| URL: | https://tr.ee/HWP1nd |
| Full analysis: | https://app.any.run/tasks/bb9fe315-ac4a-4a6b-a5f7-a50ba3ef16a3 |
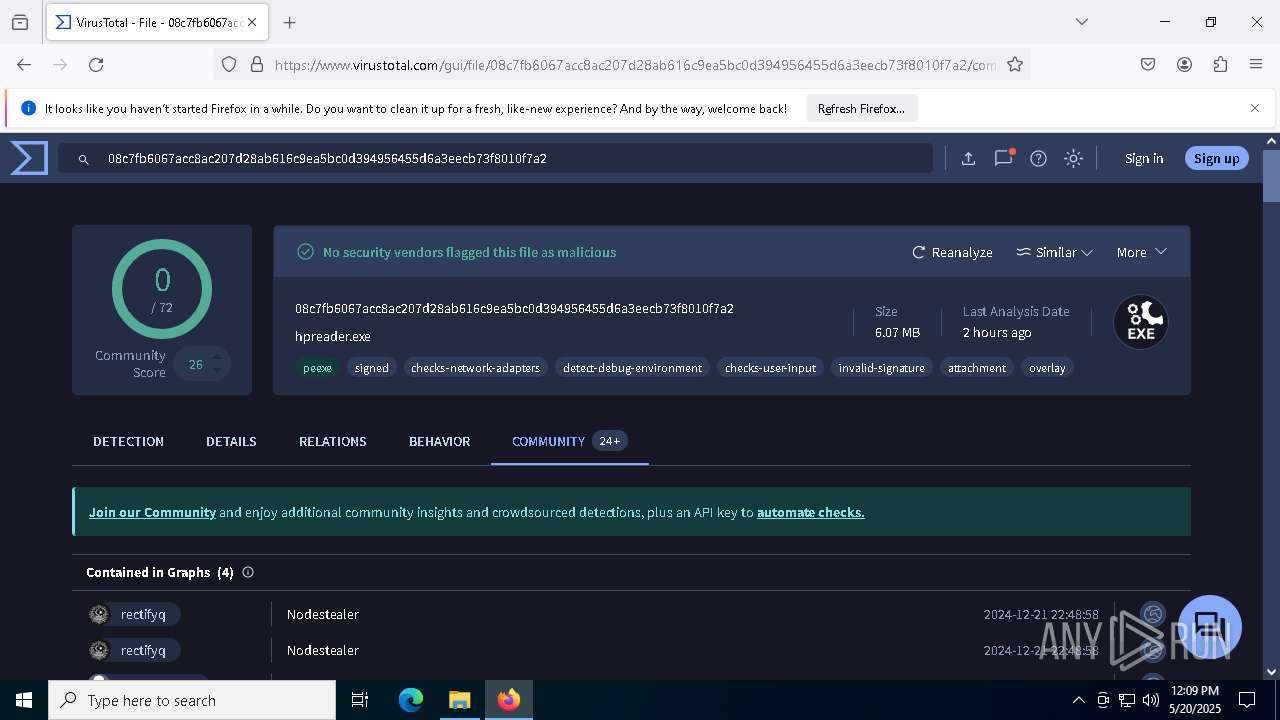
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | May 20, 2025, 12:06:45 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 3778255CAAA89FA14110899B836A3889 |
| SHA1: | B37B26C9AEB67E9E3D74F59BEE9A57F18B5094F6 |
| SHA256: | 9AFCF23AE5F5BCA396383AC850195851EAEBCBEC98211710FCF1A2600BD94E05 |
| SSDEEP: | 3:N8fLAZ1:2jg |
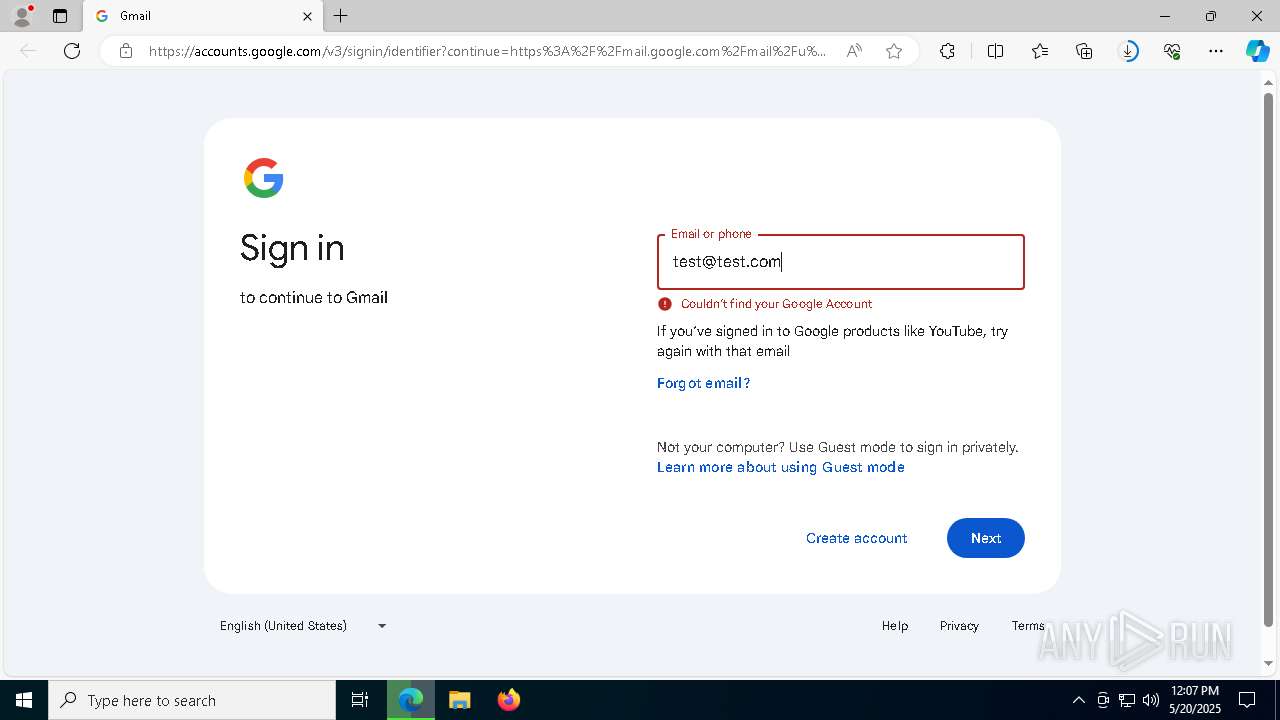
MALICIOUS
ASYNCRAT has been detected (SURICATA)
- RegAsm.exe (PID: 9584)
Suspicious browser debugging (Possible cookie theft)
- chrome.exe (PID: 8304)
- msedge.exe (PID: 2416)
SUSPICIOUS
Likely accesses (executes) a file from the Public directory
- cmd.exe (PID: 7640)
- cmd.exe (PID: 9776)
- svchost.exe (PID: 8088)
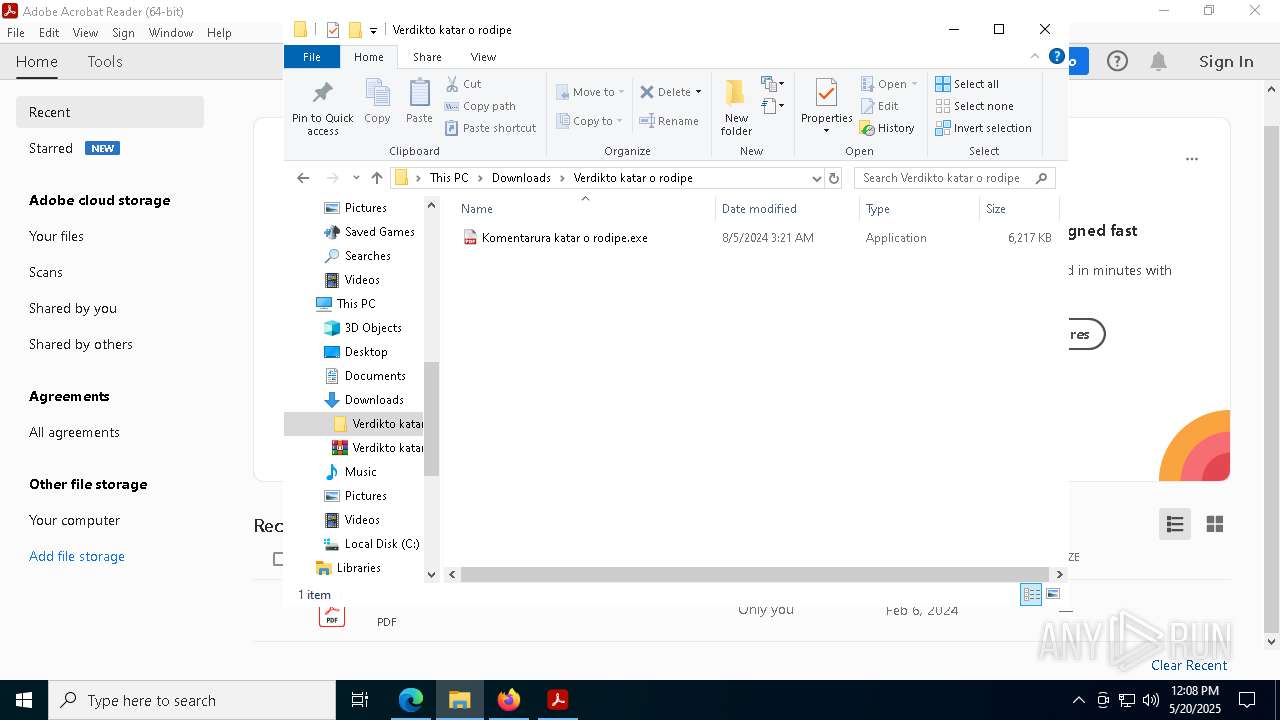
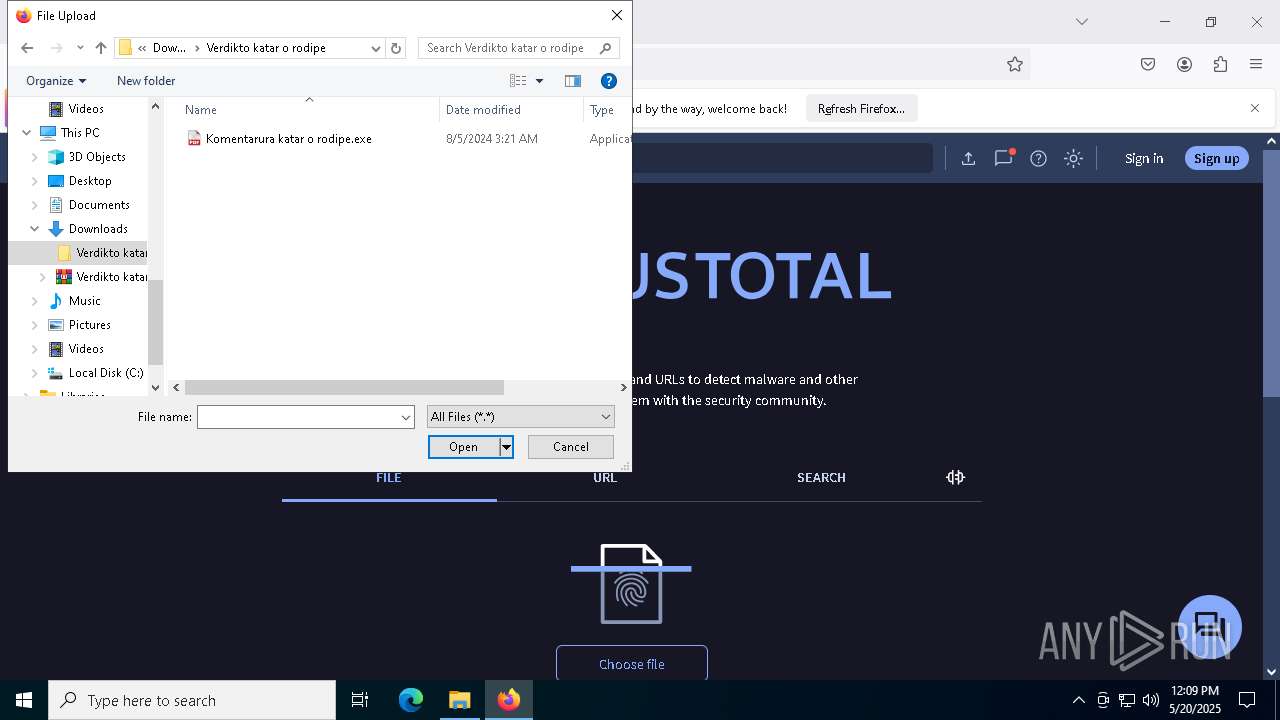
Starts CMD.EXE for commands execution
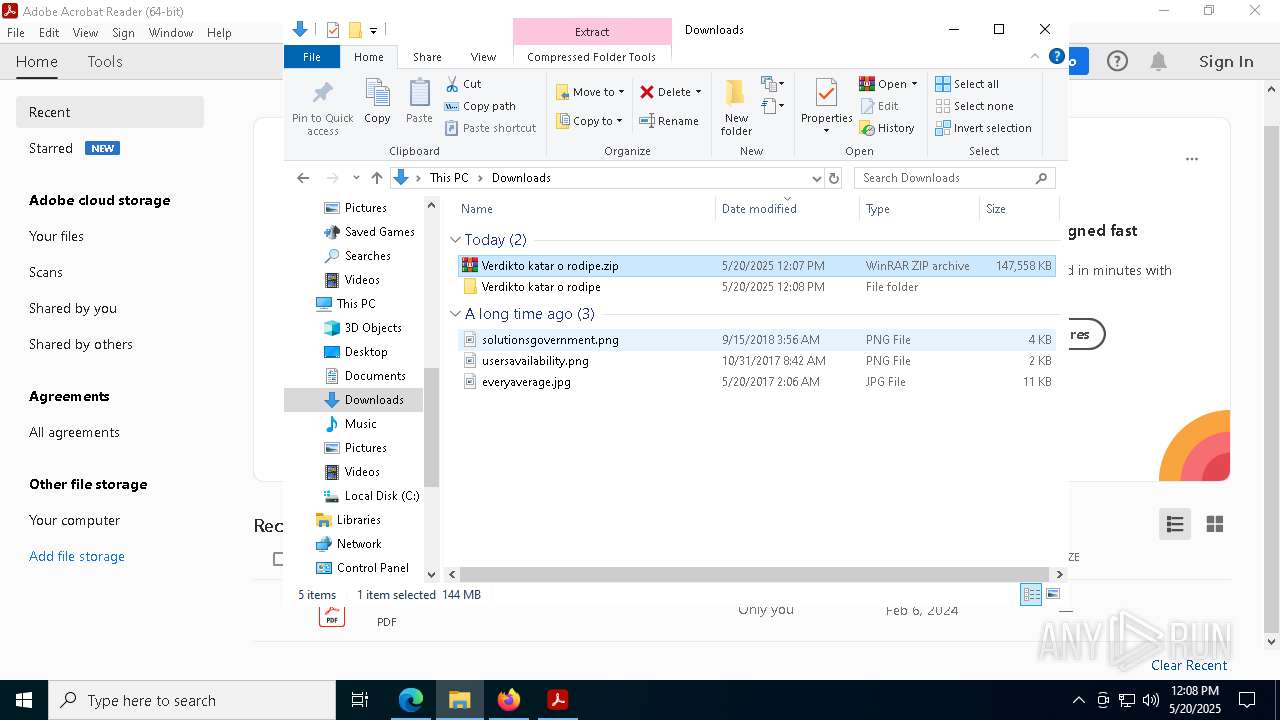
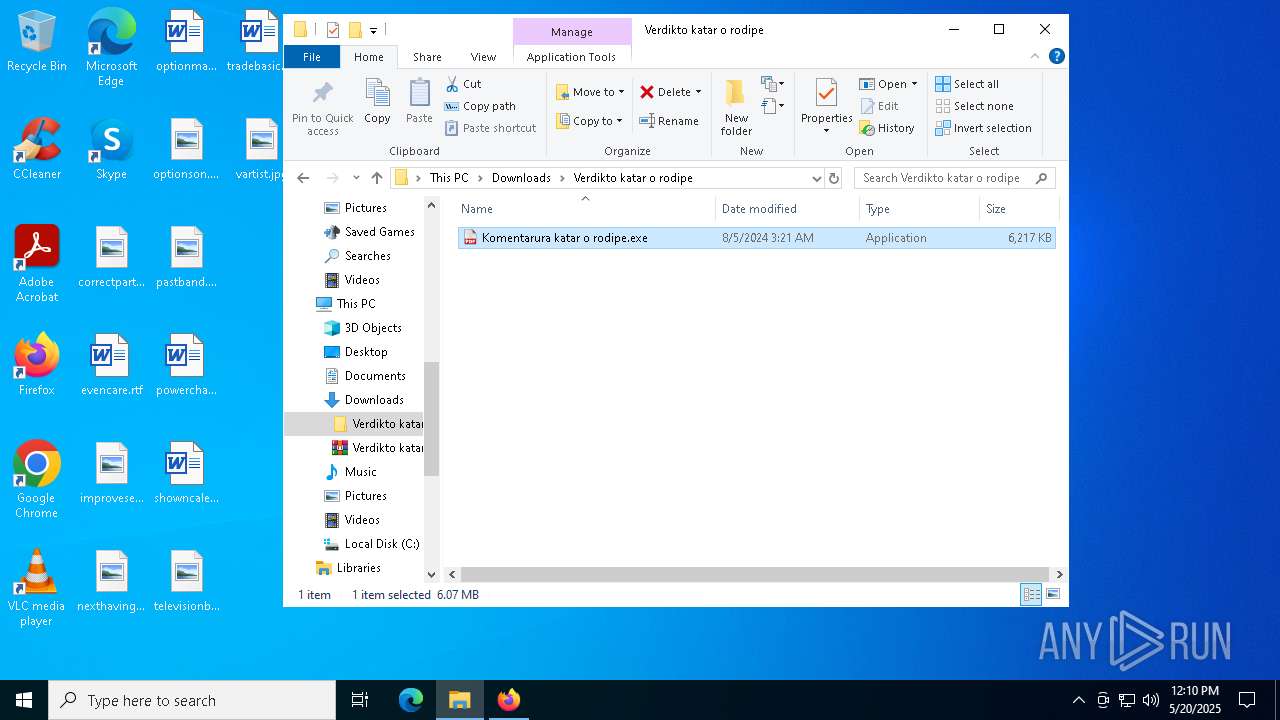
- Komentarura katar o rodipe.exe (PID: 7184)
- Komentarura katar o rodipe.exe (PID: 9756)
- svchost.exe (PID: 8088)
Reads security settings of Internet Explorer
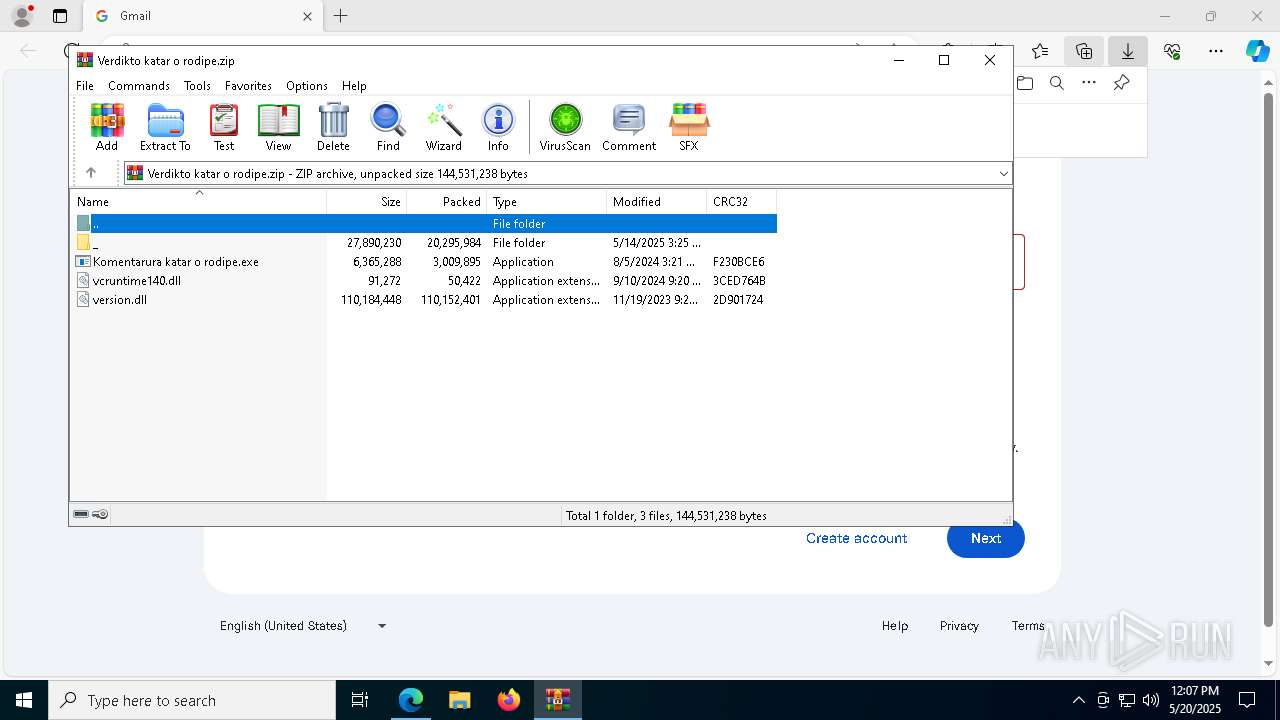
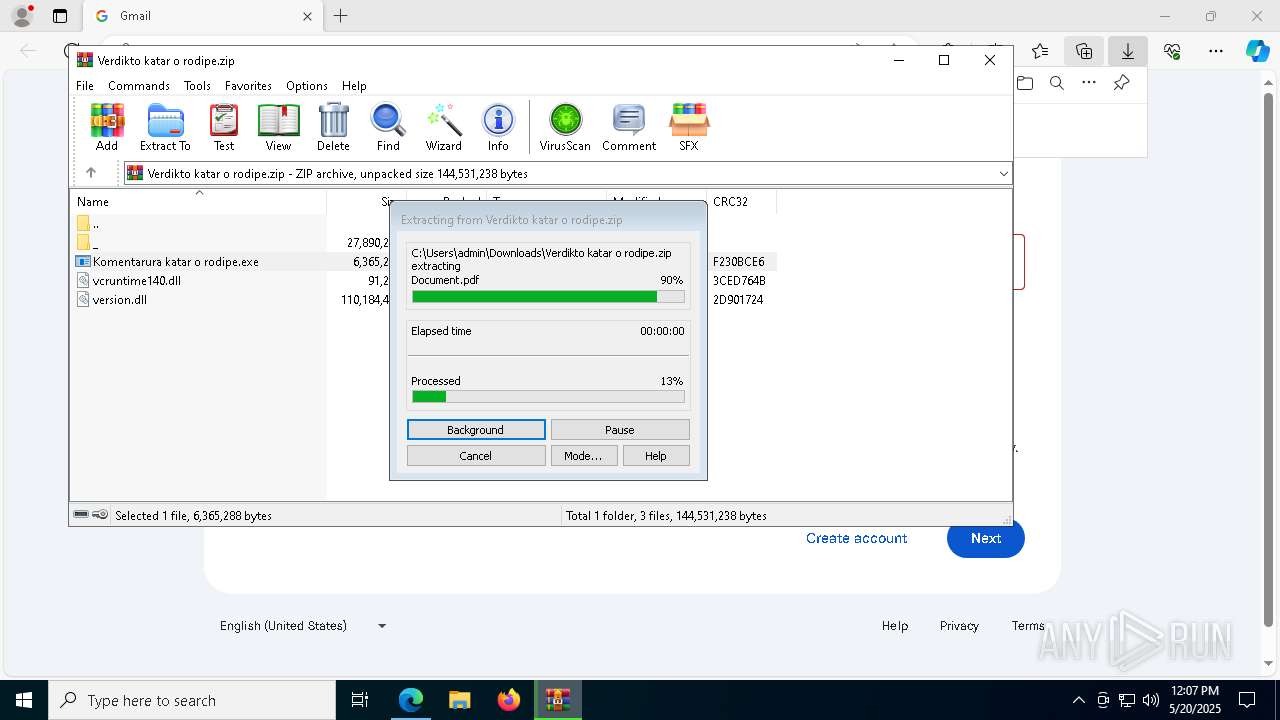
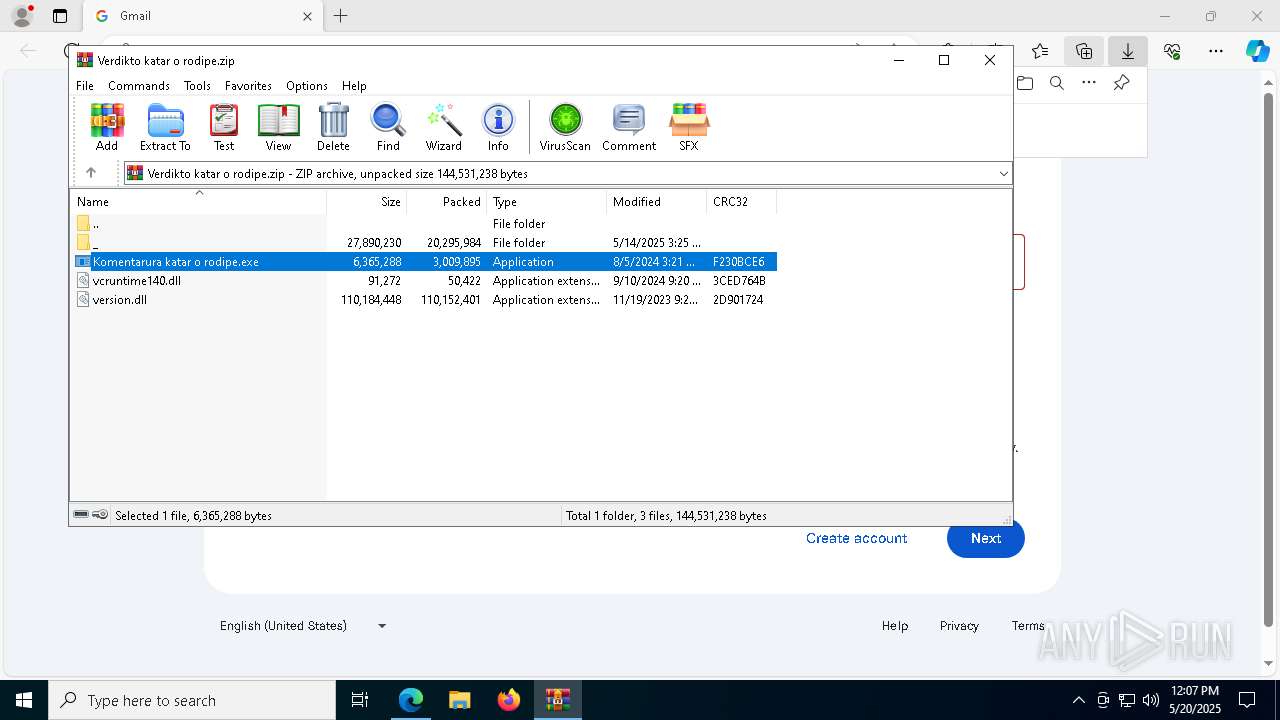
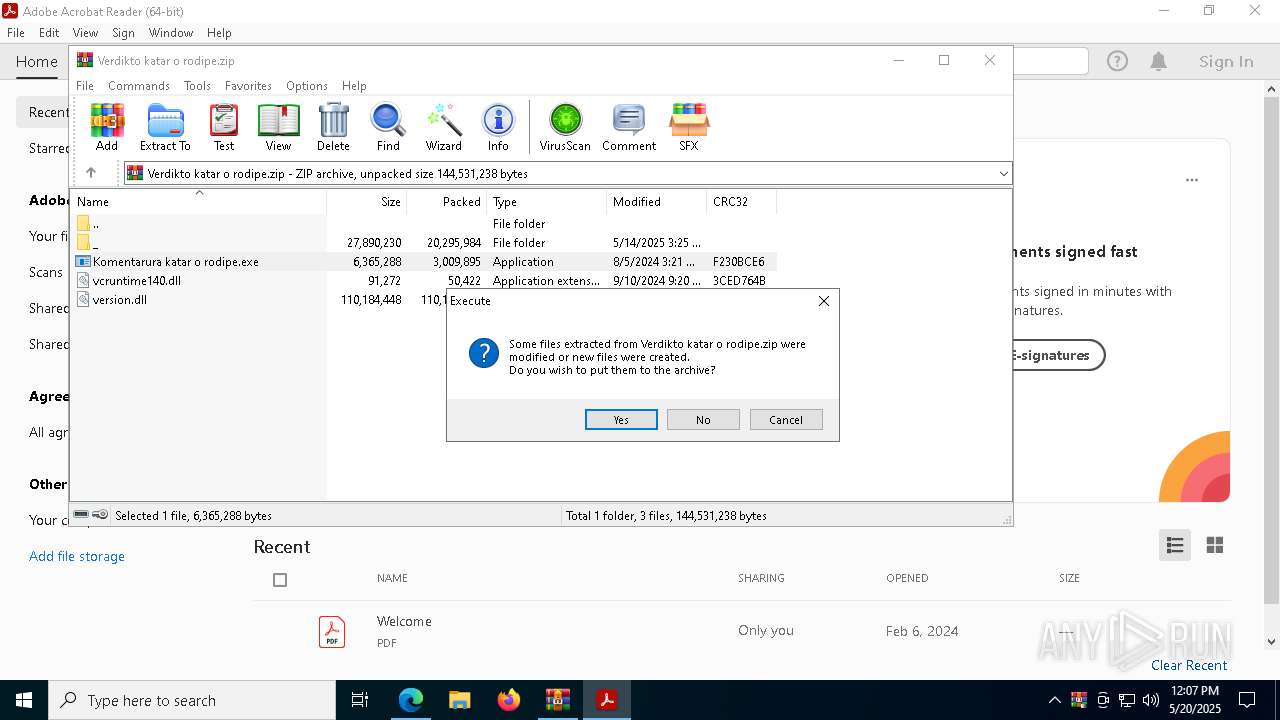
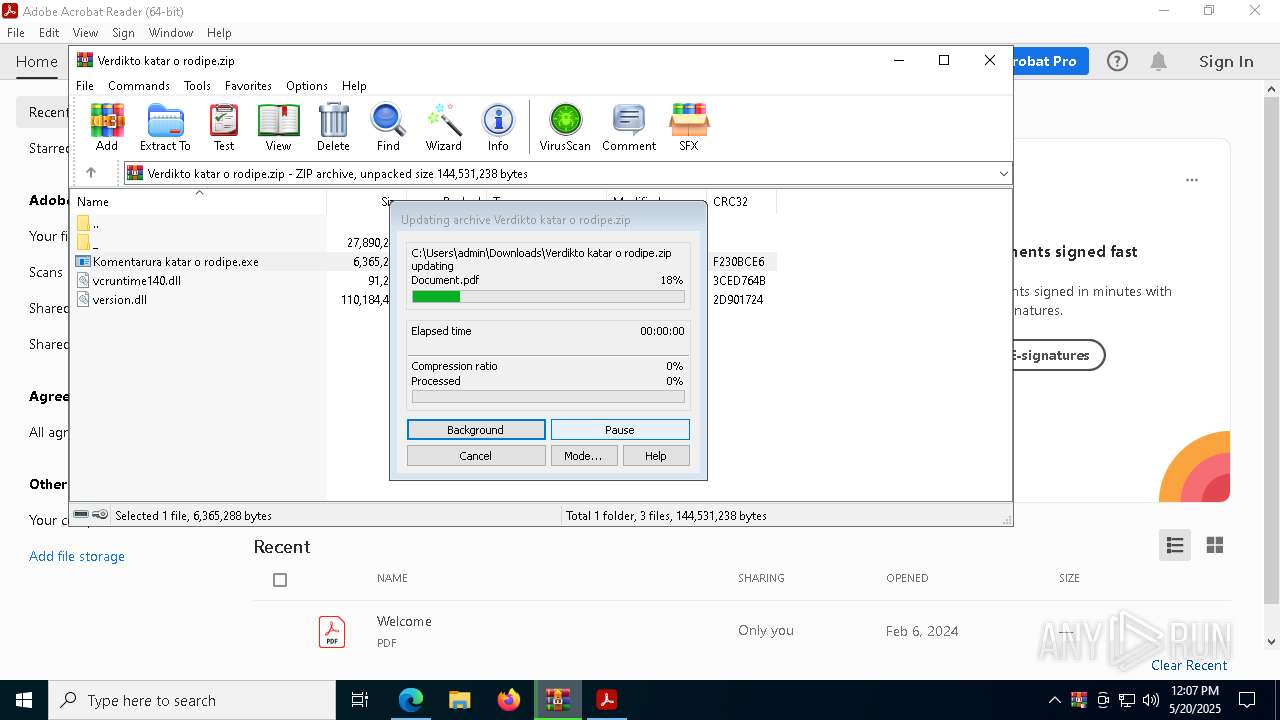
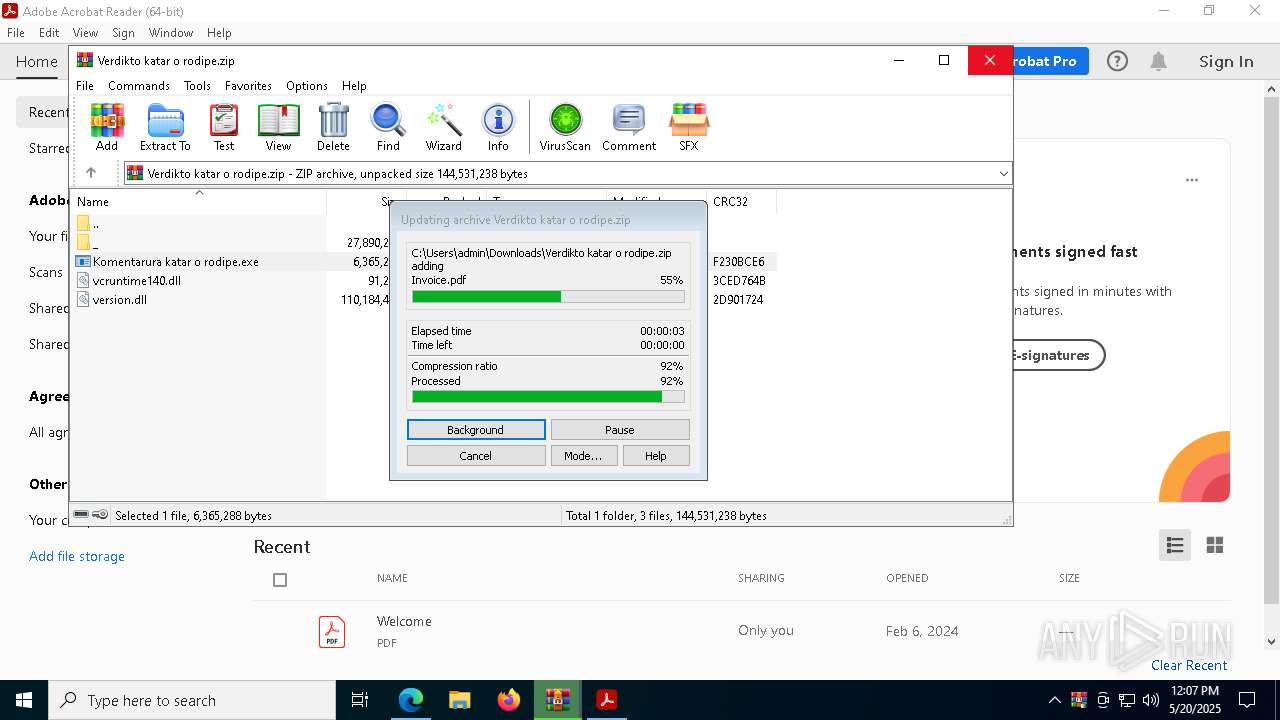
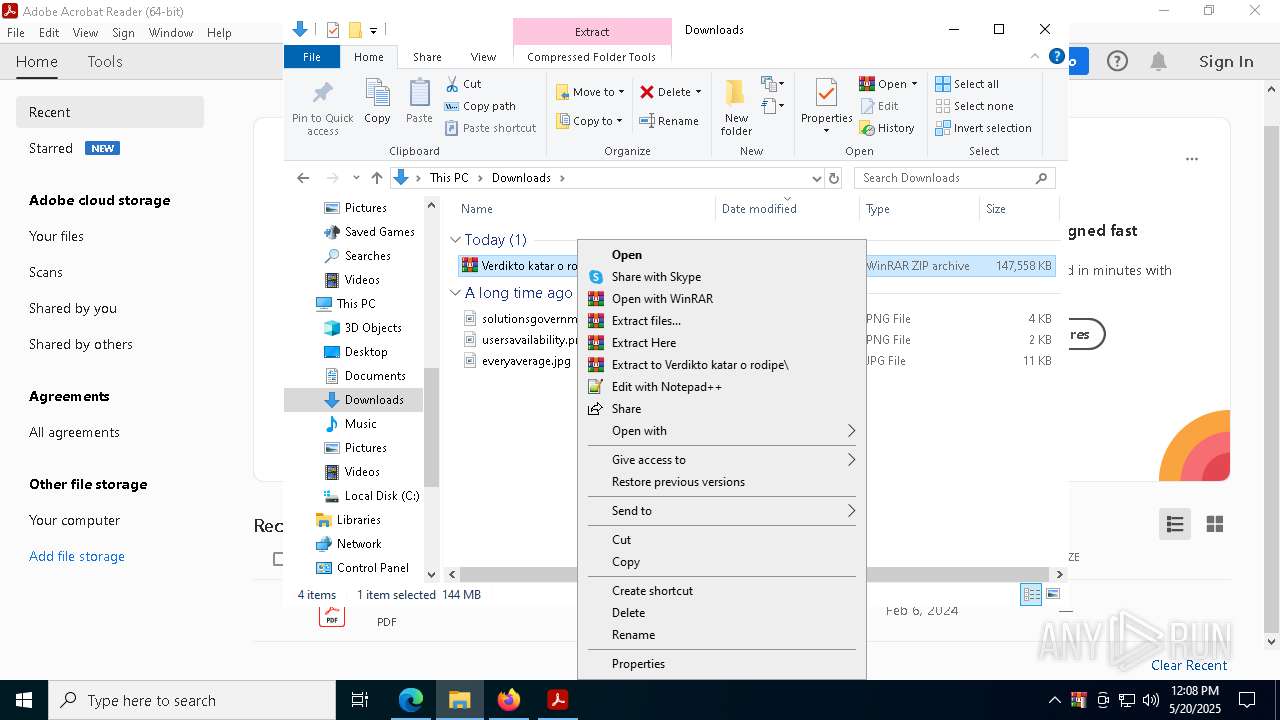
- WinRAR.exe (PID: 684)
Process drops legitimate windows executable
- WinRAR.exe (PID: 684)
- Images.png (PID: 7948)
- WinRAR.exe (PID: 9588)
Decoding a file from Base64 using CertUtil
- cmd.exe (PID: 7640)
- cmd.exe (PID: 9776)
Starts application with an unusual extension
- cmd.exe (PID: 7640)
The executable file from the user directory is run by the CMD process
- Images.png (PID: 7948)
Process drops python dynamic module
- Images.png (PID: 7948)
There is functionality for taking screenshot (YARA)
- Images.png (PID: 7948)
The process drops C-runtime libraries
- Images.png (PID: 7948)
Executable content was dropped or overwritten
- Images.png (PID: 7948)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- svchost.exe (PID: 8088)
Uses TASKKILL.EXE to kill Browsers
- cmd.exe (PID: 2240)
- cmd.exe (PID: 5772)
Checks for external IP
- svchost.exe (PID: 2196)
Uses TASKKILL.EXE to kill process
- svchost.exe (PID: 8088)
Get information on the list of running processes
- svchost.exe (PID: 8088)
Connects to unusual port
- RegAsm.exe (PID: 9584)
Contacting a server suspected of hosting an CnC
- RegAsm.exe (PID: 9584)
INFO
Checks supported languages
- identity_helper.exe (PID: 672)
- Komentarura katar o rodipe.exe (PID: 7184)
- Images.png (PID: 7948)
Reads Environment values
- identity_helper.exe (PID: 672)
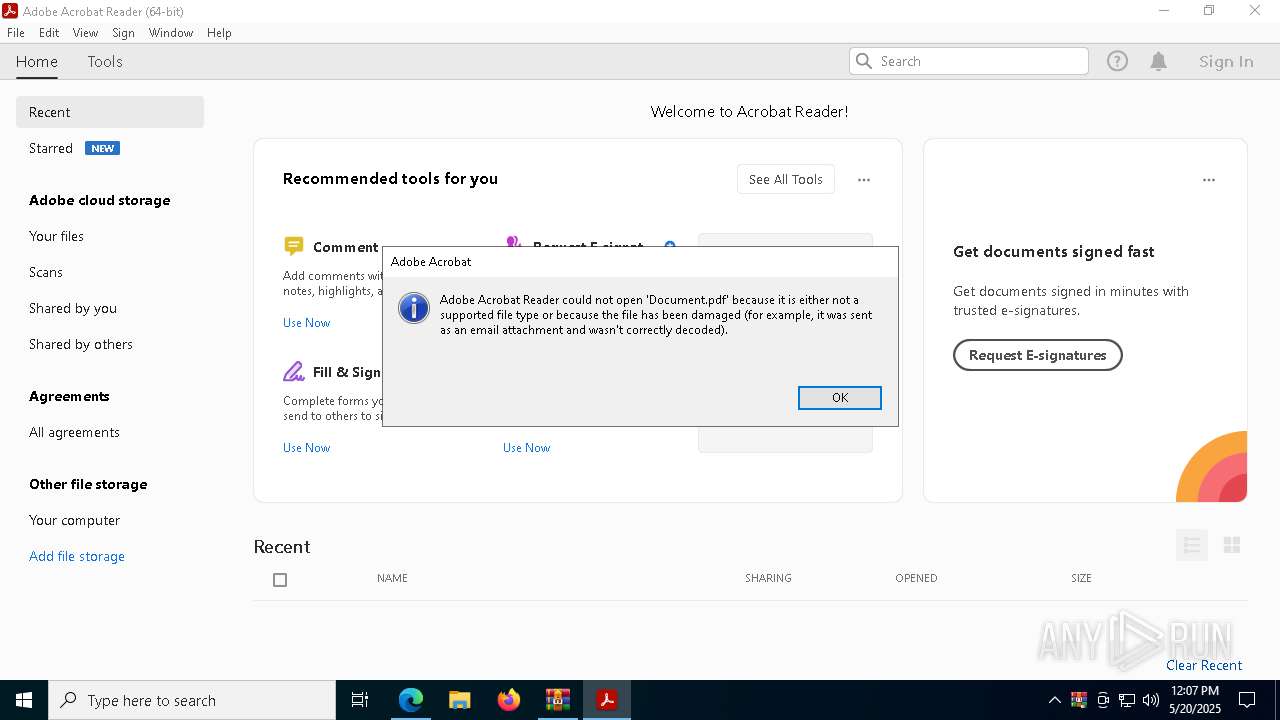
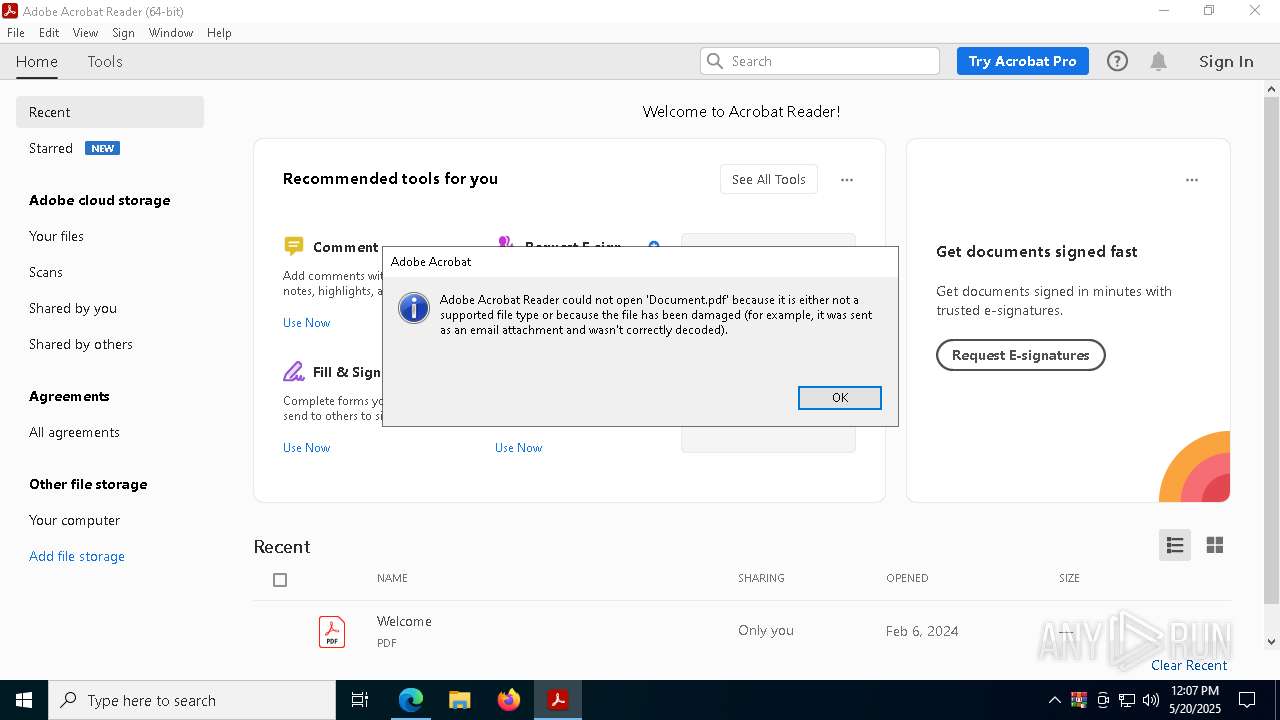
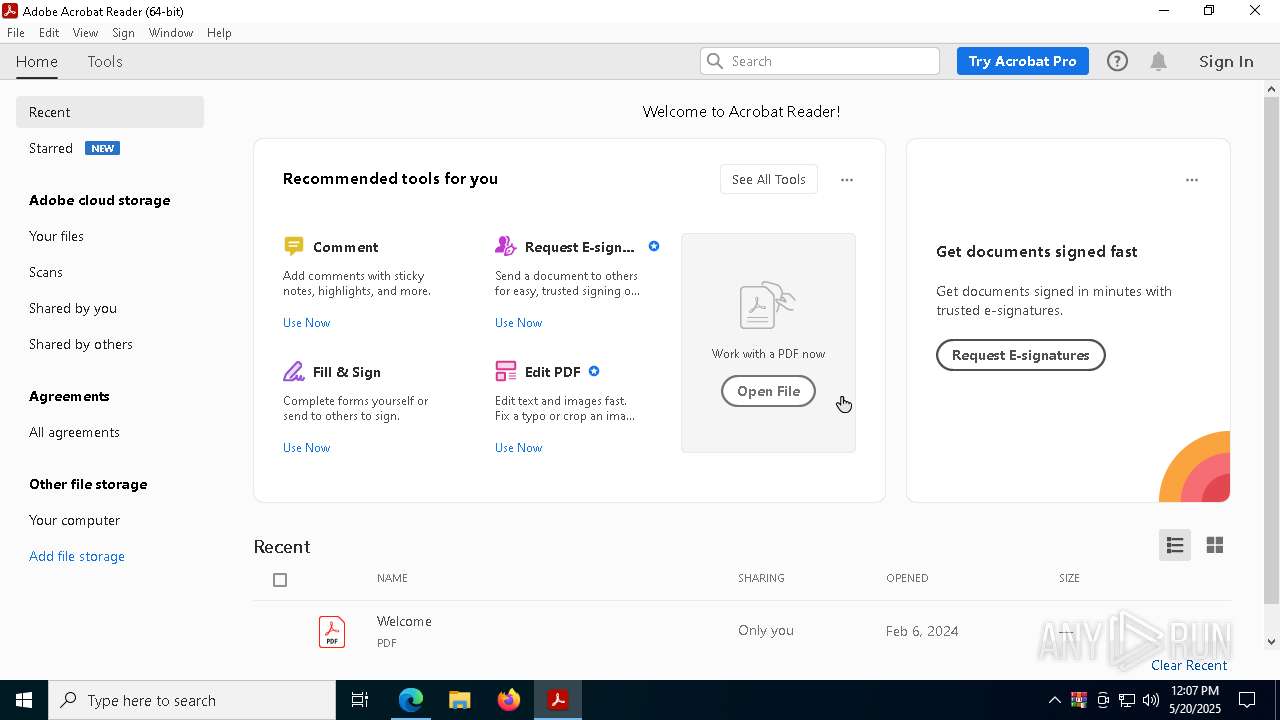
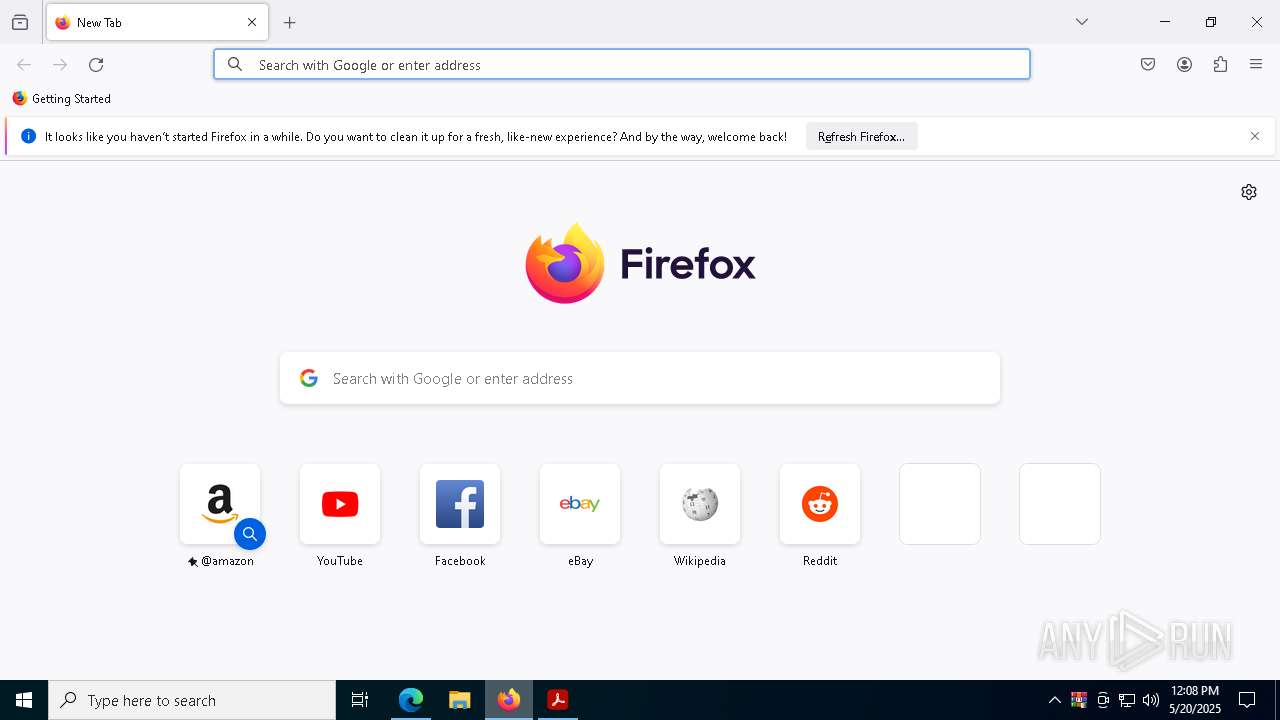
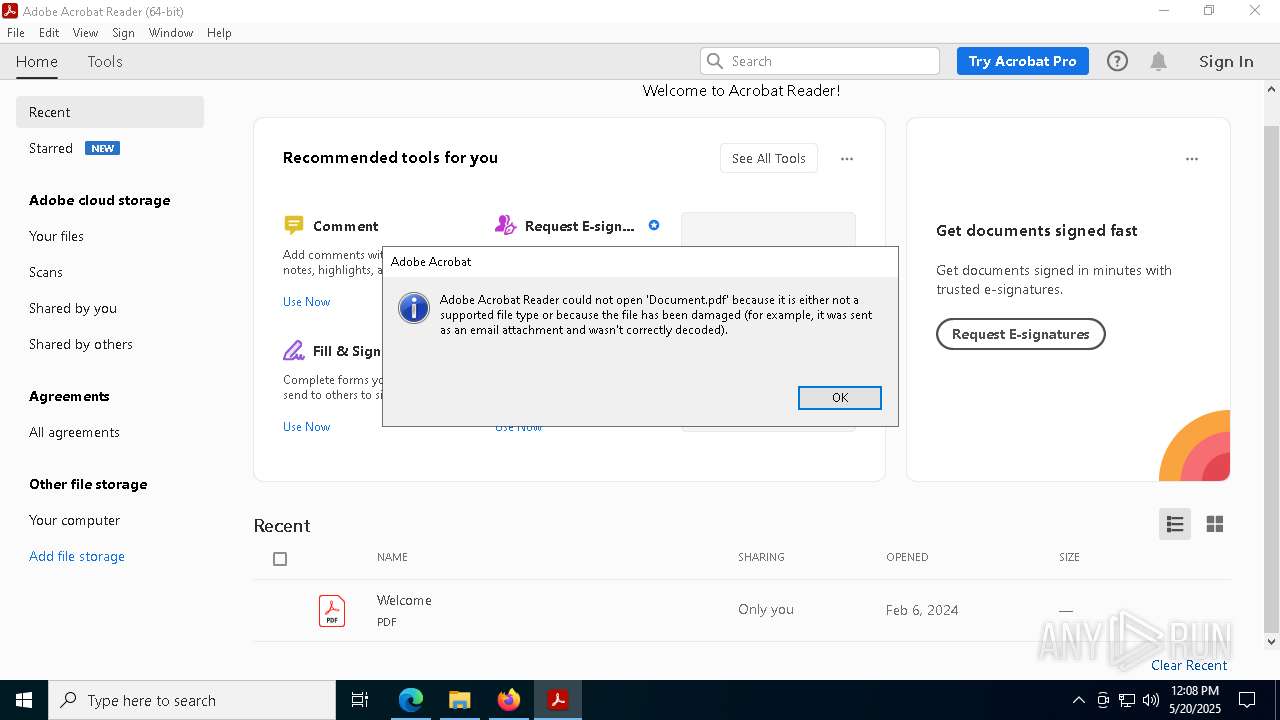
Application launched itself
- msedge.exe (PID: 2432)
- Acrobat.exe (PID: 1760)
- firefox.exe (PID: 8812)
- firefox.exe (PID: 8832)
- Acrobat.exe (PID: 9856)
- msedge.exe (PID: 2416)
- chrome.exe (PID: 8304)
- AcroCEF.exe (PID: 1324)
Reads the computer name
- identity_helper.exe (PID: 672)
- Images.png (PID: 7948)
The sample compiled with english language support
- WinRAR.exe (PID: 684)
- Images.png (PID: 7948)
- WinRAR.exe (PID: 9588)
Reads Microsoft Office registry keys
- msedge.exe (PID: 2432)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 684)
- WinRAR.exe (PID: 9588)
Create files in a temporary directory
- certutil.exe (PID: 8184)
Reads the machine GUID from the registry
- Images.png (PID: 7948)
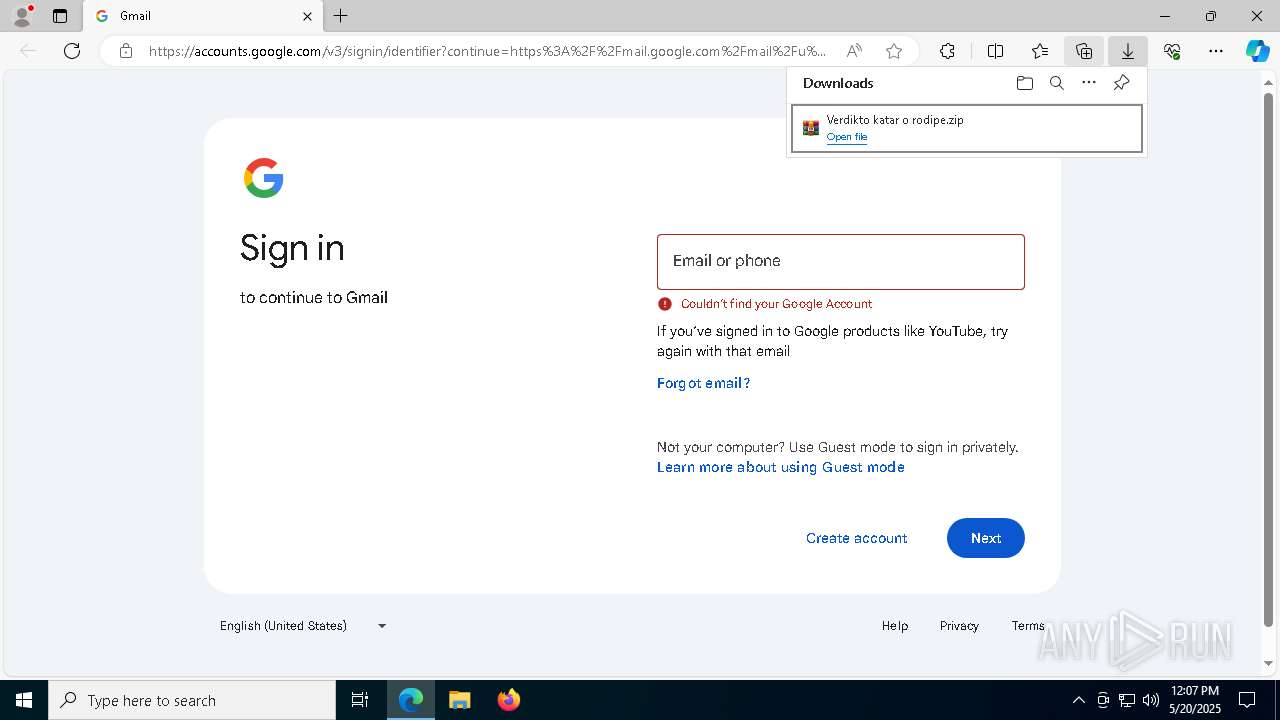
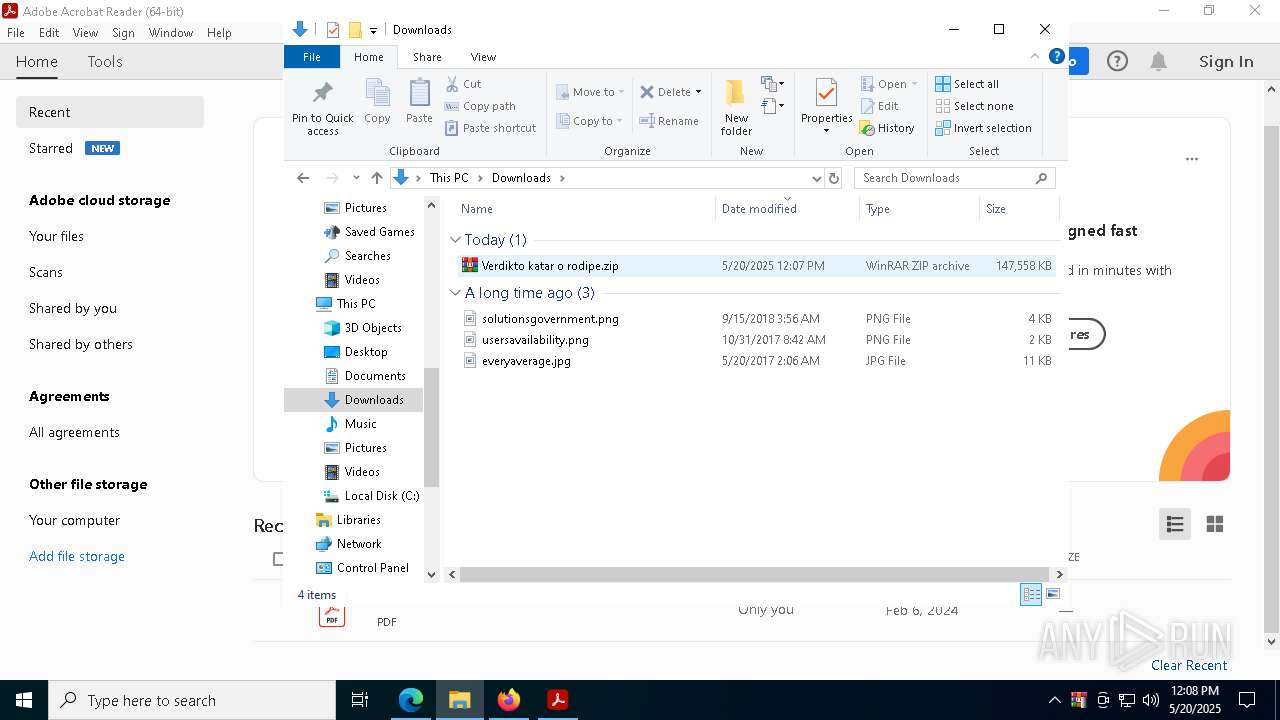
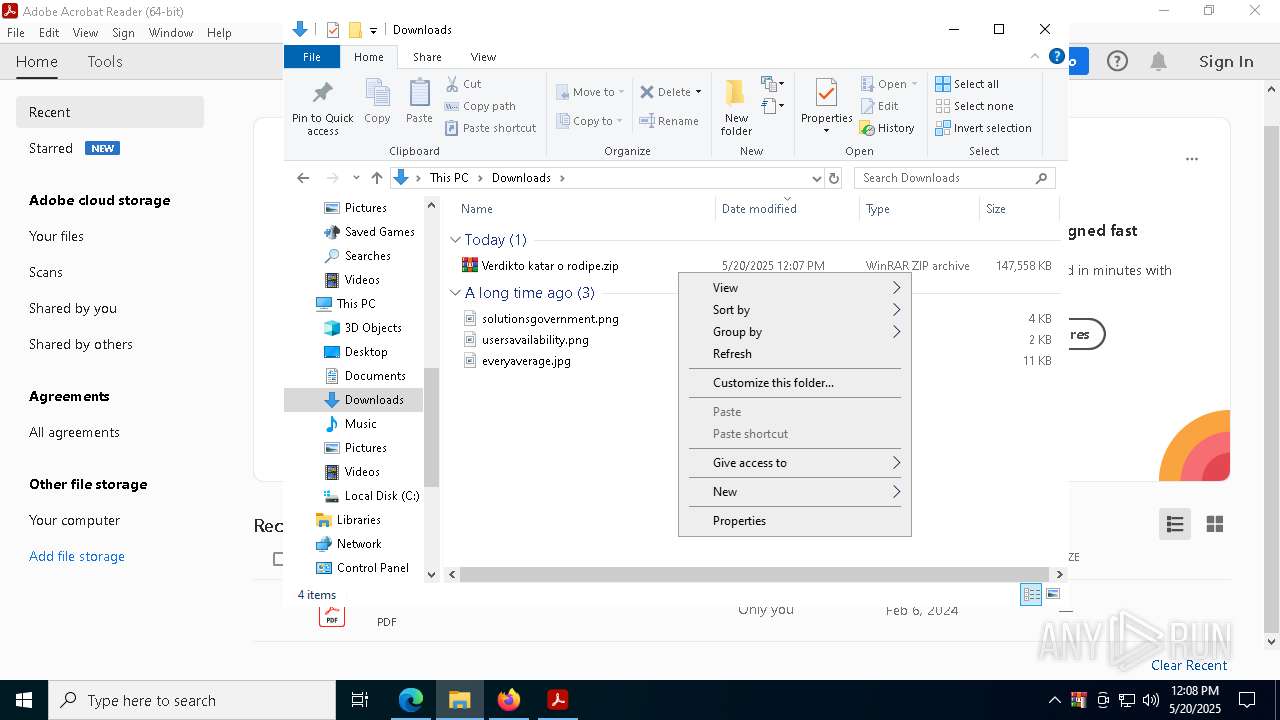
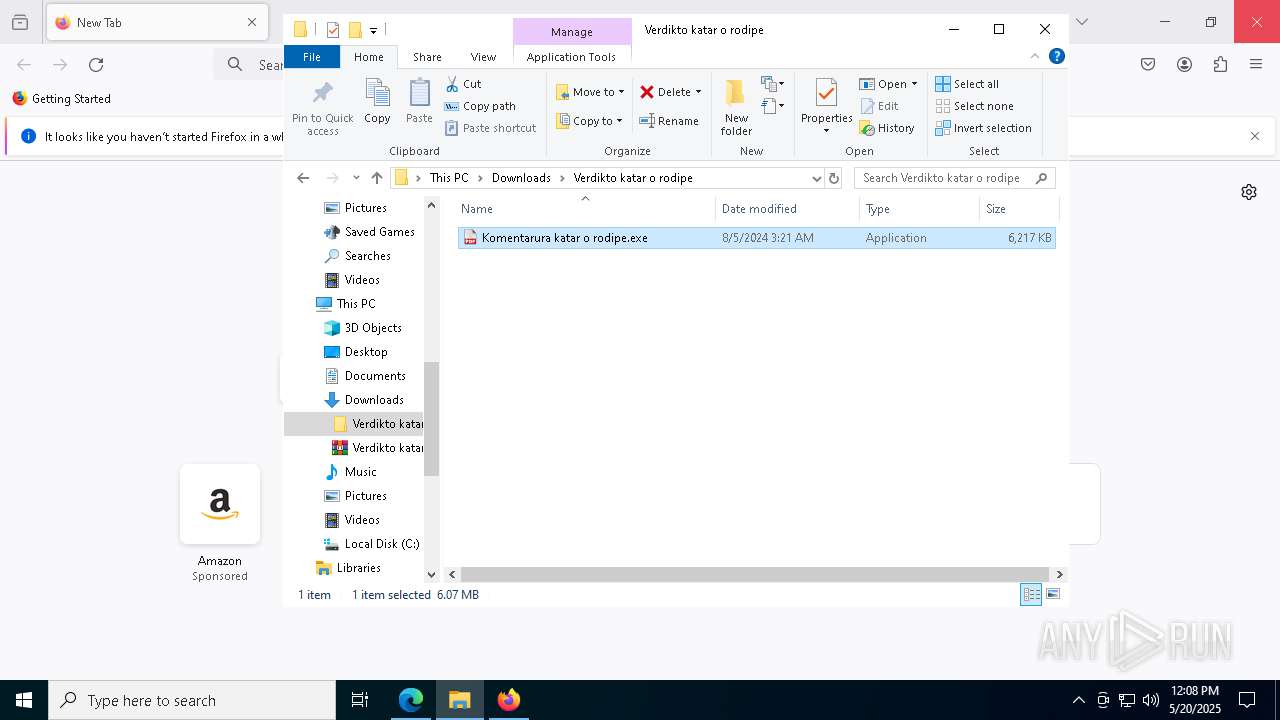
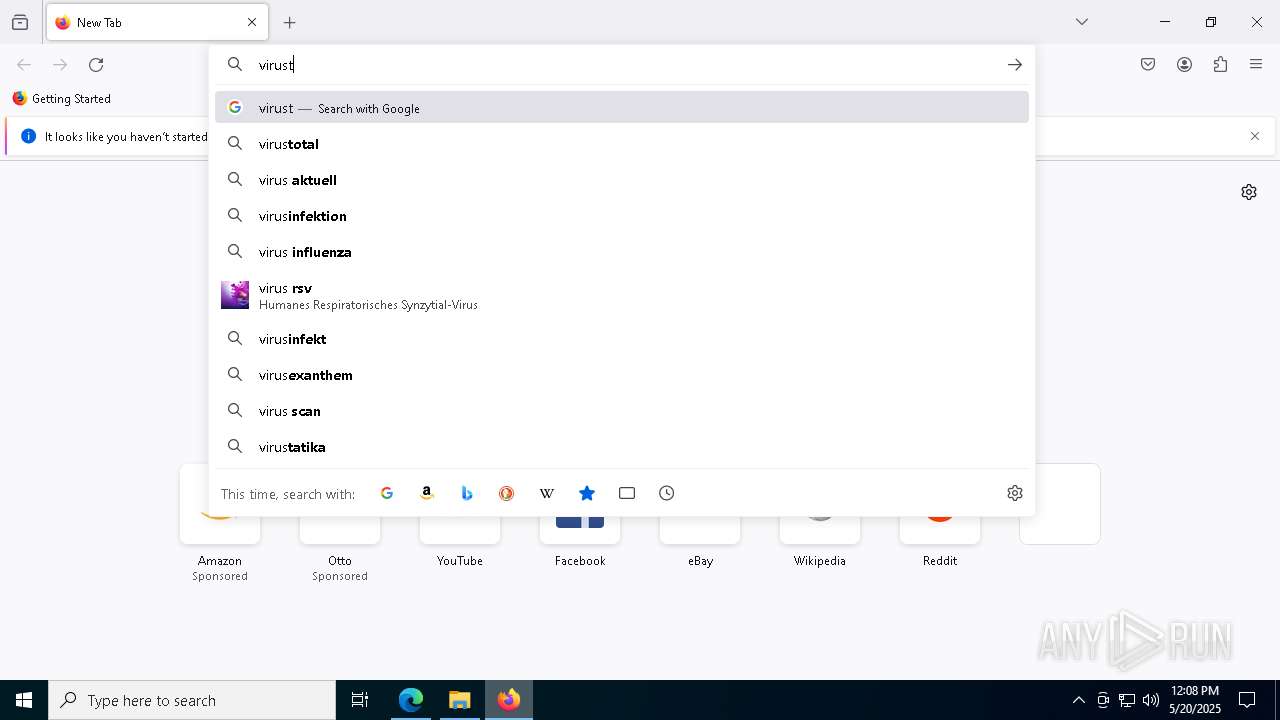
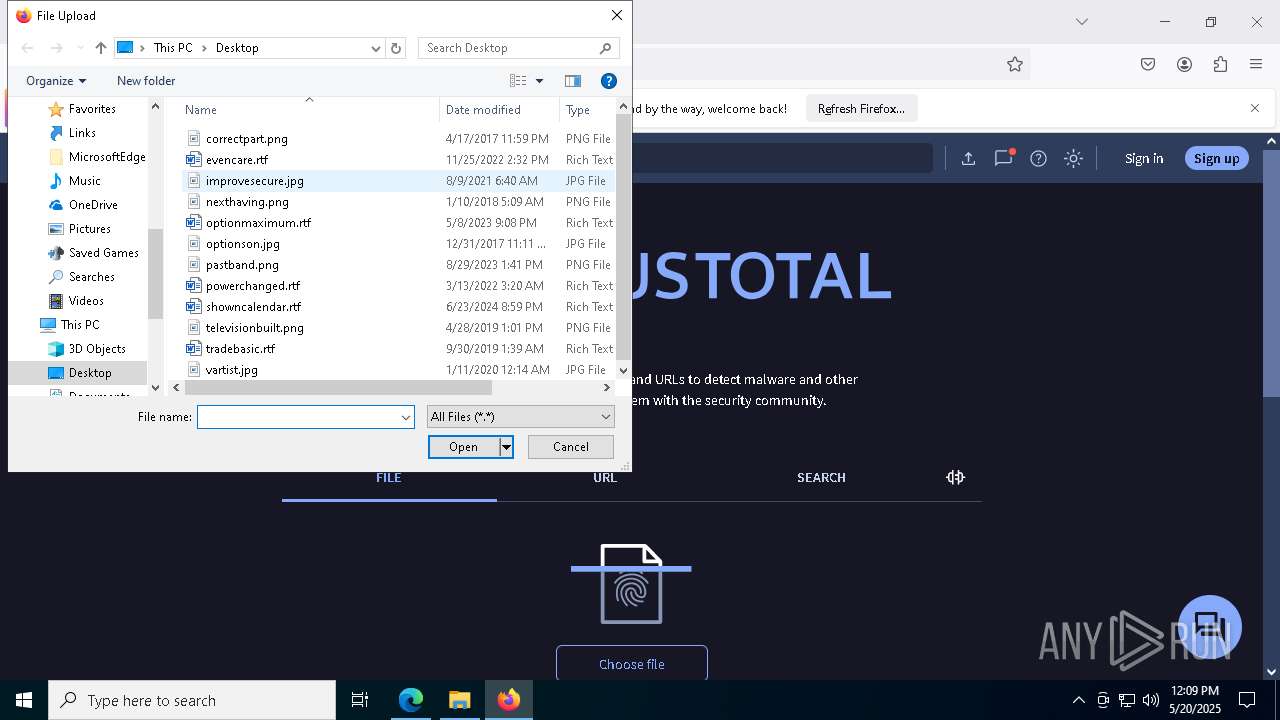
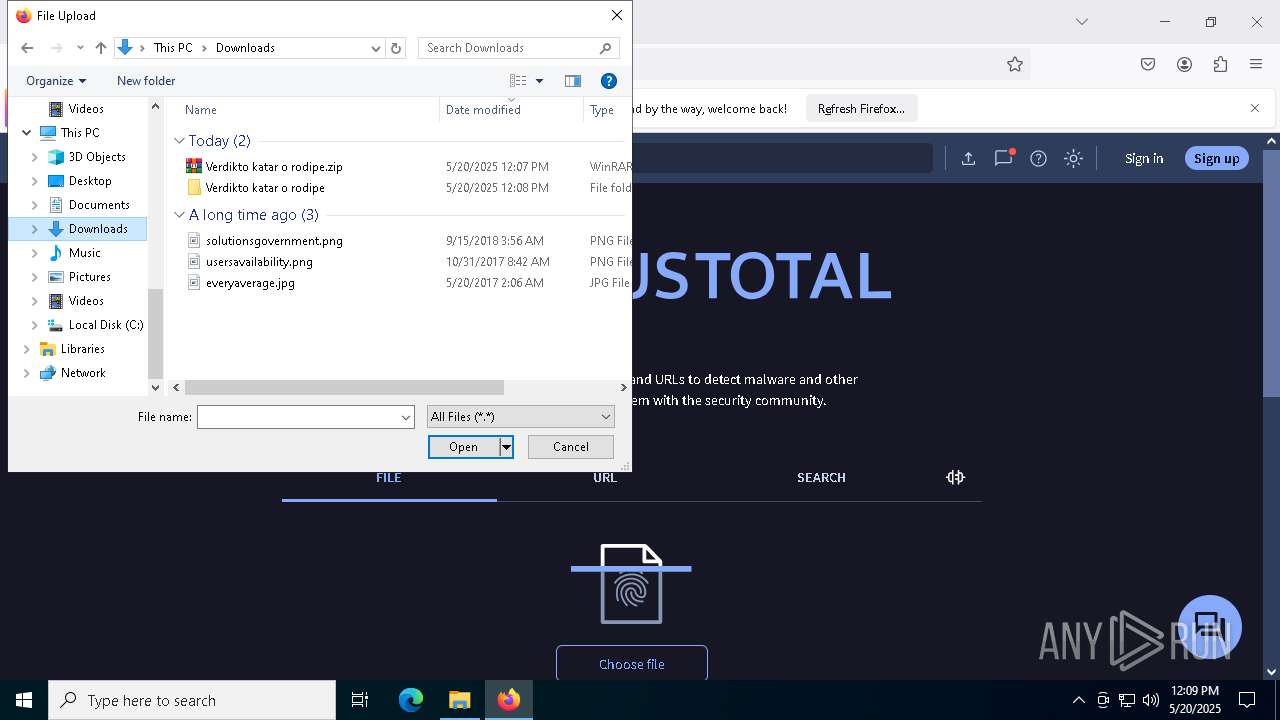
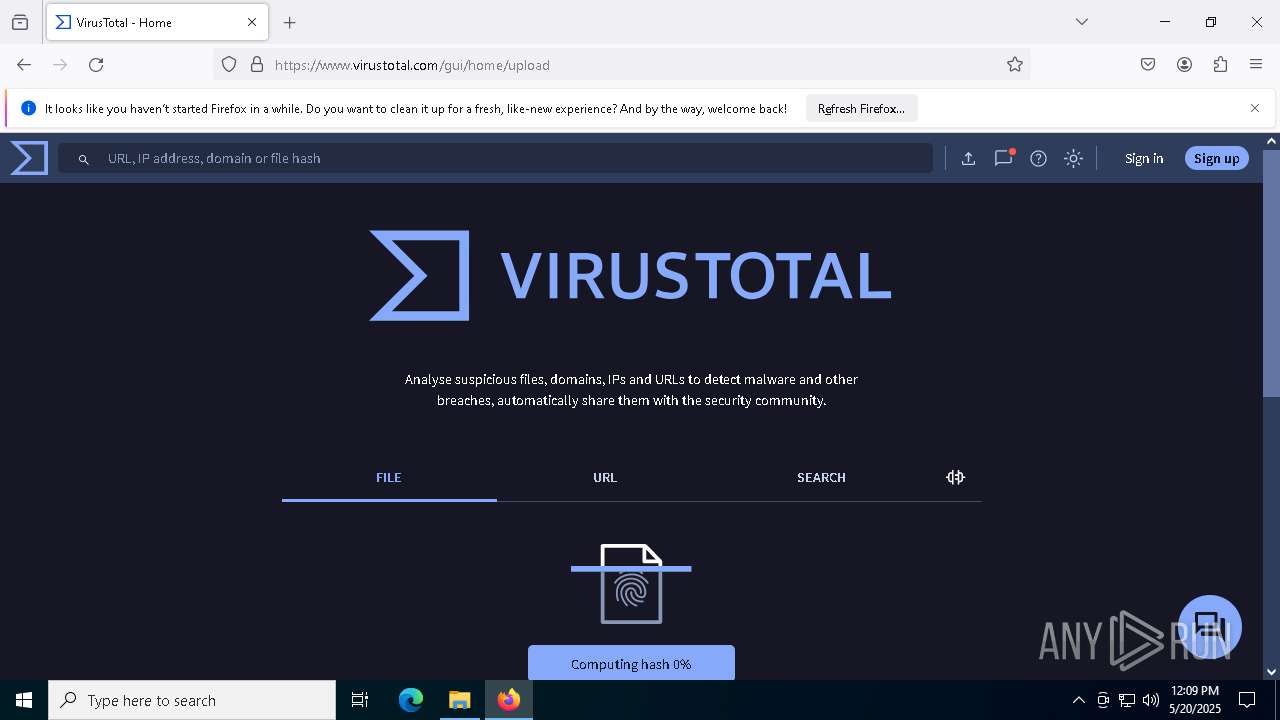
Manual execution by a user
- firefox.exe (PID: 8812)
- WinRAR.exe (PID: 9588)
- Komentarura katar o rodipe.exe (PID: 9756)
Reads the software policy settings
- slui.exe (PID: 6816)
Python executable
- svchost.exe (PID: 8088)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
250
Monitored processes
114
Malicious processes
6
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | taskkill /F /PID 4112 | C:\Windows\SysWOW64\taskkill.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 536 | "C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=utility --log-severity=disable --user-agent-product="ReaderServices/23.1.20093 Chrome/105.0.0.0" --lang=en-US --log-file="C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\debug.log" --mojo-platform-channel-handle=2108 --field-trial-handle=1604,i,14535777647322955319,14672688903136322304,131072 --disable-features=BackForwardCache,CalculateNativeWinOcclusion,WinUseBrowserSpellChecker /prefetch:8 | C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe | — | AcroCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe AcroCEF Exit code: 0 Version: 23.1.20093.0 Modules
| |||||||||||||||
| 660 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=8376 --field-trial-handle=2264,i,5379562475618902673,13245918016219159164,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 664 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=23 --mojo-platform-channel-handle=5708 --field-trial-handle=2264,i,5379562475618902673,13245918016219159164,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 1 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 672 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6732 --field-trial-handle=2264,i,5379562475618902673,13245918016219159164,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
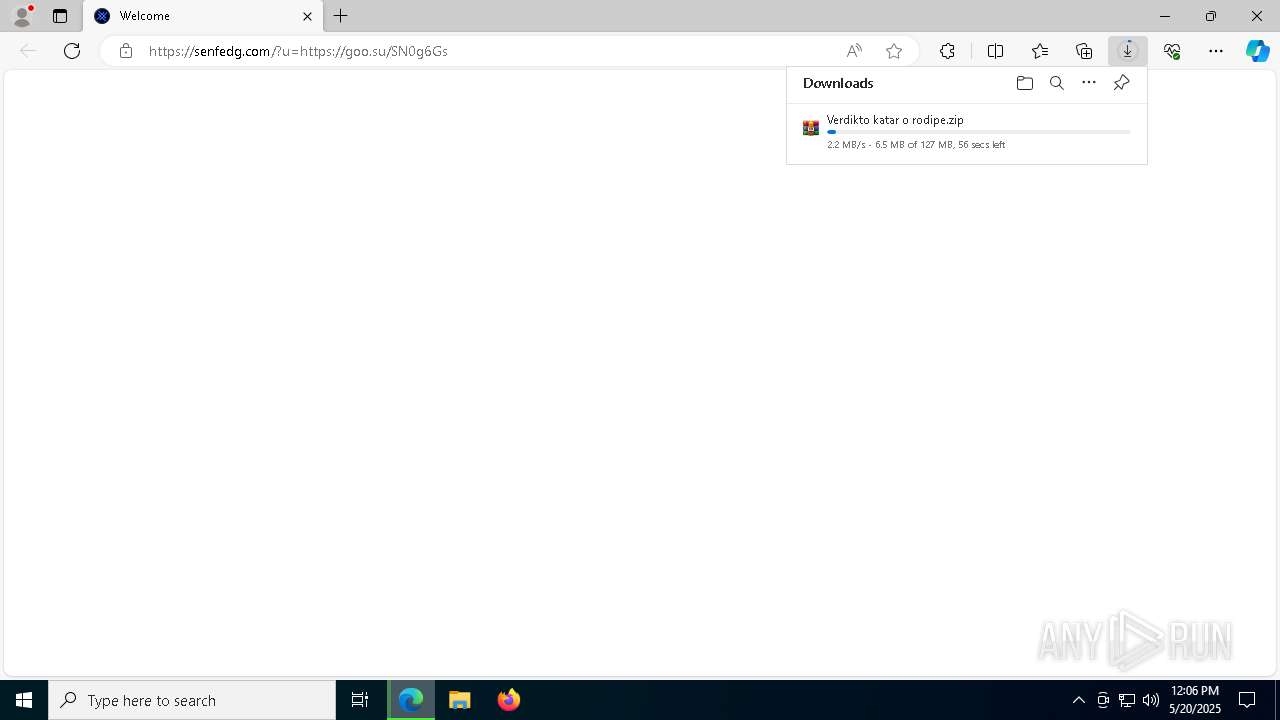
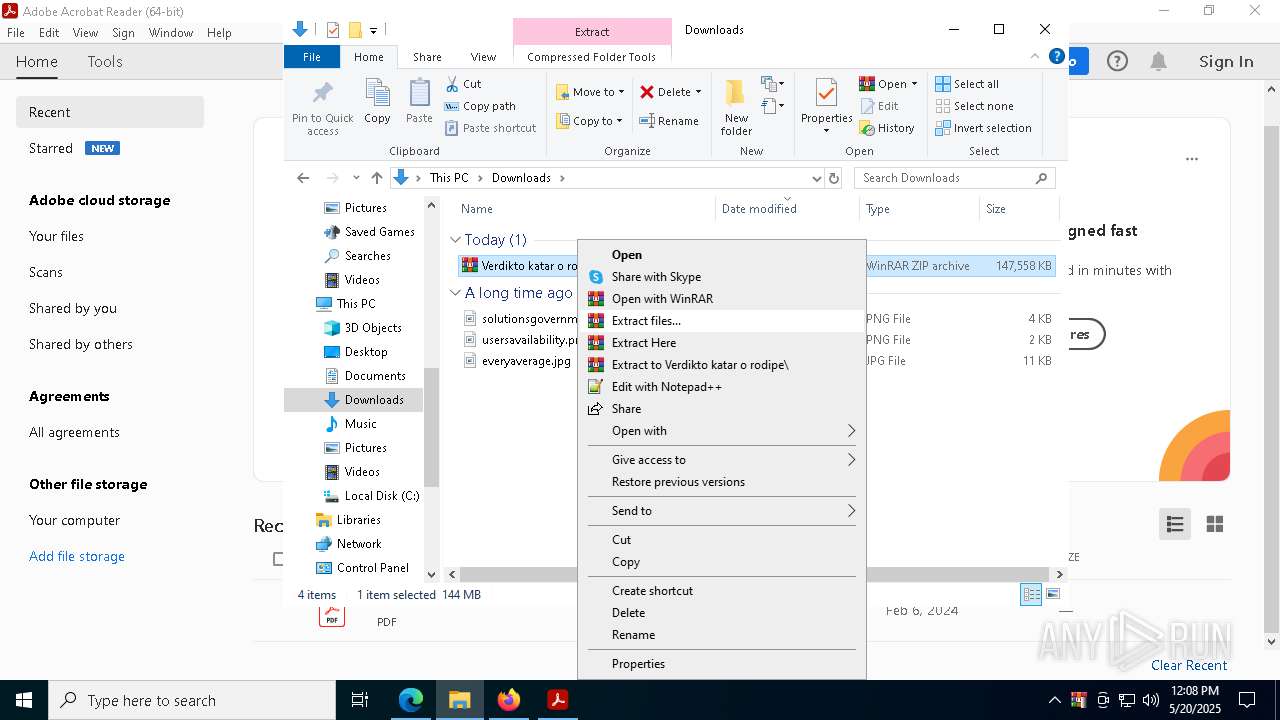
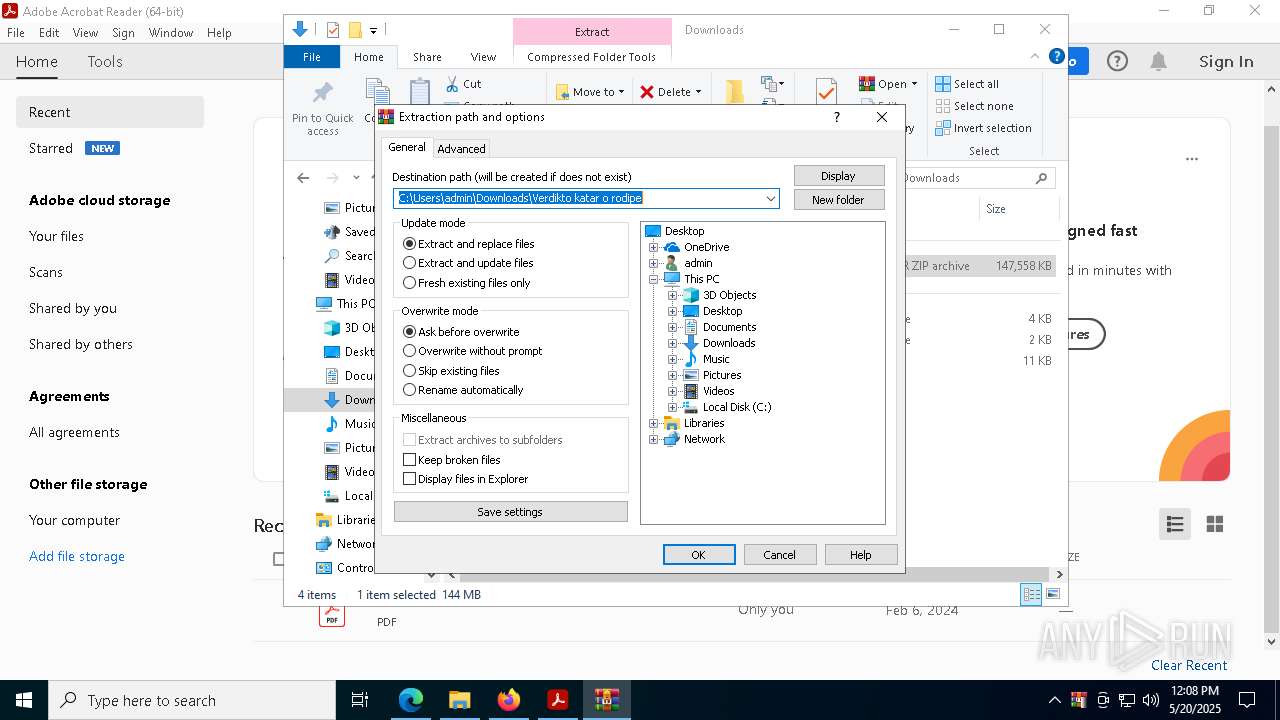
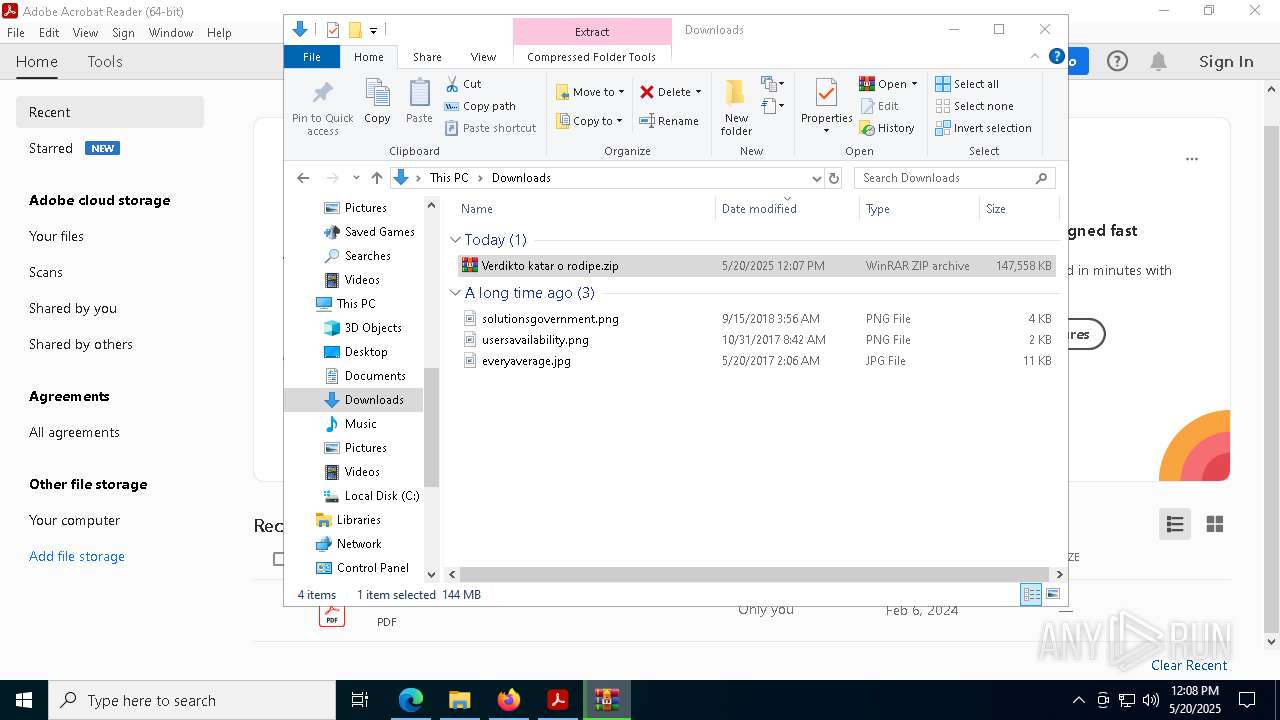
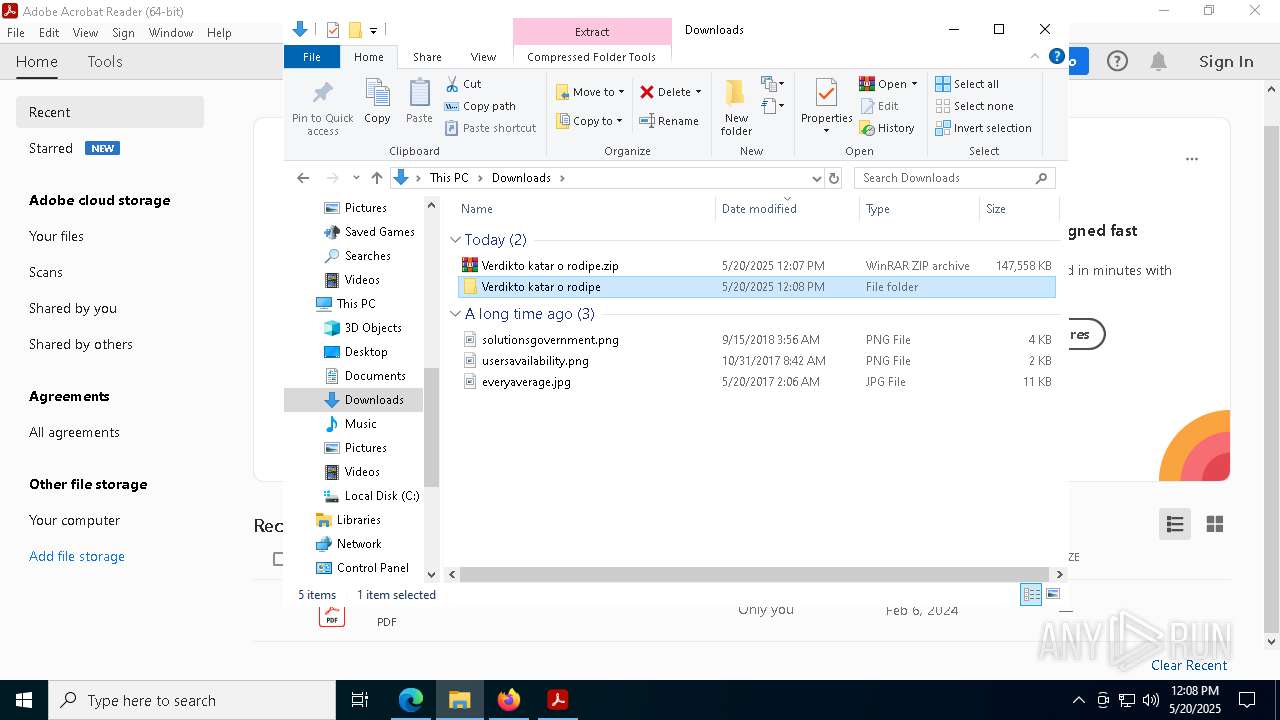
| 684 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\Verdikto katar o rodipe.zip" | C:\Program Files\WinRAR\WinRAR.exe | msedge.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 720 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=3764 --field-trial-handle=2264,i,5379562475618902673,13245918016219159164,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1128 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=29 --mojo-platform-channel-handle=7732 --field-trial-handle=2264,i,5379562475618902673,13245918016219159164,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 1 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1132 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7296 --field-trial-handle=2264,i,5379562475618902673,13245918016219159164,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1168 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=39 --mojo-platform-channel-handle=8120 --field-trial-handle=2264,i,5379562475618902673,13245918016219159164,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 1 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
56 453
Read events
56 099
Write events
327
Delete events
27
Modification events
| (PID) Process: | (2432) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262766 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {1982DC44-E56A-4EB1-BB1B-0FC1B7B07365} | |||
| (PID) Process: | (2432) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2432) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2432) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2432) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (2432) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 18DCE65D26942F00 | |||
| (PID) Process: | (2432) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 3AAFEF5D26942F00 | |||
| (PID) Process: | (2432) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262766 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {9B050F95-AC9A-439D-A23A-19505CBA62E7} | |||
| (PID) Process: | (2432) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262766 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {49506584-0CE8-4559-AD64-79FDF9347B51} | |||
| (PID) Process: | (2432) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262766 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {302E9A5D-8B64-4EF1-BD79-67931A628BF9} | |||
Executable files
139
Suspicious files
1 136
Text files
1 487
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2432 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b6a0.TMP | — | |
MD5:— | SHA256:— | |||
| 2432 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b6bf.TMP | — | |
MD5:— | SHA256:— | |||
| 2432 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b6bf.TMP | — | |
MD5:— | SHA256:— | |||
| 2432 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2432 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2432 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2432 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b6bf.TMP | — | |
MD5:— | SHA256:— | |||
| 2432 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2432 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b6de.TMP | — | |
MD5:— | SHA256:— | |||
| 2432 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
67
TCP/UDP connections
184
DNS requests
236
Threats
26
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2268 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2268 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4692 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1748312758&P2=404&P3=2&P4=cPZPfaisDNMt4JW2u%2foNsF4hIRovVZj28tHraHcE2Gkduz2qt5TphqXBir%2bA6EXz1DXgD07%2fQ2BZHEjuYC0Faw%3d%3d | unknown | — | — | whitelisted |
4692 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1748312758&P2=404&P3=2&P4=cPZPfaisDNMt4JW2u%2foNsF4hIRovVZj28tHraHcE2Gkduz2qt5TphqXBir%2bA6EXz1DXgD07%2fQ2BZHEjuYC0Faw%3d%3d | unknown | — | — | whitelisted |
4692 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1748312758&P2=404&P3=2&P4=cPZPfaisDNMt4JW2u%2foNsF4hIRovVZj28tHraHcE2Gkduz2qt5TphqXBir%2bA6EXz1DXgD07%2fQ2BZHEjuYC0Faw%3d%3d | unknown | — | — | whitelisted |
4692 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1748316360&P2=404&P3=2&P4=mWI3%2ffrwHnZuLTh78g1E1usg9%2fzFReaCrnDaEnIAwGw6%2bcUCIy1Mv1S457z0x7NhCPg12EDsrFmKsRuqsxwsPQ%3d%3d | unknown | — | — | whitelisted |
4692 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1748316360&P2=404&P3=2&P4=mWI3%2ffrwHnZuLTh78g1E1usg9%2fzFReaCrnDaEnIAwGw6%2bcUCIy1Mv1S457z0x7NhCPg12EDsrFmKsRuqsxwsPQ%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
7380 | msedge.exe | 104.26.2.56:443 | goo.su | — | — | suspicious |
7380 | msedge.exe | 13.107.43.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2432 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7380 | msedge.exe | 151.101.130.133:443 | tr.ee | FASTLY | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
tr.ee |
| malicious |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
goo.su |
| unknown |
senfedg.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7380 | msedge.exe | Misc activity | ET INFO Observed URL Shortener Service Domain (tr .ee) in TLS SNI |
7380 | msedge.exe | Misc activity | ET INFO Observed URL Shortener Service (tr .ee) in DNS Lookup |
7380 | msedge.exe | Misc activity | ET INFO Observed URL Shortener Service (tr .ee) in DNS Lookup |
7380 | msedge.exe | Misc activity | ET INFO Observed URL Shortener Service Domain in DNS Lookup (goo .su) |
7380 | msedge.exe | Misc activity | INFO [ANY.RUN] Possible short link service (goo .su) |
7380 | msedge.exe | Misc activity | ET INFO Observed URL Shortener Service Domain in DNS Lookup (goo .su) |
7380 | msedge.exe | Misc activity | ET INFO Observed URL Shortener Service Domain (goo .su in TLS SNI) |
7380 | msedge.exe | Misc activity | INFO [ANY.RUN] Possible short link service (goo .su) |
7380 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
7380 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |