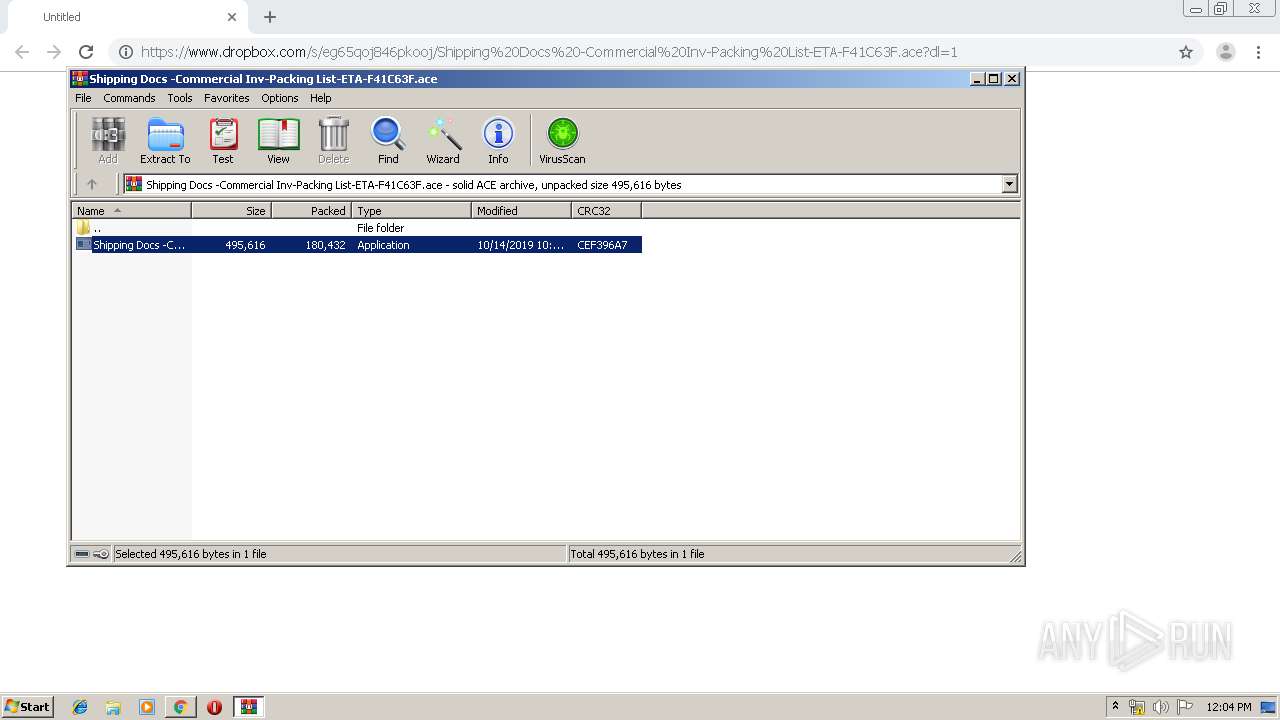
| URL: | https://www.dropbox.com/s/eg65qoj846pkooj/Shipping%20Docs%20-Commercial%20Inv-Packing%20List-ETA-F41C63F.ace?dl=1 |
| Full analysis: | https://app.any.run/tasks/e21784aa-8401-4bb3-8db4-511ea2dd79d1 |
| Verdict: | Malicious activity |
| Threats: | LokiBot was developed in 2015 to steal information from a variety of applications. Despite the age, this malware is still rather popular among cybercriminals. |
| Analysis date: | October 14, 2019, 11:01:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
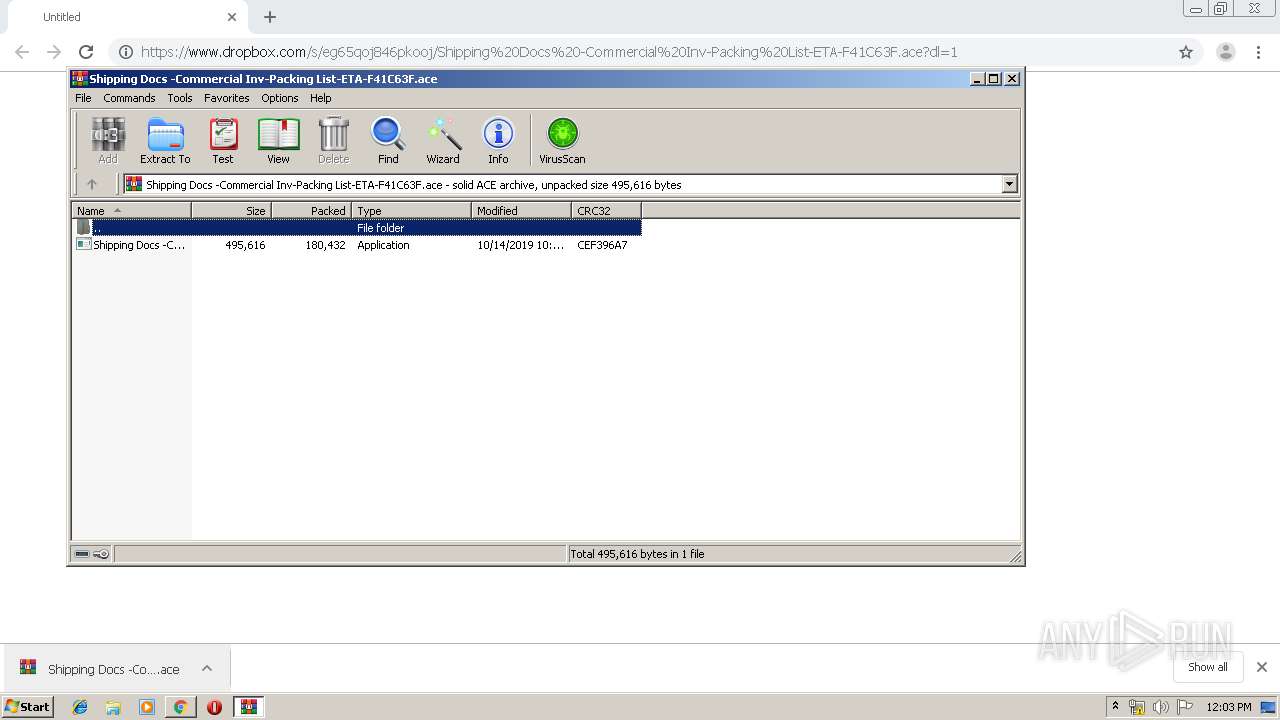
| MD5: | 11EE7E6FD16230F07599CFD87BC70434 |
| SHA1: | 0067D5D2E4D07F5672877B0A3219FEDE00852978 |
| SHA256: | 9E1FC7B27E01541CC176F93B3A4A49826EC1924129342C6FCC60B32F6E32DF5B |
| SSDEEP: | 3:N8DSLcVHGkqUTClKm2Auwi9MWLT5ZMFiWu0kIt/a/H5:2OLHkJcnw9fLTQKIRM |
MALICIOUS
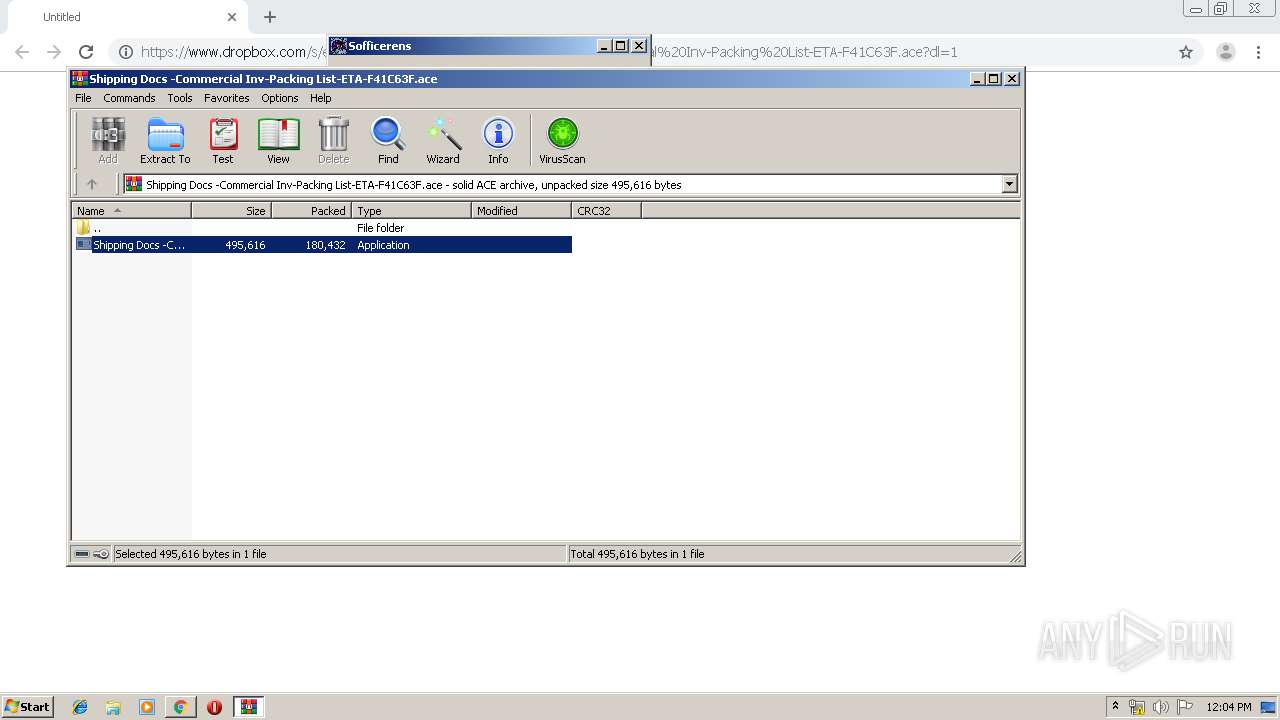
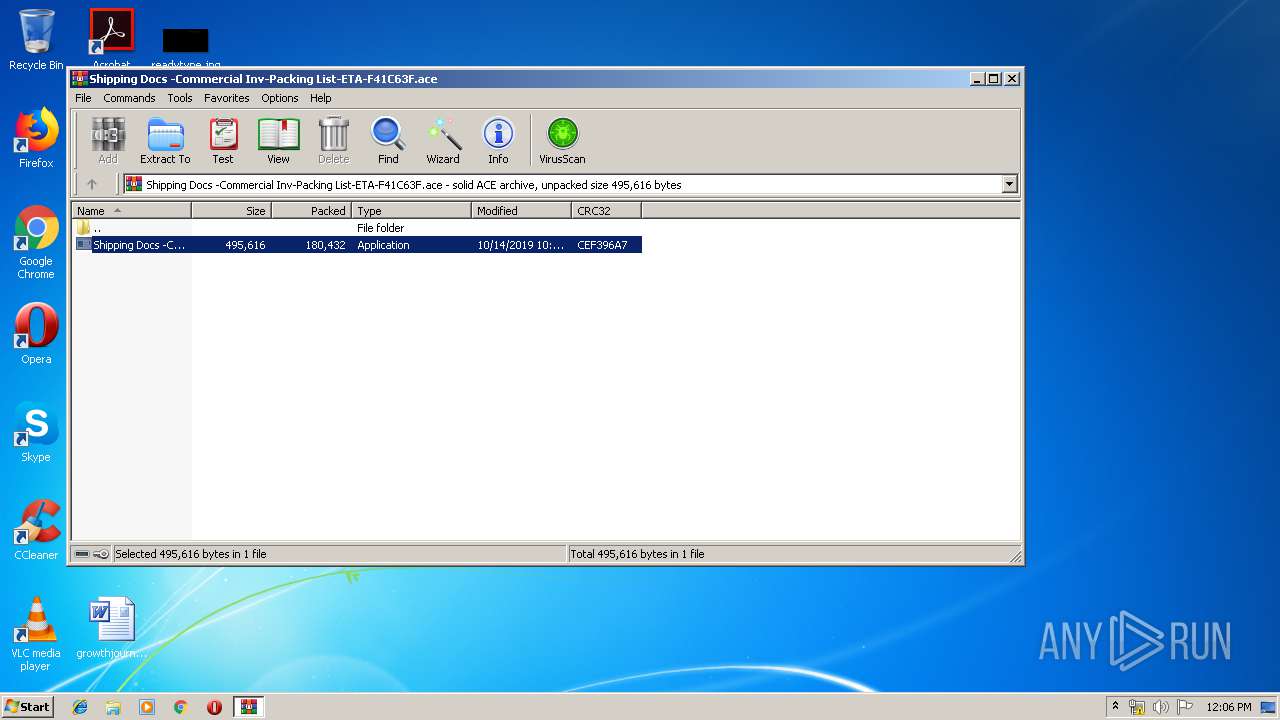
Application was dropped or rewritten from another process
- Shipping Docs -Commercial Inv-Packing List-ETA-F41C63F.exe (PID: 884)
- Shipping Docs -Commercial Inv-Packing List-ETA-F41C63F.exe (PID: 4044)
- Meshuggana8.exe (PID: 2276)
- Meshuggana8.exe (PID: 2208)
- Meshuggana8.exe (PID: 3940)
Changes the autorun value in the registry
- Meshuggana8.exe (PID: 2276)
Detected artifacts of LokiBot
- Meshuggana8.exe (PID: 3940)
LOKIBOT was detected
- Meshuggana8.exe (PID: 3940)
Connects to CnC server
- Meshuggana8.exe (PID: 3940)
Actions looks like stealing of personal data
- Meshuggana8.exe (PID: 3940)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3704)
- Shipping Docs -Commercial Inv-Packing List-ETA-F41C63F.exe (PID: 4044)
- Meshuggana8.exe (PID: 3940)
Starts itself from another location
- Shipping Docs -Commercial Inv-Packing List-ETA-F41C63F.exe (PID: 4044)
Application launched itself
- Meshuggana8.exe (PID: 2208)
- Meshuggana8.exe (PID: 2276)
Loads DLL from Mozilla Firefox
- Meshuggana8.exe (PID: 3940)
Creates files in the user directory
- Meshuggana8.exe (PID: 3940)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2408)
INFO
Application launched itself
- chrome.exe (PID: 2408)
Reads the hosts file
- chrome.exe (PID: 1704)
- chrome.exe (PID: 2408)
Reads Internet Cache Settings
- chrome.exe (PID: 2408)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
70
Monitored processes
32
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 504 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,5156873244943368525,9036509816412299753,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1880041339810051939 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2224 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 884 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3704.7933\Shipping Docs -Commercial Inv-Packing List-ETA-F41C63F.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3704.7933\Shipping Docs -Commercial Inv-Packing List-ETA-F41C63F.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 1036 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,5156873244943368525,9036509816412299753,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1812625182210542848 --mojo-platform-channel-handle=488 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,5156873244943368525,9036509816412299753,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12571695339598370934 --mojo-platform-channel-handle=4124 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1584 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,5156873244943368525,9036509816412299753,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6134243993908086146 --mojo-platform-channel-handle=2788 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1704 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,5156873244943368525,9036509816412299753,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=12378276146776722651 --mojo-platform-channel-handle=1640 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1980 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,5156873244943368525,9036509816412299753,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6302884031977672627 --mojo-platform-channel-handle=4216 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2104 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,5156873244943368525,9036509816412299753,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4423288071060747538 --mojo-platform-channel-handle=4712 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2208 | "C:\Users\admin\Staahejens7\Meshuggana8.exe" | C:\Users\admin\Staahejens7\Meshuggana8.exe | — | Meshuggana8.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 2232 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2480 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 596
Read events
1 446
Write events
145
Delete events
5
Modification events
| (PID) Process: | (2408) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2408) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2408) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2408) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2408) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2232) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2408-13215524513648000 |
Value: 259 | |||
| (PID) Process: | (2408) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2408) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2408) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2408) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2408-13215524513648000 |
Value: 259 | |||
Executable files
3
Suspicious files
55
Text files
266
Unknown types
16
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2408 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\95ed2809-6162-45c1-b950-db45e7d48c13.tmp | — | |
MD5:— | SHA256:— | |||
| 2408 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2408 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2408 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2408 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2408 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF39a9d7.TMP | text | |
MD5:— | SHA256:— | |||
| 2408 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF39a9a8.TMP | text | |
MD5:— | SHA256:— | |||
| 2408 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2408 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2408 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
29
DNS requests
18
Threats
32
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1704 | chrome.exe | GET | 302 | 172.217.18.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 512 b | whitelisted |
1704 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://crl4.digicert.com/DigiCertHighAssuranceEVRootCA.crl | US | der | 528 b | whitelisted |
1704 | chrome.exe | GET | 200 | 173.194.138.200:80 | http://r3---sn-aigzrn7d.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mip=185.92.25.7&mm=28&mn=sn-aigzrn7d&ms=nvh&mt=1571050999&mv=m&mvi=2&pl=24&shardbypass=yes | US | crx | 293 Kb | whitelisted |
3940 | Meshuggana8.exe | POST | — | 206.217.131.238:80 | http://halwaja.com/zxfghshjvdbjsngfhrgdjmh/zdxfgf/Panel/five/fre.php | US | — | — | malicious |
3940 | Meshuggana8.exe | POST | — | 206.217.131.238:80 | http://halwaja.com/zxfghshjvdbjsngfhrgdjmh/zdxfgf/Panel/five/fre.php | US | — | — | malicious |
1704 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRJ9L2KGL92BpjF3kAtaDtxauTmhgQUPdNQpdagre7zSmAKZdMh1Pj41g8CEAU5fm3dSuY9dJCdoTinHgw%3D | US | der | 471 b | whitelisted |
3940 | Meshuggana8.exe | POST | — | 206.217.131.238:80 | http://halwaja.com/zxfghshjvdbjsngfhrgdjmh/zdxfgf/Panel/five/fre.php | US | — | — | malicious |
1704 | chrome.exe | GET | 302 | 172.217.18.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 507 b | whitelisted |
3940 | Meshuggana8.exe | POST | — | 206.217.131.238:80 | http://halwaja.com/zxfghshjvdbjsngfhrgdjmh/zdxfgf/Panel/five/fre.php | US | — | — | malicious |
3940 | Meshuggana8.exe | POST | — | 206.217.131.238:80 | http://halwaja.com/zxfghshjvdbjsngfhrgdjmh/zdxfgf/Panel/five/fre.php | US | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1704 | chrome.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1704 | chrome.exe | 216.58.207.36:443 | www.google.com | Google Inc. | US | whitelisted |
1704 | chrome.exe | 172.217.18.163:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1704 | chrome.exe | 162.125.66.6:443 | uc2787b299e32cad2448e955d406.dl.dropboxusercontent.com | Dropbox, Inc. | DE | shared |
1704 | chrome.exe | 216.58.206.14:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
1704 | chrome.exe | 172.217.23.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1704 | chrome.exe | 216.58.206.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
1704 | chrome.exe | 162.125.66.1:443 | www.dropbox.com | Dropbox, Inc. | DE | shared |
1704 | chrome.exe | 172.217.22.78:443 | clients1.google.com | Google Inc. | US | whitelisted |
1704 | chrome.exe | 216.58.208.35:443 | www.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.dropbox.com |
| shared |
accounts.google.com |
| shared |
ocsp.digicert.com |
| whitelisted |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
crl4.digicert.com |
| whitelisted |
uc2787b299e32cad2448e955d406.dl.dropboxusercontent.com |
| suspicious |
sb-ssl.google.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3940 | Meshuggana8.exe | A Network Trojan was detected | ET TROJAN LokiBot User-Agent (Charon/Inferno) |
3940 | Meshuggana8.exe | A Network Trojan was detected | ET TROJAN LokiBot Checkin |
3940 | Meshuggana8.exe | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M1 |
3940 | Meshuggana8.exe | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M2 |
3940 | Meshuggana8.exe | A Network Trojan was detected | MALWARE [PTsecurity] Loki Bot Check-in M2 |
3940 | Meshuggana8.exe | A Network Trojan was detected | ET TROJAN LokiBot User-Agent (Charon/Inferno) |
3940 | Meshuggana8.exe | A Network Trojan was detected | ET TROJAN LokiBot Checkin |
3940 | Meshuggana8.exe | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M1 |
3940 | Meshuggana8.exe | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M2 |
3940 | Meshuggana8.exe | A Network Trojan was detected | MALWARE [PTsecurity] Loki Bot Check-in M2 |
5 ETPRO signatures available at the full report