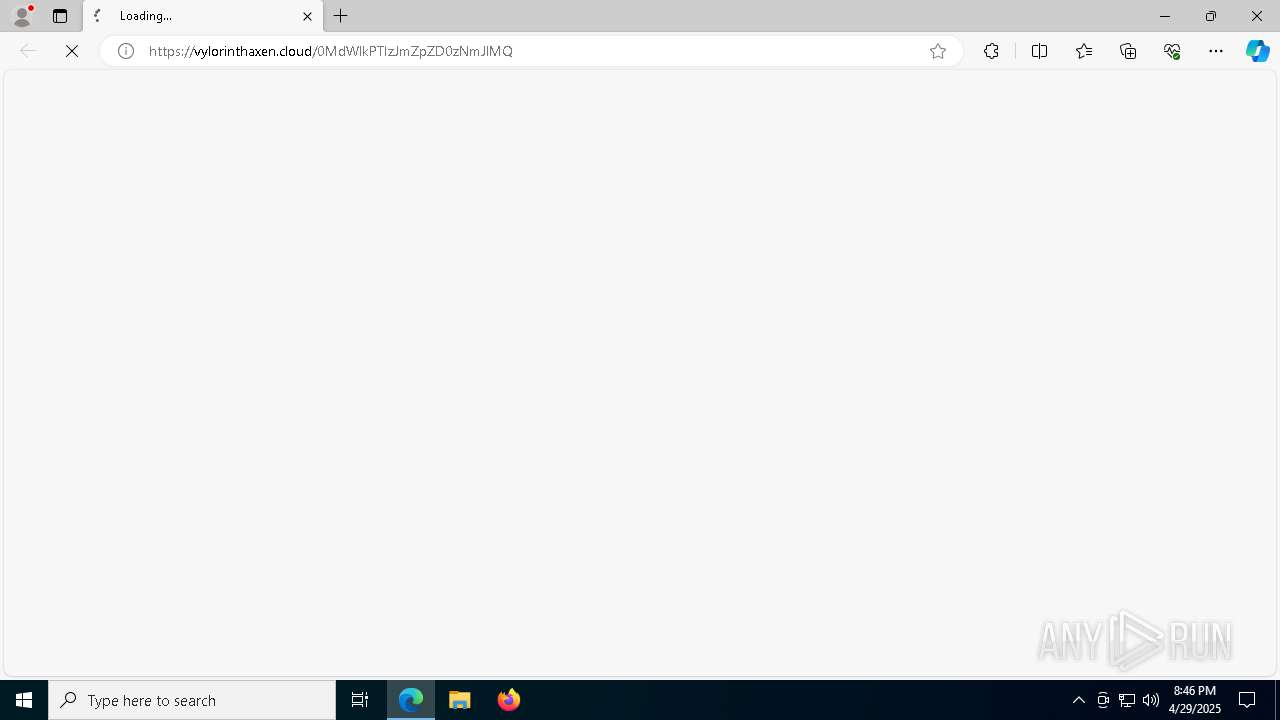
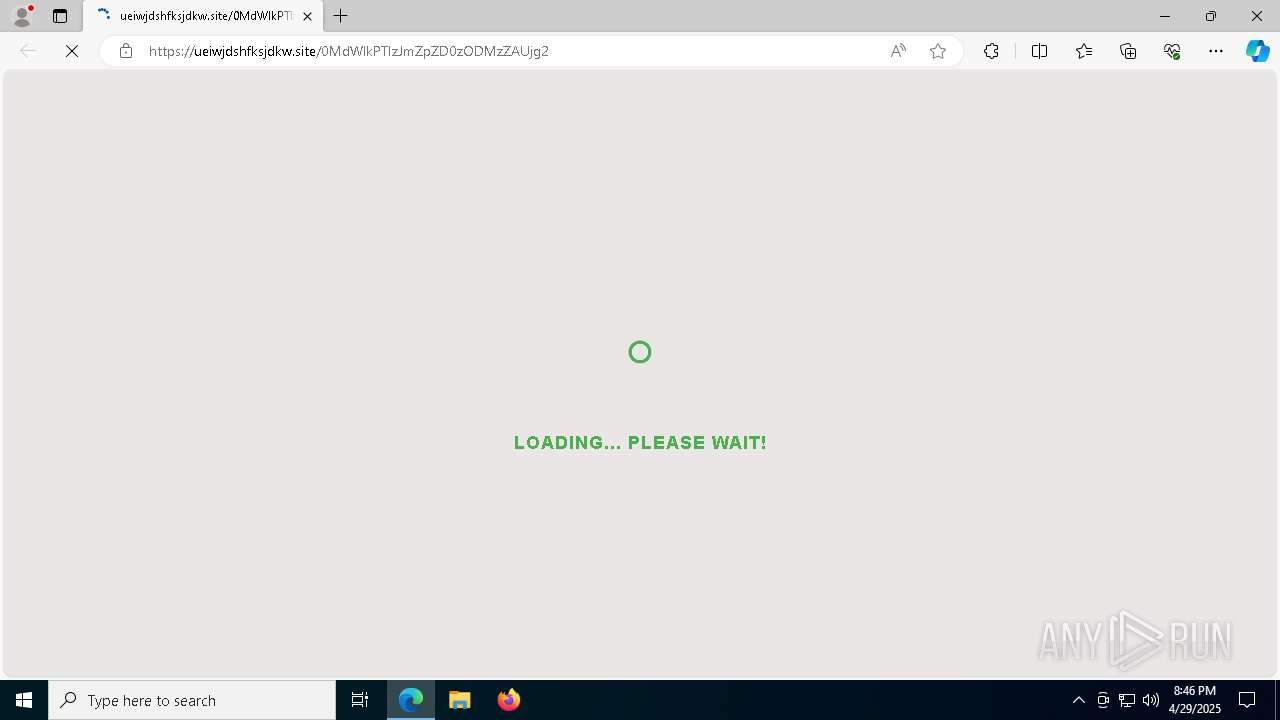
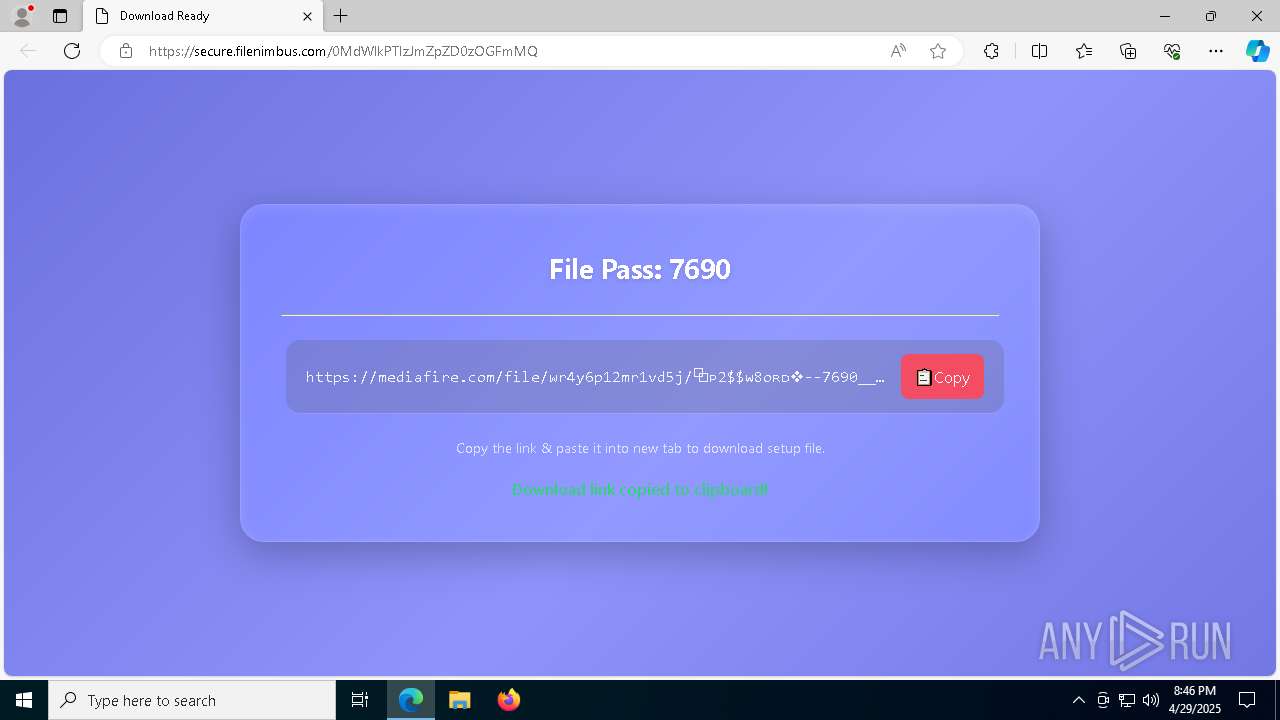
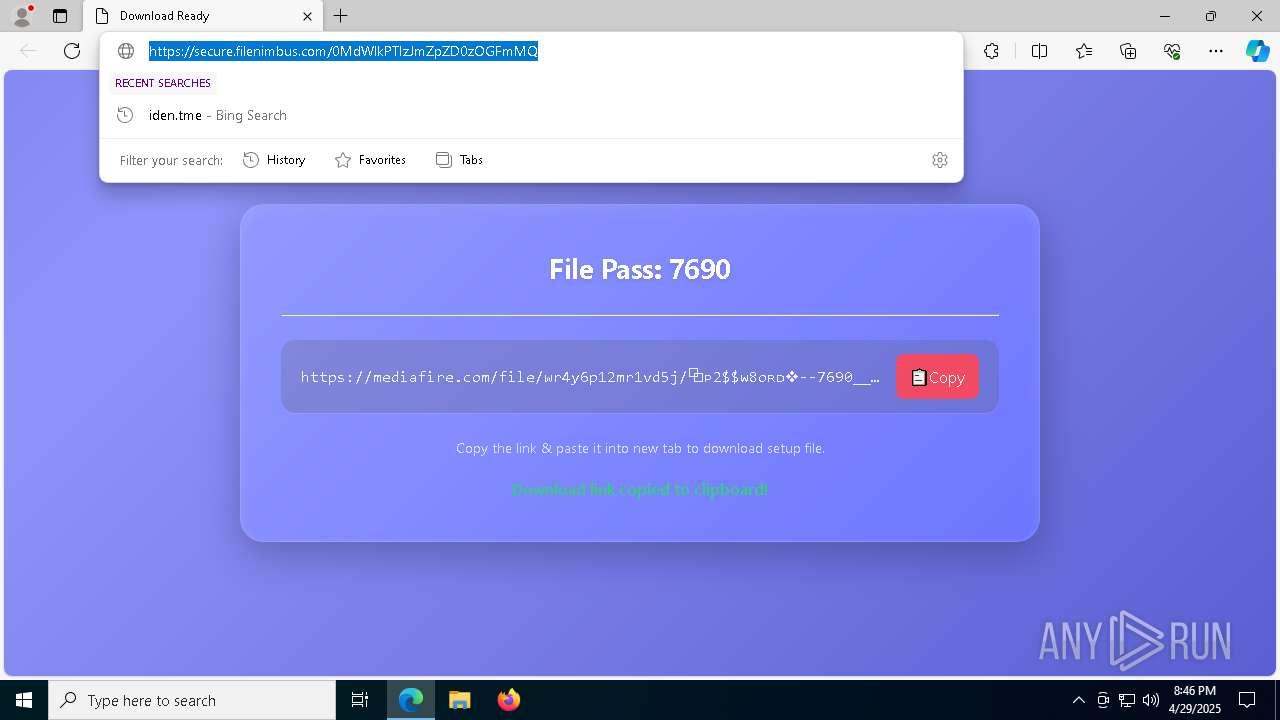
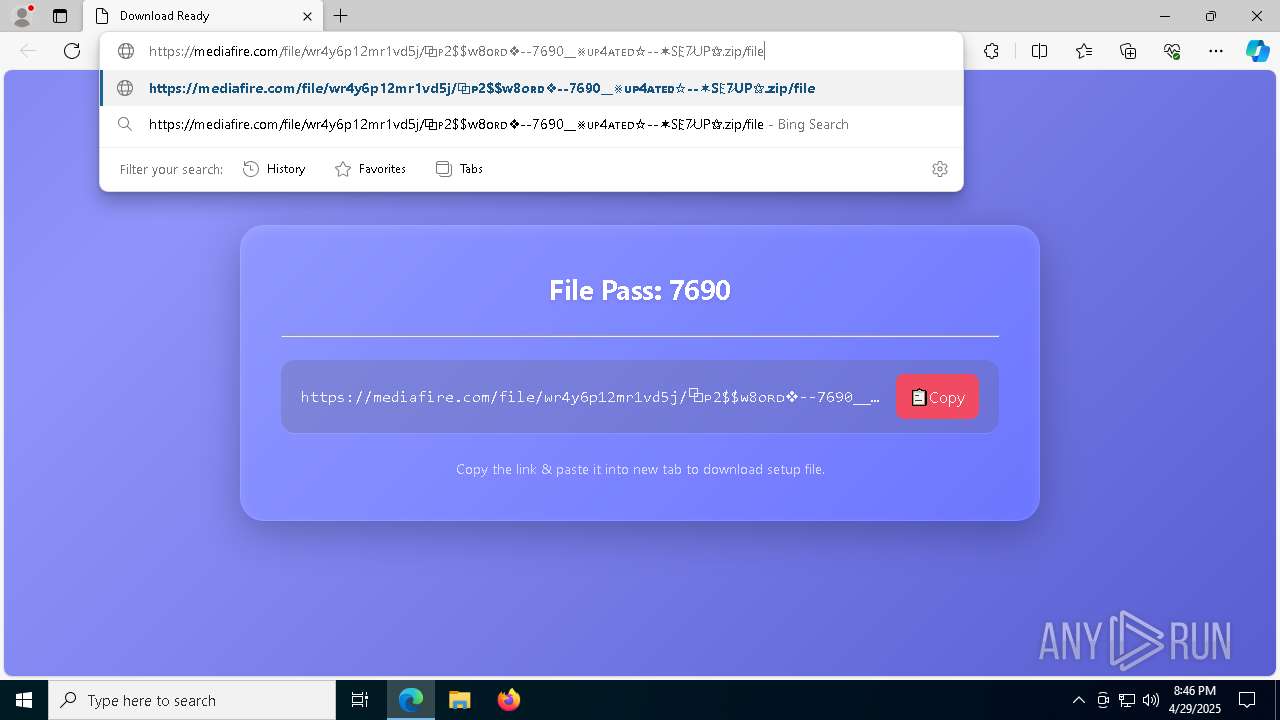
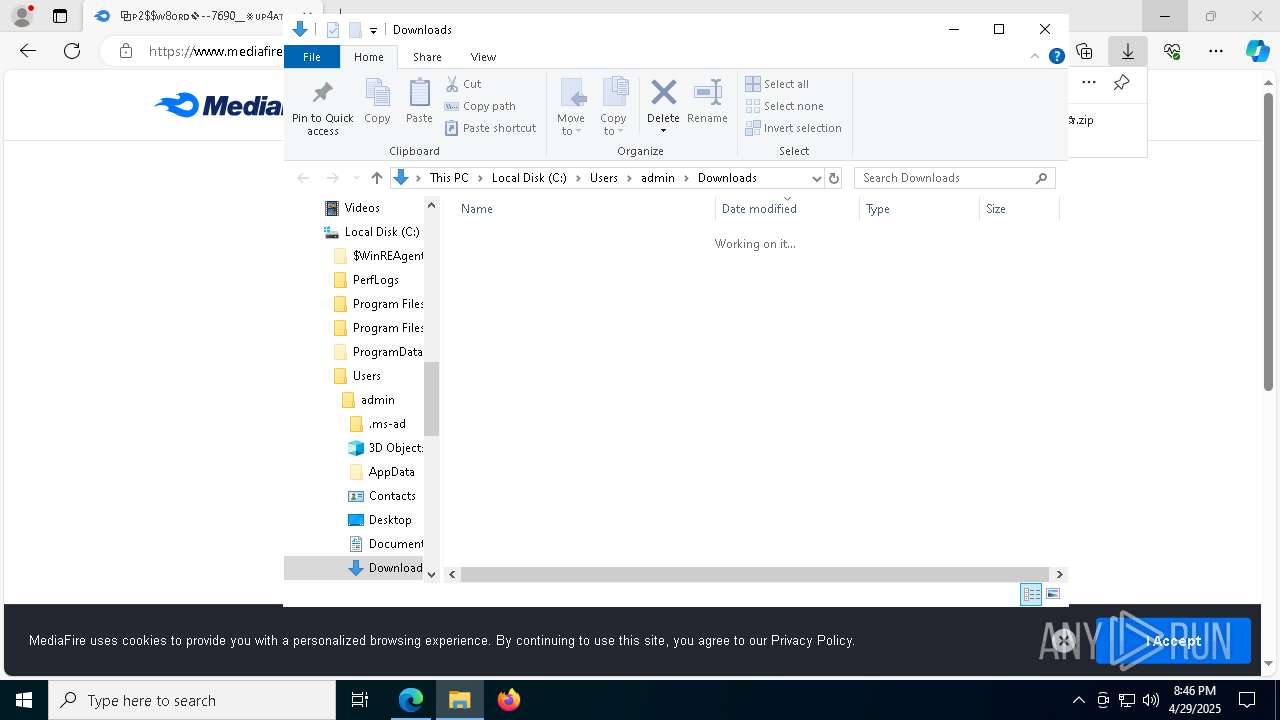
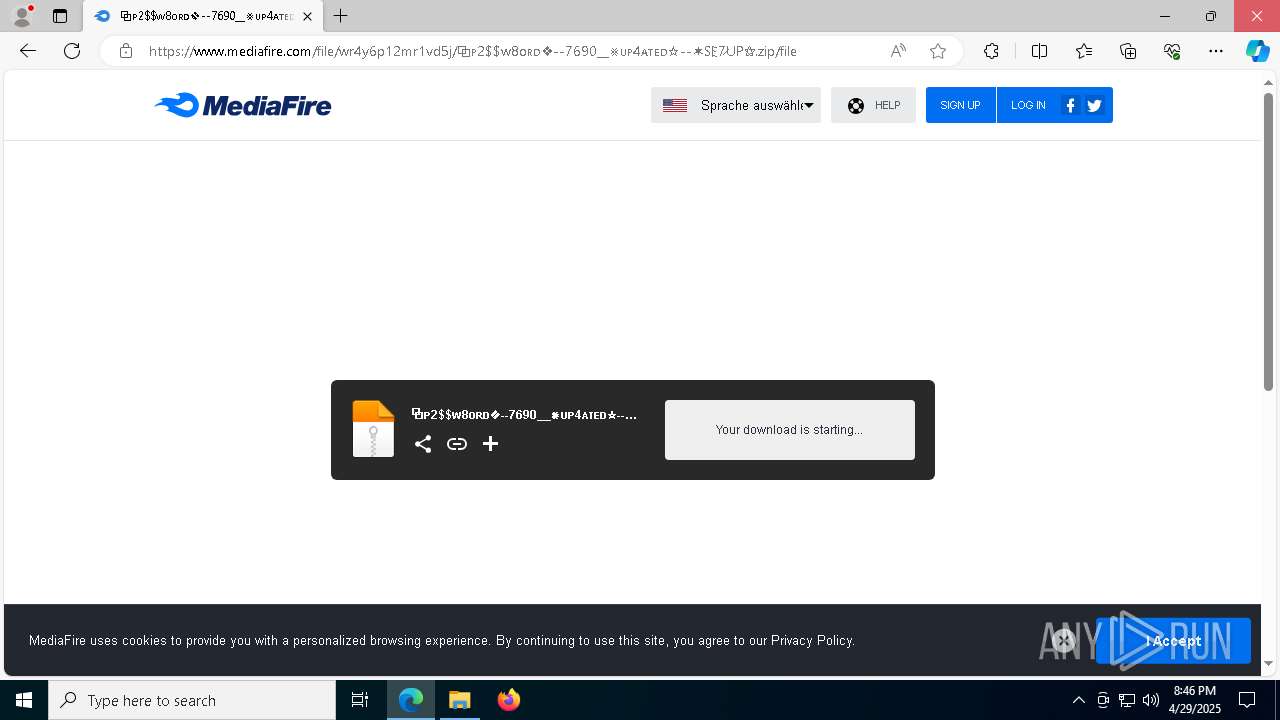
| URL: | https://vylorinthaxen.cloud/0MdWlkPTIzJmZpZD0zNmJlMQ |
| Full analysis: | https://app.any.run/tasks/61247a70-665b-4547-a254-5355a939a57a |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | April 29, 2025, 20:46:09 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 51EBBD9146B6EDDDEE9AD9F3C64C9579 |
| SHA1: | 0D8CB5A613816977FCE4D8FC52E3E503BD9171FD |
| SHA256: | 9BC2A0DC02E35C71829B81DA92EE3E07C8FA8885F0B768A24CB58D166FAC825E |
| SSDEEP: | 3:N82NLrheLBOoLRlon:2WL4LBrRu |
MALICIOUS
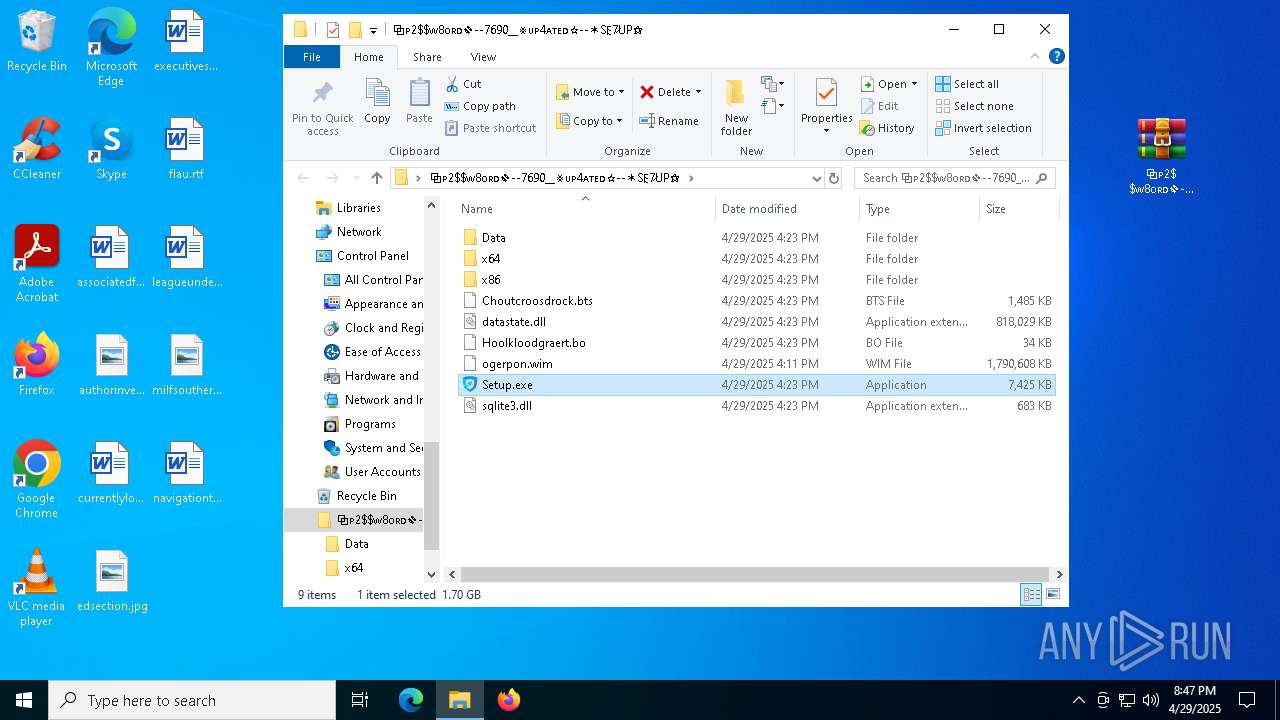
LUMMA has been detected (YARA)
- Pergolesi.com (PID: 8024)
Executing a file with an untrusted certificate
- LCZTW3JME4ZCU7IMZR.exe (PID: 6228)
SUSPICIOUS
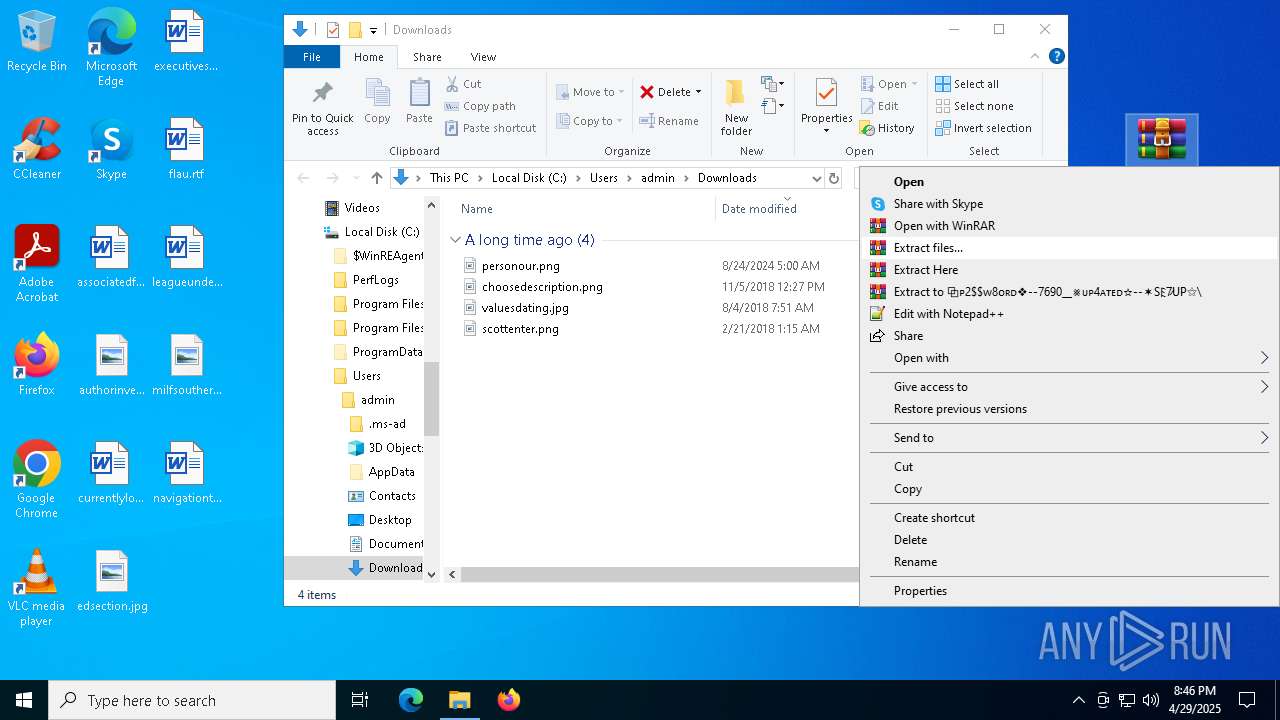
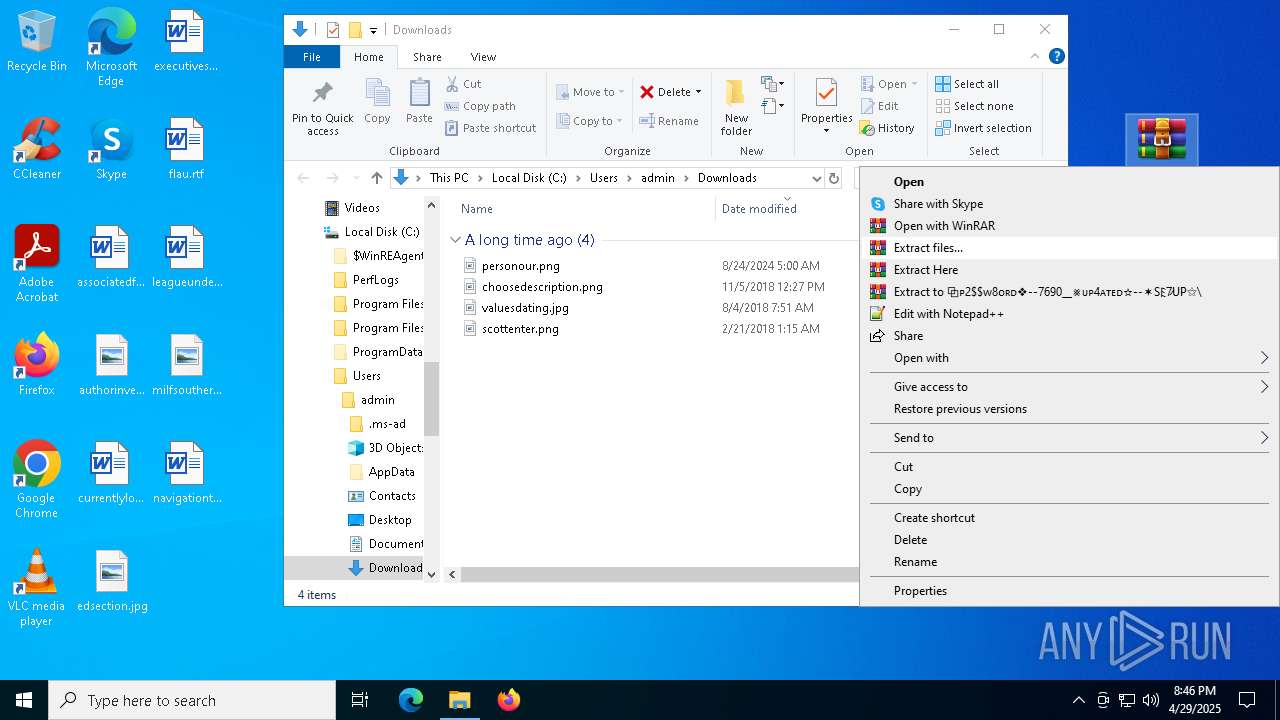
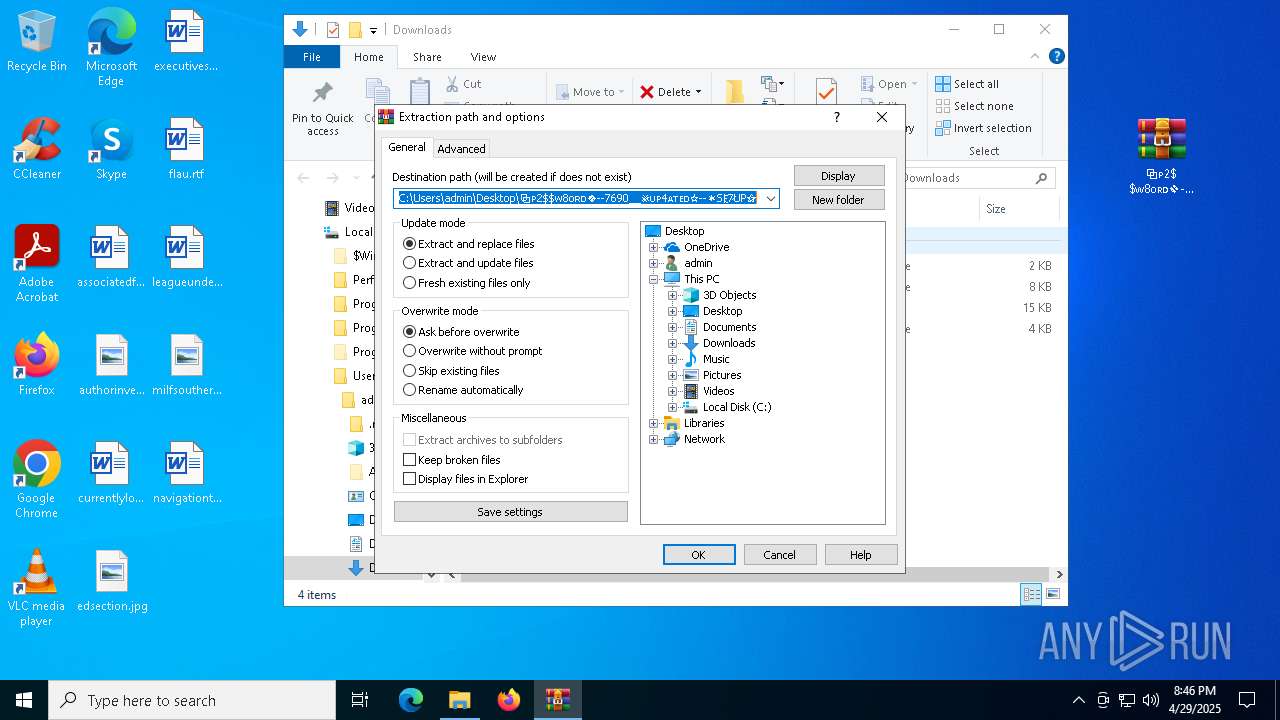
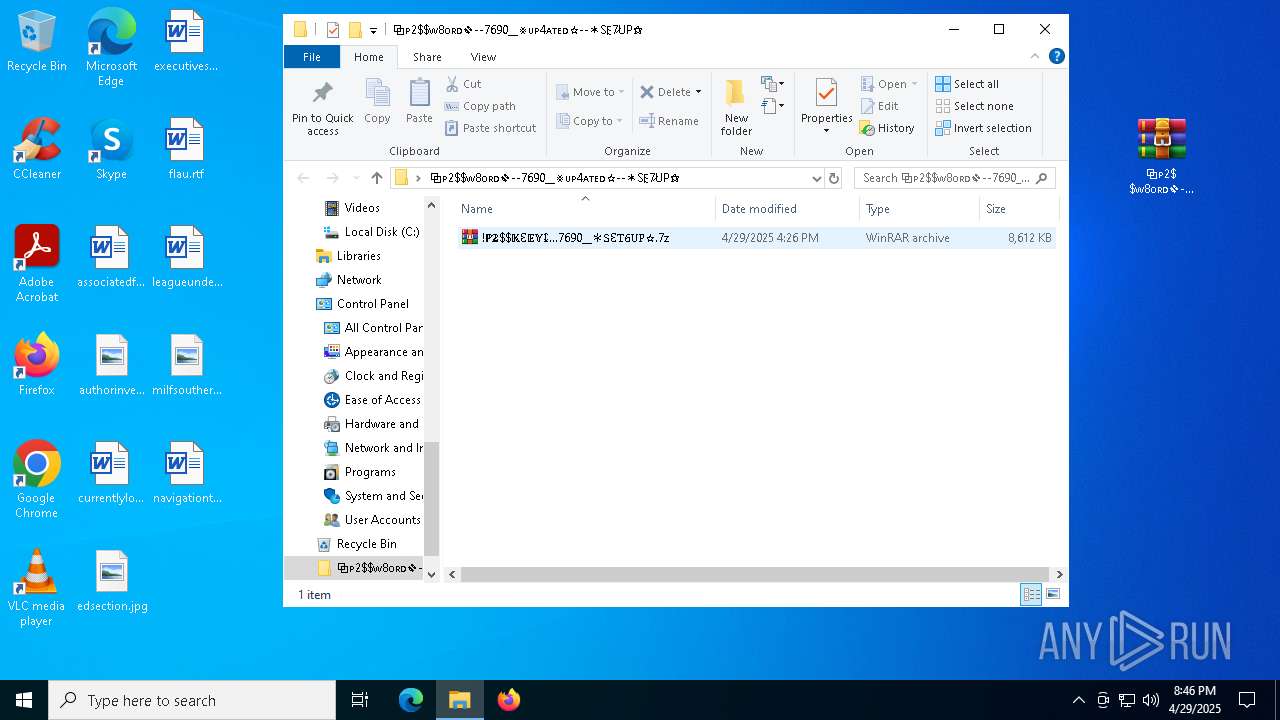
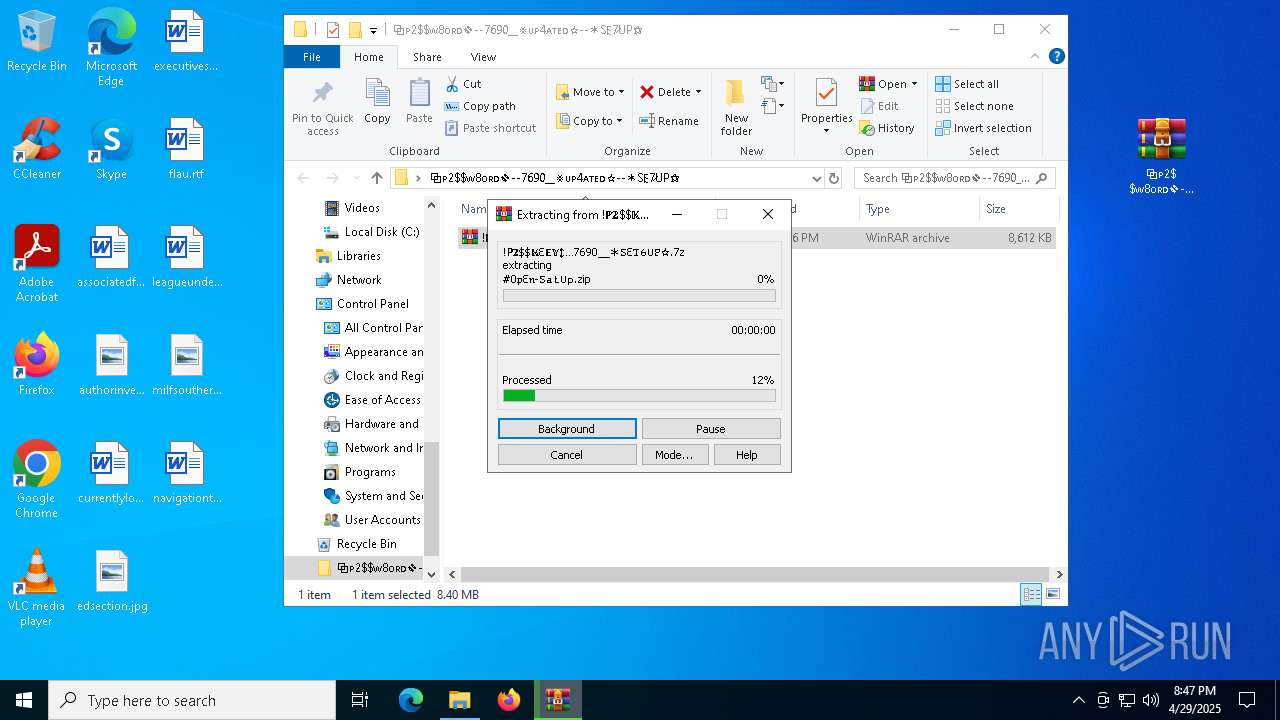
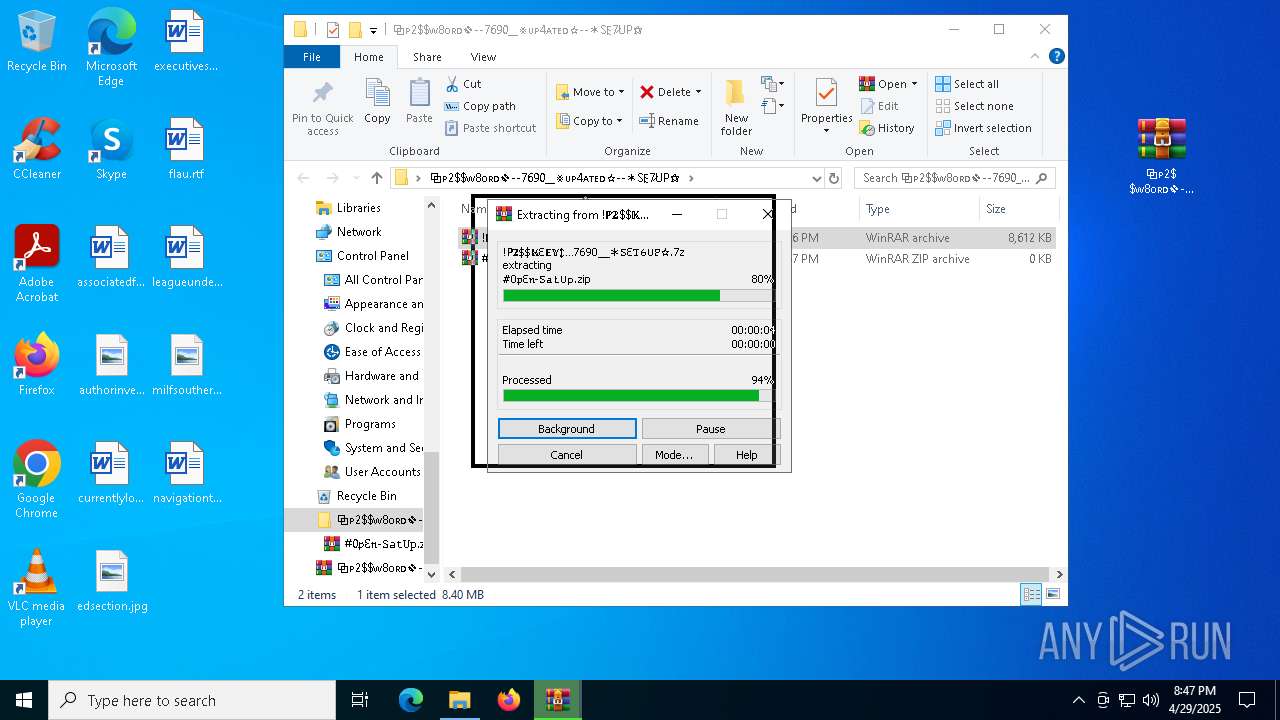
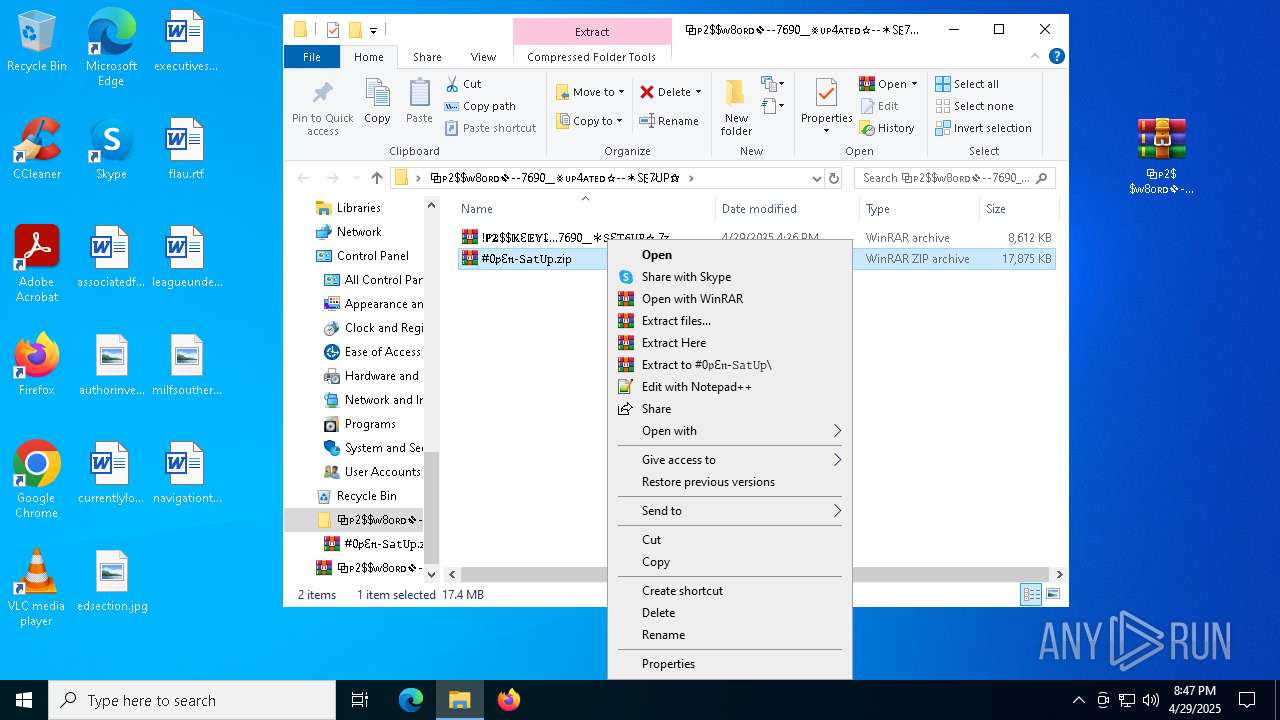
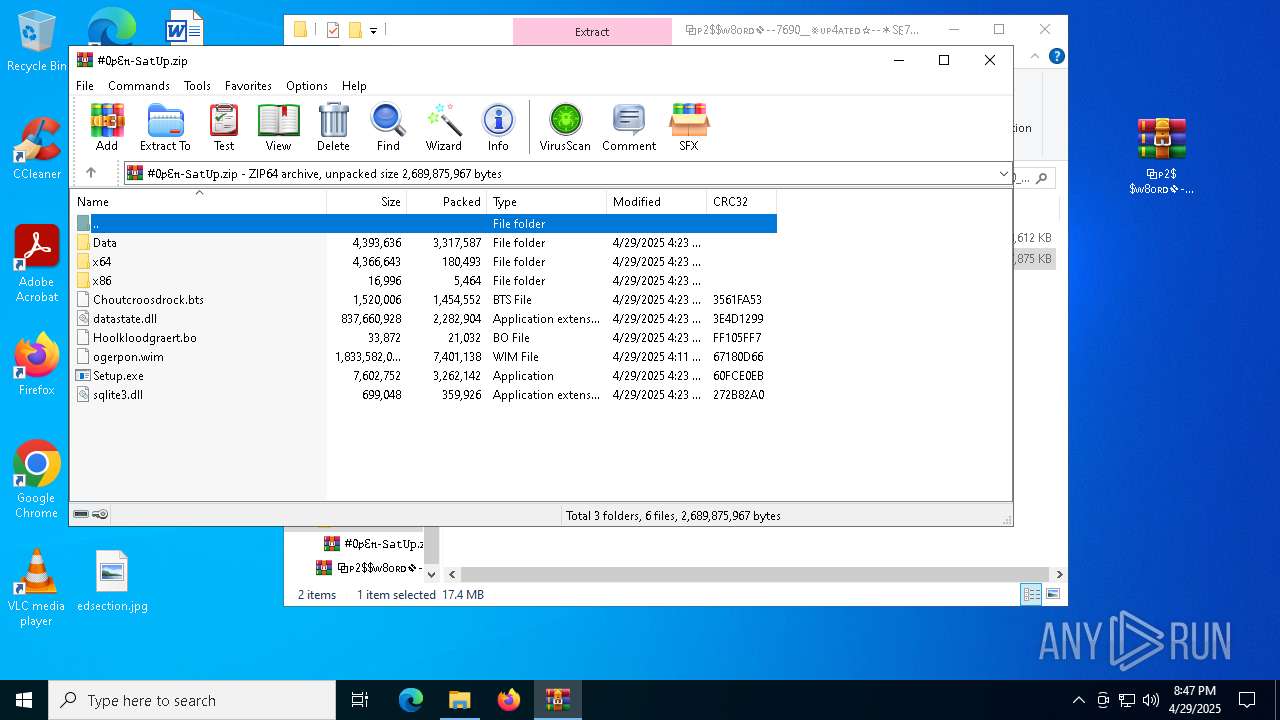
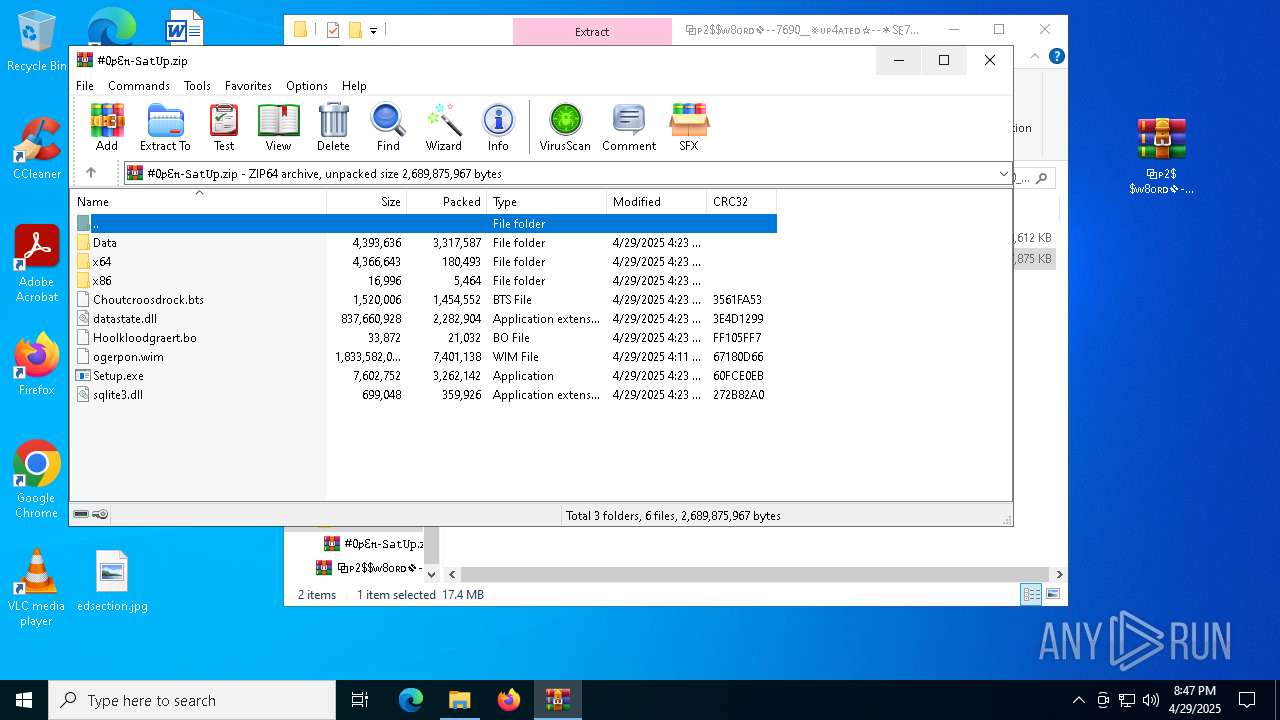
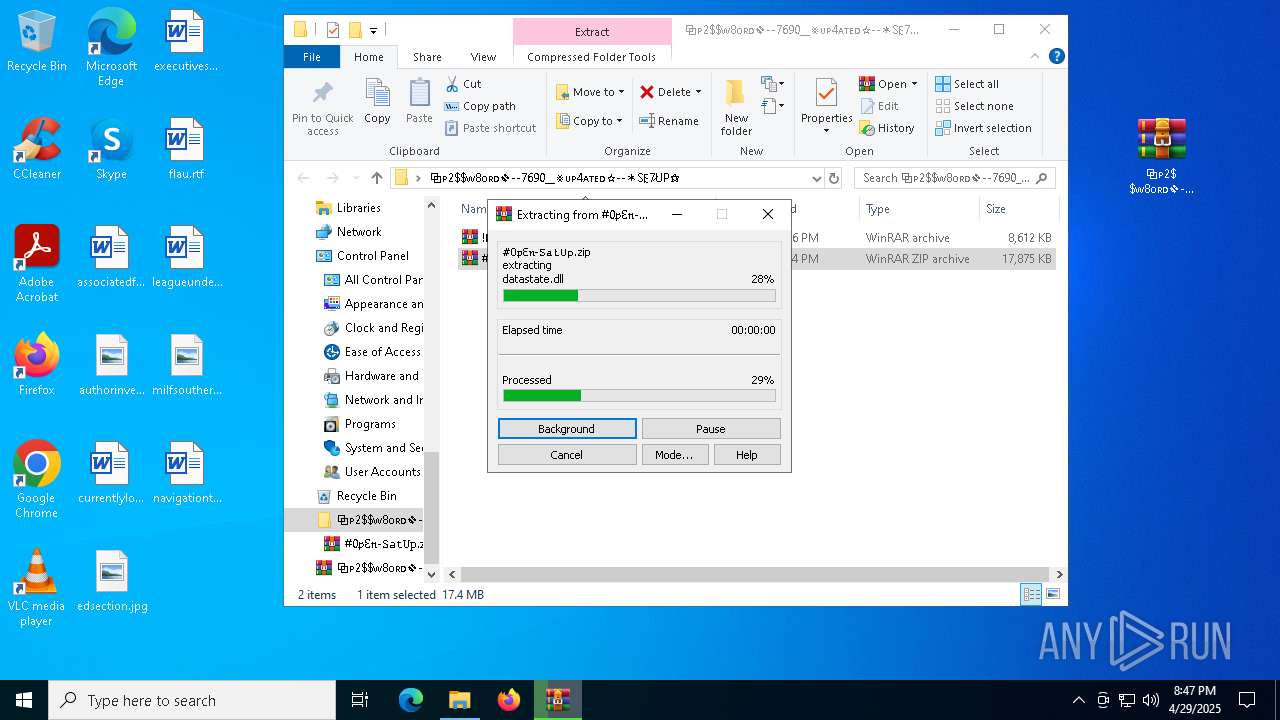
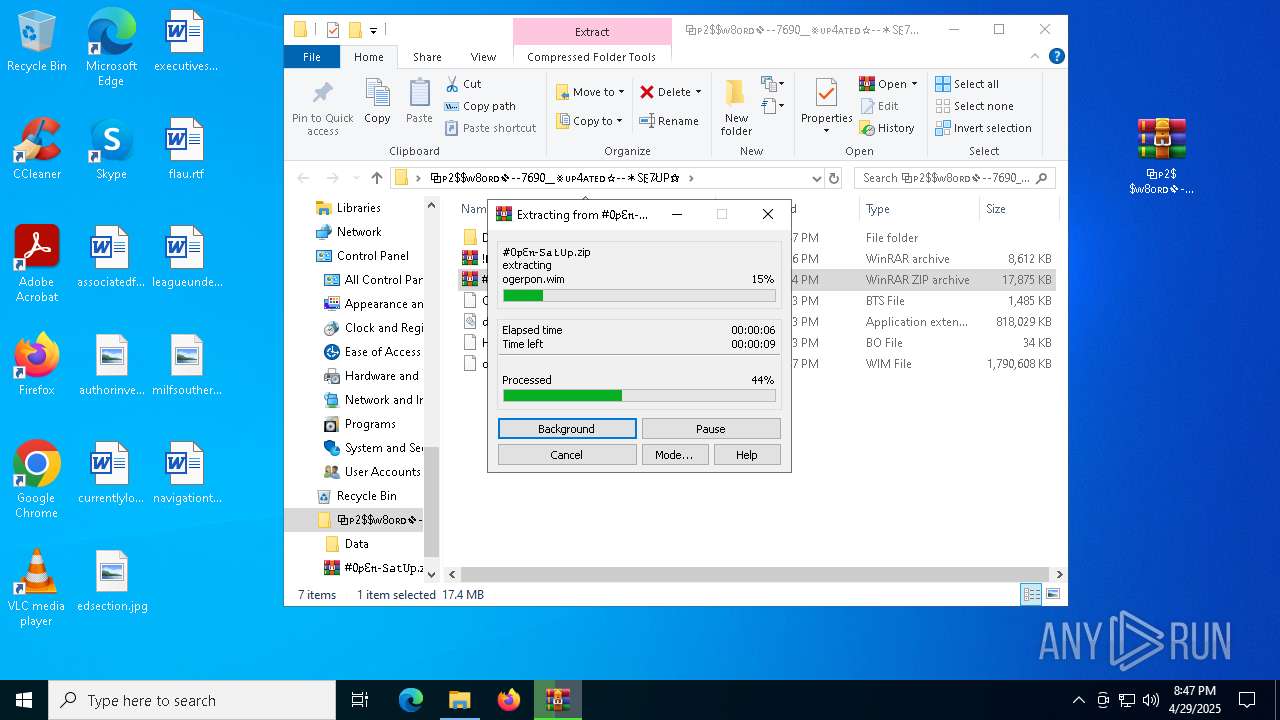
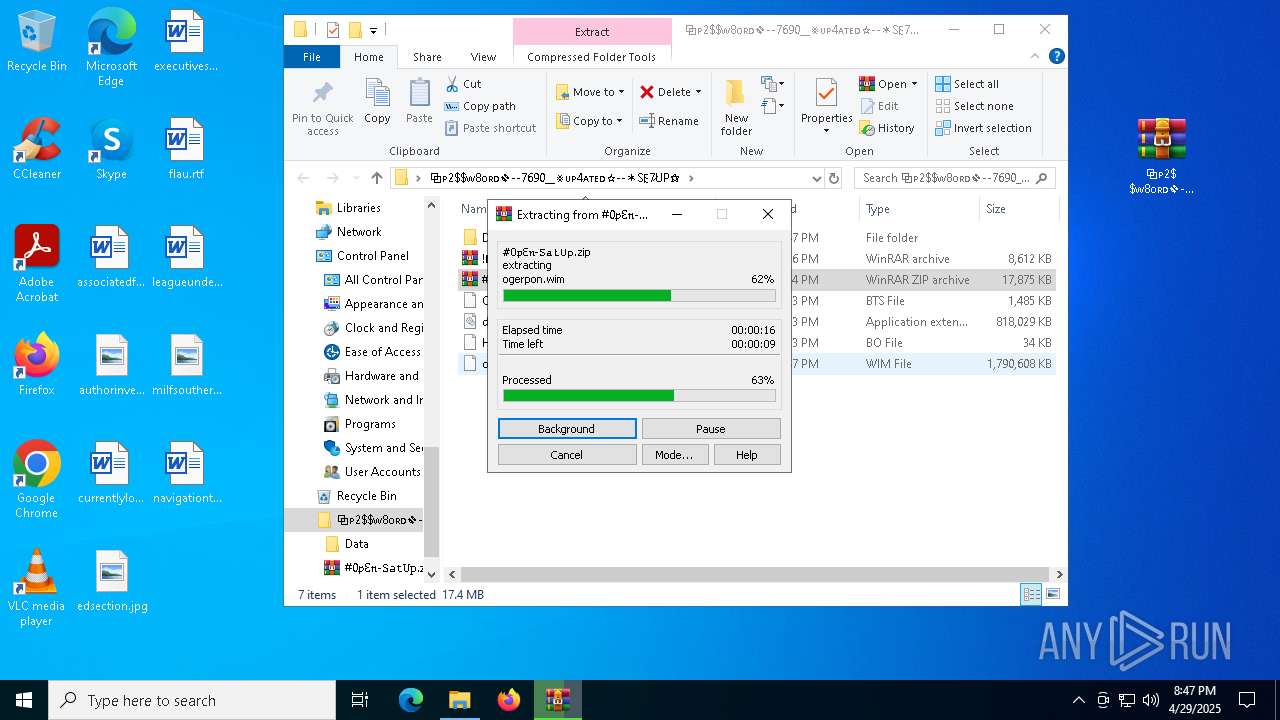
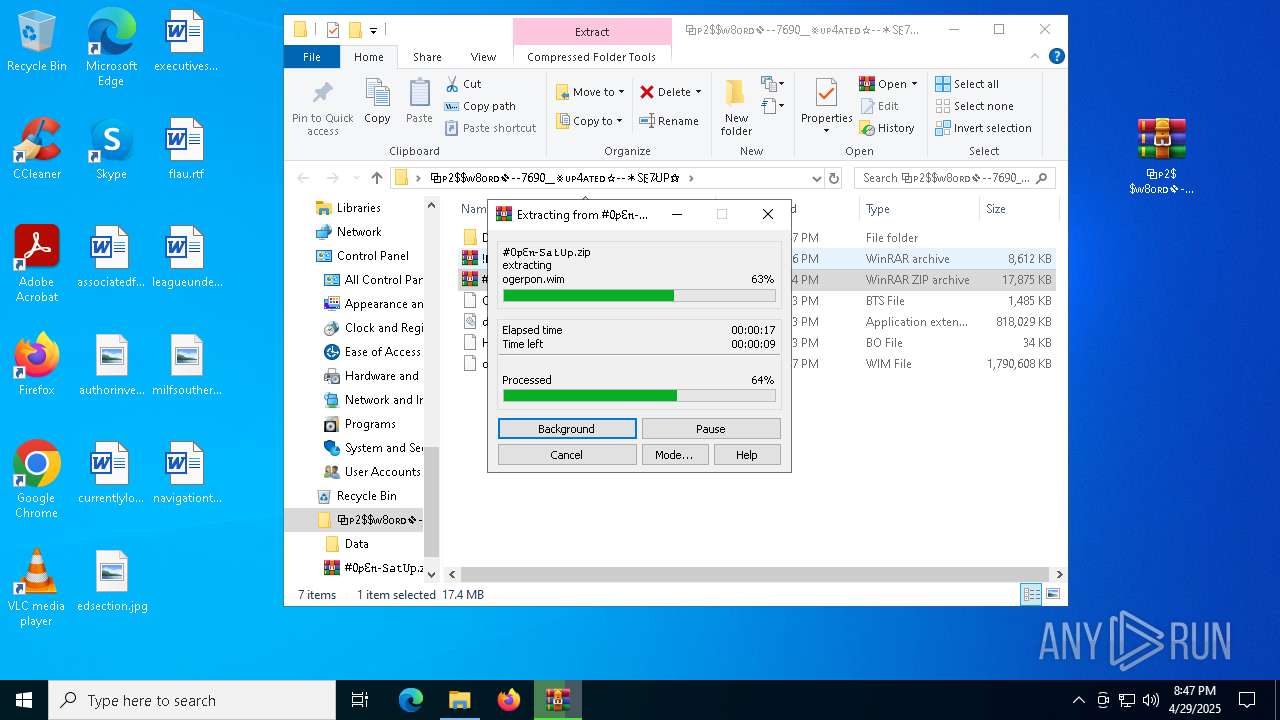
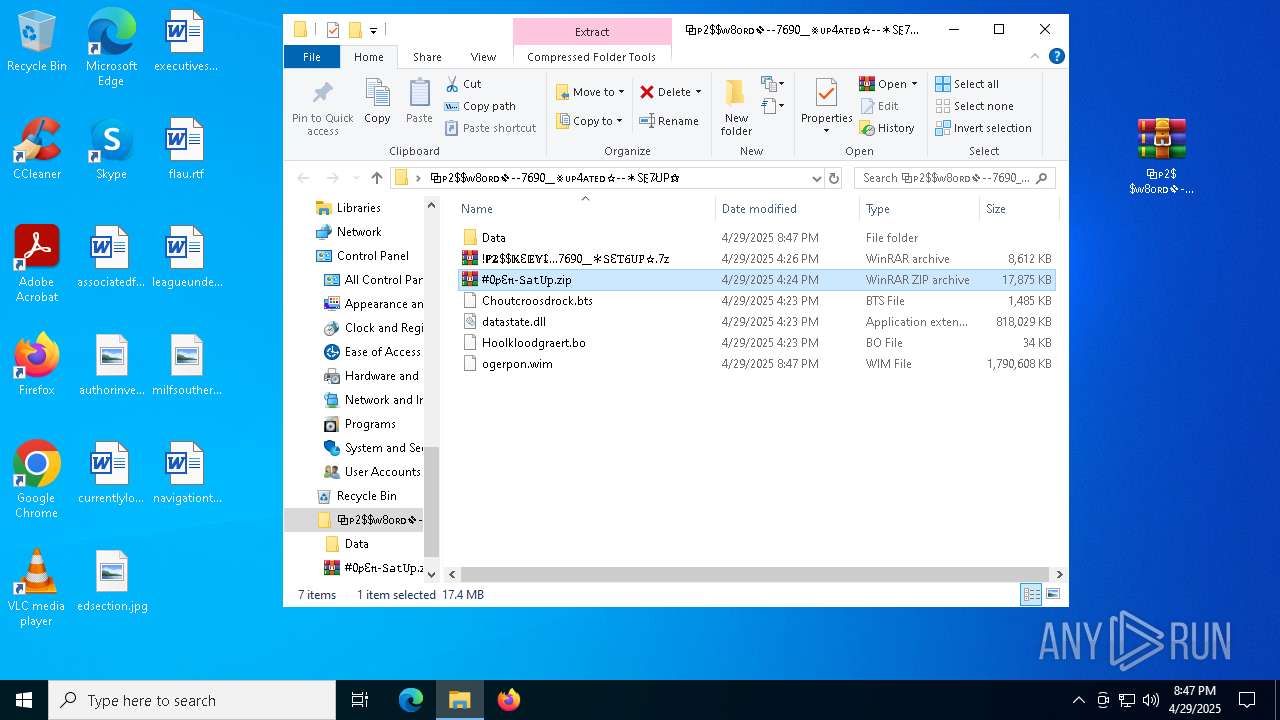
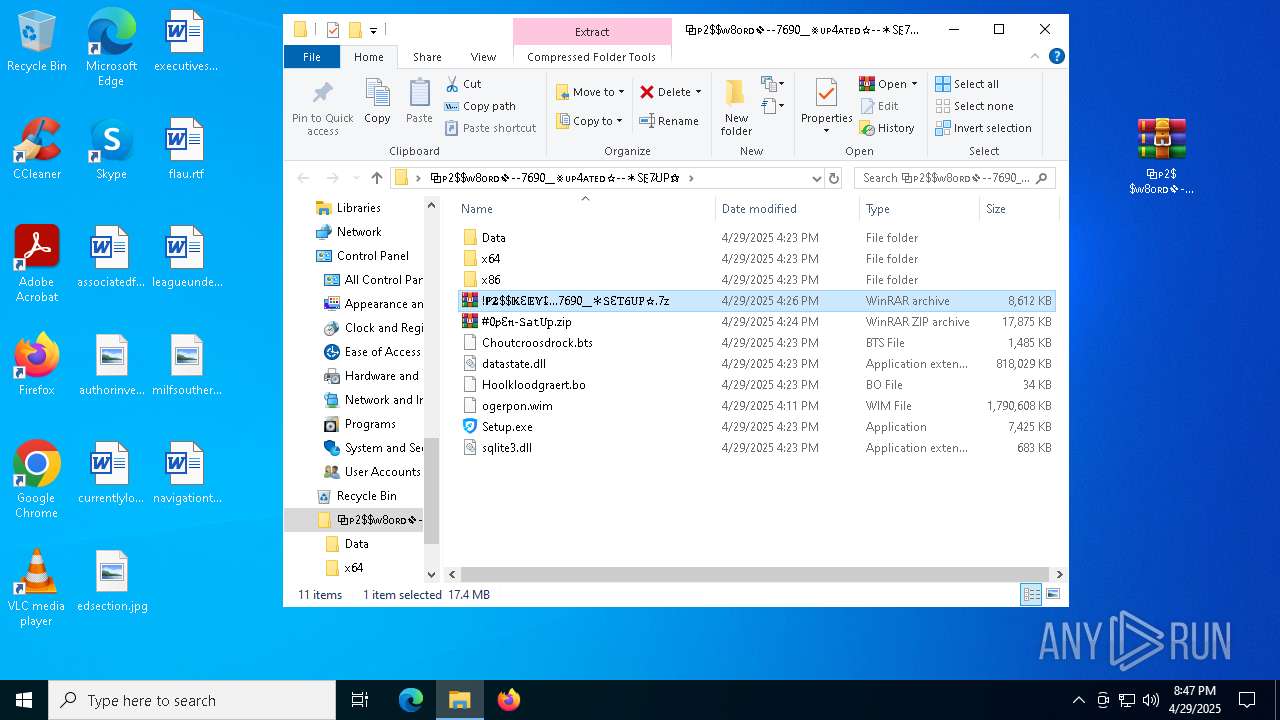
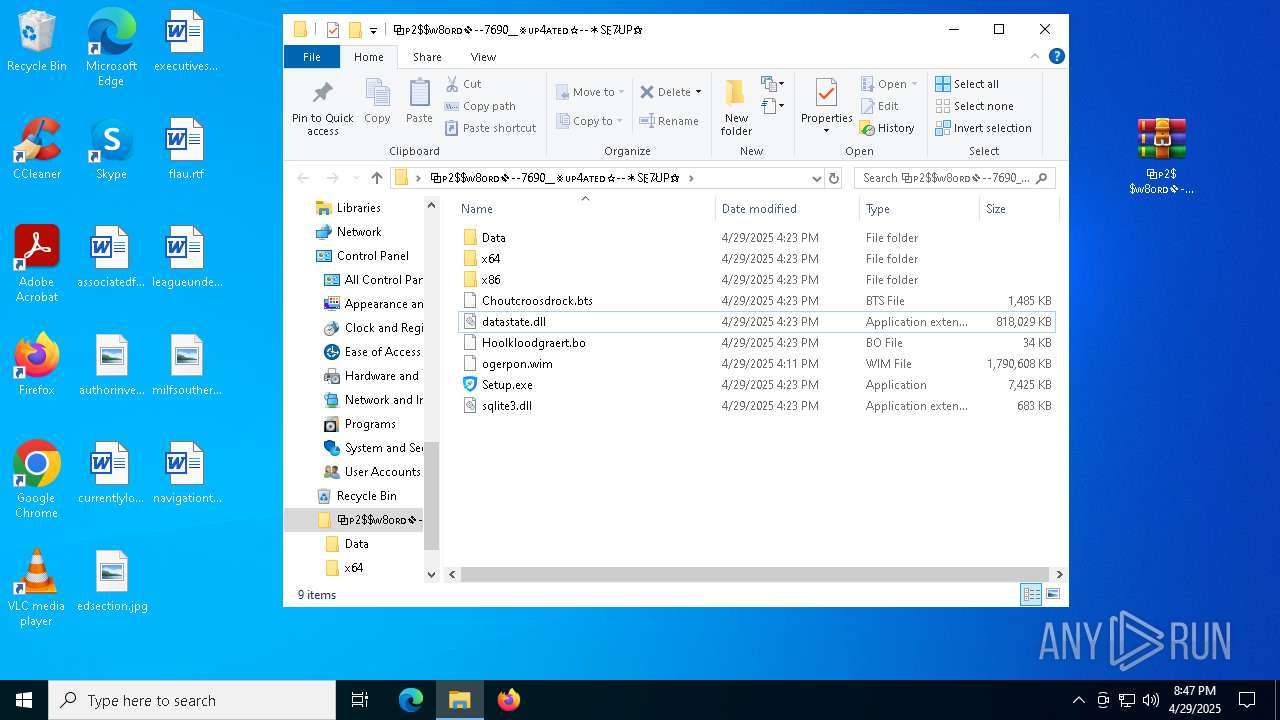
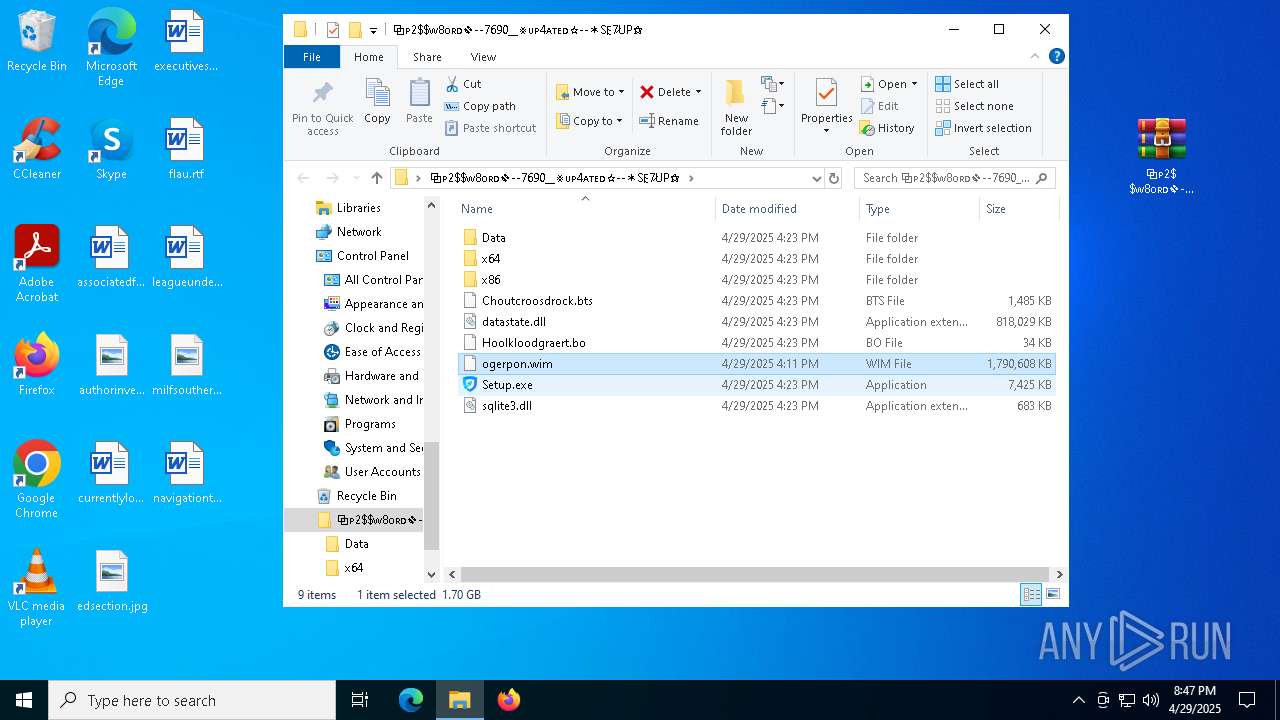
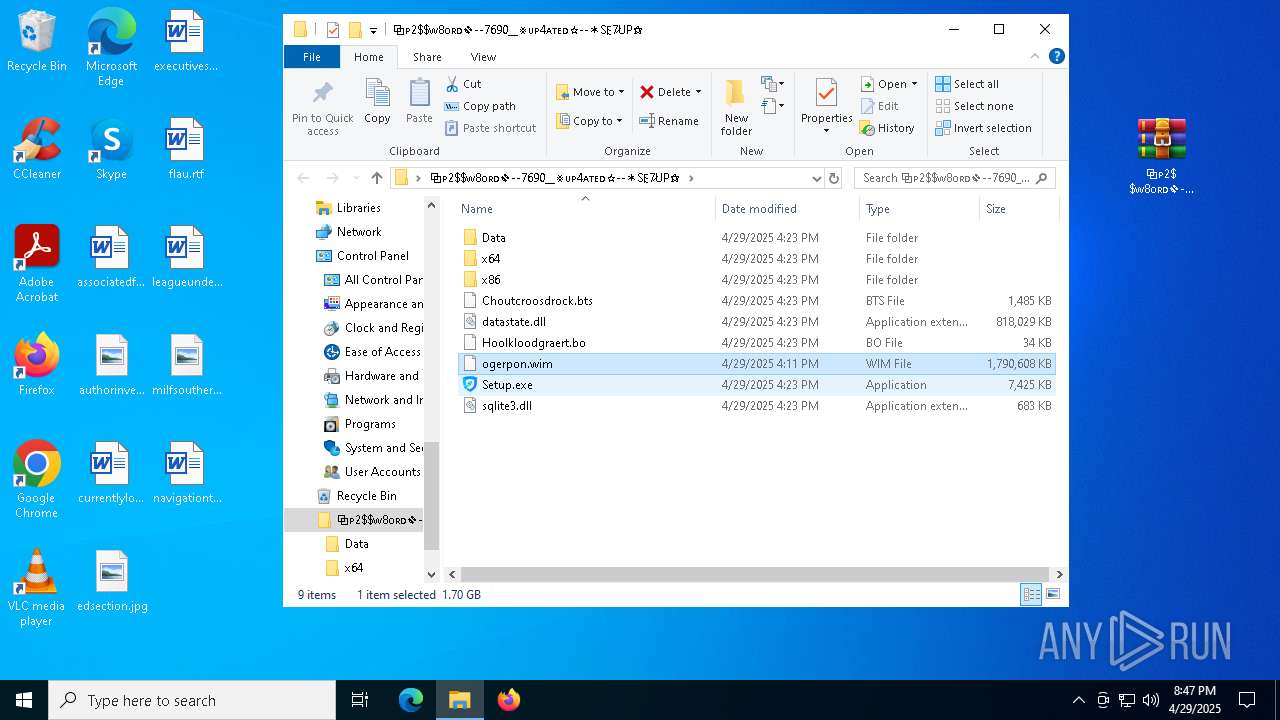
Process drops legitimate windows executable
- WinRAR.exe (PID: 7592)
- Pergolesi.com (PID: 8024)
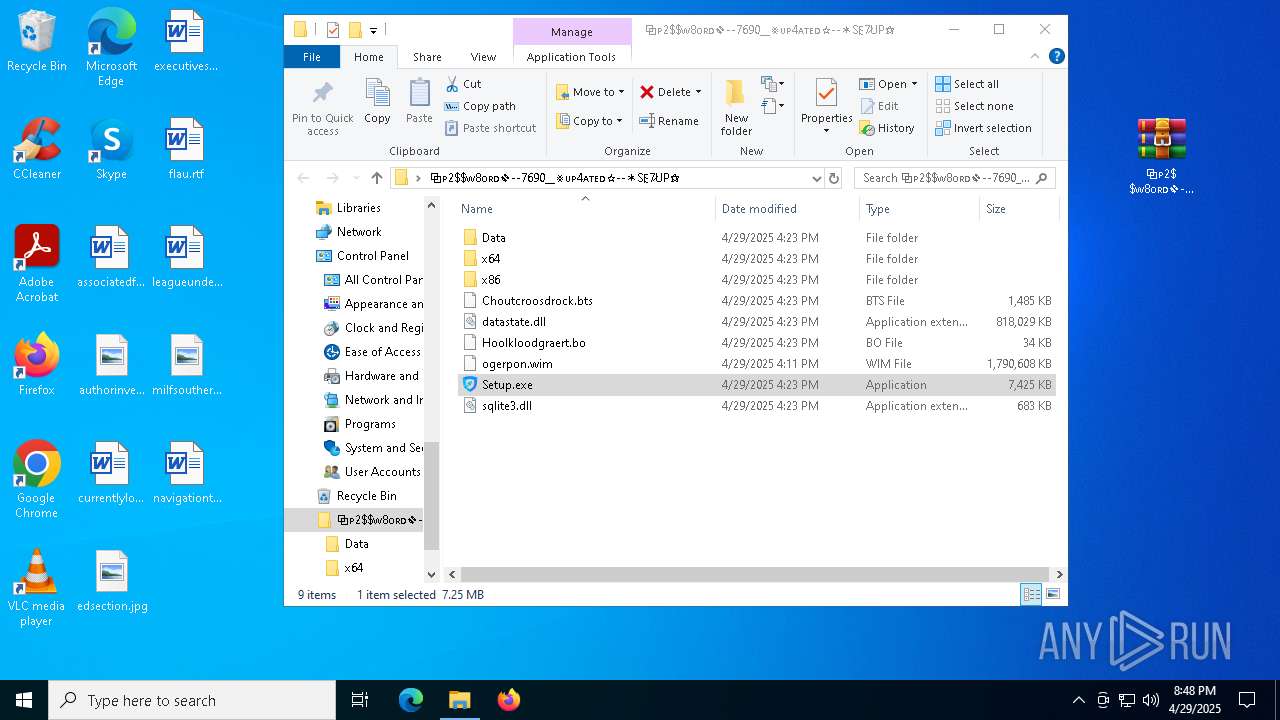
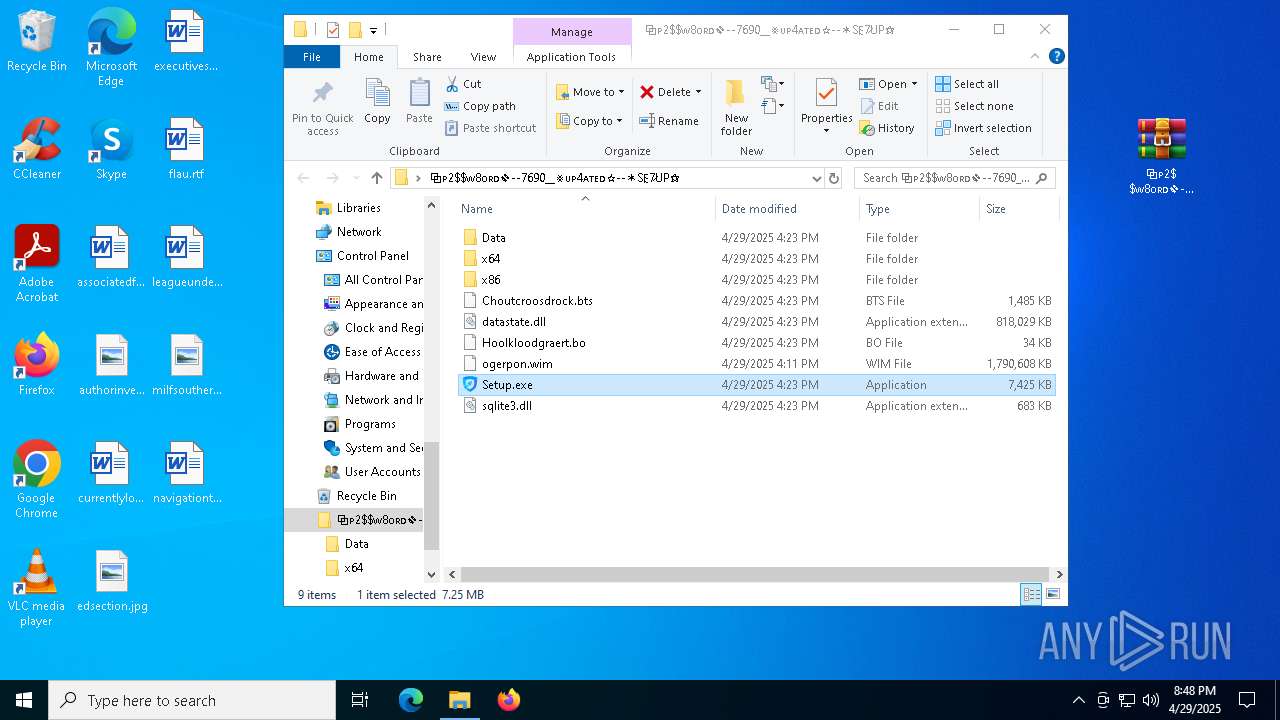
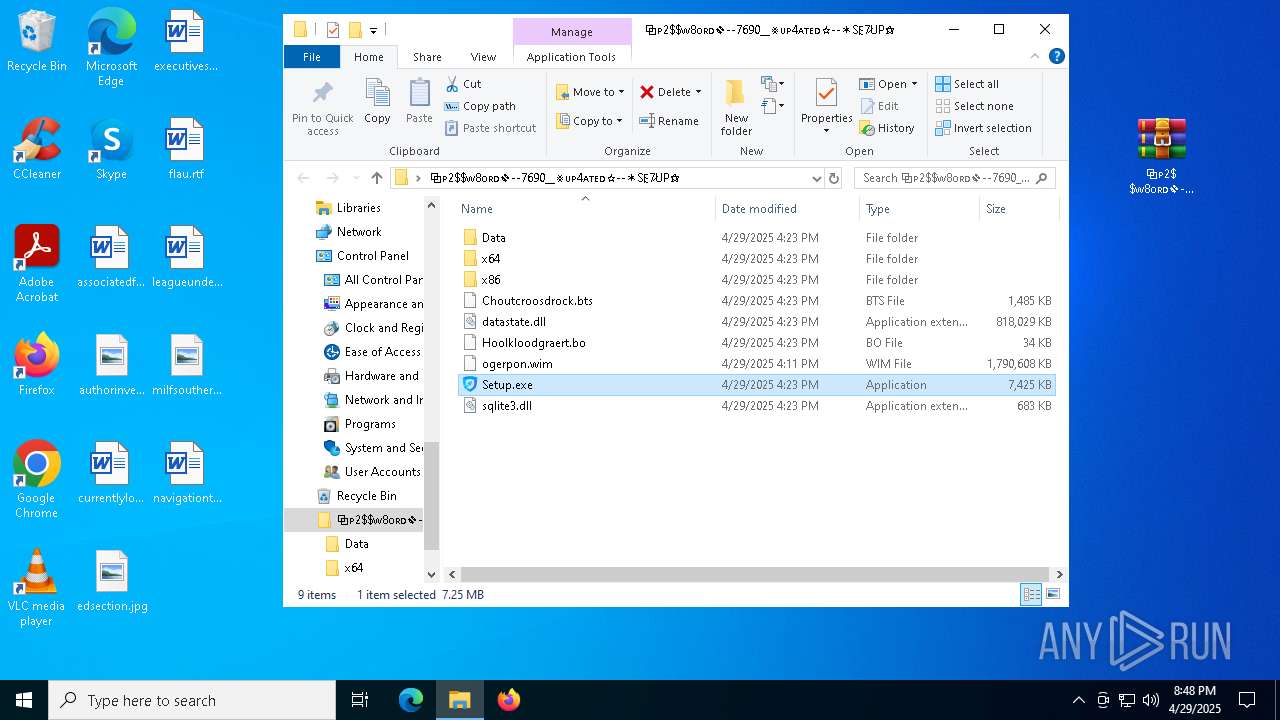
Process drops SQLite DLL files
- WinRAR.exe (PID: 7592)
- Setup.exe (PID: 6252)
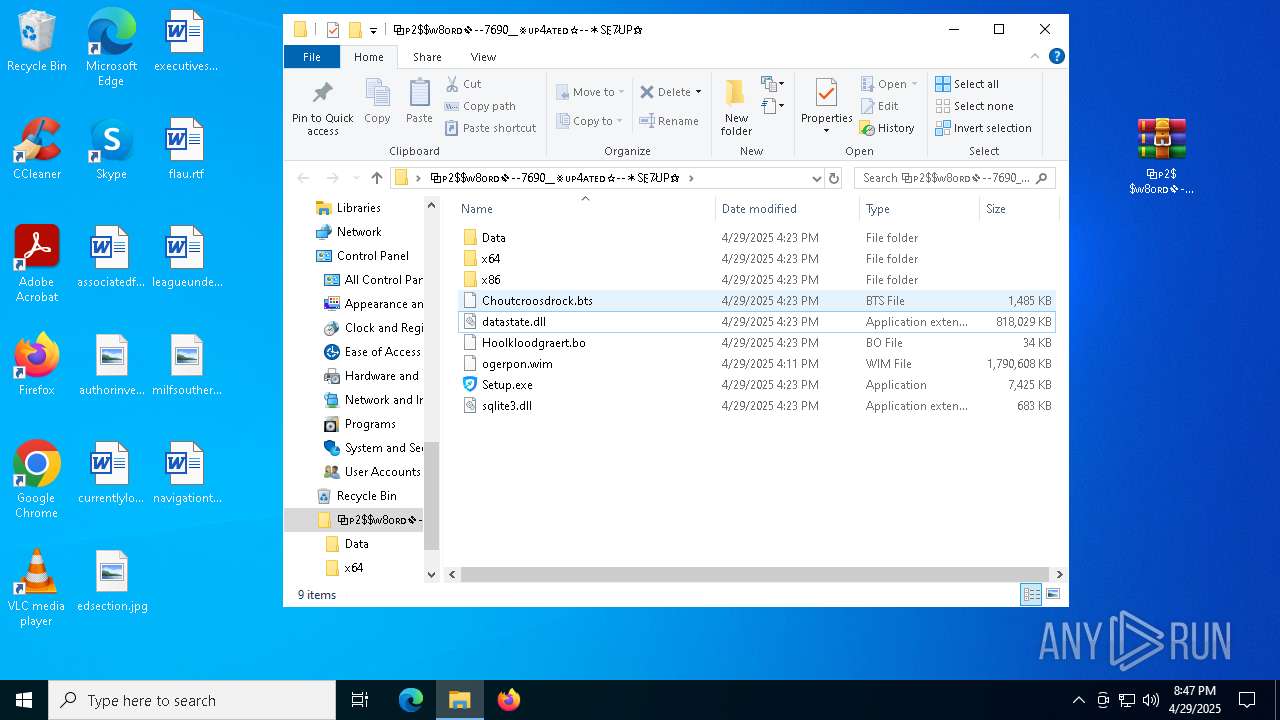
Executable content was dropped or overwritten
- Setup.exe (PID: 6252)
- Pergolesi.com (PID: 8024)
- Clus-Blue.exe (PID: 7248)
Starts application with an unusual extension
- Setup.exe (PID: 6252)
There is functionality for taking screenshot (YARA)
- Pergolesi.com (PID: 8024)
The process drops C-runtime libraries
- Pergolesi.com (PID: 8024)
INFO
Checks supported languages
- identity_helper.exe (PID: 7540)
- identity_helper.exe (PID: 8048)
Application launched itself
- msedge.exe (PID: 2852)
- msedge.exe (PID: 1328)
Reads the computer name
- identity_helper.exe (PID: 8048)
- identity_helper.exe (PID: 7540)
Reads Environment values
- identity_helper.exe (PID: 7540)
- identity_helper.exe (PID: 8048)
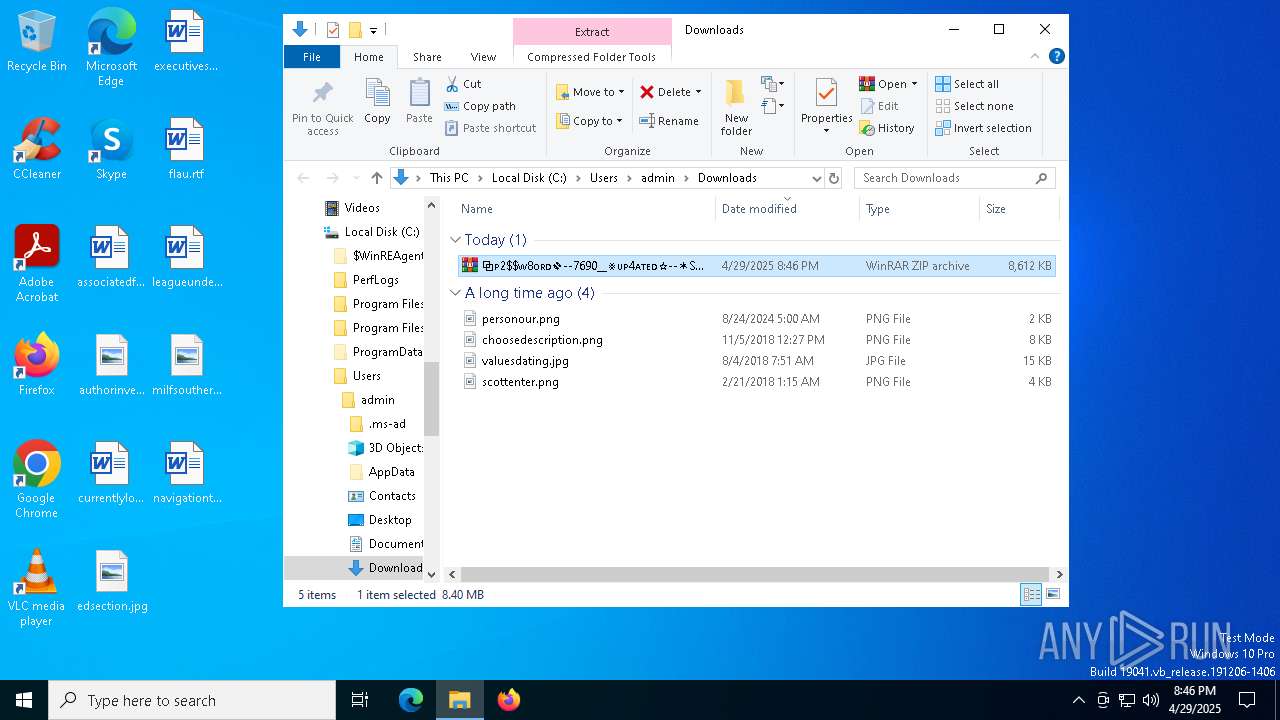
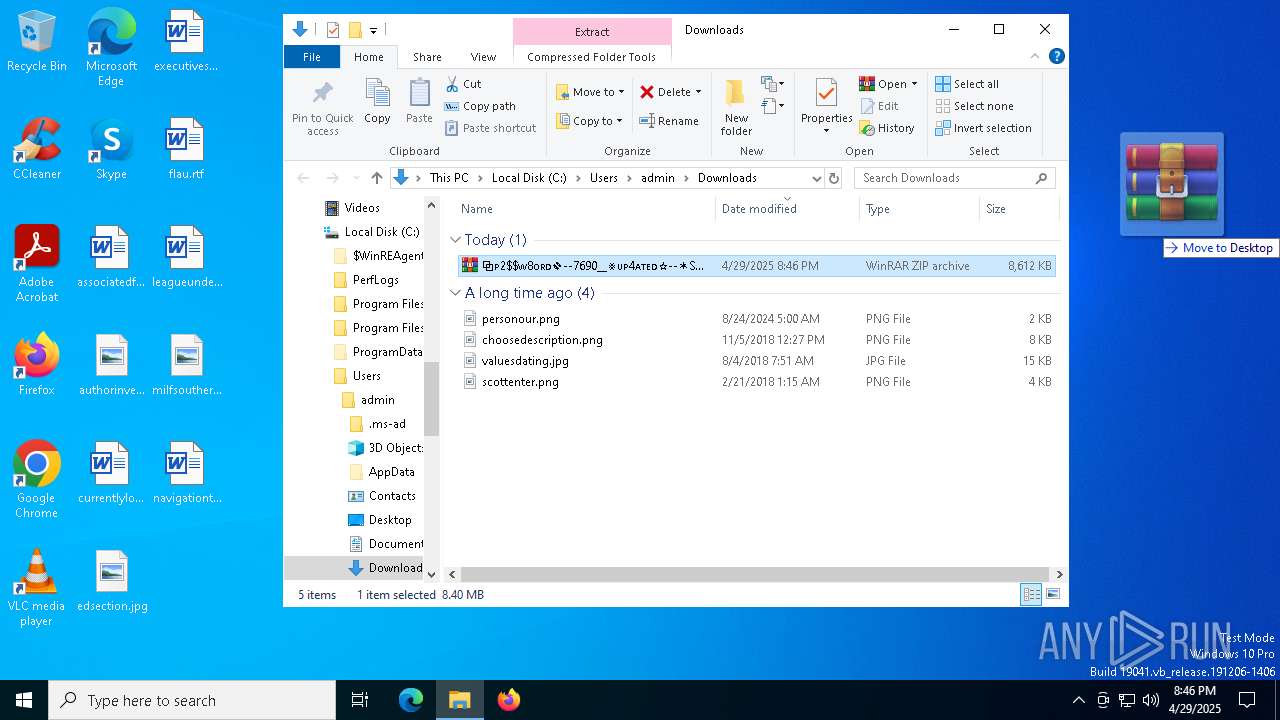
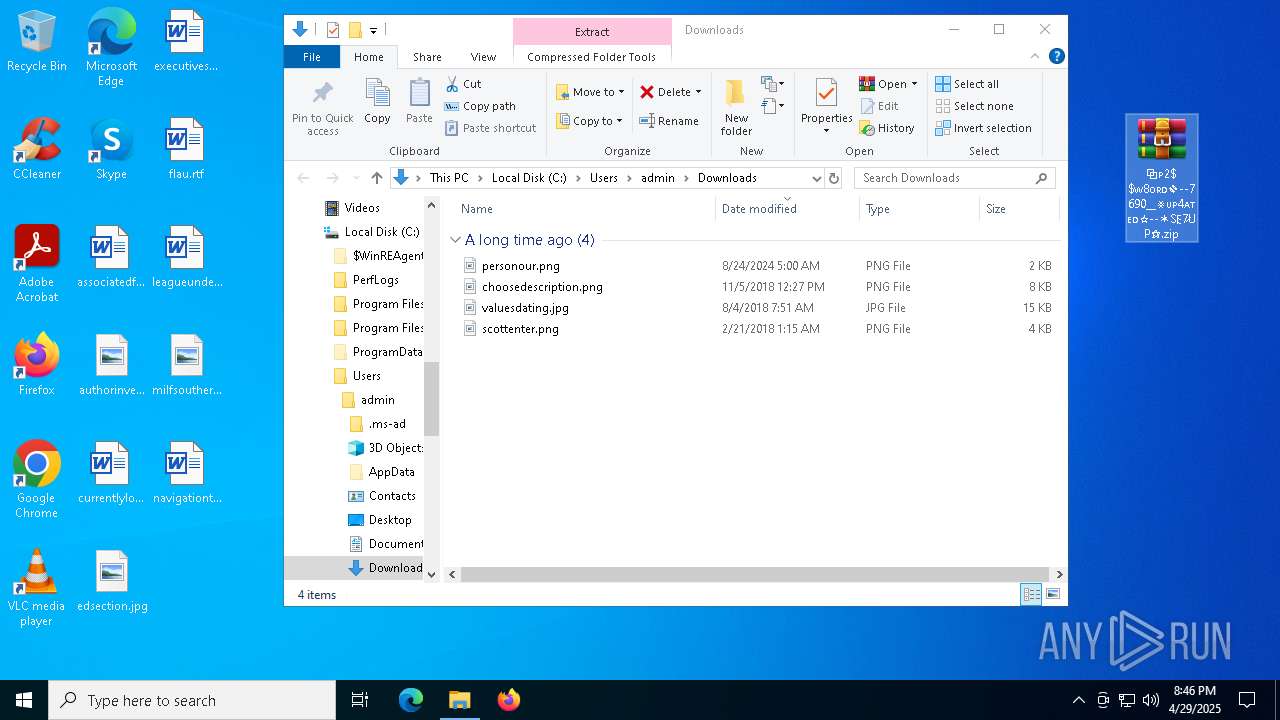
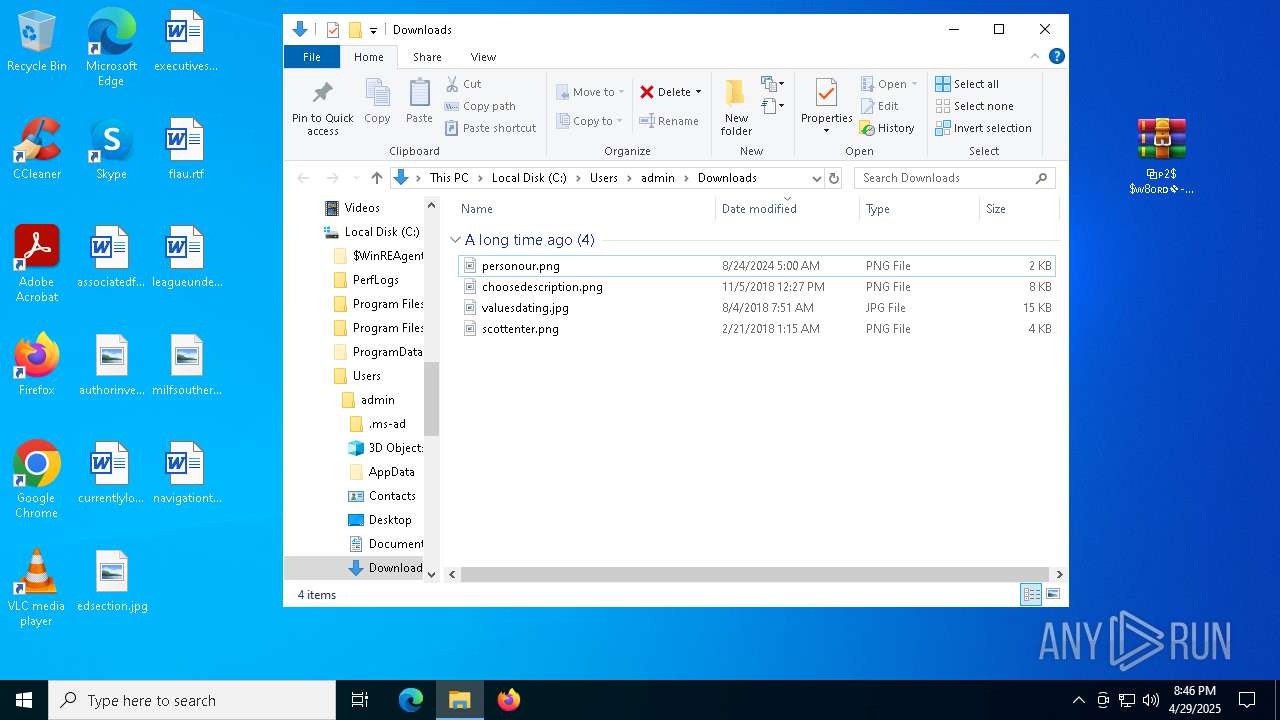
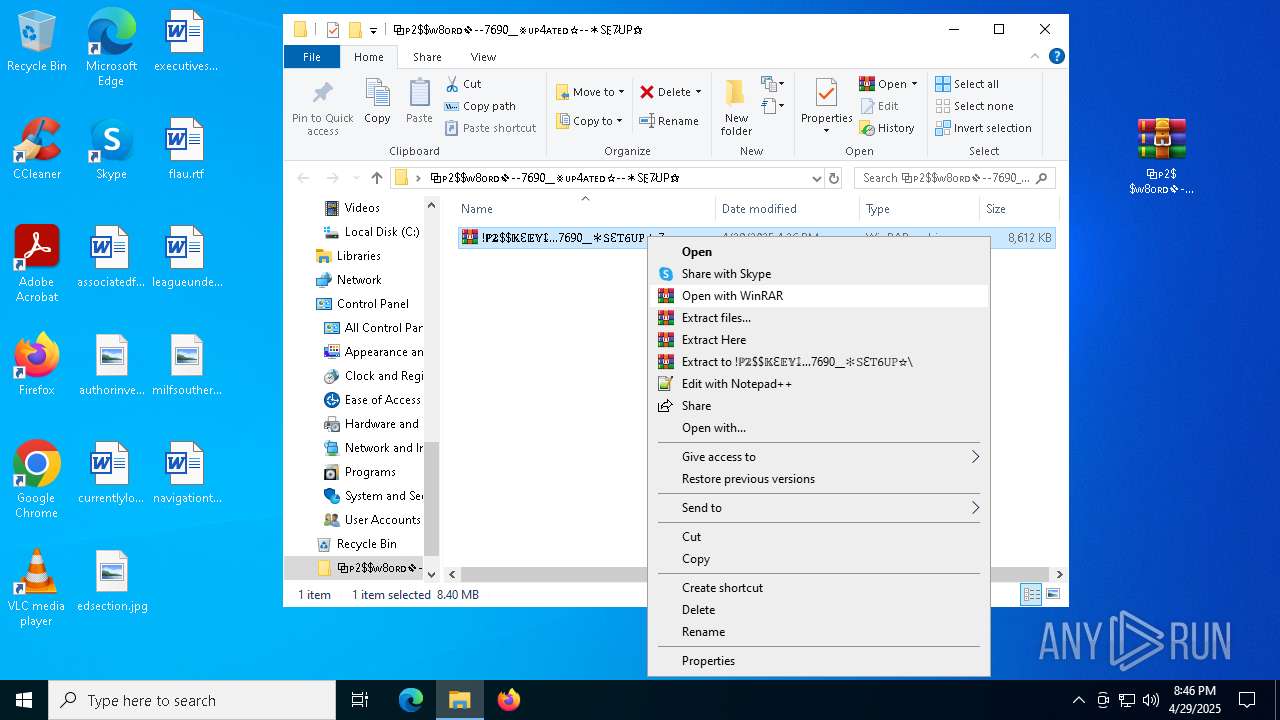
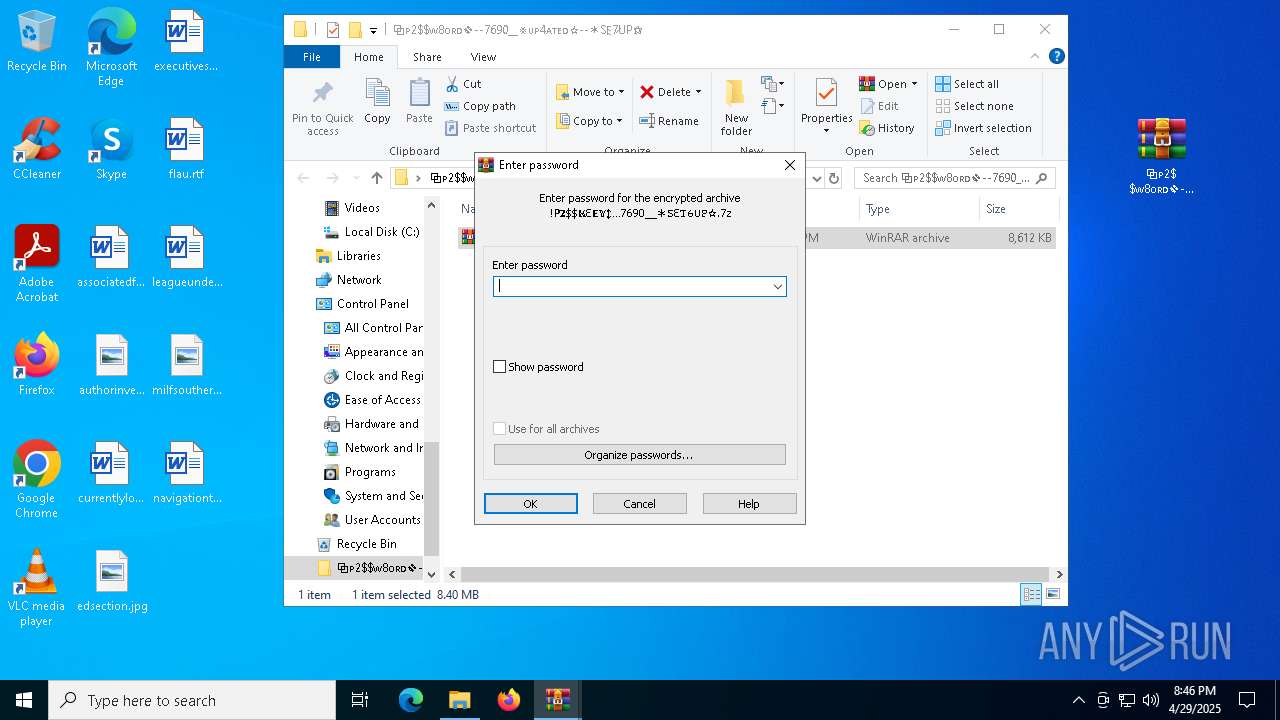
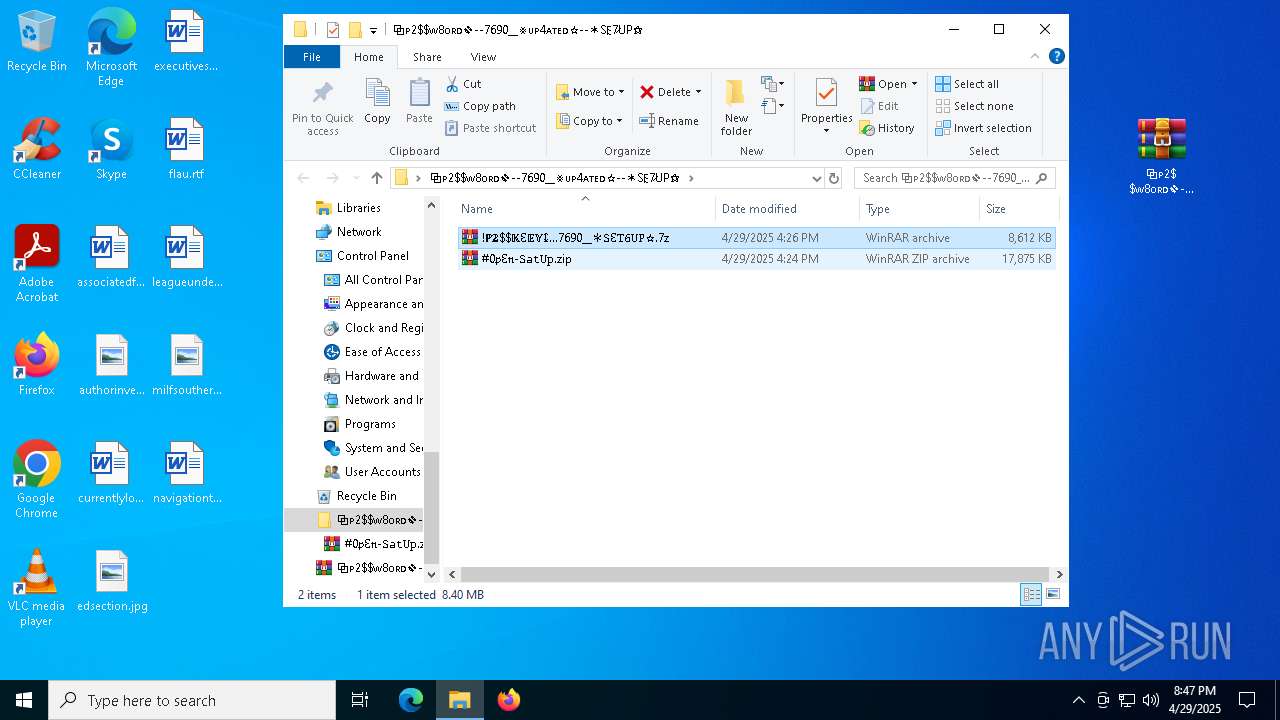
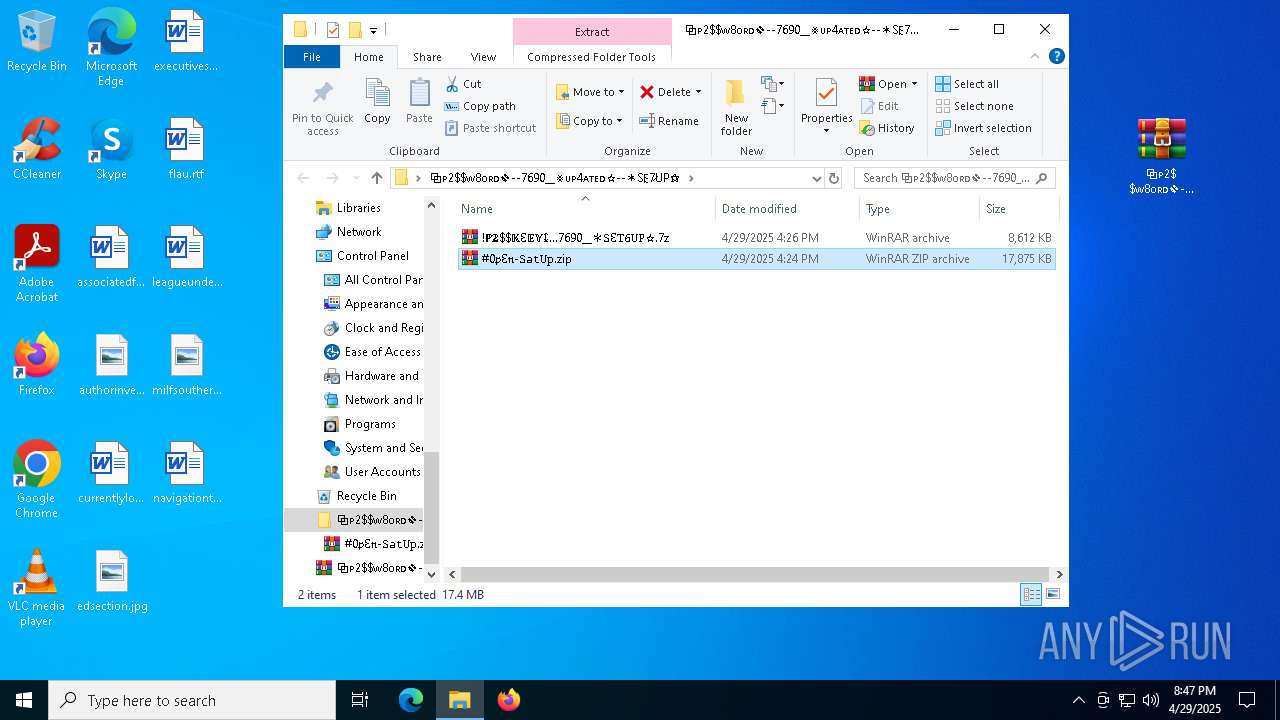
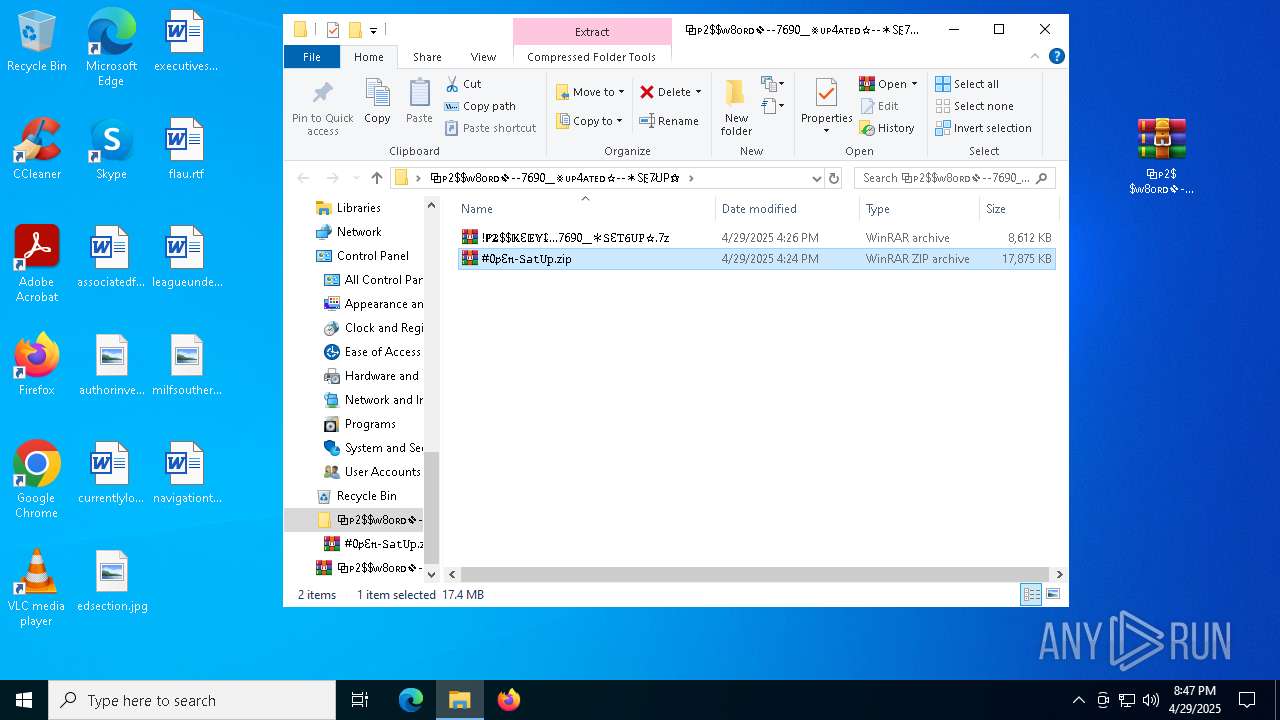
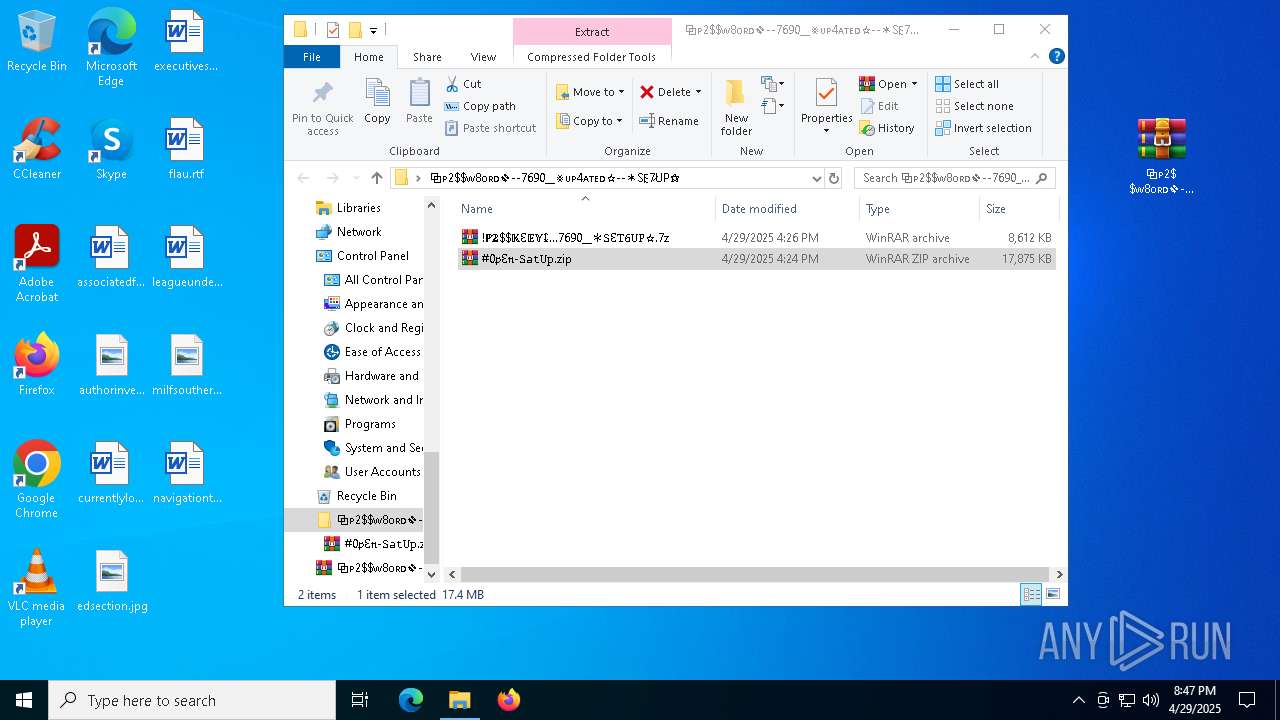
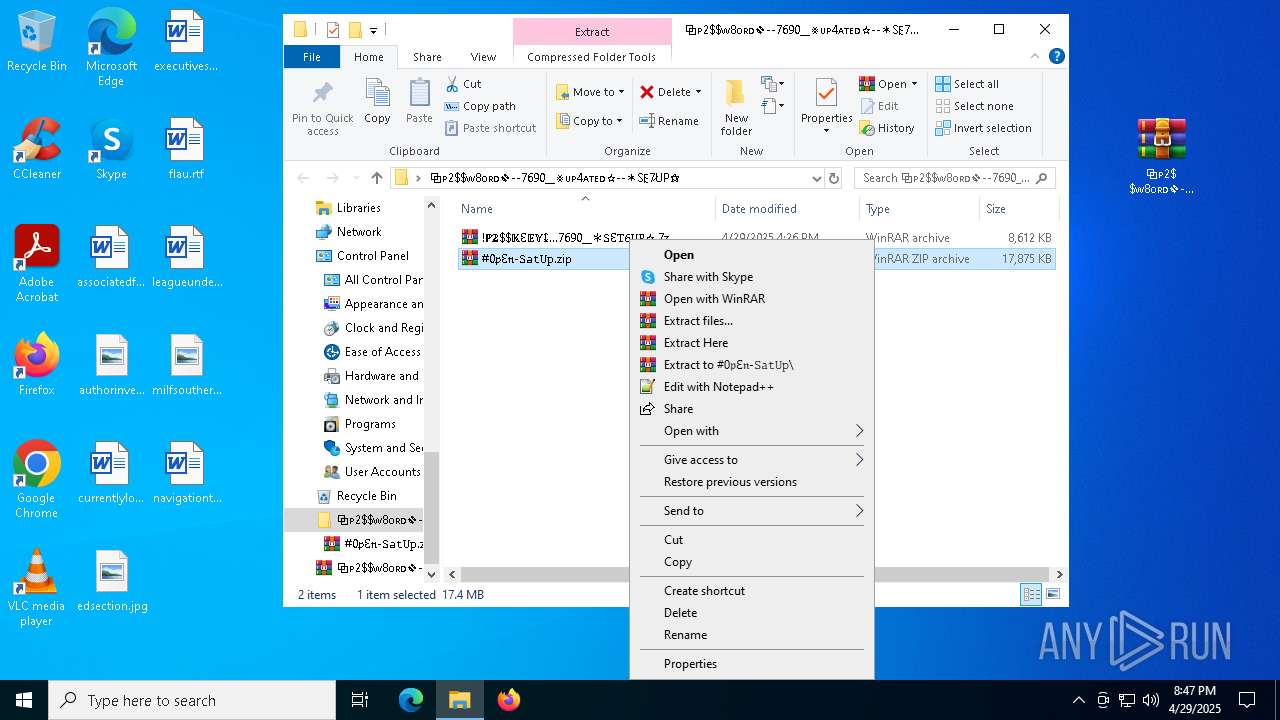
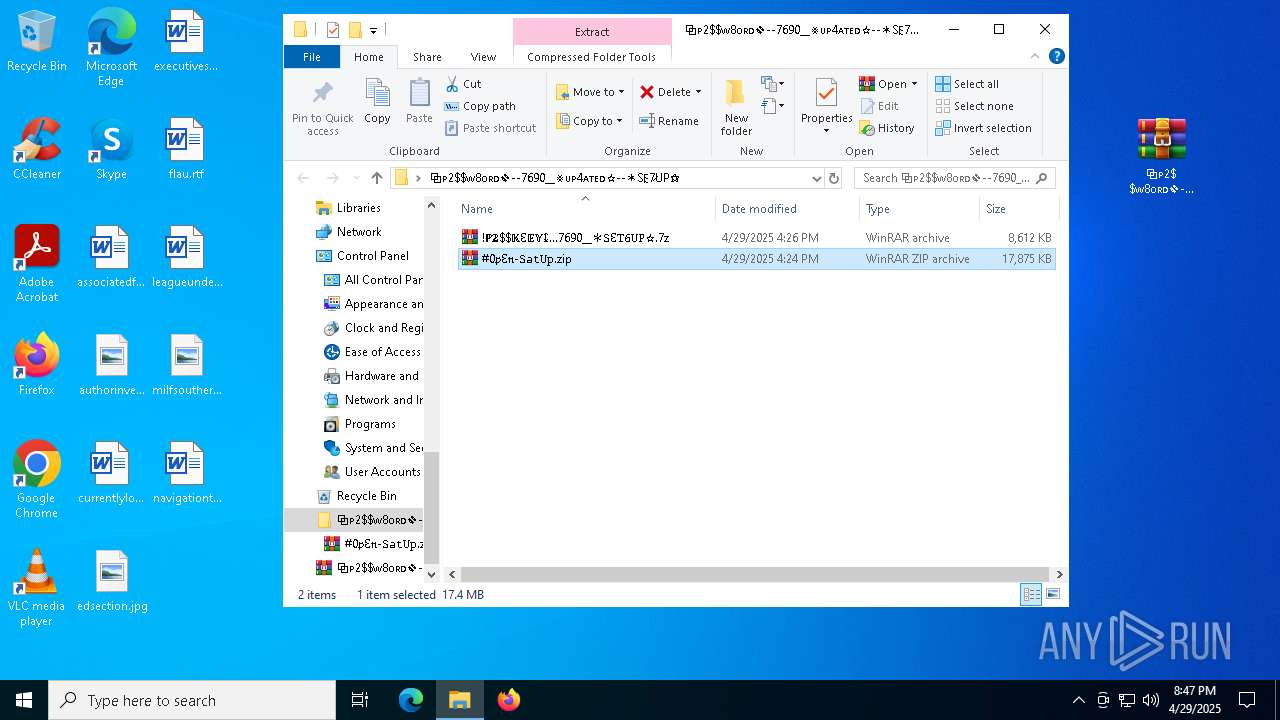
Manual execution by a user
- WinRAR.exe (PID: 7544)
- WinRAR.exe (PID: 7244)
- WinRAR.exe (PID: 7592)
- WinRAR.exe (PID: 2284)
- Setup.exe (PID: 6252)
- Setup.exe (PID: 6584)
The sample compiled with english language support
- WinRAR.exe (PID: 7592)
- Setup.exe (PID: 6252)
- Pergolesi.com (PID: 8024)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7592)
Compiled with Borland Delphi (YARA)
- Setup.exe (PID: 6252)
The sample compiled with chinese language support
- Clus-Blue.exe (PID: 7248)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
206
Monitored processes
74
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 664 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6520 --field-trial-handle=2372,i,5640963818357010809,5096701225978776374,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 856 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=35 --mojo-platform-channel-handle=5204 --field-trial-handle=2372,i,5640963818357010809,5096701225978776374,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 872 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5016 --field-trial-handle=2100,i,11437073628869044401,13522815182414035593,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1056 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=2400 --field-trial-handle=2100,i,11437073628869044401,13522815182414035593,262144 --variations-seed-version /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1180 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=4832 --field-trial-handle=2100,i,11437073628869044401,13522815182414035593,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1240 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4892 --field-trial-handle=2100,i,11437073628869044401,13522815182414035593,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1328 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
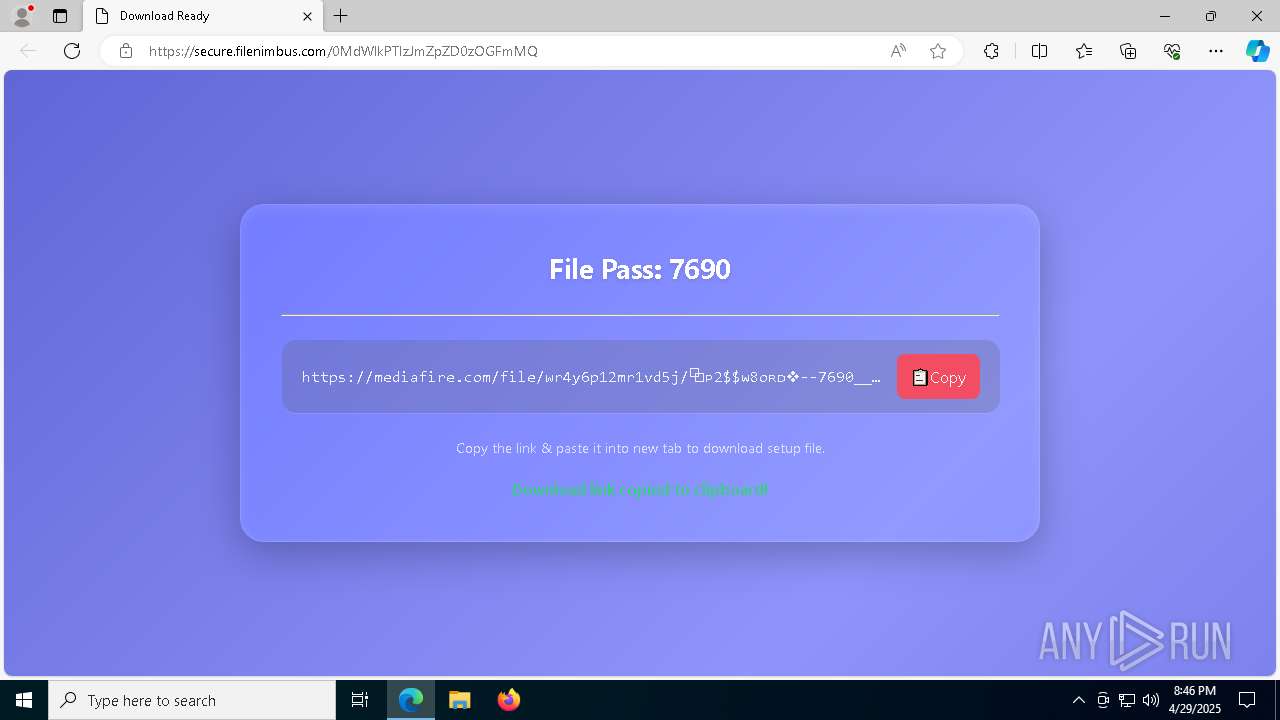
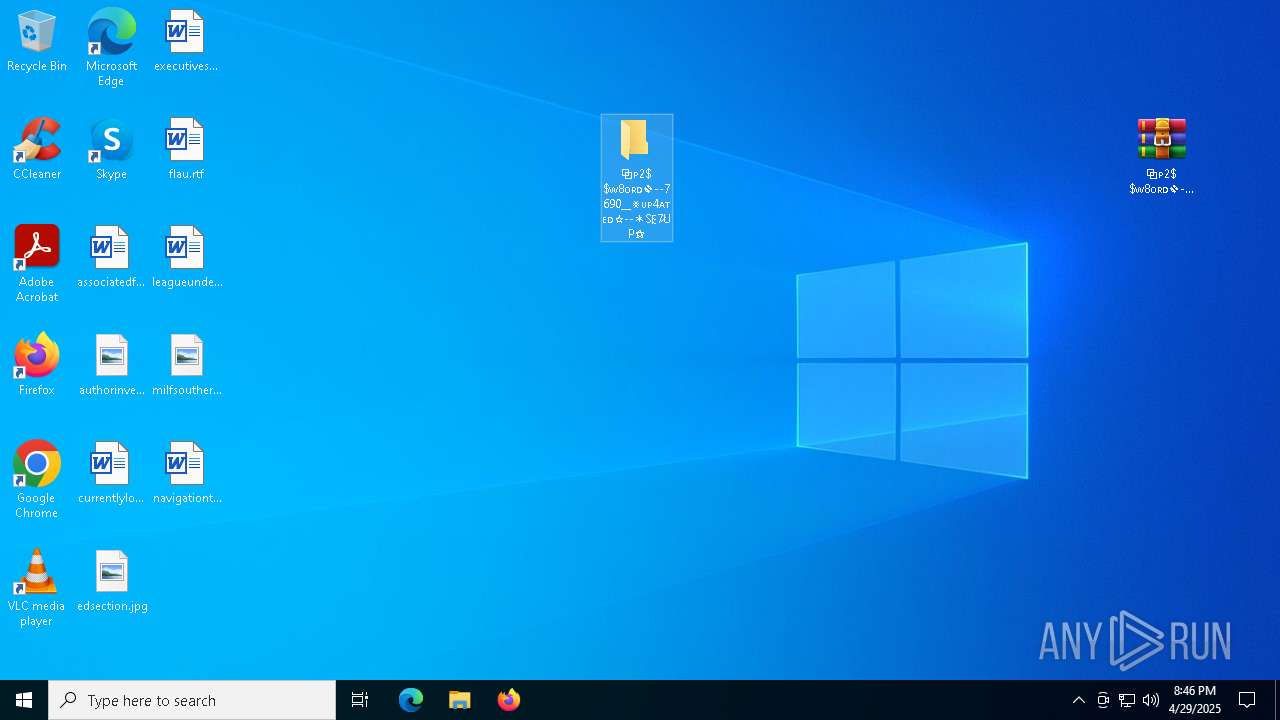
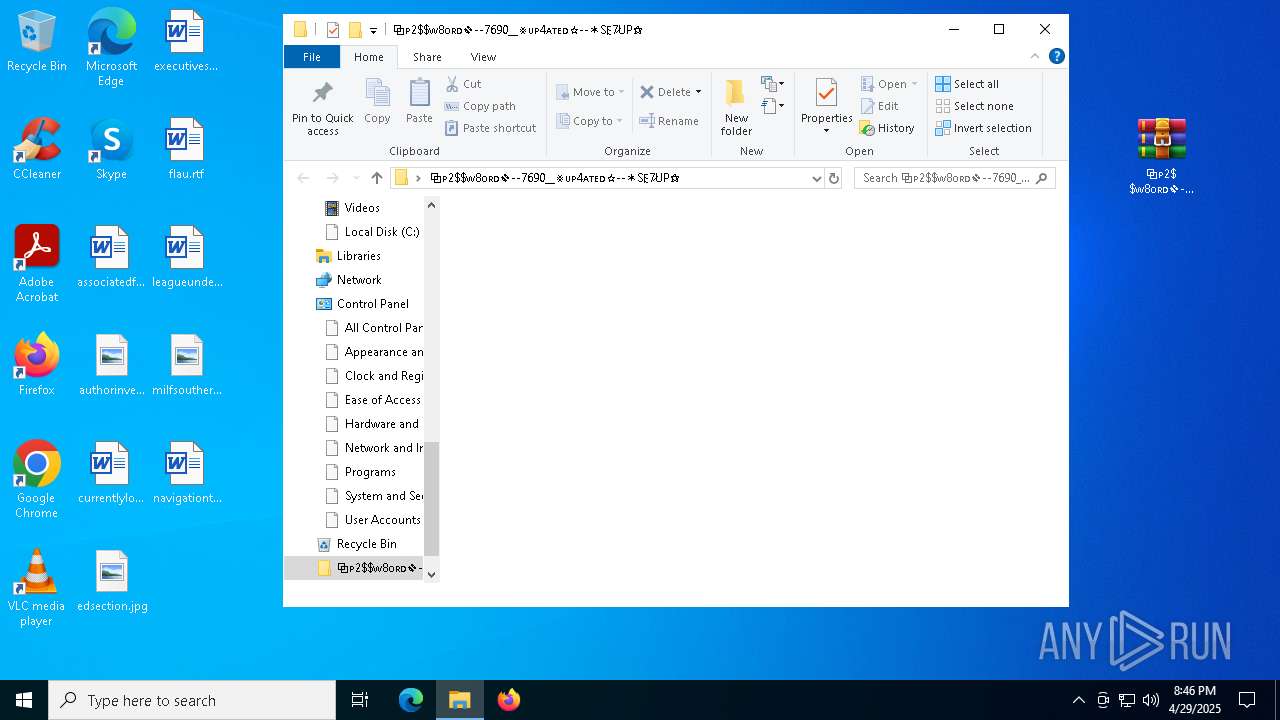
| 2284 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\⧉ᴘ2$ᴡ8ᴏʀᴅ❖--7690__⨳ᴜᴘ4ᴀᴛᴇᴅ☆--✶S𐌄7̷UP⚝\#0𝔭Ɛ𝔫-𝚂𝚊𝚝𝚄𝚙.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2392 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
13 225
Read events
13 148
Write events
64
Delete events
13
Modification events
| (PID) Process: | (2852) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2852) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2852) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2852) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (2852) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: E3A5B62C87922F00 | |||
| (PID) Process: | (2852) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: E490C22C87922F00 | |||
| (PID) Process: | (2852) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328322 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {69CA4439-3D90-46EA-8218-30F433057F8F} | |||
| (PID) Process: | (2852) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328322 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {16CF17D6-270E-4BAA-AB7D-860A048C0035} | |||
| (PID) Process: | (2852) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328322 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {77316976-EADA-4F49-8AD6-9F269685B447} | |||
| (PID) Process: | (2852) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328322 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {267DD674-1622-4640-AC87-99B0B0D27131} | |||
Executable files
37
Suspicious files
344
Text files
157
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2852 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b3d1.TMP | — | |
MD5:— | SHA256:— | |||
| 2852 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b3d1.TMP | — | |
MD5:— | SHA256:— | |||
| 2852 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b3e1.TMP | — | |
MD5:— | SHA256:— | |||
| 2852 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b3d1.TMP | — | |
MD5:— | SHA256:— | |||
| 2852 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2852 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2852 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2852 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2852 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b3f0.TMP | — | |
MD5:— | SHA256:— | |||
| 2852 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
19
TCP/UDP connections
107
DNS requests
122
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.216.77.35:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8144 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8144 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1240 | svchost.exe | GET | 206 | 23.50.131.74:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9530bc3d-28ec-4dca-8d8d-874a68b1b861?P1=1746514145&P2=404&P3=2&P4=A0Hl5HEbQkDncd3wU3lDofgul%2bYb5Pk34AOfDvSD8mKJPq3BZtSJLRjjLt7Xr%2ffOOfVy5VJe%2fd5DqaZQeA3txw%3d%3d | unknown | — | — | whitelisted |
1240 | svchost.exe | HEAD | 200 | 23.50.131.74:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9530bc3d-28ec-4dca-8d8d-874a68b1b861?P1=1746514145&P2=404&P3=2&P4=A0Hl5HEbQkDncd3wU3lDofgul%2bYb5Pk34AOfDvSD8mKJPq3BZtSJLRjjLt7Xr%2ffOOfVy5VJe%2fd5DqaZQeA3txw%3d%3d | unknown | — | — | whitelisted |
1240 | svchost.exe | GET | 206 | 23.50.131.74:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9530bc3d-28ec-4dca-8d8d-874a68b1b861?P1=1746514145&P2=404&P3=2&P4=A0Hl5HEbQkDncd3wU3lDofgul%2bYb5Pk34AOfDvSD8mKJPq3BZtSJLRjjLt7Xr%2ffOOfVy5VJe%2fd5DqaZQeA3txw%3d%3d | unknown | — | — | whitelisted |
1240 | svchost.exe | GET | 206 | 23.50.131.74:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9530bc3d-28ec-4dca-8d8d-874a68b1b861?P1=1746514145&P2=404&P3=2&P4=A0Hl5HEbQkDncd3wU3lDofgul%2bYb5Pk34AOfDvSD8mKJPq3BZtSJLRjjLt7Xr%2ffOOfVy5VJe%2fd5DqaZQeA3txw%3d%3d | unknown | — | — | whitelisted |
1240 | svchost.exe | GET | 206 | 23.50.131.74:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9530bc3d-28ec-4dca-8d8d-874a68b1b861?P1=1746514145&P2=404&P3=2&P4=A0Hl5HEbQkDncd3wU3lDofgul%2bYb5Pk34AOfDvSD8mKJPq3BZtSJLRjjLt7Xr%2ffOOfVy5VJe%2fd5DqaZQeA3txw%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 23.216.77.35:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7312 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2852 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7312 | msedge.exe | 172.67.218.196:443 | vylorinthaxen.cloud | — | — | unknown |
7312 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
vylorinthaxen.cloud |
| unknown |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
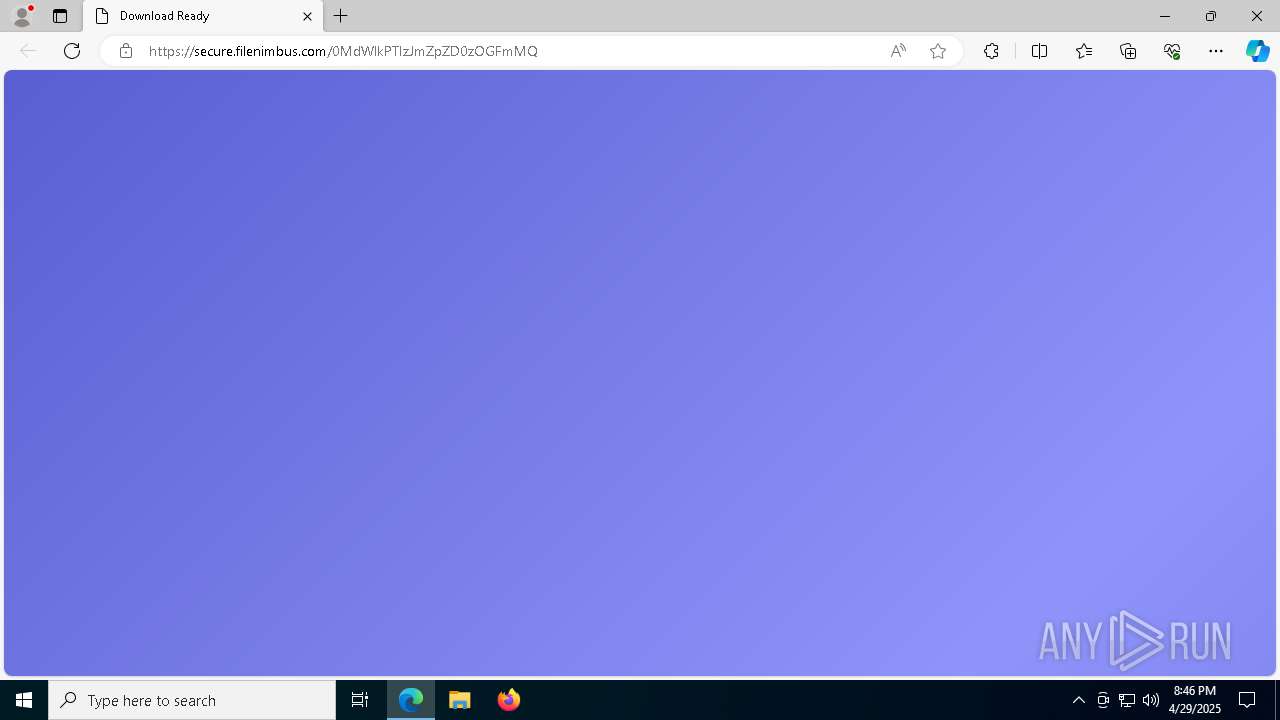
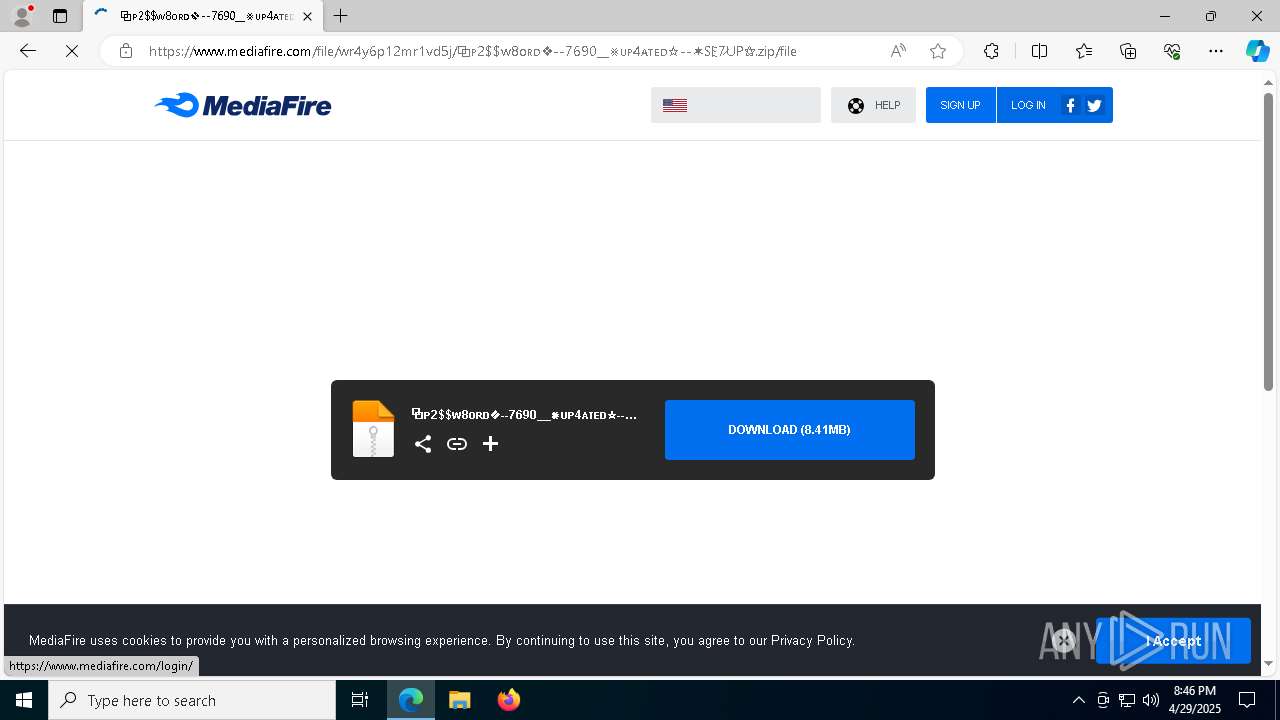
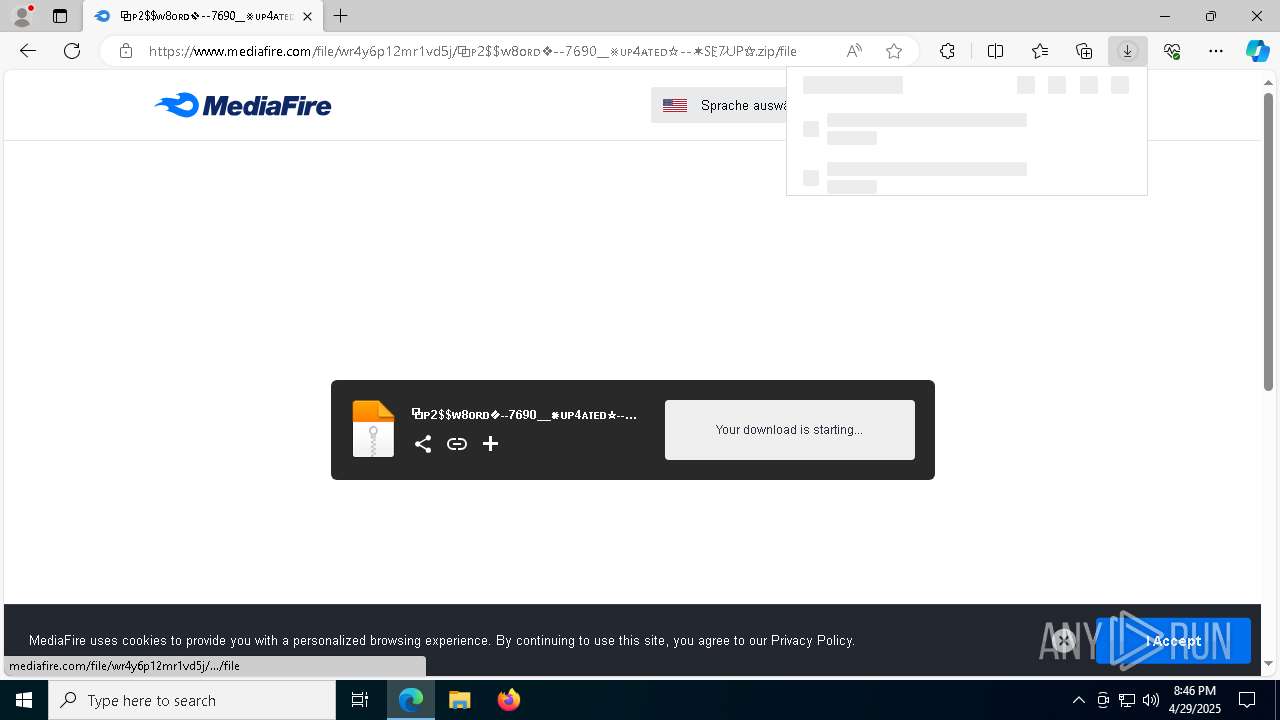
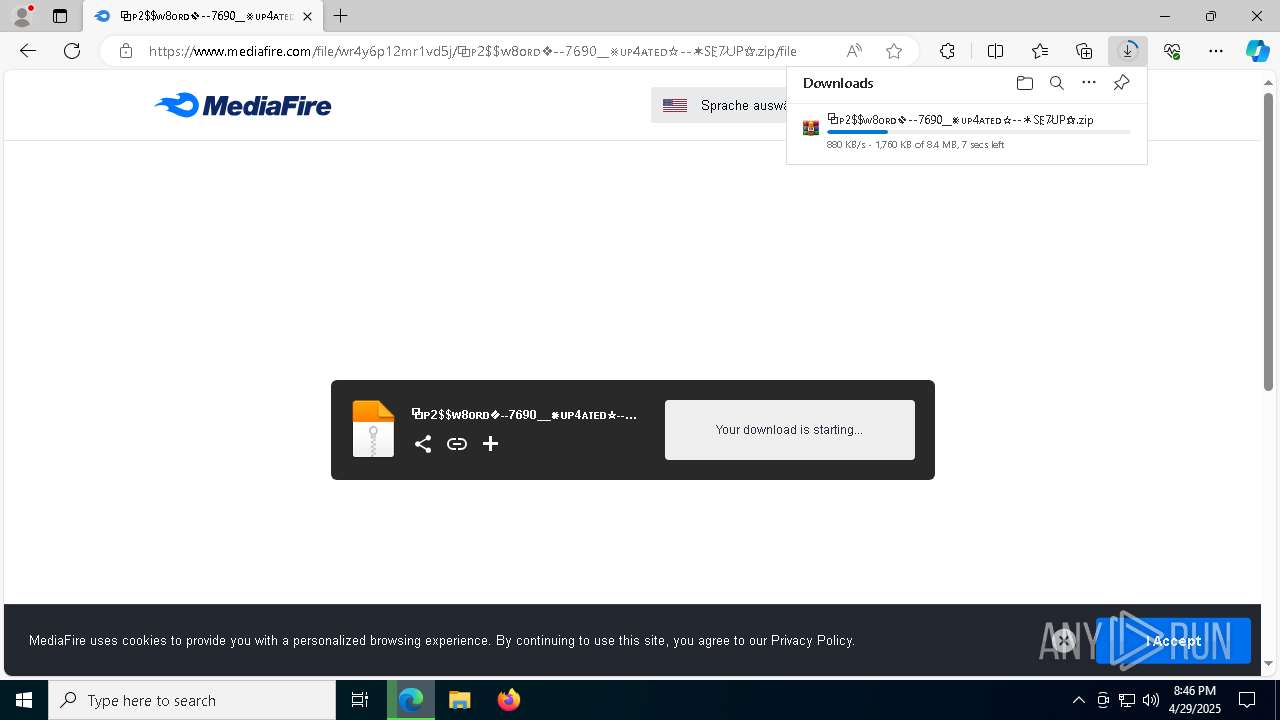
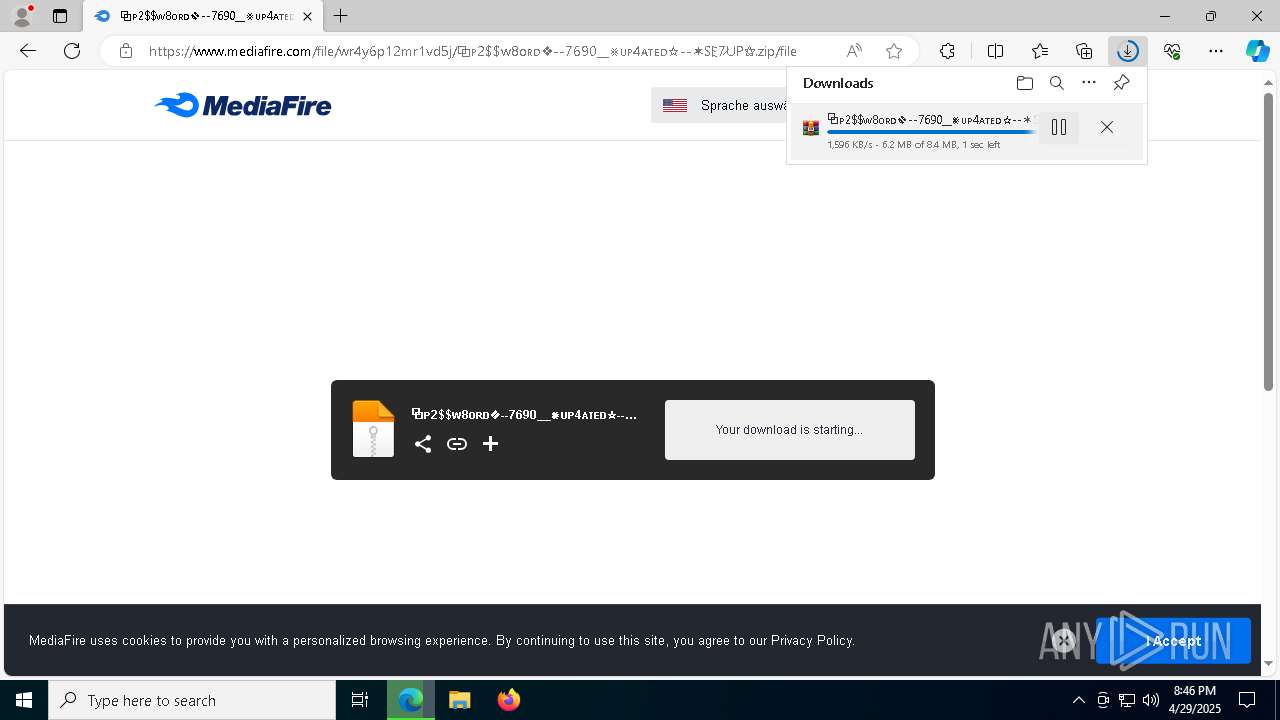
7312 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
7312 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
7312 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
7312 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
2196 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |