| File name: | Flasher.exe |
| Full analysis: | https://app.any.run/tasks/546ae205-b023-4a92-8818-453911c724b2 |
| Verdict: | Malicious activity |
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
| Analysis date: | May 31, 2025, 06:14:56 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 6 sections |
| MD5: | 7175D81D25F930437CBE872DA4D6146E |
| SHA1: | AFF6402B462E139B998E4AFC4CDEF7CDB246F788 |
| SHA256: | 9A3F94EB934151C3114D646D229289B5670A0F99F99393A6F2B692EC5CF9CAB3 |
| SSDEEP: | 98304:Mb312s4I/KcuT0od2IblSN0PPD/BHzWin3iy:9 |
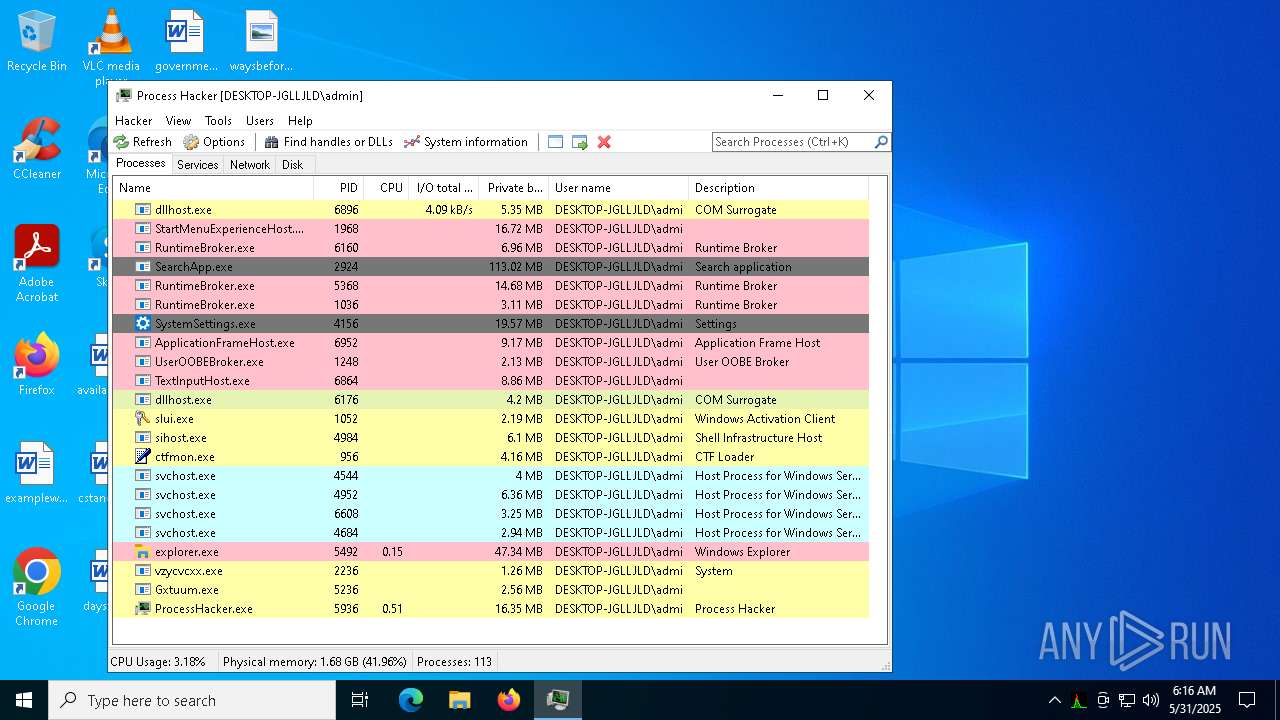
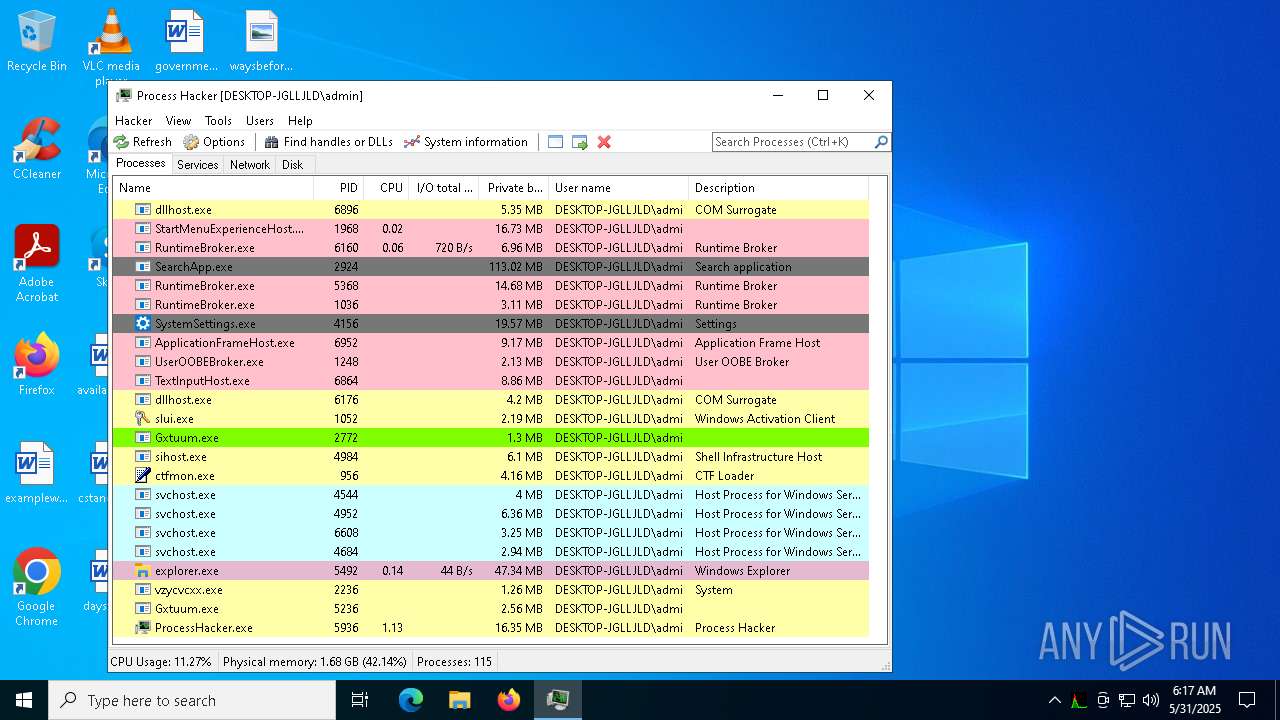
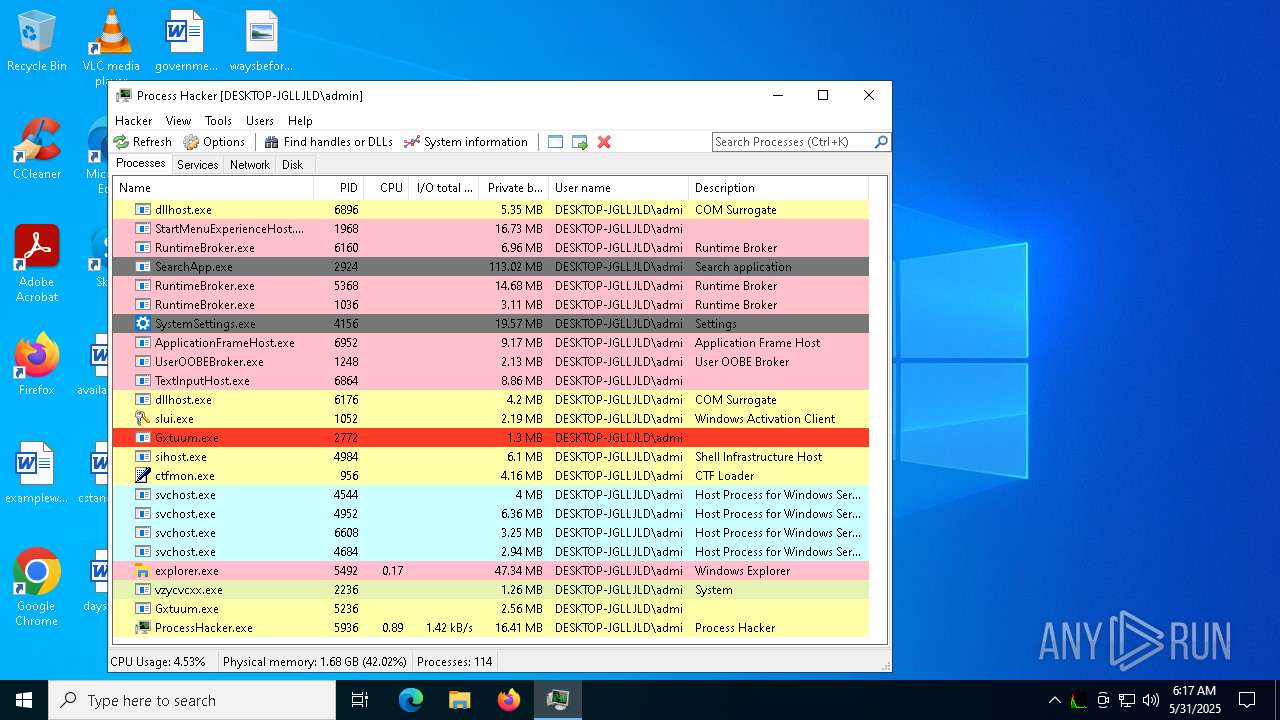
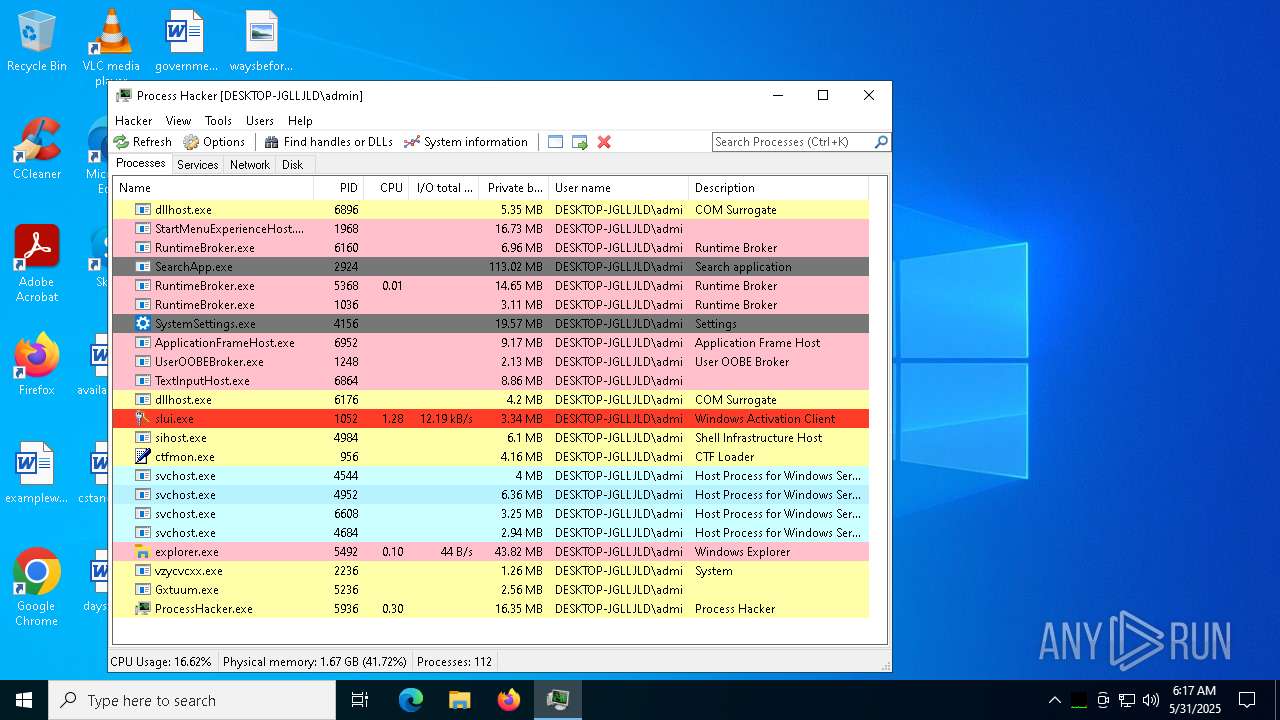
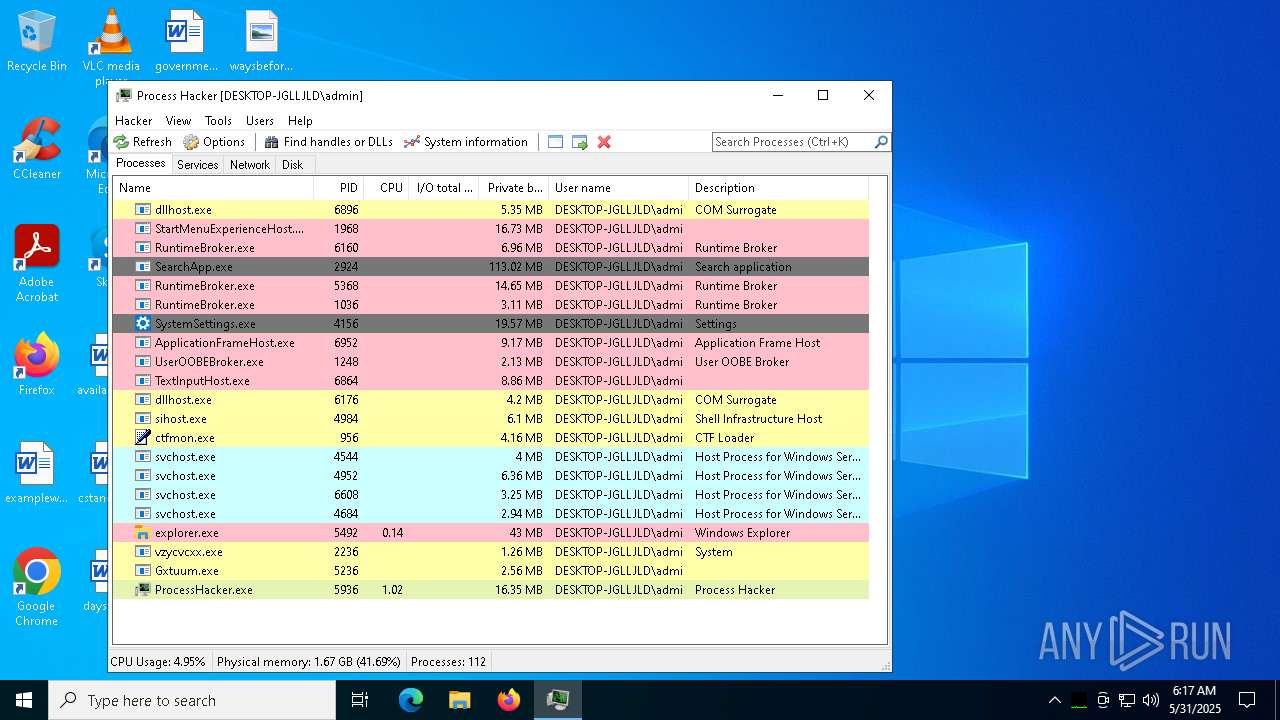
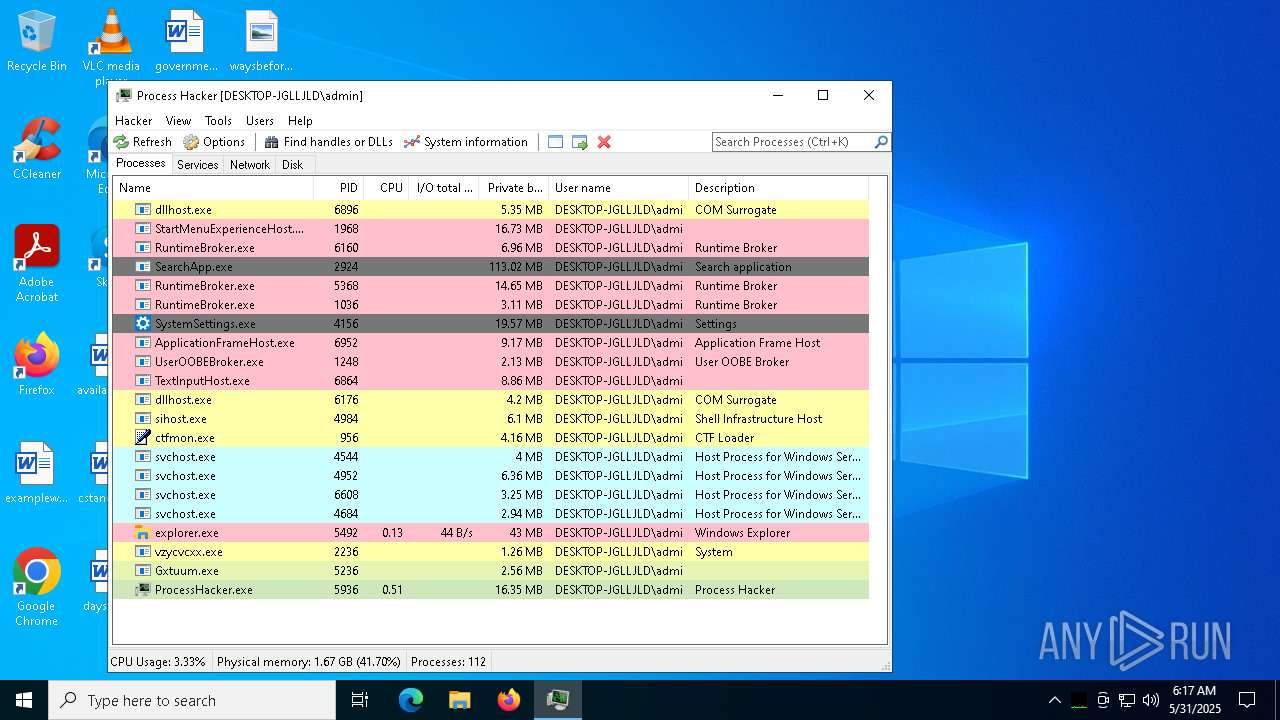
MALICIOUS
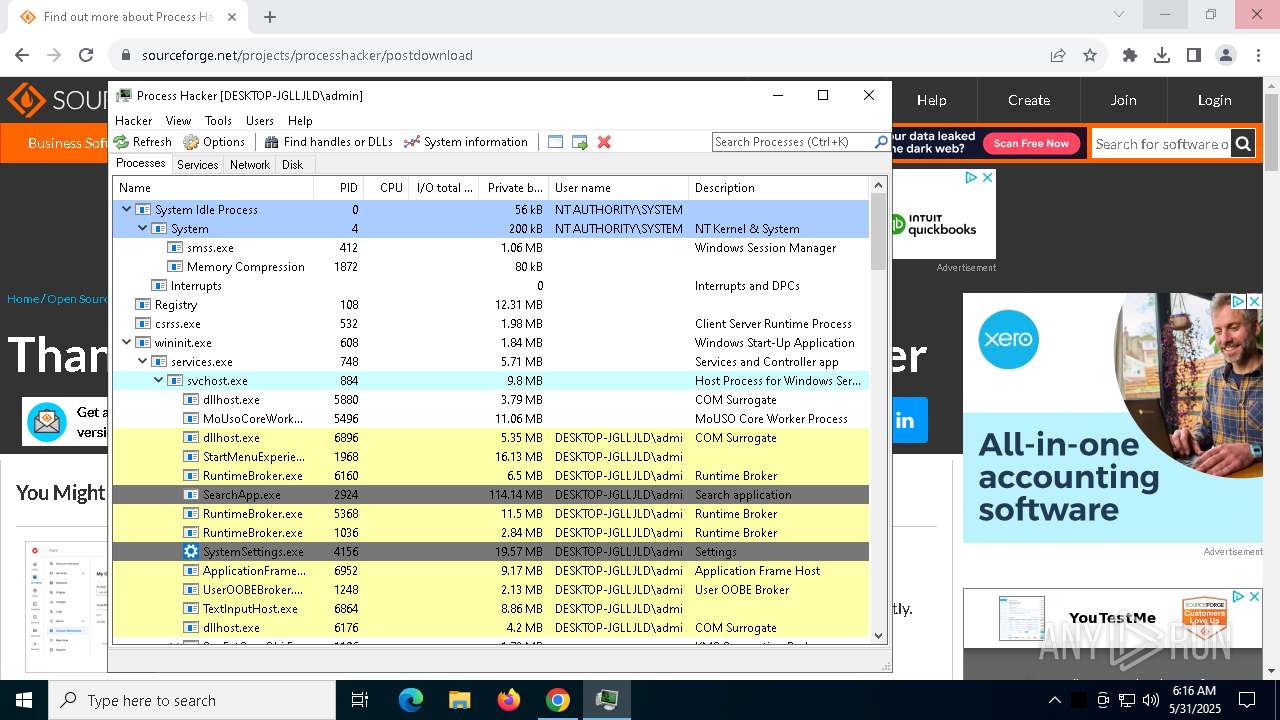
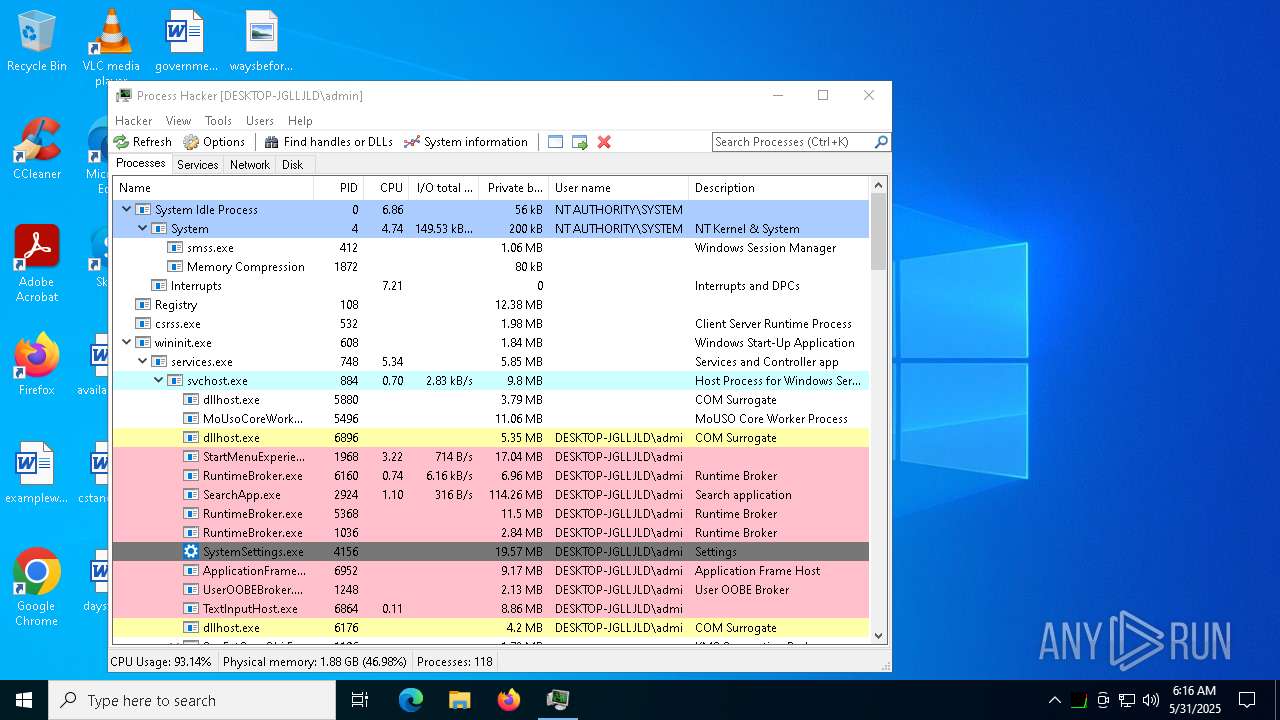
Runs injected code in another process
- ezezeww.exe (PID: 7500)
Application was injected by another process
- explorer.exe (PID: 5492)
Changes the autorun value in the registry
- ezezeww.exe (PID: 7500)
- vzycvcxx.exe (PID: 2236)
- explorer.exe (PID: 5492)
SVCSTEALER mutex has been found
- vzycvcxx.exe (PID: 2236)
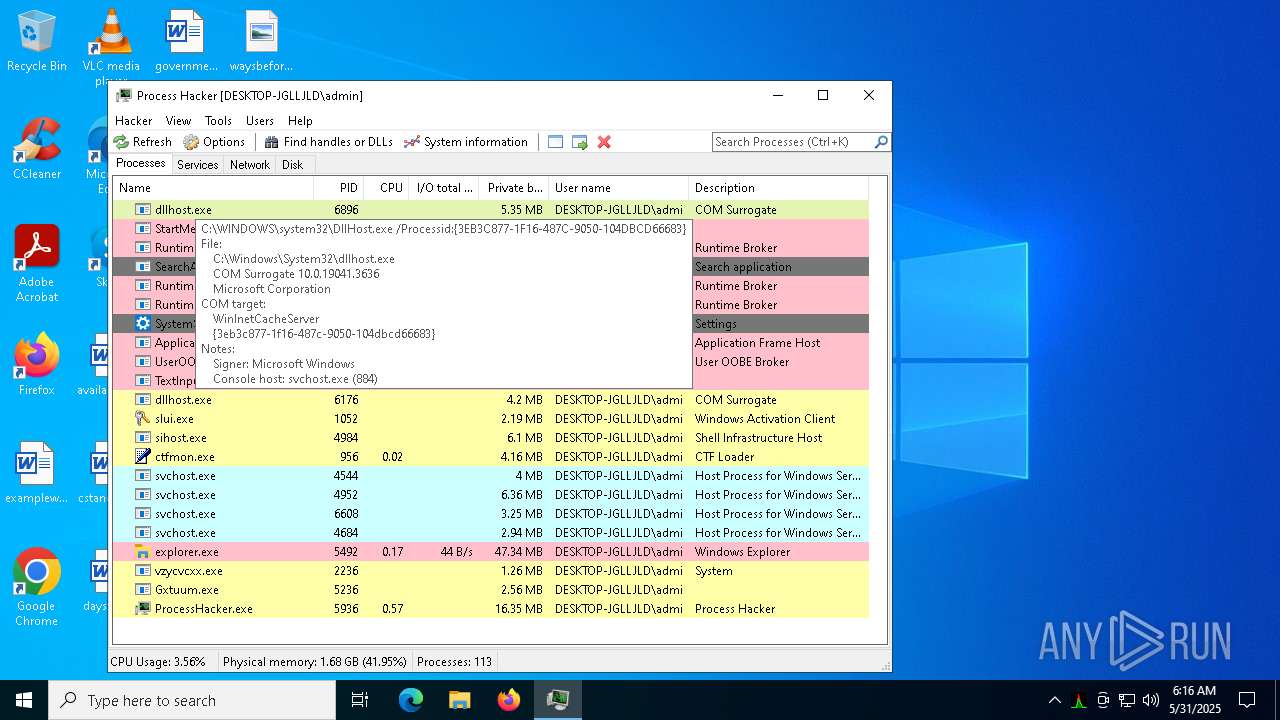
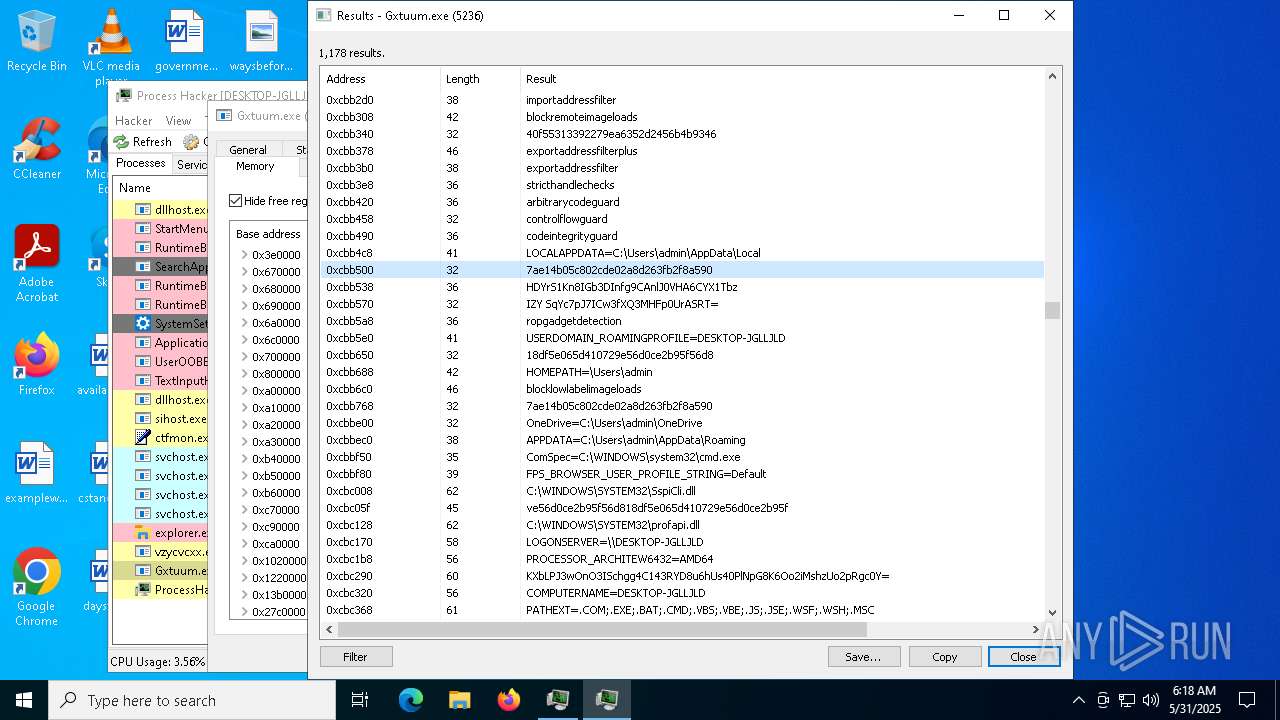
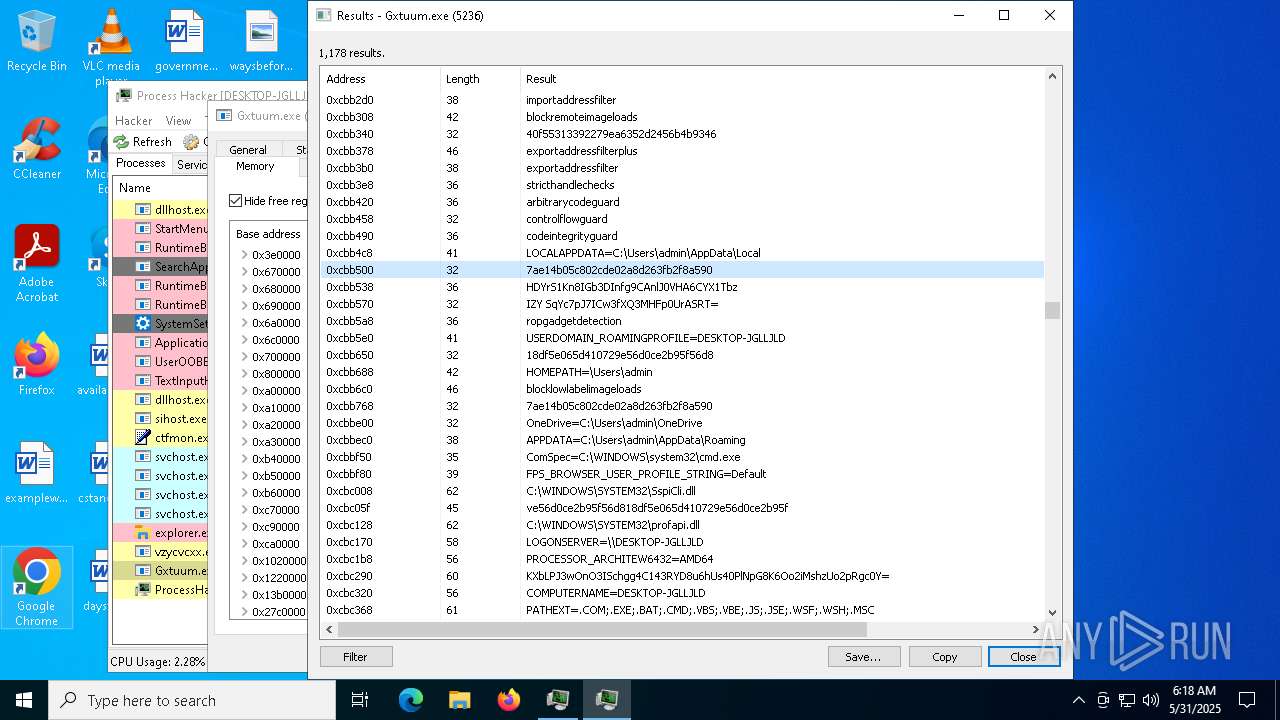
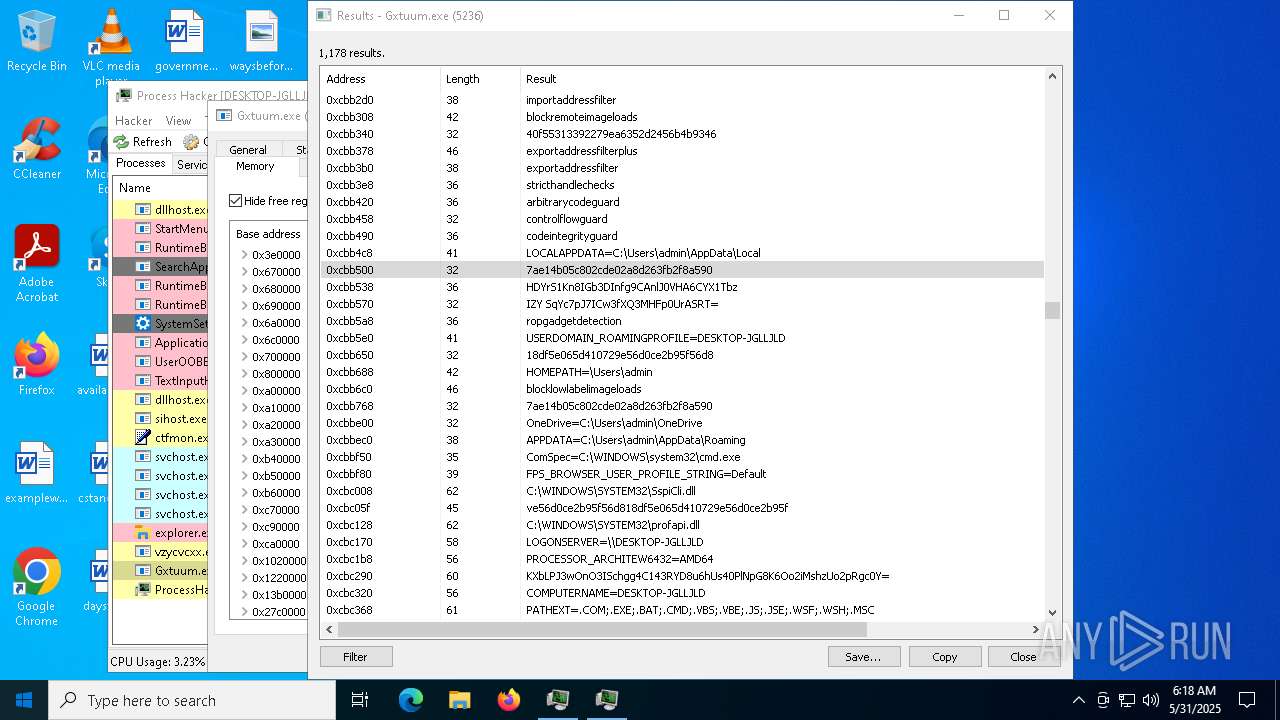
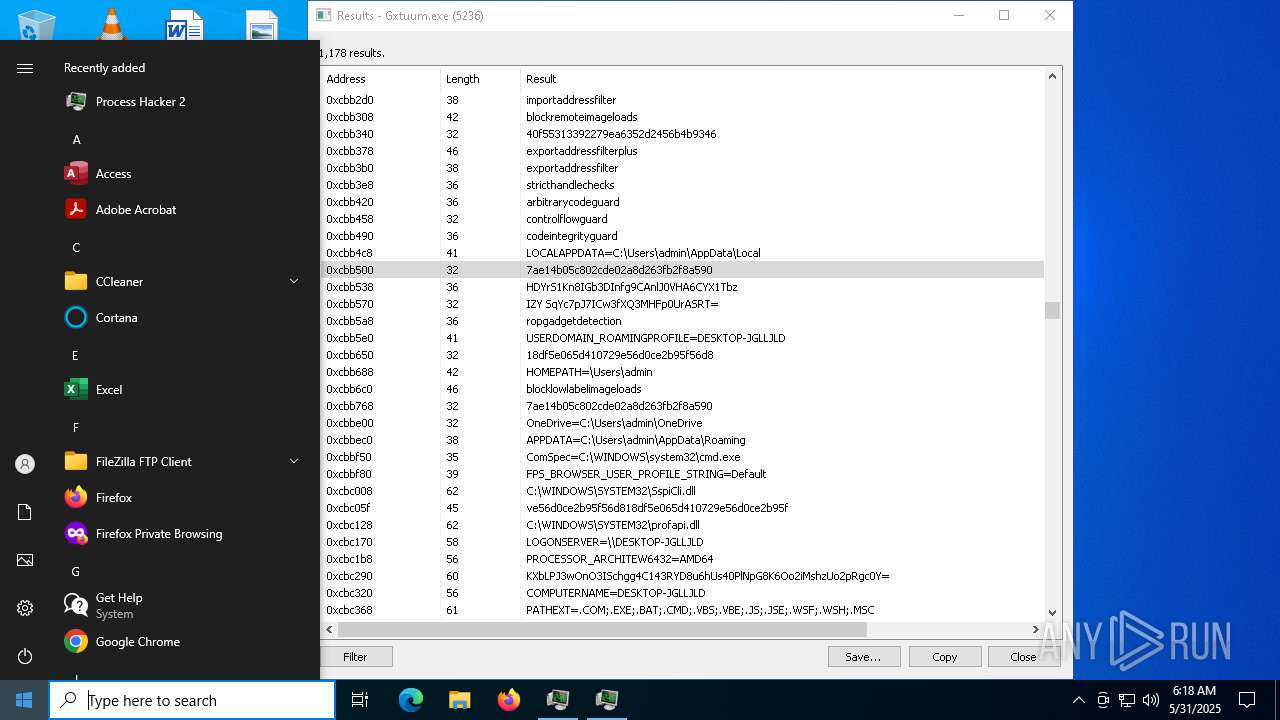
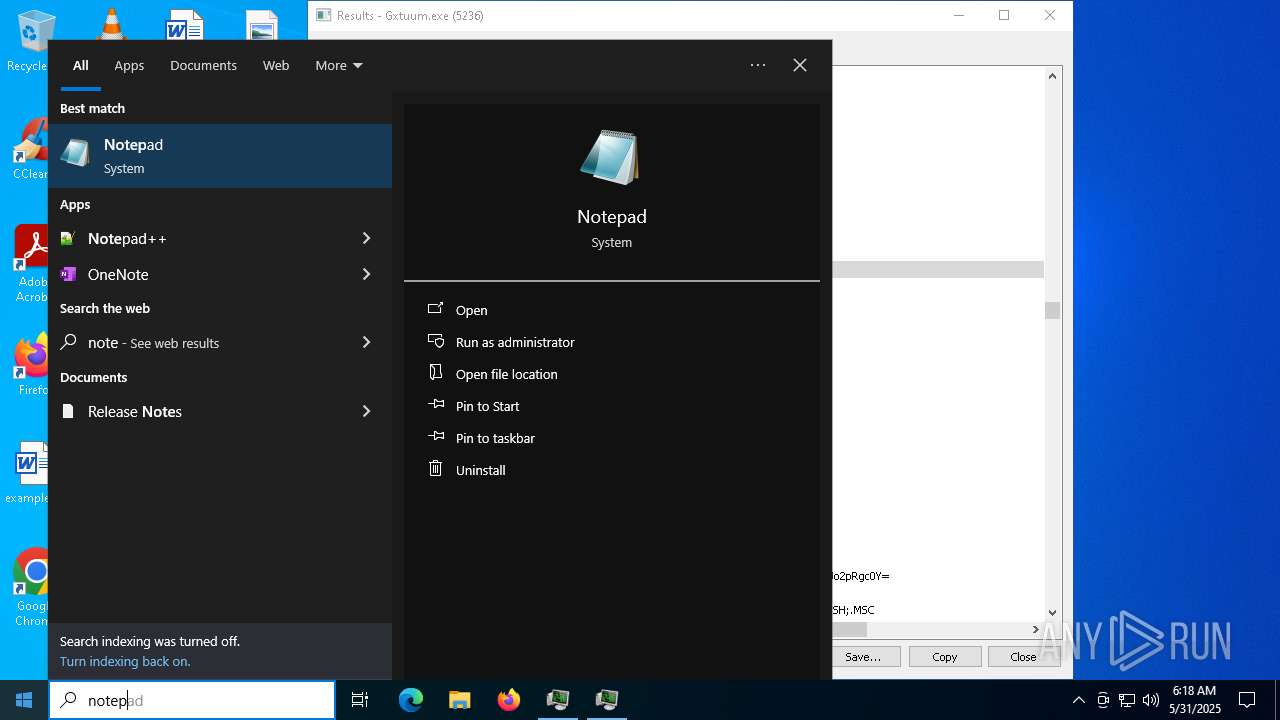
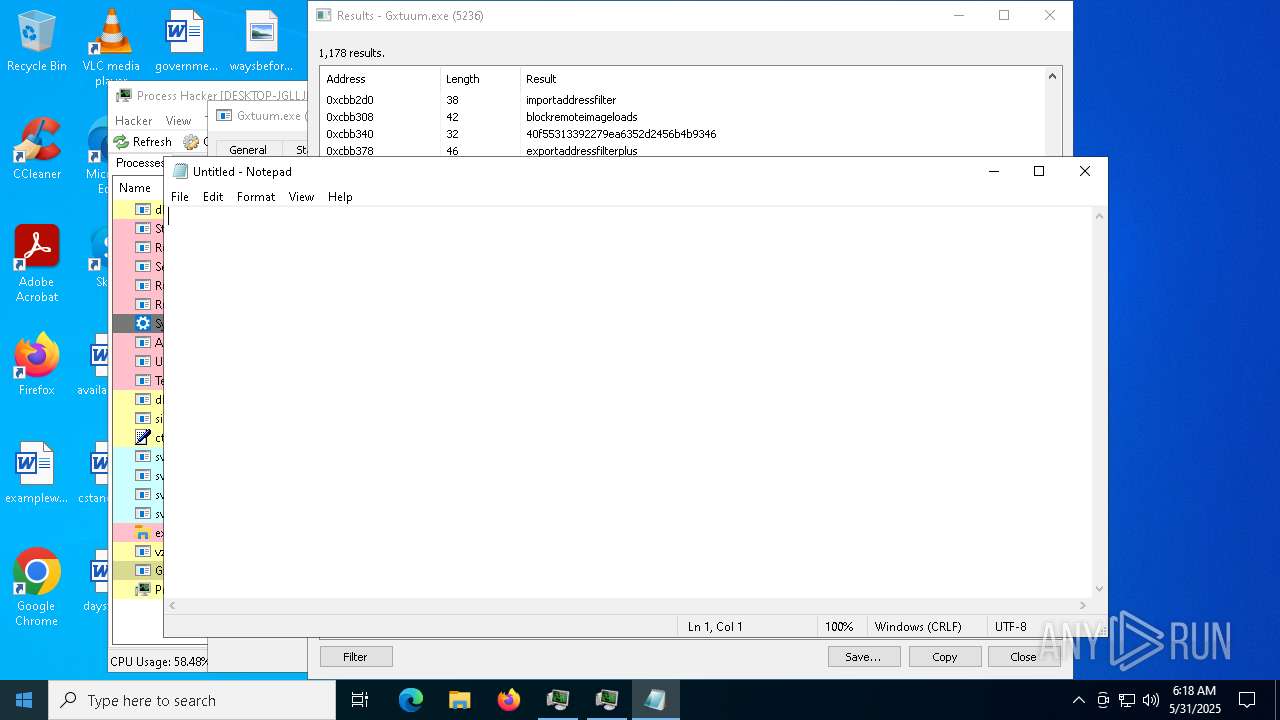
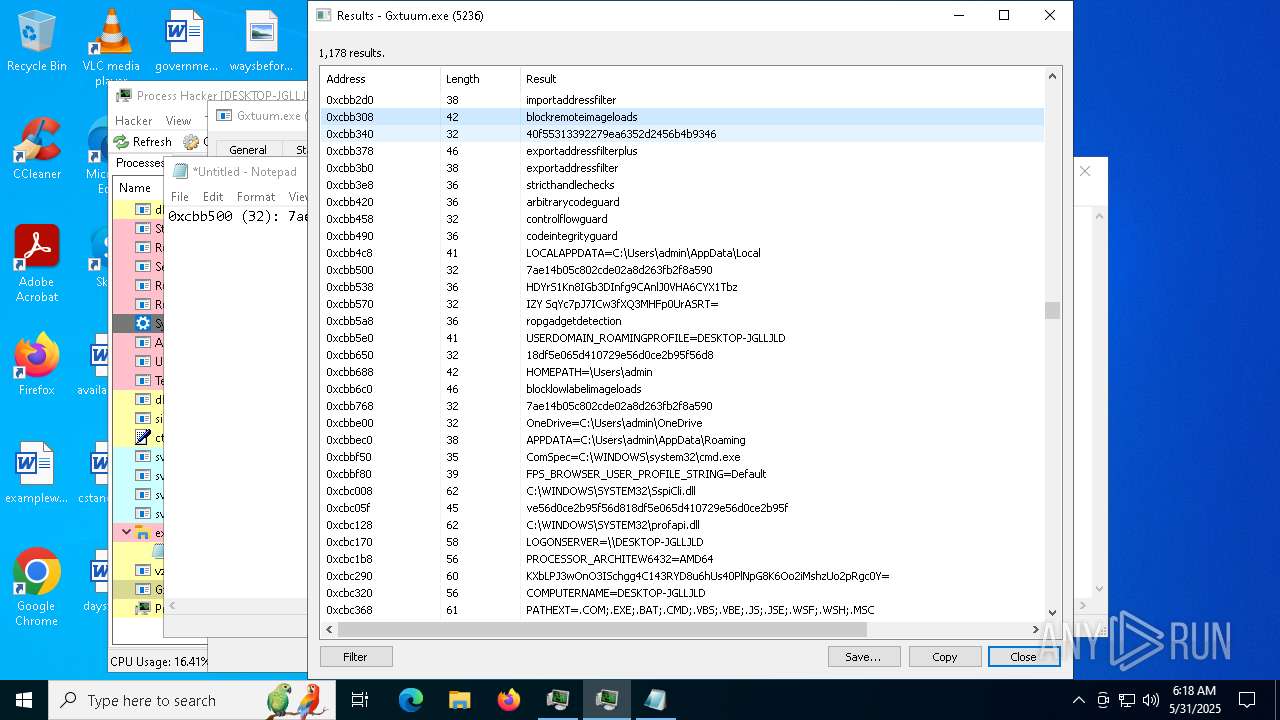
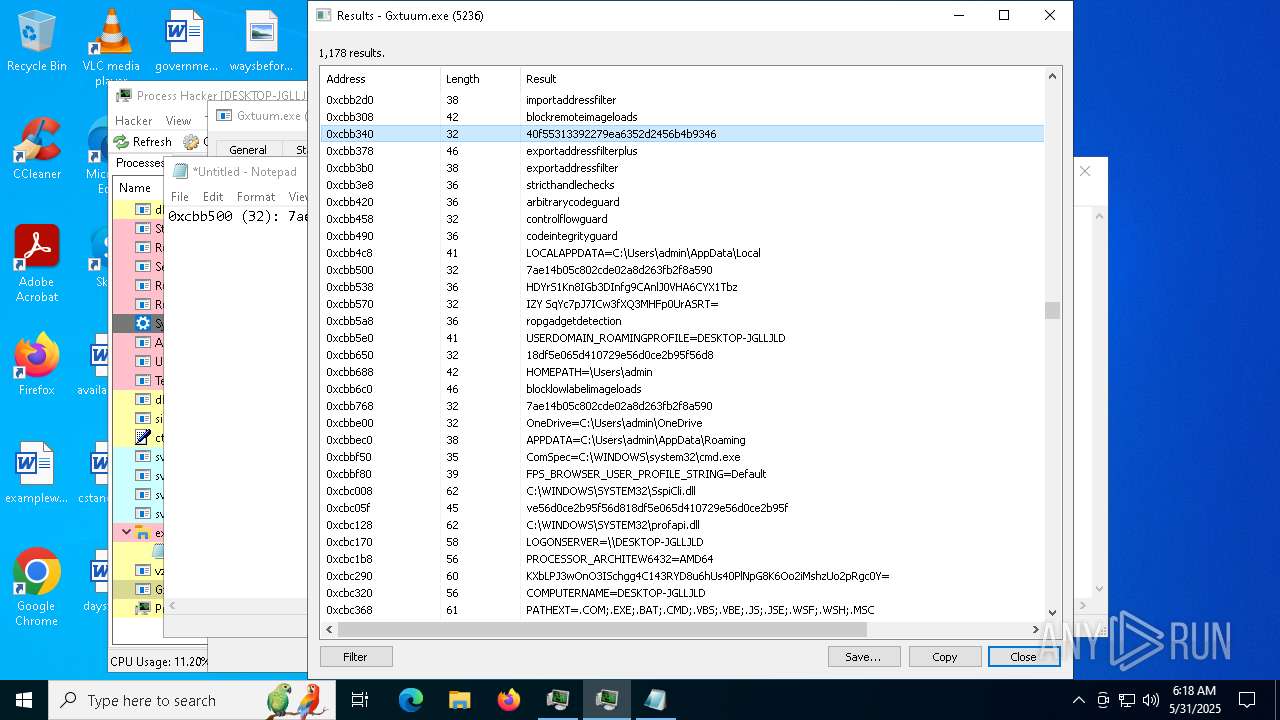
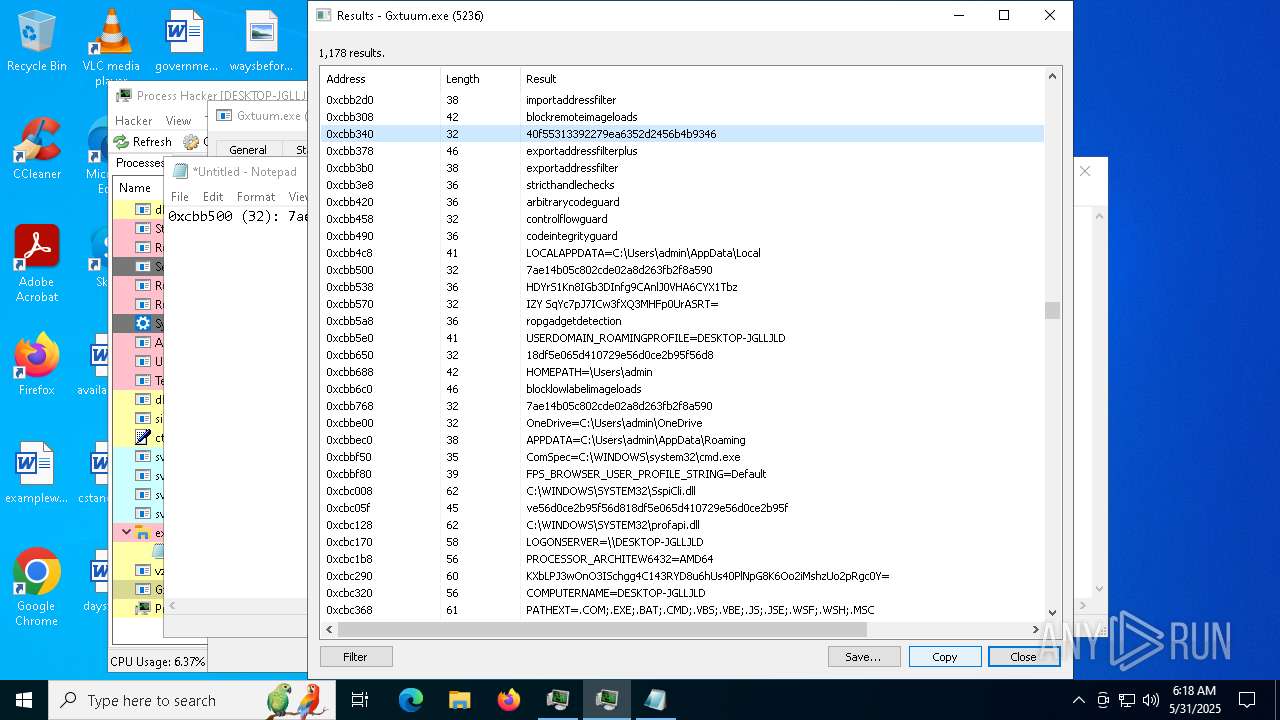
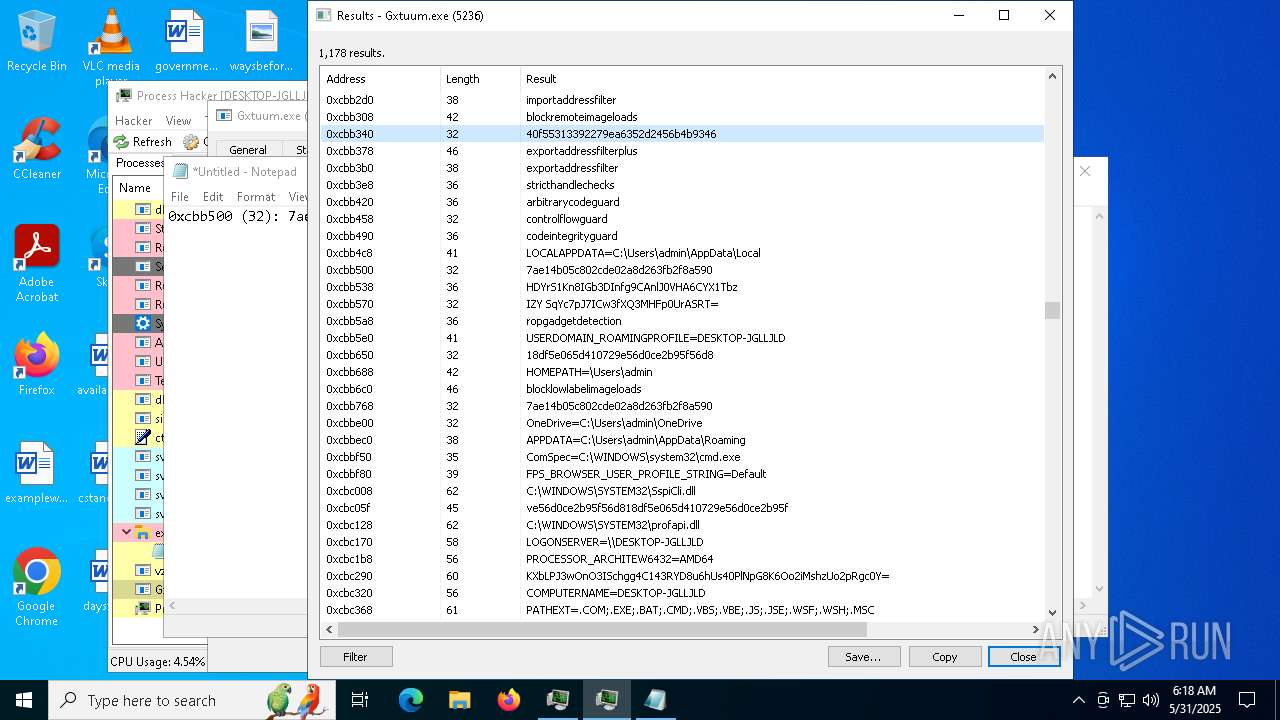
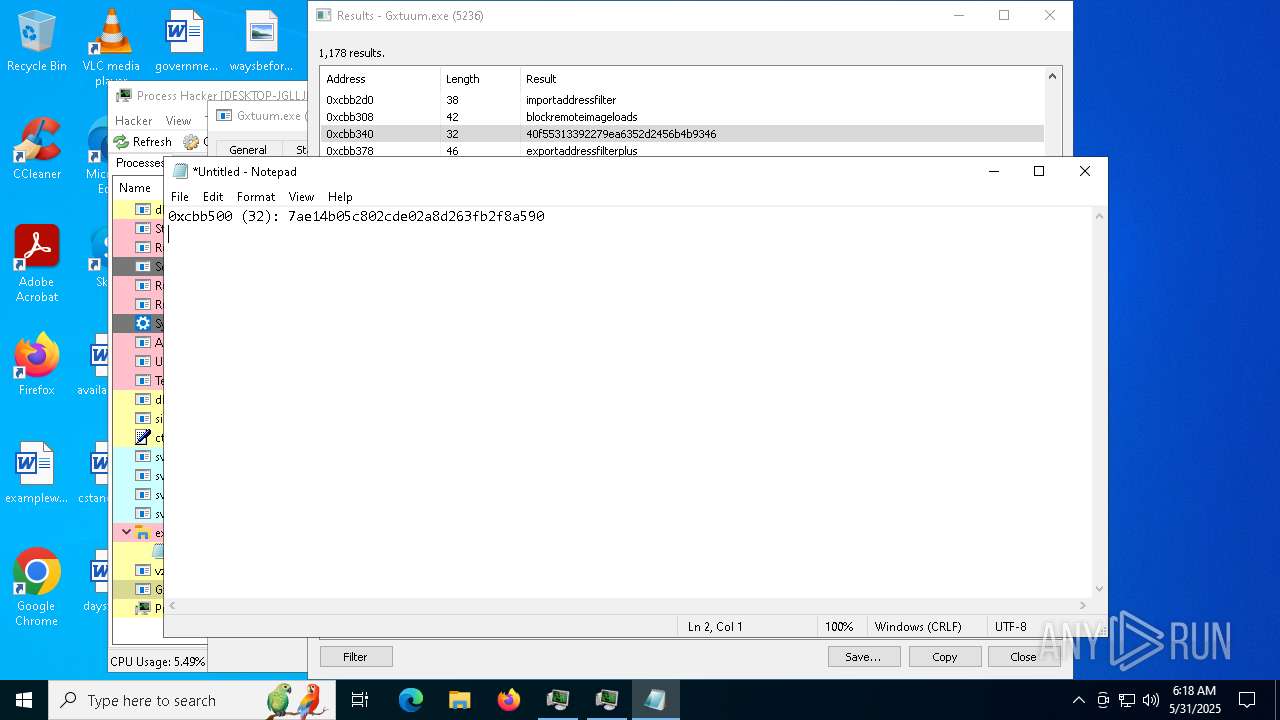
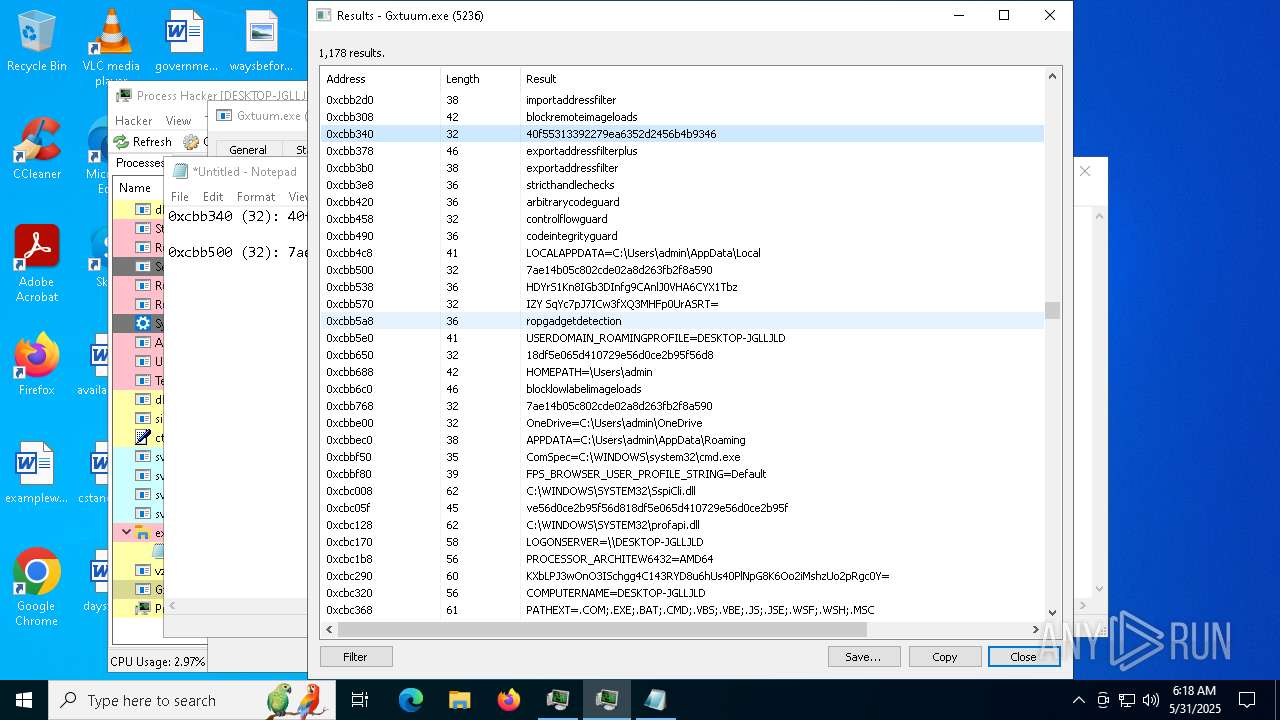
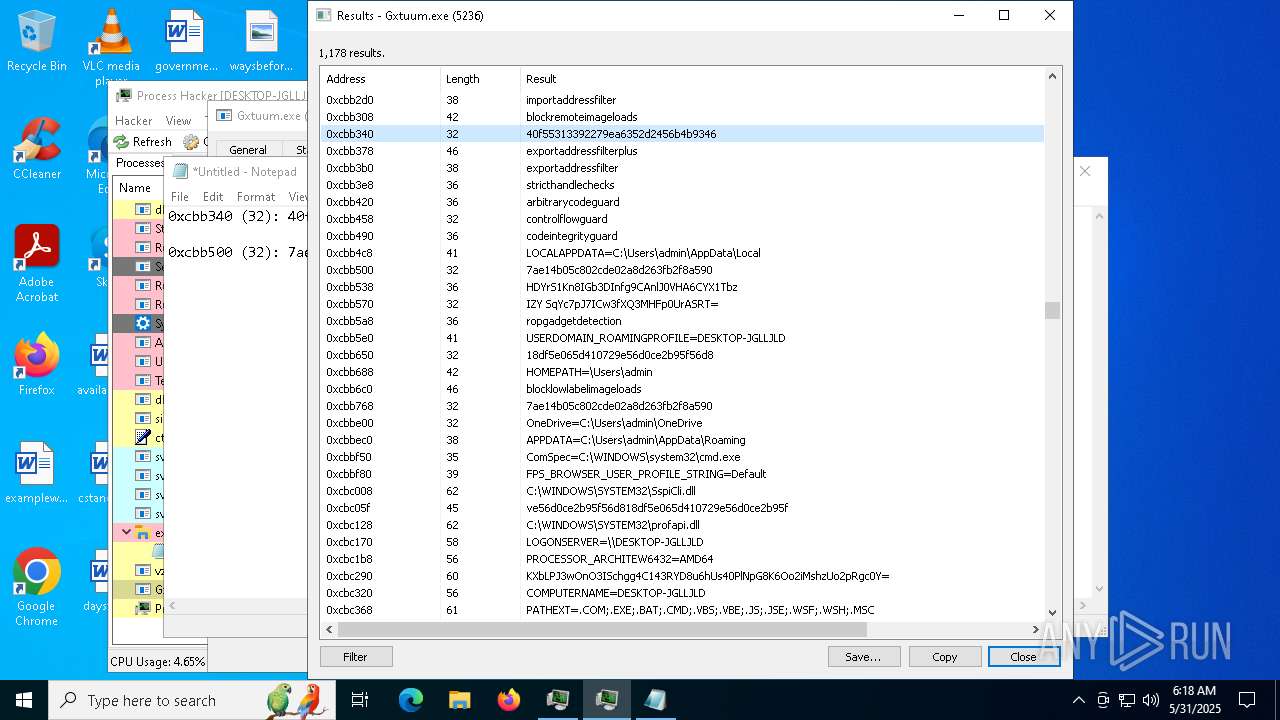
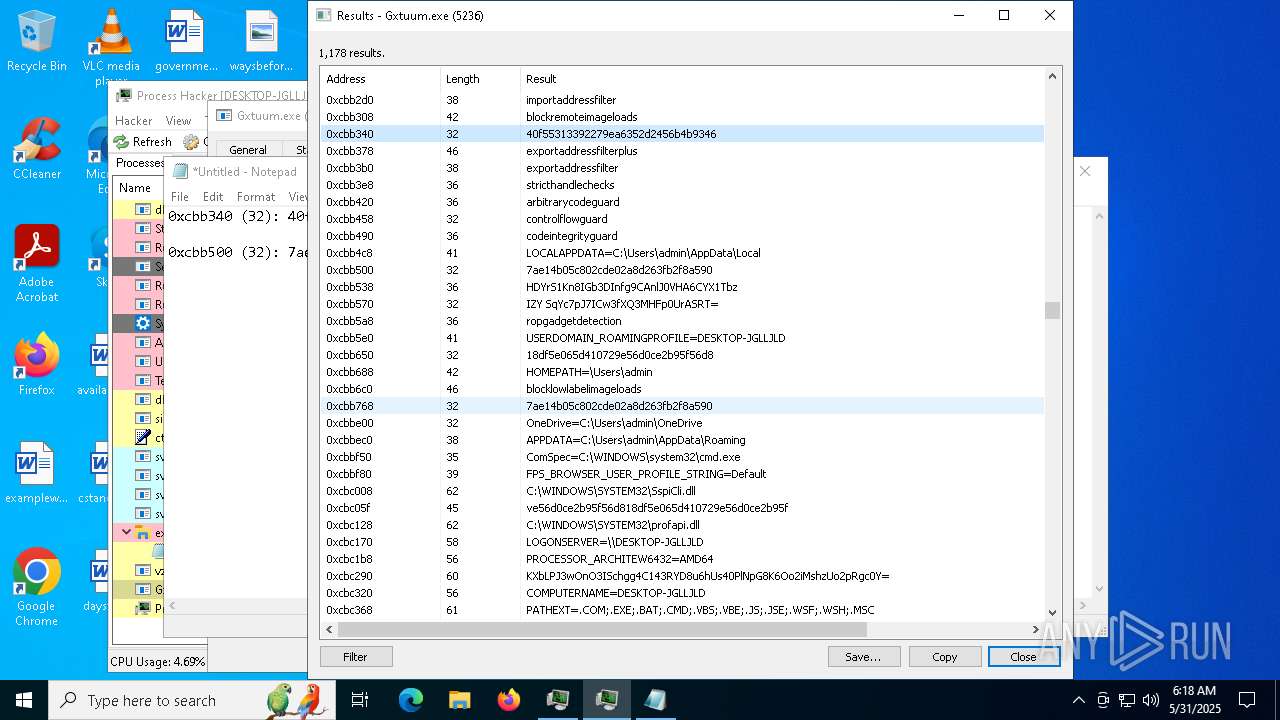
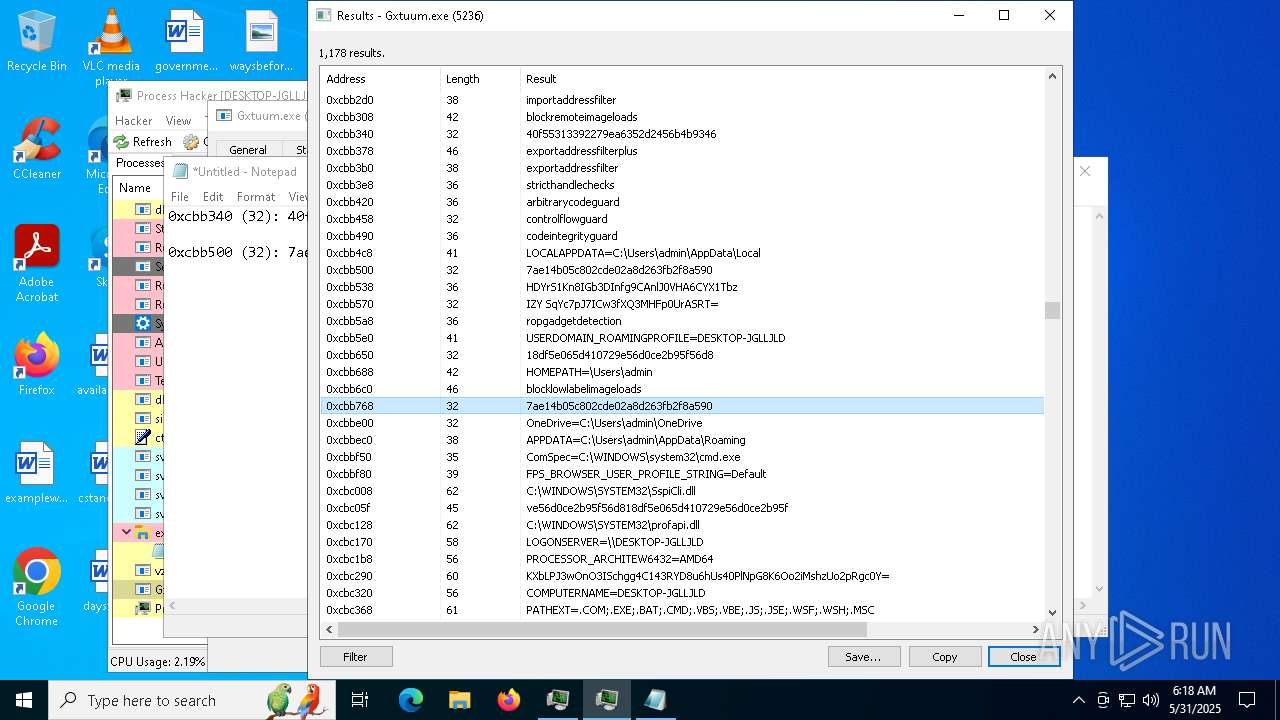
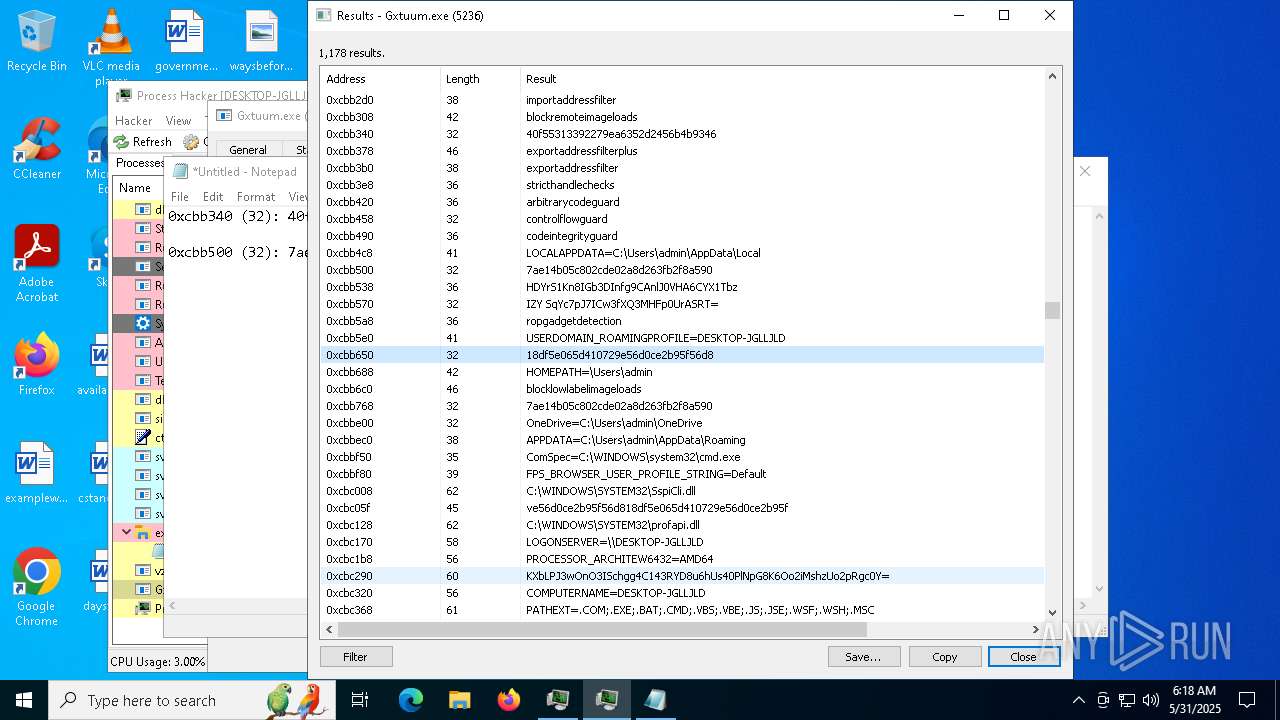
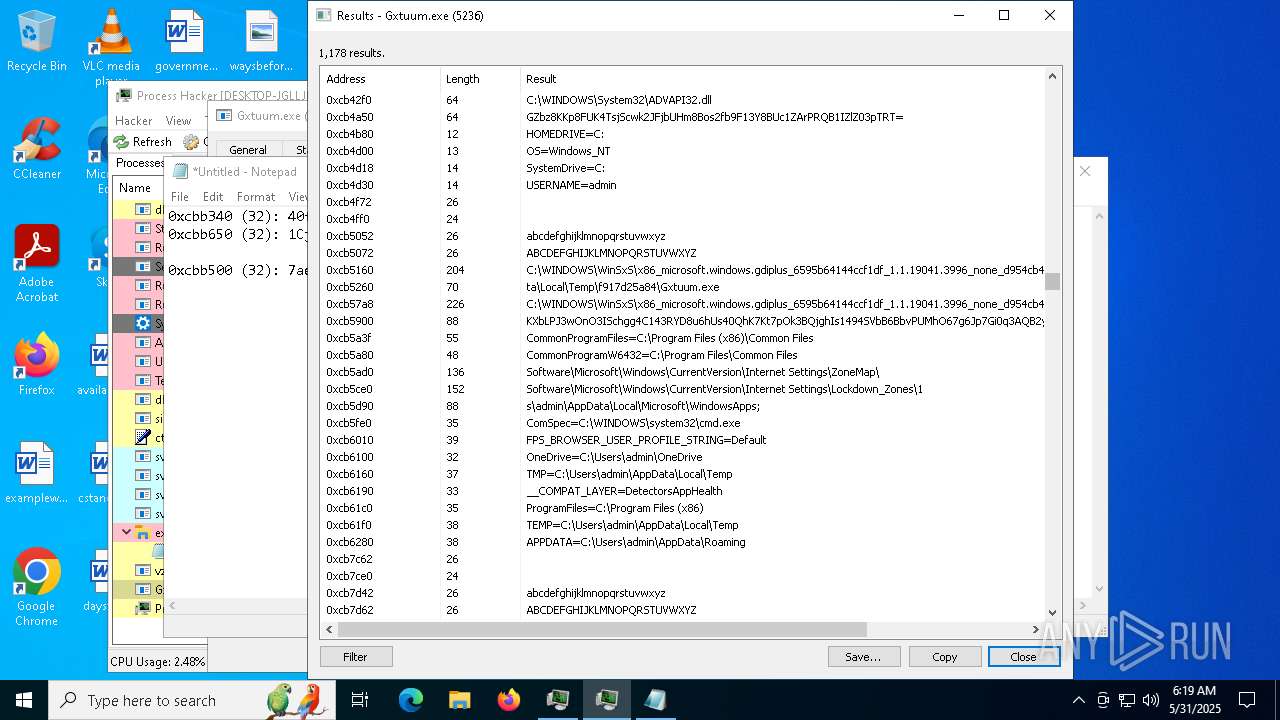
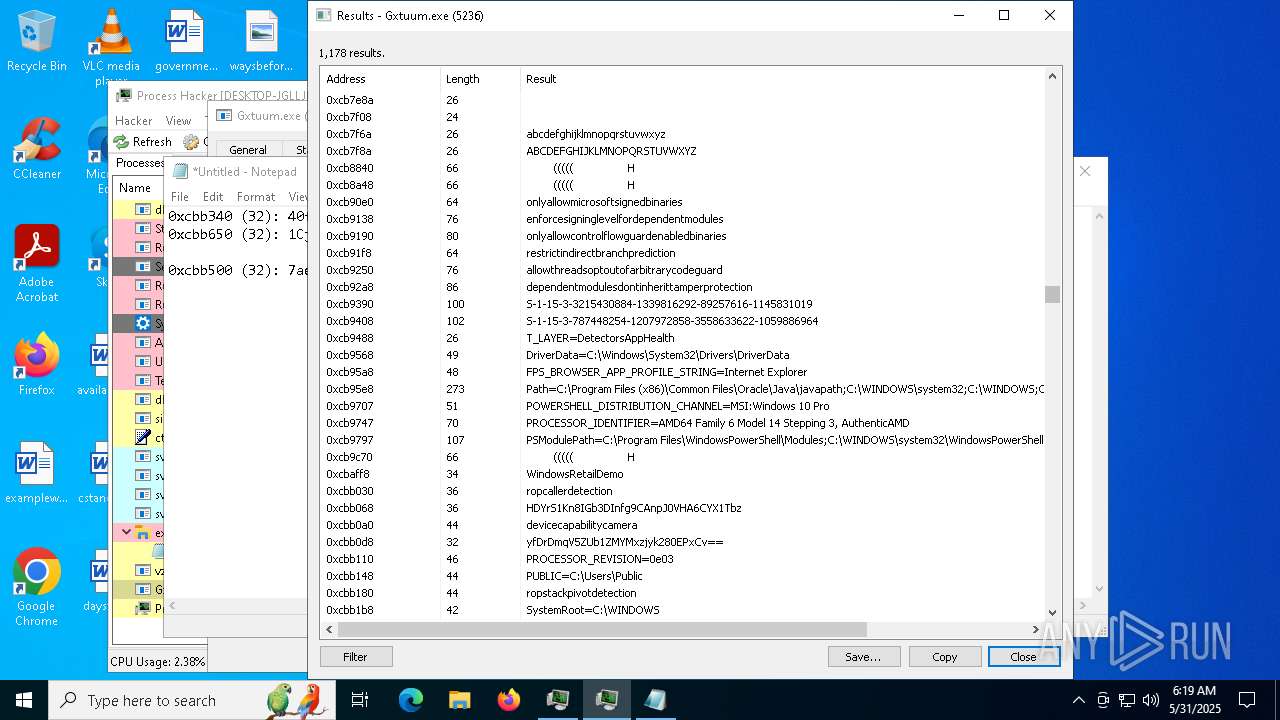
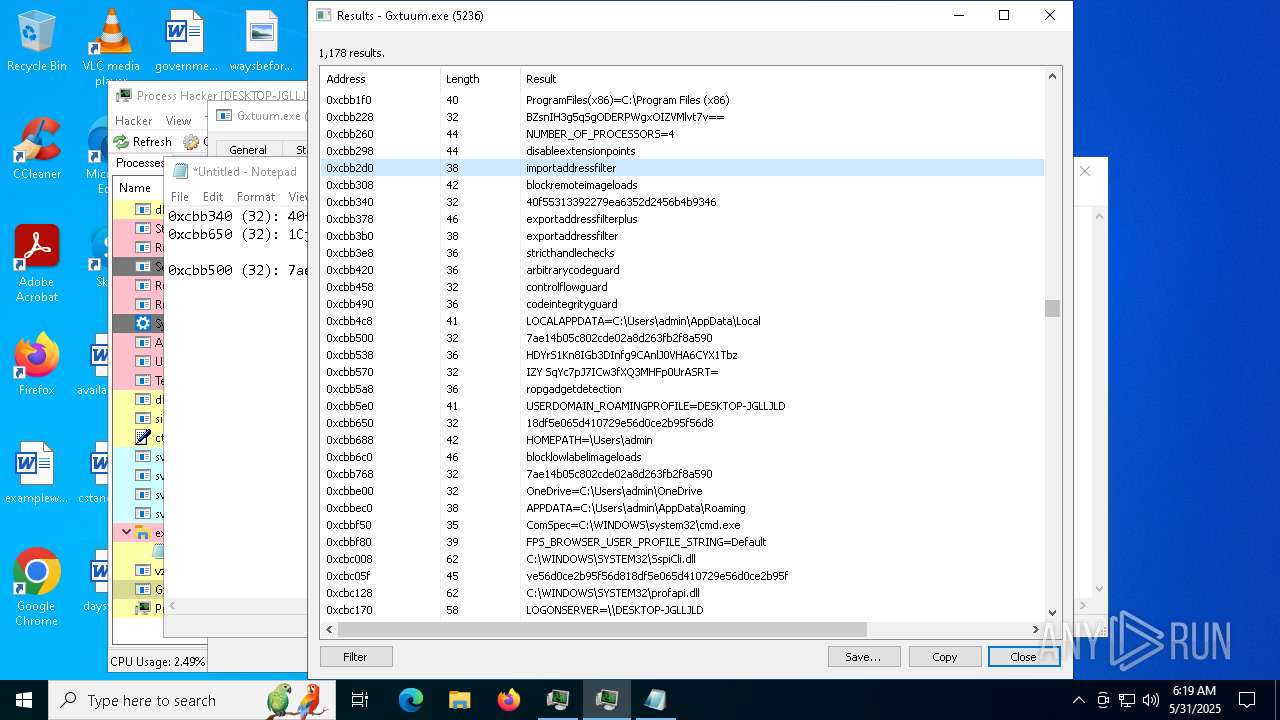
AMADEY has been detected (YARA)
- Gxtuum.exe (PID: 5236)
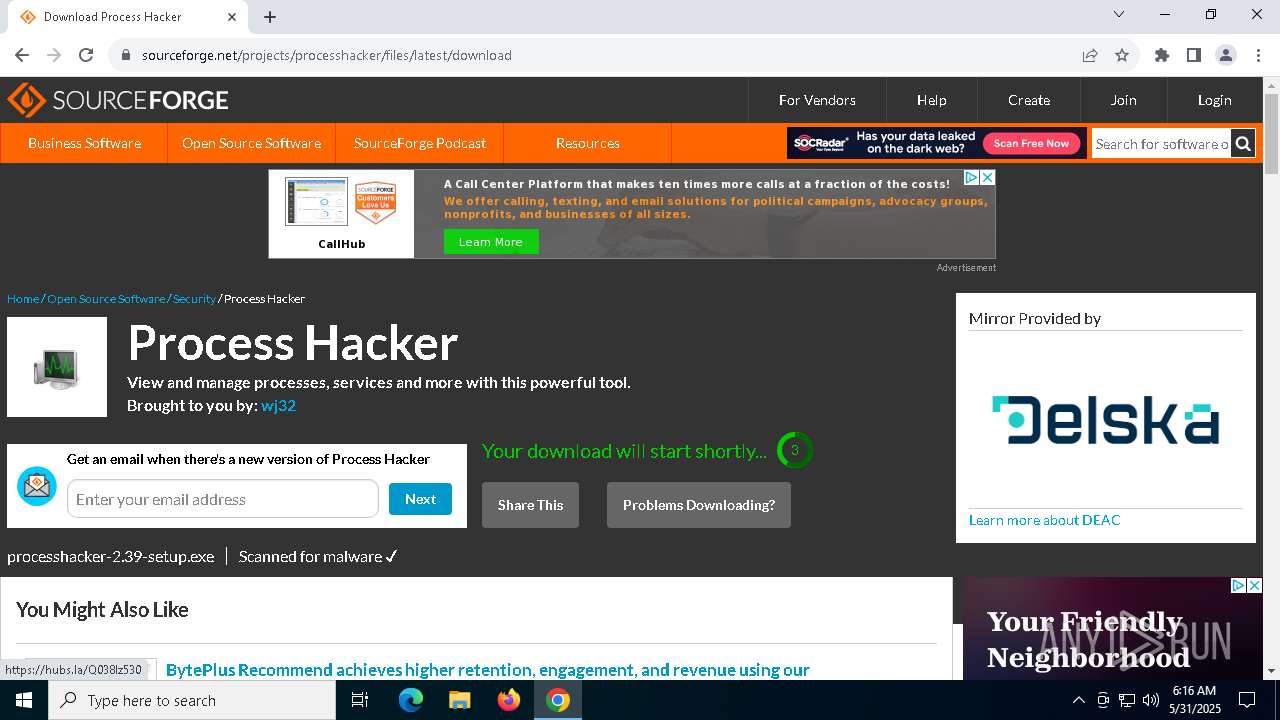
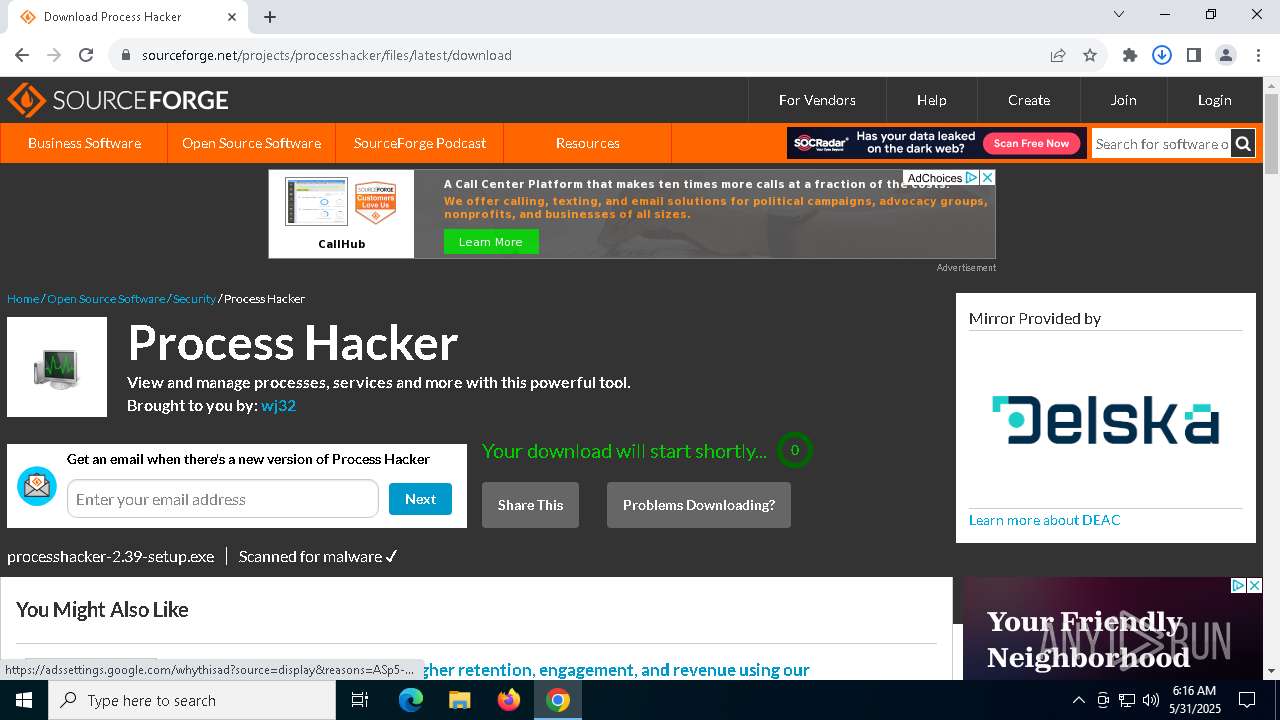
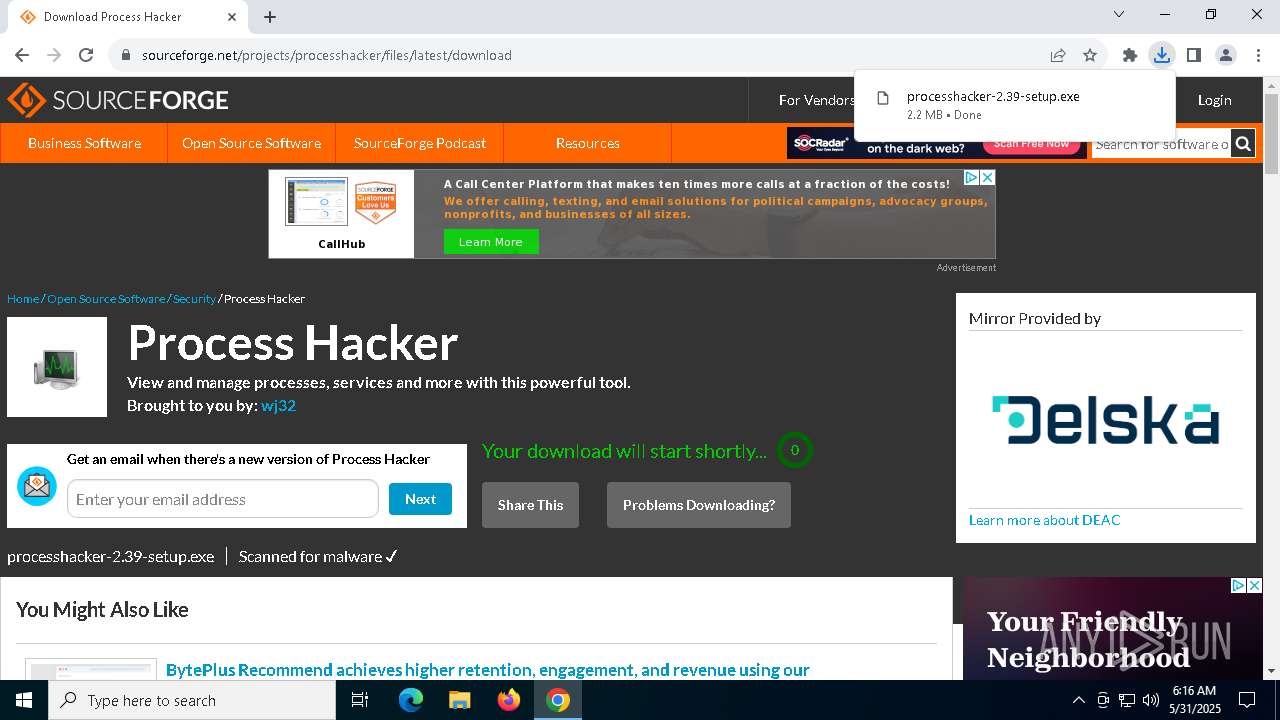
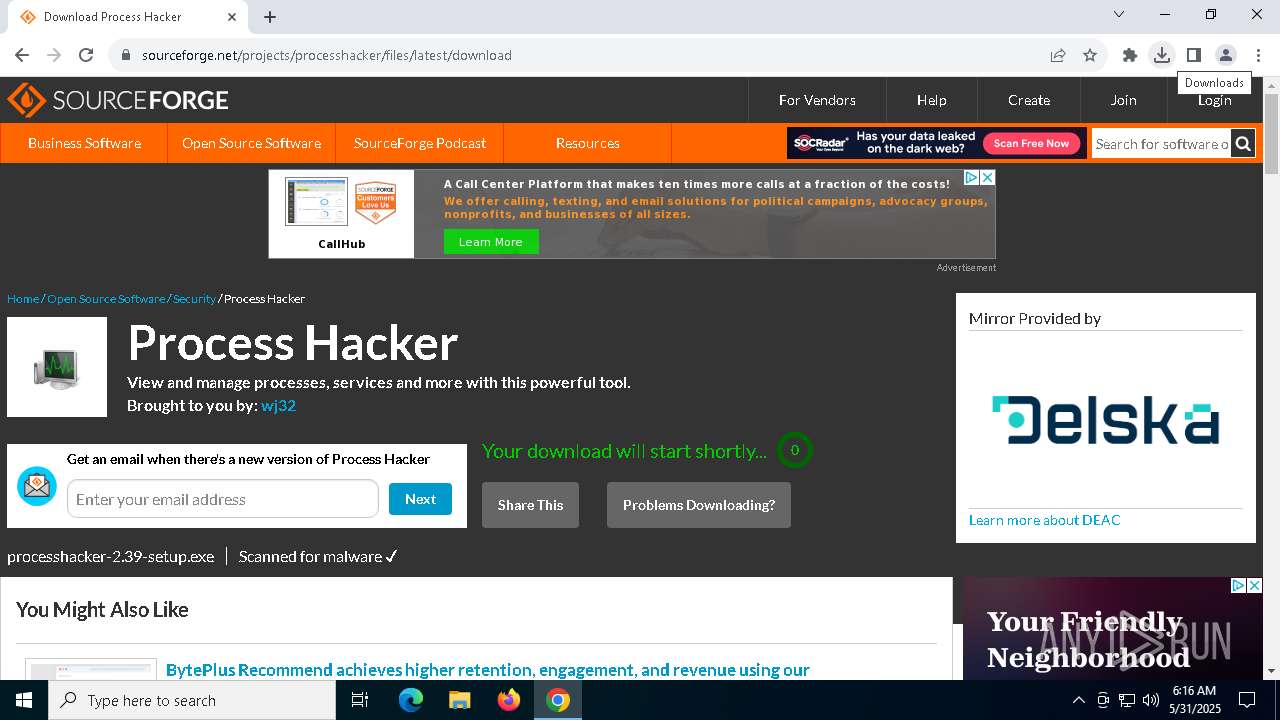
Vulnerable driver has been detected
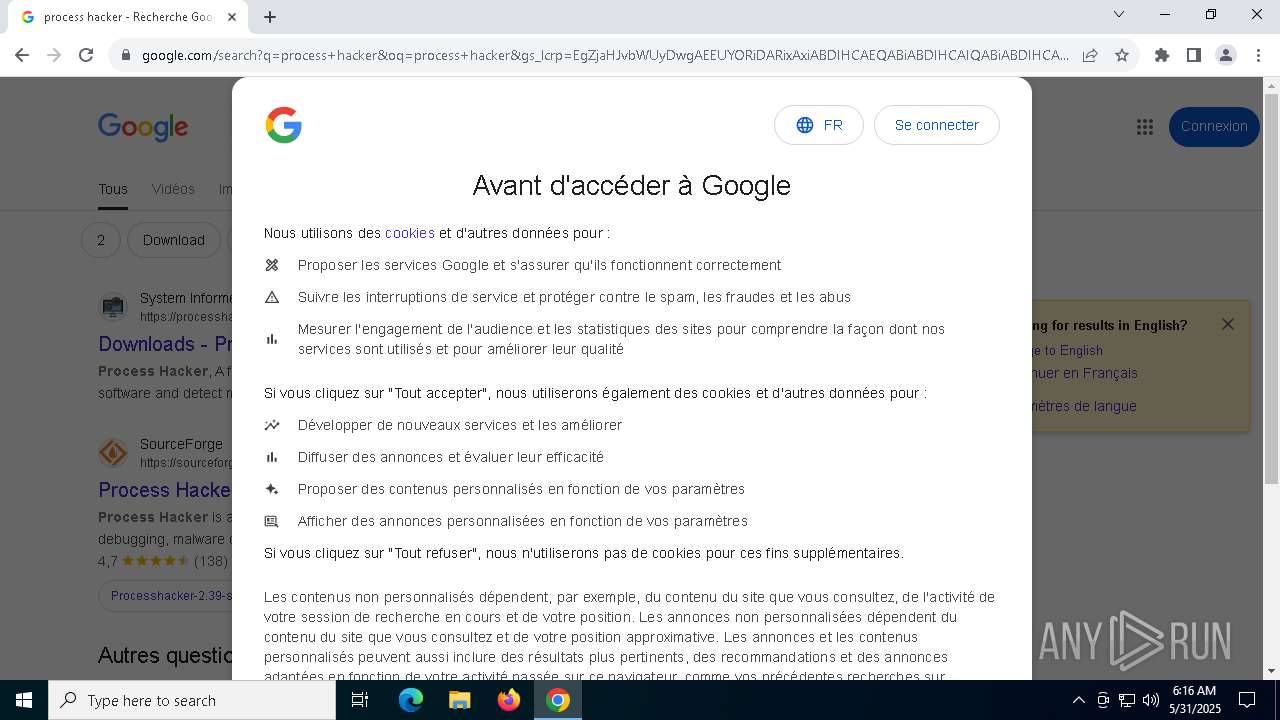
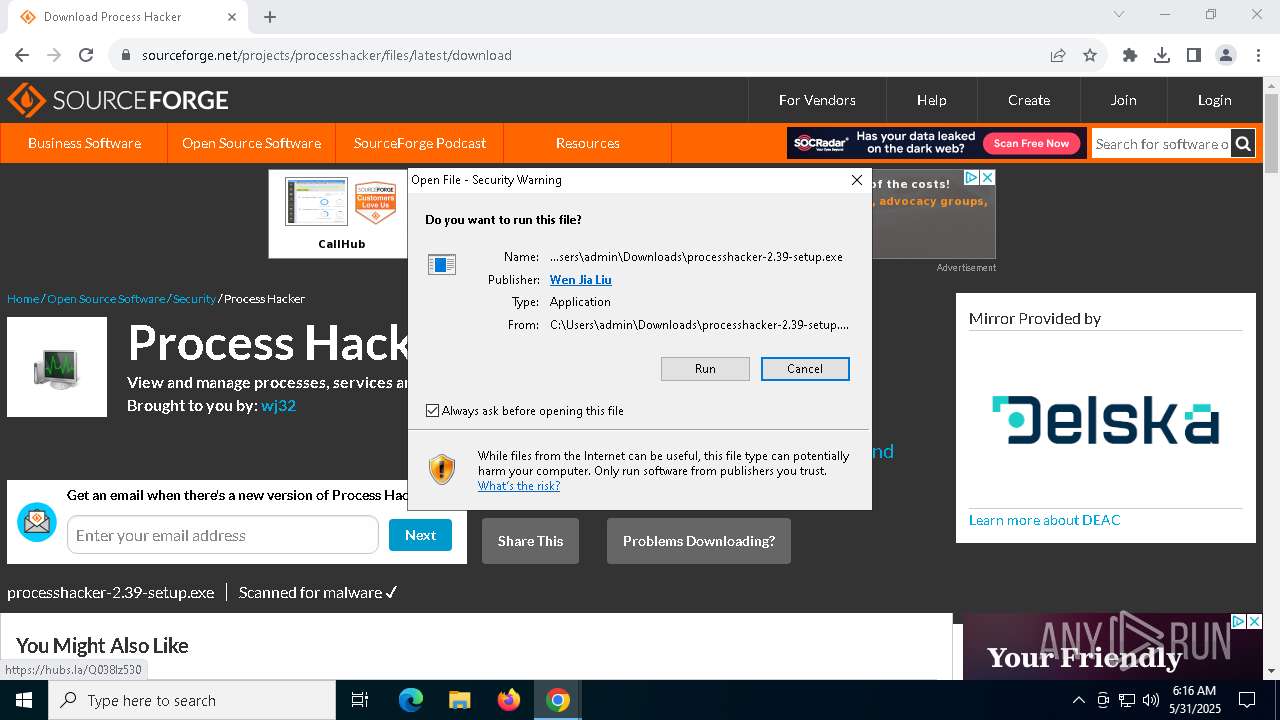
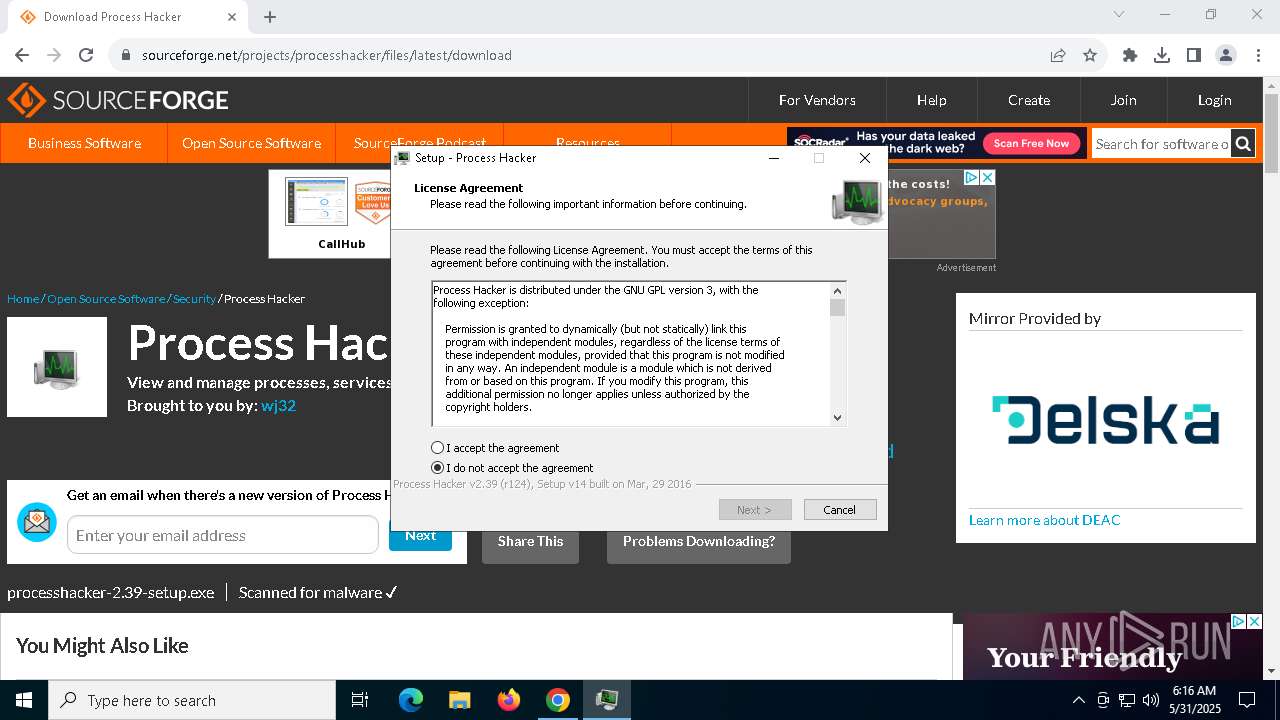
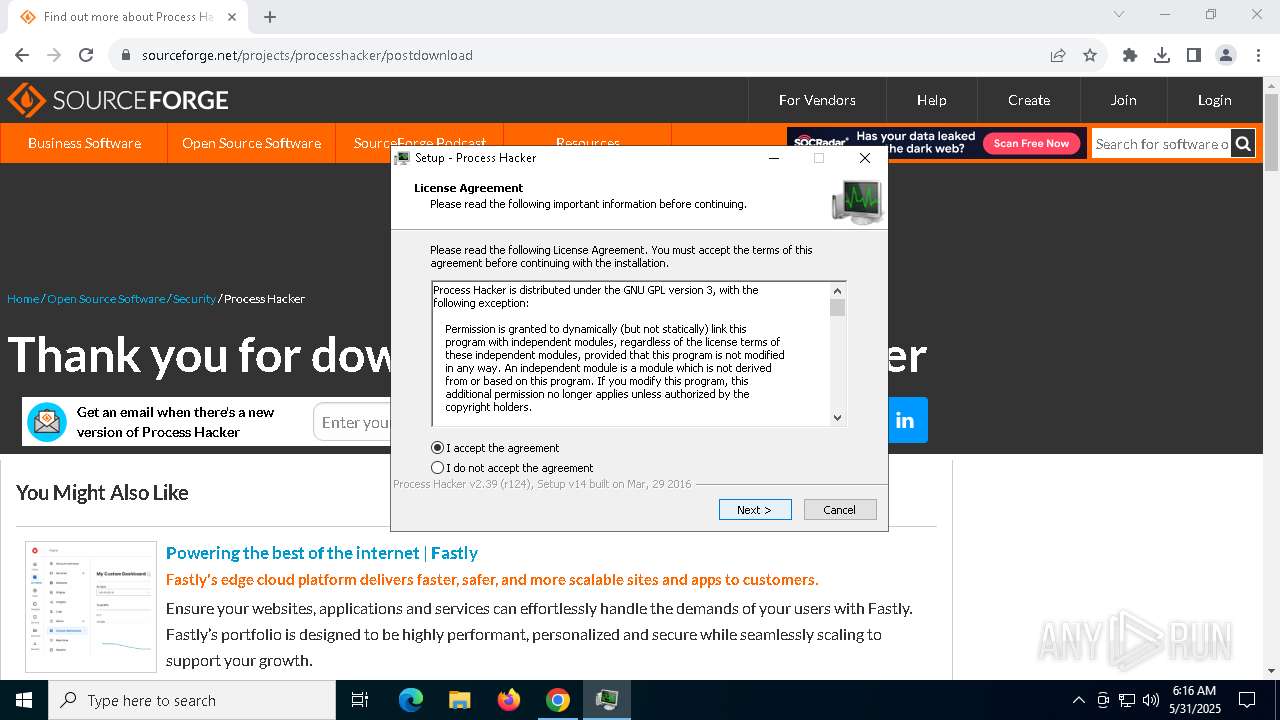
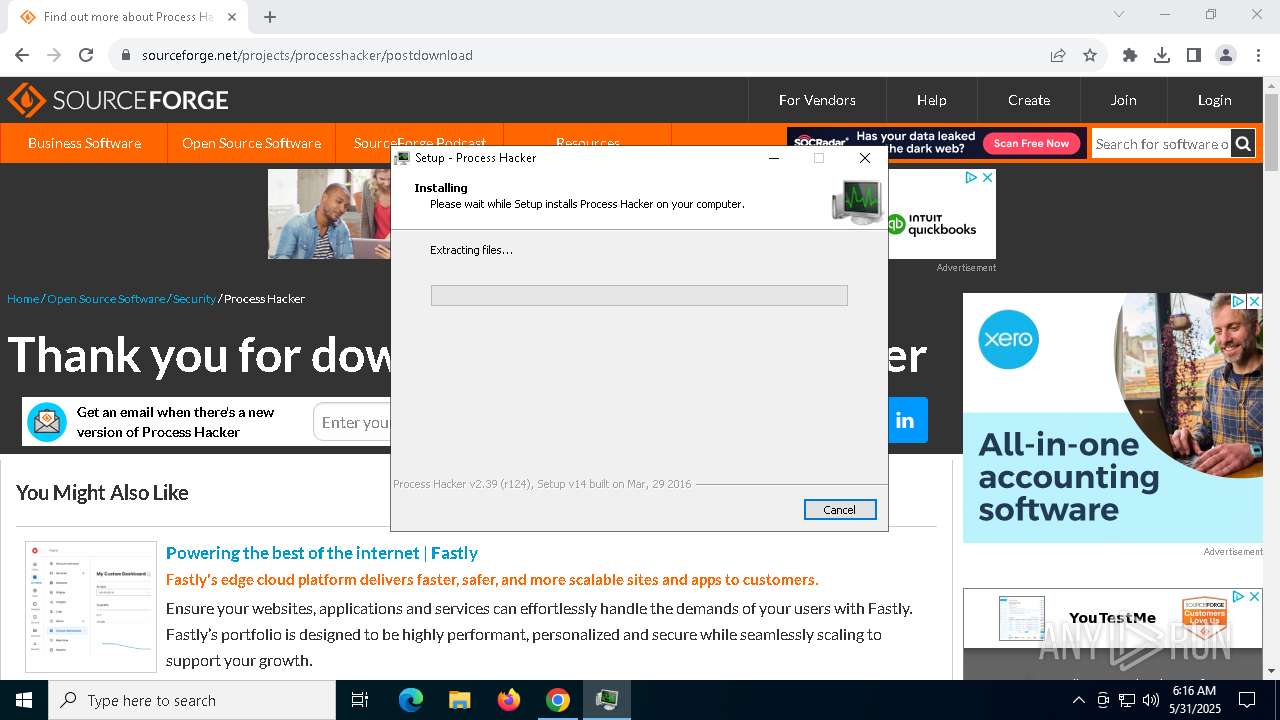
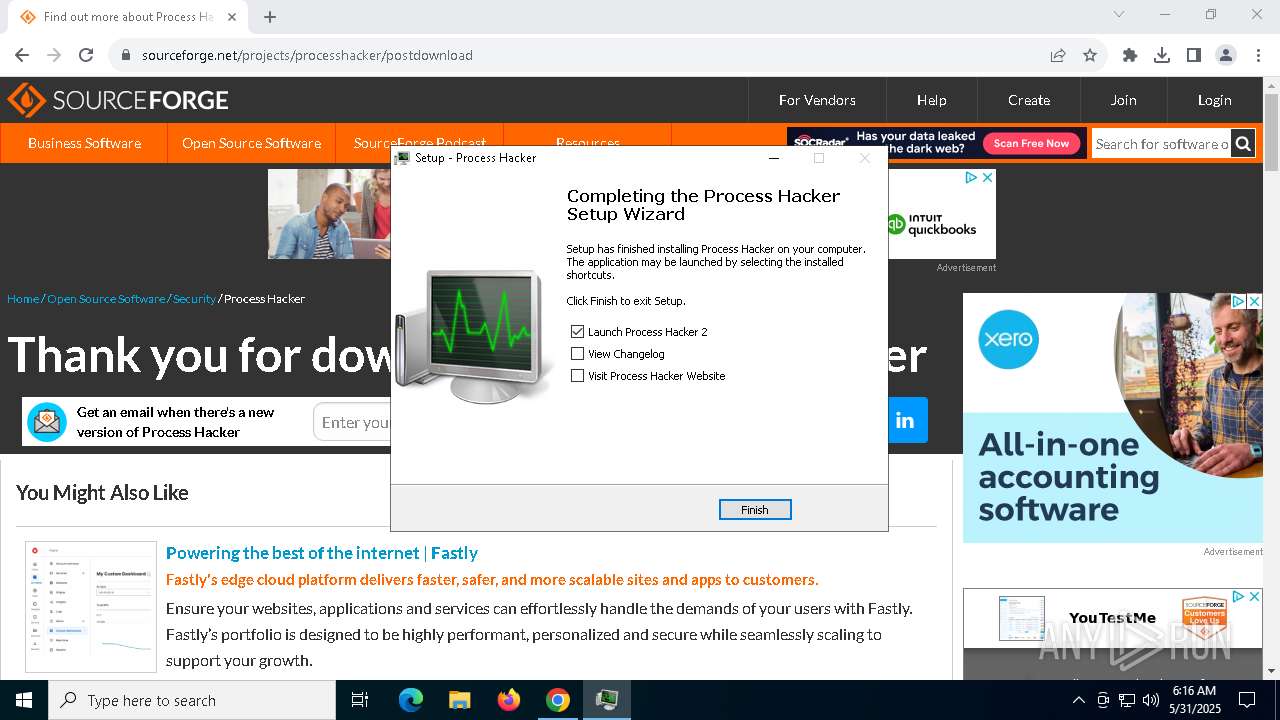
- processhacker-2.39-setup.tmp (PID: 5392)
SUSPICIOUS
Executable content was dropped or overwritten
- Flasher.exe (PID: 7148)
- ezezeww.exe (PID: 7500)
- vzycvcxx.exe (PID: 2236)
- fdnwxcx.exe (PID: 5552)
- processhacker-2.39-setup.exe (PID: 7284)
- processhacker-2.39-setup.exe (PID: 3140)
- processhacker-2.39-setup.tmp (PID: 5392)
Process drops legitimate windows executable
- Flasher.exe (PID: 7148)
- vzycvcxx.exe (PID: 2236)
- processhacker-2.39-setup.tmp (PID: 5392)
Reads the date of Windows installation
- Flasher.exe (PID: 7148)
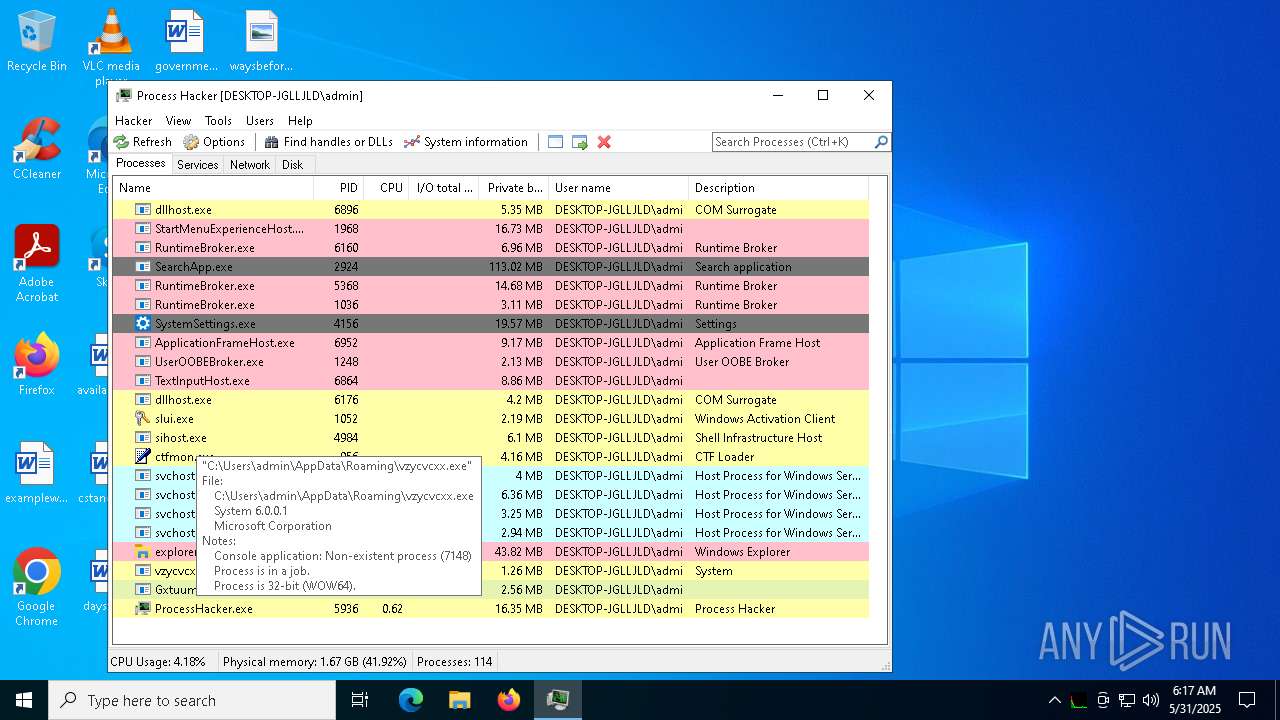
The process creates files with name similar to system file names
- vzycvcxx.exe (PID: 2236)
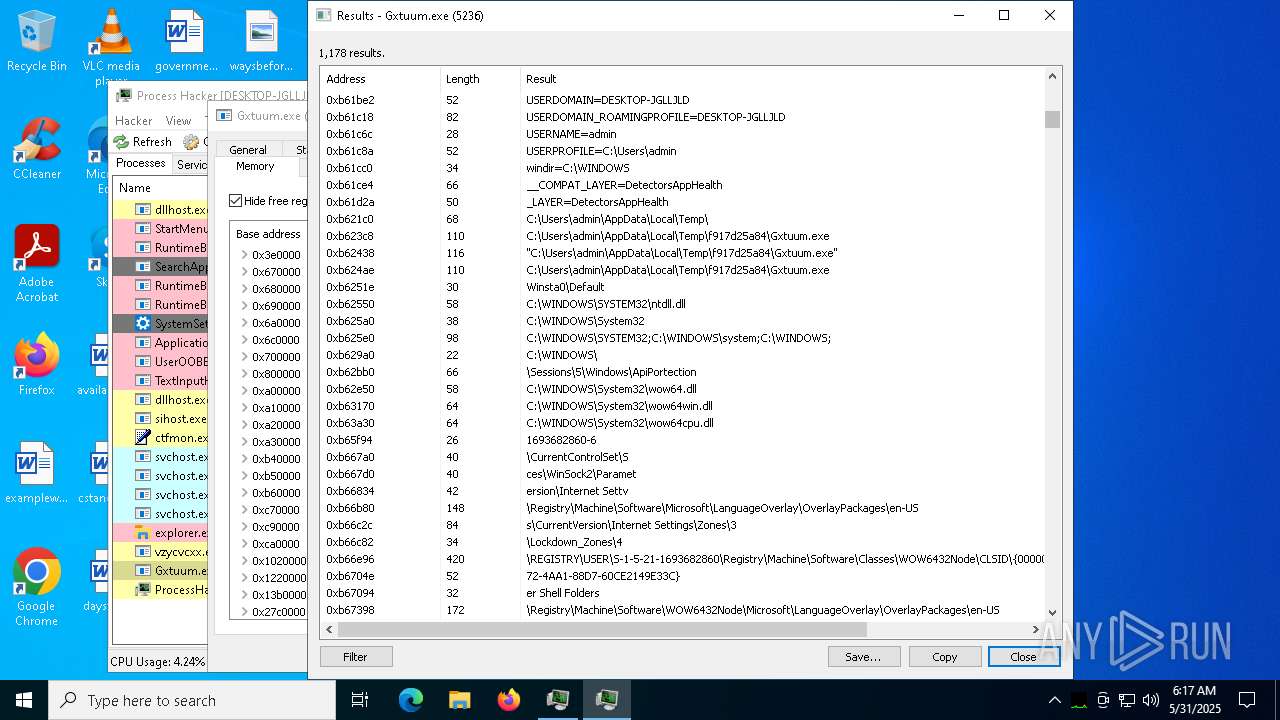
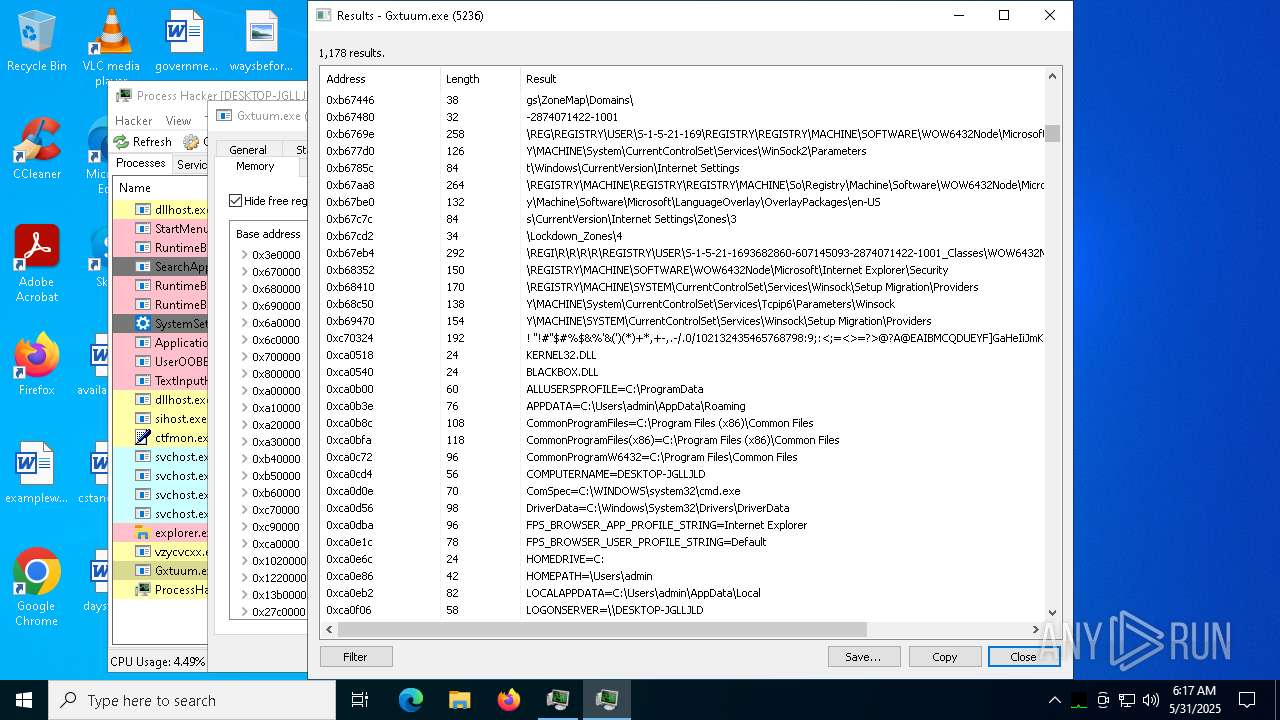
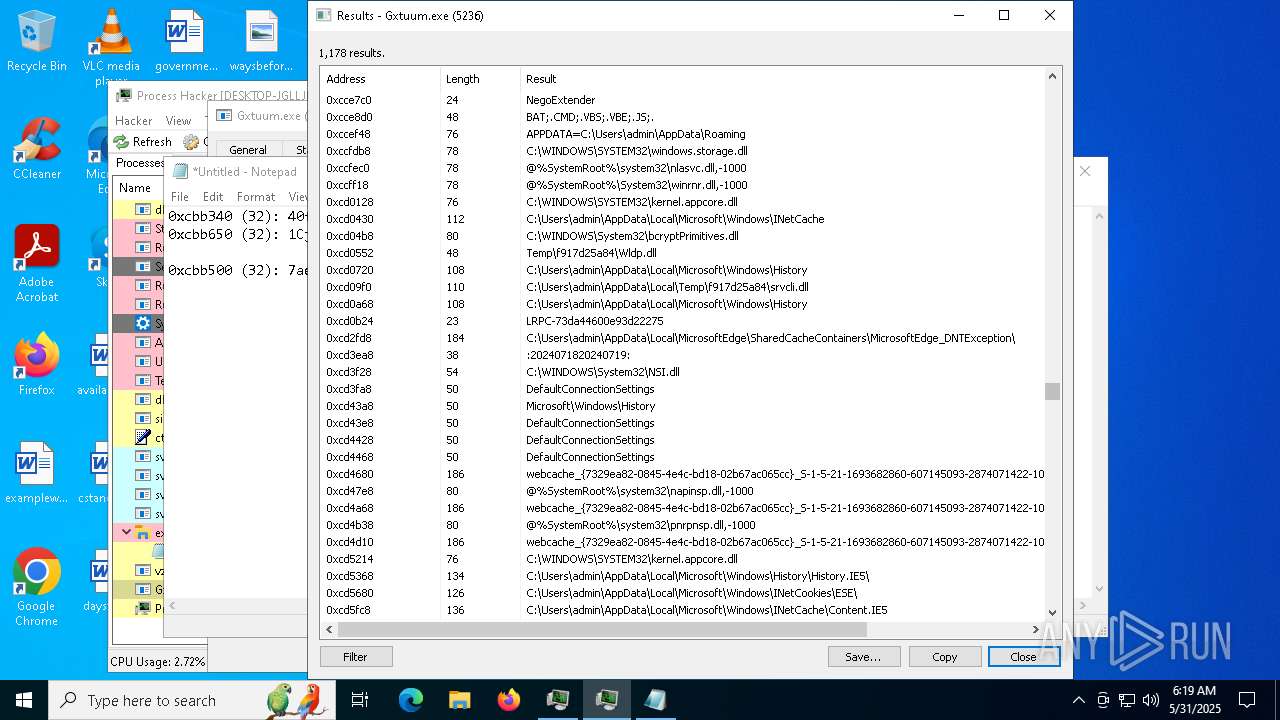
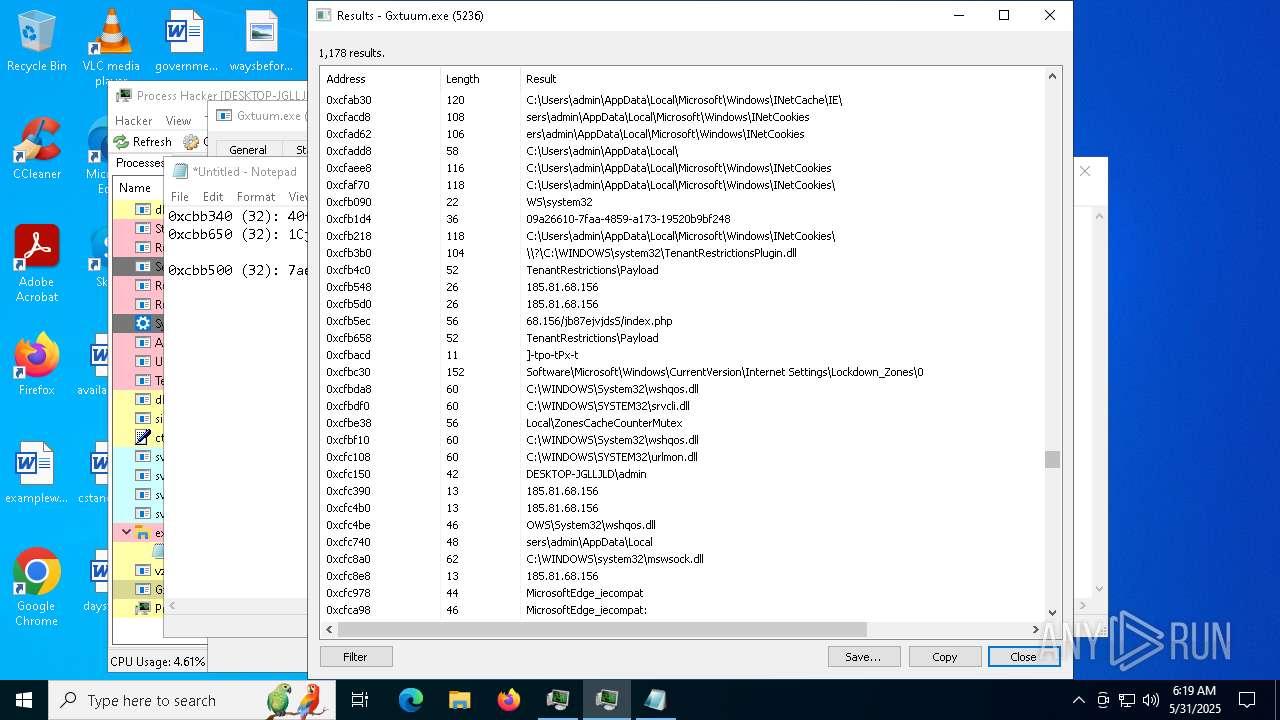
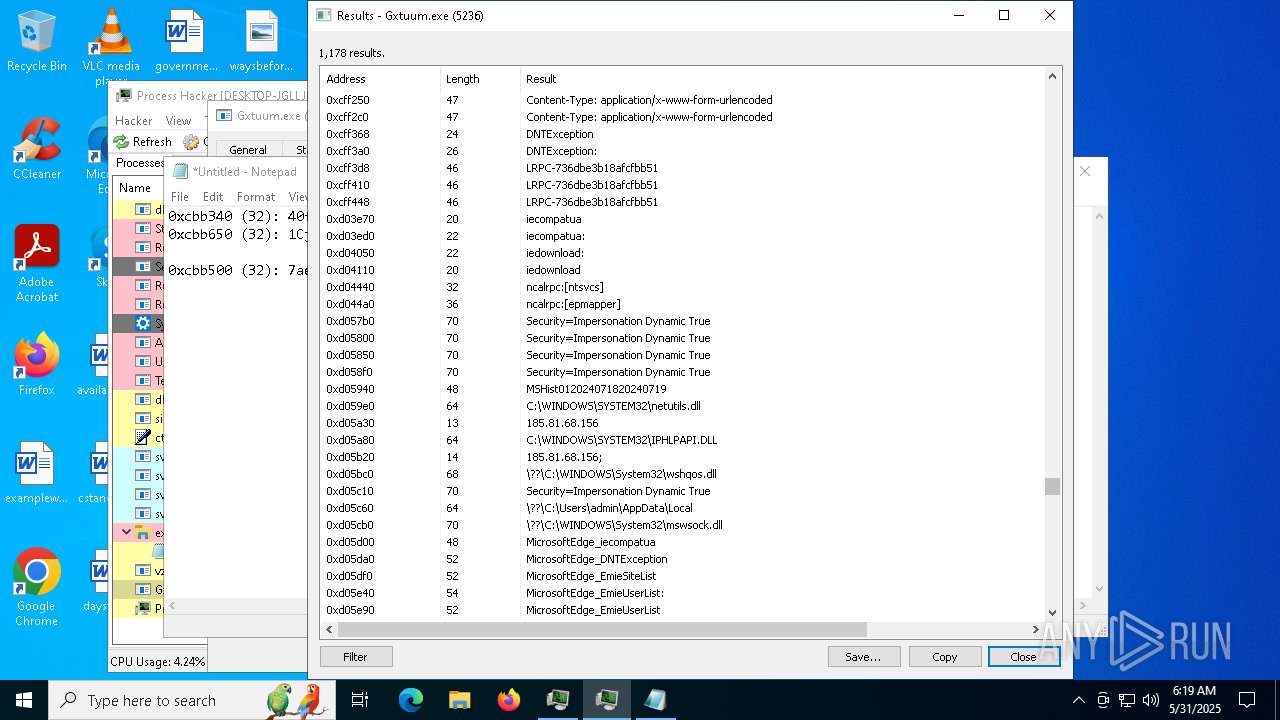
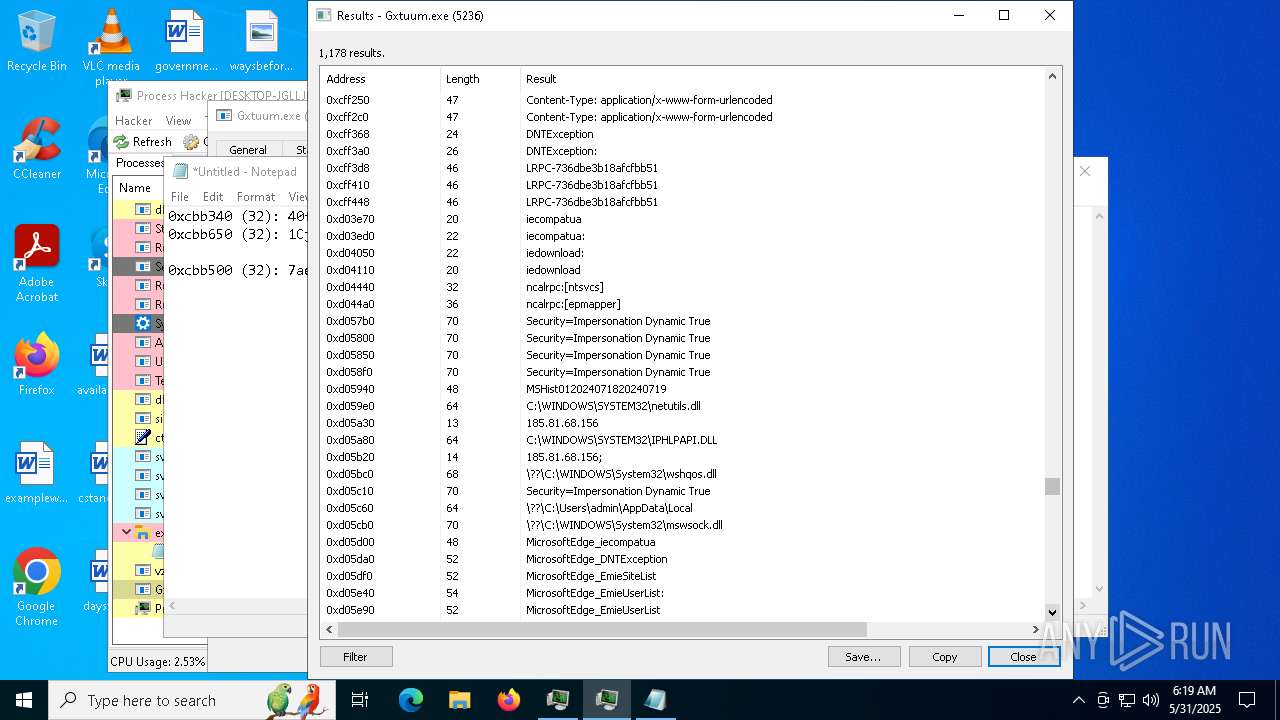
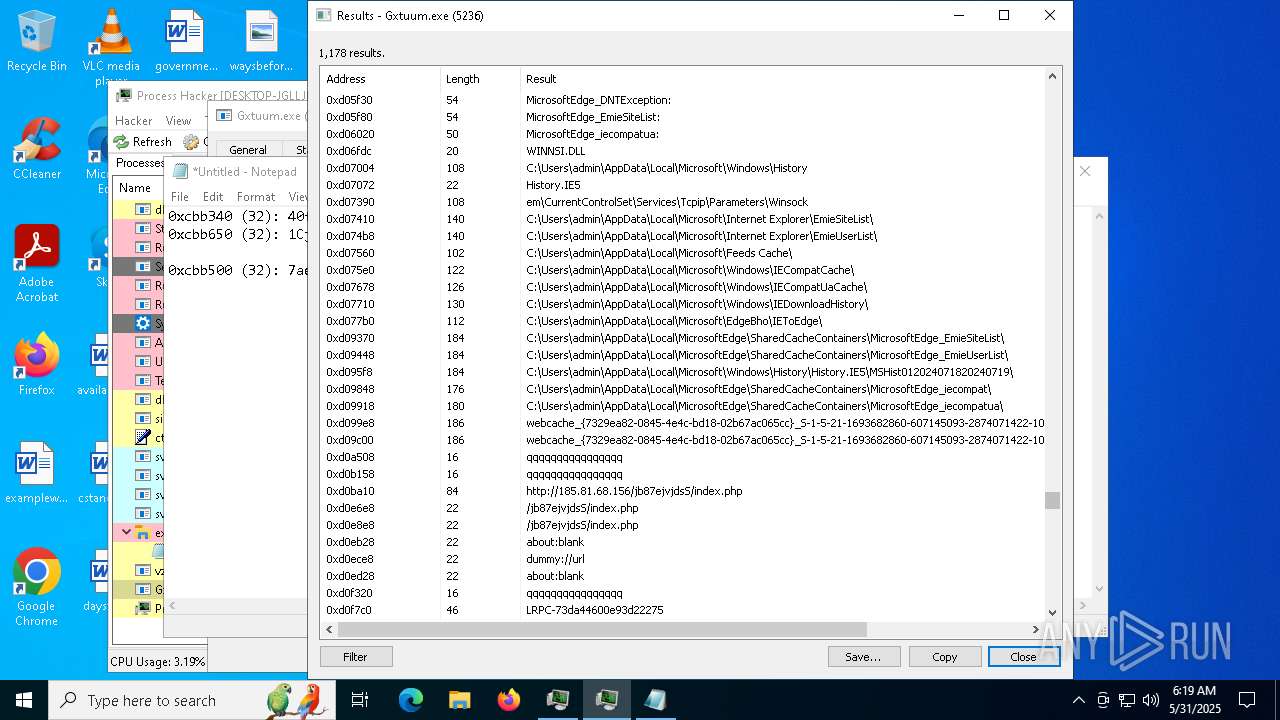
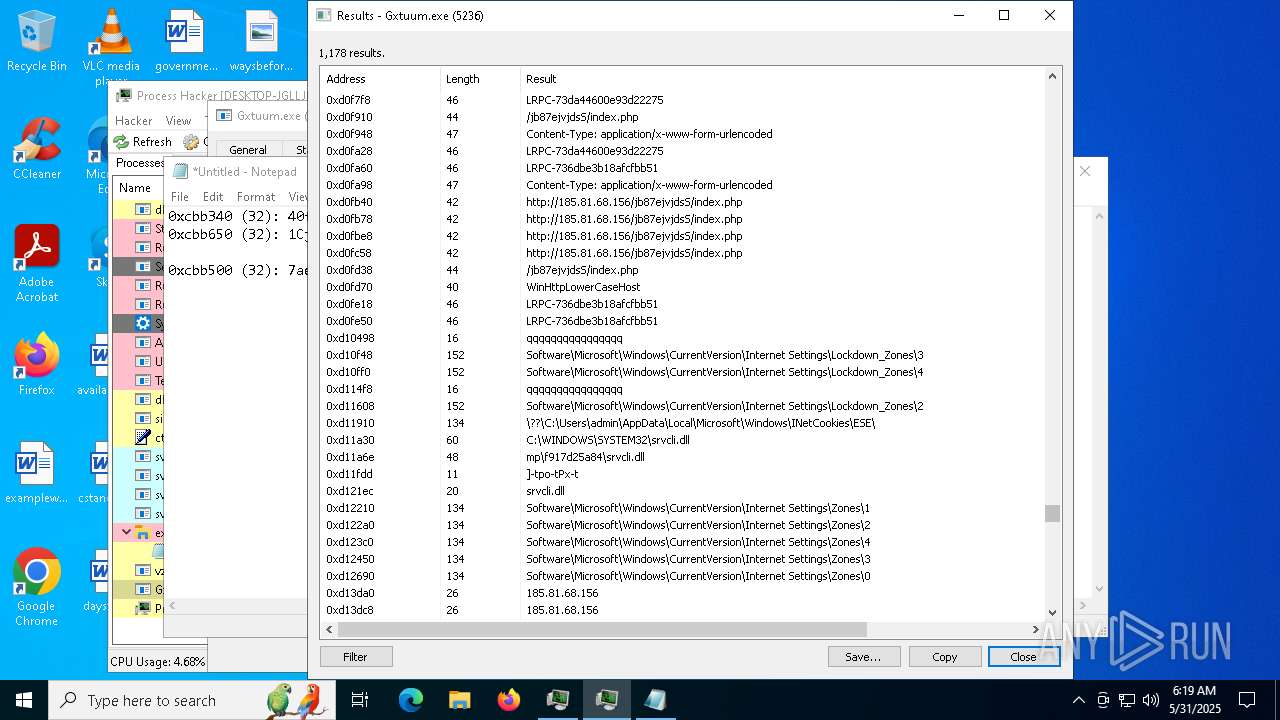
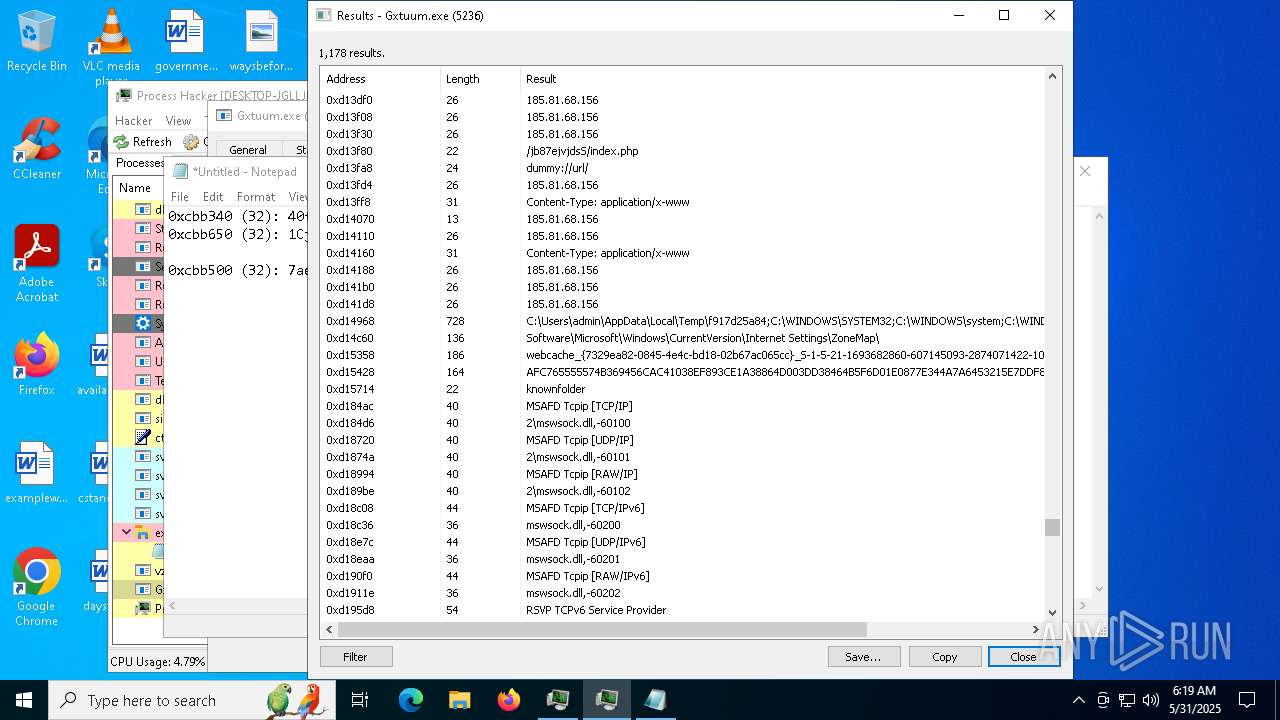
Reads security settings of Internet Explorer
- fdnwxcx.exe (PID: 5552)
- Gxtuum.exe (PID: 5236)
- processhacker-2.39-setup.tmp (PID: 1040)
- ProcessHacker.exe (PID: 5936)
- Flasher.exe (PID: 7148)
Starts itself from another location
- fdnwxcx.exe (PID: 5552)
Found regular expressions for crypto-addresses (YARA)
- vzycvcxx.exe (PID: 2236)
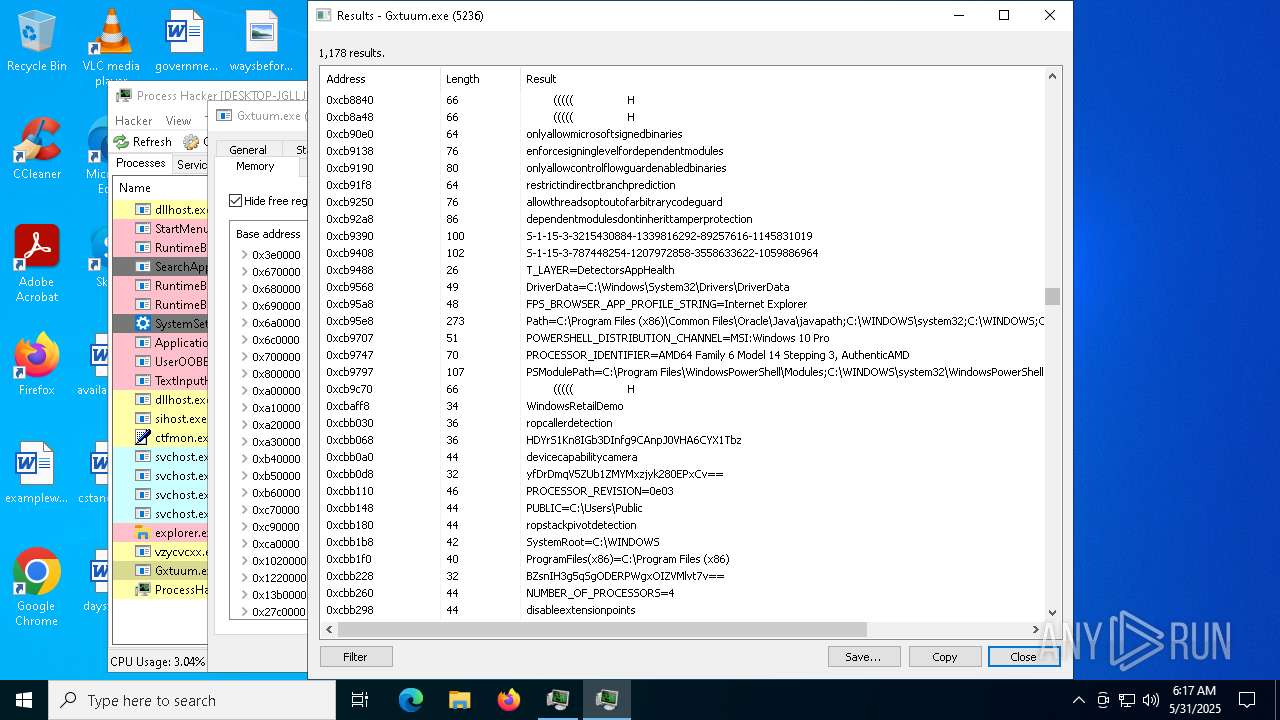
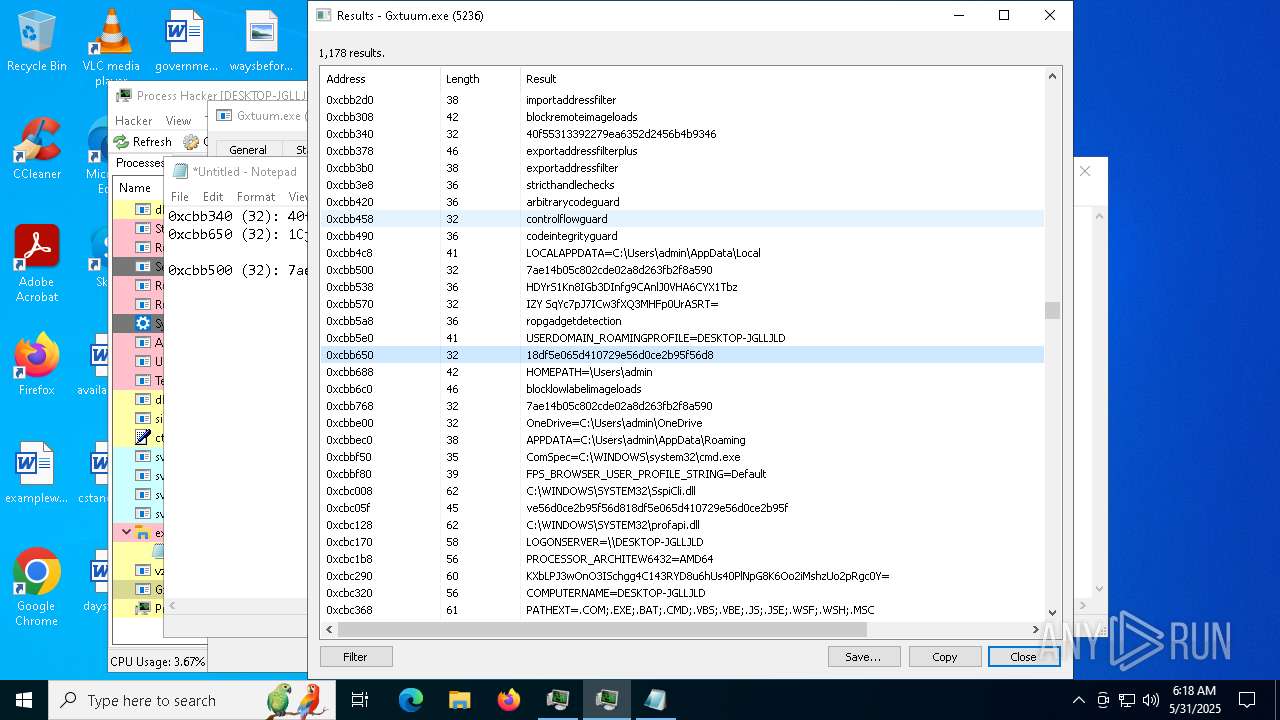
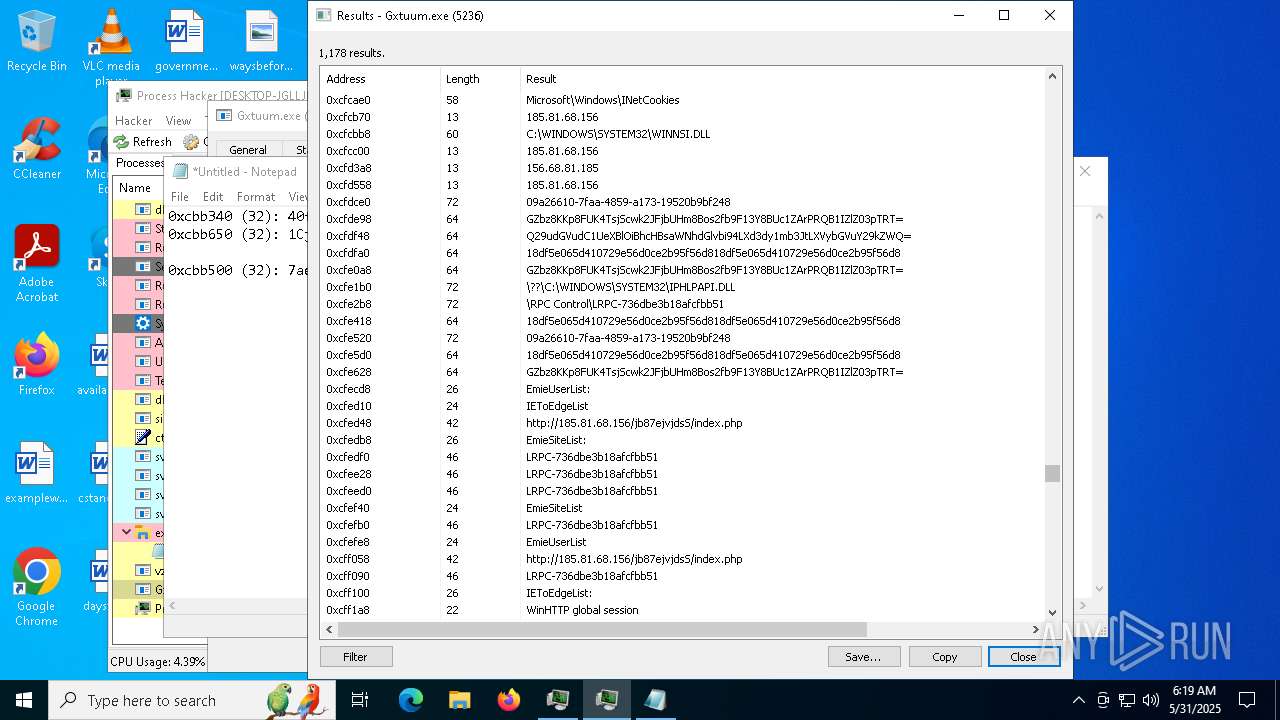
There is functionality for enable RDP (YARA)
- Gxtuum.exe (PID: 5236)
The process executes via Task Scheduler
- Gxtuum.exe (PID: 660)
- Gxtuum.exe (PID: 2772)
- Gxtuum.exe (PID: 7548)
- Gxtuum.exe (PID: 2088)
- Gxtuum.exe (PID: 7676)
There is functionality for taking screenshot (YARA)
- Gxtuum.exe (PID: 5236)
Reads the Windows owner or organization settings
- processhacker-2.39-setup.tmp (PID: 5392)
Drops a system driver (possible attempt to evade defenses)
- processhacker-2.39-setup.tmp (PID: 5392)
INFO
The sample compiled with english language support
- Flasher.exe (PID: 7148)
- vzycvcxx.exe (PID: 2236)
- processhacker-2.39-setup.tmp (PID: 5392)
Creates files or folders in the user directory
- Flasher.exe (PID: 7148)
- explorer.exe (PID: 5492)
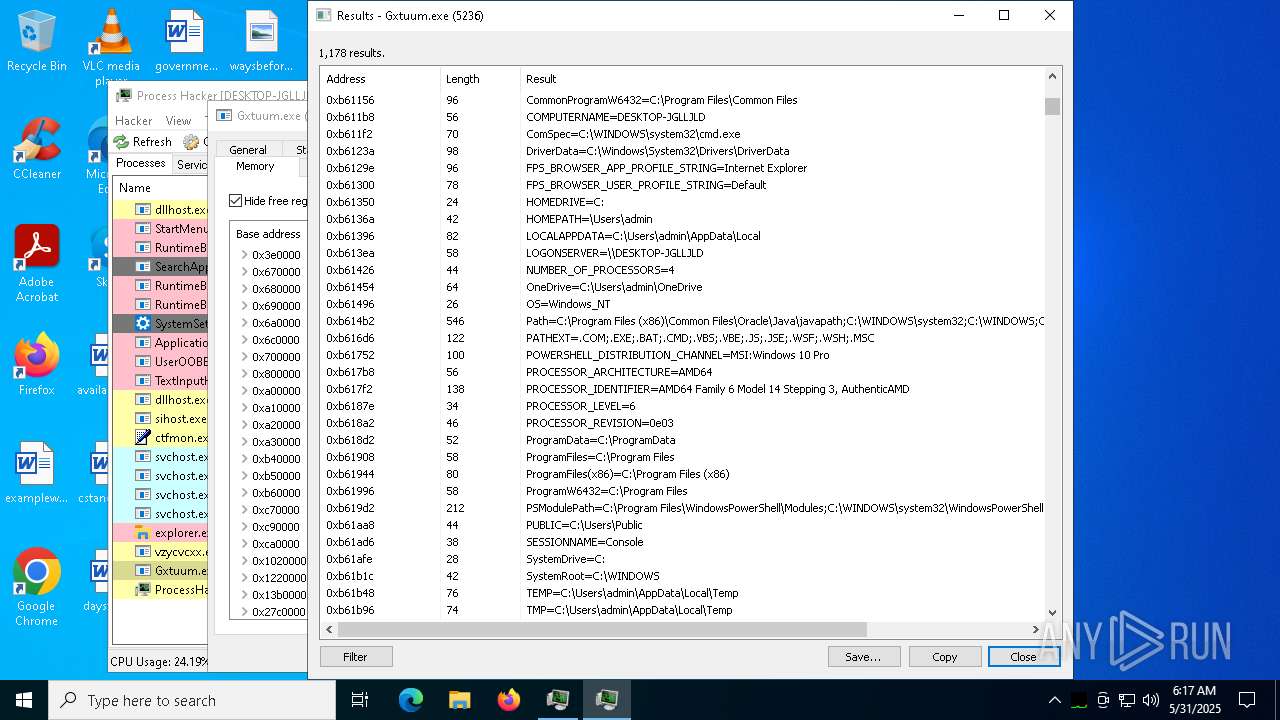
Checks supported languages
- Flasher.exe (PID: 7148)
- ezezeww.exe (PID: 7500)
- vcpcjo.exe (PID: 4700)
- vzycvcxx.exe (PID: 2236)
- Gxtuum.exe (PID: 660)
- Gxtuum.exe (PID: 5236)
- processhacker-2.39-setup.tmp (PID: 1040)
- processhacker-2.39-setup.exe (PID: 7284)
- processhacker-2.39-setup.exe (PID: 3140)
- processhacker-2.39-setup.tmp (PID: 5392)
- ProcessHacker.exe (PID: 5936)
- Gxtuum.exe (PID: 2772)
- fdnwxcx.exe (PID: 5552)
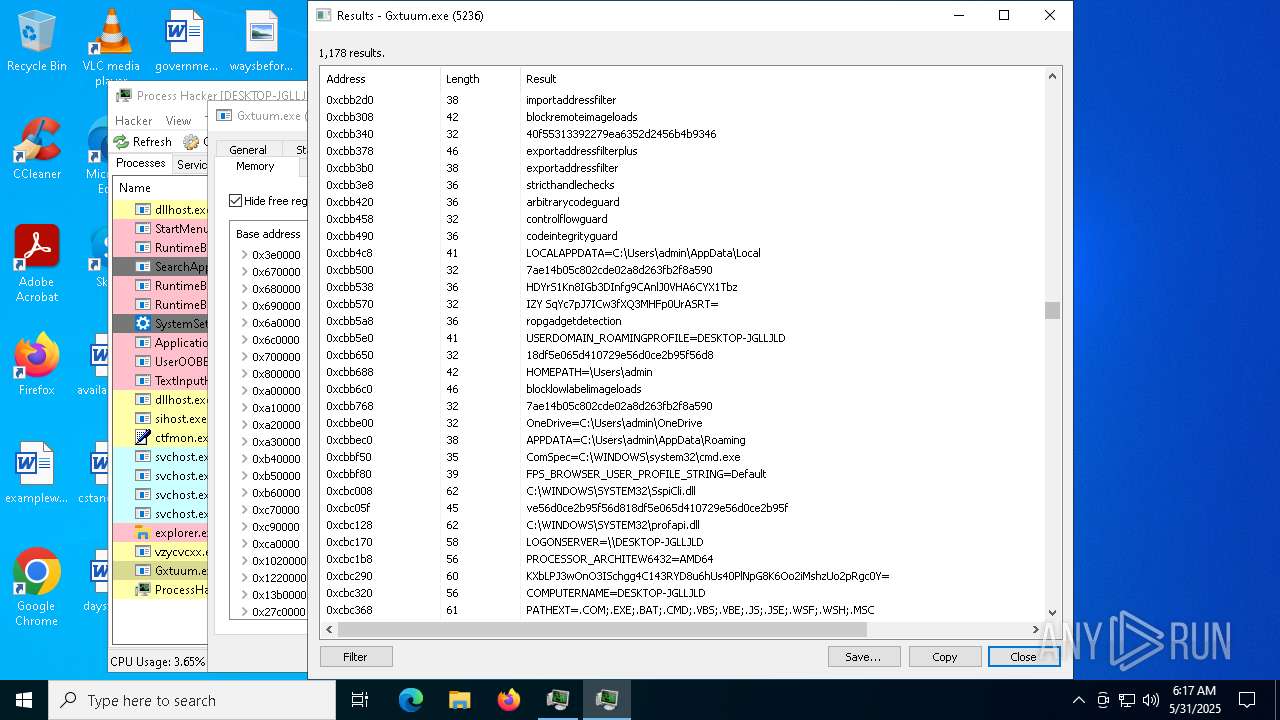
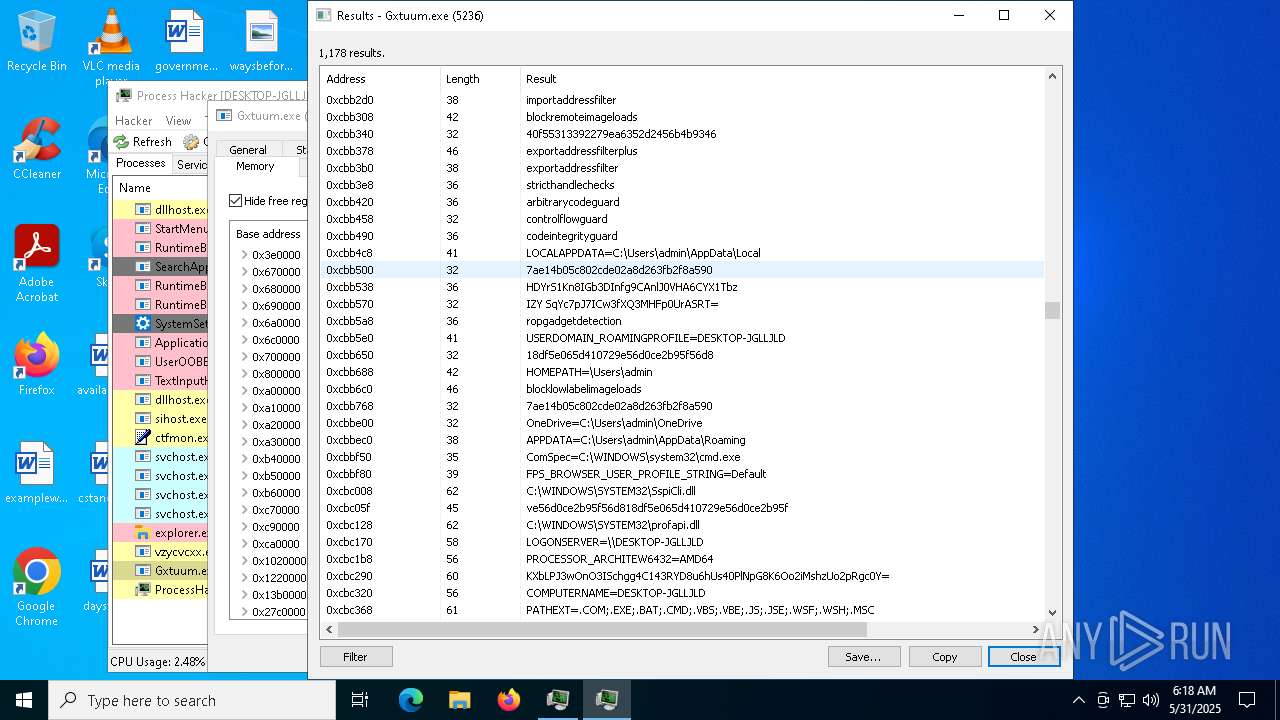
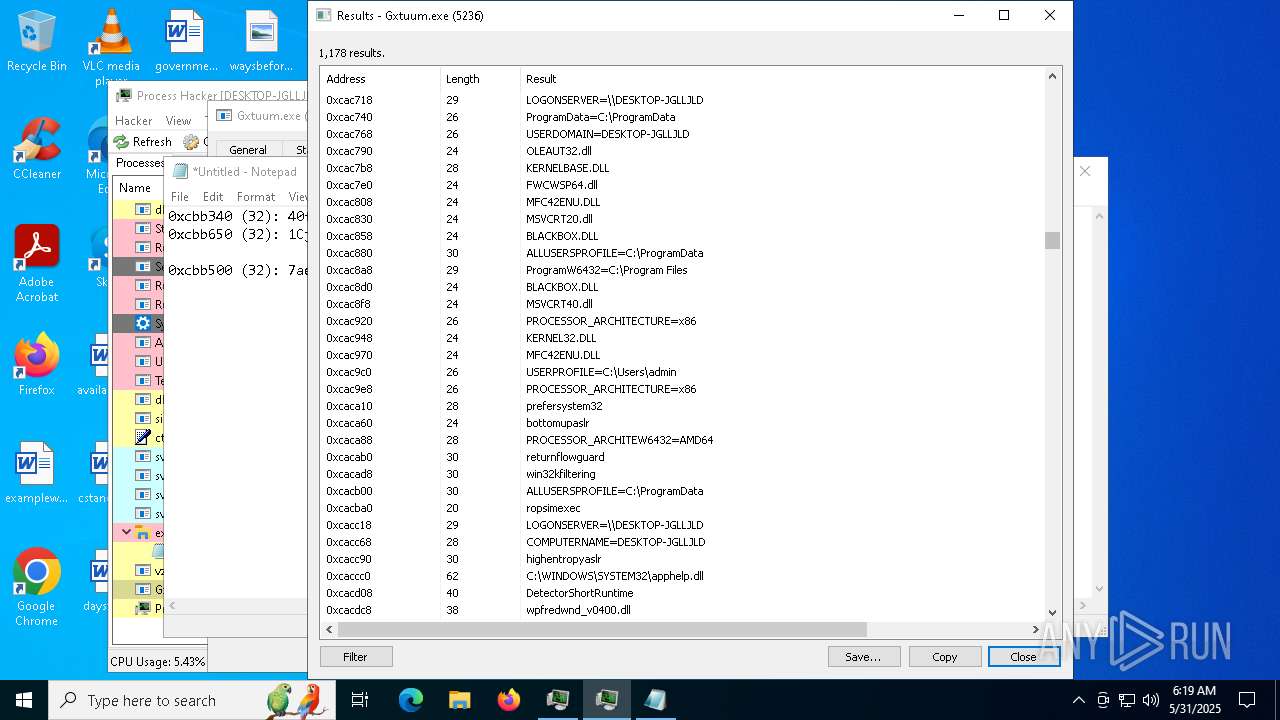
Reads the computer name
- Flasher.exe (PID: 7148)
- vcpcjo.exe (PID: 4700)
- fdnwxcx.exe (PID: 5552)
- Gxtuum.exe (PID: 5236)
- processhacker-2.39-setup.tmp (PID: 1040)
- processhacker-2.39-setup.tmp (PID: 5392)
- ProcessHacker.exe (PID: 5936)
Reads the machine GUID from the registry
- ezezeww.exe (PID: 7500)
- ProcessHacker.exe (PID: 5936)
Creates files in the program directory
- ezezeww.exe (PID: 7500)
- vzycvcxx.exe (PID: 2236)
- processhacker-2.39-setup.tmp (PID: 5392)
Launch of the file from Registry key
- ezezeww.exe (PID: 7500)
- vzycvcxx.exe (PID: 2236)
- explorer.exe (PID: 5492)
Create files in a temporary directory
- fdnwxcx.exe (PID: 5552)
- processhacker-2.39-setup.exe (PID: 7284)
- processhacker-2.39-setup.exe (PID: 3140)
- processhacker-2.39-setup.tmp (PID: 5392)
Process checks computer location settings
- fdnwxcx.exe (PID: 5552)
- processhacker-2.39-setup.tmp (PID: 1040)
- Flasher.exe (PID: 7148)
Reads security settings of Internet Explorer
- explorer.exe (PID: 5492)
Checks proxy server information
- Gxtuum.exe (PID: 5236)
- explorer.exe (PID: 5492)
- ProcessHacker.exe (PID: 5936)
- slui.exe (PID: 1052)
Application launched itself
- chrome.exe (PID: 900)
Reads the software policy settings
- slui.exe (PID: 3156)
- ProcessHacker.exe (PID: 5936)
- slui.exe (PID: 1052)
Executable content was dropped or overwritten
- chrome.exe (PID: 7932)
- chrome.exe (PID: 900)
Launch of the file from Downloads directory
- chrome.exe (PID: 900)
PROCESSHACKER mutex has been found
- processhacker-2.39-setup.tmp (PID: 5392)
Creates a software uninstall entry
- processhacker-2.39-setup.tmp (PID: 5392)
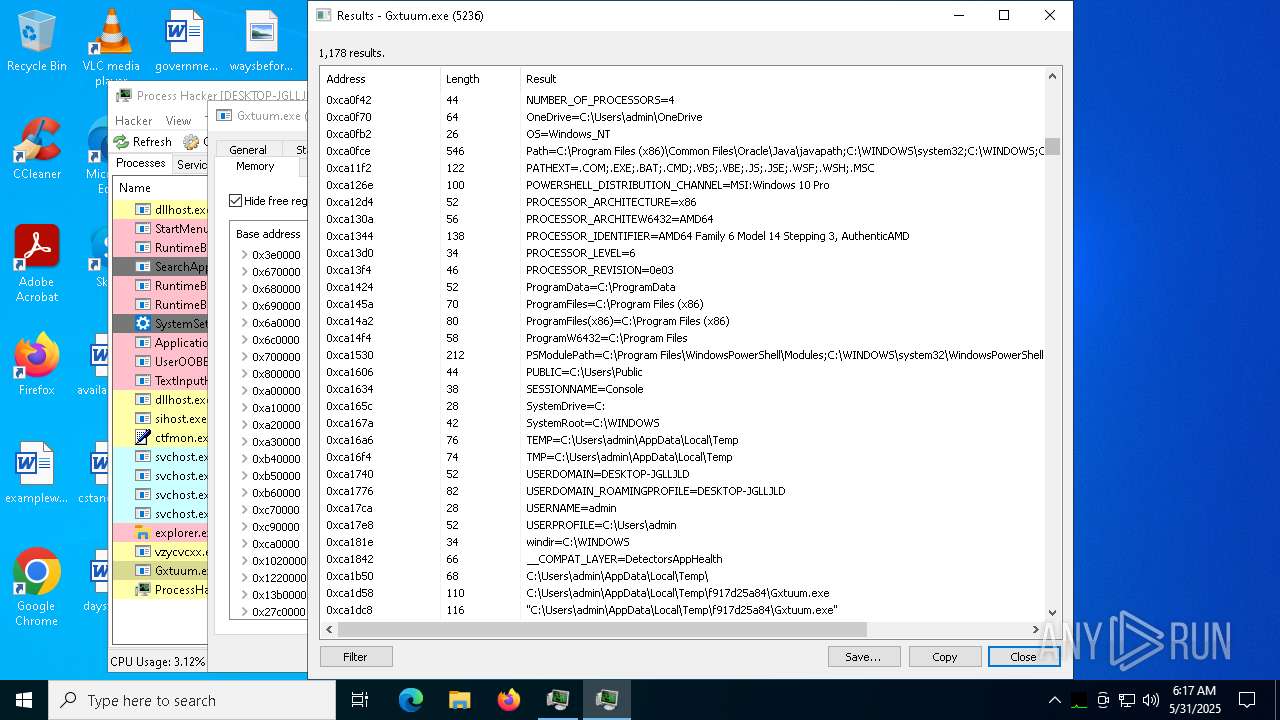
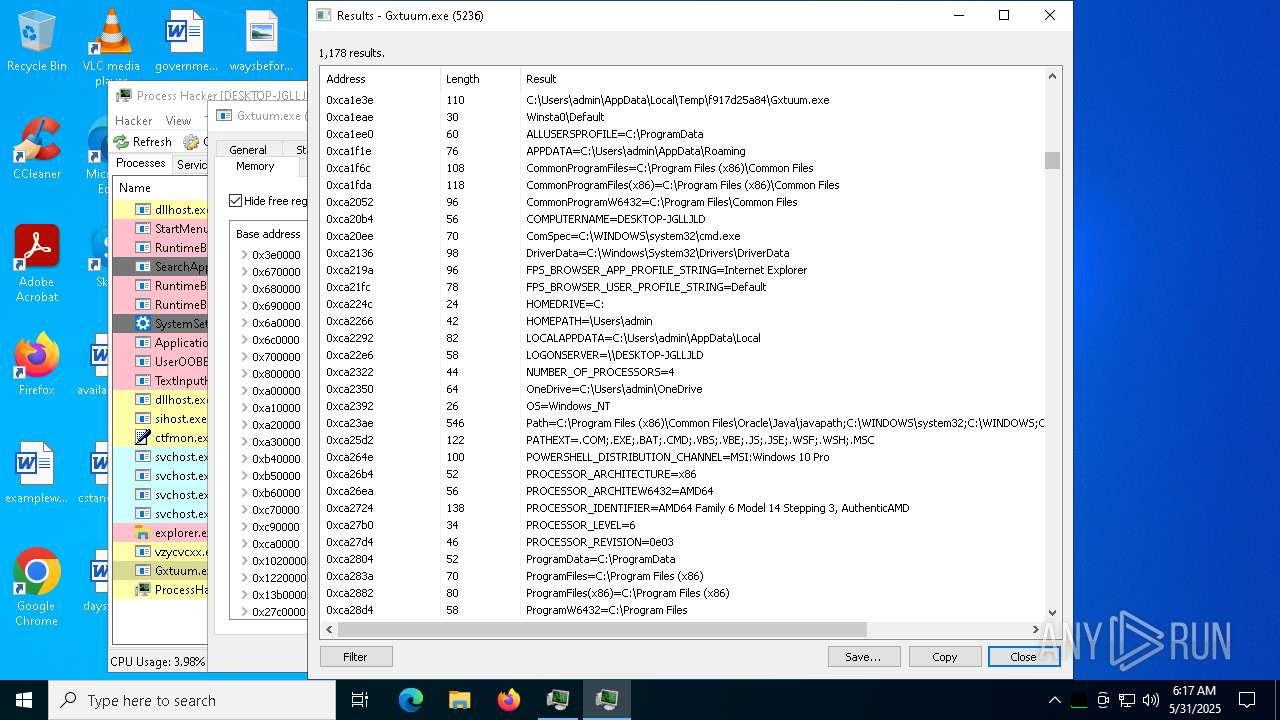
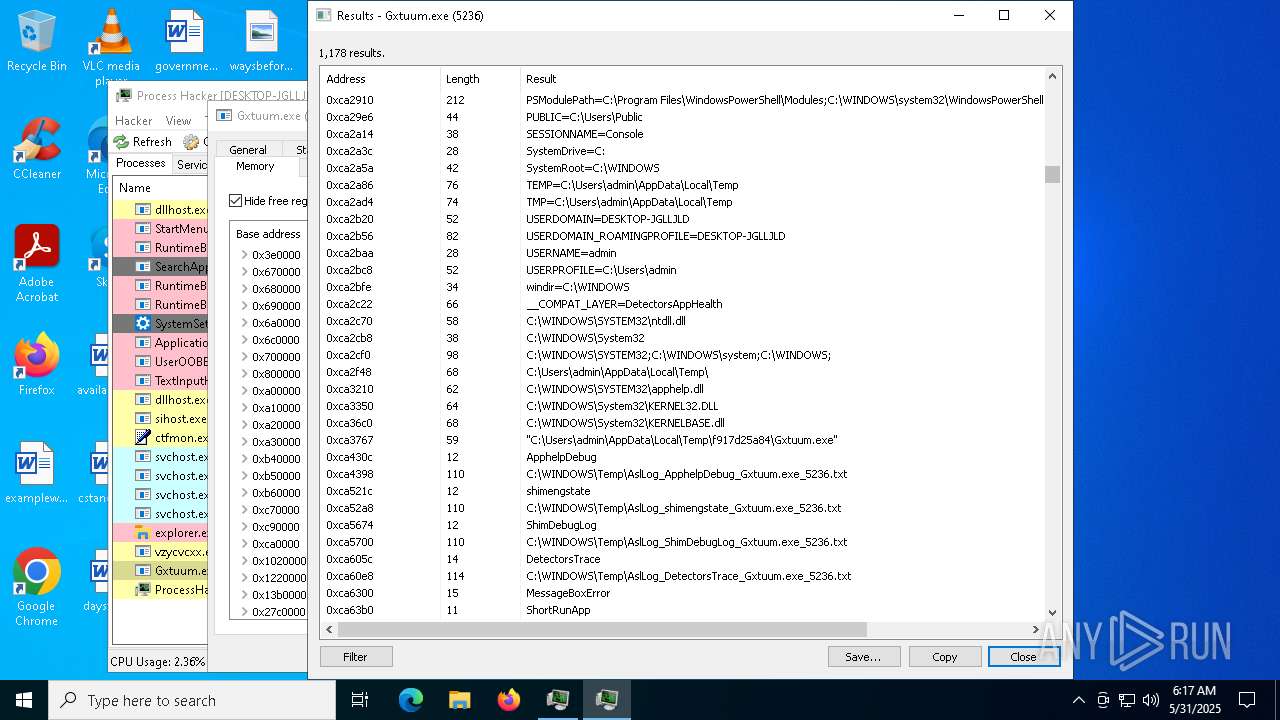
Reads Environment values
- ProcessHacker.exe (PID: 5936)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
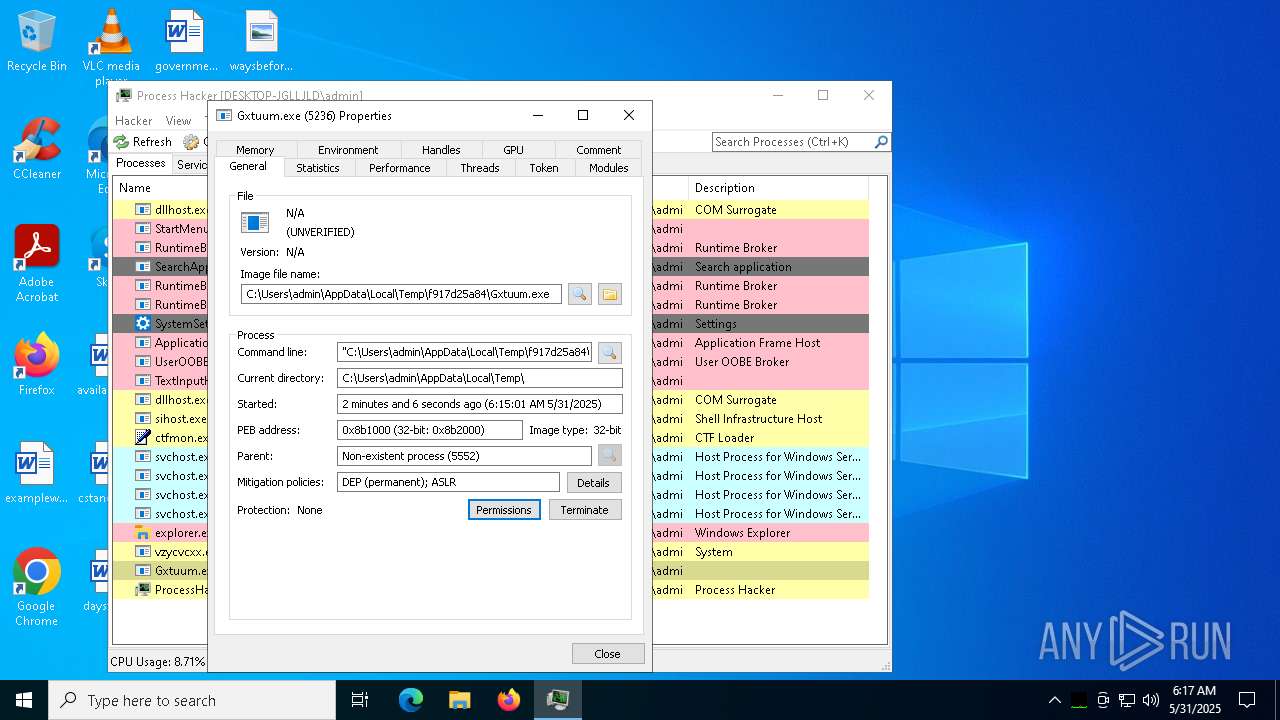
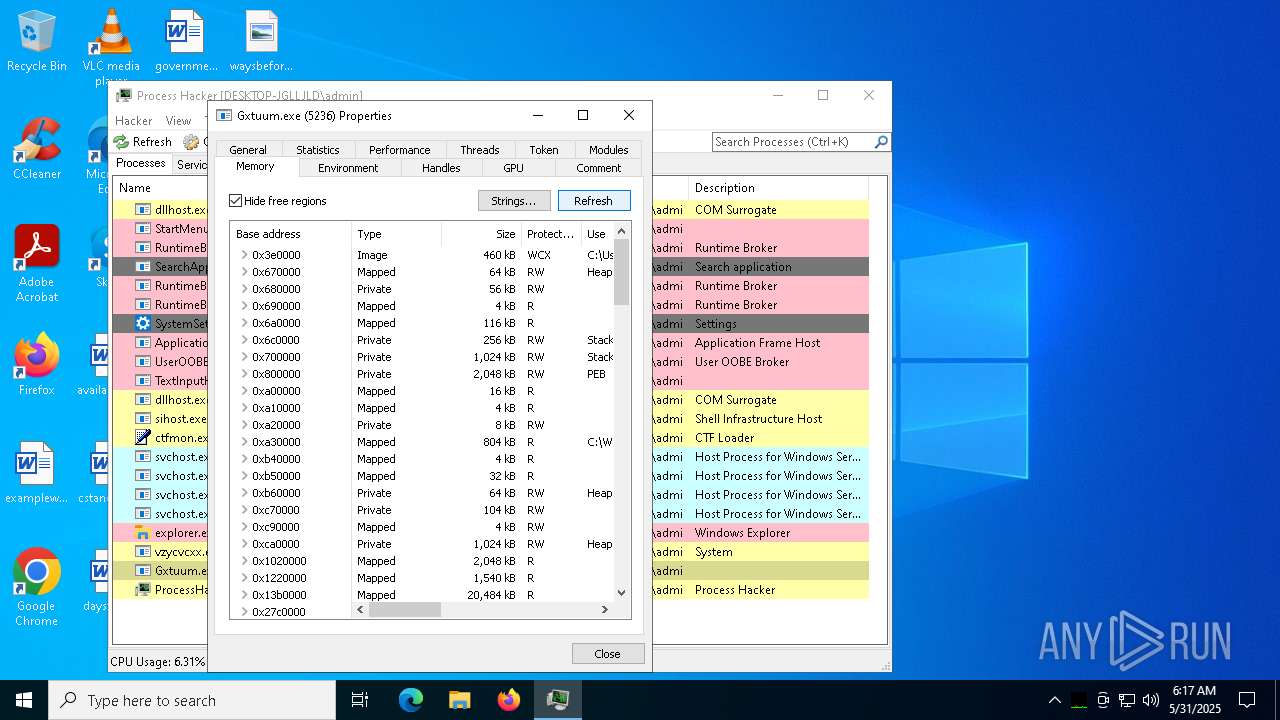
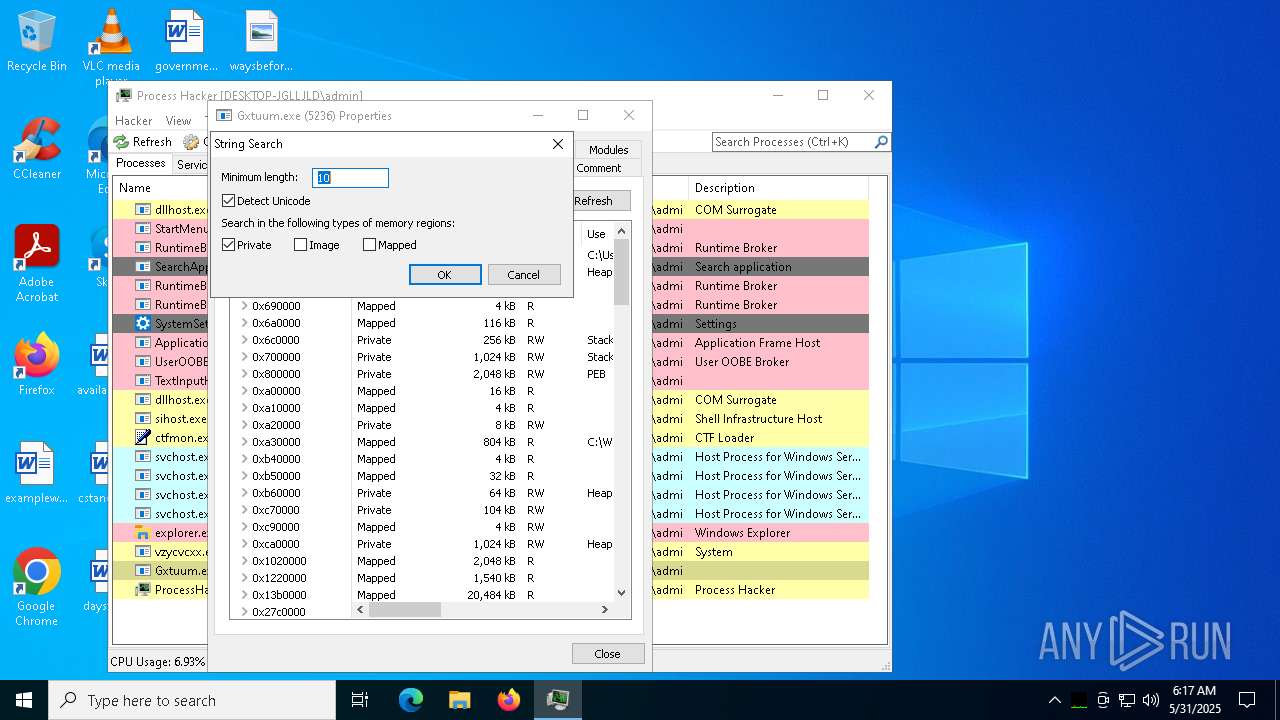
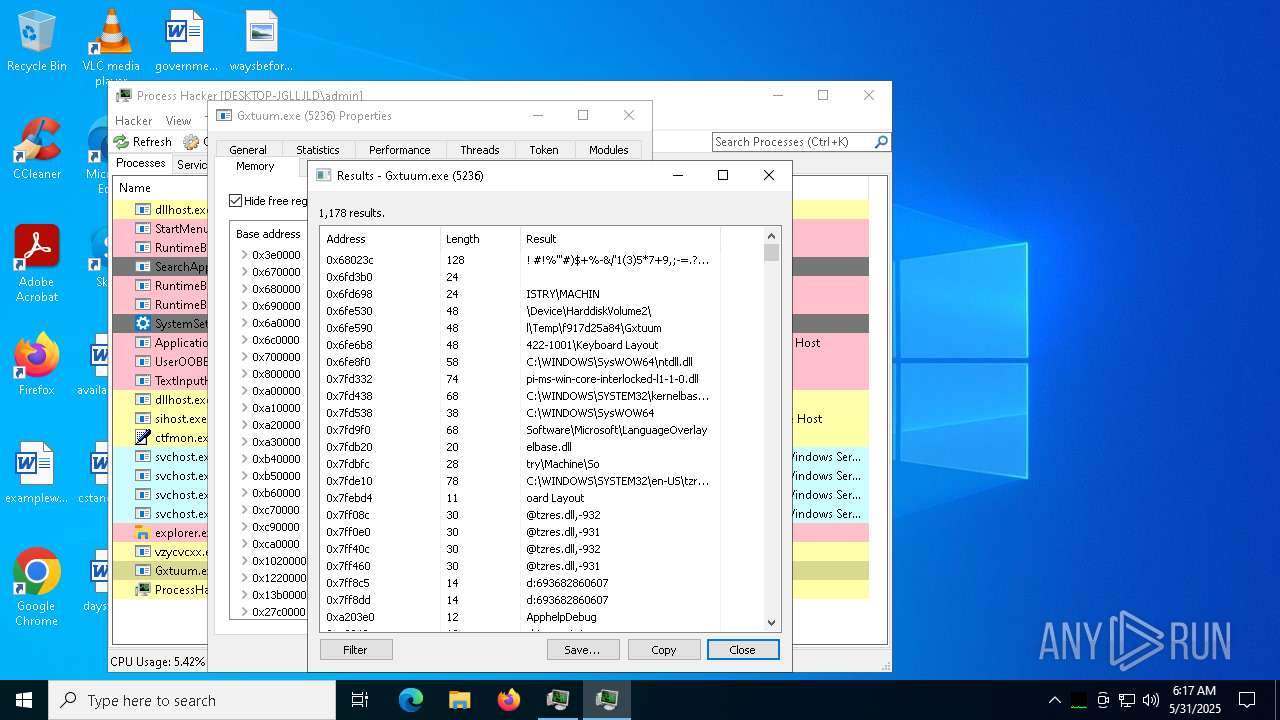
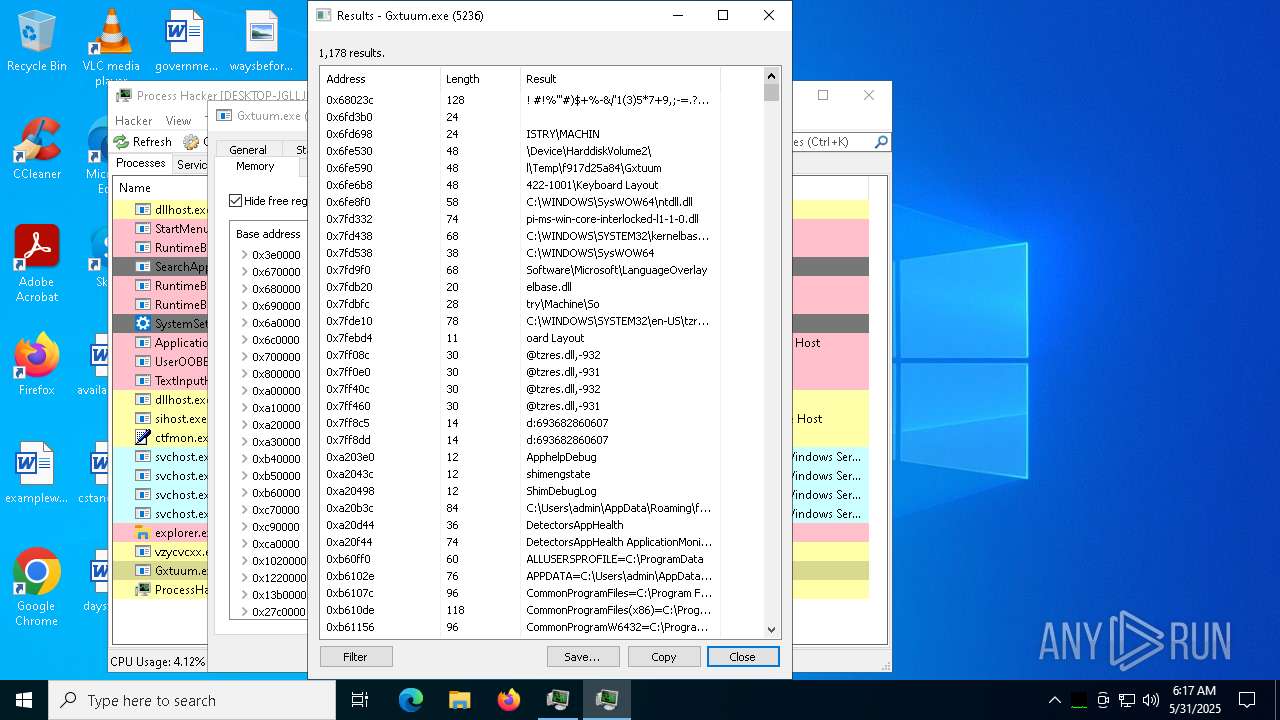
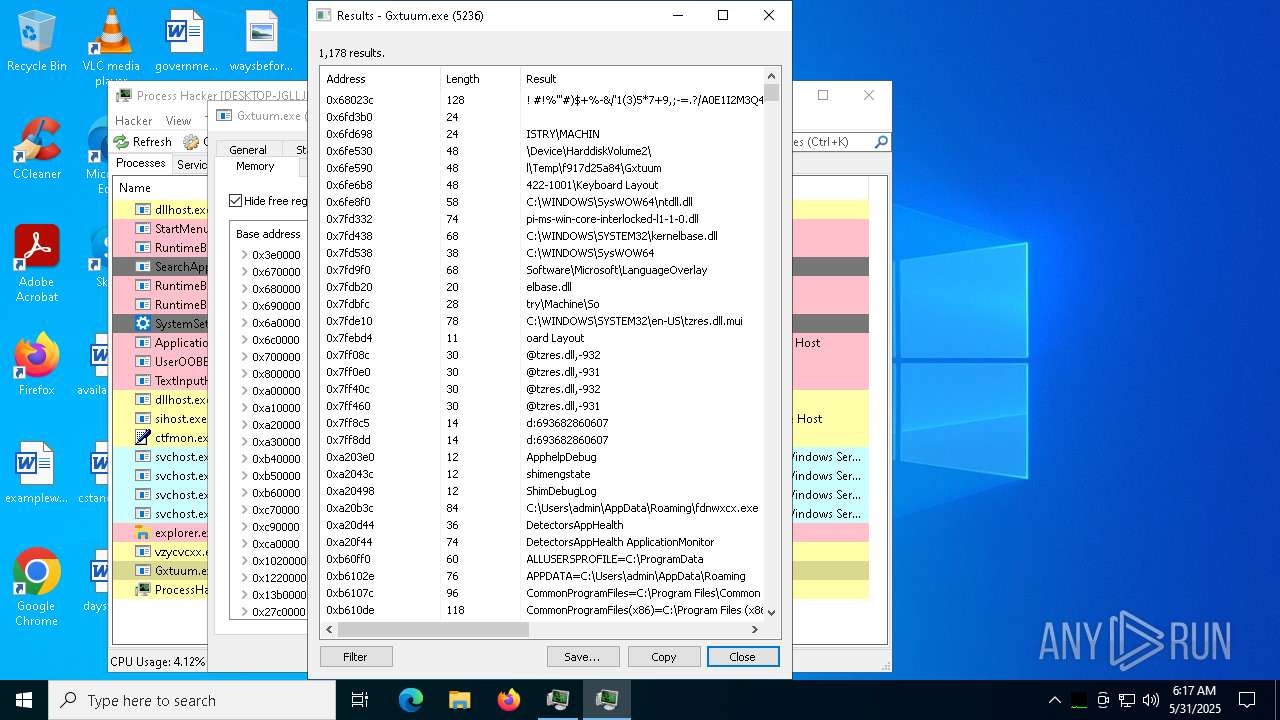
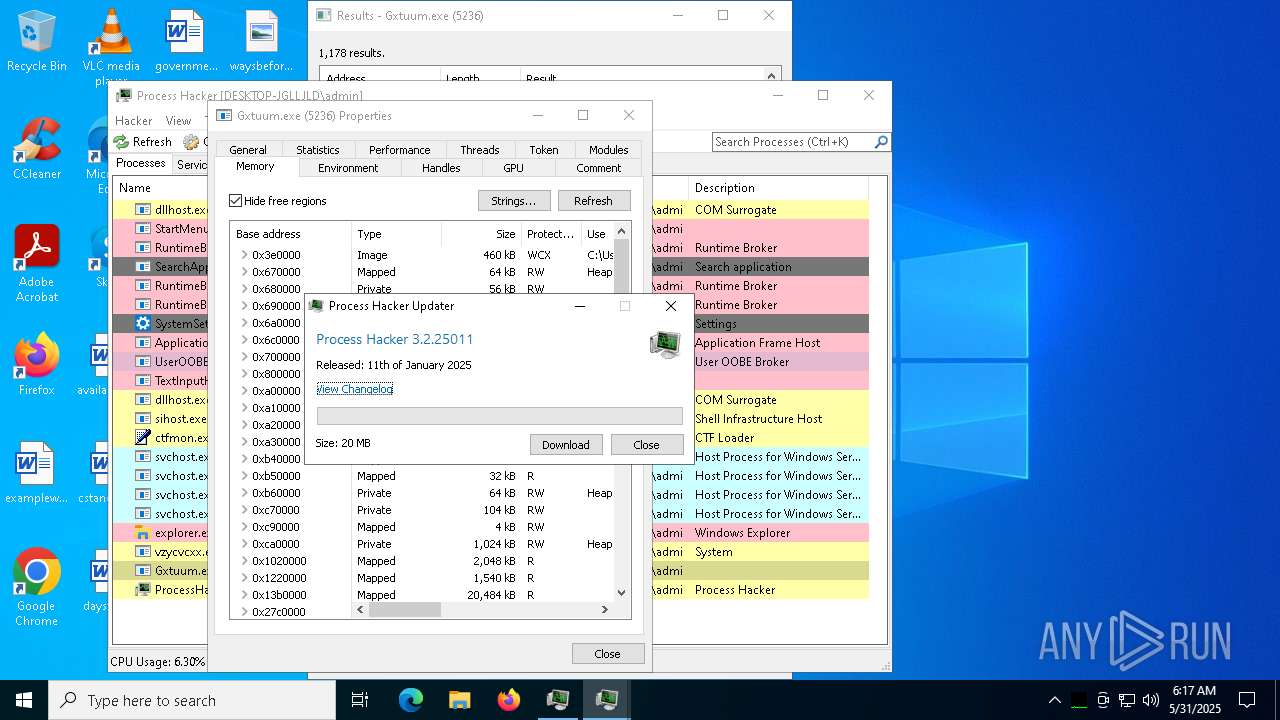
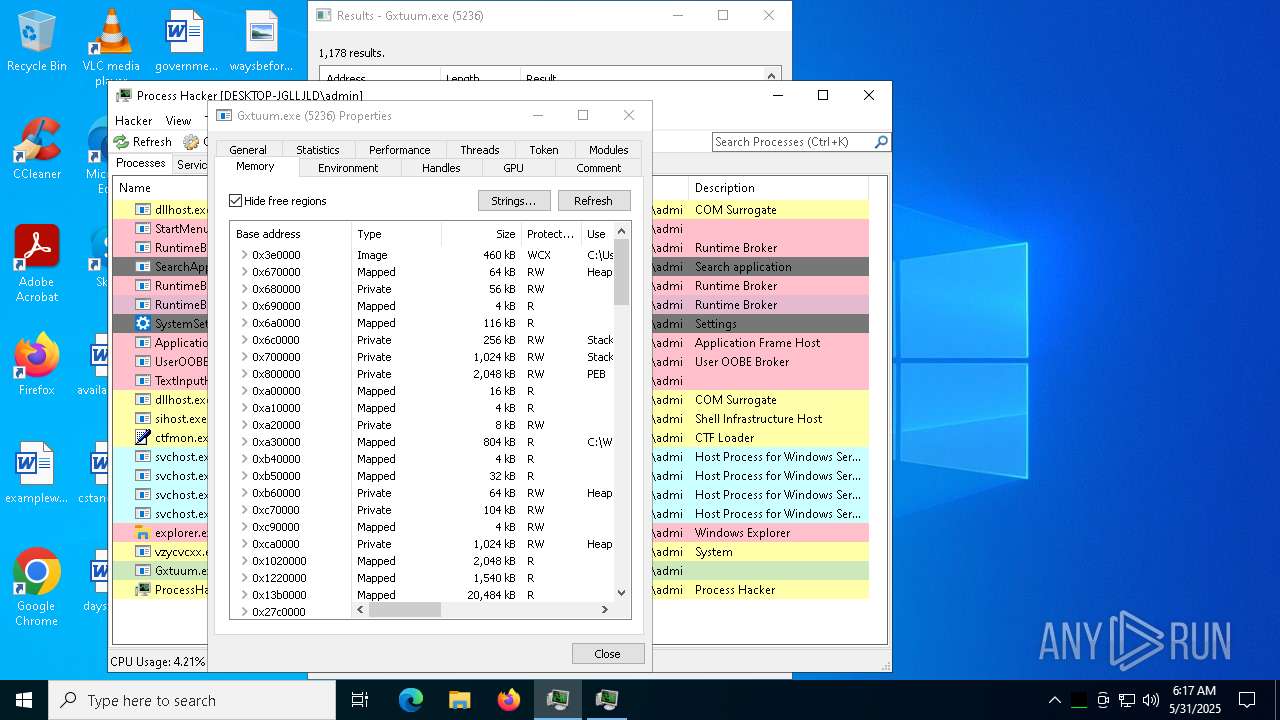
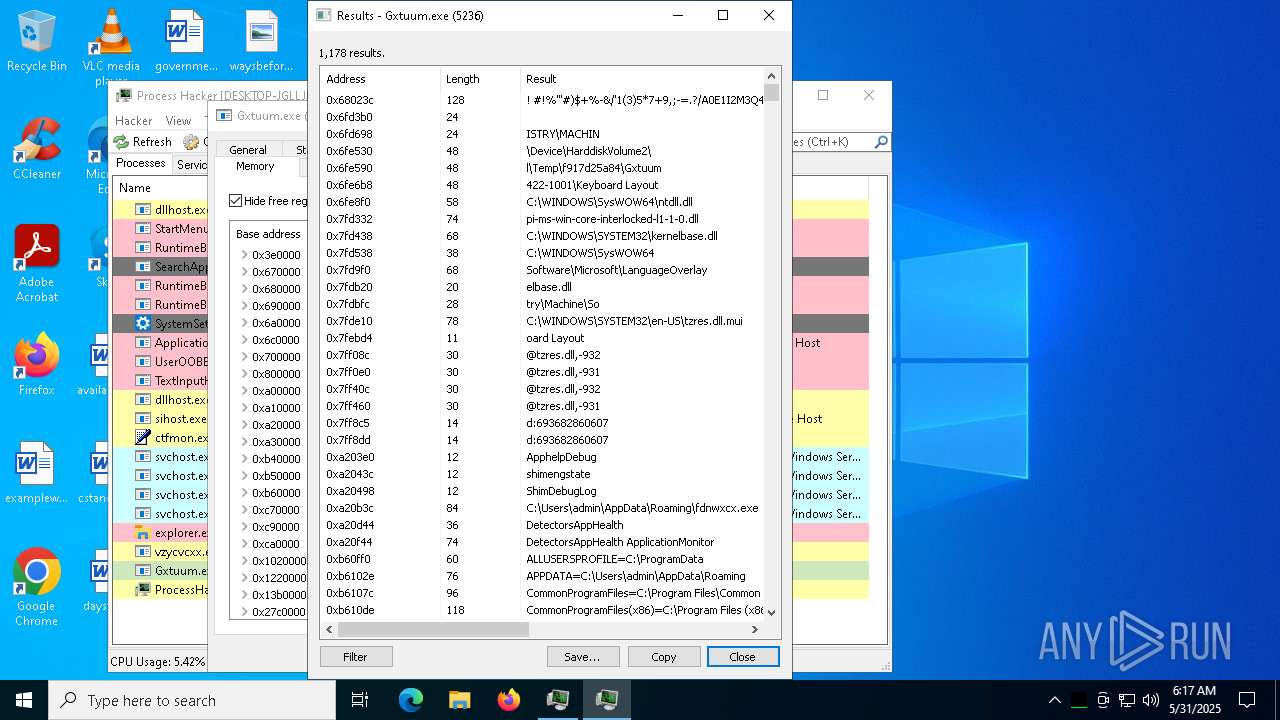
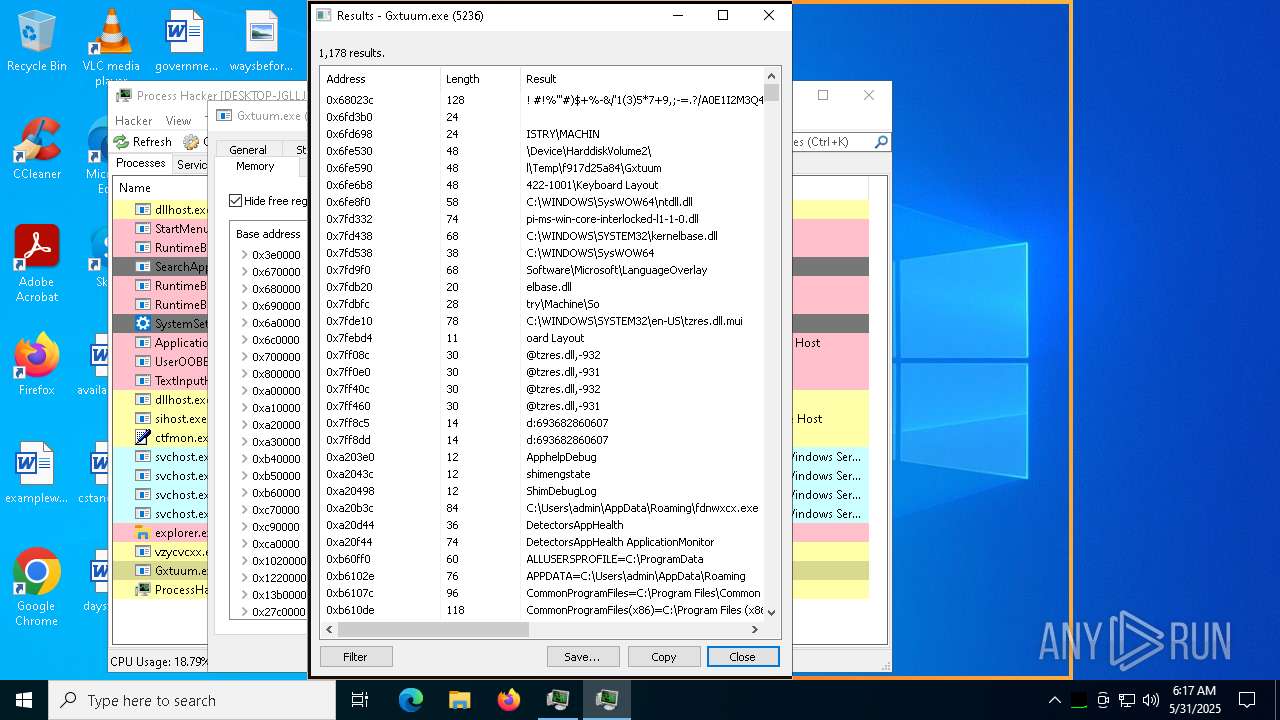
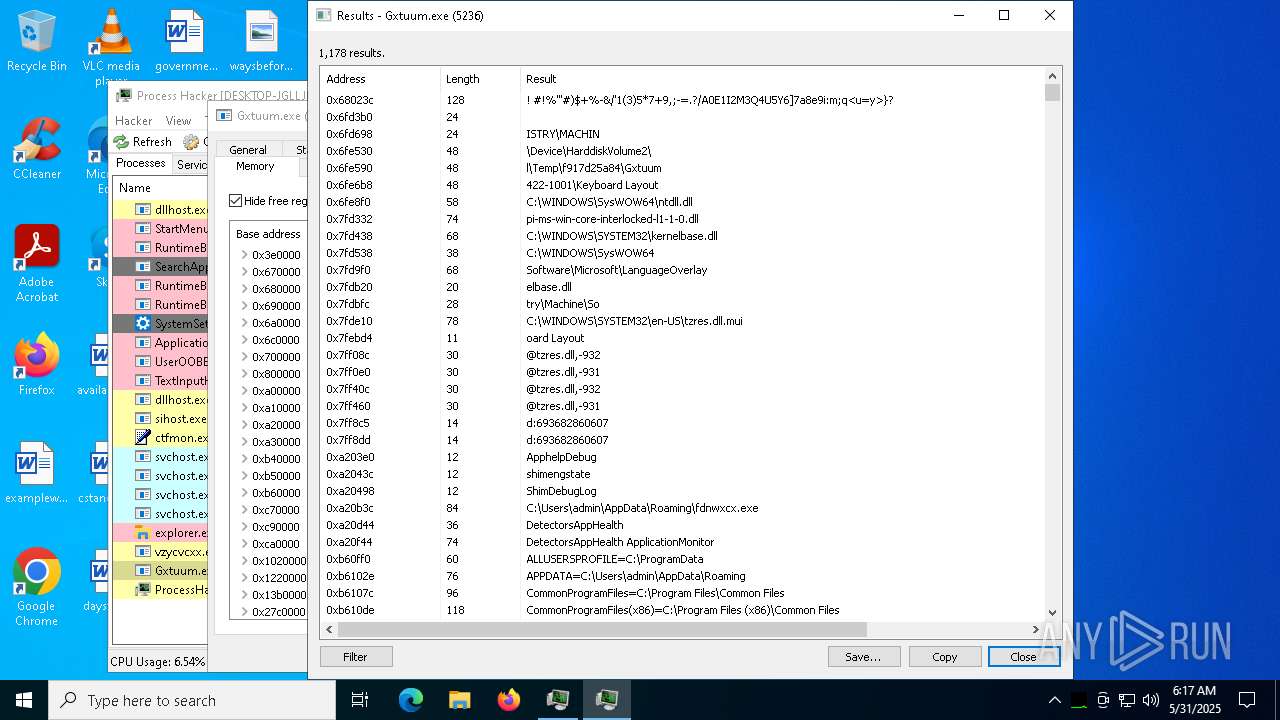
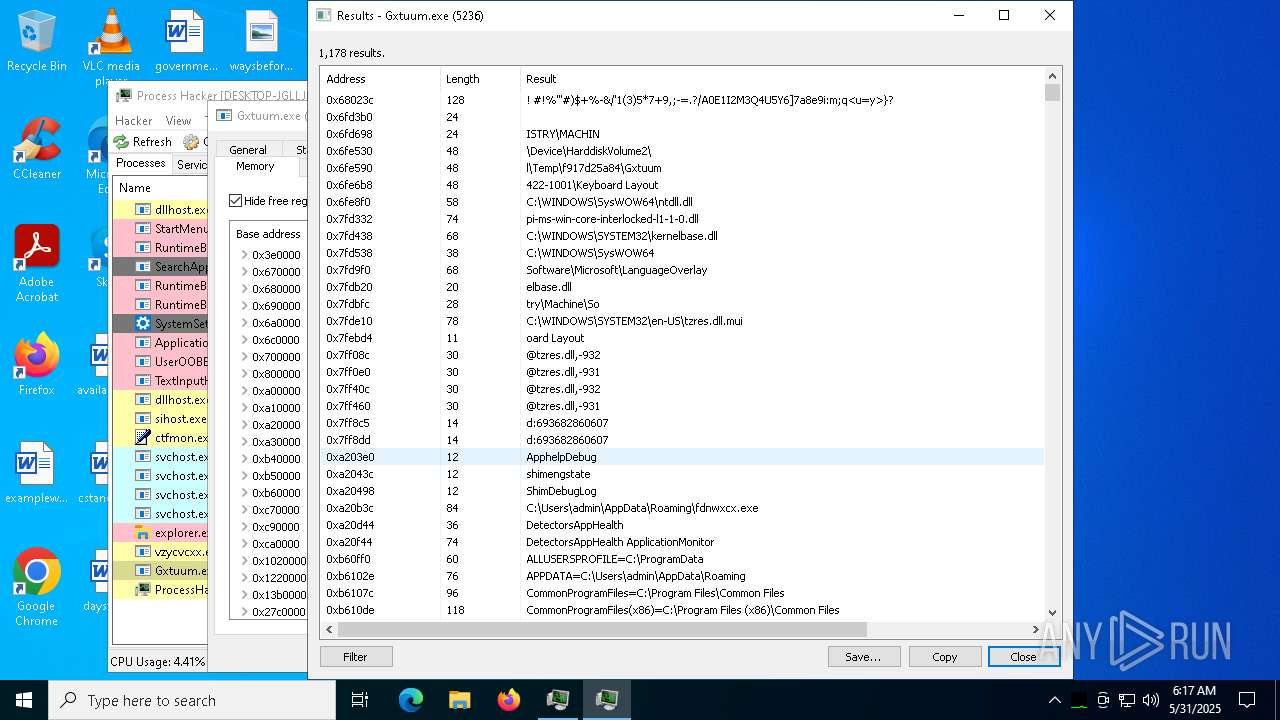
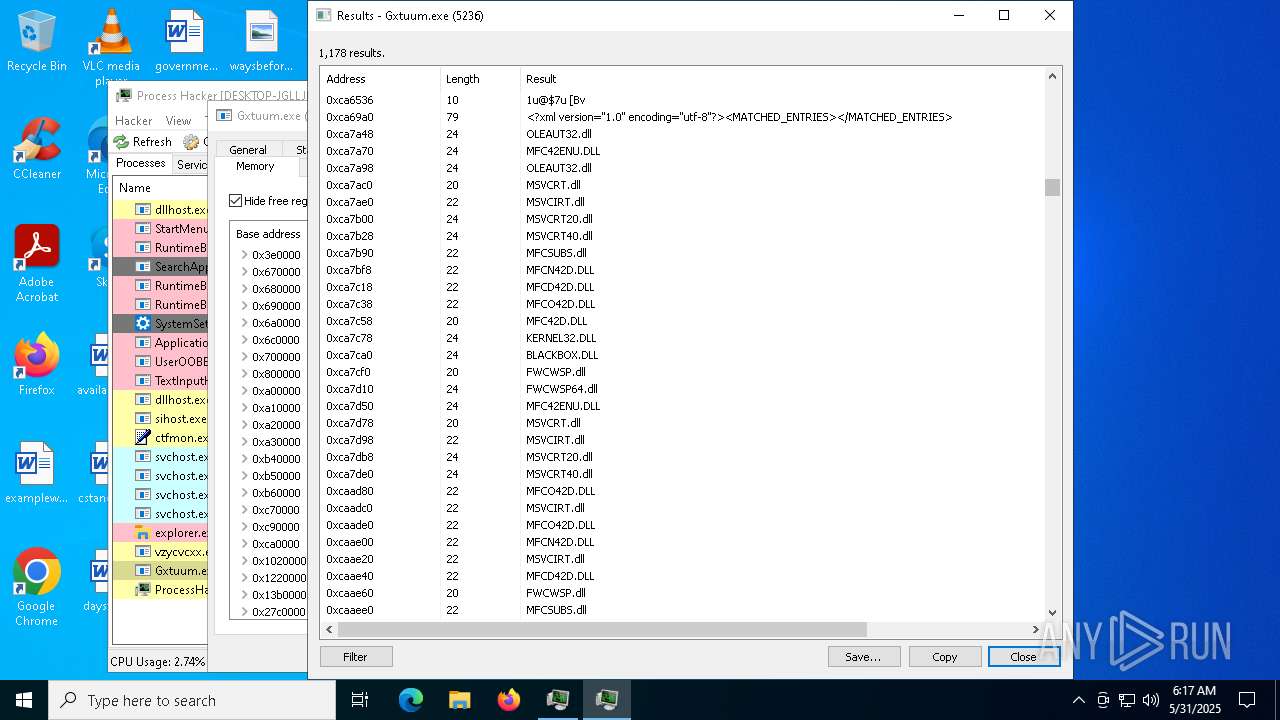
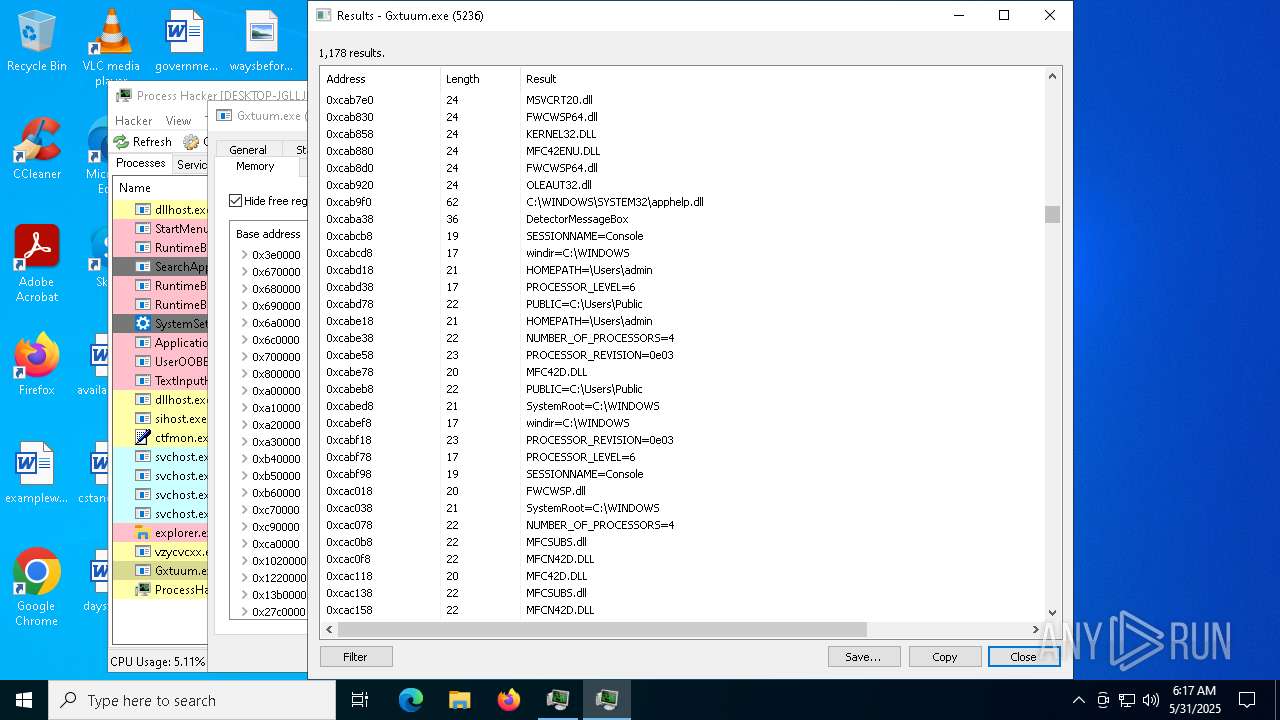
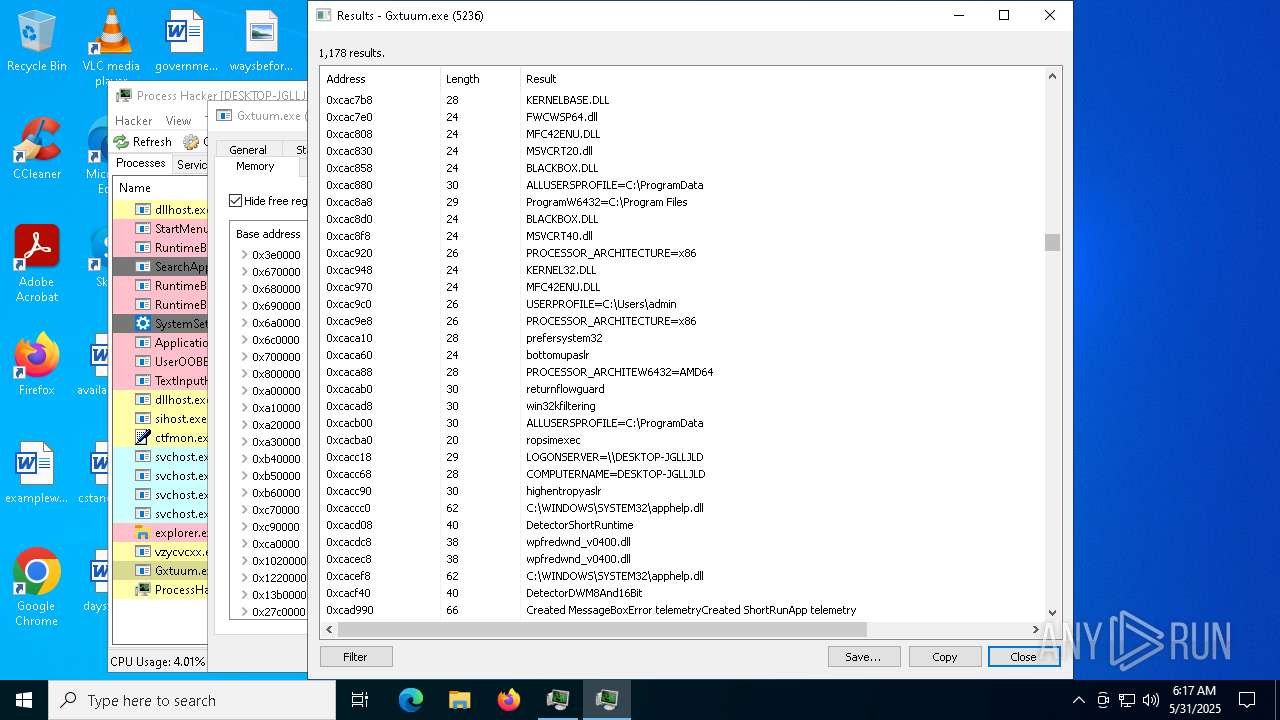
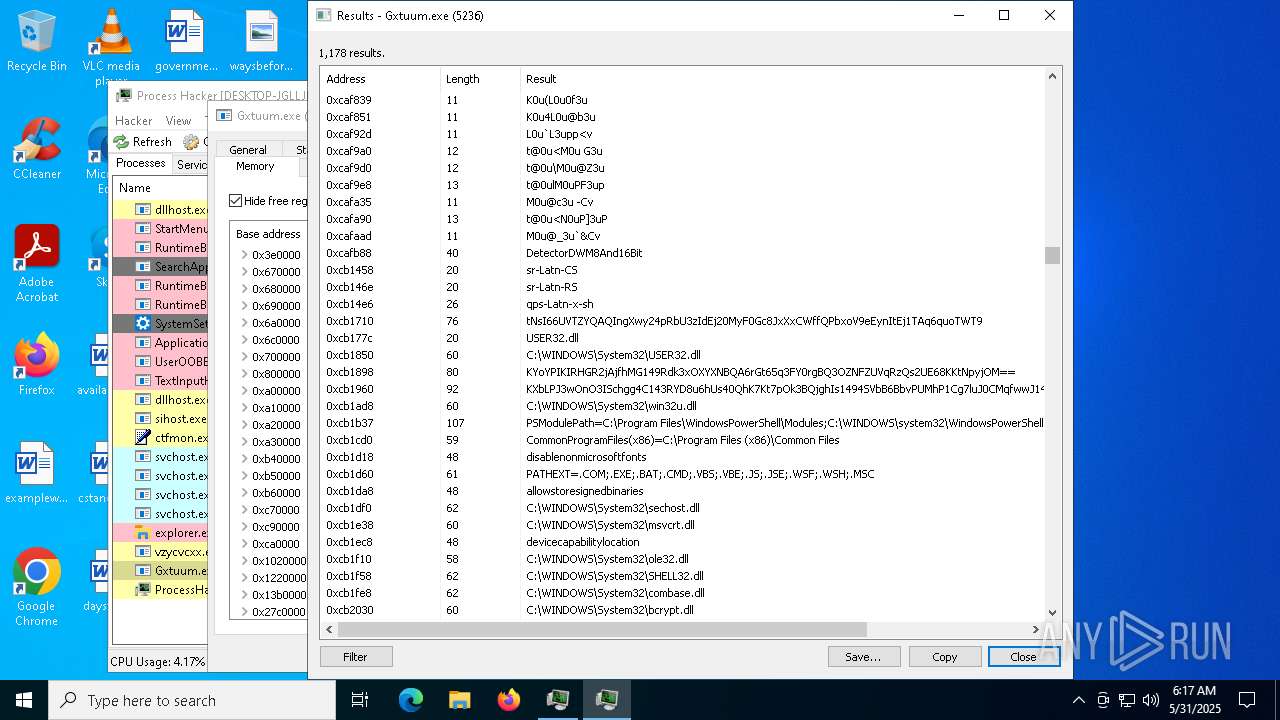
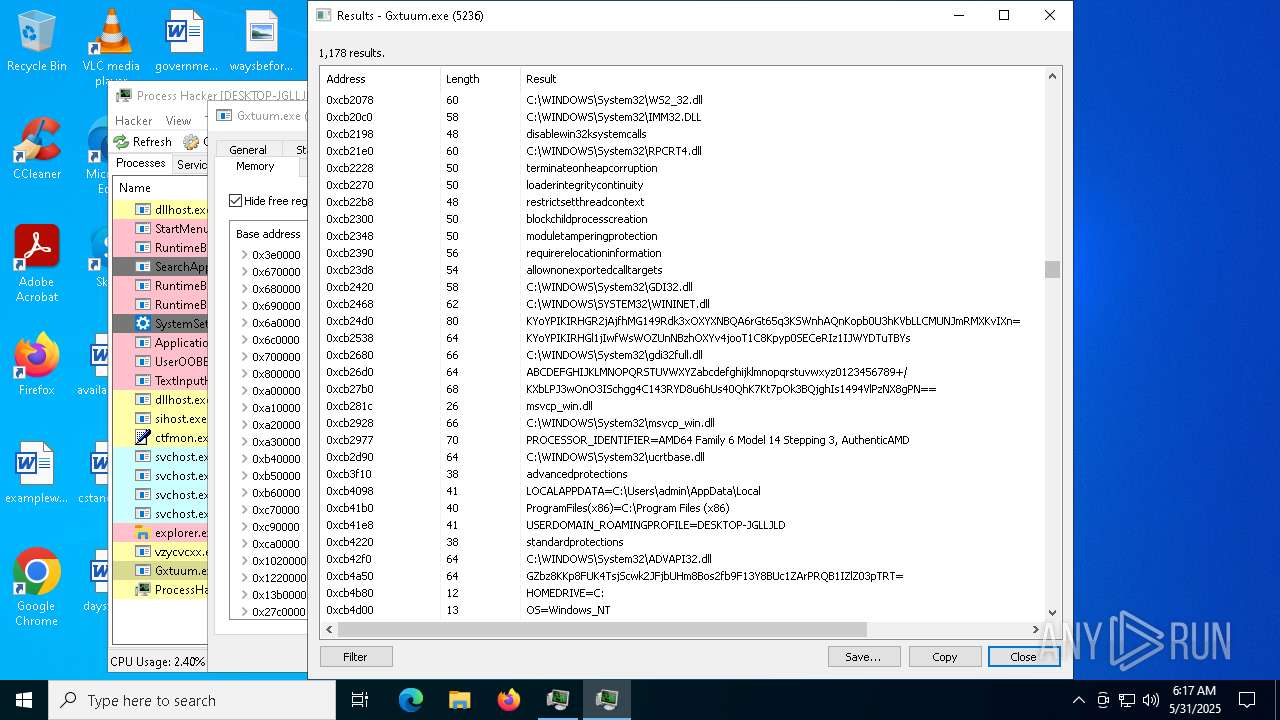
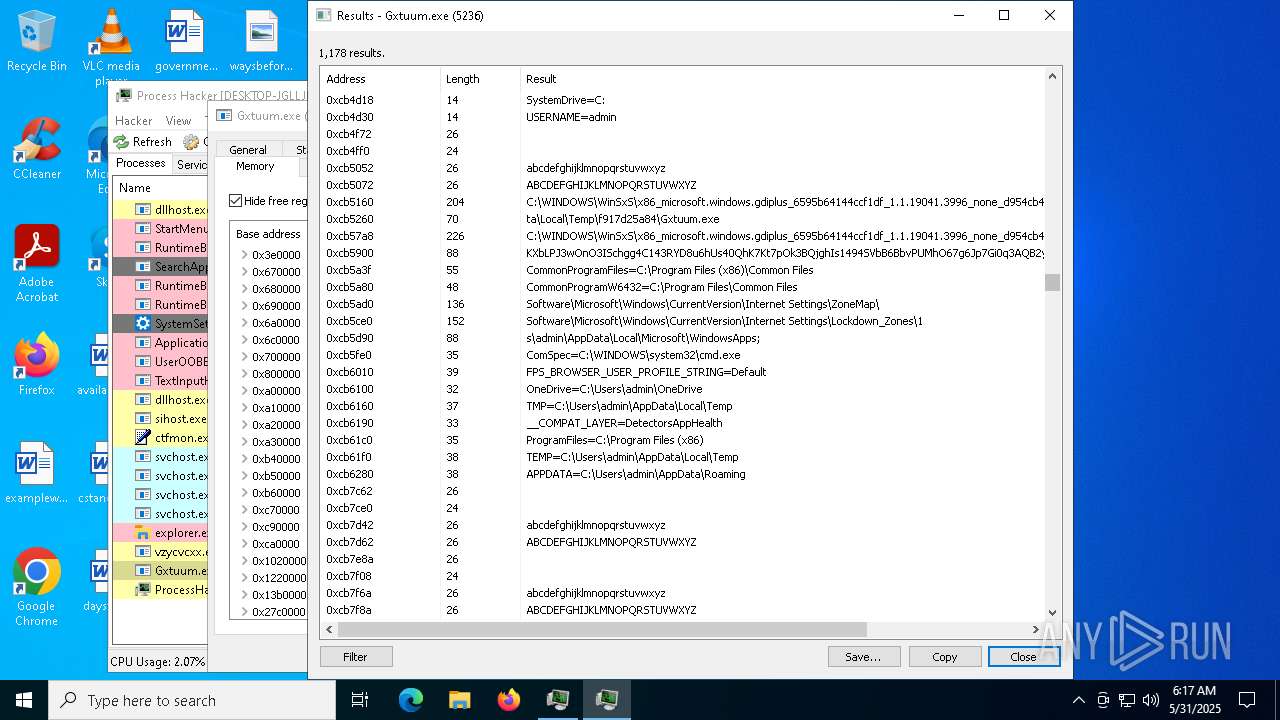
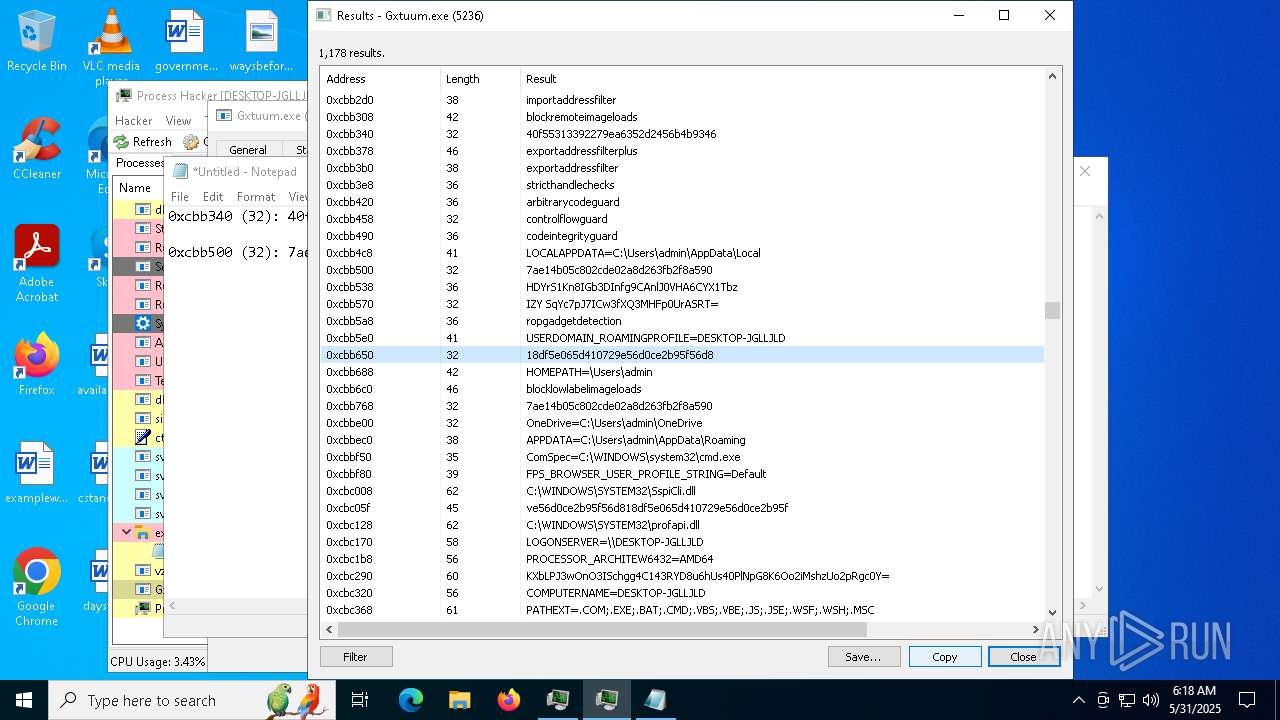
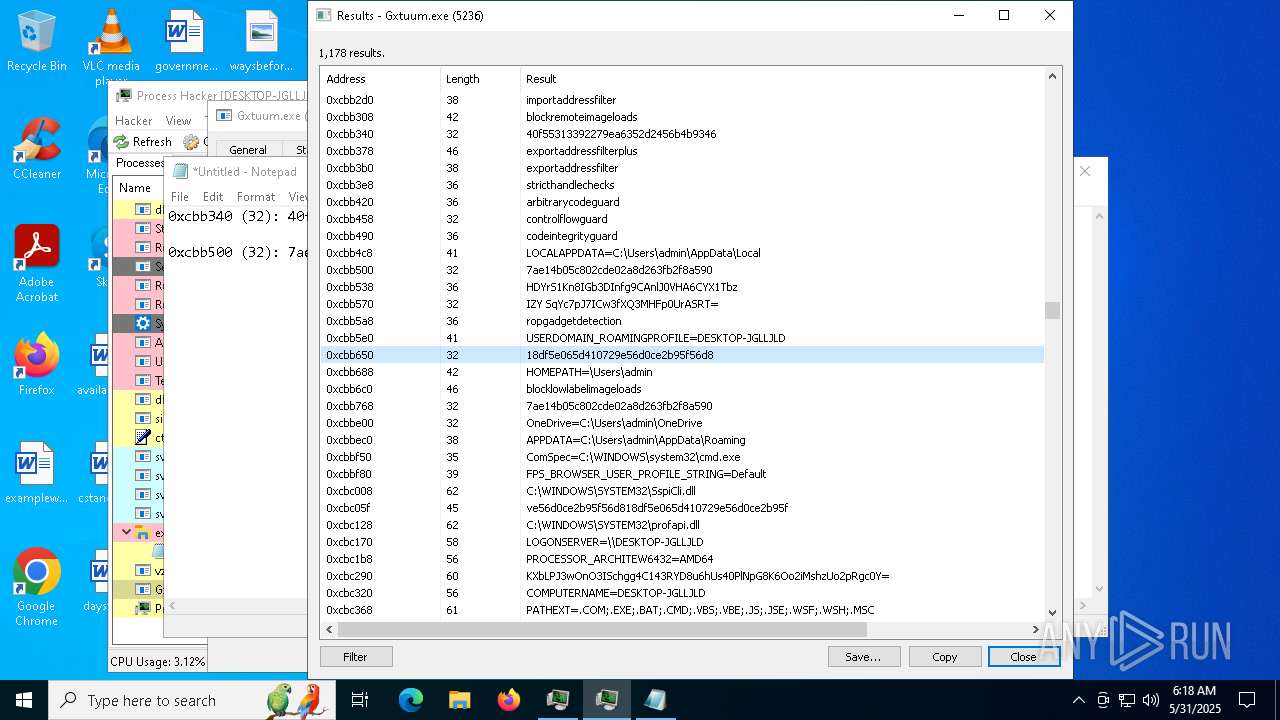
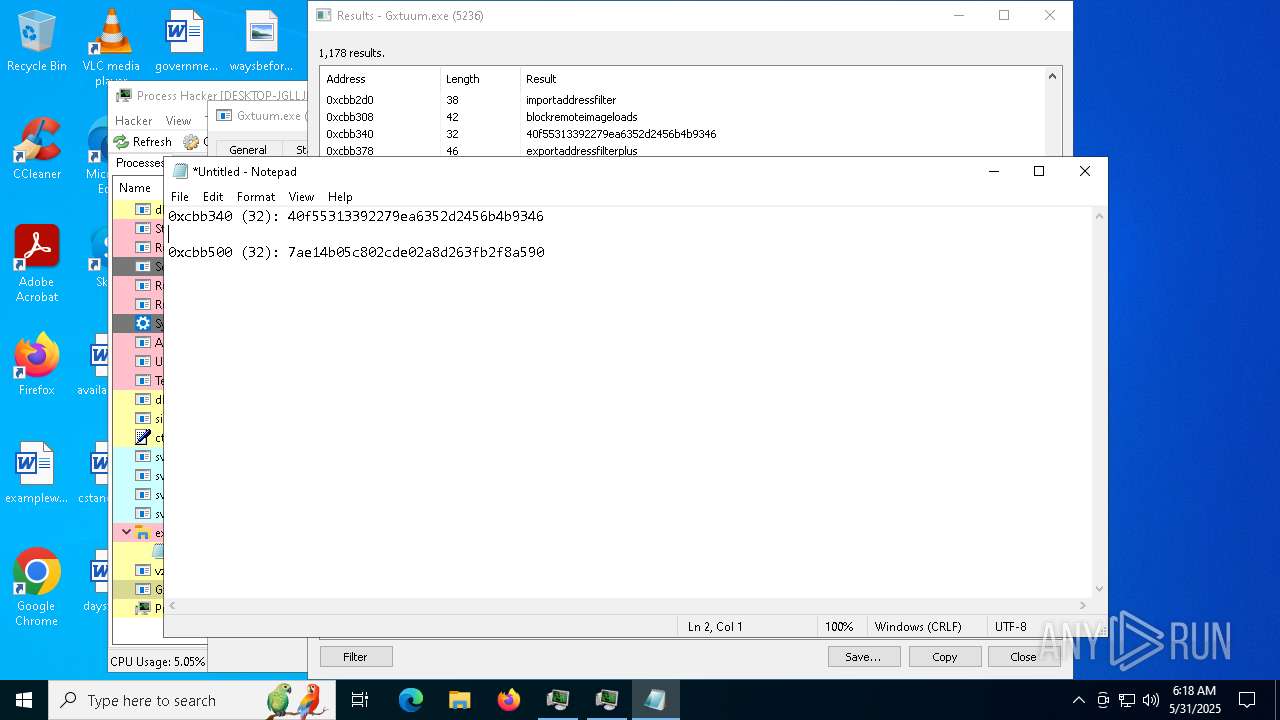
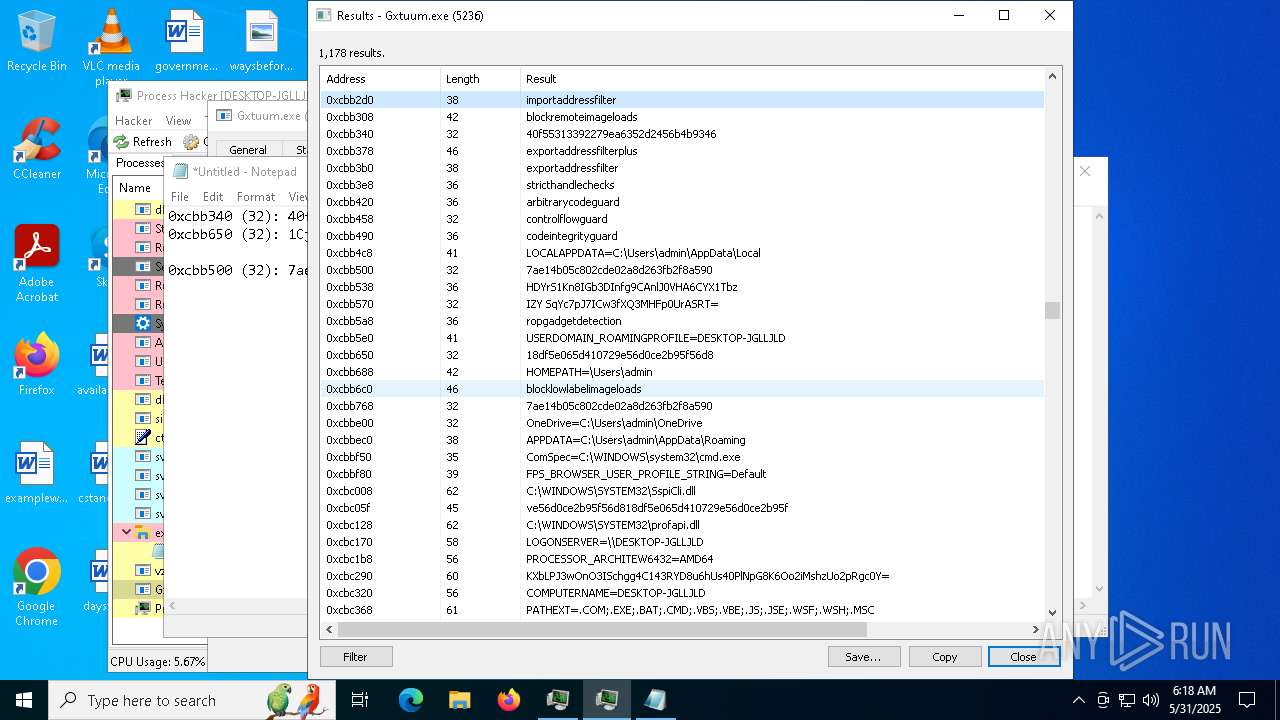
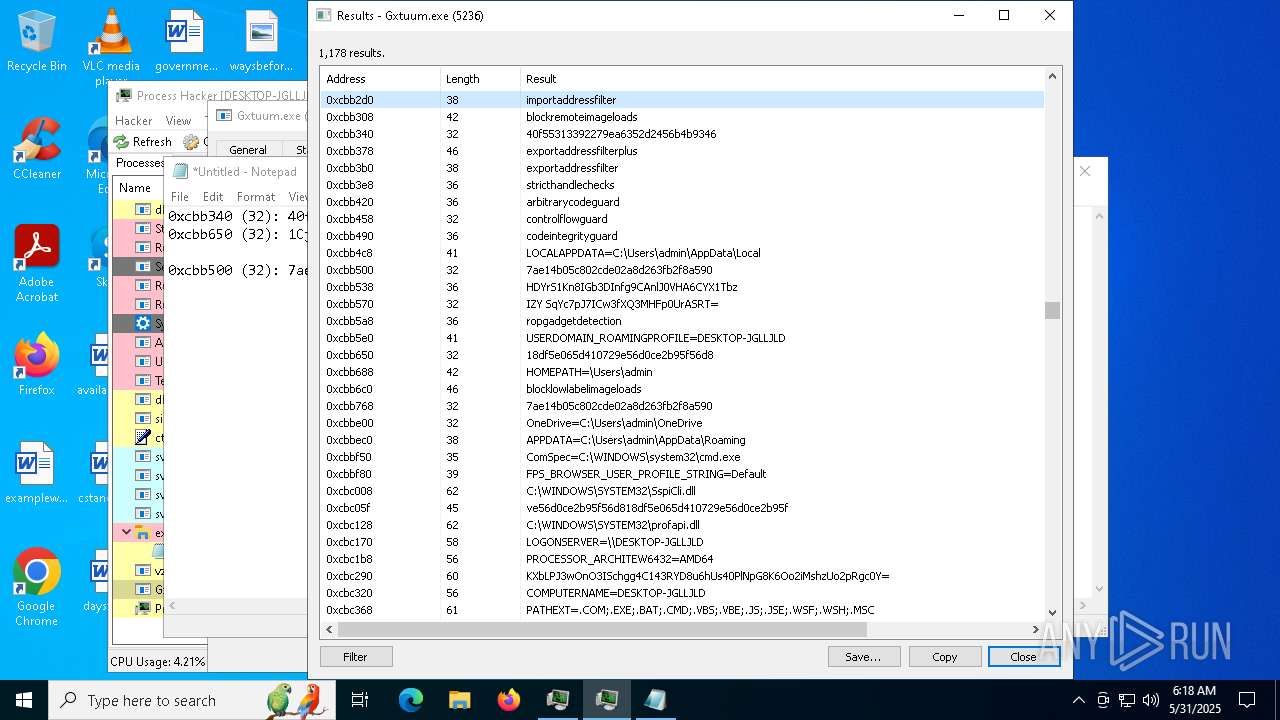
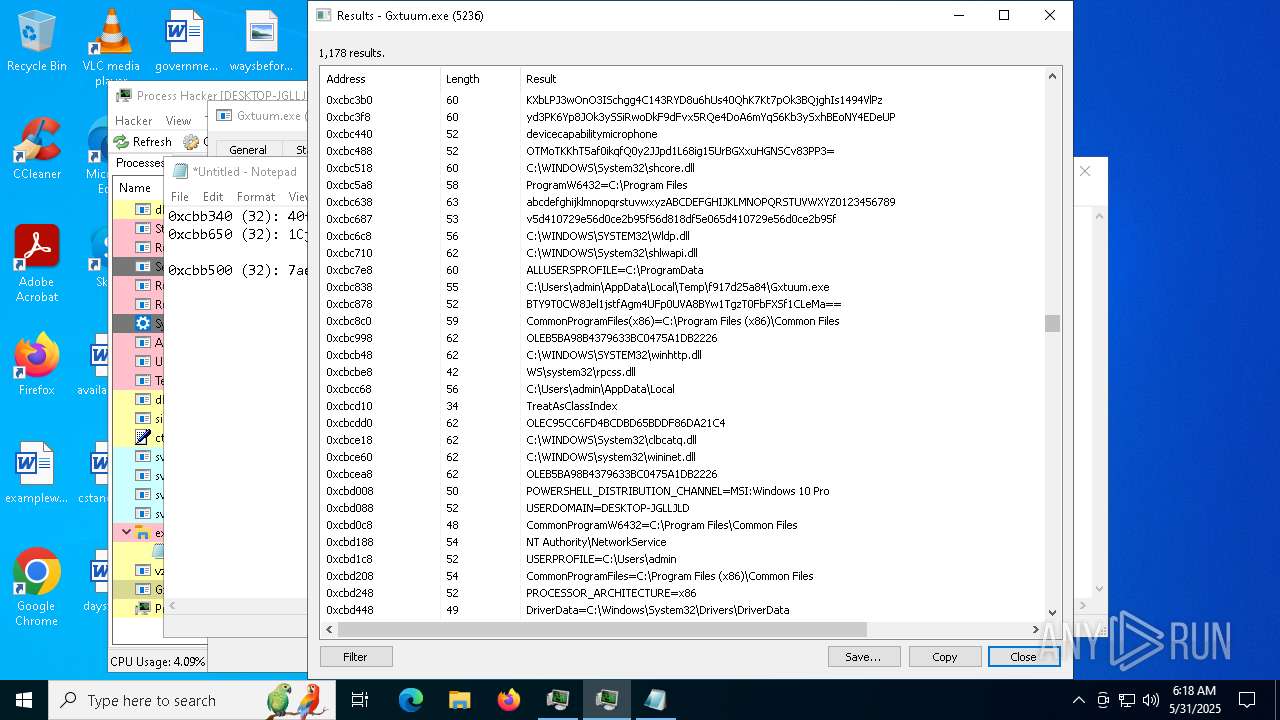
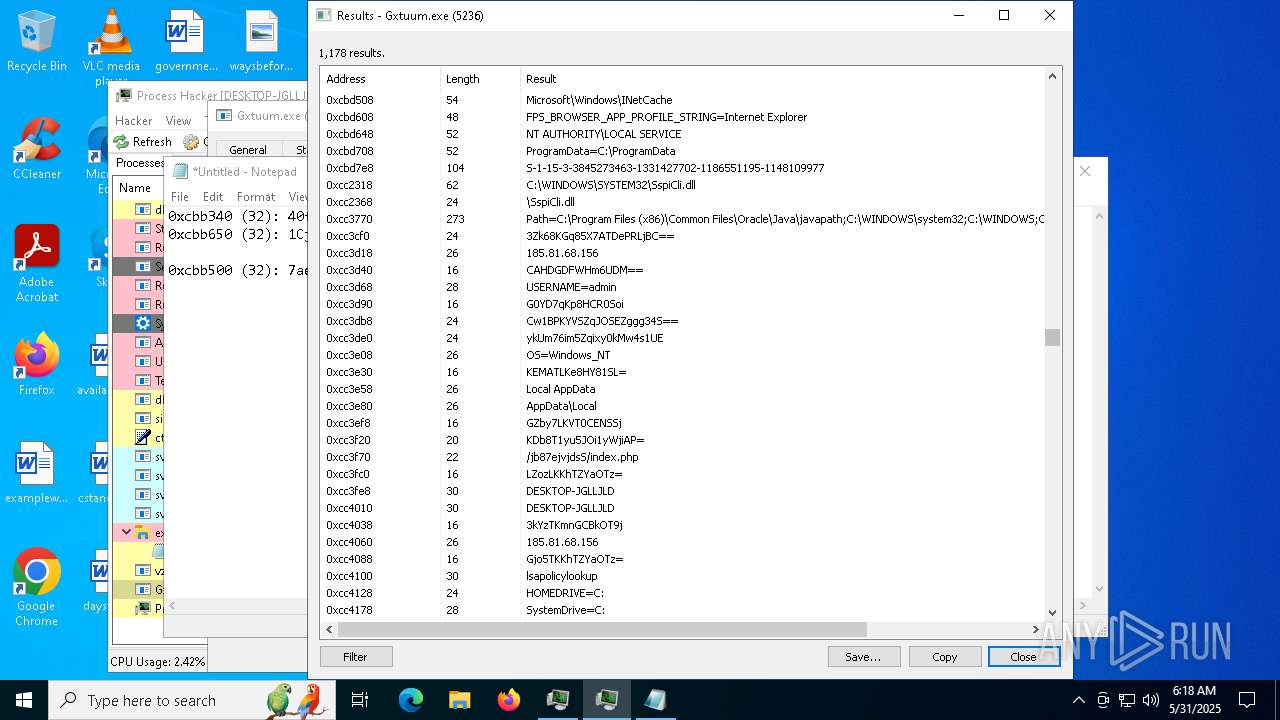
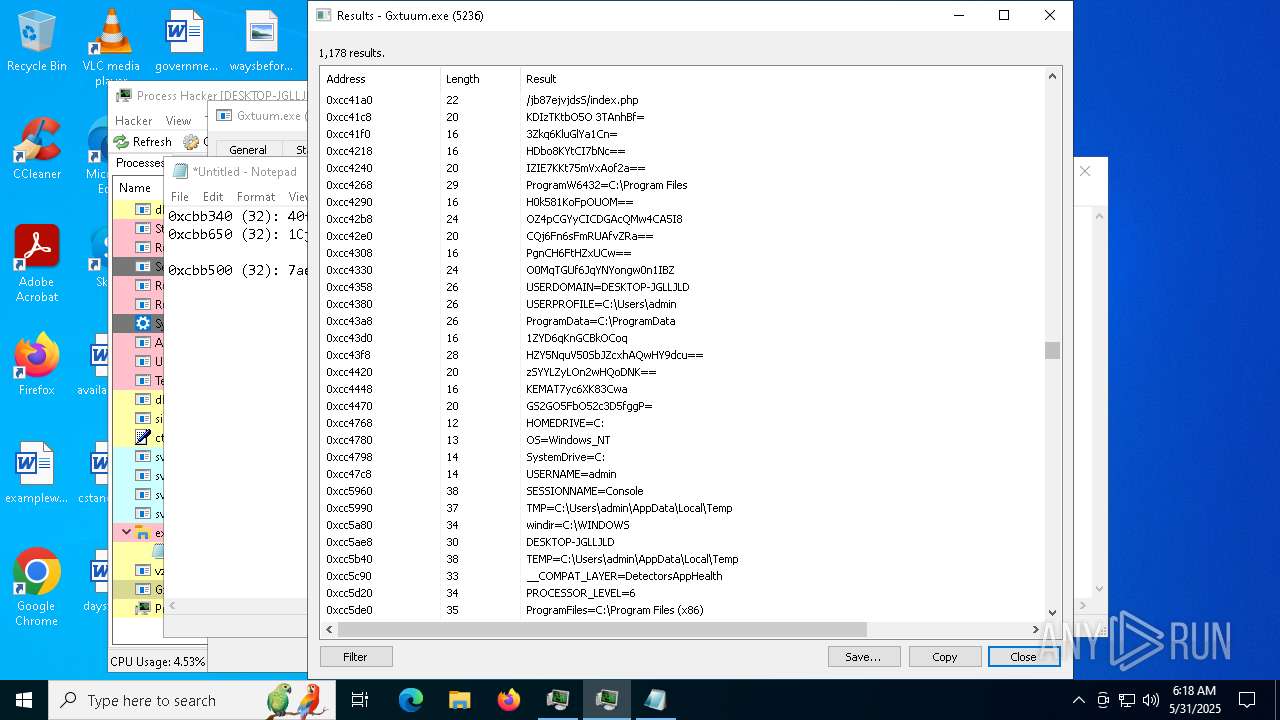
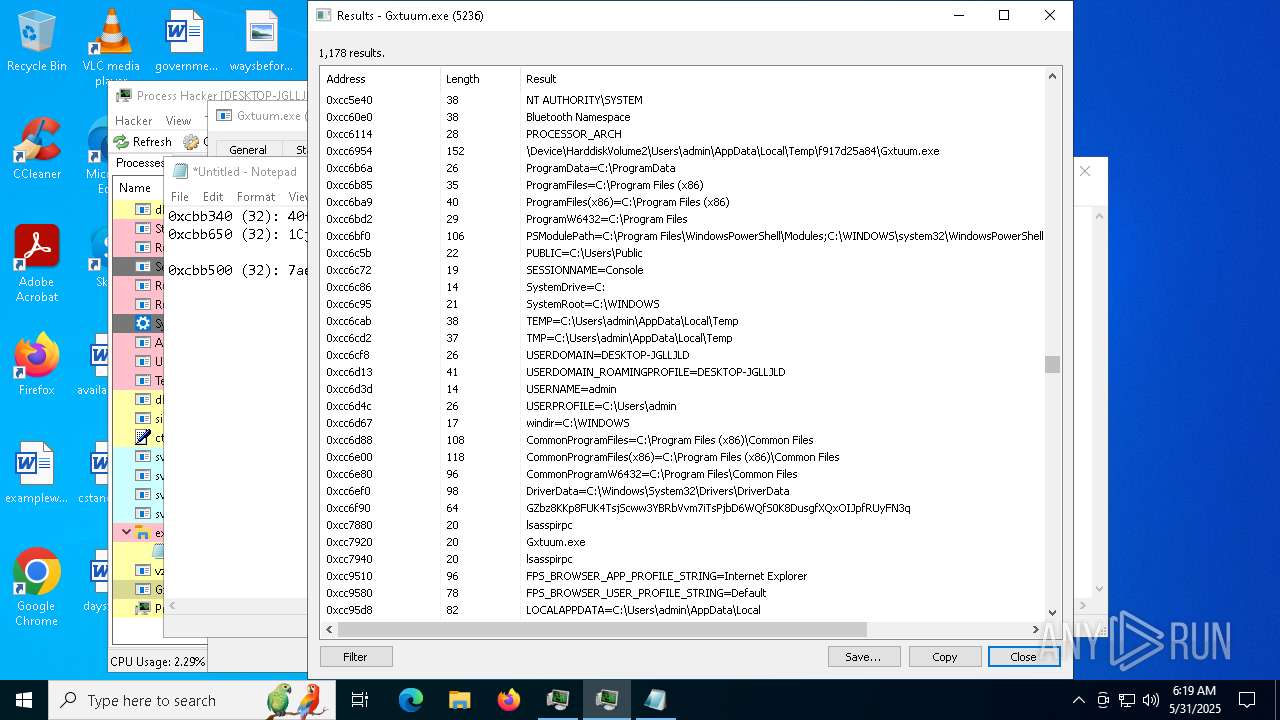
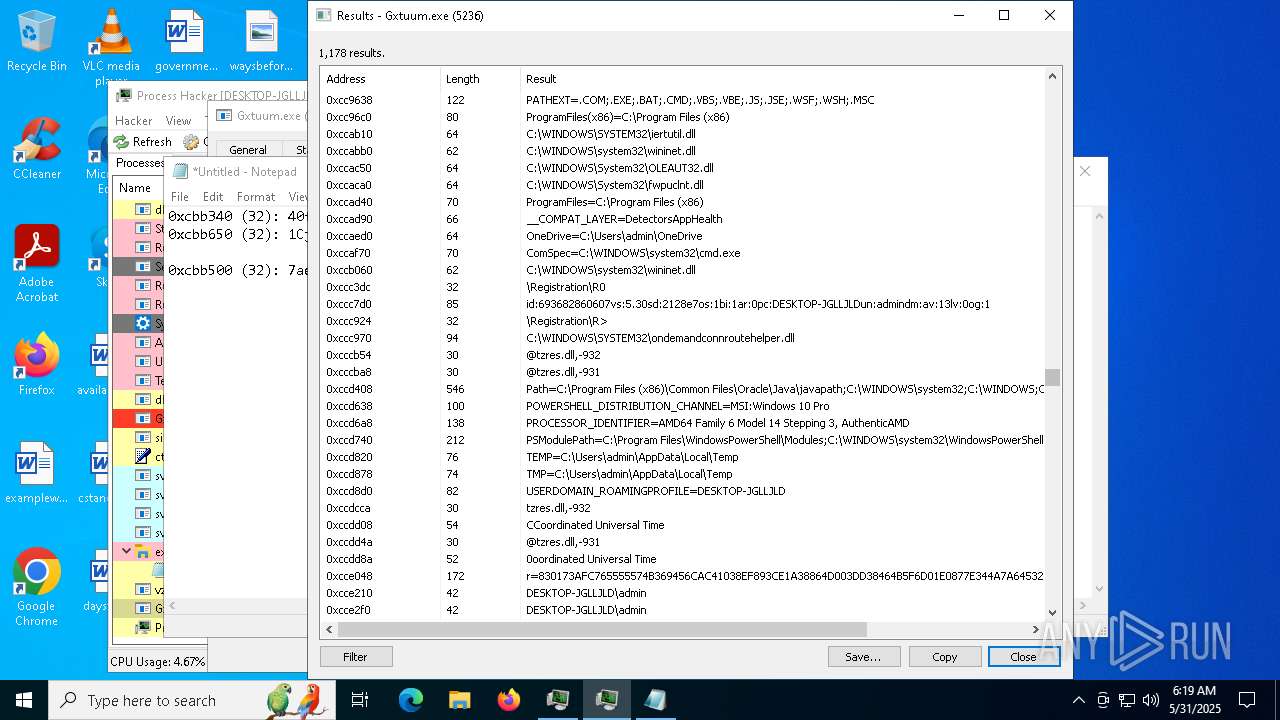
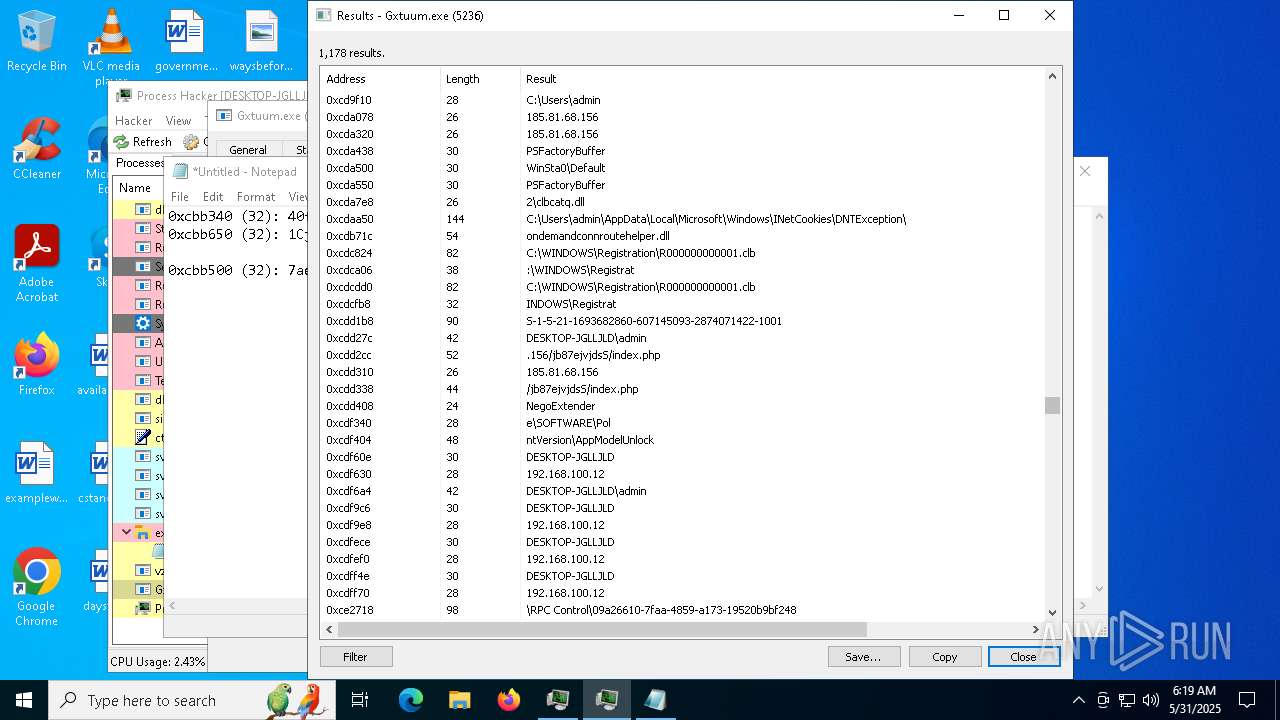
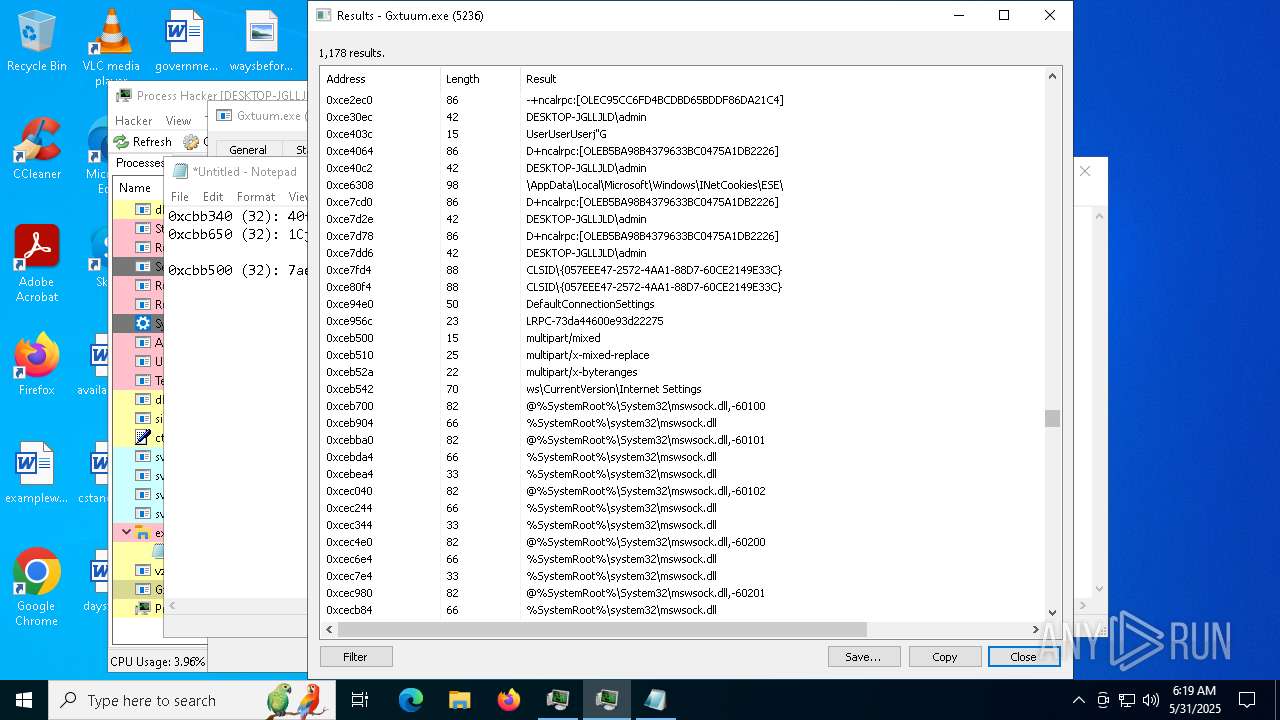
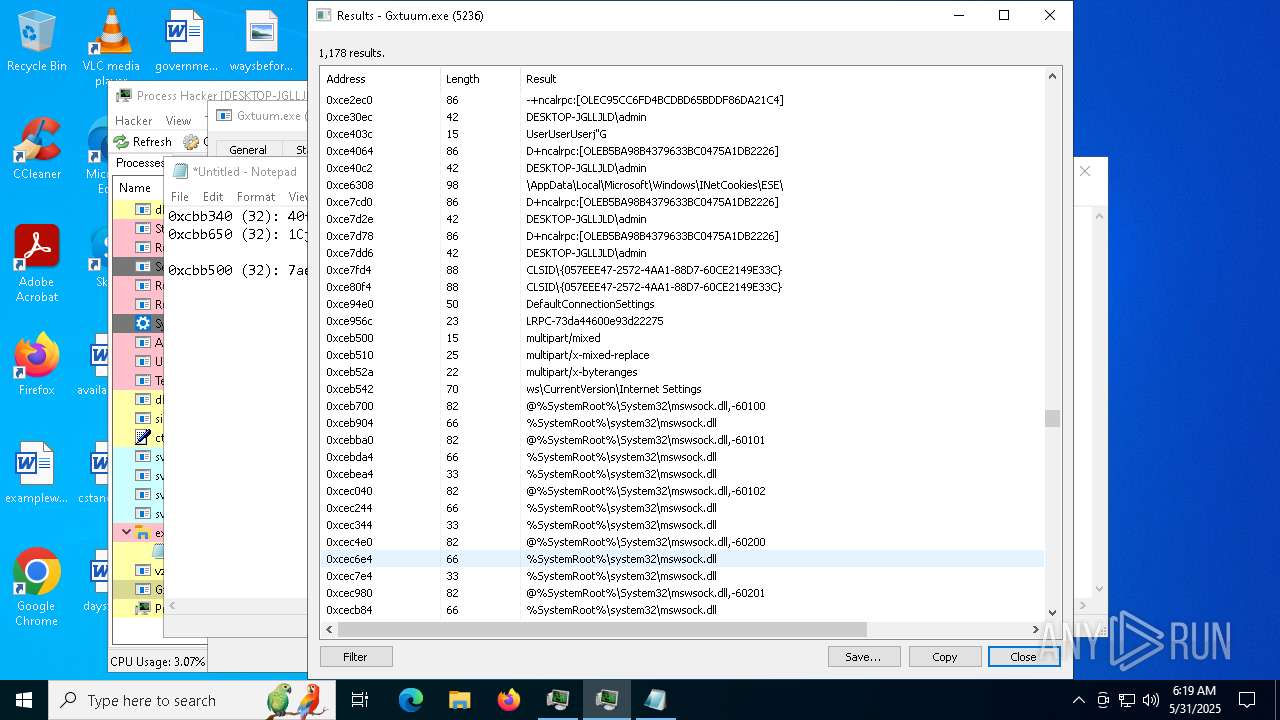
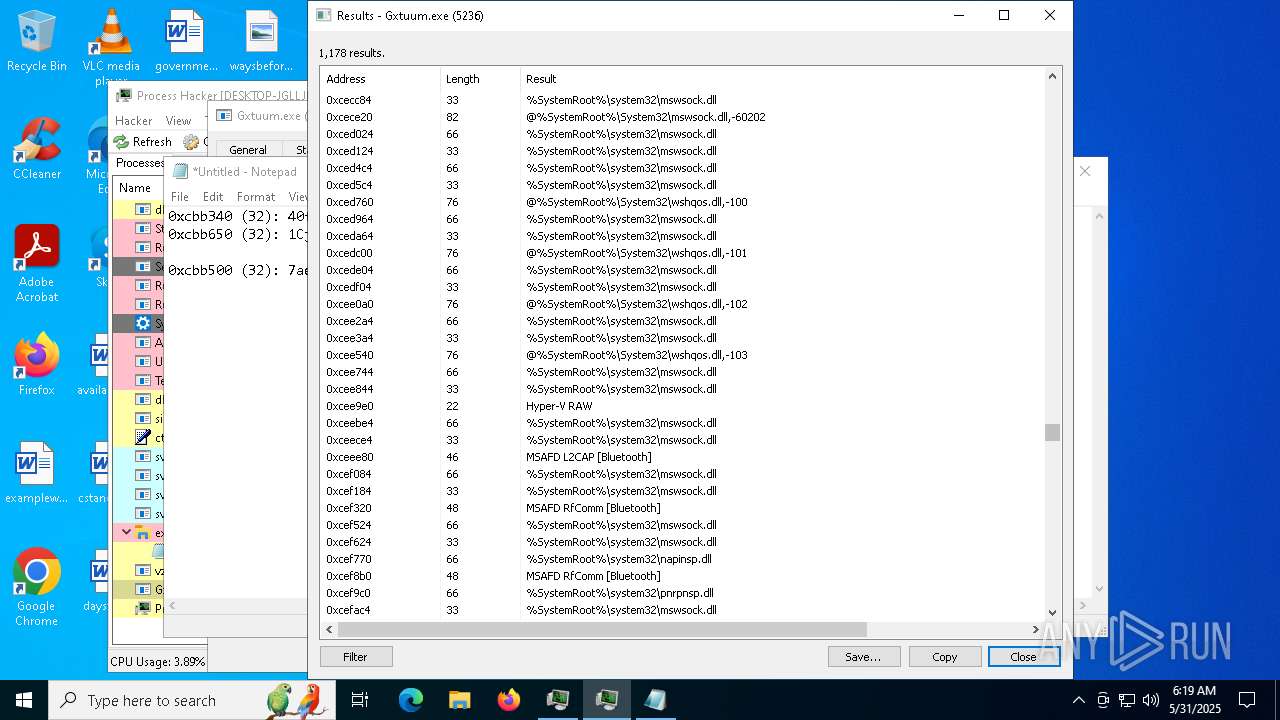
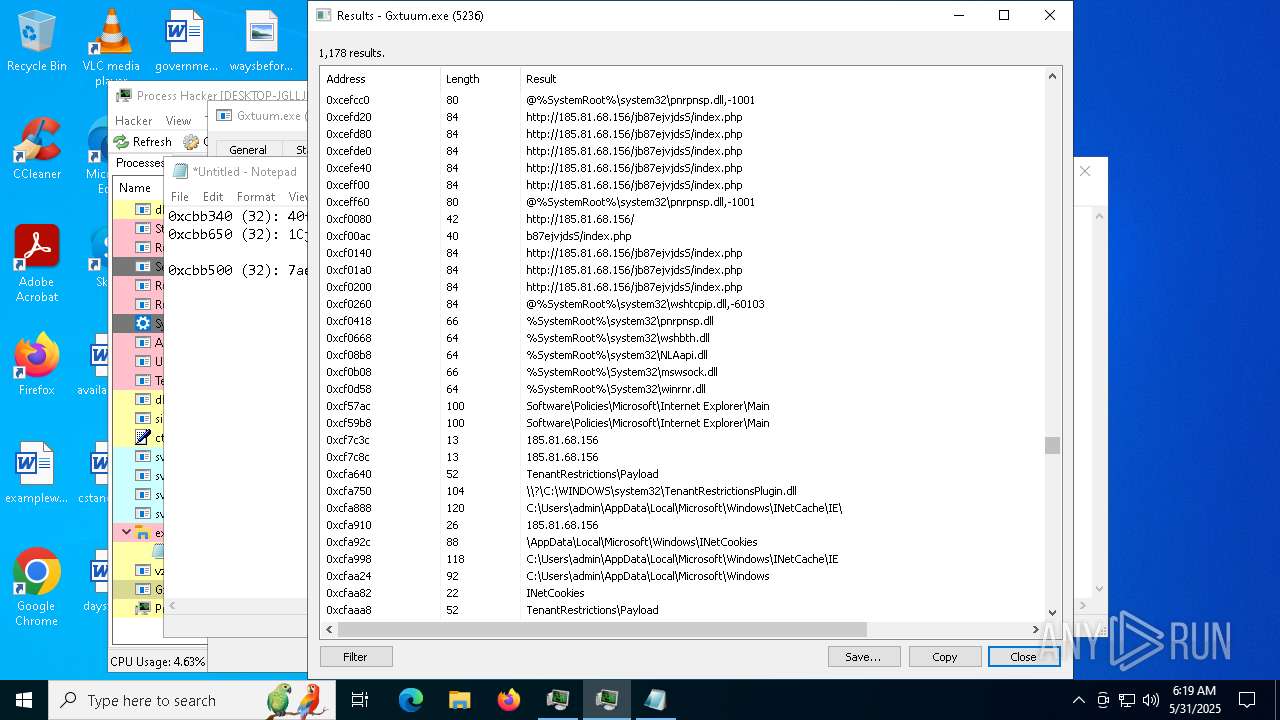
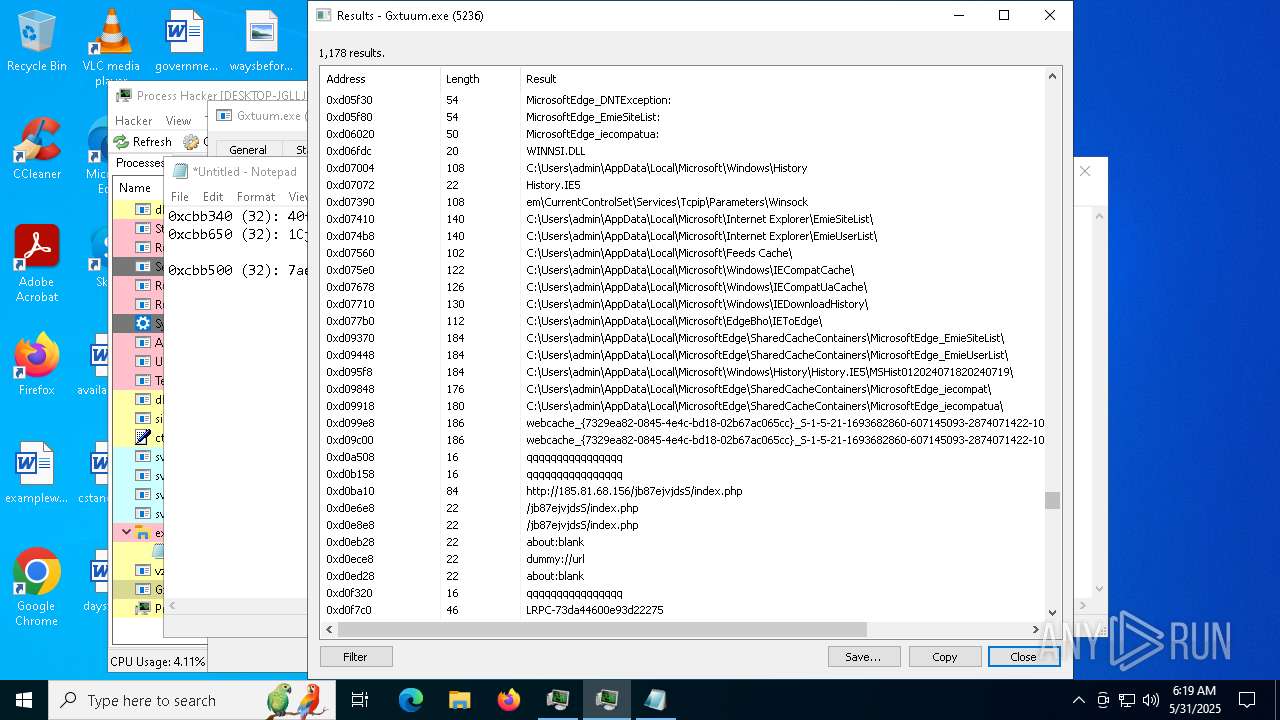
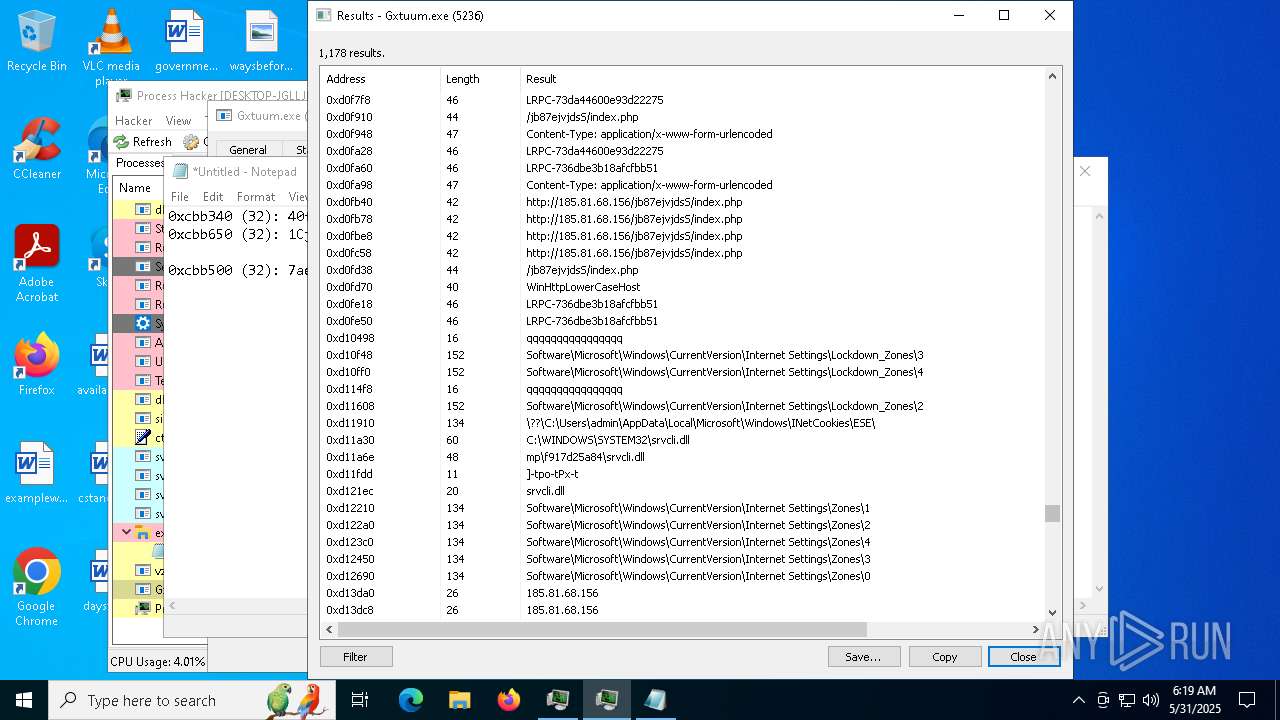
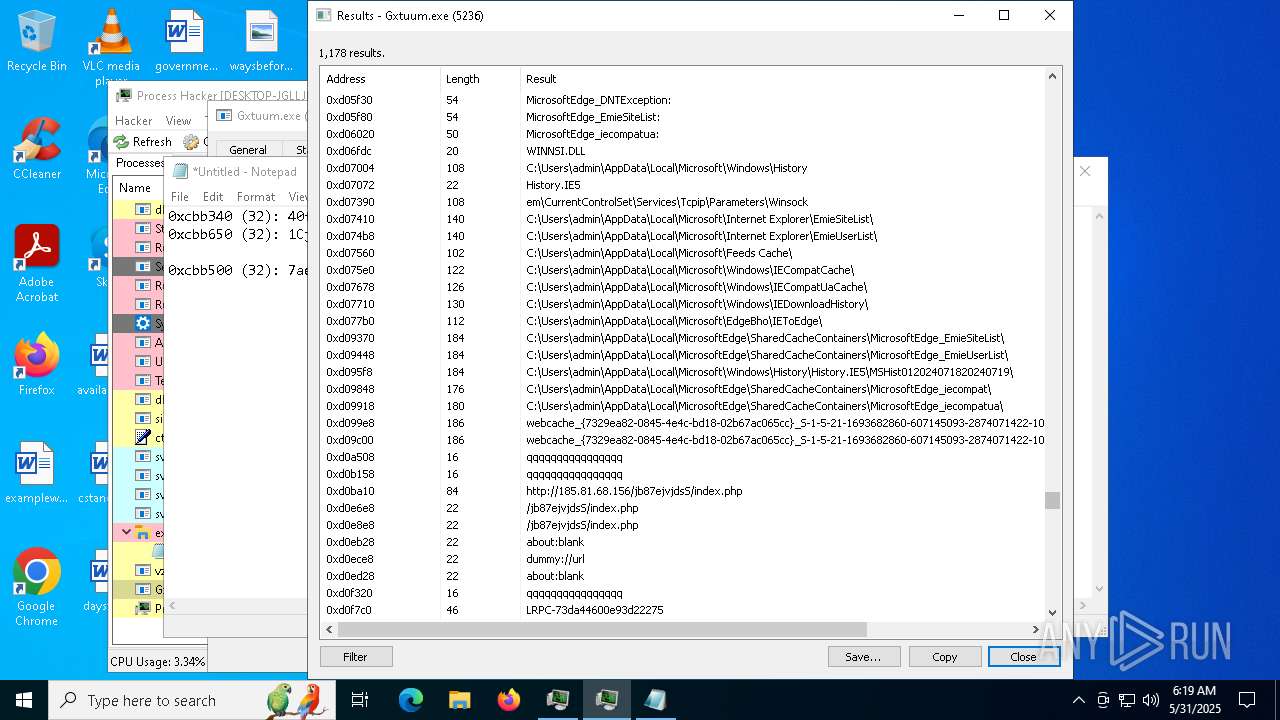
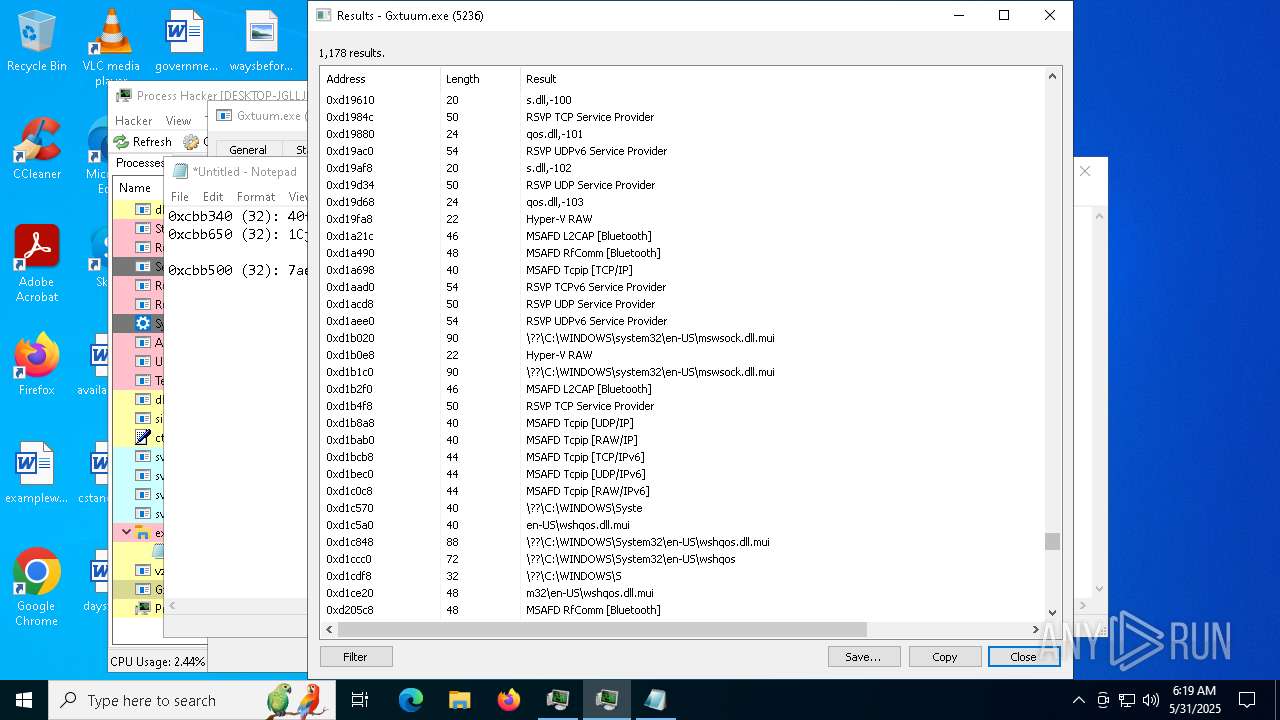
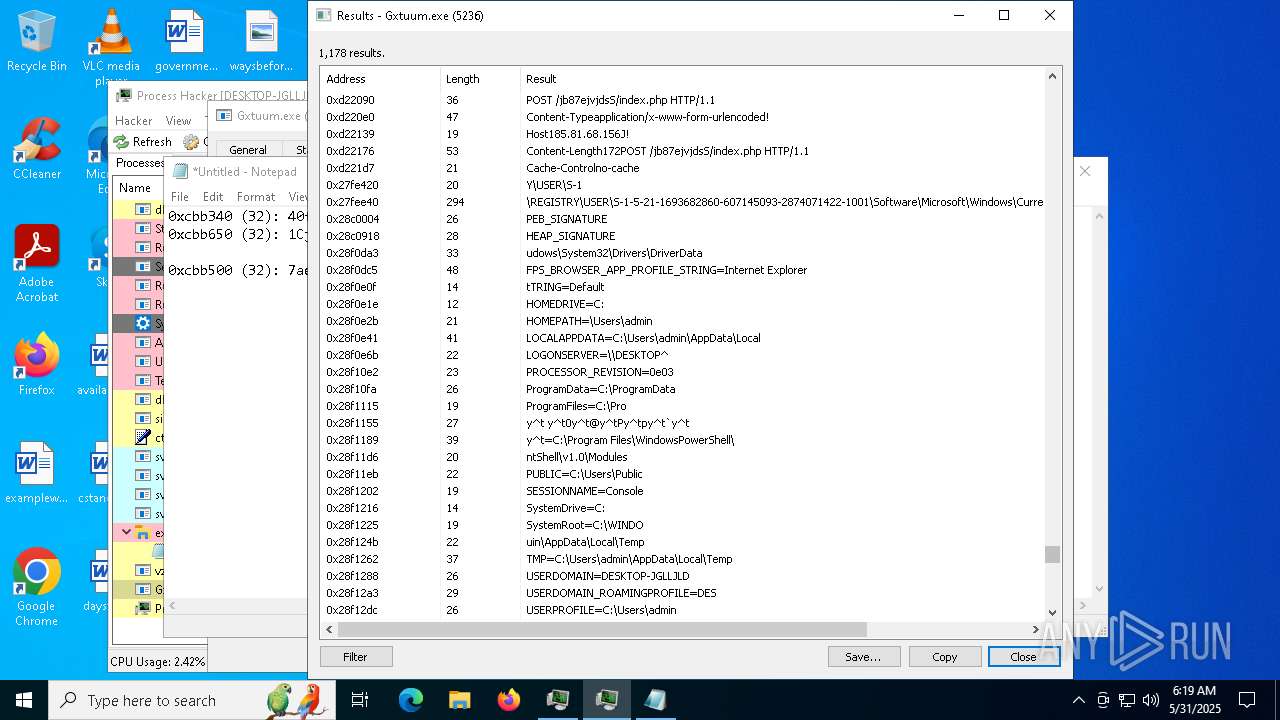
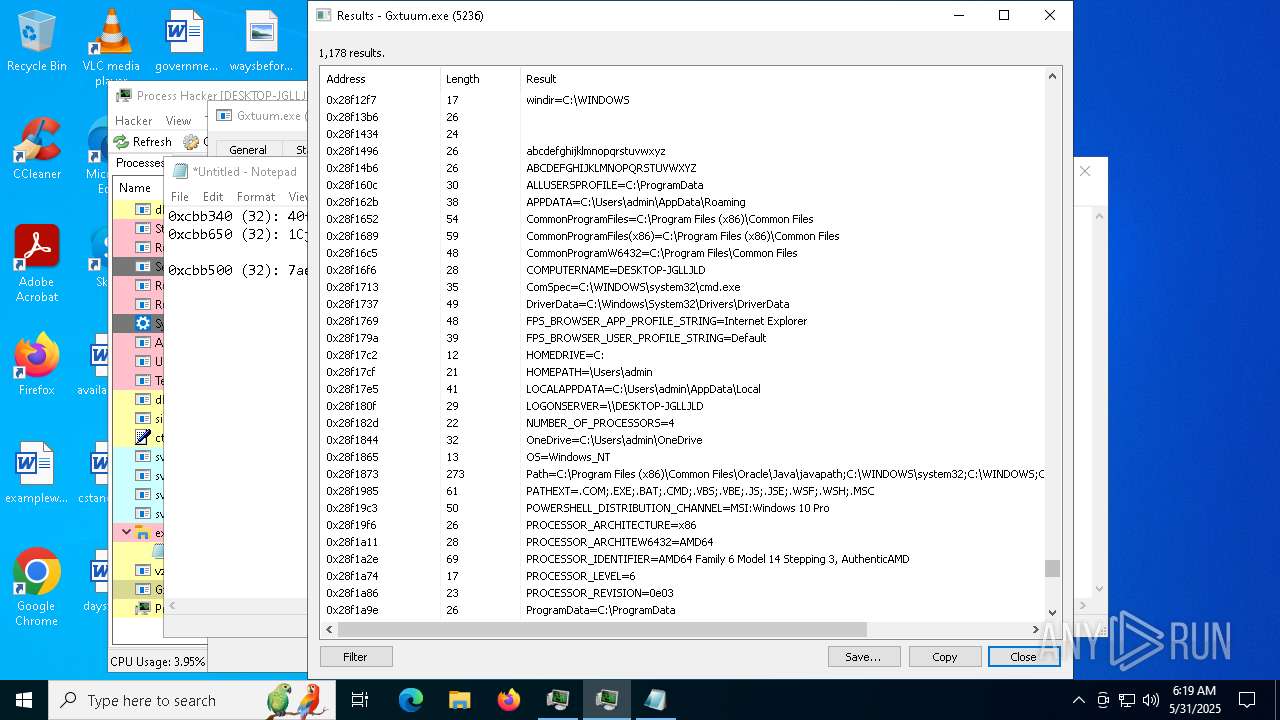
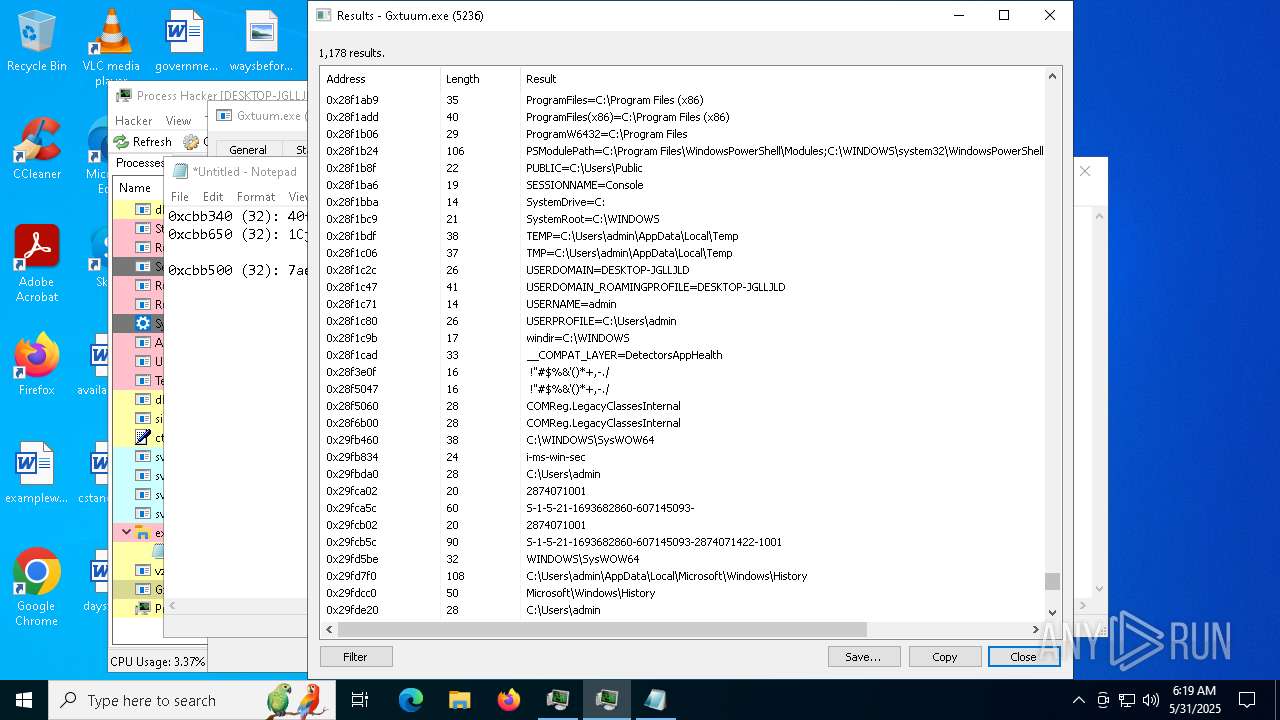
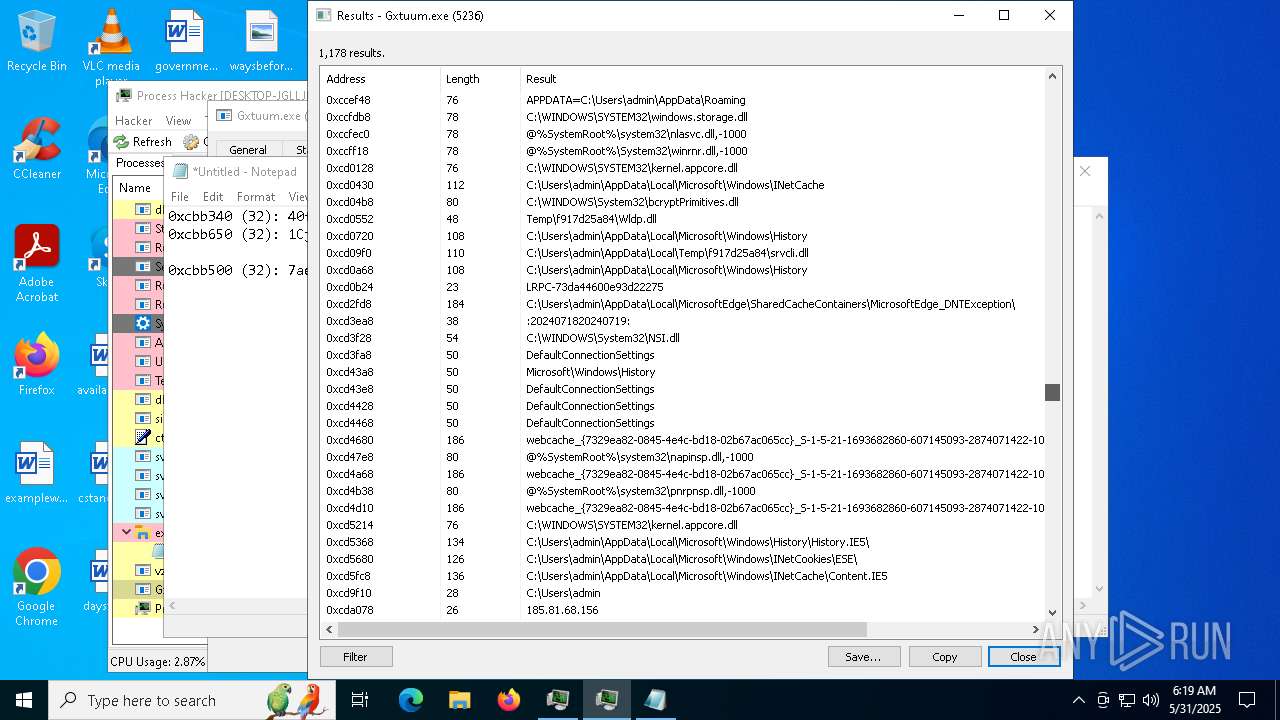
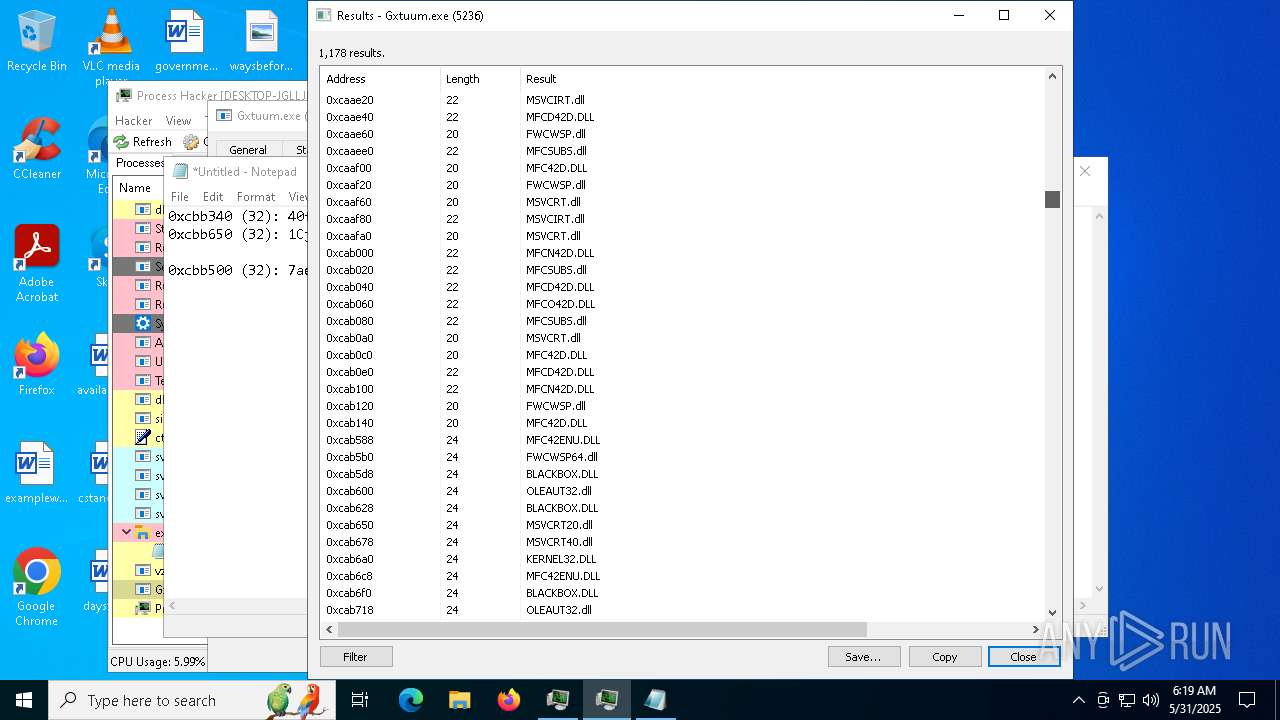
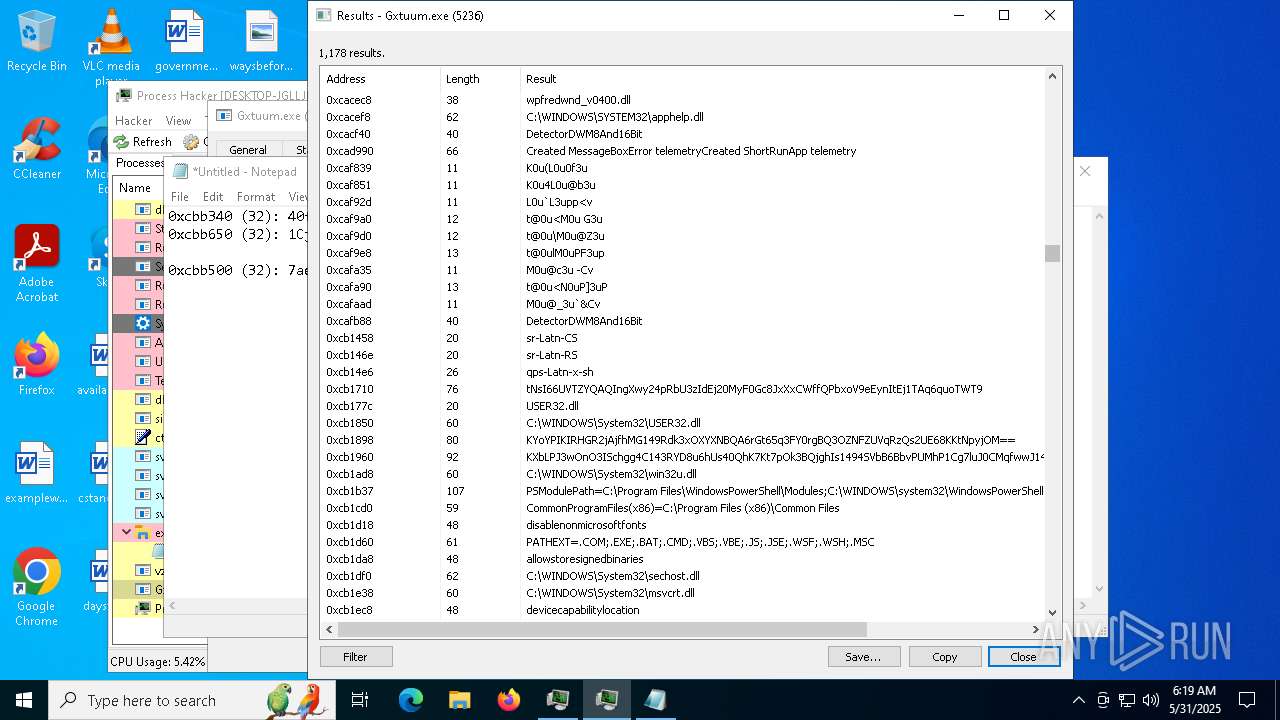
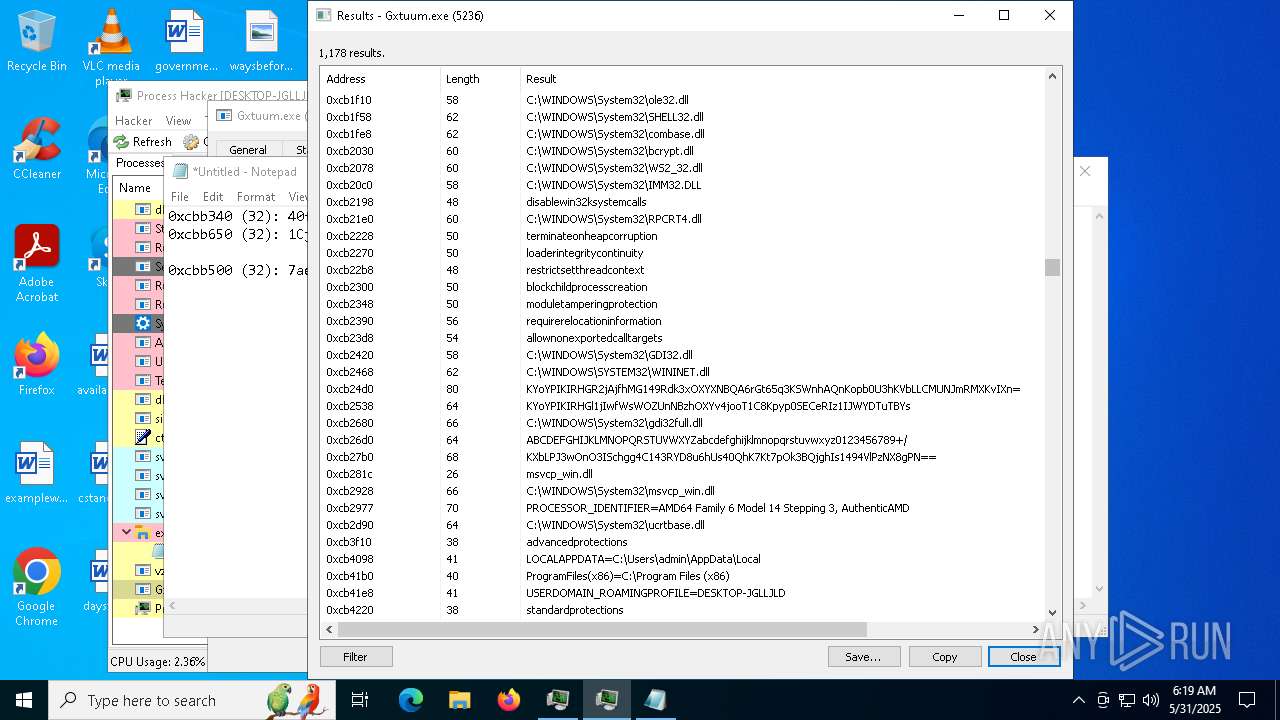
Amadey
(PID) Process(5236) Gxtuum.exe
C2185.81.68.156
URLhttp://185.81.68.156/jb87ejvjdsS/index.php
Version5.30
Options
Drop directoryf917d25a84
Drop nameGxtuum.exe
Strings (125)2025
0000043f
S-%lu-
rundll32.exe
-%lu
og:
\App
AVG
ProductName
exe
SYSTEM\ControlSet001\Services\BasicDisplay\Video
WinDefender
d1
f917d25a84
"taskkill /f /im "
--
&&
<d>
\0000
av:
lv:
&unit=
ComputerName
GET
185.81.68.156
00000423
sd:
360TotalSecurity
random
Gxtuum.exe
5.30
Startup
SOFTWARE\Microsoft\Windows NT\CurrentVersion
Sophos
Programs
-executionpolicy remotesigned -File "
/jb87ejvjdsS/index.php
.jpg
cred.dll|clip.dll|
Comodo
rundll32
Powershell.exe
clip.dll
" && timeout 1 && del
%USERPROFILE%
pc:
------
Rem
:::
dm:
------
ar:
SYSTEM\CurrentControlSet\Control\UnitedVideo\CONTROL\VIDEO\
e2
AVAST Software
=
Keyboard Layout\Preload
st=s
ProgramData\
e3
?scr=1
#
cmd
Content-Disposition: form-data; name="data"; filename="
00000419
wb
r=
ps1
SOFTWARE\Microsoft\Windows\CurrentVersion\Run
Bitdefender
DefaultSettings.YResolution
vs:
+++
/Plugins/
e1
"
Content-Type: application/octet-stream
abcdefghijklmnopqrstuvwxyz0123456789-_
dll
Kaspersky Lab
id:
kernel32.dll
msi
&& Exit"
ESET
/k
Panda Security
DefaultSettings.XResolution
00000422
SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Shell Folders
http://
https://
/quiet
<c>
rb
Content-Type: application/x-www-form-urlencoded
|
cred.dll
shutdown -s -t 0
CurrentBuild
shell32.dll
Content-Type: multipart/form-data; boundary=----
\
POST
GetNativeSystemInfo
2022
SYSTEM\CurrentControlSet\Control\ComputerName\ComputerName
un:
-unicode-
2019
VideoID
Doctor Web
Avira
bi:
%-lu
SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce
os:
SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\User Shell Folders
zip
Norton
Main
" && ren
2016
cmd /C RMDIR /s/q
0123456789
"
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (46.3) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (41) |
| .exe | | | Win32 Executable (generic) (6.6) |
| .exe | | | Generic Win/DOS Executable (2.9) |
| .exe | | | DOS Executable Generic (2.9) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:03:20 13:28:25+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.4 |
| CodeSize: | 123392 |
| InitializedDataSize: | 1857024 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x5f88 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.2.1.1 |
| ProductVersionNumber: | 3.1.1.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Software |
| FileDescription: | Software |
| FileVersion: | 6.0.0.0 |
| InternalName: | Software.exe |
| LegalCopyright: | (C) 2026 |
| OriginalFileName: | Software.exe |
| ProductName: | Software |
| ProductVersion: | 3.1.1.1 |
Total processes
177
Monitored processes
45
Malicious processes
8
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 660 | "C:\Users\admin\AppData\Local\Temp\f917d25a84\Gxtuum.exe" | C:\Users\admin\AppData\Local\Temp\f917d25a84\Gxtuum.exe | — | svchost.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 900 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "--disable-features=OptimizationGuideModelDownloading,OptimizationHintsFetching,OptimizationTargetPrediction,OptimizationHints" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1040 | "C:\Users\admin\AppData\Local\Temp\is-AU5IS.tmp\processhacker-2.39-setup.tmp" /SL5="$1E02C6,1874675,150016,C:\Users\admin\Downloads\processhacker-2.39-setup.exe" | C:\Users\admin\AppData\Local\Temp\is-AU5IS.tmp\processhacker-2.39-setup.tmp | — | processhacker-2.39-setup.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 1052 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1196 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1660 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=6824 --field-trial-handle=1964,i,13739407978511101592,12239278288388752116,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2088 | "C:\Users\admin\AppData\Local\Temp\f917d25a84\Gxtuum.exe" | C:\Users\admin\AppData\Local\Temp\f917d25a84\Gxtuum.exe | — | svchost.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2092 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.ProcessorMetrics --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4888 --field-trial-handle=1964,i,13739407978511101592,12239278288388752116,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2236 | "C:\Users\admin\AppData\Roaming\vzycvcxx.exe" | C:\Users\admin\AppData\Roaming\vzycvcxx.exe | Flasher.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: System Version: 6.0.0.1 Modules
| |||||||||||||||
Total events
20 277
Read events
20 015
Write events
246
Delete events
16
Modification events
| (PID) Process: | (7500) ezezeww.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\bbeecafdaeec |
| Operation: | write | Name: | CurrentPath |
Value: C:\Users\admin\AppData\Roaming\ezezeww.exe | |||
| (PID) Process: | (7500) ezezeww.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | bbeecafdaeec |
Value: "C:\ProgramData\bbeecafdaeec.exe" | |||
| (PID) Process: | (2236) vzycvcxx.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | SystemHandler |
Value: C:\Users\admin\AppData\Roaming\vzycvcxx.exe | |||
| (PID) Process: | (2236) vzycvcxx.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | SystemHandler |
Value: C:\ProgramData\svchost.exe | |||
| (PID) Process: | (5492) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | bbeecafdaeec |
Value: "C:\Users\admin\AppData\Roaming\ezezeww.exe" | |||
| (PID) Process: | (5492) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\bbeecafdaeec |
| Operation: | write | Name: | CurrentPath |
Value: C:\Users\admin\AppData\Roaming\ezezeww.exe | |||
| (PID) Process: | (5492) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\StartupApproved\Run |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (5492) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\StartupApproved\StartupFolder |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (5492) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | bbeecafdaeec |
Value: "C:\ProgramData\bbeecafdaeec.exe" | |||
| (PID) Process: | (5236) Gxtuum.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
Executable files
54
Suspicious files
317
Text files
34
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF120a78.TMP | — | |
MD5:— | SHA256:— | |||
| 900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old~RF120a78.TMP | — | |
MD5:— | SHA256:— | |||
| 900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF120a87.TMP | — | |
MD5:— | SHA256:— | |||
| 900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF120a87.TMP | — | |
MD5:— | SHA256:— | |||
| 900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF120a97.TMP | — | |
MD5:— | SHA256:— | |||
| 900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
23
TCP/UDP connections
125
DNS requests
118
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.20.245.139:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
3760 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7284 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4776 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/aevtvjsxpcrwhjvp5w32fej6zq_9.56.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.56.0_all_acq3rupi4ymeq53so4pzqroatfea.crx3 | unknown | — | — | whitelisted |
7284 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4776 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/aevtvjsxpcrwhjvp5w32fej6zq_9.56.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.56.0_all_acq3rupi4ymeq53so4pzqroatfea.crx3 | unknown | — | — | whitelisted |
4776 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/aevtvjsxpcrwhjvp5w32fej6zq_9.56.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.56.0_all_acq3rupi4ymeq53so4pzqroatfea.crx3 | unknown | — | — | whitelisted |
4776 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/aevtvjsxpcrwhjvp5w32fej6zq_9.56.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.56.0_all_acq3rupi4ymeq53so4pzqroatfea.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5608 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.20.245.139:80 | crl.microsoft.com | Akamai International B.V. | SE | whitelisted |
5496 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
3760 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3760 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
900 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
5492 | explorer.exe | 185.81.68.156:80 | — | Chang Way Technologies Co. Limited | RU | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| whitelisted |
www.google.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
encrypted-tbn0.gstatic.com |
| whitelisted |
login.live.com |
| whitelisted |