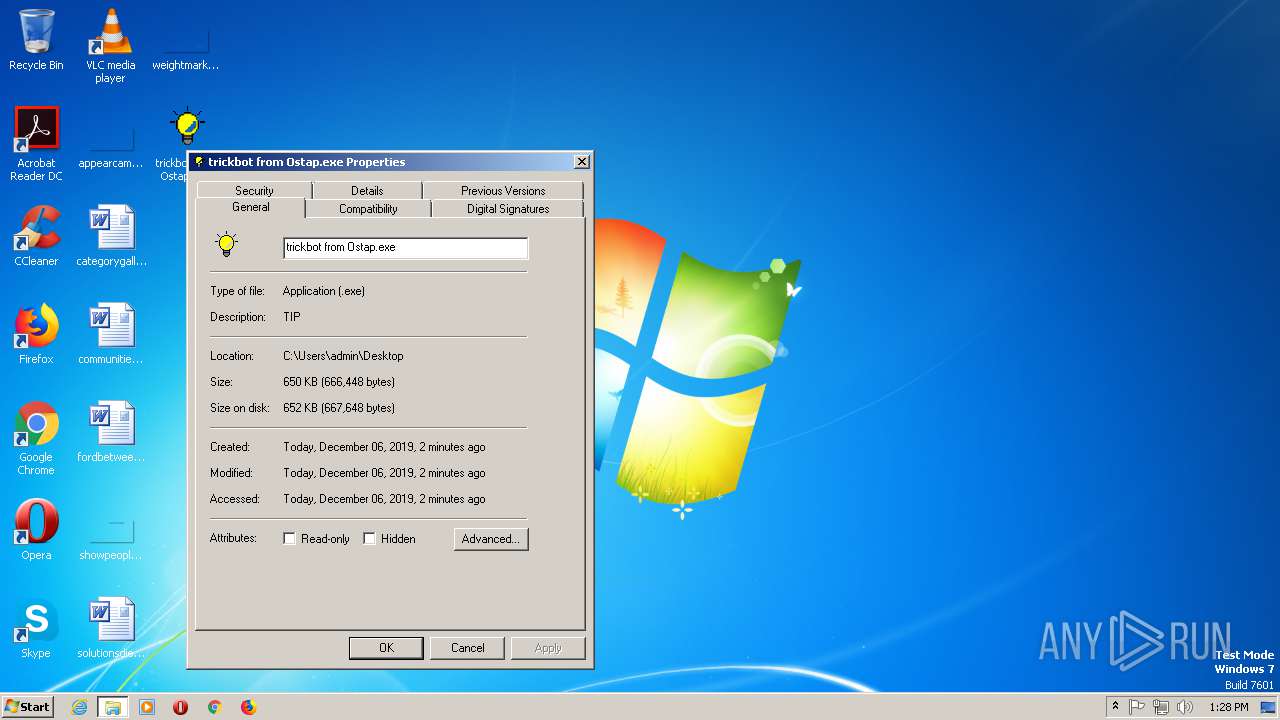
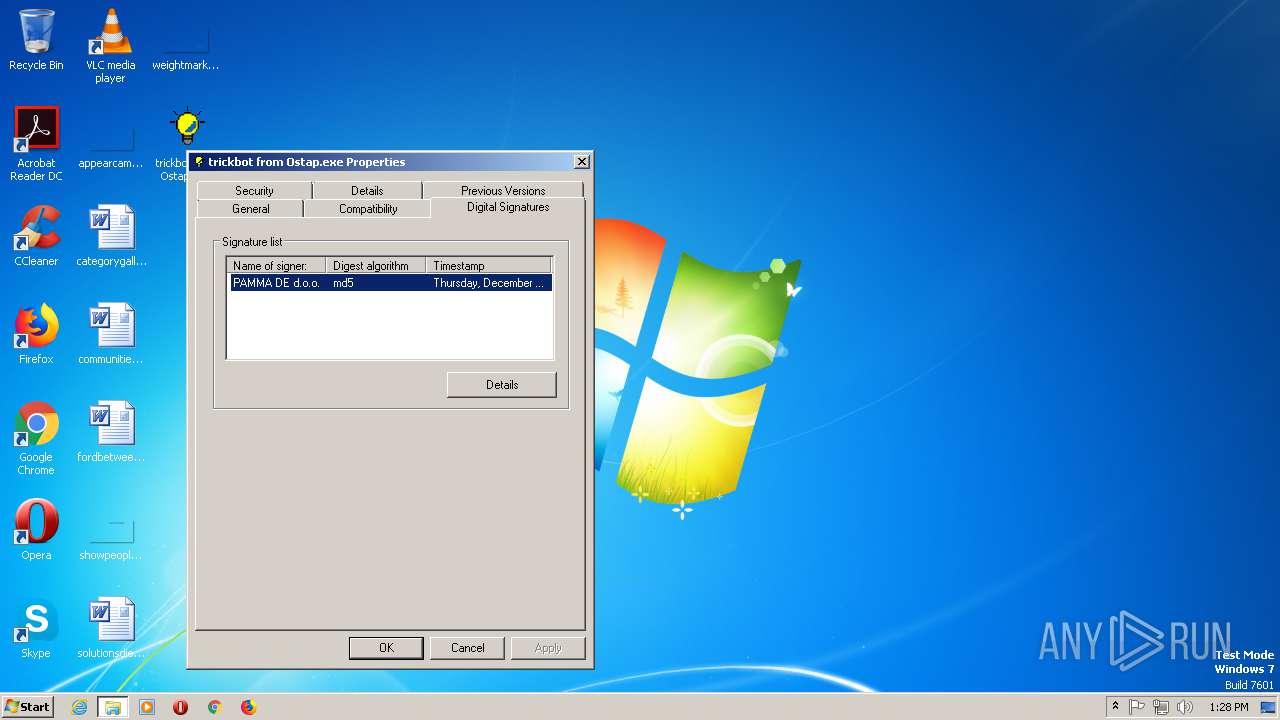
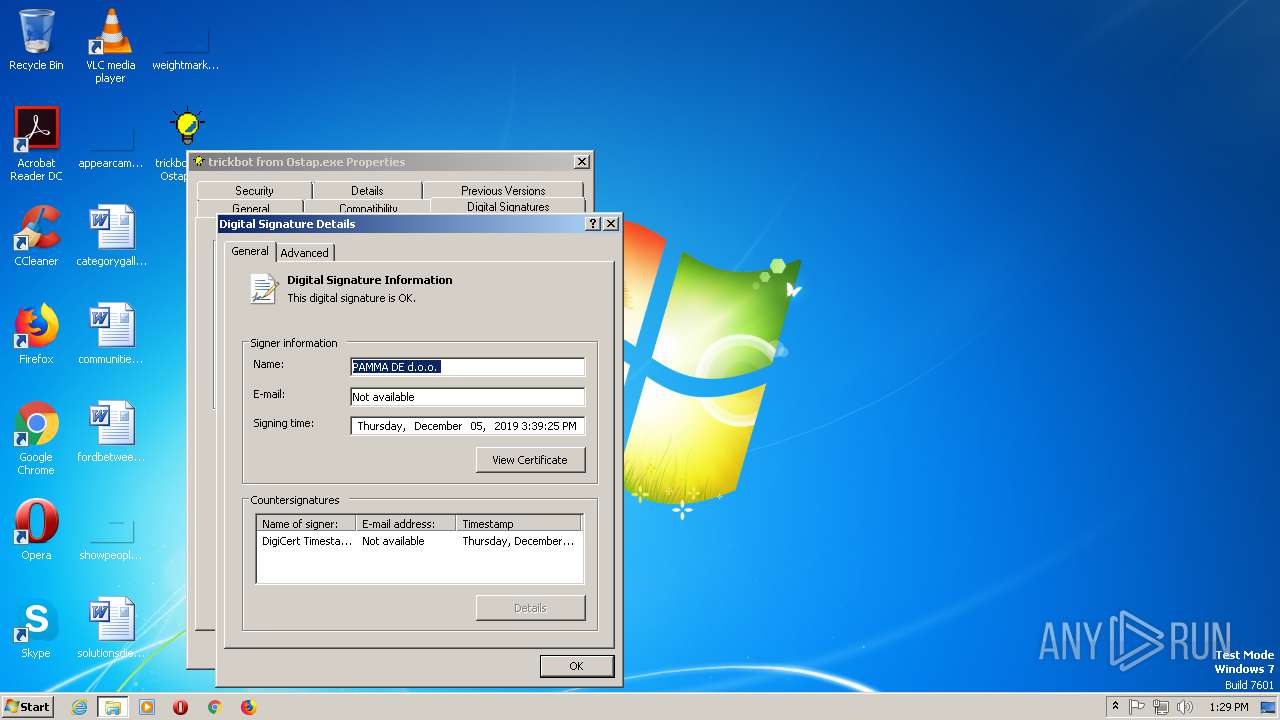
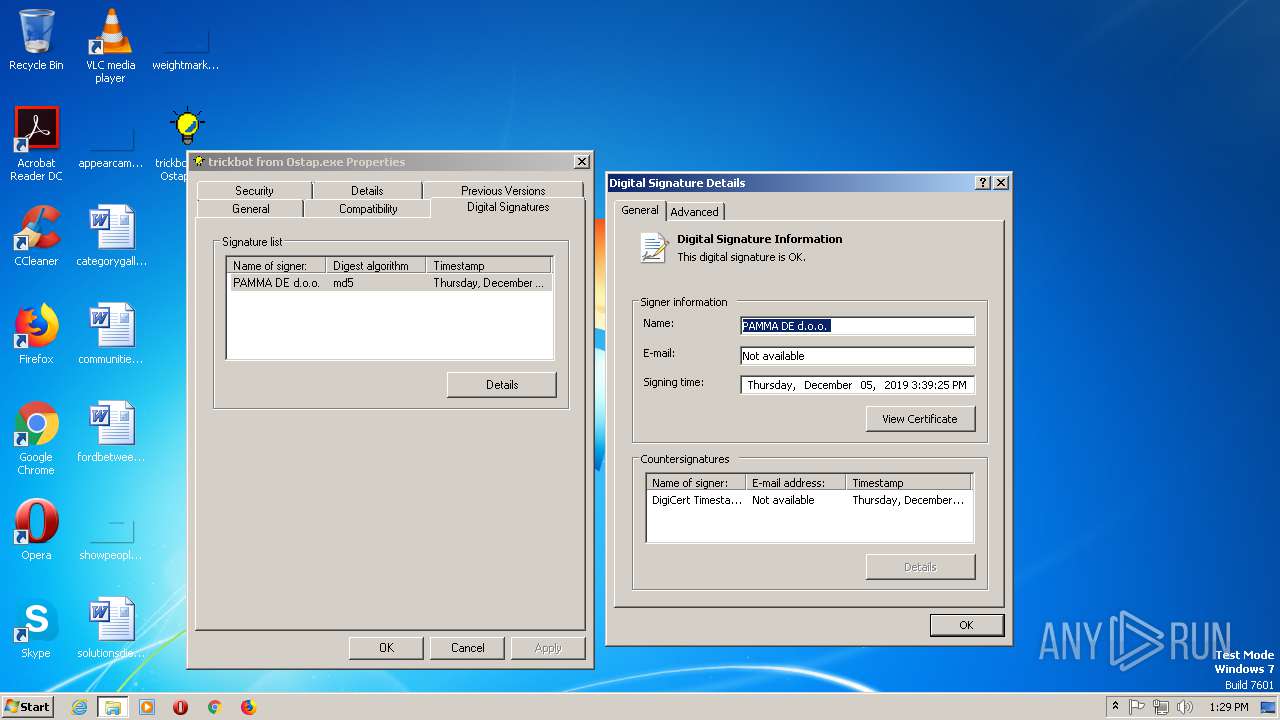
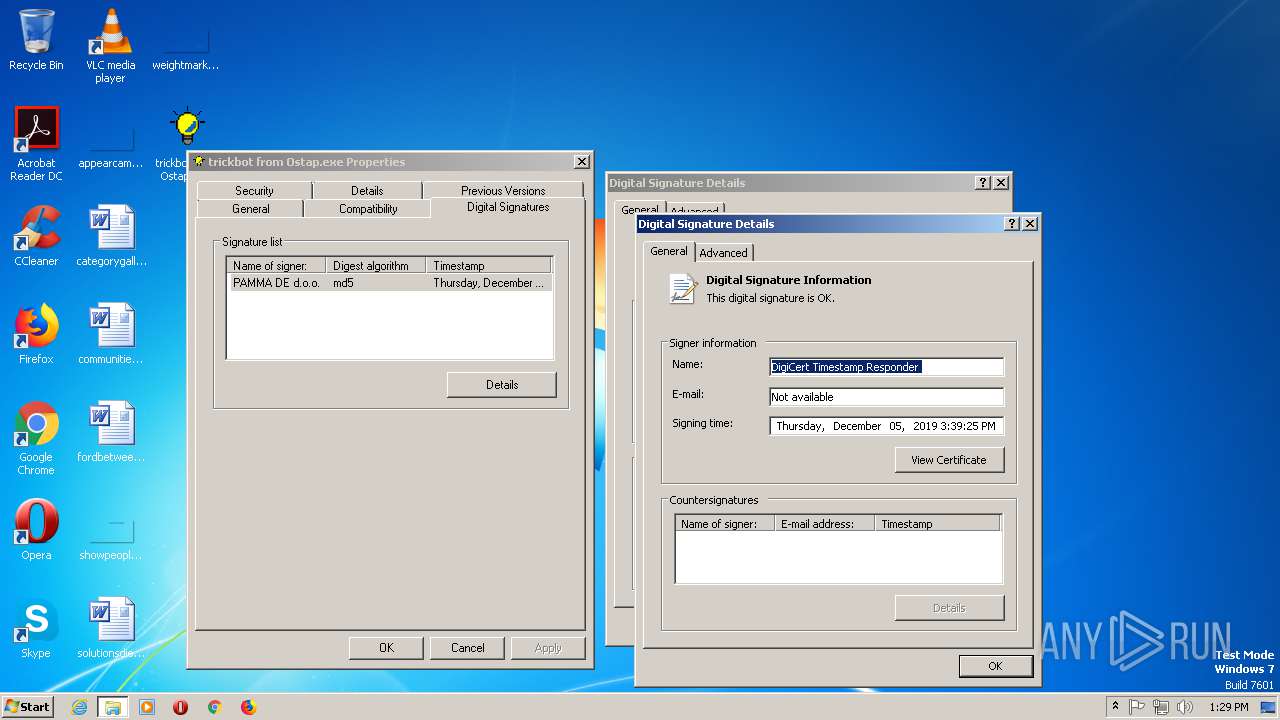
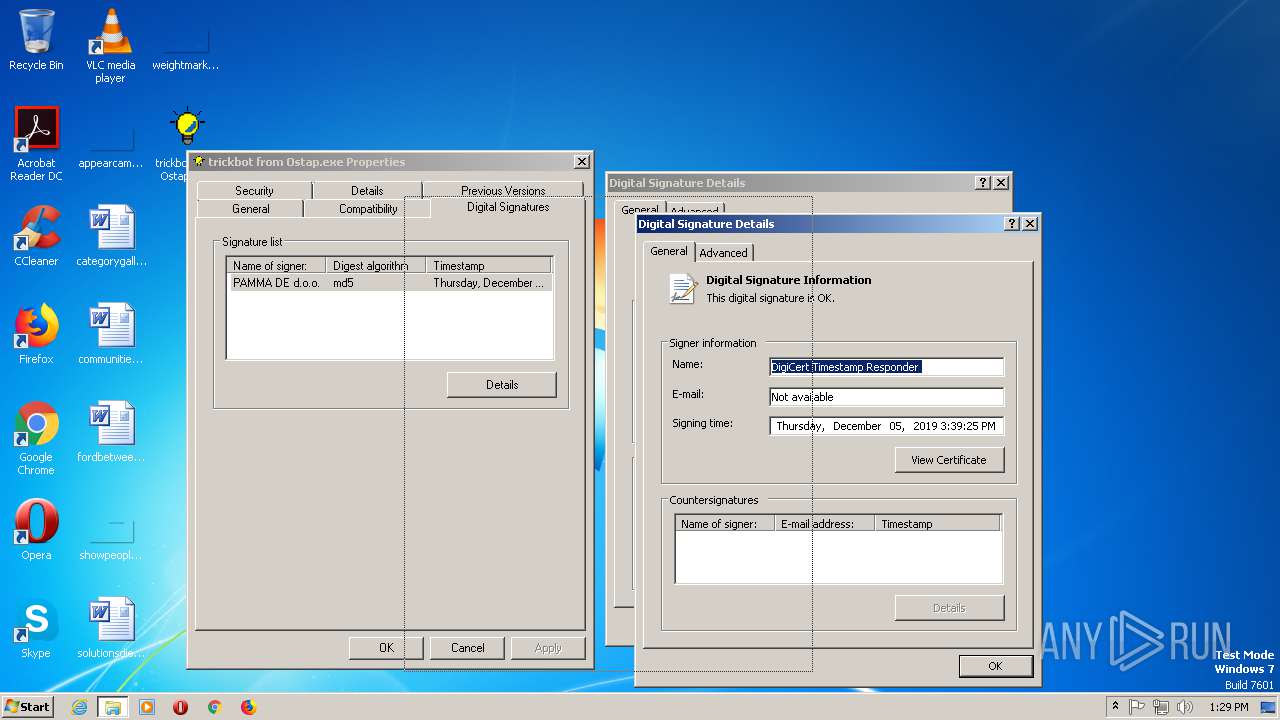
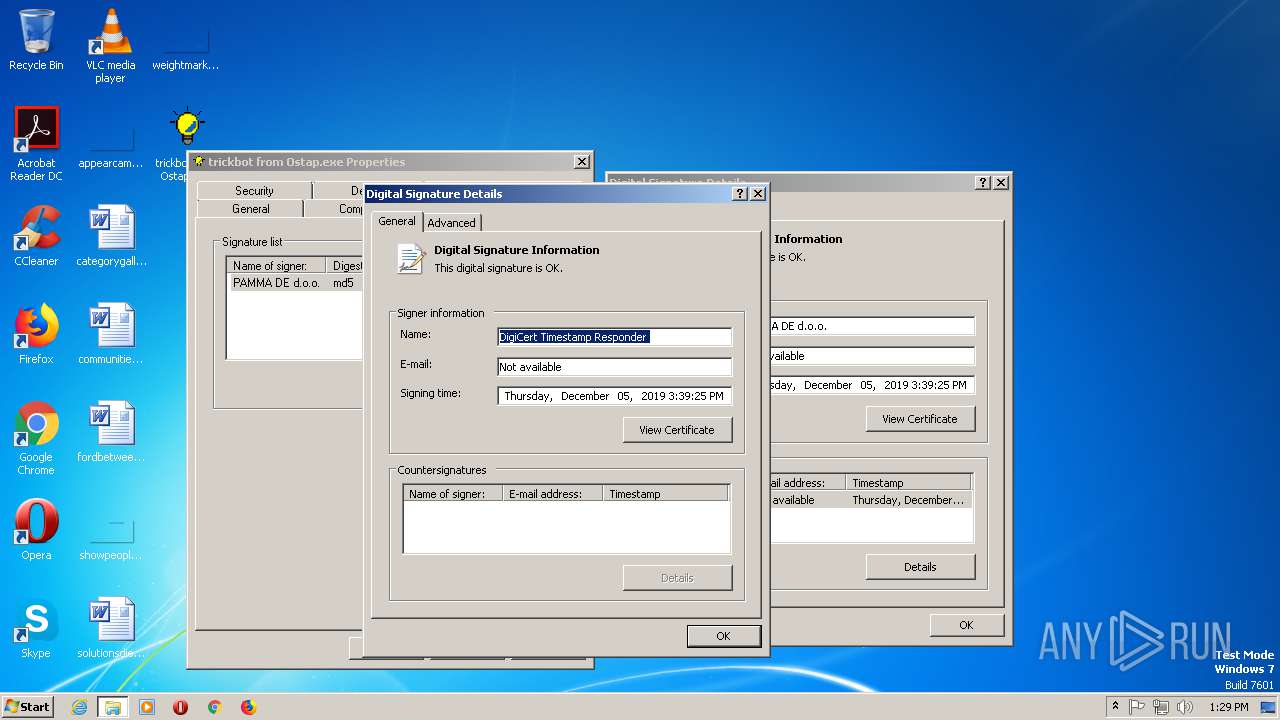
| File name: | trickbot from Ostap |
| Full analysis: | https://app.any.run/tasks/61798da2-6722-452d-b0c3-b8a9d6ce336b |
| Verdict: | Malicious activity |
| Threats: | TrickBot is an advanced banking trojan that attackers can use to steal payment credentials from the victims. It can redirect the victim to a fake banking cabinet and retrieve credentials typed in on the webpage. |
| Analysis date: | December 06, 2019, 13:26:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | F9216C50EEC98CA8DAC13DDF5D1F2C70 |
| SHA1: | FE66949B45B97B4F6615C89FE1441A4D758E05A9 |
| SHA256: | 9B0D4D9CFE5A69A10D449562A8A704318BB85BCE21B7B84549E7F6B05A4DC5DD |
| SSDEEP: | 12288:Y6t2DE6D60alZ5vNIppyp+ib37RY6d/1EWk8k+cIx:Z2DEL0a0ppzibLe6d/1EWo+H |
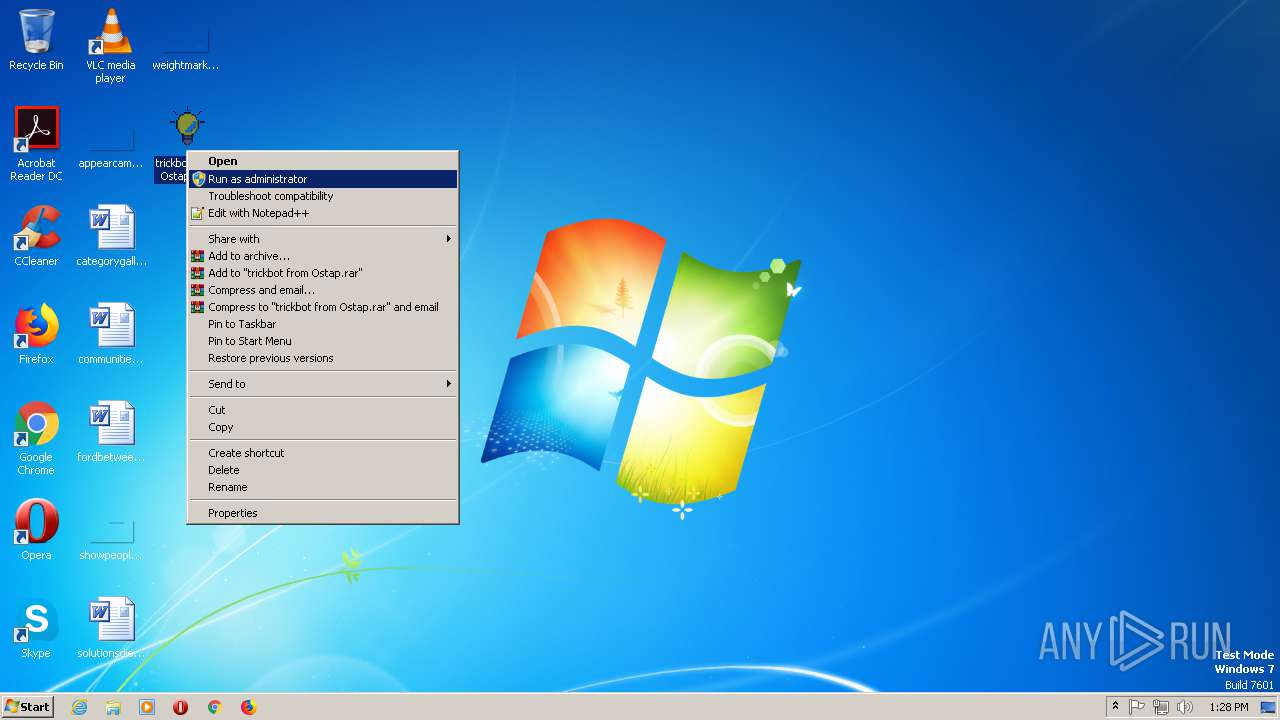
MALICIOUS
Uses SVCHOST.EXE for hidden code execution
- tticmbqt ftqo Qutar.exe (PID: 2732)
- trickbot from Ostap.exe (PID: 344)
Known privilege escalation attack
- DllHost.exe (PID: 2548)
Connects to CnC server
- svchost.exe (PID: 1652)
Loads the Task Scheduler COM API
- svchost.exe (PID: 1652)
TRICKBOT was detected
- svchost.exe (PID: 1652)
Changes settings of System certificates
- explorer.exe (PID: 1936)
SUSPICIOUS
Connects to unusual port
- svchost.exe (PID: 1652)
Executable content was dropped or overwritten
- svchost.exe (PID: 1652)
Creates files in the user directory
- svchost.exe (PID: 1652)
Executed via COM
- DllHost.exe (PID: 2548)
Executed via Task Scheduler
- tticmbqt ftqo Qutar.exe (PID: 1260)
Reads the machine GUID from the registry
- svchost.exe (PID: 1652)
- svchost.exe (PID: 2744)
- explorer.exe (PID: 1936)
Searches for installed software
- svchost.exe (PID: 1652)
INFO
Reads settings of System Certificates
- svchost.exe (PID: 1652)
- explorer.exe (PID: 1936)
Dropped object may contain Bitcoin addresses
- svchost.exe (PID: 1652)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (35) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (30.9) |
| .scr | | | Windows screen saver (14.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (7.3) |
| .exe | | | Win32 Executable (generic) (5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:12:05 16:28:27+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 5 |
| CodeSize: | 310784 |
| InitializedDataSize: | 319488 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x6a10 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.2.0.0 |
| ProductVersionNumber: | 1.2.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Private build, Special build |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | ZZ. Software (Bart Roelant) |
| FileDescription: | TIP MFC Application |
| FileVersion: | 1, 2, 0, 0 |
| InternalName: | TIP |
| LegalCopyright: | No Copyright © 1995 |
| OriginalFileName: | TIP.EXE |
| PrivateBuild: | 100 |
| ProductName: | TIP Application |
| ProductVersion: | 1, 2, 0, 0 |
| SpecialBuild: | 100 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Dec-2019 15:28:27 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | ZZ. Software (Bart Roelant) |
| FileDescription: | TIP MFC Application |
| FileVersion: | 1, 2, 0, 0 |
| InternalName: | TIP |
| LegalCopyright: | No Copyright © 1995 |
| OriginalFilename: | TIP.EXE |
| PrivateBuild: | 100 |
| ProductName: | TIP Application |
| ProductVersion: | 1, 2, 0, 0 |
| SpecialBuild: | 100 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 05-Dec-2019 15:28:27 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0004BCE0 | 0x0004BE00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.34805 |
.rdata | 0x0004D000 | 0x0000D753 | 0x0000D800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.659 |
.data | 0x0005B000 | 0x00009984 | 0x00006200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.6654 |
.idata | 0x00065000 | 0x0000329C | 0x00003400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.80213 |
.rsrc | 0x00069000 | 0x000313E4 | 0x00031400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.85212 |
.reloc | 0x0009B000 | 0x00005D52 | 0x00005E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.09522 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.43609 | 820 | Latin 1 / Western European | English - United States | RT_VERSION |
2 | 2.17367 | 296 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 2.4028 | 744 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 2.68898 | 296 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 3.02695 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
6 | 2.74274 | 180 | Latin 1 / Western European | English - United States | RT_CURSOR |
9 | 3.32391 | 702 | Latin 1 / Western European | English - United States | RT_STRING |
100 | 3.40869 | 448 | Latin 1 / Western European | English - United States | RT_DIALOG |
105 | 3.36166 | 404 | Latin 1 / Western European | English - United States | RT_DIALOG |
128 | 2.37086 | 34 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
WINSPOOL.DRV |
comdlg32.dll |
Total processes
45
Monitored processes
7
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 344 | "C:\Users\admin\Desktop\trickbot from Ostap.exe" | C:\Users\admin\Desktop\trickbot from Ostap.exe | — | explorer.exe | |||||||||||
User: admin Company: ZZ. Software (Bart Roelant) Integrity Level: MEDIUM Description: TIP MFC Application Exit code: 0 Version: 1, 2, 0, 0 Modules
| |||||||||||||||
| 1260 | "C:\Users\admin\AppData\Roaming\syshealth\tticmbqt ftqo Qutar.exe" | C:\Users\admin\AppData\Roaming\syshealth\tticmbqt ftqo Qutar.exe | — | taskeng.exe | |||||||||||
User: admin Company: ZZ. Software (Bart Roelant) Integrity Level: MEDIUM Description: TIP MFC Application Exit code: 0 Version: 1, 2, 0, 0 Modules
| |||||||||||||||
| 1652 | C:\Windows\system32\svchost.exe | C:\Windows\system32\svchost.exe | trickbot from Ostap.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1936 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2548 | C:\Windows\SysWOW64\DllHost.exe /Processid:{3E5FC7F9-9A51-4367-9063-A120244FBEC7} | C:\Windows\SysWOW64\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2732 | "C:\Users\admin\AppData\Roaming\syshealth\tticmbqt ftqo Qutar.exe" | C:\Users\admin\AppData\Roaming\syshealth\tticmbqt ftqo Qutar.exe | — | DllHost.exe | |||||||||||
User: admin Company: ZZ. Software (Bart Roelant) Integrity Level: HIGH Description: TIP MFC Application Exit code: 0 Version: 1, 2, 0, 0 Modules
| |||||||||||||||
| 2744 | C:\Windows\system32\svchost.exe | C:\Windows\system32\svchost.exe | — | tticmbqt ftqo Qutar.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
4 198
Read events
4 136
Write events
62
Delete events
0
Modification events
| (PID) Process: | (1652) svchost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1936) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2548) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2548) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2548) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2548) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1936) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | @sendmail.dll,-21 |
Value: Desktop (create shortcut) | |||
| (PID) Process: | (1936) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | @zipfldr.dll,-10148 |
Value: Compressed (zipped) folder | |||
| (PID) Process: | (1936) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | @sendmail.dll,-4 |
Value: Mail recipient | |||
| (PID) Process: | (1936) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\FXSRESM.dll,-120 |
Value: Fax recipient | |||
Executable files
1
Suspicious files
3
Text files
1
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1652 | svchost.exe | C:\Users\admin\AppData\Local\Temp\Cab586E.tmp | — | |
MD5:— | SHA256:— | |||
| 1652 | svchost.exe | C:\Users\admin\AppData\Local\Temp\Tar586F.tmp | — | |
MD5:— | SHA256:— | |||
| 1652 | svchost.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:— | SHA256:— | |||
| 1652 | svchost.exe | C:\Users\admin\AppData\Roaming\syshealth\tips.ini | text | |
MD5:— | SHA256:— | |||
| 1652 | svchost.exe | C:\Users\admin\AppData\Roaming\syshealth\tticmbqt ftqo Qutar.exe | executable | |
MD5:— | SHA256:— | |||
| 1936 | explorer.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E0968A1E3A40D2582E7FD463BAEB59CD | der | |
MD5:— | SHA256:— | |||
| 1936 | explorer.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E0968A1E3A40D2582E7FD463BAEB59CD | binary | |
MD5:— | SHA256:— | |||
| 1652 | svchost.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:5AD071A3917588E8CD883B123B395B21 | SHA256:DE62965C15528DA598B0079D2D20D953DD6F71B13A23807BFF0666D03F69C0FA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
5
DNS requests
5
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1936 | explorer.exe | GET | 200 | 91.199.212.52:80 | http://crt.usertrust.com/USERTrustRSAAddTrustCA.crt | GB | der | 1.37 Kb | whitelisted |
1652 | svchost.exe | GET | 200 | 23.23.83.153:443 | https://api.ipify.org/?format=text | US | text | 12 b | shared |
1652 | svchost.exe | GET | 200 | 8.253.204.120:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?a26f2fbd21f14c7c | US | compressed | 57.4 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1652 | svchost.exe | 181.196.207.202:449 | — | CORPORACION NACIONAL DE TELECOMUNICACIONES - CNT EP | EC | malicious |
1652 | svchost.exe | 8.253.204.120:80 | ctldl.windowsupdate.com | Global Crossing | US | suspicious |
1652 | svchost.exe | 23.23.83.153:443 | api.ipify.org | Amazon.com, Inc. | US | malicious |
1652 | svchost.exe | 116.203.16.95:80 | ip.anysrc.net | 334,Udyog Vihar | IN | malicious |
1936 | explorer.exe | 91.199.212.52:80 | crt.usertrust.com | Comodo CA Ltd | GB | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ctldl.windowsupdate.com |
| whitelisted |
ip.anysrc.net |
| shared |
dns.msftncsi.com |
| shared |
api.ipify.org |
| shared |
crt.usertrust.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1652 | svchost.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 6 |
1652 | svchost.exe | Not Suspicious Traffic | ET POLICY OpenSSL Demo CA - Internet Widgits Pty (O) |
2 ETPRO signatures available at the full report