| File name: | a3a47448f45b0374c3cde59e1a7bfb0d.exe |
| Full analysis: | https://app.any.run/tasks/010872b1-7cfb-4553-a649-330ebe04d3a5 |
| Verdict: | Malicious activity |
| Threats: | WarZone RAT is a remote access trojan, which is written in C++ and offered as a malware-as-a-service. It packs a wide range of capabilities, from stealing victims’ files and passwords to capturing desktop activities. WarZone RAT is primarily distributed via phishing emails and receives regular updates from its C2. |
| Analysis date: | April 01, 2023, 13:27:50 |
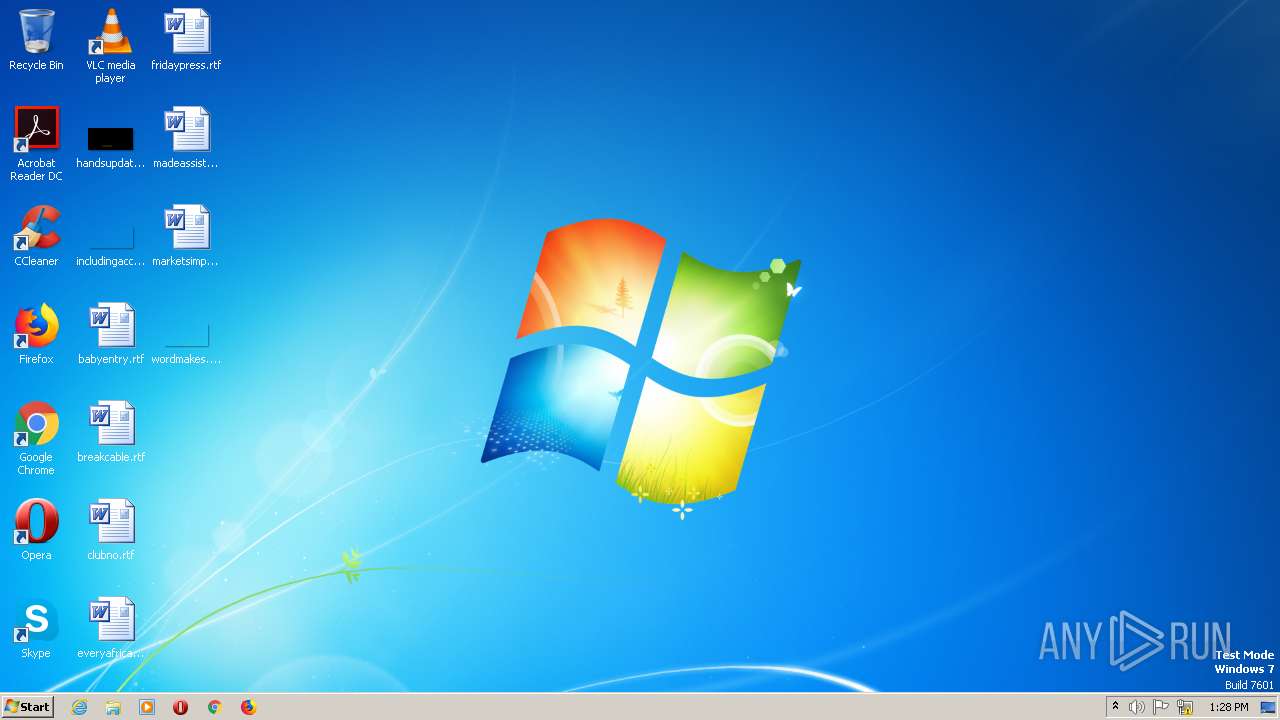
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | A3A47448F45B0374C3CDE59E1A7BFB0D |
| SHA1: | E00B404F1A143C99E1CF095EF27678022539BE43 |
| SHA256: | 9B1CD01F7D8E52A581FA6D6B2FD0DBB61361C3E6BDA603F0F5FDED0F938ADA10 |
| SSDEEP: | 3072:4fY/TU9fE9PEtuJbfgN0XwaZlq5cSeZCV8Pt7oih6Qrpu+hmzFmr7J0Fjp+VDf84:uYa6XfnXwuI5KCVAxCQFZsFImp+DfG6 |
MALICIOUS
Application was dropped or rewritten from another process
- ghibzkdm.exe (PID: 1260)
- ghibzkdm.exe (PID: 592)
Steals credentials from Web Browsers
- ghibzkdm.exe (PID: 592)
WARZONE detected by memory dumps
- ghibzkdm.exe (PID: 592)
Connects to the CnC server
- ghibzkdm.exe (PID: 592)
AVEMARIA was detected
- ghibzkdm.exe (PID: 592)
Loads dropped or rewritten executable
- ghibzkdm.exe (PID: 592)
Actions looks like stealing of personal data
- ghibzkdm.exe (PID: 592)
SUSPICIOUS
Executable content was dropped or overwritten
- a3a47448f45b0374c3cde59e1a7bfb0d.exe (PID: 1636)
- ghibzkdm.exe (PID: 1260)
- ghibzkdm.exe (PID: 592)
Application launched itself
- ghibzkdm.exe (PID: 1260)
Accesses Microsoft Outlook profiles
- ghibzkdm.exe (PID: 592)
Connects to unusual port
- ghibzkdm.exe (PID: 592)
INFO
Reads the computer name
- a3a47448f45b0374c3cde59e1a7bfb0d.exe (PID: 1636)
- ghibzkdm.exe (PID: 592)
The process checks LSA protection
- a3a47448f45b0374c3cde59e1a7bfb0d.exe (PID: 1636)
- ghibzkdm.exe (PID: 592)
Checks supported languages
- a3a47448f45b0374c3cde59e1a7bfb0d.exe (PID: 1636)
- ghibzkdm.exe (PID: 1260)
- ghibzkdm.exe (PID: 592)
Create files in a temporary directory
- a3a47448f45b0374c3cde59e1a7bfb0d.exe (PID: 1636)
- ghibzkdm.exe (PID: 592)
Creates files or folders in the user directory
- ghibzkdm.exe (PID: 1260)
- ghibzkdm.exe (PID: 592)
Reads the machine GUID from the registry
- ghibzkdm.exe (PID: 592)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
WarZone
(PID) Process(592) ghibzkdm.exe
C2 (2)top.not2beabused01.xyz:1668
sub.not2beabused01.xyz:1668
BuildID2D23HO01JRH
Options
Install FlagFalse
Startup FlagFalse
Reverse Proxy local port5000
Offline logTrue
PersistanceFalse
UAC bypassFalse
Defender bypassFalse
Use ADSFalse
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| ProductName: | 78.97.57.19 |
|---|---|
| LegalTrademarks: | seedlip |
| LegalCopyright: | Copyright pullup |
| FileVersion: | 78.97.57.19 |
| FileDescription: | nonaphoristically |
| CompanyName: | hircarra |
| CharacterSet: | Unicode |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x0000 |
| ProductVersionNumber: | 78.97.57.19 |
| FileVersionNumber: | 78.97.57.19 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | 6 |
| OSVersion: | 4 |
| EntryPoint: | 0x3640 |
| UninitializedDataSize: | 2048 |
| InitializedDataSize: | 141824 |
| CodeSize: | 26624 |
| LinkerVersion: | 6 |
| PEType: | PE32 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| TimeStamp: | 2021:09:25 21:56:47+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 25-Sep-2021 21:56:47 |
| Detected languages: |
|
| CompanyName: | hircarra |
| FileDescription: | nonaphoristically |
| FileVersion: | 78.97.57.19 |
| LegalCopyright: | Copyright pullup |
| LegalTrademarks: | seedlip |
| ProductName: | 78.97.57.19 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 25-Sep-2021 21:56:47 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00006676 | 0x00006800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.41746 |
.rdata | 0x00008000 | 0x0000139A | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.14107 |
.data | 0x0000A000 | 0x00020378 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.11058 |
.ndata | 0x0002B000 | 0x00010000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0003B000 | 0x00005478 | 0x00005600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.44822 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.29934 | 830 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.30559 | 2440 | UNKNOWN | English - United States | RT_ICON |
3 | 5.63361 | 2216 | UNKNOWN | English - United States | RT_ICON |
4 | 4.21181 | 1736 | UNKNOWN | English - United States | RT_ICON |
5 | 3.52843 | 1720 | UNKNOWN | English - United States | RT_ICON |
6 | 3.87508 | 1544 | UNKNOWN | English - United States | RT_ICON |
7 | 3.05652 | 1384 | UNKNOWN | English - United States | RT_ICON |
8 | 3.92448 | 1128 | UNKNOWN | English - United States | RT_ICON |
9 | 3.41398 | 744 | UNKNOWN | English - United States | RT_ICON |
10 | 3.01683 | 488 | UNKNOWN | English - United States | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
31
Monitored processes
3
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 592 | "C:\Users\admin\AppData\Local\Temp\ghibzkdm.exe" | C:\Users\admin\AppData\Local\Temp\ghibzkdm.exe | ghibzkdm.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
WarZone(PID) Process(592) ghibzkdm.exe C2 (2)top.not2beabused01.xyz:1668 sub.not2beabused01.xyz:1668 BuildID2D23HO01JRH Options Install FlagFalse Startup FlagFalse Reverse Proxy local port5000 Offline logTrue PersistanceFalse UAC bypassFalse Defender bypassFalse Use ADSFalse | |||||||||||||||
| 1260 | "C:\Users\admin\AppData\Local\Temp\ghibzkdm.exe" C:\Users\admin\AppData\Local\Temp\xaaktctbkvc.h | C:\Users\admin\AppData\Local\Temp\ghibzkdm.exe | a3a47448f45b0374c3cde59e1a7bfb0d.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1636 | "C:\Users\admin\AppData\Local\Temp\a3a47448f45b0374c3cde59e1a7bfb0d.exe" | C:\Users\admin\AppData\Local\Temp\a3a47448f45b0374c3cde59e1a7bfb0d.exe | explorer.exe | ||||||||||||
User: admin Company: hircarra Integrity Level: MEDIUM Description: nonaphoristically Exit code: 0 Version: 78.97.57.19 Modules
| |||||||||||||||
Total events
1 808
Read events
1 808
Write events
0
Delete events
0
Modification events
Executable files
16
Suspicious files
8
Text files
28
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1636 | a3a47448f45b0374c3cde59e1a7bfb0d.exe | C:\Users\admin\AppData\Local\Temp\xaaktctbkvc.h | binary | |
MD5:— | SHA256:— | |||
| 1636 | a3a47448f45b0374c3cde59e1a7bfb0d.exe | C:\Users\admin\AppData\Local\Temp\tmbugjrwpz.kh | binary | |
MD5:— | SHA256:— | |||
| 1636 | a3a47448f45b0374c3cde59e1a7bfb0d.exe | C:\Users\admin\AppData\Local\Temp\nssB609.tmp | binary | |
MD5:— | SHA256:— | |||
| 592 | ghibzkdm.exe | C:\Users\admin\AppData\Local\Google\Media\2023-4-1_13.28.49_.jpeg | image | |
MD5:— | SHA256:— | |||
| 1636 | a3a47448f45b0374c3cde59e1a7bfb0d.exe | C:\Users\admin\AppData\Local\Temp\ghibzkdm.exe | executable | |
MD5:— | SHA256:— | |||
| 592 | ghibzkdm.exe | C:\Users\admin\AppData\Local\Google\Media\2023-4-1_13.28.19_.jpeg | image | |
MD5:— | SHA256:— | |||
| 592 | ghibzkdm.exe | C:\Users\admin\AppData\Local\Google\Media\2023-4-1_13.28.39_.jpeg | image | |
MD5:— | SHA256:— | |||
| 592 | ghibzkdm.exe | C:\Users\admin\AppData\Local\Google\Media\2023-4-1_13.28.29_.jpeg | image | |
MD5:— | SHA256:— | |||
| 592 | ghibzkdm.exe | C:\Users\admin\AppData\Local\Google\Media\2023-4-1_13.28.9_.jpeg | image | |
MD5:— | SHA256:— | |||
| 592 | ghibzkdm.exe | C:\Users\admin\AppData\Local\Google\Media\2023-4-1_13.28.59_.jpeg | image | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
2
Threats
15
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
592 | ghibzkdm.exe | 20.112.52.29:80 | microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | malicious |
592 | ghibzkdm.exe | 38.117.65.122:1668 | top.not2beabused01.xyz | RAVAND | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
top.not2beabused01.xyz |
| malicious |
microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
592 | ghibzkdm.exe | A Network Trojan was detected | ET MALWARE Warzone RAT Response (Inbound) |
592 | ghibzkdm.exe | A Network Trojan was detected | ET MALWARE Warzone RAT Response (Inbound) |
592 | ghibzkdm.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
12 ETPRO signatures available at the full report