| File name: | 7518a561-9863-4190-7075-08d8247b0d84345d1b67-7480-e55c-270b-c411be9963a7.eml |
| Full analysis: | https://app.any.run/tasks/70cf54d3-adb8-4d46-91d8-5350cc877152 |
| Verdict: | Malicious activity |
| Threats: | LokiBot was developed in 2015 to steal information from a variety of applications. Despite the age, this malware is still rather popular among cybercriminals. |
| Analysis date: | July 13, 2020, 04:24:33 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
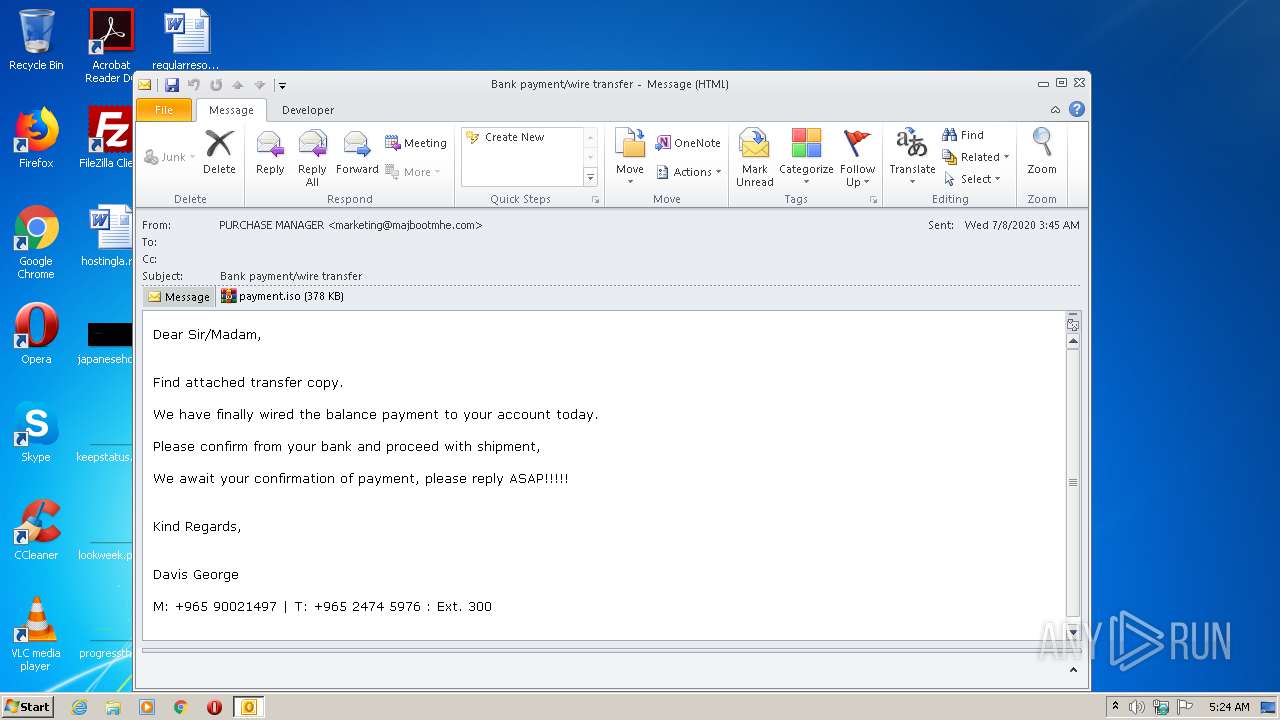
| MIME: | message/rfc822 |
| File info: | RFC 822 mail, ASCII text, with CRLF line terminators |
| MD5: | 1537A98D691B1B93303E112B678DADA1 |
| SHA1: | C12372D9B0AF1D5DD0B587B6B02CCC811ED346B9 |
| SHA256: | 9D16A5F07FF46439CC1E1040A70CC95E3EFD055C1FE8FCDB633F681D2614D364 |
| SSDEEP: | 12288:hXFF3iaeDG6UL2EDVSD5RrqksprcnqNz2Fp:hXPvKHULJDwr0rcYo |
MALICIOUS
Connects to CnC server
- payment.exe (PID: 2244)
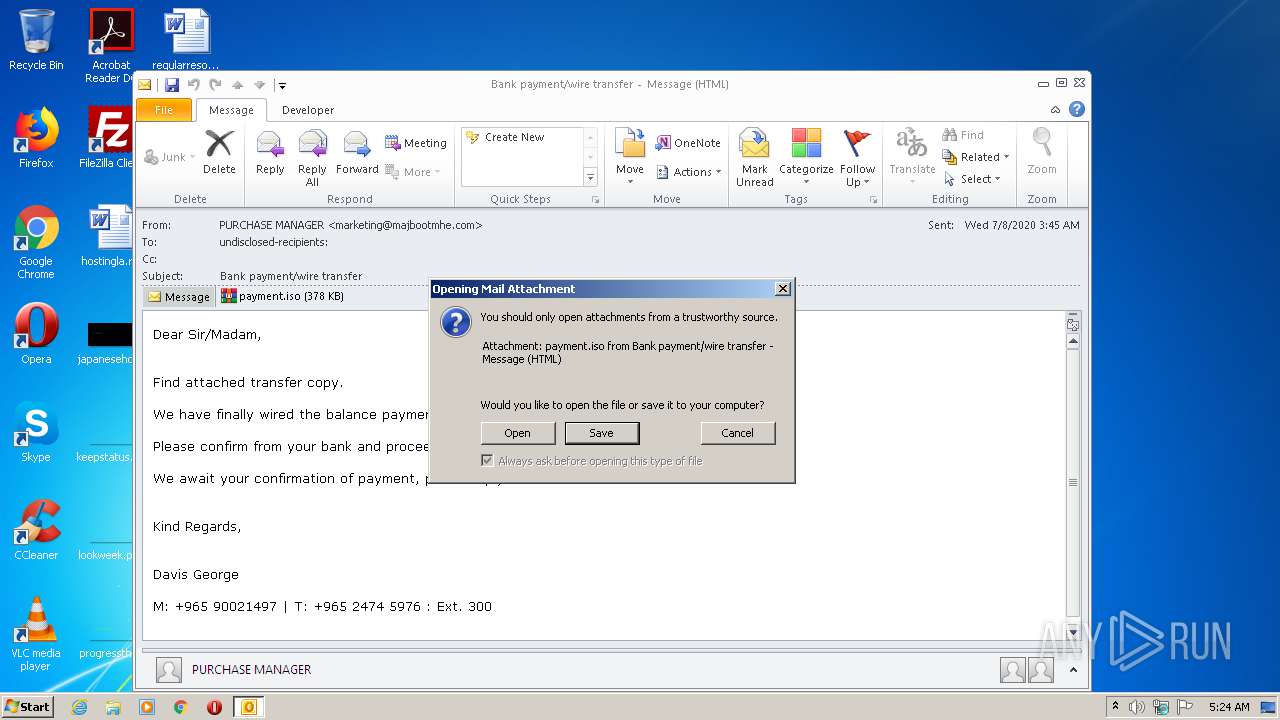
Application was dropped or rewritten from another process
- payment.exe (PID: 2244)
- payment.exe (PID: 1004)
- payment.exe (PID: 4060)
LOKIBOT was detected
- payment.exe (PID: 2244)
Actions looks like stealing of personal data
- payment.exe (PID: 2244)
SUSPICIOUS
Creates files in the user directory
- payment.exe (PID: 2244)
- OUTLOOK.EXE (PID: 1488)
Executable content was dropped or overwritten
- payment.exe (PID: 2244)
- WinRAR.exe (PID: 1944)
Loads DLL from Mozilla Firefox
- payment.exe (PID: 2244)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 1488)
INFO
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 1488)
Manual execution by user
- explorer.exe (PID: 3540)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .eml | | | E-Mail message (Var. 5) (100) |
|---|
Total processes
40
Monitored processes
6
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1004 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa1944.14393\payment.exe" 2 2244 1455437 | C:\Users\admin\AppData\Local\Temp\Rar$EXa1944.14393\payment.exe | — | payment.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
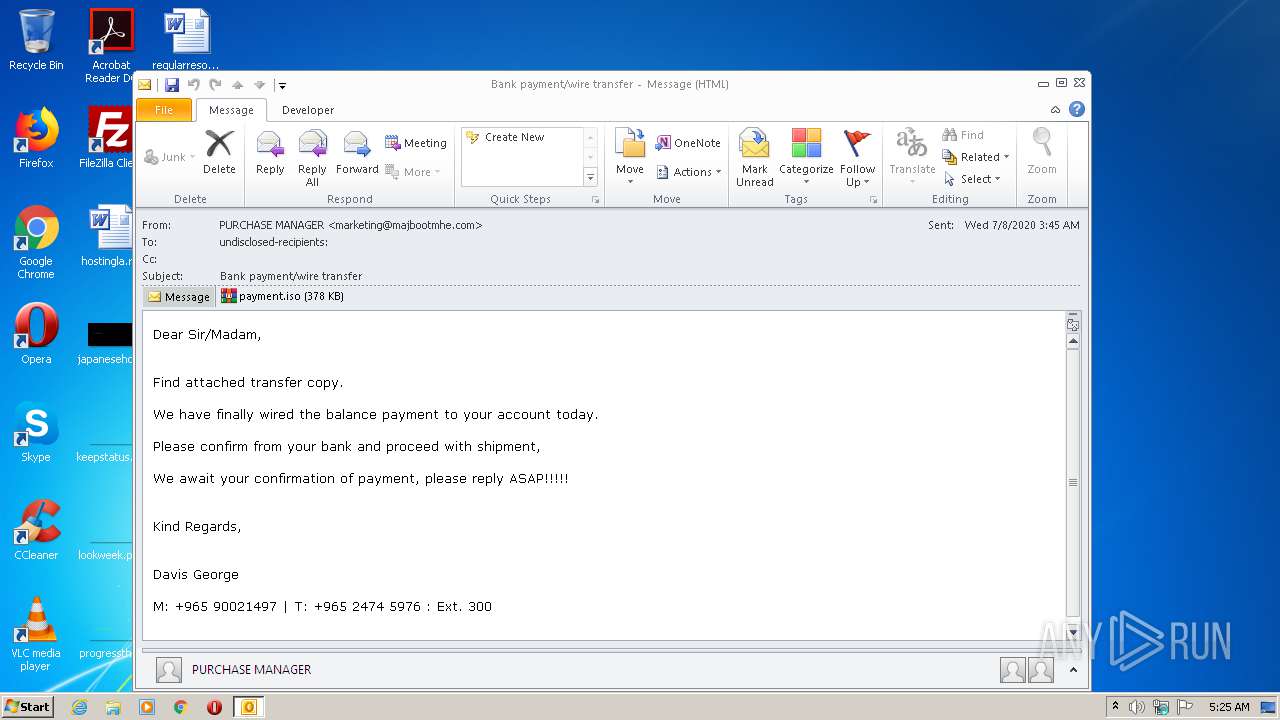
| 1488 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" /eml "C:\Users\admin\AppData\Local\Temp\7518a561-9863-4190-7075-08d8247b0d84345d1b67-7480-e55c-270b-c411be9963a7.eml" | C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
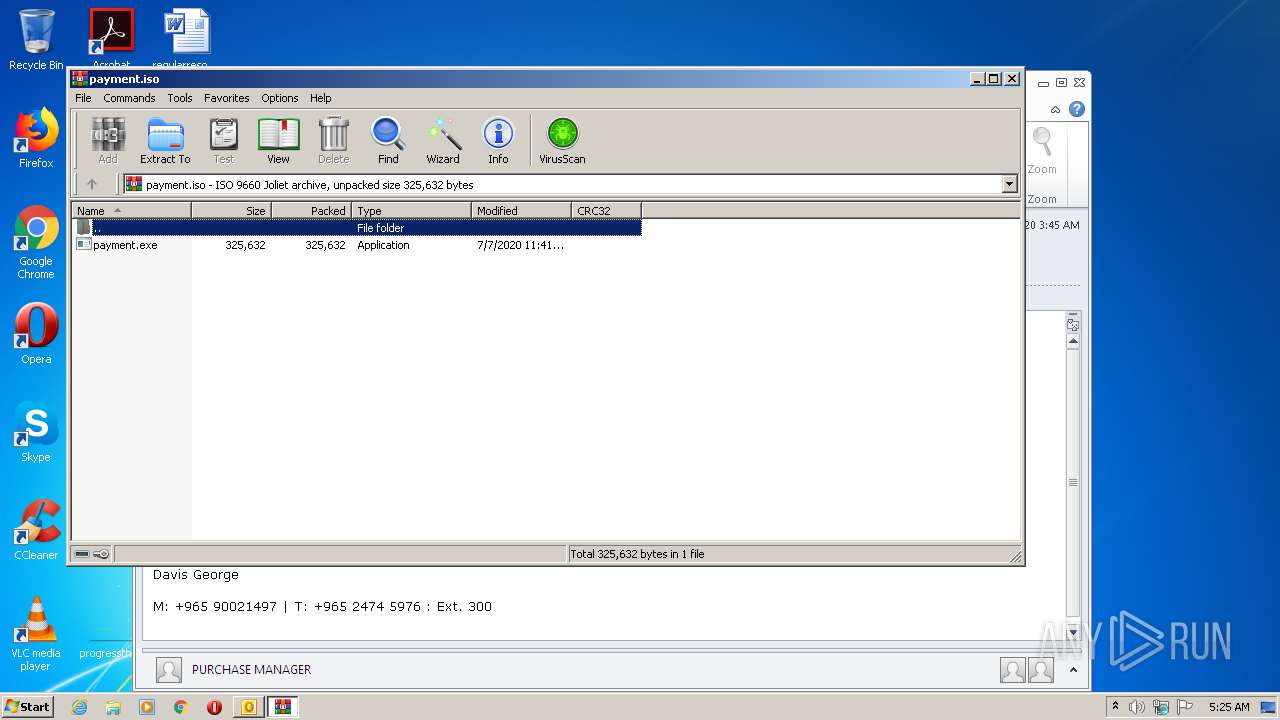
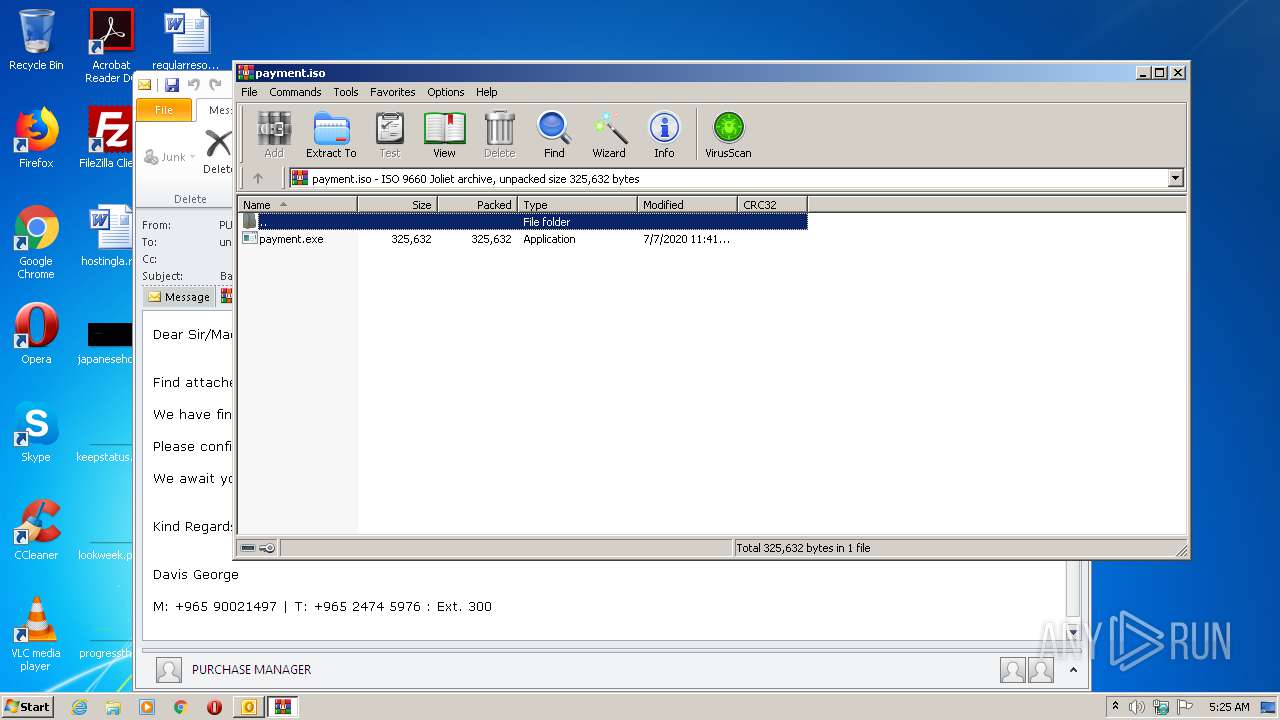
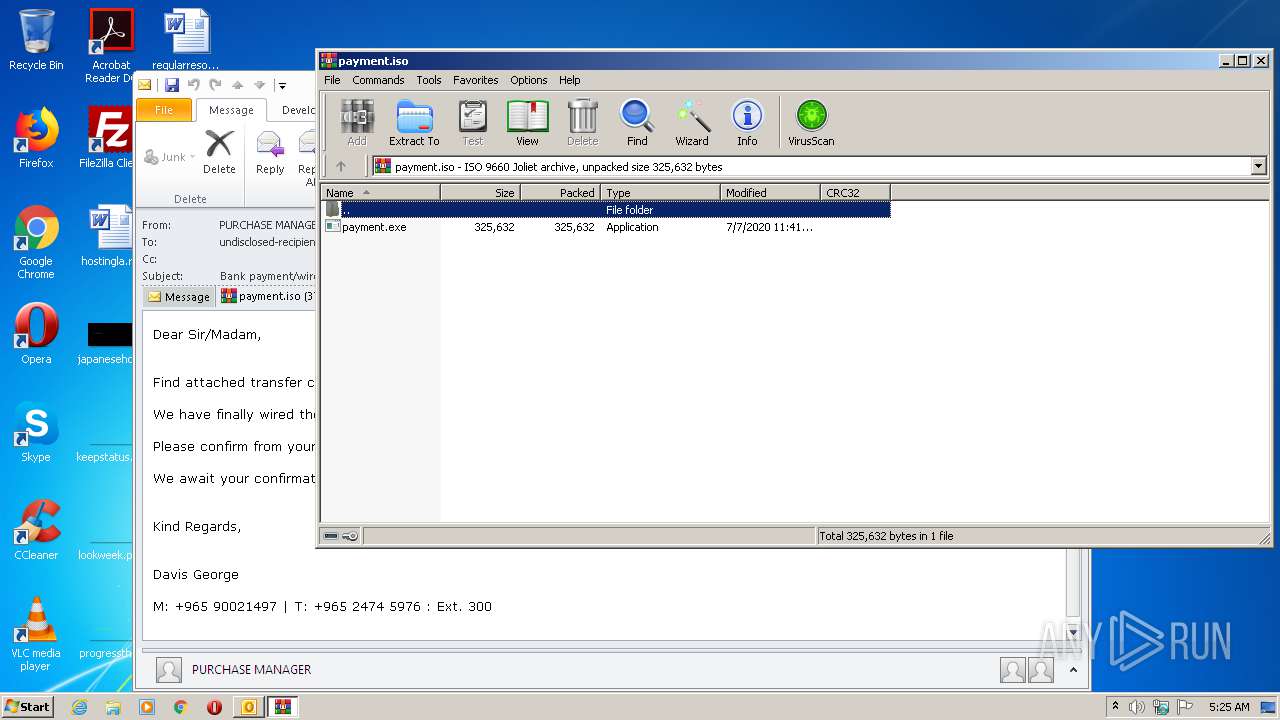
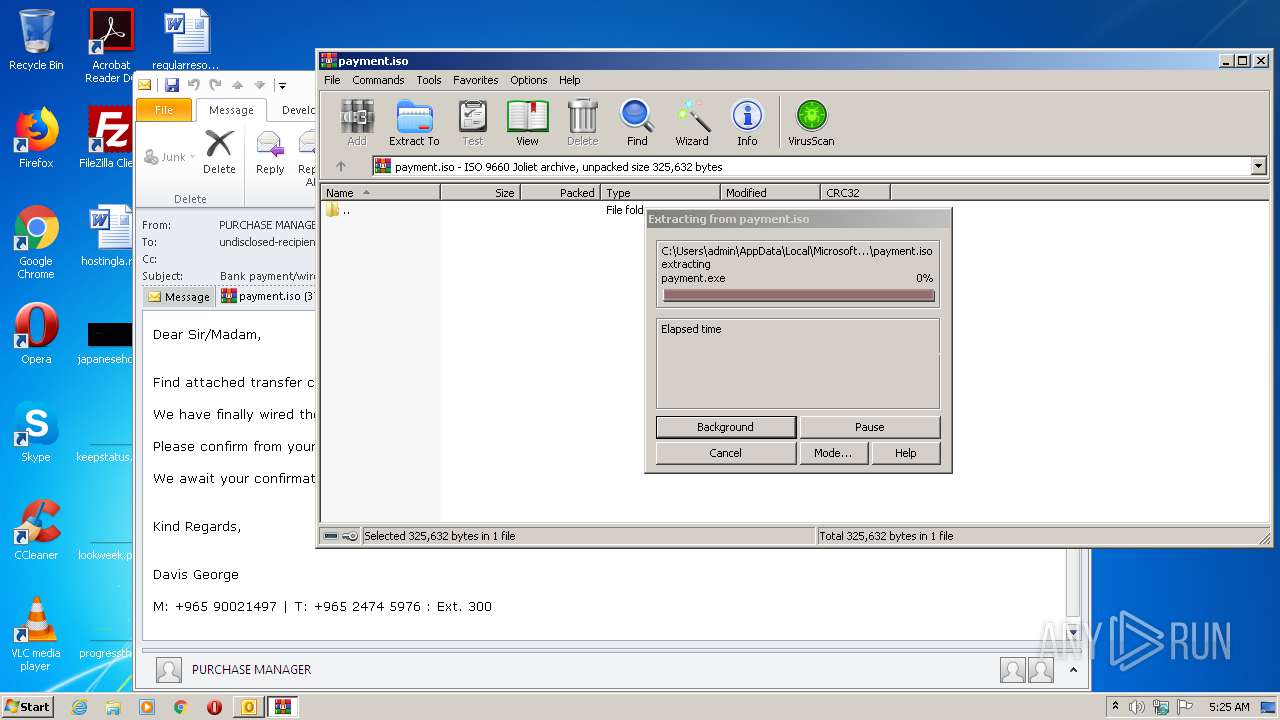
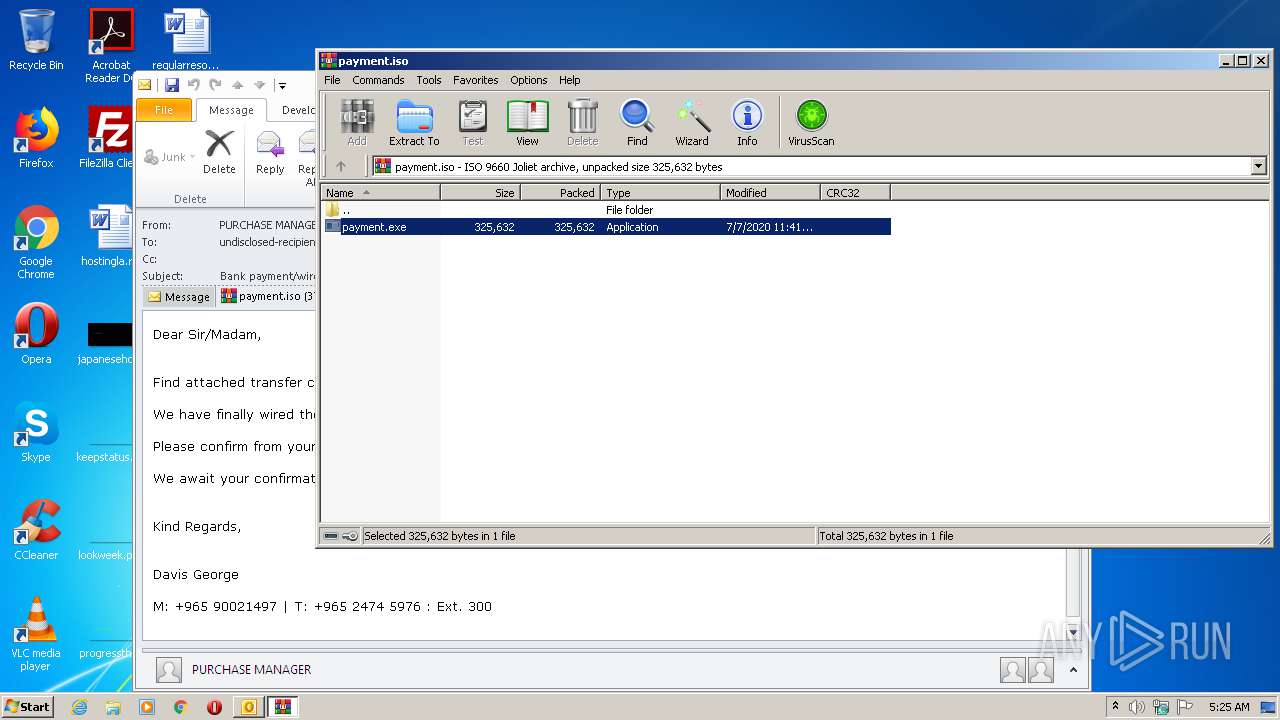
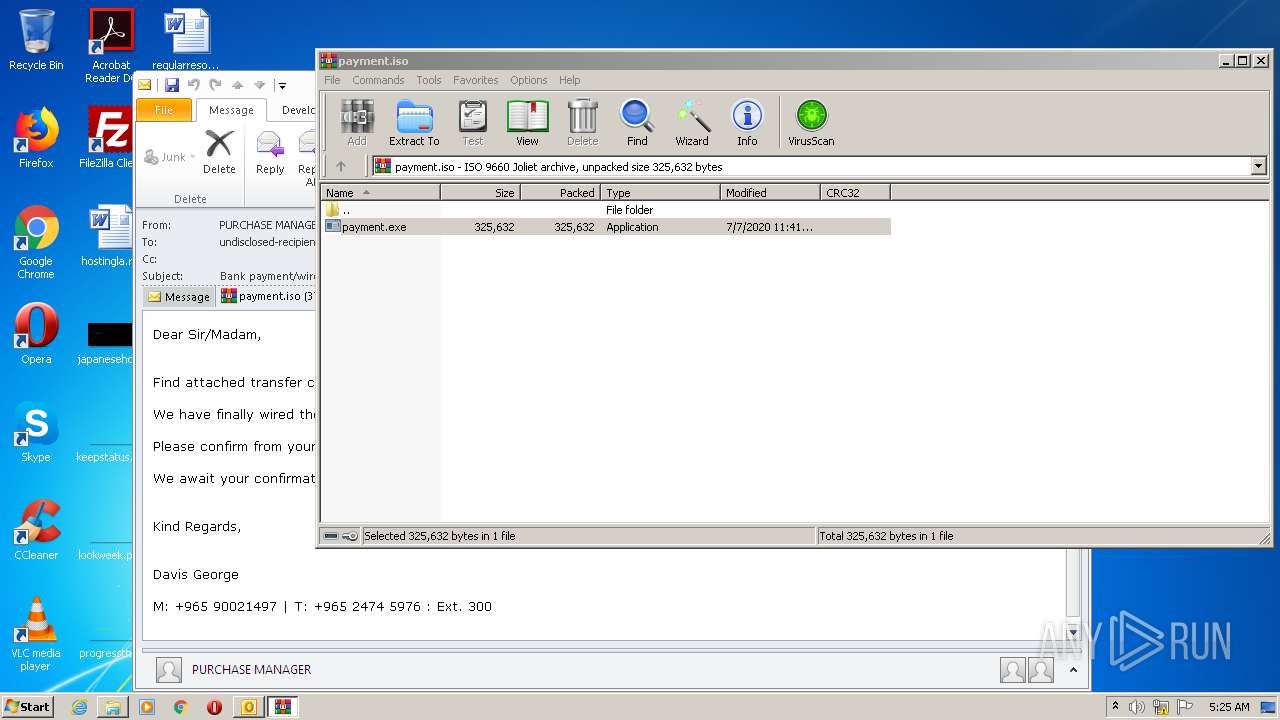
| 1944 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\W2EX6RKV\payment.iso" | C:\Program Files\WinRAR\WinRAR.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2244 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa1944.14393\payment.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa1944.14393\payment.exe | payment.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3540 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4060 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa1944.14393\payment.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa1944.14393\payment.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
2 345
Read events
1 769
Write events
557
Delete events
19
Modification events
| (PID) Process: | (1488) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1488) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (1488) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (1488) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (1488) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (1488) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (1488) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (1488) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (1488) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (1488) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
2
Suspicious files
0
Text files
29
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1488 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRD386.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1488 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\tmpD5C9.tmp | — | |
MD5:— | SHA256:— | |||
| 1488 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\W2EX6RKV\payment (2).iso\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 2244 | payment.exe | C:\Users\admin\AppData\Roaming\F63AAA\A71D80.lck | — | |
MD5:— | SHA256:— | |||
| 1488 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 1488 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 1488 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\mapisvc.inf | text | |
MD5:48DD6CAE43CE26B992C35799FCD76898 | SHA256:7BFE1F3691E2B4FB4D61FBF5E9F7782FBE49DA1342DBD32201C2CC8E540DBD1A | |||
| 1488 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_RssRule_2_F1625DB961666C4C8AA710B276C6A32A.dat | xml | |
MD5:D8B37ED0410FB241C283F72B76987F18 | SHA256:31E68049F6B7F21511E70CD7F2D95B9CF1354CF54603E8F47C1FC40F40B7A114 | |||
| 1488 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_ContactPrefs_2_87E8F33919DB46438B7D5321567A887A.dat | xml | |
MD5:BBCF400BD7AE536EB03054021D6A6398 | SHA256:383020065C1F31F4FB09F448599A6D5E532C390AF4E5B8AF0771FE17A23222AD | |||
| 1488 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_AvailabilityOptions_2_AE83054A32946A4D84D6D1A79DBC06E6.dat | xml | |
MD5:EEAA832C12F20DE6AAAA9C7B77626E72 | SHA256:C4C9A90F2C961D9EE79CF08FBEE647ED7DE0202288E876C7BAAD00F4CA29CA16 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
4
DNS requests
2
Threats
19
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1488 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
2244 | payment.exe | POST | 404 | 194.180.224.87:80 | http://mecharnise.ir/ea1/fre.php | unknown | text | 15 b | malicious |
2244 | payment.exe | POST | 404 | 194.180.224.87:80 | http://mecharnise.ir/ea1/fre.php | unknown | text | 15 b | malicious |
2244 | payment.exe | POST | 404 | 194.180.224.87:80 | http://mecharnise.ir/ea1/fre.php | unknown | binary | 23 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1488 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
2244 | payment.exe | 194.180.224.87:80 | mecharnise.ir | — | — | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
mecharnise.ir |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2244 | payment.exe | A Network Trojan was detected | ET TROJAN LokiBot User-Agent (Charon/Inferno) |
2244 | payment.exe | A Network Trojan was detected | ET TROJAN LokiBot Checkin |
2244 | payment.exe | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M1 |
2244 | payment.exe | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M2 |
2244 | payment.exe | A Network Trojan was detected | MALWARE [PTsecurity] Loki Bot Check-in M2 |
2244 | payment.exe | A Network Trojan was detected | ET TROJAN LokiBot User-Agent (Charon/Inferno) |
2244 | payment.exe | A Network Trojan was detected | ET TROJAN LokiBot Checkin |
2244 | payment.exe | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M1 |
2244 | payment.exe | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M2 |
2244 | payment.exe | A Network Trojan was detected | MALWARE [PTsecurity] Loki Bot Check-in M2 |
3 ETPRO signatures available at the full report