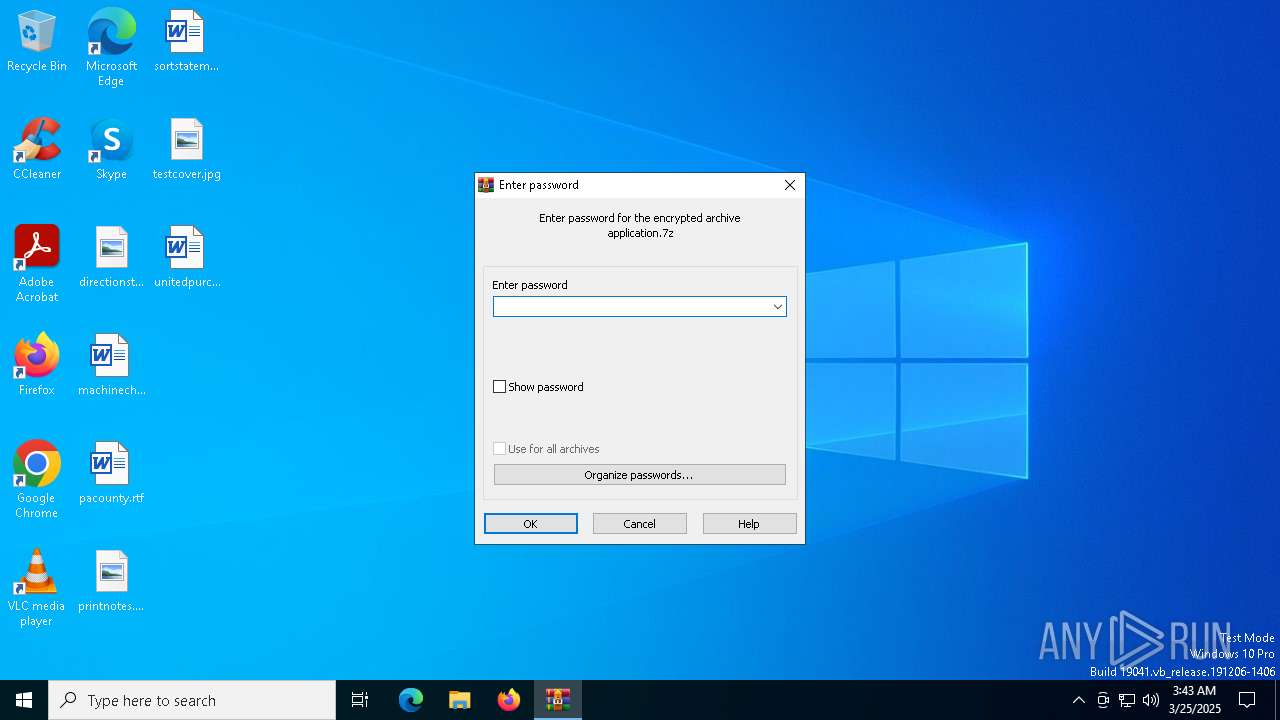
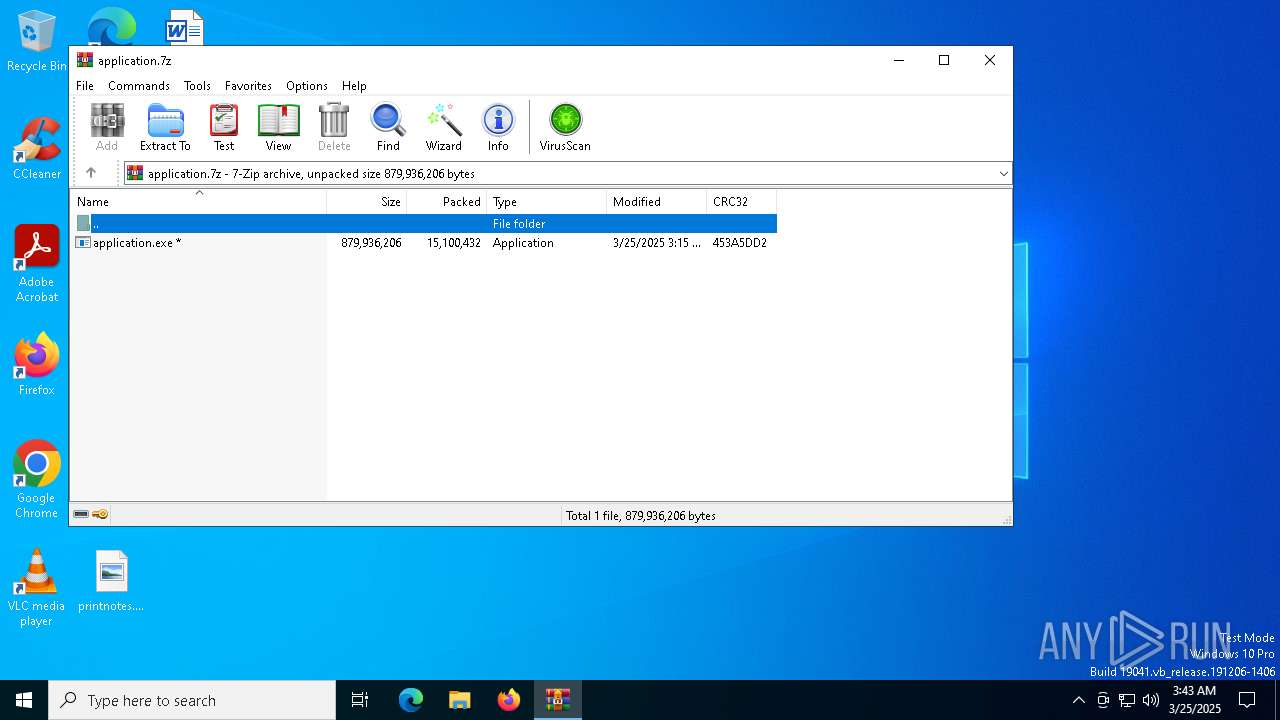
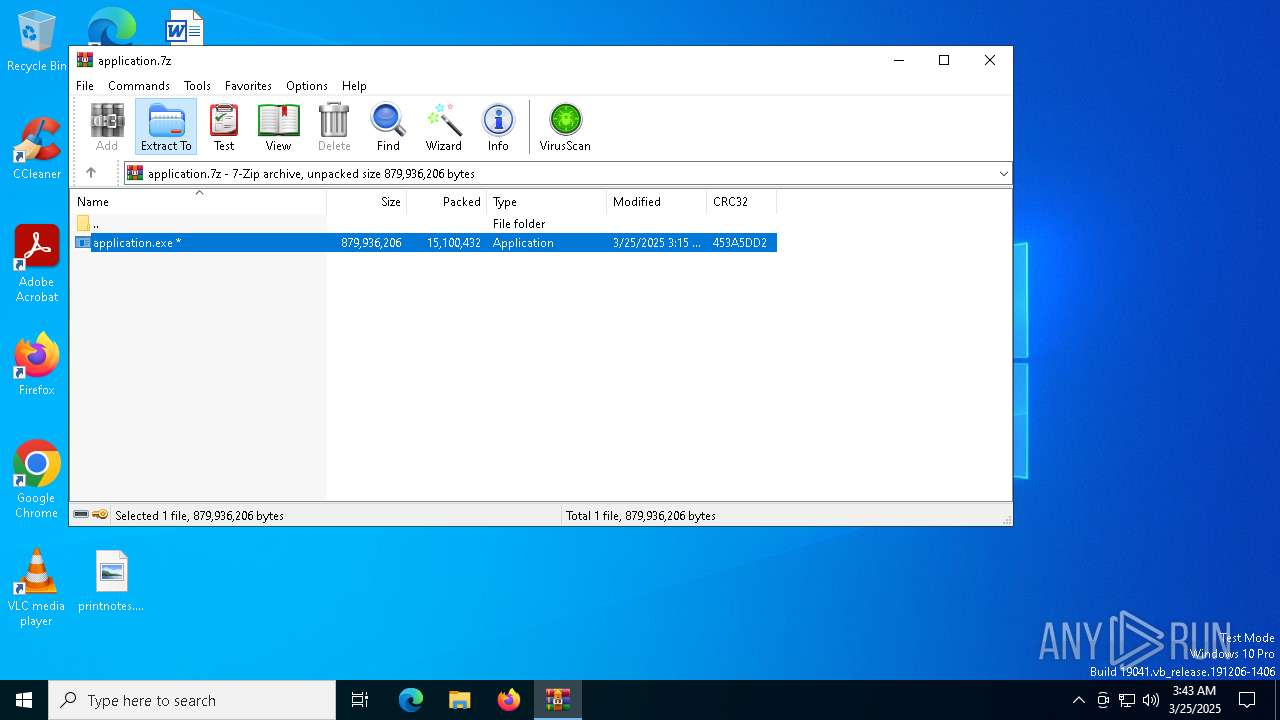
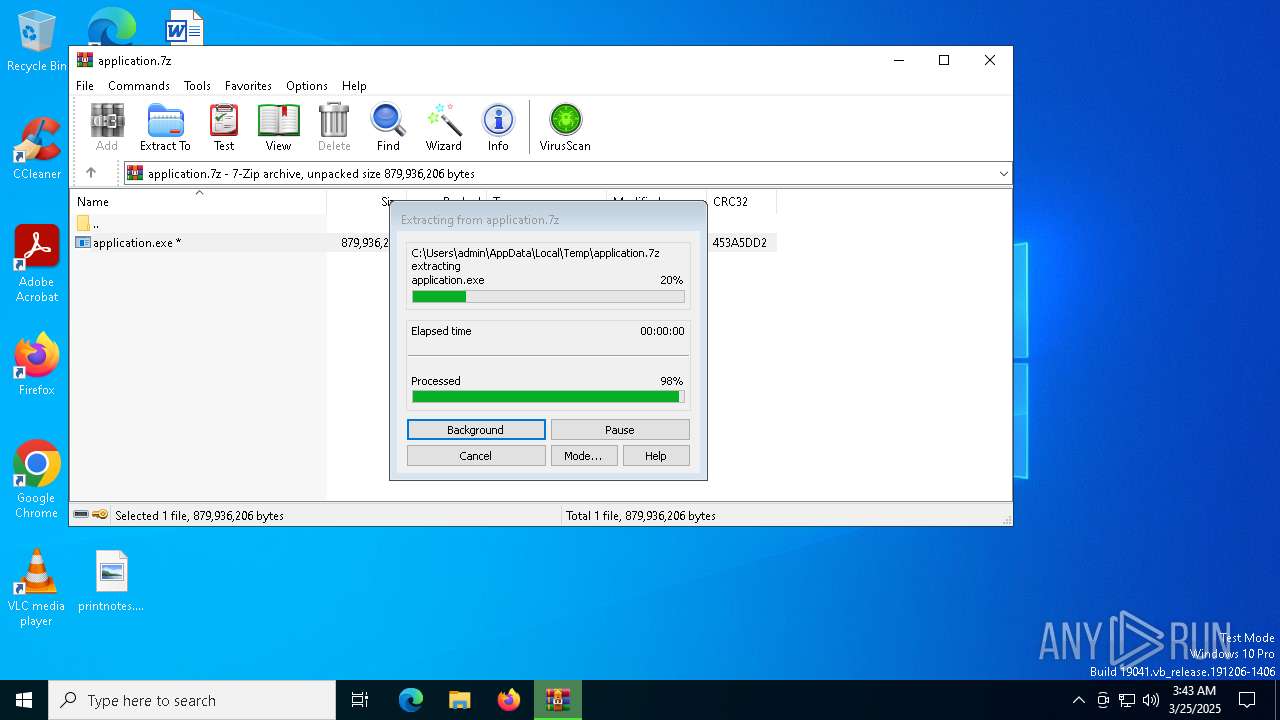
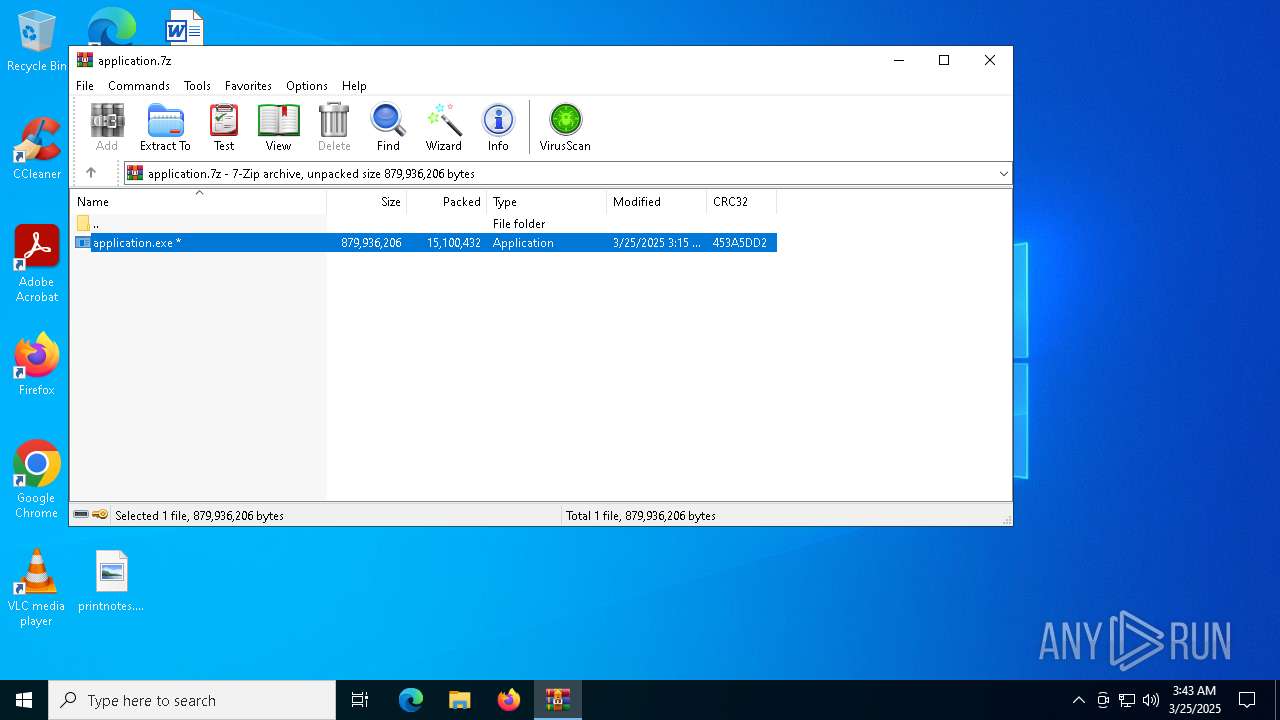
| File name: | application.7z |
| Full analysis: | https://app.any.run/tasks/341bc5ee-4d6e-4ed0-b6c8-f92c8615368d |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | March 25, 2025, 03:43:24 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | FE47F345B8B108F4E3B35EAA06B7CE19 |
| SHA1: | 3E5604F51BDF0C1B08FDCAC81F6B660FEF166C7E |
| SHA256: | 9D6D414DFA63BBB8487D470D4B6B0480952CDB568EC101CE97B7FACFF1D9992C |
| SSDEEP: | 98304:8SzS6r0RtwKHDjF+3XNtb6ntydwdNW3Bmw/mzTlQIZjv/a3m4fIjpWftkMdBN1YW:qJSUBBwdCjeb3G4Tk29vP3zrXw+V |
MALICIOUS
Actions looks like stealing of personal data
- Stylus.com (PID: 2644)
LUMMA mutex has been found
- Stylus.com (PID: 2644)
Steals credentials from Web Browsers
- Stylus.com (PID: 2644)
SUSPICIOUS
Reads security settings of Internet Explorer
- application.exe (PID: 6676)
Starts CMD.EXE for commands execution
- application.exe (PID: 6676)
- cmd.exe (PID: 6148)
Executing commands from a ".bat" file
- application.exe (PID: 6676)
Get information on the list of running processes
- cmd.exe (PID: 6148)
Application launched itself
- cmd.exe (PID: 6148)
There is functionality for taking screenshot (YARA)
- application.exe (PID: 6676)
- Stylus.com (PID: 2644)
Searches for installed software
- Stylus.com (PID: 2644)
Starts the AutoIt3 executable file
- cmd.exe (PID: 6148)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 6148)
The executable file from the user directory is run by the CMD process
- Stylus.com (PID: 2644)
Starts application with an unusual extension
- cmd.exe (PID: 6148)
INFO
Checks supported languages
- application.exe (PID: 6676)
- extrac32.exe (PID: 6228)
- Stylus.com (PID: 2644)
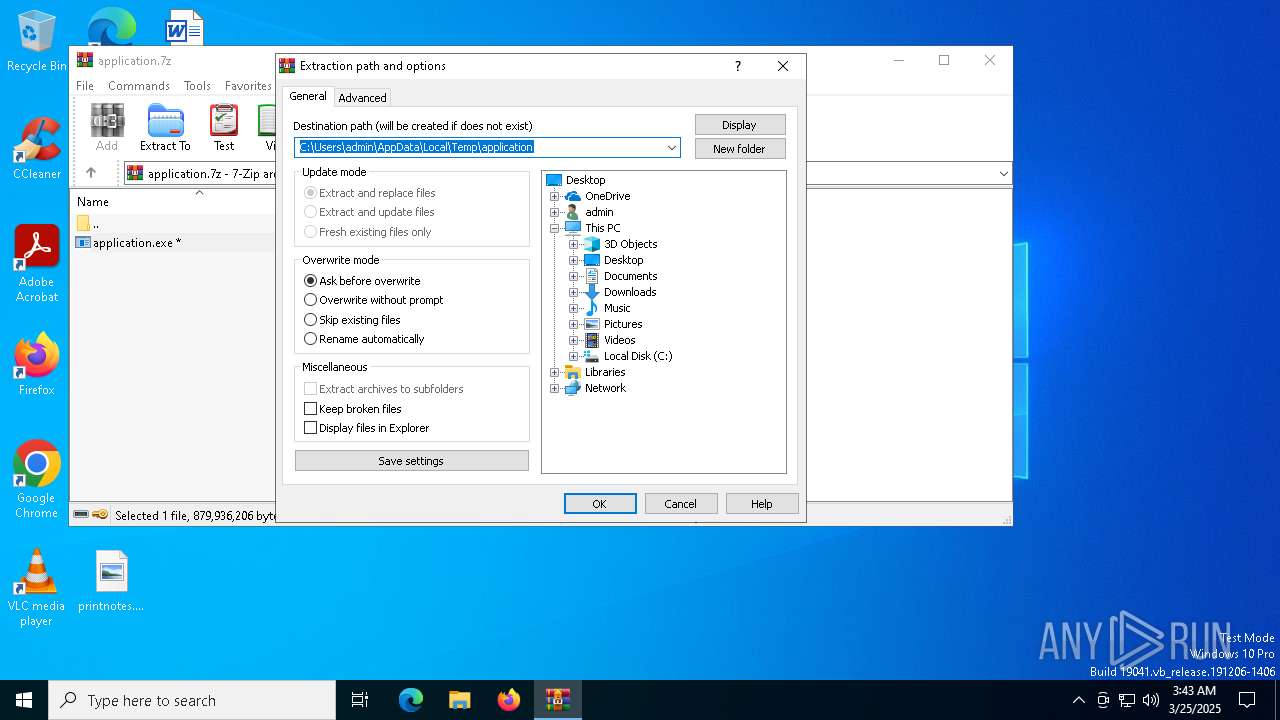
Manual execution by a user
- application.exe (PID: 6676)
Reads mouse settings
- Stylus.com (PID: 2644)
Create files in a temporary directory
- application.exe (PID: 6676)
- extrac32.exe (PID: 6228)
Reads the computer name
- application.exe (PID: 6676)
- extrac32.exe (PID: 6228)
- Stylus.com (PID: 2644)
Process checks computer location settings
- application.exe (PID: 6676)
Reads the software policy settings
- slui.exe (PID: 5528)
- Stylus.com (PID: 2644)
Checks proxy server information
- slui.exe (PID: 5528)
Creates a new folder
- cmd.exe (PID: 5988)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
EXIF
ZIP
| FileVersion: | 7z v0.04 |
|---|
Total processes
144
Monitored processes
16
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 644 | findstr /V "ROPE" Reduction | C:\Windows\SysWOW64\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2616 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2644 | Stylus.com b | C:\Users\admin\AppData\Local\Temp\213205\Stylus.com | cmd.exe | ||||||||||||
User: admin Company: AutoIt Team Integrity Level: MEDIUM Description: AutoIt v3 Script (Beta) Exit code: 0 Version: 3, 3, 15, 5 Modules
| |||||||||||||||
| 4120 | tasklist | C:\Windows\SysWOW64\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4212 | choice /d y /t 5 | C:\Windows\SysWOW64\choice.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Offers the user a choice Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4620 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\application.7z | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 5392 | findstr "SophosHealth bdservicehost AvastUI AVGUI nsWscSvc ekrn" | C:\Windows\SysWOW64\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5528 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5668 | findstr /I "opssvc wrsa" | C:\Windows\SysWOW64\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5988 | cmd /c md 213205 | C:\Windows\SysWOW64\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
3 568
Read events
3 543
Write events
12
Delete events
13
Modification events
| (PID) Process: | (4620) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (4620) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (4620) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (4620) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\application.7z | |||
| (PID) Process: | (4620) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4620) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4620) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (4620) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (4620) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (4620) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 15 |
Value: | |||
Executable files
0
Suspicious files
22
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6676 | application.exe | C:\Users\admin\AppData\Local\Temp\Vote.ppsm | binary | |
MD5:3B6E624A9419881590D1C0049B2A365F | SHA256:B6FA7422F7EEA91FDD799322B4735C705243428B7609BEBAE6EE3FD8A905567D | |||
| 6676 | application.exe | C:\Users\admin\AppData\Local\Temp\Convicted.ppsm | binary | |
MD5:9A822020F91DAD05B3004C413C4E04BE | SHA256:339B7CFC4D0C718F67E8CB9B436DBC57B6EE27553D7ED3AE2088BE13A2E44B02 | |||
| 6676 | application.exe | C:\Users\admin\AppData\Local\Temp\Gradually.ppsm | text | |
MD5:E1856DE13C496EA780D42B4FC2715E2D | SHA256:F974EEA730A497C06EC1EAF2B510348A6C88572DF27B718FB4509E1A2C282B04 | |||
| 6228 | extrac32.exe | C:\Users\admin\AppData\Local\Temp\Antique | binary | |
MD5:7BC422FC8DE15BEC5C1E9757C6DB7503 | SHA256:0C4E91841A11F98AB44F3EE711D4C3AE9FC1E9D11D01588DC97F7A57D4EC3712 | |||
| 6676 | application.exe | C:\Users\admin\AppData\Local\Temp\Discusses.ppsm | binary | |
MD5:0BC7C743D062D8ED7B3B8BA82E10FF4E | SHA256:487AD22FDC23B487448C40133ED5B7BA5A8D3582795FF3499BBDBFE453B16A1E | |||
| 6676 | application.exe | C:\Users\admin\AppData\Local\Temp\Nearest.ppsm | binary | |
MD5:0D34CFC57D72AF20088EF0E4E51E05C1 | SHA256:789C9145D08288B9CBBE48DDD38EA09D6F80B62B87583BFFCF495D8D5625D356 | |||
| 6676 | application.exe | C:\Users\admin\AppData\Local\Temp\Crest.ppsm | binary | |
MD5:C712A96D907320AED5950C6F894B3A96 | SHA256:A2110D23A32B9197FFA3A29A2E84F204AE3B3CB2201655887CE94E97E1C1F1B2 | |||
| 6676 | application.exe | C:\Users\admin\AppData\Local\Temp\None.ppsm | binary | |
MD5:CDB8342B66A2ABC866AEAC43CEA9566D | SHA256:1106B1D6C921B0901AAA2D142F6C88CE8636C773BD09E4AA81EC55ECA55DB95E | |||
| 6676 | application.exe | C:\Users\admin\AppData\Local\Temp\Tmp.ppsm | binary | |
MD5:D420AC9A927B1DA4B3453C5C9BEC9AE4 | SHA256:A6F23C41EF456889692AF6EF407BE424A907BAA6B765DDEC898FE7897F21C4DD | |||
| 6148 | cmd.exe | C:\Users\admin\AppData\Local\Temp\Gradually.ppsm.bat | text | |
MD5:E1856DE13C496EA780D42B4FC2715E2D | SHA256:F974EEA730A497C06EC1EAF2B510348A6C88572DF27B718FB4509E1A2C282B04 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
31
DNS requests
21
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.164.72:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5256 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5256 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5380 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.16.164.72:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 20.197.71.89:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | SG | whitelisted |
6544 | svchost.exe | 20.190.160.65:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
3216 | svchost.exe | 20.197.71.89:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | SG | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5380 | backgroundTaskHost.exe | 20.31.169.57:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
arc.msn.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |