| File name: | 9e68a6dcf4297dda701425246945cac9200ef48bf6c0669e89d84bbb74c12dd6.exe |
| Full analysis: | https://app.any.run/tasks/e55ec8de-00c3-40f1-8587-8b989f4ff795 |
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
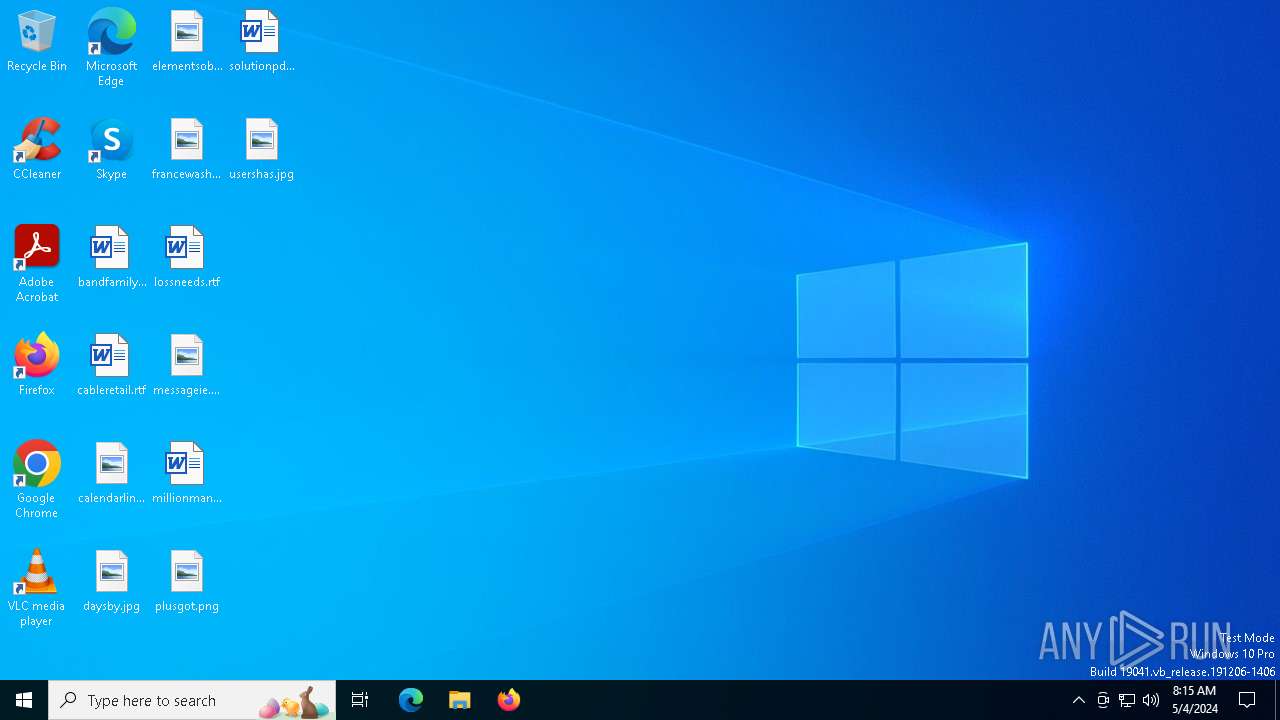
| Analysis date: | May 04, 2024, 08:15:26 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 763D8BAEC13234BEDA899FAD4EB0D416 |
| SHA1: | 96C298717FFAFDE5F4F96B02F94C05EB1F1427E1 |
| SHA256: | 9E68A6DCF4297DDA701425246945CAC9200EF48BF6C0669E89D84BBB74C12DD6 |
| SSDEEP: | 24576:H1LyIOYFWm6cVnv8a/6oxImTxuFR88vhDioZozB4Q/SuWVhqolA:H1uIOGWm6cVnv8a/64RTxuFR88pDioSV |
MALICIOUS
Drops the executable file immediately after the start
- 9e68a6dcf4297dda701425246945cac9200ef48bf6c0669e89d84bbb74c12dd6.exe (PID: 6204)
Steals credentials from Web Browsers
- 9e68a6dcf4297dda701425246945cac9200ef48bf6c0669e89d84bbb74c12dd6.exe (PID: 6436)
Actions looks like stealing of personal data
- 9e68a6dcf4297dda701425246945cac9200ef48bf6c0669e89d84bbb74c12dd6.exe (PID: 6436)
Scans artifacts that could help determine the target
- 9e68a6dcf4297dda701425246945cac9200ef48bf6c0669e89d84bbb74c12dd6.exe (PID: 6436)
AGENTTESLA has been detected (YARA)
- 9e68a6dcf4297dda701425246945cac9200ef48bf6c0669e89d84bbb74c12dd6.exe (PID: 6436)
AGENTTESLA has been detected (SURICATA)
- 9e68a6dcf4297dda701425246945cac9200ef48bf6c0669e89d84bbb74c12dd6.exe (PID: 6436)
SUSPICIOUS
Process drops legitimate windows executable
- 9e68a6dcf4297dda701425246945cac9200ef48bf6c0669e89d84bbb74c12dd6.exe (PID: 6204)
Application launched itself
- 9e68a6dcf4297dda701425246945cac9200ef48bf6c0669e89d84bbb74c12dd6.exe (PID: 6204)
Starts a Microsoft application from unusual location
- 9e68a6dcf4297dda701425246945cac9200ef48bf6c0669e89d84bbb74c12dd6.exe (PID: 6436)
- 9e68a6dcf4297dda701425246945cac9200ef48bf6c0669e89d84bbb74c12dd6.exe (PID: 6204)
Potential Corporate Privacy Violation
- 9e68a6dcf4297dda701425246945cac9200ef48bf6c0669e89d84bbb74c12dd6.exe (PID: 6436)
Device Retrieving External IP Address Detected
- 9e68a6dcf4297dda701425246945cac9200ef48bf6c0669e89d84bbb74c12dd6.exe (PID: 6436)
Checks for external IP
- 9e68a6dcf4297dda701425246945cac9200ef48bf6c0669e89d84bbb74c12dd6.exe (PID: 6436)
Connects to SMTP port
- 9e68a6dcf4297dda701425246945cac9200ef48bf6c0669e89d84bbb74c12dd6.exe (PID: 6436)
The process connected to a server suspected of theft
- 9e68a6dcf4297dda701425246945cac9200ef48bf6c0669e89d84bbb74c12dd6.exe (PID: 6436)
INFO
Reads the computer name
- 9e68a6dcf4297dda701425246945cac9200ef48bf6c0669e89d84bbb74c12dd6.exe (PID: 6204)
- 9e68a6dcf4297dda701425246945cac9200ef48bf6c0669e89d84bbb74c12dd6.exe (PID: 6436)
Checks supported languages
- 9e68a6dcf4297dda701425246945cac9200ef48bf6c0669e89d84bbb74c12dd6.exe (PID: 6204)
- 9e68a6dcf4297dda701425246945cac9200ef48bf6c0669e89d84bbb74c12dd6.exe (PID: 6436)
Reads the machine GUID from the registry
- 9e68a6dcf4297dda701425246945cac9200ef48bf6c0669e89d84bbb74c12dd6.exe (PID: 6204)
- 9e68a6dcf4297dda701425246945cac9200ef48bf6c0669e89d84bbb74c12dd6.exe (PID: 6436)
Reads the software policy settings
- 9e68a6dcf4297dda701425246945cac9200ef48bf6c0669e89d84bbb74c12dd6.exe (PID: 6436)
Reads Environment values
- 9e68a6dcf4297dda701425246945cac9200ef48bf6c0669e89d84bbb74c12dd6.exe (PID: 6436)
Checks proxy server information
- 9e68a6dcf4297dda701425246945cac9200ef48bf6c0669e89d84bbb74c12dd6.exe (PID: 6436)
Reads Microsoft Office registry keys
- 9e68a6dcf4297dda701425246945cac9200ef48bf6c0669e89d84bbb74c12dd6.exe (PID: 6436)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
AgentTesla
(PID) Process(6436) 9e68a6dcf4297dda701425246945cac9200ef48bf6c0669e89d84bbb74c12dd6.exe
Protocolsmtp
Hostnl9.nlkoddos.com
Port587
Username99@jolnsmad.site
PasswordMyname321@
TRiD
| .exe | | | Win64 Executable (generic) (61.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.6) |
| .exe | | | Win32 Executable (generic) (10) |
| .exe | | | Win16/32 Executable Delphi generic (4.6) |
| .exe | | | Generic Win/DOS Executable (4.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:05:03 01:53:39+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 712192 |
| InitializedDataSize: | 8704 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xafdee |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.1.0.0 |
| ProductVersionNumber: | 1.1.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | Microsoft® C Runtime Library _codecvt_ids |
| CompanyName: | Microsoft Corporation |
| FileDescription: | .Netframwork |
| FileVersion: | 1.1.0.0 |
| InternalName: | lKxu.exe |
| LegalCopyright: | Copyright: © Microsoft Corporation. |
| LegalTrademarks: | All rights reserved. |
| OriginalFileName: | lKxu.exe |
| ProductName: | Microsoft® Visual Studio® |
| ProductVersion: | 1.1.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
126
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 5032 | C:\Users\admin\AppData\Local\Microsoft\OneDrive\19.043.0304.0013\FileCoAuth.exe -Embedding | C:\Users\admin\AppData\Local\Microsoft\OneDrive\19.043.0304.0013\FileCoAuth.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft OneDriveFile Co-Authoring Executable Exit code: 0 Version: 19.043.0304.0013 Modules
| |||||||||||||||
| 6204 | "C:\Users\admin\AppData\Local\Temp\9e68a6dcf4297dda701425246945cac9200ef48bf6c0669e89d84bbb74c12dd6.exe" | C:\Users\admin\AppData\Local\Temp\9e68a6dcf4297dda701425246945cac9200ef48bf6c0669e89d84bbb74c12dd6.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: .Netframwork Exit code: 0 Version: 1.1.0.0 Modules
| |||||||||||||||
| 6436 | "C:\Users\admin\AppData\Local\Temp\9e68a6dcf4297dda701425246945cac9200ef48bf6c0669e89d84bbb74c12dd6.exe" | C:\Users\admin\AppData\Local\Temp\9e68a6dcf4297dda701425246945cac9200ef48bf6c0669e89d84bbb74c12dd6.exe | 9e68a6dcf4297dda701425246945cac9200ef48bf6c0669e89d84bbb74c12dd6.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: .Netframwork Version: 1.1.0.0 Modules
AgentTesla(PID) Process(6436) 9e68a6dcf4297dda701425246945cac9200ef48bf6c0669e89d84bbb74c12dd6.exe Protocolsmtp Hostnl9.nlkoddos.com Port587 Username99@jolnsmad.site PasswordMyname321@ | |||||||||||||||
Total events
1 695
Read events
1 680
Write events
15
Delete events
0
Modification events
| (PID) Process: | (6436) 9e68a6dcf4297dda701425246945cac9200ef48bf6c0669e89d84bbb74c12dd6.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (6436) 9e68a6dcf4297dda701425246945cac9200ef48bf6c0669e89d84bbb74c12dd6.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6436) 9e68a6dcf4297dda701425246945cac9200ef48bf6c0669e89d84bbb74c12dd6.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (6436) 9e68a6dcf4297dda701425246945cac9200ef48bf6c0669e89d84bbb74c12dd6.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (6436) 9e68a6dcf4297dda701425246945cac9200ef48bf6c0669e89d84bbb74c12dd6.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (6436) 9e68a6dcf4297dda701425246945cac9200ef48bf6c0669e89d84bbb74c12dd6.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (6436) 9e68a6dcf4297dda701425246945cac9200ef48bf6c0669e89d84bbb74c12dd6.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (6436) 9e68a6dcf4297dda701425246945cac9200ef48bf6c0669e89d84bbb74c12dd6.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (6436) 9e68a6dcf4297dda701425246945cac9200ef48bf6c0669e89d84bbb74c12dd6.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6436) 9e68a6dcf4297dda701425246945cac9200ef48bf6c0669e89d84bbb74c12dd6.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5032 | FileCoAuth.exe | C:\Users\admin\AppData\Local\Microsoft\OneDrive\logs\Common\FileCoAuth-2024-05-04.0816.5032.1.aodl | binary | |
MD5:28DCA2FF4B34B5A52A2E59DF202A6ED3 | SHA256:33BACCB7296F1ED1F995FC77A23049F261CF391AC0388F9E8DD161F8C17B7F94 | |||
| 5032 | FileCoAuth.exe | C:\Users\admin\AppData\Local\Microsoft\OneDrive\logs\Common\FileCoAuth-2024-05-04.0816.5032.1.odl | binary | |
MD5:E7ED663936E9689AC3023F6F25409B48 | SHA256:E88CB7AD811D5C1B7FA05ADA2CEE3C046F9B27B34BC38AC50C651E30462DCEBA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
53
DNS requests
19
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
736 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | unknown |
4680 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAzlnDD9eoNTLi0BRrMy%2BWU%3D | unknown | — | — | unknown |
5228 | svchost.exe | GET | 200 | 104.117.186.29:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
6436 | 9e68a6dcf4297dda701425246945cac9200ef48bf6c0669e89d84bbb74c12dd6.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/line/?fields=hosting | unknown | — | — | unknown |
6788 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | unknown |
4288 | SIHClient.exe | GET | 200 | 104.117.186.29:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | unknown |
4288 | SIHClient.exe | GET | 200 | 104.117.186.29:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | unknown |
2908 | OfficeClickToRun.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 239.255.255.250:1900 | — | — | — | unknown |
5228 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
5712 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
5140 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
5228 | svchost.exe | 104.117.186.29:80 | www.microsoft.com | AKAMAI-AS | US | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4680 | SearchApp.exe | 93.186.134.216:443 | — | TELECOM ITALIA SPARKLE S.p.A. | IT | unknown |
4680 | SearchApp.exe | 93.186.134.219:443 | — | TELECOM ITALIA SPARKLE S.p.A. | IT | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4680 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
api.ipify.org |
| shared |
ip-api.com |
| shared |
go.microsoft.com |
| whitelisted |
nl9.nlkoddos.com |
| malicious |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2184 | svchost.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
6436 | 9e68a6dcf4297dda701425246945cac9200ef48bf6c0669e89d84bbb74c12dd6.exe | Misc activity | ET INFO External IP Address Lookup Domain (ipify .org) in TLS SNI |
6436 | 9e68a6dcf4297dda701425246945cac9200ef48bf6c0669e89d84bbb74c12dd6.exe | Potential Corporate Privacy Violation | AV POLICY Internal Host Retrieving External IP Address (ip-api. com) |
6436 | 9e68a6dcf4297dda701425246945cac9200ef48bf6c0669e89d84bbb74c12dd6.exe | Device Retrieving External IP Address Detected | POLICY [ANY.RUN] External Hosting Lookup by ip-api |
6436 | 9e68a6dcf4297dda701425246945cac9200ef48bf6c0669e89d84bbb74c12dd6.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup ip-api.com |
6436 | 9e68a6dcf4297dda701425246945cac9200ef48bf6c0669e89d84bbb74c12dd6.exe | Misc activity | INFO [ANY.RUN] SMTP email client opens transfer with server (EHLO) |
6436 | 9e68a6dcf4297dda701425246945cac9200ef48bf6c0669e89d84bbb74c12dd6.exe | Successful Credential Theft Detected | STEALER [ANY.RUN] Exfiltration via SMTP (AgentTesla) |