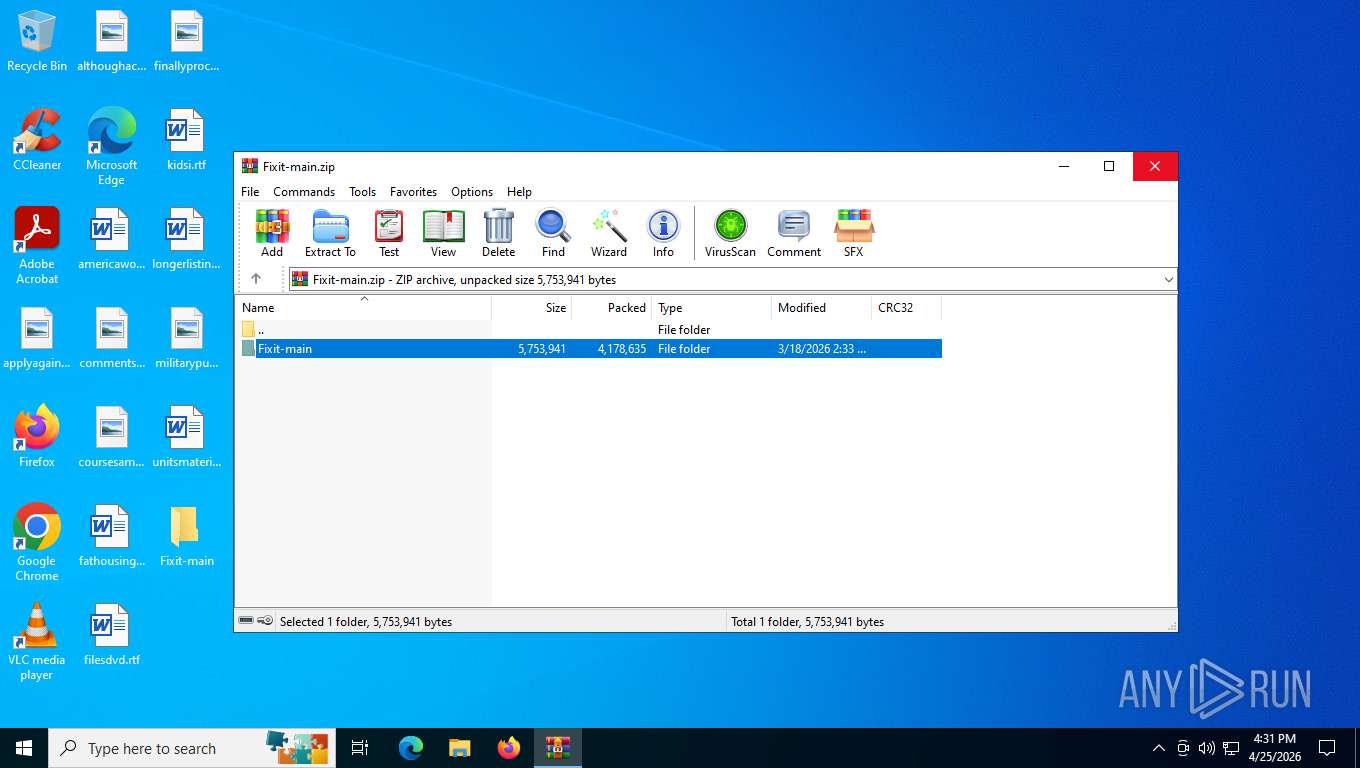
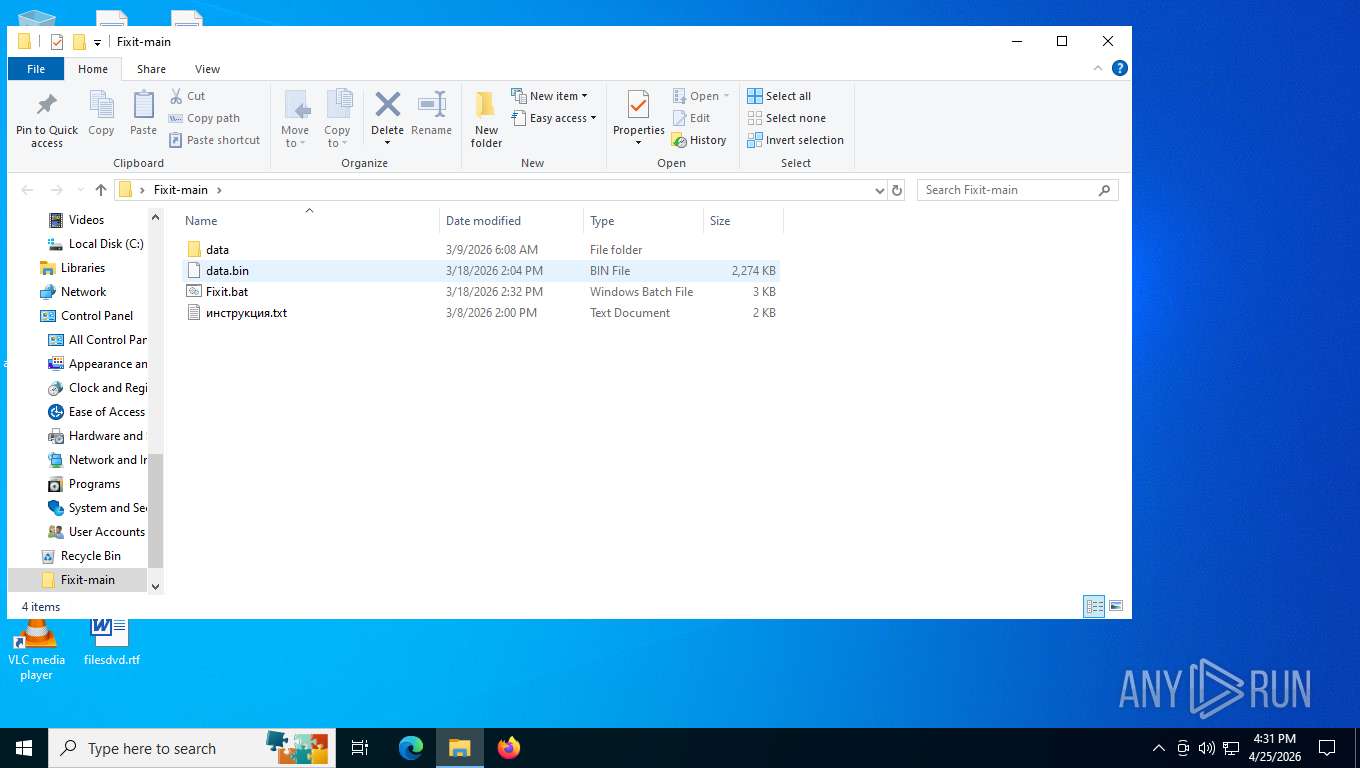
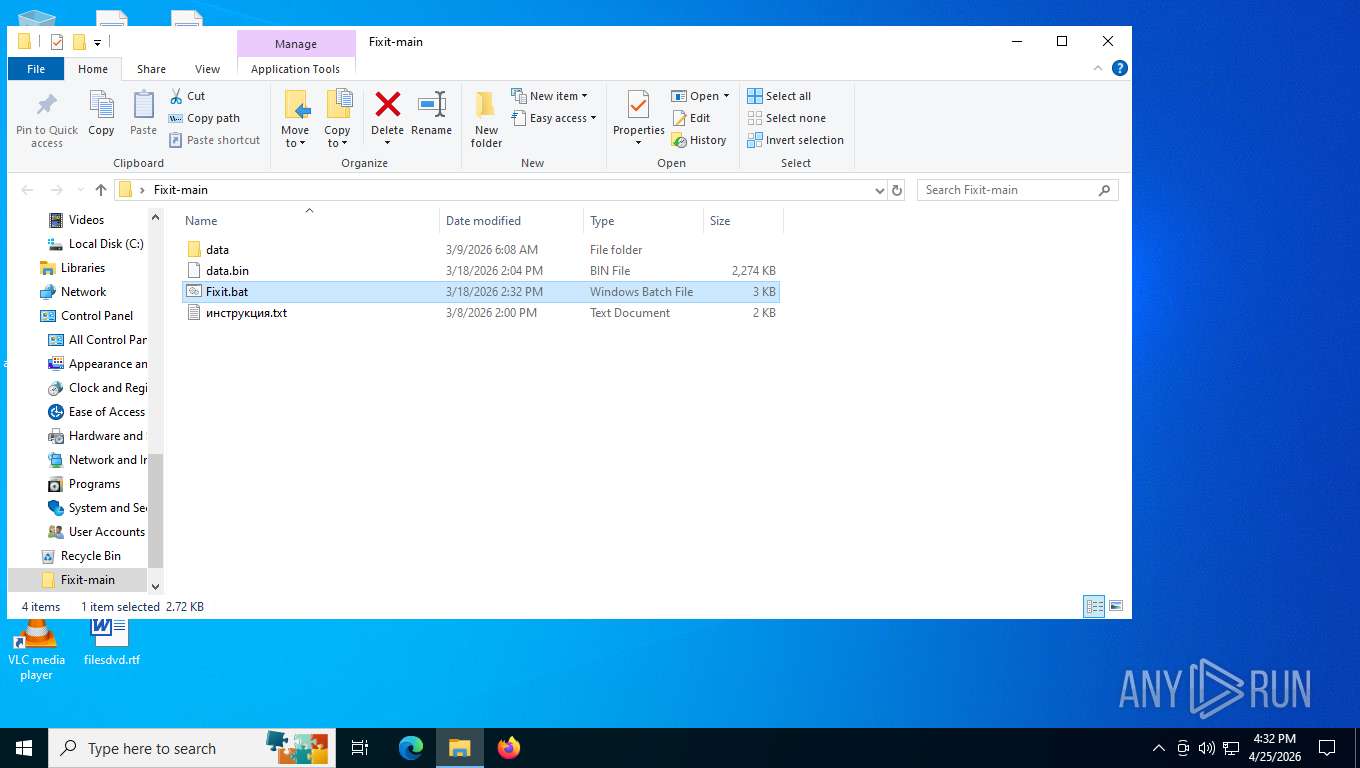
| File name: | Fixit-main.zip |
| Full analysis: | https://app.any.run/tasks/fe0955fd-958d-48bb-aeb8-f5912a67134a |
| Verdict: | Malicious activity |
| Threats: | Crypto mining malware is a resource-intensive threat that infiltrates computers with the purpose of mining cryptocurrencies. This type of threat can be deployed either on an infected machine or a compromised website. In both cases the miner will utilize the computing power of the device and its network bandwidth. |
| Analysis date: | April 25, 2026, 20:30:27 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=store |
| MD5: | 626F176217E8227E2120AE933A7D5C04 |
| SHA1: | 5138841AF39428D44A53458B6757FF5BDDC37153 |
| SHA256: | 9E97EC1BA22DA414C73F768C0B786396EB86D0B216402B7714359A15959BAC2C |
| SSDEEP: | 98304:SsVmWkAPEIS67vSVZ9A+gZtkPaSZXYxWIWqg4hR/AcxyJNumhO+ptWpDmoBnys1x:Si5rF9dK2 |
MALICIOUS
Run PowerShell with an invisible window
- powershell.exe (PID: 5748)
Changes Windows Defender settings
- cmd.exe (PID: 7604)
- update.exe (PID: 3696)
- gmstcccpdzbb.exe (PID: 8068)
Adds path to the Windows Defender exclusion list
- cmd.exe (PID: 7604)
Executing a file with an untrusted certificate
- update.exe (PID: 3696)
- gmstcccpdzbb.exe (PID: 8068)
Uninstalls Malicious Software Removal Tool (MRT)
- cmd.exe (PID: 5616)
- cmd.exe (PID: 3152)
XMRIG has been detected
- update.exe (PID: 3696)
- gmstcccpdzbb.exe (PID: 8068)
Adds extension to the Windows Defender exclusion list
- update.exe (PID: 3696)
- gmstcccpdzbb.exe (PID: 8068)
MINER has been detected (SURICATA)
- svchost.exe (PID: 2232)
Vulnerable driver has been detected
- gmstcccpdzbb.exe (PID: 8068)
XMRIG has been detected (YARA)
- svchost.exe (PID: 7240)
SUSPICIOUS
Starts CMD.EXE for commands execution
- cmd.exe (PID: 2692)
- cmd.exe (PID: 7604)
- cmd.exe (PID: 7596)
- cmd.exe (PID: 5616)
- cmd.exe (PID: 6384)
- cmd.exe (PID: 3152)
Starts application with an unusual extension
- cmd.exe (PID: 6384)
- cmd.exe (PID: 7596)
- cmd.exe (PID: 7604)
- cmd.exe (PID: 2692)
Starts NET.EXE to display or manage information about active sessions
- cmd.exe (PID: 6384)
- net.exe (PID: 2268)
- net.exe (PID: 2220)
- cmd.exe (PID: 7596)
Starts process via Powershell
- powershell.exe (PID: 5748)
Manipulates environment variables
- powershell.exe (PID: 5748)
- powershell.exe (PID: 6424)
- powershell.exe (PID: 1352)
- powershell.exe (PID: 5784)
- powershell.exe (PID: 8160)
- powershell.exe (PID: 4968)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 6384)
- cmd.exe (PID: 7604)
- update.exe (PID: 3696)
- gmstcccpdzbb.exe (PID: 8068)
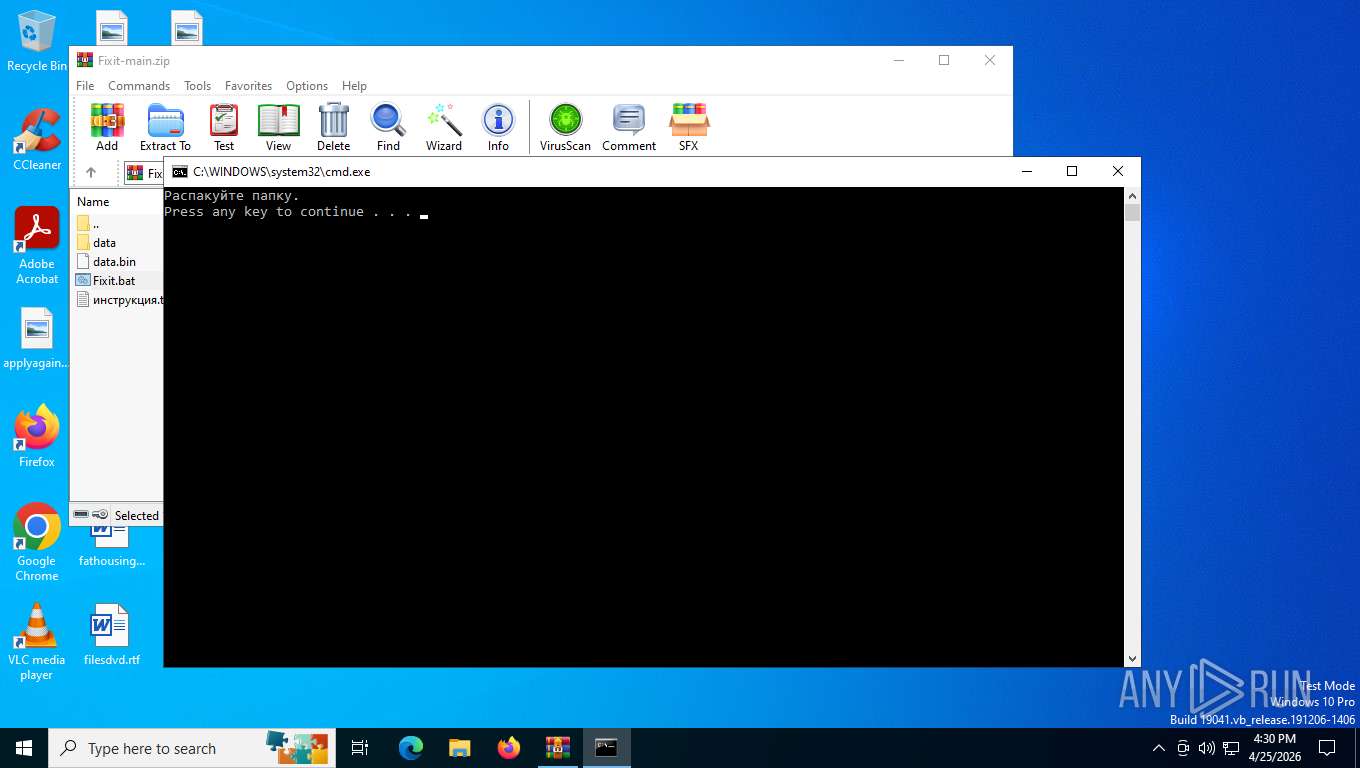
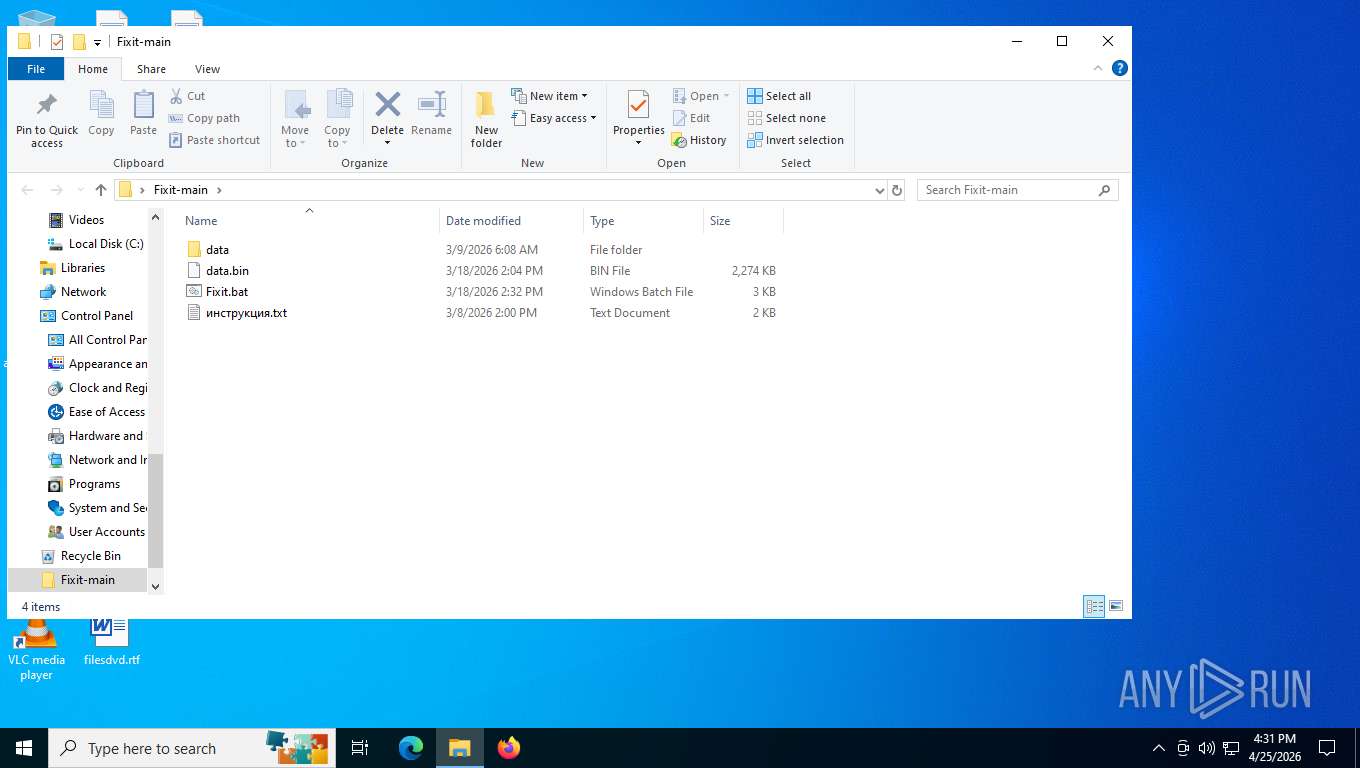
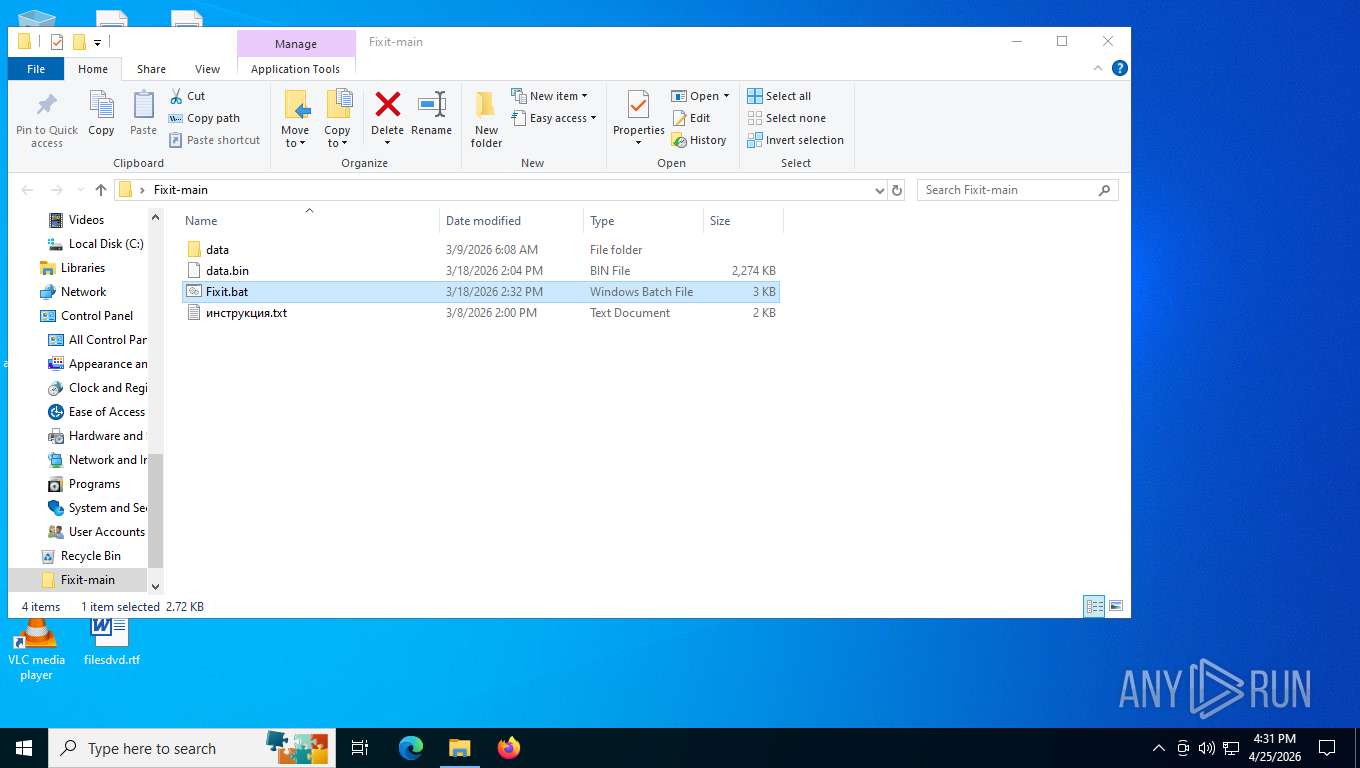
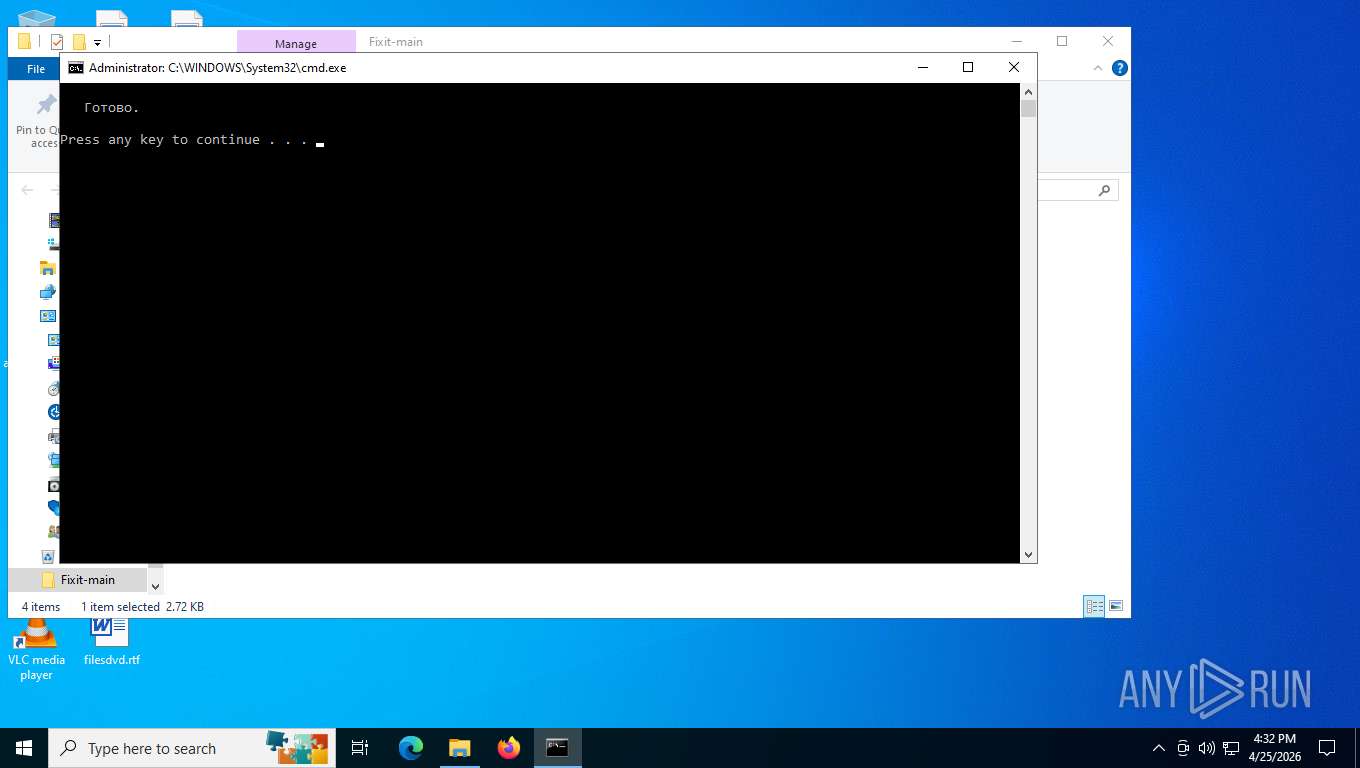
Executing commands from a ".bat" file
- WinRAR.exe (PID: 7484)
- powershell.exe (PID: 5748)
- cmd.exe (PID: 7596)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 6384)
- cmd.exe (PID: 7604)
Using short paths in the command line
- cmd.exe (PID: 7596)
- cmd.exe (PID: 7604)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 7596)
Adds exclusion path to Windows Defender (POWERSHELL)
- cmd.exe (PID: 7604)
- update.exe (PID: 3696)
- gmstcccpdzbb.exe (PID: 8068)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 1352)
- powershell.exe (PID: 5784)
Writes data into a file (POWERSHELL)
- powershell.exe (PID: 5784)
- powershell.exe (PID: 1352)
Using the short paths format
- cmd.exe (PID: 7604)
- WinRAR.exe (PID: 8036)
WINRAR started outside default location
- WinRAR.exe (PID: 8036)
Starts CMD.EXE with AutoRun commands disabled
- cmd.exe (PID: 5816)
Starts CMD.EXE with special quote handling
- cmd.exe (PID: 5816)
The process creates files with name similar to system file names
- WinRAR.exe (PID: 8036)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 8036)
- update.exe (PID: 3696)
- gmstcccpdzbb.exe (PID: 8068)
The process executes files with name similar to system file names
- cmd.exe (PID: 7604)
The executable file from the user directory is run by the CMD process
- update.exe (PID: 3696)
- ping.exe (PID: 4172)
Stops a currently running service
- sc.exe (PID: 7260)
- sc.exe (PID: 4916)
- sc.exe (PID: 2324)
- sc.exe (PID: 7356)
- sc.exe (PID: 6812)
- sc.exe (PID: 4368)
- sc.exe (PID: 7424)
- sc.exe (PID: 1652)
- sc.exe (PID: 7820)
- sc.exe (PID: 7340)
- sc.exe (PID: 3452)
Process uninstalls Windows update
- wusa.exe (PID: 7864)
- wusa.exe (PID: 6104)
Script adds exclusion extension to Windows Defender
- update.exe (PID: 3696)
- gmstcccpdzbb.exe (PID: 8068)
Uses powercfg.exe to modify the power settings
- update.exe (PID: 3696)
- gmstcccpdzbb.exe (PID: 8068)
Suspicious power configuration changes
- powercfg.exe (PID: 6200)
- powercfg.exe (PID: 5228)
- powercfg.exe (PID: 2136)
- powercfg.exe (PID: 3692)
- powercfg.exe (PID: 6240)
- powercfg.exe (PID: 8128)
- powercfg.exe (PID: 4112)
- powercfg.exe (PID: 7316)
Modifies hosts file to alter network resolution
- update.exe (PID: 3696)
- gmstcccpdzbb.exe (PID: 8068)
Creates a new Windows service
- sc.exe (PID: 1352)
Deletes a service using sc.exe
- sc.exe (PID: 4396)
Windows service management via SC.EXE
- sc.exe (PID: 4396)
- sc.exe (PID: 3172)
Executes as Windows Service
- gmstcccpdzbb.exe (PID: 8068)
Drops a system driver (possible attempt to evade defenses)
- gmstcccpdzbb.exe (PID: 8068)
Crypto Currency Mining Activity Detected
- svchost.exe (PID: 2232)
INFO
Generic archive extractor
- WinRAR.exe (PID: 7484)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7484)
Changes the display of characters in the console
- cmd.exe (PID: 6384)
- cmd.exe (PID: 7596)
- cmd.exe (PID: 7604)
- cmd.exe (PID: 2692)
Manual execution by a user
- cmd.exe (PID: 6384)
Checks supported languages
- chcp.com (PID: 7316)
- chcp.com (PID: 3136)
- chcp.com (PID: 4312)
- WinRAR.exe (PID: 8036)
- ping.exe (PID: 4172)
- update.exe (PID: 3696)
- chcp.com (PID: 7876)
- gmstcccpdzbb.exe (PID: 8068)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 7484)
Application launched itself
- cmd.exe (PID: 7596)
- cmd.exe (PID: 7604)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6424)
- powershell.exe (PID: 8160)
- powershell.exe (PID: 4968)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 6424)
- powershell.exe (PID: 8160)
- powershell.exe (PID: 4968)
Gets data length (POWERSHELL)
- powershell.exe (PID: 5784)
Reads the computer name
- WinRAR.exe (PID: 8036)
Reads the machine GUID from the registry
- WinRAR.exe (PID: 8036)
The sample compiled with english language support
- WinRAR.exe (PID: 8036)
- update.exe (PID: 3696)
- WinRAR.exe (PID: 7484)
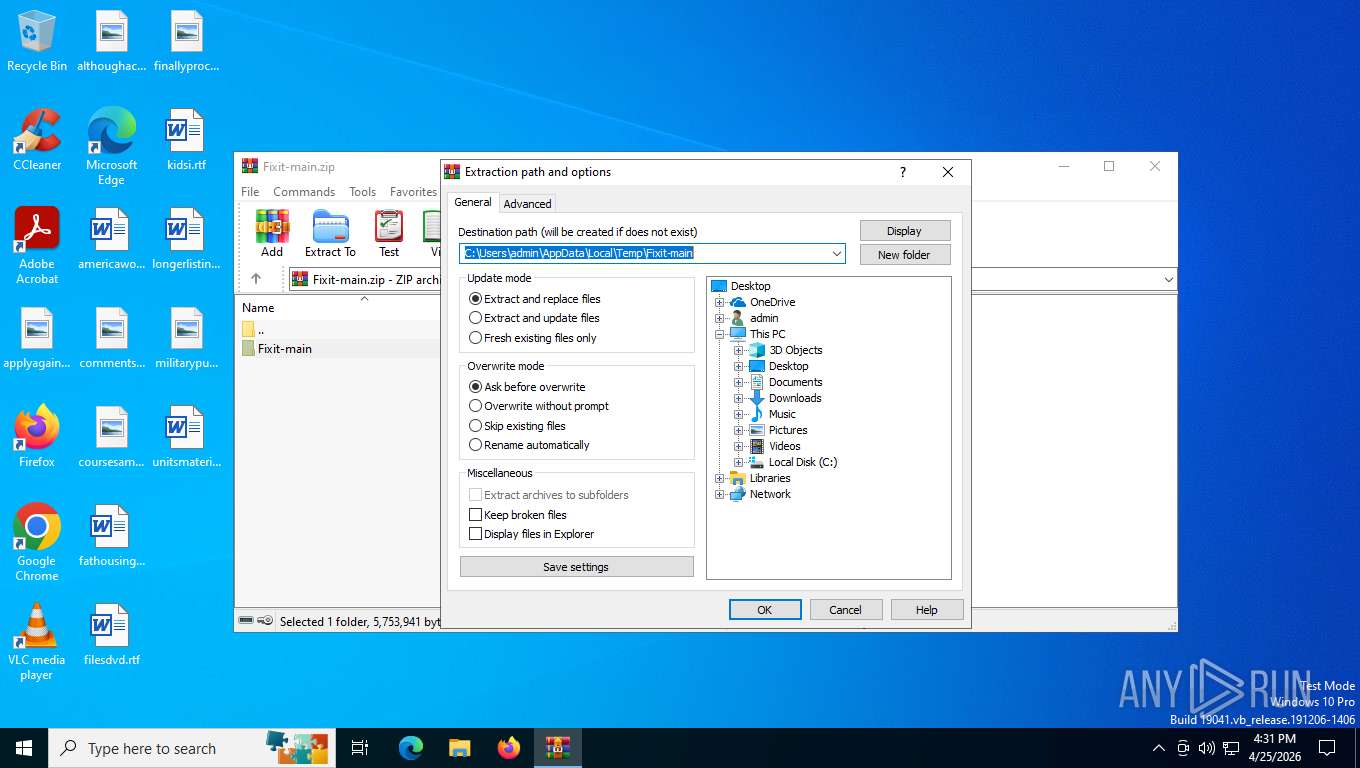
Create files in a temporary directory
- WinRAR.exe (PID: 8036)
The sample compiled with japanese language support
- gmstcccpdzbb.exe (PID: 8068)
UPX packer has been detected
- svchost.exe (PID: 7240)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
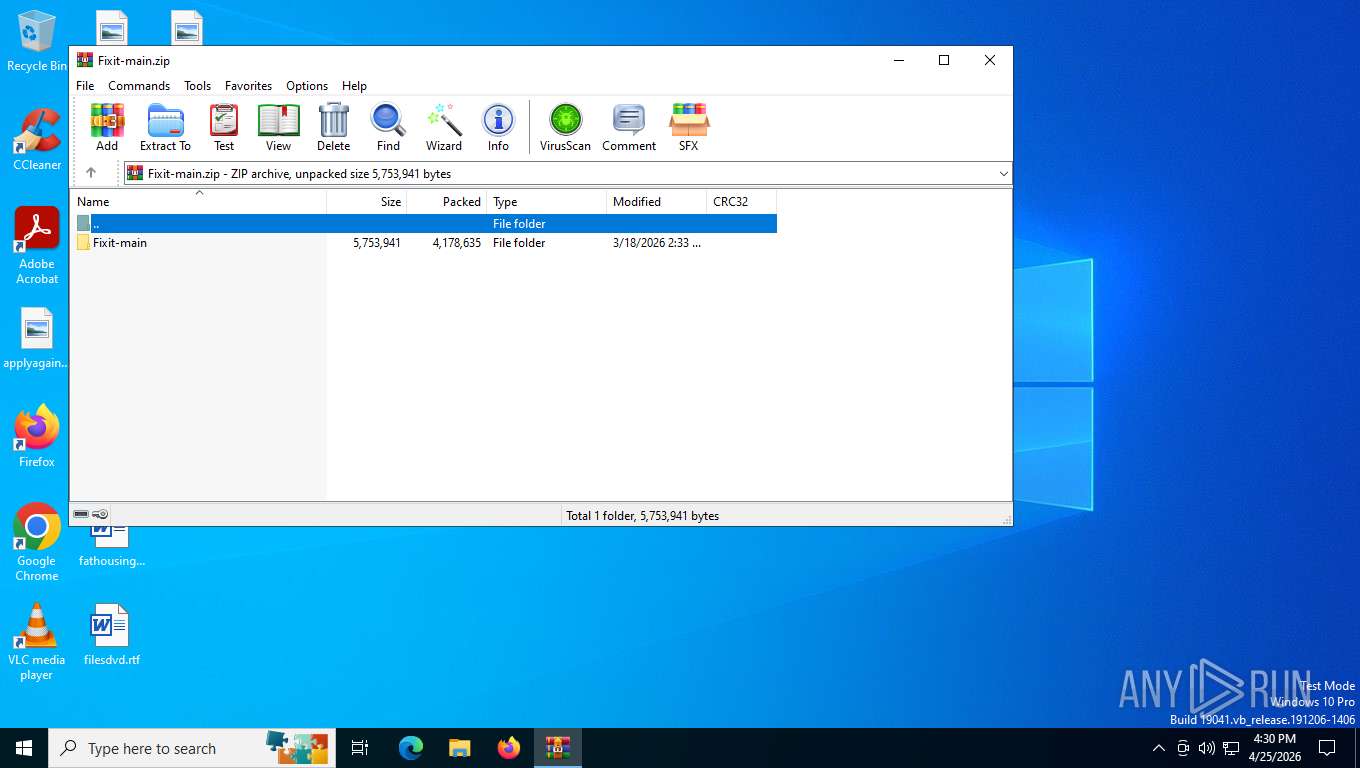
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2026:03:18 21:33:54 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | Fixit-main/ |
Total processes
235
Monitored processes
98
Malicious processes
8
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1032 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | sc.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1140 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | sc.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1268 | timeout /t 2 /nobreak | C:\Windows\System32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: timeout - pauses command processing Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1352 | powershell -NoProfile -Command "$p=[Text.Encoding]::UTF8.GetString([Convert]::FromBase64String('TkpHbmVyamc1ZzQ1dGh2R1JHNDV5')); [IO.File]::WriteAllText($env:temp+'\c.dat', $p)" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1352 | C:\WINDOWS\system32\sc.exe create "XLZQHCLS" binpath= "C:\ProgramData\oaocofwmfjha\gmstcccpdzbb.exe" start= "auto" | C:\Windows\System32\sc.exe | — | update.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1652 | C:\WINDOWS\system32\sc.exe stop UsoSvc | C:\Windows\System32\sc.exe | — | gmstcccpdzbb.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Service Control Manager Configuration Tool Exit code: 1061 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2016 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powercfg.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2100 | timeout /t 2 /nobreak | C:\Windows\System32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: timeout - pauses command processing Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2100 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | sc.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2120 | timeout /t 2 /nobreak | C:\Windows\System32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: timeout - pauses command processing Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
36 522
Read events
36 479
Write events
30
Delete events
13
Modification events
| (PID) Process: | (7484) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7484) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7484) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Downloads\chromium_build 1.zip | |||
| (PID) Process: | (7484) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Fixit-main.zip | |||
| (PID) Process: | (7484) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7484) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7484) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7484) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7484) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\3d\52C64B7E |
| Operation: | write | Name: | @C:\WINDOWS\System32\acppage.dll,-6002 |
Value: Windows Batch File | |||
| (PID) Process: | (7484) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 15 |
Value: | |||
Executable files
5
Suspicious files
6
Text files
24
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
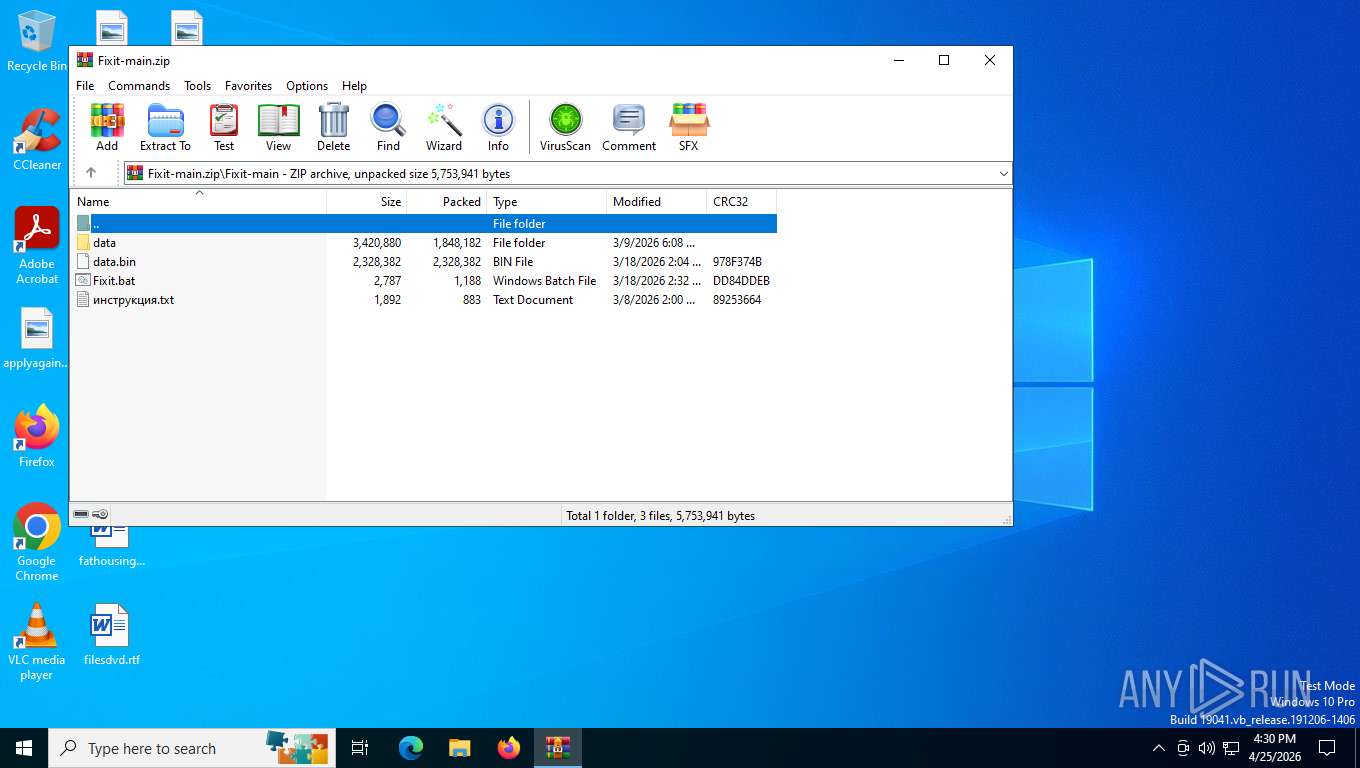
| 7484 | WinRAR.exe | C:\Users\admin\Desktop\Fixit-main\Fixit.bat | text | |
MD5:0A49FD8B16608102C53A6AEB1130CF11 | SHA256:FC8DA02CB7FE1BAA366E7F99B4DF240DB14A7F5859BD0202503A43DB768AA7CE | |||
| 6424 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_5yiptma3.2wr.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7484 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa7484.17579\Fixit.bat | text | |
MD5:0A49FD8B16608102C53A6AEB1130CF11 | SHA256:FC8DA02CB7FE1BAA366E7F99B4DF240DB14A7F5859BD0202503A43DB768AA7CE | |||
| 7484 | WinRAR.exe | C:\Users\admin\Desktop\Fixit-main\инструкция.txt | text | |
MD5:6993C61FFCB925A77168E0FAF09FFAE9 | SHA256:F5AF7397D9E717FC2FEDF48FD48748D54CEF9B0496891F319320F0CEA1E344FE | |||
| 7484 | WinRAR.exe | C:\Users\admin\Desktop\Fixit-main\data\WinRAR.exe | executable | |
MD5:EE7D68CA3A687CBAB0A1140EC044CC50 | SHA256:1E2207CF8AB08BE4FCA9F58C3407C858B68DF3910B649DDE6837A3A29B4257B3 | |||
| 7484 | WinRAR.exe | C:\Users\admin\Desktop\Fixit-main\data.bin | binary | |
MD5:81F425ACD3A1A3708C6DFD4D29D11C74 | SHA256:19DE6564C3FF7B285F4E19088B6767967902C1529C8C5CE0E1BBE10BD0DBB8FB | |||
| 5748 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:08ABB56D51ACC56630B719C41841EAA3 | SHA256:F5E771A03C0696863526BB43D89E51BB8DC6DB97D6FA10FD678E567E5447CB3C | |||
| 7596 | cmd.exe | C:\Users\admin\AppData\Local\Temp\data.bin | binary | |
MD5:81F425ACD3A1A3708C6DFD4D29D11C74 | SHA256:19DE6564C3FF7B285F4E19088B6767967902C1529C8C5CE0E1BBE10BD0DBB8FB | |||
| 5748 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_1xr2v0pj.0wf.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6424 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_llaugsxz.dez.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
47
TCP/UDP connections
34
DNS requests
24
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5276 | MoUsoCoreWorker.exe | GET | 304 | 20.73.194.208:443 | https://settings-win.data.microsoft.com/settings/v3.0/wsd/muse?ProcessorClockSpeed=3094&FlightIds=&UpdateOfferedDays=4294967295&BranchReadinessLevel=CB&OEMManufacturerName=DELL&IsCloudDomainJoined=0&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&sku=48&ActivationChannel=Retail&AttrDataVer=186&IsMDMEnrolled=0&ProcessorCores=6&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&TotalPhysicalRAM=6144&PrimaryDiskType=4294967295&FlightingBranchName=&ChassisTypeId=1&OEMModelNumber=DELL&SystemVolumeTotalCapacity=260281&sampleId=95271487&deviceClass=Windows.Desktop&App=muse&DisableDualScan=0&AppVer=10.0&OEMSubModel=J5CR&locale=en-US&IsAlwaysOnAlwaysConnectedCapable=0&ms=0&DefaultUserRegion=244&UpdateServiceUrl=http%3A%2F%2Fneverupdatewindows10.com&osVer=10.0.19045.4046.amd64fre.vb_release.191206-1406&os=windows&deviceId=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&DeferQualityUpdatePeriodInDays=0&ring=Retail&DeferFeatureUpdatePeriodInDays=30 | US | — | — | whitelisted |
5304 | SIHClient.exe | GET | 304 | 135.232.92.137:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | US | — | — | whitelisted |
5316 | svchost.exe | GET | 200 | 23.11.41.157:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAz1vQYrVgL0erhQLCPM8GY%3D | NL | binary | 471 b | whitelisted |
— | — | GET | 200 | 204.79.197.203:80 | http://oneocsp.microsoft.com/ocsp/MFQwUjBQME4wTDAJBgUrDgMCGgUABBQ3L3%2F%2Fa6ADK8NraY2GXzVaYrHG4AQUb6t%2B2v%2BXQ3LsO2d33oJhNYhHQoUCEzMAAAAGb6JMMcOVb6sAAAAAAAY%3D | US | binary | 960 b | whitelisted |
5304 | SIHClient.exe | GET | 200 | 135.233.95.135:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | US | — | — | whitelisted |
5304 | SIHClient.exe | GET | 200 | 135.232.92.137:443 | https://slscr.update.microsoft.com/sls/ping | US | — | — | whitelisted |
5304 | SIHClient.exe | GET | 304 | 135.232.92.137:443 | https://slscr.update.microsoft.com/SLS/%7BE7A50285-D08D-499D-9FF8-180FDC2332BC%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | US | — | — | whitelisted |
5316 | svchost.exe | POST | 400 | 40.126.32.133:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | US | text | 204 b | whitelisted |
5316 | svchost.exe | POST | 200 | 40.126.32.133:443 | https://login.live.com/RST2.srf | US | xml | 1.24 Kb | whitelisted |
6260 | svchost.exe | GET | 304 | 40.127.240.158:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/UpdateHealthTools?os=Windows&osVer=10.0.19041.1.amd64fre.vb_release.191206-&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=s:BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&sampleId=s:95271487&appVer=10.0.19041.3626&FlightRing=Retail&TelemetryLevel=1&HidOverGattReg=C%3A%5CWINDOWS%5CSystem32%5CDriverStore%5CFileRepository%5Chidbthle.inf_amd64_9610b4821fdf82a5%5CMicrosoft.Bluetooth.Profiles.HidOverGatt.dll&AppVer=&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&OEMModel=DELL&UpdateOfferedDays=4294967295&ProcessorManufacturer=AuthenticAMD&InstallDate=1661339444&OEMModelBaseBoard=&BranchReadinessLevel=CB&OEMSubModel=J5CR&IsCloudDomainJoined=0&DeferFeatureUpdatePeriodInDays=30&IsDeviceRetailDemo=0&FlightingBranchName=&OSUILocale=en-US&DeviceFamily=Windows.Desktop&WuClientVer=10.0.19041.3996&UninstallActive=1&IsFlightingEnabled=0&OSSkuId=48&ProcessorClockSpeed=3094&TotalPhysicalRAM=6144&SecureBootCapable=0&App=SedimentPack&ProcessorCores=6&CurrentBranch=vb_release&InstallLanguage=en-US&DeferQualityUpdatePeriodInDays=0&OEMName_Uncleaned=DELL&TPMVersion=0&PrimaryDiskTotalCapacity=262144&InstallationType=Client&AttrDataVer=186&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&IsEdgeWithChromiumInstalled=1&OSVersion=10.0.19045.4046&IsMDMEnrolled=0&ActivationChannel=Retail&FirmwareVersion=A.40&TrendInstalledKey=1&OSArchitecture=AMD64&DefaultUserRegion=244&UpdateManagementGroup=2 | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
6260 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5276 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 48.192.1.64:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5532 | SearchApp.exe | 2.16.241.205:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 23.11.41.157:80 | ocsp.digicert.com | AKAMAI-AMS | NL | whitelisted |
— | — | 204.79.197.203:80 | oneocsp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
5316 | svchost.exe | 40.126.32.133:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5316 | svchost.exe | 23.11.41.157:80 | ocsp.digicert.com | AKAMAI-AMS | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
activation-v2.sls.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
oneocsp.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6260 | svchost.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
2232 | svchost.exe | Crypto Currency Mining Activity Detected | ET COINMINER CoinMiner Domain in DNS Lookup (pool .hashvault .pro) |