| File name: | Proforma Invoice.exe |
| Full analysis: | https://app.any.run/tasks/7e2fb693-e0ee-48e1-b928-66cf6c62d6a3 |
| Verdict: | Malicious activity |
| Threats: | FormBook is a data stealer that is being distributed as a MaaS. FormBook differs from a lot of competing malware by its extreme ease of use that allows even the unexperienced threat actors to use FormBook virus. |
| Analysis date: | May 24, 2019, 11:29:12 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 6649129098CAA5F9397A1DF582FEC1BB |
| SHA1: | EA0232FFA0D8C0B71B4FB35DFBD381D03C6F3063 |
| SHA256: | 9D8EEDA2C397ED38C99999881EBC1AE4EAEFF581189956AF092878002622F447 |
| SSDEEP: | 12288:y1fHjCHB1yZvRnwcXwxXr7ypm4eSs1k2s5YqK7:GAB1yZvRnwcXw7KeSsQY9 |
MALICIOUS
Uses Task Scheduler to run other applications
- Proforma Invoice.exe (PID: 3056)
- p08ad-4dtb.exe (PID: 2692)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 2816)
- schtasks.exe (PID: 3364)
FORMBOOK was detected
- explorer.exe (PID: 252)
Connects to CnC server
- explorer.exe (PID: 252)
Formbook was detected
- wuauclt.exe (PID: 2208)
- Firefox.exe (PID: 2660)
Changes the autorun value in the registry
- wuauclt.exe (PID: 2208)
Actions looks like stealing of personal data
- wuauclt.exe (PID: 2208)
Loads dropped or rewritten executable
- wuauclt.exe (PID: 2208)
Uses SVCHOST.EXE for hidden code execution
- explorer.exe (PID: 252)
Stealing of credential data
- cmd.exe (PID: 2344)
- wuauclt.exe (PID: 2208)
SUSPICIOUS
Reads Internet Cache Settings
- explorer.exe (PID: 252)
Creates files in the user directory
- explorer.exe (PID: 252)
- Proforma Invoice.exe (PID: 3056)
- wuauclt.exe (PID: 2208)
Executed via COM
- DllHost.exe (PID: 2952)
- DllHost.exe (PID: 2956)
- DllHost.exe (PID: 4084)
Executable content was dropped or overwritten
- Proforma Invoice.exe (PID: 3056)
- explorer.exe (PID: 252)
- wuauclt.exe (PID: 2208)
- DllHost.exe (PID: 4084)
Application launched itself
- Proforma Invoice.exe (PID: 3056)
- p08ad-4dtb.exe (PID: 2692)
Starts CMD.EXE for commands execution
- wuauclt.exe (PID: 2208)
Loads DLL from Mozilla Firefox
- wuauclt.exe (PID: 2208)
Creates files in the program directory
- DllHost.exe (PID: 4084)
INFO
Manual execution by user
- WINWORD.EXE (PID: 3148)
- WINWORD.EXE (PID: 1876)
- wuauclt.exe (PID: 2208)
- WINWORD.EXE (PID: 2896)
Creates files in the user directory
- WINWORD.EXE (PID: 3148)
- WINWORD.EXE (PID: 1876)
- WINWORD.EXE (PID: 2896)
- Firefox.exe (PID: 2660)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3148)
- WINWORD.EXE (PID: 1876)
- WINWORD.EXE (PID: 2896)
Starts Microsoft Office Application
- explorer.exe (PID: 252)
Dropped object may contain Bitcoin addresses
- Proforma Invoice.exe (PID: 3056)
- explorer.exe (PID: 252)
- DllHost.exe (PID: 4084)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:05:24 03:58:32+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 259072 |
| InitializedDataSize: | 350208 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x413be |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | ListDir |
| CompanyName: | - |
| FileDescription: | ListDir |
| FileVersion: | 1.0.0.0 |
| InternalName: | ListDir.exe |
| LegalCopyright: | Copyright © 2009 |
| LegalTrademarks: | - |
| OriginalFileName: | ListDir.exe |
| ProductName: | ListDir |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 24-May-2019 01:58:32 |
| Comments: | ListDir |
| CompanyName: | - |
| FileDescription: | ListDir |
| FileVersion: | 1.0.0.0 |
| InternalName: | ListDir.exe |
| LegalCopyright: | Copyright © 2009 |
| LegalTrademarks: | - |
| OriginalFilename: | ListDir.exe |
| ProductName: | ListDir |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 24-May-2019 01:58:32 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x0003F3C4 | 0x0003F400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.95011 |
.rsrc | 0x00042000 | 0x0005546C | 0x00055600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.7535 |
.reloc | 0x00098000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 7.91463 | 27540 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 7.87658 | 11631 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 4.91967 | 296 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 5.52031 | 488 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 5.50697 | 744 | Latin 1 / Western European | UNKNOWN | RT_ICON |
7 | 5.11998 | 1640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
8 | 5.18944 | 2664 | Latin 1 / Western European | UNKNOWN | RT_ICON |
9 | 4.96162 | 3560 | Latin 1 / Western European | UNKNOWN | RT_ICON |
10 | 5.07979 | 5864 | Latin 1 / Western European | UNKNOWN | RT_ICON |
Imports
mscoree.dll |
Total processes
57
Monitored processes
18
Malicious processes
4
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 252 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | ctfmon.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
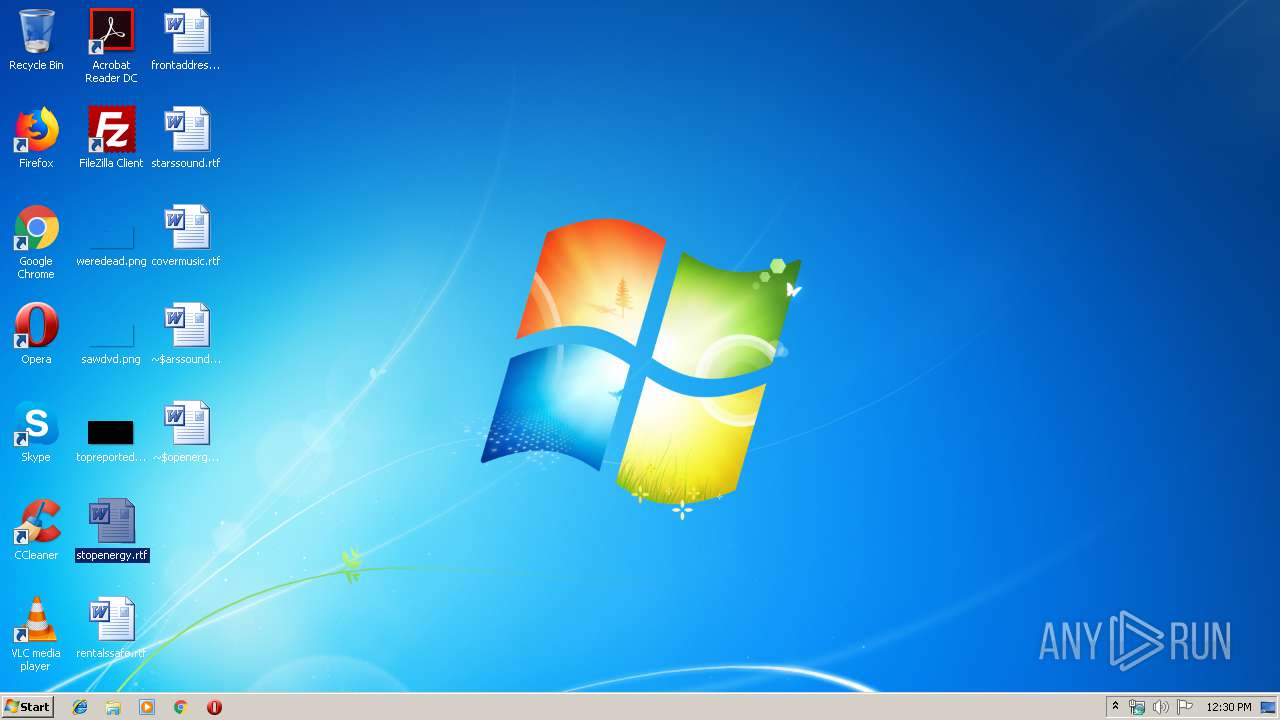
| 1876 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\stopenergy.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2208 | "C:\Windows\System32\wuauclt.exe" | C:\Windows\System32\wuauclt.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Update Exit code: 0 Version: 7.5.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2344 | /c copy "C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Login Data" "C:\Users\admin\AppData\Local\Temp\DB1" /V | C:\Windows\System32\cmd.exe | wuauclt.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2480 | "C:\Program Files\Kqpy\p08ad-4dtb.exe" | C:\Program Files\Kqpy\p08ad-4dtb.exe | — | p08ad-4dtb.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: ListDir Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2532 | "C:\Windows\System32\svchost.exe" | C:\Windows\System32\svchost.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2660 | "C:\Program Files\Mozilla Firefox\Firefox.exe" | C:\Program Files\Mozilla Firefox\Firefox.exe | wuauclt.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 65.0.2 Modules
| |||||||||||||||
| 2692 | "C:\Program Files\Kqpy\p08ad-4dtb.exe" | C:\Program Files\Kqpy\p08ad-4dtb.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: ListDir Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2816 | "C:\Windows\System32\schtasks.exe" /Create /TN "Updates\BooHAxnTjmIN" /XML "C:\Users\admin\AppData\Local\Temp\tmpA988.tmp" | C:\Windows\System32\schtasks.exe | — | Proforma Invoice.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2896 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\starssound.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
5 959
Read events
5 707
Write events
203
Delete events
49
Modification events
| (PID) Process: | (3148) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | }! |
Value: 7F7D21004C0C0000010000000000000000000000 | |||
| (PID) Process: | (3148) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3148) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (252) explorer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1320681502 | |||
| (PID) Process: | (252) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | {7P5N40RS-N0SO-4OSP-874N-P0S2R0O9SN8R}\Zvpebfbsg Bssvpr\Bssvpr14\JVAJBEQ.RKR |
Value: 00000000010000000000000000000000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF3068BCF82312D50100000000 | |||
| (PID) Process: | (252) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 0000000006000000020000008995000003000000020000001B6900004D006900630072006F0073006F00660074002E004100750074006F00470065006E006500720061007400650064002E007B00310035003900360032003100370035002D0037004400460043002D0042003100440037002D0042003000440031002D004500420034004300300038004600460044003700350034007D000000350201000000000000000000A27650E935023CE735025E7C37777CE93502787C3777030000008A018C01EC92CB026CE73502F77C37770100000050E93502847C3777BCE73502B0E73502C8E73502000000000000000000000000B8E7350250E93502000000000000000000000000F0E83502F0E8350200000000010000007CE93502F0E83502B2FE3777F270377785FC3777B5860A759A7C3677EC92CB02A27E367734E935021800000014FB3502006F367700000000000000001CE935023C003E007CE93502C34E9D00BCE7350200000000D84609000000350218E8350204EB350200000088C8000000C8000000C8000000C8000000F2010300000000000000D868A8D33A030106004000000000F0EA35021053D8687FEB9C7620000000220000001053D868102FD8020000000011000000B8450A00B0450A00A8D33A03ACE800001FB258415CE835028291BE75ACE8350260E835022795BE750000000054CAD20288E83502CD94BE7554CAD20234E93502C8C5D202E194BE7500000000C8C5D20234E9350290E8350203000000020000001B6900004D006900630072006F0073006F00660074002E004100750074006F00470065006E006500720061007400650064002E007B00310035003900360032003100370035002D0037004400460043002D0042003100440037002D0042003000440031002D004500420034004300300038004600460044003700350034007D000000350201000000000000000000A27650E935023CE735025E7C37777CE93502787C3777030000008A018C01EC92CB026CE73502F77C37770100000050E93502847C3777BCE73502B0E73502C8E73502000000000000000000000000B8E7350250E93502000000000000000000000000F0E83502F0E8350200000000010000007CE93502F0E83502B2FE3777F270377785FC3777B5860A759A7C3677EC92CB02A27E367734E935021800000014FB3502006F367700000000000000001CE935023C003E007CE93502C34E9D00BCE7350200000000D84609000000350218E8350204EB350200000088C8000000C8000000C8000000C8000000F2010300000000000000D868A8D33A030106004000000000F0EA35021053D8687FEB9C7620000000220000001053D868102FD8020000000011000000B8450A00B0450A00A8D33A03ACE800001FB258415CE835028291BE75ACE8350260E835022795BE750000000054CAD20288E83502CD94BE7554CAD20234E93502C8C5D202E194BE7500000000C8C5D20234E9350290E8350203000000020000001B6900004D006900630072006F0073006F00660074002E004100750074006F00470065006E006500720061007400650064002E007B00310035003900360032003100370035002D0037004400460043002D0042003100440037002D0042003000440031002D004500420034004300300038004600460044003700350034007D000000350201000000000000000000A27650E935023CE735025E7C37777CE93502787C3777030000008A018C01EC92CB026CE73502F77C37770100000050E93502847C3777BCE73502B0E73502C8E73502000000000000000000000000B8E7350250E93502000000000000000000000000F0E83502F0E8350200000000010000007CE93502F0E83502B2FE3777F270377785FC3777B5860A759A7C3677EC92CB02A27E367734E935021800000014FB3502006F367700000000000000001CE935023C003E007CE93502C34E9D00BCE7350200000000D84609000000350218E8350204EB350200000088C8000000C8000000C8000000C8000000F2010300000000000000D868A8D33A030106004000000000F0EA35021053D8687FEB9C7620000000220000001053D868102FD8020000000011000000B8450A00B0450A00A8D33A03ACE800001FB258415CE835028291BE75ACE8350260E835022795BE750000000054CAD20288E83502CD94BE7554CAD20234E93502C8C5D202E194BE7500000000C8C5D20234E9350290E83502 | |||
| (PID) Process: | (252) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.rtf\OpenWithList |
| Operation: | write | Name: | a |
Value: WINWORD.EXE | |||
| (PID) Process: | (252) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.rtf\OpenWithList |
| Operation: | write | Name: | MRUList |
Value: a | |||
| (PID) Process: | (252) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.rtf\OpenWithProgids |
| Operation: | write | Name: | Word.RTF.8 |
Value: | |||
| (PID) Process: | (252) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\RecentDocs |
| Operation: | write | Name: | 2 |
Value: 7300740061007200730073006F0075006E0064002E00720074006600000080003200000000000000000000007374617273736F756E642E727466202832292E6C6E6B00005A0008000400EFBE00000000000000002A000000000000000000000000000000000000000000000000007300740061007200730073006F0075006E0064002E0072007400660020002800320029002E006C006E006B00000026000000 | |||
Executable files
4
Suspicious files
79
Text files
10
Unknown types
20
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3148 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR97F.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3148 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{389A53B2-EB07-4237-A049-383BF162EBC9}.tmp | — | |
MD5:— | SHA256:— | |||
| 3148 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{CAEBFC7C-1734-4BE3-8BA6-331383CF36EC}.tmp | — | |
MD5:— | SHA256:— | |||
| 1876 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR4B7A.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1876 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{87282B04-9461-432A-9A89-8630E2791BA4}.tmp | — | |
MD5:— | SHA256:— | |||
| 1876 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{5F25ADE2-9064-4ACC-8ECD-2B0D355973D1}.tmp | — | |
MD5:— | SHA256:— | |||
| 2896 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRFD45.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2896 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{18DD7313-3764-4144-859A-2E25D38A59D7}.tmp | — | |
MD5:— | SHA256:— | |||
| 2896 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{E9DC503B-442D-4DE5-91D3-50877F1D5384}.tmp | — | |
MD5:— | SHA256:— | |||
| 3148 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
19
TCP/UDP connections
20
DNS requests
11
Threats
30
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
252 | explorer.exe | GET | 200 | 198.187.30.17:80 | http://www.discountclick.info/ak77/?_Df4AN=Buu56UTaTqtSsibq+MpAZXqn1/hVIFk6d9ttzuiG6xkdue37aKxAyLNLnsm0REyA35hEtw==&rLw=g818FTbp0f&sql=1 | US | binary | 323 Kb | malicious |
252 | explorer.exe | POST | 404 | 198.187.30.17:80 | http://www.discountclick.info/ak77/ | US | html | 298 b | malicious |
252 | explorer.exe | POST | — | 198.187.30.17:80 | http://www.discountclick.info/ak77/ | US | — | — | malicious |
252 | explorer.exe | POST | — | 85.233.160.22:80 | http://www.limordollar.com/ak77/ | GB | — | — | malicious |
252 | explorer.exe | GET | 200 | 85.233.160.22:80 | http://www.limordollar.com/ak77/?_Df4AN=pAVhzMkpk0mkamOER64mVrJ1yPnr+64es6MGrbcV3aCKgQHtRP4se699Yd7rHYXOwJlUHQ==&rLw=g818FTbp0f | GB | html | 491 b | malicious |
252 | explorer.exe | POST | — | 85.233.160.22:80 | http://www.limordollar.com/ak77/ | GB | — | — | malicious |
252 | explorer.exe | POST | — | 85.233.160.22:80 | http://www.limordollar.com/ak77/ | GB | — | — | malicious |
252 | explorer.exe | POST | 404 | 198.187.30.17:80 | http://www.discountclick.info/ak77/ | US | html | 298 b | malicious |
252 | explorer.exe | POST | — | 35.246.6.109:80 | http://www.bookroseroom.com/ak77/ | US | — | — | malicious |
252 | explorer.exe | POST | — | 192.0.78.25:80 | http://www.steviedandrea.com/ak77/ | US | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 85.233.160.22:80 | www.limordollar.com | Namesco Limited | GB | malicious |
252 | explorer.exe | 192.0.78.25:80 | www.steviedandrea.com | Automattic, Inc | US | malicious |
— | — | 192.0.78.25:80 | www.steviedandrea.com | Automattic, Inc | US | malicious |
252 | explorer.exe | 85.233.160.22:80 | www.limordollar.com | Namesco Limited | GB | malicious |
252 | explorer.exe | 35.246.6.109:80 | www.bookroseroom.com | — | US | malicious |
252 | explorer.exe | 154.210.164.153:80 | www.wafangdian9.com | MULTACOM CORPORATION | US | malicious |
252 | explorer.exe | 198.187.30.17:80 | www.discountclick.info | Namecheap, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.wafangdian9.com |
| unknown |
www.discountclick.info |
| malicious |
www.coinweekend.com |
| unknown |
www.limordollar.com |
| malicious |
www.bookroseroom.com |
| malicious |
www.formanspools.com |
| unknown |
www.steviedandrea.com |
| malicious |
www.qlajq.win |
| unknown |
www.1fypc7rmkce.biz |
| unknown |
www.knightsbridge-internet.net |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
252 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
252 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
252 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
252 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
252 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
252 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
252 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
252 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
252 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (POST) |
252 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
12 ETPRO signatures available at the full report