| File name: | Setup_x32_x64.bin |
| Full analysis: | https://app.any.run/tasks/9a9e1728-2438-4fa2-9ae2-8ad9d00c9cfe |
| Verdict: | Malicious activity |
| Threats: | Remote access trojans (RATs) are a type of malware that enables attackers to establish complete to partial control over infected computers. Such malicious programs often have a modular design, offering a wide range of functionalities for conducting illicit activities on compromised systems. Some of the most common features of RATs include access to the users’ data, webcam, and keystrokes. This malware is often distributed through phishing emails and links. |
| Analysis date: | August 12, 2022, 16:00:06 |
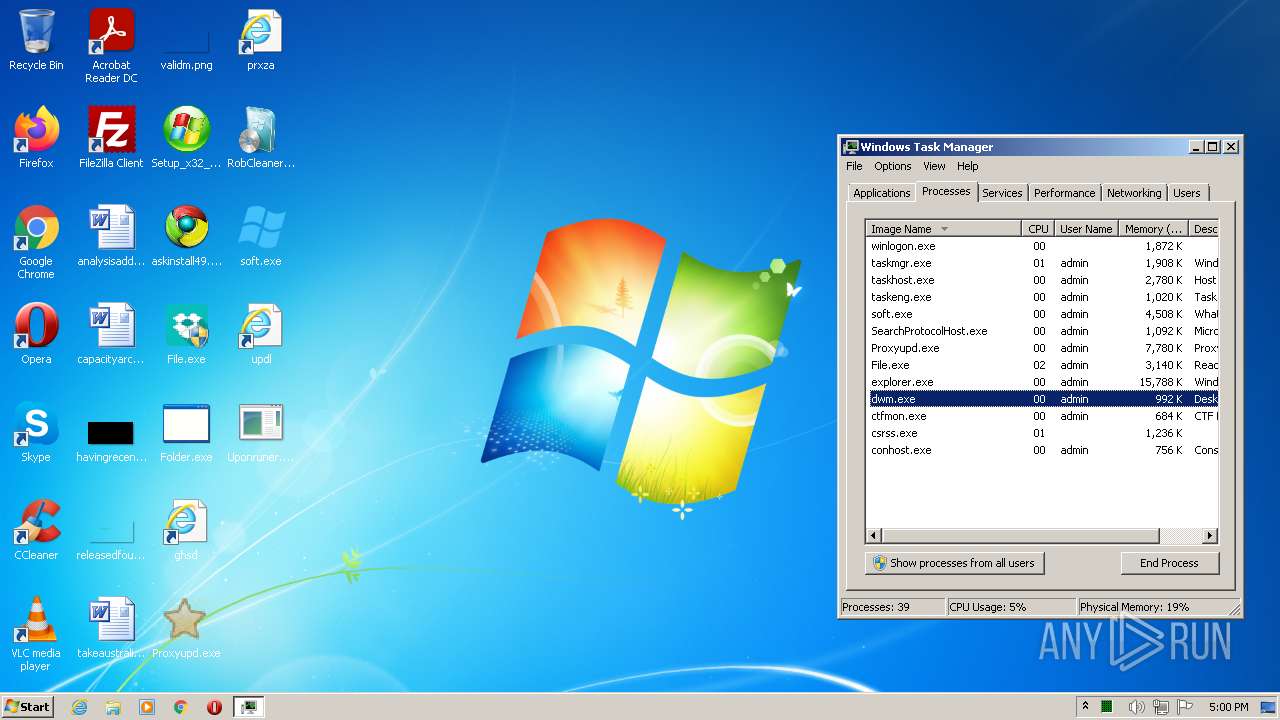
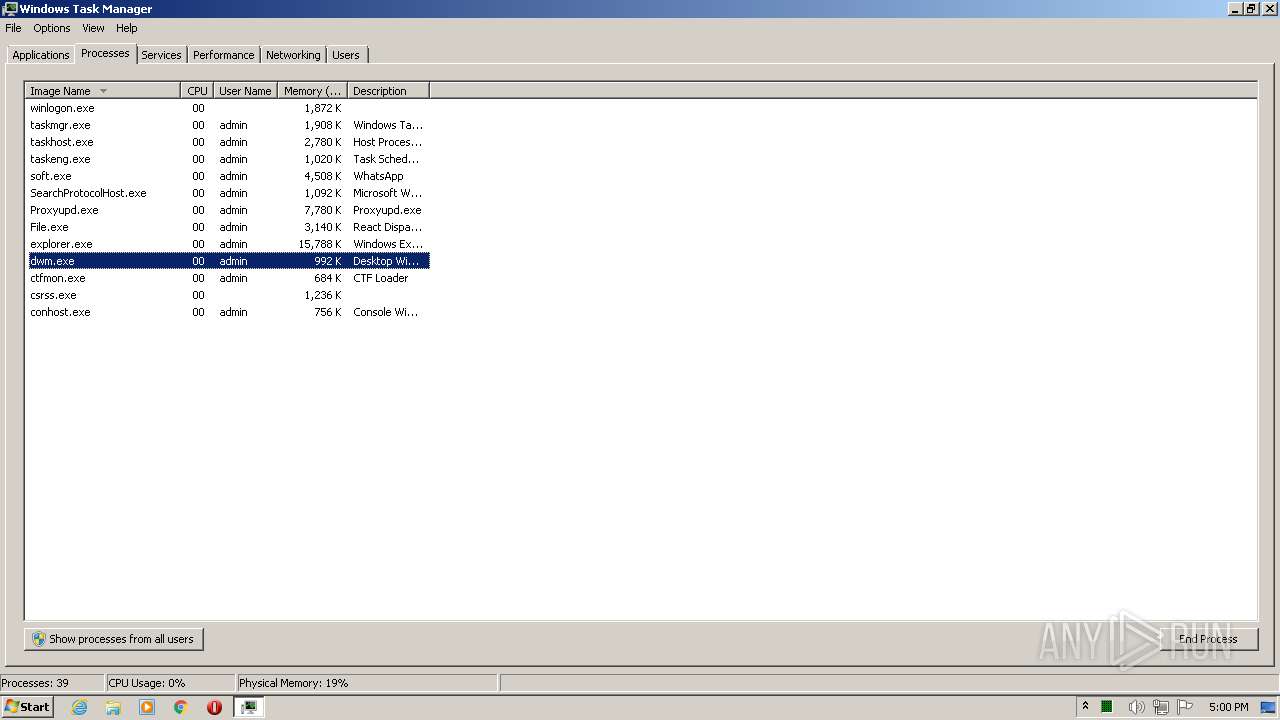
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 5F7F42F26F25E4E7342C00E05C0176FA |
| SHA1: | 582EA6AA20547C8B7F83CECCBA5B3B4B1E7E4FB7 |
| SHA256: | 9E719C4DD5E1086D5197FDED7B8CDB0D3D592C0636B0D469FCDA22C9723E8E7C |
| SSDEEP: | 49152:PbA37xyPeKsyMV/mmzApSr+EHgHjCLZsMbGEpD6e3h3igtpz+vDzfvmWvoDH:PbReKyAugDmZsMwO3TpgfuWvQ |
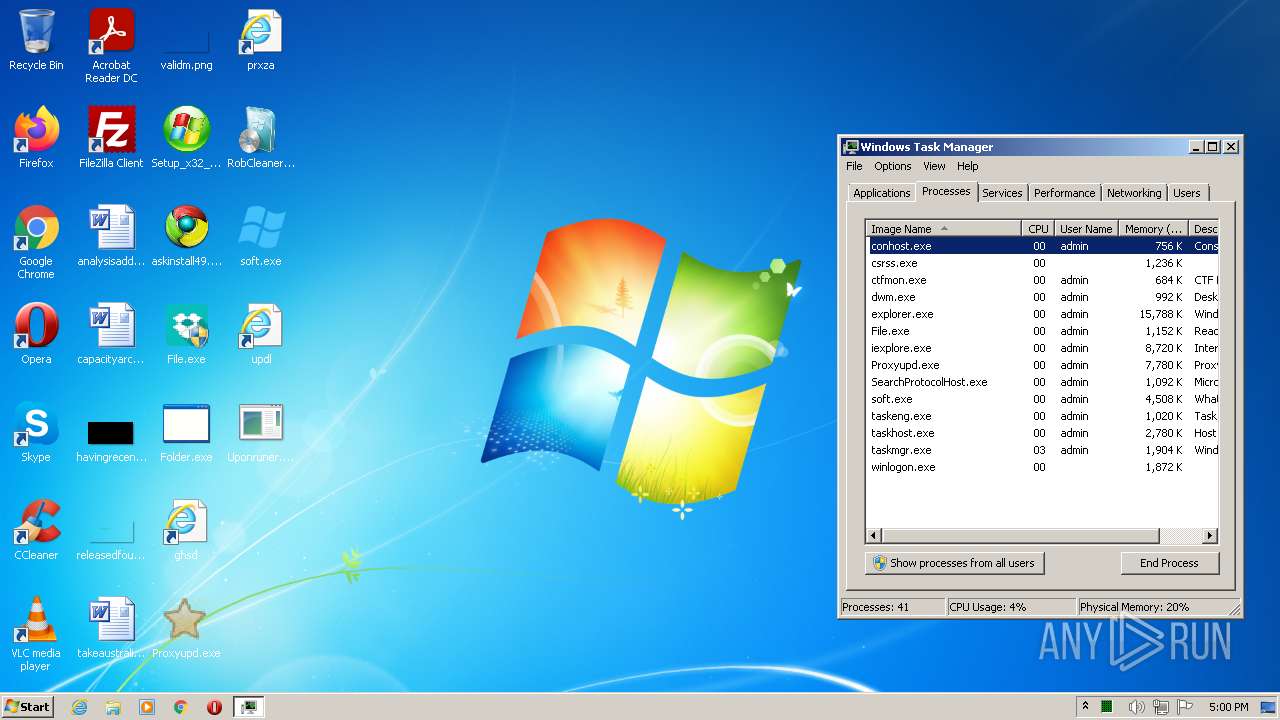
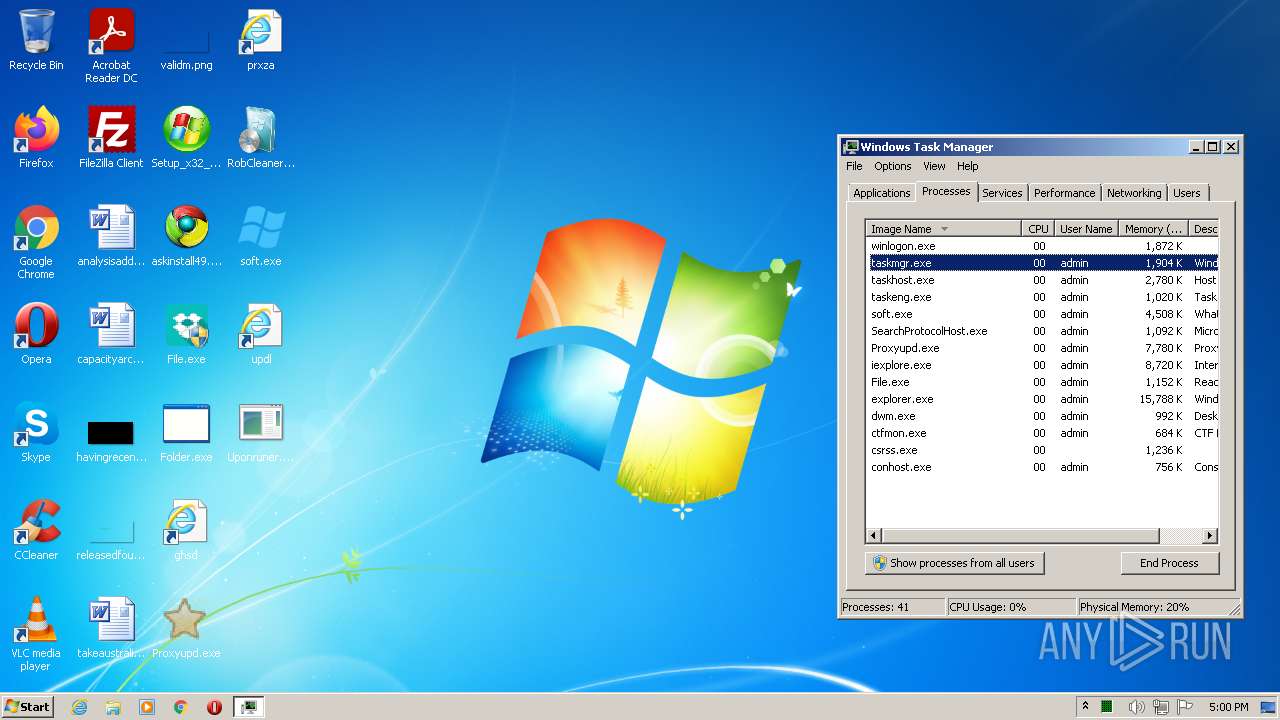
MALICIOUS
Drops executable file immediately after starts
- Setup_x32_x64.bin.exe (PID: 2392)
Application was dropped or rewritten from another process
- Proxyupd.exe (PID: 3132)
- soft.exe (PID: 2936)
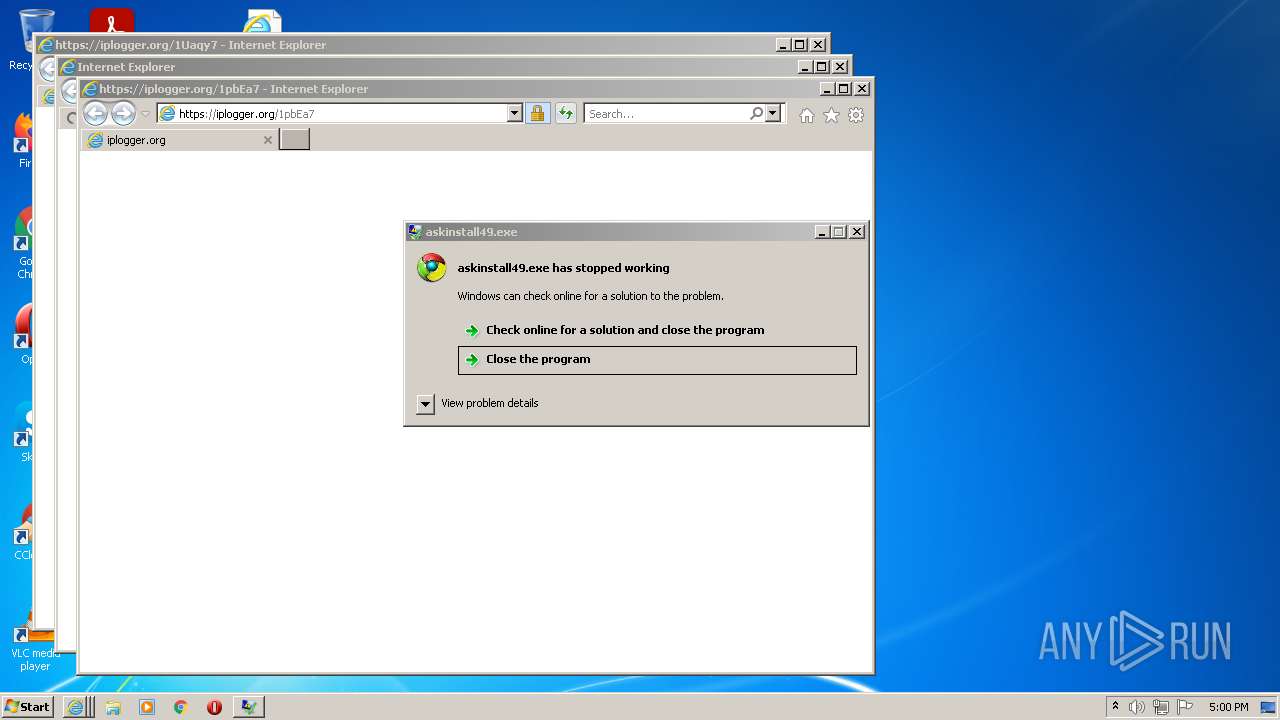
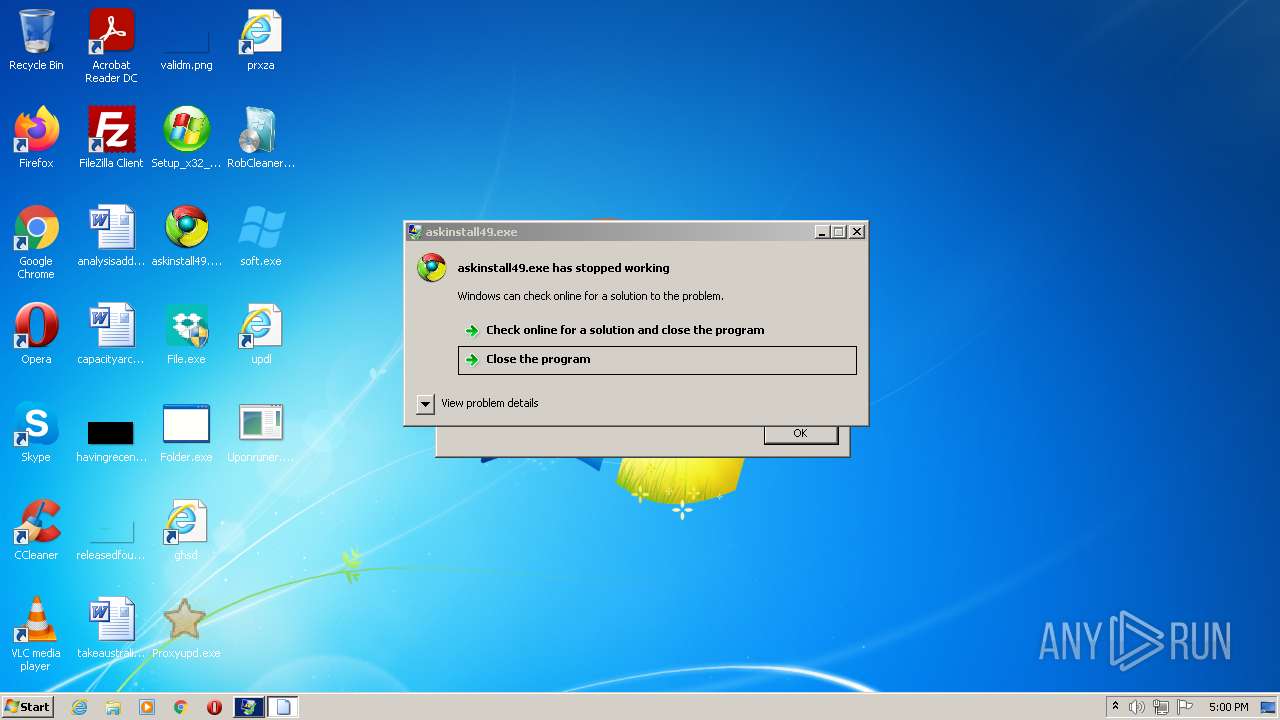
- askinstall49.exe (PID: 3648)
- Folder.exe (PID: 2136)
- File.exe (PID: 3724)
- RobCleanerInstl3183813.exe (PID: 1076)
- Folder.exe (PID: 3792)
- File.exe (PID: 1928)
- askinstall49.exe (PID: 3280)
Changes settings of System certificates
- askinstall49.exe (PID: 3280)
REDLINE was detected
- soft.exe (PID: 2936)
REDLINE detected by memory dumps
- Proxyupd.exe (PID: 3132)
- soft.exe (PID: 2936)
Connects to CnC server
- soft.exe (PID: 2936)
SUSPICIOUS
Executable content was dropped or overwritten
- Setup_x32_x64.bin.exe (PID: 2392)
Executed via COM
- iexplore.exe (PID: 3804)
- DllHost.exe (PID: 2636)
Checks supported languages
- Setup_x32_x64.bin.exe (PID: 2392)
- soft.exe (PID: 2936)
- Folder.exe (PID: 2136)
- Proxyupd.exe (PID: 3132)
- RobCleanerInstl3183813.exe (PID: 1076)
- askinstall49.exe (PID: 3648)
- Folder.exe (PID: 3792)
- File.exe (PID: 1928)
- askinstall49.exe (PID: 3280)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 276)
- iexplore.exe (PID: 1304)
- iexplore.exe (PID: 2848)
Reads the computer name
- Setup_x32_x64.bin.exe (PID: 2392)
- soft.exe (PID: 2936)
- Folder.exe (PID: 2136)
- RobCleanerInstl3183813.exe (PID: 1076)
- Proxyupd.exe (PID: 3132)
- askinstall49.exe (PID: 3648)
- Folder.exe (PID: 3792)
- File.exe (PID: 1928)
- askinstall49.exe (PID: 3280)
Drops a file with a compile date too recent
- Setup_x32_x64.bin.exe (PID: 2392)
Reads Windows owner or organization settings
- soft.exe (PID: 2936)
Application launched itself
- Folder.exe (PID: 2136)
Reads Environment values
- RobCleanerInstl3183813.exe (PID: 1076)
Adds / modifies Windows certificates
- askinstall49.exe (PID: 3280)
Checks for external IP
- iexplore.exe (PID: 276)
- iexplore.exe (PID: 2848)
- iexplore.exe (PID: 3804)
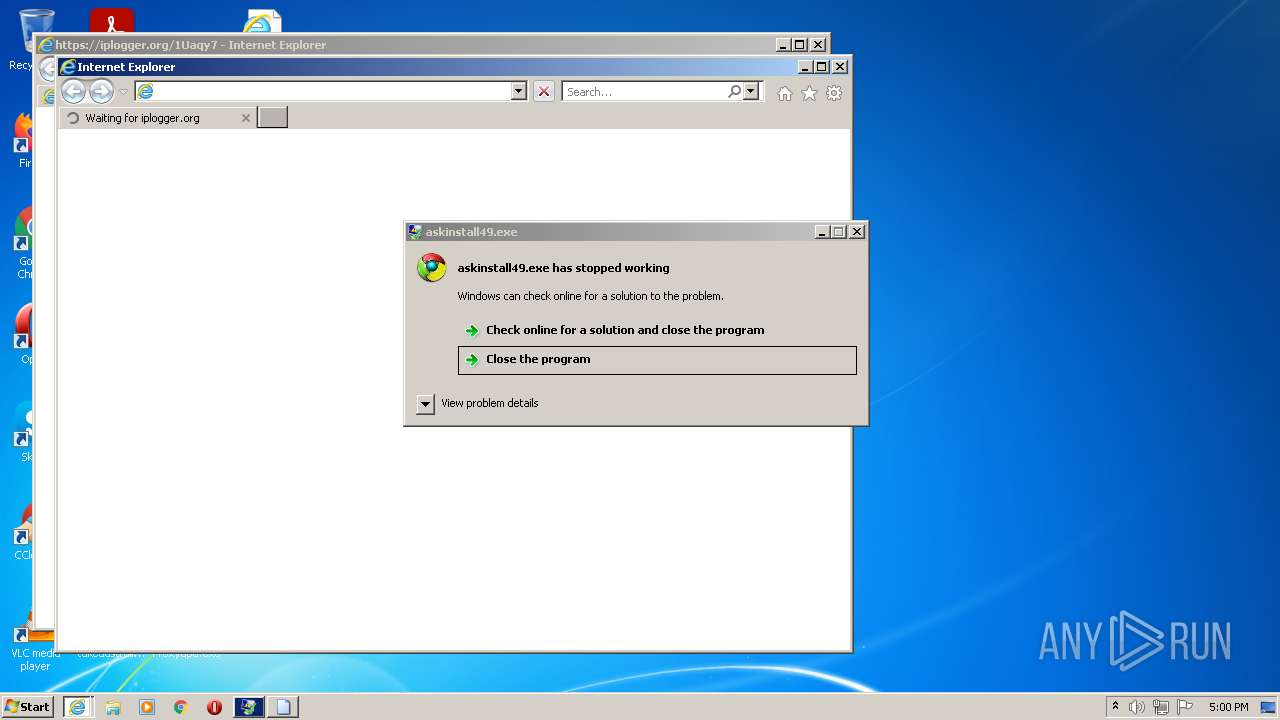
- askinstall49.exe (PID: 3280)
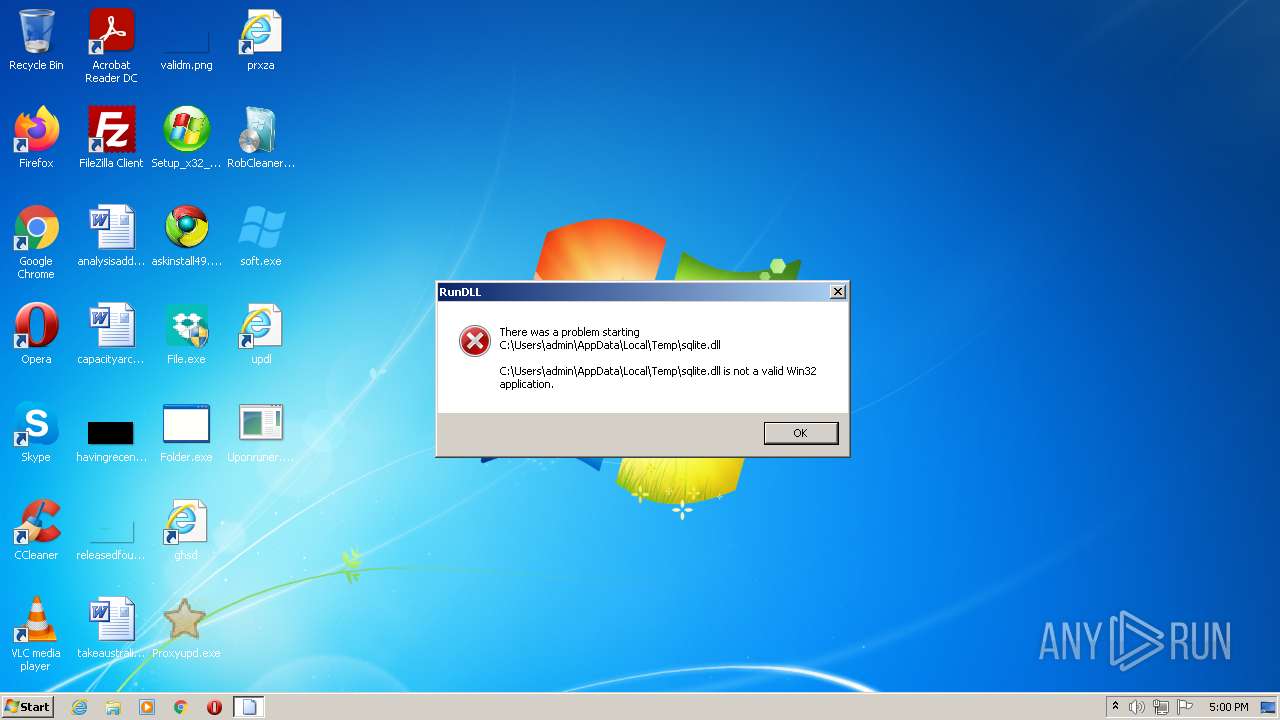
Executed via WMI
- rundll32.exe (PID: 3968)
INFO
Checks supported languages
- ntvdm.exe (PID: 2268)
- iexplore.exe (PID: 3804)
- iexplore.exe (PID: 276)
- iexplore.exe (PID: 1304)
- iexplore.exe (PID: 2848)
- DllHost.exe (PID: 2636)
- rundll32.exe (PID: 3968)
- taskmgr.exe (PID: 3644)
Application launched itself
- iexplore.exe (PID: 3804)
Reads the computer name
- iexplore.exe (PID: 276)
- iexplore.exe (PID: 3804)
- iexplore.exe (PID: 1304)
- iexplore.exe (PID: 2848)
- DllHost.exe (PID: 2636)
- taskmgr.exe (PID: 3644)
Changes internet zones settings
- iexplore.exe (PID: 3804)
Checks Windows Trust Settings
- iexplore.exe (PID: 276)
- iexplore.exe (PID: 2848)
- askinstall49.exe (PID: 3280)
- iexplore.exe (PID: 3804)
Reads settings of System Certificates
- iexplore.exe (PID: 276)
- iexplore.exe (PID: 2848)
- askinstall49.exe (PID: 3280)
- iexplore.exe (PID: 3804)
- RobCleanerInstl3183813.exe (PID: 1076)
- Folder.exe (PID: 3792)
- File.exe (PID: 1928)
Reads internet explorer settings
- iexplore.exe (PID: 276)
- iexplore.exe (PID: 2848)
Reads the date of Windows installation
- iexplore.exe (PID: 3804)
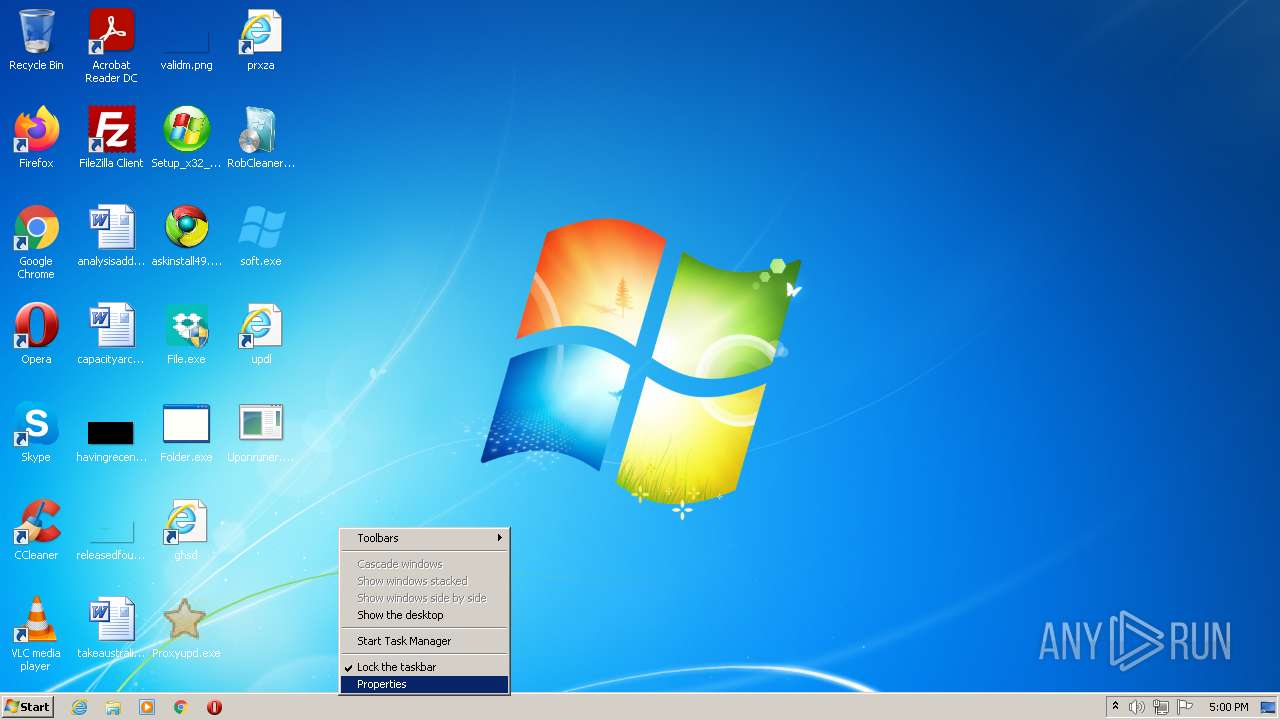
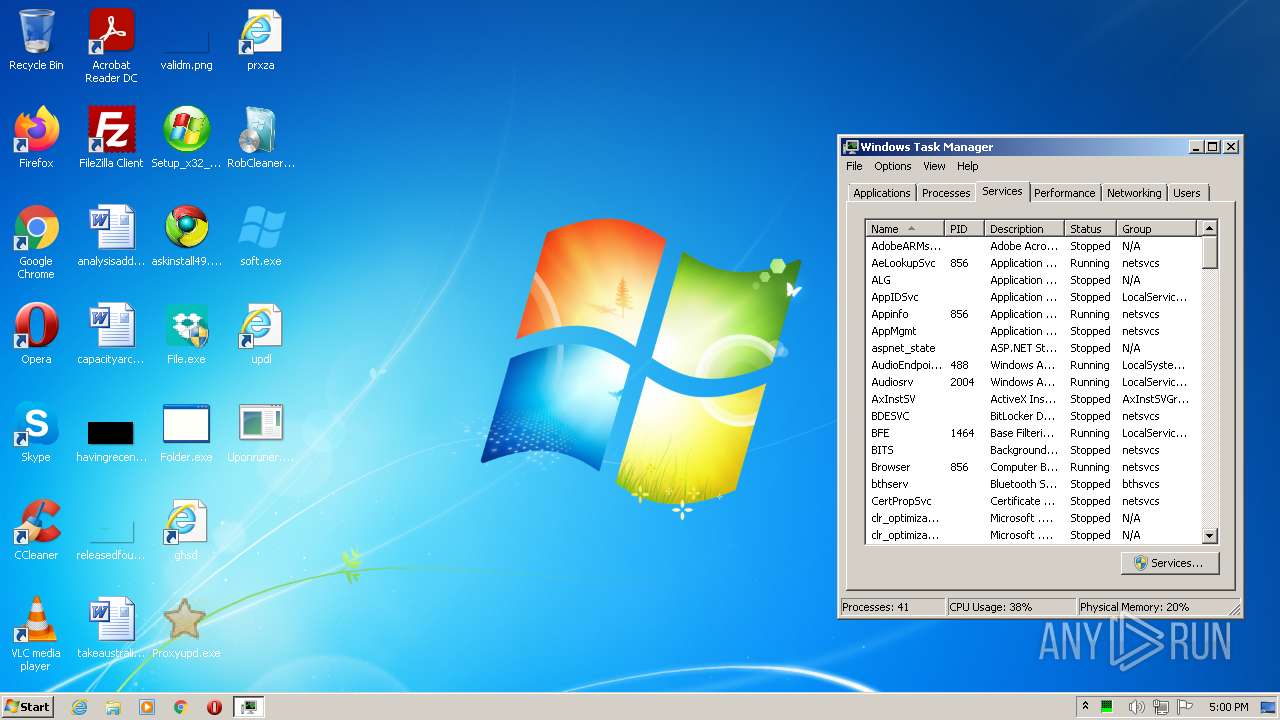
Manual execution by user
- taskmgr.exe (PID: 3644)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
RedLine
(PID) Process(3132) Proxyupd.exe
C2 (1)78.46.137.240:21314
BotnetUpdate
Err_msg
Auth_value910ca2116f2e220a6801edd5a725ab65
US (183)
LEnvironmentogiEnvironmentn DatEnvironmenta
Environment
WSystem.Texteb DatSystem.Texta
System.Text
CoCryptographyokieCryptographys
Cryptography
ExtGenericension CooGenerickies
Generic
OFileInfopeFileInfora GFileInfoX StabFileInfole
FileInfo
OpLinqera GLinqX
Linq
ApGenericpDaGenericta\RGenericoamiGenericng\
Network
Extension
UNKNOWN
.
1
cFileStreamredFileStreamit_cFileStreamardFileStreams
FileStream
\
Network\
Host
Port
:
User
Pass
MANGO
eNetworkCredentialxpirNetworkCredentialy
NetworkCredential
%USEWanaLifeRPROFILE%\AppDaWanaLifeta\LWanaLifeocal
WanaLife
Def
Win
String.Replace
String.Remove
bcrFileStream.IOypt.dFileStream.IOll
FileStream.IO
BCrMemoryStreamyptOpeMemoryStreamnAlgorithmProviMemoryStreamder
MemoryStream
BCrFileStreamyptCloseAlgoritFileStreamhmProvFileStreamider
BCrIOStreamyptDecrIOStreamypt
IOStream
BCrFile.ReadyptDesFile.ReadtroyKFile.Readey
File.Read
BCFile.OpenryptGeFile.OpentPropeFile.Openrty
File.Open
BCFile.CloseryptSFile.CloseetPrFile.CloseoperFile.Closety
File.Close
BCrFile.ReadAllTextyptImFile.ReadAllTextportKFile.ReadAllTextey
File.ReadAllText
windows-1251
AES
Microsoft Primitive Provider
ChainingModeGCM
AuthTagLength
ChainingMode
ObjectLength
KeyDataBlob
-
net.tcp://
/
localhost
910ca2116f2e220a6801edd5a725ab65
Authorization
ns1
UNKNWON
CB8THD0sHxA5PT5bCg89WT4sKRw5PT4QCCRJVA==
ED02AiowFAk=
Fetish
Yandex\YaAddon
ToString
asf
*wallet*
_
\TeEnvironmentlegraEnvironmentm DEnvironmentesktoEnvironmentp\tdEnvironmentata
String
Replace
string.Replace
%USERPFile.WriteROFILE%\AppFile.WriteData\RoamiFile.Writeng
File.Write
Handler
npvo*
%USERPserviceInterface.ExtensionROFILE%\ApserviceInterface.ExtensionpData\LocaserviceInterface.Extensionl
serviceInterface.Extension
ProldCharotonVoldCharPN
oldChar
nSystem.CollectionspvoSystem.Collections*
System.Collections
(
UNIQUE
cstringmstringd
string
/ProcessC Process
Process
|
"
gasdl94ja;sdiasdl94ja;s32
asdl94ja;s
Gasdl94jlajsdetDevasdl94jlajsdiceCapasdl94jlajsds
asdl94jlajsd
Width
Height
CopyFromScreen
https://api.ip.sb/ip
80
81
0.0.0.0
SELSystem.Windows.FormsECT * FRSystem.Windows.FormsOM WinSystem.Windows.Forms32_ProcSystem.Windows.Formsessor
System.Windows.Forms
Name
NumberOfCores
roSystem.Linqot\CISystem.LinqMV2
System.Linq
SELSystem.LinqECT * FRSystem.LinqOM WinSystem.Linq32_VideoCoSystem.Linqntroller
AdapterRAM
SOFTWARE\WOW6432Node\Clients\StartMenuInternet
SOFTWARE\Clients\StartMenuInternet
shell\open\command
Unknown Version
SELESystem.ManagementCT * FRSystem.ManagementOM WiSystem.Managementn32_DisSystem.ManagementkDrivSystem.Managemente
System.Management
SerialNumber
SELSystem.Text.RegularExpressionsECT * FRSystem.Text.RegularExpressionsOM Win32_PSystem.Text.RegularExpressionsrocess WSystem.Text.RegularExpressionshere SessSystem.Text.RegularExpressionsionId='
'
FileSystem
SSystem.ELECT * FRSystem.OM WiSystem.n32_ProcSystem.ess WherSystem.e SessiSystem.onId='
System.
ExecutablePath
[
]
Concat0 MConcatb oConcatr Concat0
Concat
SELEMemoryCT * FMemoryROM WiMemoryn32_OperMemoryatingSMemoryystem
Memory
{0}{1}{2}
x32
x64
x86
SOFTWARE\Microsoft\Windows NT\CurrentVersion
ProductName
CSDVersion
Unknown
_[
System.Core, Version=3.5.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089
System.Security.Cryptography.AesCryptoServiceProvider
8eb2d54ia3.gfgl59y95
{11111-22222-10009-11111}
{11111-22222-50001-00000}
GetDelegateForFunctionPointer
__
System.Reflection.ReflectionContext
clrjit.dll
m_ptr
System.Reflection.RuntimeModule
m_pData
e6601k5eym.29fm4uxu3
file:///
Location
Find
ResourceA
Virtual
Alloc
Write
Process
Protect
Open
Close
Handle
kernel
32.dll
{11111-22222-10001-00001}
{11111-22222-10001-00002}
{11111-22222-20001-00001}
{11111-22222-20001-00002}
{11111-22222-40001-00001}
{11111-22222-40001-00002}
{11111-22222-50001-00001}
{11111-22222-50001-00002}
C2 (1)78.46.137.240:21314
BotnetUpdate
Err_msg
Auth_value910ca2116f2e220a6801edd5a725ab65
US (183)
LEnvironmentogiEnvironmentn DatEnvironmenta
Environment
WSystem.Texteb DatSystem.Texta
System.Text
CoCryptographyokieCryptographys
Cryptography
ExtGenericension CooGenerickies
Generic
OFileInfopeFileInfora GFileInfoX StabFileInfole
FileInfo
OpLinqera GLinqX
Linq
ApGenericpDaGenericta\RGenericoamiGenericng\
Network
Extension
UNKNOWN
.
1
cFileStreamredFileStreamit_cFileStreamardFileStreams
FileStream
\
Network\
Host
Port
:
User
Pass
MANGO
eNetworkCredentialxpirNetworkCredentialy
NetworkCredential
%USEWanaLifeRPROFILE%\AppDaWanaLifeta\LWanaLifeocal
WanaLife
Def
Win
String.Replace
String.Remove
bcrFileStream.IOypt.dFileStream.IOll
FileStream.IO
BCrMemoryStreamyptOpeMemoryStreamnAlgorithmProviMemoryStreamder
MemoryStream
BCrFileStreamyptCloseAlgoritFileStreamhmProvFileStreamider
BCrIOStreamyptDecrIOStreamypt
IOStream
BCrFile.ReadyptDesFile.ReadtroyKFile.Readey
File.Read
BCFile.OpenryptGeFile.OpentPropeFile.Openrty
File.Open
BCFile.CloseryptSFile.CloseetPrFile.CloseoperFile.Closety
File.Close
BCrFile.ReadAllTextyptImFile.ReadAllTextportKFile.ReadAllTextey
File.ReadAllText
windows-1251
AES
Microsoft Primitive Provider
ChainingModeGCM
AuthTagLength
ChainingMode
ObjectLength
KeyDataBlob
-
net.tcp://
/
localhost
910ca2116f2e220a6801edd5a725ab65
Authorization
ns1
UNKNWON
CB8THD0sHxA5PT5bCg89WT4sKRw5PT4QCCRJVA==
ED02AiowFAk=
Fetish
Yandex\YaAddon
ToString
asf
*wallet*
_
\TeEnvironmentlegraEnvironmentm DEnvironmentesktoEnvironmentp\tdEnvironmentata
String
Replace
string.Replace
%USERPFile.WriteROFILE%\AppFile.WriteData\RoamiFile.Writeng
File.Write
Handler
npvo*
%USERPserviceInterface.ExtensionROFILE%\ApserviceInterface.ExtensionpData\LocaserviceInterface.Extensionl
serviceInterface.Extension
ProldCharotonVoldCharPN
oldChar
nSystem.CollectionspvoSystem.Collections*
System.Collections
(
UNIQUE
cstringmstringd
string
/ProcessC Process
Process
|
"
gasdl94ja;sdiasdl94ja;s32
asdl94ja;s
Gasdl94jlajsdetDevasdl94jlajsdiceCapasdl94jlajsds
asdl94jlajsd
Width
Height
CopyFromScreen
https://api.ip.sb/ip
80
81
0.0.0.0
SELSystem.Windows.FormsECT * FRSystem.Windows.FormsOM WinSystem.Windows.Forms32_ProcSystem.Windows.Formsessor
System.Windows.Forms
Name
NumberOfCores
roSystem.Linqot\CISystem.LinqMV2
System.Linq
SELSystem.LinqECT * FRSystem.LinqOM WinSystem.Linq32_VideoCoSystem.Linqntroller
AdapterRAM
SOFTWARE\WOW6432Node\Clients\StartMenuInternet
SOFTWARE\Clients\StartMenuInternet
shell\open\command
Unknown Version
SELESystem.ManagementCT * FRSystem.ManagementOM WiSystem.Managementn32_DisSystem.ManagementkDrivSystem.Managemente
System.Management
SerialNumber
SELSystem.Text.RegularExpressionsECT * FRSystem.Text.RegularExpressionsOM Win32_PSystem.Text.RegularExpressionsrocess WSystem.Text.RegularExpressionshere SessSystem.Text.RegularExpressionsionId='
'
FileSystem
SSystem.ELECT * FRSystem.OM WiSystem.n32_ProcSystem.ess WherSystem.e SessiSystem.onId='
System.
ExecutablePath
[
]
Concat0 MConcatb oConcatr Concat0
Concat
SELEMemoryCT * FMemoryROM WiMemoryn32_OperMemoryatingSMemoryystem
Memory
{0}{1}{2}
x32
x64
x86
SOFTWARE\Microsoft\Windows NT\CurrentVersion
ProductName
CSDVersion
Unknown
_[
System.Core, Version=3.5.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089
System.Security.Cryptography.AesCryptoServiceProvider
8eb2d54ia3.gfgl59y95
{11111-22222-10009-11111}
{11111-22222-50001-00000}
GetDelegateForFunctionPointer
__
System.Reflection.ReflectionContext
clrjit.dll
m_ptr
System.Reflection.RuntimeModule
m_pData
e6601k5eym.29fm4uxu3
file:///
Location
Find
ResourceA
Virtual
Alloc
Write
Process
Protect
Open
Close
Handle
kernel
32.dll
{11111-22222-10001-00001}
{11111-22222-10001-00002}
{11111-22222-20001-00001}
{11111-22222-20001-00002}
{11111-22222-40001-00001}
{11111-22222-40001-00002}
{11111-22222-50001-00001}
{11111-22222-50001-00002}
C2 (1)78.46.137.240:21314
BotnetUpdate
Err_msg
Auth_value910ca2116f2e220a6801edd5a725ab65
US (183)
LEnvironmentogiEnvironmentn DatEnvironmenta
Environment
WSystem.Texteb DatSystem.Texta
System.Text
CoCryptographyokieCryptographys
Cryptography
ExtGenericension CooGenerickies
Generic
OFileInfopeFileInfora GFileInfoX StabFileInfole
FileInfo
OpLinqera GLinqX
Linq
ApGenericpDaGenericta\RGenericoamiGenericng\
Network
Extension
UNKNOWN
.
1
cFileStreamredFileStreamit_cFileStreamardFileStreams
FileStream
\
Network\
Host
Port
:
User
Pass
MANGO
eNetworkCredentialxpirNetworkCredentialy
NetworkCredential
%USEWanaLifeRPROFILE%\AppDaWanaLifeta\LWanaLifeocal
WanaLife
Def
Win
String.Replace
String.Remove
bcrFileStream.IOypt.dFileStream.IOll
FileStream.IO
BCrMemoryStreamyptOpeMemoryStreamnAlgorithmProviMemoryStreamder
MemoryStream
BCrFileStreamyptCloseAlgoritFileStreamhmProvFileStreamider
BCrIOStreamyptDecrIOStreamypt
IOStream
BCrFile.ReadyptDesFile.ReadtroyKFile.Readey
File.Read
BCFile.OpenryptGeFile.OpentPropeFile.Openrty
File.Open
BCFile.CloseryptSFile.CloseetPrFile.CloseoperFile.Closety
File.Close
BCrFile.ReadAllTextyptImFile.ReadAllTextportKFile.ReadAllTextey
File.ReadAllText
windows-1251
AES
Microsoft Primitive Provider
ChainingModeGCM
AuthTagLength
ChainingMode
ObjectLength
KeyDataBlob
-
net.tcp://
/
localhost
910ca2116f2e220a6801edd5a725ab65
Authorization
ns1
UNKNWON
CB8THD0sHxA5PT5bCg89WT4sKRw5PT4QCCRJVA==
ED02AiowFAk=
Fetish
Yandex\YaAddon
ToString
asf
*wallet*
_
\TeEnvironmentlegraEnvironmentm DEnvironmentesktoEnvironmentp\tdEnvironmentata
String
Replace
string.Replace
%USERPFile.WriteROFILE%\AppFile.WriteData\RoamiFile.Writeng
File.Write
Handler
npvo*
%USERPserviceInterface.ExtensionROFILE%\ApserviceInterface.ExtensionpData\LocaserviceInterface.Extensionl
serviceInterface.Extension
ProldCharotonVoldCharPN
oldChar
nSystem.CollectionspvoSystem.Collections*
System.Collections
(
UNIQUE
cstringmstringd
string
/ProcessC Process
Process
|
"
gasdl94ja;sdiasdl94ja;s32
asdl94ja;s
Gasdl94jlajsdetDevasdl94jlajsdiceCapasdl94jlajsds
asdl94jlajsd
Width
Height
CopyFromScreen
https://api.ip.sb/ip
80
81
0.0.0.0
SELSystem.Windows.FormsECT * FRSystem.Windows.FormsOM WinSystem.Windows.Forms32_ProcSystem.Windows.Formsessor
System.Windows.Forms
Name
NumberOfCores
roSystem.Linqot\CISystem.LinqMV2
System.Linq
SELSystem.LinqECT * FRSystem.LinqOM WinSystem.Linq32_VideoCoSystem.Linqntroller
AdapterRAM
SOFTWARE\WOW6432Node\Clients\StartMenuInternet
SOFTWARE\Clients\StartMenuInternet
shell\open\command
Unknown Version
SELESystem.ManagementCT * FRSystem.ManagementOM WiSystem.Managementn32_DisSystem.ManagementkDrivSystem.Managemente
System.Management
SerialNumber
SELSystem.Text.RegularExpressionsECT * FRSystem.Text.RegularExpressionsOM Win32_PSystem.Text.RegularExpressionsrocess WSystem.Text.RegularExpressionshere SessSystem.Text.RegularExpressionsionId='
'
FileSystem
SSystem.ELECT * FRSystem.OM WiSystem.n32_ProcSystem.ess WherSystem.e SessiSystem.onId='
System.
ExecutablePath
[
]
Concat0 MConcatb oConcatr Concat0
Concat
SELEMemoryCT * FMemoryROM WiMemoryn32_OperMemoryatingSMemoryystem
Memory
{0}{1}{2}
x32
x64
x86
SOFTWARE\Microsoft\Windows NT\CurrentVersion
ProductName
CSDVersion
Unknown
_[
System.Core, Version=3.5.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089
System.Security.Cryptography.AesCryptoServiceProvider
8eb2d54ia3.gfgl59y95
{11111-22222-10009-11111}
{11111-22222-50001-00000}
GetDelegateForFunctionPointer
__
System.Reflection.ReflectionContext
clrjit.dll
m_ptr
System.Reflection.RuntimeModule
m_pData
e6601k5eym.29fm4uxu3
file:///
Location
Find
ResourceA
Virtual
Alloc
Write
Process
Protect
Open
Close
Handle
kernel
32.dll
{11111-22222-10001-00001}
{11111-22222-10001-00002}
{11111-22222-20001-00001}
{11111-22222-20001-00002}
{11111-22222-40001-00001}
{11111-22222-40001-00002}
{11111-22222-50001-00001}
{11111-22222-50001-00002}
C2 (1)78.46.137.240:21314
BotnetUpdate
Err_msg
Auth_value910ca2116f2e220a6801edd5a725ab65
US (183)
LEnvironmentogiEnvironmentn DatEnvironmenta
Environment
WSystem.Texteb DatSystem.Texta
System.Text
CoCryptographyokieCryptographys
Cryptography
ExtGenericension CooGenerickies
Generic
OFileInfopeFileInfora GFileInfoX StabFileInfole
FileInfo
OpLinqera GLinqX
Linq
ApGenericpDaGenericta\RGenericoamiGenericng\
Network
Extension
UNKNOWN
.
1
cFileStreamredFileStreamit_cFileStreamardFileStreams
FileStream
\
Network\
Host
Port
:
User
Pass
MANGO
eNetworkCredentialxpirNetworkCredentialy
NetworkCredential
%USEWanaLifeRPROFILE%\AppDaWanaLifeta\LWanaLifeocal
WanaLife
Def
Win
String.Replace
String.Remove
bcrFileStream.IOypt.dFileStream.IOll
FileStream.IO
BCrMemoryStreamyptOpeMemoryStreamnAlgorithmProviMemoryStreamder
MemoryStream
BCrFileStreamyptCloseAlgoritFileStreamhmProvFileStreamider
BCrIOStreamyptDecrIOStreamypt
IOStream
BCrFile.ReadyptDesFile.ReadtroyKFile.Readey
File.Read
BCFile.OpenryptGeFile.OpentPropeFile.Openrty
File.Open
BCFile.CloseryptSFile.CloseetPrFile.CloseoperFile.Closety
File.Close
BCrFile.ReadAllTextyptImFile.ReadAllTextportKFile.ReadAllTextey
File.ReadAllText
windows-1251
AES
Microsoft Primitive Provider
ChainingModeGCM
AuthTagLength
ChainingMode
ObjectLength
KeyDataBlob
-
net.tcp://
/
localhost
910ca2116f2e220a6801edd5a725ab65
Authorization
ns1
UNKNWON
CB8THD0sHxA5PT5bCg89WT4sKRw5PT4QCCRJVA==
ED02AiowFAk=
Fetish
Yandex\YaAddon
ToString
asf
*wallet*
_
\TeEnvironmentlegraEnvironmentm DEnvironmentesktoEnvironmentp\tdEnvironmentata
String
Replace
string.Replace
%USERPFile.WriteROFILE%\AppFile.WriteData\RoamiFile.Writeng
File.Write
Handler
npvo*
%USERPserviceInterface.ExtensionROFILE%\ApserviceInterface.ExtensionpData\LocaserviceInterface.Extensionl
serviceInterface.Extension
ProldCharotonVoldCharPN
oldChar
nSystem.CollectionspvoSystem.Collections*
System.Collections
(
UNIQUE
cstringmstringd
string
/ProcessC Process
Process
|
"
gasdl94ja;sdiasdl94ja;s32
asdl94ja;s
Gasdl94jlajsdetDevasdl94jlajsdiceCapasdl94jlajsds
asdl94jlajsd
Width
Height
CopyFromScreen
https://api.ip.sb/ip
80
81
0.0.0.0
SELSystem.Windows.FormsECT * FRSystem.Windows.FormsOM WinSystem.Windows.Forms32_ProcSystem.Windows.Formsessor
System.Windows.Forms
Name
NumberOfCores
roSystem.Linqot\CISystem.LinqMV2
System.Linq
SELSystem.LinqECT * FRSystem.LinqOM WinSystem.Linq32_VideoCoSystem.Linqntroller
AdapterRAM
SOFTWARE\WOW6432Node\Clients\StartMenuInternet
SOFTWARE\Clients\StartMenuInternet
shell\open\command
Unknown Version
SELESystem.ManagementCT * FRSystem.ManagementOM WiSystem.Managementn32_DisSystem.ManagementkDrivSystem.Managemente
System.Management
SerialNumber
SELSystem.Text.RegularExpressionsECT * FRSystem.Text.RegularExpressionsOM Win32_PSystem.Text.RegularExpressionsrocess WSystem.Text.RegularExpressionshere SessSystem.Text.RegularExpressionsionId='
'
FileSystem
SSystem.ELECT * FRSystem.OM WiSystem.n32_ProcSystem.ess WherSystem.e SessiSystem.onId='
System.
ExecutablePath
[
]
Concat0 MConcatb oConcatr Concat0
Concat
SELEMemoryCT * FMemoryROM WiMemoryn32_OperMemoryatingSMemoryystem
Memory
{0}{1}{2}
x32
x64
x86
SOFTWARE\Microsoft\Windows NT\CurrentVersion
ProductName
CSDVersion
Unknown
_[
System.Core, Version=3.5.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089
System.Security.Cryptography.AesCryptoServiceProvider
8eb2d54ia3.gfgl59y95
{11111-22222-10009-11111}
{11111-22222-50001-00000}
GetDelegateForFunctionPointer
__
System.Reflection.ReflectionContext
clrjit.dll
m_ptr
System.Reflection.RuntimeModule
m_pData
e6601k5eym.29fm4uxu3
file:///
Location
Find
ResourceA
Virtual
Alloc
Write
Process
Protect
Open
Close
Handle
kernel
32.dll
{11111-22222-10001-00001}
{11111-22222-10001-00002}
{11111-22222-20001-00001}
{11111-22222-20001-00002}
{11111-22222-40001-00001}
{11111-22222-40001-00002}
{11111-22222-50001-00001}
{11111-22222-50001-00002}
C2 (1)78.46.137.240:21314
BotnetUpdate
Err_msg
Auth_value910ca2116f2e220a6801edd5a725ab65
US (183)
LEnvironmentogiEnvironmentn DatEnvironmenta
Environment
WSystem.Texteb DatSystem.Texta
System.Text
CoCryptographyokieCryptographys
Cryptography
ExtGenericension CooGenerickies
Generic
OFileInfopeFileInfora GFileInfoX StabFileInfole
FileInfo
OpLinqera GLinqX
Linq
ApGenericpDaGenericta\RGenericoamiGenericng\
Network
Extension
UNKNOWN
.
1
cFileStreamredFileStreamit_cFileStreamardFileStreams
FileStream
\
Network\
Host
Port
:
User
Pass
MANGO
eNetworkCredentialxpirNetworkCredentialy
NetworkCredential
%USEWanaLifeRPROFILE%\AppDaWanaLifeta\LWanaLifeocal
WanaLife
Def
Win
String.Replace
String.Remove
bcrFileStream.IOypt.dFileStream.IOll
FileStream.IO
BCrMemoryStreamyptOpeMemoryStreamnAlgorithmProviMemoryStreamder
MemoryStream
BCrFileStreamyptCloseAlgoritFileStreamhmProvFileStreamider
BCrIOStreamyptDecrIOStreamypt
IOStream
BCrFile.ReadyptDesFile.ReadtroyKFile.Readey
File.Read
BCFile.OpenryptGeFile.OpentPropeFile.Openrty
File.Open
BCFile.CloseryptSFile.CloseetPrFile.CloseoperFile.Closety
File.Close
BCrFile.ReadAllTextyptImFile.ReadAllTextportKFile.ReadAllTextey
File.ReadAllText
windows-1251
AES
Microsoft Primitive Provider
ChainingModeGCM
AuthTagLength
ChainingMode
ObjectLength
KeyDataBlob
-
net.tcp://
/
localhost
910ca2116f2e220a6801edd5a725ab65
Authorization
ns1
UNKNWON
CB8THD0sHxA5PT5bCg89WT4sKRw5PT4QCCRJVA==
ED02AiowFAk=
Fetish
Yandex\YaAddon
ToString
asf
*wallet*
_
\TeEnvironmentlegraEnvironmentm DEnvironmentesktoEnvironmentp\tdEnvironmentata
String
Replace
string.Replace
%USERPFile.WriteROFILE%\AppFile.WriteData\RoamiFile.Writeng
File.Write
Handler
npvo*
%USERPserviceInterface.ExtensionROFILE%\ApserviceInterface.ExtensionpData\LocaserviceInterface.Extensionl
serviceInterface.Extension
ProldCharotonVoldCharPN
oldChar
nSystem.CollectionspvoSystem.Collections*
System.Collections
(
UNIQUE
cstringmstringd
string
/ProcessC Process
Process
|
"
gasdl94ja;sdiasdl94ja;s32
asdl94ja;s
Gasdl94jlajsdetDevasdl94jlajsdiceCapasdl94jlajsds
asdl94jlajsd
Width
Height
CopyFromScreen
https://api.ip.sb/ip
80
81
0.0.0.0
SELSystem.Windows.FormsECT * FRSystem.Windows.FormsOM WinSystem.Windows.Forms32_ProcSystem.Windows.Formsessor
System.Windows.Forms
Name
NumberOfCores
roSystem.Linqot\CISystem.LinqMV2
System.Linq
SELSystem.LinqECT * FRSystem.LinqOM WinSystem.Linq32_VideoCoSystem.Linqntroller
AdapterRAM
SOFTWARE\WOW6432Node\Clients\StartMenuInternet
SOFTWARE\Clients\StartMenuInternet
shell\open\command
Unknown Version
SELESystem.ManagementCT * FRSystem.ManagementOM WiSystem.Managementn32_DisSystem.ManagementkDrivSystem.Managemente
System.Management
SerialNumber
SELSystem.Text.RegularExpressionsECT * FRSystem.Text.RegularExpressionsOM Win32_PSystem.Text.RegularExpressionsrocess WSystem.Text.RegularExpressionshere SessSystem.Text.RegularExpressionsionId='
'
FileSystem
SSystem.ELECT * FRSystem.OM WiSystem.n32_ProcSystem.ess WherSystem.e SessiSystem.onId='
System.
ExecutablePath
[
]
Concat0 MConcatb oConcatr Concat0
Concat
SELEMemoryCT * FMemoryROM WiMemoryn32_OperMemoryatingSMemoryystem
Memory
{0}{1}{2}
x32
x64
x86
SOFTWARE\Microsoft\Windows NT\CurrentVersion
ProductName
CSDVersion
Unknown
_[
System.Core, Version=3.5.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089
System.Security.Cryptography.AesCryptoServiceProvider
8eb2d54ia3.gfgl59y95
{11111-22222-10009-11111}
{11111-22222-50001-00000}
GetDelegateForFunctionPointer
__
System.Reflection.ReflectionContext
clrjit.dll
m_ptr
System.Reflection.RuntimeModule
m_pData
e6601k5eym.29fm4uxu3
file:///
Location
Find
ResourceA
Virtual
Alloc
Write
Process
Protect
Open
Close
Handle
kernel
32.dll
{11111-22222-10001-00001}
{11111-22222-10001-00002}
{11111-22222-20001-00001}
{11111-22222-20001-00002}
{11111-22222-40001-00001}
{11111-22222-40001-00002}
{11111-22222-50001-00001}
{11111-22222-50001-00002}
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 5.1 |
| ImageVersion: | - |
| OSVersion: | 5.1 |
| EntryPoint: | 0x1ec40 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 143360 |
| CodeSize: | 201216 |
| LinkerVersion: | 14 |
| PEType: | PE32 |
| TimeStamp: | 2020:12:01 19:00:55+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 01-Dec-2020 18:00:55 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000118 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 01-Dec-2020 18:00:55 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000310EA | 0x00031200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.70808 |
.rdata | 0x00033000 | 0x0000A612 | 0x0000A800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.22174 |
.data | 0x0003E000 | 0x00023728 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.70882 |
.didat | 0x00062000 | 0x00000188 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.29825 |
.rsrc | 0x00063000 | 0x00015168 | 0x00015200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.24093 |
.reloc | 0x00079000 | 0x00002268 | 0x00002400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.55486 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.25329 | 1875 | Latin 1 / Western European | English - United States | RT_MANIFEST |
7 | 3.1586 | 482 | Latin 1 / Western European | English - United States | RT_STRING |
8 | 3.11685 | 460 | Latin 1 / Western European | English - United States | RT_STRING |
9 | 3.11236 | 440 | Latin 1 / Western European | English - United States | RT_STRING |
10 | 2.99727 | 326 | Latin 1 / Western European | English - United States | RT_STRING |
11 | 3.2036 | 1094 | Latin 1 / Western European | English - United States | RT_STRING |
12 | 3.12889 | 358 | Latin 1 / Western European | English - United States | RT_STRING |
13 | 3.01704 | 338 | Latin 1 / Western European | English - United States | RT_STRING |
14 | 2.94627 | 266 | Latin 1 / Western European | English - United States | RT_STRING |
15 | 2.83619 | 188 | Latin 1 / Western European | English - United States | RT_STRING |
Imports
KERNEL32.dll |
USER32.dll (delay-loaded) |
gdiplus.dll |
Total processes
64
Monitored processes
18
Malicious processes
5
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 276 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3804 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1076 | "C:\Users\admin\Desktop\RobCleanerInstl3183813.exe" | C:\Users\admin\Desktop\RobCleanerInstl3183813.exe | Setup_x32_x64.bin.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 2 Modules
| |||||||||||||||
| 1304 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3804 CREDAT:660740 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1928 | "C:\Users\admin\Desktop\File.exe" | C:\Users\admin\Desktop\File.exe | Setup_x32_x64.bin.exe | ||||||||||||
User: admin Company: React Integrity Level: HIGH Description: React Dispatcher Exit code: 0 Version: 1.11020.9.51 Modules
| |||||||||||||||
| 2136 | "C:\Users\admin\Desktop\Folder.exe" | C:\Users\admin\Desktop\Folder.exe | — | Setup_x32_x64.bin.exe | |||||||||||
User: admin Company: DCloud Integrity Level: MEDIUM Description: HBuilder X Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2268 | "C:\Windows\system32\ntvdm.exe" -i1 | C:\Windows\system32\ntvdm.exe | — | Setup_x32_x64.bin.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: NTVDM.EXE Exit code: 3221225477 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2392 | "C:\Users\admin\Desktop\Setup_x32_x64.bin.exe" | C:\Users\admin\Desktop\Setup_x32_x64.bin.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2636 | C:\Windows\system32\DllHost.exe /Processid:{3E5FC7F9-9A51-4367-9063-A120244FBEC7} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2848 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3804 CREDAT:791813 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2936 | "C:\Users\admin\Desktop\soft.exe" | C:\Users\admin\Desktop\soft.exe | Setup_x32_x64.bin.exe | ||||||||||||
User: admin Company: WhatsApp Integrity Level: MEDIUM Description: WhatsApp Exit code: 0 Version: 2.2147.16 Modules
| |||||||||||||||
Total events
33 097
Read events
32 814
Write events
281
Delete events
2
Modification events
| (PID) Process: | (2392) Setup_x32_x64.bin.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2392) Setup_x32_x64.bin.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2392) Setup_x32_x64.bin.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2392) Setup_x32_x64.bin.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2392) Setup_x32_x64.bin.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {FBF23B40-E3F0-101B-8488-00AA003E56F8} {000214E4-0000-0000-C000-000000000046} 0xFFFF |
Value: 01000000000000005497D79A64AED801 | |||
| (PID) Process: | (3804) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3804) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3804) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30977636 | |||
| (PID) Process: | (3804) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3804) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30977636 | |||
Executable files
6
Suspicious files
19
Text files
17
Unknown types
18
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2392 | Setup_x32_x64.bin.exe | C:\Users\admin\Desktop\prxza.url | url | |
MD5:3E507ECAAC6710D93C101C67AE45FDAB | SHA256:083F728D22BC6F1ED6BFA9ECAEB68528A9EB433C0E8E67A52426047EC3E41488 | |||
| 2392 | Setup_x32_x64.bin.exe | C:\Users\admin\Desktop\Proxyupd.exe | executable | |
MD5:8C792B086A9FA3171EEEAC333EA6BAAC | SHA256:533777FEBFFF2581EA3C3F1046EE55D205D2779515B3A15346C674C15D228B9E | |||
| 2392 | Setup_x32_x64.bin.exe | C:\Users\admin\Desktop\Uponruner.exe | html | |
MD5:1BB797B159991465A4CEEF0A13533805 | SHA256:0E52663D6A86B622ACAA750C2CC5D7F5F5988DD14B6004B12D3FA71D0377CC8C | |||
| 2392 | Setup_x32_x64.bin.exe | C:\Users\admin\Desktop\updl.url | url | |
MD5:63ECA19A06A3306A8809412209B18736 | SHA256:3B36FB19771EF78578C65167A7718441208E84DDFA8C172A25DC544759B8BB31 | |||
| 2392 | Setup_x32_x64.bin.exe | C:\Users\admin\Desktop\Folder.exe | executable | |
MD5:4538DA85464E576893AEC470FC71229A | SHA256:8AFF0E13328A2129CA13284D80BED1F72100A78A2C4FA696B2AA95A6152F2983 | |||
| 276 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:— | SHA256:— | |||
| 2392 | Setup_x32_x64.bin.exe | C:\Users\admin\Desktop\RobCleanerInstl3183813.exe | executable | |
MD5:3D84583F1C9579C143908CD10995192D | SHA256:6D42D81B33383DEC14C27239B249849101FAF172A6B3BC9C6CB460F299BD5309 | |||
| 276 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 276 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:— | SHA256:— | |||
| 276 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
58
DNS requests
16
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1928 | File.exe | GET | — | 45.144.225.57:80 | http://45.144.225.57/server.txt | unknown | — | — | malicious |
3804 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/Omniroot2025.crl | US | der | 7.78 Kb | whitelisted |
1928 | File.exe | GET | — | 212.193.30.45:80 | http://212.193.30.45/proxies.txt | RU | — | — | malicious |
3280 | askinstall49.exe | GET | 200 | 199.59.243.220:80 | http://ww25.listincode.com/?subid1=20220813-0200-18c3-9506-aa74fb7125a6 | US | html | 1.32 Kb | malicious |
3804 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/DigiCertGlobalRootCA.crl | US | der | 631 b | whitelisted |
2848 | iexplore.exe | GET | 200 | 8.241.45.126:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?bf2580af180538f9 | US | compressed | 60.2 Kb | whitelisted |
276 | iexplore.exe | GET | 200 | 96.16.145.230:80 | http://x1.c.lencr.org/ | US | der | 717 b | whitelisted |
276 | iexplore.exe | GET | 200 | 8.241.45.126:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?cc0203724e2cda9a | US | compressed | 60.2 Kb | whitelisted |
3280 | askinstall49.exe | GET | 200 | 184.24.77.45:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgMaRMZ%2B%2B%2BuiJhlSccYe89niuA%3D%3D | US | der | 503 b | shared |
276 | iexplore.exe | GET | 200 | 8.241.45.126:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?7c329ac4985ce8d8 | US | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3804 | iexplore.exe | 148.251.234.83:443 | iplogger.org | Hetzner Online GmbH | DE | malicious |
3804 | iexplore.exe | 131.253.33.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
276 | iexplore.exe | 148.251.234.83:443 | iplogger.org | Hetzner Online GmbH | DE | malicious |
1304 | iexplore.exe | 148.251.234.83:443 | iplogger.org | Hetzner Online GmbH | DE | malicious |
2848 | iexplore.exe | 148.251.234.83:443 | iplogger.org | Hetzner Online GmbH | DE | malicious |
276 | iexplore.exe | 8.241.45.126:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
2936 | soft.exe | 81.177.49.219:80 | — | JSC RTComm.RU | RU | malicious |
1076 | RobCleanerInstl3183813.exe | 188.114.97.3:443 | dpcapps.me | Cloudflare Inc | US | malicious |
3132 | Proxyupd.exe | 78.46.137.240:21314 | — | Hetzner Online GmbH | DE | malicious |
3792 | Folder.exe | 172.67.143.210:443 | gp.gamebuy768.com | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
iplogger.org |
| shared |
ctldl.windowsupdate.com |
| whitelisted |
dpcapps.me |
| malicious |
gp.gamebuy768.com |
| malicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.listincode.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
r3.o.lencr.org |
| shared |
ww25.listincode.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potential Corporate Privacy Violation | ET POLICY IP Check Domain (iplogger .org in DNS Lookup) |
276 | iexplore.exe | Potential Corporate Privacy Violation | ET POLICY IP Check Domain (iplogger .org in TLS SNI) |
2848 | iexplore.exe | Potential Corporate Privacy Violation | ET POLICY IP Check Domain (iplogger .org in TLS SNI) |
2848 | iexplore.exe | Potential Corporate Privacy Violation | ET POLICY IP Check Domain (iplogger .org in TLS SNI) |
3804 | iexplore.exe | Potential Corporate Privacy Violation | ET POLICY IP Check Domain (iplogger .org in TLS SNI) |
3280 | askinstall49.exe | Potential Corporate Privacy Violation | ET POLICY IP Check Domain (iplogger .org in TLS SNI) |
3804 | iexplore.exe | Potential Corporate Privacy Violation | ET POLICY IP Check Domain (iplogger .org in TLS SNI) |
1928 | File.exe | A Network Trojan was detected | ET MALWARE User-Agent (???) |
1928 | File.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
1 ETPRO signatures available at the full report