| File name: | dhl_doc897654657687.zip |
| Full analysis: | https://app.any.run/tasks/de0c2035-de5b-4017-b322-b5697c34f725 |
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | December 06, 2019, 13:42:19 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
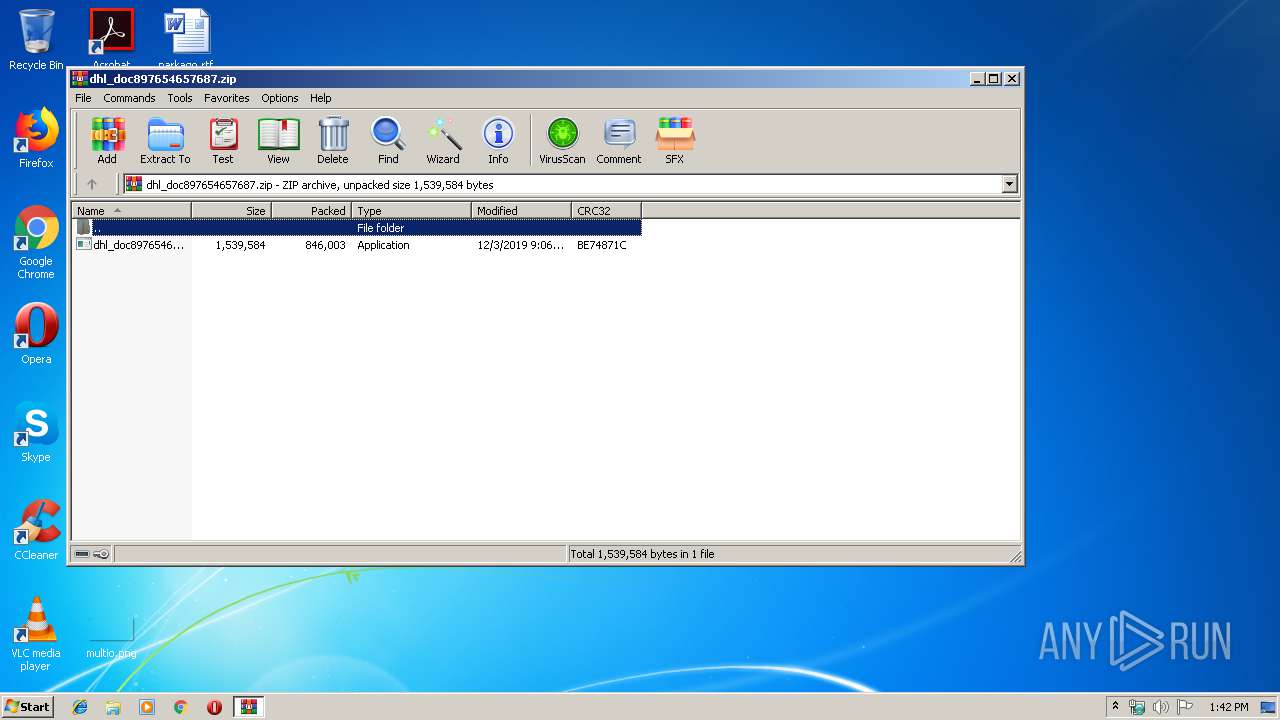
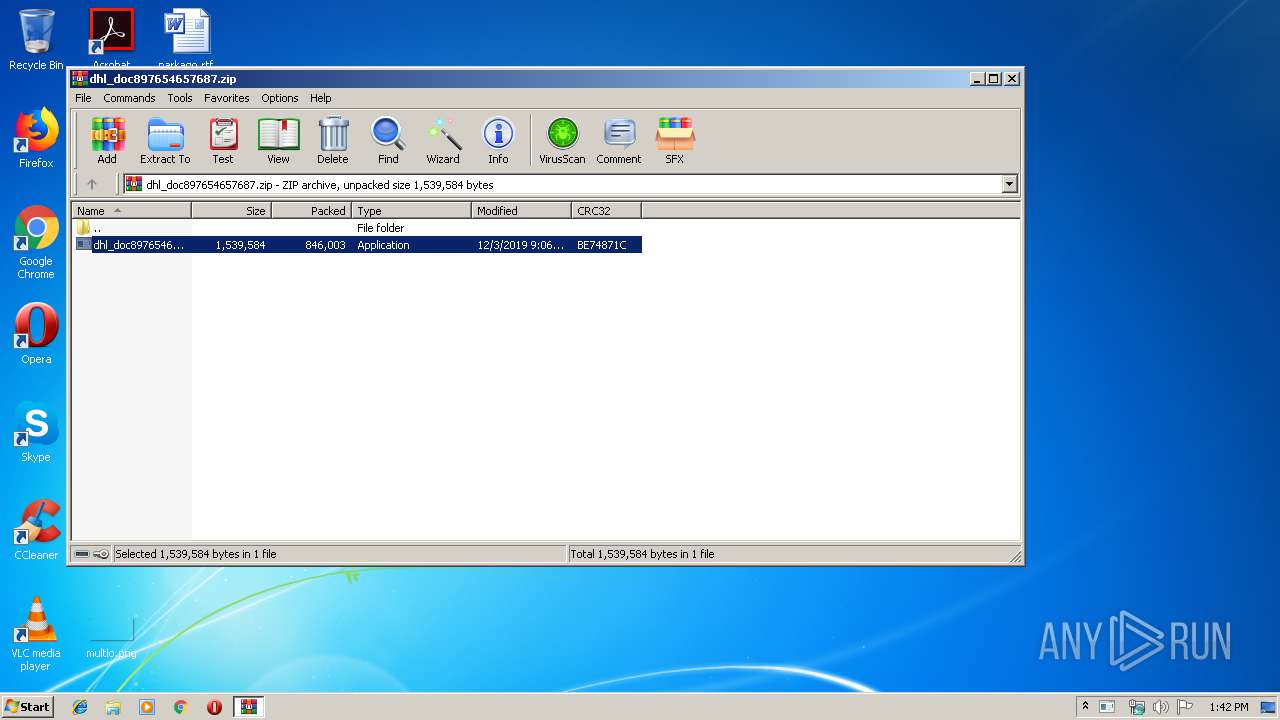
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 256A44C226AAF9A90C3DCCF0FBE992F9 |
| SHA1: | F97F855E5D2D739D2C82FEA95BEB30246EF6FCBD |
| SHA256: | 9E5E957C144299E1316833A02E4176DEAEEABCCEC7D05C4C884A3F3C8629D33D |
| SSDEEP: | 12288:MJO72HKicPNmZH5DCAqhRyENFBf0s8oX0x1Z1uB/c32SZl7YoO9nOk1JEZdHNpPD:MJOwKXPUwAcNFesbKz32M7Yo9GEnNjB |
MALICIOUS
Application was dropped or rewritten from another process
- dhl_doc897654657687.exe (PID: 3900)
- dhl_doc897654657687.exe (PID: 1908)
- RegAsm.exe (PID: 4056)
- RegAsm.exe (PID: 2184)
AGENTTESLA was detected
- RegAsm.exe (PID: 4056)
- RegAsm.exe (PID: 2184)
Changes the autorun value in the registry
- RegAsm.exe (PID: 4056)
- RegAsm.exe (PID: 2184)
Actions looks like stealing of personal data
- RegAsm.exe (PID: 4056)
- RegAsm.exe (PID: 2184)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2240)
- RegAsm.exe (PID: 4056)
- RegAsm.exe (PID: 2184)
Creates files in the user directory
- RegAsm.exe (PID: 4056)
- RegAsm.exe (PID: 2184)
Uses RUNDLL32.EXE to load library
- dhl_doc897654657687.exe (PID: 3900)
- dhl_doc897654657687.exe (PID: 1908)
Reads Internet Cache Settings
- rundll32.exe (PID: 2060)
- rundll32.exe (PID: 1520)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:12:03 09:06:00 |
| ZipCRC: | 0xbe74871c |
| ZipCompressedSize: | 846003 |
| ZipUncompressedSize: | 1539584 |
| ZipFileName: | dhl_doc897654657687.exe |
Total processes
40
Monitored processes
7
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1520 | "C:\Windows\system32\rundll32.exe" "C:\Windows\system32\WININET.dll",DispatchAPICall 1 | C:\Windows\system32\rundll32.exe | — | dhl_doc897654657687.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1908 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2240.28576\dhl_doc897654657687.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2240.28576\dhl_doc897654657687.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2060 | "C:\Windows\system32\rundll32.exe" "C:\Windows\system32\WININET.dll",DispatchAPICall 1 | C:\Windows\system32\rundll32.exe | — | dhl_doc897654657687.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2184 | "C:\\\\Windows\\\\Microsoft.NET\\\\Framework\\\\v2.0.50727\\\\RegAsm.exe" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\RegAsm.exe | dhl_doc897654657687.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 2.0.50727.5420 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 2240 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\dhl_doc897654657687.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3900 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2240.26563\dhl_doc897654657687.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2240.26563\dhl_doc897654657687.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 4056 | "C:\\\\Windows\\\\Microsoft.NET\\\\Framework\\\\v2.0.50727\\\\RegAsm.exe" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\RegAsm.exe | dhl_doc897654657687.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Exit code: 4294967295 Version: 2.0.50727.5420 (Win7SP1.050727-5400) Modules
| |||||||||||||||
Total events
694
Read events
628
Write events
66
Delete events
0
Modification events
| (PID) Process: | (2240) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2240) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2240) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2240) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-1 |
Value: Network | |||
| (PID) Process: | (2240) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\dhl_doc897654657687.zip | |||
| (PID) Process: | (2240) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2240) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2240) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2240) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2240) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
4
Suspicious files
0
Text files
4
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2060 | rundll32.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 2240 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2240.28576\dhl_doc897654657687.exe | executable | |
MD5:— | SHA256:— | |||
| 2240 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2240.26563\dhl_doc897654657687.exe | executable | |
MD5:— | SHA256:— | |||
| 4056 | RegAsm.exe | C:\Users\admin\AppData\Local\Temp\1248c86a-67ca-40b0-bc90-842e9c5f5969 | sqlite | |
MD5:— | SHA256:— | |||
| 2184 | RegAsm.exe | C:\Users\admin\AppData\Local\Temp\f84b3c21-f03a-4727-8dad-2153fb60be17 | sqlite | |
MD5:— | SHA256:— | |||
| 2060 | rundll32.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\K2NLTDG8\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
| 2060 | rundll32.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\1UBFIJ8P\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
| 2060 | rundll32.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\9A85MI8N\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
| 4056 | RegAsm.exe | C:\Users\admin\AppData\Roaming\NewApp\NewApp.exe | executable | |
MD5:278EDBD499374BF73621F8C1F969D894 | SHA256:C6999B9F79932C3B4F1C461A69D9DC8DC301D6A155ABC33EFE1B6E9E4A038391 | |||
| 2060 | rundll32.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\O5EG7CV1\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
2
Threats
2
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4056 | RegAsm.exe | 130.185.87.19:587 | mail.artecimel.pt | Almouroltec Servicos De Informatica E Internet Lda | PT | unknown |
2184 | RegAsm.exe | 130.185.87.19:587 | mail.artecimel.pt | Almouroltec Servicos De Informatica E Internet Lda | PT | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.timeapi.org |
| unknown |
mail.artecimel.pt |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4056 | RegAsm.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
2184 | RegAsm.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |