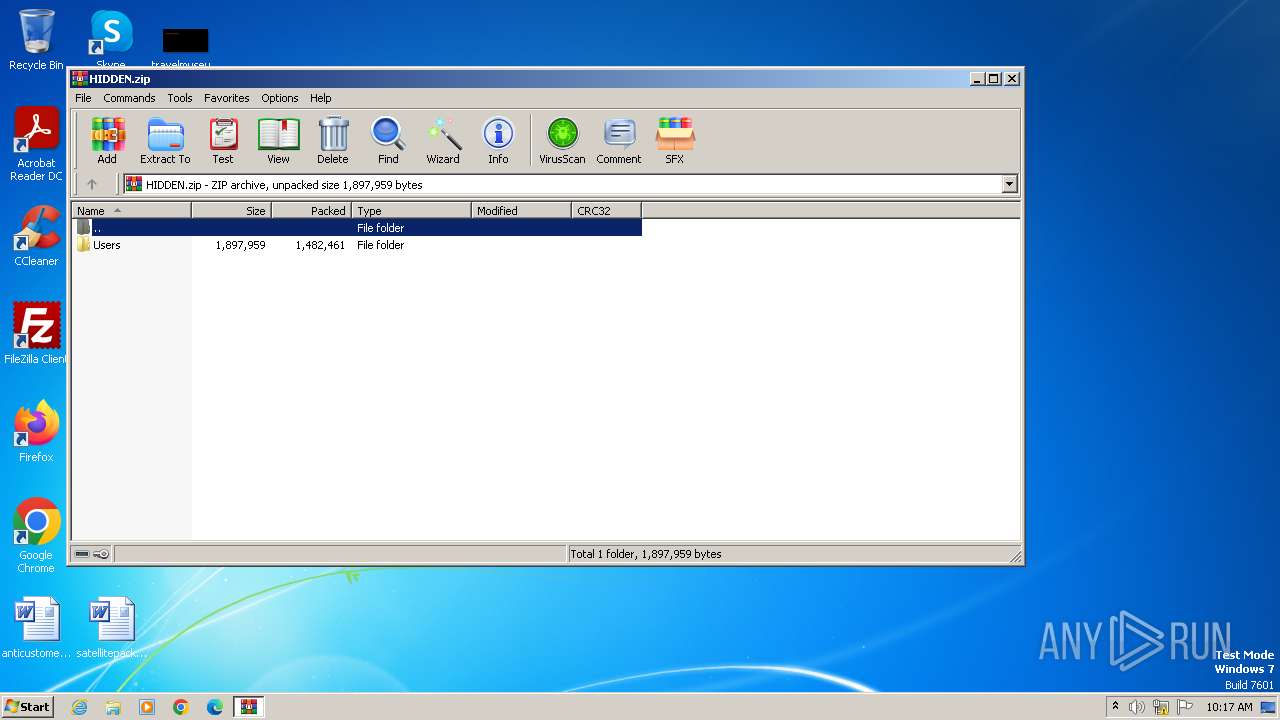
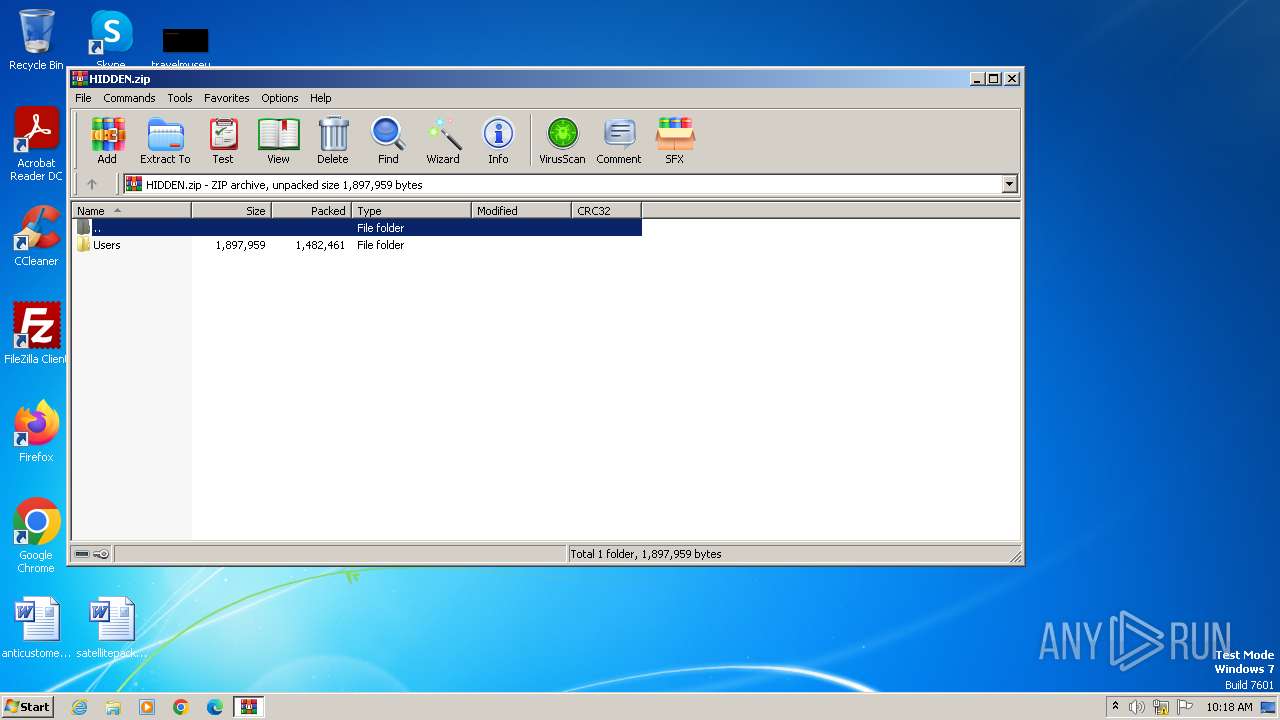
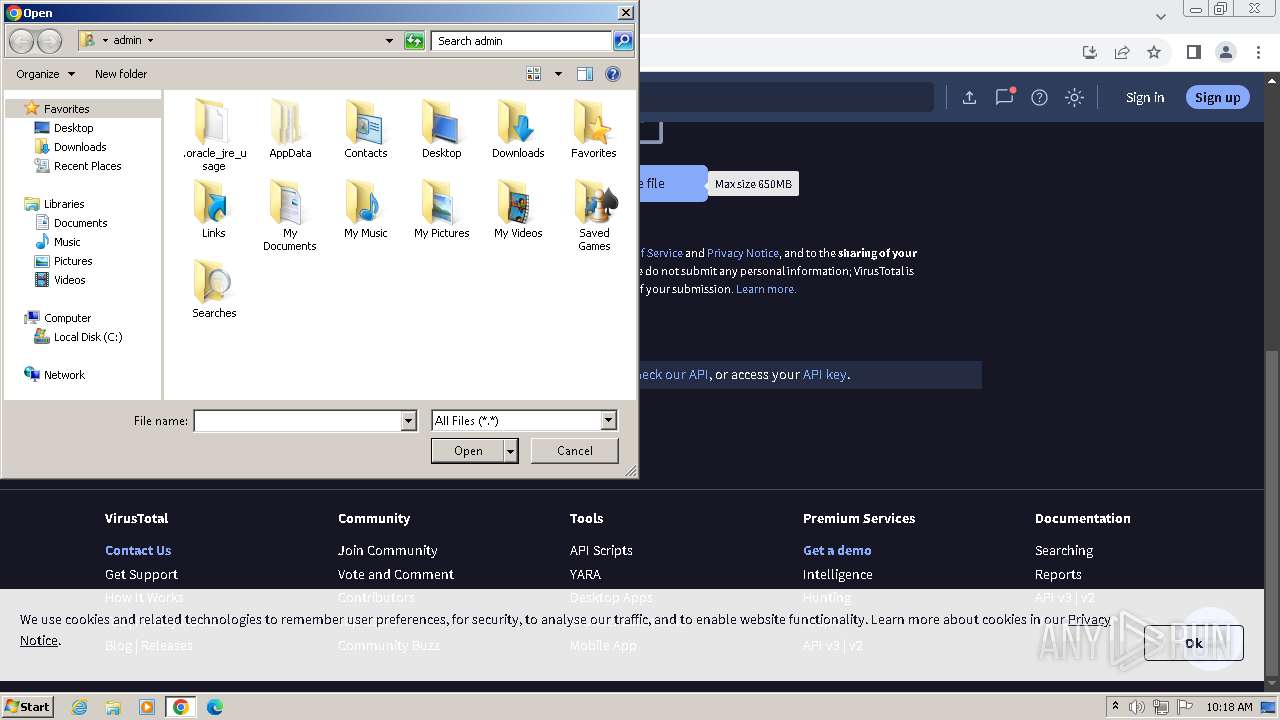
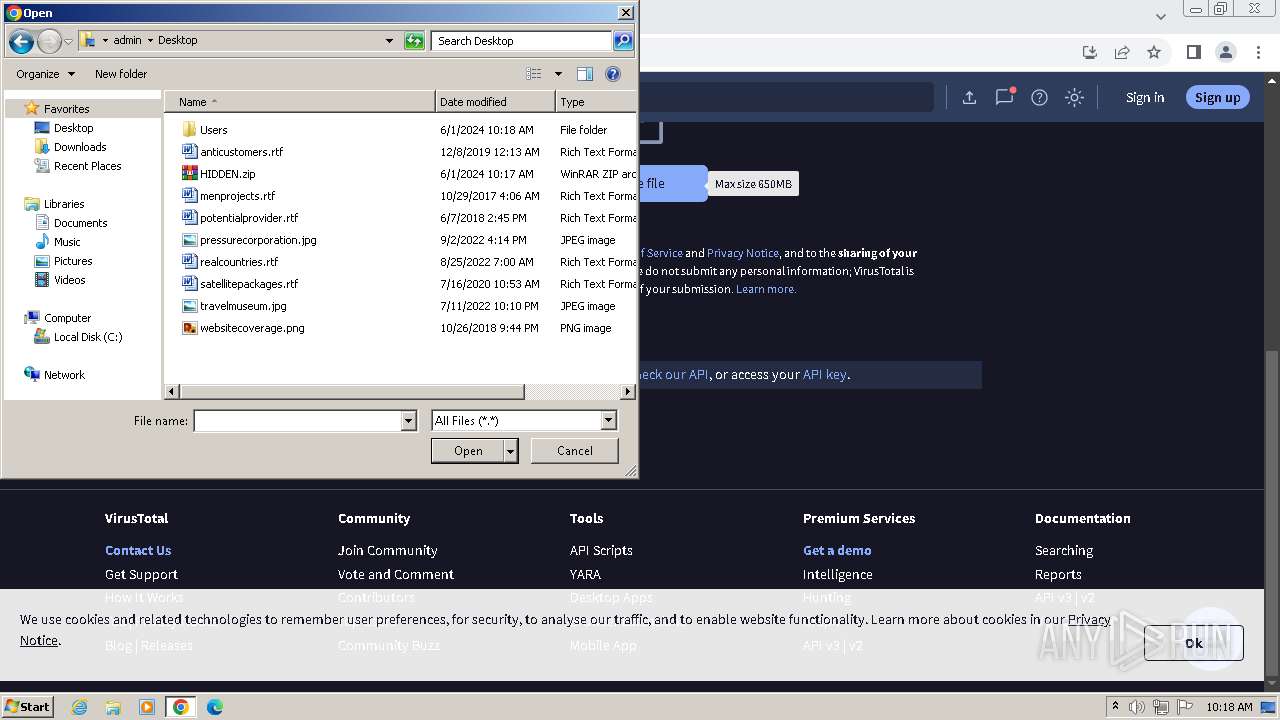
| File name: | HIDDEN.zip |
| Full analysis: | https://app.any.run/tasks/296dcd51-1388-4243-af48-91ae39653bc4 |
| Verdict: | Malicious activity |
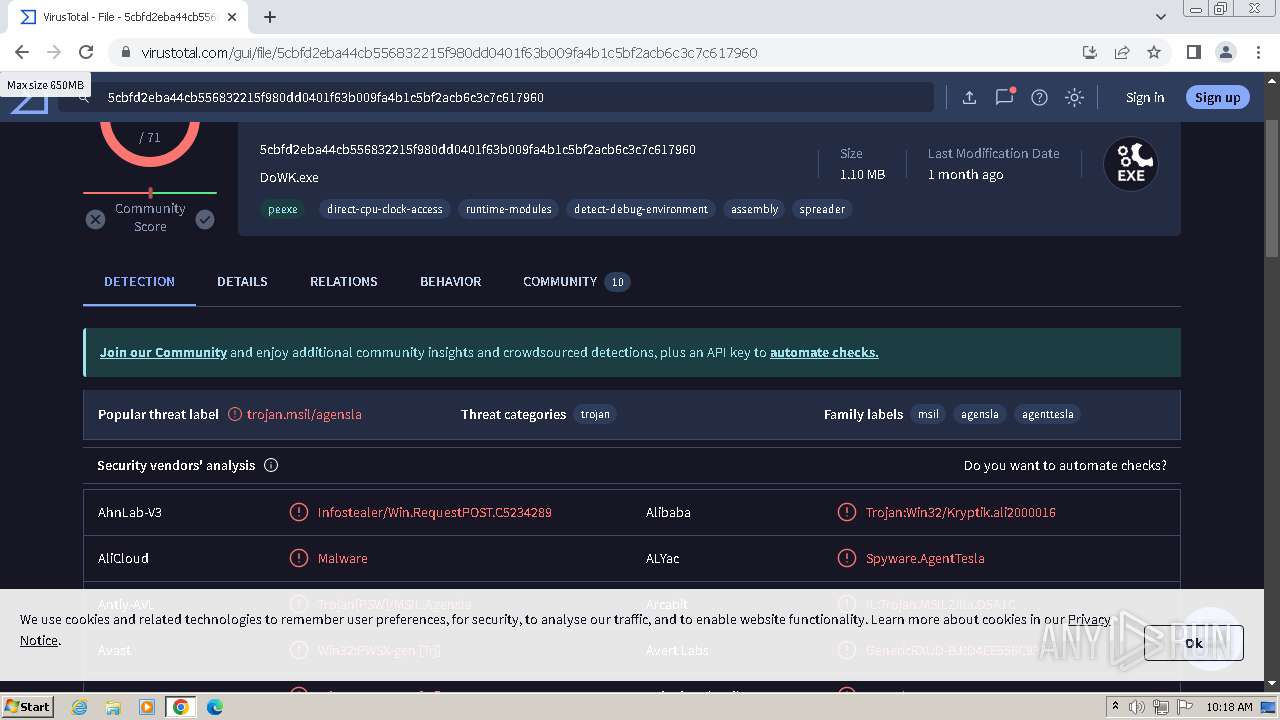
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | June 01, 2024, 09:17:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | F1A5663A157E1DA8B470FAAF188144CA |
| SHA1: | 296BFE955E300AF3759F557999E6DDFD0A2695EA |
| SHA256: | 9AC200E2E1A34A81A8CB48F85088B8AB12322795E6102D18C8034E7CD82F46E6 |
| SSDEEP: | 49152:jx5l3HVm9v4fjW9kQzoT9GtbEvPFNJ7TMDbeUYu+e8M+EA/Mogjm/8lj3rZfIUEa:jxbHV60n5wt4XFNd0bHYs83EToge039z |
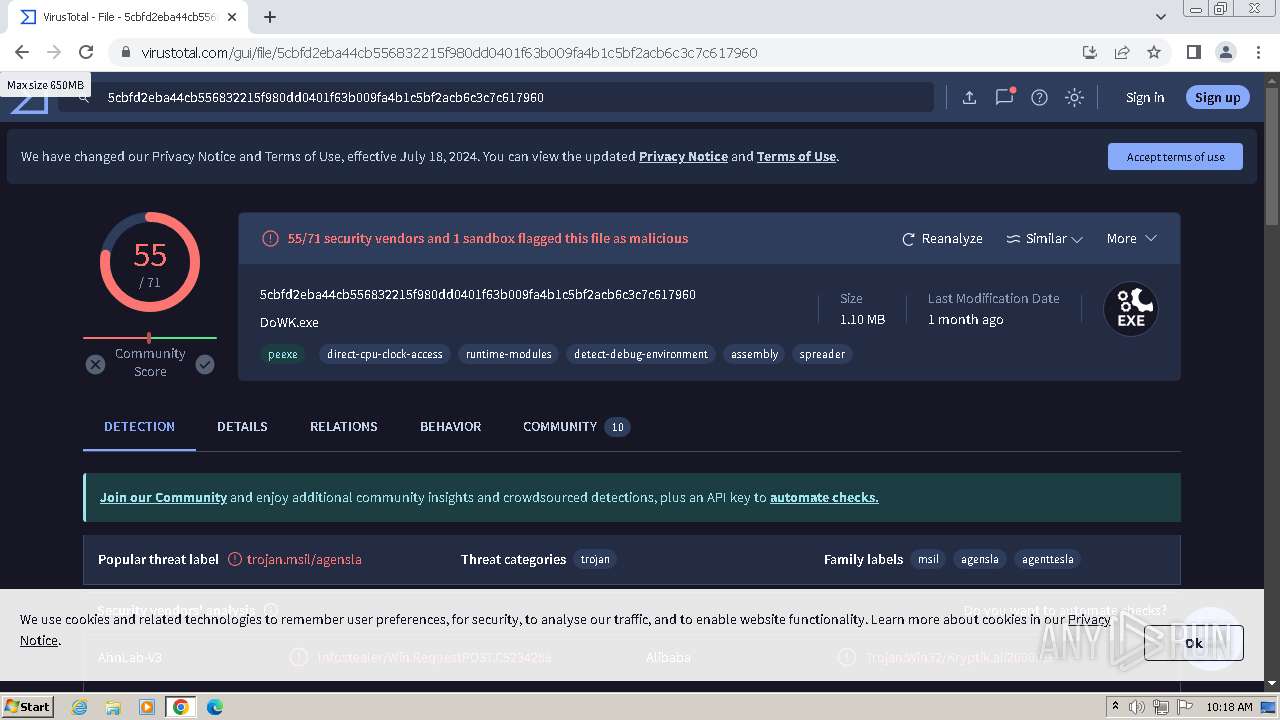
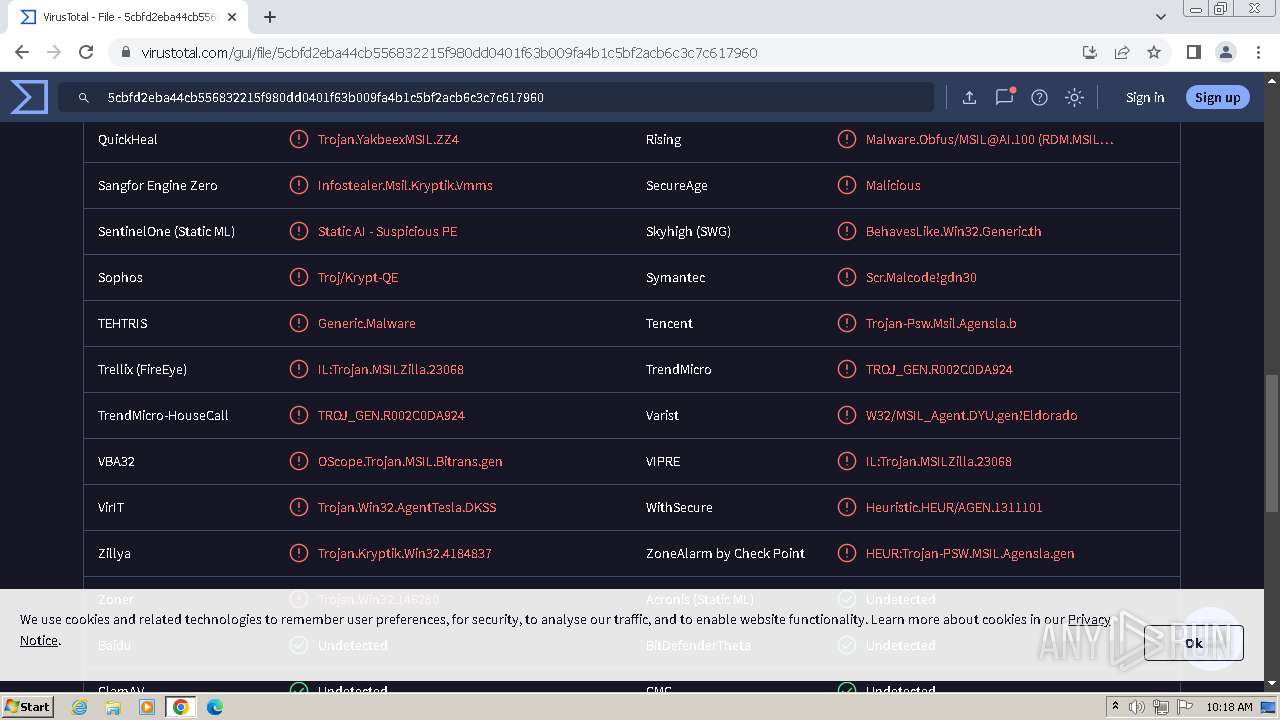
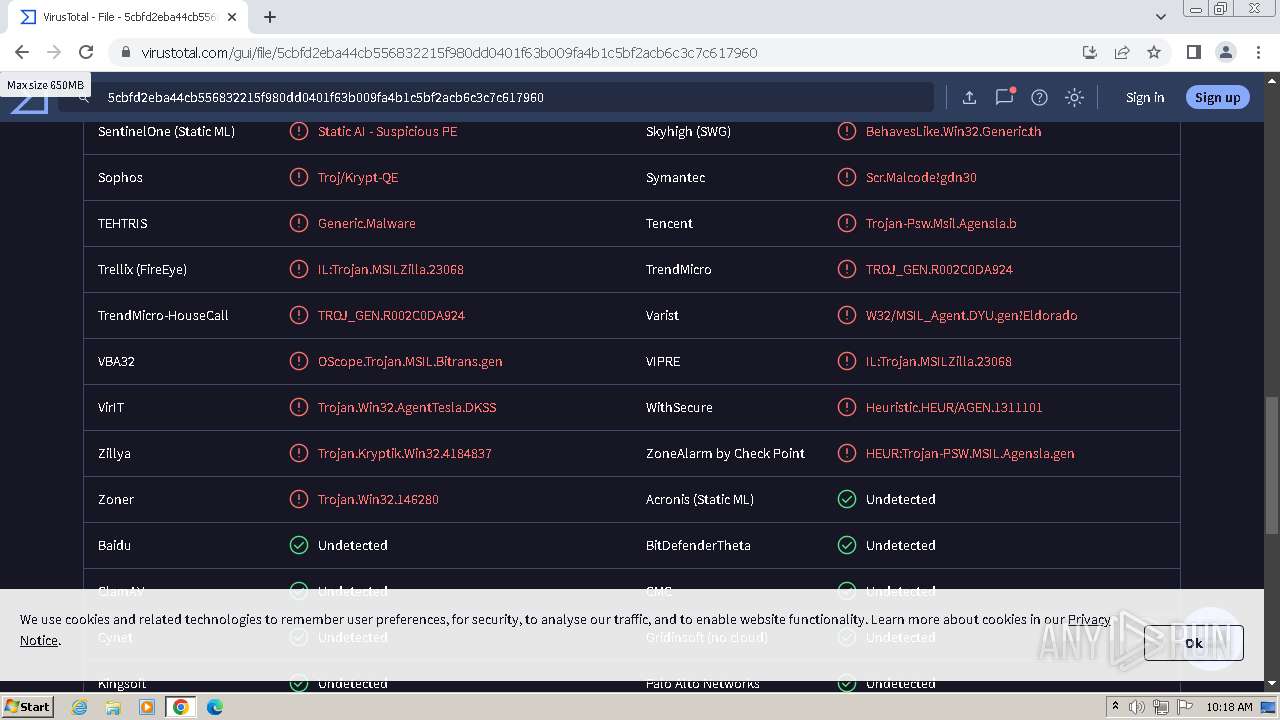
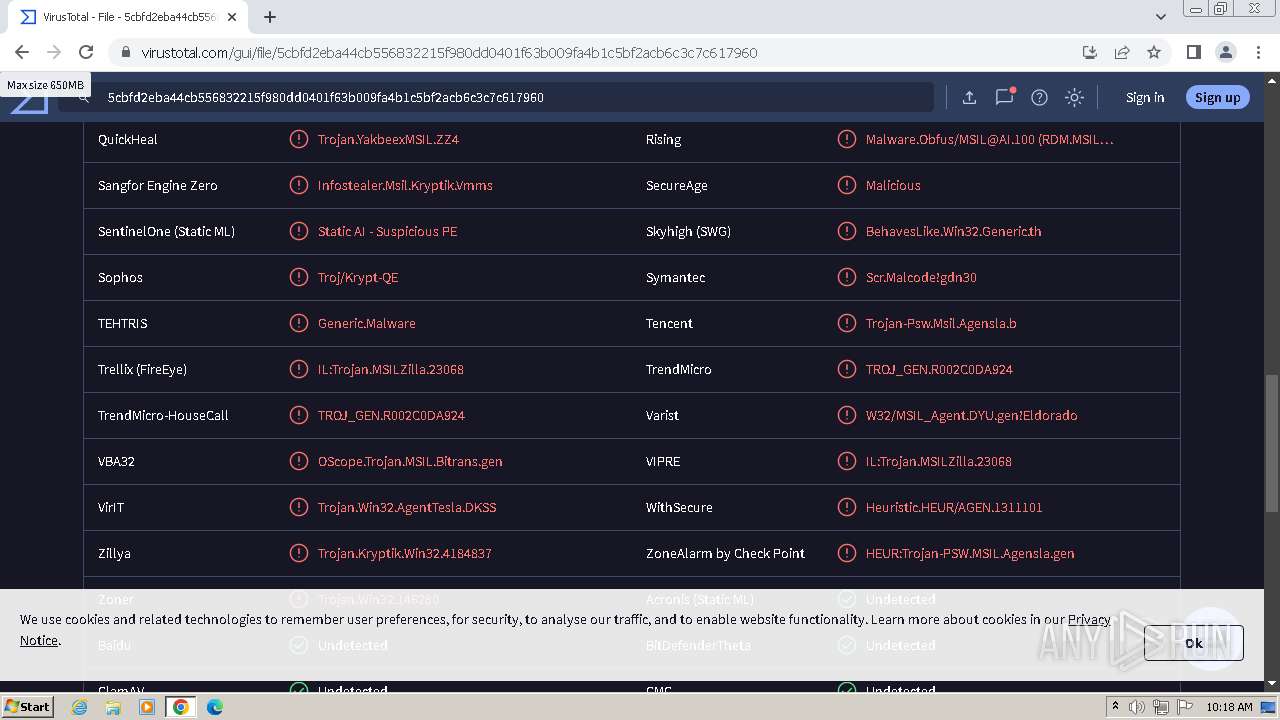
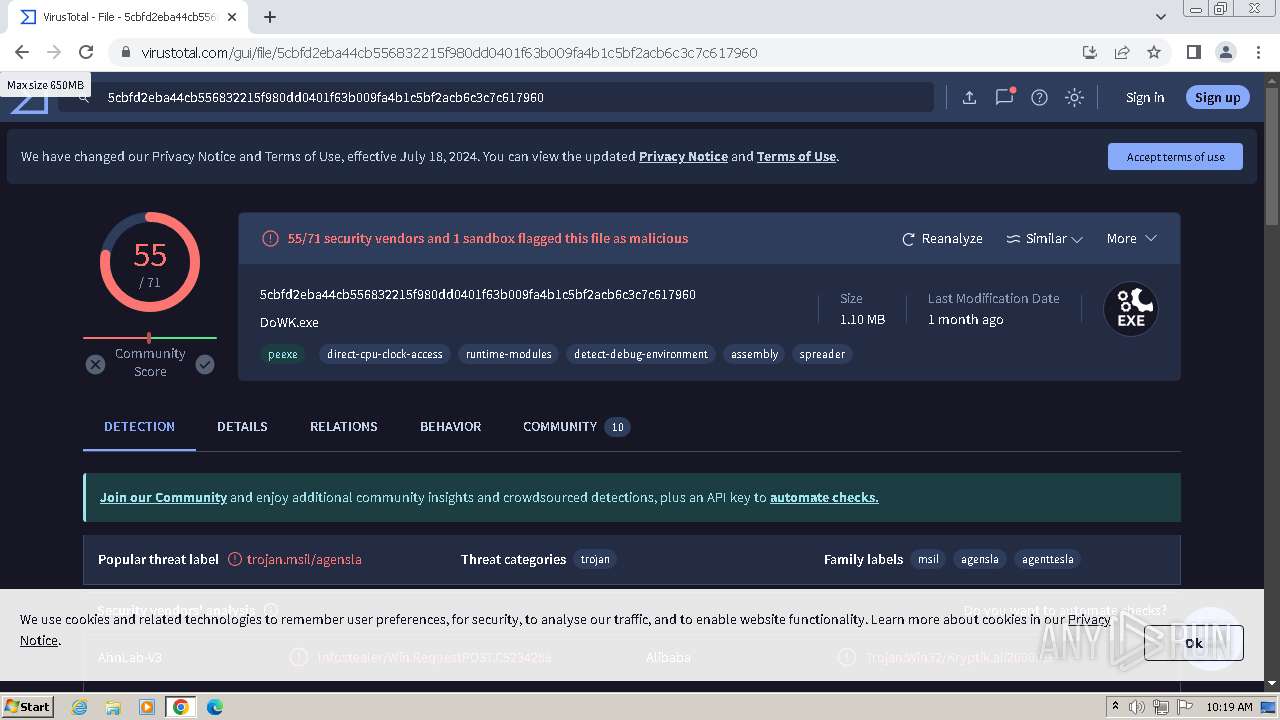
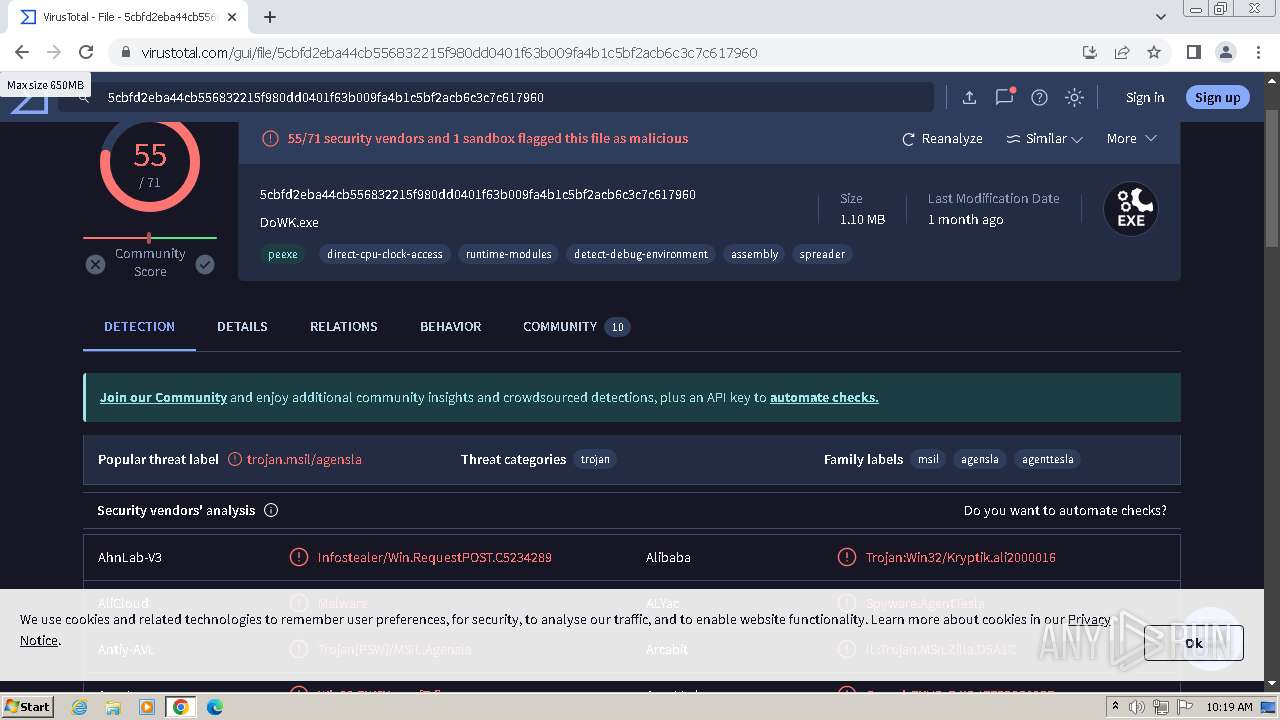
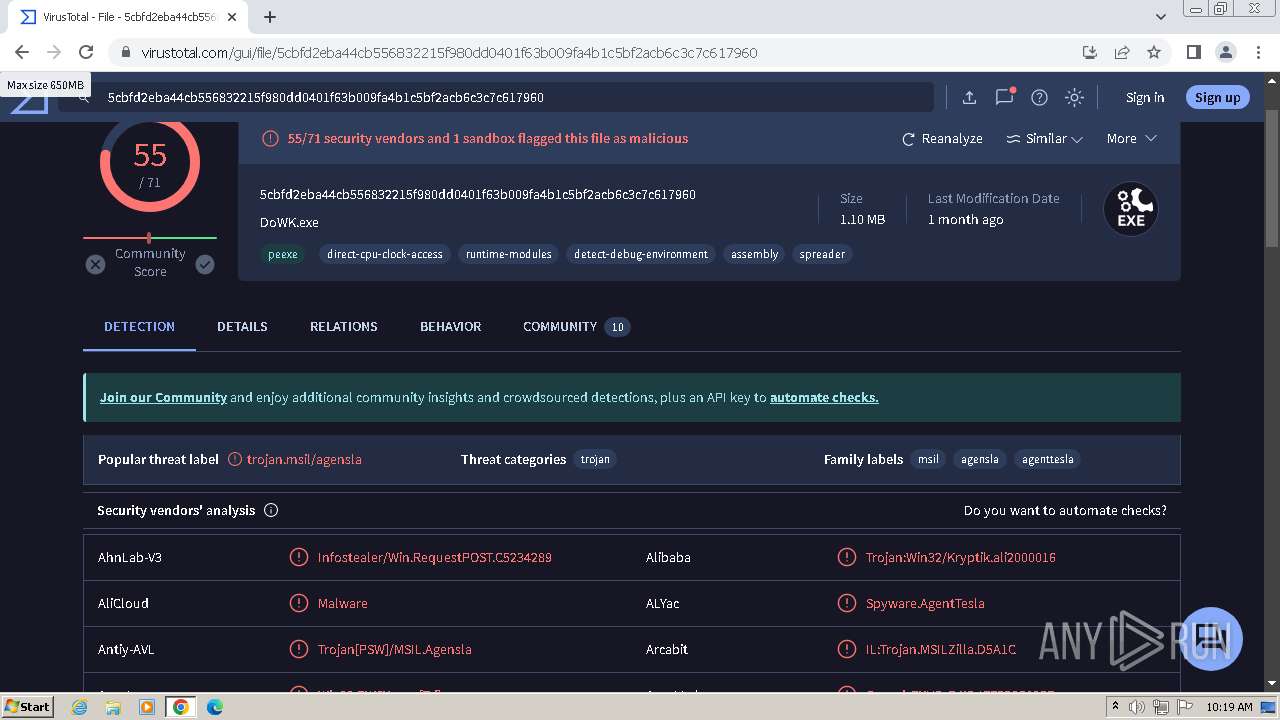
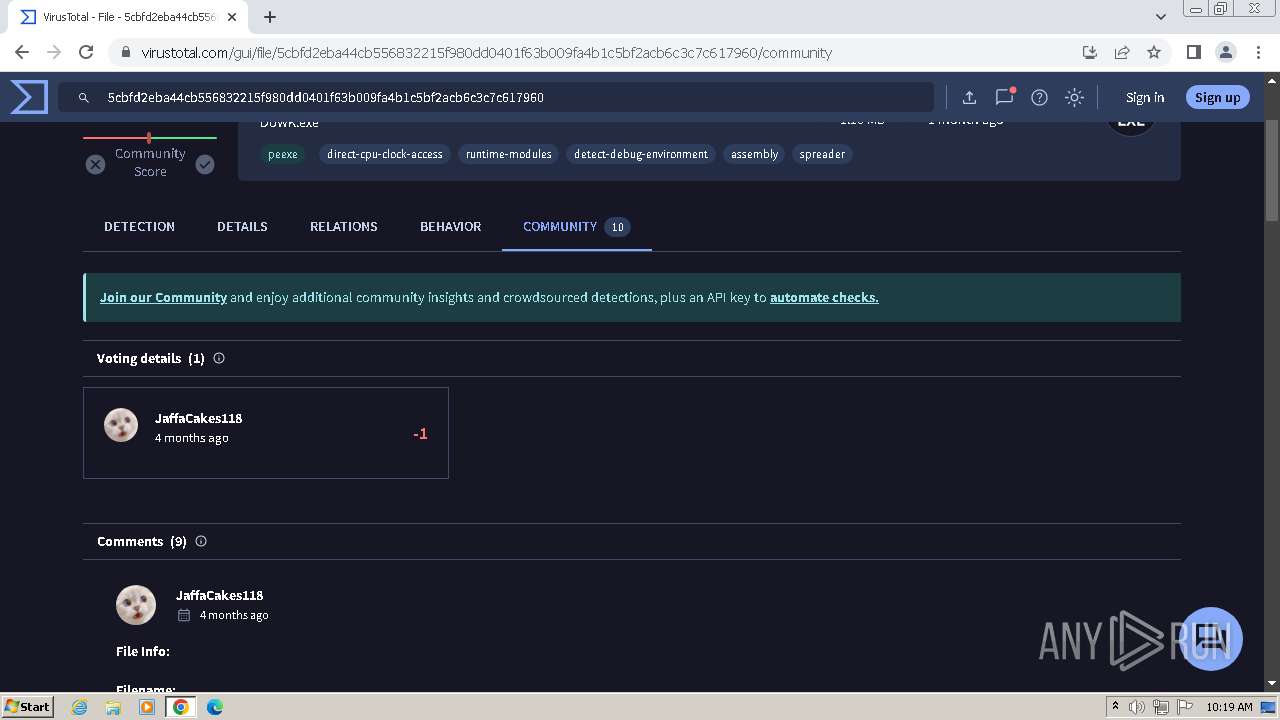
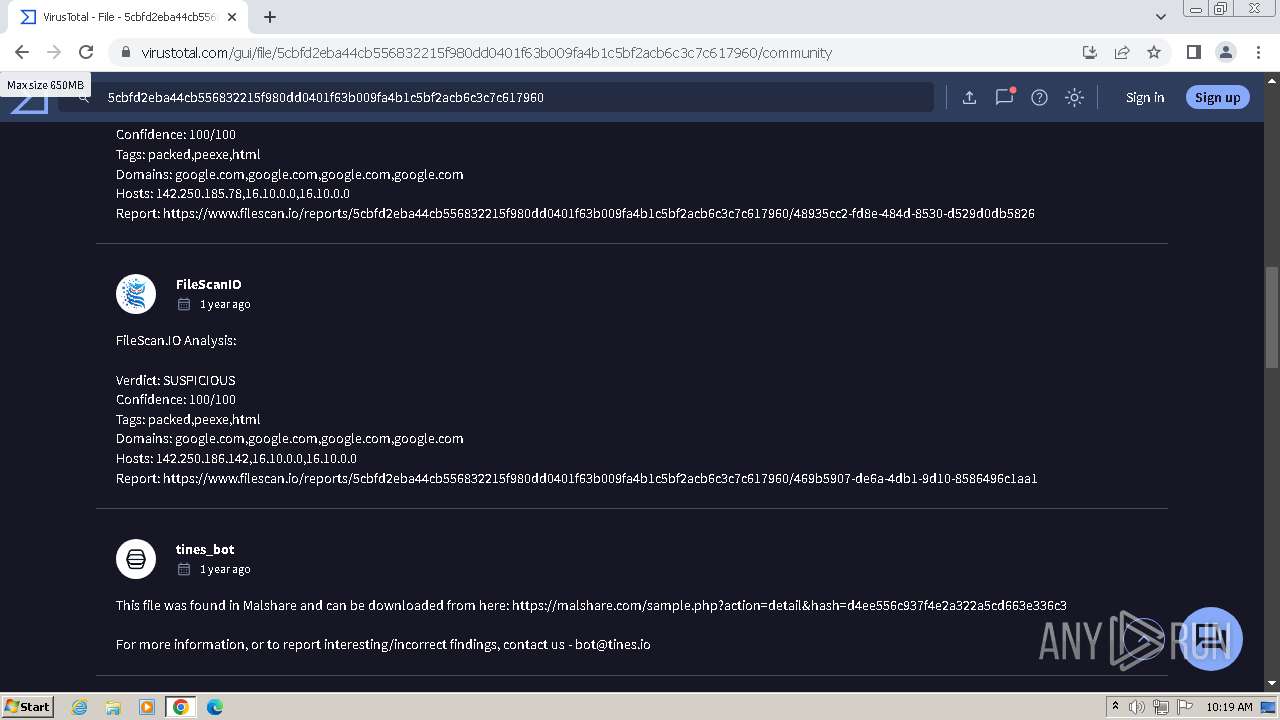
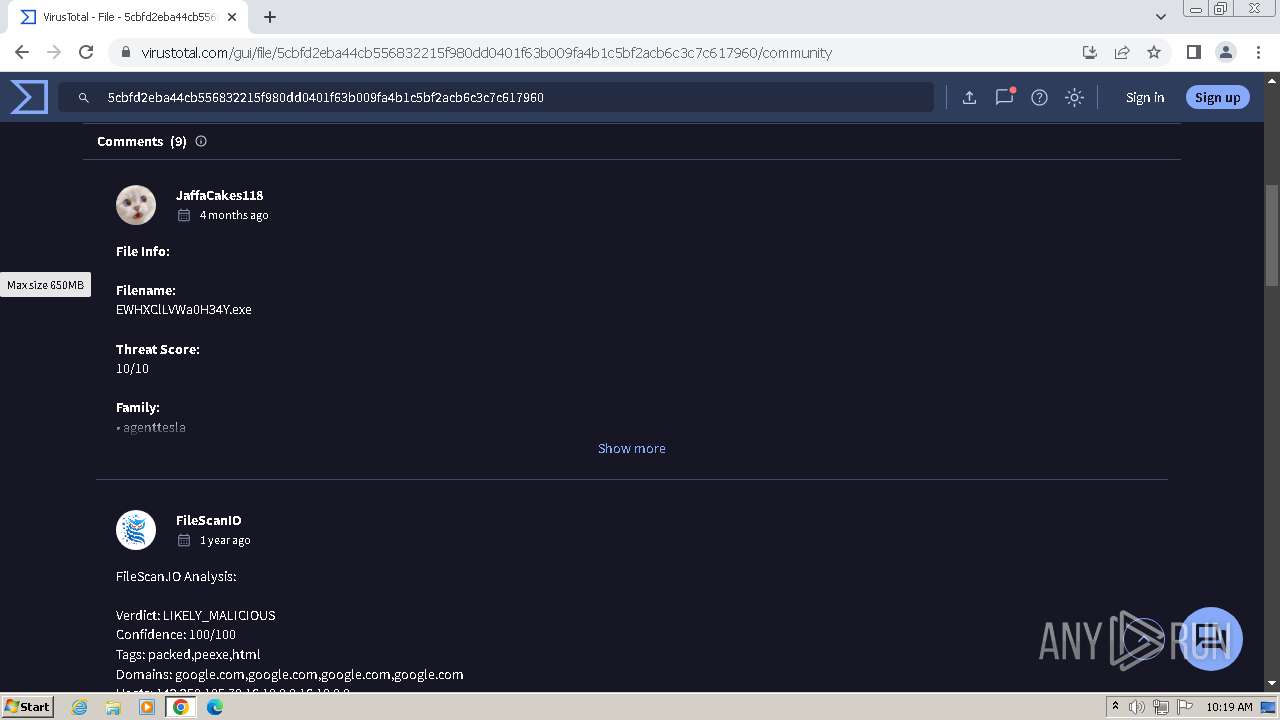
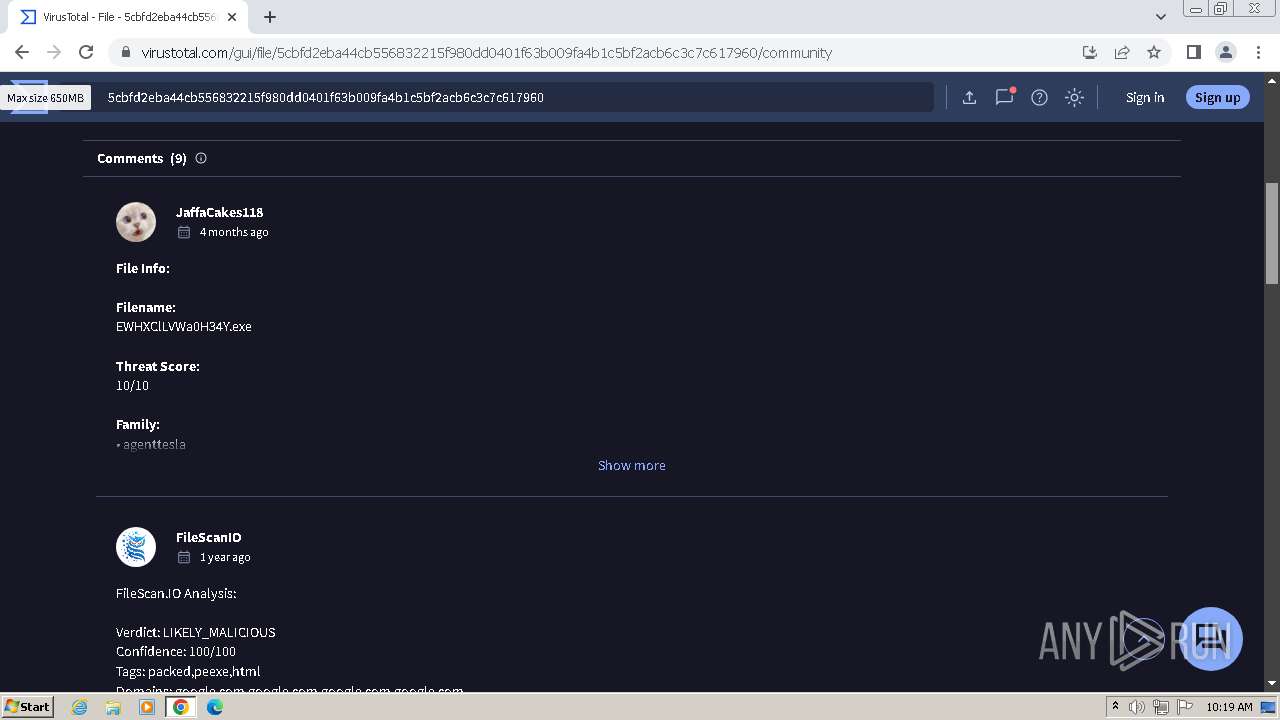
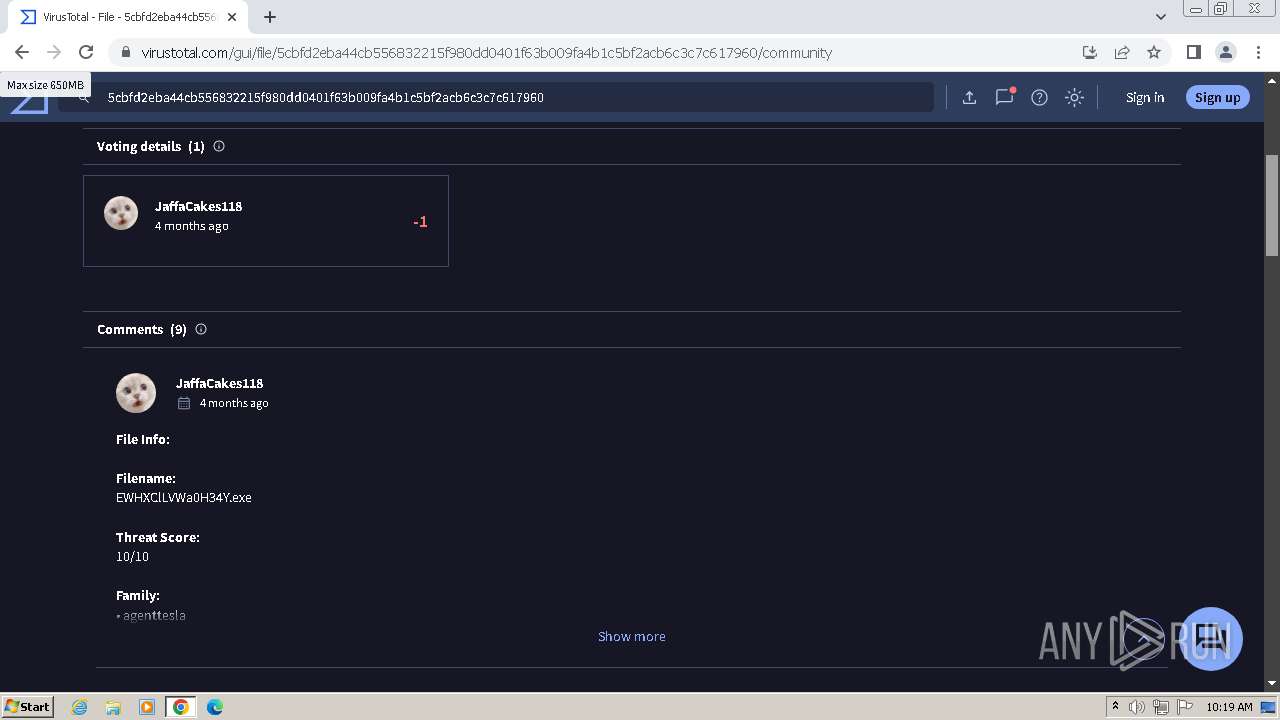
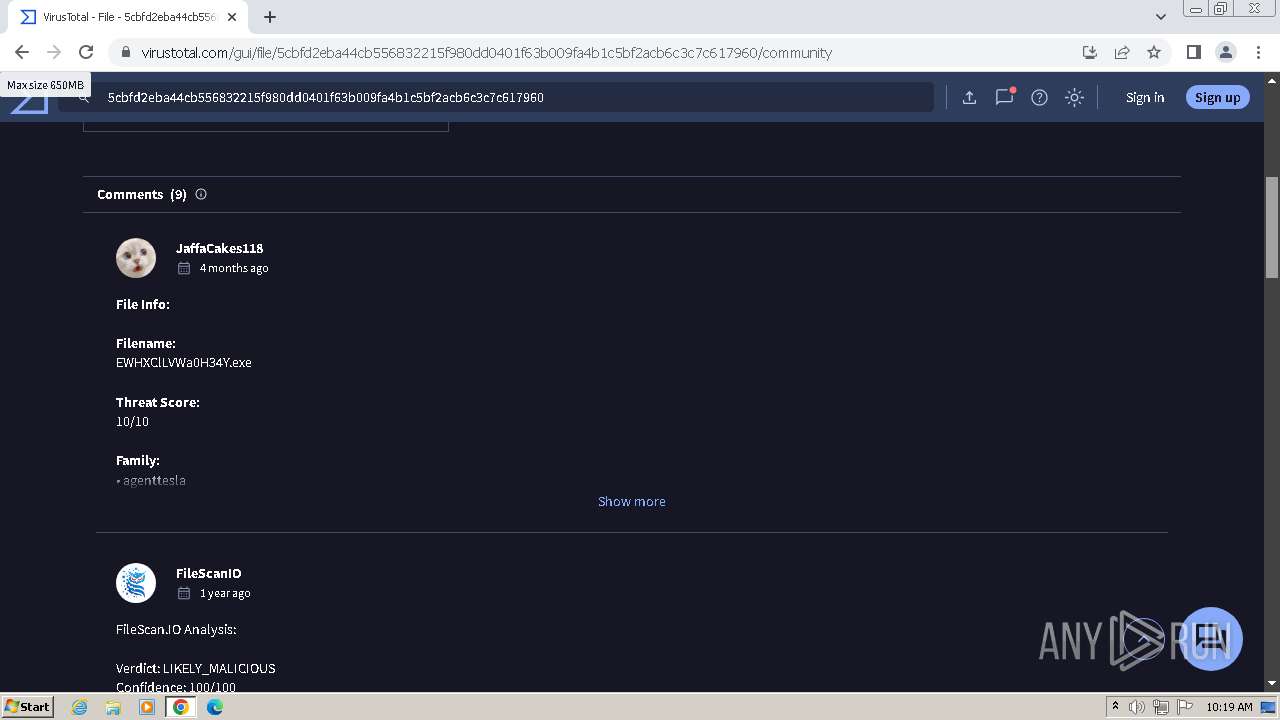
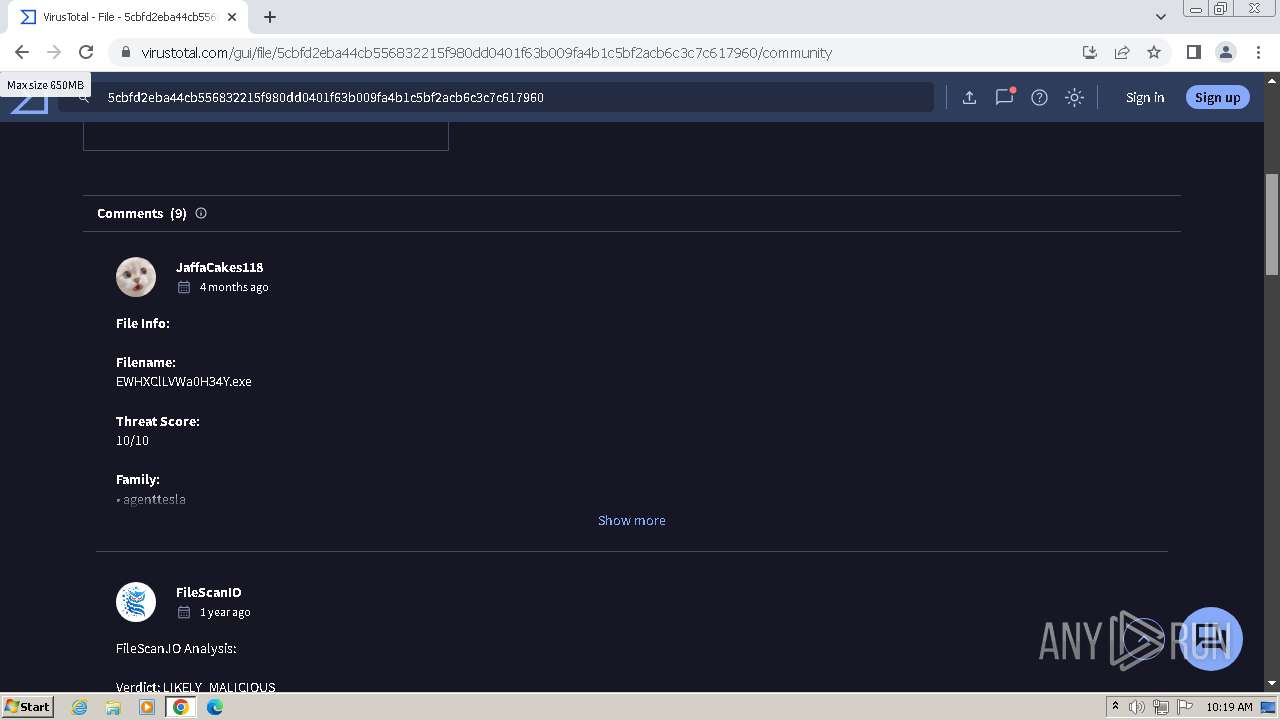
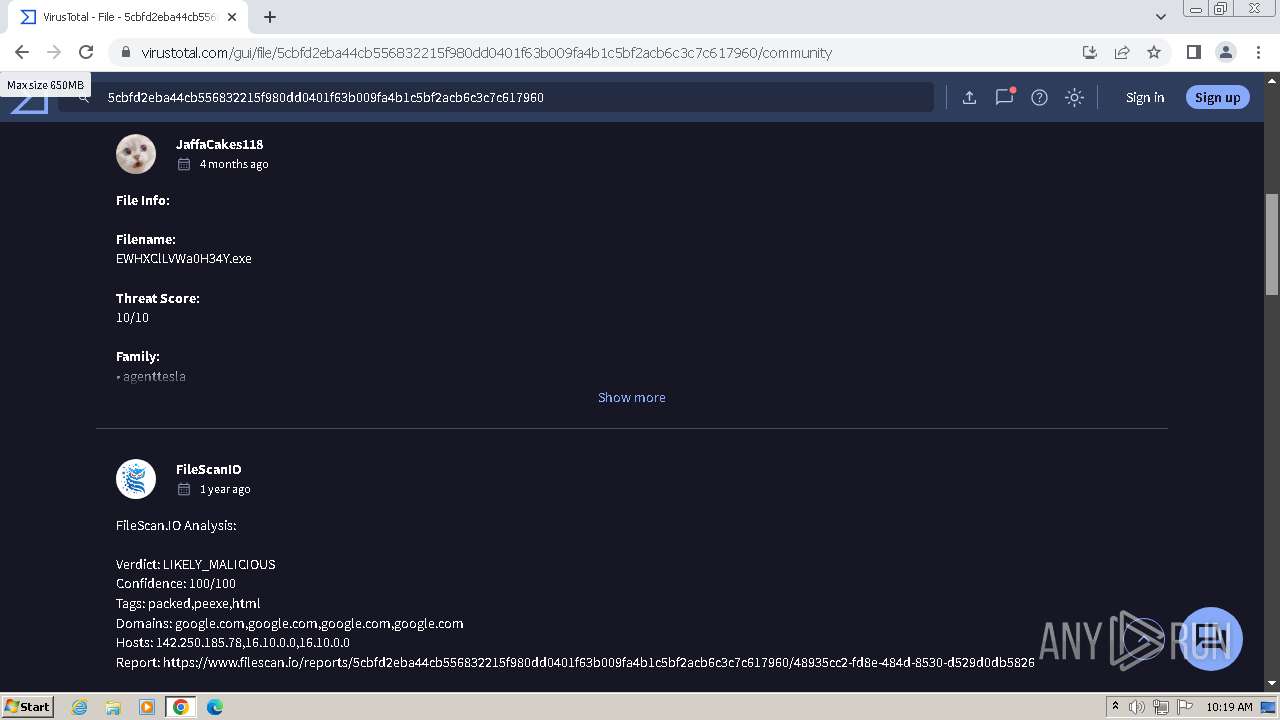
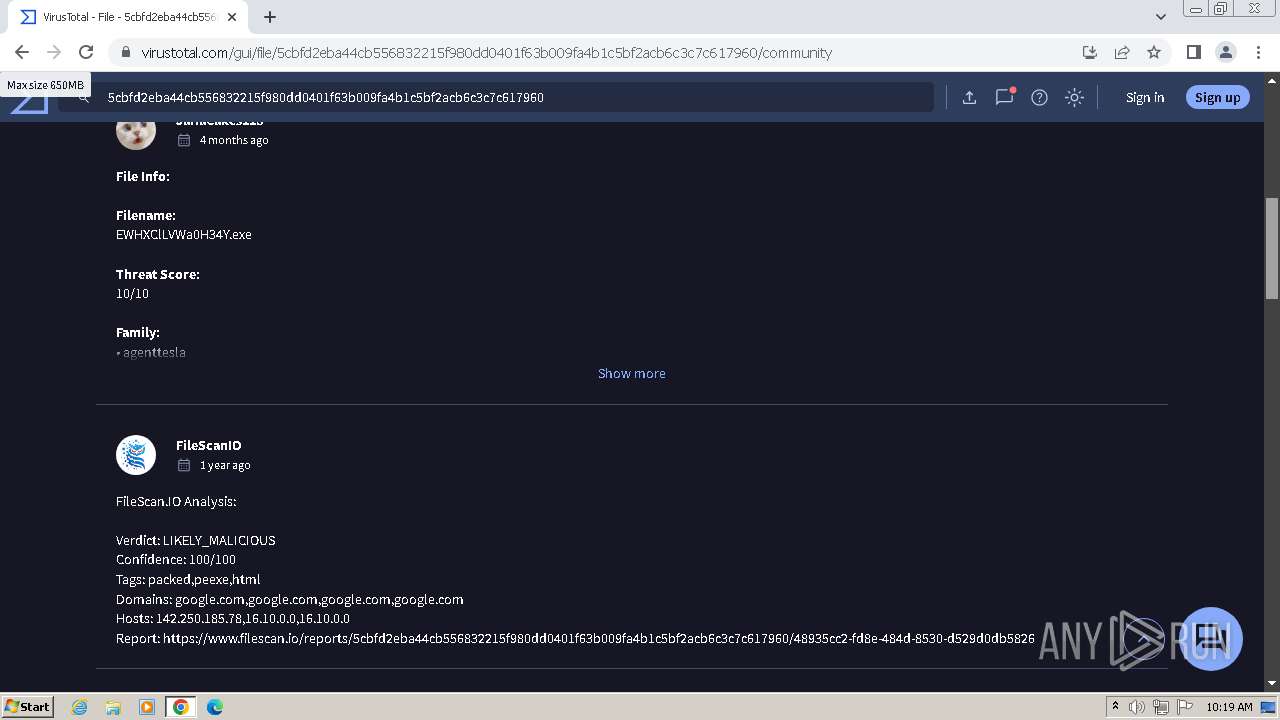
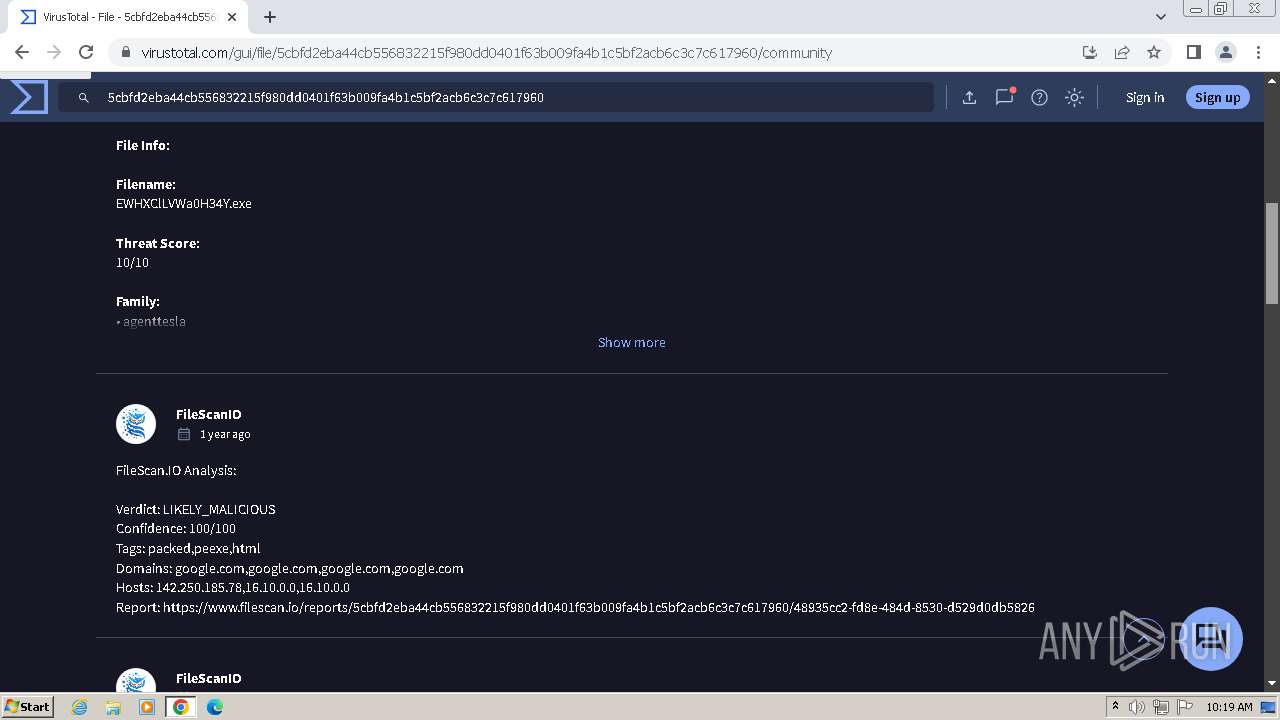
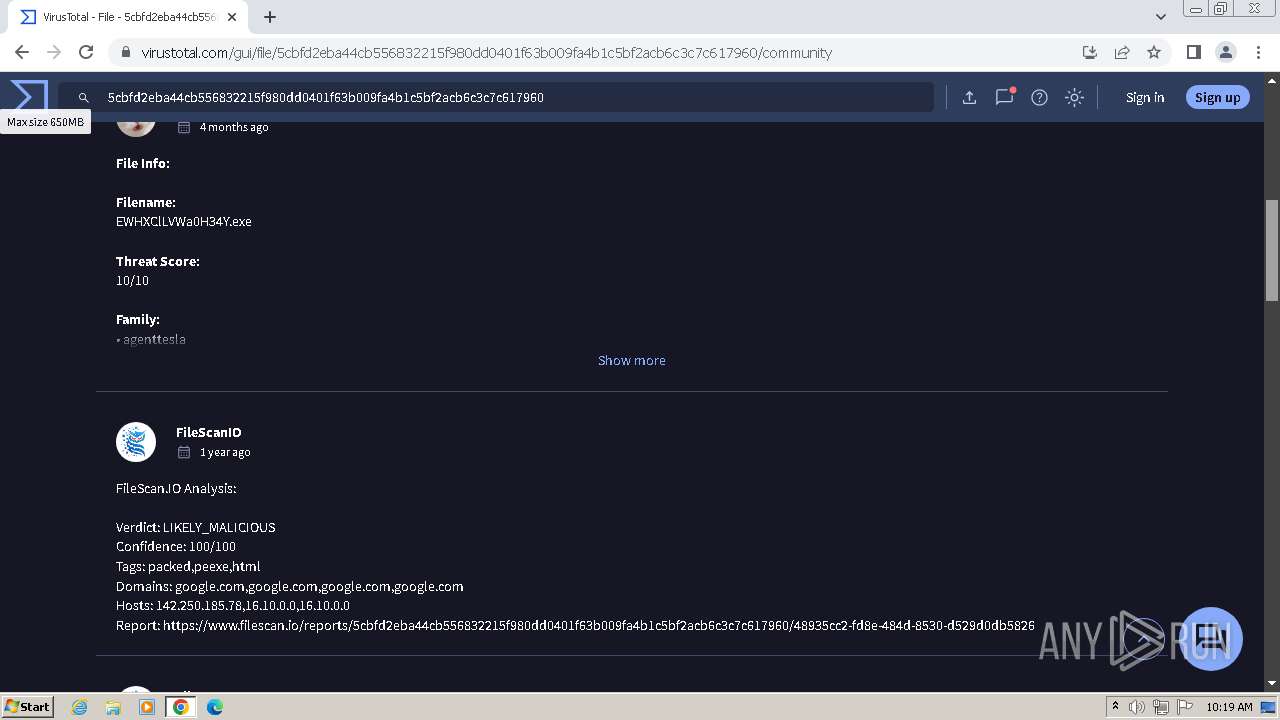
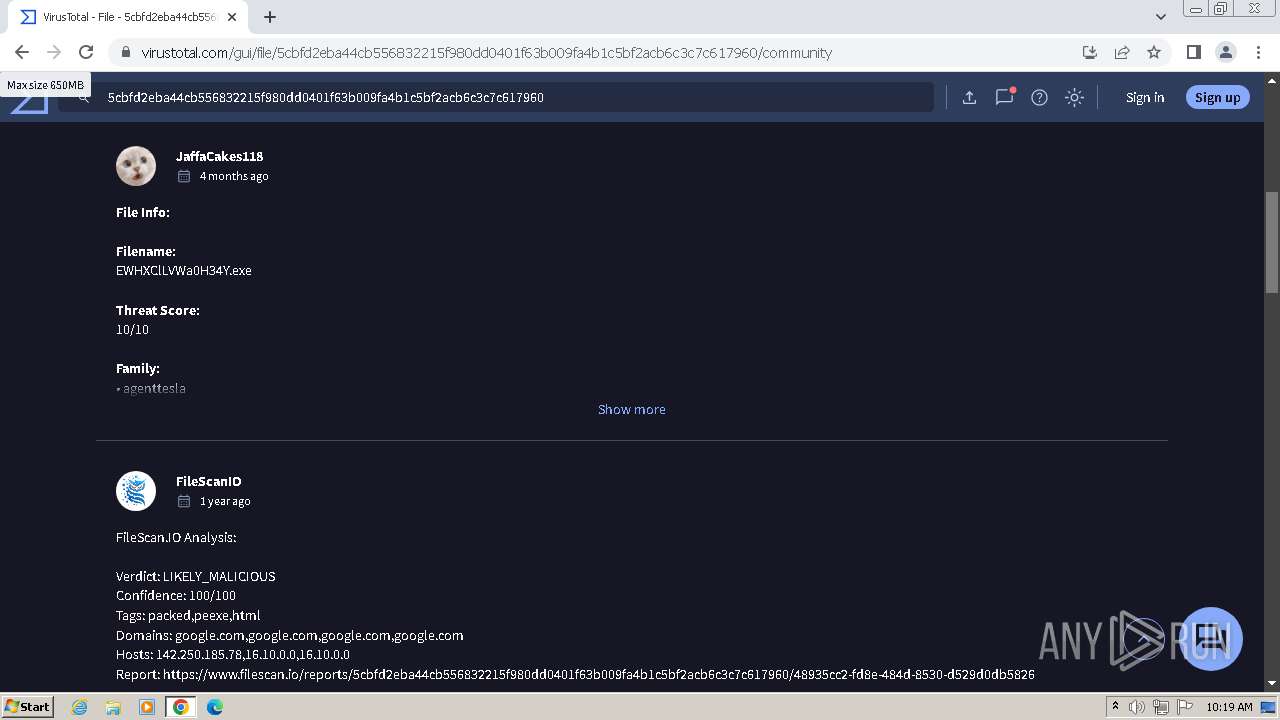
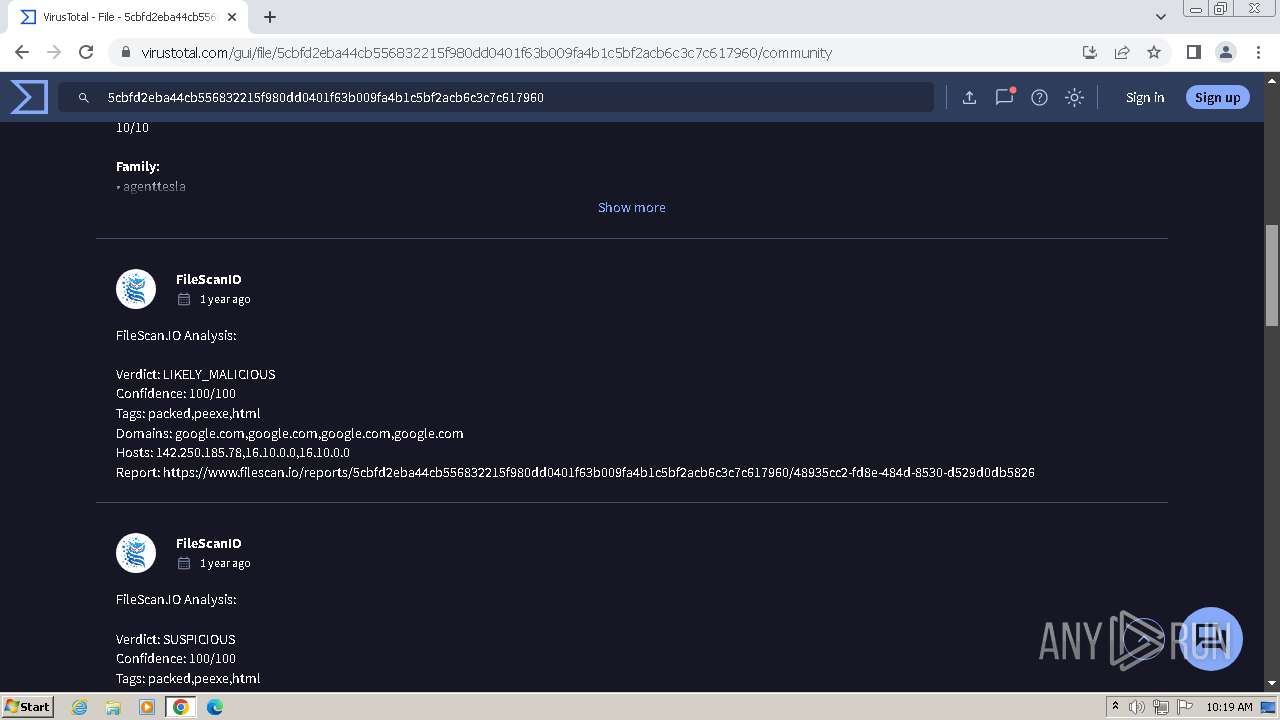
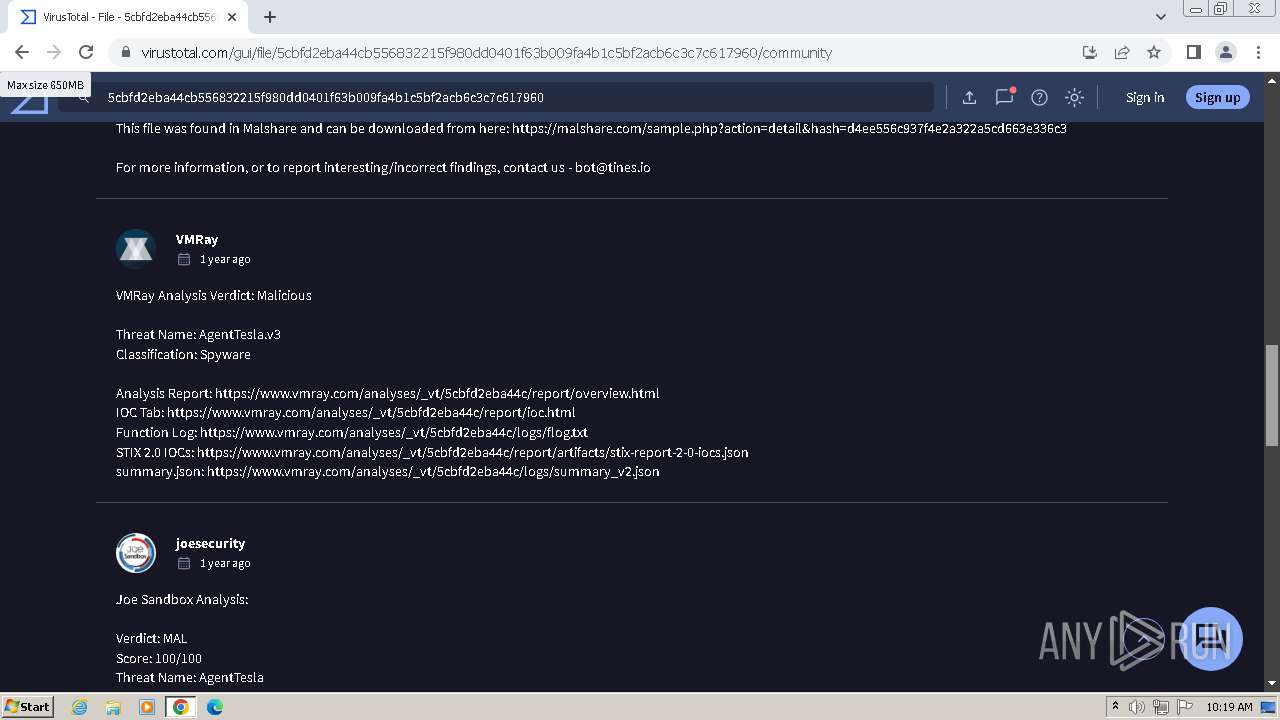
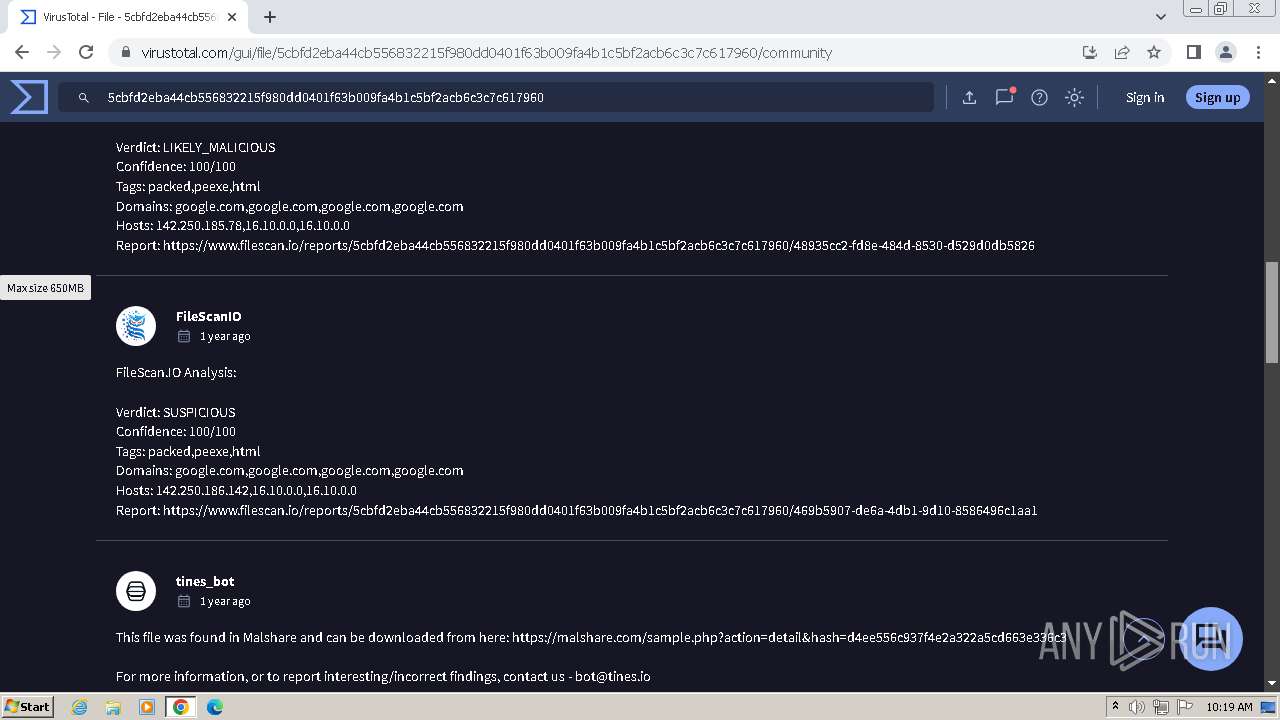
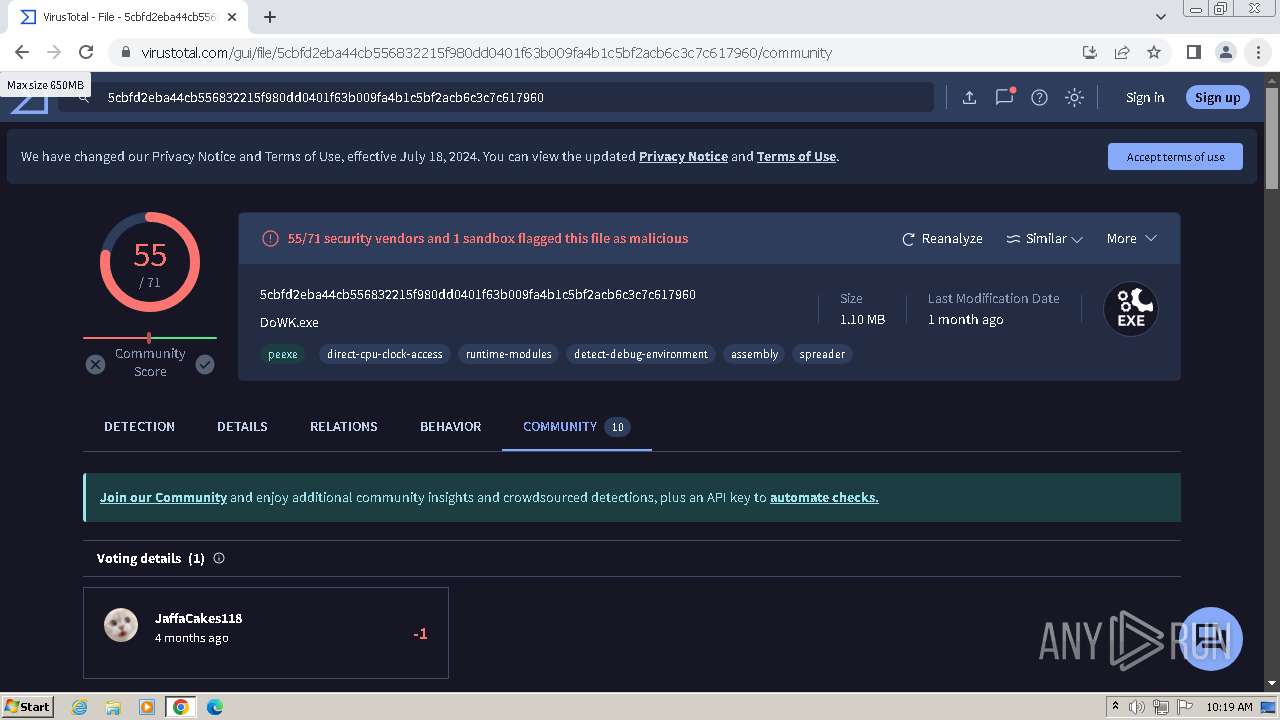
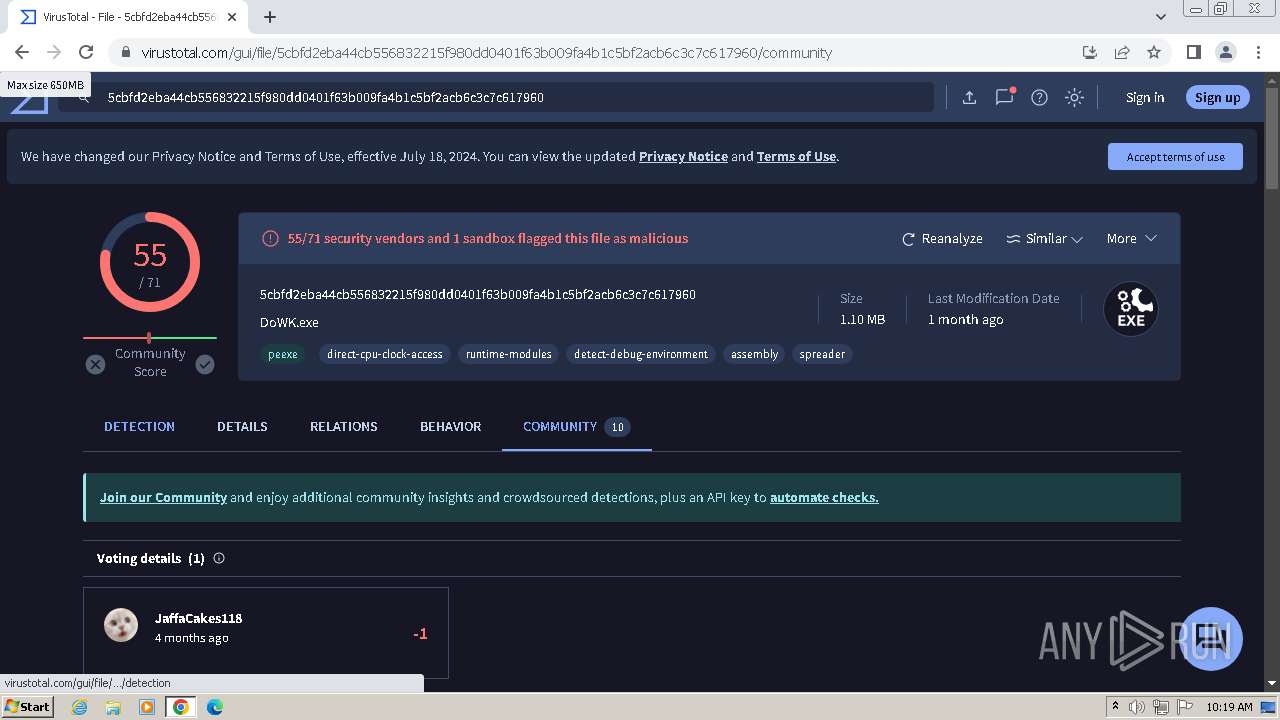
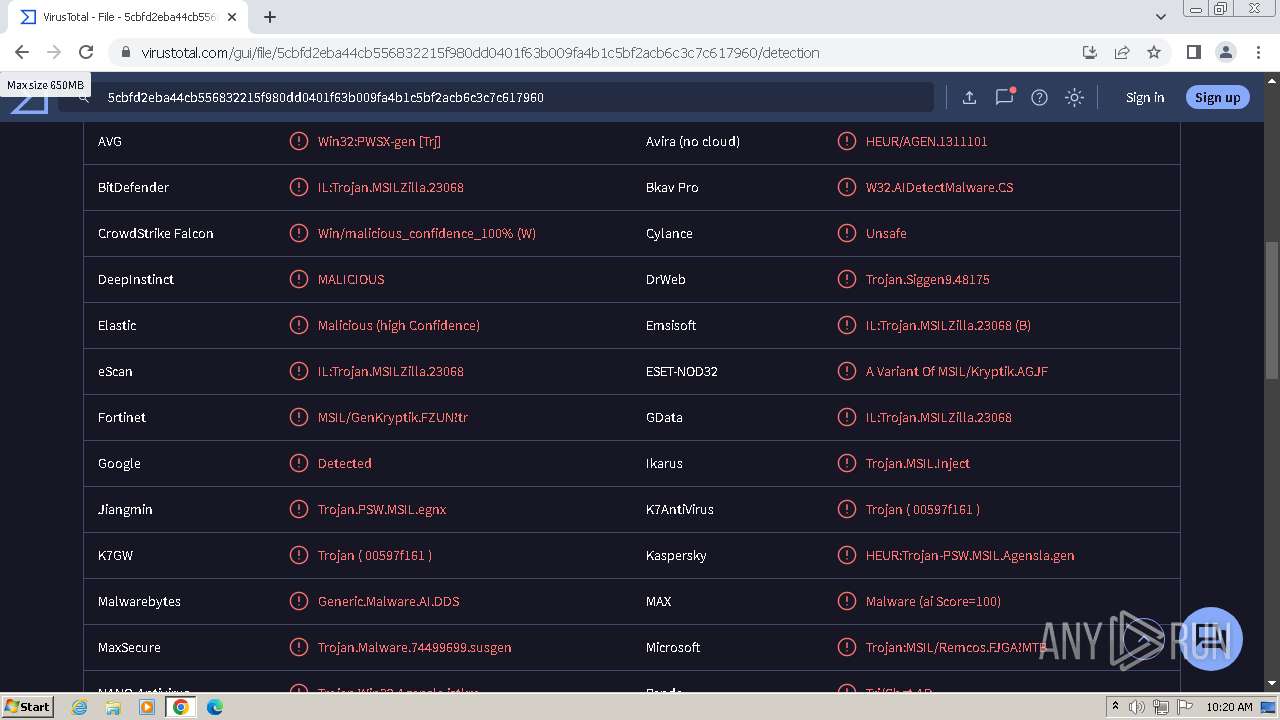
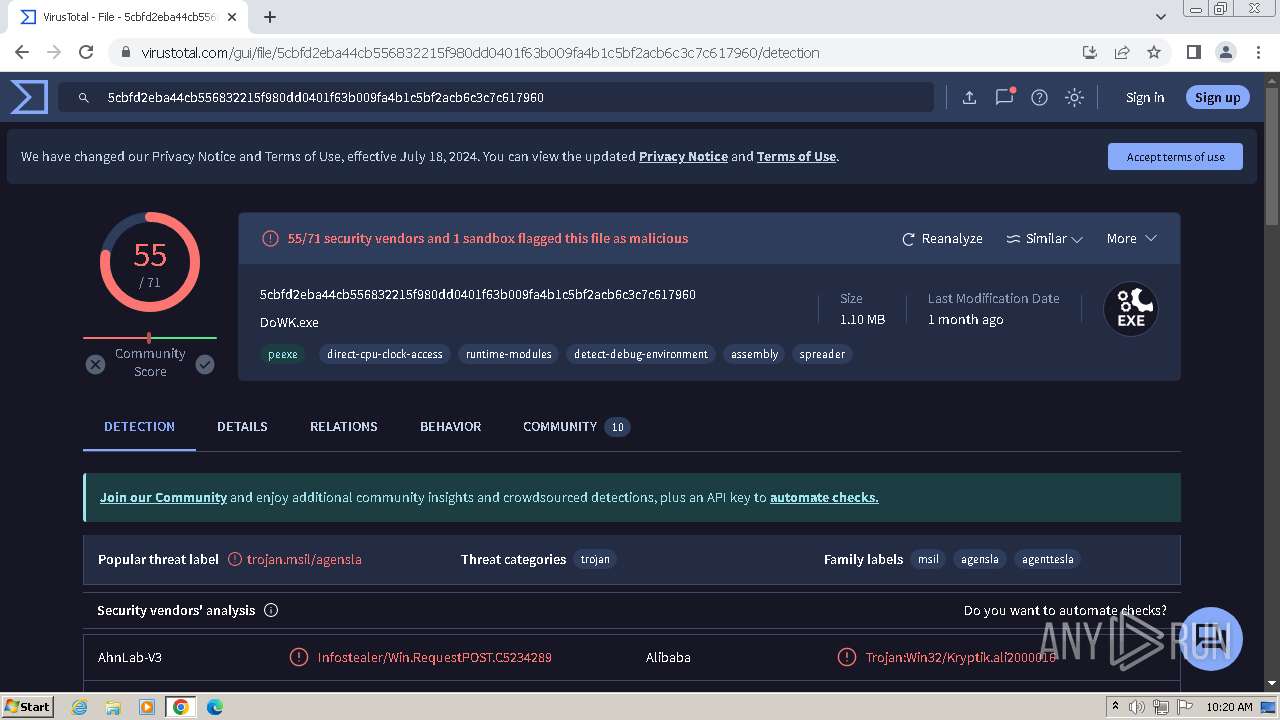
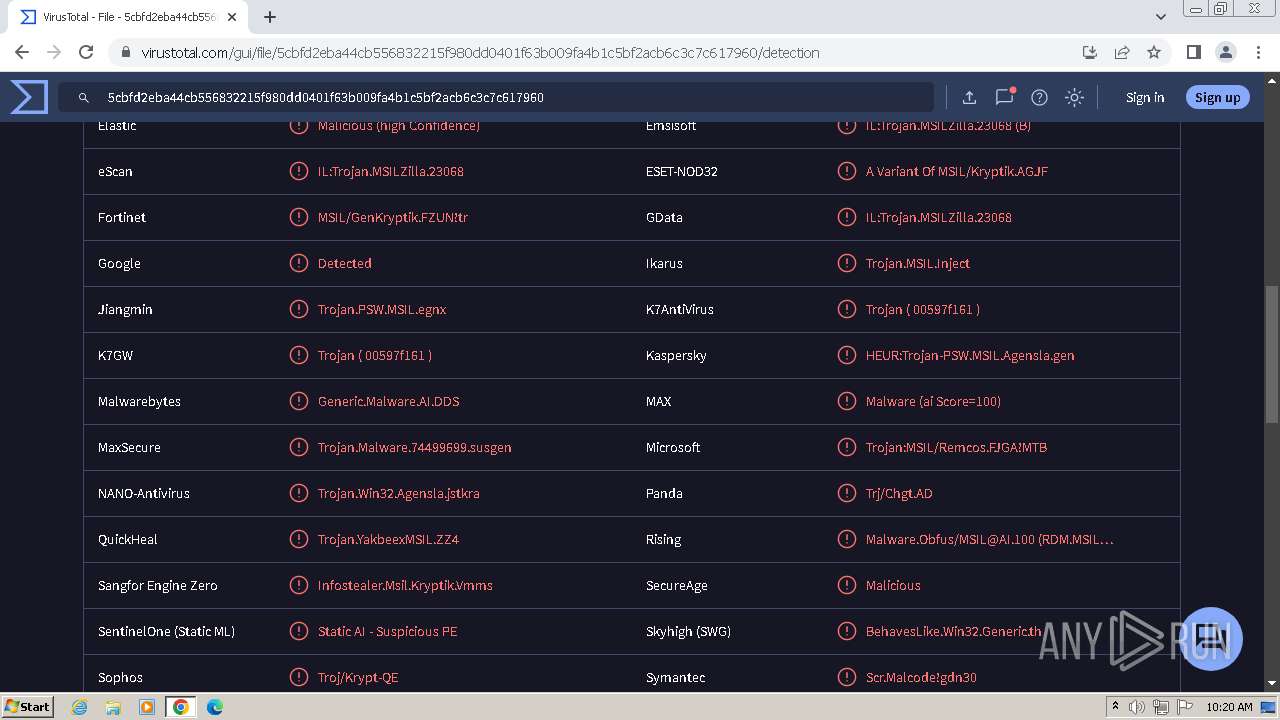
MALICIOUS
Drops the executable file immediately after the start
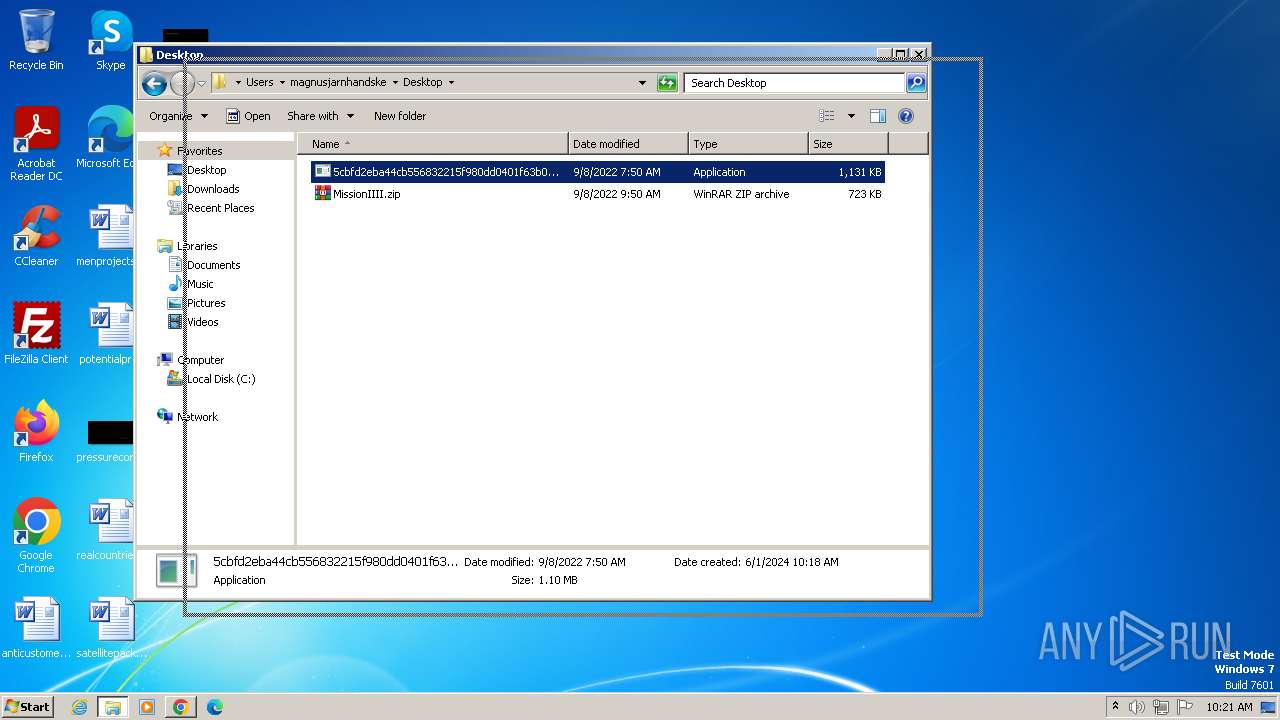
- 5cbfd2eba44cb556832215f980dd0401f63b009fa4b1c5bf2acb6c3c7c617960.exe (PID: 2060)
Steals credentials from Web Browsers
- 5cbfd2eba44cb556832215f980dd0401f63b009fa4b1c5bf2acb6c3c7c617960.exe (PID: 2060)
AGENTTESLA has been detected (YARA)
- 5cbfd2eba44cb556832215f980dd0401f63b009fa4b1c5bf2acb6c3c7c617960.exe (PID: 2060)
Actions looks like stealing of personal data
- 5cbfd2eba44cb556832215f980dd0401f63b009fa4b1c5bf2acb6c3c7c617960.exe (PID: 2060)
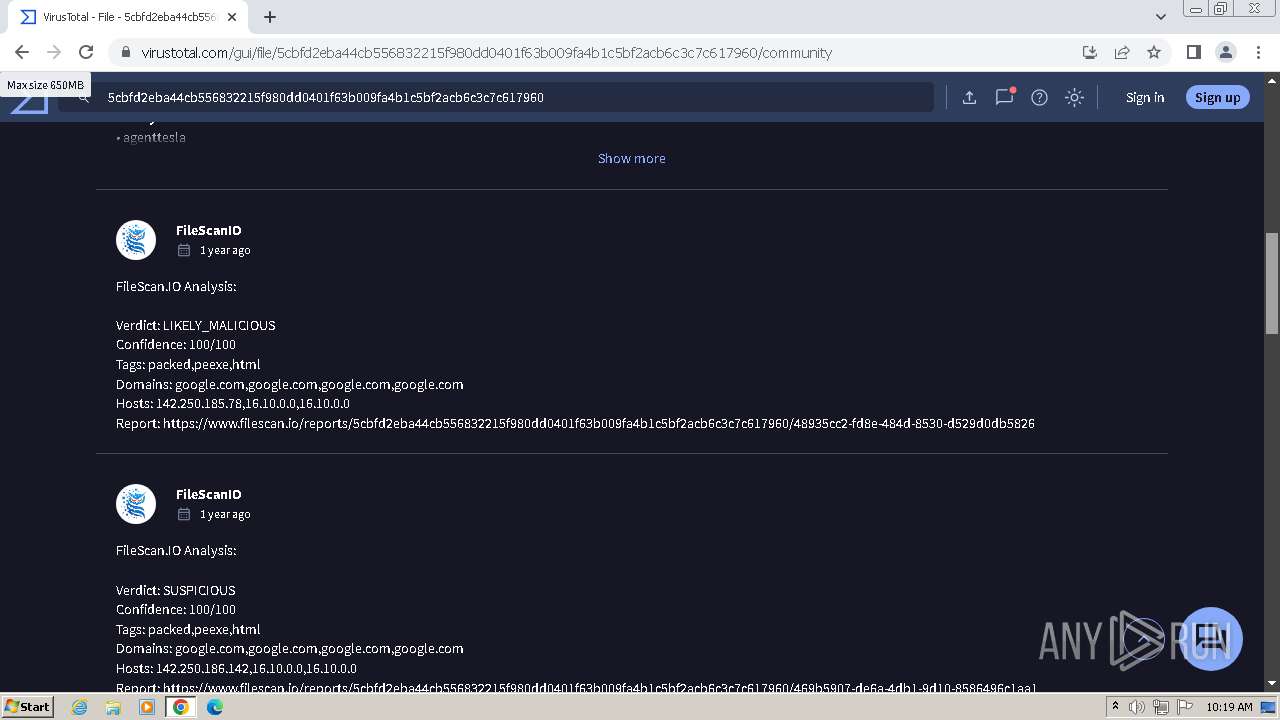
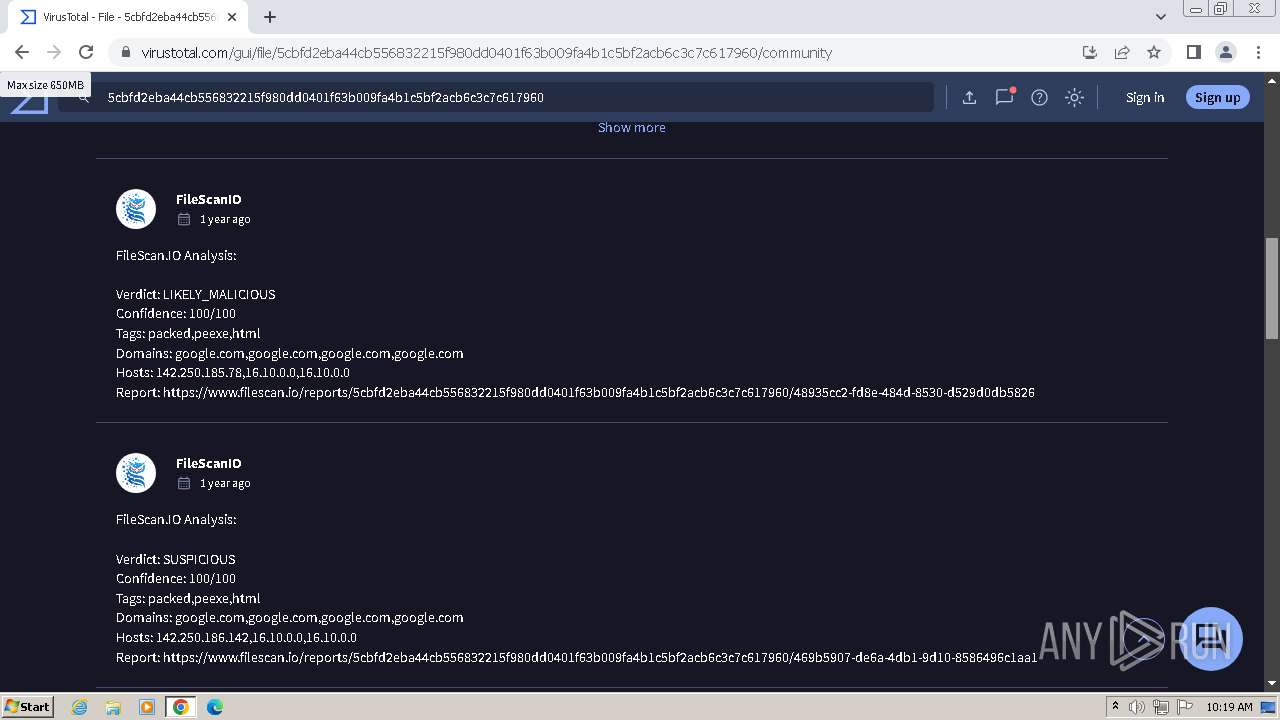
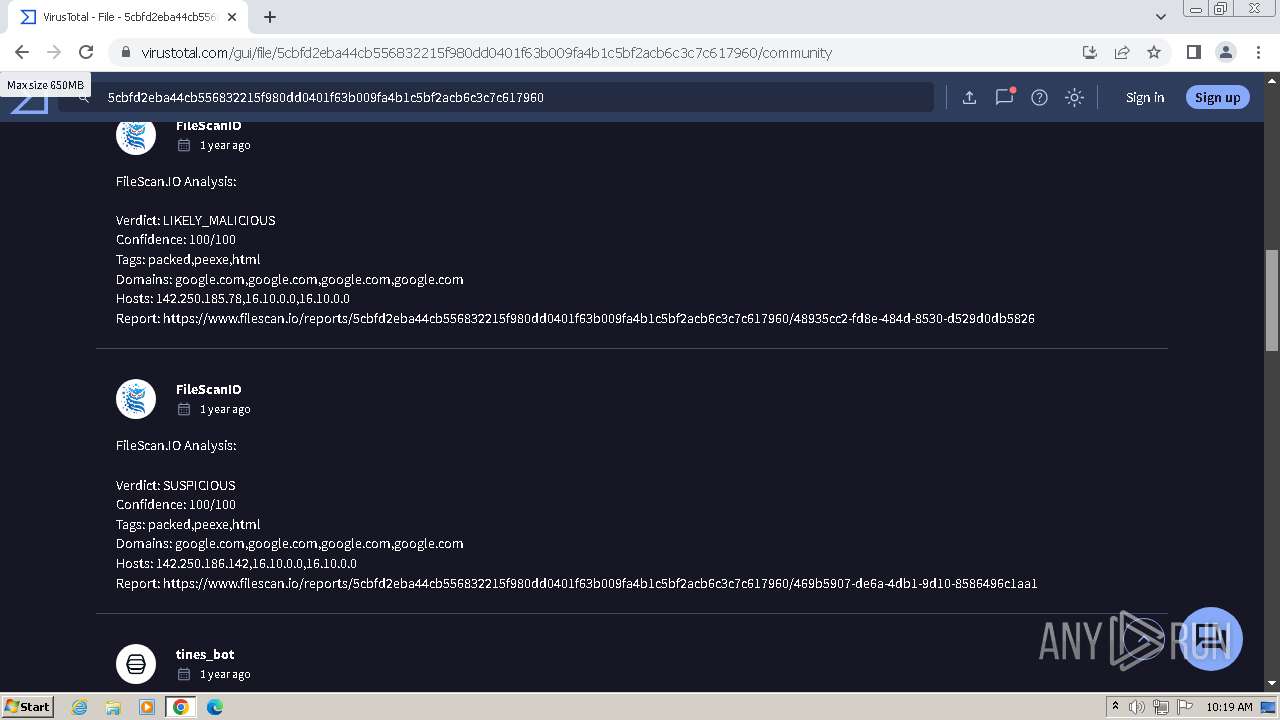
SUSPICIOUS
Executable content was dropped or overwritten
- 5cbfd2eba44cb556832215f980dd0401f63b009fa4b1c5bf2acb6c3c7c617960.exe (PID: 2060)
Application launched itself
- 5cbfd2eba44cb556832215f980dd0401f63b009fa4b1c5bf2acb6c3c7c617960.exe (PID: 3804)
Reads settings of System Certificates
- 5cbfd2eba44cb556832215f980dd0401f63b009fa4b1c5bf2acb6c3c7c617960.exe (PID: 2060)
Accesses Microsoft Outlook profiles
- 5cbfd2eba44cb556832215f980dd0401f63b009fa4b1c5bf2acb6c3c7c617960.exe (PID: 2060)
Adds/modifies Windows certificates
- 5cbfd2eba44cb556832215f980dd0401f63b009fa4b1c5bf2acb6c3c7c617960.exe (PID: 2060)
Connects to SMTP port
- 5cbfd2eba44cb556832215f980dd0401f63b009fa4b1c5bf2acb6c3c7c617960.exe (PID: 2060)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3972)
- chrome.exe (PID: 3032)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 3972)
- chrome.exe (PID: 3032)
Checks supported languages
- wmpnscfg.exe (PID: 444)
- 5cbfd2eba44cb556832215f980dd0401f63b009fa4b1c5bf2acb6c3c7c617960.exe (PID: 3804)
- 5cbfd2eba44cb556832215f980dd0401f63b009fa4b1c5bf2acb6c3c7c617960.exe (PID: 2060)
Reads the computer name
- wmpnscfg.exe (PID: 444)
- 5cbfd2eba44cb556832215f980dd0401f63b009fa4b1c5bf2acb6c3c7c617960.exe (PID: 3804)
- 5cbfd2eba44cb556832215f980dd0401f63b009fa4b1c5bf2acb6c3c7c617960.exe (PID: 2060)
Reads the machine GUID from the registry
- 5cbfd2eba44cb556832215f980dd0401f63b009fa4b1c5bf2acb6c3c7c617960.exe (PID: 3804)
- 5cbfd2eba44cb556832215f980dd0401f63b009fa4b1c5bf2acb6c3c7c617960.exe (PID: 2060)
Application launched itself
- chrome.exe (PID: 2104)
Reads Environment values
- 5cbfd2eba44cb556832215f980dd0401f63b009fa4b1c5bf2acb6c3c7c617960.exe (PID: 2060)
Manual execution by a user
- wmpnscfg.exe (PID: 444)
- chrome.exe (PID: 2104)
- 5cbfd2eba44cb556832215f980dd0401f63b009fa4b1c5bf2acb6c3c7c617960.exe (PID: 3804)
Reads the software policy settings
- 5cbfd2eba44cb556832215f980dd0401f63b009fa4b1c5bf2acb6c3c7c617960.exe (PID: 2060)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
AgentTesla
(PID) Process(2060) 5cbfd2eba44cb556832215f980dd0401f63b009fa4b1c5bf2acb6c3c7c617960.exe
Protocolsmtp
Hostmail.bohotels.hu
Port587
Usernamedirector@bo18hotel.hu
Passwordv4Jdahdirect
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | None |
| ZipModifyDate: | 2022:09:08 10:50:50 |
| ZipCRC: | 0x5692091a |
| ZipCompressedSize: | 740339 |
| ZipUncompressedSize: | 740339 |
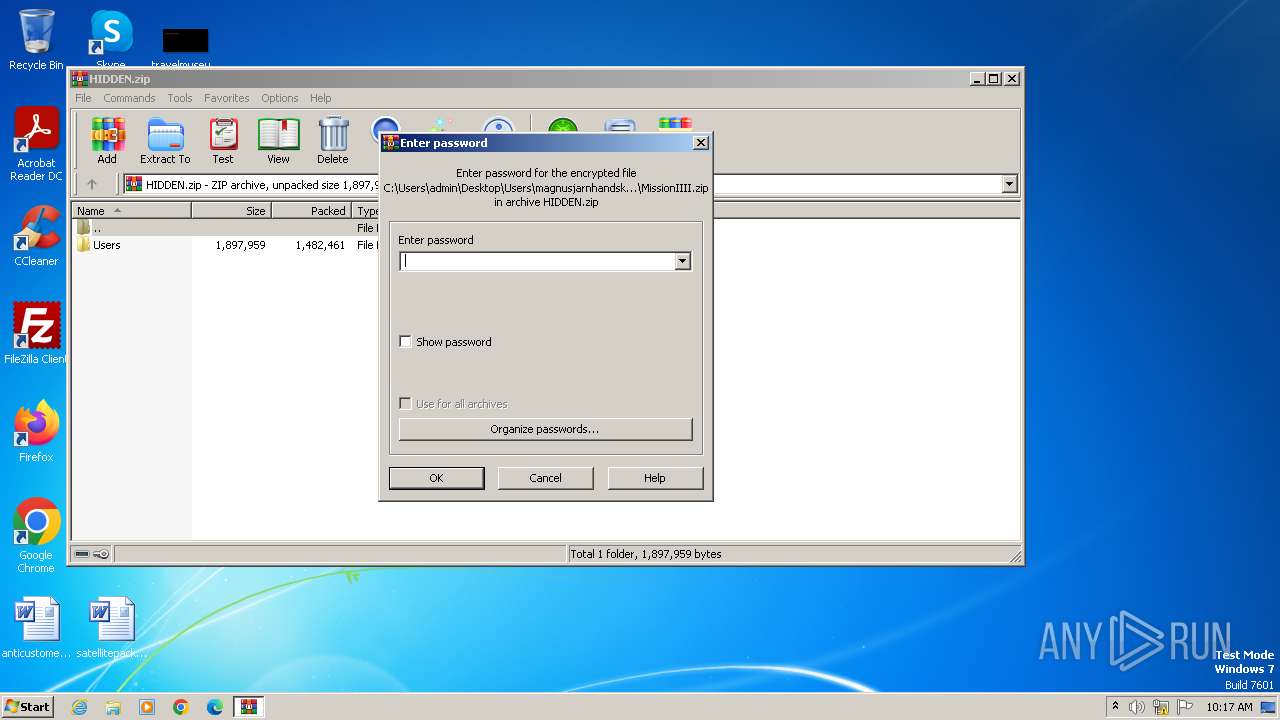
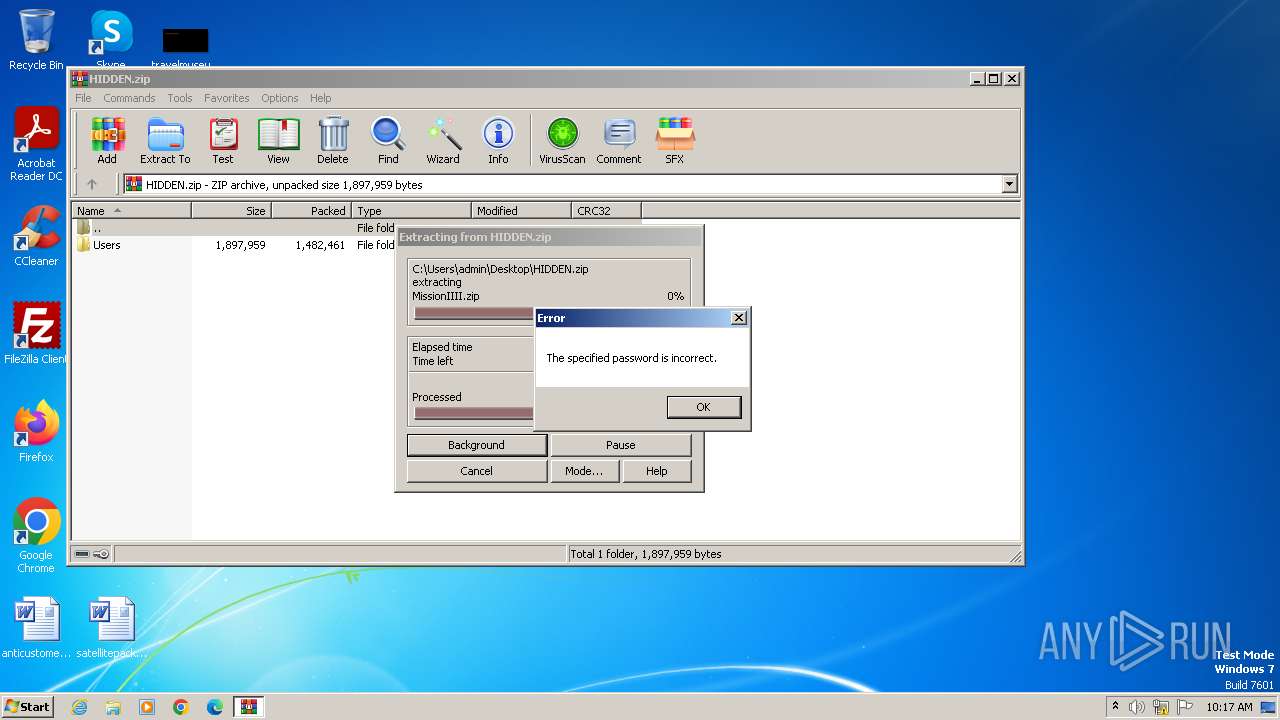
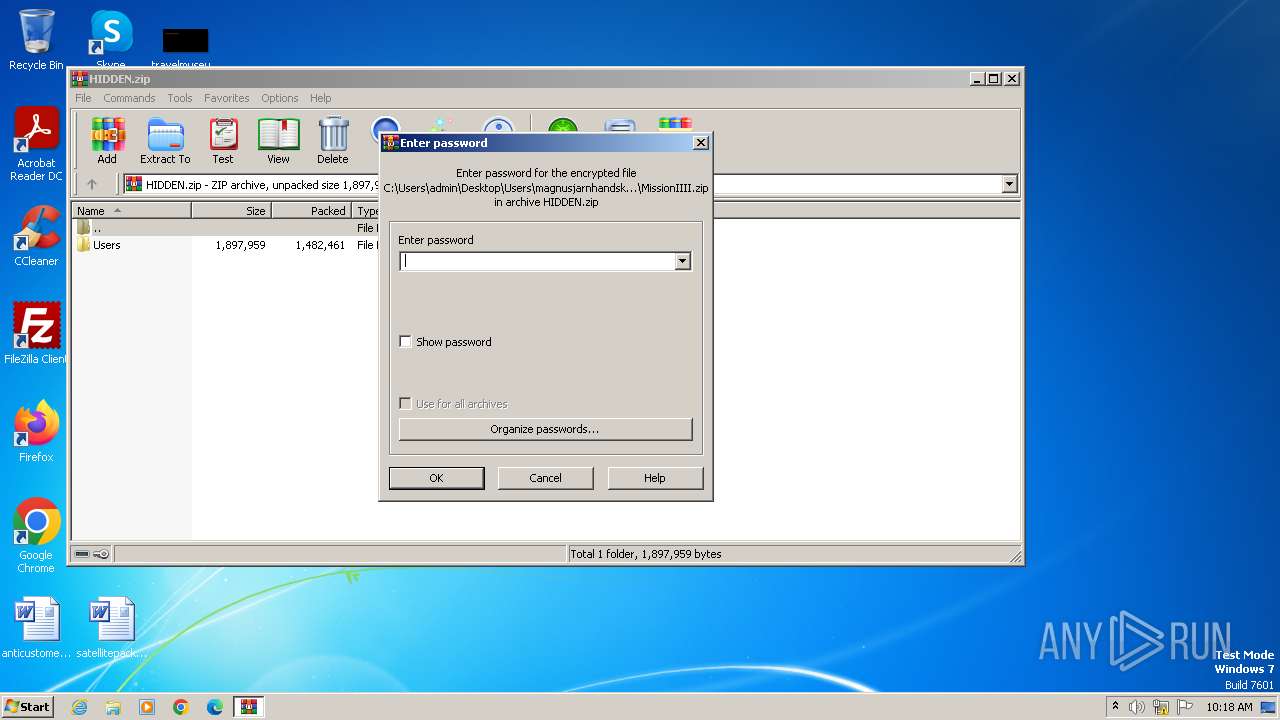
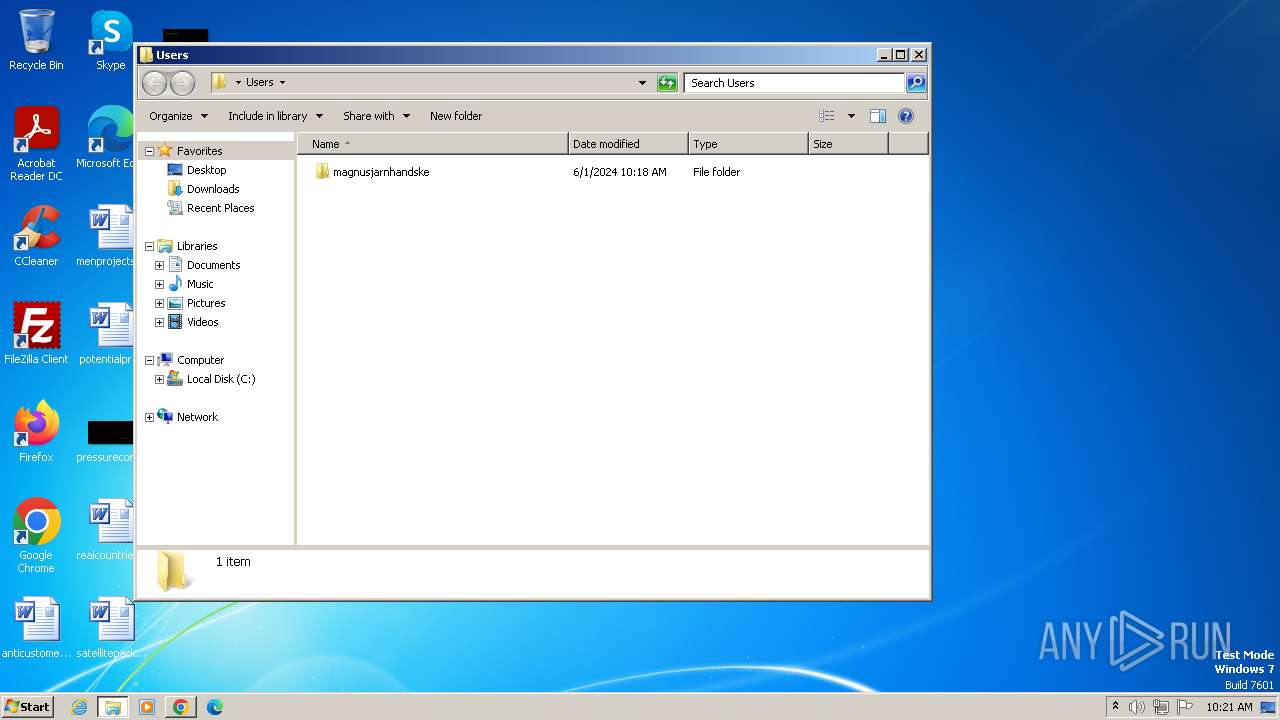
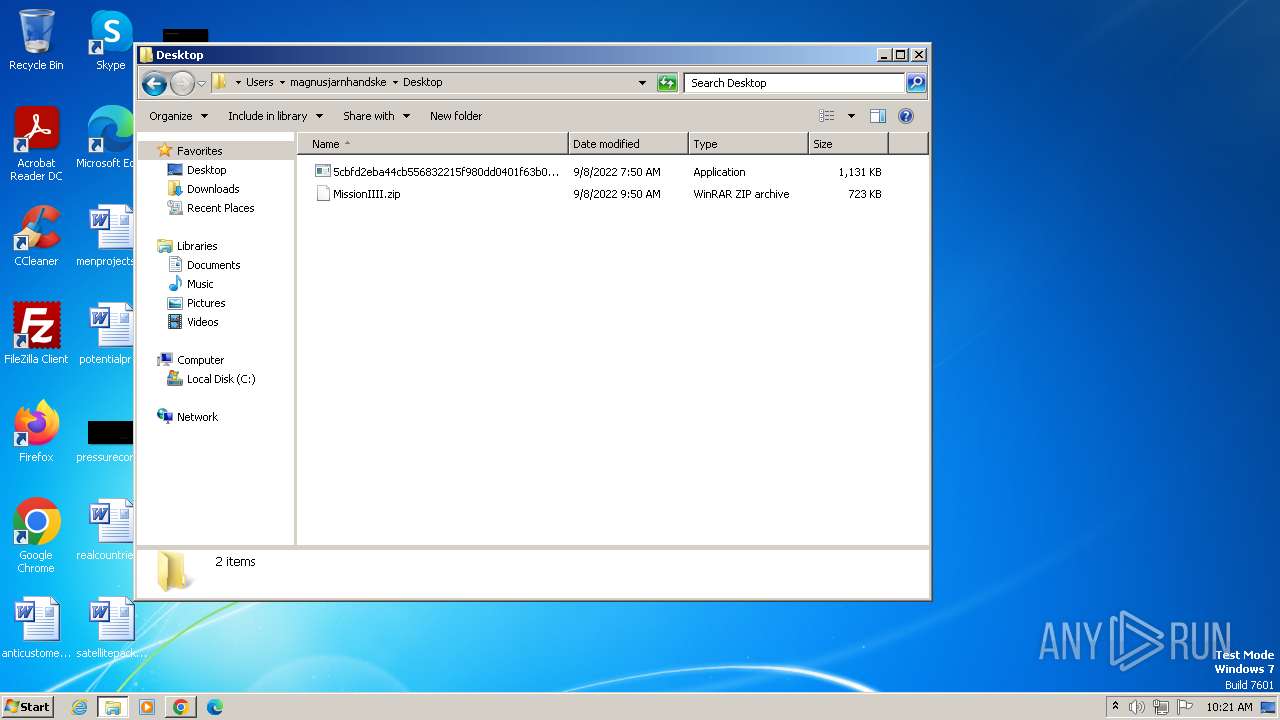
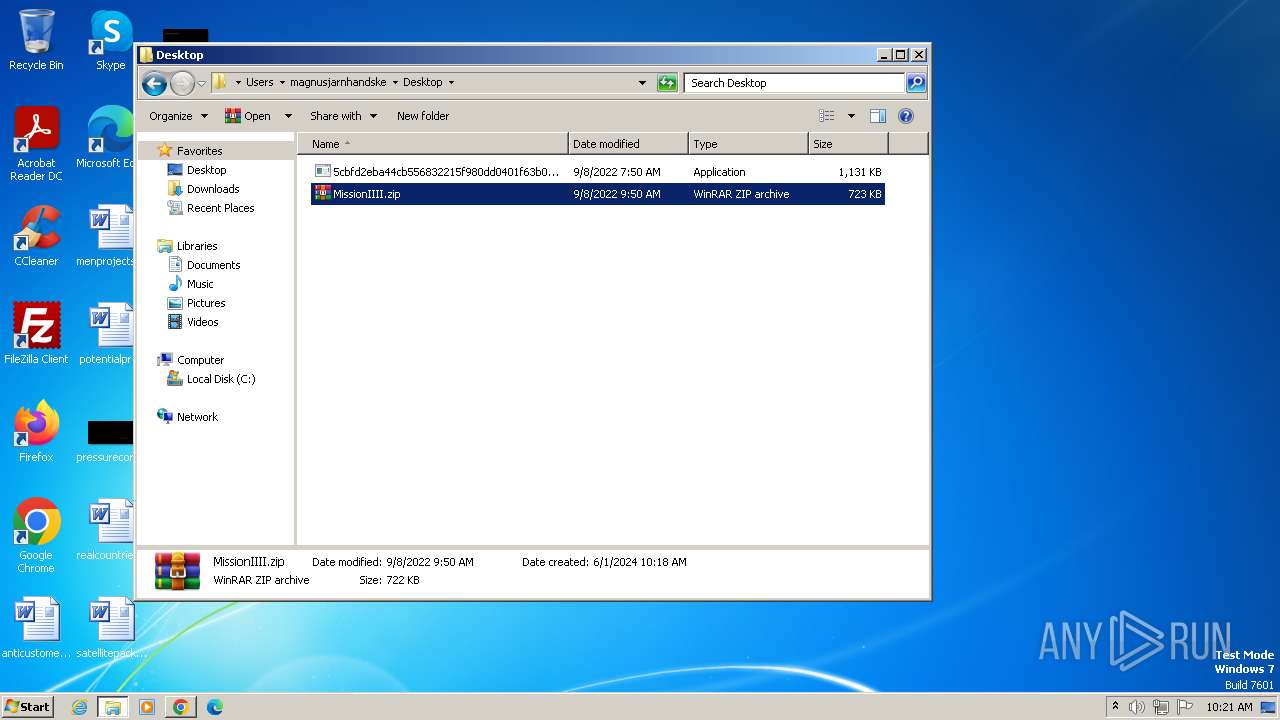
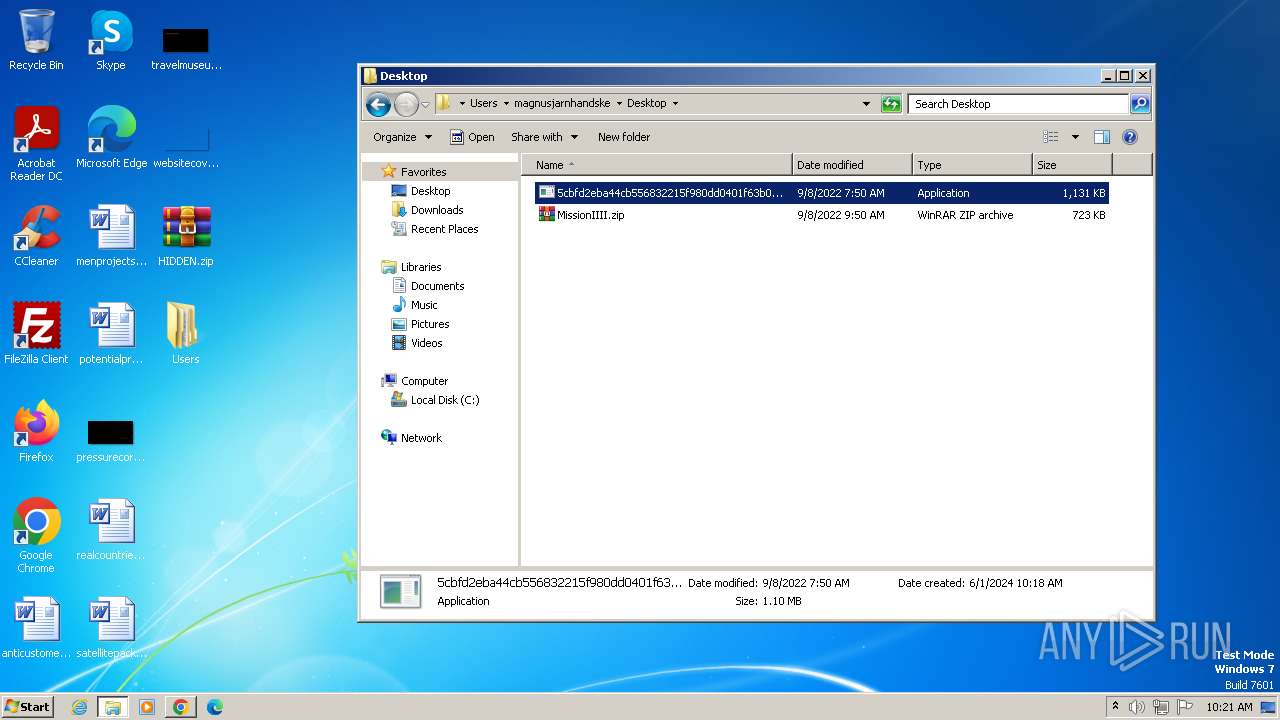
| ZipFileName: | Users/magnusjarnhandske/Desktop/MissionIIII.zip |
Total processes
65
Monitored processes
27
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 304 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1608 --field-trial-handle=1136,i,16594965699301777781,3309817735337202452,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 444 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 824 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --use-gl=angle --use-angle=swiftshader-webgl --mojo-platform-channel-handle=1528 --field-trial-handle=1136,i,16594965699301777781,3309817735337202452,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 864 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=109.0.5414.120 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6dcb8b38,0x6dcb8b48,0x6dcb8b54 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1200 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=3160 --field-trial-handle=1136,i,16594965699301777781,3309817735337202452,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1284 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --first-renderer-process --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=2120 --field-trial-handle=1136,i,16594965699301777781,3309817735337202452,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1696 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3944 --field-trial-handle=1136,i,16594965699301777781,3309817735337202452,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1764 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1304 --field-trial-handle=1136,i,16594965699301777781,3309817735337202452,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1964 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=11 --mojo-platform-channel-handle=3804 --field-trial-handle=1136,i,16594965699301777781,3309817735337202452,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1988 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=3972 --field-trial-handle=1136,i,16594965699301777781,3309817735337202452,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
21 263
Read events
20 874
Write events
349
Delete events
40
Modification events
| (PID) Process: | (3972) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3972) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3972) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3972) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (3972) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (3972) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (3972) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\HIDDEN.zip | |||
| (PID) Process: | (3972) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3972) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3972) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
6
Suspicious files
217
Text files
46
Unknown types
201
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2104 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF10b48c.TMP | — | |
MD5:— | SHA256:— | |||
| 2104 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2104 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
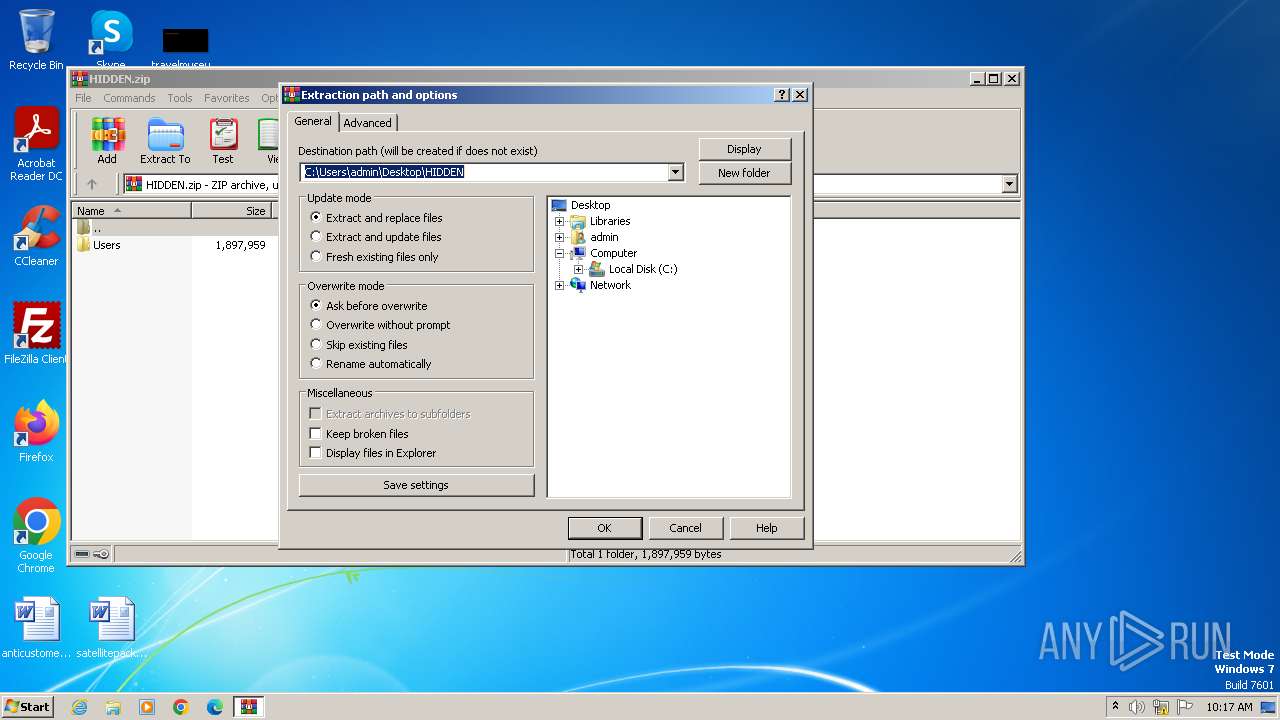
| 3972 | WinRAR.exe | C:\Users\admin\Desktop\Users\magnusjarnhandske\Desktop\MissionIIII.zip | compressed | |
MD5:C193F5E652FD05893FBA4678267658F5 | SHA256:821829EFAD0573B261874985FB34432A2320D53C3DA6F0AB21CA7161F382D754 | |||
| 2104 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | text | |
MD5:98CC34E7F20FD8F55568DB9B3D3B507E | SHA256:8D3D74EC41FF0CCE1F26B23F66E5981B7F59C40AB0DBB468B3A3E5E63C80F3C7 | |||
| 2104 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\16276c68-ed42-4391-b17d-51be73c9f46c.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 2104 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF10b49c.TMP | text | |
MD5:358570F689377CE6838812643E03734B | SHA256:5B41FCC2E1A843AEAB9437B06E27B798870FF10D86A51B163BF48862BCD32590 | |||
| 2104 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:456D3EF989973A7C218E338A6CFFAD25 | SHA256:75631D994431F254B94255C50038A3657BFC45D76FCE9D794D514E57CA678872 | |||
| 2104 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 3972 | WinRAR.exe | C:\Users\admin\Desktop\Users\magnusjarnhandske\Desktop\5cbfd2eba44cb556832215f980dd0401f63b009fa4b1c5bf2acb6c3c7c617960.exe | executable | |
MD5:D4EE556C937F4E2A322A5CD663E336C3 | SHA256:5CBFD2EBA44CB556832215F980DD0401F63B009FA4B1C5BF2ACB6C3C7C617960 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
36
TCP/UDP connections
49
DNS requests
54
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
884 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1088 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2104 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
1764 | chrome.exe | 142.250.74.195:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
1764 | chrome.exe | 108.177.119.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
1764 | chrome.exe | 142.250.186.36:443 | www.google.com | GOOGLE | US | whitelisted |
1764 | chrome.exe | 142.250.186.131:443 | update.googleapis.com | GOOGLE | US | whitelisted |
2104 | chrome.exe | 224.0.0.251:5353 | — | — | — | unknown |
1764 | chrome.exe | 142.250.185.110:443 | encrypted-tbn0.gstatic.com | GOOGLE | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| whitelisted |
update.googleapis.com |
| unknown |
encrypted-tbn0.gstatic.com |
| whitelisted |
lh5.googleusercontent.com |
| whitelisted |
virustotal.com |
| whitelisted |
www.virustotal.com |
| whitelisted |
www.recaptcha.net |
| whitelisted |
www.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Misc activity | INFO [ANY.RUN] SMTP email client opens transfer with server (EHLO) |