| File name: | wireframe.exe |
| Full analysis: | https://app.any.run/tasks/c9e2ee7c-751c-46e7-a046-4decd7ed1b9c |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
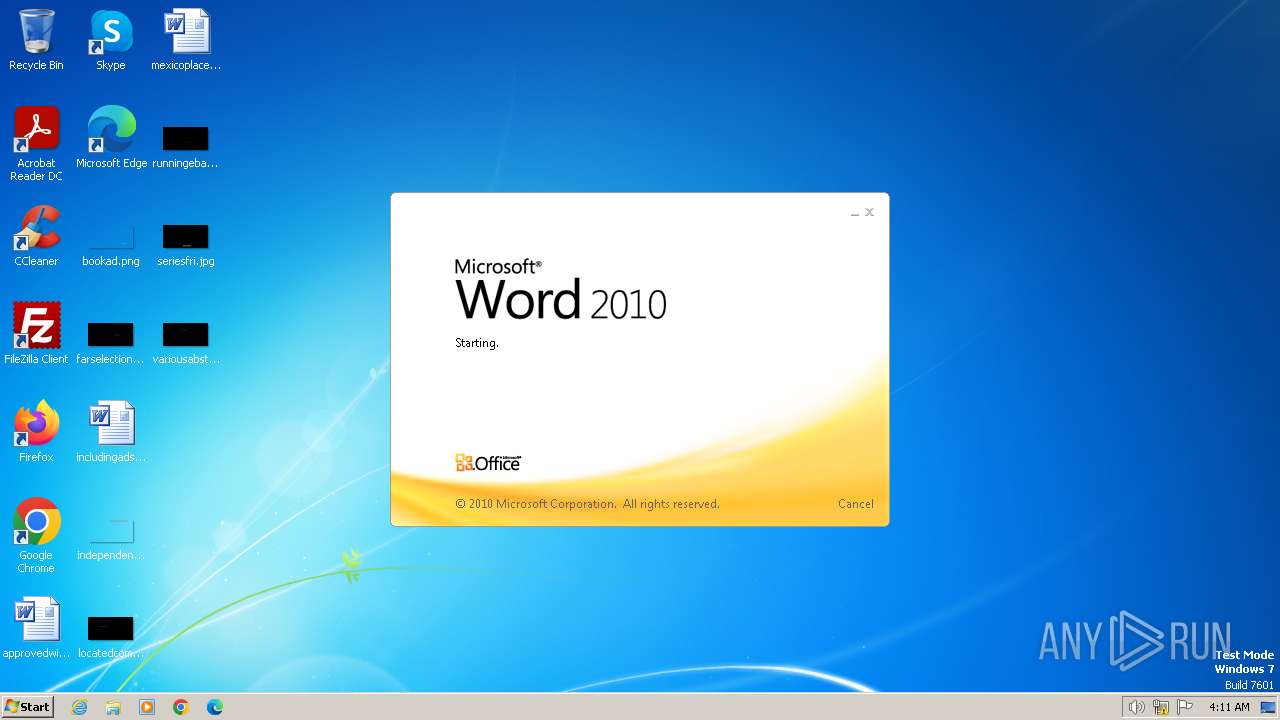
| Analysis date: | October 01, 2024, 03:11:15 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 2FD03624E271EC70349CE56FB30F563B |
| SHA1: | 7ED2E38DECB996A7F695BF7B80E0C102F4D01F10 |
| SHA256: | 9C83A89EA0E56D5AF9AA37D2DABED20B2412DB8C9694A13128EA173A73557487 |
| SSDEEP: | 1536:DCWYHwZU0YIv/bzdHIn2UpeOGBLPH73bTXSAgLni3Rimmx:DCWYHwZU0YI1HI8b73bTfBOx |
MALICIOUS
ASYNCRAT has been detected (MUTEX)
- wireframe.exe (PID: 1652)
- NvidiaGPU.exe (PID: 1964)
Changes the autorun value in the registry
- wireframe.exe (PID: 1652)
ASYNCRAT has been detected (YARA)
- NvidiaGPU.exe (PID: 1964)
SUSPICIOUS
Executing commands from a ".bat" file
- wireframe.exe (PID: 1652)
Executable content was dropped or overwritten
- wireframe.exe (PID: 1652)
The executable file from the user directory is run by the CMD process
- NvidiaGPU.exe (PID: 1964)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 2844)
Starts CMD.EXE for commands execution
- wireframe.exe (PID: 1652)
INFO
Reads the computer name
- wireframe.exe (PID: 1652)
- NvidiaGPU.exe (PID: 1964)
- wmpnscfg.exe (PID: 3700)
Checks supported languages
- wireframe.exe (PID: 1652)
- NvidiaGPU.exe (PID: 1964)
- wmpnscfg.exe (PID: 3700)
Reads the machine GUID from the registry
- wireframe.exe (PID: 1652)
- NvidiaGPU.exe (PID: 1964)
Create files in a temporary directory
- wireframe.exe (PID: 1652)
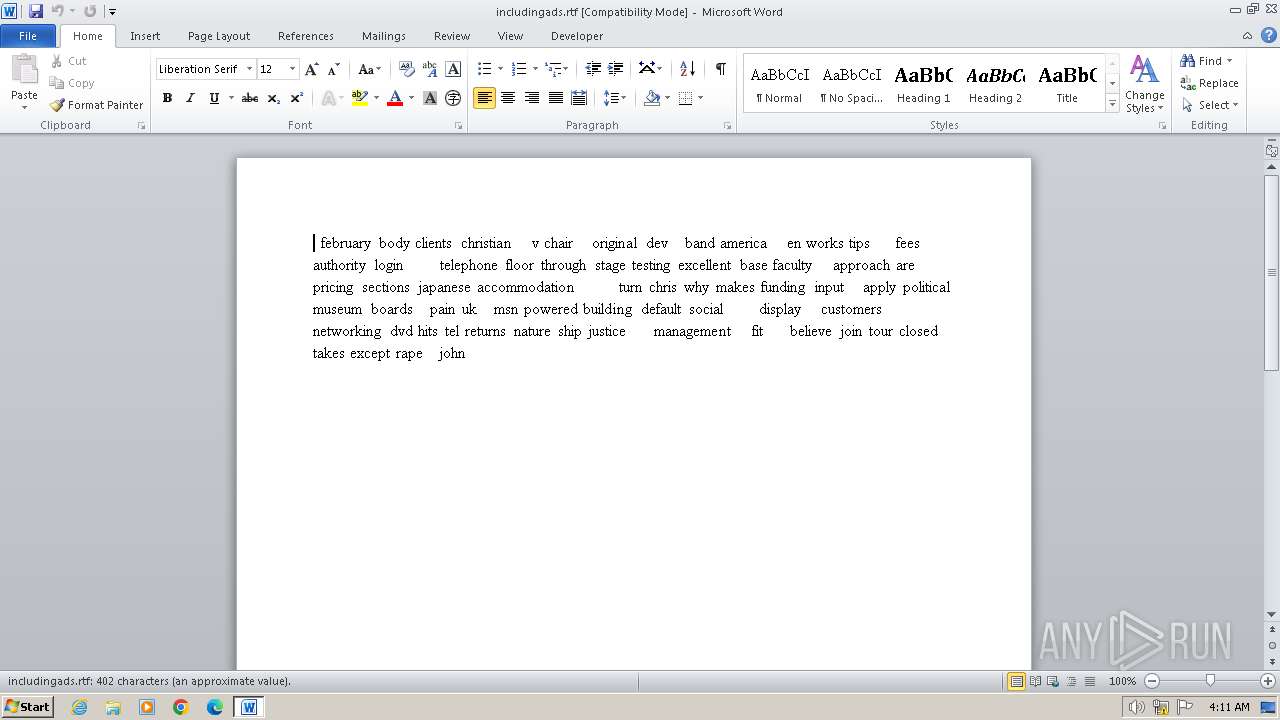
Manual execution by a user
- wmpnscfg.exe (PID: 3700)
- WINWORD.EXE (PID: 1968)
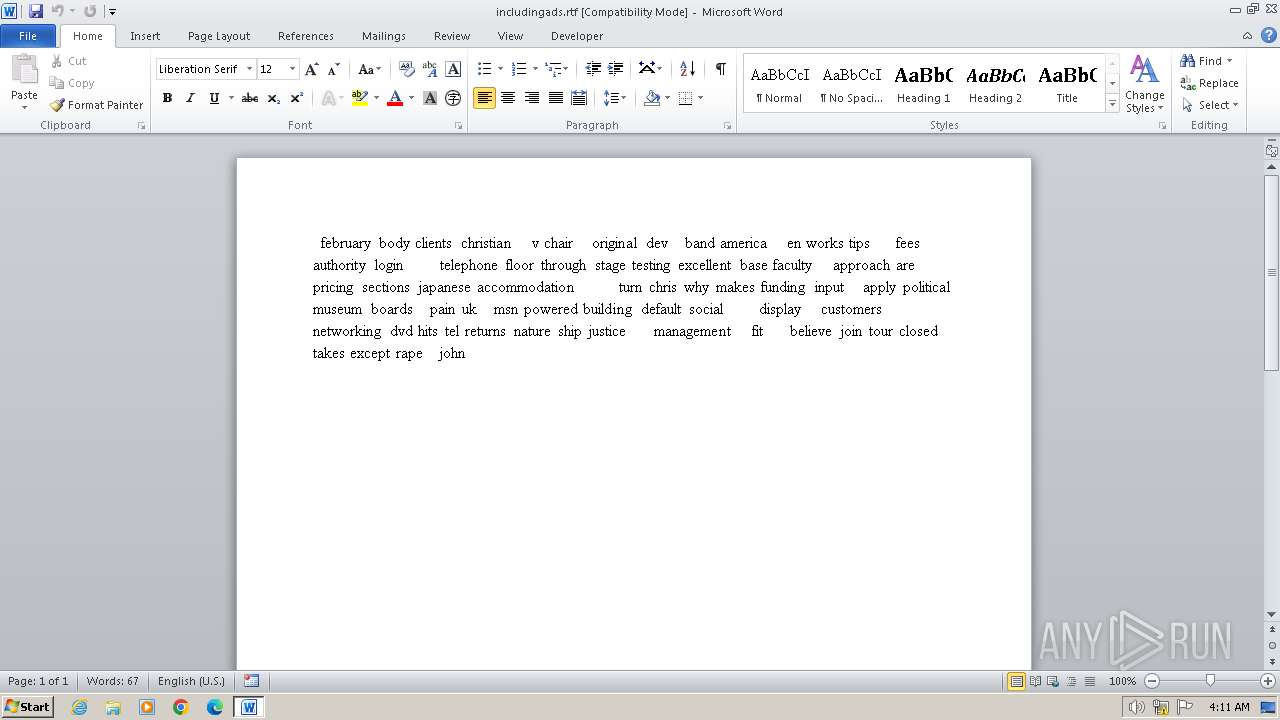
The process uses the downloaded file
- WINWORD.EXE (PID: 1968)
Creates files or folders in the user directory
- wireframe.exe (PID: 1652)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
AsyncRat
(PID) Process(1964) NvidiaGPU.exe
C2 (1)tasteless-minister.auto.playit.gg
Ports (1)41642
Version0.5.7B
BotnetDefault
Options
AutoRuntrue
MutexAsyncMutex_6SI8OkPnk
InstallFolder%AppData%
BSoDfalse
AntiVMfalse
Certificates
Cert1MIIE8jCCAtqgAwIBAgIQAKqeG6Bxfhz4xeRrMfhyCzANBgkqhkiG9w0BAQ0FADAaMRgwFgYDVQQDDA9Bc3luY1JBVCBTZXJ2ZXIwIBcNMjEwOTE3MTgxNjEwWhgPOTk5OTEyMzEyMzU5NTlaMBoxGDAWBgNVBAMMD0FzeW5jUkFUIFNlcnZlcjCCAiIwDQYJKoZIhvcNAQEBBQADggIPADCCAgoCggIBAKpxov4wpRTDDXFrXtYxeVMbvDq2MN3sx/sKRlMSno7E/fa3VHgaQlA9keKXbqfJP/NwgMeCF3Mb...
Server_SignatureFLT3e3sTjL3GhIbKCSByGbU7kf3widkmGPhXmWJNYaMNWQJCm9MnUwISCvGip55ZhmKtFIREttuE7EzQN826UFNitfSuVAFG69nYeLuH789/hWz5rM9+l+MRi9YCo27BeGdULunxI52AYf0ccqa2E8lk0E36kcl6VZdqrooQzWb5XksEFdOVJ42c1PLUe5egjaPnVpVN4wzgS1wc71V6tlc8b8P4GtrRAbs3iuGuSZBg5uHeoI9W06b2lmAEl8a6tQ2xtKP3Wt6vTIMw4Ca+WjYId41XVHfB7f/3VcbXy4AJ...
Keys
AES69165940473d6b1d8eaad32415025aa011f190bada01eb1734ab70839c0bbf3e
Saltbfeb1e56fbcd973bb219022430a57843003d5644d21e62b9d4f180e7e6c33941
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (56.7) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (21.3) |
| .scr | | | Windows screen saver (10.1) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
| .exe | | | Win32 Executable (generic) (3.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:05:10 05:24:51+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 43008 |
| InitializedDataSize: | 2560 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xc77e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | - |
| FileVersion: | 1.0.0.0 |
| InternalName: | Stub.exe |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFileName: | Stub.exe |
| ProductName: | - |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
44
Monitored processes
7
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 748 | C:\Windows\system32\DllHost.exe /Processid:{76D0CB12-7604-4048-B83C-1005C7DDC503} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1652 | "C:\Users\admin\AppData\Local\Temp\wireframe.exe" | C:\Users\admin\AppData\Local\Temp\wireframe.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1964 | "C:\Users\admin\AppData\Roaming\NvidiaGPU.exe" | C:\Users\admin\AppData\Roaming\NvidiaGPU.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Version: 1.0.0.0 Modules
AsyncRat(PID) Process(1964) NvidiaGPU.exe C2 (1)tasteless-minister.auto.playit.gg Ports (1)41642 Version0.5.7B BotnetDefault Options AutoRuntrue MutexAsyncMutex_6SI8OkPnk InstallFolder%AppData% BSoDfalse AntiVMfalse Certificates Cert1MIIE8jCCAtqgAwIBAgIQAKqeG6Bxfhz4xeRrMfhyCzANBgkqhkiG9w0BAQ0FADAaMRgwFgYDVQQDDA9Bc3luY1JBVCBTZXJ2ZXIwIBcNMjEwOTE3MTgxNjEwWhgPOTk5OTEyMzEyMzU5NTlaMBoxGDAWBgNVBAMMD0FzeW5jUkFUIFNlcnZlcjCCAiIwDQYJKoZIhvcNAQEBBQADggIPADCCAgoCggIBAKpxov4wpRTDDXFrXtYxeVMbvDq2MN3sx/sKRlMSno7E/fa3VHgaQlA9keKXbqfJP/NwgMeCF3Mb... Server_SignatureFLT3e3sTjL3GhIbKCSByGbU7kf3widkmGPhXmWJNYaMNWQJCm9MnUwISCvGip55ZhmKtFIREttuE7EzQN826UFNitfSuVAFG69nYeLuH789/hWz5rM9+l+MRi9YCo27BeGdULunxI52AYf0ccqa2E8lk0E36kcl6VZdqrooQzWb5XksEFdOVJ42c1PLUe5egjaPnVpVN4wzgS1wc71V6tlc8b8P4GtrRAbs3iuGuSZBg5uHeoI9W06b2lmAEl8a6tQ2xtKP3Wt6vTIMw4Ca+WjYId41XVHfB7f/3VcbXy4AJ... Keys AES69165940473d6b1d8eaad32415025aa011f190bada01eb1734ab70839c0bbf3e Saltbfeb1e56fbcd973bb219022430a57843003d5644d21e62b9d4f180e7e6c33941 | |||||||||||||||
| 1968 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\includingads.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2844 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\tmpD432.tmp.bat"" | C:\Windows\System32\cmd.exe | — | wireframe.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3684 | timeout 3 | C:\Windows\System32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3700 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
4 248
Read events
3 741
Write events
193
Delete events
314
Modification events
| (PID) Process: | (1652) wireframe.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1652) wireframe.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | NvidiaGPU |
Value: "C:\Users\admin\AppData\Roaming\NvidiaGPU.exe" | |||
| (PID) Process: | (1964) NvidiaGPU.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (748) dllhost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: DllHost.exe | |||
| (PID) Process: | (748) dllhost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows Photo Viewer\Viewer |
| Operation: | write | Name: | MainWndPos |
Value: 6000000034000000A00400008002000000000000 | |||
| (PID) Process: | (1968) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | z1- |
Value: 7A312D00B0070000010000000000000000000000 | |||
| (PID) Process: | (1968) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1968) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (1968) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (1968) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
Executable files
2
Suspicious files
6
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1968 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR35DA.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1968 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | binary | |
MD5:661C794043B7247D438B6A4854AE64F8 | SHA256:A2E2CF59EC7EE2F7483DE1141796091D3ADF024266BC6E36C3D6C72F6074EC0E | |||
| 1968 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:6FE0DFAE7E3A4ABD1D7C8C0FA50BC9AC | SHA256:4D0C8EED2AD3ADC9DB8D7CEAE2C4177A5186CB4179232BF2F1C7809B7D75D8FE | |||
| 1968 | WINWORD.EXE | C:\Users\admin\Desktop\~$cludingads.rtf | binary | |
MD5:20BD95524950BD6FD7726096402D9468 | SHA256:D5C9113600EF4780B02505A919068710AE8D7A2A9780E153AF185CFC57E315A4 | |||
| 1652 | wireframe.exe | C:\Users\admin\AppData\Roaming\NvidiaGPU.exe | executable | |
MD5:2FD03624E271EC70349CE56FB30F563B | SHA256:9C83A89EA0E56D5AF9AA37D2DABED20B2412DB8C9694A13128EA173A73557487 | |||
| 1968 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{FC71B6A4-6776-4D8A-9729-6021111D3DC2}.tmp | binary | |
MD5:C475264E0B7FD409E7375F0F8734144A | SHA256:9DAD122B87CC7C326C984358421E7261C8526A0598642F42605C6052C49C5061 | |||
| 1968 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\includingads.rtf.LNK | binary | |
MD5:00418385854BDAB946284C951186E14C | SHA256:4DD361B5F54EC9521177C2ACEBBFCC94722282819EBD2DB9505CB4C9E22231D9 | |||
| 1652 | wireframe.exe | C:\Users\admin\AppData\Local\Temp\tmpD432.tmp.bat | text | |
MD5:D9620FECC155C4279C805FF6882F08AC | SHA256:5FD192C13AFDCAAB4BBE0F6D20E7C344E55F1A72B578A0741D1C1ED50A586799 | |||
| 1968 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{381F742E-8DFD-4DD6-ACAF-08089B3676A3}.tmp | binary | |
MD5:5D4D94EE7E06BBB0AF9584119797B23A | SHA256:4826C0D860AF884D3343CA6460B0006A7A2CE7DBCCC4D743208585D997CC5FD1 | |||
| 1968 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{6A5AE4C2-D103-4F2E-9F25-9D231E233173}.tmp | binary | |
MD5:FF7B188E41B384A5286418ABB7FF02F2 | SHA256:B957778B37017F624EC5DE1EDED321141FE0A6A7570DF0643EA258D507807318 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
7
DNS requests
2
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | whitelisted |
1060 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
2564 | svchost.exe | 239.255.255.250:3702 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
tasteless-minister.auto.playit.gg |
| malicious |