| File name: | 99c0e75f8605e8ca554aaa823b36b795097c54fc58bb14eb13e22beac0054d57 |
| Full analysis: | https://app.any.run/tasks/33a71ed6-6f07-45c5-b110-a36f0d4a00ea |
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | December 14, 2024, 01:17:23 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
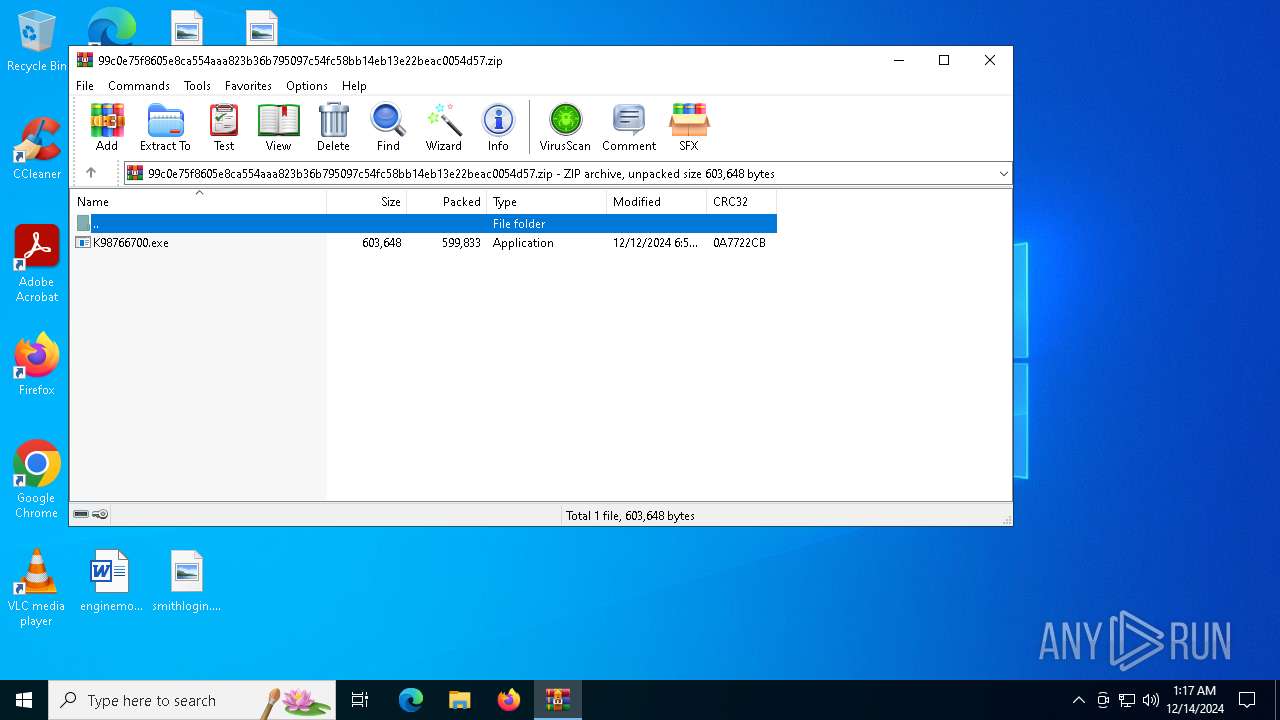
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 6BD15BA8E668389936424C0AE33AA249 |
| SHA1: | C462B8382500D499E840F95DFC9DBF3EDD635375 |
| SHA256: | 99C0E75F8605E8CA554AAA823B36B795097C54FC58BB14EB13E22BEAC0054D57 |
| SSDEEP: | 24576:QPvulErDBMyByPKn00v6+6k2f0bD7vHcSn8Pej1pFtbgMAh3agHTPa1oM8MC7Ue:QPvulErDBMyByPKn00v6+B2f0bD7vHcn |
MALICIOUS
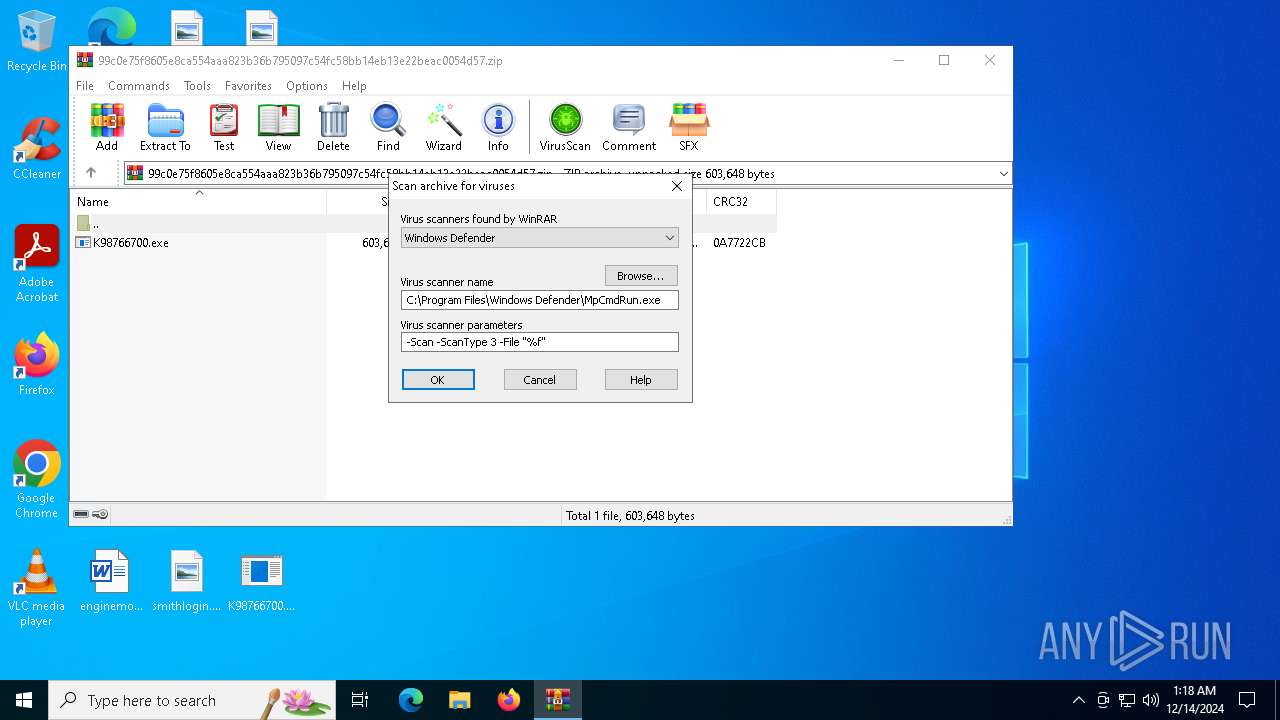
Generic archive extractor
- WinRAR.exe (PID: 3608)
Adds path to the Windows Defender exclusion list
- K98766700.exe (PID: 4188)
Actions looks like stealing of personal data
- InstallUtil.exe (PID: 4512)
Steals credentials from Web Browsers
- InstallUtil.exe (PID: 4512)
Connects to the CnC server
- InstallUtil.exe (PID: 4512)
AGENTTESLA has been detected (SURICATA)
- InstallUtil.exe (PID: 4512)
AGENTTESLA has been detected (YARA)
- InstallUtil.exe (PID: 4512)
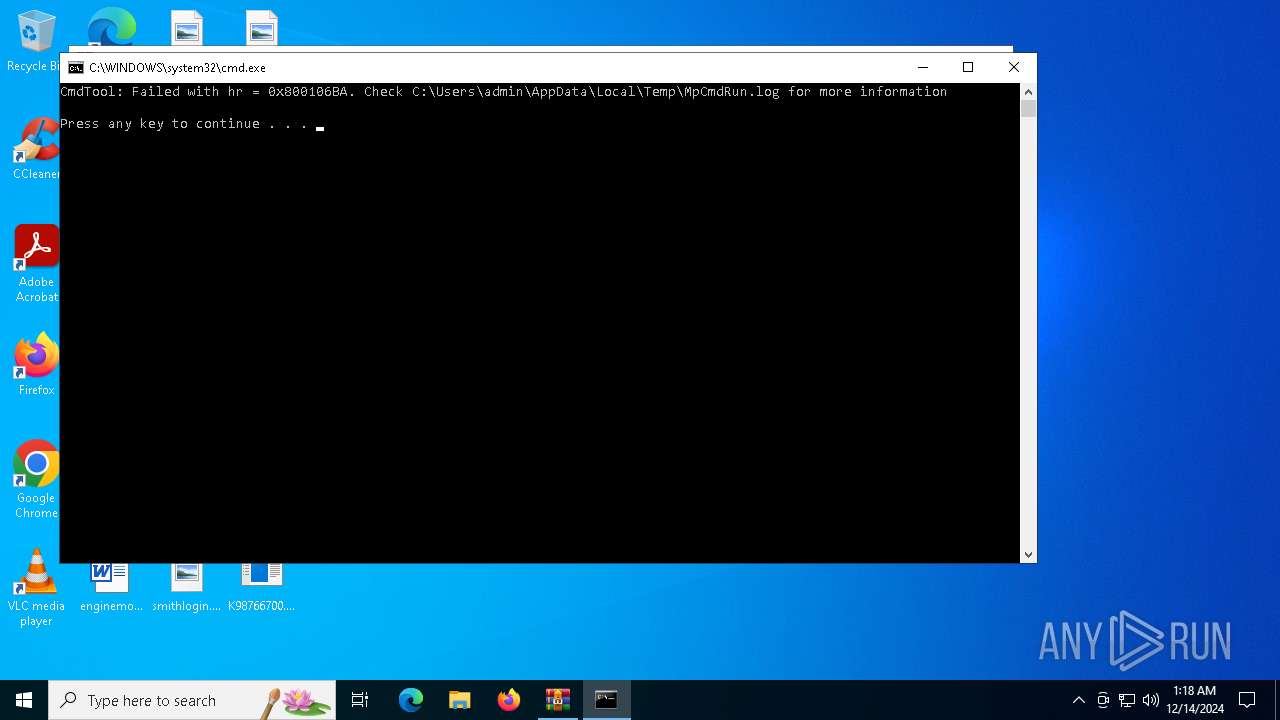
Antivirus name has been found in the command line (generic signature)
- MpCmdRun.exe (PID: 6352)
SUSPICIOUS
Reads security settings of Internet Explorer
- K98766700.exe (PID: 4188)
- WinRAR.exe (PID: 3608)
Reads the date of Windows installation
- K98766700.exe (PID: 4188)
Starts POWERSHELL.EXE for commands execution
- K98766700.exe (PID: 4188)
Script adds exclusion path to Windows Defender
- K98766700.exe (PID: 4188)
Executes application which crashes
- K98766700.exe (PID: 4188)
Checks for external IP
- svchost.exe (PID: 2192)
- InstallUtil.exe (PID: 4512)
Connects to FTP
- InstallUtil.exe (PID: 4512)
Connects to unusual port
- InstallUtil.exe (PID: 4512)
Starts CMD.EXE for commands execution
- WinRAR.exe (PID: 3608)
Executing commands from a ".bat" file
- WinRAR.exe (PID: 3608)
INFO
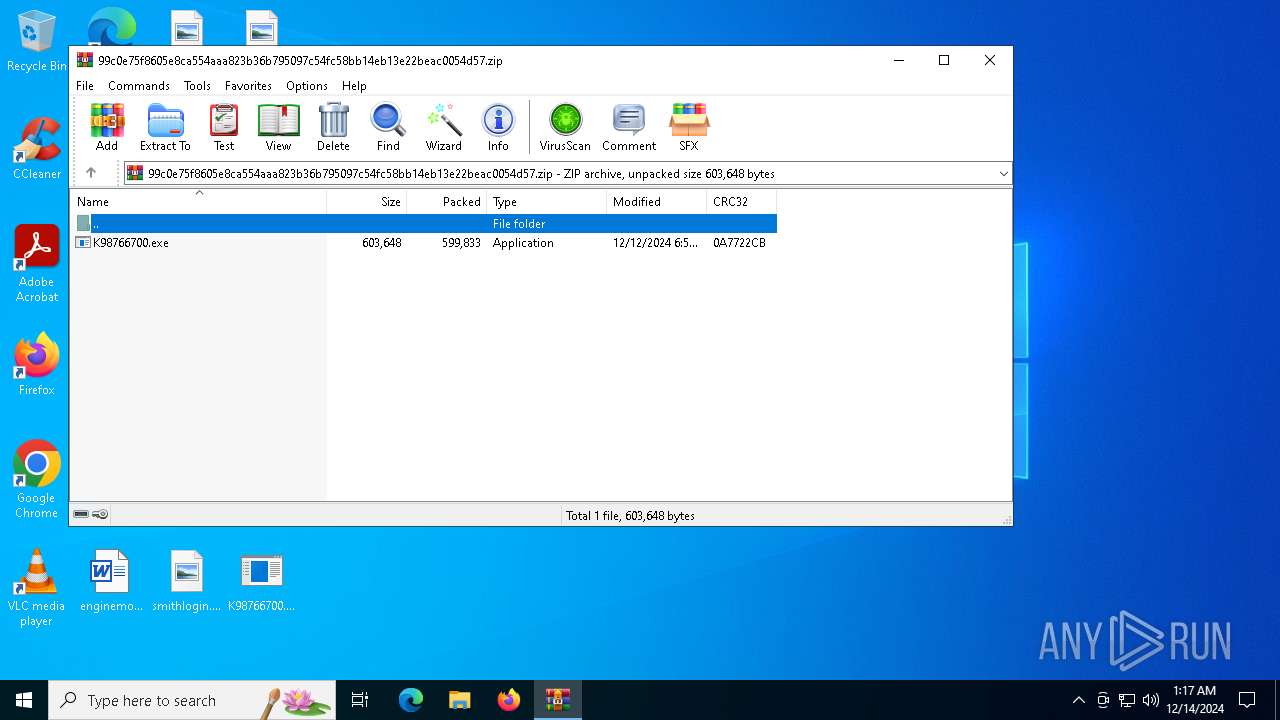
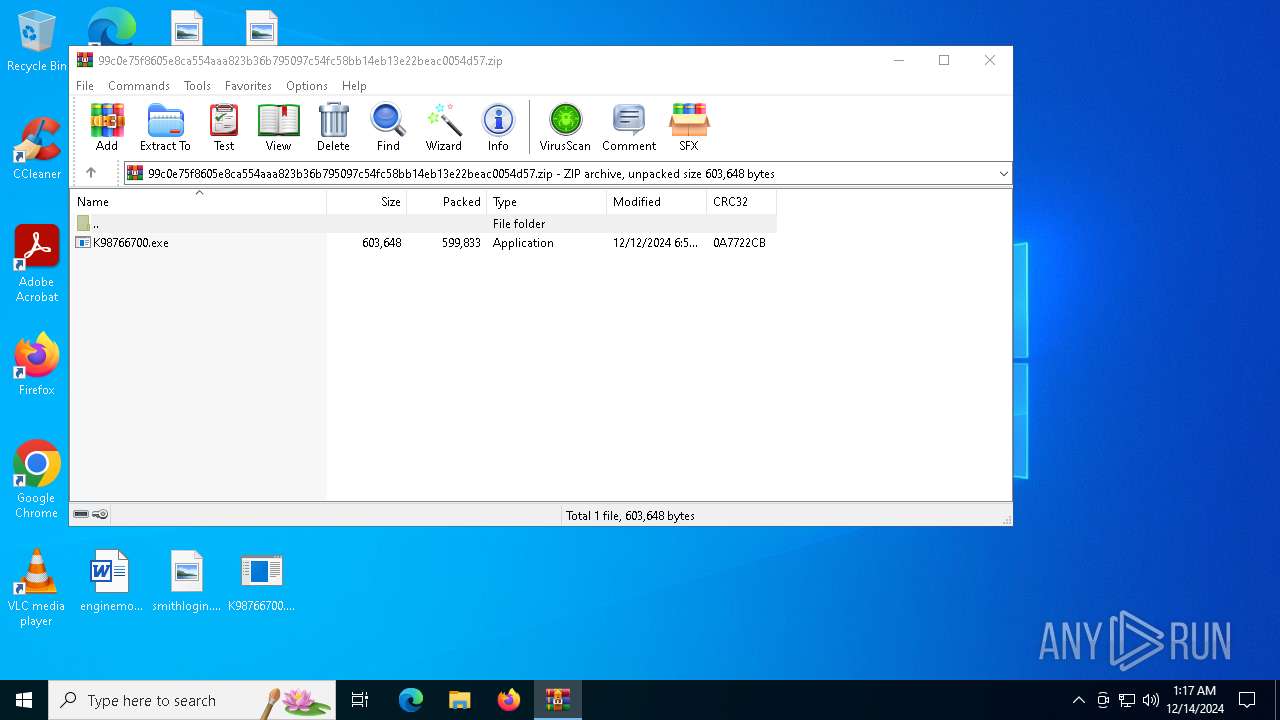
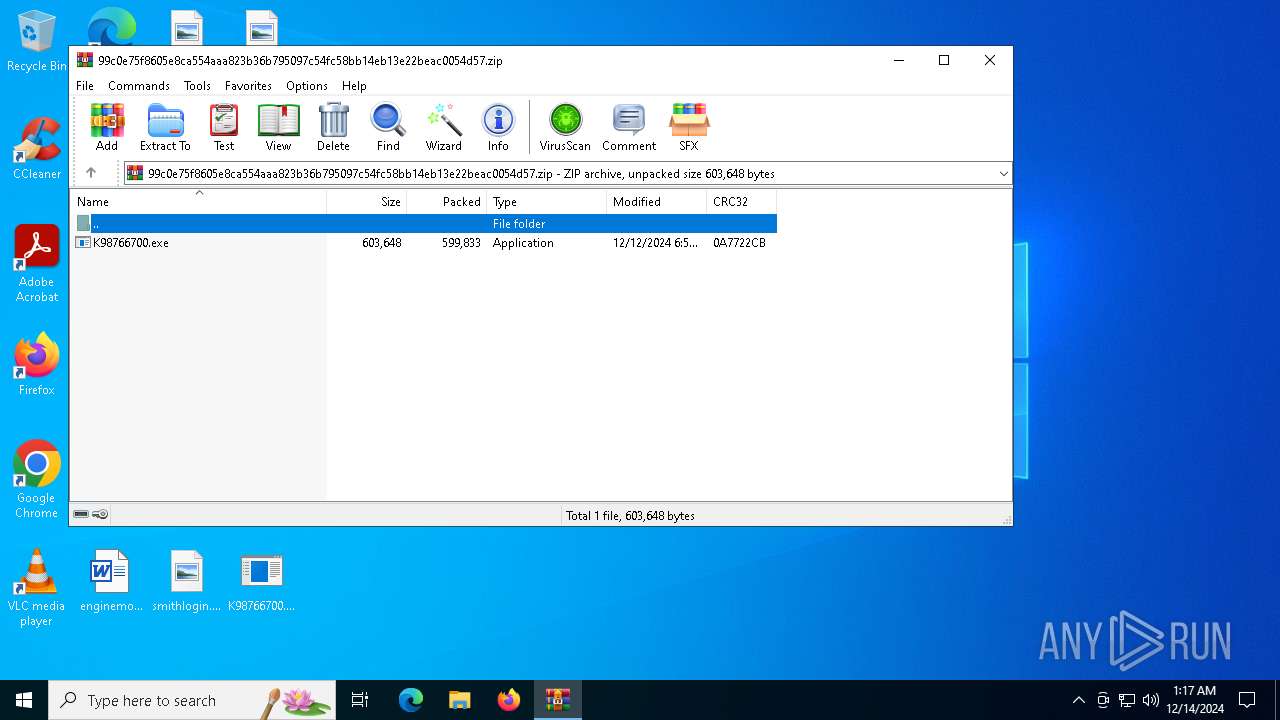
Manual execution by a user
- K98766700.exe (PID: 4188)
The process uses the downloaded file
- K98766700.exe (PID: 4188)
- WinRAR.exe (PID: 3608)
Process checks computer location settings
- K98766700.exe (PID: 4188)
Checks supported languages
- K98766700.exe (PID: 4188)
- InstallUtil.exe (PID: 4512)
- MpCmdRun.exe (PID: 6352)
Reads the machine GUID from the registry
- K98766700.exe (PID: 4188)
- InstallUtil.exe (PID: 4512)
Reads the computer name
- InstallUtil.exe (PID: 4512)
- MpCmdRun.exe (PID: 6352)
Checks proxy server information
- WerFault.exe (PID: 5916)
- InstallUtil.exe (PID: 4512)
Reads the software policy settings
- WerFault.exe (PID: 5916)
Creates files or folders in the user directory
- WerFault.exe (PID: 5916)
Disables trace logs
- InstallUtil.exe (PID: 4512)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 5588)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 5588)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3608)
Create files in a temporary directory
- MpCmdRun.exe (PID: 6352)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2024:12:12 18:58:20 |
| ZipCRC: | 0x0a7722cb |
| ZipCompressedSize: | 599833 |
| ZipUncompressedSize: | 603648 |
| ZipFileName: | K98766700.exe |
Total processes
132
Monitored processes
12
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2512 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\installutil.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\InstallUtil.exe | — | K98766700.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: .NET Framework installation utility Exit code: 4294967295 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 3608 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\99c0e75f8605e8ca554aaa823b36b795097c54fc58bb14eb13e22beac0054d57.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 4188 | "C:\Users\admin\Desktop\K98766700.exe" | C:\Users\admin\Desktop\K98766700.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: ConsoleApplication2 Exit code: 3221226356 Version: 1.0.0.0 Modules
| |||||||||||||||
| 4512 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\installutil.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\InstallUtil.exe | K98766700.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: .NET Framework installation utility Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 5588 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" Add-MpPreference -ExclusionPath "C:\Users\admin\Desktop\K98766700.exe" -Force | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | K98766700.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5720 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\jsc.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\jsc.exe | — | K98766700.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: jsc.exe Version: 14.8.9037.0 built by: NET481REL1 | |||||||||||||||
| 5888 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5916 | C:\WINDOWS\system32\WerFault.exe -u -p 4188 -s 1796 | C:\Windows\System32\WerFault.exe | K98766700.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6280 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\Rar$VR3608.39405\Rar$Scan33775.bat" " | C:\Windows\System32\cmd.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
14 558
Read events
14 534
Write events
24
Delete events
0
Modification events
| (PID) Process: | (3608) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (3608) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (3608) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (3608) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\99c0e75f8605e8ca554aaa823b36b795097c54fc58bb14eb13e22beac0054d57.zip | |||
| (PID) Process: | (3608) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3608) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3608) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3608) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (4188) K98766700.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Notifications\Settings\Windows.SystemToast.SecurityAndMaintenance |
| Operation: | write | Name: | Enabled |
Value: 0 | |||
| (PID) Process: | (4512) InstallUtil.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\installutil_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
Executable files
1
Suspicious files
2
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5916 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportQueue\AppCrash_K98766700.exe_b42f30558af35465798edc7071f0d64132e69297_79343039_cbdf95f0-4ce2-41bc-b2c8-ba35e3cada47\Report.wer | — | |
MD5:— | SHA256:— | |||
| 5916 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\K98766700.exe.4188.dmp | — | |
MD5:— | SHA256:— | |||
| 5916 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER76E9.tmp.dmp | binary | |
MD5:466C63AD2C9F17F3855F0A37A3361F02 | SHA256:88D92351CE52686C0C39067B6E8C44B038D24D1F289AE34BA80DF436926FB5C0 | |||
| 5588 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_fk1oyfm3.gkc.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5916 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER796B.tmp.xml | xml | |
MD5:2DE7437823360240E536FDD6B3495FDB | SHA256:56B5CFBC2F4CB442E4FB839138A3B21C20966B356B120AA7599BBBB2B4D29026 | |||
| 3608 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR3608.39405\99c0e75f8605e8ca554aaa823b36b795097c54fc58bb14eb13e22beac0054d57.zip\K98766700.exe | executable | |
MD5:E39C7CF026DF55A909A7E18EEA93B027 | SHA256:B862FBE92F3DE0E033B66E3C9D3AFAD4D6FF41D8B3553094F66A98DB6BA59F0C | |||
| 5588 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:FA1CA69AE1D64385724E9CFFF861A6A2 | SHA256:453909CA0E238266796968A32763883B37218699D3EE8ABB6D271FEEE50E0BEB | |||
| 5588 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_zi0dk0ys.tz3.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6352 | MpCmdRun.exe | C:\Users\admin\AppData\Local\Temp\MpCmdRun.log | text | |
MD5:1D1B99AAEDF55DB30DDCC1D717816D59 | SHA256:1B68313335638C2B5A47DE54711F0CB393FD13ADC6703B4AA212C0B80DDC6547 | |||
| 5916 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER794B.tmp.WERInternalMetadata.xml | xml | |
MD5:0BDEAAAF623A251FDEEADD0BE5649861 | SHA256:5385F880CDCB6F9B4F34B21156EAADAF6B9B45199781D5D163AD4BE1EF34819E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
24
DNS requests
10
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
188 | svchost.exe | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
188 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4512 | InstallUtil.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/line/?fields=hosting | unknown | — | — | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
188 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 2.23.209.133:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.16.241.12:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
188 | svchost.exe | 2.16.241.12:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
188 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
5916 | WerFault.exe | 20.189.173.22:443 | watson.events.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
watson.events.data.microsoft.com |
| whitelisted |
ip-api.com |
| shared |
ftp.antoniomayol.com |
| unknown |
self.events.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
2192 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
4512 | InstallUtil.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup ip-api.com |
4512 | InstallUtil.exe | Device Retrieving External IP Address Detected | POLICY [ANY.RUN] External Hosting Lookup by ip-api |
4512 | InstallUtil.exe | A Network Trojan was detected | ET MALWARE AgentTesla Exfil via FTP |
4512 | InstallUtil.exe | Misc activity | INFO [ANY.RUN] FTP protocol command for uploading a file |
4512 | InstallUtil.exe | A Network Trojan was detected | STEALER [ANY.RUN] AgentTesla Exfiltration (raw TCP) |
4512 | InstallUtil.exe | A Network Trojan was detected | STEALER [ANY.RUN] AgentTesla Exfiltration (raw TCP) |
4512 | InstallUtil.exe | Misc activity | INFO [ANY.RUN] FTP server is ready for the new user |
2 ETPRO signatures available at the full report