| File name: | 9add0058168ebc360f67d2af1f773e477f760df31616adea2a8042a998098879 |
| Full analysis: | https://app.any.run/tasks/064e0af9-ece5-4132-8d4f-f8a777599e50 |
| Verdict: | Malicious activity |
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
| Analysis date: | April 29, 2025, 03:33:30 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | 78708CFF77DBE798CF5DD92A1B118B33 |
| SHA1: | 8C614106F0969FA83F2FE27237DCE9F45059A921 |
| SHA256: | 9ADD0058168EBC360F67D2AF1F773E477F760DF31616ADEA2A8042A998098879 |
| SSDEEP: | 98304:gn2gJ/uk0+Xv45msIJMtb30rtIQehUH1kupC3/UFE7CUfWr9P4eB/7cZBGXkzVy0:EynlpLbXF |
MALICIOUS
AMADEY mutex has been found
- 1H12L7.exe (PID: 6640)
- rapes.exe (PID: 7280)
- rapes.exe (PID: 2100)
AMADEY has been found (auto)
- 9add0058168ebc360f67d2af1f773e477f760df31616adea2a8042a998098879.exe (PID: 5380)
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2196)
AMADEY has been detected (YARA)
- rapes.exe (PID: 7280)
Connects to the CnC server
- svchost.exe (PID: 2196)
SUSPICIOUS
Process drops legitimate windows executable
- 9add0058168ebc360f67d2af1f773e477f760df31616adea2a8042a998098879.exe (PID: 5380)
Reads the BIOS version
- 1H12L7.exe (PID: 6640)
- rapes.exe (PID: 7280)
- 2m4221.exe (PID: 7296)
- rapes.exe (PID: 2100)
Starts a Microsoft application from unusual location
- 9add0058168ebc360f67d2af1f773e477f760df31616adea2a8042a998098879.exe (PID: 5380)
Executable content was dropped or overwritten
- 9add0058168ebc360f67d2af1f773e477f760df31616adea2a8042a998098879.exe (PID: 5380)
- 1H12L7.exe (PID: 6640)
Reads security settings of Internet Explorer
- 1H12L7.exe (PID: 6640)
- rapes.exe (PID: 7280)
Starts itself from another location
- 1H12L7.exe (PID: 6640)
Contacting a server suspected of hosting an CnC
- svchost.exe (PID: 2196)
There is functionality for enable RDP (YARA)
- rapes.exe (PID: 7280)
The process executes via Task Scheduler
- rapes.exe (PID: 2100)
INFO
The sample compiled with english language support
- 9add0058168ebc360f67d2af1f773e477f760df31616adea2a8042a998098879.exe (PID: 5380)
Checks supported languages
- 9add0058168ebc360f67d2af1f773e477f760df31616adea2a8042a998098879.exe (PID: 5380)
- 1H12L7.exe (PID: 6640)
- rapes.exe (PID: 7280)
- 2m4221.exe (PID: 7296)
- rapes.exe (PID: 2100)
Reads the computer name
- 1H12L7.exe (PID: 6640)
- rapes.exe (PID: 7280)
- 2m4221.exe (PID: 7296)
Create files in a temporary directory
- 1H12L7.exe (PID: 6640)
- 9add0058168ebc360f67d2af1f773e477f760df31616adea2a8042a998098879.exe (PID: 5380)
Process checks computer location settings
- 1H12L7.exe (PID: 6640)
Checks proxy server information
- rapes.exe (PID: 7280)
Reads the software policy settings
- 2m4221.exe (PID: 7296)
Themida protector has been detected
- rapes.exe (PID: 7280)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Amadey
(PID) Process(7280) rapes.exe
C2176.113.115.6
URLhttp://176.113.115.6/Ni9kiput/index.php
Version5.21
Options
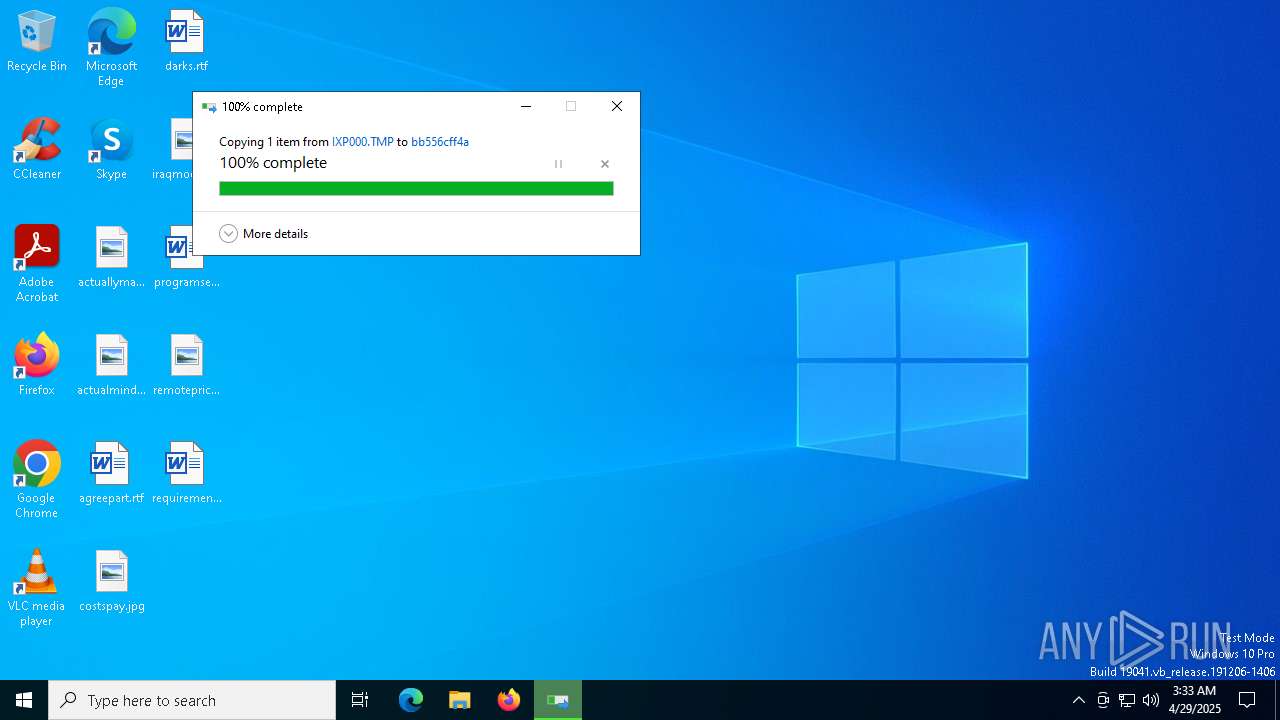
Drop directorybb556cff4a
Drop namerapes.exe
Strings (125)S-%lu-
og:
clip.dll
ProgramData\
shell32.dll
<c>
vs:
Programs
&&
VideoID
ESET
av:
\App
0000043f
Doctor Web
:::
SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\User Shell Folders
------
rundll32.exe
00000422
0123456789
st=s
00000419
Content-Type: application/x-www-form-urlencoded
/Plugins/
msi
ar:
GetNativeSystemInfo
Norton
-%lu
Sophos
bb556cff4a
zip
SOFTWARE\Microsoft\Windows NT\CurrentVersion
"
Content-Type: application/octet-stream
|
+++
176.113.115.6
" && ren
pc:
#
d1
cmd /C RMDIR /s/q
Bitdefender
Comodo
<d>
Kaspersky Lab
DefaultSettings.YResolution
Main
-executionpolicy remotesigned -File "
&& Exit"
ProductName
&unit=
2022
Panda Security
=
Rem
cmd
\0000
id:
sd:
--
/quiet
rundll32
SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Shell Folders
%-lu
random
GET
"taskkill /f /im "
Content-Disposition: form-data; name="data"; filename="
00000423
2016
?scr=1
ComputerName
Keyboard Layout\Preload
Powershell.exe
POST
http://
AVAST Software
SYSTEM\CurrentControlSet\Control\UnitedVideo\CONTROL\VIDEO\
ps1
DefaultSettings.XResolution
Startup
CurrentBuild
e3
cred.dll|clip.dll|
------
/Ni9kiput/index.php
WinDefender
wb
https://
rapes.exe
Avira
2025
" && timeout 1 && del
cred.dll
un:
SYSTEM\ControlSet001\Services\BasicDisplay\Video
rb
5.21
SYSTEM\CurrentControlSet\Control\ComputerName\ComputerName
360TotalSecurity
SOFTWARE\Microsoft\Windows\CurrentVersion\Run
e1
lv:
shutdown -s -t 0
/k
e2
SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce
exe
%USERPROFILE%
-unicode-
r=
.jpg
dll
Content-Type: multipart/form-data; boundary=----
2019
bi:
\
"
kernel32.dll
os:
abcdefghijklmnopqrstuvwxyz0123456789-_
dm:
AVG
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2022:05:24 22:49:06+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.13 |
| CodeSize: | 25600 |
| InitializedDataSize: | 3695616 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x6a60 |
| OSVersion: | 10 |
| ImageVersion: | 10 |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 11.0.17763.1 |
| ProductVersionNumber: | 11.0.17763.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Win32 Cabinet Self-Extractor |
| FileVersion: | 11.00.17763.1 (WinBuild.160101.0800) |
| InternalName: | Wextract |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFileName: | WEXTRACT.EXE .MUI |
| ProductName: | Internet Explorer |
| ProductVersion: | 11.00.17763.1 |
Total processes
134
Monitored processes
8
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2100 | "C:\Users\admin\AppData\Local\Temp\bb556cff4a\rapes.exe" | C:\Users\admin\AppData\Local\Temp\bb556cff4a\rapes.exe | — | svchost.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5380 | "C:\Users\admin\AppData\Local\Temp\9add0058168ebc360f67d2af1f773e477f760df31616adea2a8042a998098879.exe" | C:\Users\admin\AppData\Local\Temp\9add0058168ebc360f67d2af1f773e477f760df31616adea2a8042a998098879.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Win32 Cabinet Self-Extractor Exit code: 0 Version: 11.00.17763.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6640 | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\1H12L7.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\1H12L7.exe | 9add0058168ebc360f67d2af1f773e477f760df31616adea2a8042a998098879.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 7280 | "C:\Users\admin\AppData\Local\Temp\bb556cff4a\rapes.exe" | C:\Users\admin\AppData\Local\Temp\bb556cff4a\rapes.exe | 1H12L7.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
Amadey(PID) Process(7280) rapes.exe C2176.113.115.6 URLhttp://176.113.115.6/Ni9kiput/index.php Version5.21 Options Drop directorybb556cff4a Drop namerapes.exe Strings (125)S-%lu- og: clip.dll ProgramData\ shell32.dll <c> vs: Programs && VideoID ESET av: \App 0000043f Doctor Web ::: SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\User Shell Folders ------ rundll32.exe 00000422 0123456789 st=s 00000419 Content-Type: application/x-www-form-urlencoded /Plugins/ msi ar: GetNativeSystemInfo Norton -%lu Sophos bb556cff4a zip SOFTWARE\Microsoft\Windows NT\CurrentVersion "
Content-Type: application/octet-stream | +++ 176.113.115.6 " && ren pc: # d1 cmd /C RMDIR /s/q Bitdefender Comodo <d> Kaspersky Lab DefaultSettings.YResolution Main -executionpolicy remotesigned -File " && Exit" ProductName &unit= 2022 Panda Security = Rem cmd \0000 id: sd: -- /quiet rundll32 SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Shell Folders %-lu random GET "taskkill /f /im " Content-Disposition: form-data; name="data"; filename=" 00000423 2016 ?scr=1 ComputerName Keyboard Layout\Preload Powershell.exe POST http:// AVAST Software SYSTEM\CurrentControlSet\Control\UnitedVideo\CONTROL\VIDEO\ ps1 DefaultSettings.XResolution Startup CurrentBuild e3 cred.dll|clip.dll| ------ /Ni9kiput/index.php WinDefender wb https:// rapes.exe Avira 2025 " && timeout 1 && del cred.dll un: SYSTEM\ControlSet001\Services\BasicDisplay\Video rb 5.21 SYSTEM\CurrentControlSet\Control\ComputerName\ComputerName 360TotalSecurity SOFTWARE\Microsoft\Windows\CurrentVersion\Run e1 lv: shutdown -s -t 0 /k e2 SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce exe %USERPROFILE% -unicode- r= .jpg dll Content-Type: multipart/form-data; boundary=---- 2019 bi: \ " kernel32.dll os: abcdefghijklmnopqrstuvwxyz0123456789-_ dm: AVG | |||||||||||||||
| 7296 | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\2m4221.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\2m4221.exe | 9add0058168ebc360f67d2af1f773e477f760df31616adea2a8042a998098879.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 7544 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7576 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
1 208
Read events
1 205
Write events
3
Delete events
0
Modification events
| (PID) Process: | (7280) rapes.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (7280) rapes.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (7280) rapes.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
3
Suspicious files
1
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5380 | 9add0058168ebc360f67d2af1f773e477f760df31616adea2a8042a998098879.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\2m4221.exe | executable | |
MD5:5E79DF97975B488E901487DB545D5DE8 | SHA256:AA38C813AAFC36532F6D8E826F2F7665B26C2C0EF2FF7395C21230F2640CB966 | |||
| 5380 | 9add0058168ebc360f67d2af1f773e477f760df31616adea2a8042a998098879.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\1H12L7.exe | executable | |
MD5:93DA4BDBAE52D91D32A34C140466E8CF | SHA256:878228E580CD27A72A847922F9B16B7D16D0797C68AA9E6642AE3DA13518DE7A | |||
| 6640 | 1H12L7.exe | C:\Windows\Tasks\rapes.job | binary | |
MD5:301BC75718F7AA22785D817DAF53C466 | SHA256:BD15A6519B2419BE854FD816D7E31C3772E95AA251E983101996C9063C8E0084 | |||
| 6640 | 1H12L7.exe | C:\Users\admin\AppData\Local\Temp\bb556cff4a\rapes.exe | executable | |
MD5:93DA4BDBAE52D91D32A34C140466E8CF | SHA256:878228E580CD27A72A847922F9B16B7D16D0797C68AA9E6642AE3DA13518DE7A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
23
DNS requests
26
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 868 b | whitelisted |
1812 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | NL | binary | 419 b | whitelisted |
1812 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | NL | binary | 407 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
7296 | 2m4221.exe | 23.197.130.99:443 | steamcommunity.com | Akamai International B.V. | US | whitelisted |
6544 | svchost.exe | 20.190.160.17:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
pirtyoffensiz.bet |
| malicious |
uncertainyelemz.bet |
| malicious |
hobbyedsmoker.live |
| malicious |
dsfljsdfjewf.info |
| malicious |
deaddereaste.today |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (uncertainyelemz .bet) |
2196 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (dsfljsdfjewf .info) |
2196 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (pirtyoffensiz .bet) |
2196 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (hobbyedsmoker .live) |
2196 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (subawhipnator .life) |
2196 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (decreaserid .world) |
2196 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (dsfljsdfjewf .info) |
2196 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (pastedeputten .life) |
2196 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (deaddereaste .today) |
2196 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (privileggoe .live) |