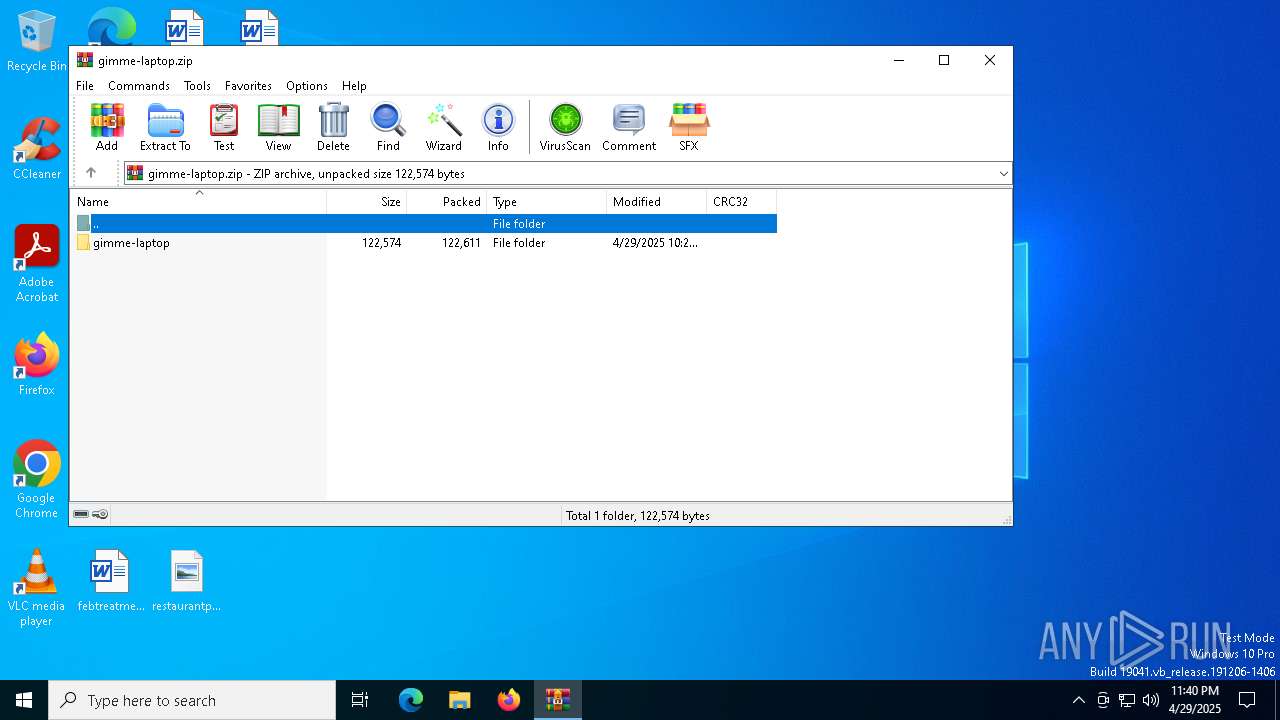
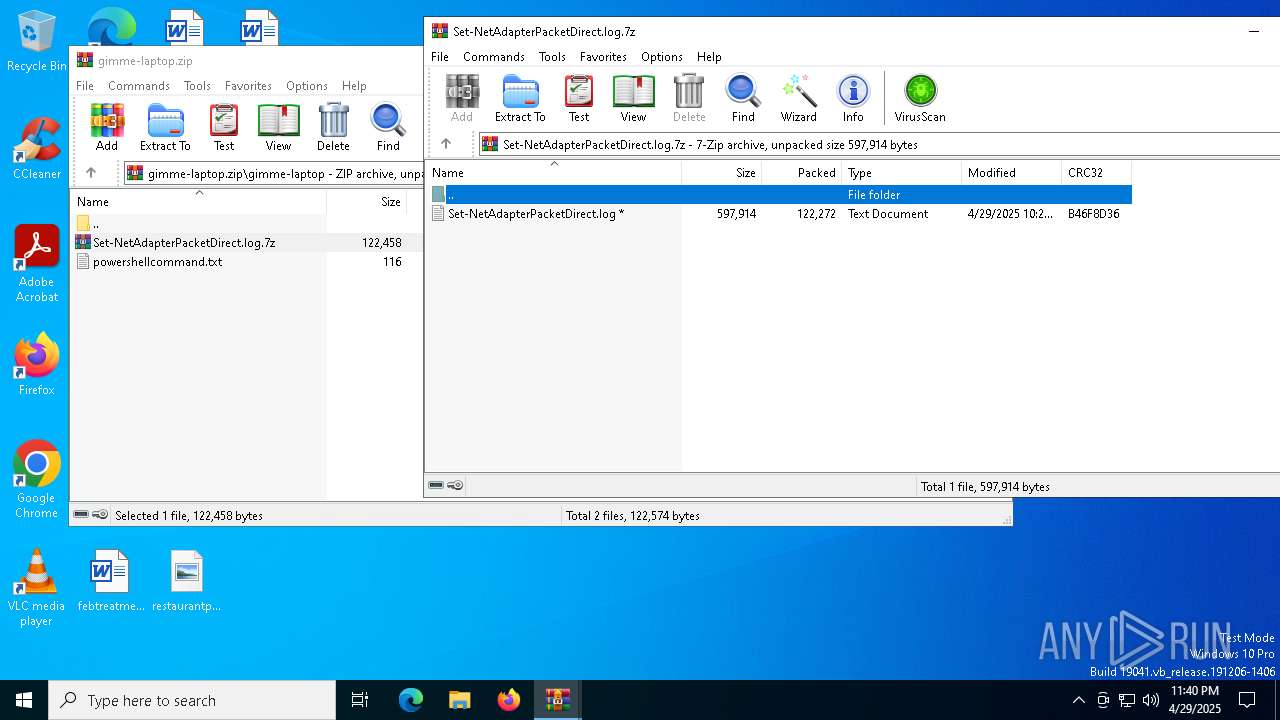
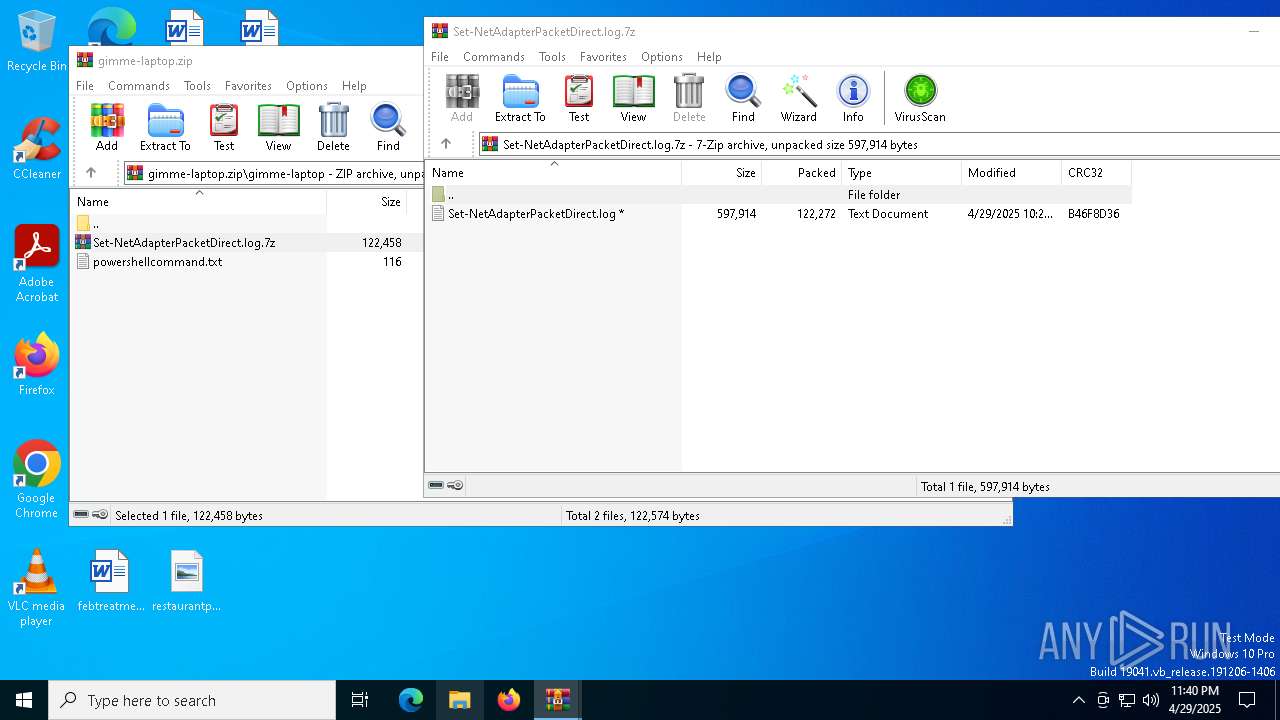
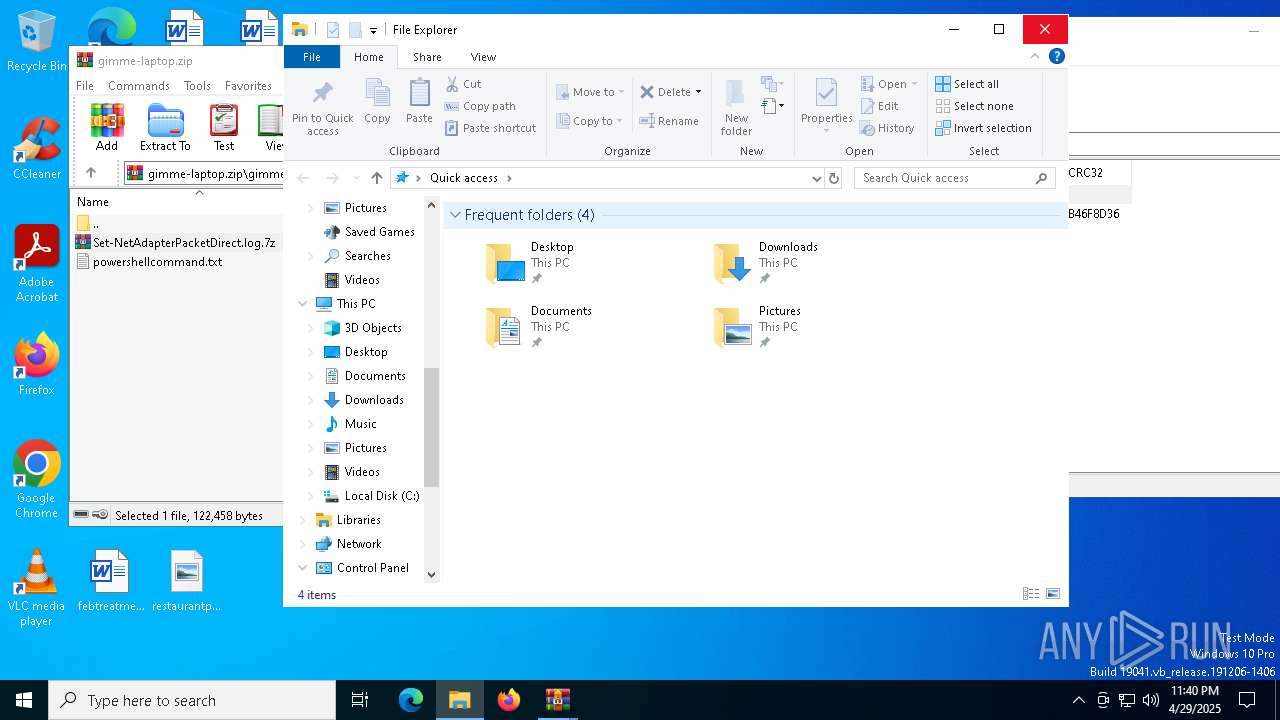
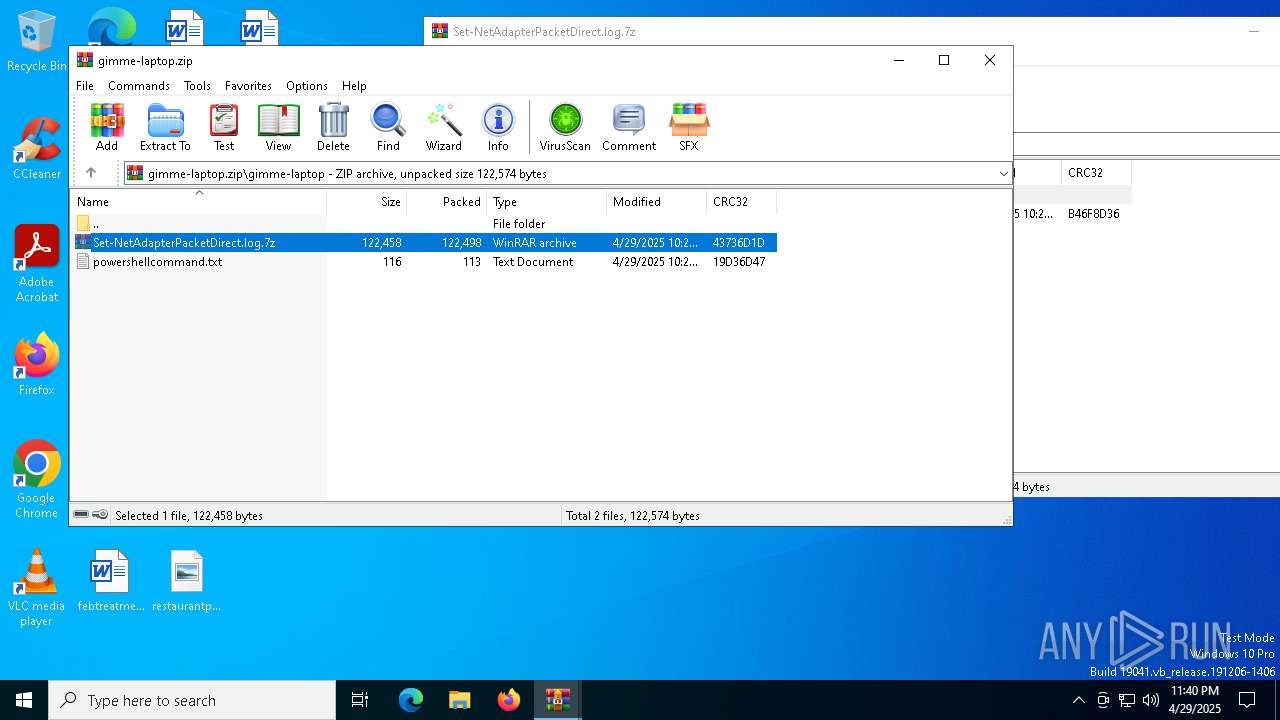
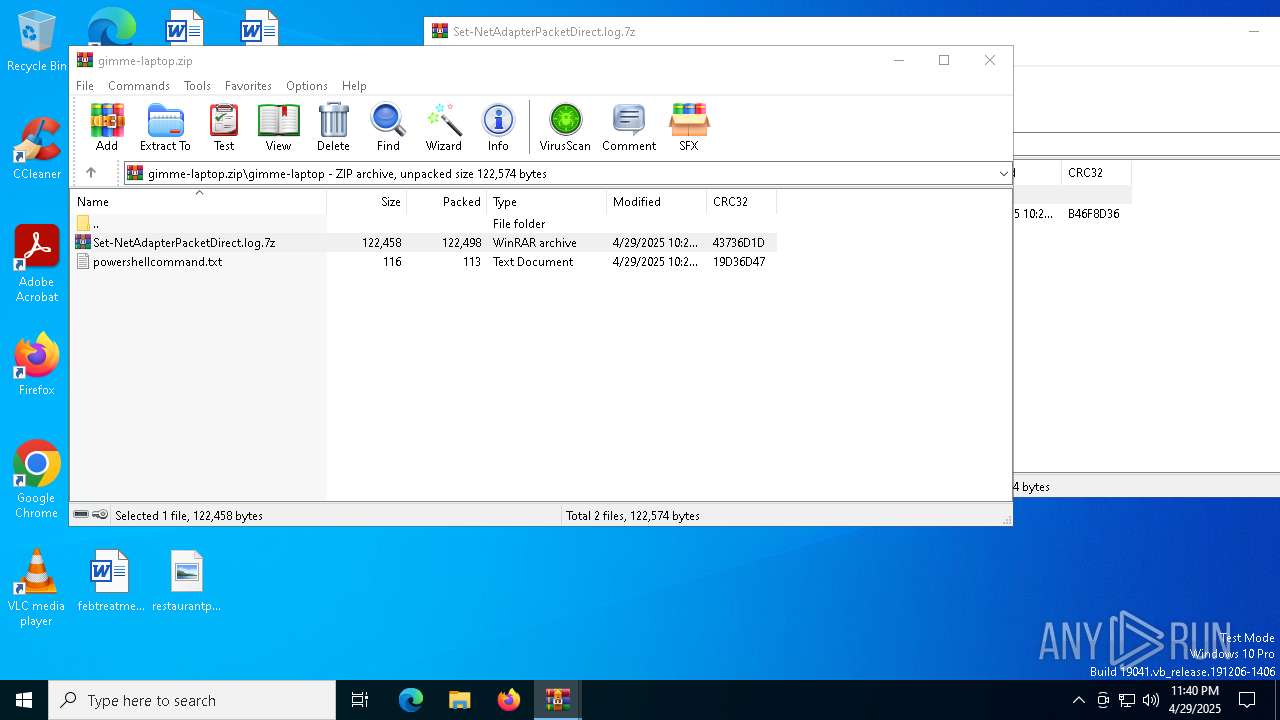
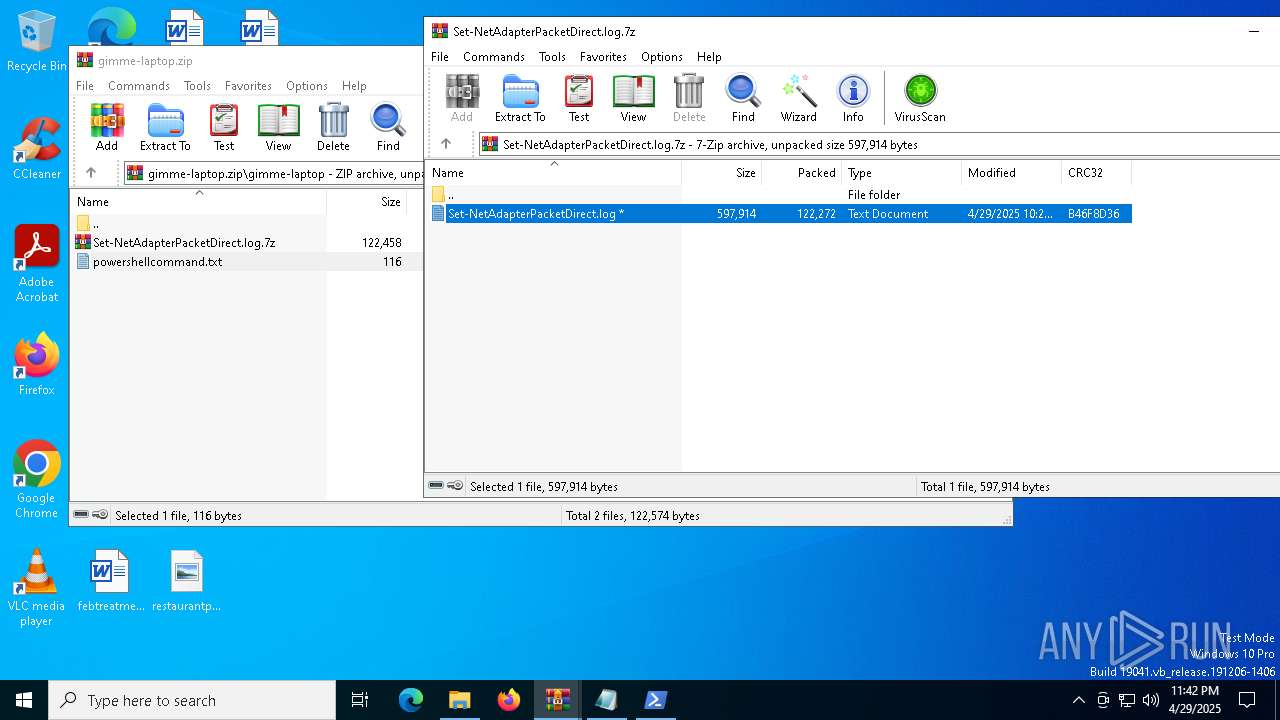
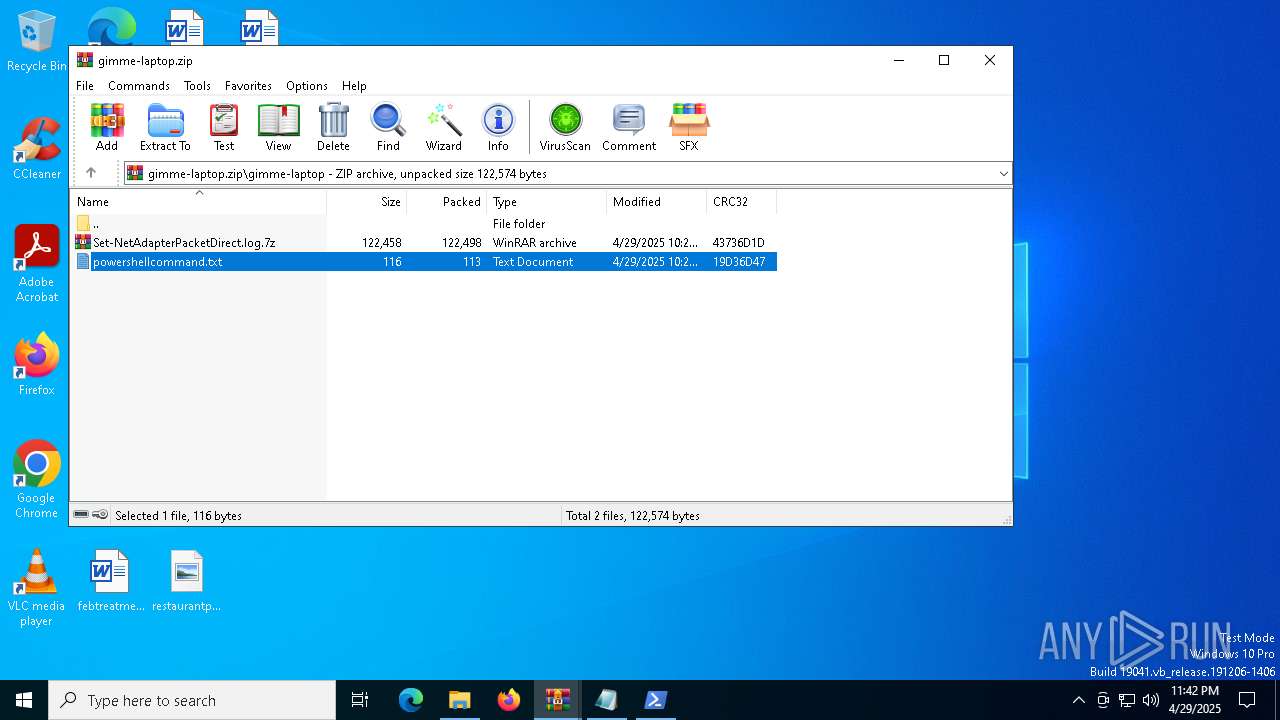
| File name: | gimme-laptop.zip |
| Full analysis: | https://app.any.run/tasks/5034c49f-2b39-4c56-a49a-dbf57e2fc0f3 |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | April 29, 2025, 23:40:17 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=store |
| MD5: | 8A75155531EBB01982211BCB38547728 |
| SHA1: | 913BAF18B563831D6EAB66A7BBE21397DB449FA9 |
| SHA256: | 9E51BE4B50B7CB8BD5156EBCC43603DE7F5A8EDA22D1B269F149CB8735C2E9F8 |
| SSDEEP: | 3072:JBxCcDDi0JyLUYdf9S6ucjjS71ibvOOSRlp35ivl25:JmNnBdFS6BjGqGTP5 |
MALICIOUS
ASYNCRAT has been detected (MUTEX)
- powershell.exe (PID: 5544)
ASYNCRAT has been detected (SURICATA)
- powershell.exe (PID: 5544)
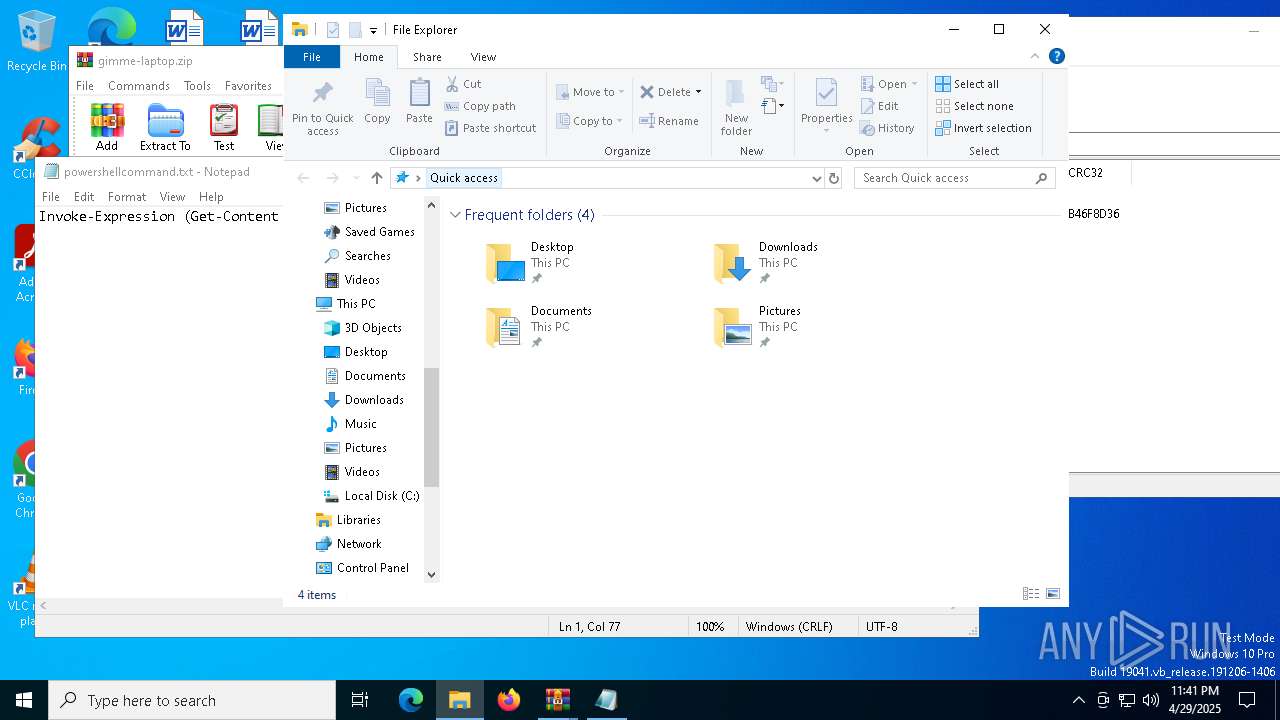
Actions looks like stealing of personal data
- powershell.exe (PID: 5544)
Steals credentials from Web Browsers
- powershell.exe (PID: 5544)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 7316)
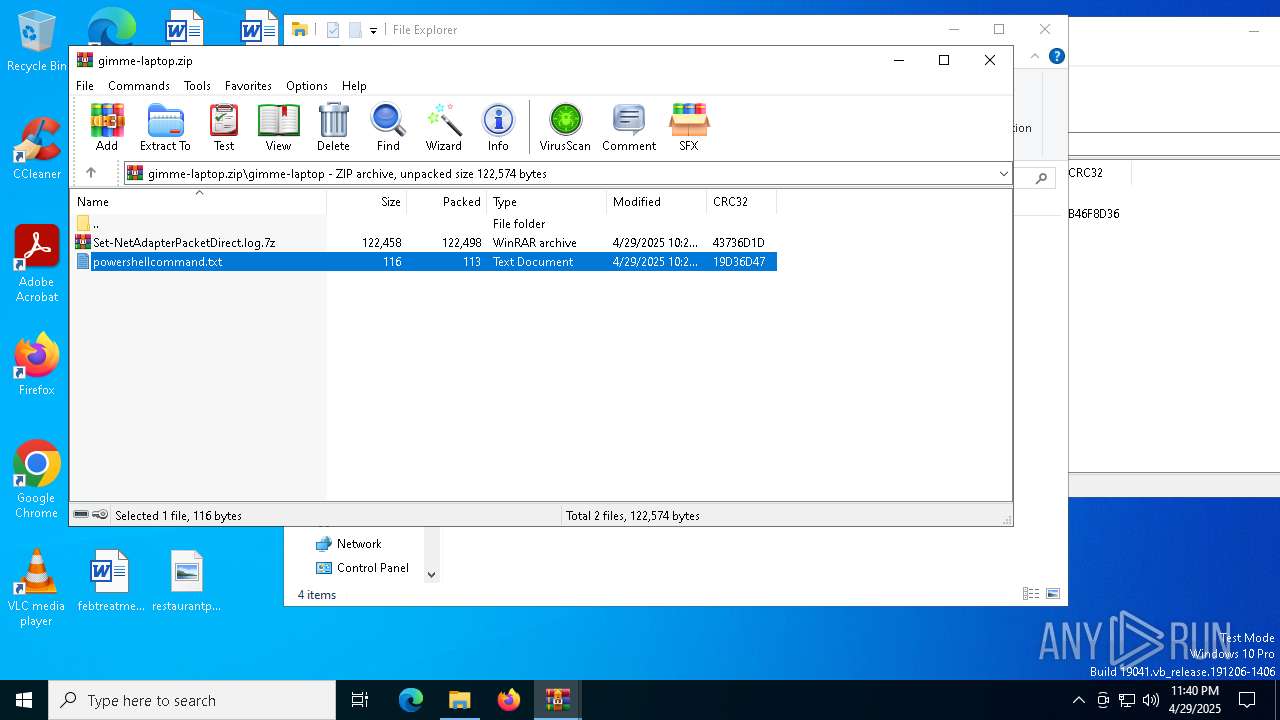
Generic archive extractor
- WinRAR.exe (PID: 7316)
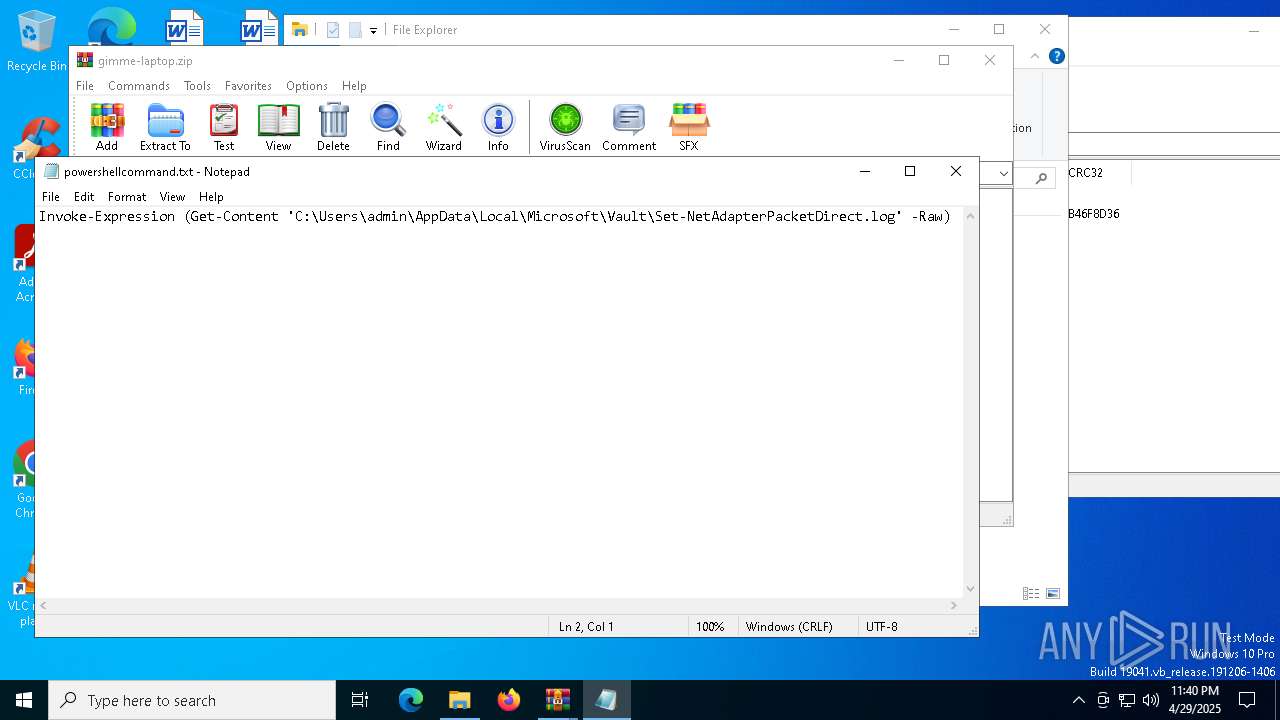
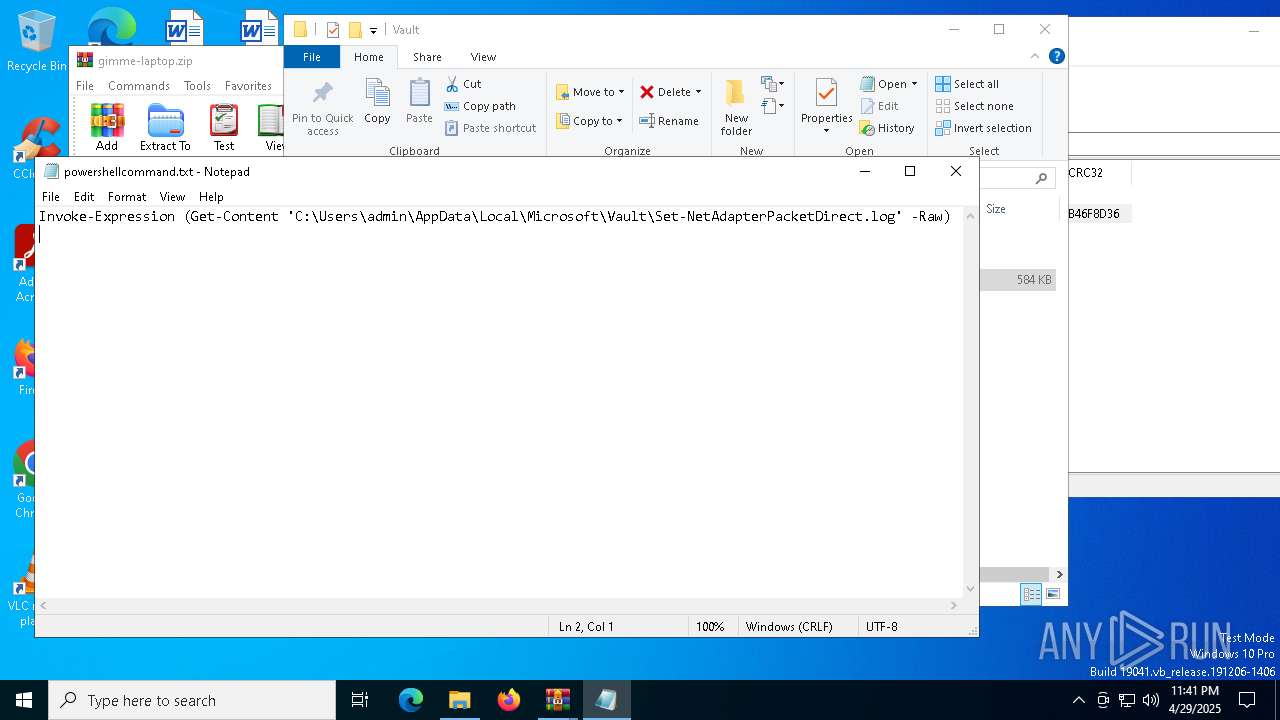
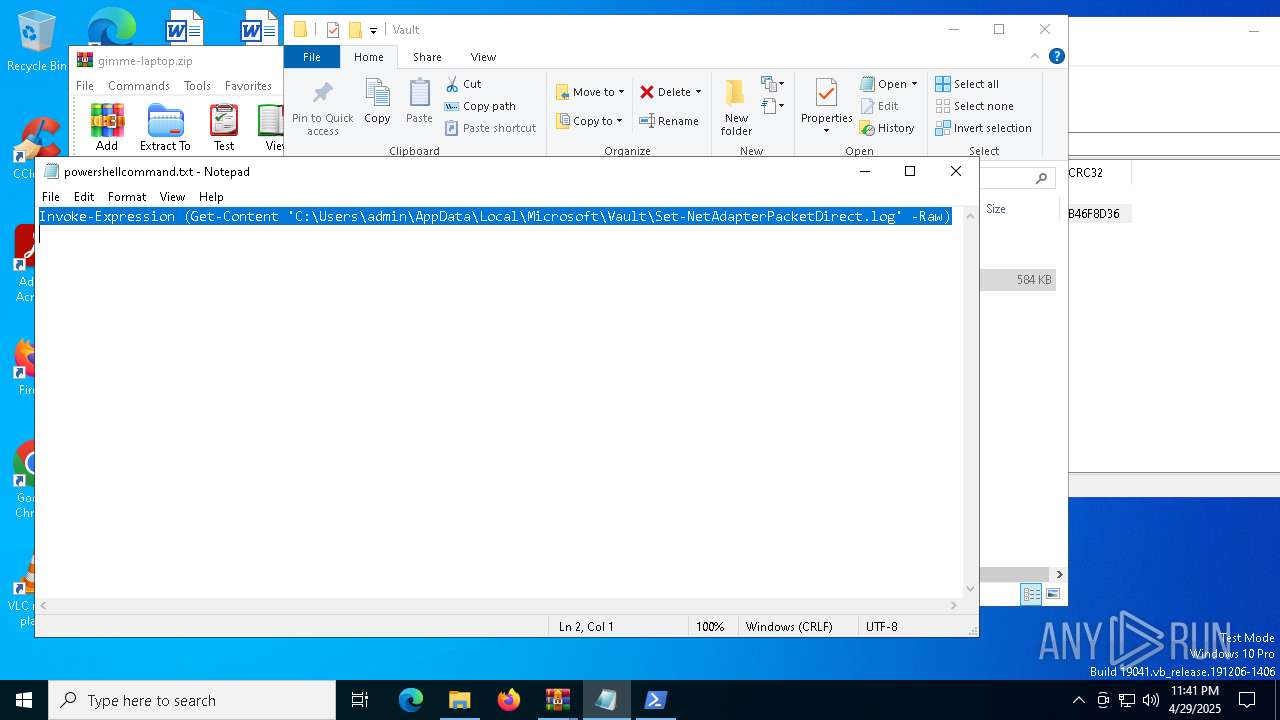
Start notepad (likely ransomware note)
- WinRAR.exe (PID: 7316)
Application launched itself
- WinRAR.exe (PID: 7316)
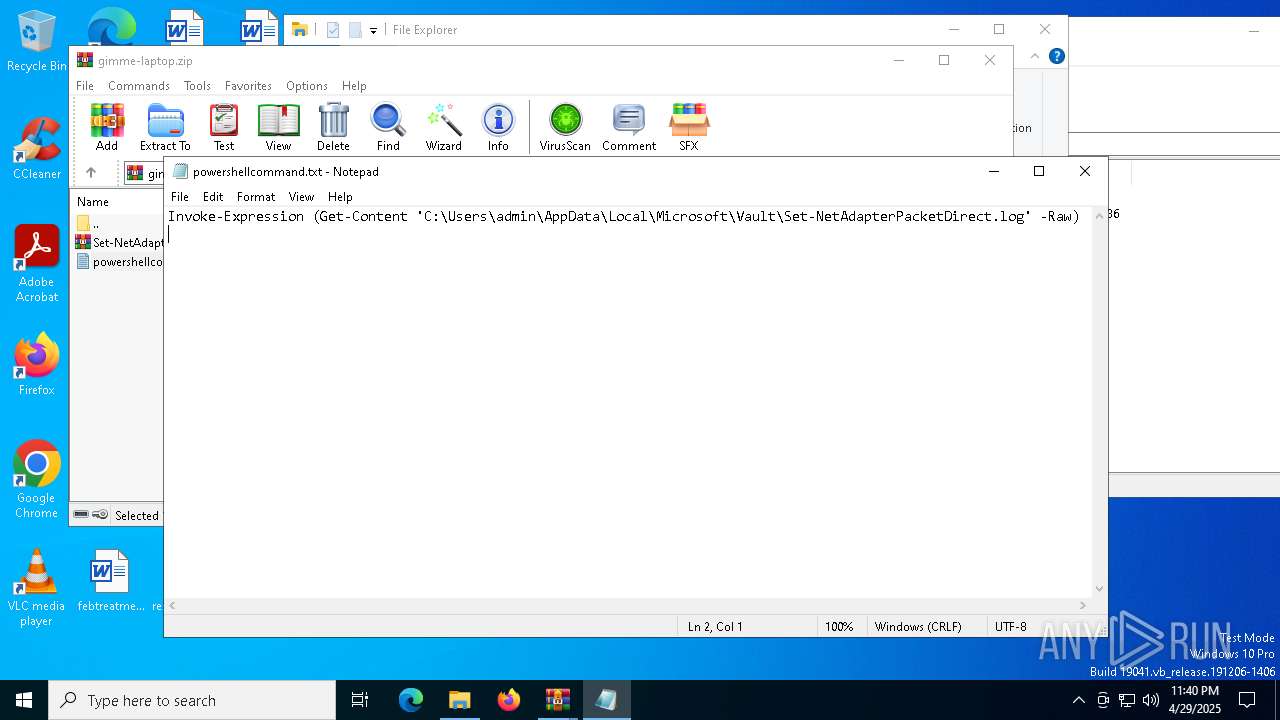
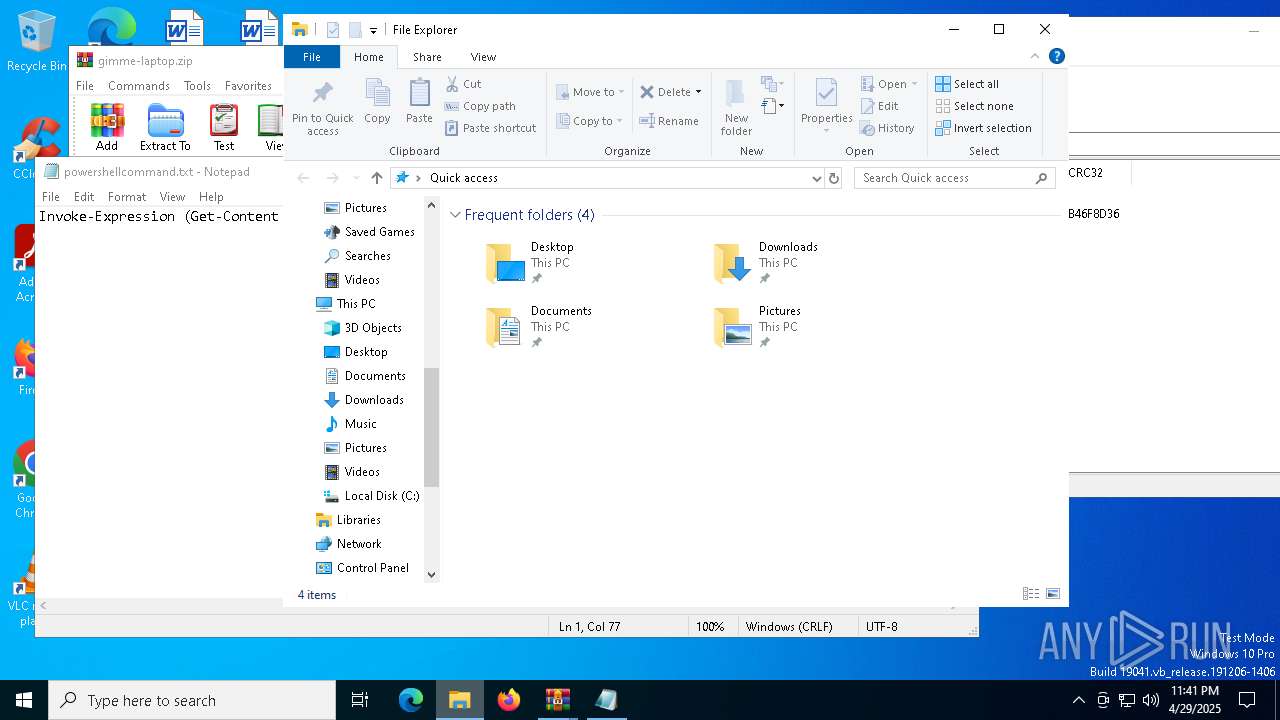
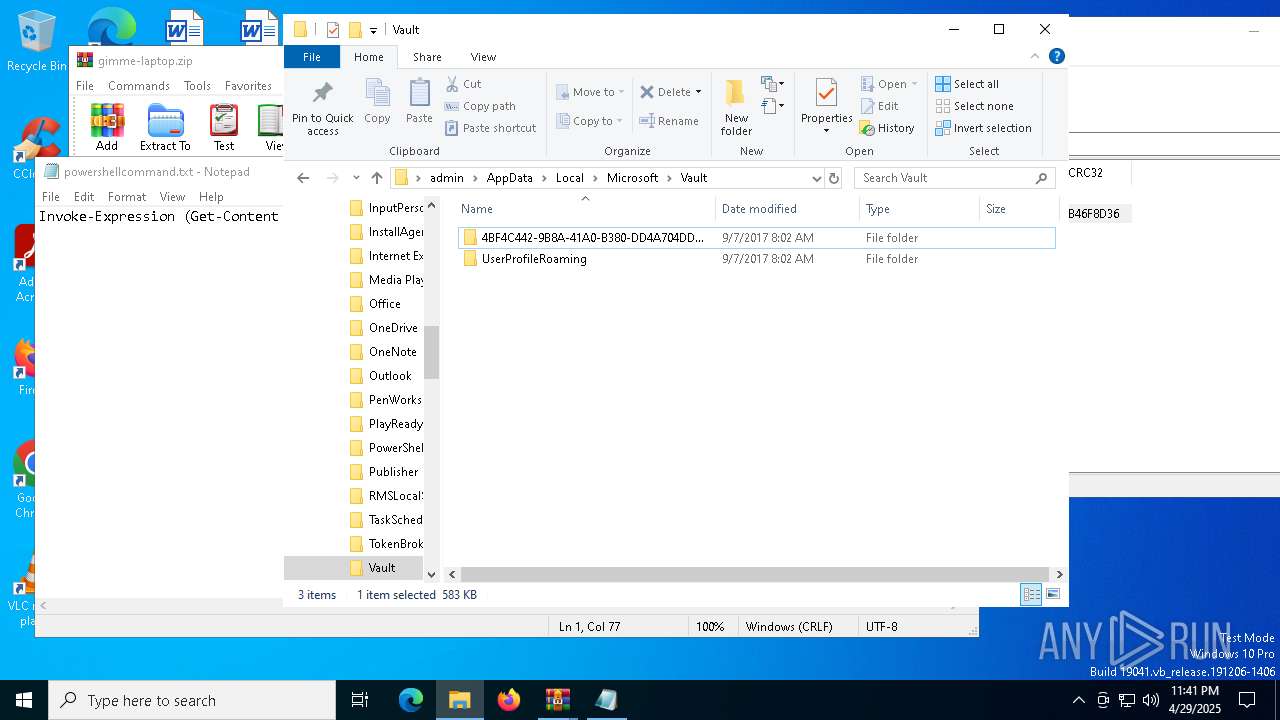
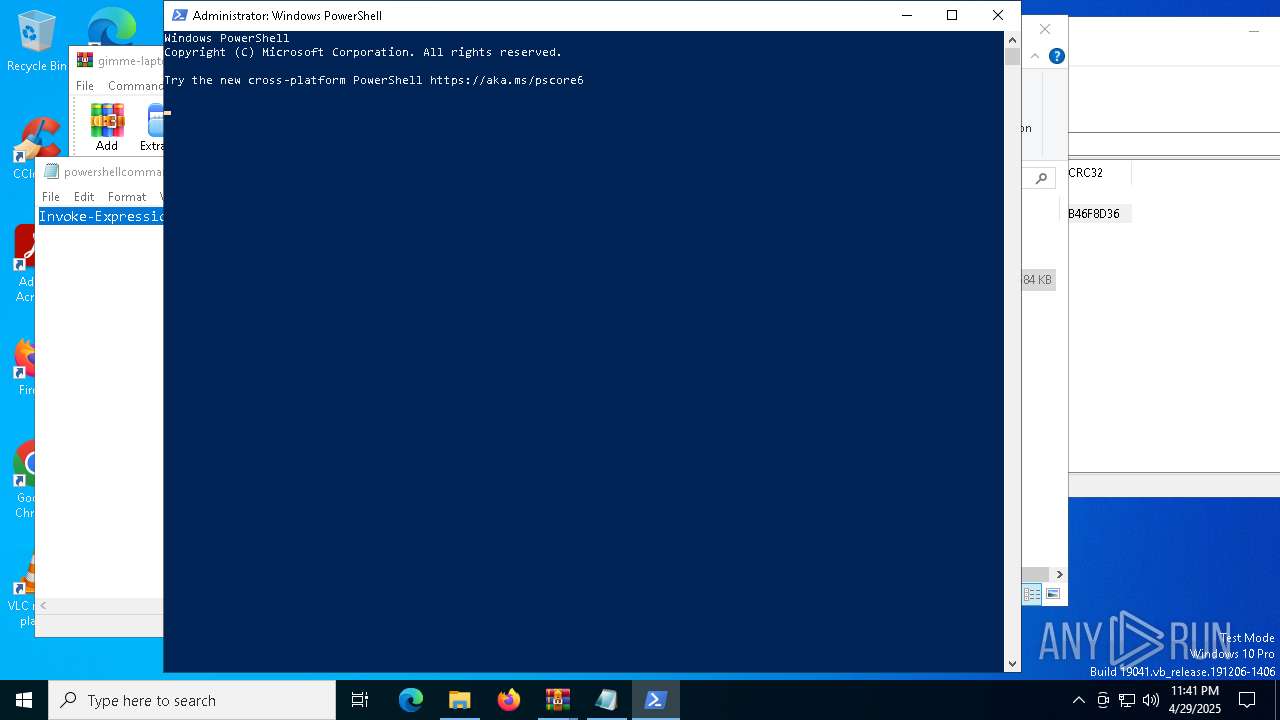
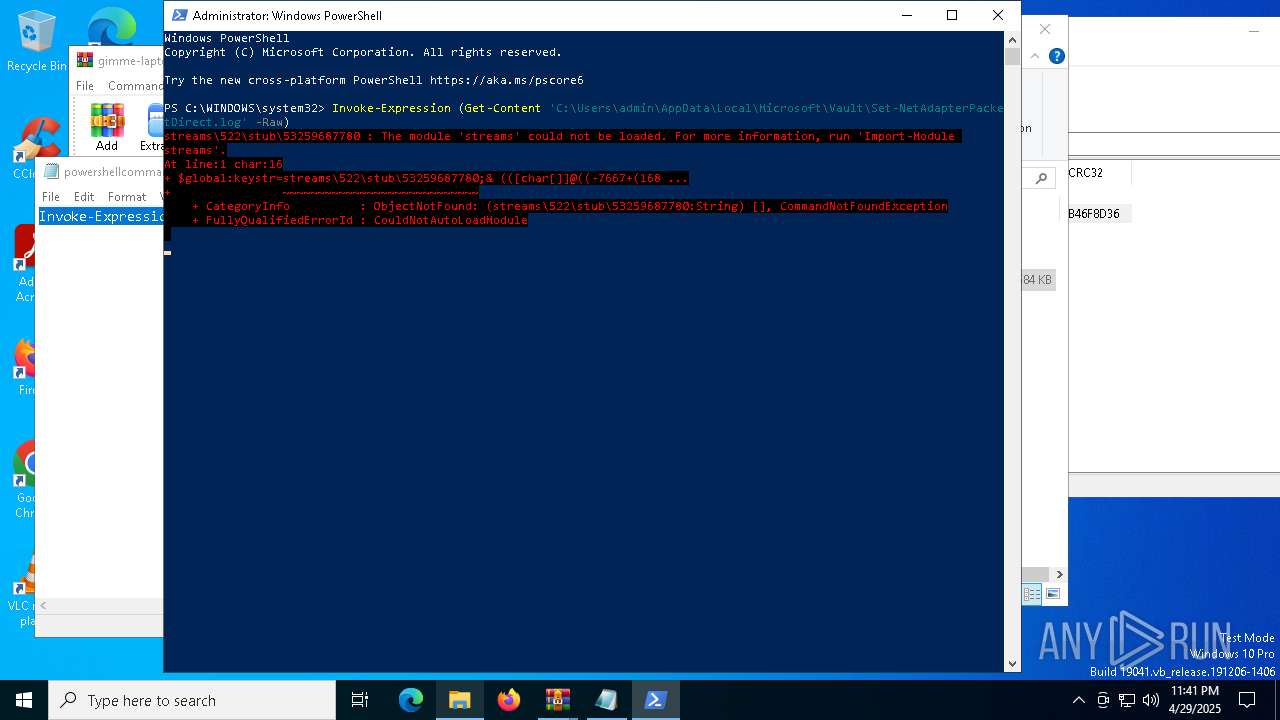
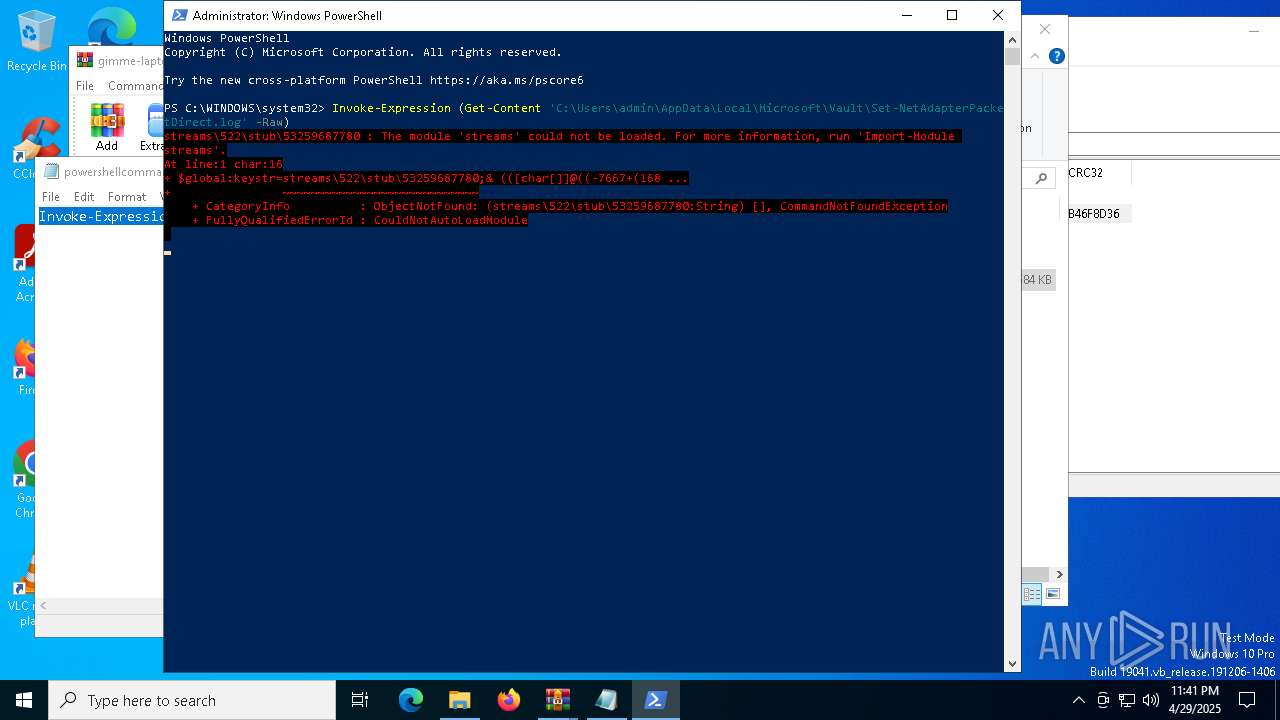
Gets content of a file (POWERSHELL)
- powershell.exe (PID: 5544)
CSC.EXE is used to compile C# code
- csc.exe (PID: 6372)
Executable content was dropped or overwritten
- csc.exe (PID: 6372)
- powershell.exe (PID: 5544)
Contacting a server suspected of hosting an CnC
- powershell.exe (PID: 5544)
Connects to unusual port
- powershell.exe (PID: 5544)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 5544)
Checks for external IP
- svchost.exe (PID: 2196)
- powershell.exe (PID: 5544)
Loads DLL from Mozilla Firefox
- powershell.exe (PID: 5544)
Uses NETSH.EXE to add a firewall rule or allowed programs
- powershell.exe (PID: 5544)
The process verifies whether the antivirus software is installed
- powershell.exe (PID: 5544)
Adds/modifies Windows certificates
- powershell.exe (PID: 5544)
INFO
Reads Microsoft Office registry keys
- WinRAR.exe (PID: 7316)
Reads security settings of Internet Explorer
- notepad.exe (PID: 496)
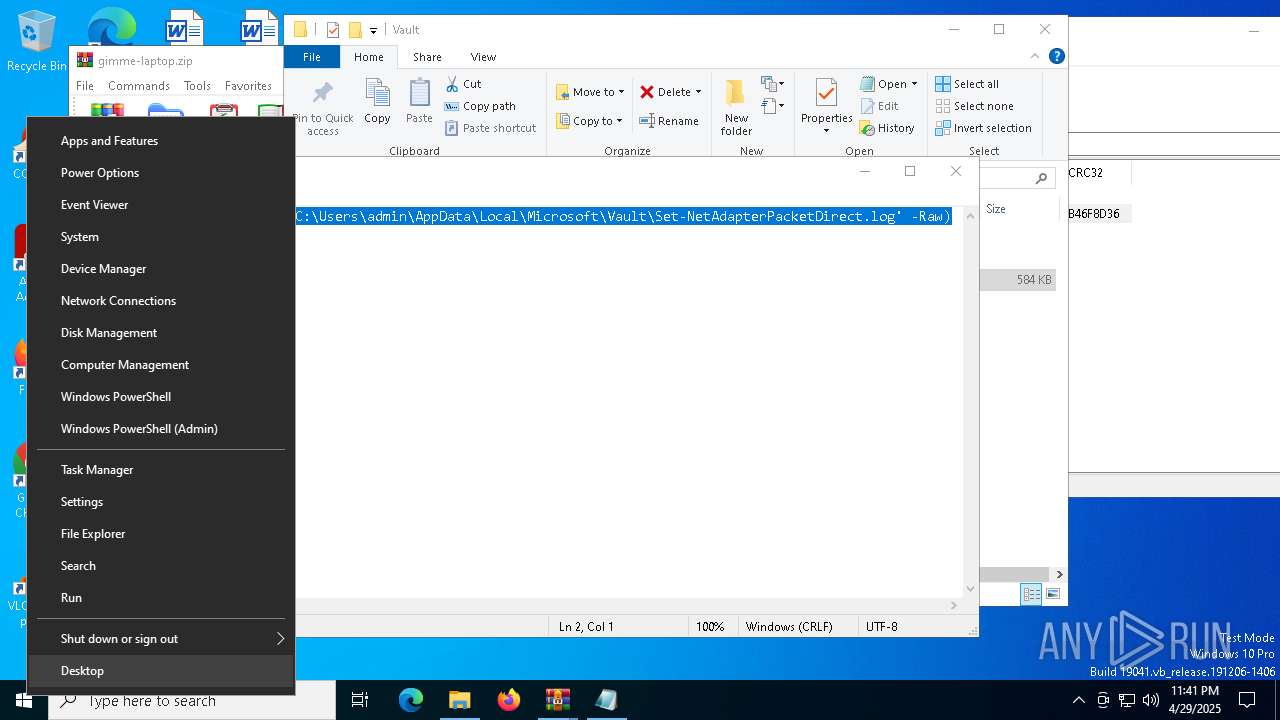
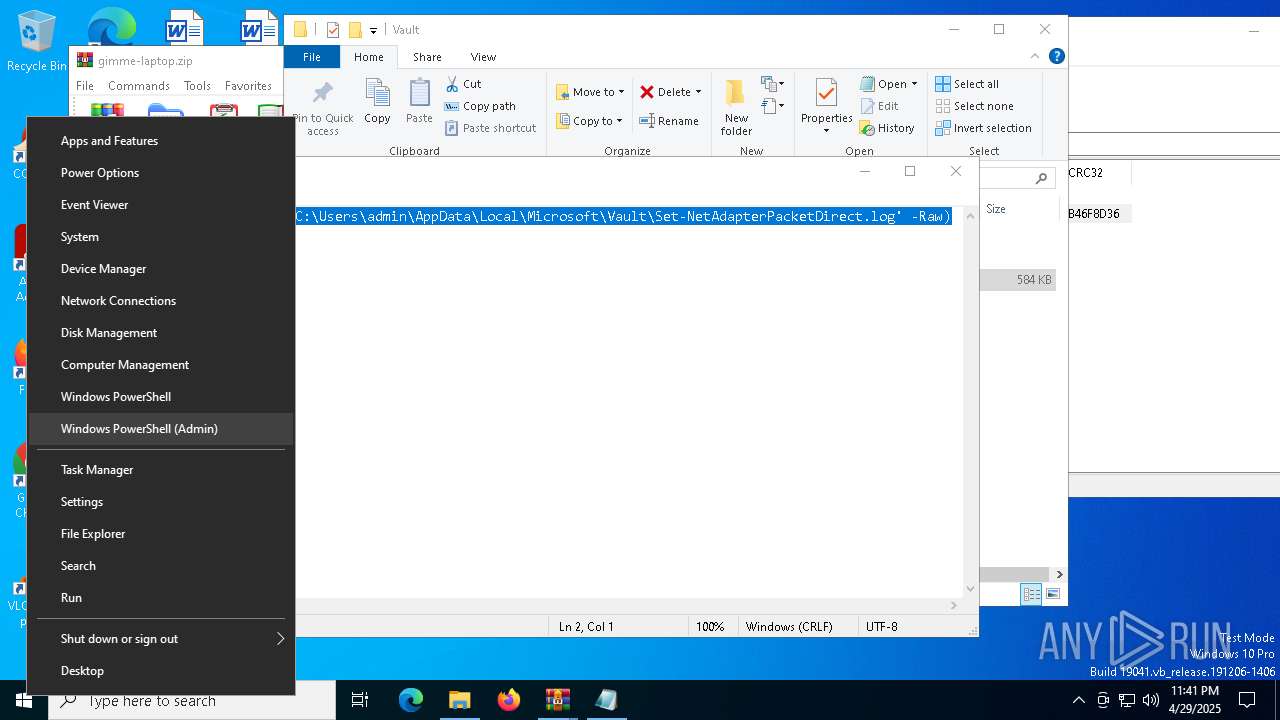
Manual execution by a user
- powershell.exe (PID: 5544)
Checks current location (POWERSHELL)
- powershell.exe (PID: 5544)
Reads the software policy settings
- slui.exe (PID: 7512)
- slui.exe (PID: 6240)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 5544)
Reads the machine GUID from the registry
- csc.exe (PID: 6372)
Checks supported languages
- csc.exe (PID: 6372)
- cvtres.exe (PID: 1532)
Create files in a temporary directory
- csc.exe (PID: 6372)
- cvtres.exe (PID: 1532)
Gets data length (POWERSHELL)
- powershell.exe (PID: 5544)
Disables trace logs
- powershell.exe (PID: 5544)
Checks proxy server information
- powershell.exe (PID: 5544)
- slui.exe (PID: 6240)
Converts byte array into Unicode string (POWERSHELL)
- powershell.exe (PID: 5544)
Creates files in the program directory
- powershell.exe (PID: 5544)
The sample compiled with english language support
- powershell.exe (PID: 5544)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2025:04:29 15:25:30 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | gimme-laptop/ |
Total processes
147
Monitored processes
15
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 496 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\Temp\Rar$DIa7316.36265\powershellcommand.txt | C:\Windows\System32\notepad.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1532 | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RESAE5E.tmp" "c:\Users\admin\AppData\Local\Temp\gh3wupmc\CSCD3F57EE095AE4F59BBB19C733A37782E.TMP" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 14.32.31326.0 Modules
| |||||||||||||||
| 2108 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5544 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6240 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6372 | "C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\gh3wupmc\gh3wupmc.cmdline" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Visual C# Command Line Compiler Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 6572 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
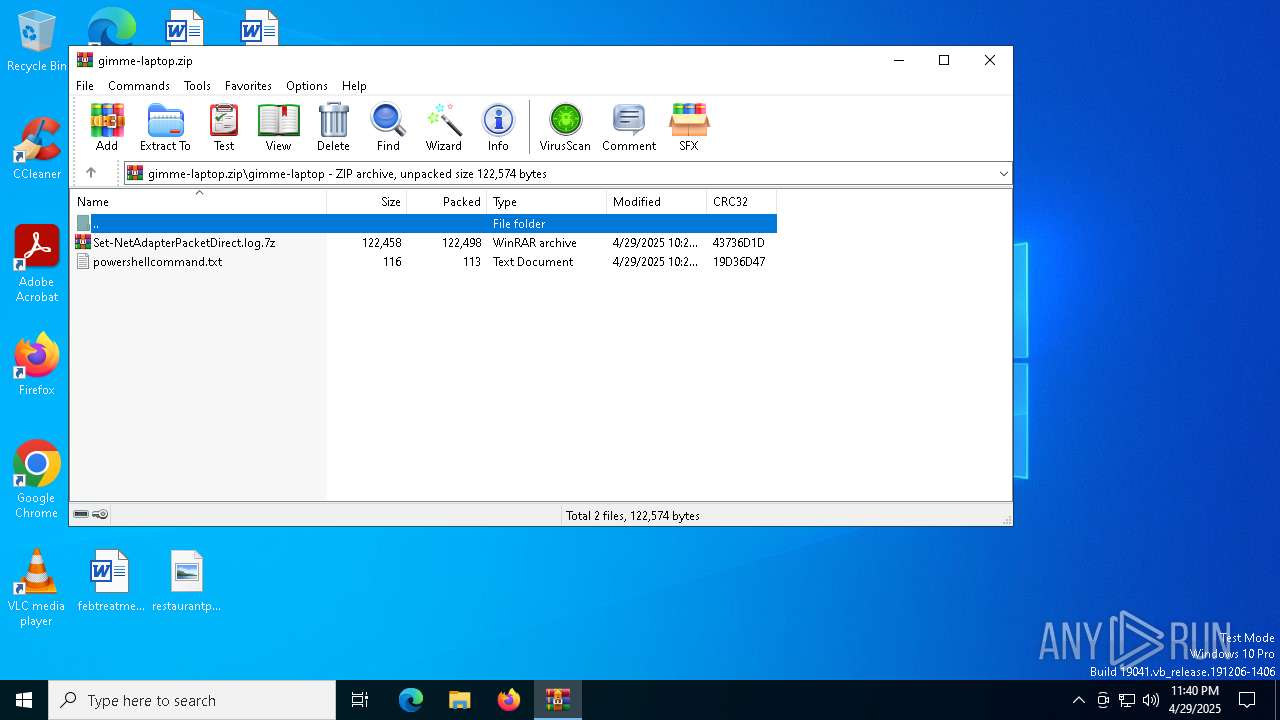
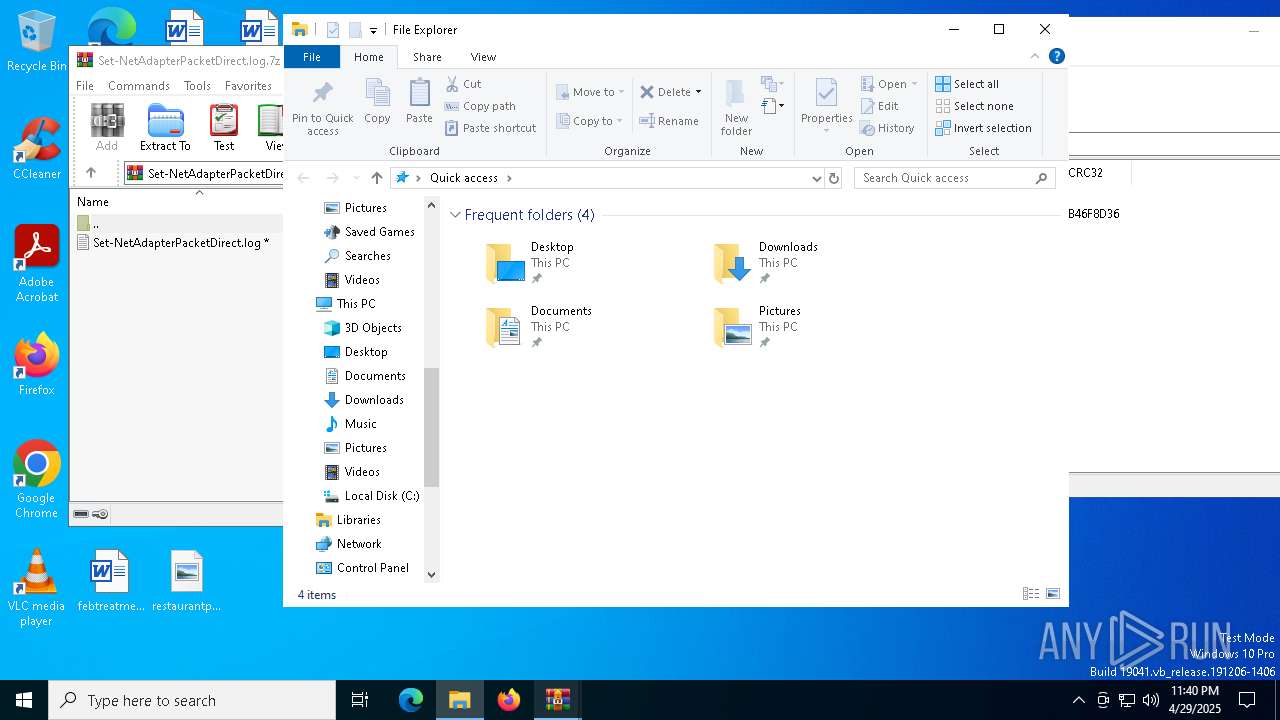
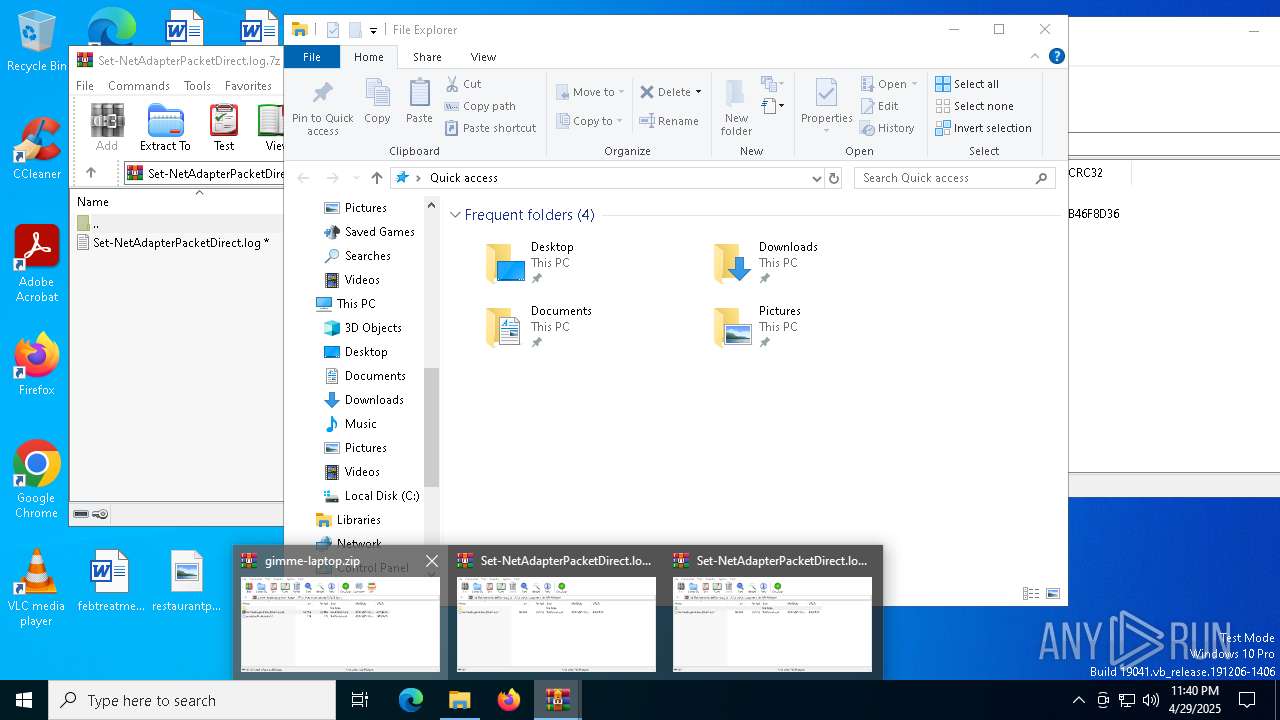
| 7316 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\gimme-laptop.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 7480 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
27 190
Read events
27 156
Write events
31
Delete events
3
Modification events
| (PID) Process: | (7316) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7316) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7316) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7316) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\gimme-laptop.zip | |||
| (PID) Process: | (7316) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7316) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7316) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7316) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7784) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7784) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
Executable files
2
Suspicious files
19
Text files
10
Unknown types
1
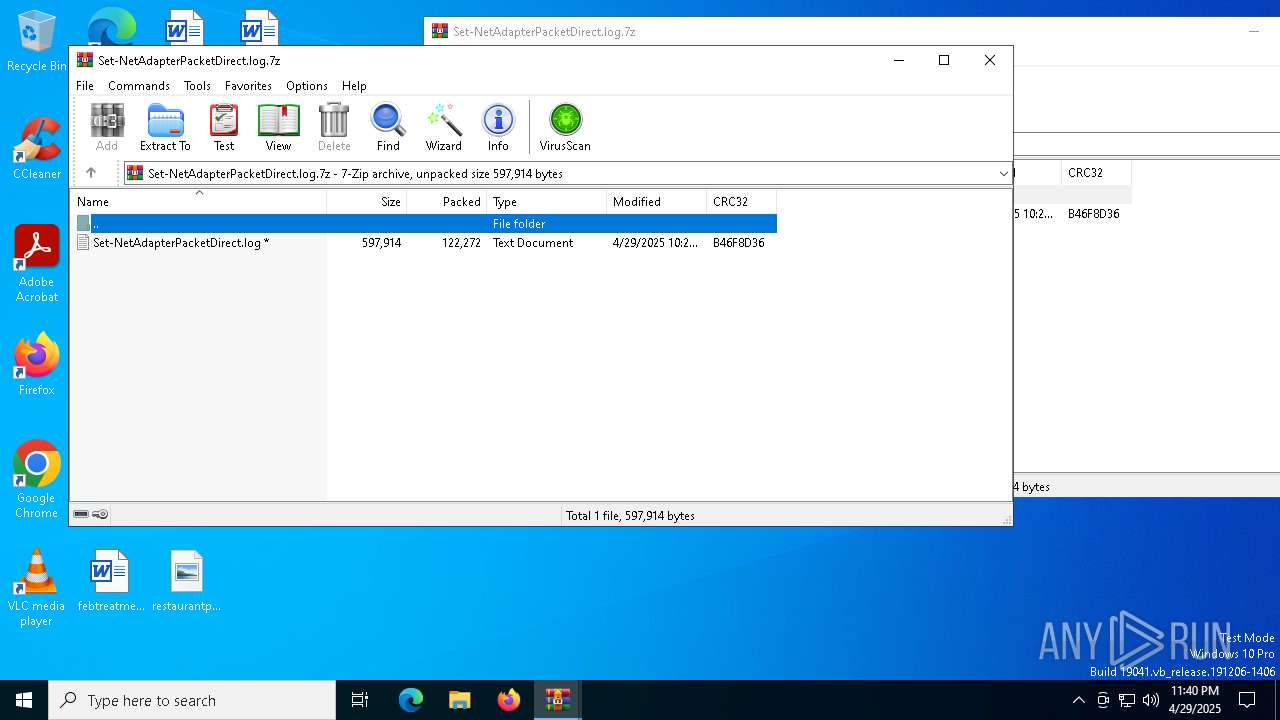
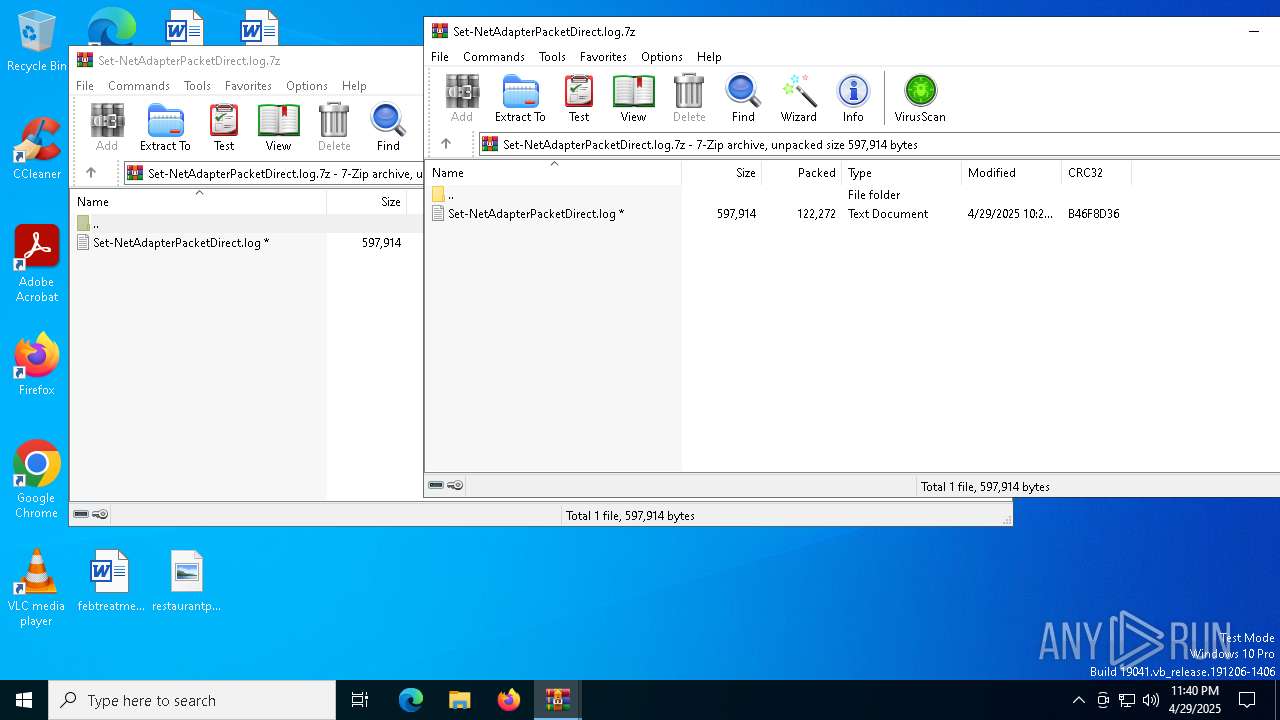
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5544 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\Q1PELYVACQR7AVR38H9W.temp | binary | |
MD5:D337882104B4CB00366AB7BFEC040B31 | SHA256:0225AEAC759198FD26A4E4FC5E6714BBDDC62FFF267731873A1F951863B6E3F0 | |||
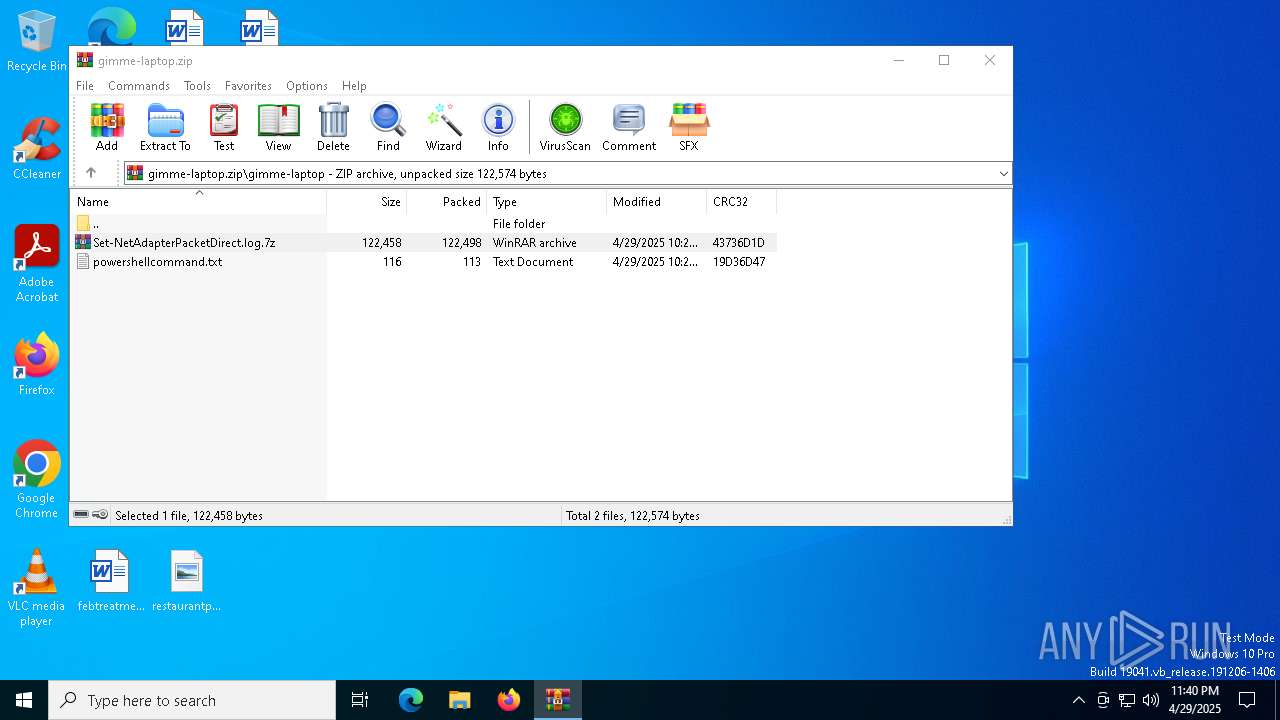
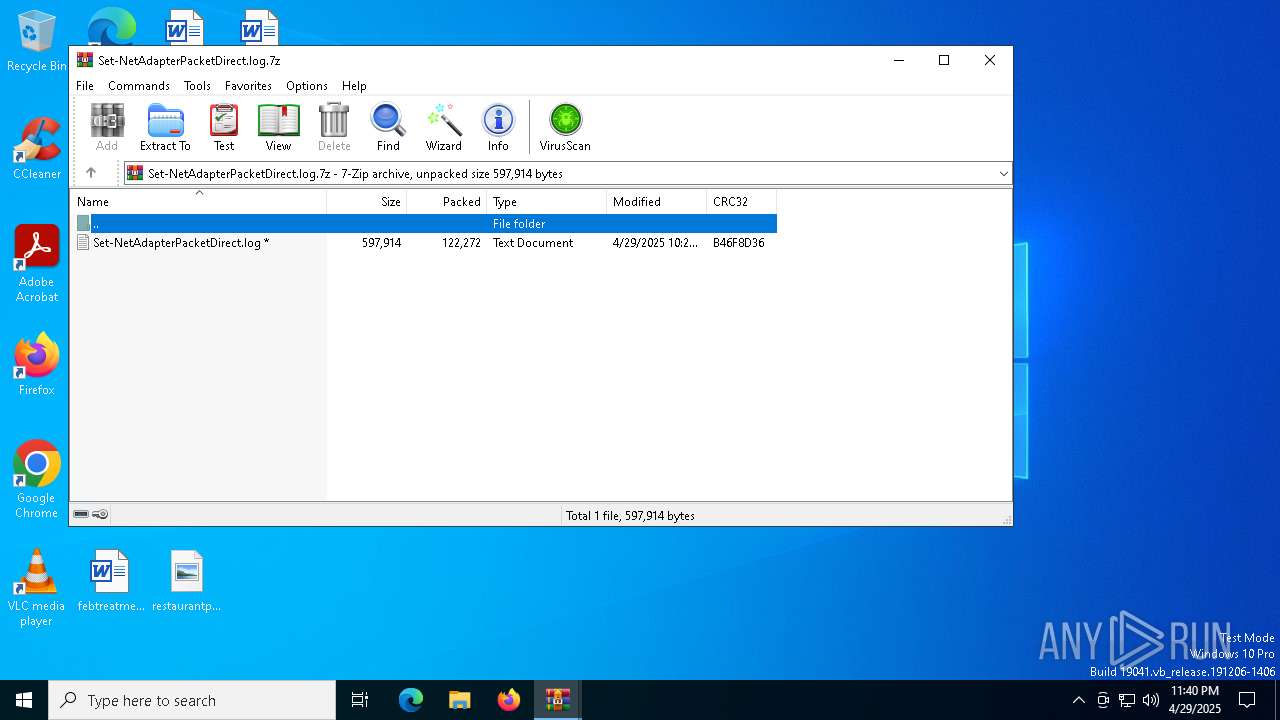
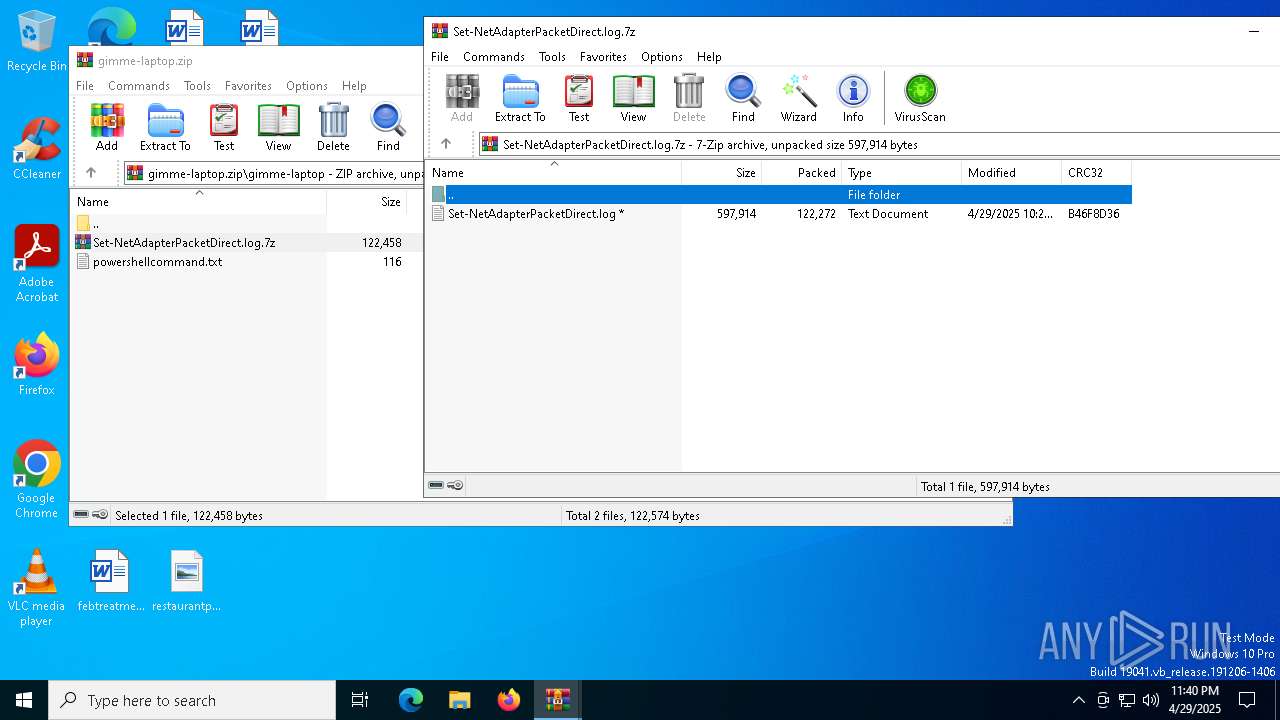
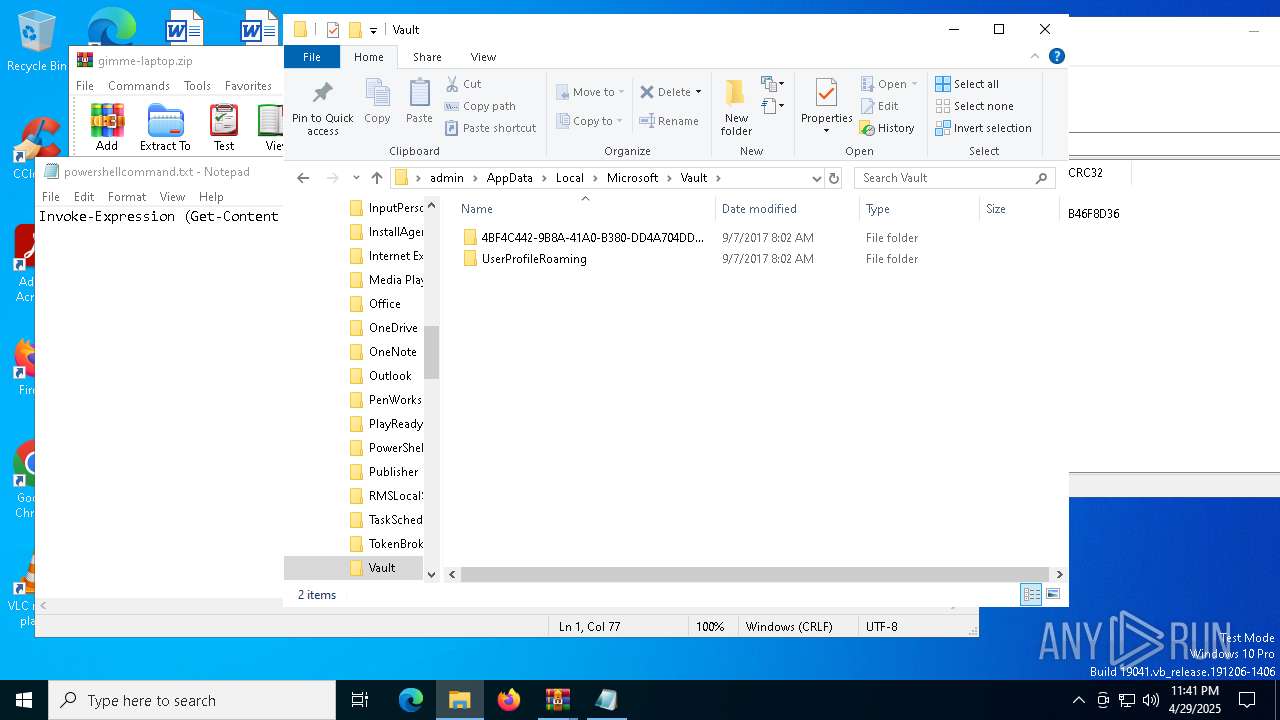
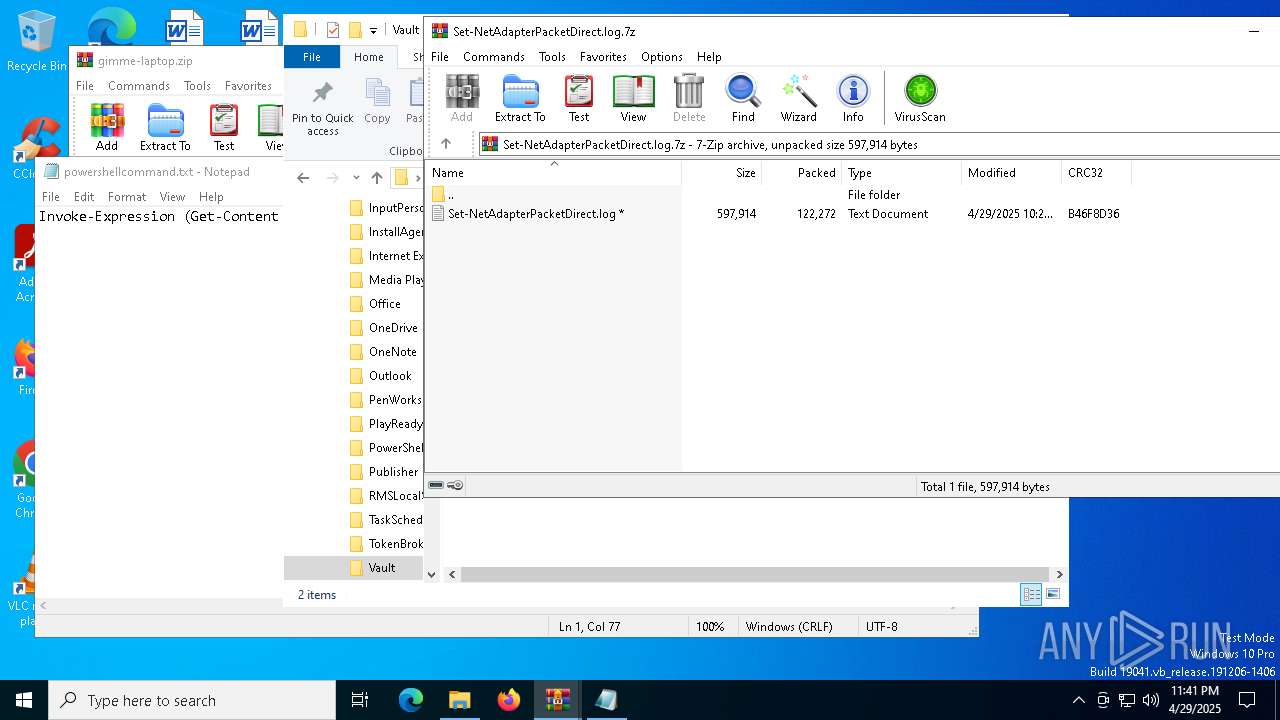
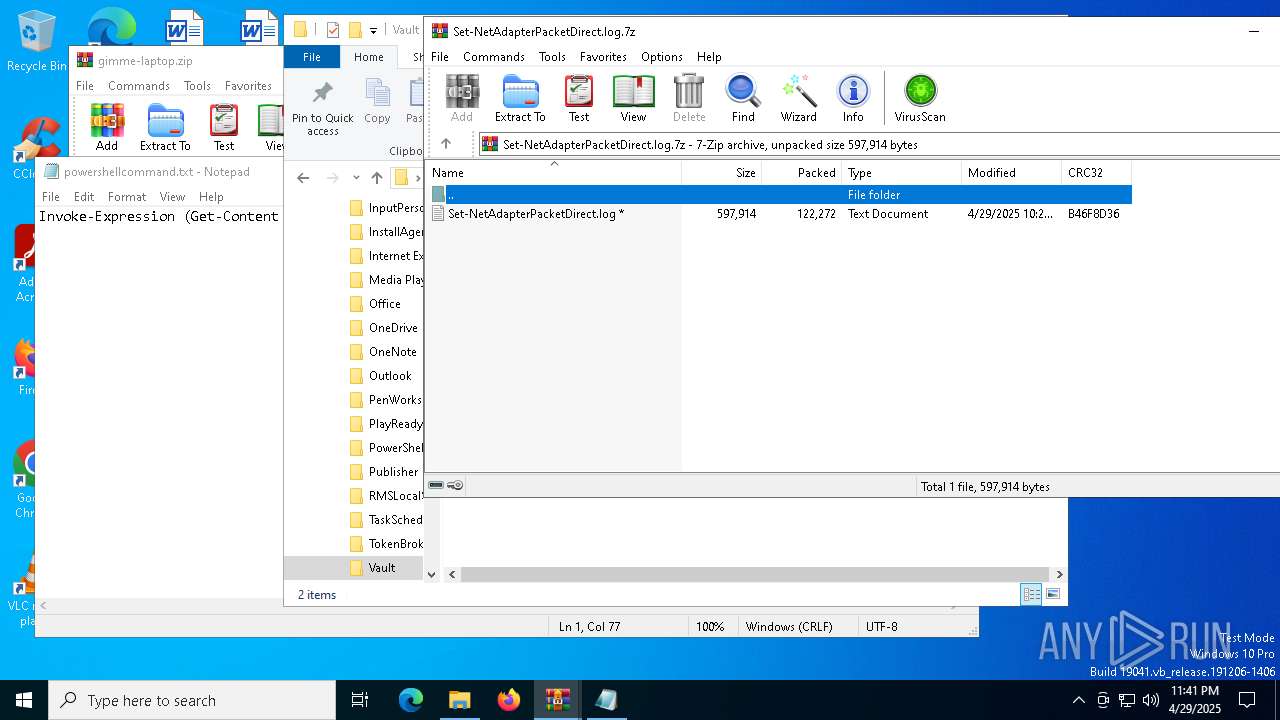
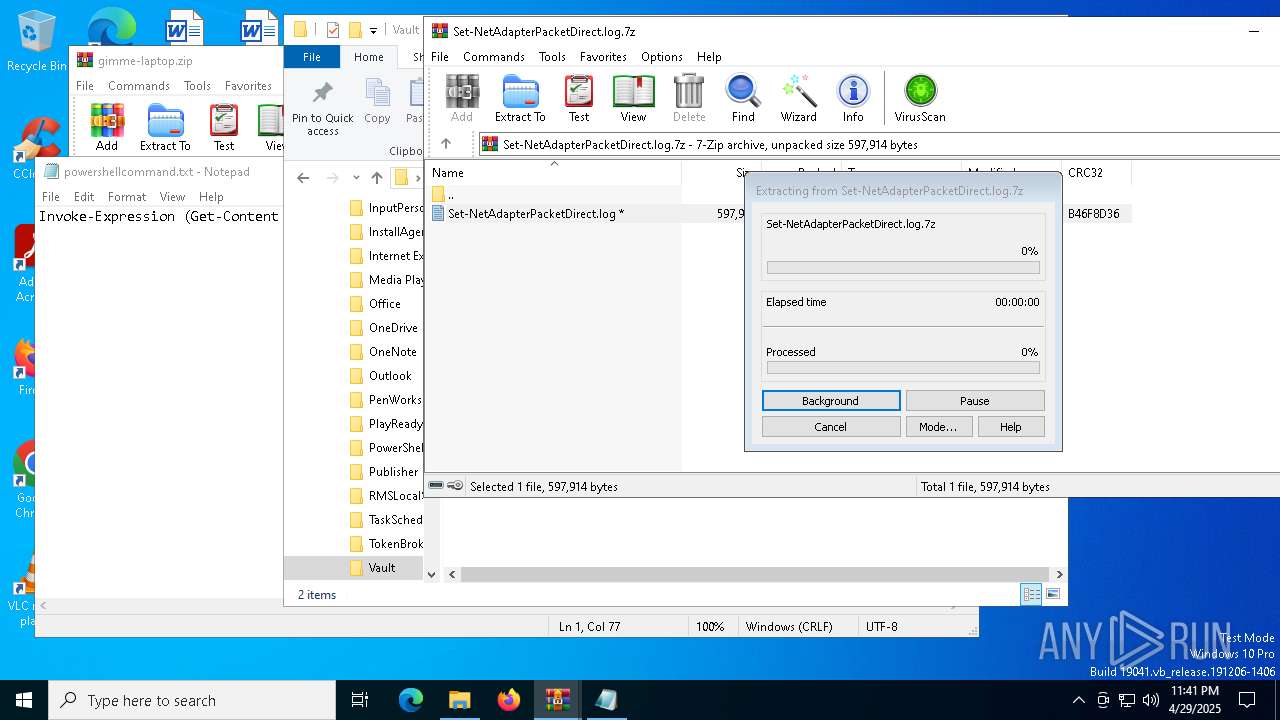
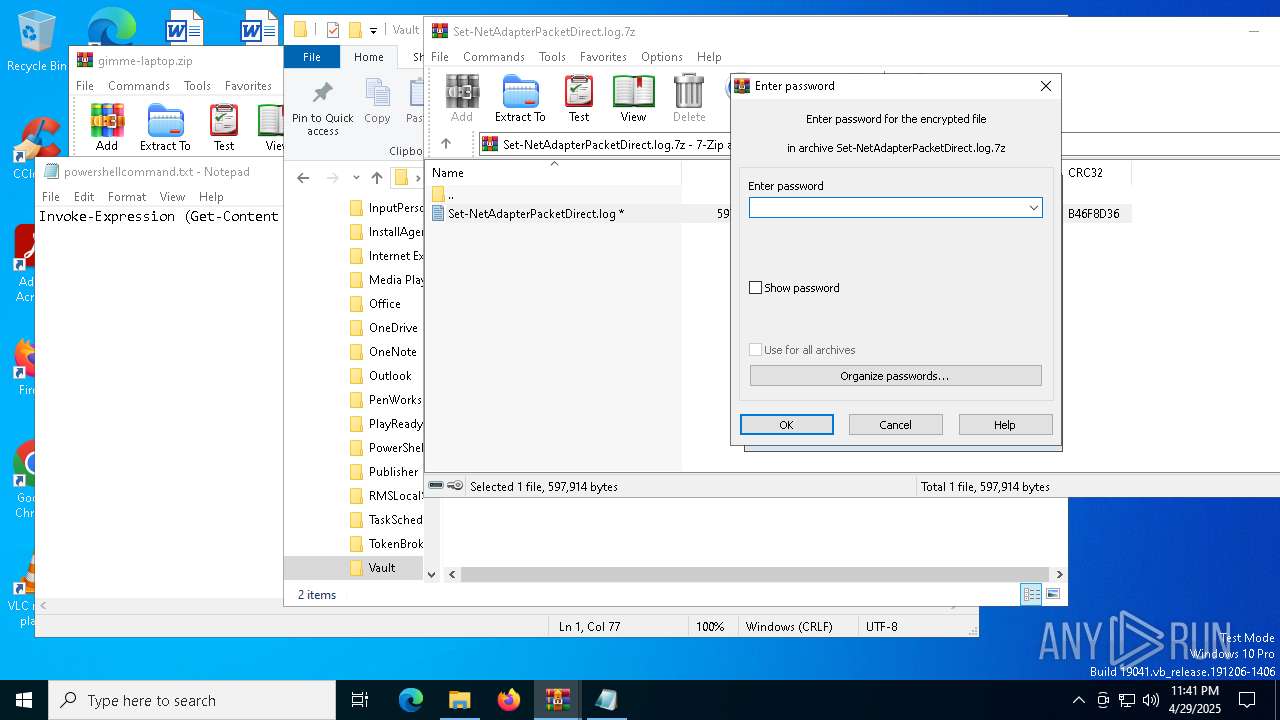
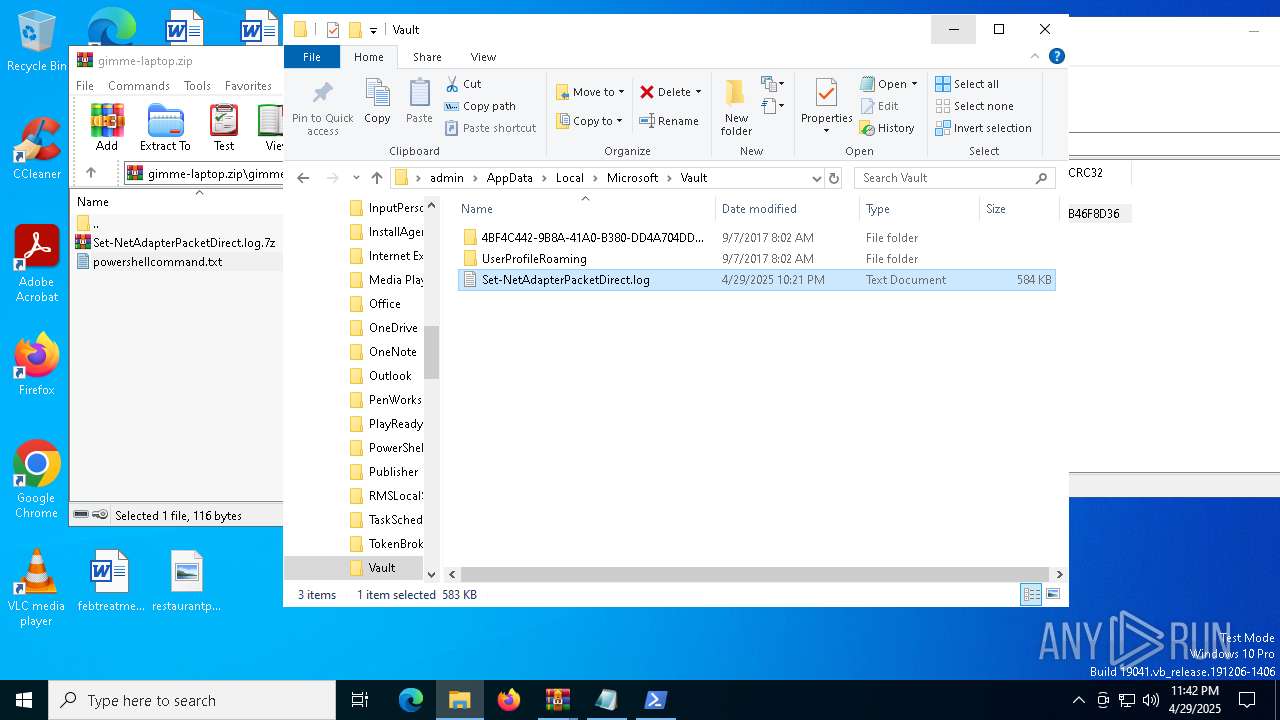
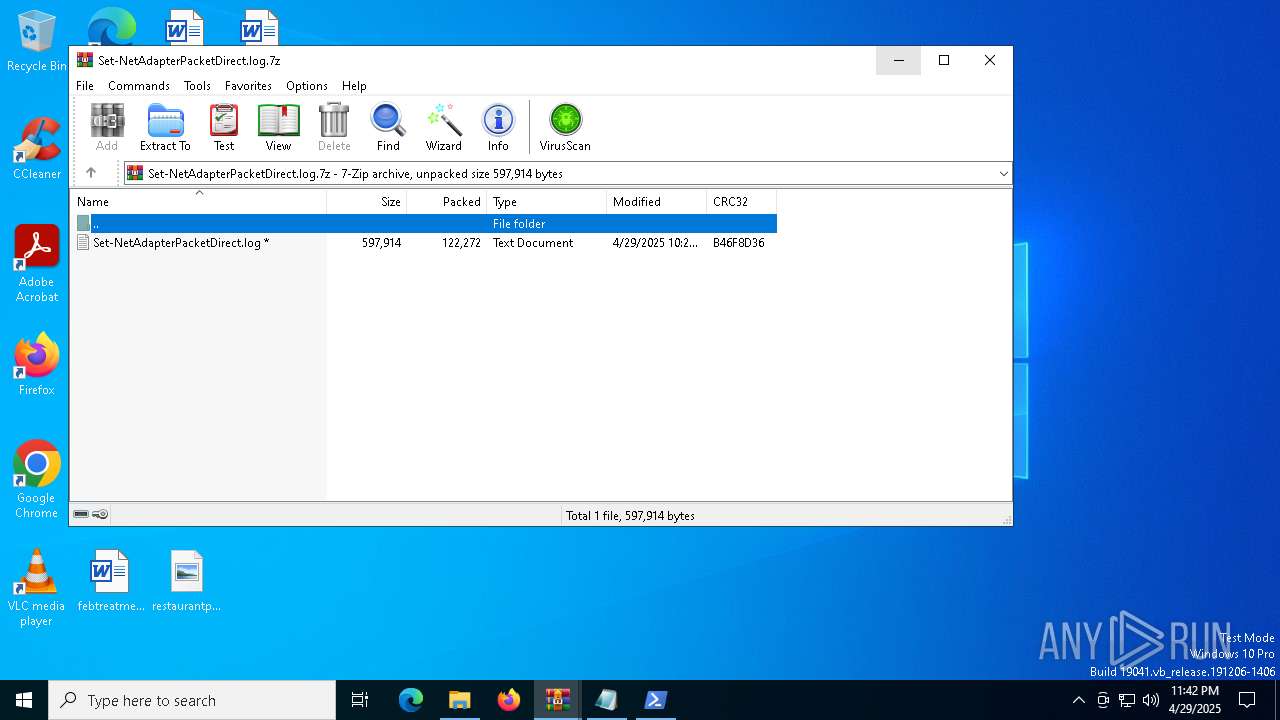
| 7316 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa7316.33779\Set-NetAdapterPacketDirect.log.7z | compressed | |
MD5:57D084159FE2A7581564AEDCE7EA23DD | SHA256:3A65CABE3F939C71AA75E668838A608A15D76F61E3A4432B99220EB9270B8983 | |||
| 5544 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\2d325786c6fc3319f19f824adefaa230 | — | |
MD5:— | SHA256:— | |||
| 7316 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa7316.36265\powershellcommand.txt | text | |
MD5:8E21C6EE29857B04B624A7DCACC34955 | SHA256:AC811255542AD87B618EE37D1C3CED67E7EEC1DEEE389CF1000D54604A4B6804 | |||
| 5544 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF118fd9.TMP | binary | |
MD5:D040F64E9E7A2BB91ABCA5613424598E | SHA256:D04E0A6940609BD6F3B561B0F6027F5CA4E8C5CF0FB0D0874B380A0374A8D670 | |||
| 5544 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_fqqwm5hm.lhh.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5544 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\PowerShell\PSReadline\ConsoleHost_history.txt | text | |
MD5:8E21C6EE29857B04B624A7DCACC34955 | SHA256:AC811255542AD87B618EE37D1C3CED67E7EEC1DEEE389CF1000D54604A4B6804 | |||
| 5544 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_yu1av5yx.zc5.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7316 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa7316.35304\Set-NetAdapterPacketDirect.log.7z | compressed | |
MD5:57D084159FE2A7581564AEDCE7EA23DD | SHA256:3A65CABE3F939C71AA75E668838A608A15D76F61E3A4432B99220EB9270B8983 | |||
| 5544 | powershell.exe | C:\Users\admin\AppData\Local\Google\Chrome\Recov Data\Default\Network\Cookies | binary | |
MD5:06AD9E737639FDC745B3B65312857109 | SHA256:C8925892CA8E213746633033AE95ACFB8DD9531BC376B82066E686AC6F40A404 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
35
DNS requests
22
Threats
12
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 104.124.11.17:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
8120 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8120 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5544 | powershell.exe | GET | 200 | 34.117.59.81:80 | http://ipinfo.io/87.249.132.10/city | unknown | — | — | whitelisted |
5544 | powershell.exe | GET | 200 | 132.226.247.73:80 | http://checkip.dyndns.org/ | unknown | — | — | whitelisted |
5544 | powershell.exe | GET | 200 | 34.117.59.81:80 | http://ipinfo.io/87.249.132.10/region | unknown | — | — | whitelisted |
5544 | powershell.exe | GET | 200 | 34.117.59.81:80 | http://ipinfo.io/87.249.132.10/country | unknown | — | — | whitelisted |
5544 | powershell.exe | GET | 200 | 142.250.184.228:80 | http://www.google.com/robots.txt | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 104.124.11.17:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2112 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 40.126.31.69:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5544 | powershell.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
5544 | powershell.exe | Domain Observed Used for C2 Detected | ET MALWARE Generic AsyncRAT/zgRAT Style SSL Cert |
2196 | svchost.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
5544 | powershell.exe | Misc activity | ET INFO External IP Address Lookup Domain (ipify .org) in TLS SNI |
5544 | powershell.exe | Malware Command and Control Activity Detected | REMOTE [ANY.RUN] AsyncRAT Successful Connection |
2196 | svchost.exe | Device Retrieving External IP Address Detected | ET DYN_DNS External IP Lookup Domain in DNS Query (checkip .dyndns .org) |
5544 | powershell.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup - checkip.dyndns.org |
2196 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ipinfo .io) |
5544 | powershell.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup ipinfo.io |
5544 | powershell.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup ipinfo.io |