| File name: | GC.rar |
| Full analysis: | https://app.any.run/tasks/7d6efd9a-8368-4c2b-bbf7-8a36be858d57 |
| Verdict: | Malicious activity |
| Threats: | Crypto mining malware is a resource-intensive threat that infiltrates computers with the purpose of mining cryptocurrencies. This type of threat can be deployed either on an infected machine or a compromised website. In both cases the miner will utilize the computing power of the device and its network bandwidth. |
| Analysis date: | December 06, 2018, 11:47:19 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
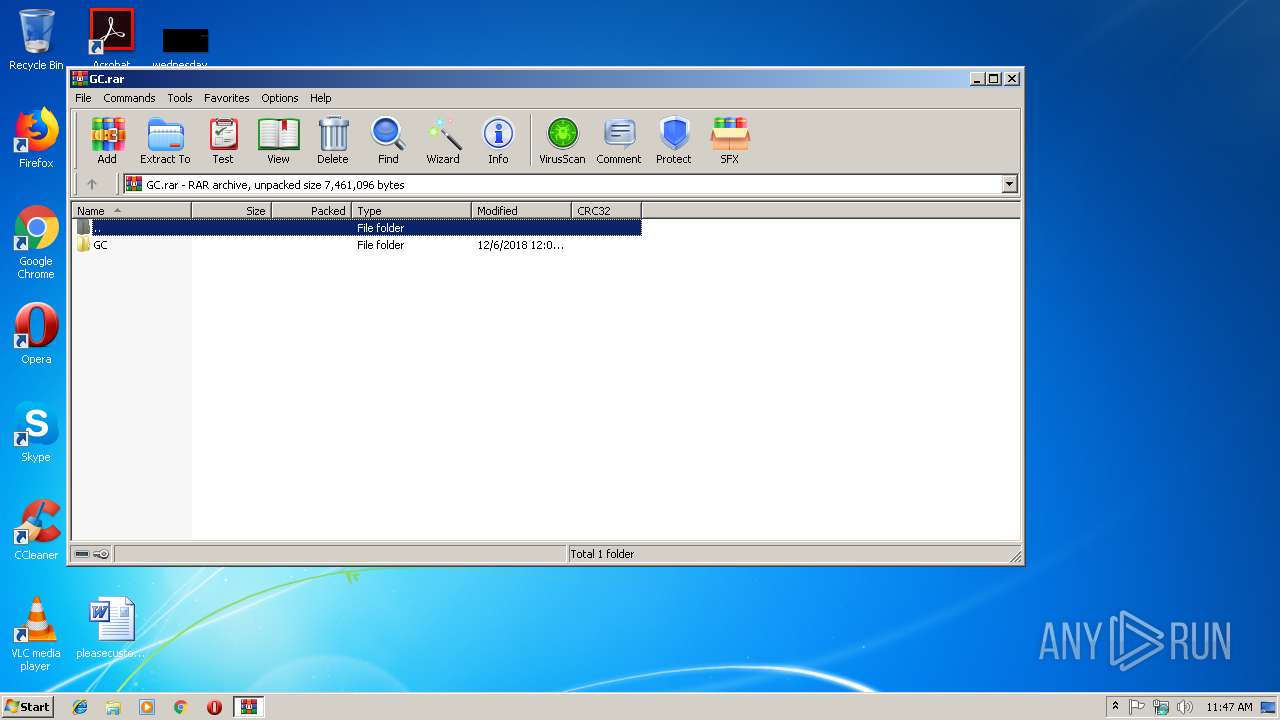
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 0DD6E9D44A15600AC39509BCC6A2CB97 |
| SHA1: | 74D2343B2D6EBAF3E808D330AE539EAE20AB436E |
| SHA256: | 9E2FB447A50E1456B12FC708D8048AC6745794D1433D8DF3A85A3F75F888A8BD |
| SSDEEP: | 196608:xdtA3R/tNwCjMeca1xHU1gQ60H8jGO48xC1MZOZKdAMQ:xDQR/tuW3I/1H8Sn8g1MZOjV |
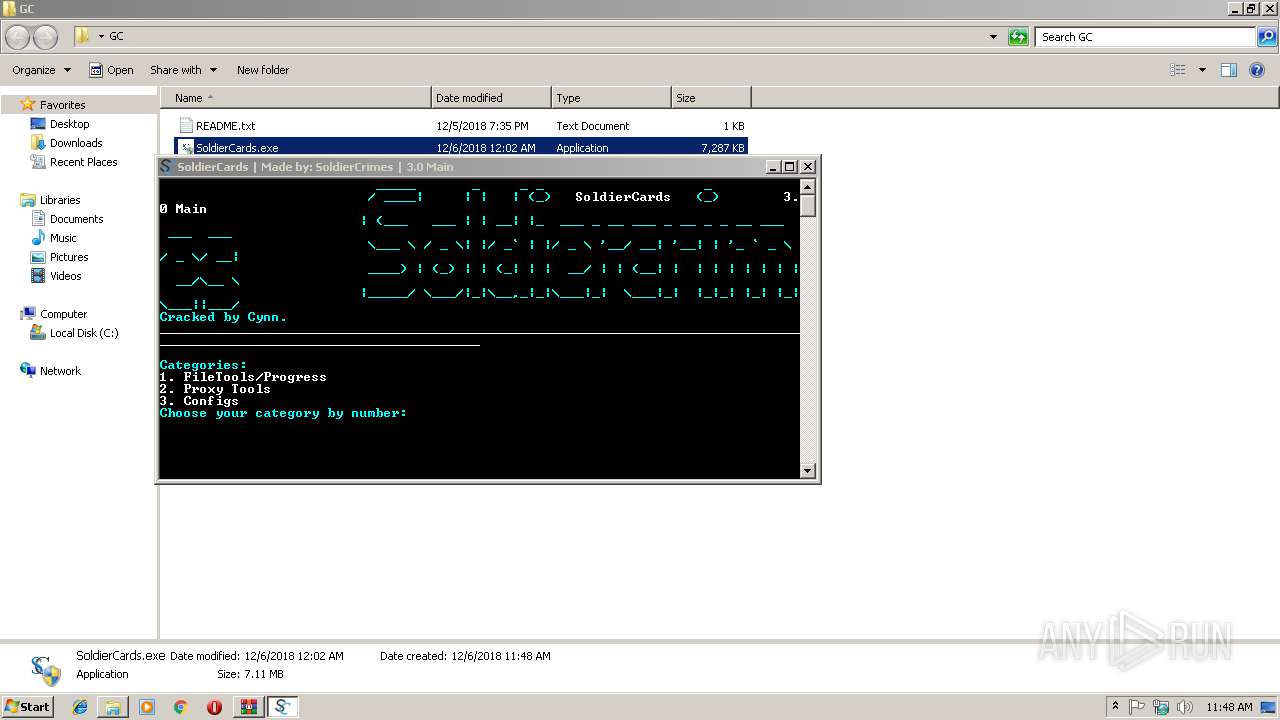
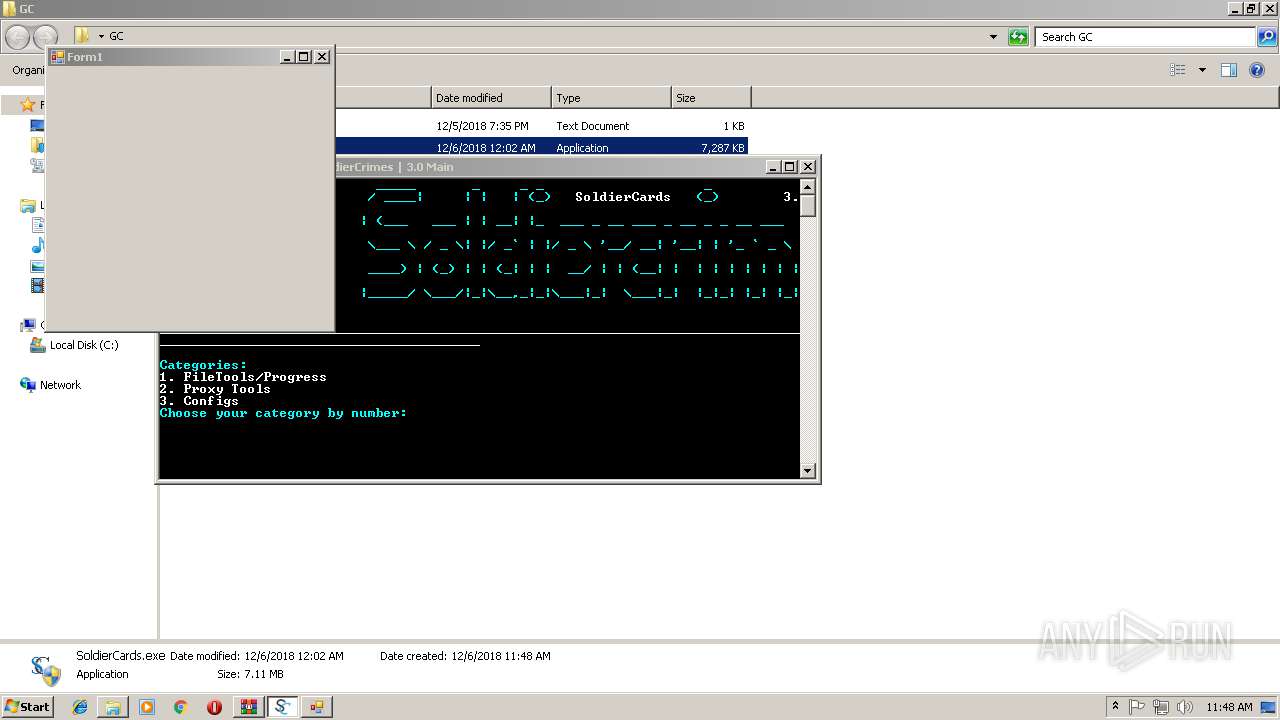
MALICIOUS
Application was dropped or rewritten from another process
- SoldierCards.exe (PID: 3888)
- EMP.EXE (PID: 2168)
- vsll.exe (PID: 4028)
- visnj.exe (PID: 3284)
- vsnj.exe (PID: 2932)
- EMP.sfx.exe (PID: 2412)
- AAYPSVOQA.exe (PID: 3600)
- data.exe (PID: 3616)
- SystemProcess.exe (PID: 3188)
- service.exe (PID: 2704)
Changes the autorun value in the registry
- EMP.EXE (PID: 2168)
- data.exe (PID: 3616)
Uses Task Scheduler to run other applications
- EMP.EXE (PID: 2168)
- vsll.exe (PID: 4028)
- SystemProcess.exe (PID: 3188)
MINER was detected
- AAYPSVOQA.exe (PID: 3600)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 2900)
- schtasks.exe (PID: 2988)
- schtasks.exe (PID: 2696)
- schtasks.exe (PID: 3268)
- schtasks.exe (PID: 2636)
Connects to CnC server
- AAYPSVOQA.exe (PID: 3600)
Writes to a start menu file
- data.exe (PID: 3616)
NJRAT was detected
- data.exe (PID: 3616)
SUSPICIOUS
Executable content was dropped or overwritten
- EMP.sfx.exe (PID: 2412)
- SoldierCards.exe (PID: 2612)
- EMP.EXE (PID: 2168)
- vsnj.exe (PID: 2932)
- data.exe (PID: 3616)
- vsll.exe (PID: 4028)
Connects to unusual port
- AAYPSVOQA.exe (PID: 3600)
- service.exe (PID: 2704)
- data.exe (PID: 3616)
Starts itself from another location
- vsnj.exe (PID: 2932)
- vsll.exe (PID: 4028)
Creates files in the user directory
- vsnj.exe (PID: 2932)
- vsll.exe (PID: 4028)
- data.exe (PID: 3616)
Reads Environment values
- service.exe (PID: 2704)
Uses NETSH.EXE for network configuration
- data.exe (PID: 3616)
INFO
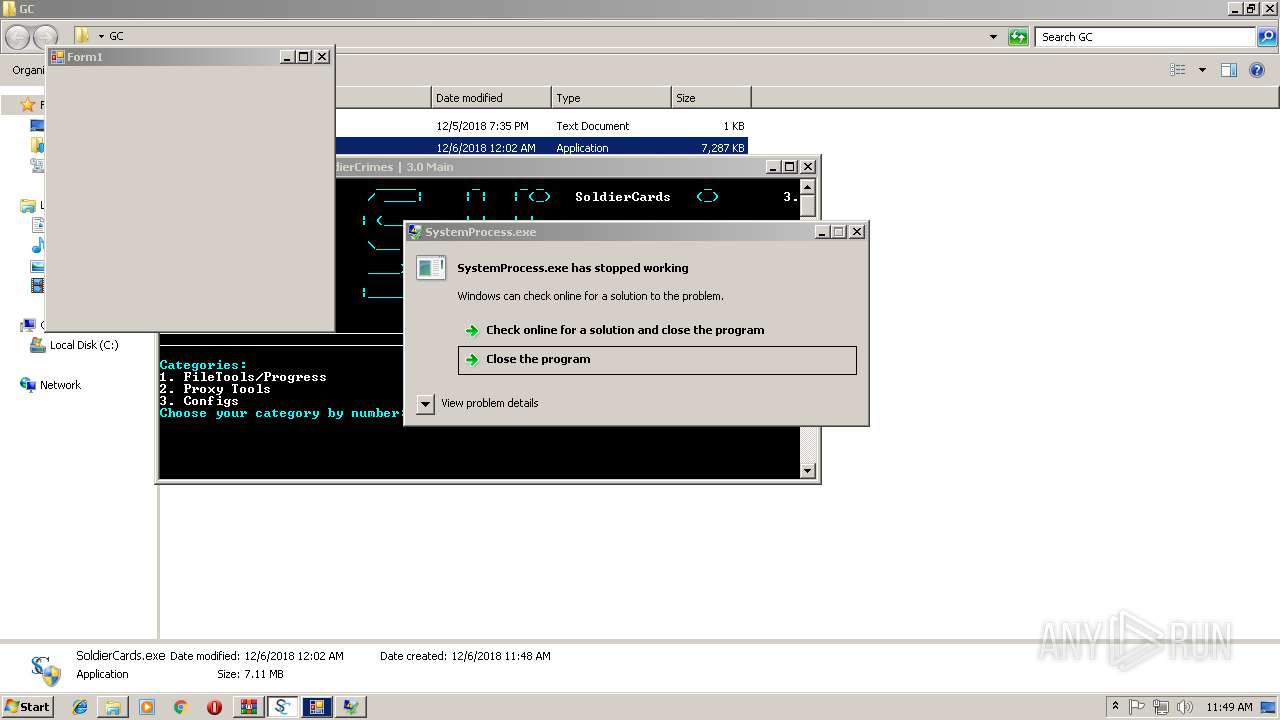
Application was crashed
- SystemProcess.exe (PID: 3188)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
63
Monitored processes
18
Malicious processes
7
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2168 | "C:\Users\admin\AppData\Local\Temp\EMP.EXE" | C:\Users\admin\AppData\Local\Temp\EMP.EXE | EMP.sfx.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
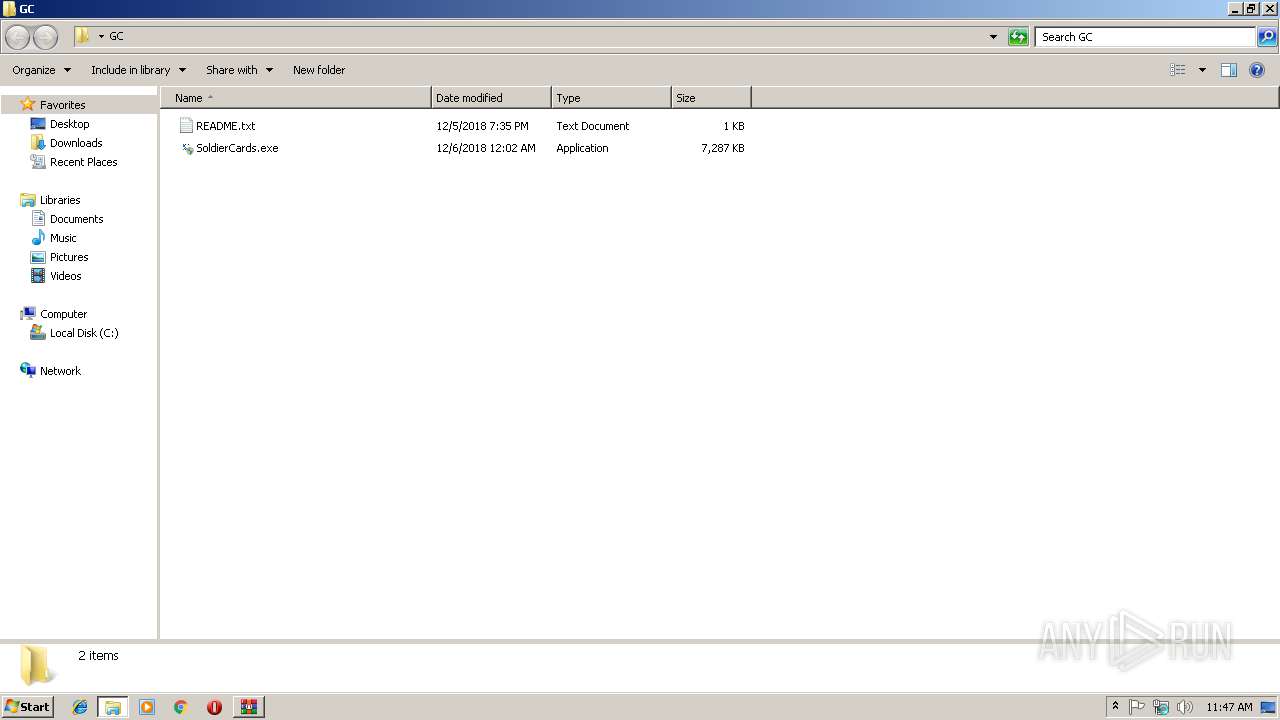
| 2412 | "C:\Users\admin\AppData\Local\Temp\EMP.sfx.exe" | C:\Users\admin\AppData\Local\Temp\EMP.sfx.exe | SoldierCards.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
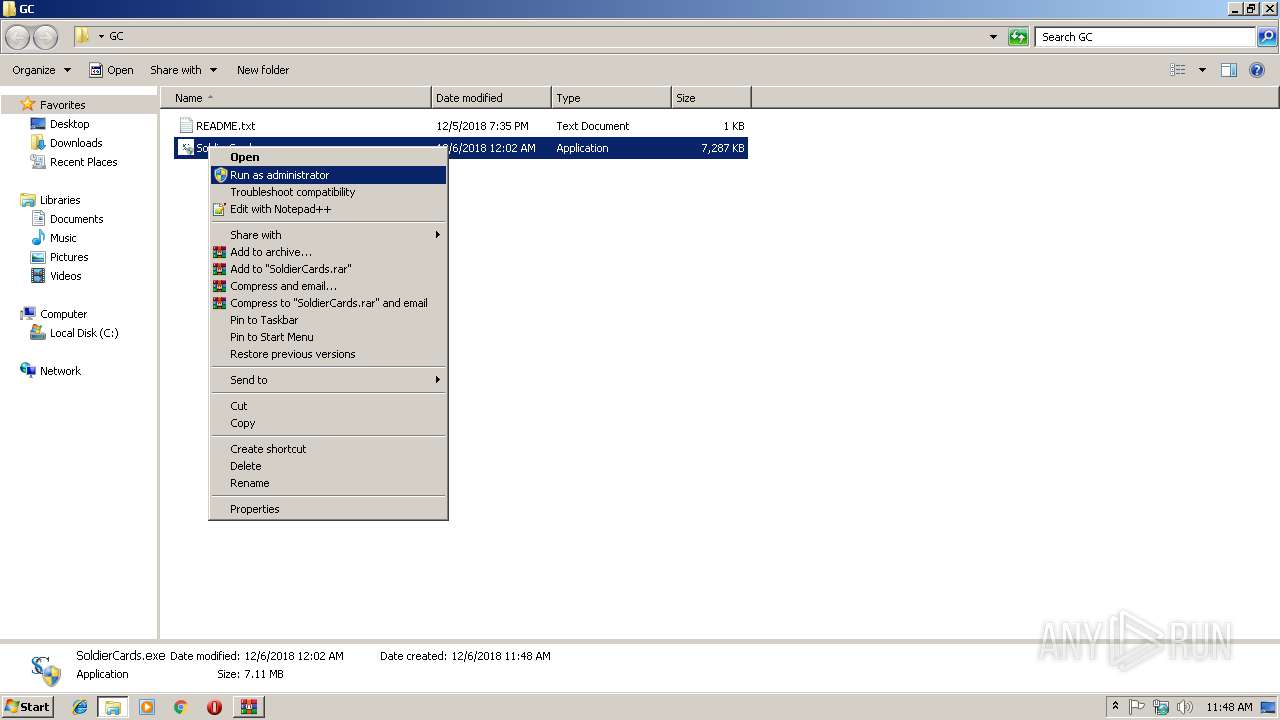
| 2612 | "C:\Users\admin\Desktop\GC\SoldierCards.exe" | C:\Users\admin\Desktop\GC\SoldierCards.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2636 | schtasks.exe /create /tn NHHBXFCOVMPT /tr C:\Users\admin\AppData\Local\HKMFRNJQSFYWAKP\SystemProcess.exe /sc onidle /i 1 | C:\Windows\system32\schtasks.exe | — | SystemProcess.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2696 | schtasks /create /f /sc ONLOGON /RL HIGHEST /tn LimeRAT-Admin /tr "'C:\Users\admin\AppData\Roaming\System32\service.exe'" | C:\Windows\system32\schtasks.exe | — | vsll.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2704 | "C:\Users\admin\AppData\Roaming\System32\service.exe" | C:\Users\admin\AppData\Roaming\System32\service.exe | vsll.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: vs Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2900 | schtasks.exe /create /tn NHHBXFCOVMPT /tr C:\Users\admin\AppData\Local\HKMFRNJQSFYWAKP\SystemProcess.exe /sc minute /mo 1 | C:\Windows\system32\schtasks.exe | — | EMP.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2932 | "C:\Users\admin\AppData\Local\Temp\vsnj.exe" | C:\Users\admin\AppData\Local\Temp\vsnj.exe | SoldierCards.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: vs Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2988 | schtasks.exe /create /tn NHHBXFCOVMPT /tr C:\Users\admin\AppData\Local\HKMFRNJQSFYWAKP\SystemProcess.exe /sc onidle /i 1 | C:\Windows\system32\schtasks.exe | — | EMP.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
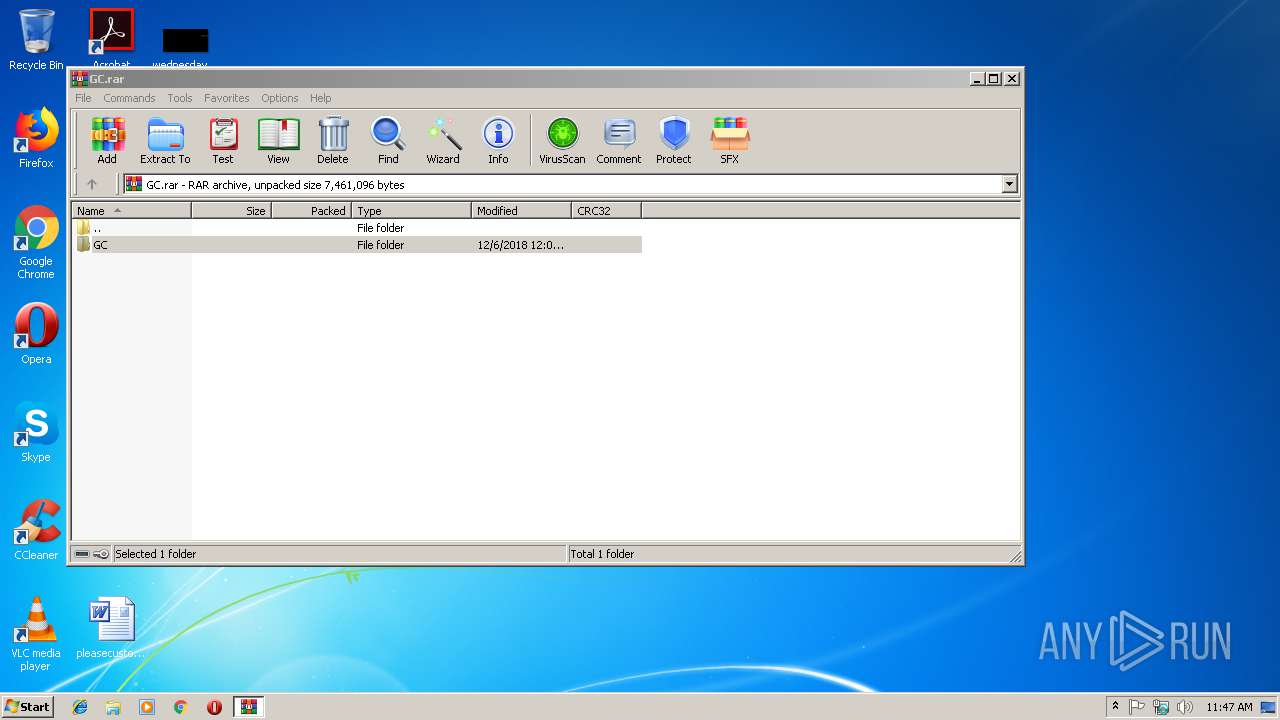
| 3160 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\GC.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
2 293
Read events
1 901
Write events
392
Delete events
0
Modification events
| (PID) Process: | (3160) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3160) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3160) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3160) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\GC.rar | |||
| (PID) Process: | (3160) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3160) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3160) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3160) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2612) SoldierCards.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2612) SoldierCards.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
11
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3160 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3160.37958\GC\README.txt | — | |
MD5:— | SHA256:— | |||
| 3160 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3160.37958\GC\SoldierCards.exe | — | |
MD5:— | SHA256:— | |||
| 2612 | SoldierCards.exe | C:\Users\admin\AppData\Local\Temp\vsnj.exe | executable | |
MD5:— | SHA256:— | |||
| 2612 | SoldierCards.exe | C:\Users\admin\AppData\Local\Temp\vsll.exe | executable | |
MD5:— | SHA256:— | |||
| 2612 | SoldierCards.exe | C:\Users\admin\AppData\Local\Temp\visnj.exe | executable | |
MD5:— | SHA256:— | |||
| 2412 | EMP.sfx.exe | C:\Users\admin\AppData\Local\Temp\EMP.exe | executable | |
MD5:— | SHA256:— | |||
| 2612 | SoldierCards.exe | C:\Users\admin\AppData\Local\Temp\EMP.sfx.exe | executable | |
MD5:— | SHA256:— | |||
| 2932 | vsnj.exe | C:\Users\admin\AppData\Roaming\data.exe | executable | |
MD5:— | SHA256:— | |||
| 4028 | vsll.exe | C:\Users\admin\AppData\Roaming\System32\service.exe | executable | |
MD5:— | SHA256:— | |||
| 2168 | EMP.EXE | C:\Users\admin\AppData\Local\HKMFRNJQSFYWAKP\SystemProcess.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
8
DNS requests
4
Threats
6
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3600 | AAYPSVOQA.exe | 80.188.53.27:5555 | xmr.bohemianpool.com | O2 Czech Republic, a.s. | CZ | suspicious |
2704 | service.exe | 79.159.172.236:8989 | — | Telefonica De Espana | ES | malicious |
3616 | data.exe | 31.4.242.170:5553 | redlocal.hopto.org | Vodafone Spain | ES | unknown |
2704 | service.exe | 104.20.208.21:443 | pastebin.com | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
xmr.bohemianpool.com |
| suspicious |
redlocal.hopto.org |
| malicious |
pastebin.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3600 | AAYPSVOQA.exe | Potential Corporate Privacy Violation | ET POLICY Cryptocurrency Miner Checkin |
3600 | AAYPSVOQA.exe | Misc activity | MINER [PTsecurity] CoinMiner CryptoNight XMRig JSON_RPC Client Login |
3600 | AAYPSVOQA.exe | Misc activity | MINER [PTsecurity] Riskware/CoinMiner JSON_RPC Response |
3600 | AAYPSVOQA.exe | Misc activity | MINER [PTsecurity] Risktool.W32.coinminer!c |
3600 | AAYPSVOQA.exe | Misc activity | MINER [PTsecurity] Riskware/CoinMiner JSON_RPC Response |
3600 | AAYPSVOQA.exe | Misc activity | MINER [PTsecurity] Risktool.W32.coinminer!c |